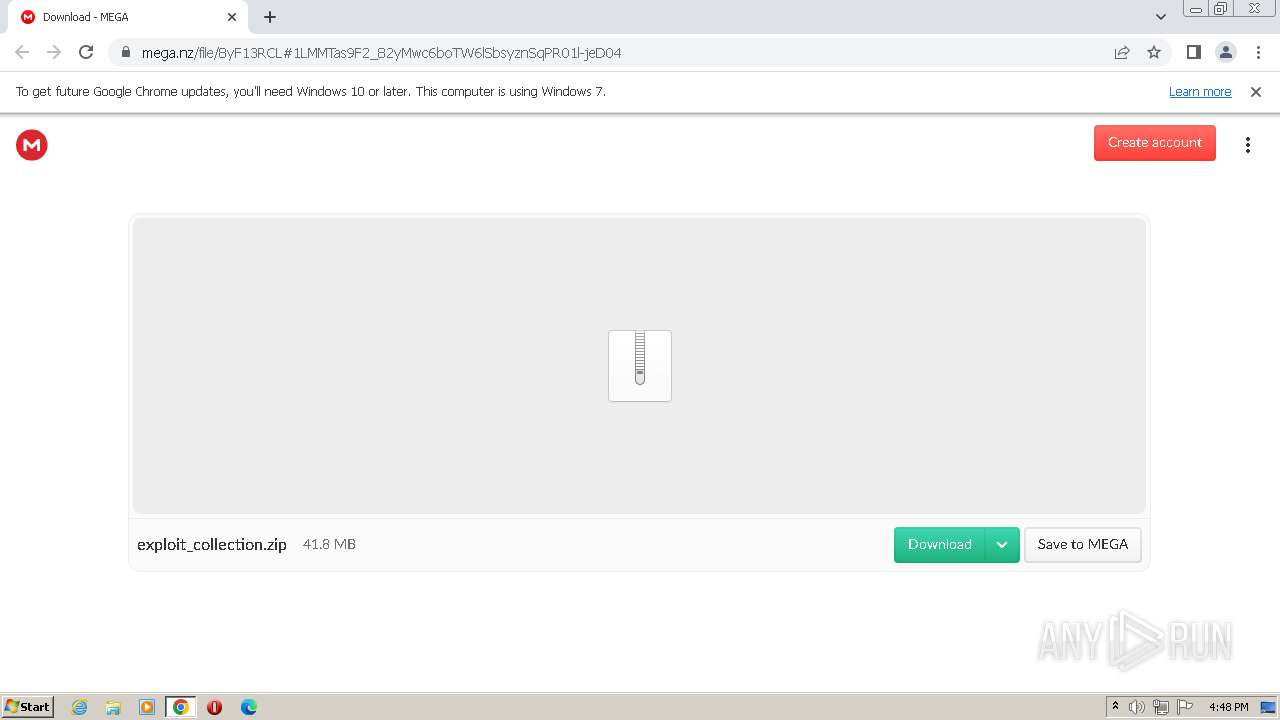
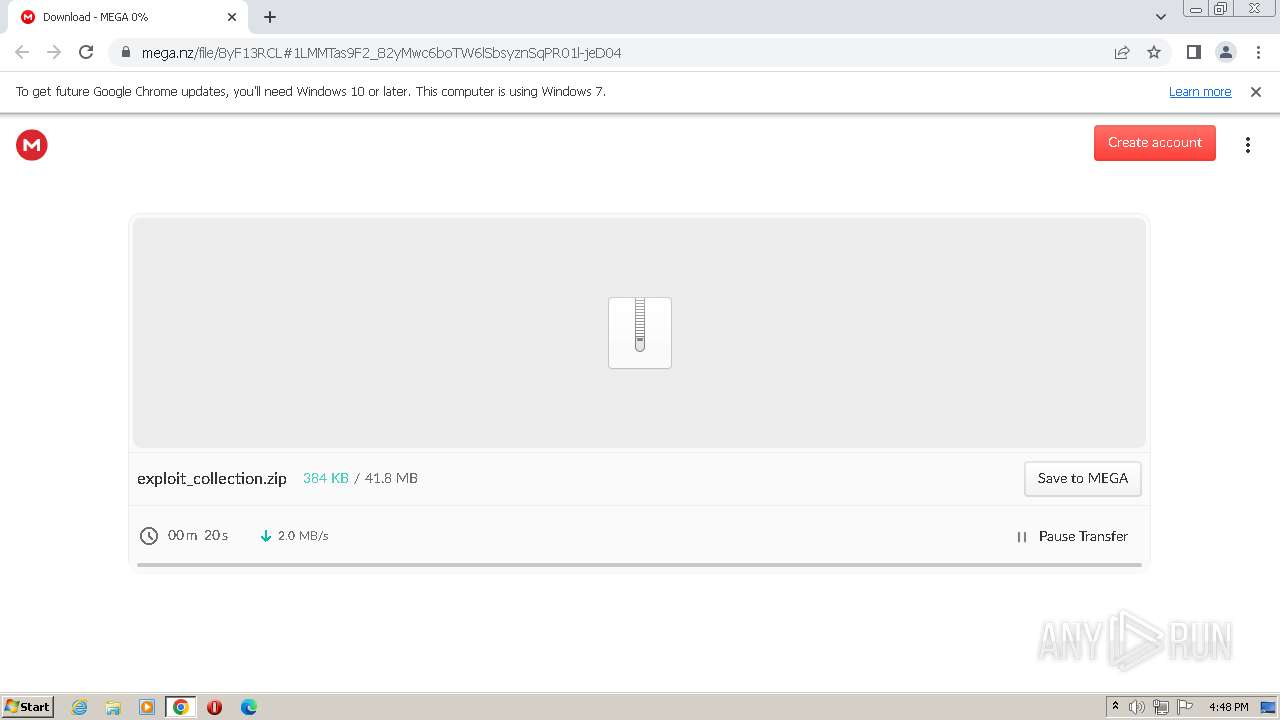
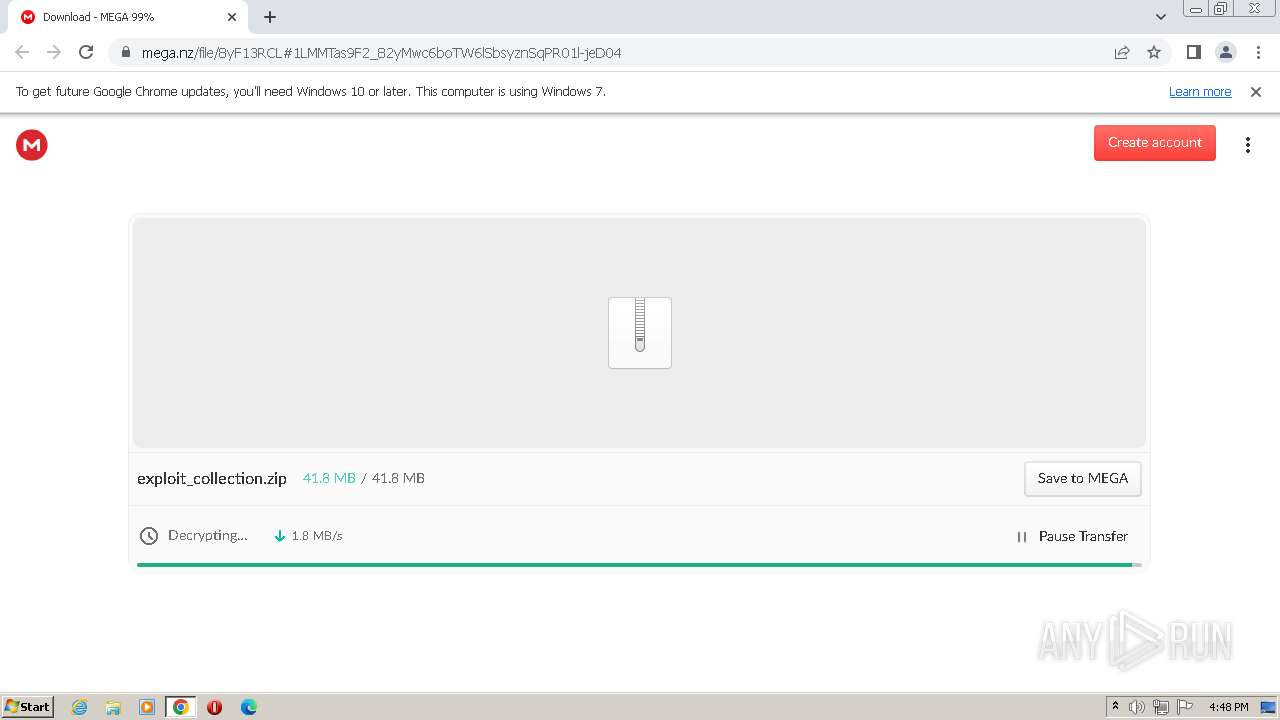
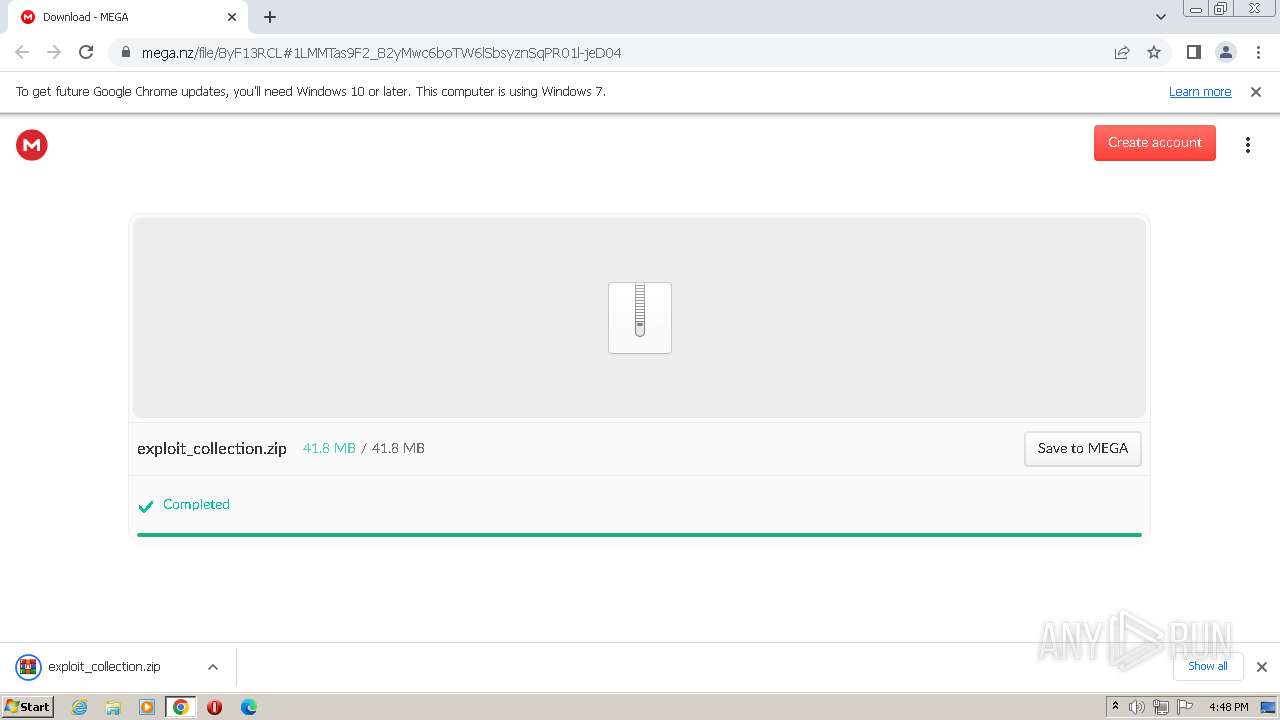
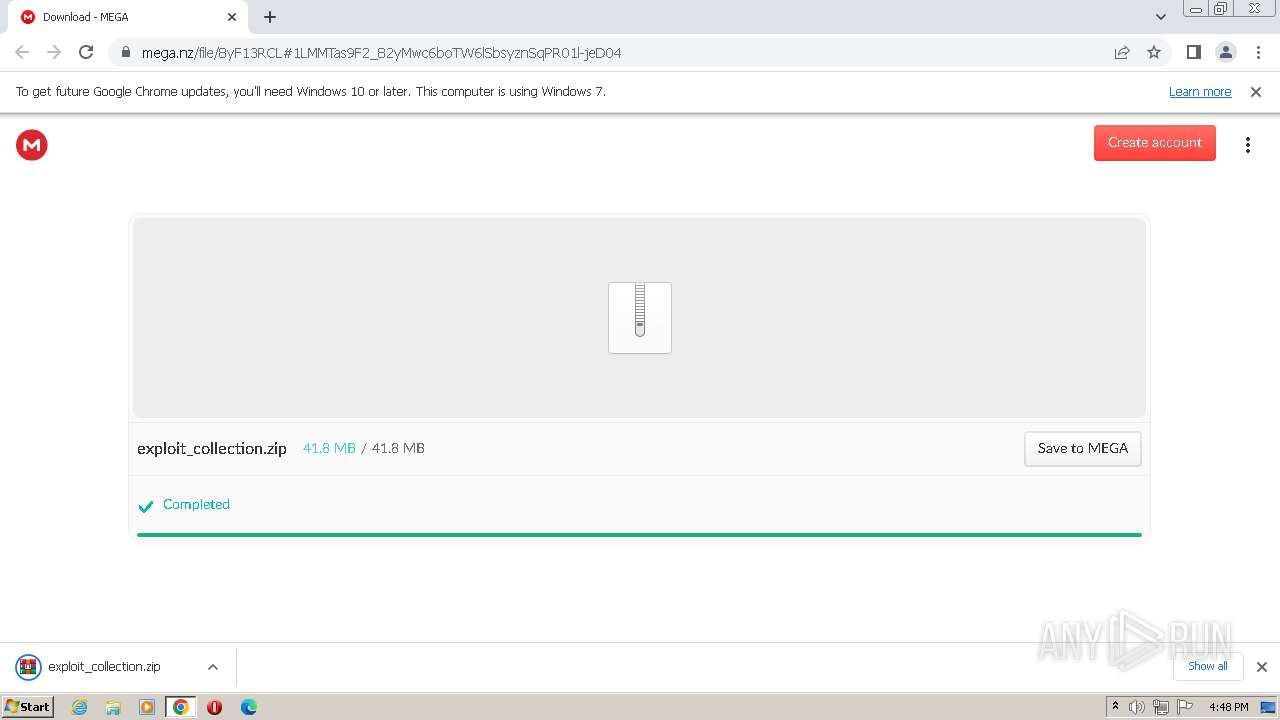
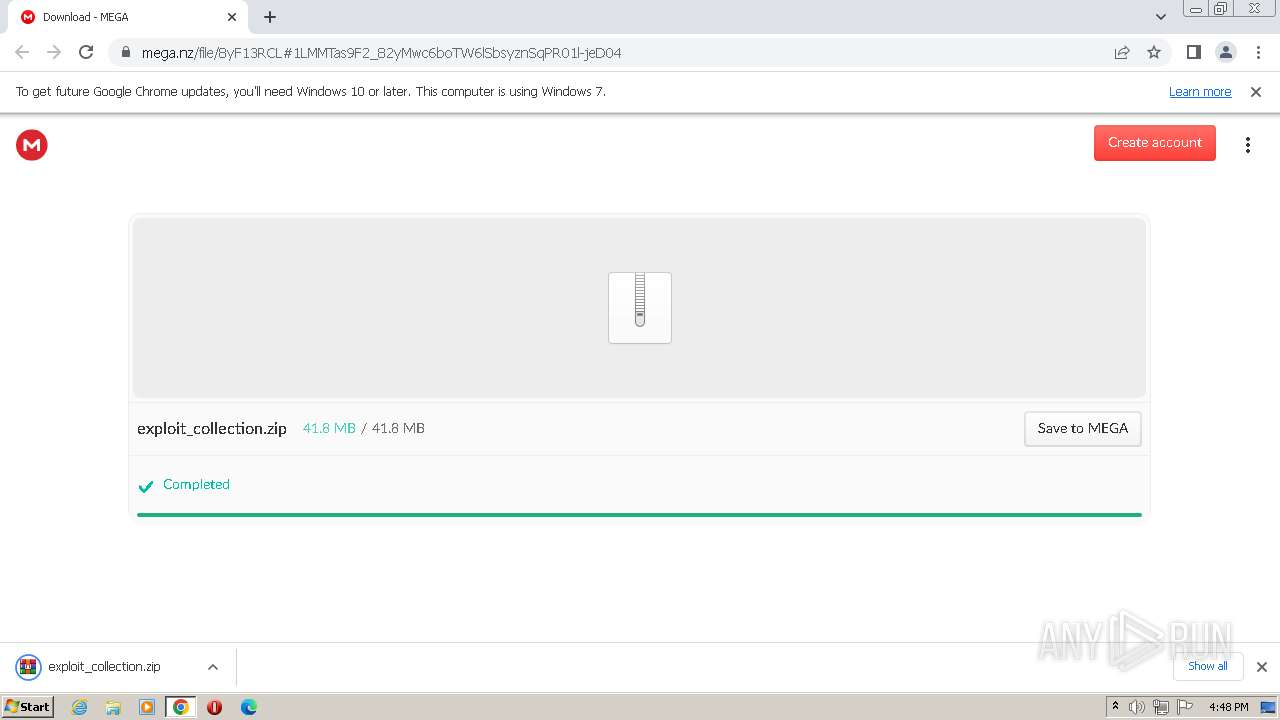
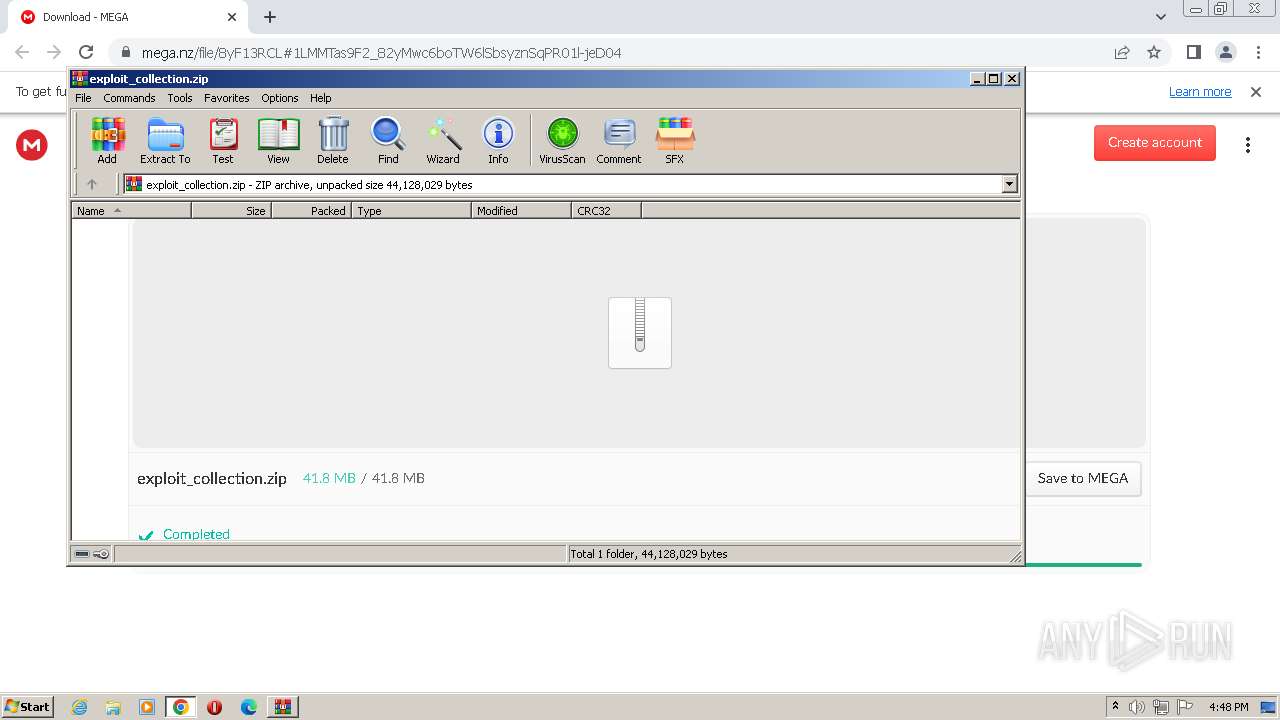
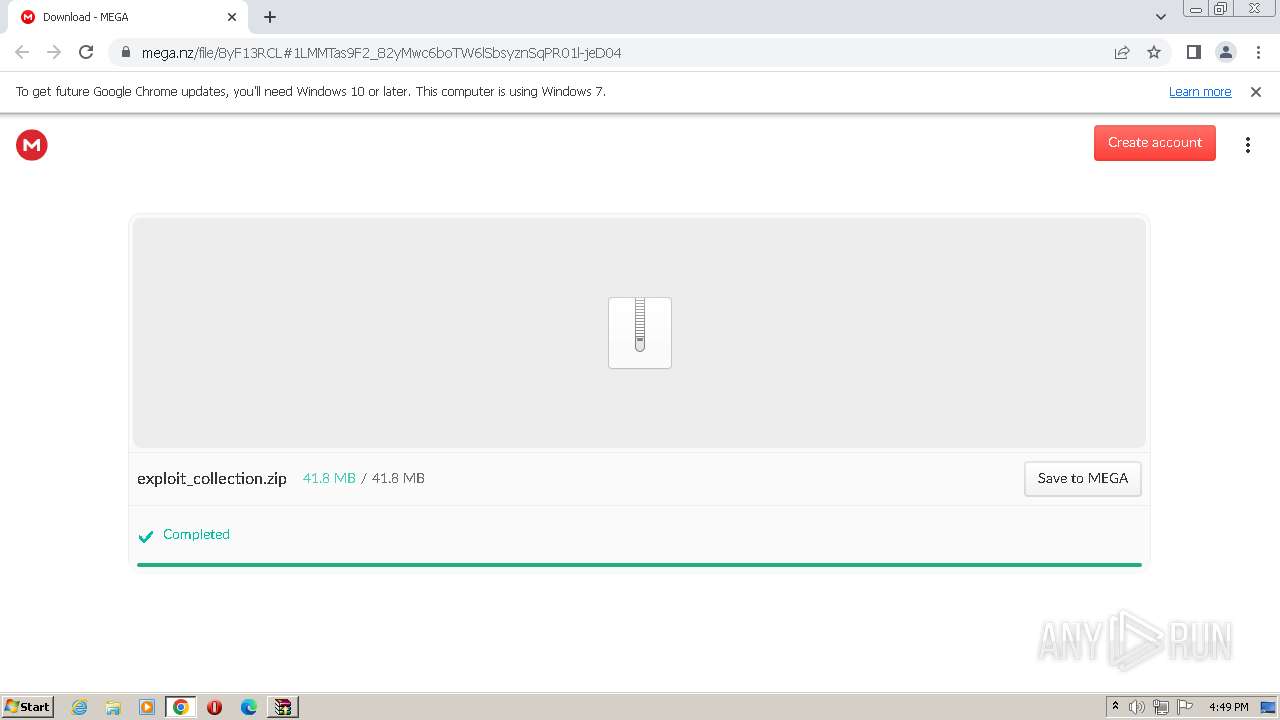
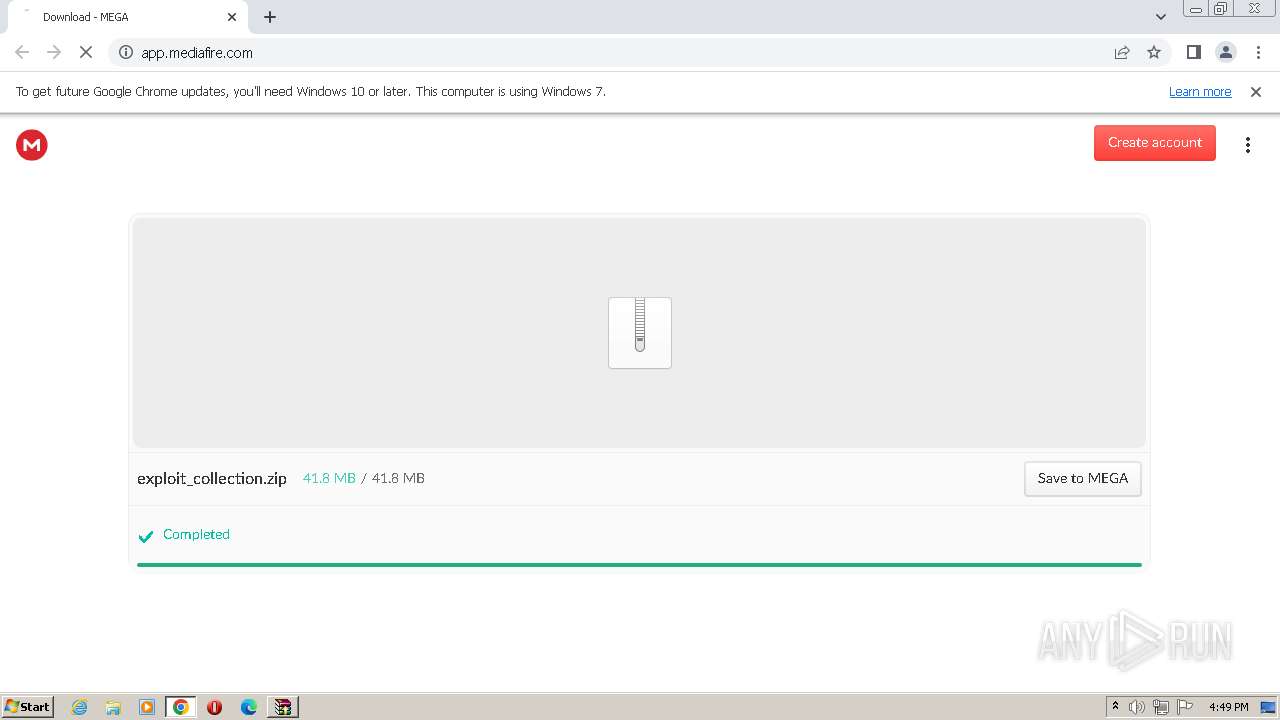
| URL: | https://mega.nz/file/8yF13RCL#1LMMTas9F2_82yMwc6boTW6lSbsyznSqPR01l-jeD04 |
| Full analysis: | https://app.any.run/tasks/ae268b90-ed8b-466f-9c3b-2291720de64f |
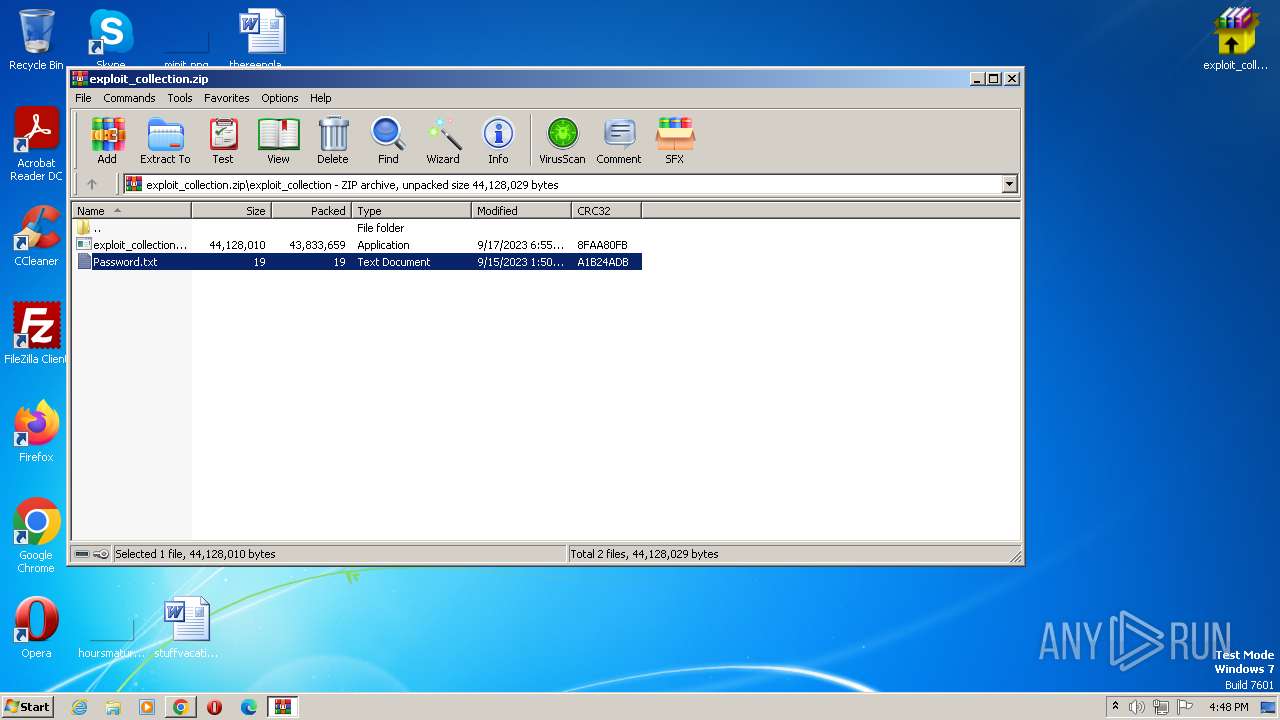
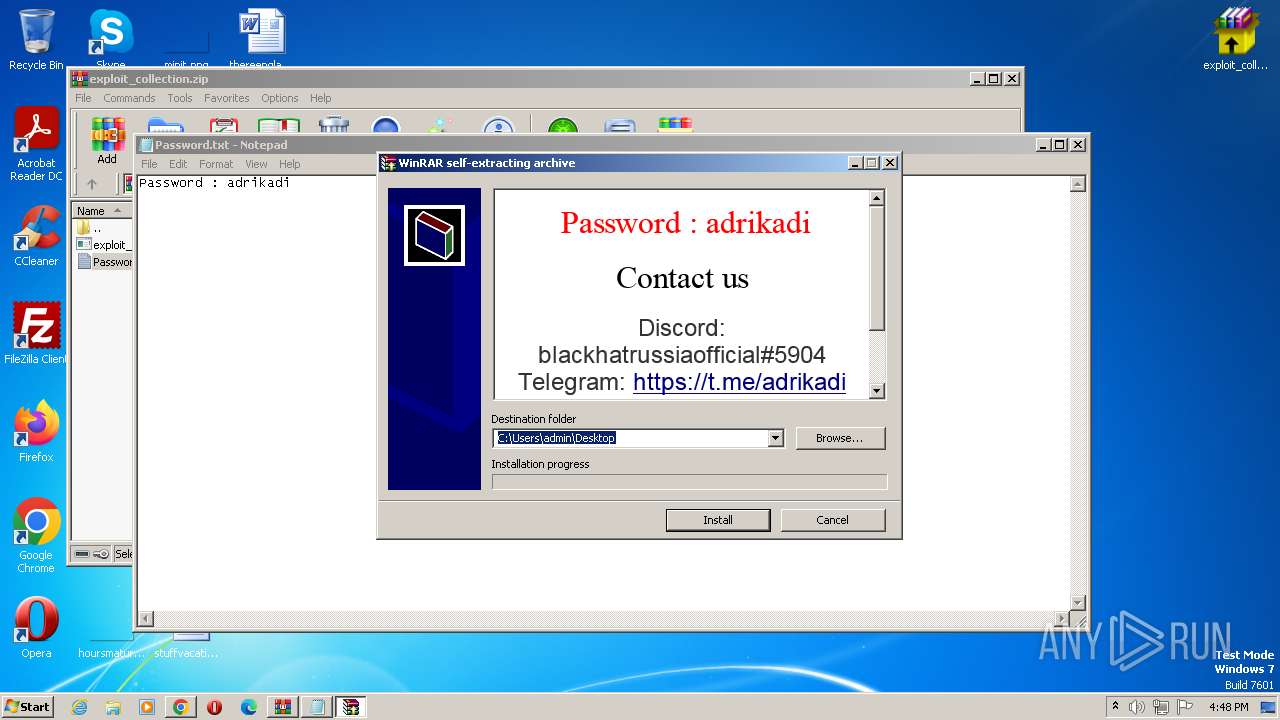
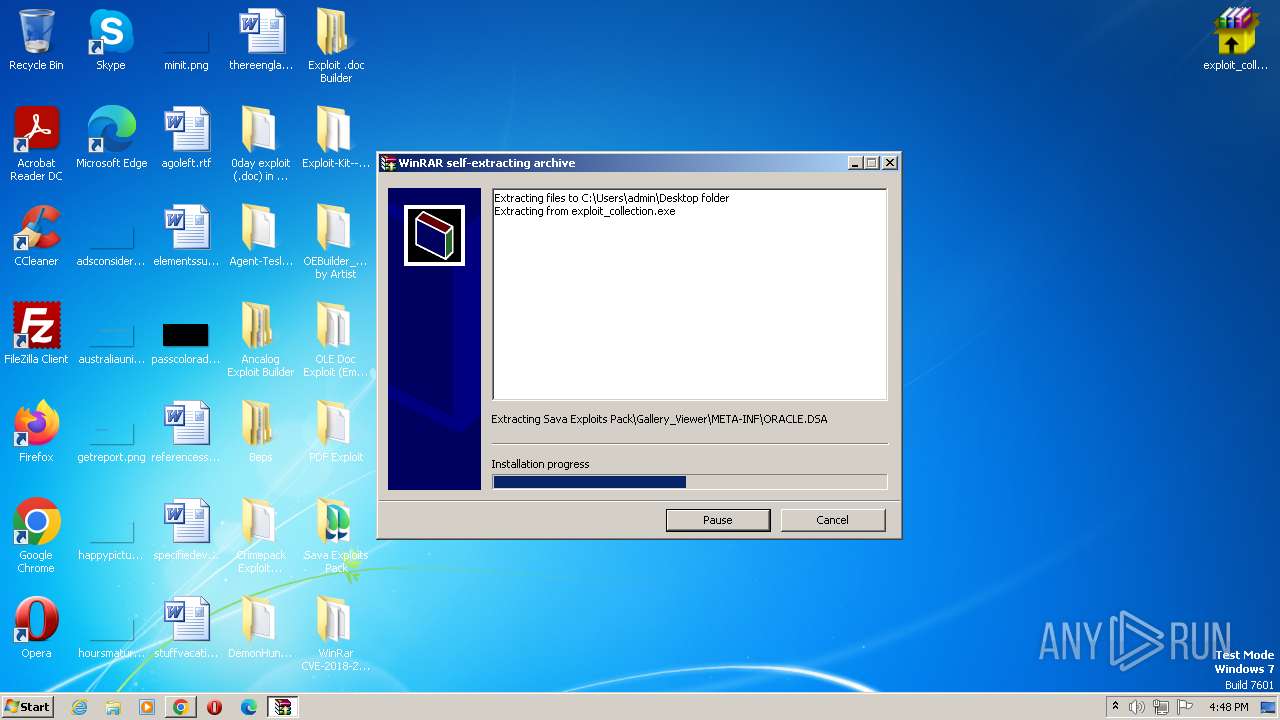
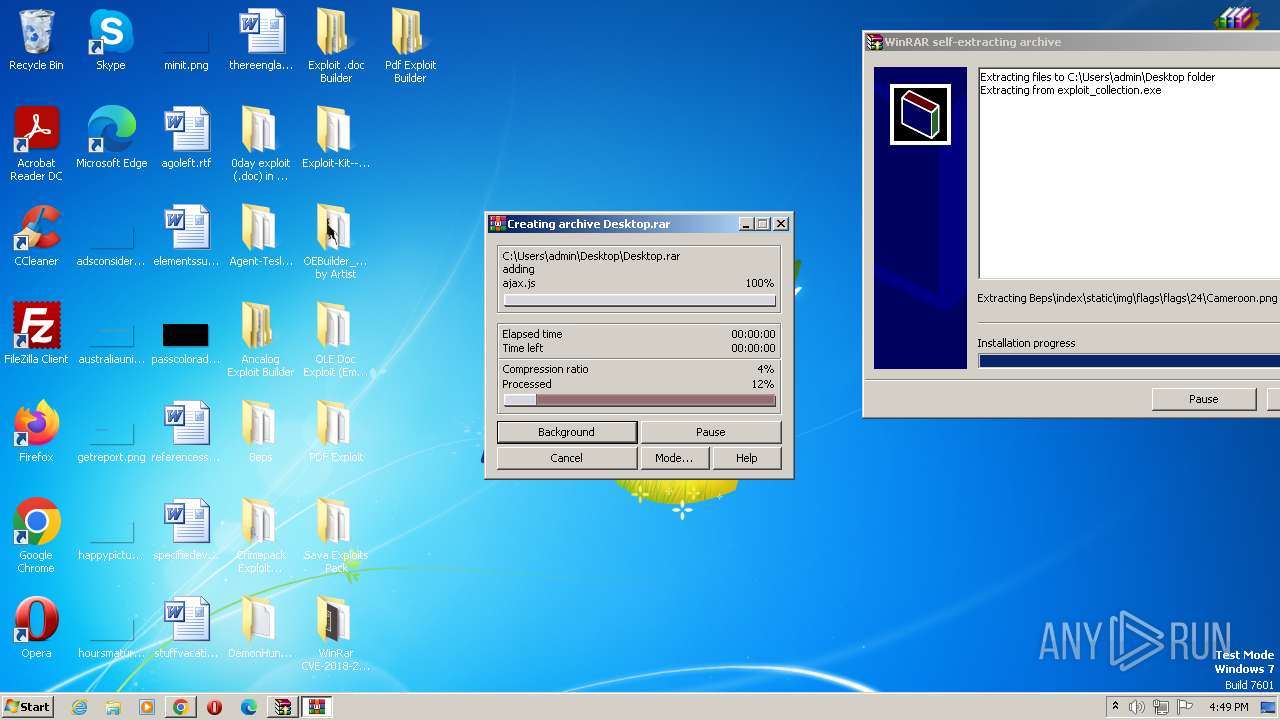
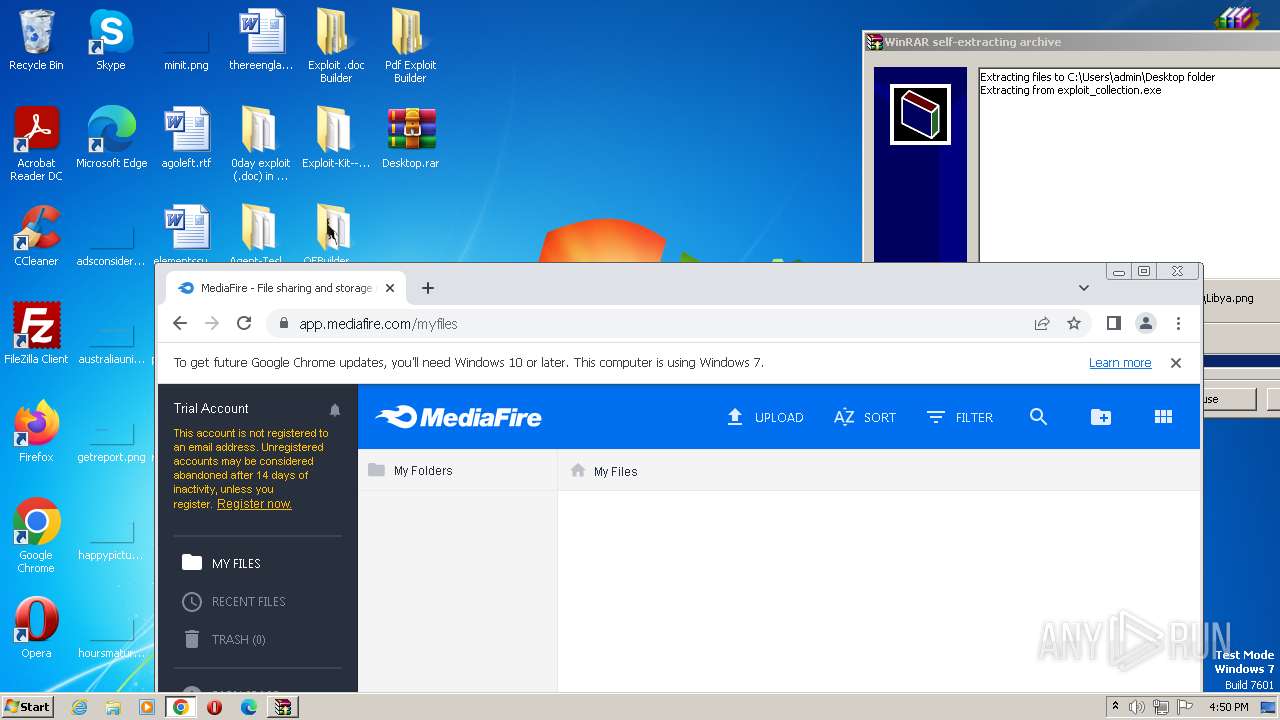
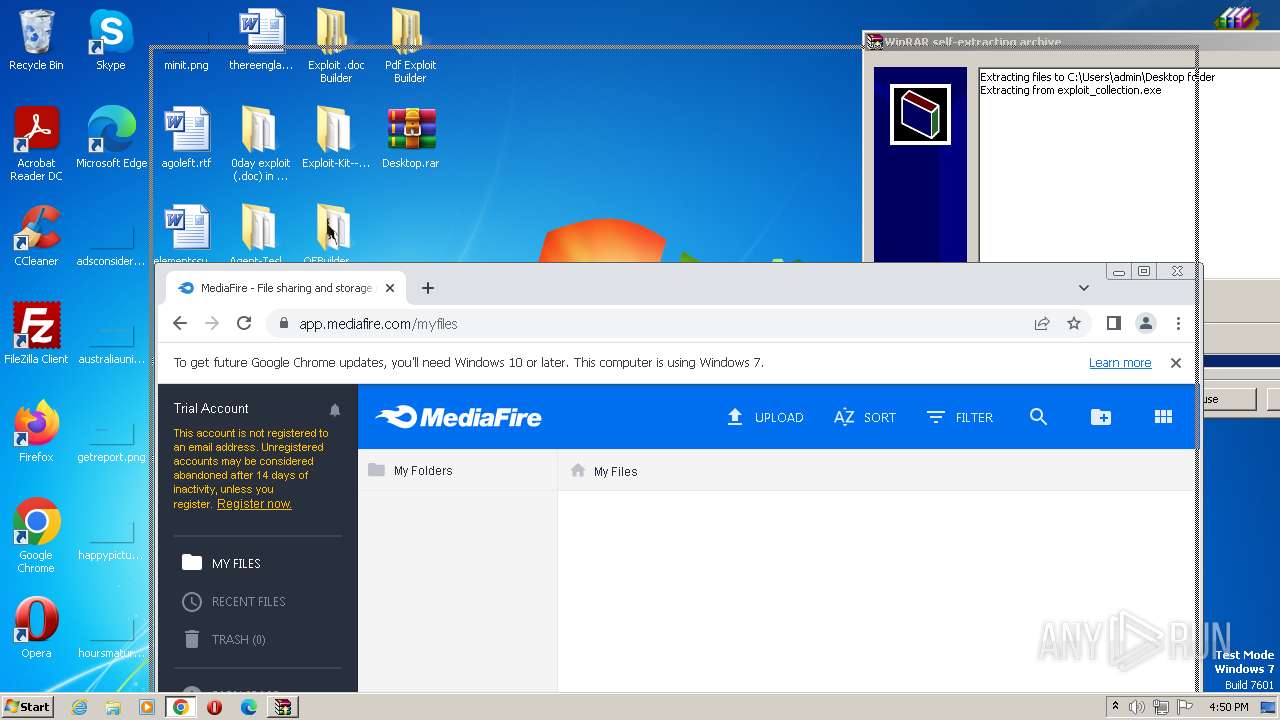
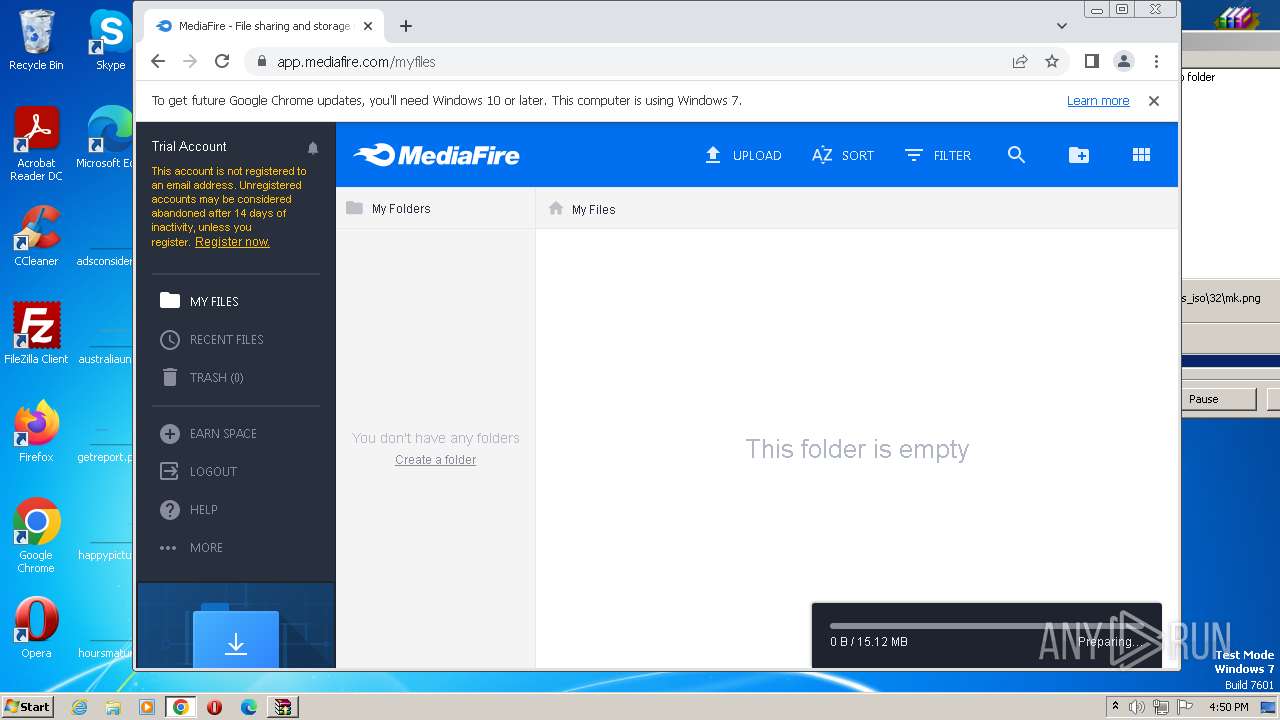
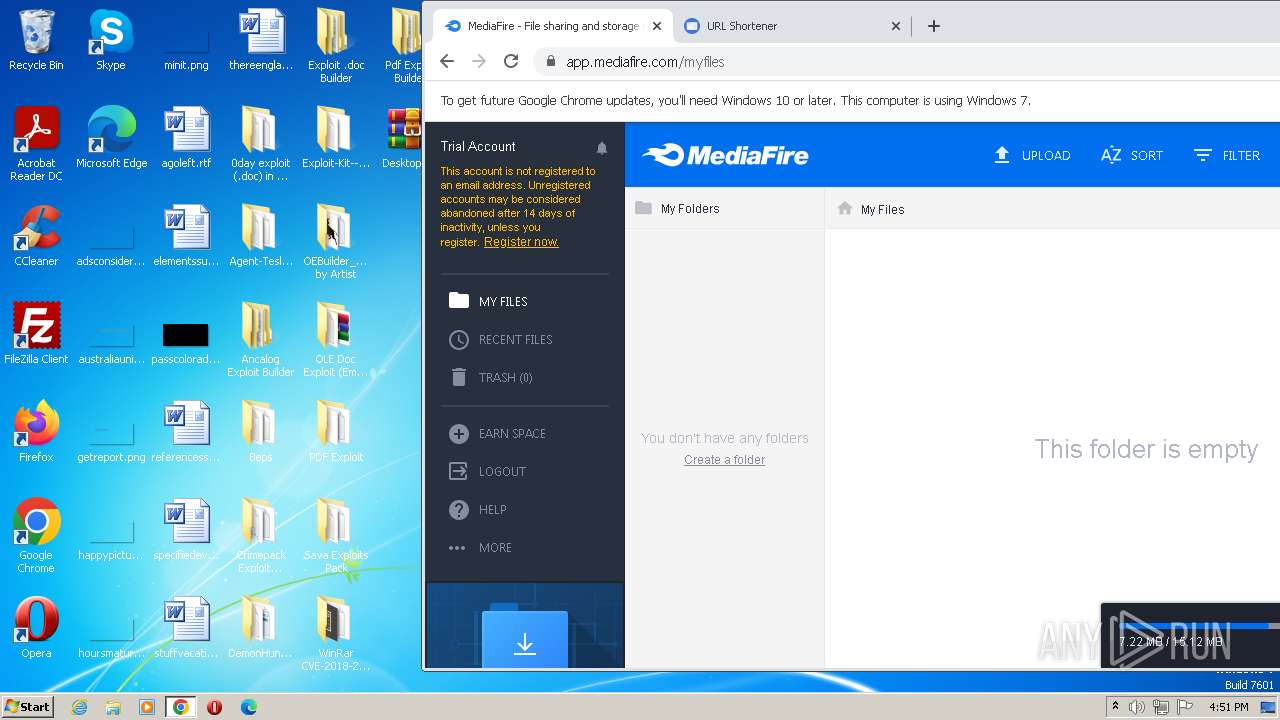
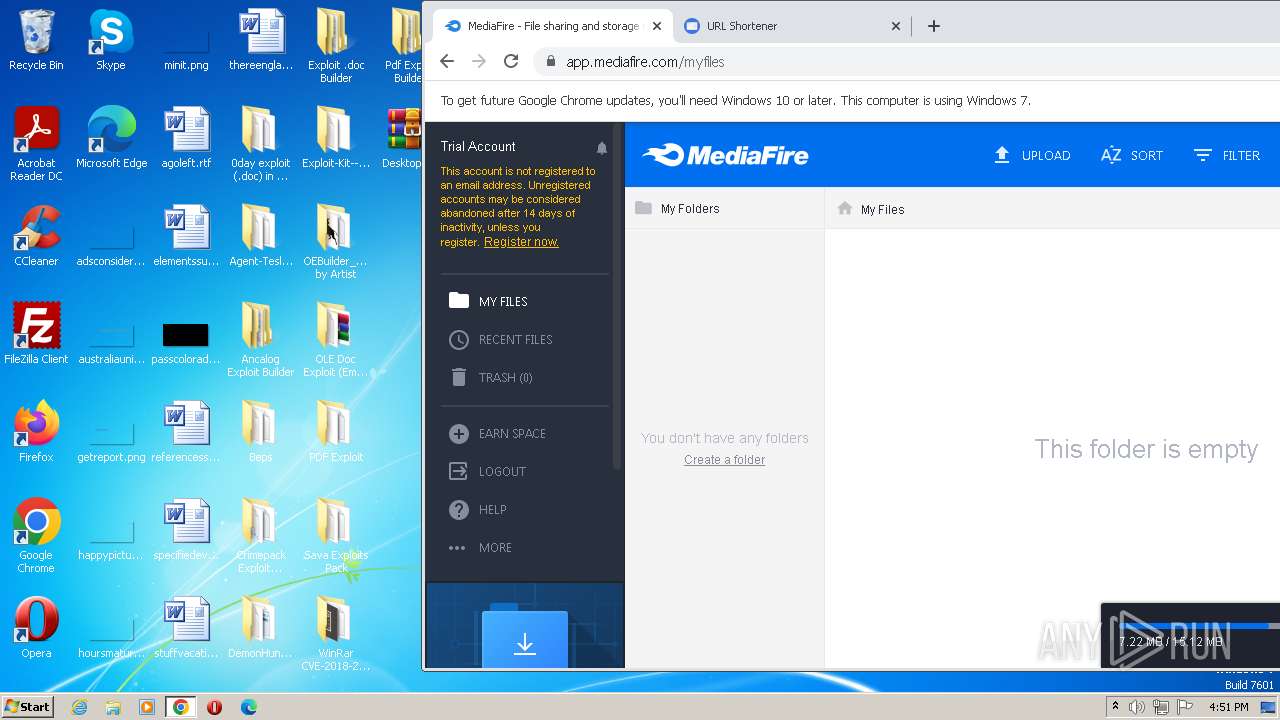
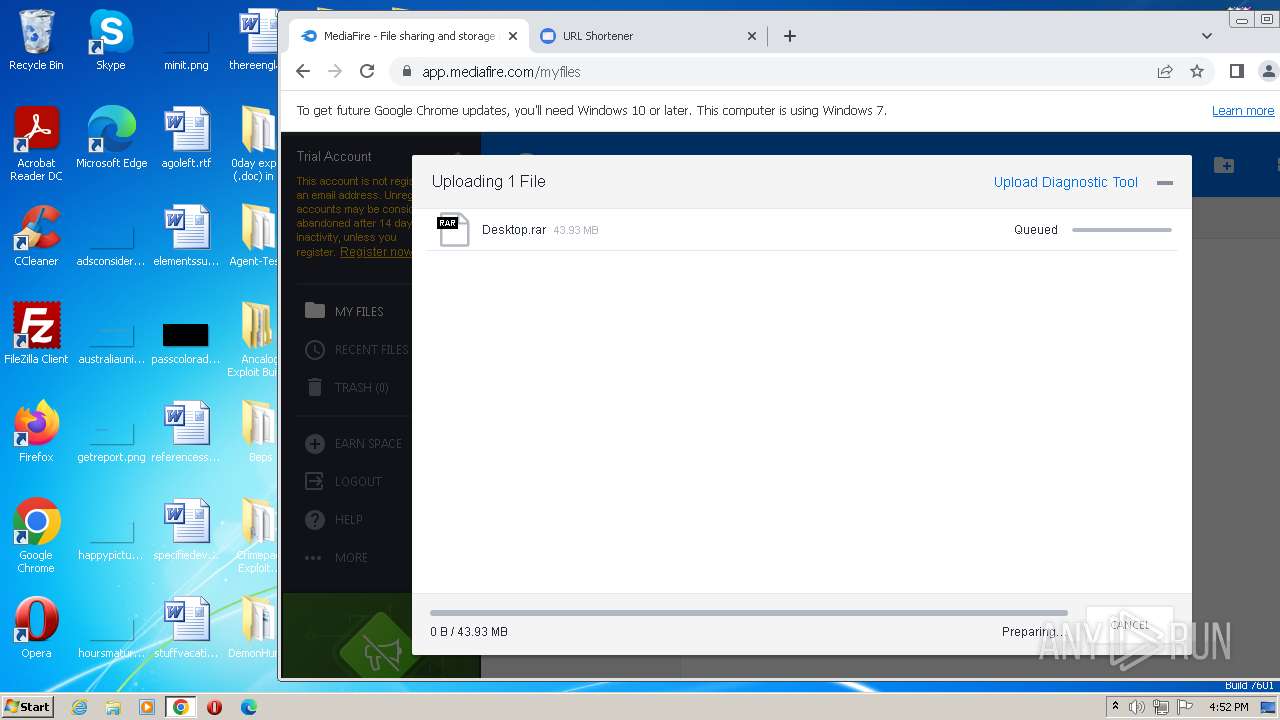
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2023, 15:47:31 |
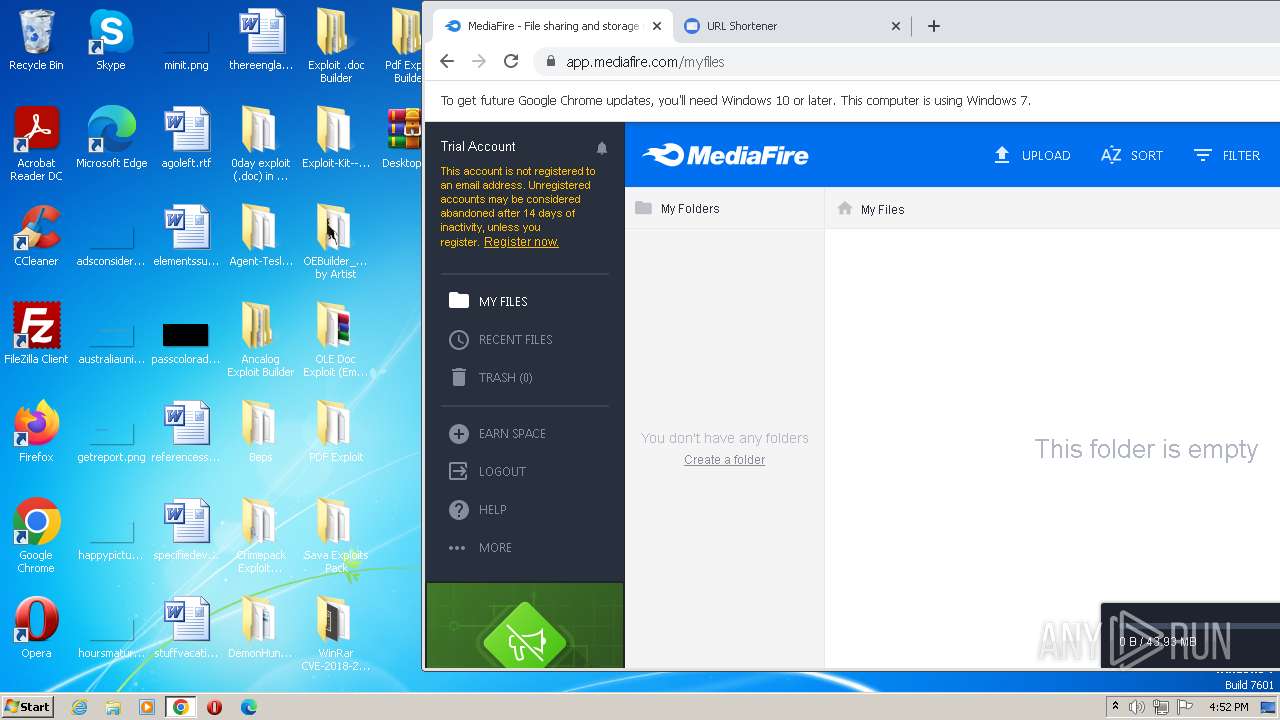
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3C76A81717128EE59159CB6BBDED687F |
| SHA1: | 813A4F3C8C50AA747B011CEFF13019C8BFF2C972 |
| SHA256: | 5BE499F4C1F53CD53643A0FD9AEE4BDC632F9EAA846D60DD3B962C04D680A8B3 |
| SSDEEP: | 3:N8X/icnWWJejXwZoAOfLz1HA:2tTwjXwIfXW |
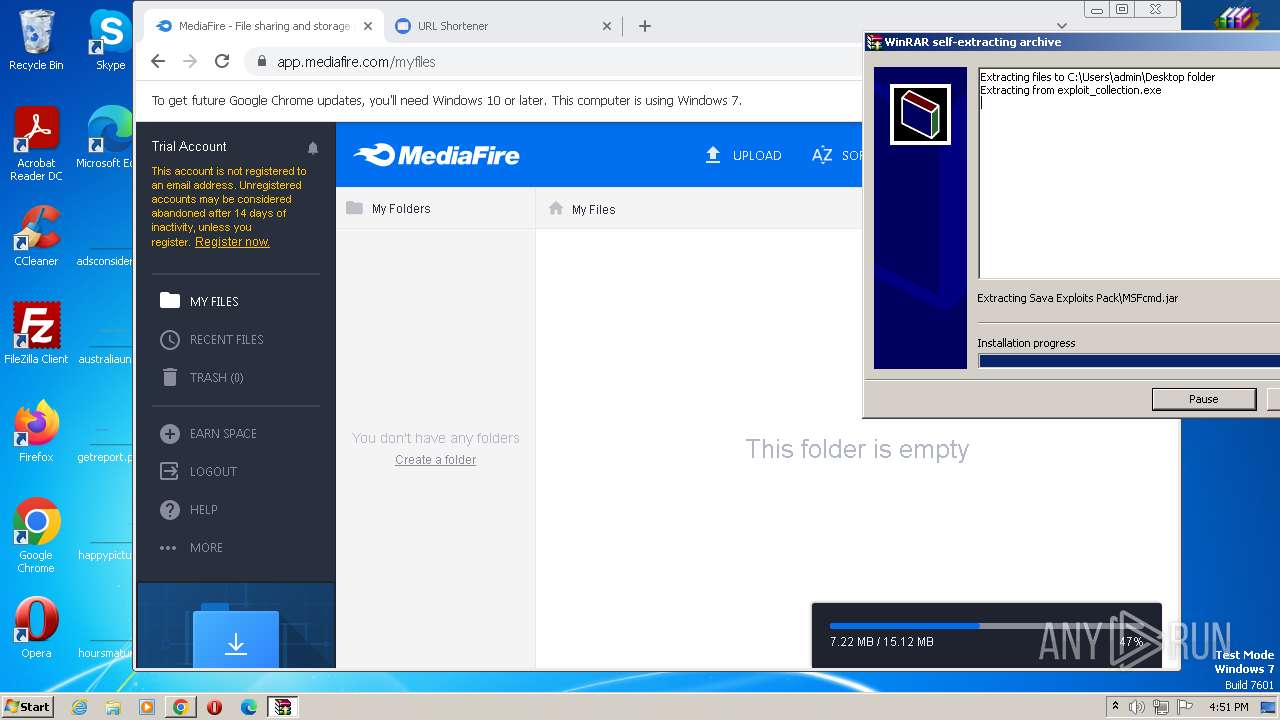
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- exploit_collection.exe (PID: 3276)
- HelpPane.exe (PID: 2896)
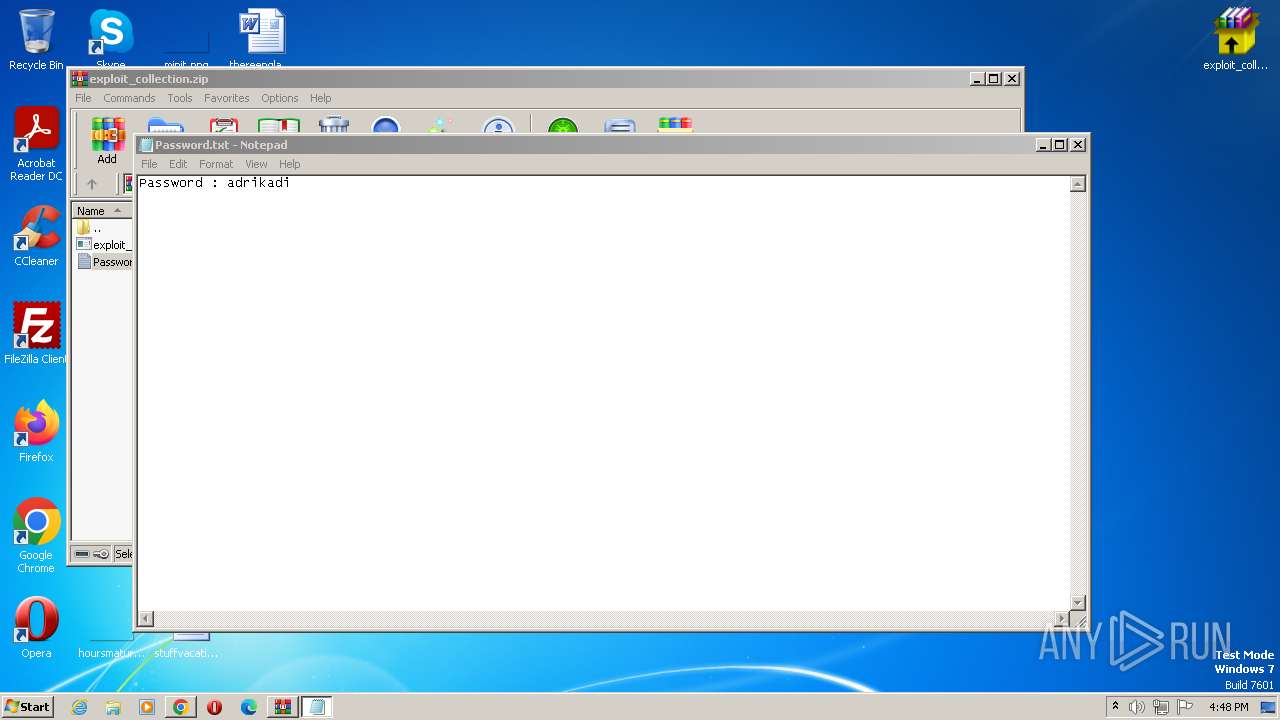
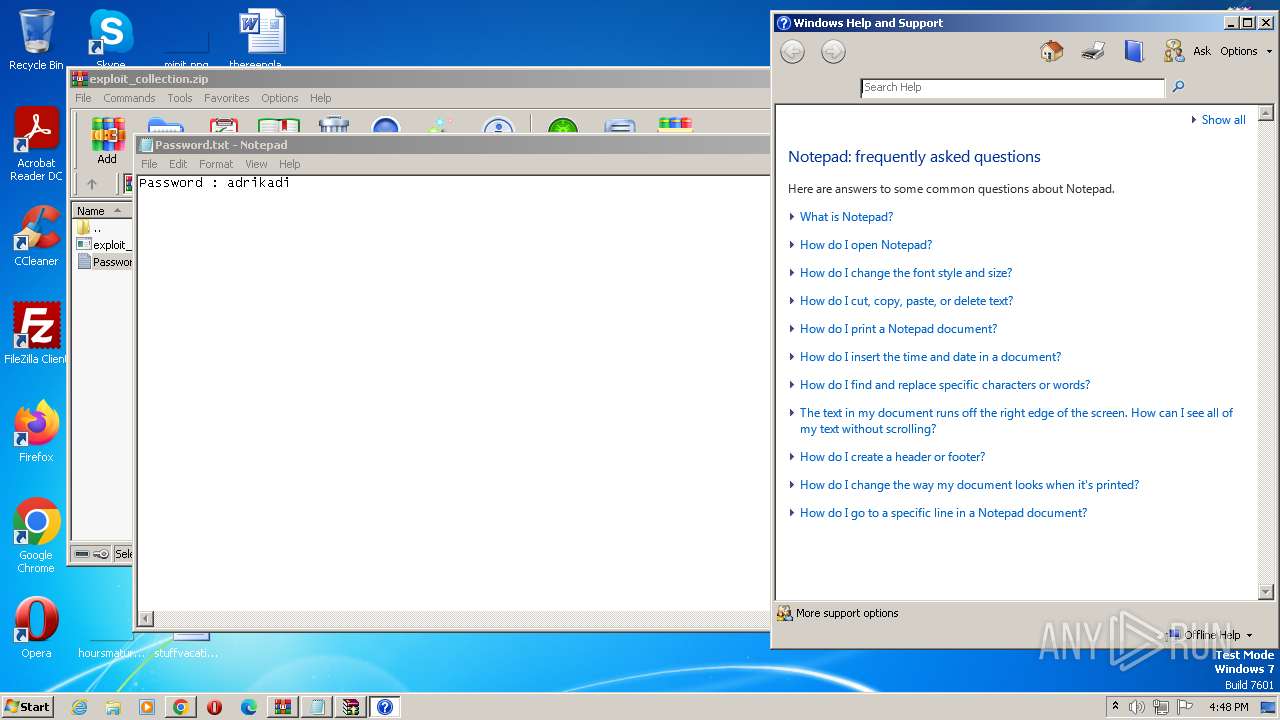
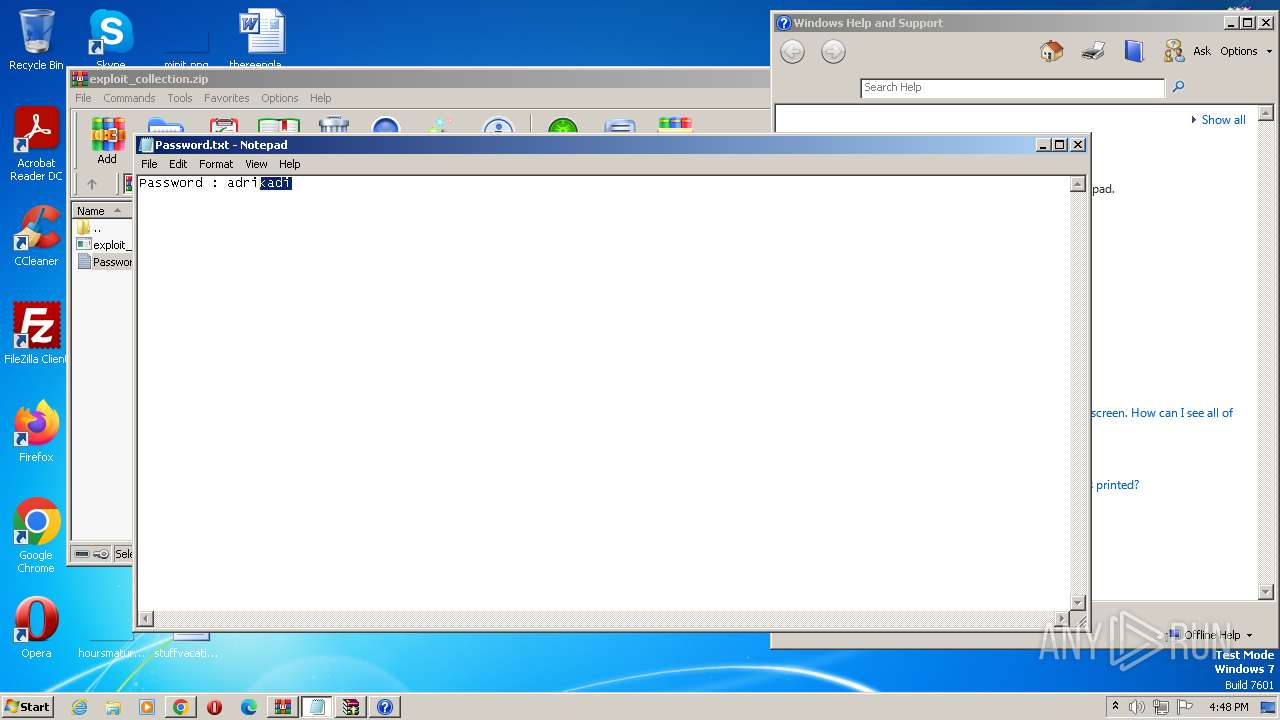
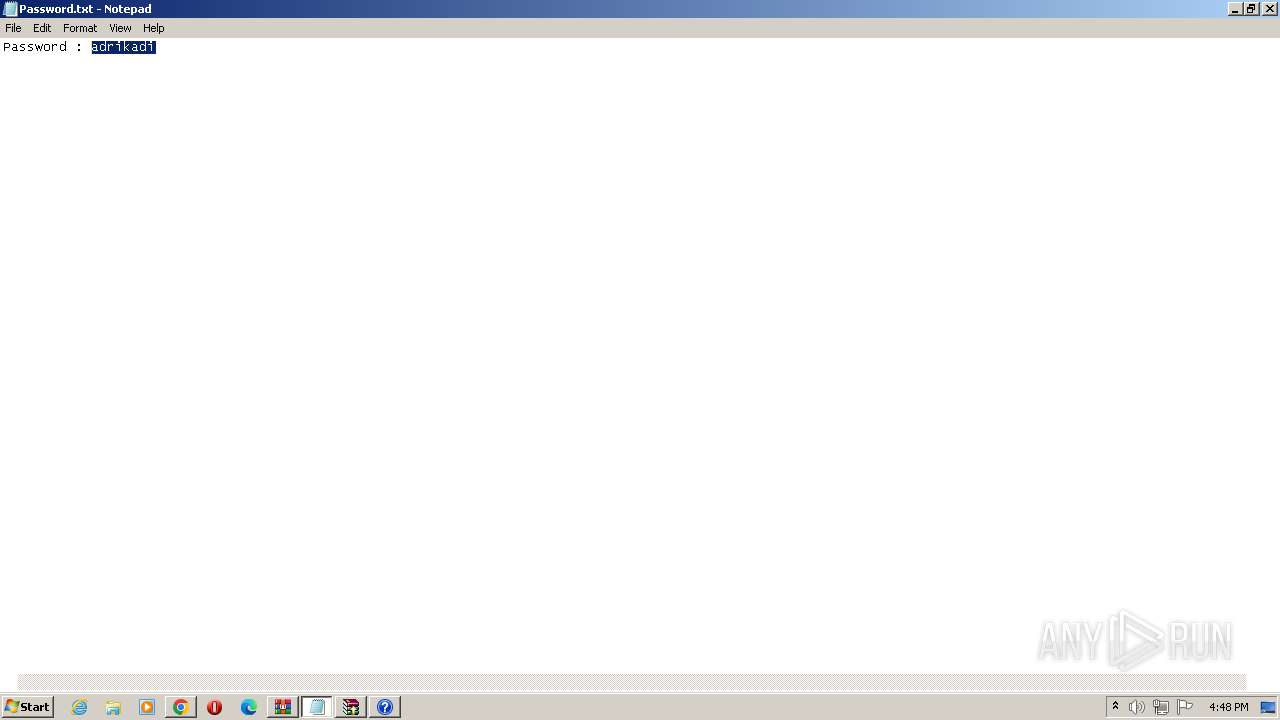
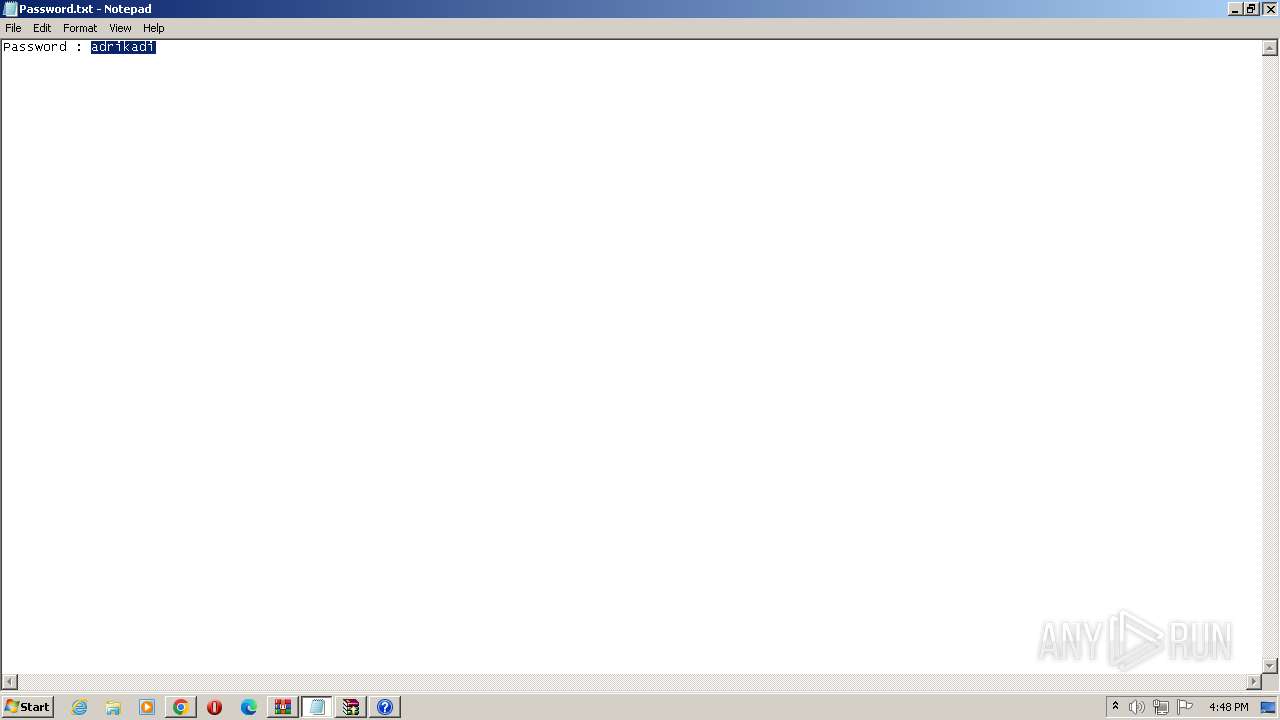
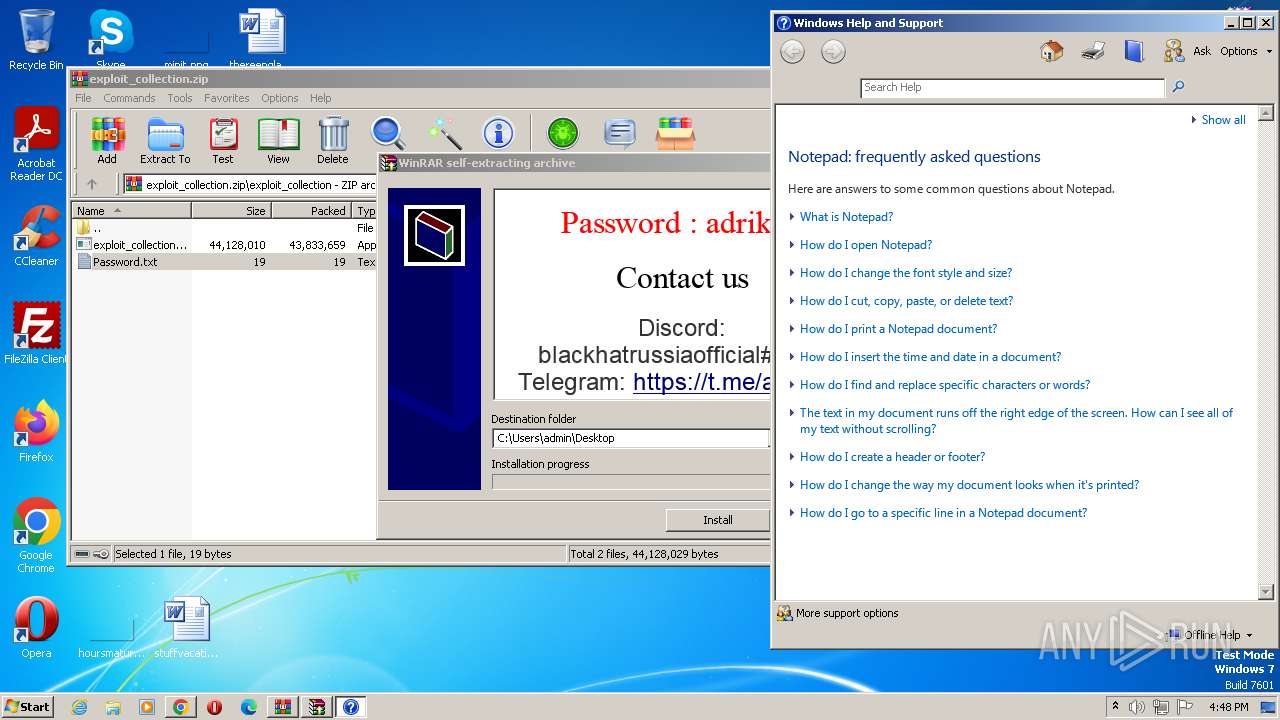
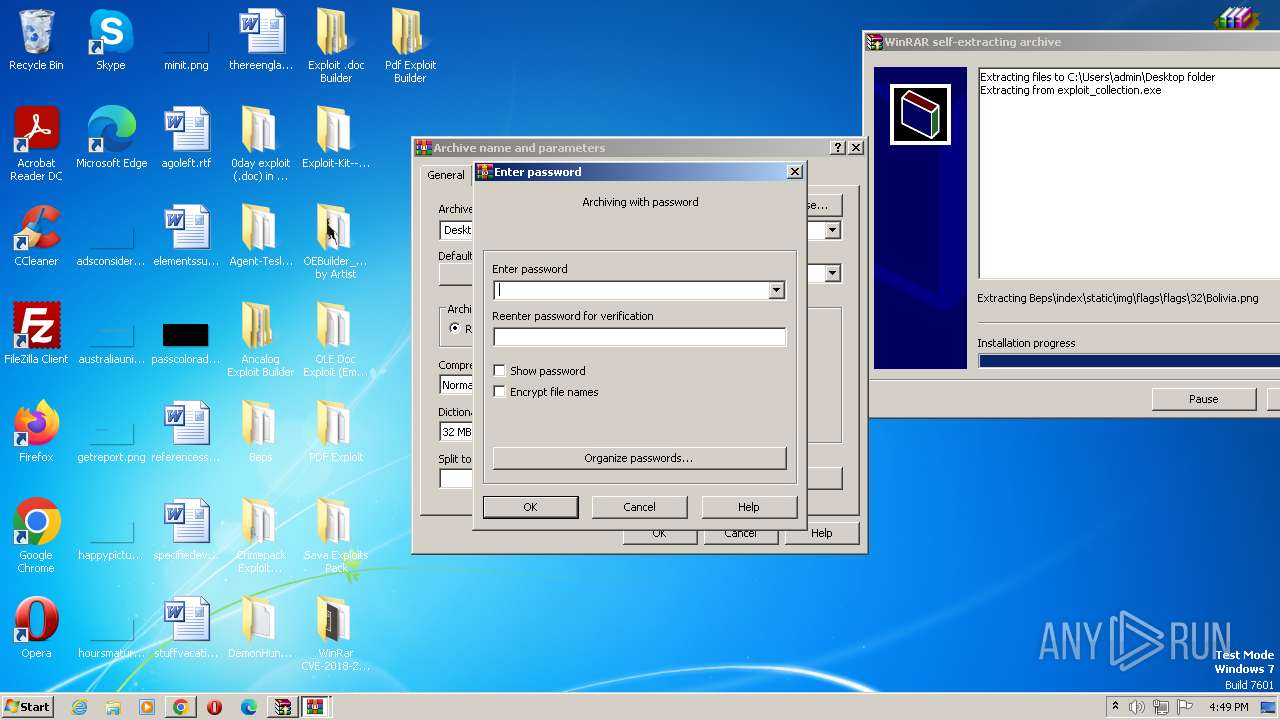
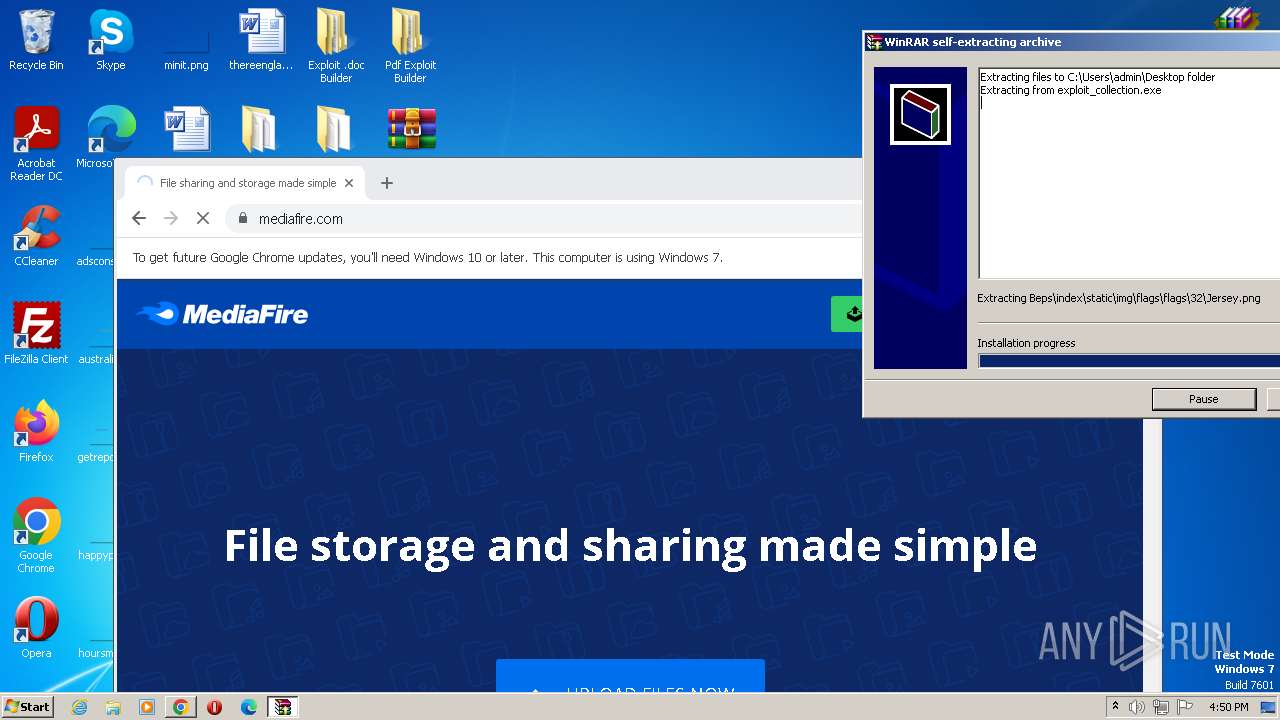
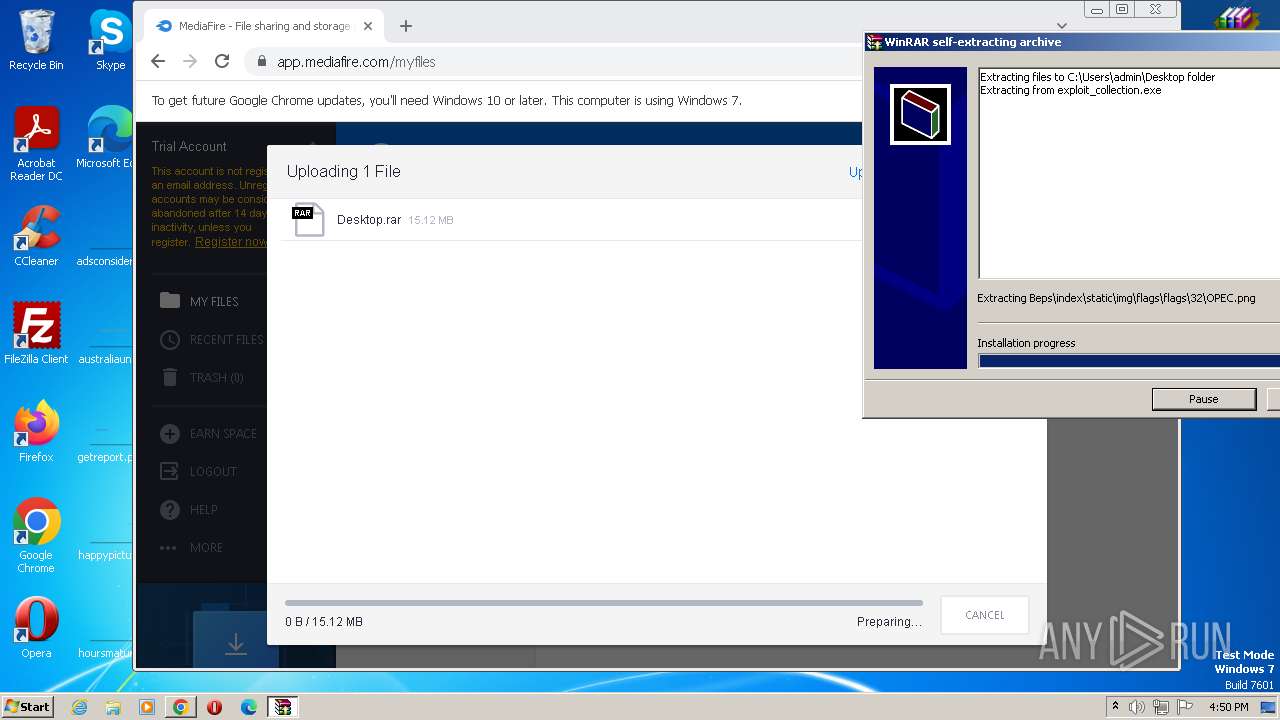
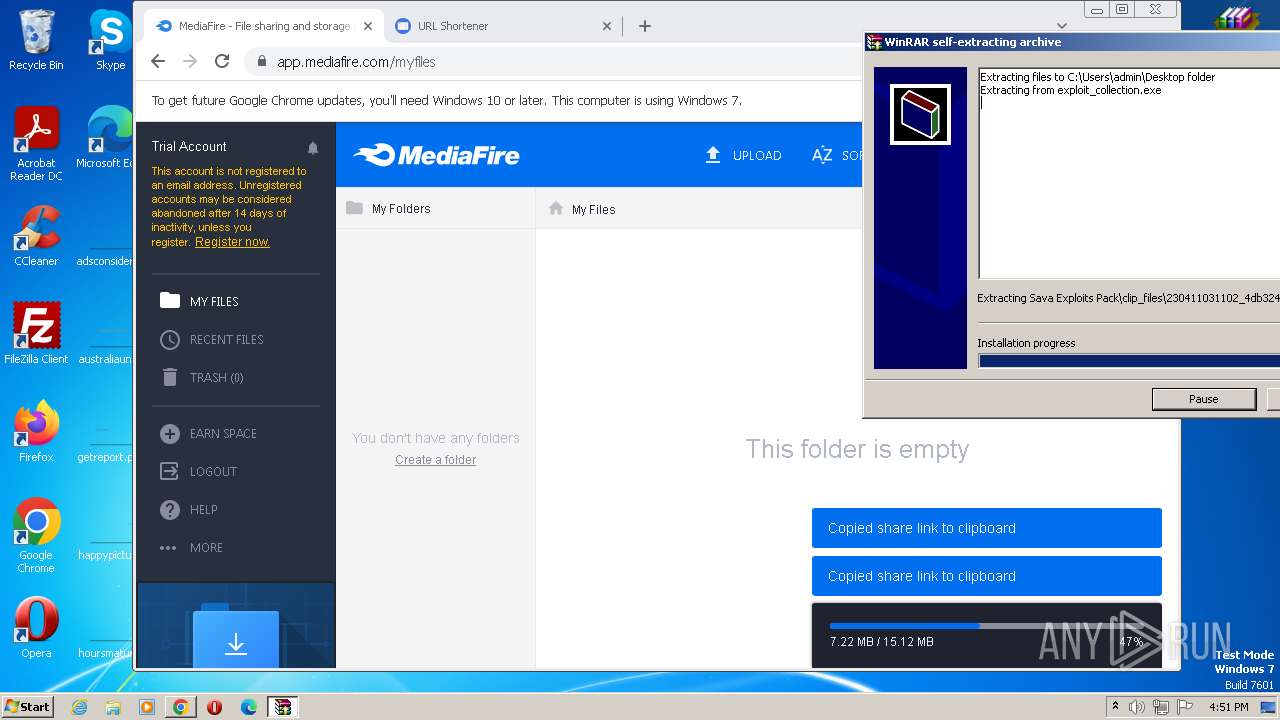
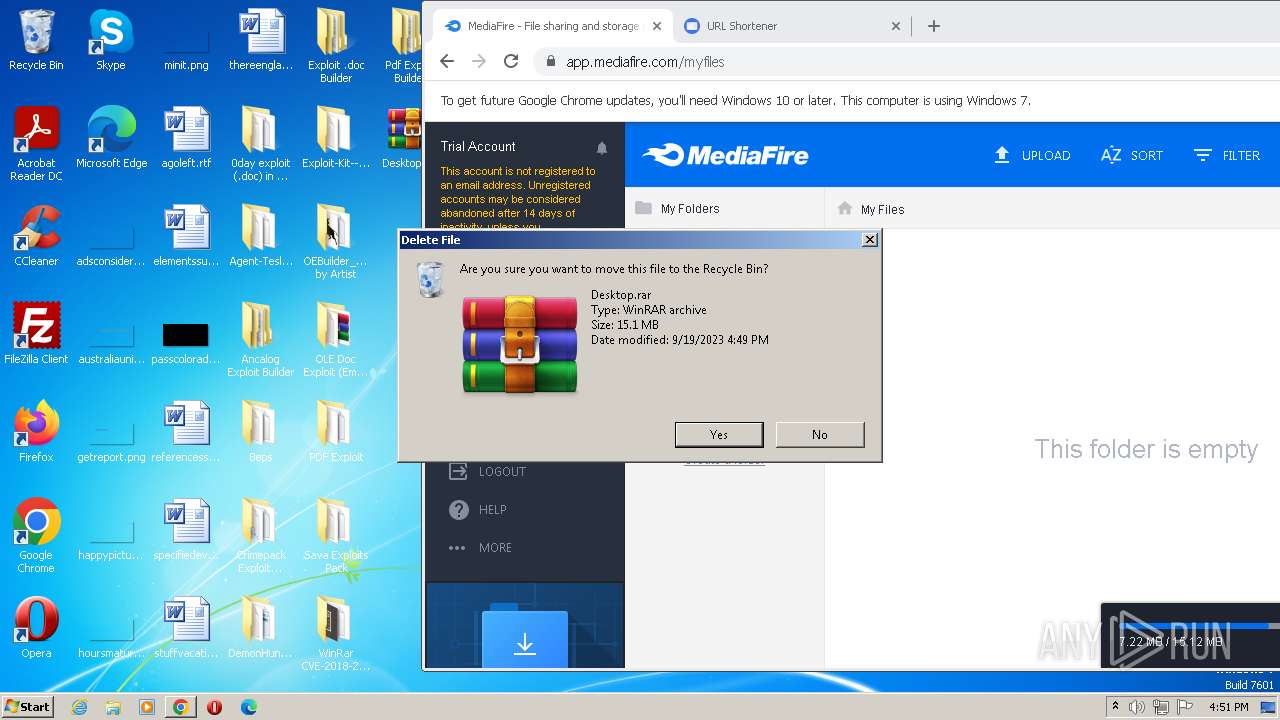
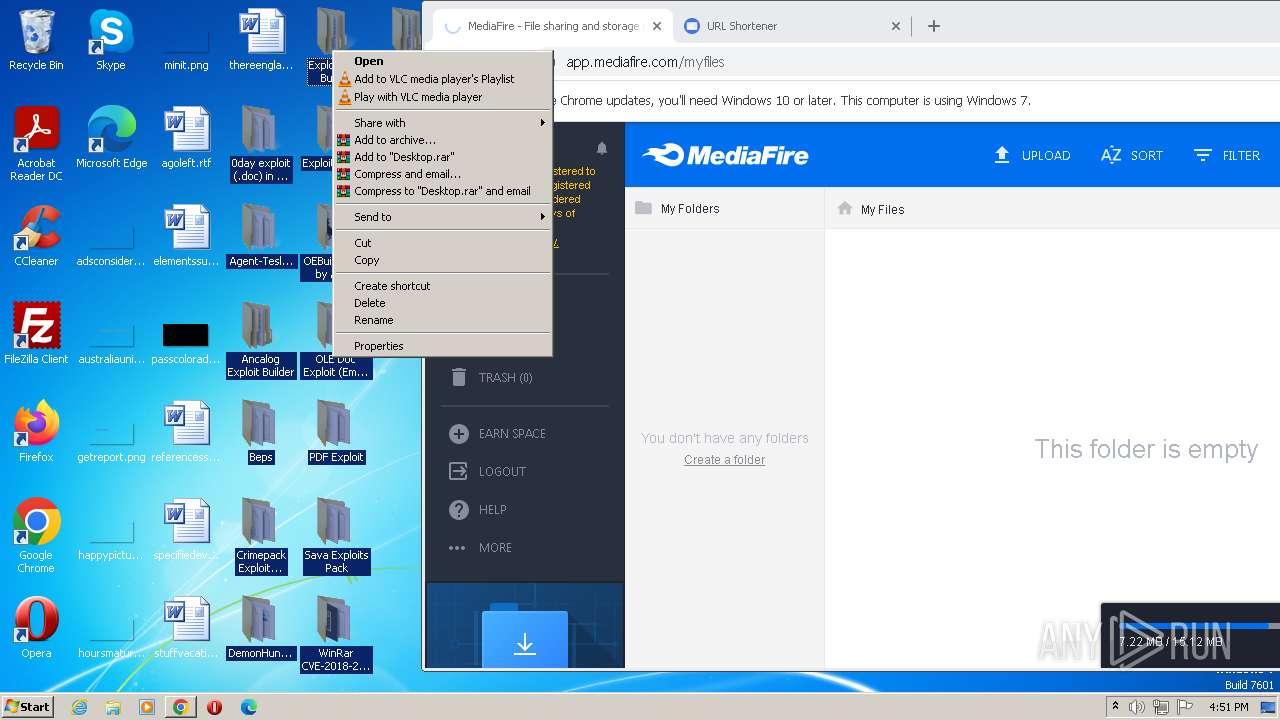
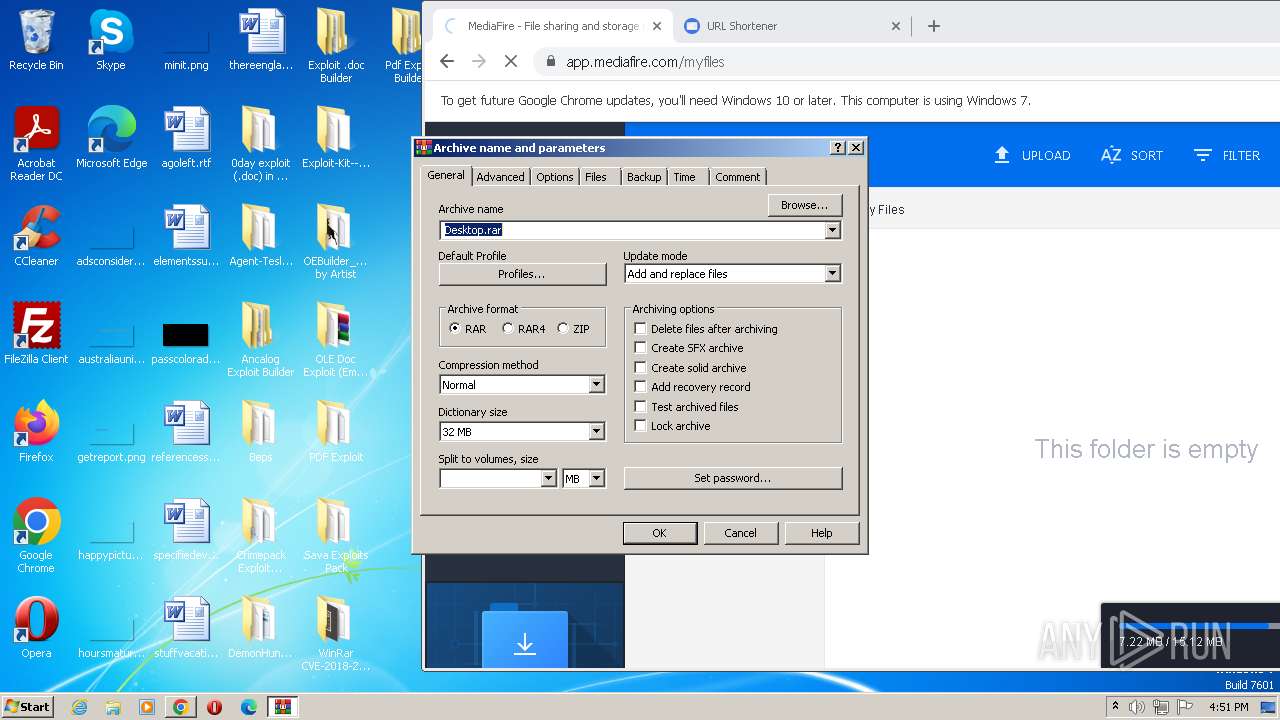
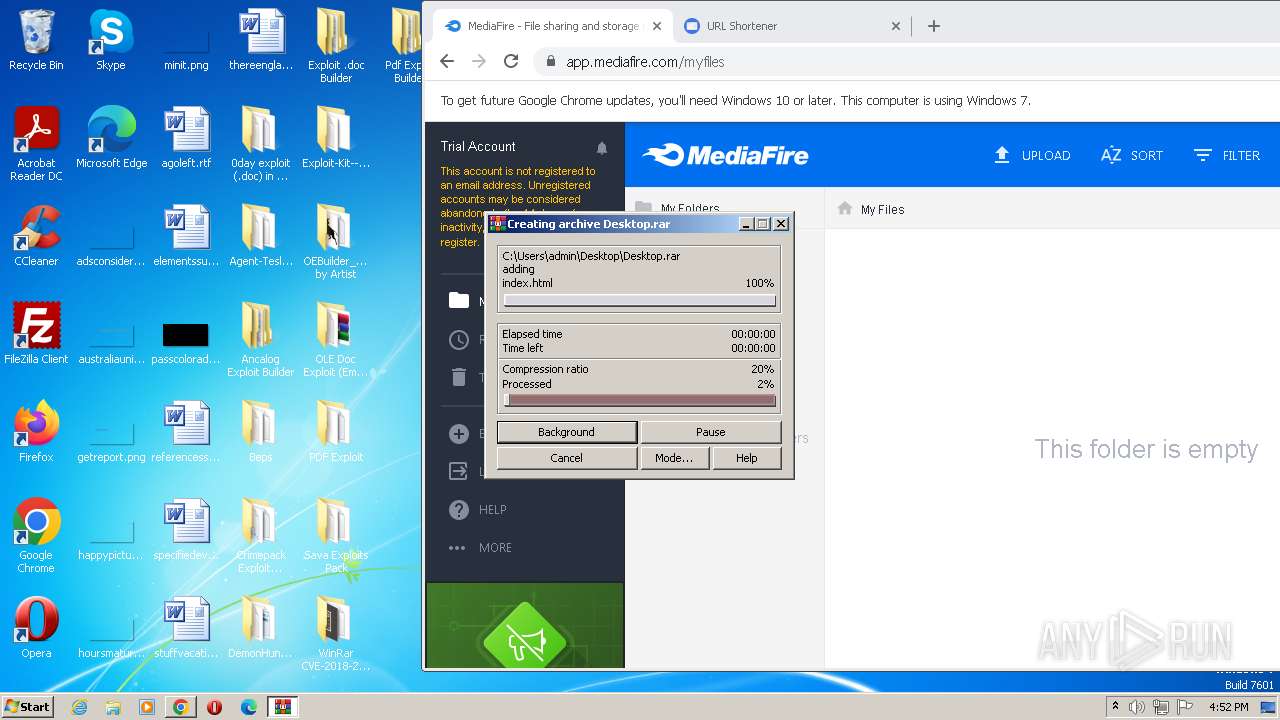
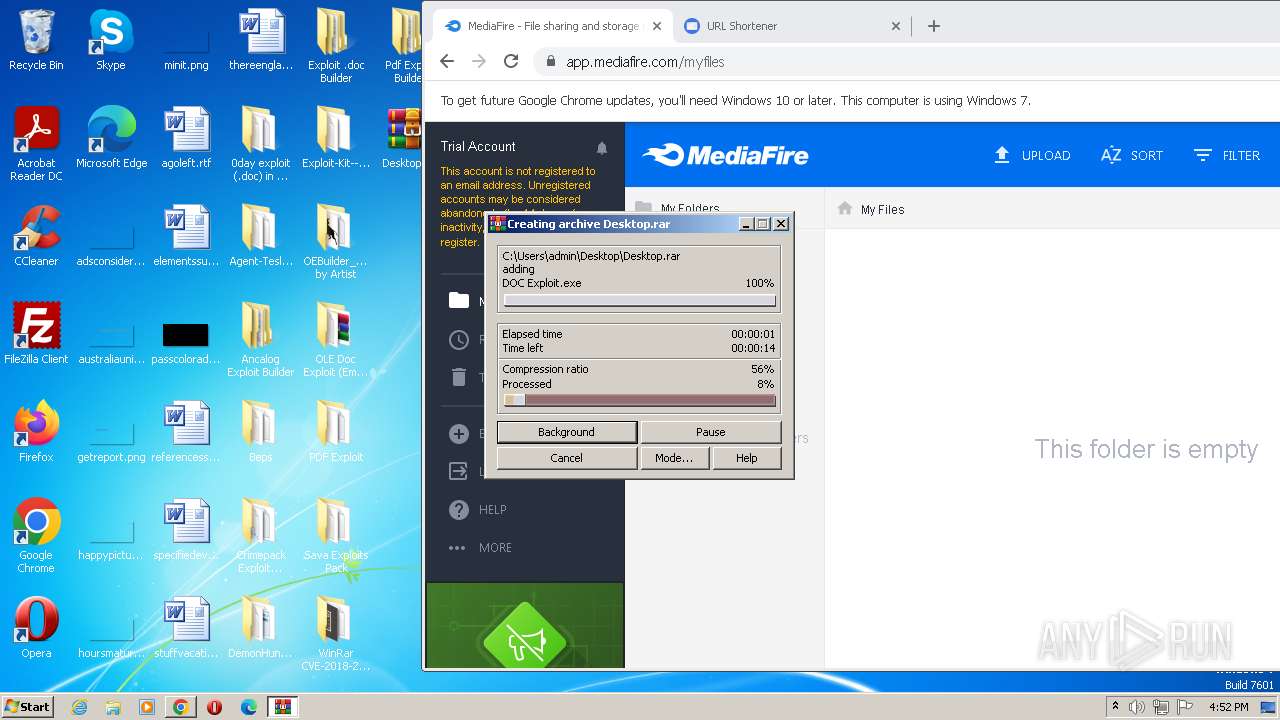
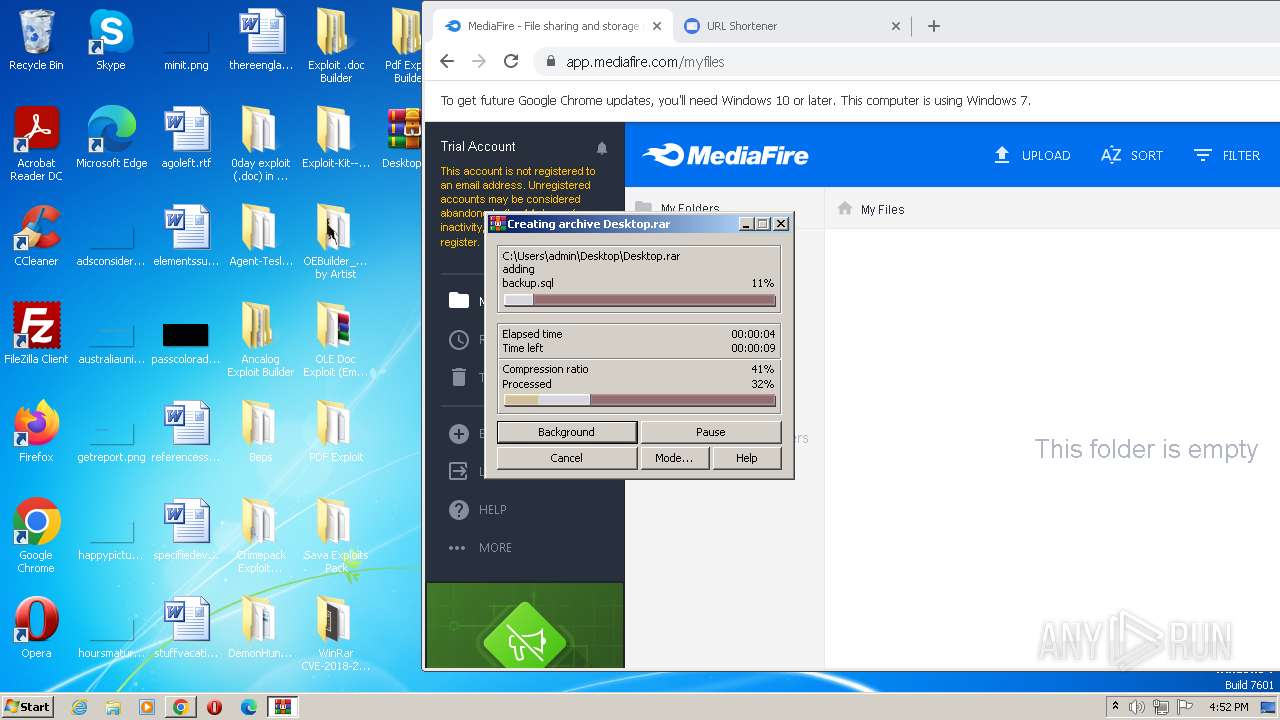
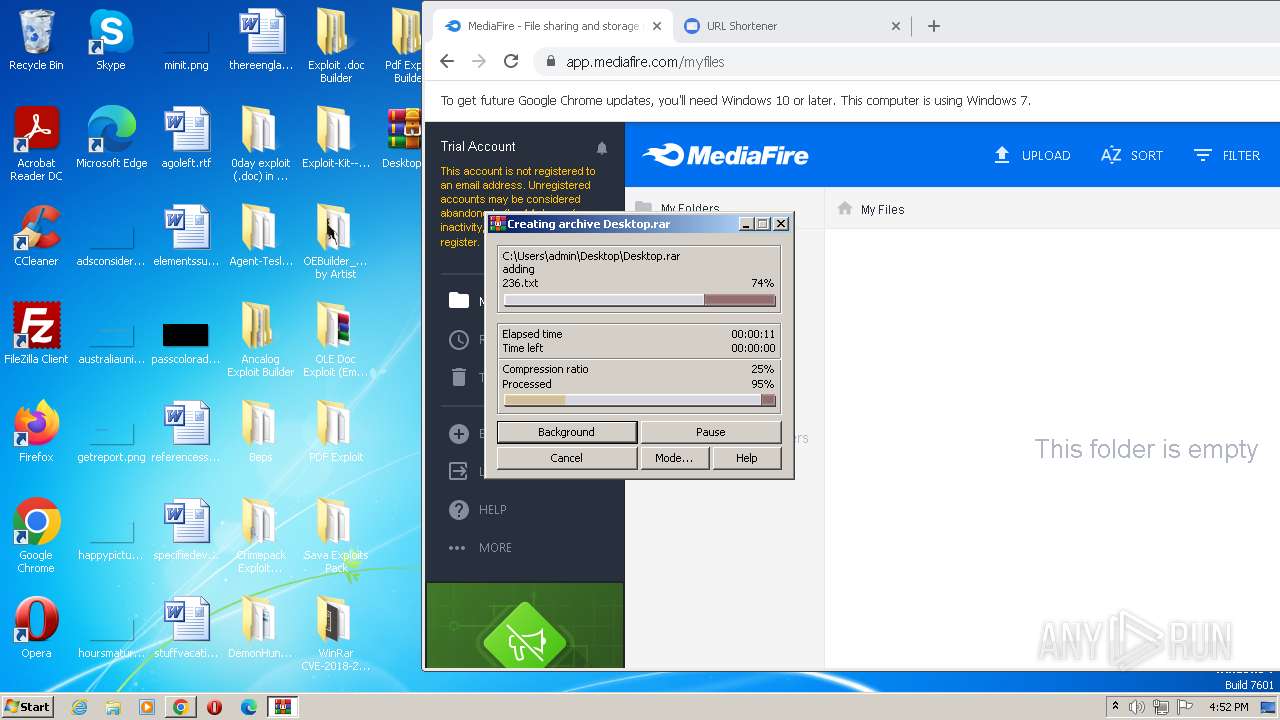
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 2548)
Reads Internet Explorer settings
- exploit_collection.exe (PID: 3276)
- HelpPane.exe (PID: 2896)
Reads Microsoft Outlook installation path
- exploit_collection.exe (PID: 3276)
- HelpPane.exe (PID: 2896)
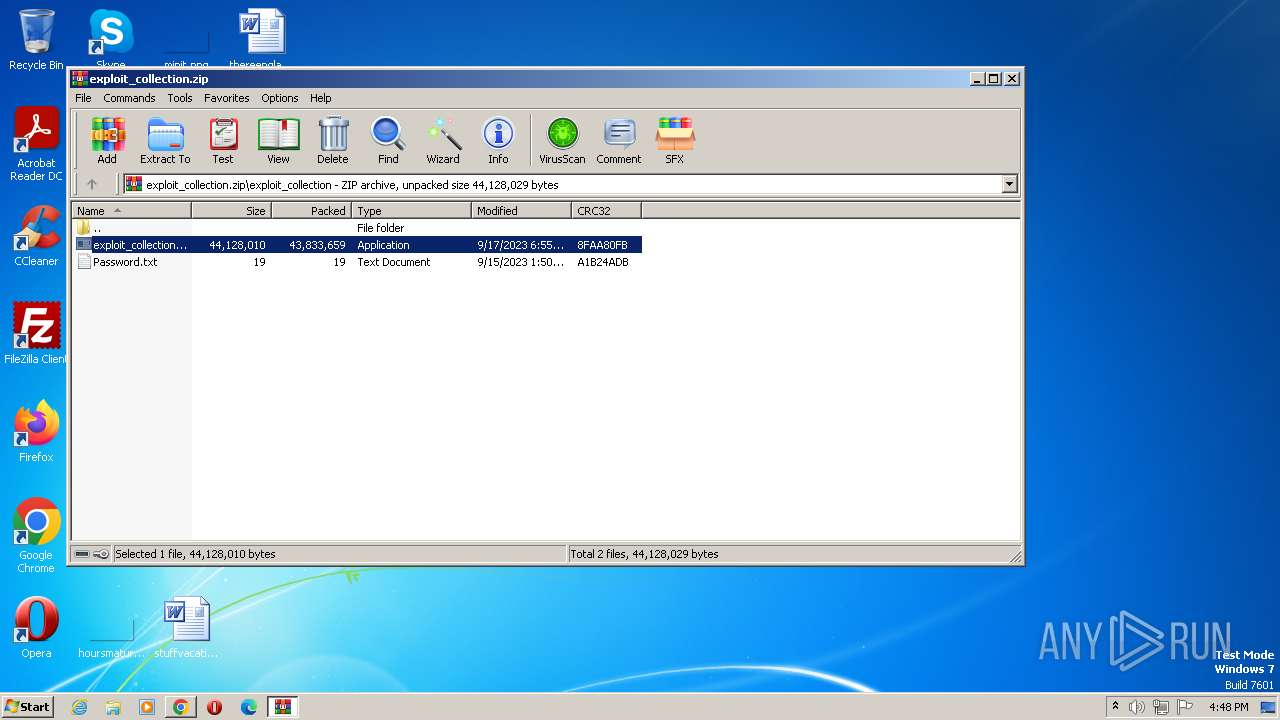
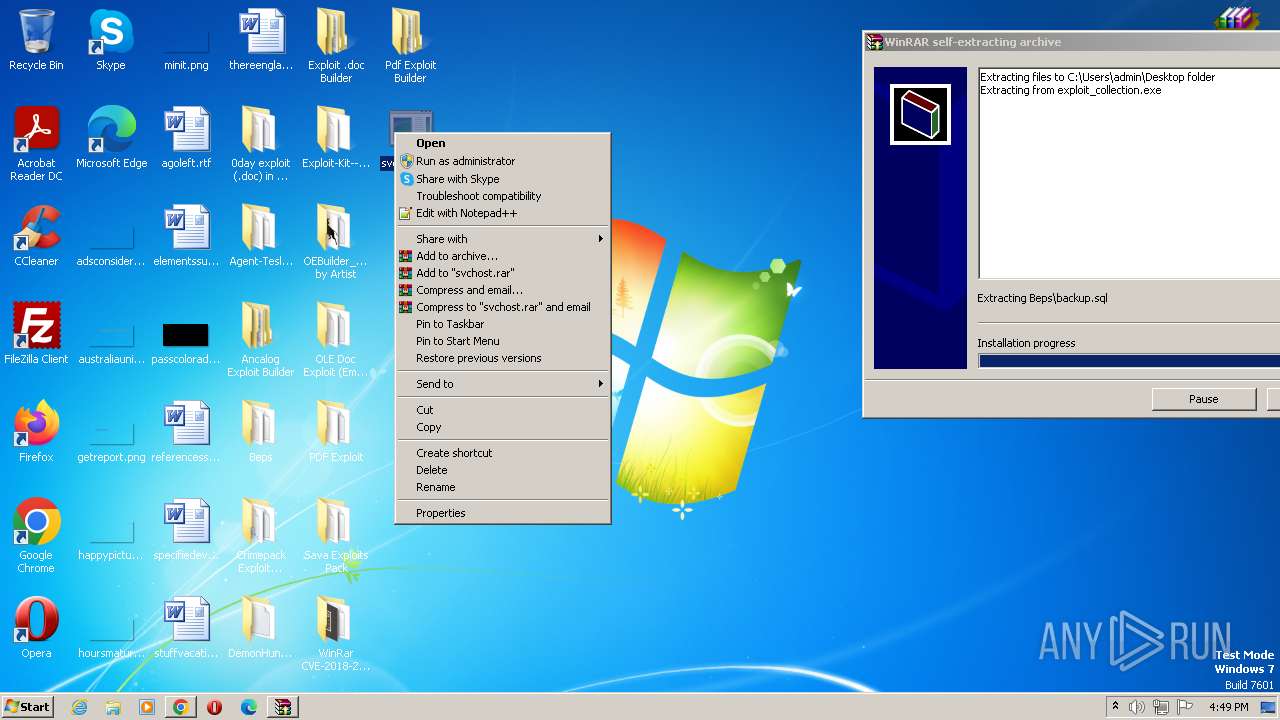
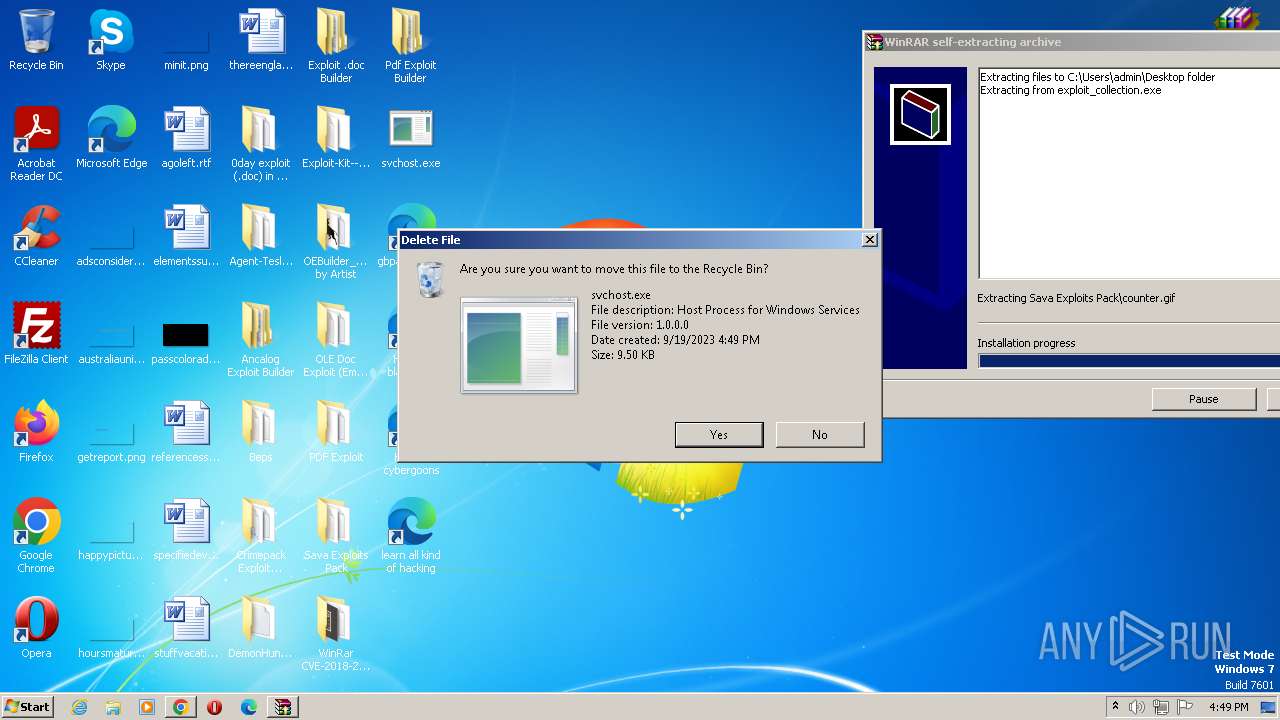
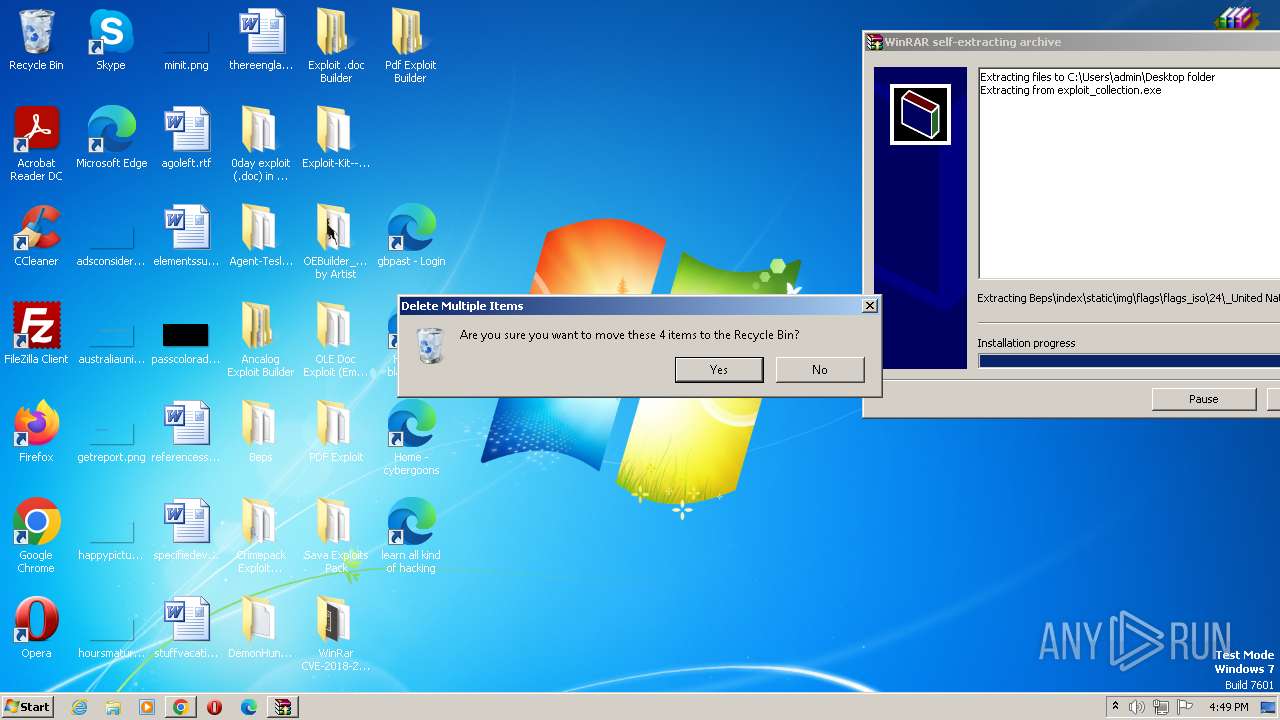
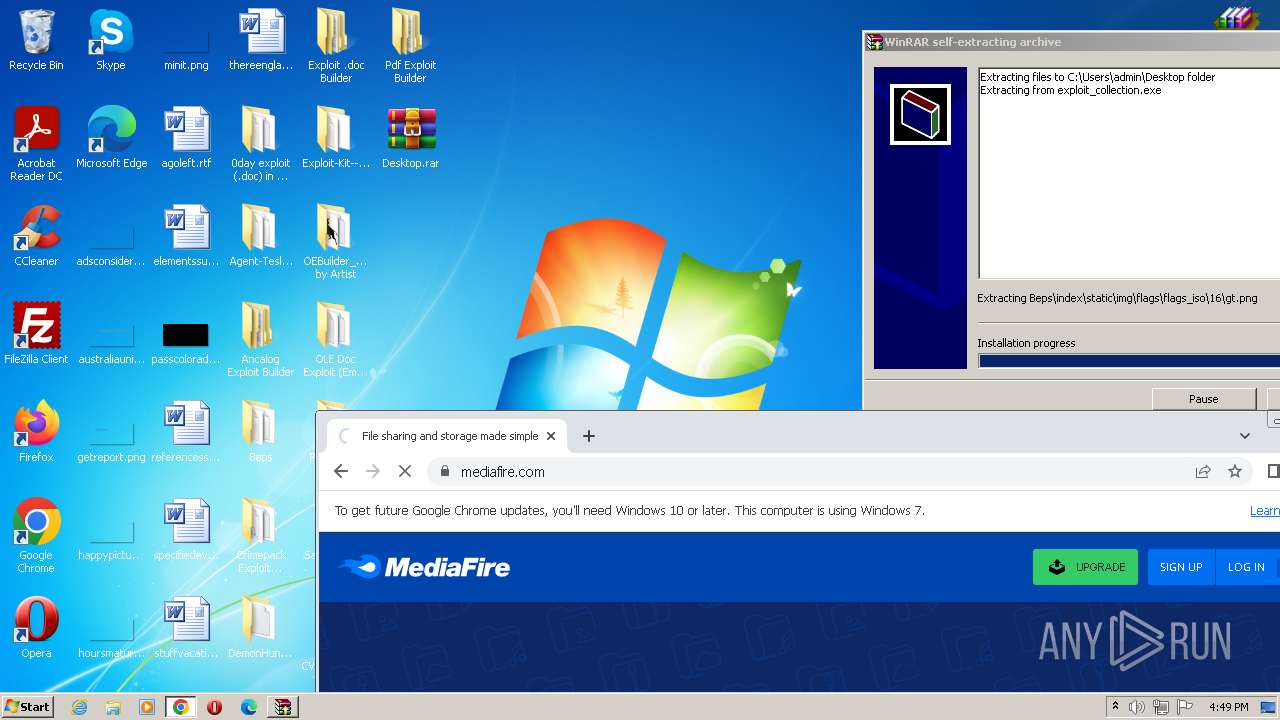
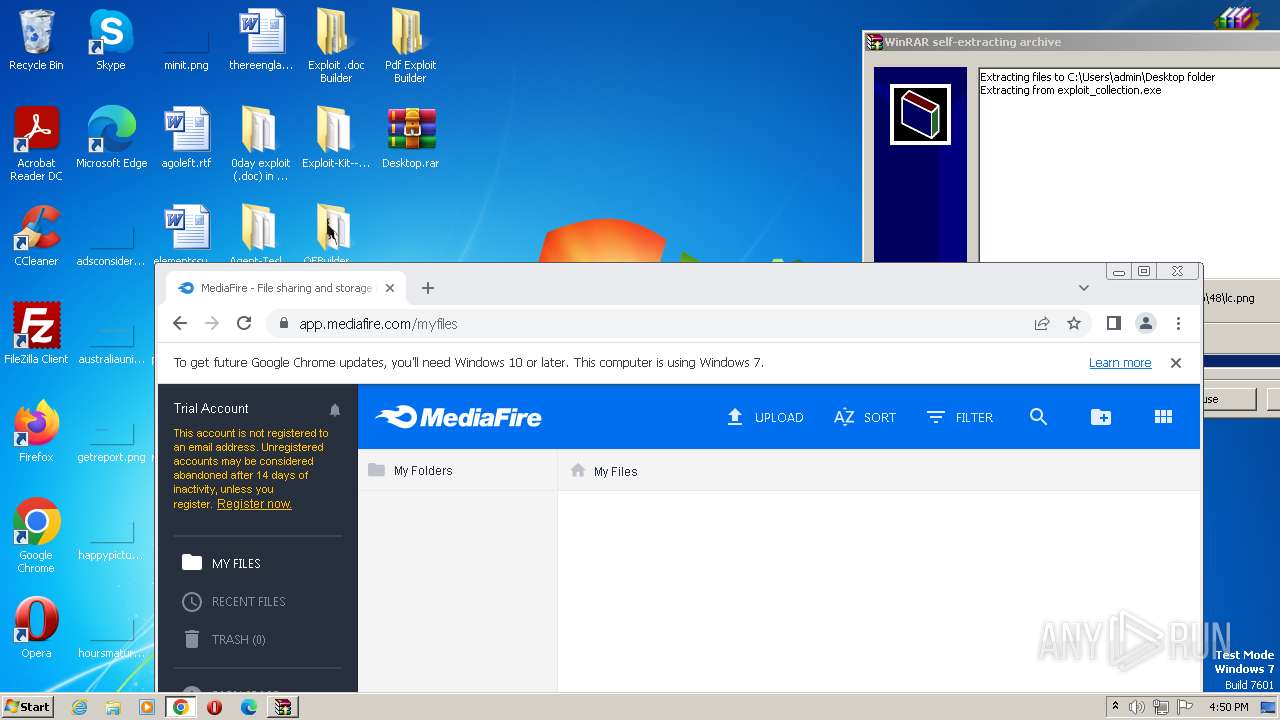
Creates executable files that already exist in Windows
- exploit_collection.exe (PID: 3276)
The process creates files with name similar to system file names
- exploit_collection.exe (PID: 3276)
INFO
Reads the computer name
- exploit_collection.exe (PID: 3276)
Checks supported languages
- exploit_collection.exe (PID: 3276)
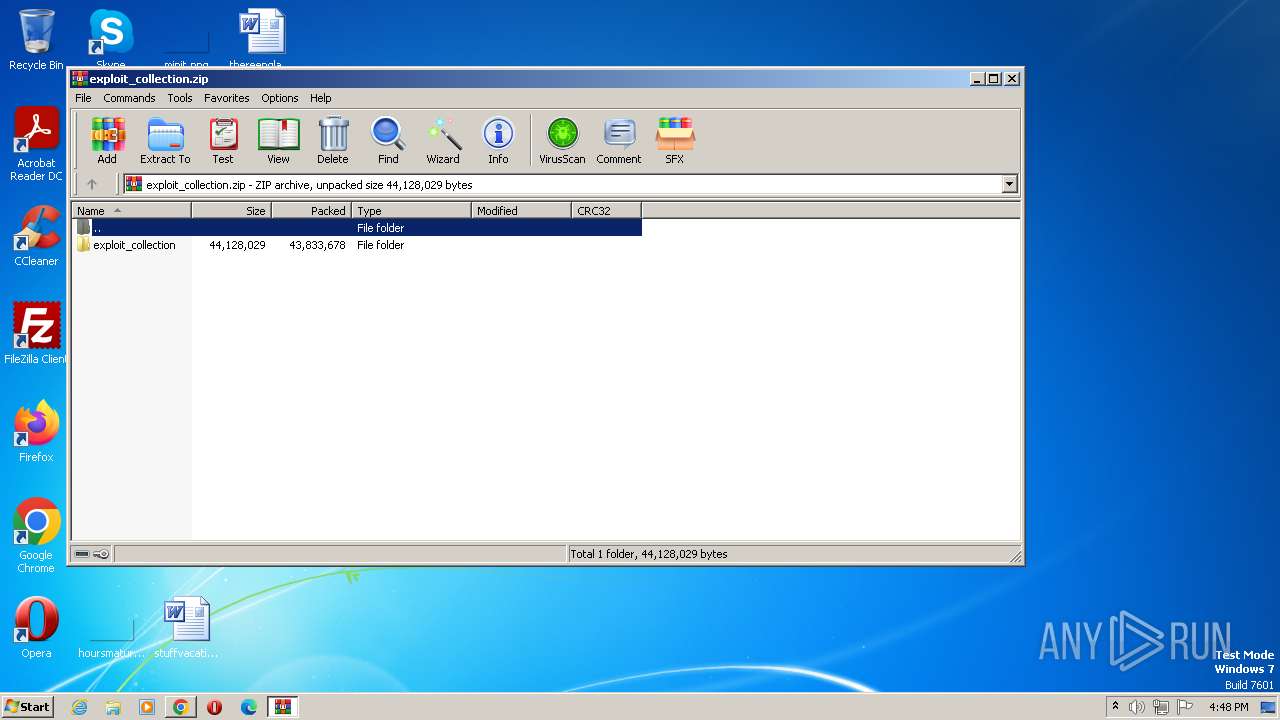
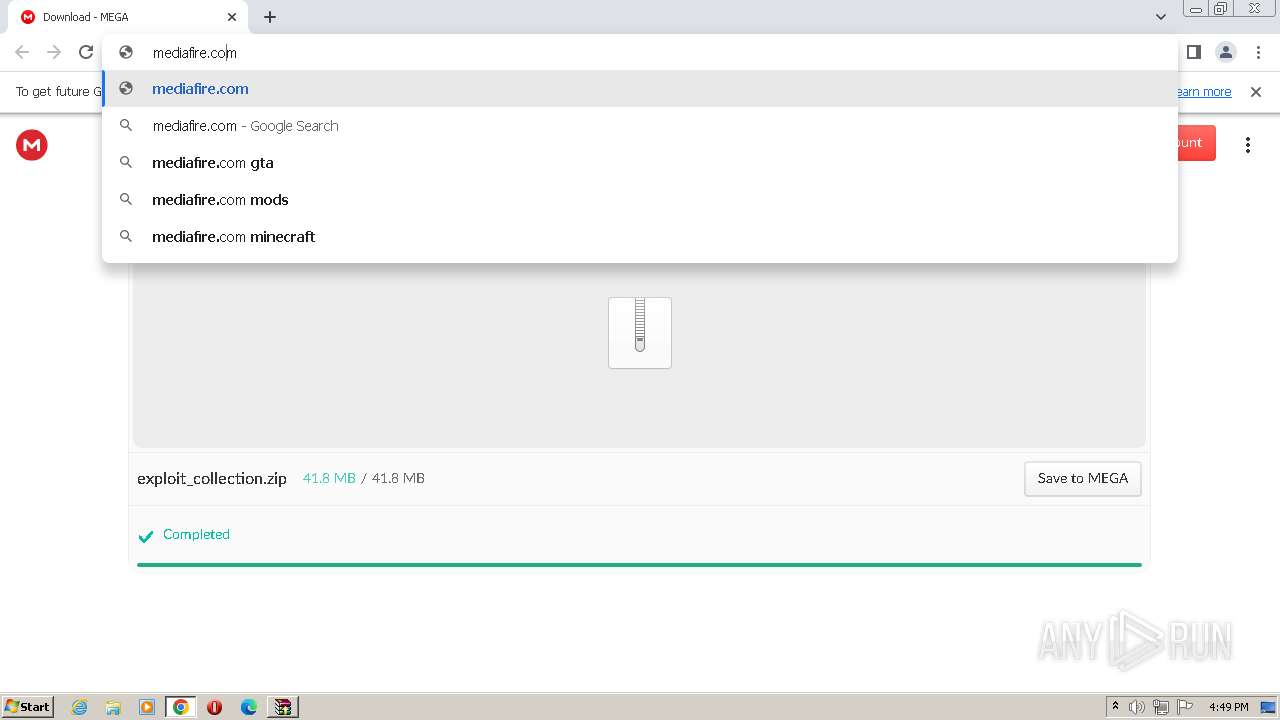
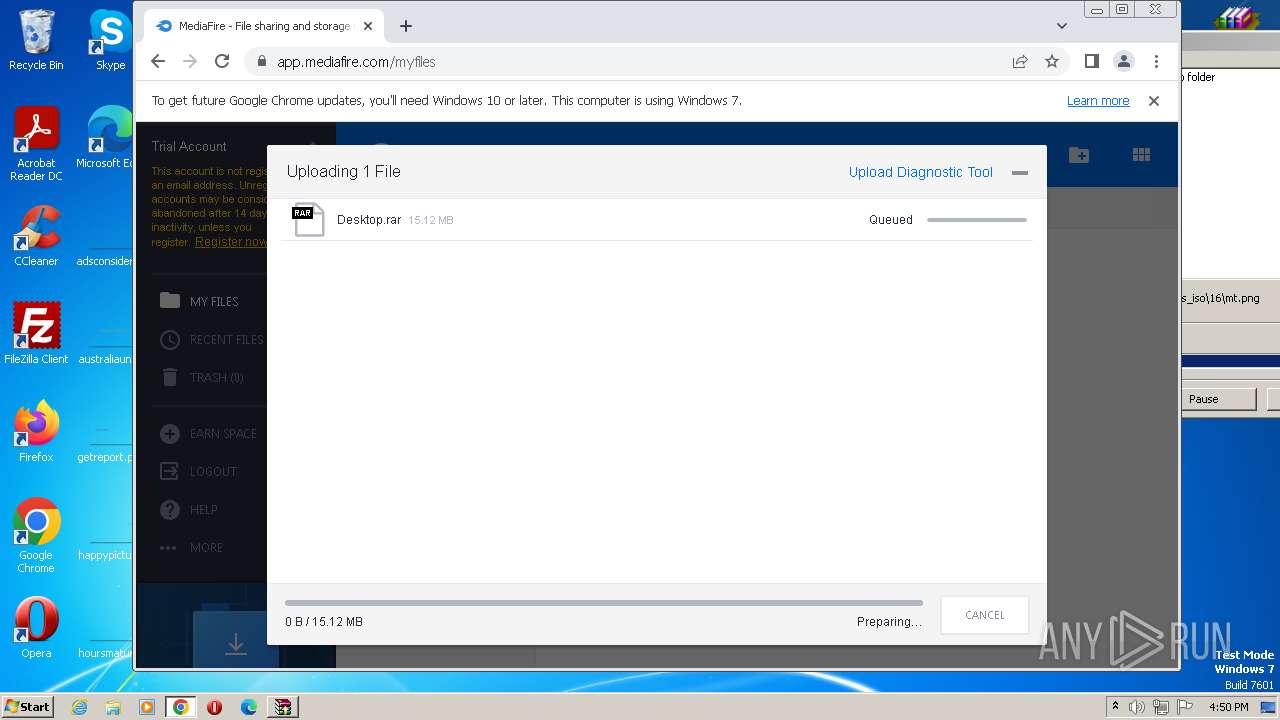
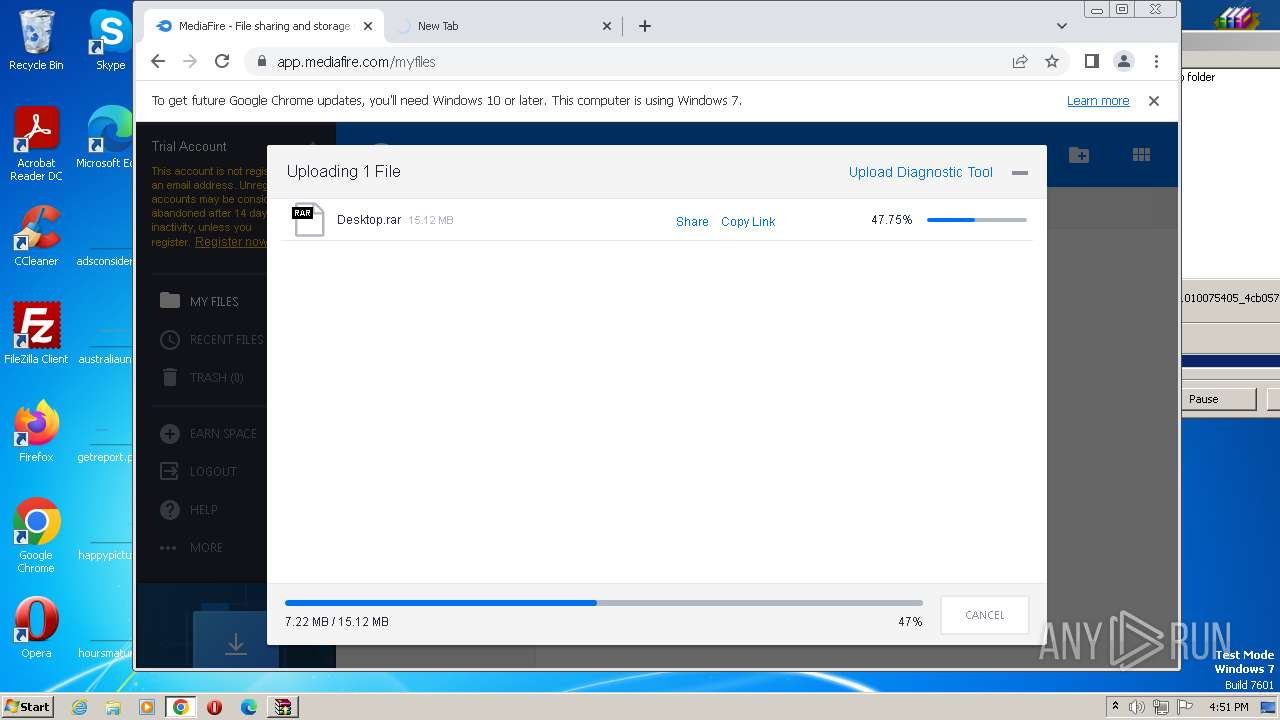
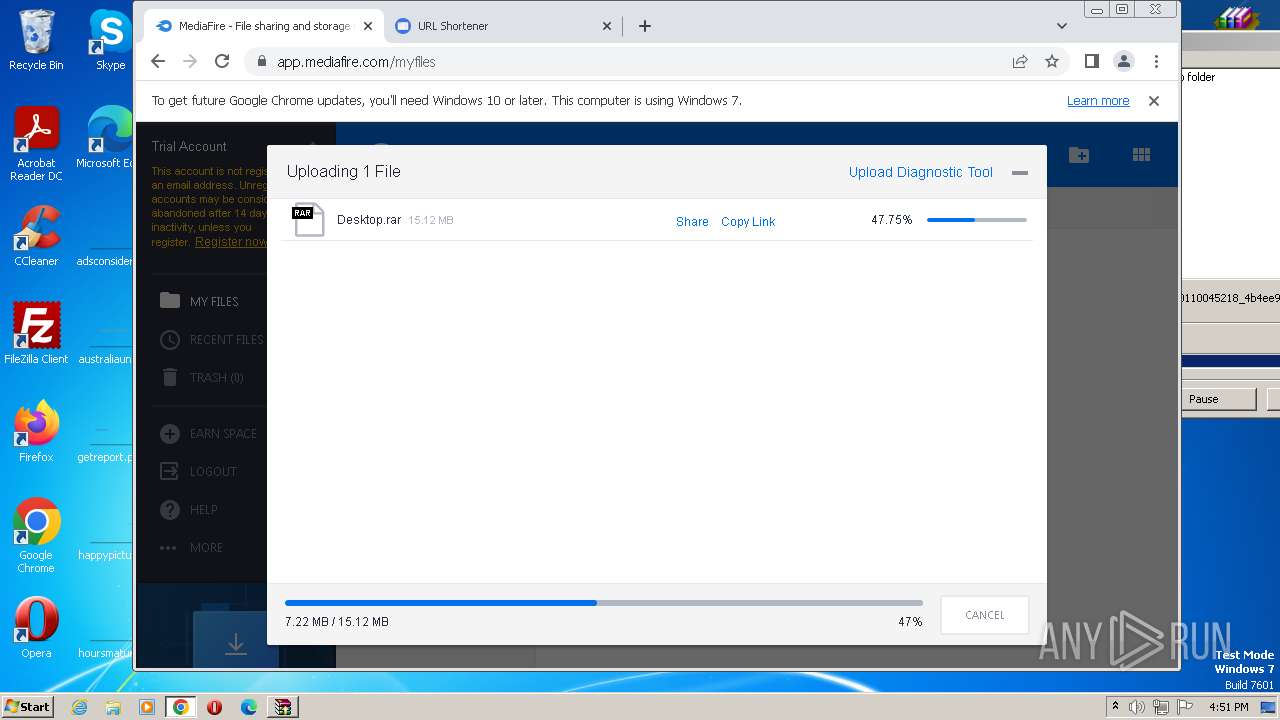
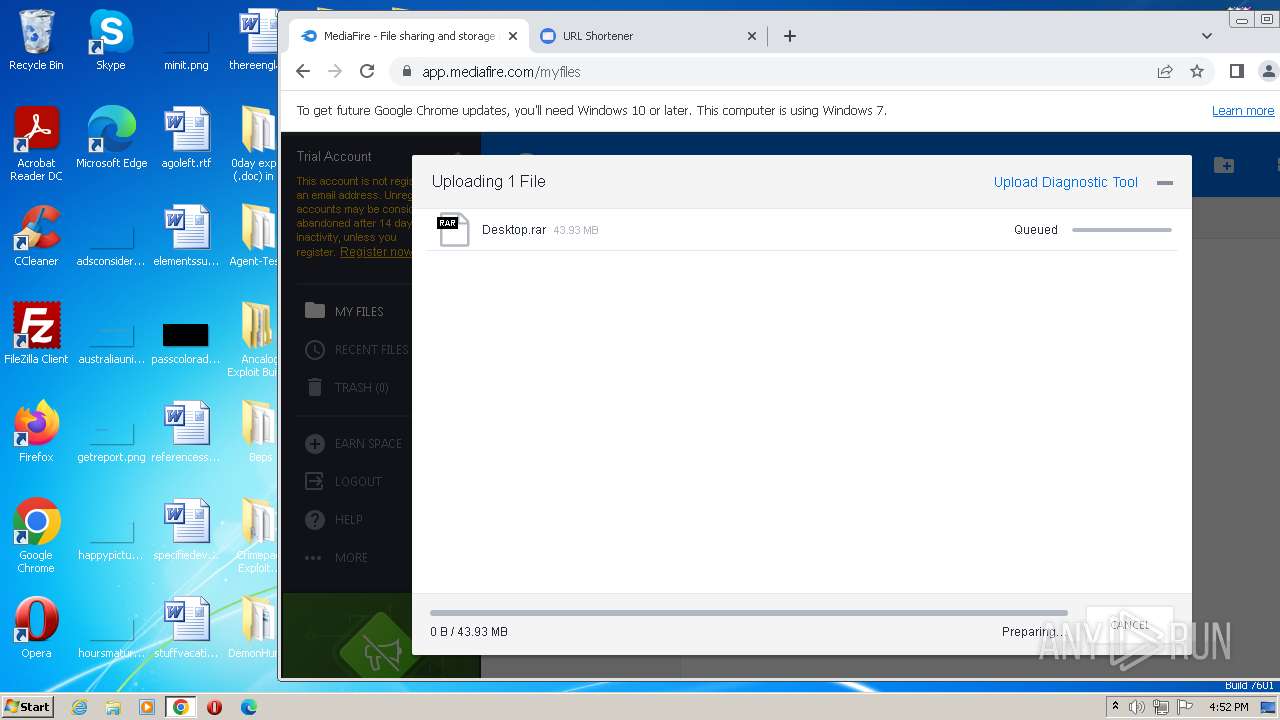
The process uses the downloaded file
- chrome.exe (PID: 1140)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 1824)
- WinRAR.exe (PID: 2548)
- chrome.exe (PID: 2000)
Reads the machine GUID from the registry
- exploit_collection.exe (PID: 3276)
- HelpPane.exe (PID: 2896)
Checks proxy server information
- exploit_collection.exe (PID: 3276)
- HelpPane.exe (PID: 2896)
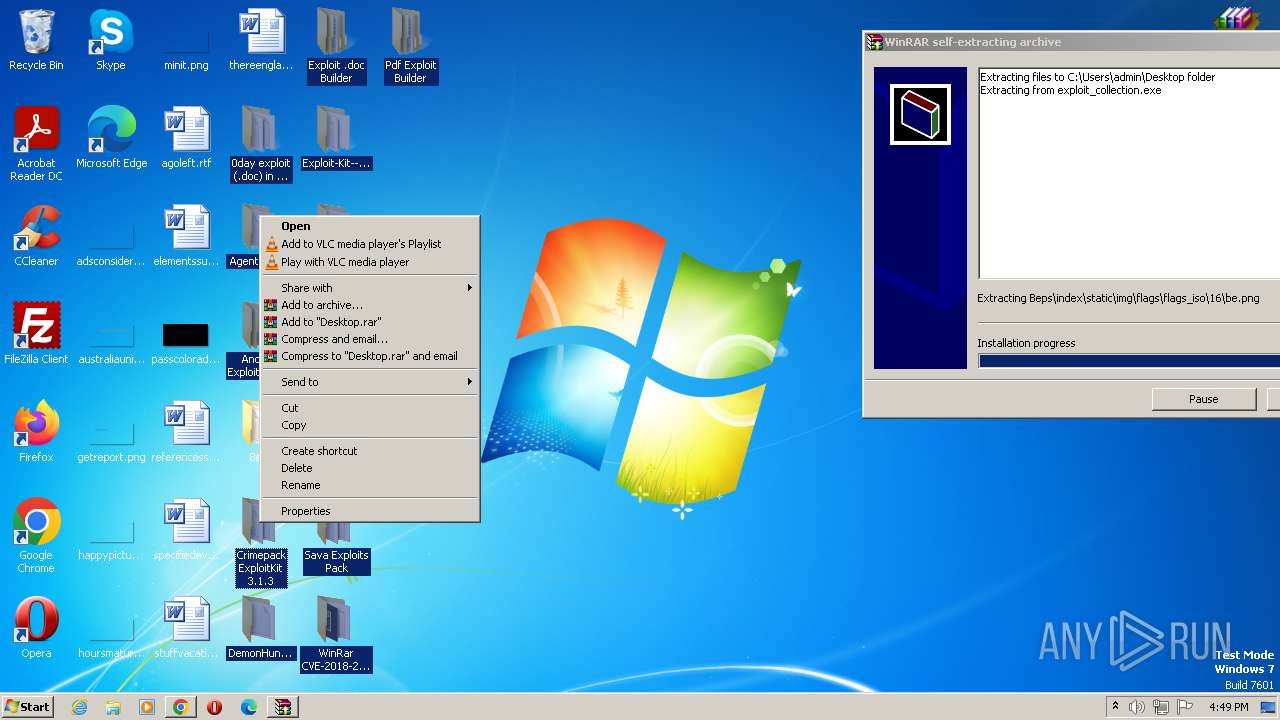
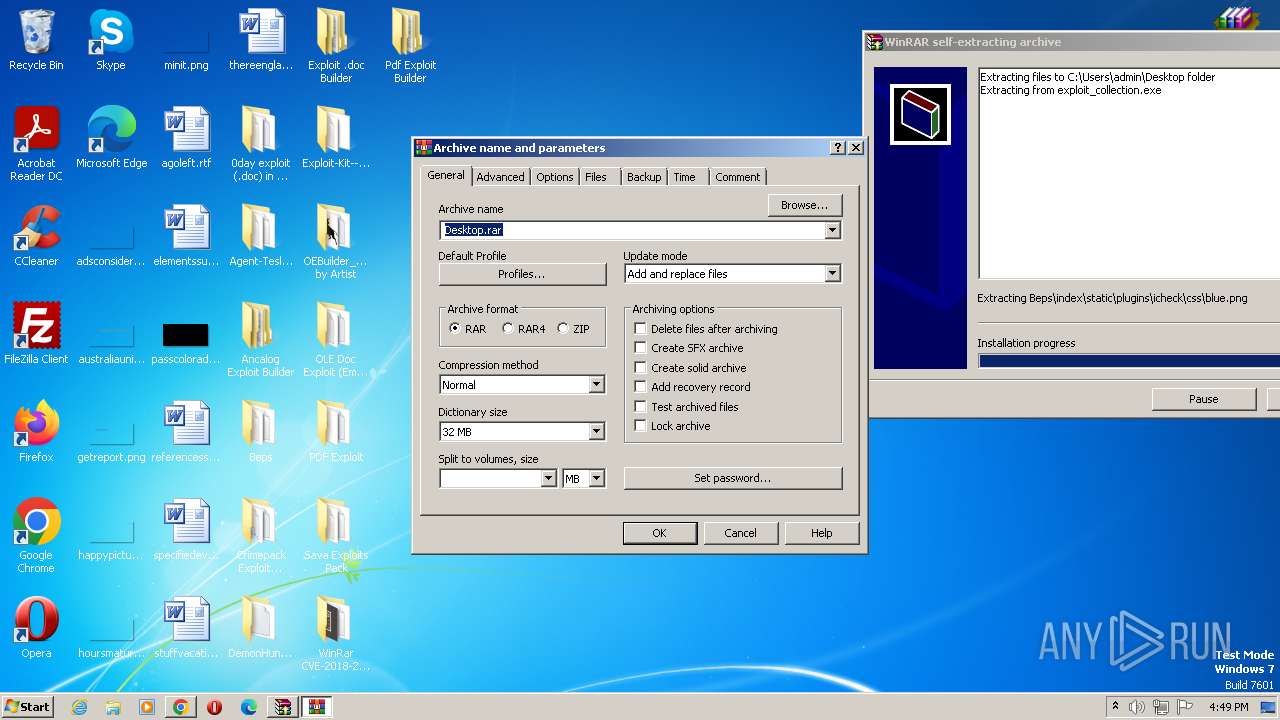
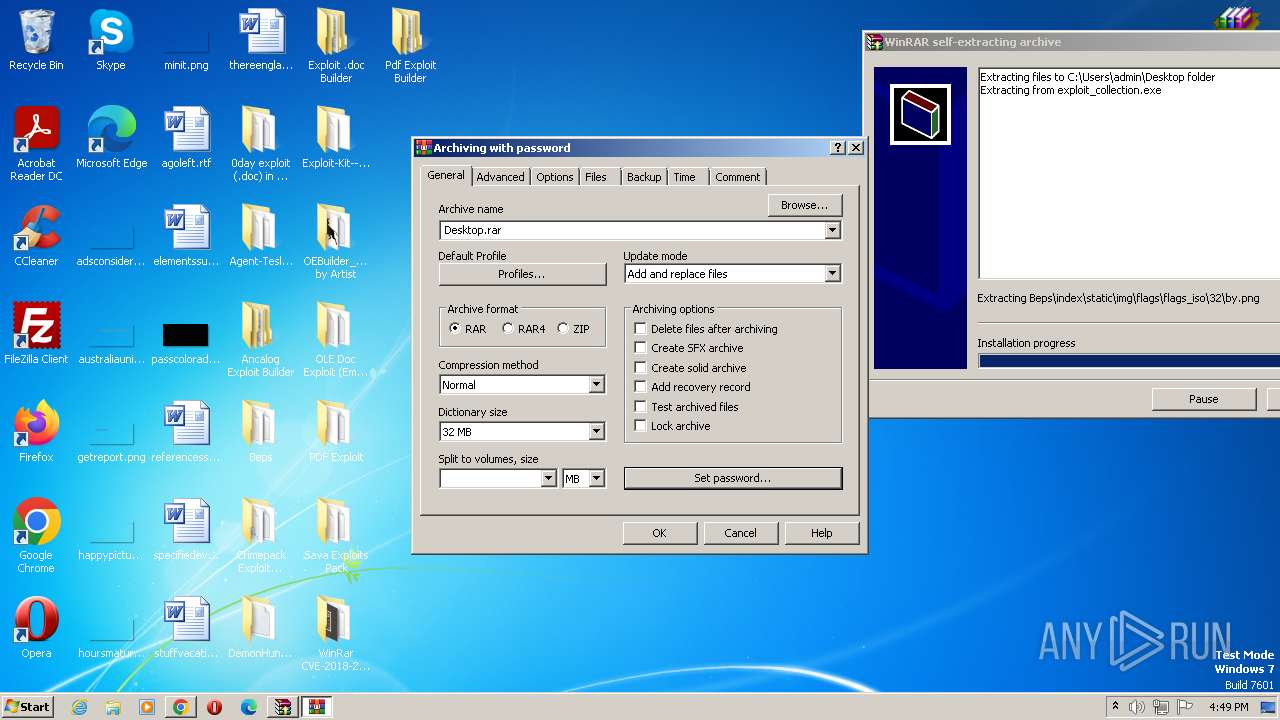
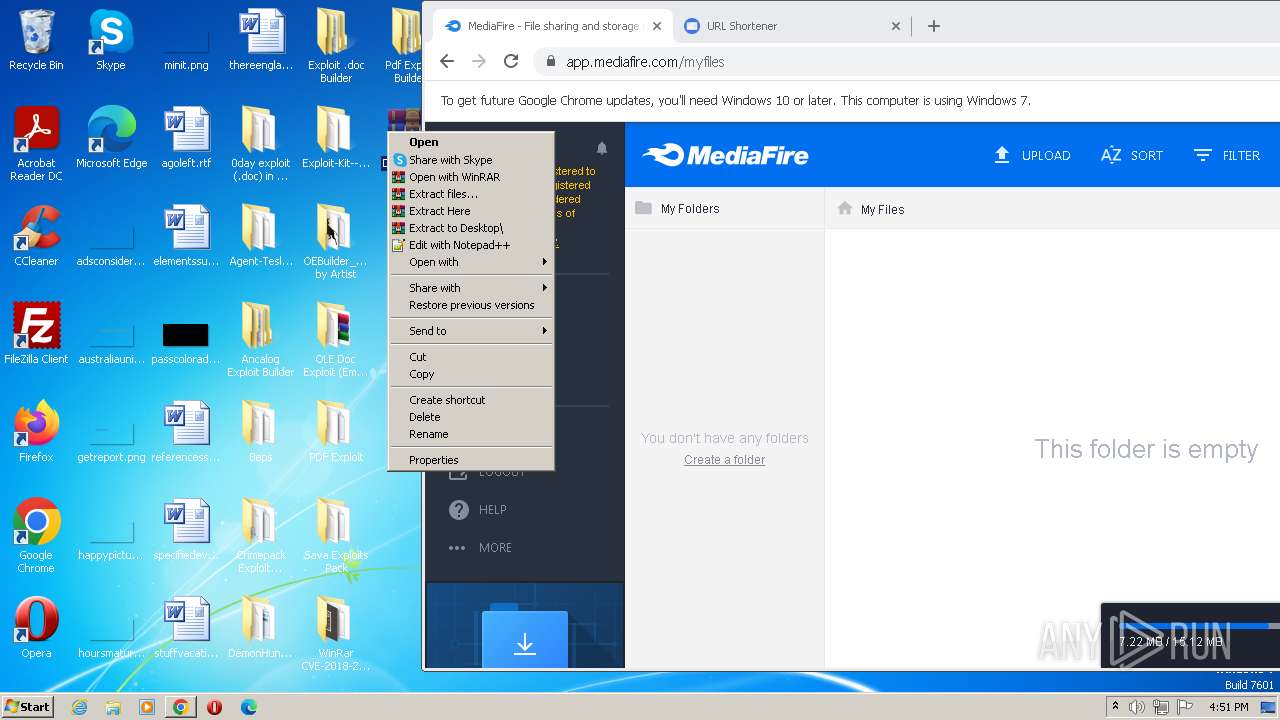
Manual execution by a user
- exploit_collection.exe (PID: 3276)
- WinRAR.exe (PID: 4064)
- WinRAR.exe (PID: 2744)
Application launched itself
- chrome.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
47
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2212 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1416 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3796 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1272 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3748 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=620 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3680 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=2568 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3720 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=3860 --field-trial-handle=1160,i,7994743315755965094,3715566500108836433,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
56 233
Read events
56 039
Write events
194
Delete events
0
Modification events
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
33
Suspicious files
418
Text files
3 150
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFf836f.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\68361d16-819c-421f-b613-7a4809649a84.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFf8a84.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf836f.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFf9699.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old~RFf9699.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
237
DNS requests
197
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 6.05 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 21.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 9.72 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 9.77 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 43.6 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 9.70 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 178 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | crx | 44.8 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 89.9 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3556 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2732 | chrome.exe | 142.250.186.77:443 | accounts.google.com | GOOGLE | US | unknown |
2732 | chrome.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
2732 | chrome.exe | 142.250.185.170:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2732 | chrome.exe | 89.44.169.134:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
2732 | chrome.exe | 66.203.125.11:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
3556 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2732 | chrome.exe | 172.217.169.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
mega.nz |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
gfs208n174.userstorage.mega.co.nz |
| unknown |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2732 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
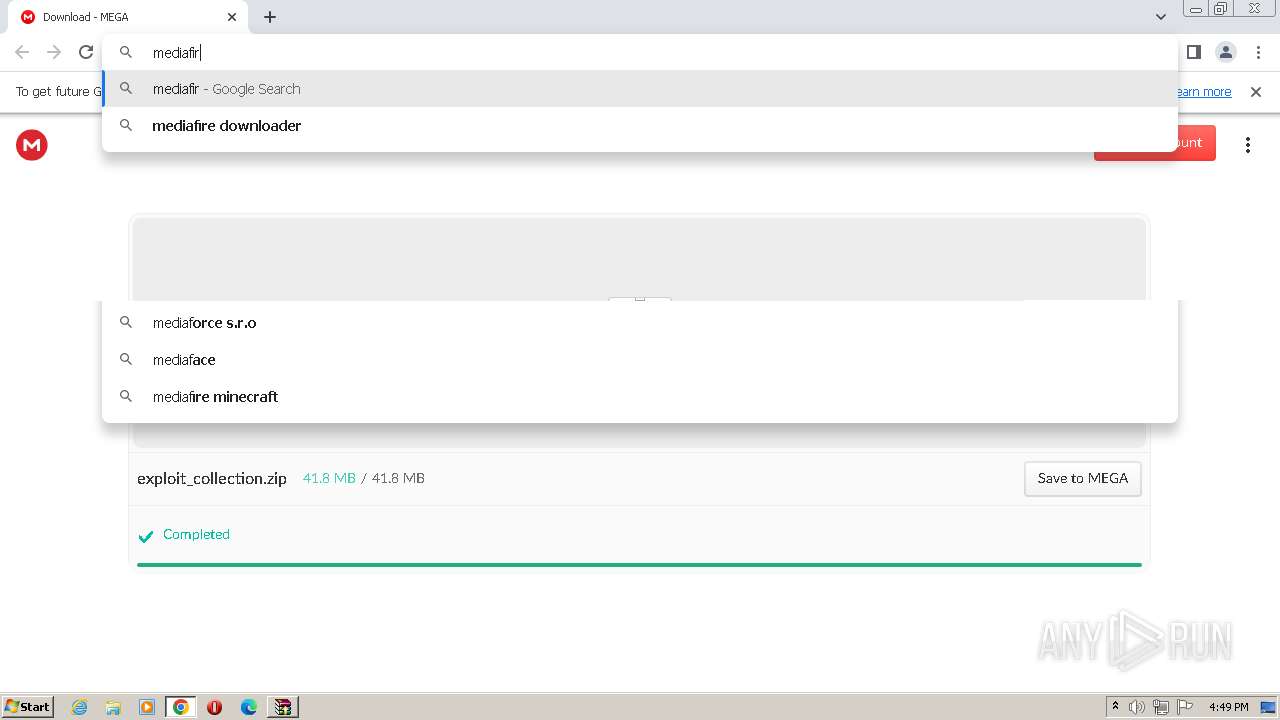
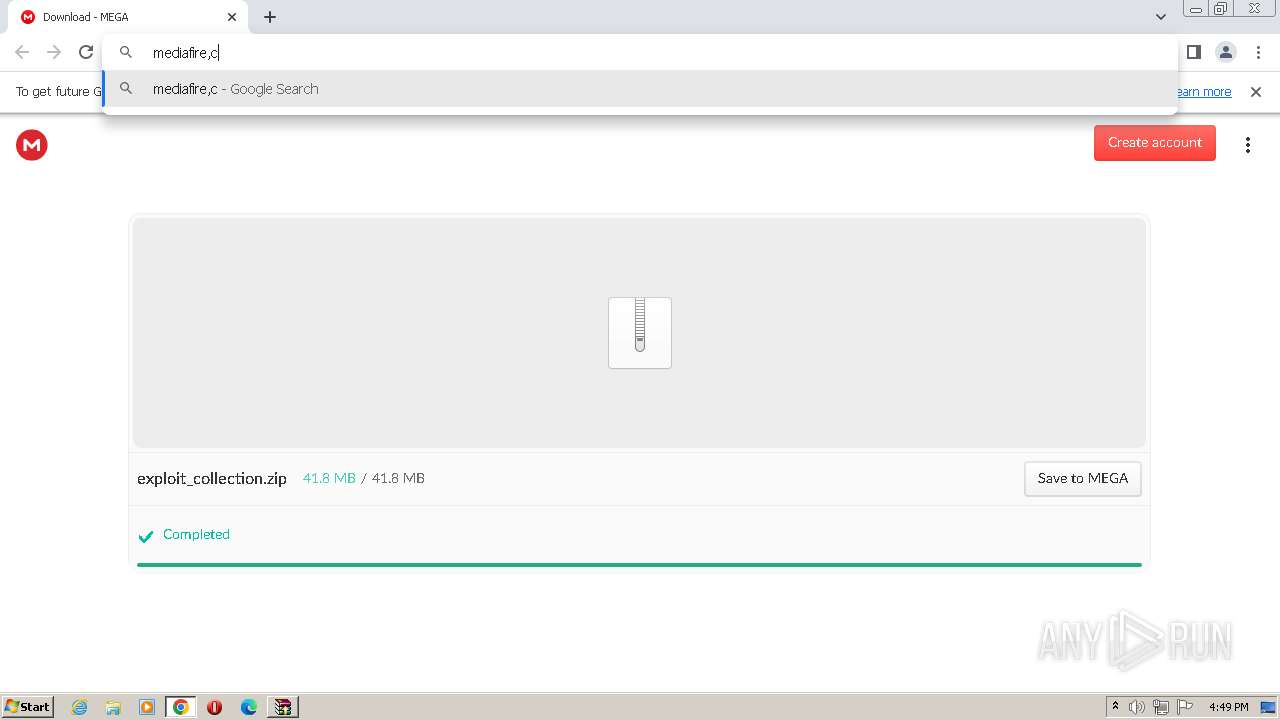
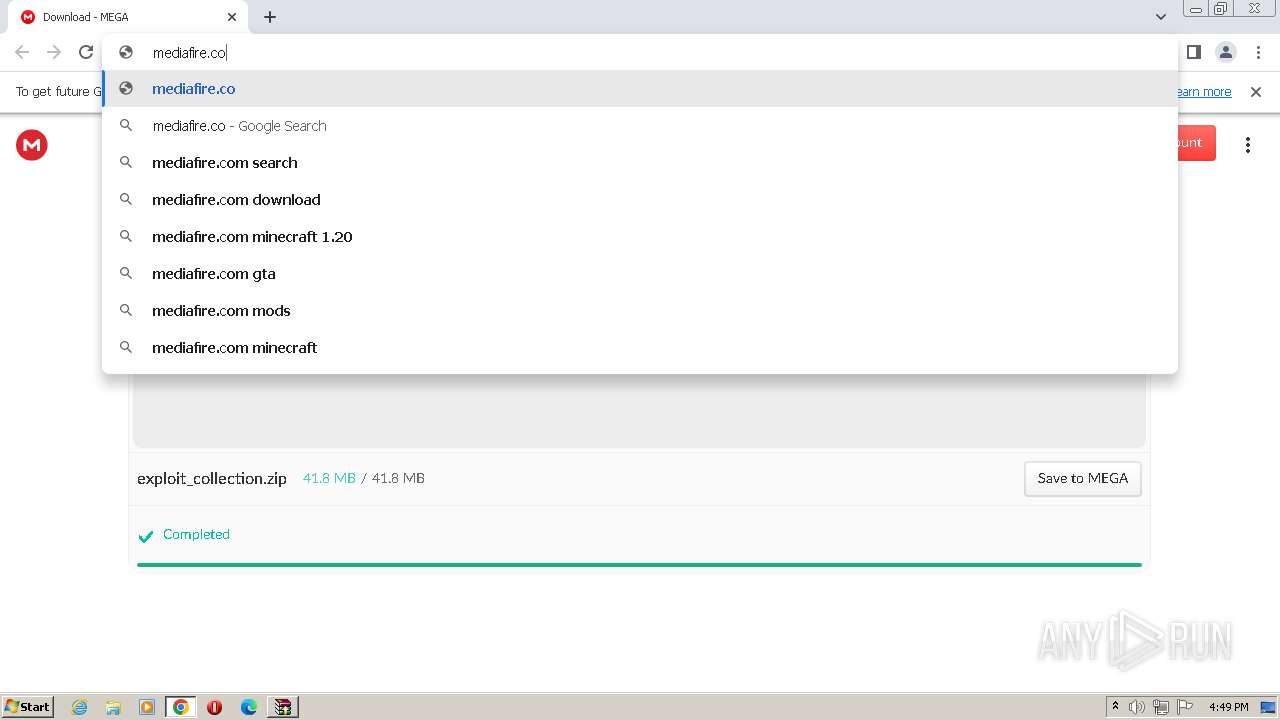
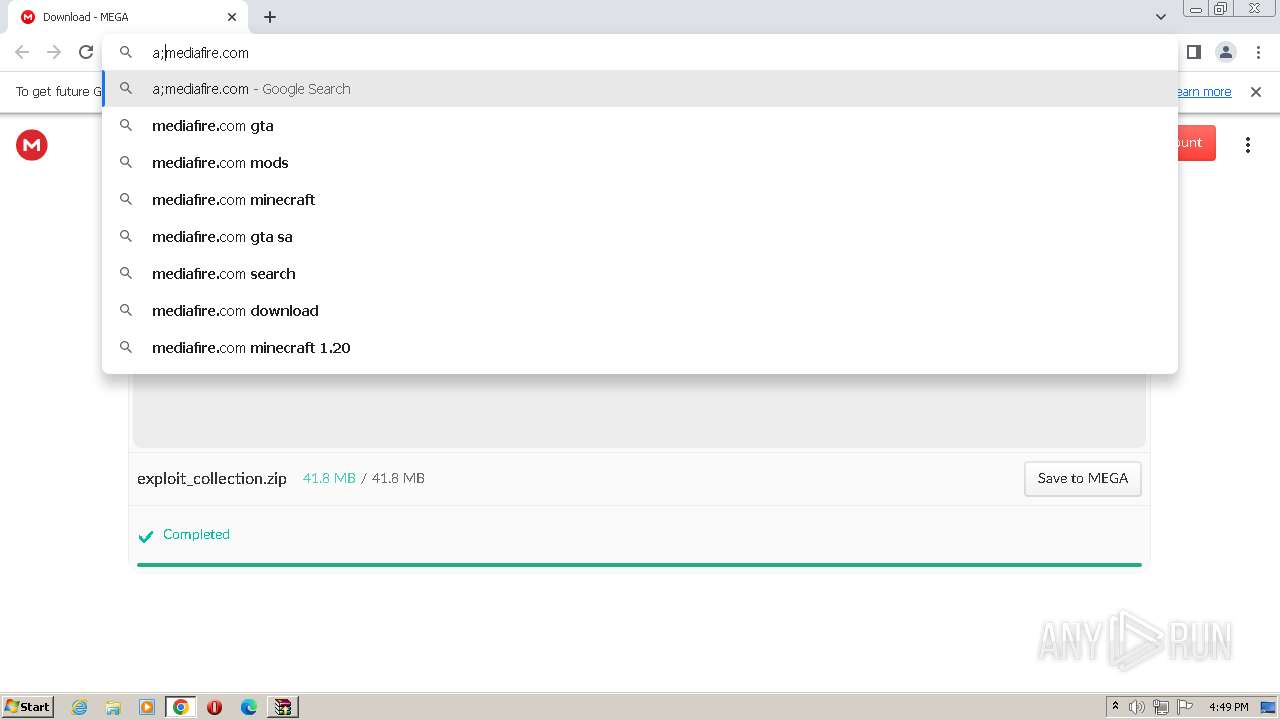
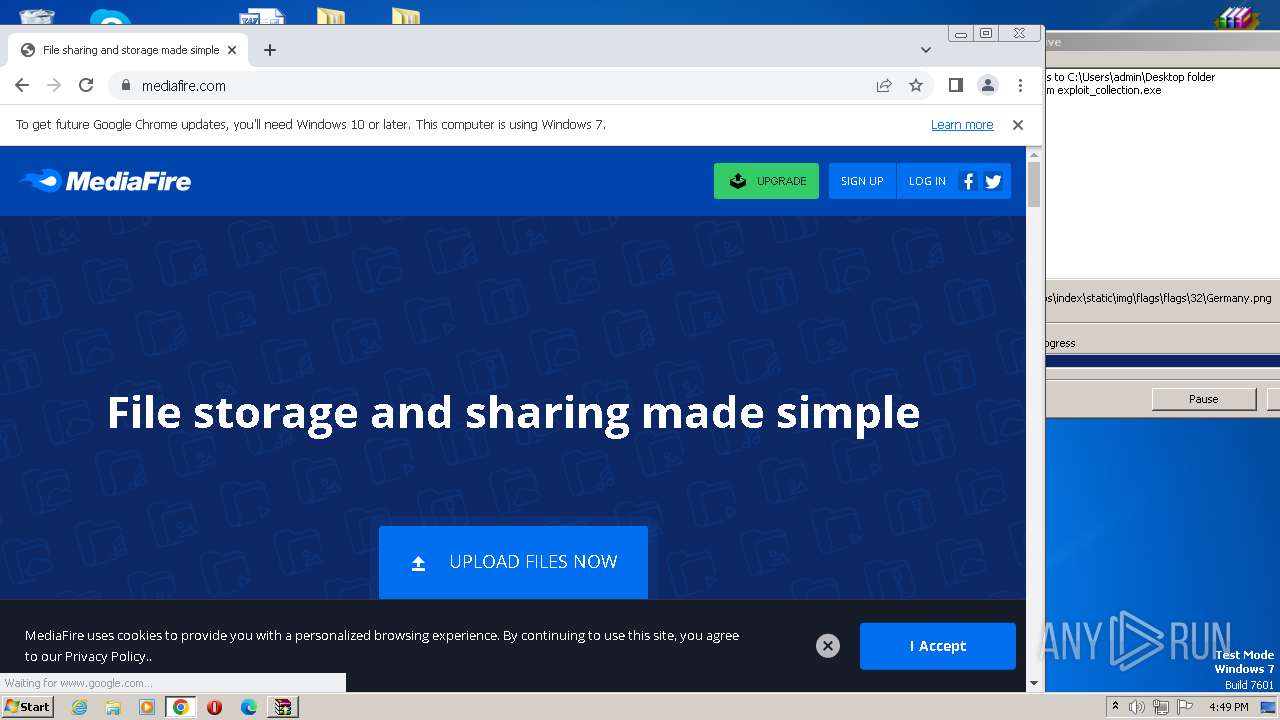
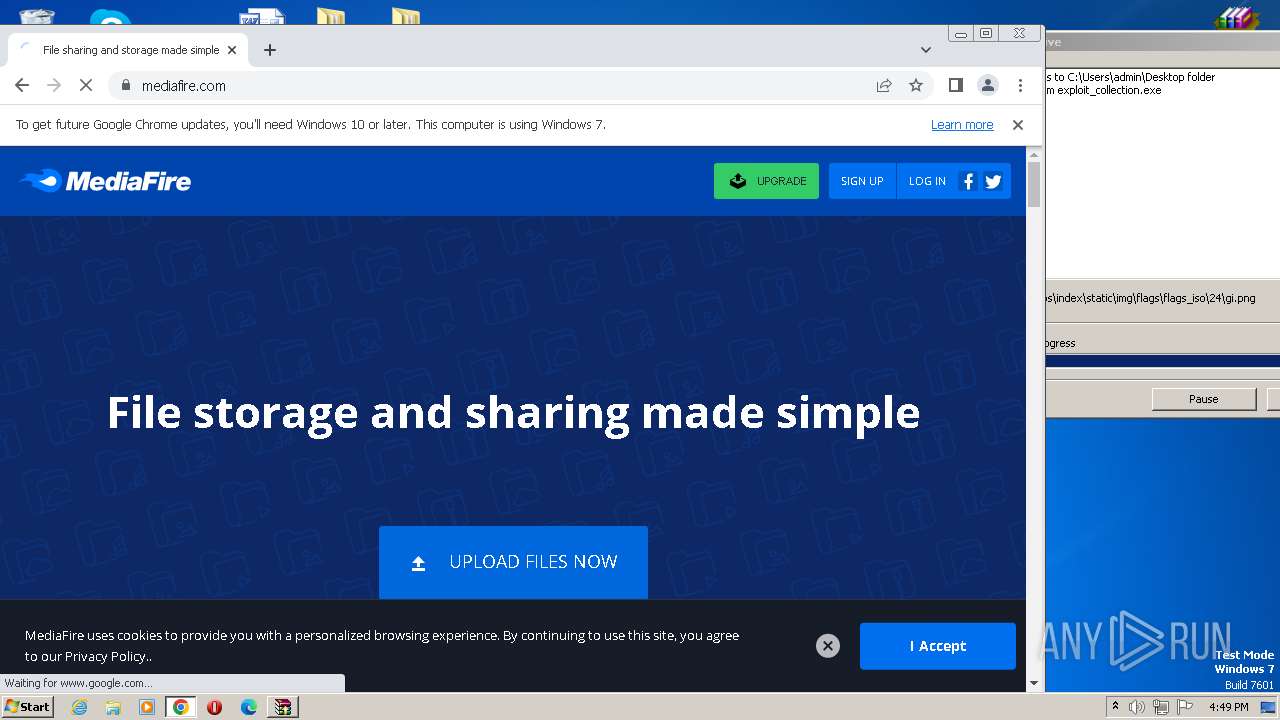
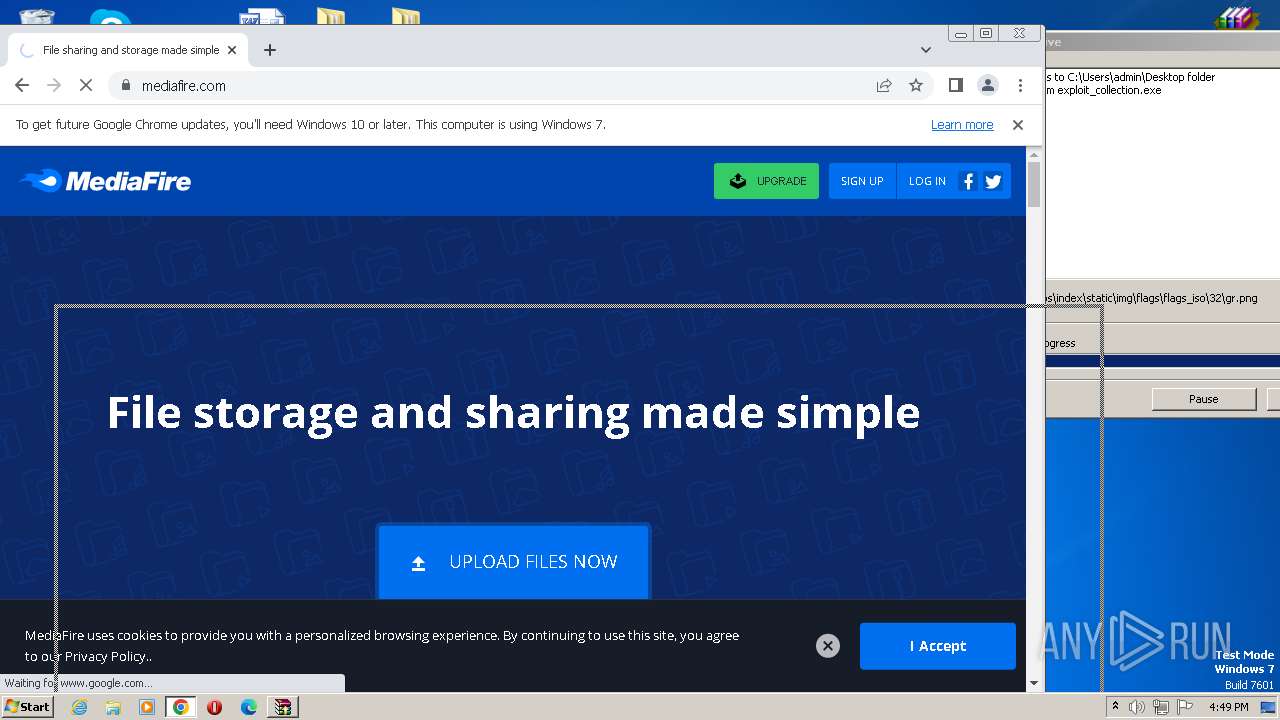
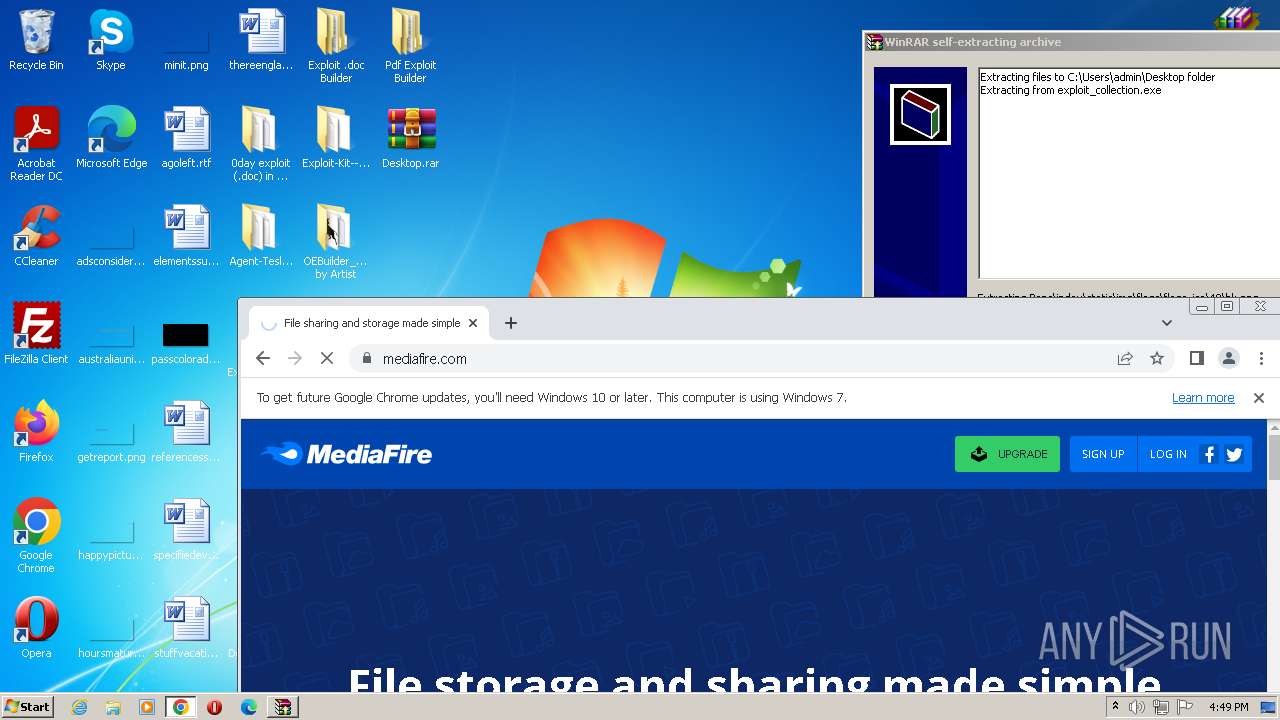
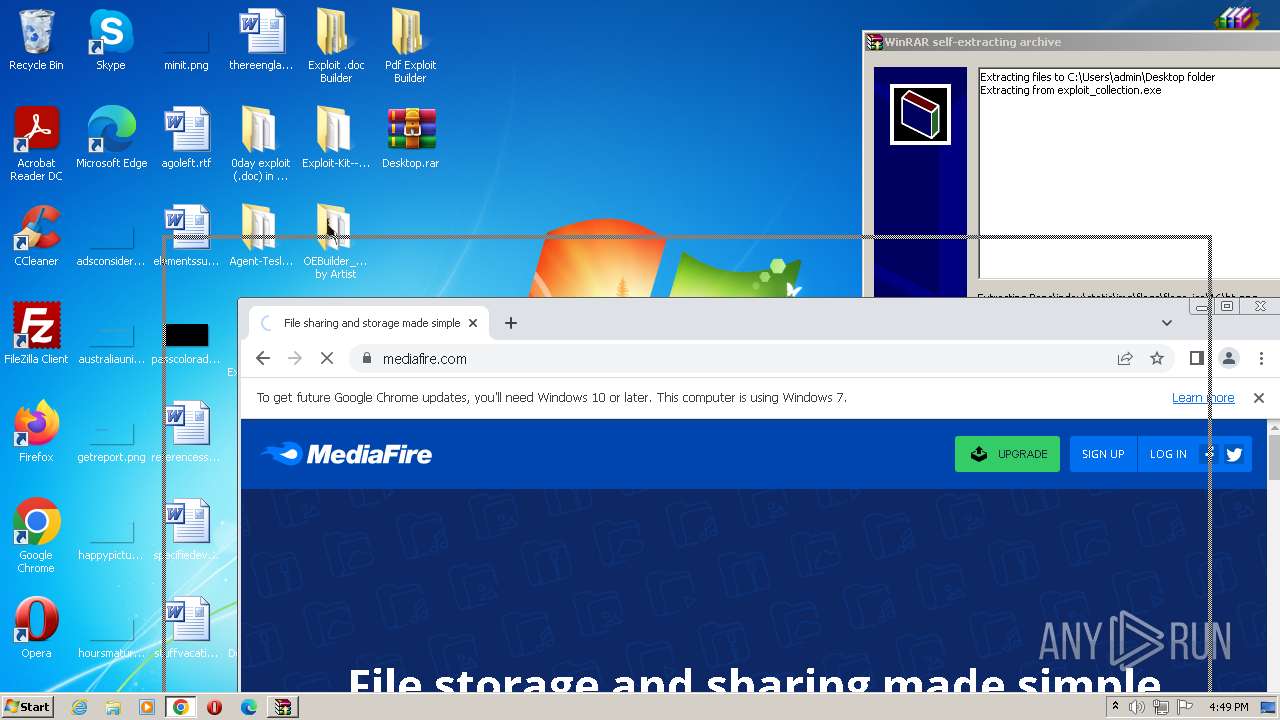
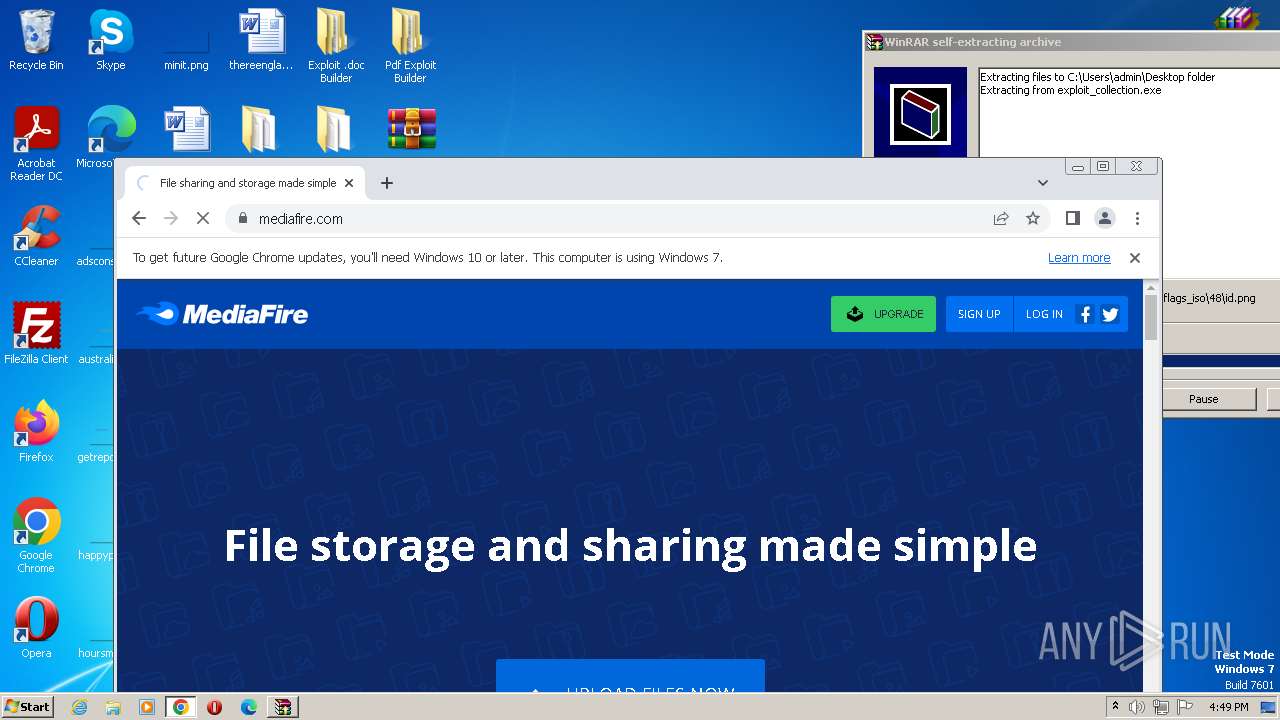
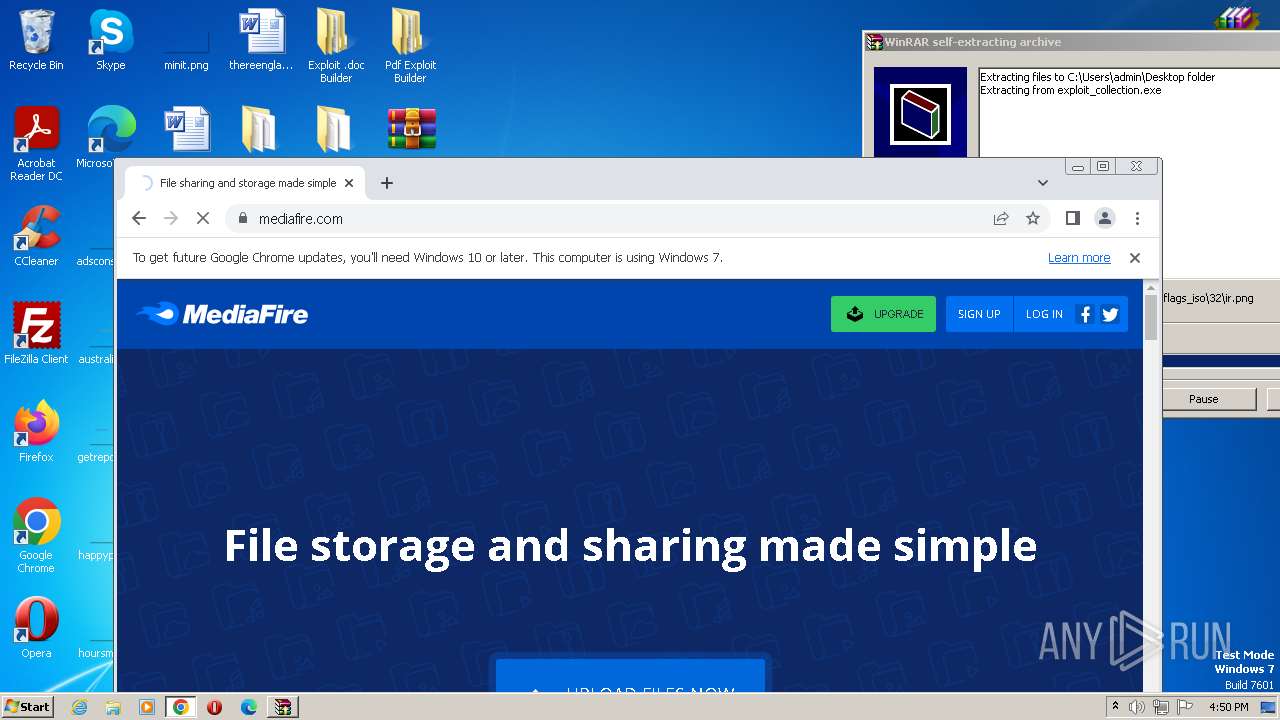
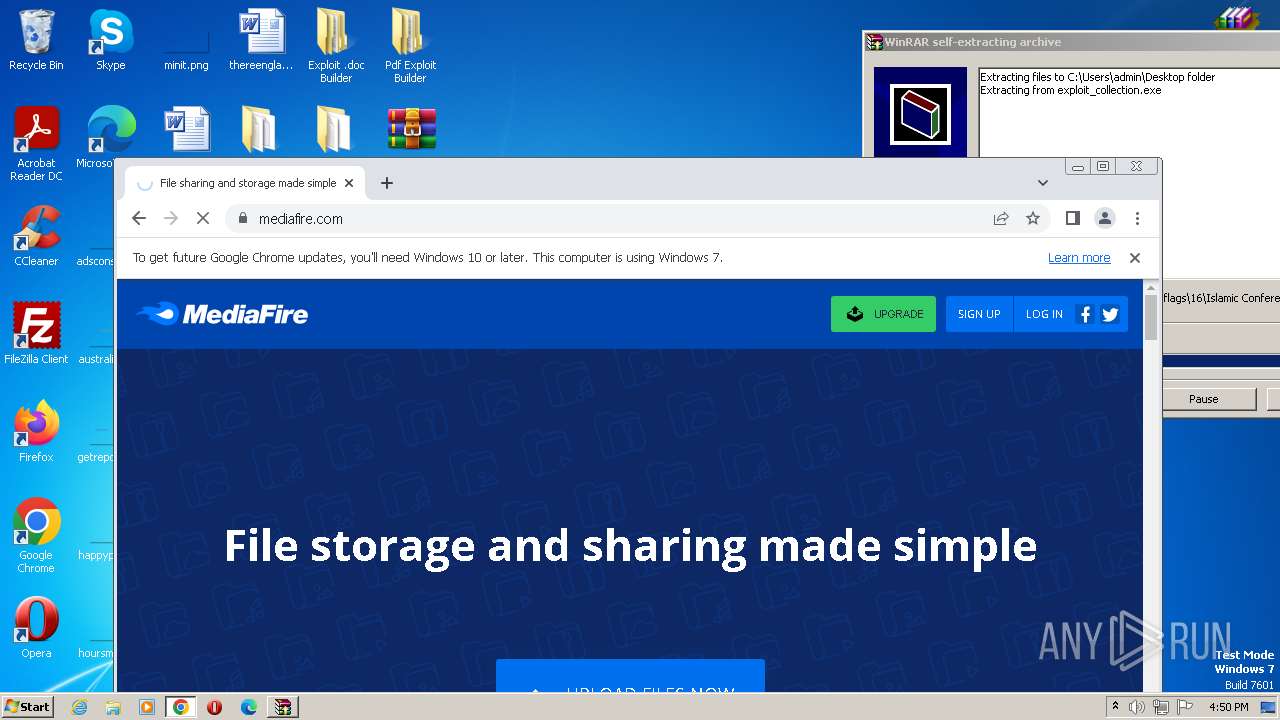
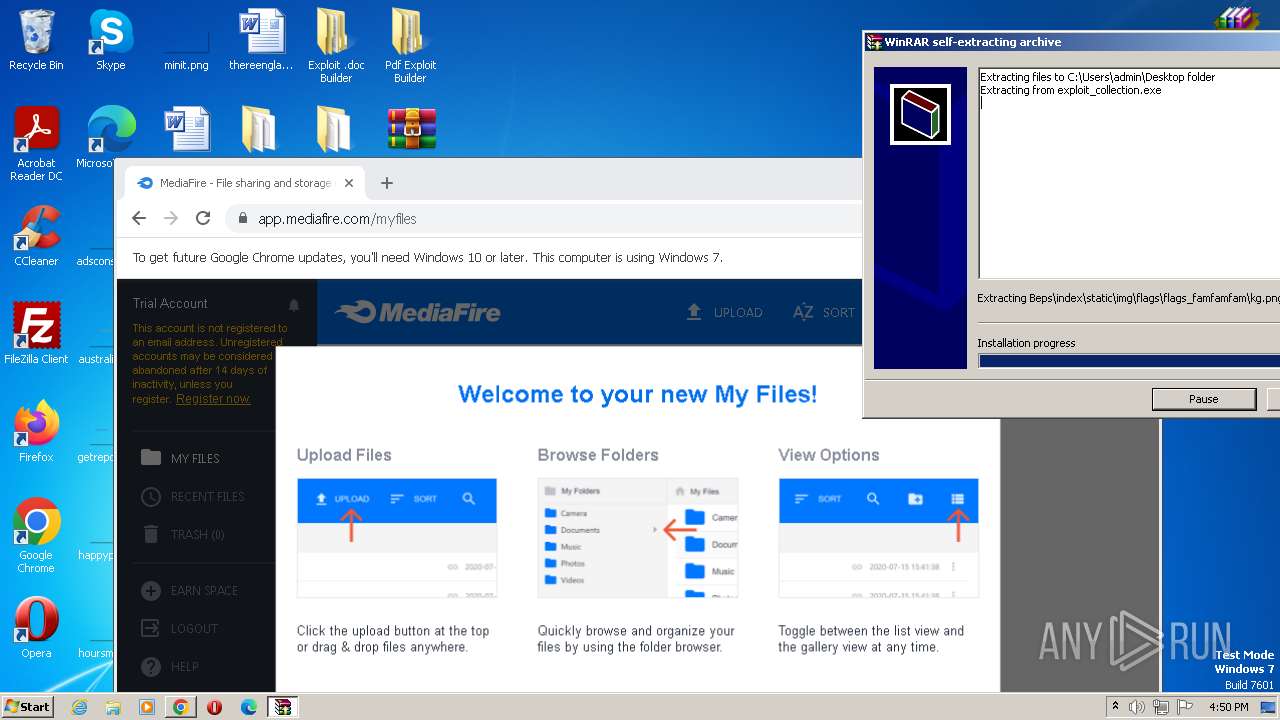
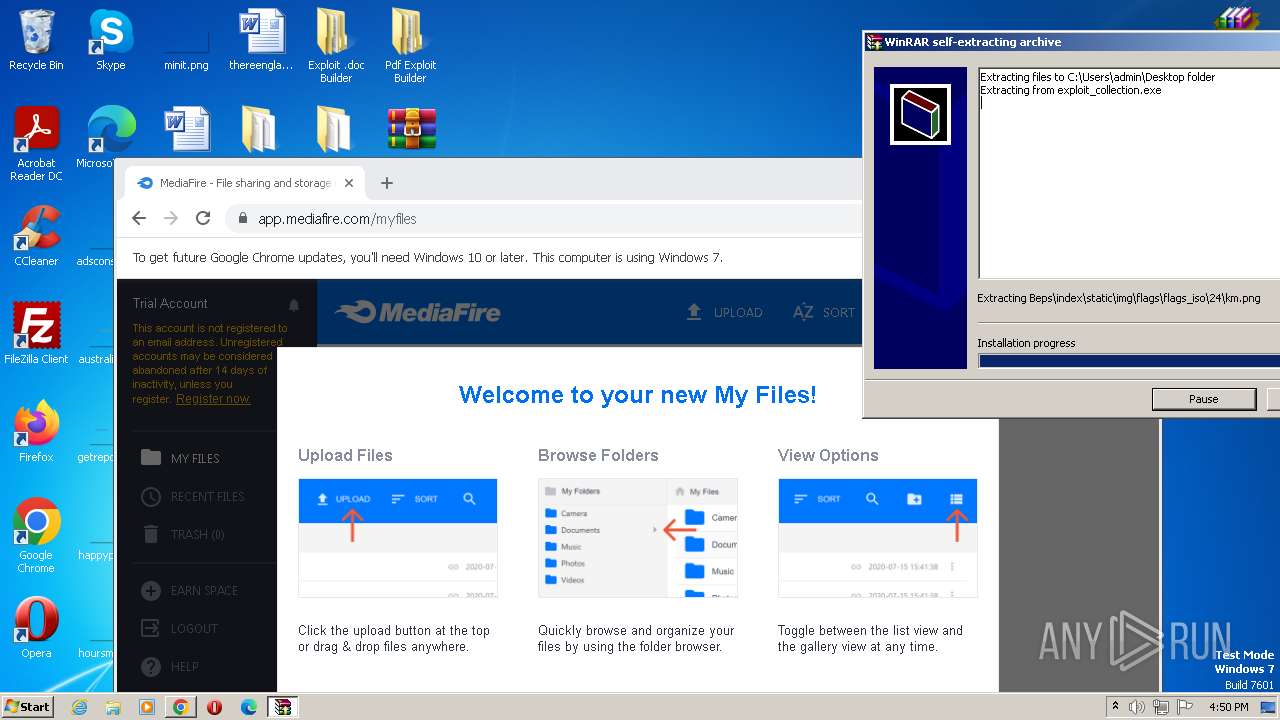
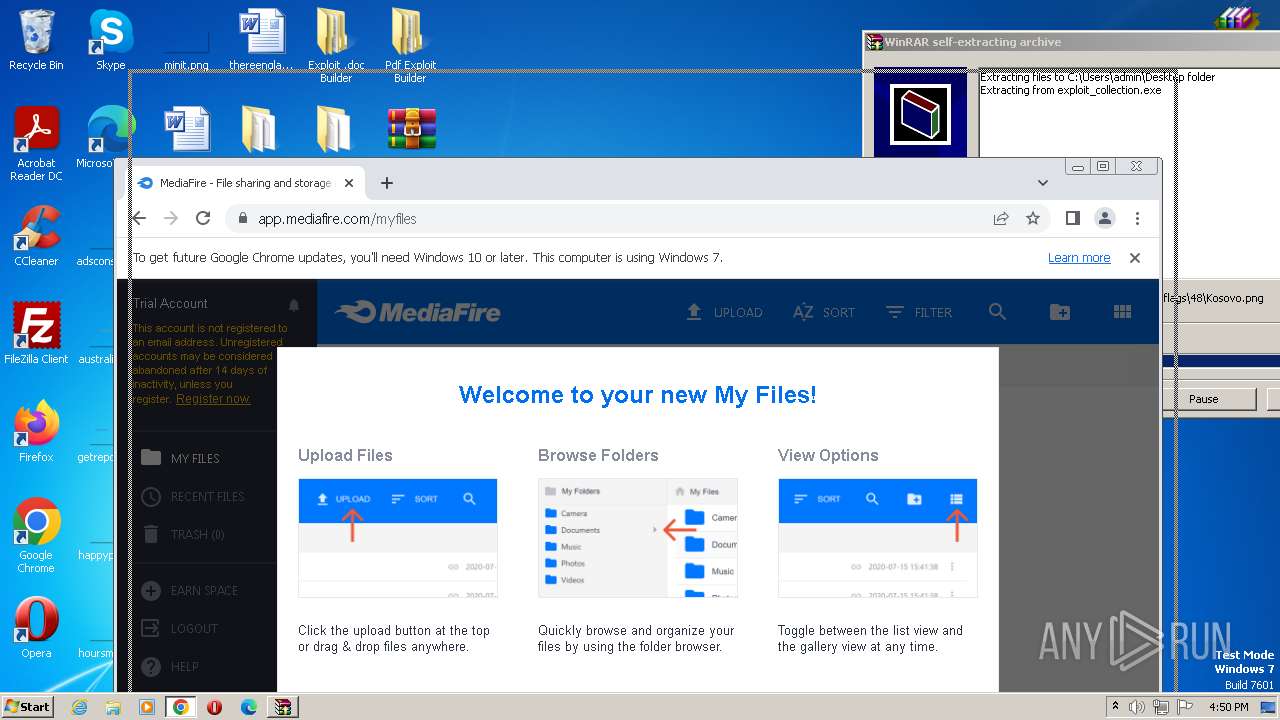
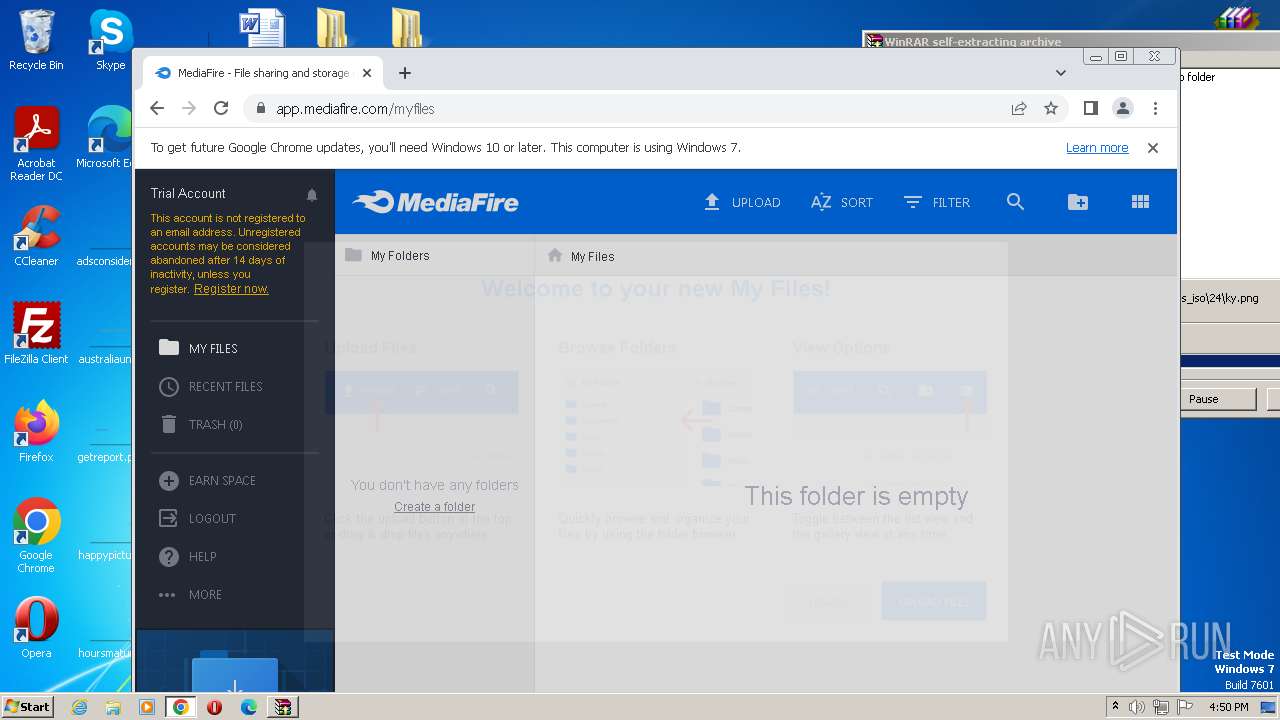
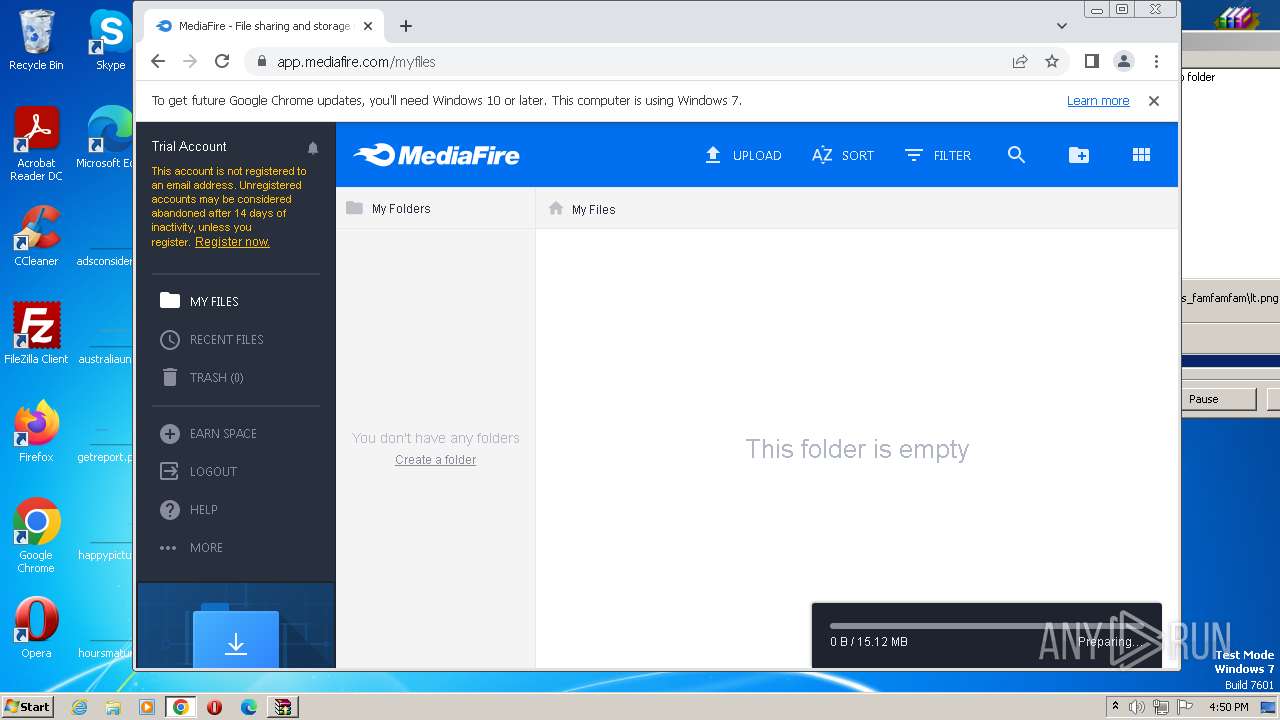
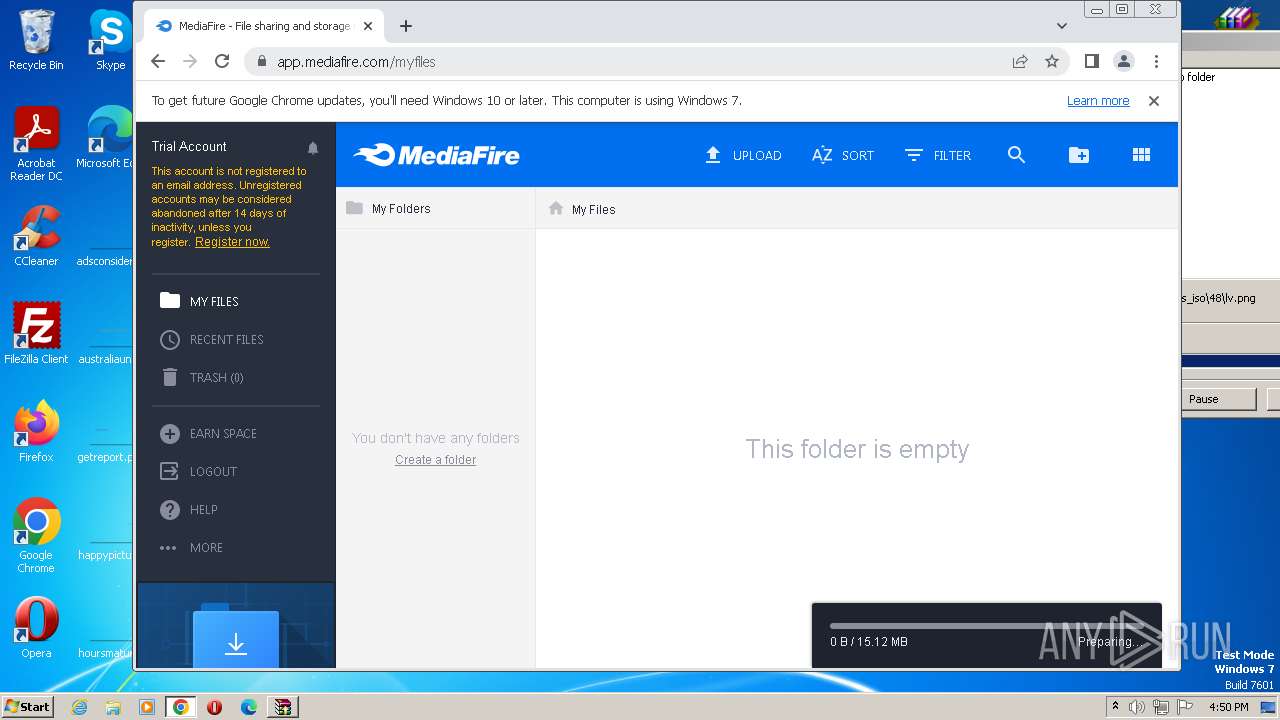
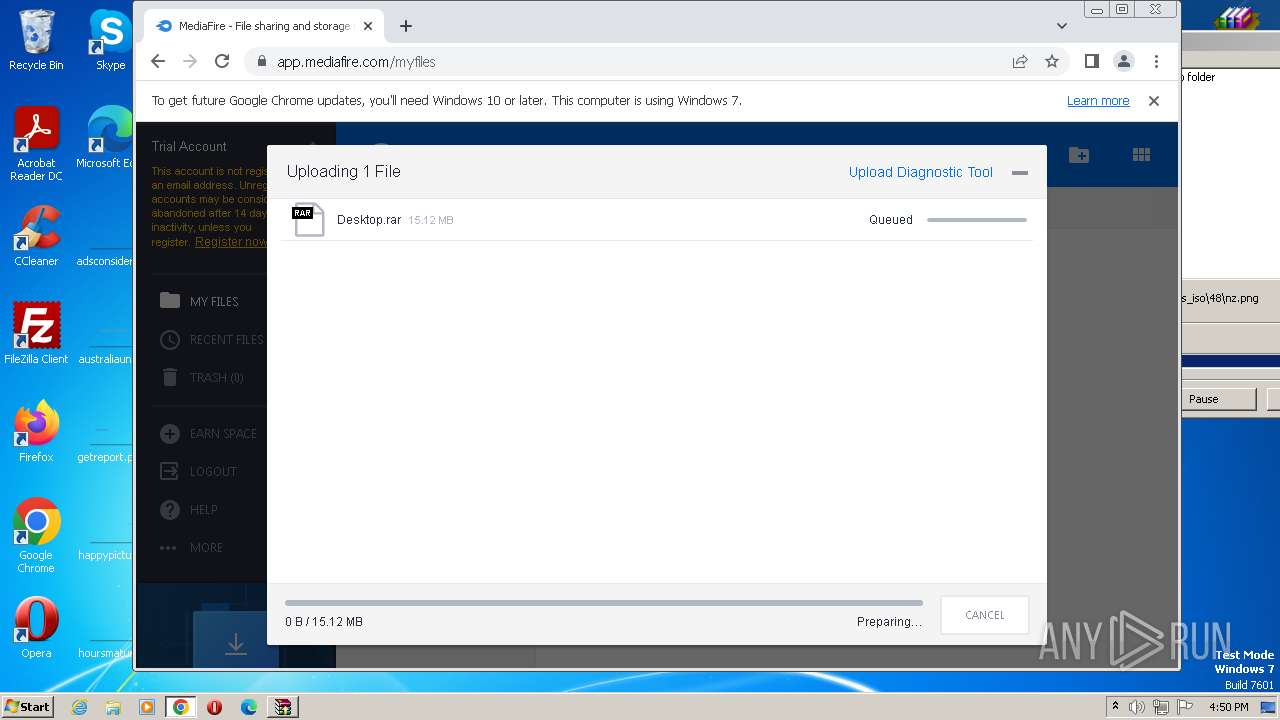
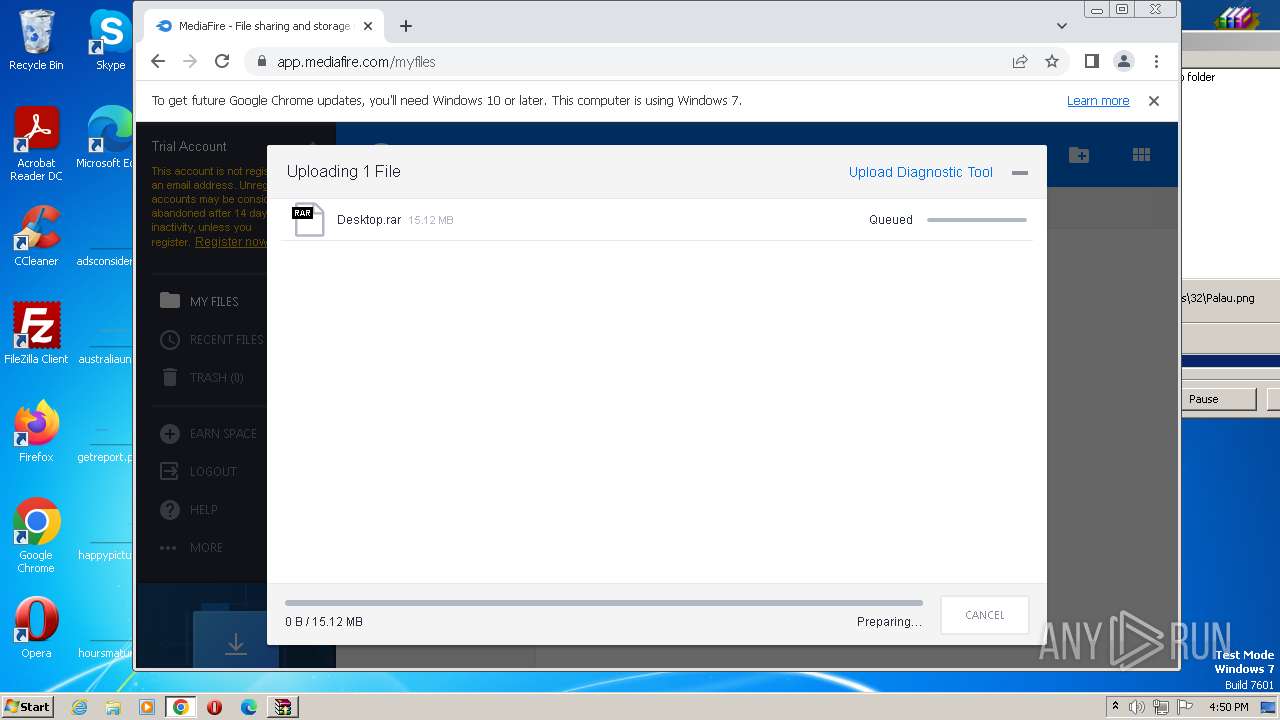
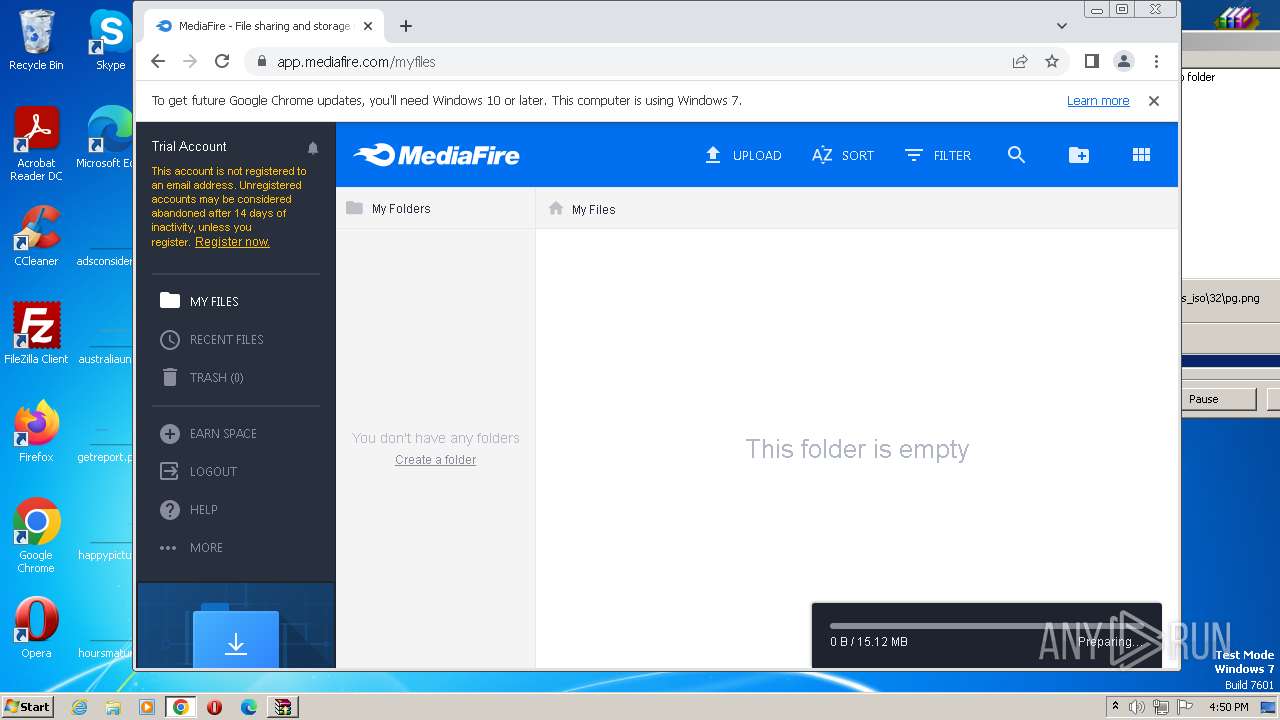
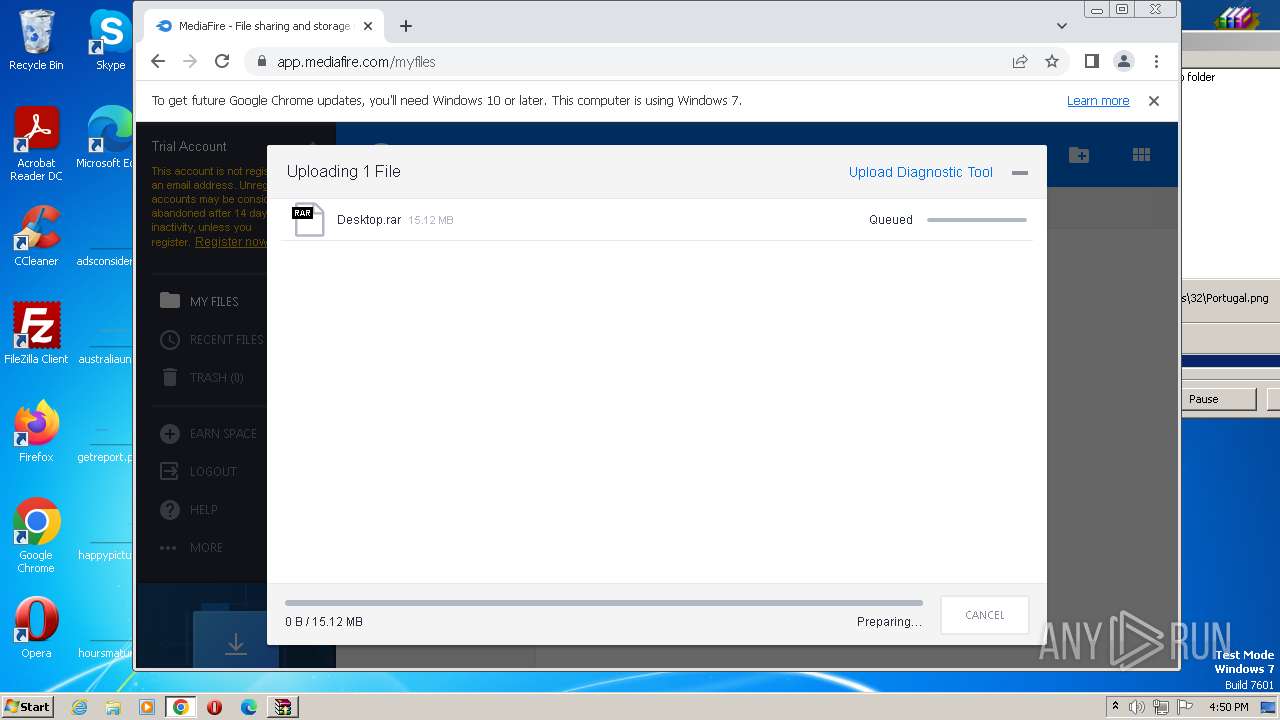
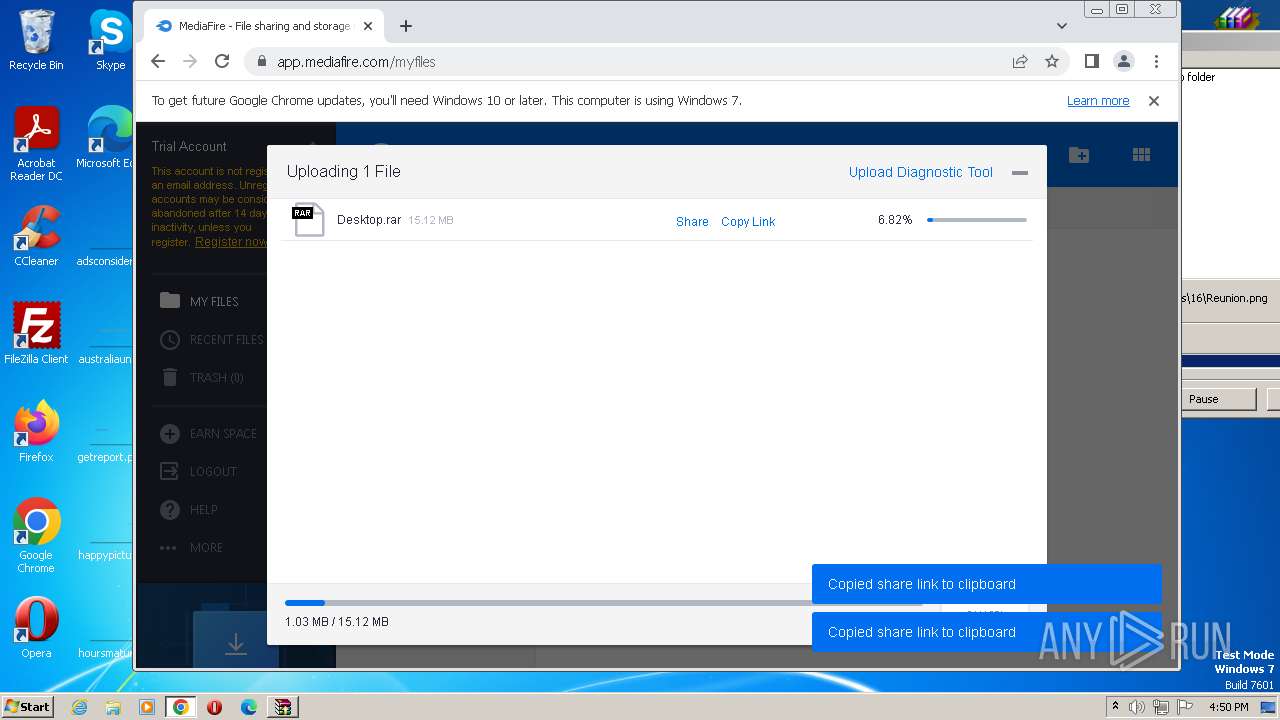
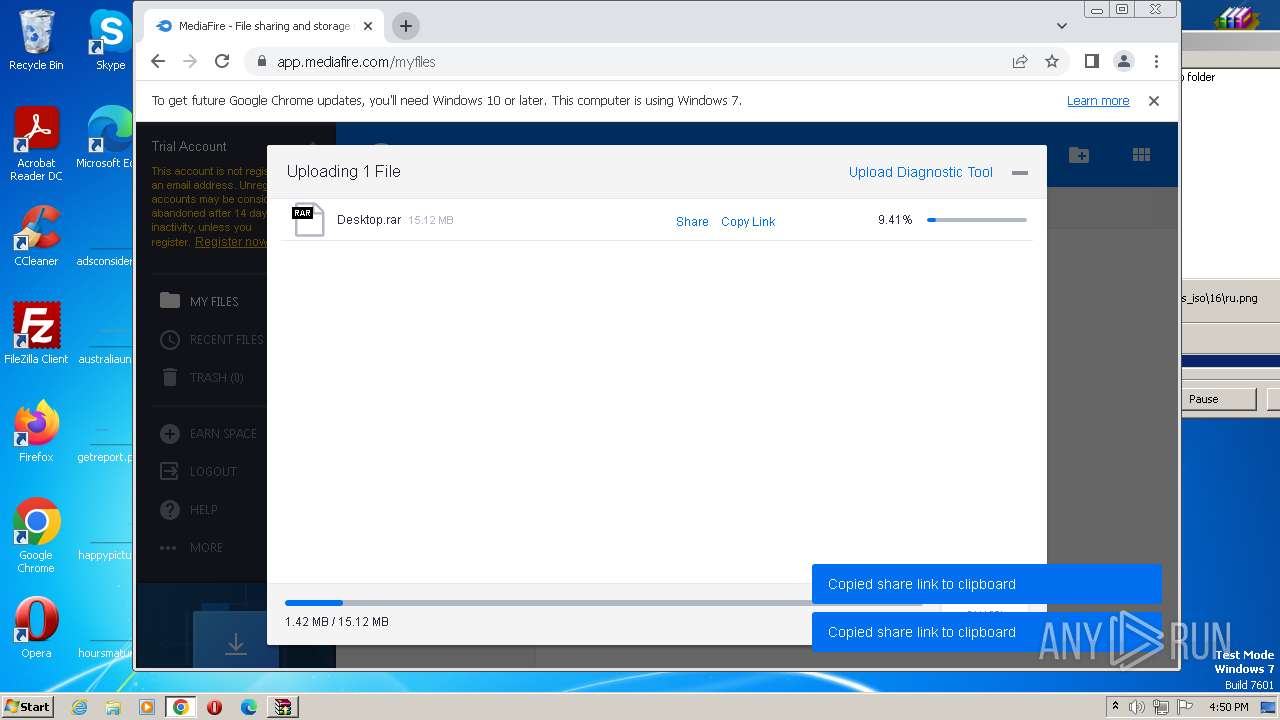
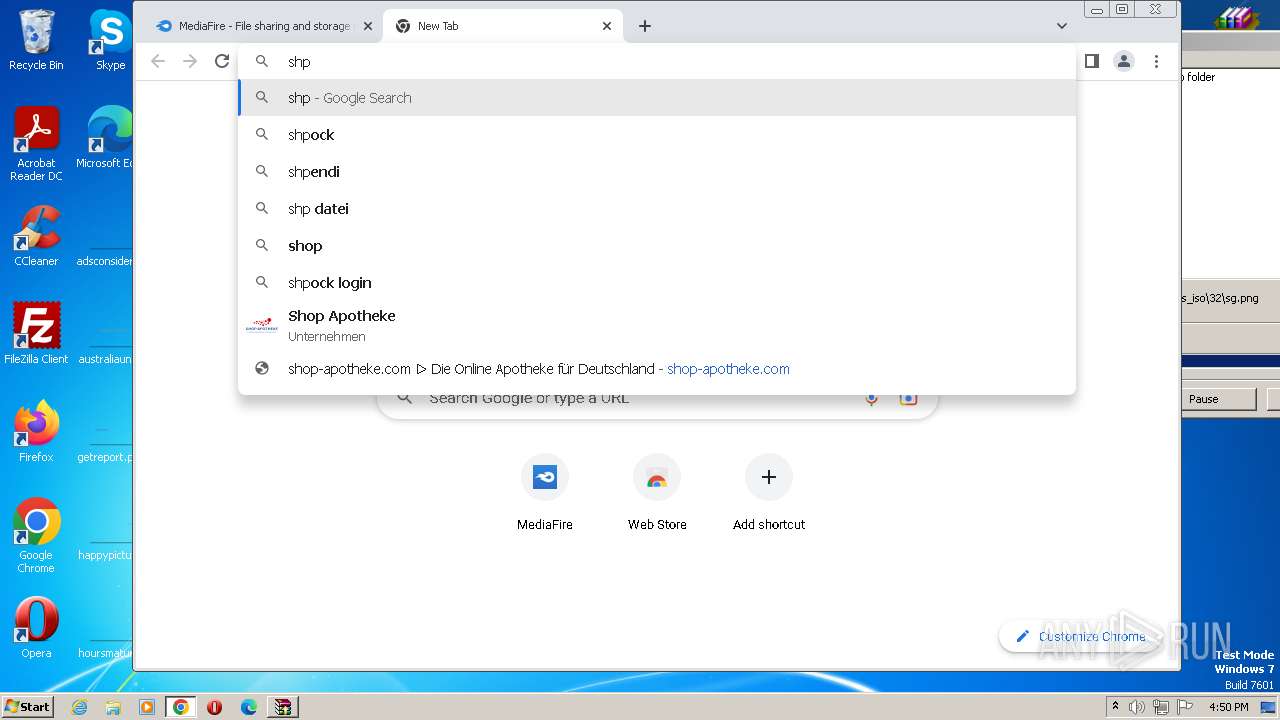
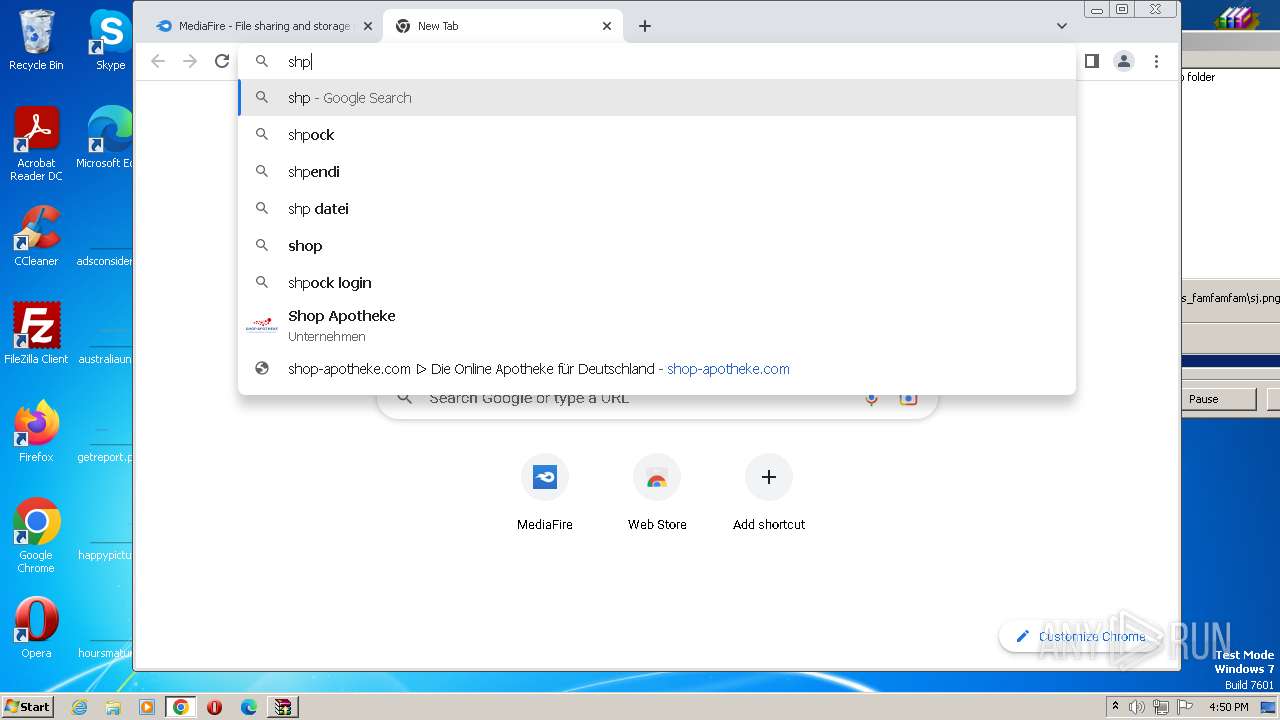
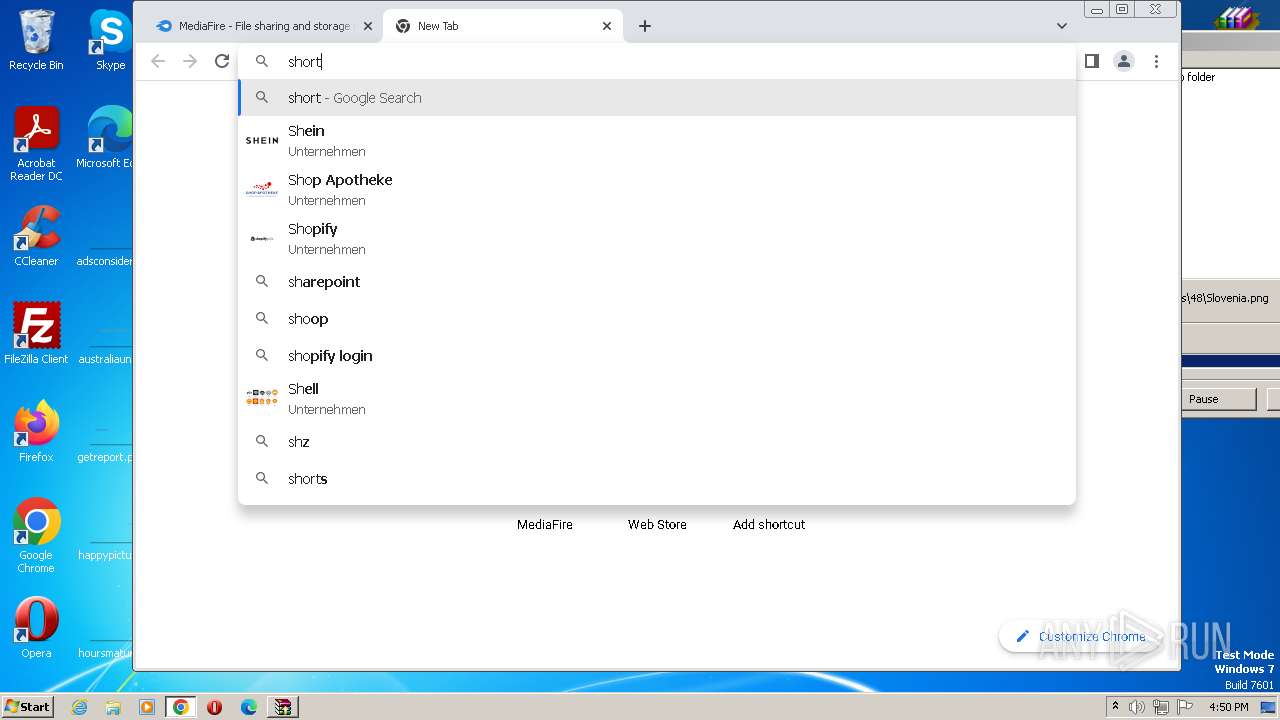
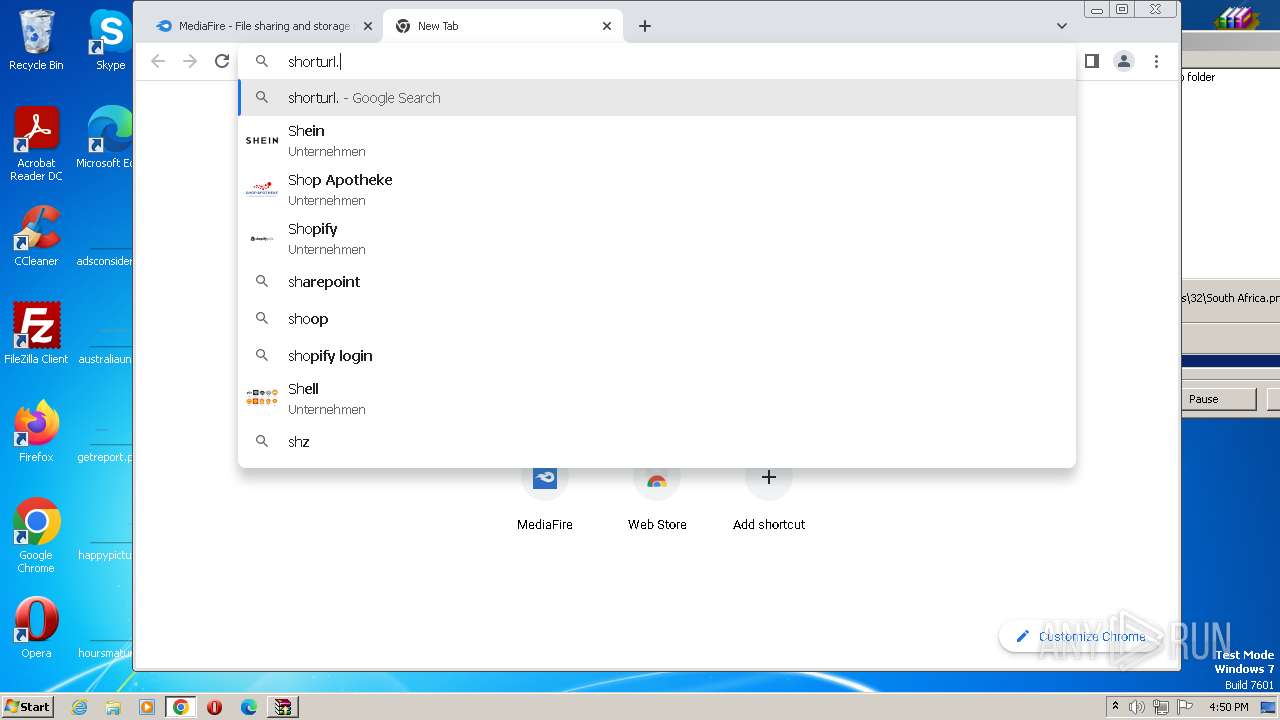
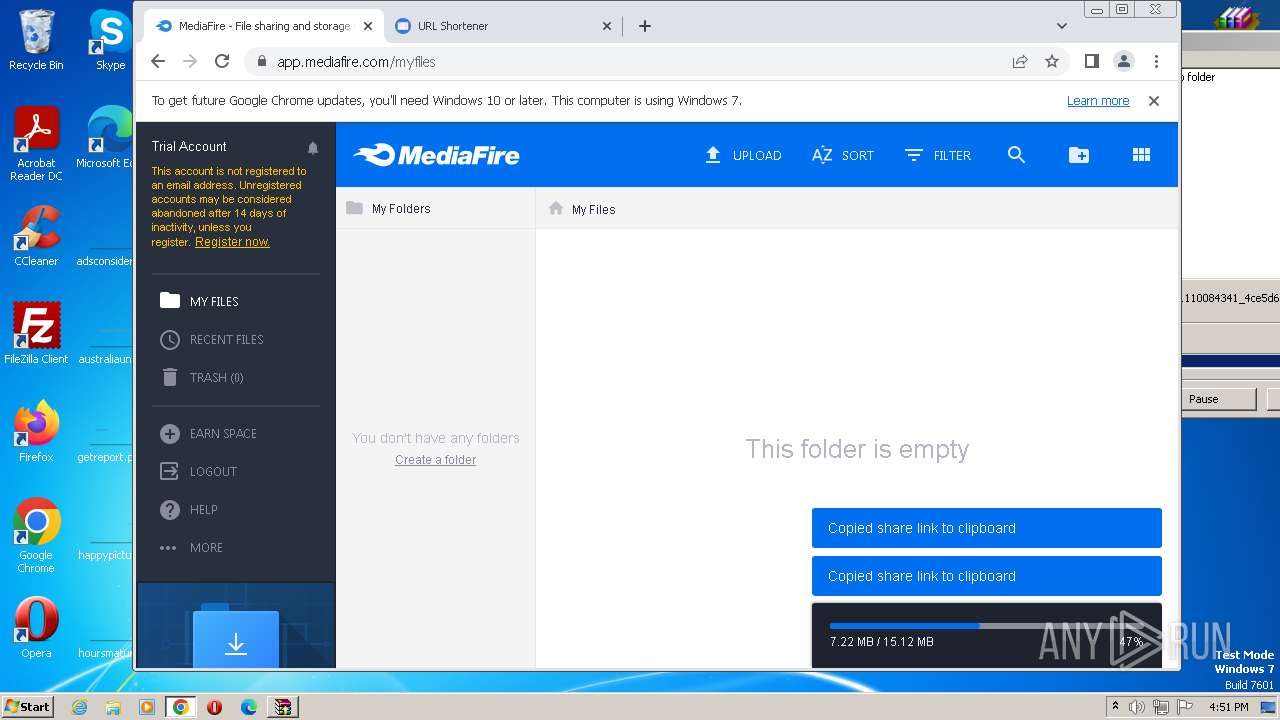
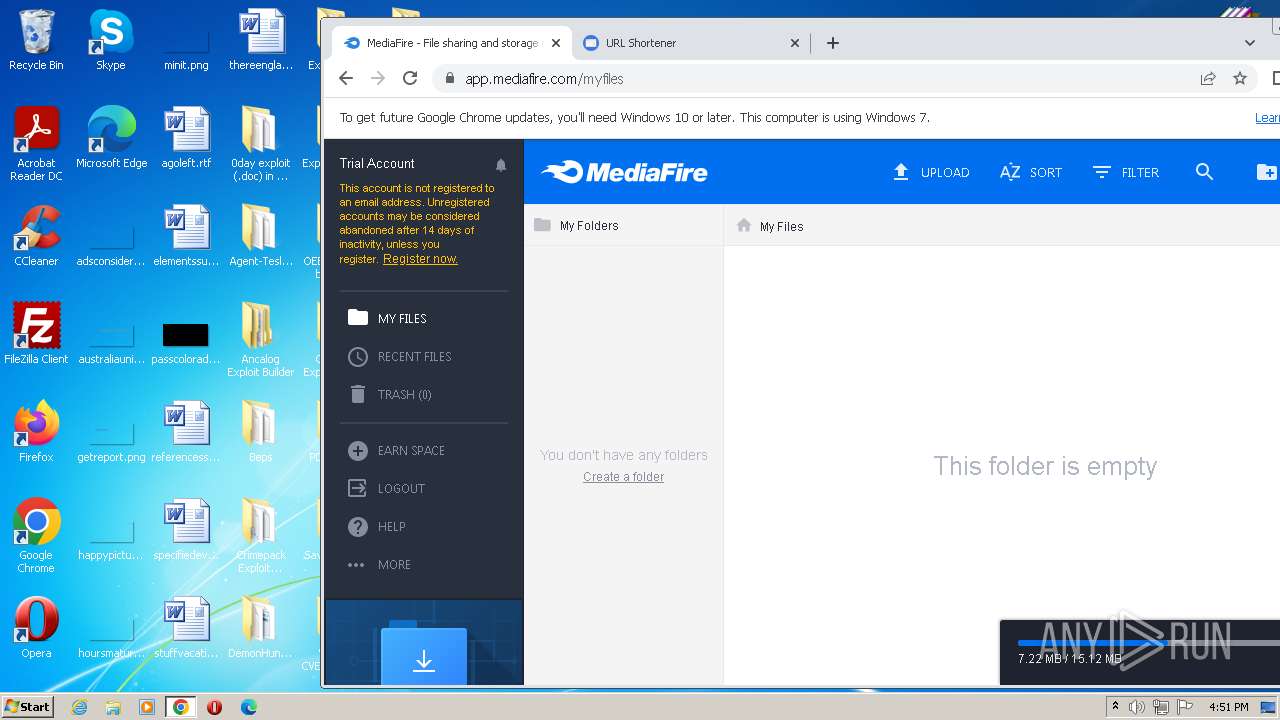
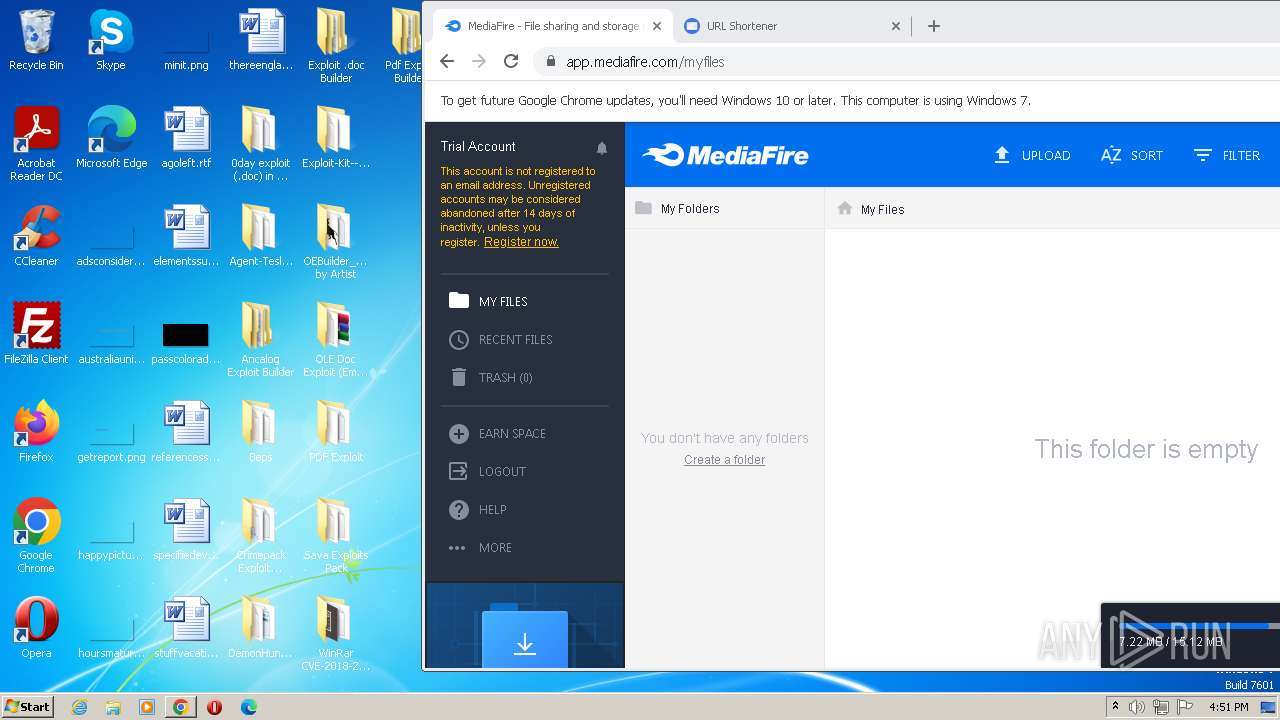
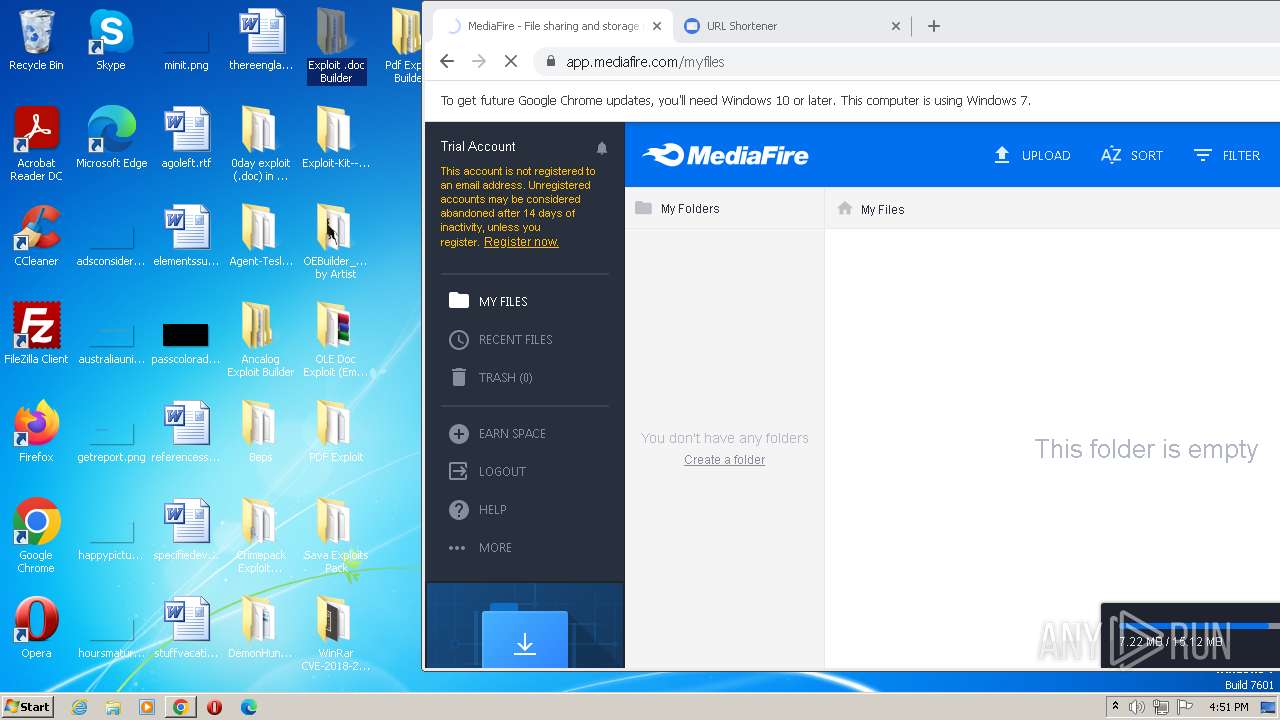
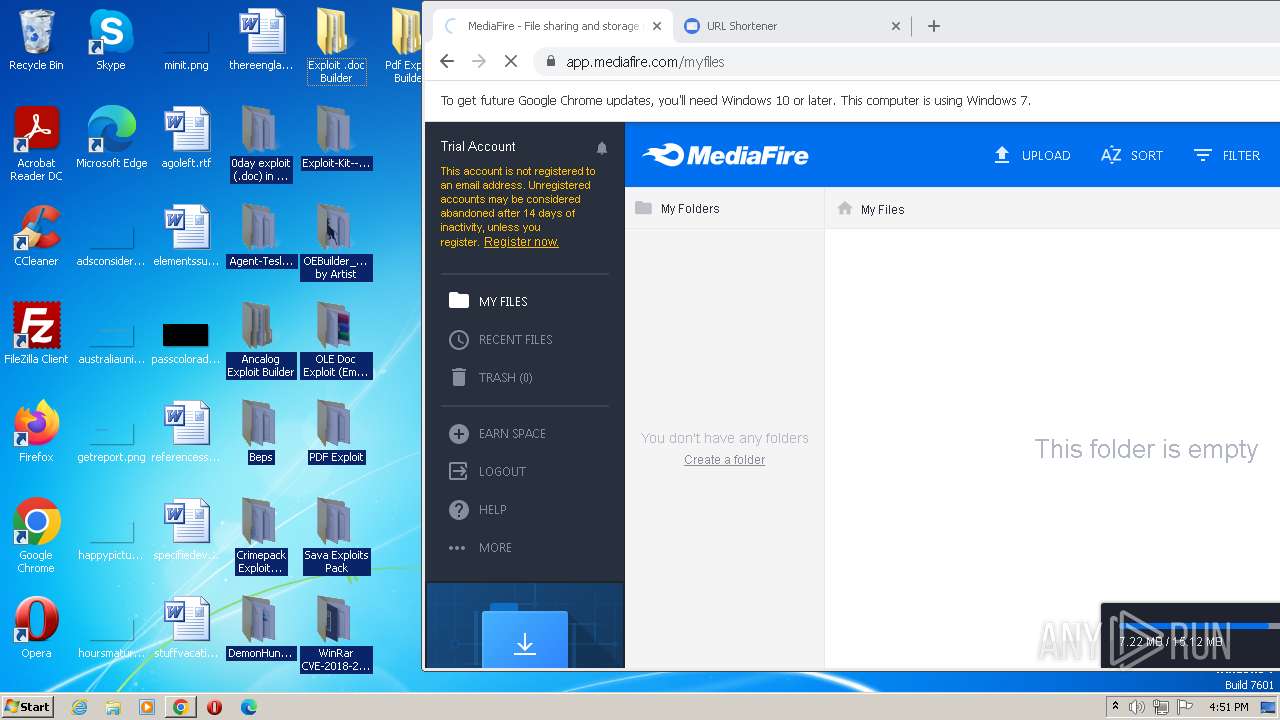
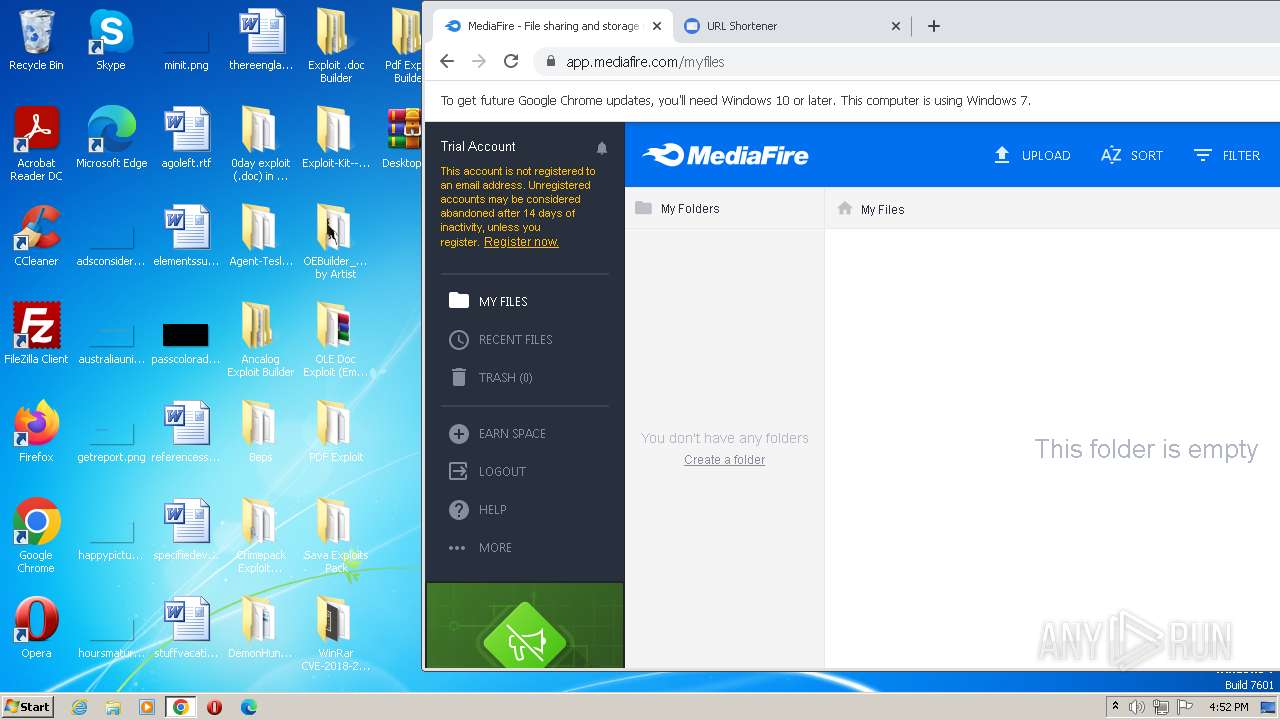
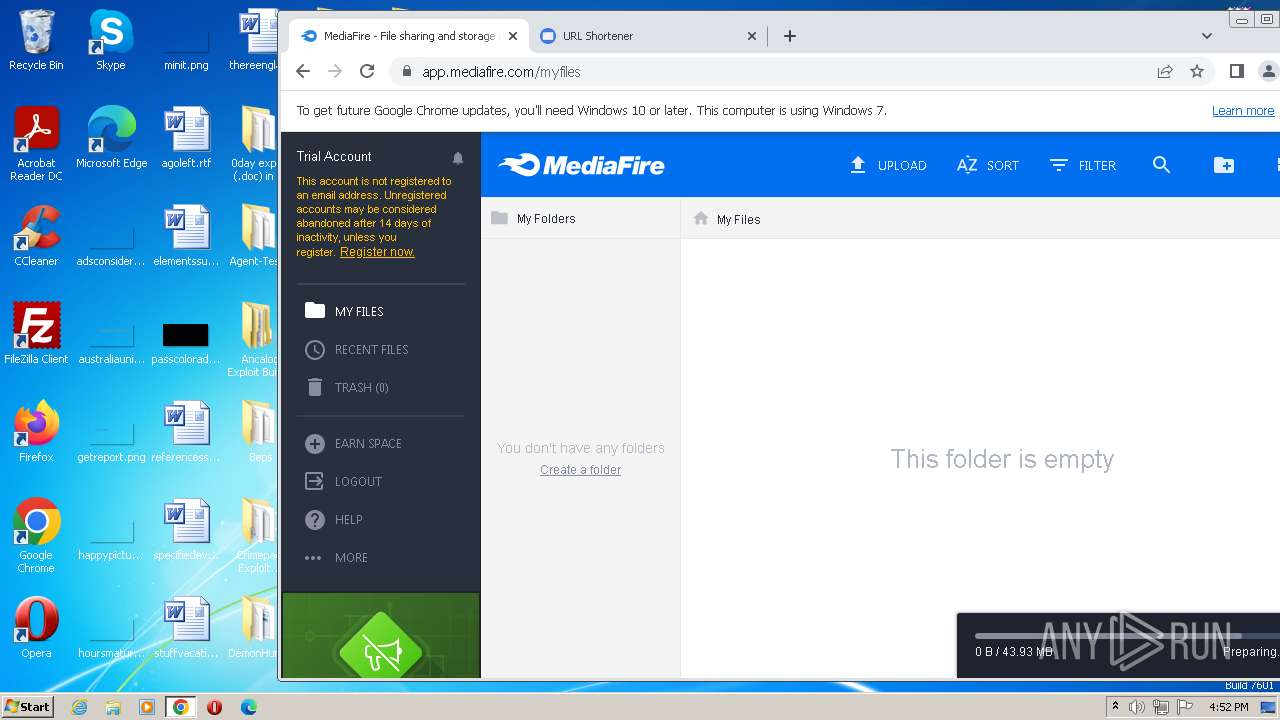
2732 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2732 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |