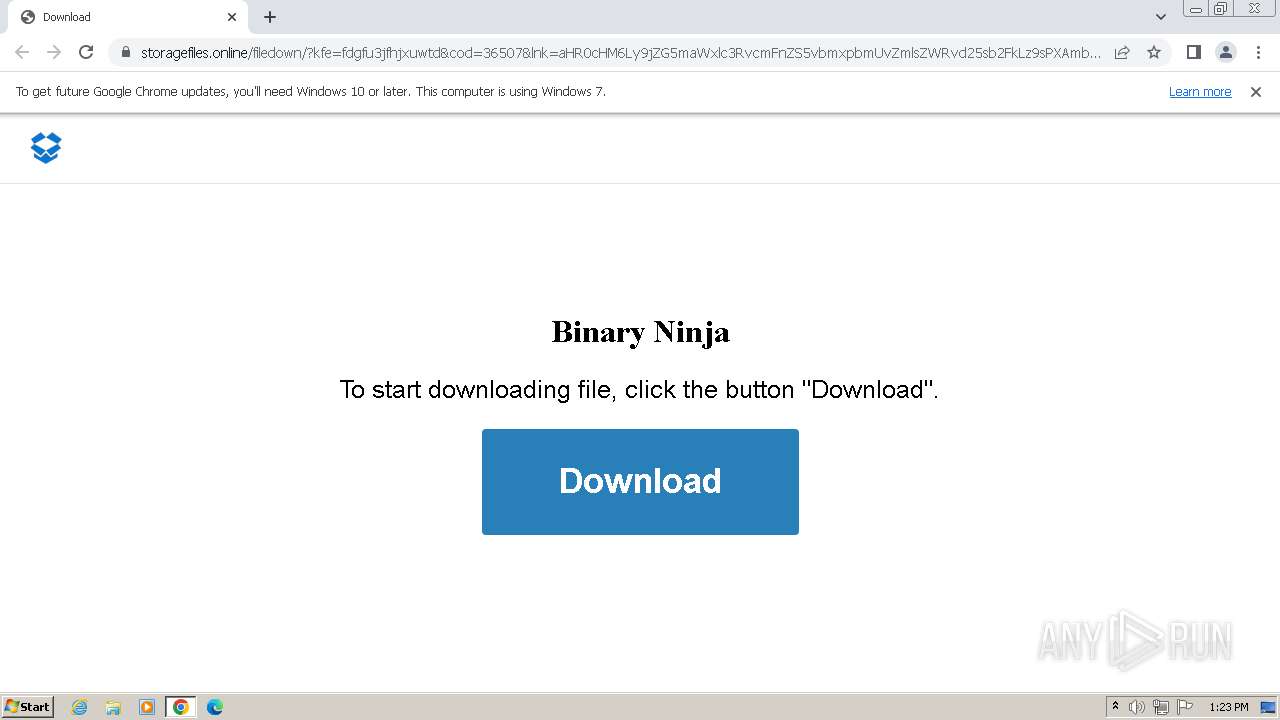
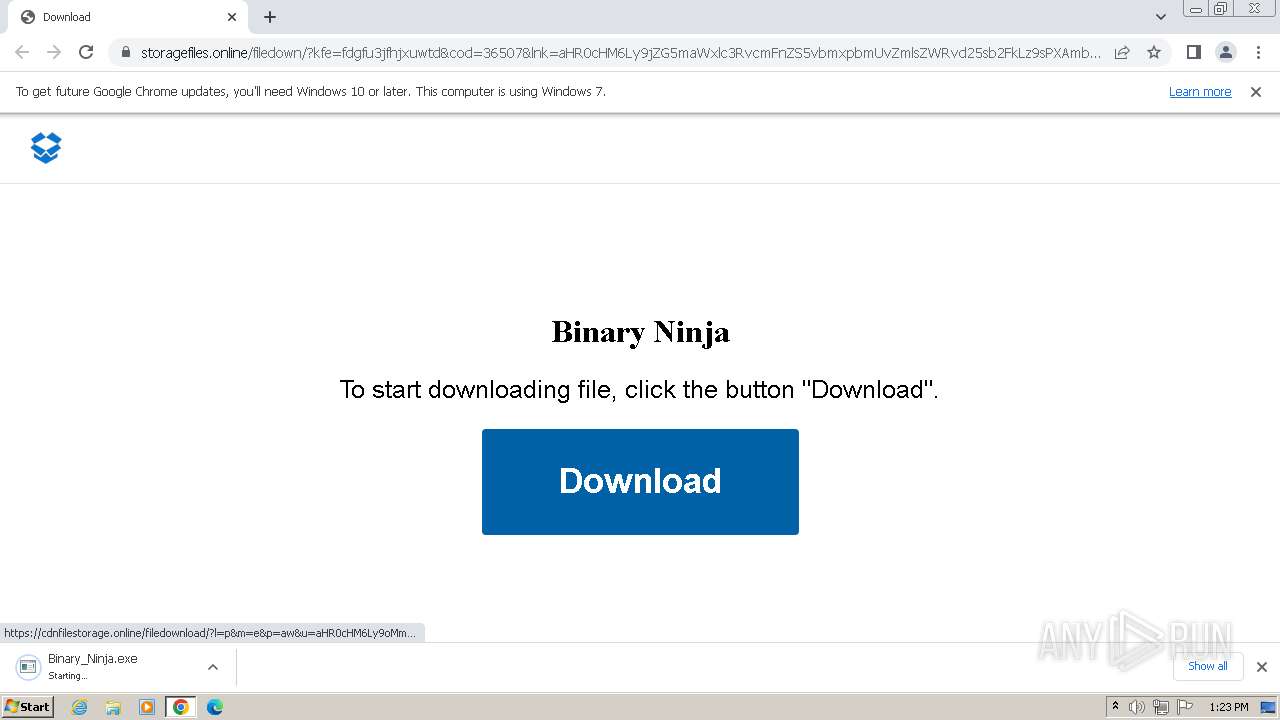
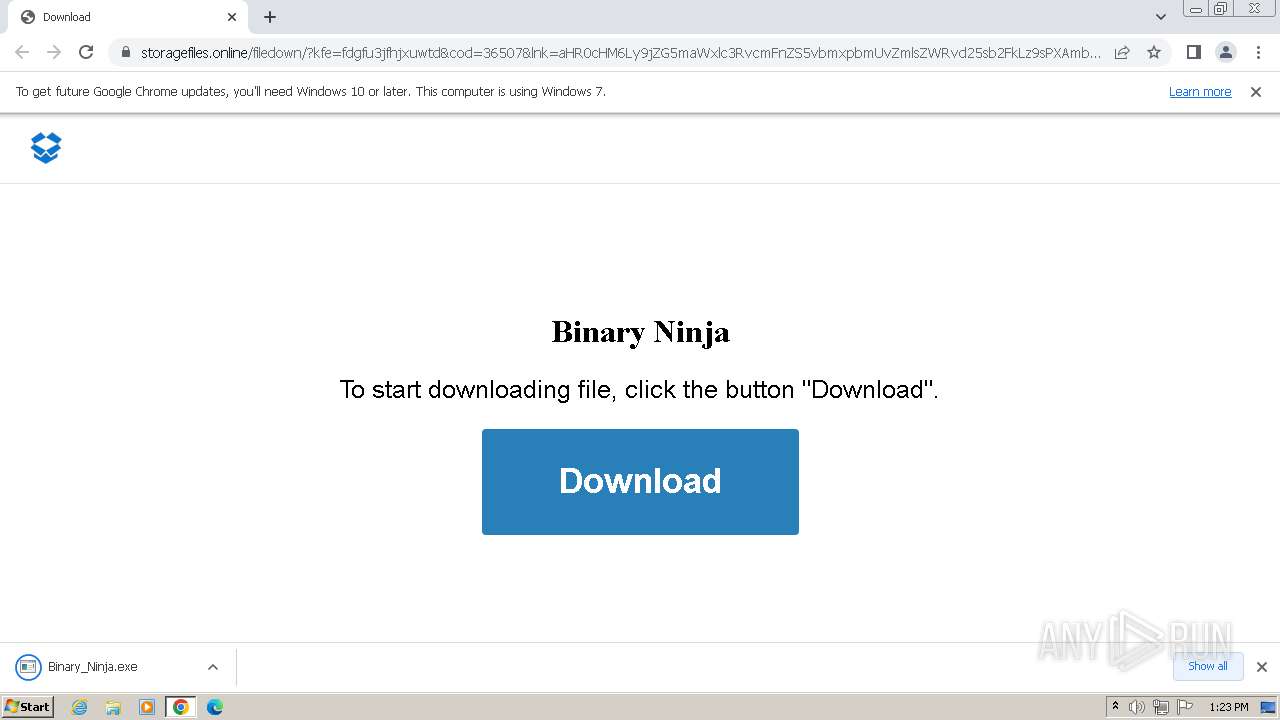
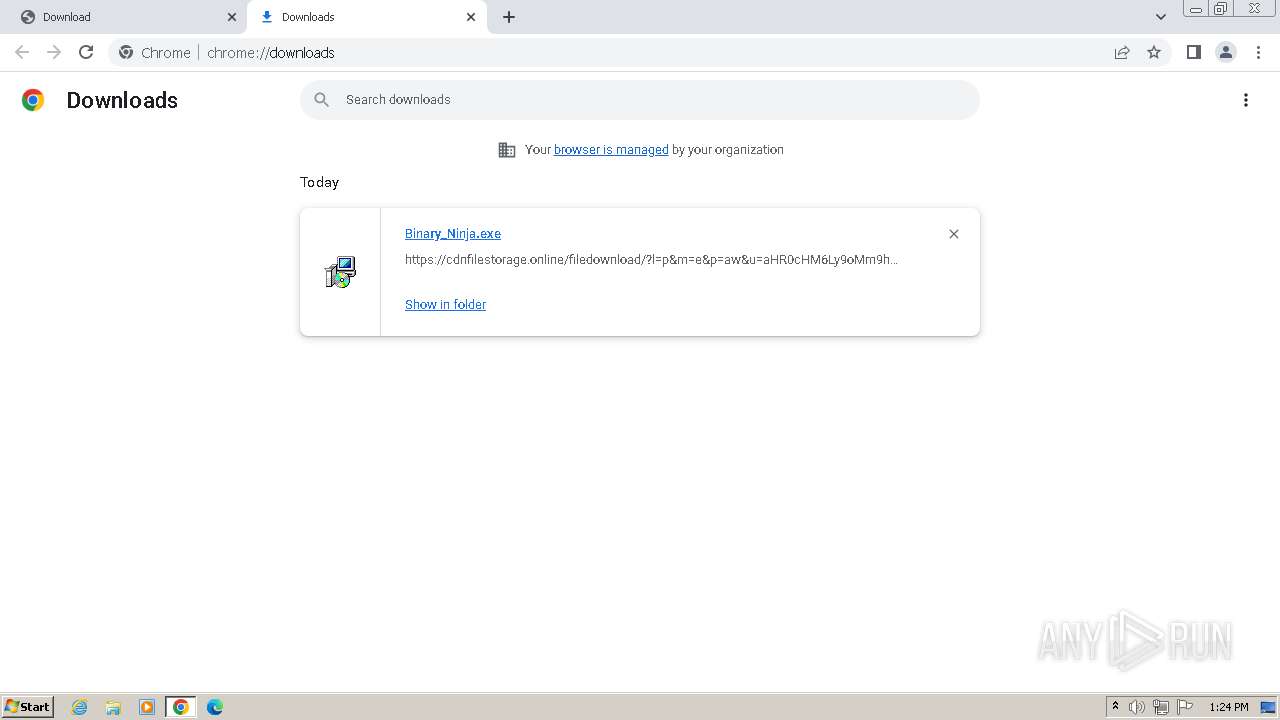
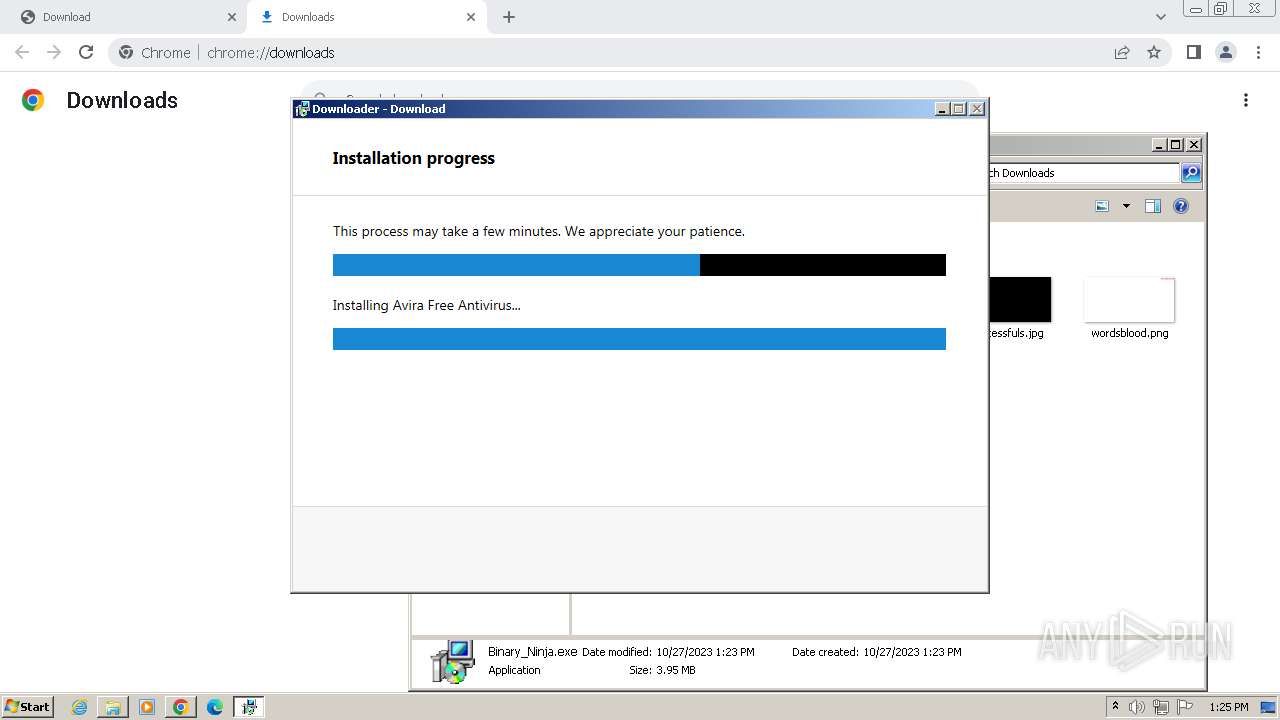
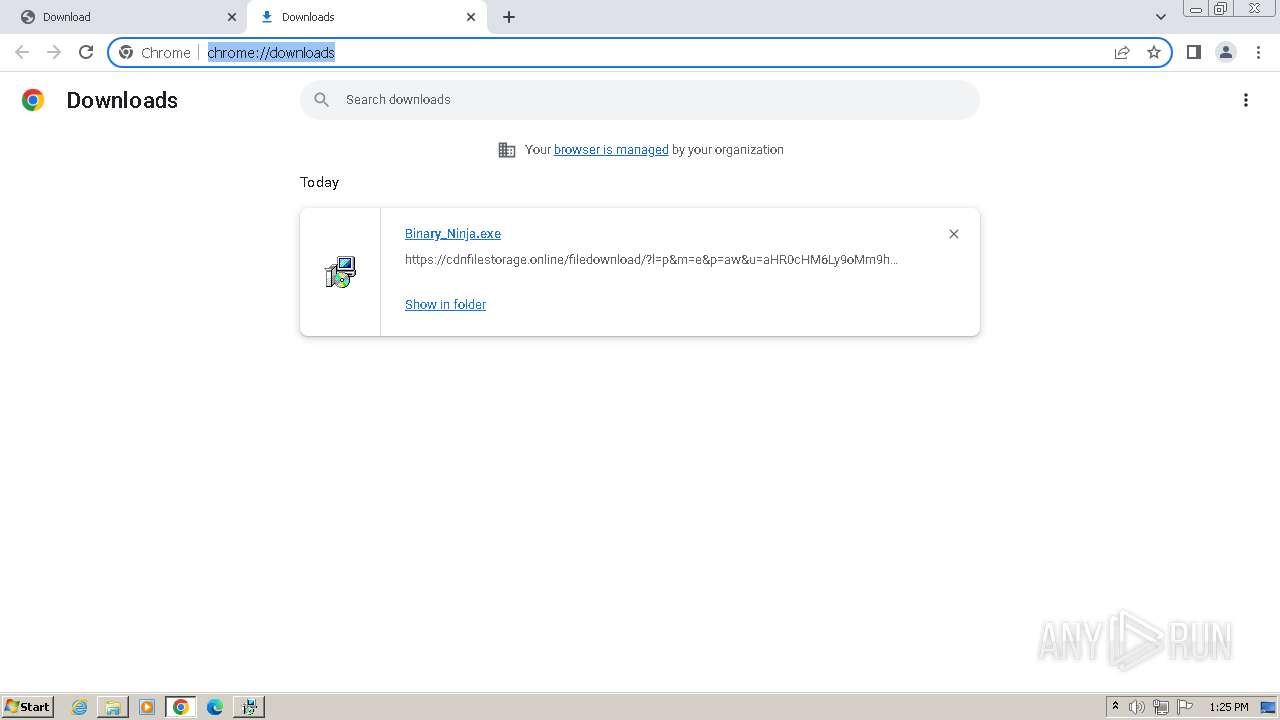
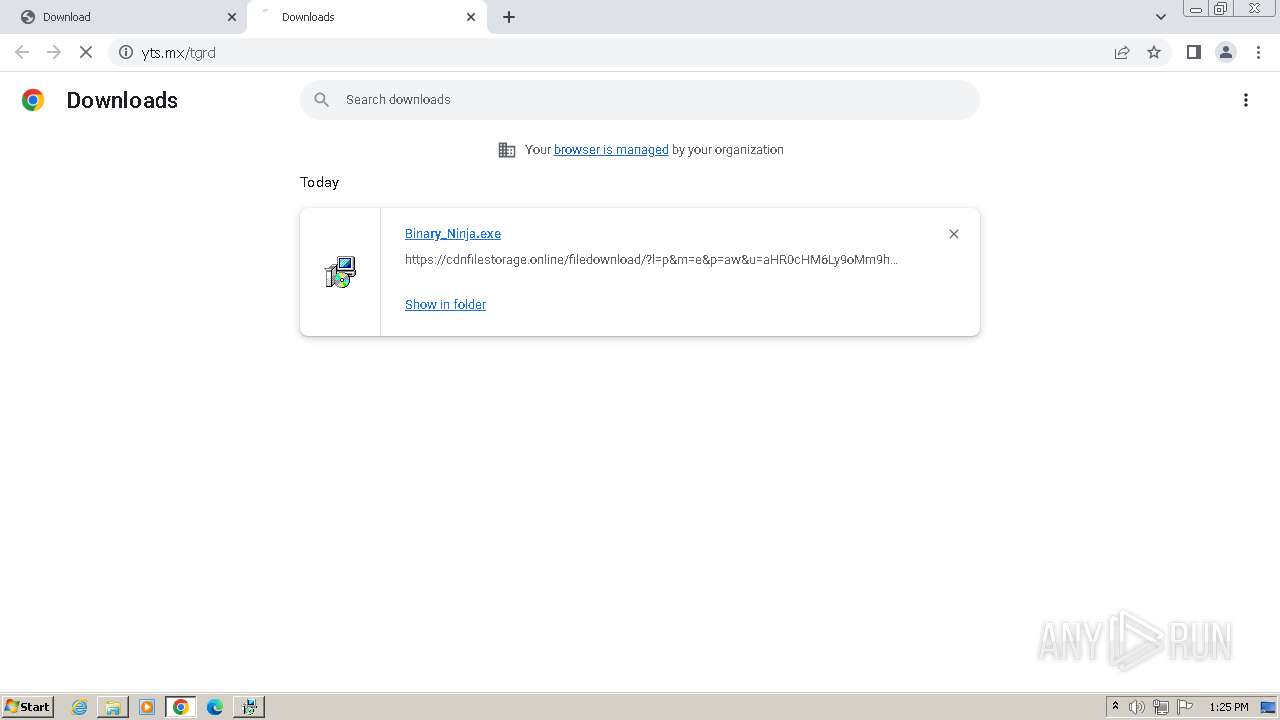
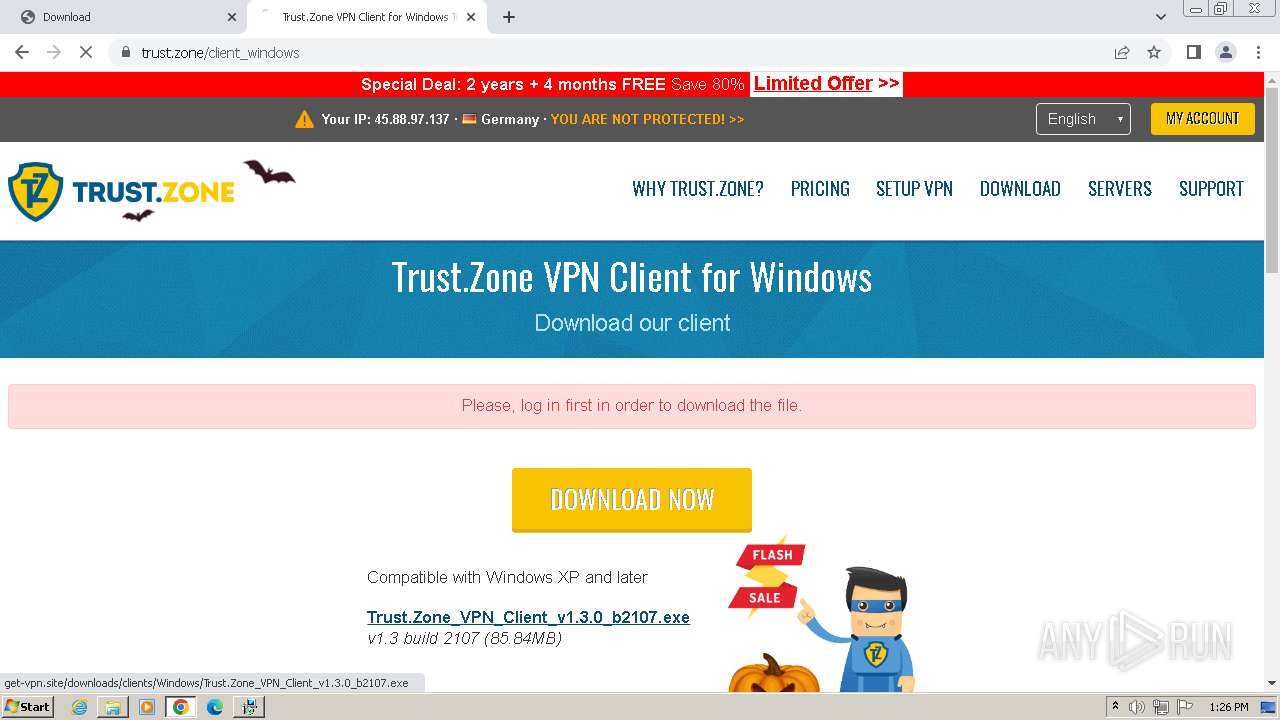
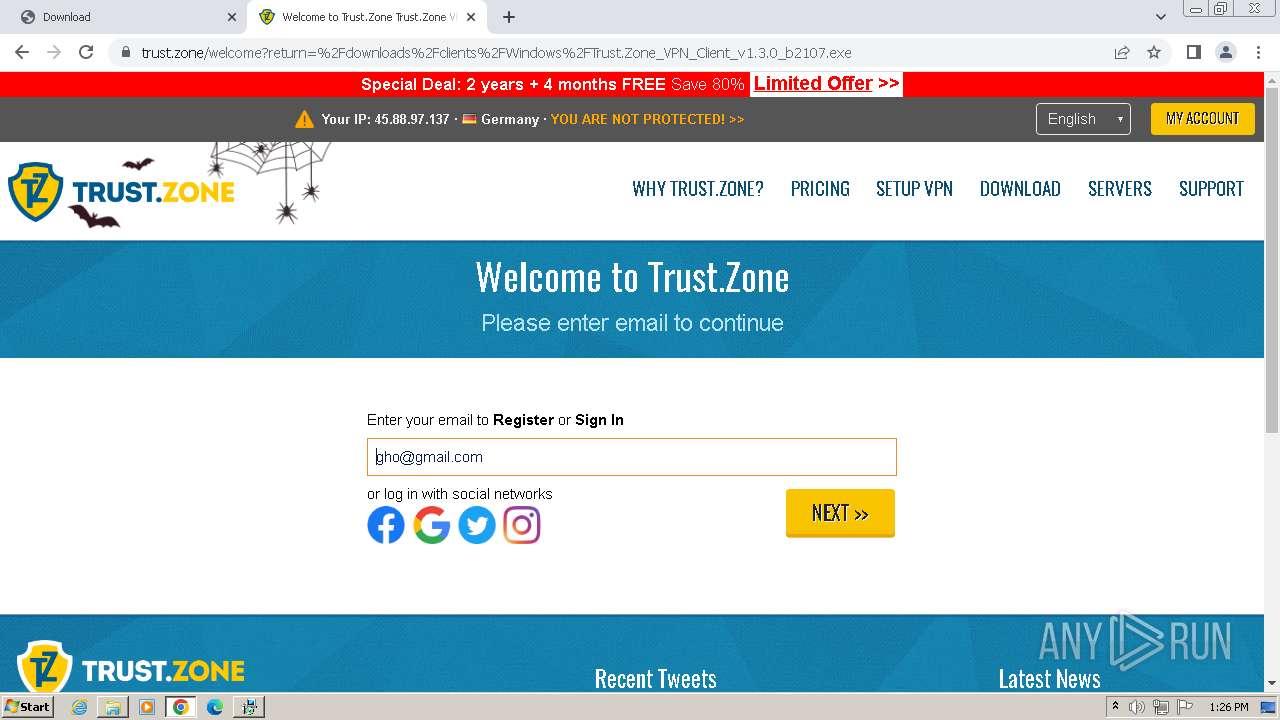
| URL: | https://storagefiles.online/filedown/?kfe=fdgfu3jfhjxuwtd&cod=36507&lnk=aHR0cHM6Ly9jZG5maWxlc3RvcmFnZS5vbmxpbmUvZmlsZWRvd25sb2FkLz9sPXAmbT1lJnA9YXcmdT1hSFIwY0hNNkx5OW9NbTloY0drdVlXUmhkMkZ5WlM1amIyMHZkakV2WkhsdVlXMXBZMkoxYm1Sc1pTOWtiM2R1Ykc5aFpDOCUyRmNUMWxlVXBvWWtkamFVOXBTa2xWZWtreFRtbEpjMGx1VWpWalEwazJTV3R3V0ZaRFNqa3VaWGxLTUdOdFJuVmpNa1pxWkVkc2RtSnJiR3RKYW05cFdXcFJOVTlIV20xYVZGVjBUbnBKZWs1VE1EQk5NazB6VEZkRk1rNUhTWFJhUjBWNFRWUlpNVTFIU1hkT2VrVXlTV2wzYVdKWFZucGpNa1p1V2xWc2EwbHFiMmxPUjFVMFdXMU5lazlIVFhoT1IwcHFXWHBLYkUxdFRtMU5WRlV6VDFkU2FGcFVWWHBhUjAweldUSlNiRTE2WkdwTmVsRTFUMU5KYzBsdVFuWmpibEpvWWtWc1JVbHFiMmxoVnpWNlpFZEdjMkpJUW5kaFUwbHpTVzVXZVdKRFNUWkpiV2d3WkVoQ2VrOXBPSFphU0dSellWaFNiR015V25CaVF6VjJZbTE0Y0dKdFZYWlpNamwwWTBNNGVrNXFWWGRPZVRoNFRtazVVMDFGY0c5WmVrcDNVV3h2ZUZGc2NGZFRSbFkwVkVSQ1NtVkhSWHBTV0doWVlXeGFjRlJxUm10VVZURjBWbXRTVTFORldrUlpNRlUxWTJ4R2NsSnJTazlTTVZwd1YydFZOVkpHVmxWTlF6VnNaVWRWWDJScU1UVk5hVnAzVUZkR00wcHRXbkJpUjFaeldWaEtibHBVTUhoS2JWazVUVk5KYzBsdE9YcFJiV3d3WTNsSk5rbHRSbk5pUTBselNXMUdkMk5GTldoaVYxVnBUMmxLUldJelpIVmlSemxvV2tkV2VVbHBkMmxoVnpWNlpFZEdjMkpIVm5sV1NHeDNXbE5KTmtsc1pHeFphMngxWXpOU2FHSkhlR3hqYVVselNXMUtNV0p0VW5OYVZXeHJTV3B2YVZOV1RsRk5SRUY0U1dsM2FWcHVWbk5pUld4MVl6TlNhR0pIZUd4amExSnNaRWRHY0dKSVRXbFBhVXBIV1ZkNGVscFRTWE5KYlZKc1lrZHNNbHBZU2pWV1NHeDNXbE5KTmtsclJuZGhVMGx6U1cxT2FHSllRbWhoVjJSMVUxZFJhVTlwU1hwT2FsVjNUakU0ZUU1cFNYTkpiazR4V1d0T2FHSllRbWhoVjJSMVUxZFJhVTlwU2xSa1YwcG1UWHBaTVUxRVpHWk5WRmxwVEVOS2FXUlhOV3RpUjFaRVkyMVdhR1JIYkhaaWExSm9aRWRWYVU5cFNYbE5SRWw2VEZSRmQweFVTVEJXUkVWNVQycFJlVTlxVlhkTWFtdDZUWHByTlUxcVdtRkphWGRwV2xob01HTnRSbnBKYW5BM1NXdE9hR0pZUW1oaFYyUjFVMWRSYVU5cFNYcE9hbFYzVGpFNGVFNXBTWE5KYkU0eFdXdE9hR0pZUW1oaFYyUjFVMWRSYVU5cFNsUmtWMHBtVFhwWk1VMUVaR1pOVkZscFpsTjNhV0ZYUmpCSmFtOTRUbXByTkUxVVZYaE5lbU4zWmxFdWN6WlVOWEY2UW1admFrUmlkRE16VkhoM1gwbExVV1F3TlZvMlFuRkhWVFZwWkVsSk5GSjJXWEZXV1NaaGNHbExaWGs5WlhsS2FHSkhZMmxQYVVwSlZYcEpNVTVwU1hOSmJsSTFZME5KTmtscmNGaFdRMG81TG1WNVNuRmtSMnRwVDJsSmVrNHlUVE5PUkVFMVQxTXdNVmxVUm1wTVZGRTBXVzFaZEU5RWFHaGFhVEEwVGtkRmVscHFhR2xPYW14cFRrZFphVXhEU25Cak0wMXBUMmxLUWxwSFJqTlpXRXBzU1VaT2RscHVVak5aV0Vwc1NVVnNkVmw1U1hOSmJVWXhXa05KTmtsdGJIVmpNMUpvWWtkNGQyTkhhMmxNUTBwNldUSTVkMXBZVFdsUGJITnBXa2M1TTJKdGVIWlpWMUpEWkZjMWEySkhWV2xZV0RBdU1qQjVWblpvYjB4NVptRkhka1pMVkZrd1ZuUnVZMWN5TVVkSGMwTndkWGxyT1VveFkyZEJhMHRXVlNaRFlXMXdZV2xuYmtsa1BUTTJOVEEzWHpFMkpsTjFZa05oYlhCaGFXZHVTV1E5VTNWaVh6TTJOVEEzWHpFMkpsVnVhWEYxWlVsa1BWSXdTbWhqTW5CQ1dqRkNXbFpJVlhoTU1FbDRZVE5GZUZkcVZtbGtNRGxZVVd0MFdtTkZPWHBSTW1SR1RrZHdjVll5V2toVWEwWkxXakJzU0dORVFuWlphM014Vlc1c1VGRlZNVE5UYTNSQ1ZsUmFWazFYU21sUFJXczFVbXhrUldGcVRUVmtWMHBaWlZkS2ExVnVjRXRPUlRrMFZqTlZlRTR6VW5GWmVYUjFUVlpLTW1OVlRsZFpWWEJLWWxoU1ZsVXhiM1pWTUVaUlZrZFNZVlpWYkVsV01FNTZWV3h2TVU1dGR3JTNEJTNEJmNvZD0zNjUwNyZuPVFtbHVZWEo1WDA1cGJtcGgmY249MSZyPTM5NDQz&name=Binary+Ninja |
| Full analysis: | https://app.any.run/tasks/695024cc-674b-4bfd-bf23-ca61c1d3a9cd |
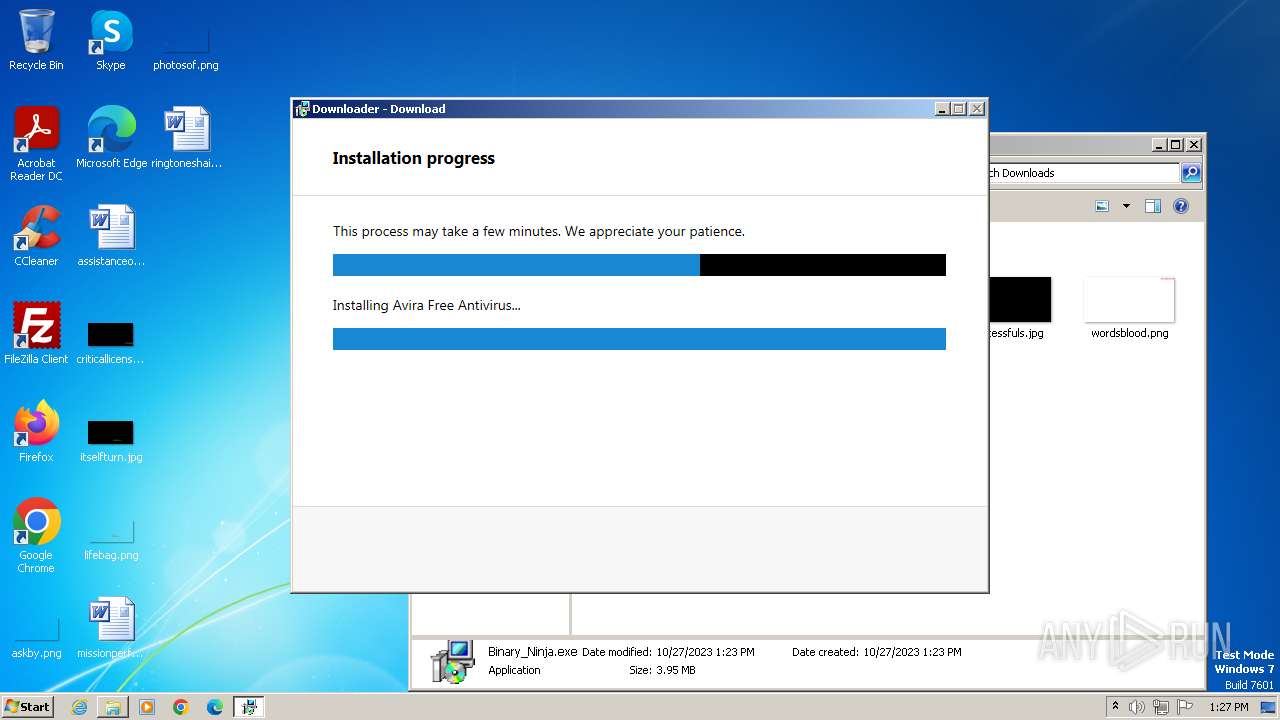
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2023, 12:23:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | D165F18BFC120712FEB348EB9C5DA03B336FAABE |
| SHA256: | 5BDF26A07B399557A0D825709CD9D3B845A14DB5E961F208E43711E23F6F45C4 |
| SSDEEP: | 48:jMYhjzEA/gBv1ToI+04Mr2uUV0MyUto1GRyIhfthArcUNdt/EU2k0wCDYC6FRIq:jMYNz7/gBv1ToI+c27V0MyUto4LAgUNn |
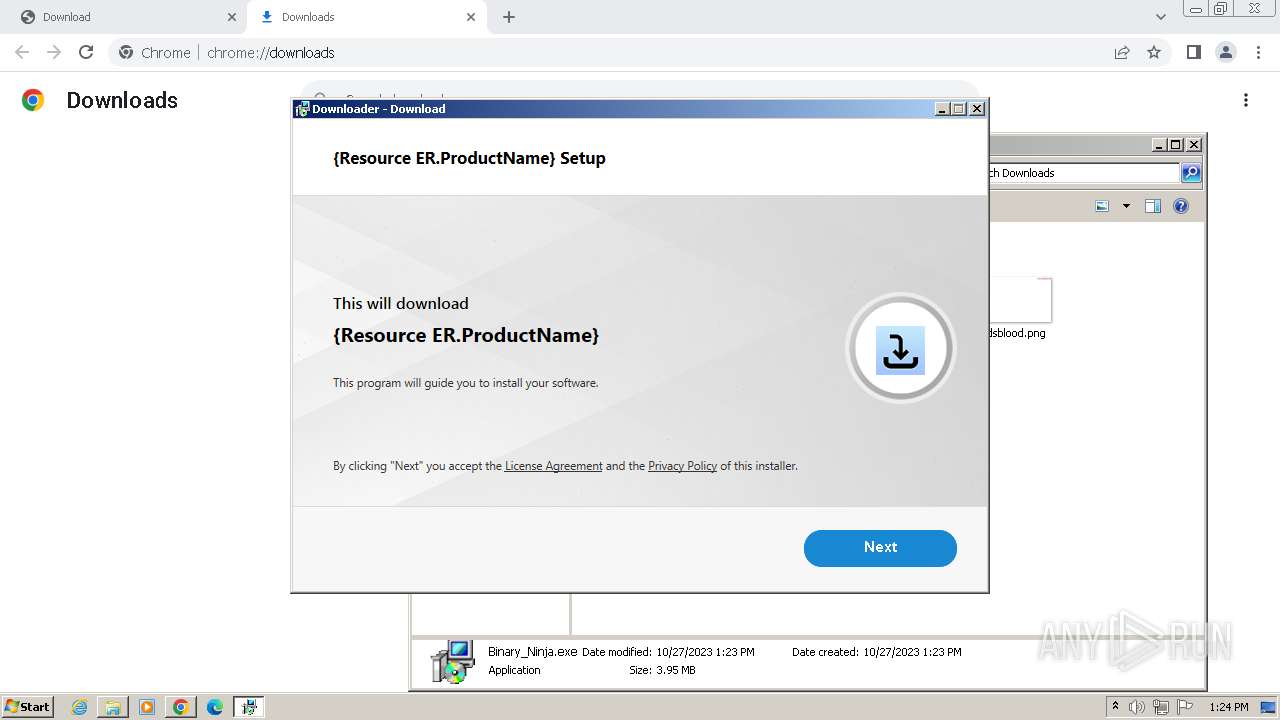
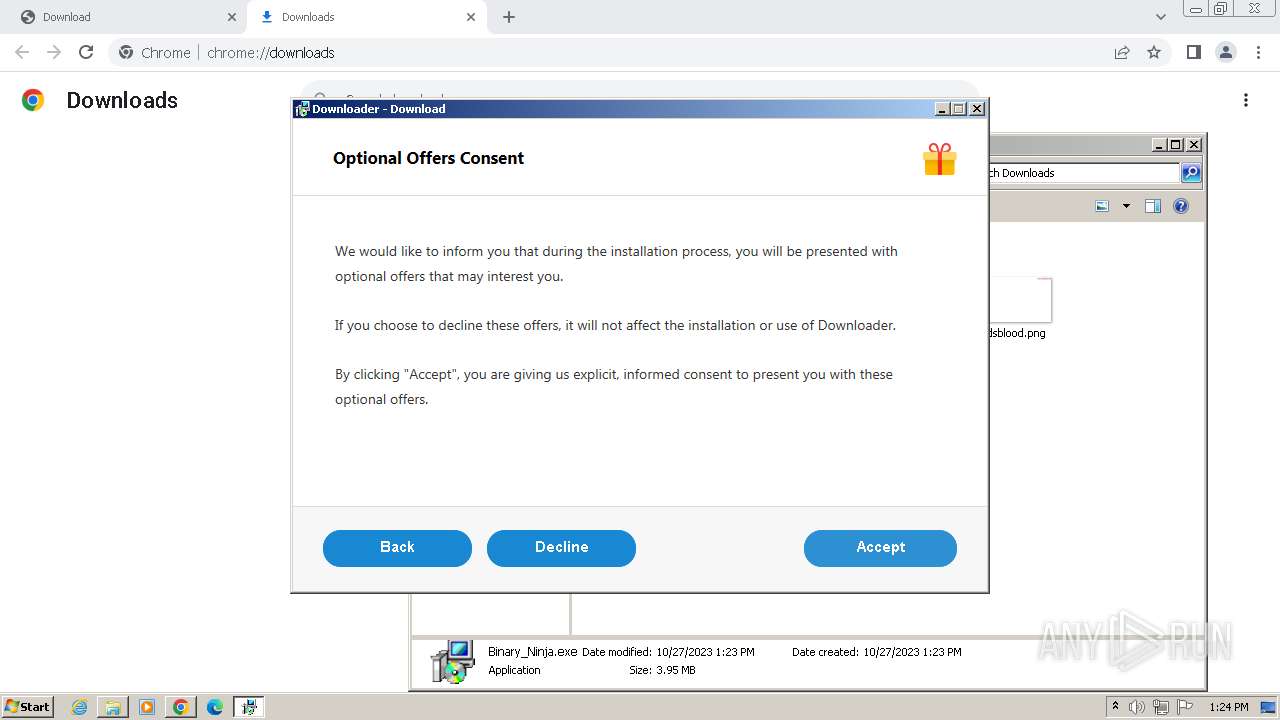
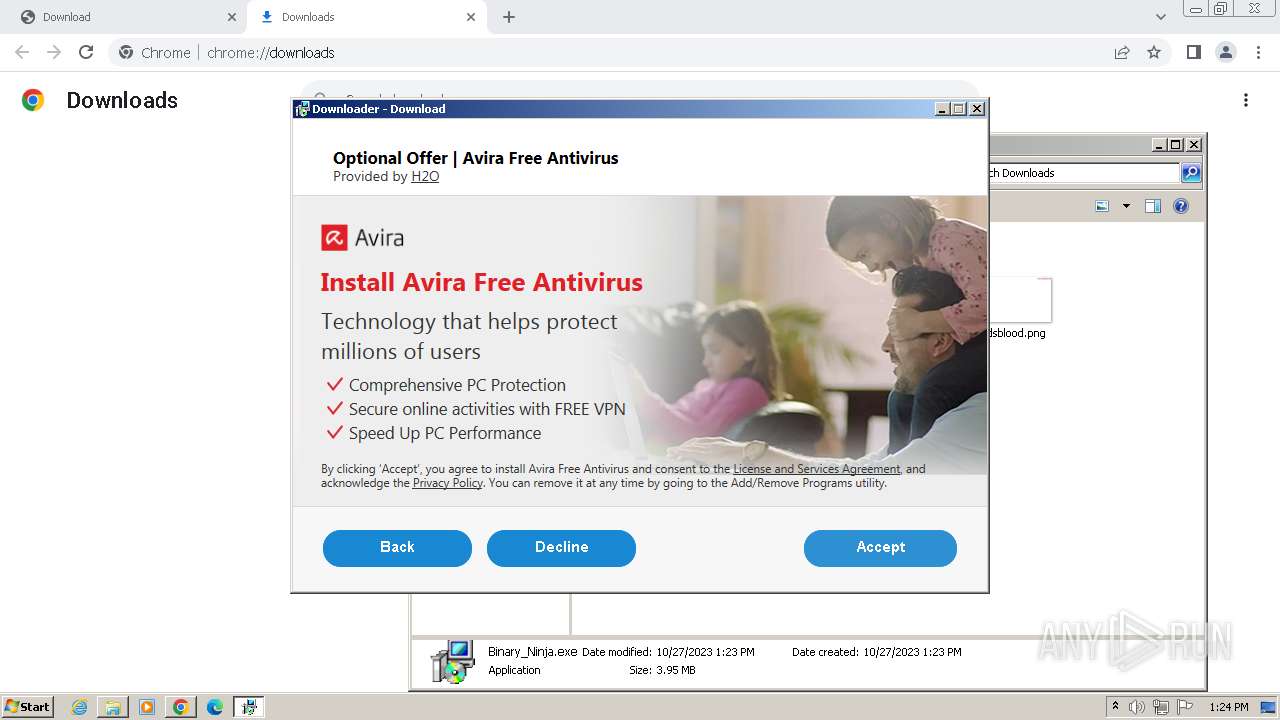
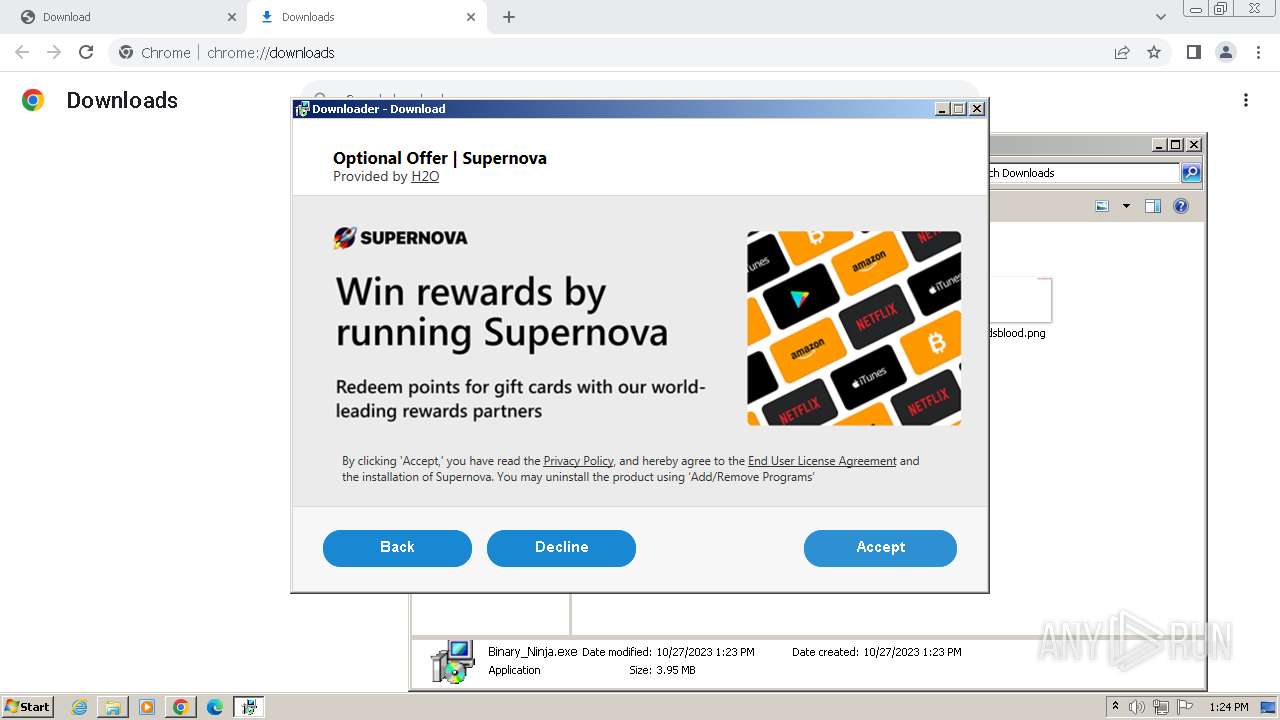
MALICIOUS
Application was dropped or rewritten from another process
- Binary_Ninja.exe (PID: 2480)
- ndp48-web.exe (PID: 2040)
- Setup.exe (PID: 3740)
- SetupUtility.exe (PID: 120)
- SetupUtility.exe (PID: 1688)
- ServiceModelReg.exe (PID: 3720)
- regtlibv12.exe (PID: 2600)
- regtlibv12.exe (PID: 1952)
- regtlibv12.exe (PID: 1164)
- regtlibv12.exe (PID: 3384)
- regtlibv12.exe (PID: 2224)
- regtlibv12.exe (PID: 2724)
- regtlibv12.exe (PID: 2576)
- aspnet_regiis.exe (PID: 1808)
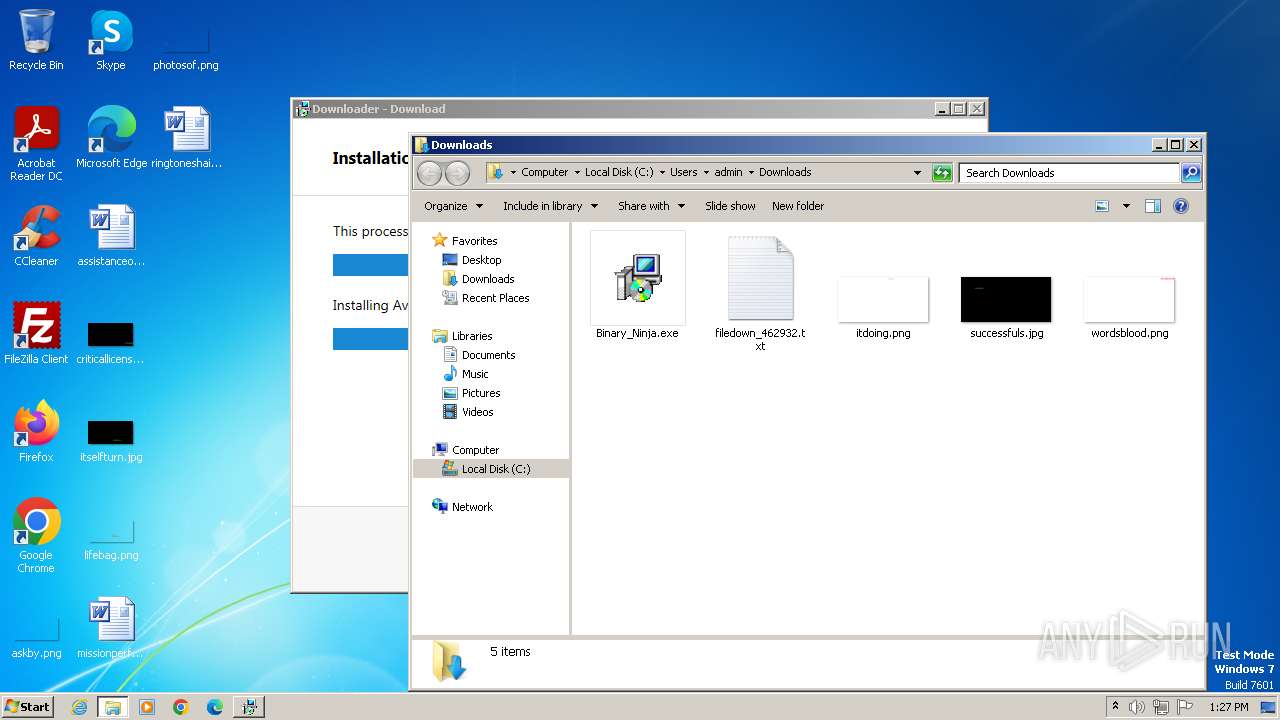
Drops the executable file immediately after the start
- Binary_Ninja.exe (PID: 2480)
- avira__sptl1___lavasoft.exe (PID: 1824)
- ndp48-web.exe (PID: 2040)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- msiexec.exe (PID: 3276)
Loads dropped or rewritten executable
- Binary_Ninja.exe (PID: 2480)
- Setup.exe (PID: 3740)
- msiexec.exe (PID: 3276)
- svchost.exe (PID: 752)
- aspnet_regiis.exe (PID: 1808)
Actions looks like stealing of personal data
- Binary_Ninja.exe (PID: 2480)
Uses Task Scheduler to run other applications
- avira__sptl1___lavasoft.exe (PID: 1824)
Creates a writable file the system directory
- msiexec.exe (PID: 3276)
- aspnet_regiis.exe (PID: 1808)
SUSPICIOUS
Process drops legitimate windows executable
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- ndp48-web.exe (PID: 2040)
- msiexec.exe (PID: 3276)
The process drops C-runtime libraries
- Binary_Ninja.exe (PID: 2480)
- msiexec.exe (PID: 3276)
Reads security settings of Internet Explorer
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- Setup.exe (PID: 3740)
Reads the Windows owner or organization settings
- Binary_Ninja.exe (PID: 2480)
- msiexec.exe (PID: 3276)
Checks Windows Trust Settings
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- Setup.exe (PID: 3740)
- msiexec.exe (PID: 3276)
Reads settings of System Certificates
- Binary_Ninja.exe (PID: 2480)
- Setup.exe (PID: 3740)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
Searches for installed software
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
The process creates files with name similar to system file names
- avira__sptl1___lavasoft.exe (PID: 1824)
- msiexec.exe (PID: 3276)
Reads the Internet Settings
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- Binary_Ninja.exe (PID: 2480)
- Setup.exe (PID: 3740)
Adds/modifies Windows certificates
- avira__sptl1___lavasoft.exe (PID: 1824)
- ndp48-web.exe (PID: 2040)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3276)
Checks for the .NET to be installed
- msiexec.exe (PID: 3276)
Uses WEVTUTIL.EXE to remove publishers and event logs from the manifest
- ServiceModelReg.exe (PID: 3720)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- ServiceModelReg.exe (PID: 3720)
INFO
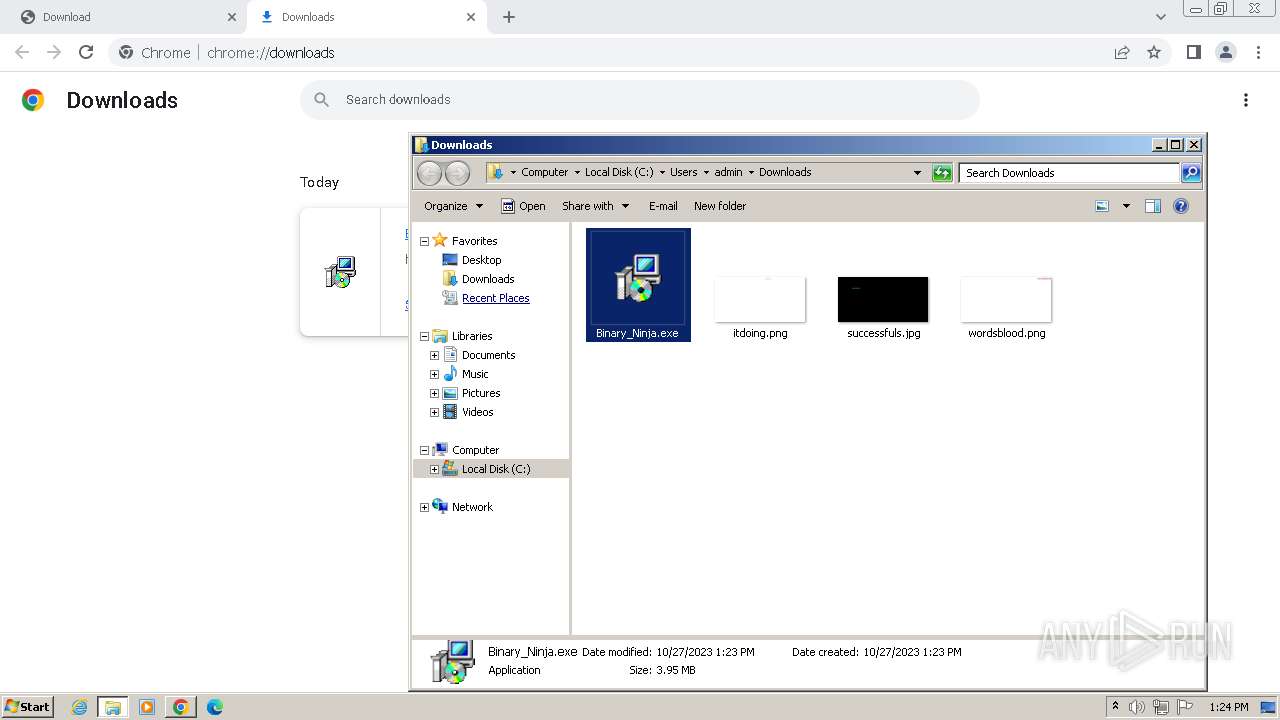
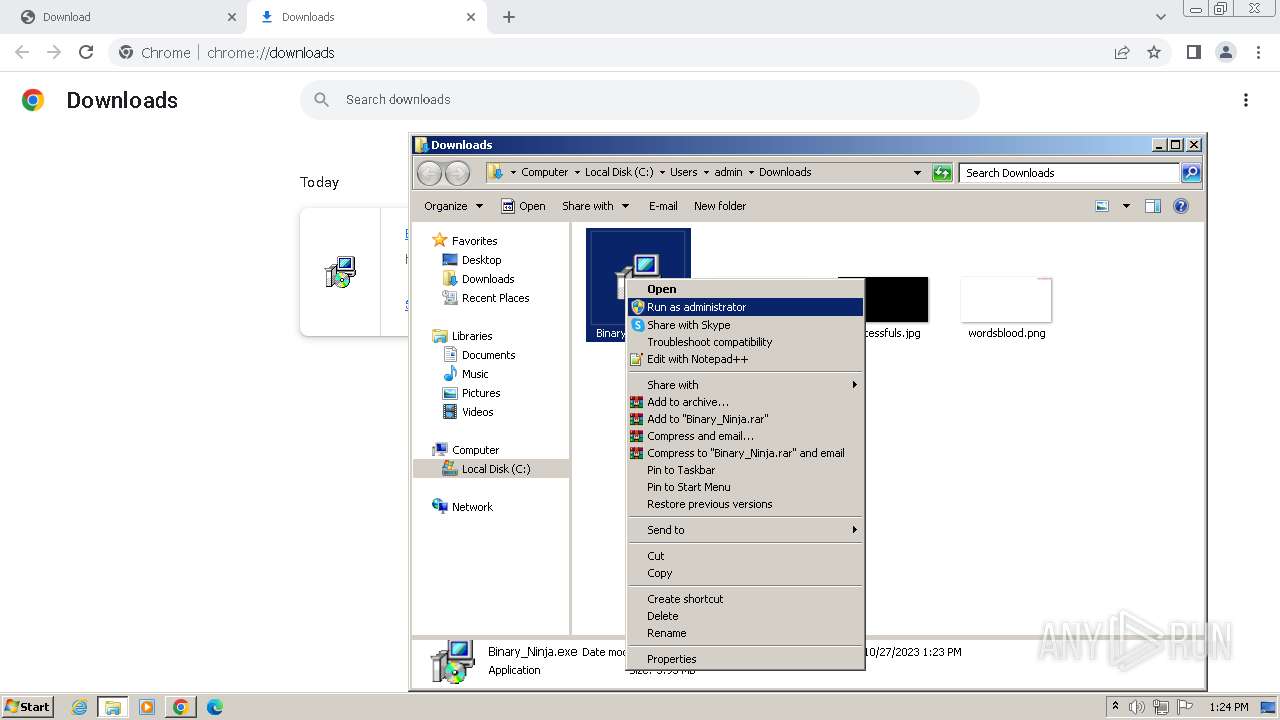
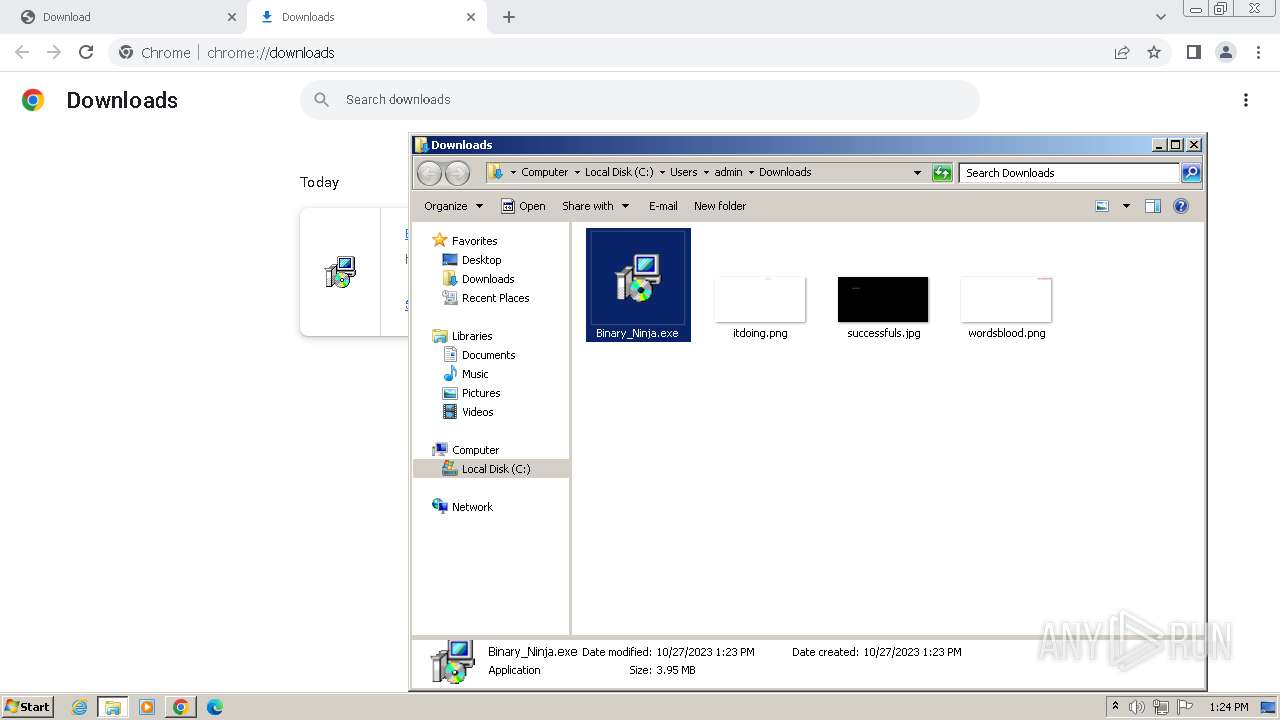
Manual execution by a user
- Binary_Ninja.exe (PID: 2480)
Reads the computer name
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- ndp48-web.exe (PID: 2040)
- Setup.exe (PID: 3740)
- SetupUtility.exe (PID: 120)
- SetupUtility.exe (PID: 1688)
- TMPF4DE.tmp.exe (PID: 3936)
- msiexec.exe (PID: 3276)
- msiexec.exe (PID: 328)
- msiexec.exe (PID: 3620)
- ServiceModelReg.exe (PID: 3720)
- aspnet_regiis.exe (PID: 1808)
The process uses the downloaded file
- chrome.exe (PID: 2464)
- Binary_Ninja.exe (PID: 2480)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 2952)
Drops the executable file immediately after the start
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3808)
Checks supported languages
- Binary_Ninja.exe (PID: 2480)
- avira__sptl1___lavasoft.exe (PID: 1824)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- ndp48-web.exe (PID: 2040)
- Setup.exe (PID: 3740)
- SetupUtility.exe (PID: 120)
- SetupUtility.exe (PID: 1688)
- TMPF4DE.tmp.exe (PID: 3936)
- msiexec.exe (PID: 3276)
- msiexec.exe (PID: 328)
- msiexec.exe (PID: 3620)
- ServiceModelReg.exe (PID: 3720)
- regtlibv12.exe (PID: 1164)
- regtlibv12.exe (PID: 1952)
- regtlibv12.exe (PID: 2224)
- regtlibv12.exe (PID: 3384)
- regtlibv12.exe (PID: 2724)
- regtlibv12.exe (PID: 2576)
- aspnet_regiis.exe (PID: 1808)
- regtlibv12.exe (PID: 2600)
Reads the machine GUID from the registry
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- ndp48-web.exe (PID: 2040)
- Setup.exe (PID: 3740)
- SetupUtility.exe (PID: 120)
- msiexec.exe (PID: 328)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 3276)
- aspnet_regiis.exe (PID: 1808)
Reads Environment values
- Binary_Ninja.exe (PID: 2480)
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- Setup.exe (PID: 3740)
Application launched itself
- chrome.exe (PID: 1796)
- msiexec.exe (PID: 3276)
Reads product name
- Binary_Ninja.exe (PID: 2480)
Creates files or folders in the user directory
- Binary_Ninja.exe (PID: 2480)
- Setup.exe (PID: 3740)
Create files in a temporary directory
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
- Binary_Ninja.exe (PID: 2480)
- ndp48-web.exe (PID: 2040)
- Setup.exe (PID: 3740)
- SetupUtility.exe (PID: 120)
- TMPF4DE.tmp.exe (PID: 3936)
- avira__sptl1___lavasoft.exe (PID: 1824)
- msiexec.exe (PID: 3276)
- ServiceModelReg.exe (PID: 3720)
- mofcomp.exe (PID: 3868)
- mofcomp.exe (PID: 3388)
- mofcomp.exe (PID: 556)
- aspnet_regiis.exe (PID: 1808)
Creates files in the program directory
- Avira.Spotlight.Bootstrapper.exe (PID: 3268)
Reads CPU info
- Setup.exe (PID: 3740)
Creates or modifies Windows services
- msiexec.exe (PID: 3276)
Creates a software uninstall entry
- msiexec.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
59
Malicious processes
18
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | SetupUtility.exe /aupause | C:\d55542d71286f914be92d103bee3\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 328 | C:\Windows\system32\MsiExec.exe -Embedding 52B28153DE51B243FC7627AD91A08E4E | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | mofcomp C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet.mof | C:\Windows\System32\wbem\mofcomp.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3724 --field-trial-handle=1156,i,18303894273143912755,5276430696171931184,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1164 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorlib.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3484 --field-trial-handle=1156,i,18303894273143912755,5276430696171931184,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e0b8b38,0x6e0b8b48,0x6e0b8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1688 | SetupUtility.exe /screboot | C:\d55542d71286f914be92d103bee3\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3852 --field-trial-handle=1156,i,18303894273143912755,5276430696171931184,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
127 347
Read events
123 310
Write events
2 367
Delete events
1 670
Modification events
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
1 941
Suspicious files
196
Text files
402
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1eb11d.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1eb11d.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1eb285.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1eb266.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1eb861.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1eb2c3.TMP | text | |
MD5:56C75810BDDDD686D123E6E36F56E012 | SHA256:3D51A6EF85A51056E1A379D795F55C84A321EC2000DD69F5D70ABA038C61522E | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF1ec522.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
79
DNS requests
63
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
864 | svchost.exe | HEAD | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | unknown | — | — | unknown |
864 | svchost.exe | GET | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | unknown | — | — | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 5.89 Kb | unknown |
3740 | Setup.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | binary | 767 b | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 8.74 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 8.07 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 14.8 Kb | unknown |
3740 | Setup.exe | GET | 200 | 46.228.146.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?287c1ce8af06889d | unknown | compressed | 4.66 Kb | unknown |
3740 | Setup.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.11 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3192 | chrome.exe | 142.250.186.77:443 | accounts.google.com | GOOGLE | US | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3192 | chrome.exe | 104.21.23.70:443 | storagefiles.online | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3192 | chrome.exe | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
1796 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3192 | chrome.exe | 104.21.38.183:443 | cdnfilestorage.online | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
storagefiles.online |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
cdnfilestorage.online |
| unknown |
sb-ssl.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
h2oapi.adaware.com |
| unknown |
flow.lavasoft.com |
| whitelisted |
sos.adaware.com |
| whitelisted |
package.avira.com |
| unknown |
Threats
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
Binary_Ninja.exe | |
Binary_Ninja.exe | |
Binary_Ninja.exe | at sciter:init-script.tis
|
Binary_Ninja.exe | Error: File not found - sciterwrapper:console.tis
|
Binary_Ninja.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
Binary_Ninja.exe | Error: File not found - sciterwrapper:console.tis
|
Binary_Ninja.exe | |
Binary_Ninja.exe | |
Binary_Ninja.exe | at sciter:init-script.tis
|
Binary_Ninja.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|