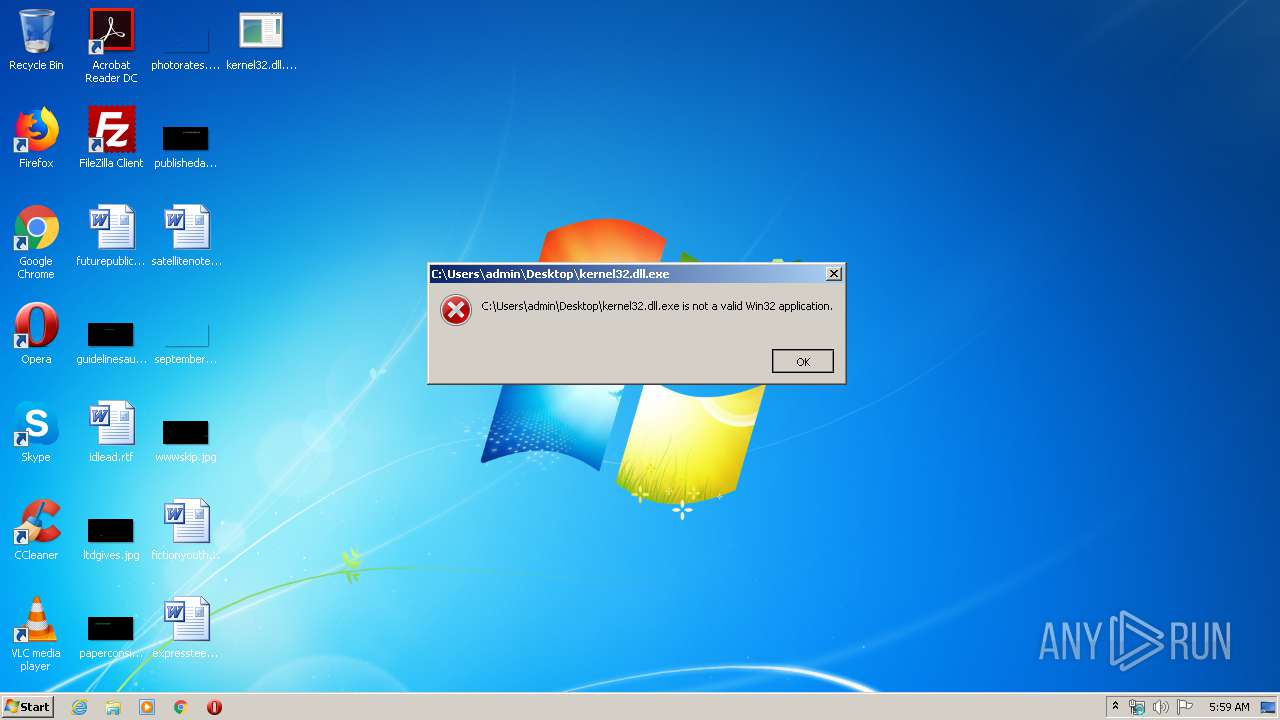
| File name: | kernel32.dll |
| Full analysis: | https://app.any.run/tasks/5db75c28-3a85-4244-958e-436b5a3cc837 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2020, 04:59:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | 226049BC657B3884E96C5B9EDC908CD7 |
| SHA1: | D194E8F2B0DBE0A2B78B4674709259190B0613EF |
| SHA256: | 5BCAAB23297A6643426F8A0DAFEB6AD24AD536CA588CB8405098384A550C7946 |
| SSDEEP: | 12288:V8NuOcWfOBb5syUVI9w4cOTzOCYV/+W5WzQ0Q+k4rH/SasC:V8NumOBb5syUG9w4cO2CYV/+hzvk4rHf |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 372)
- consent.exe (PID: 2548)
- svchost.exe (PID: 860)
Actions looks like stealing of personal data
- explorer.exe (PID: 372)
- DllHost.exe (PID: 3012)
SUSPICIOUS
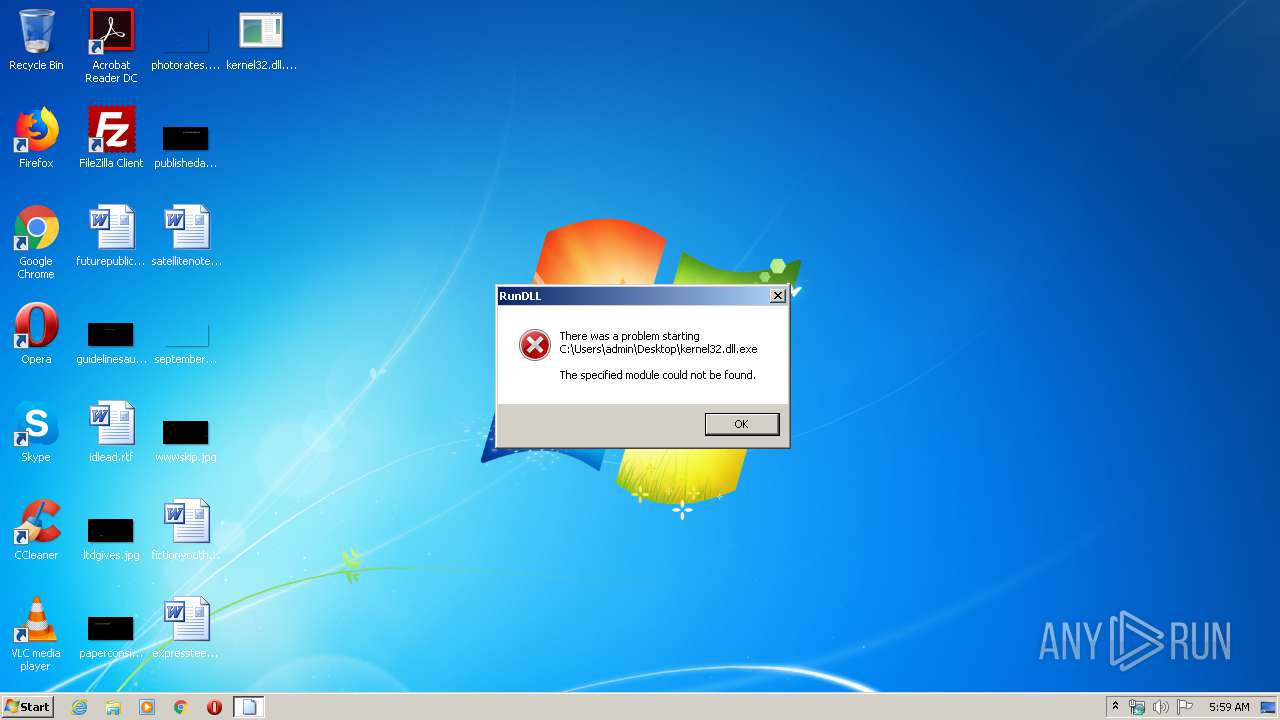
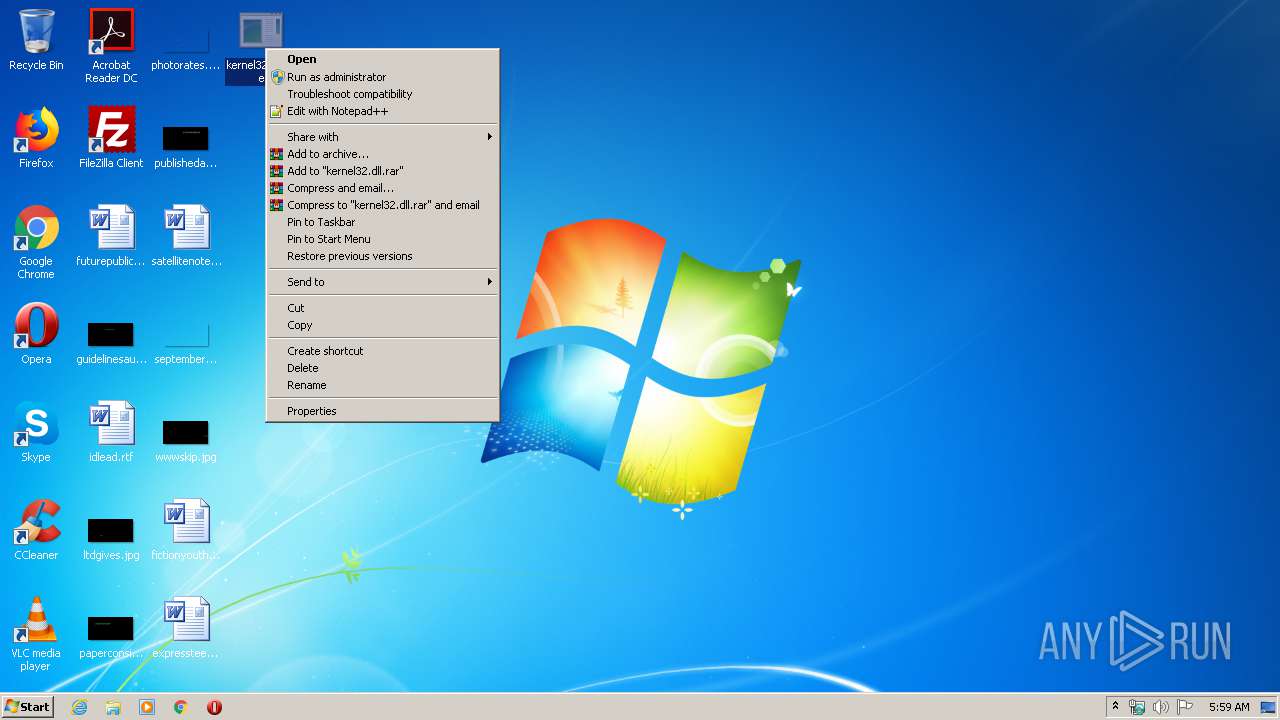
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
Executable content was dropped or overwritten
- explorer.exe (PID: 372)
Creates files in the user directory
- explorer.exe (PID: 372)
Executed via COM
- DllHost.exe (PID: 3012)
INFO
Loads main object executable
- rundll32.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (35.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (27) |
| .exe | | | Win64 Executable (generic) (23.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1982:04:09 02:25:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 409600 |
| InitializedDataSize: | 200704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x15f70 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.18362.778 |
| ProductVersionNumber: | 10.0.18362.778 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
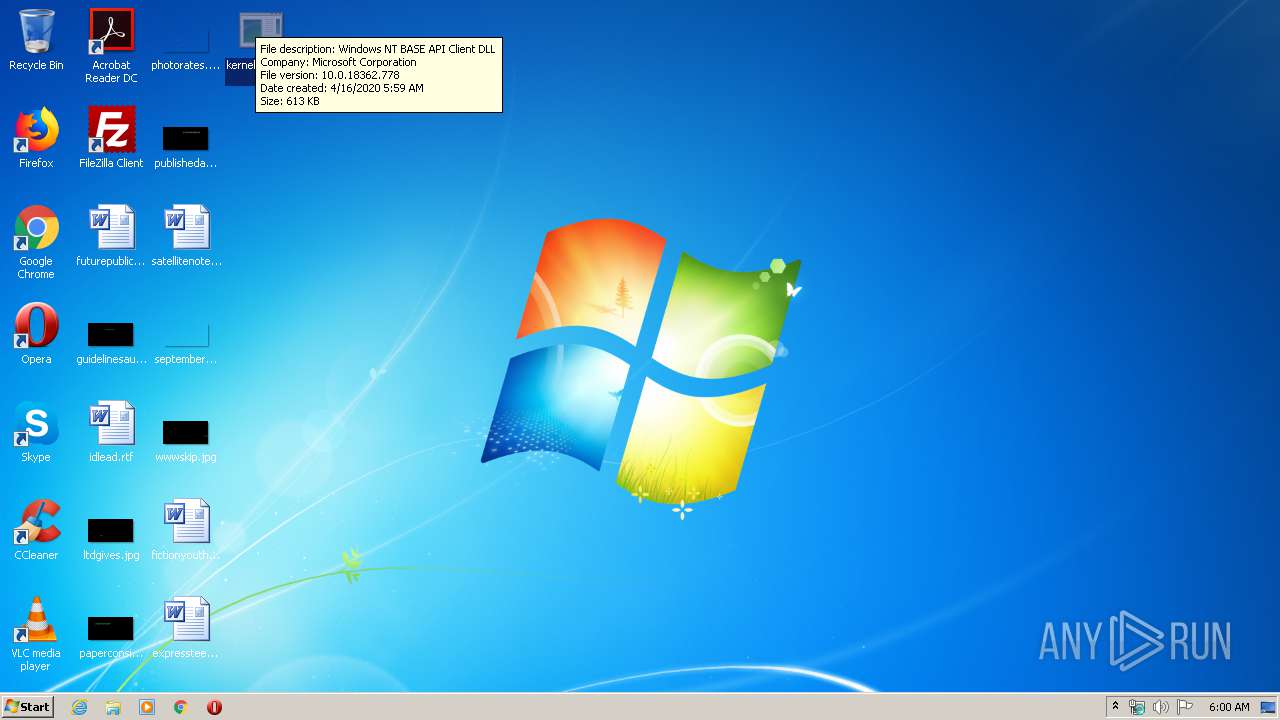
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows NT BASE API Client DLL |
| FileVersion: | 10.0.18362.778 (WinBuild.160101.0800) |
| InternalName: | kernel32 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | kernel32 |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.18362.778 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Apr-1982 00:25:11 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows NT BASE API Client DLL |
| FileVersion: | 10.0.18362.778 (WinBuild.160101.0800) |
| InternalName: | kernel32 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | kernel32 |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.18362.778 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Apr-1982 00:25:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00010000 | 0x00063EF1 | 0x00064000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55394 |
.rdata | 0x00080000 | 0x0002922C | 0x0002A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8142 |
.data | 0x000B0000 | 0x00000C50 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.09348 |
.rsrc | 0x000C0000 | 0x00000520 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.32487 |
.reloc | 0x000D0000 | 0x000047B0 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.4598 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52779 | 932 | UNKNOWN | English - United States | RT_VERSION |
Imports
KERNELBASE.dll |
api-ms-win-core-appcompat-l1-1-0.dll |
api-ms-win-core-appcompat-l1-1-1.dll |
api-ms-win-core-comm-l1-1-0.dll |
api-ms-win-core-console-l1-1-0.dll |
api-ms-win-core-console-l1-2-0.dll |
api-ms-win-core-console-l1-2-1.dll |
api-ms-win-core-console-l2-1-0.dll |
api-ms-win-core-console-l2-2-0.dll |
api-ms-win-core-console-l3-2-0.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
BaseThreadInitThunk | 1 | 0x00016340 |
InterlockedPushListSList | 2 | 0x00096140 |
Wow64Transition | 3 | 0x00081F90 |
AcquireSRWLockExclusive | 4 | 0x0009618A |
AcquireSRWLockShared | 5 | 0x000961C0 |
ActivateActCtx | 6 | 0x00021FE0 |
ActivateActCtxWorker | 7 | 0x00017CC0 |
AddAtomA | 8 | 0x0001F1C0 |
AddAtomW | 9 | 0x00013890 |
AddConsoleAliasA | 10 | 0x00024980 |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\kernel32.dll.exe", BaseThreadInitThunk | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | consent.exe 860 312 01BFB0F8 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 856
Read events
1 811
Write events
44
Delete events
1
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2548) consent.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 6 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 5 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | write | Name: | NeedToPurge |
Value: 1 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | delete value | Name: | NeedToPurge |
Value: 1 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\CLSID\{645FF040-5081-101B-9F08-00AA002F954E}\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Windows\System32\imageres.dll,-54 | |||
| (PID) Process: | (3012) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000040BF05E6AB13D601 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$I2LXY5F.exe | binary | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\publishedasked.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$R2LXY5F.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report