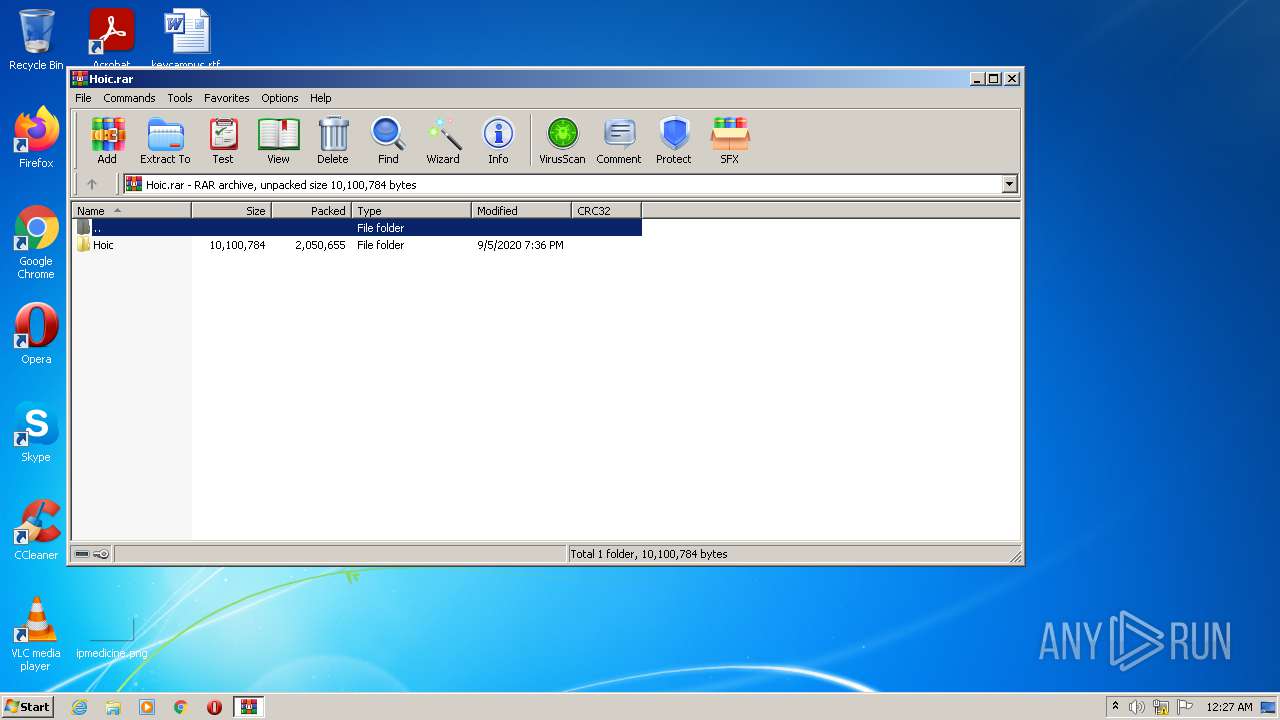
| File name: | Hoic.rar |
| Full analysis: | https://app.any.run/tasks/d3f6a5ed-cb63-44ed-bb2f-527118383581 |
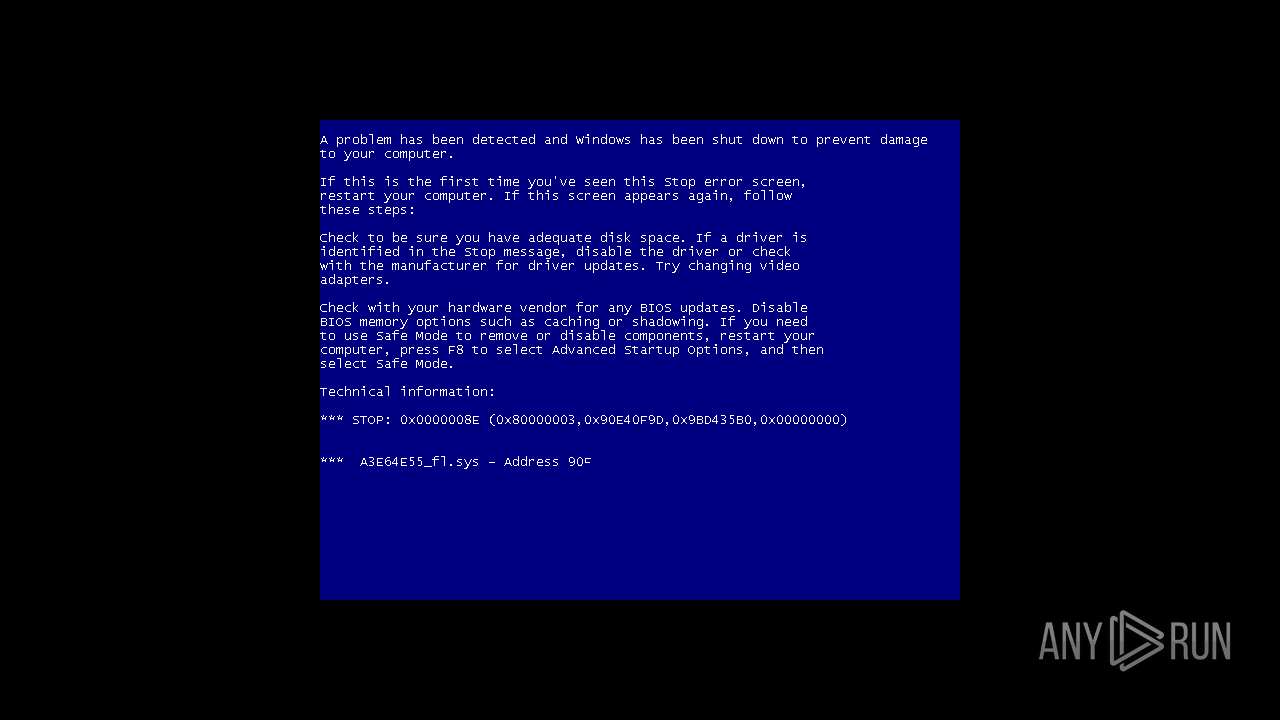
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2021, 23:27:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 50A128B0F15FFFE7EDE9FAE50FA7FBBA |
| SHA1: | CE9BF21B6E8299835B6DE7E2001F8FE5116D59AF |
| SHA256: | 5BC489AD6C6AF598480935435DCCCB55BCBEC2AF13868B67B709DDC15F50E414 |
| SSDEEP: | 49152:ZbQLb/Q8z2vs3EbOpj0NgNwTdc0gZf4qEge4/xHS:ZbCb/QG5OkKg6qEolS |
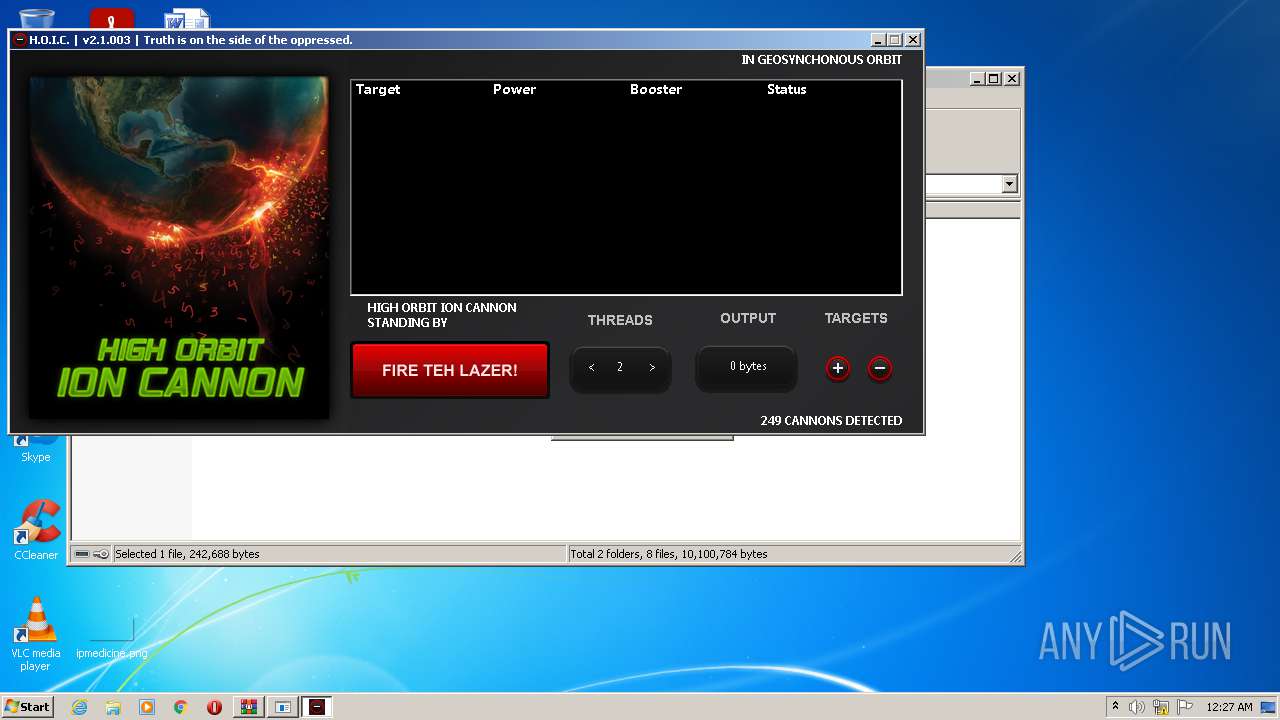
MALICIOUS
Drops executable file immediately after starts
- Launcher.exe (PID: 2188)
Application was dropped or rewritten from another process
- hoic2.1.exe (PID: 4044)
- Windows Services.exe (PID: 3020)
- Runtime Explorer.exe (PID: 2952)
- Secure System Shell.exe (PID: 3068)
- hc2.exe (PID: 1944)
- Launcher.exe (PID: 2188)
Writes to a start menu file
- Launcher.exe (PID: 2188)
Changes the autorun value in the registry
- Launcher.exe (PID: 2188)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2360)
- Launcher.exe (PID: 2188)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2360)
- Launcher.exe (PID: 2188)
Checks supported languages
- WinRAR.exe (PID: 2360)
- hoic2.1.exe (PID: 4044)
- Launcher.exe (PID: 2188)
- powershell.exe (PID: 2516)
- Windows Services.exe (PID: 3020)
- hc2.exe (PID: 1944)
- Secure System Shell.exe (PID: 3068)
- Runtime Explorer.exe (PID: 2952)
Reads the computer name
- WinRAR.exe (PID: 2360)
- hoic2.1.exe (PID: 4044)
- Launcher.exe (PID: 2188)
- powershell.exe (PID: 2516)
- Windows Services.exe (PID: 3020)
- Secure System Shell.exe (PID: 3068)
- hc2.exe (PID: 1944)
Drops a file with too old compile date
- WinRAR.exe (PID: 2360)
Executes PowerShell scripts
- Launcher.exe (PID: 2188)
Creates files in the Windows directory
- Launcher.exe (PID: 2188)
Creates files in the user directory
- Launcher.exe (PID: 2188)
- powershell.exe (PID: 2516)
Reads the date of Windows installation
- powershell.exe (PID: 2516)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2360)
- Launcher.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
46
Monitored processes
8
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\system\hc2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\system\hc2.exe | hoic2.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\system\Launcher.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\system\Launcher.exe | hoic2.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Hoic.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath C:\Windows\IMF\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Control Service Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3020 | "C:\Windows\IMF\Windows Services.exe" {Arguments If Needed} | C:\Windows\IMF\Windows Services.exe | — | Launcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3068 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
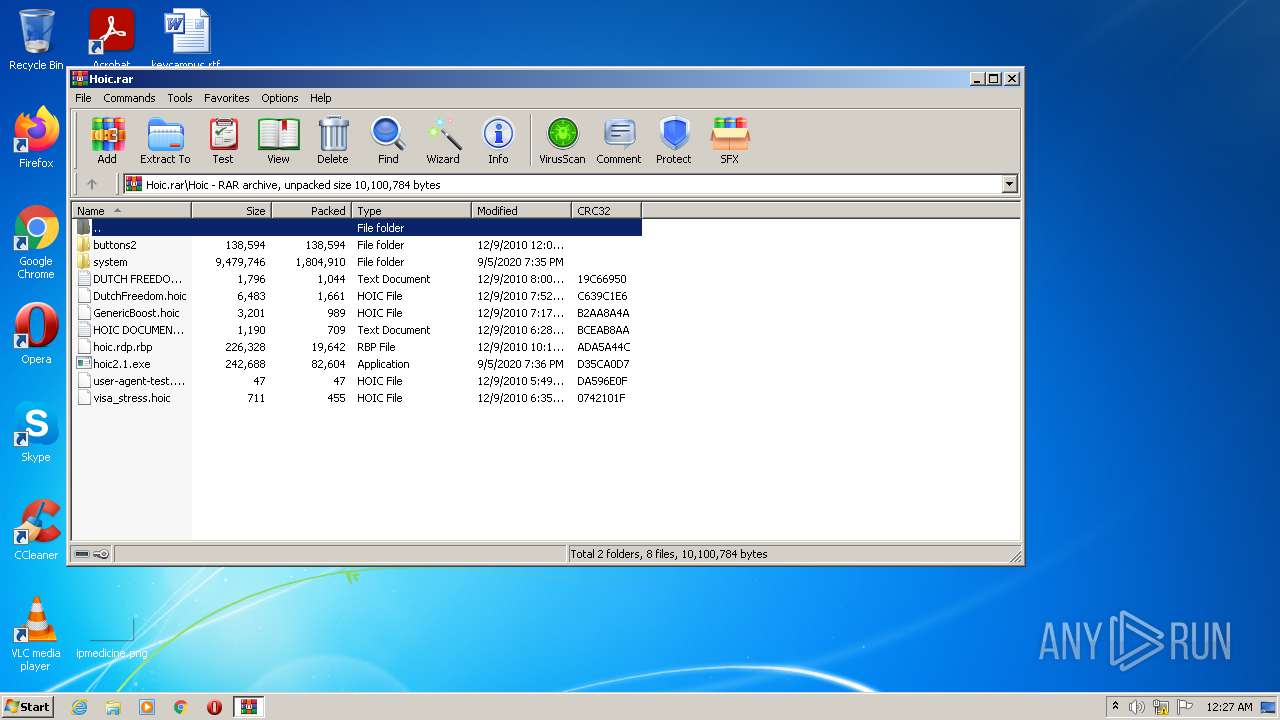
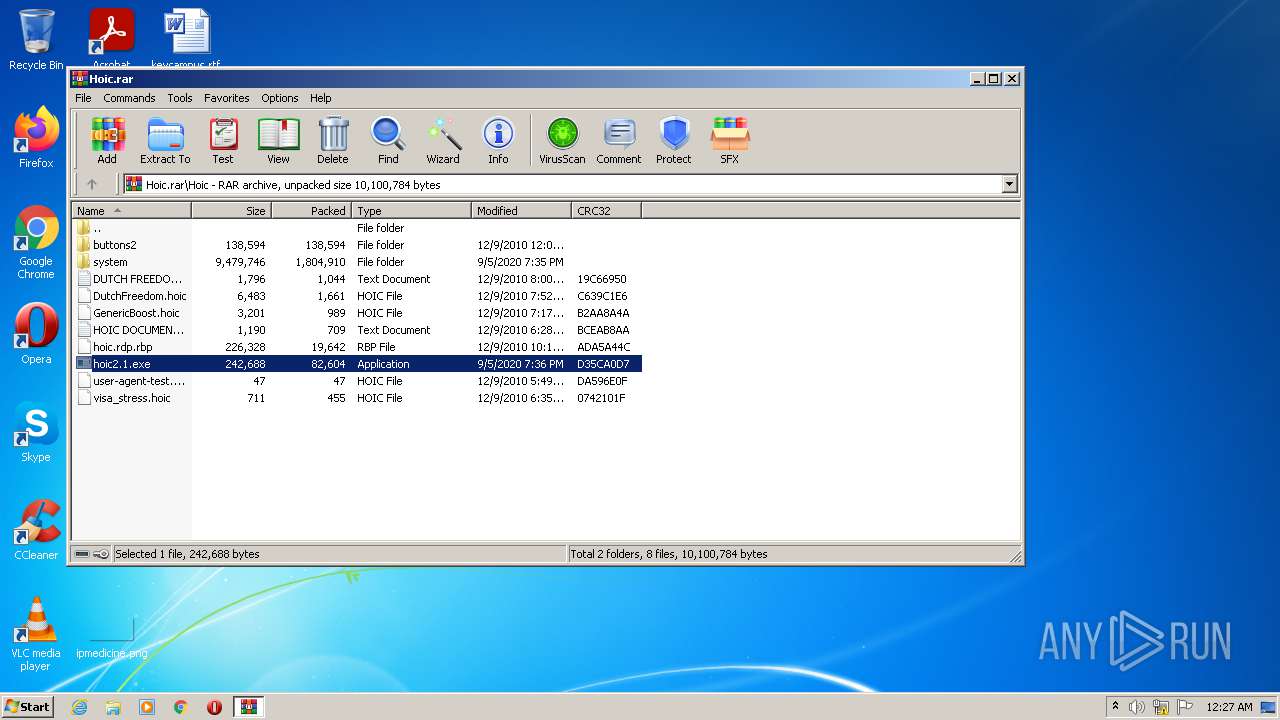
| 4044 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\hoic2.1.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\hoic2.1.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3 889
Read events
3 790
Write events
99
Delete events
0
Modification events
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Hoic.rar | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
5
Text files
50
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\4add.png | image | |
MD5:062587A5EB25732F2DC466ABA126A21C | SHA256:056BB89CE11CD2972796599913219414334C5B656CE82B3A58921918F196FC6A | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\turbo2.png | image | |
MD5:FA31B0CF31B92BE8700F0C8C4059AE03 | SHA256:88B2530D9C727E79A143281D4BD9AEDEE7B9361EC30A73BA88633FC6D2C5AA99 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\6666.png | image | |
MD5:B63B5663149586F34127FD3C47D26CCA | SHA256:6A914E505DD3613F634204F57C35AB1FAA8CFCDDB30C5585BA7EE843451AEDF2 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\button5y.png | image | |
MD5:01DCD72AB51E145129EC54CAE7CBF1E5 | SHA256:0CFC00FEE98B9E9560F2BF5EDA15F664FB8AD73343E1FE6E3F99AB3A8CE0DC34 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\button4.png | image | |
MD5:01DCD72AB51E145129EC54CAE7CBF1E5 | SHA256:0CFC00FEE98B9E9560F2BF5EDA15F664FB8AD73343E1FE6E3F99AB3A8CE0DC34 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\add.png | image | |
MD5:8ADE13213352F64D34E561D2E0A0F454 | SHA256:720EDC5F500B86904DA5161206834EE942D3B60040A856898BD95F61DA53B2DA | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\lazer.png | image | |
MD5:5DFC0A47F6309048AE3A68208685C3B8 | SHA256:4D9D71BFF3429CA055DFFF9DADE55CADA219C495153B51D8F1D7831B7C66ECB5 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\remove.png | image | |
MD5:0EFFF1A2C8D7D86CEE7B9963A7662A20 | SHA256:389F835A4174533A078DDA49F9E3130A6317A73DF98090C5E2ECAC2331A31C50 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\scripts.png | image | |
MD5:ED2D9AC71A3B1FD52877D43BFEC87ACA | SHA256:E68EACD0954A1043F2E3C5DACE4EC42BA5F0A3340D1CA898BAF46065DF6EFC74 | |||
| 2360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2360.2447\Hoic\buttons2\buttons\6266.png | image | |
MD5:D899F1C4072365D42DD6EACBDF8D9280 | SHA256:239E9707383ED676A3ED85C707F72A7CEA6877056EF688FE6EFE8545210CD013 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
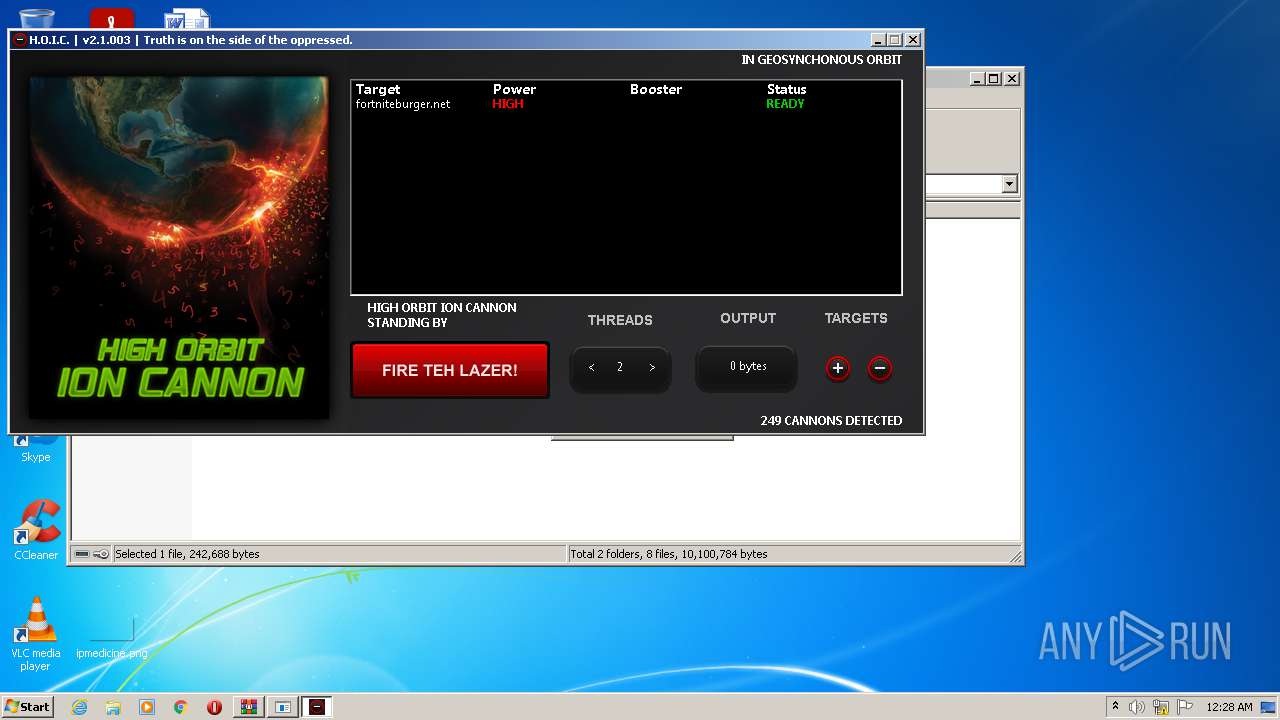
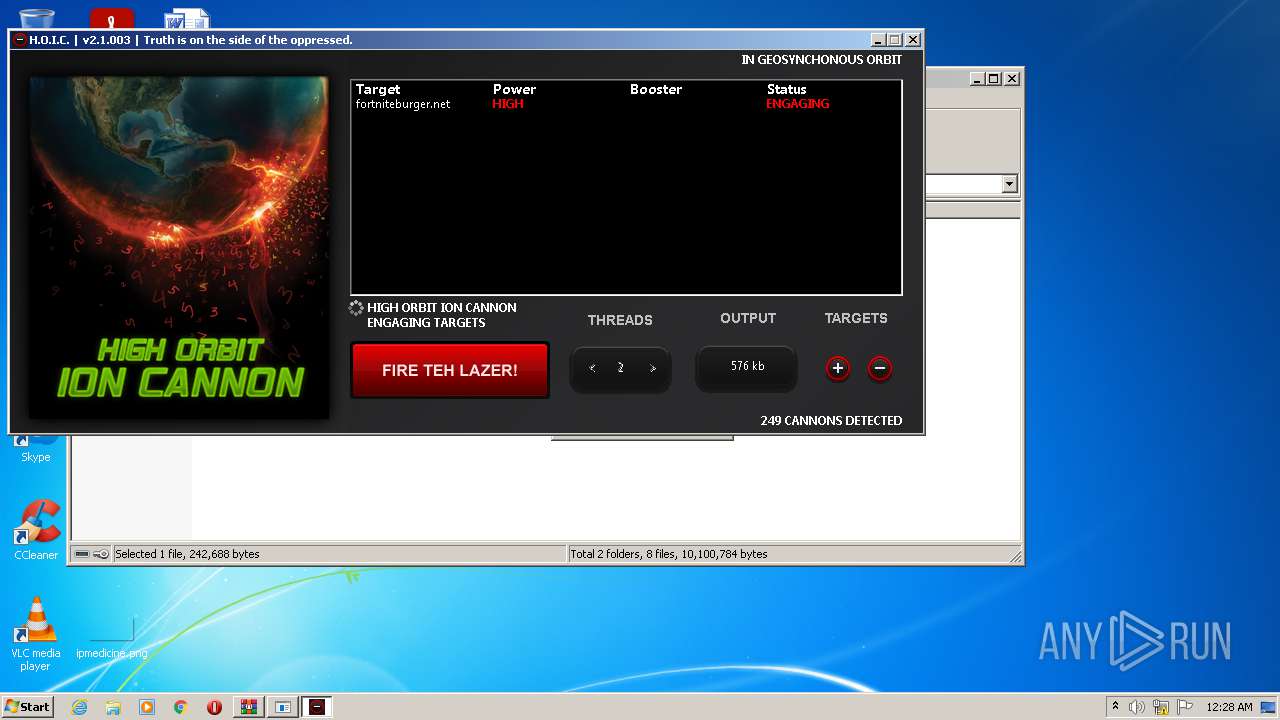
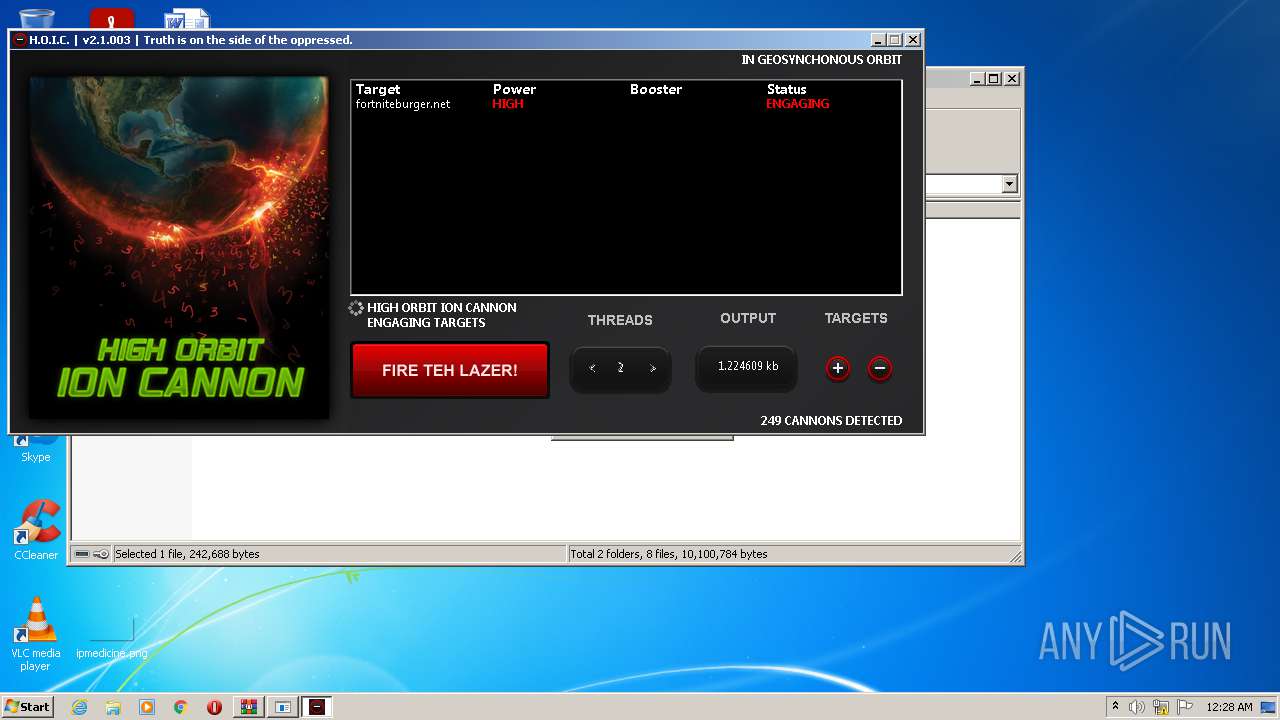
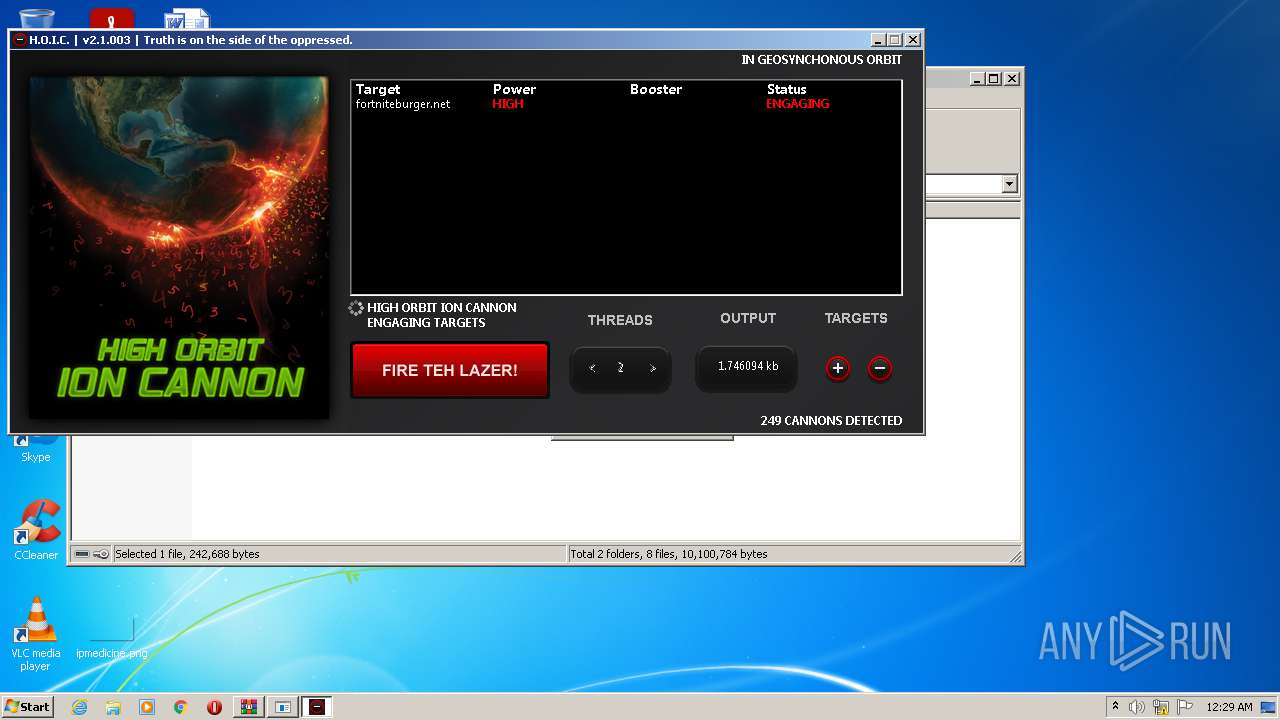
HTTP(S) requests
16 422
TCP/UDP connections
20 977
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
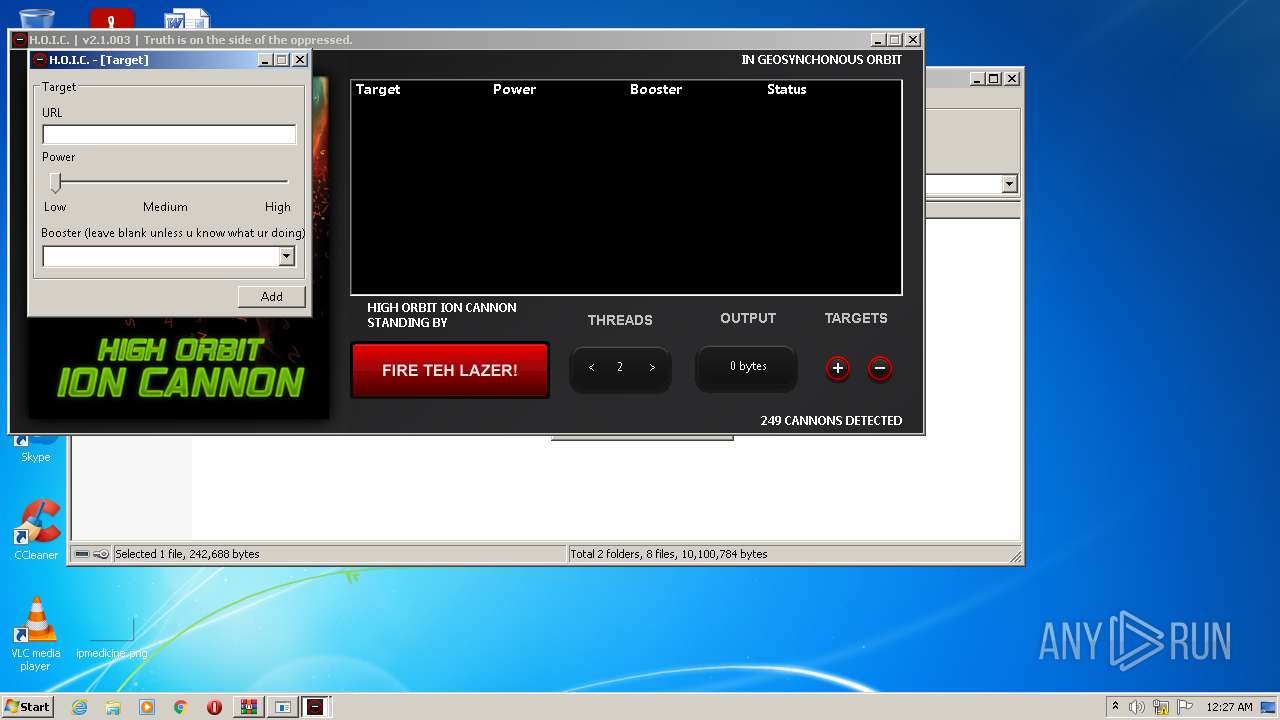
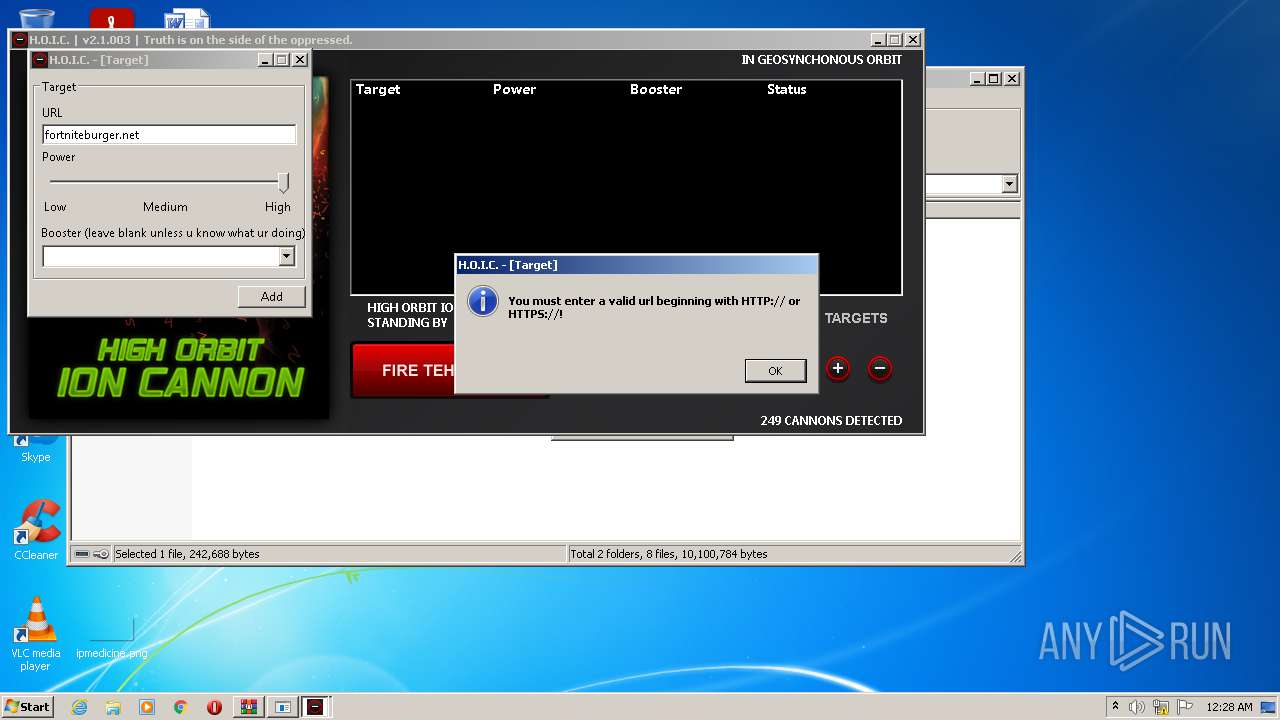
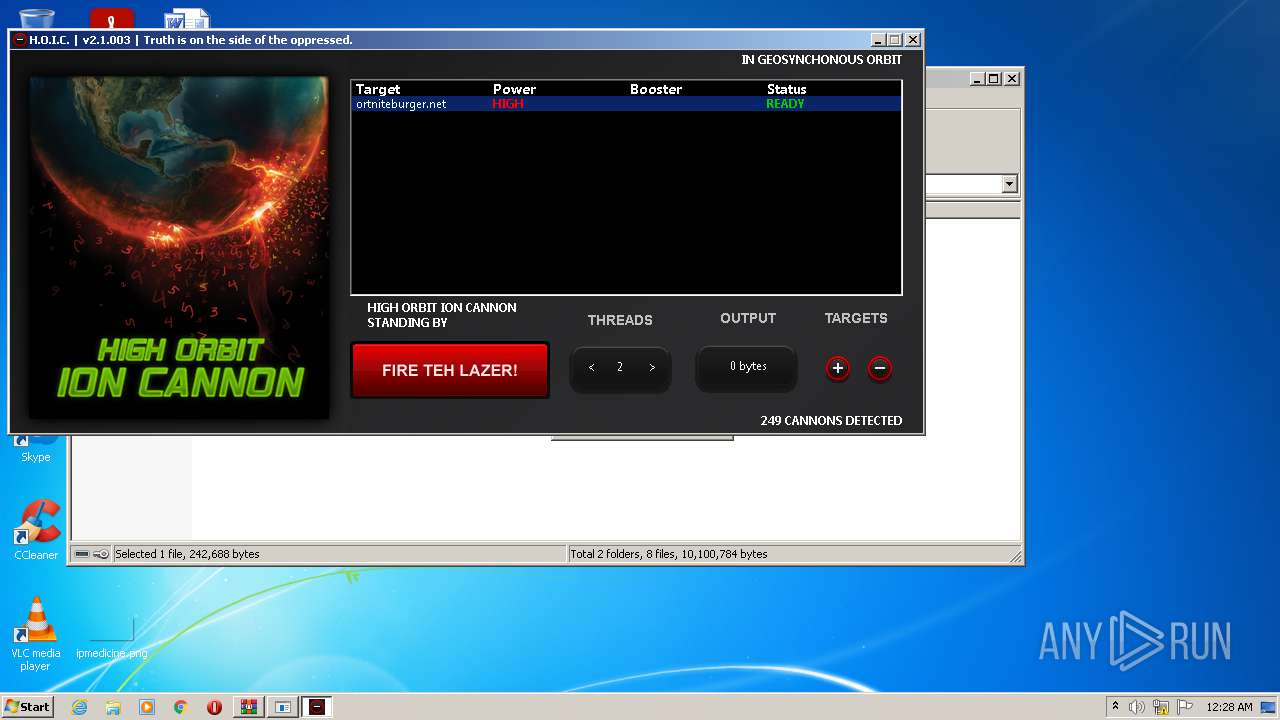
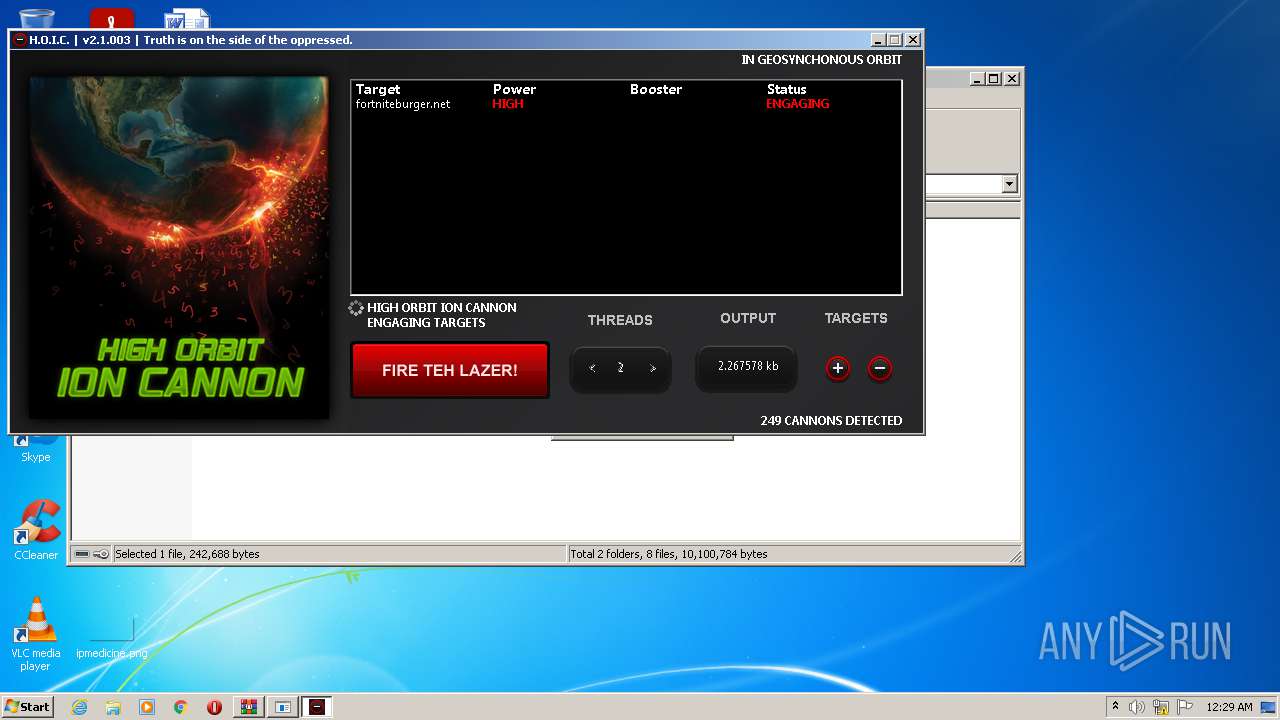
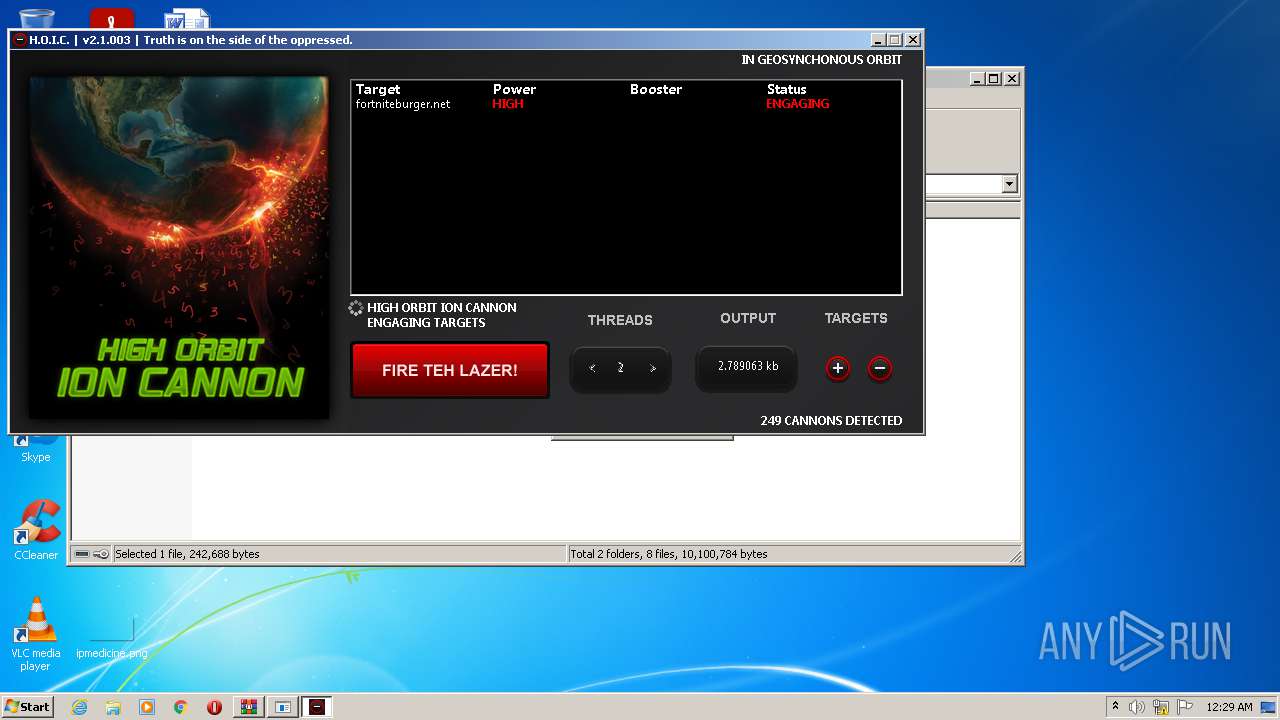
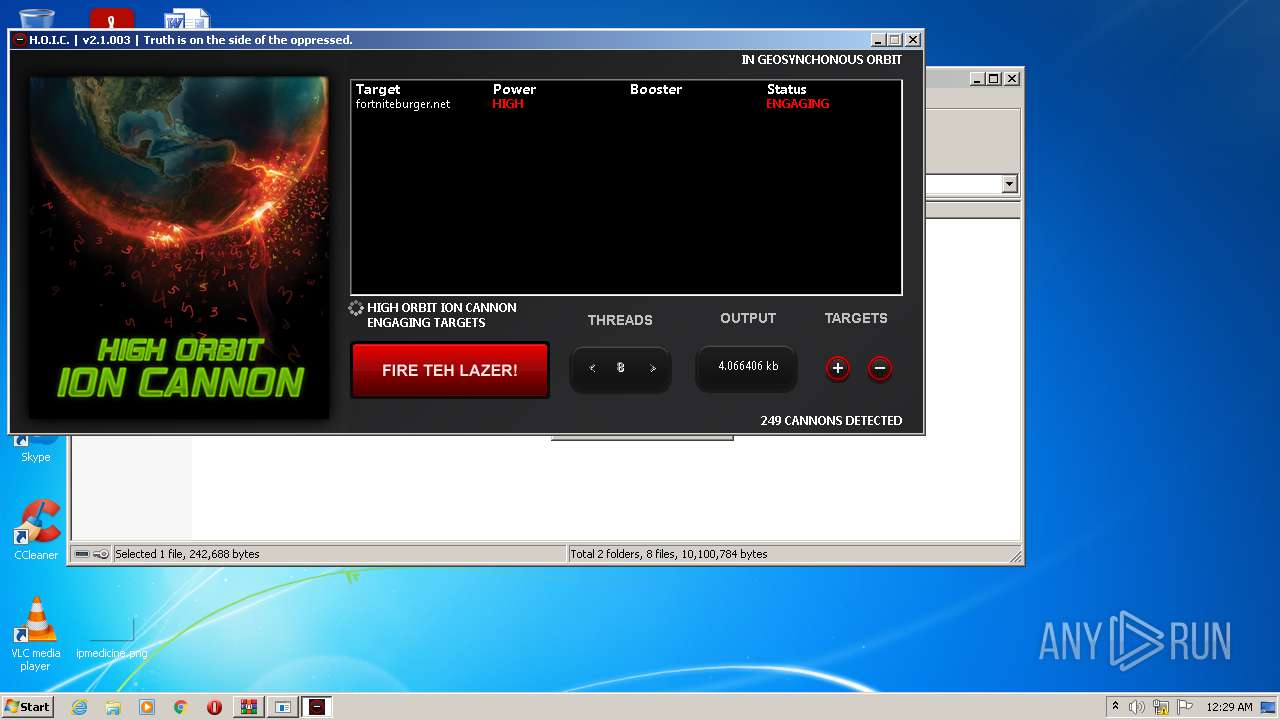
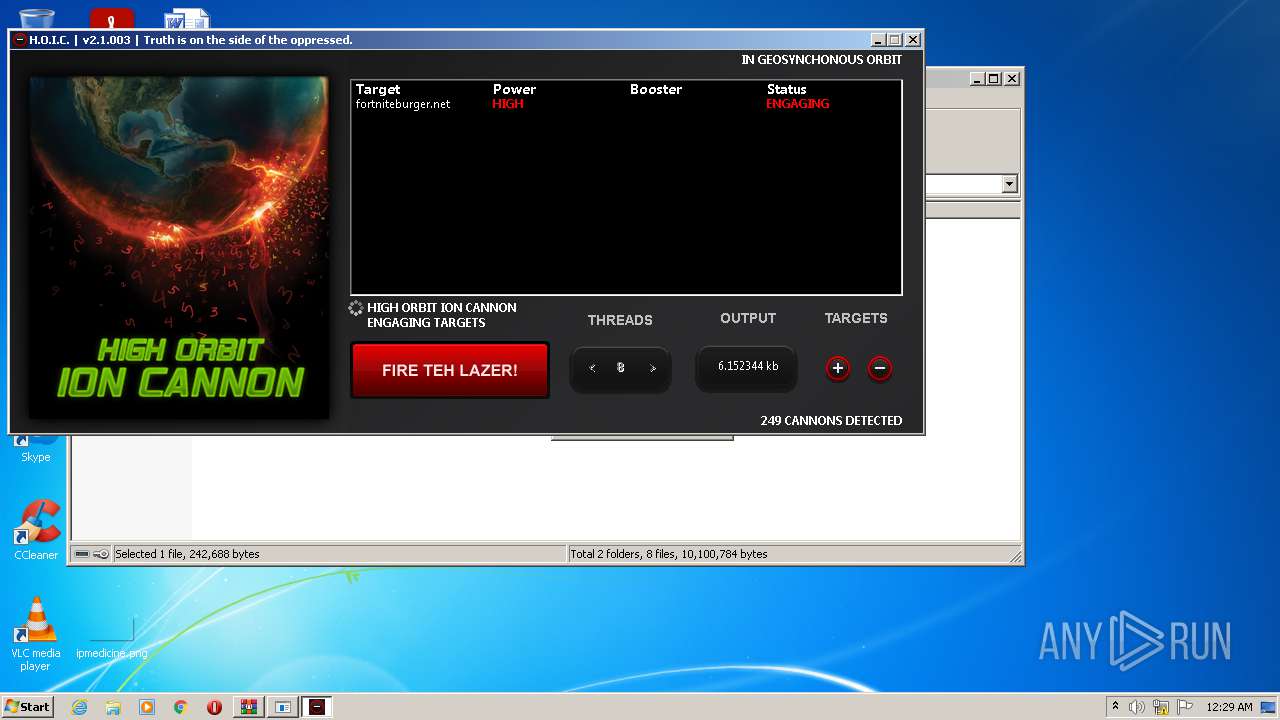
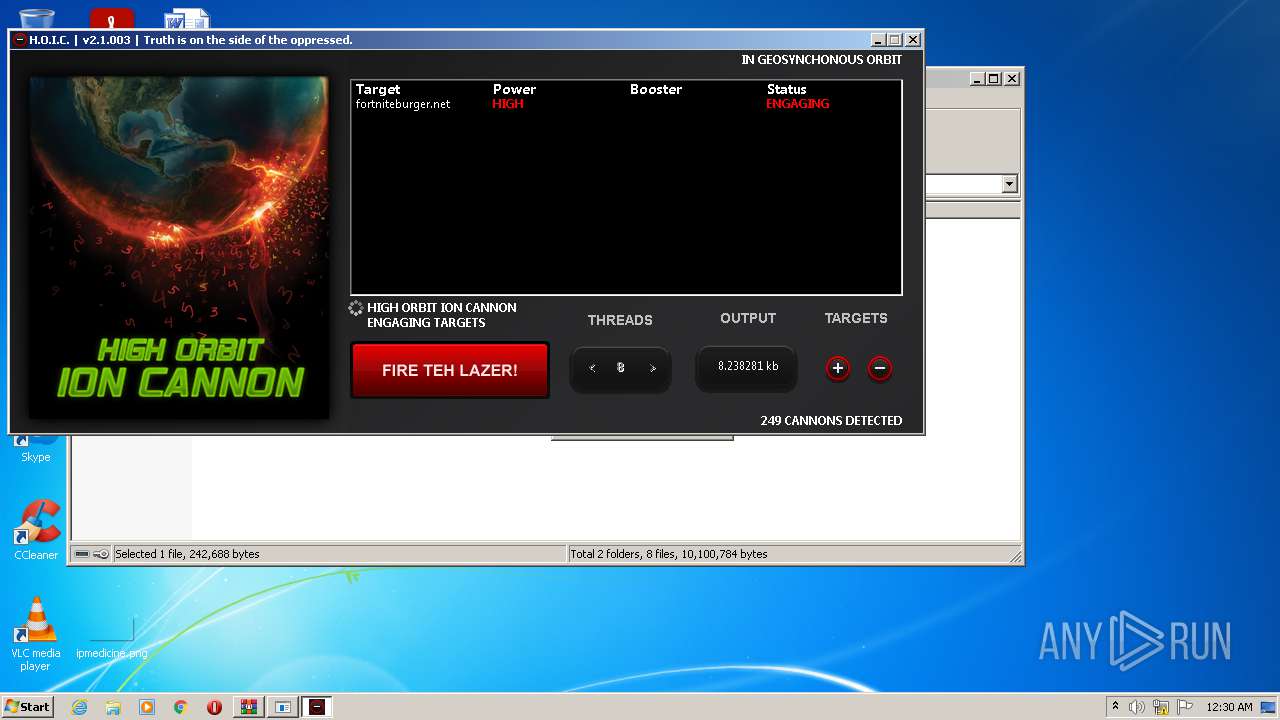
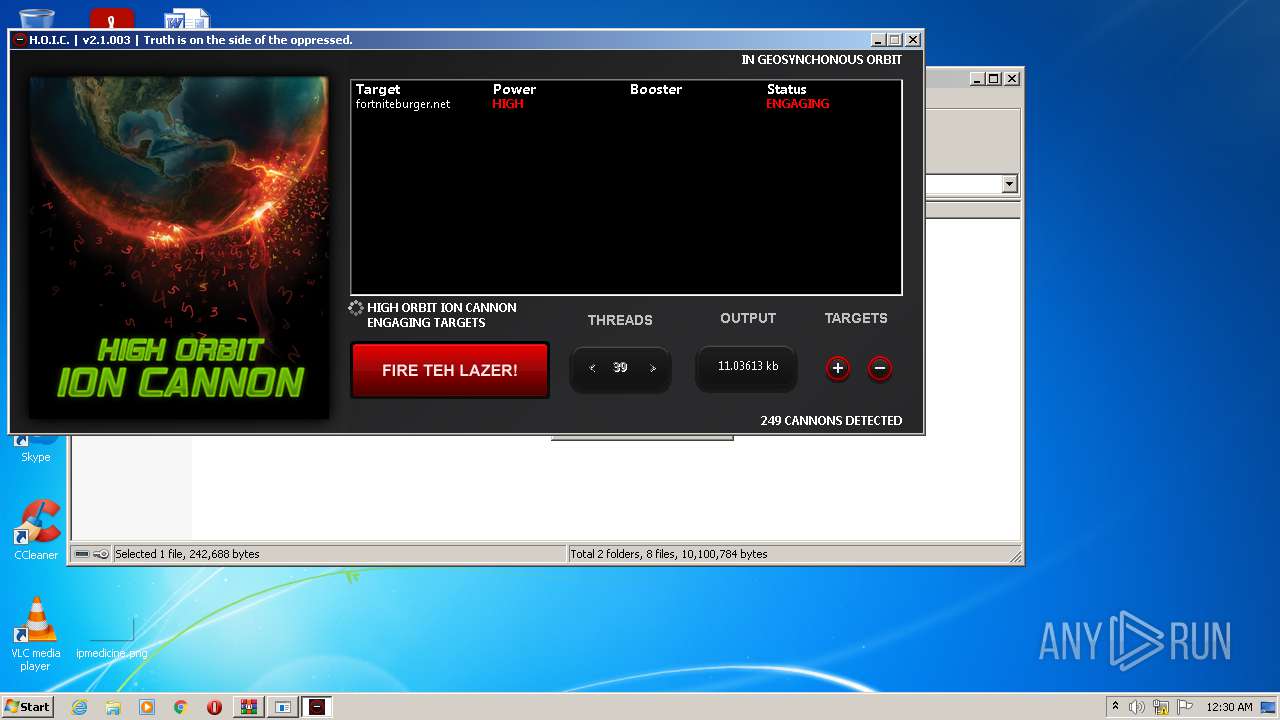
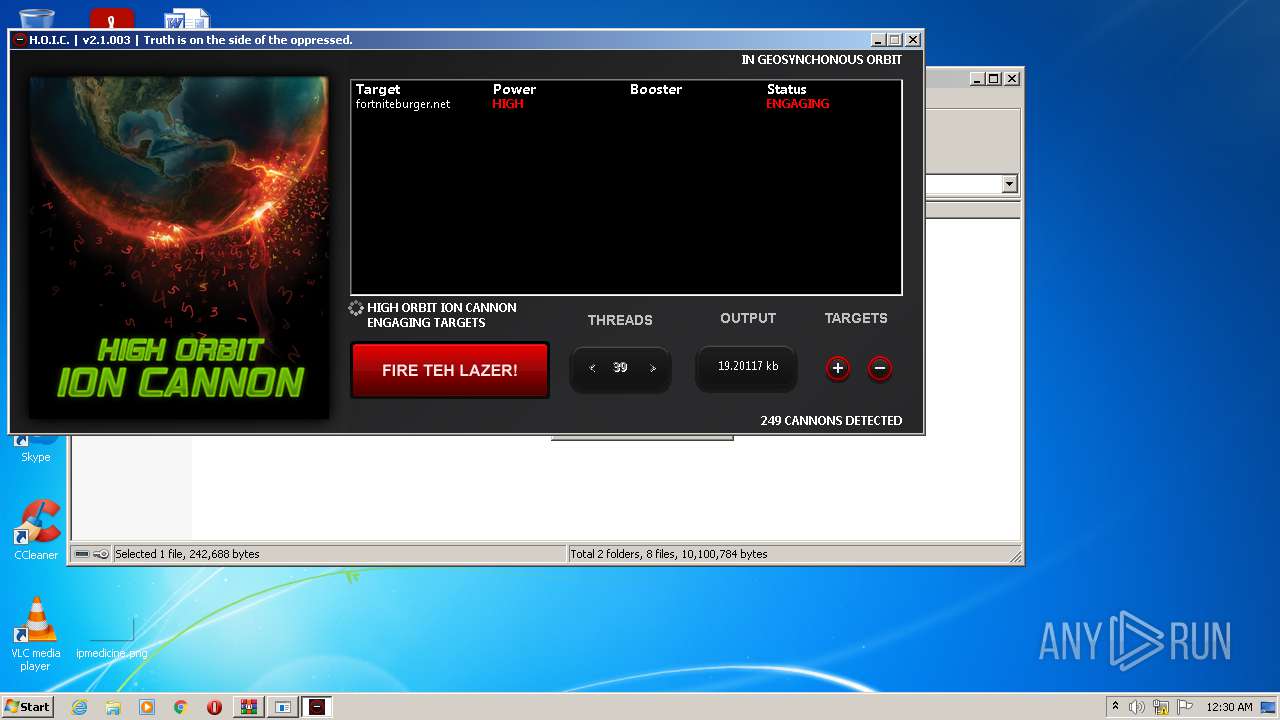
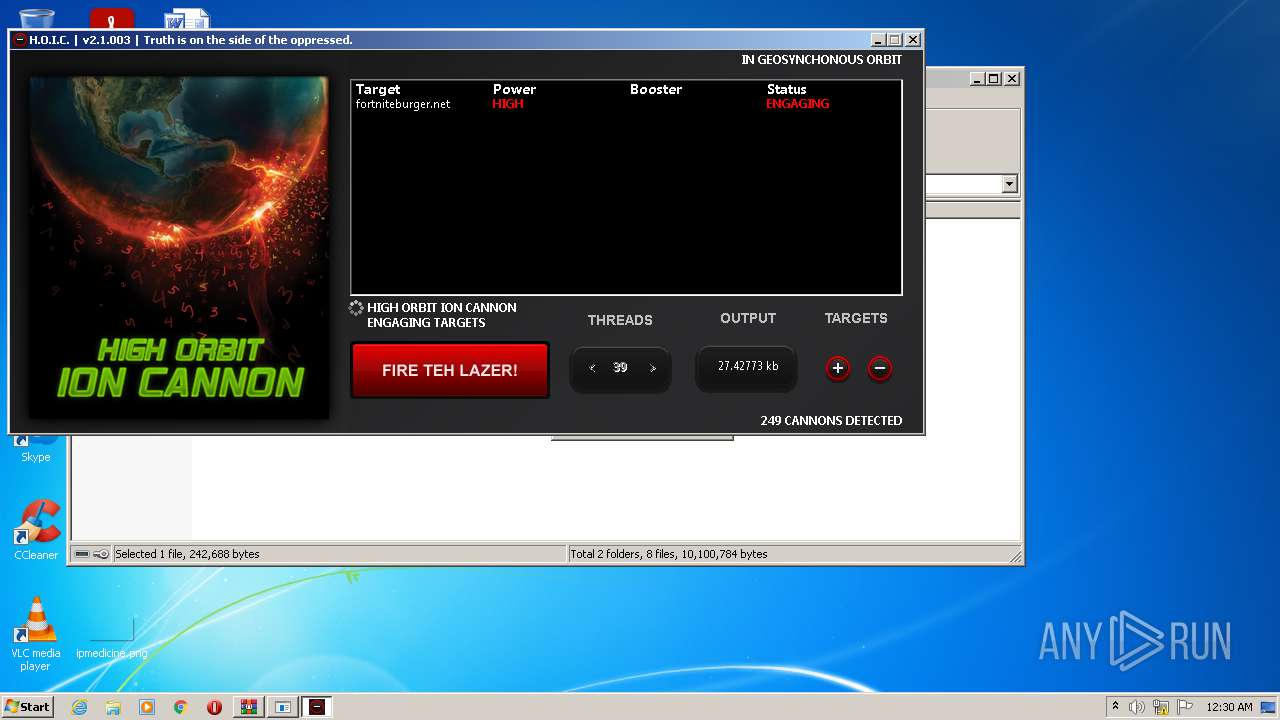
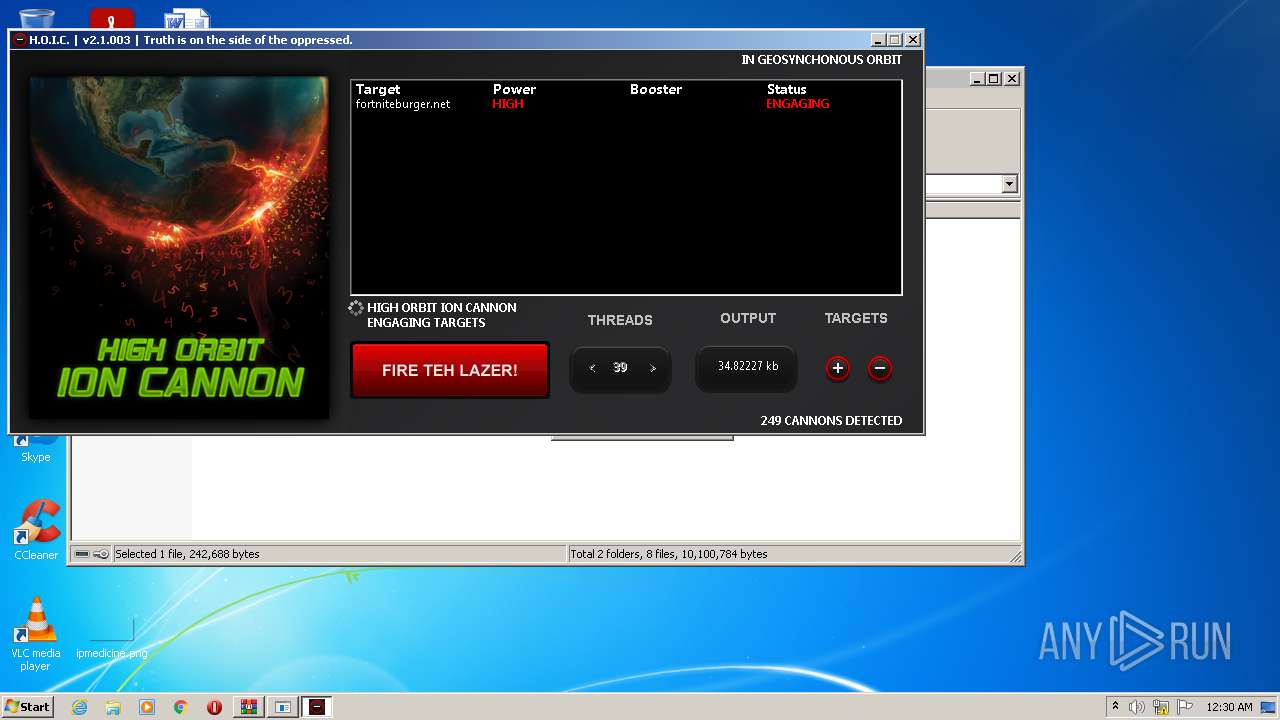
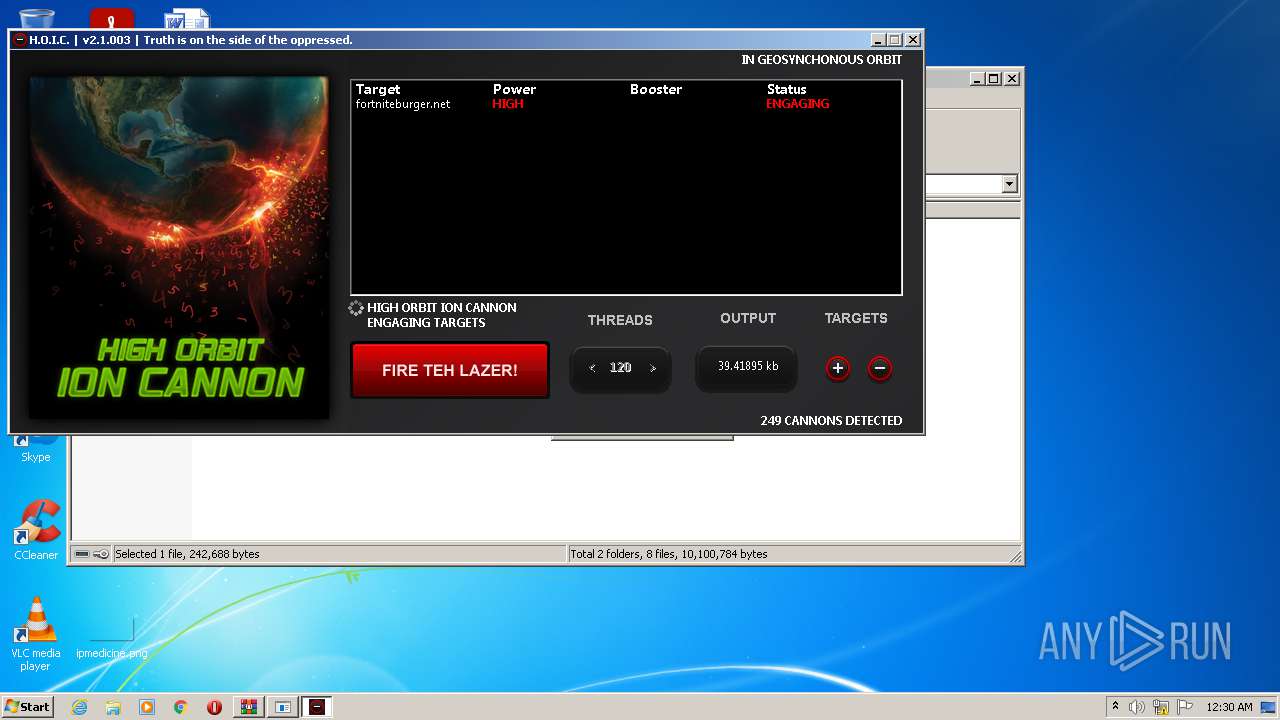
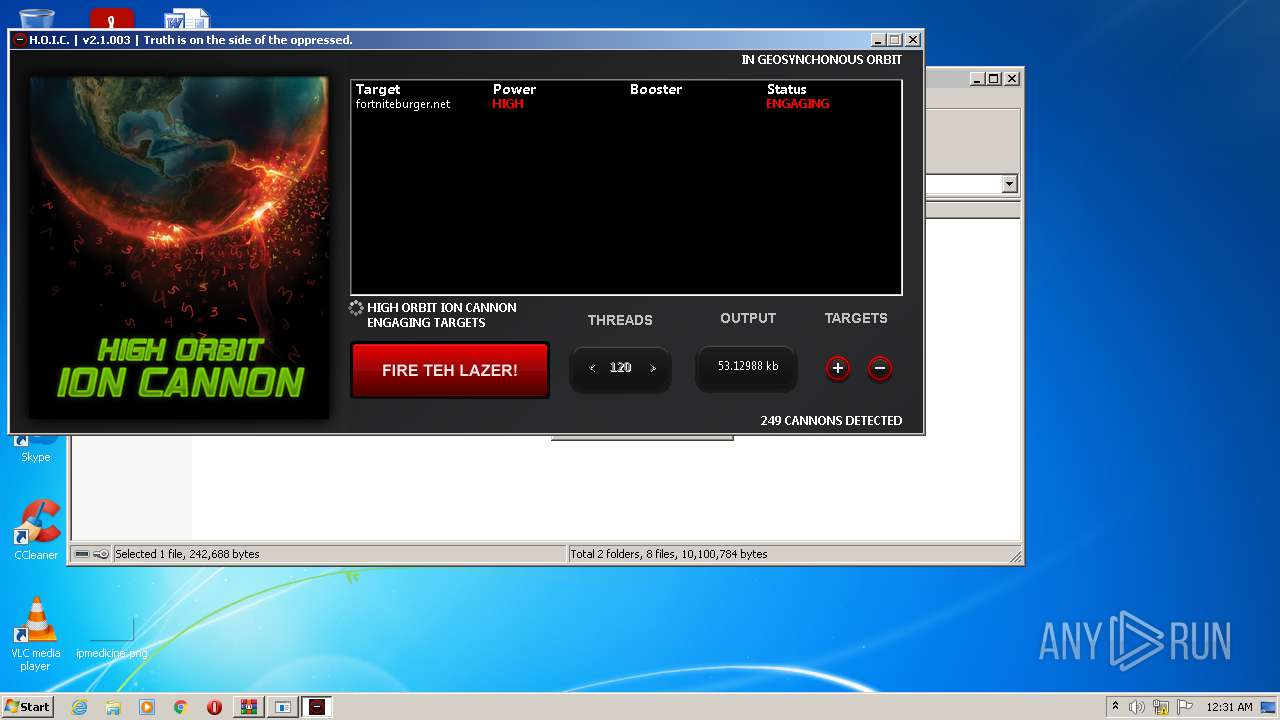
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
1944 | hc2.exe | GET | 302 | 216.239.32.21:80 | http://fortniteburger.net/ | US | html | 228 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | hc2.exe | 216.239.32.21:80 | fortniteburger.net | Google Inc. | US | whitelisted |
— | — | 216.239.32.21:80 | fortniteburger.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fortniteburger.net |
| malicious |