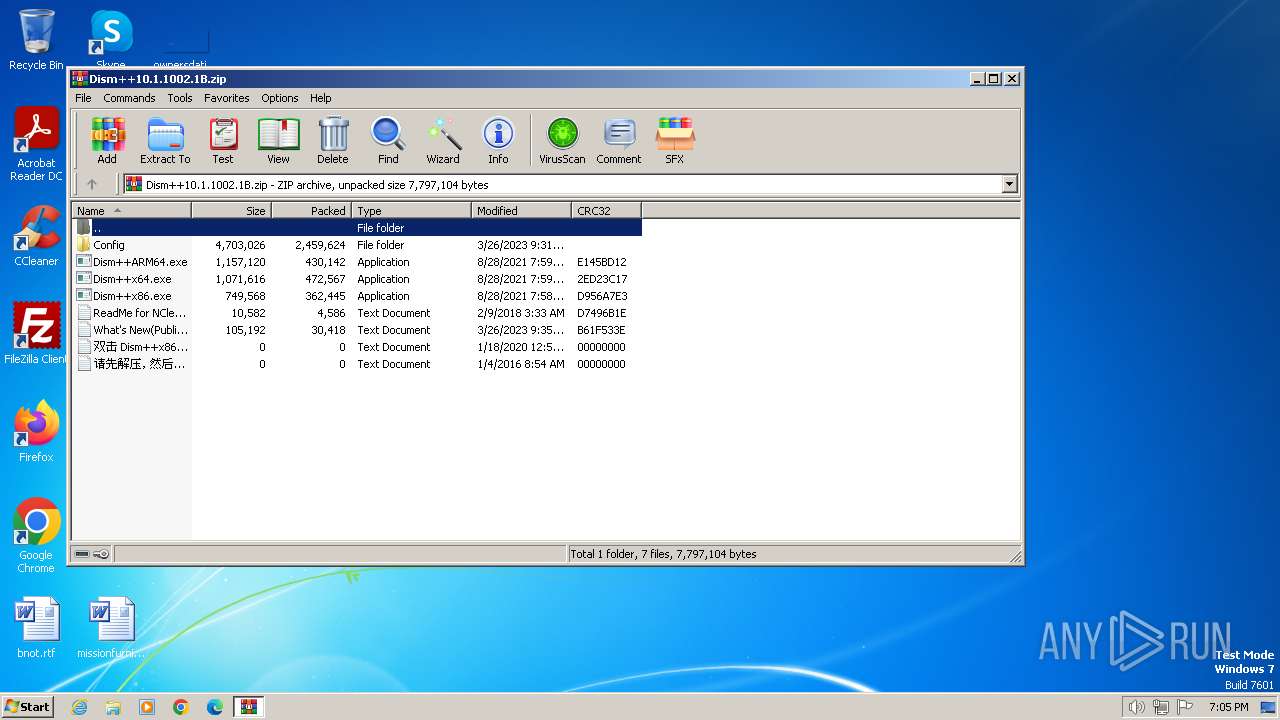
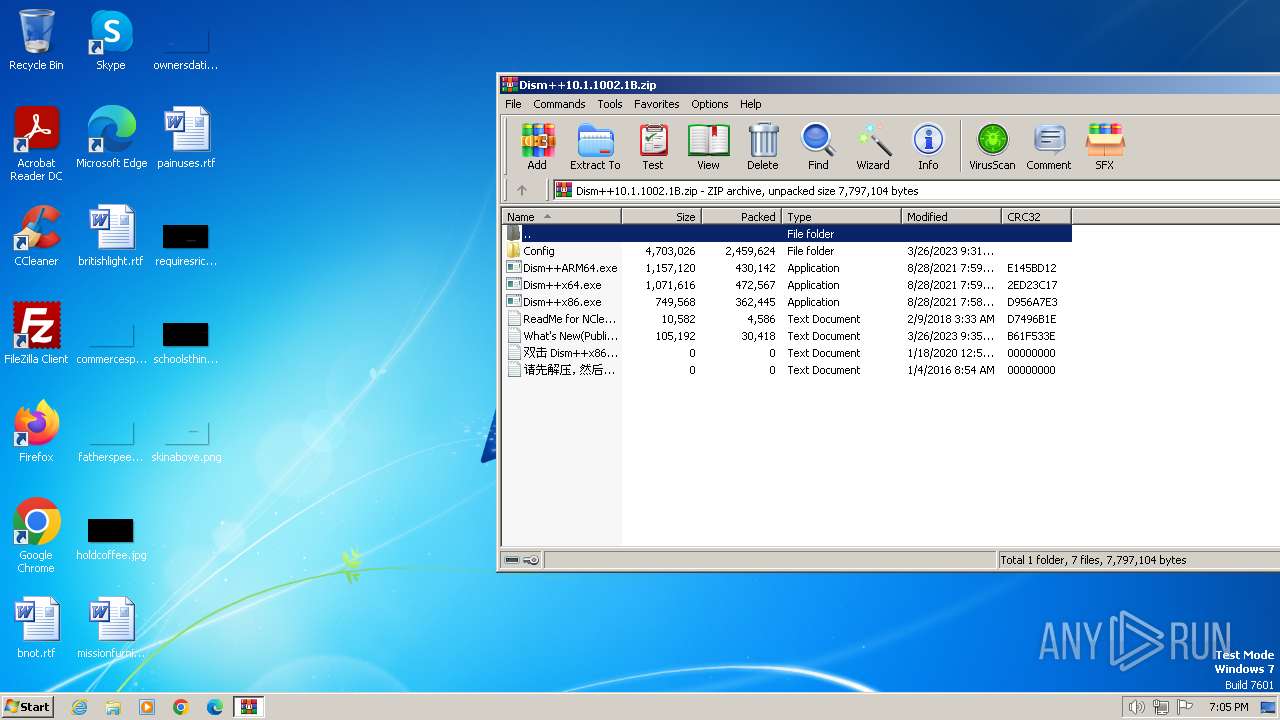
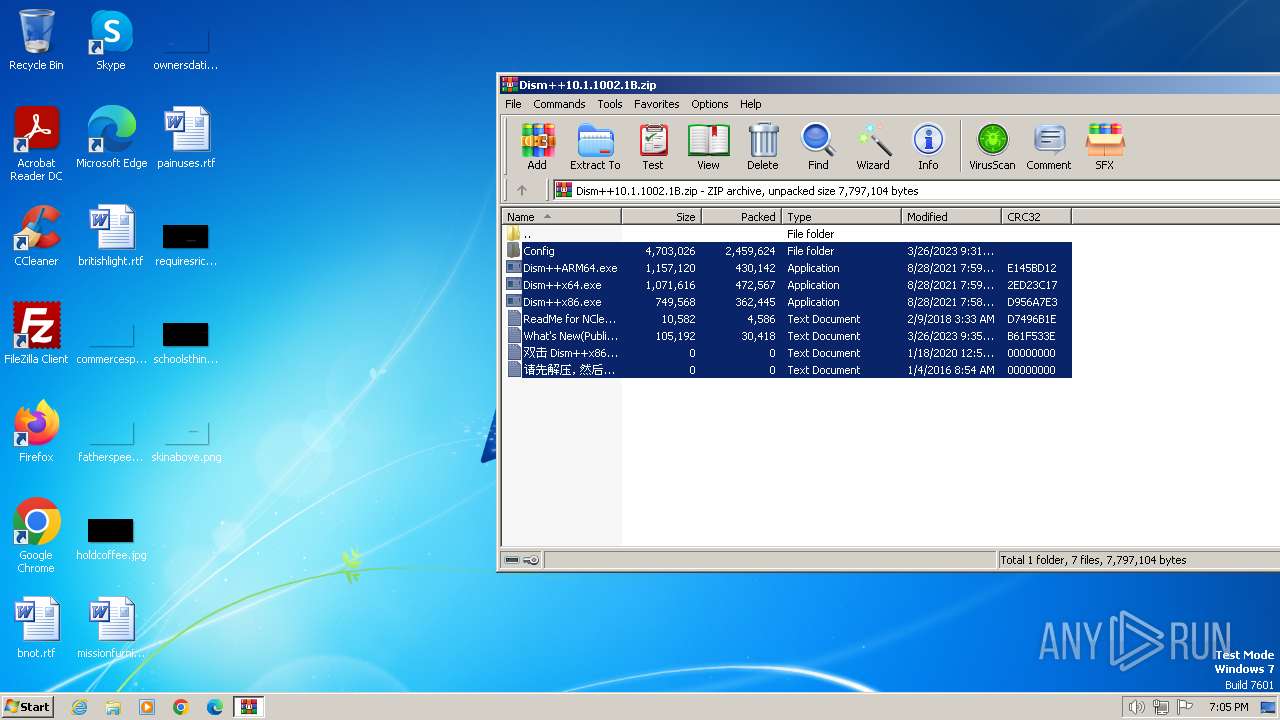
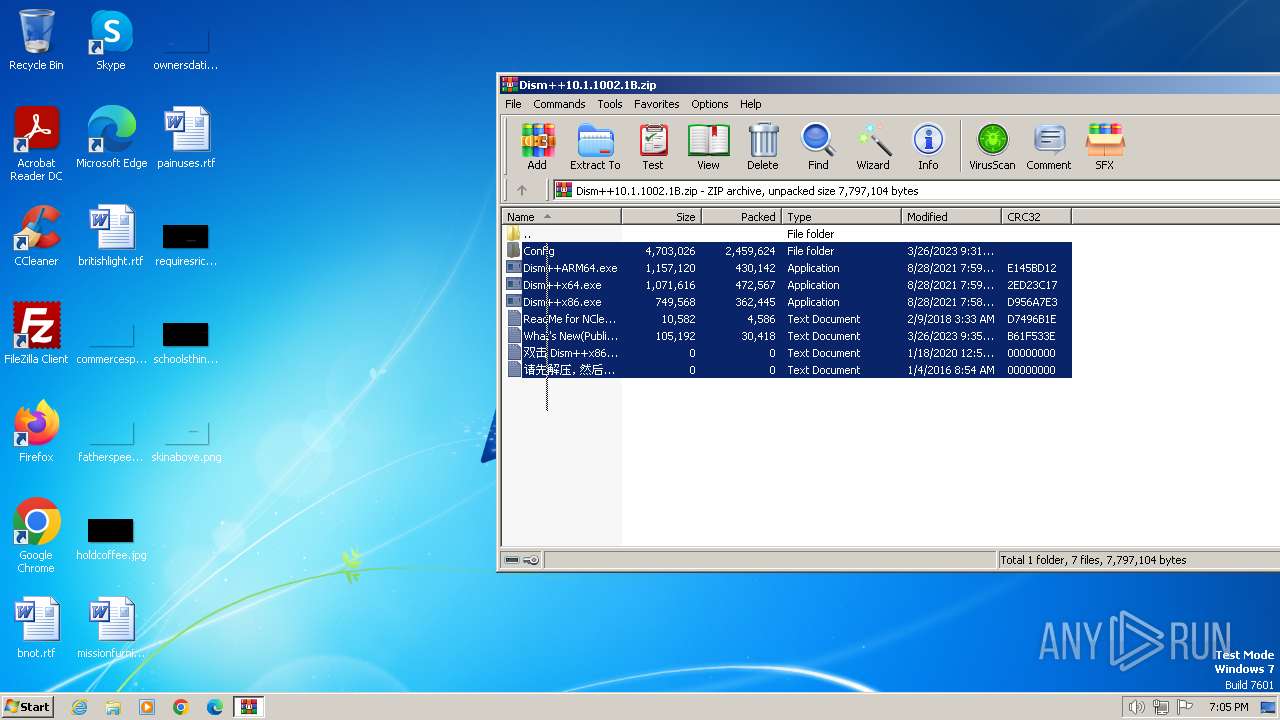
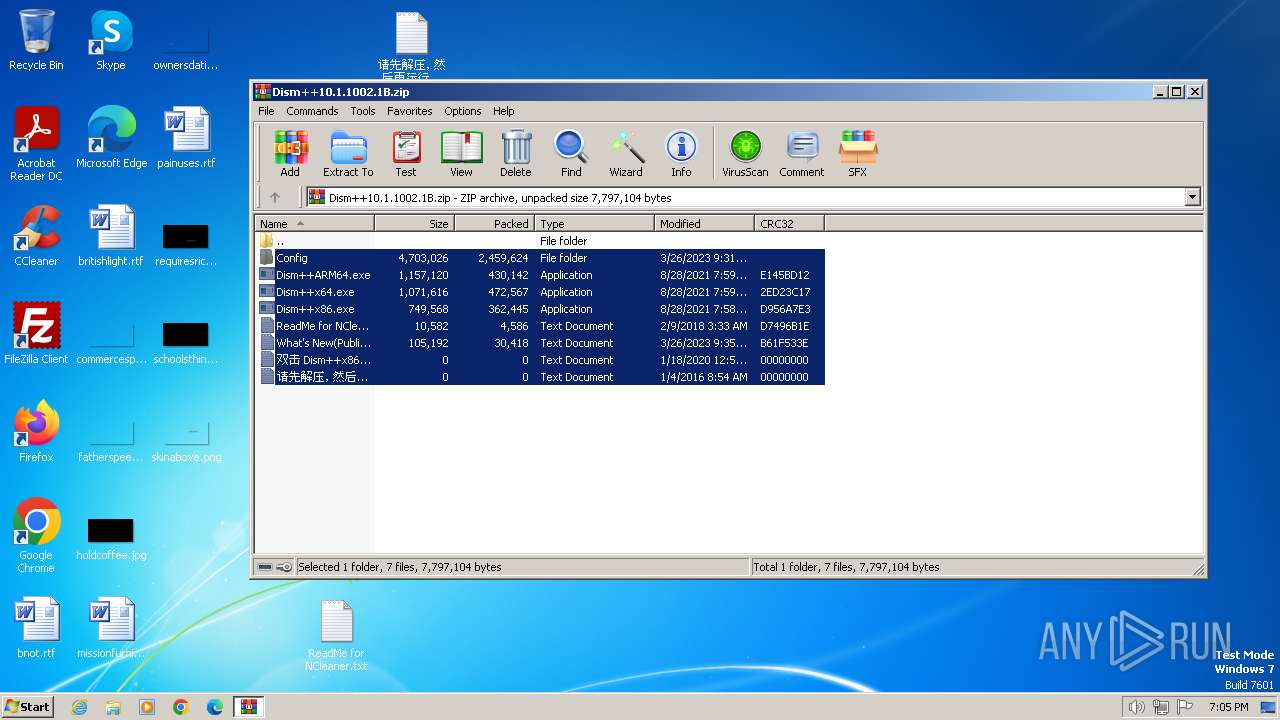
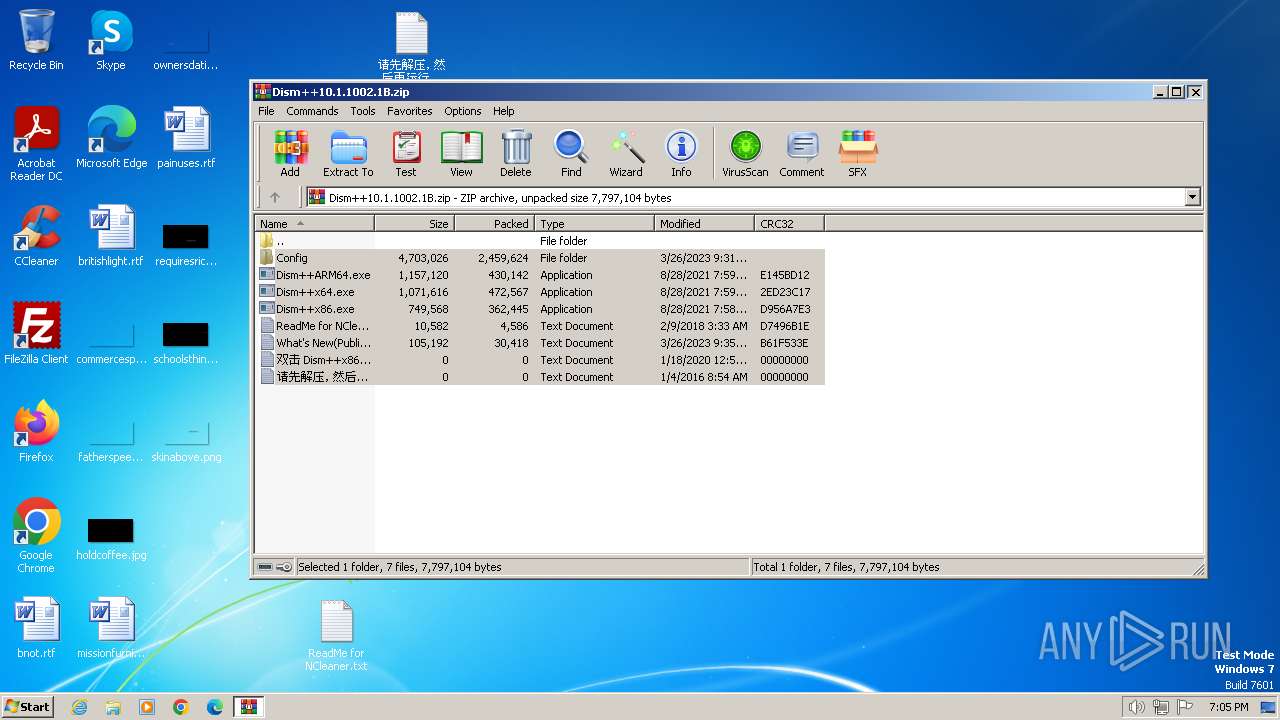
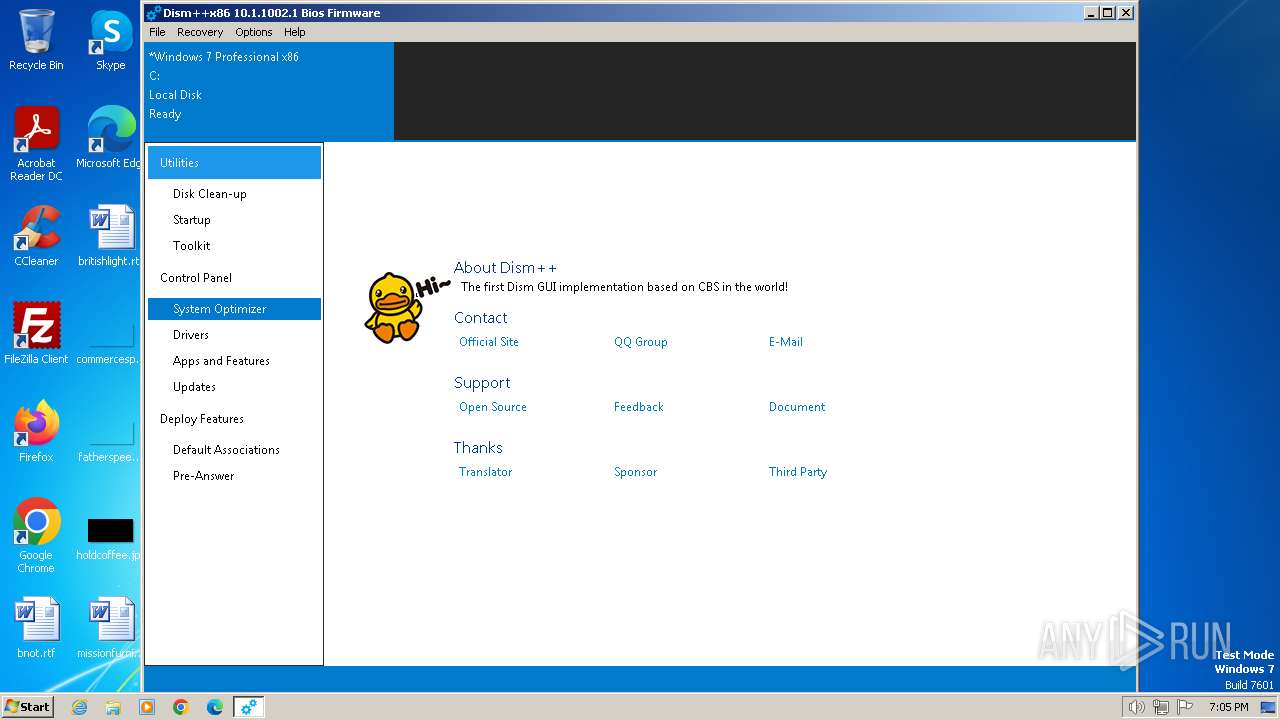
| File name: | Dism++10.1.1002.1B.zip |
| Full analysis: | https://app.any.run/tasks/693d6972-d726-421f-b1e9-7ad7cef9b956 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2024, 19:05:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F5485E418DA631B6289E4A51495BCA87 |
| SHA1: | 2ECB84172BF12FEC7C9E1F378466DB53589660FB |
| SHA256: | 5BBAB96D60704854EFD8246A7D9371688B9102261544827FC8884126D70BCB3B |
| SSDEEP: | 98304:vKBqv2ChMWSVDy+Q8YOUoYqeYfsuK0sTILg6ixyeXmziSTPB+u8:SB82KMWqyJfoEY0l0sUAxp2WIPB+u8 |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1504)
- bcdboot.exe (PID: 1808)
- uninstall.exe (PID: 1316)
- Un_A.exe (PID: 392)
Creates a writable file in the system directory
- bcdboot.exe (PID: 1808)
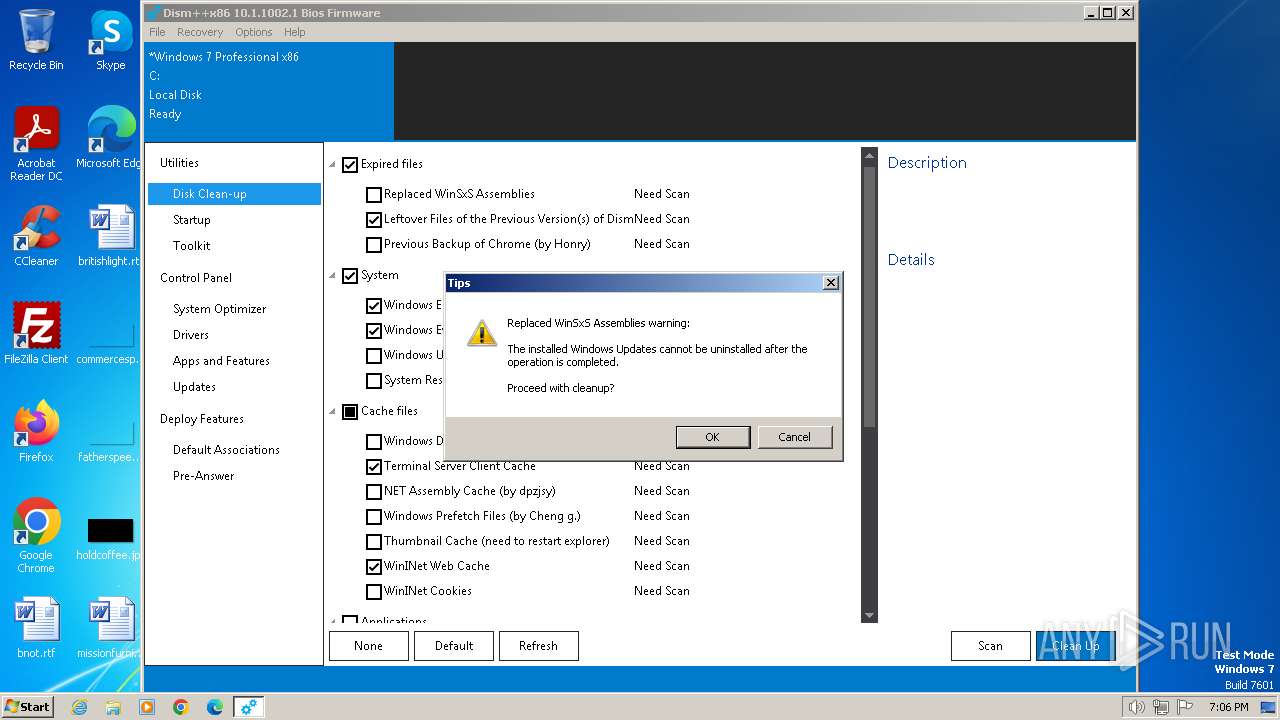
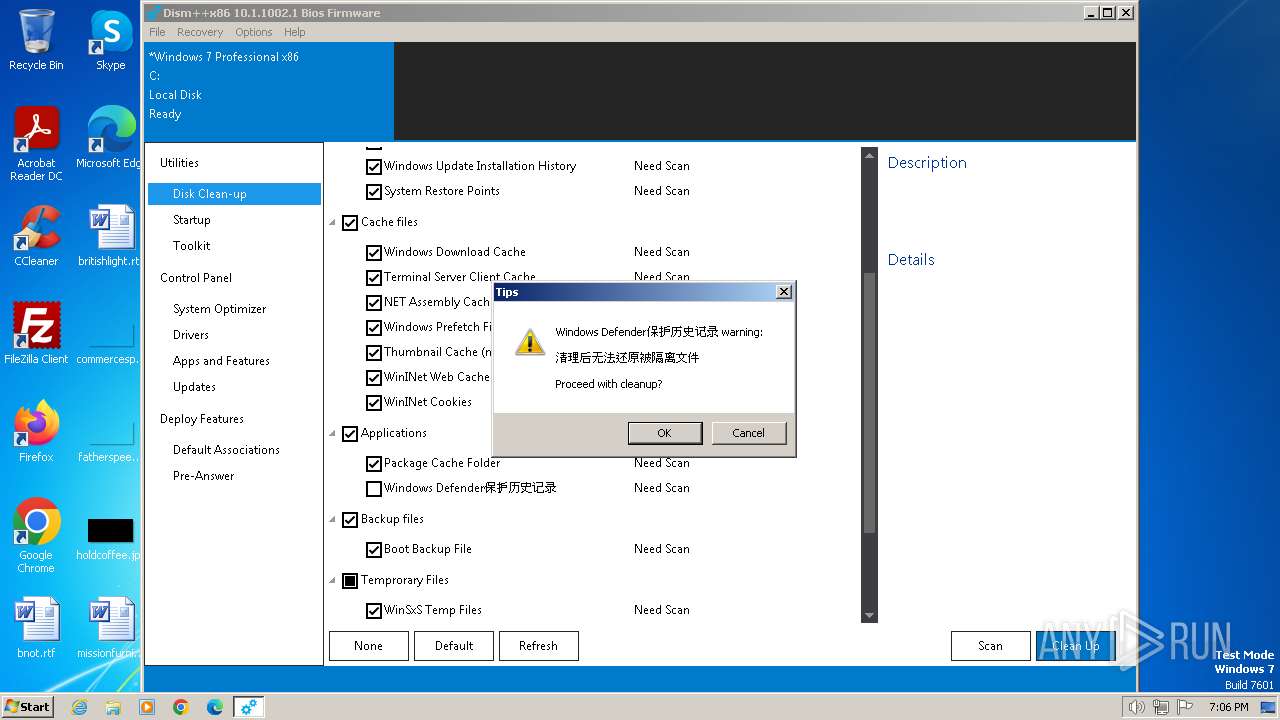
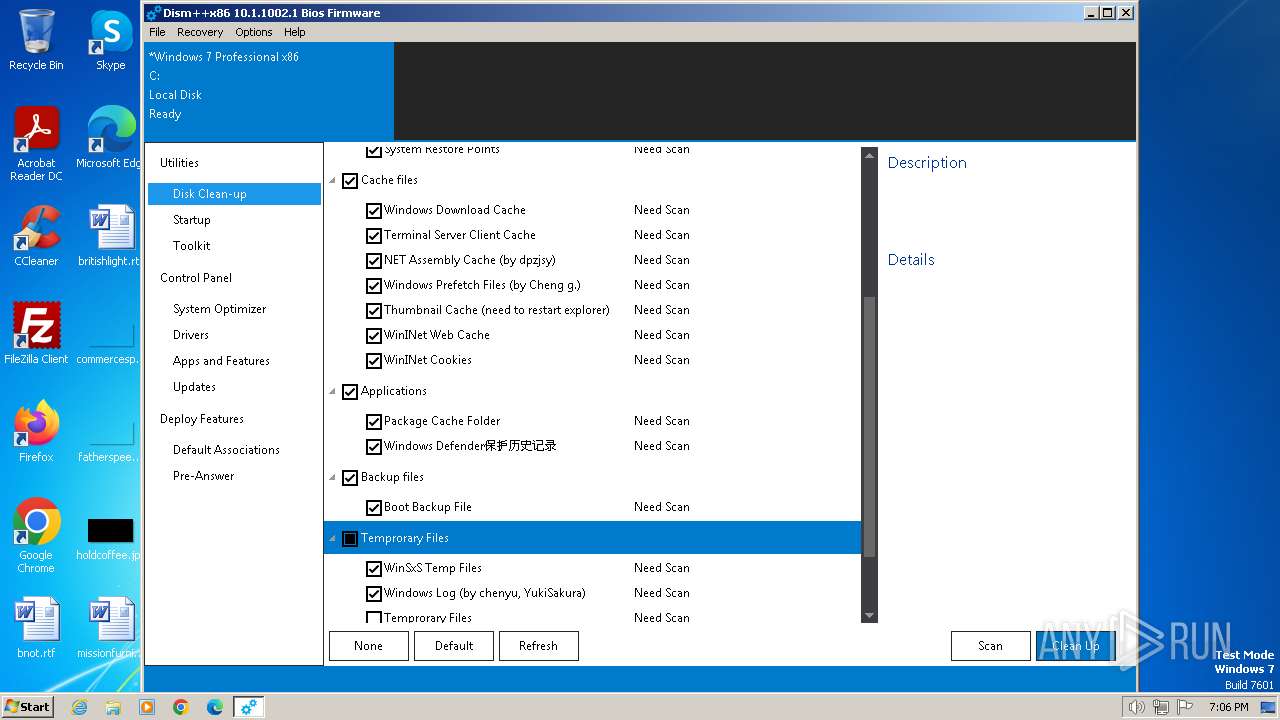
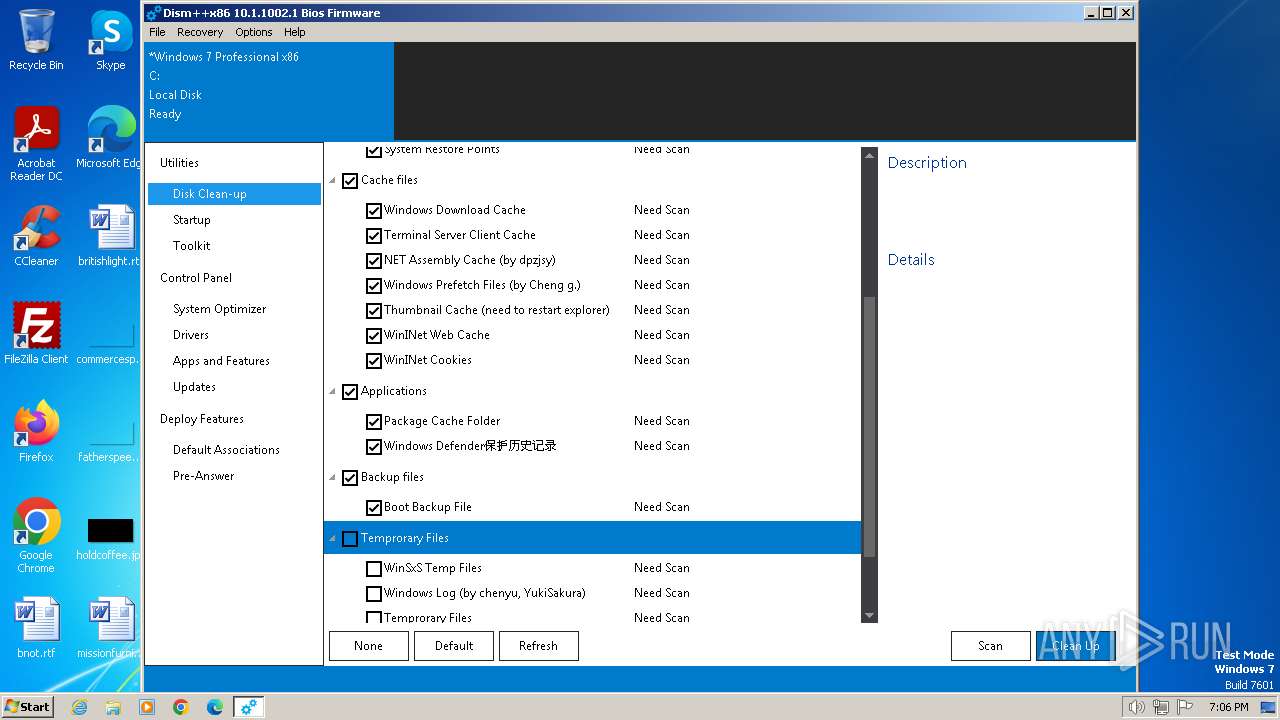
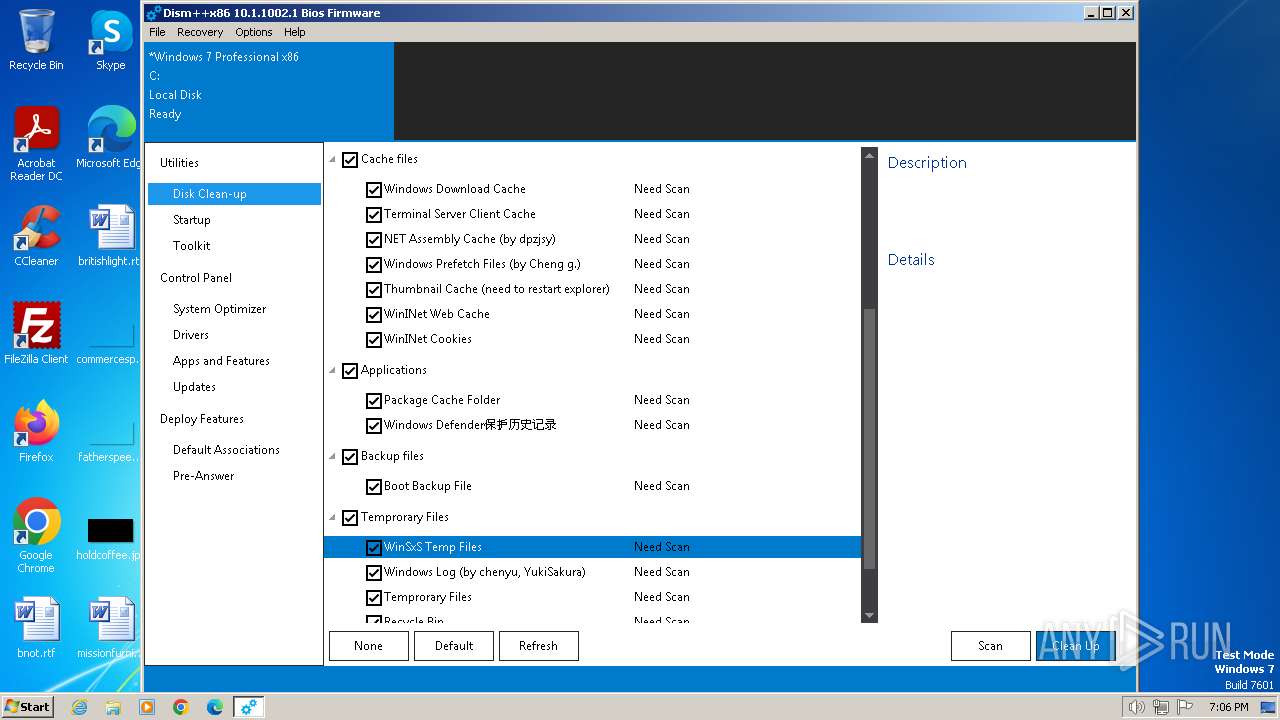
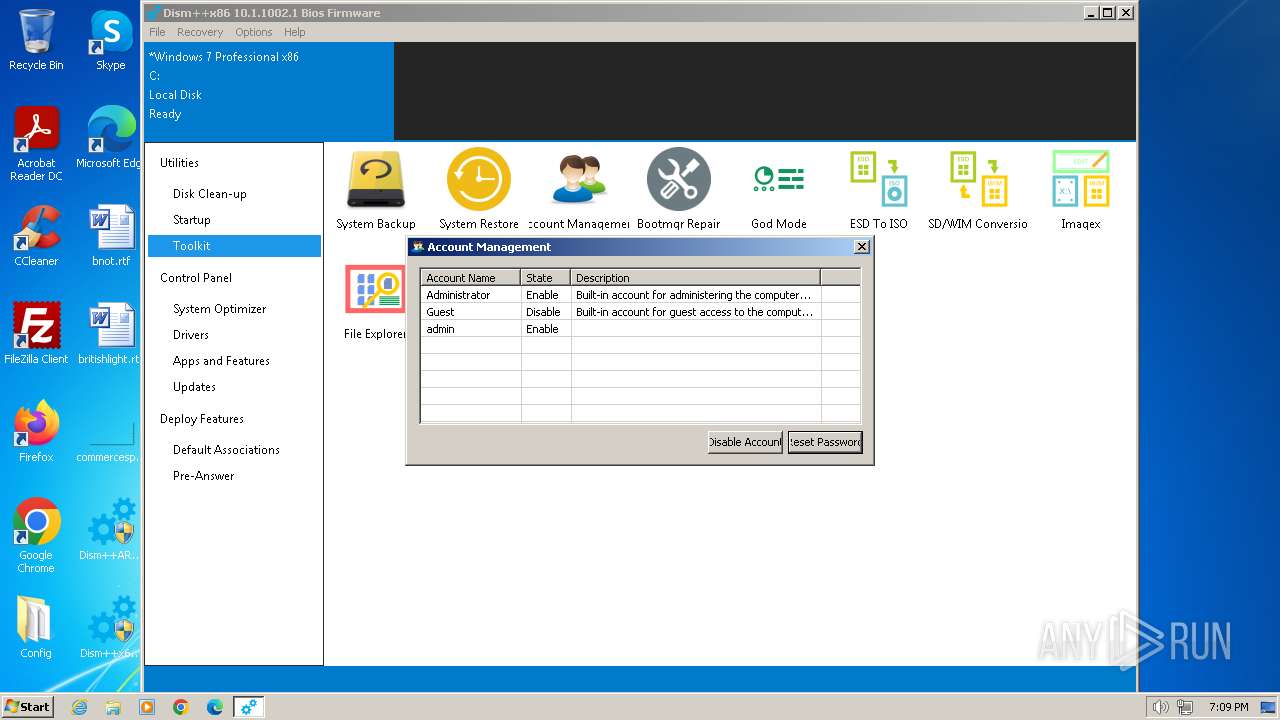
SUSPICIOUS
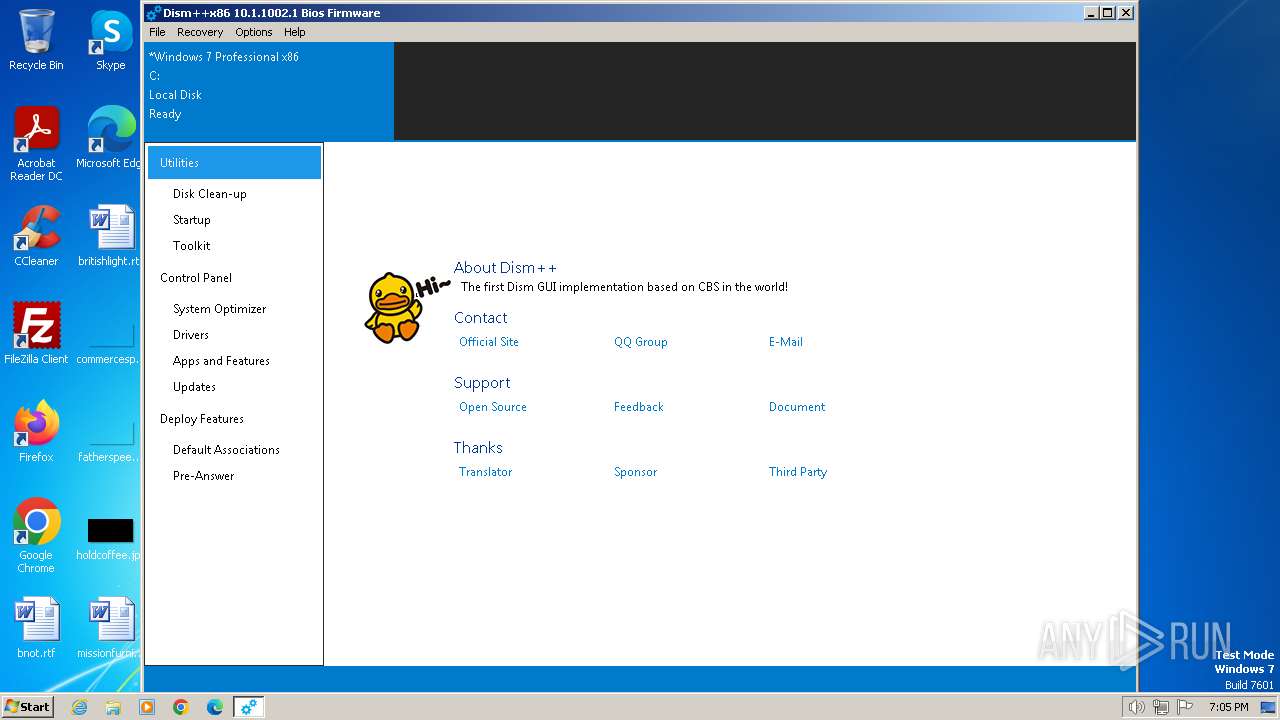
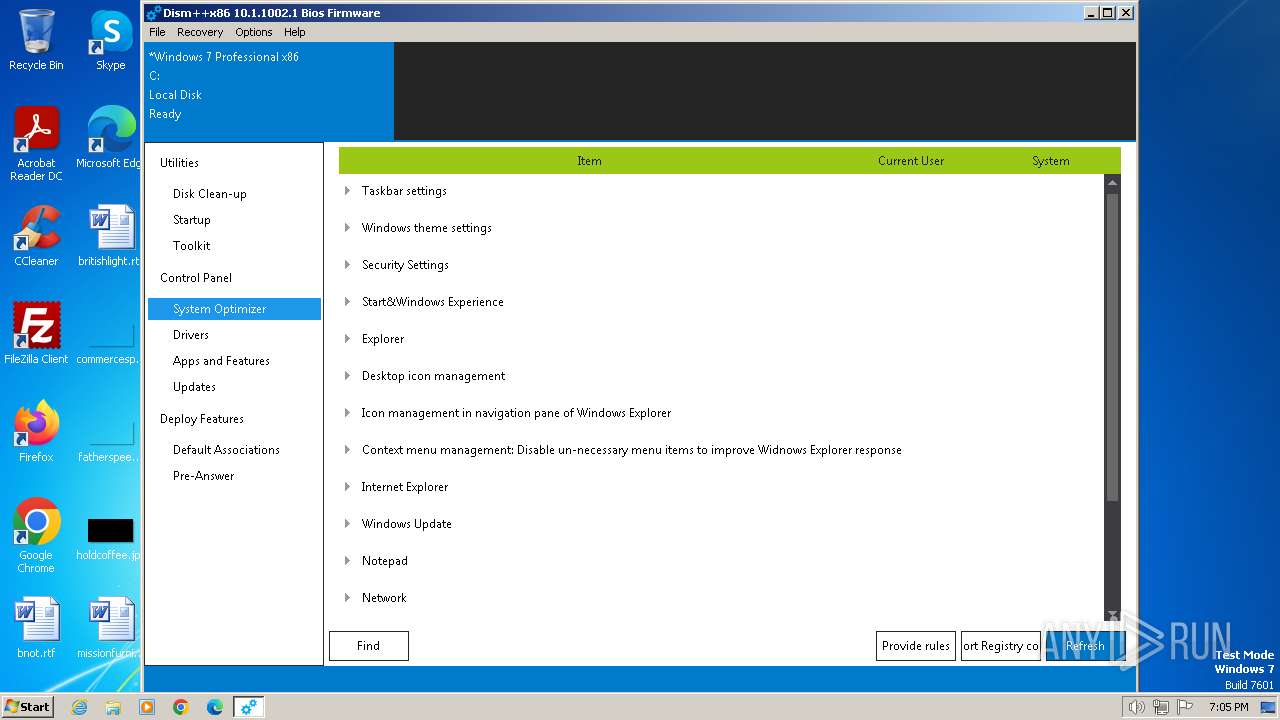
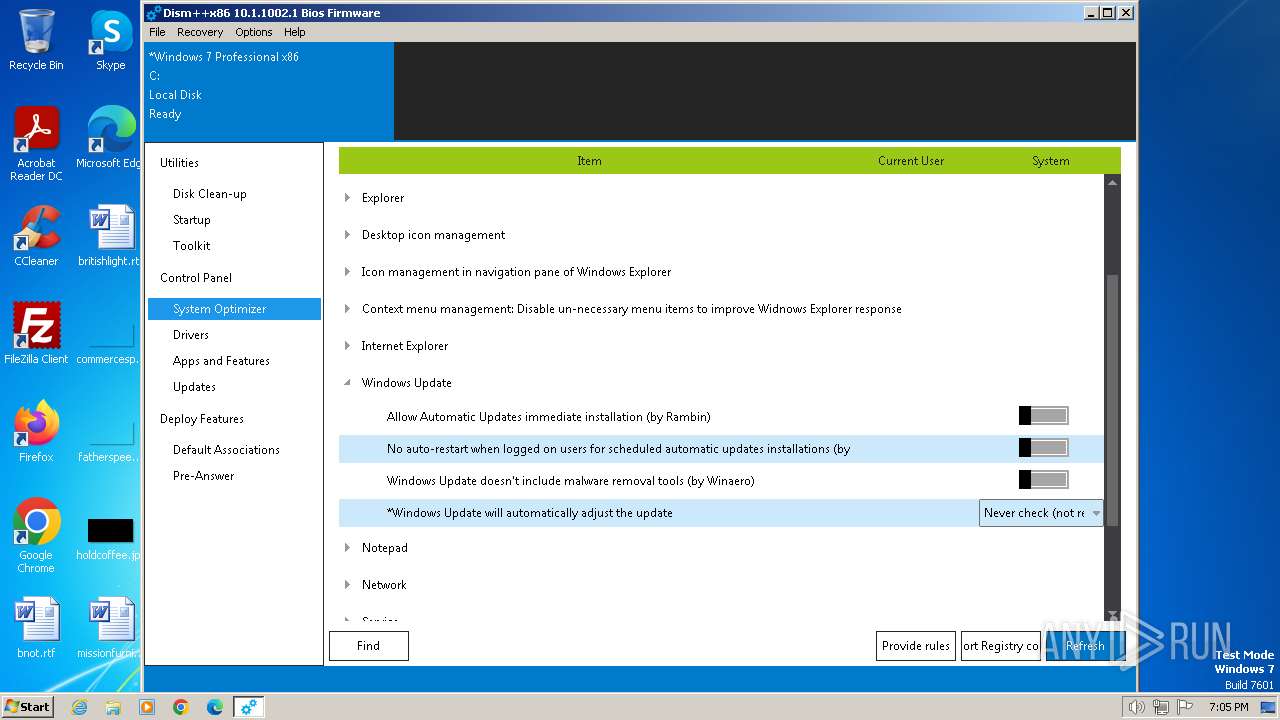
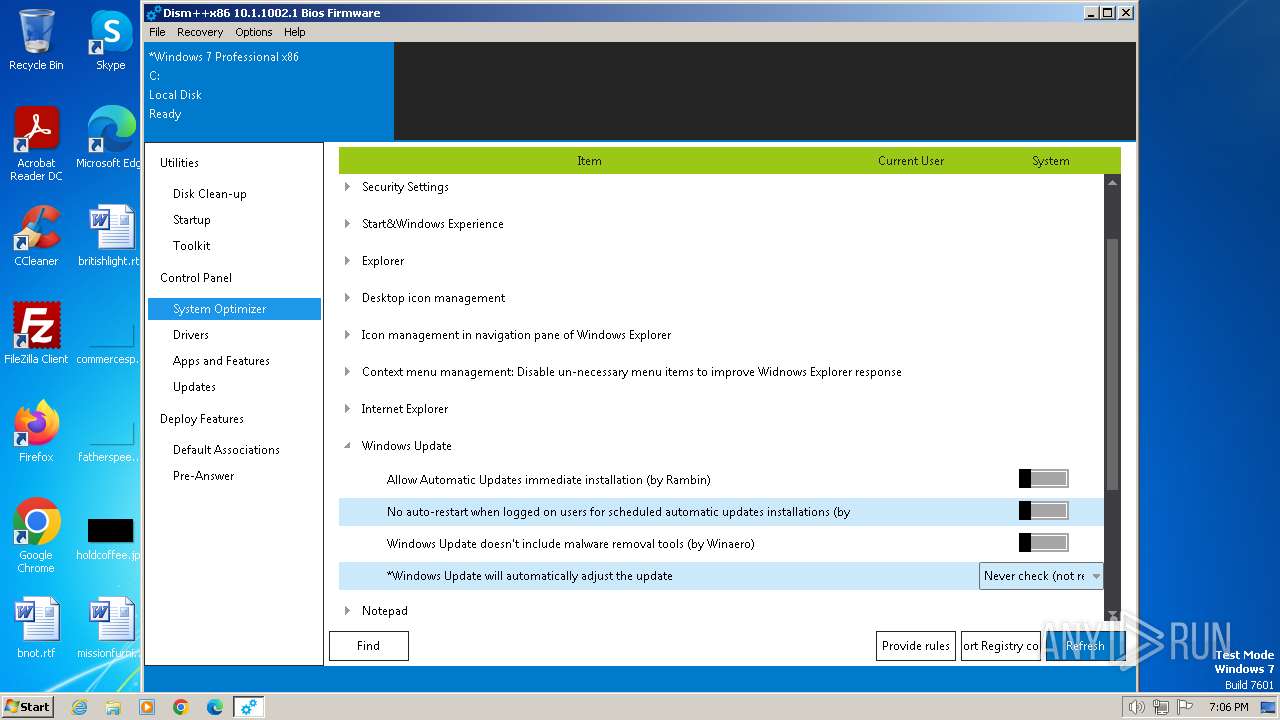
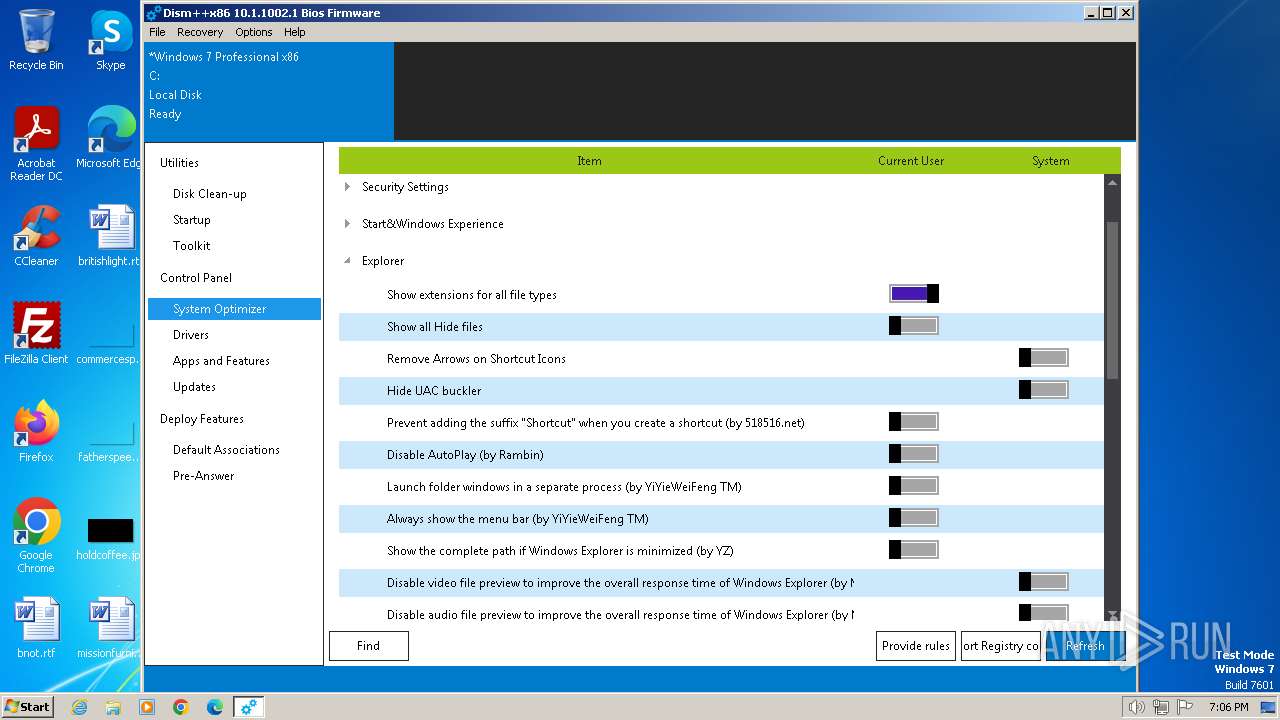
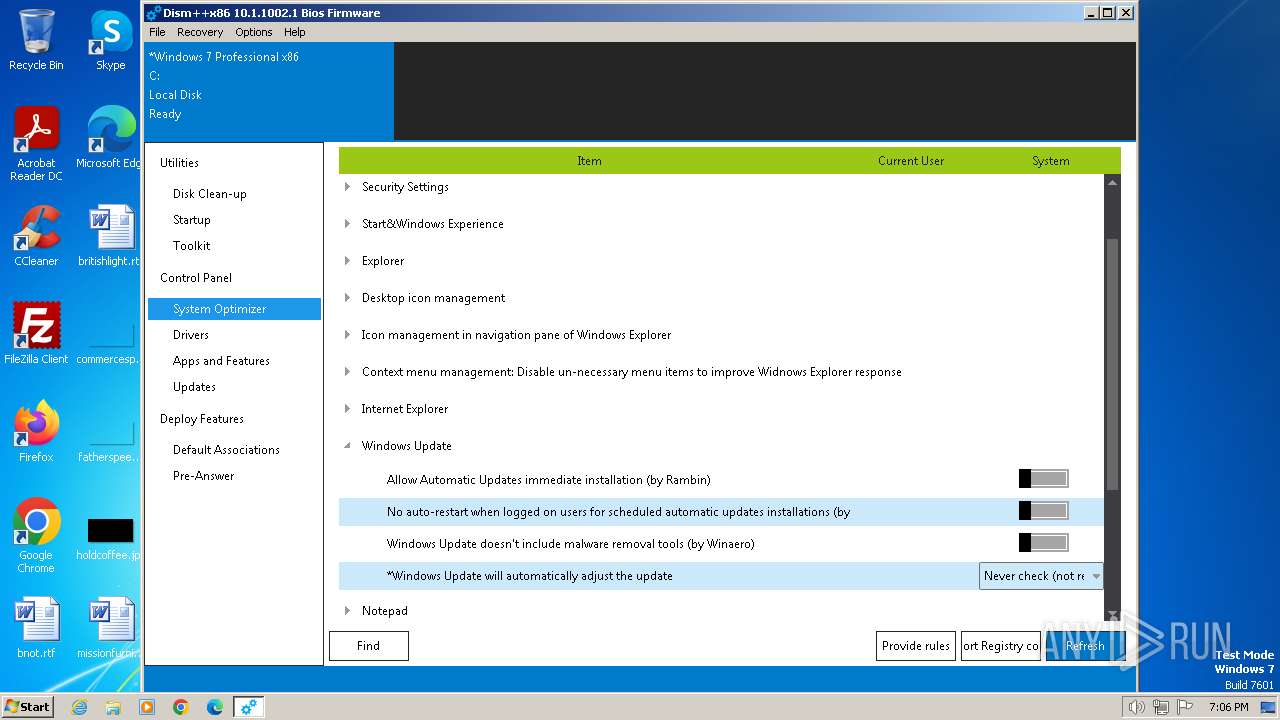
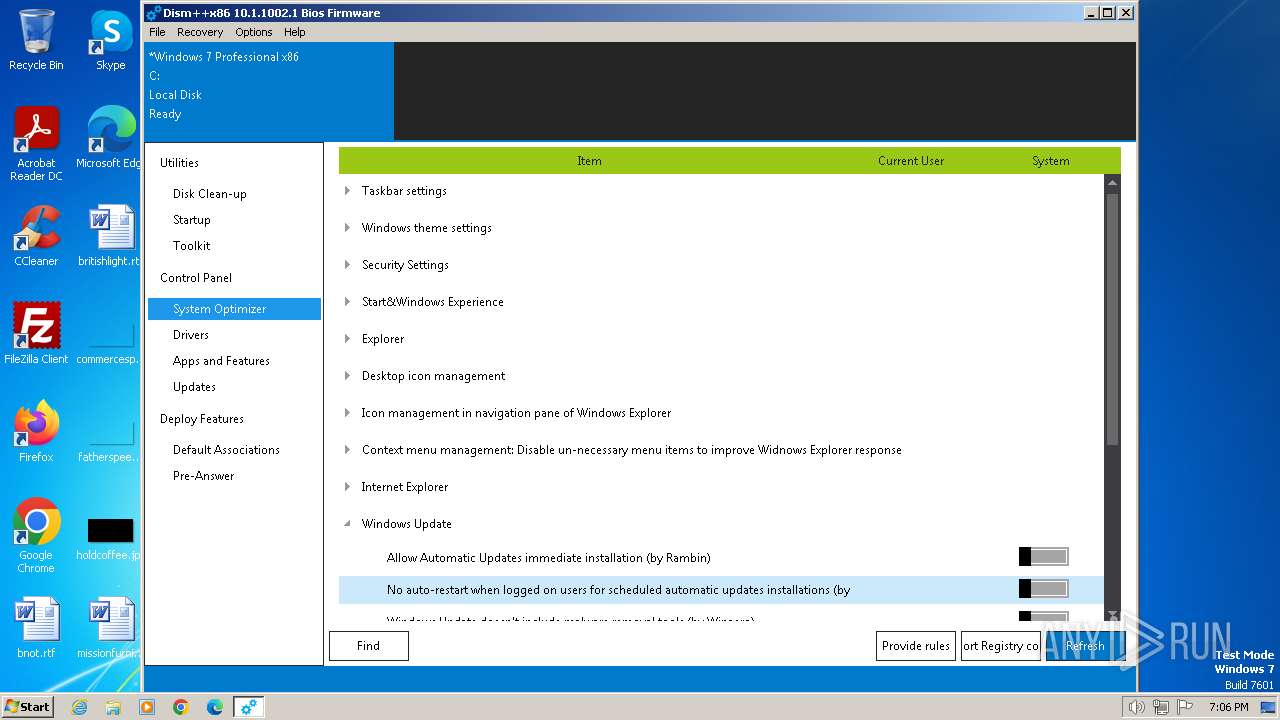
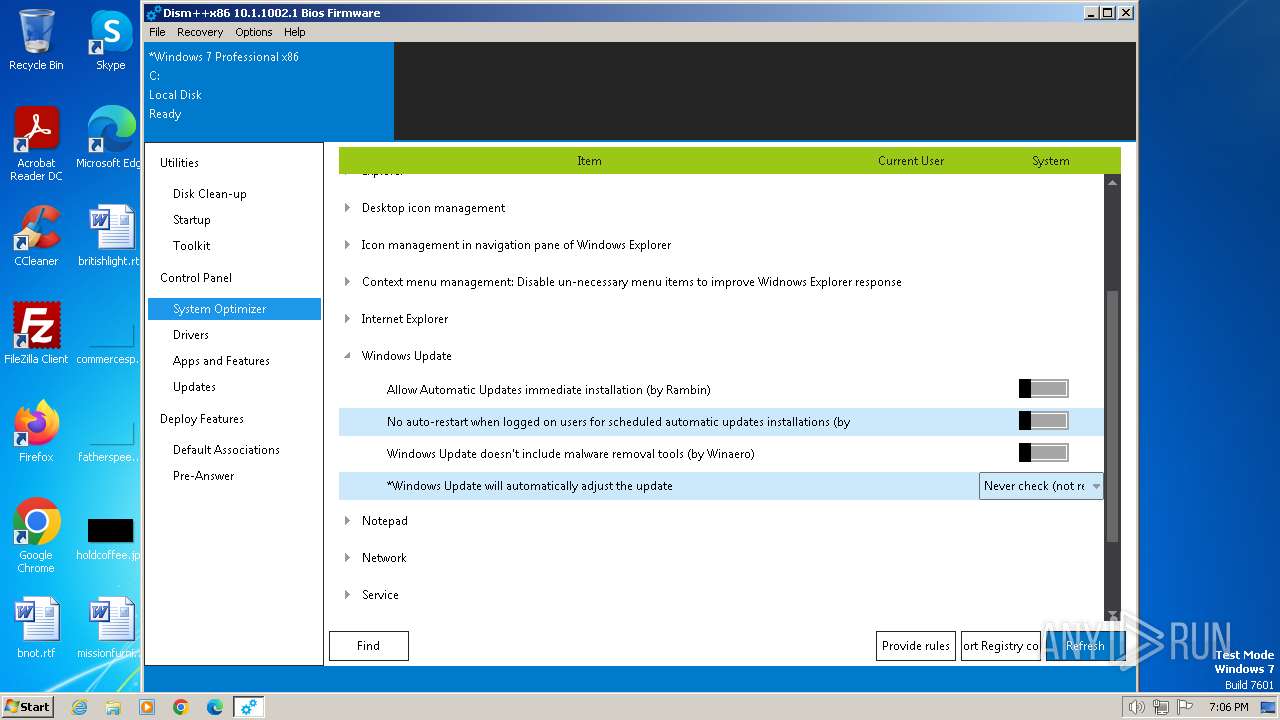
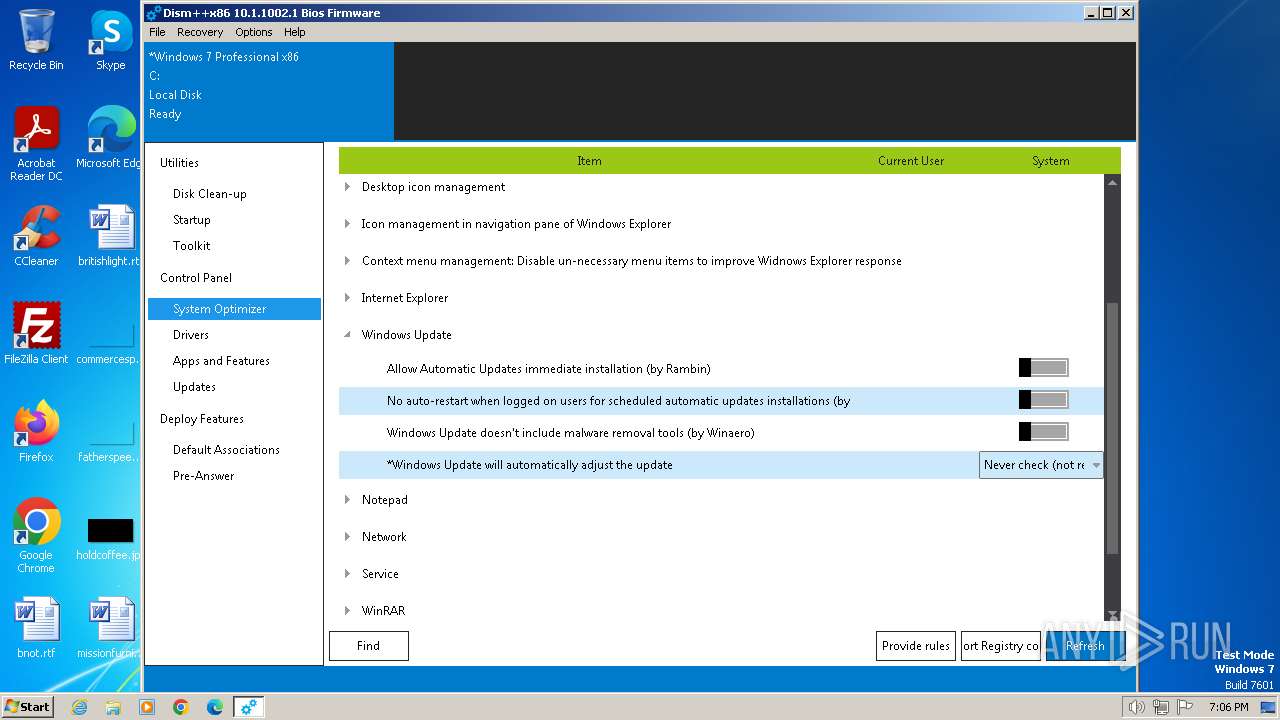
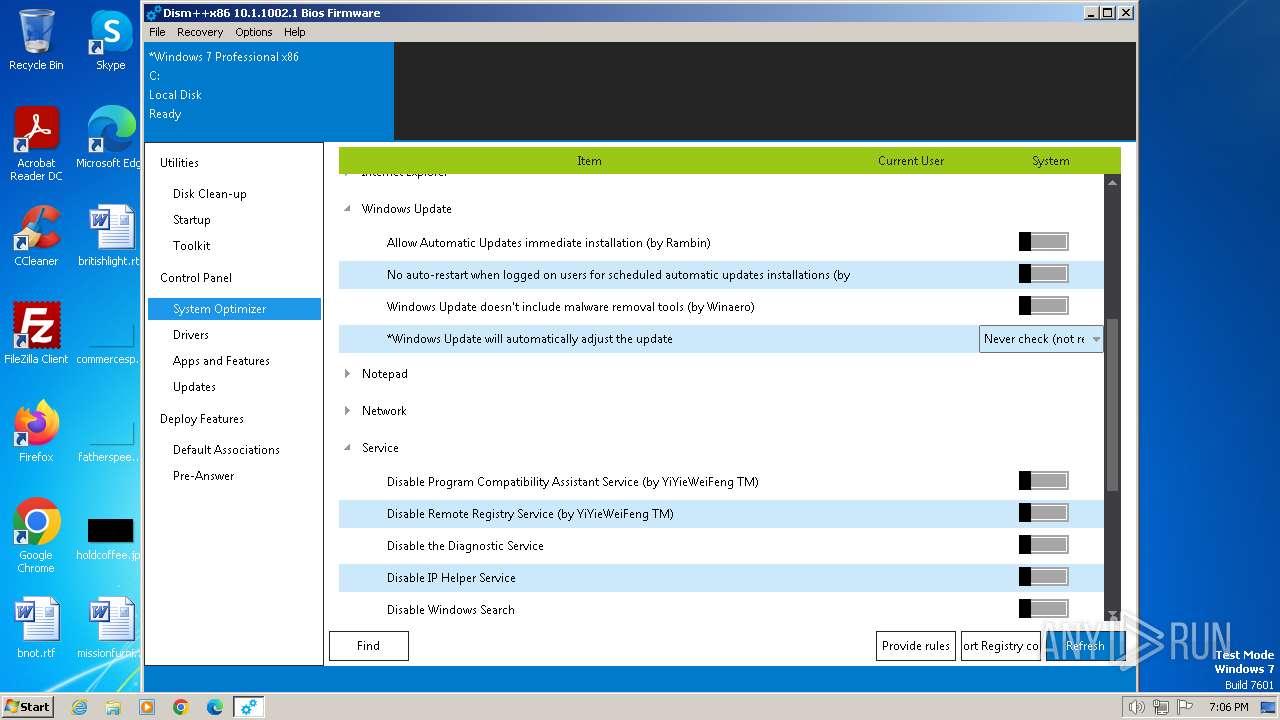
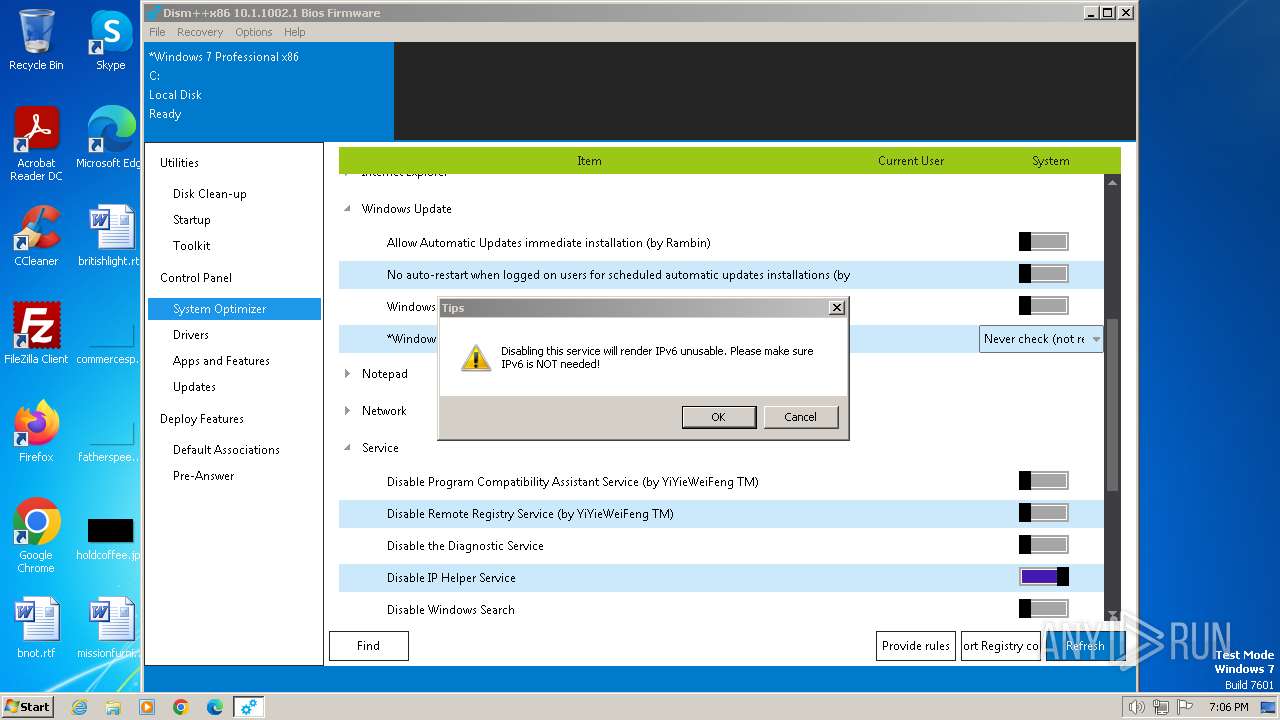
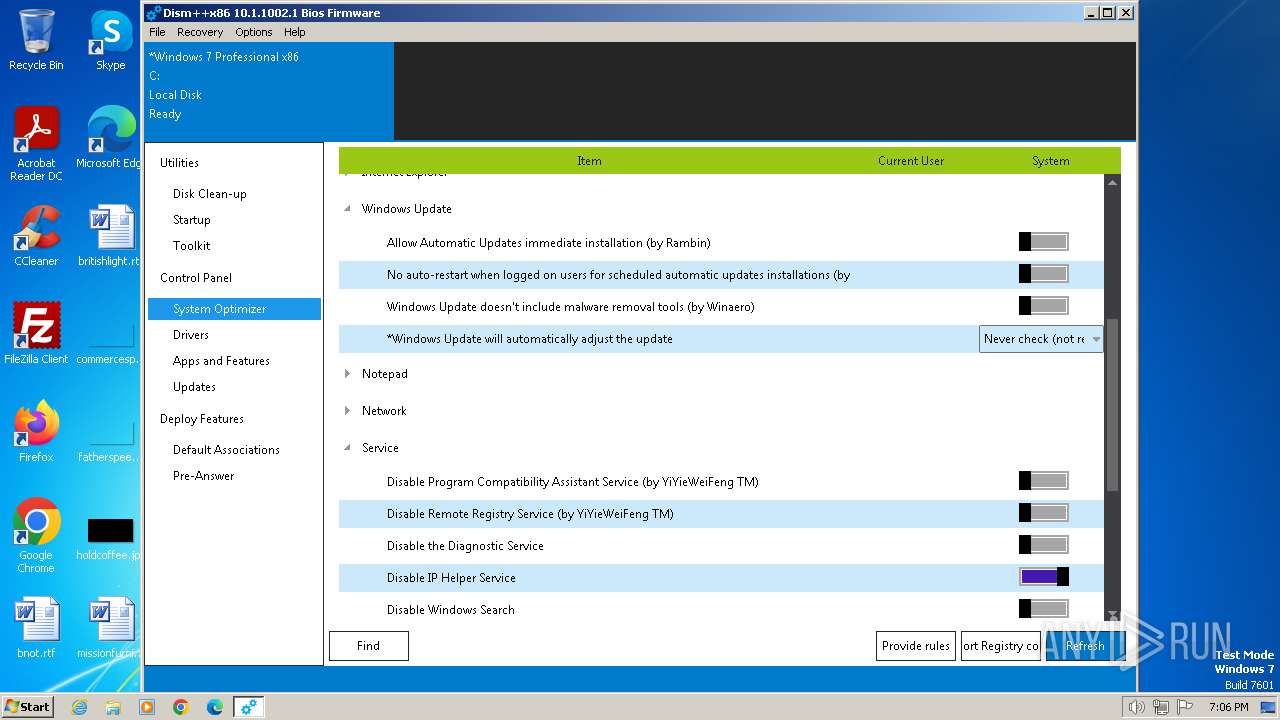
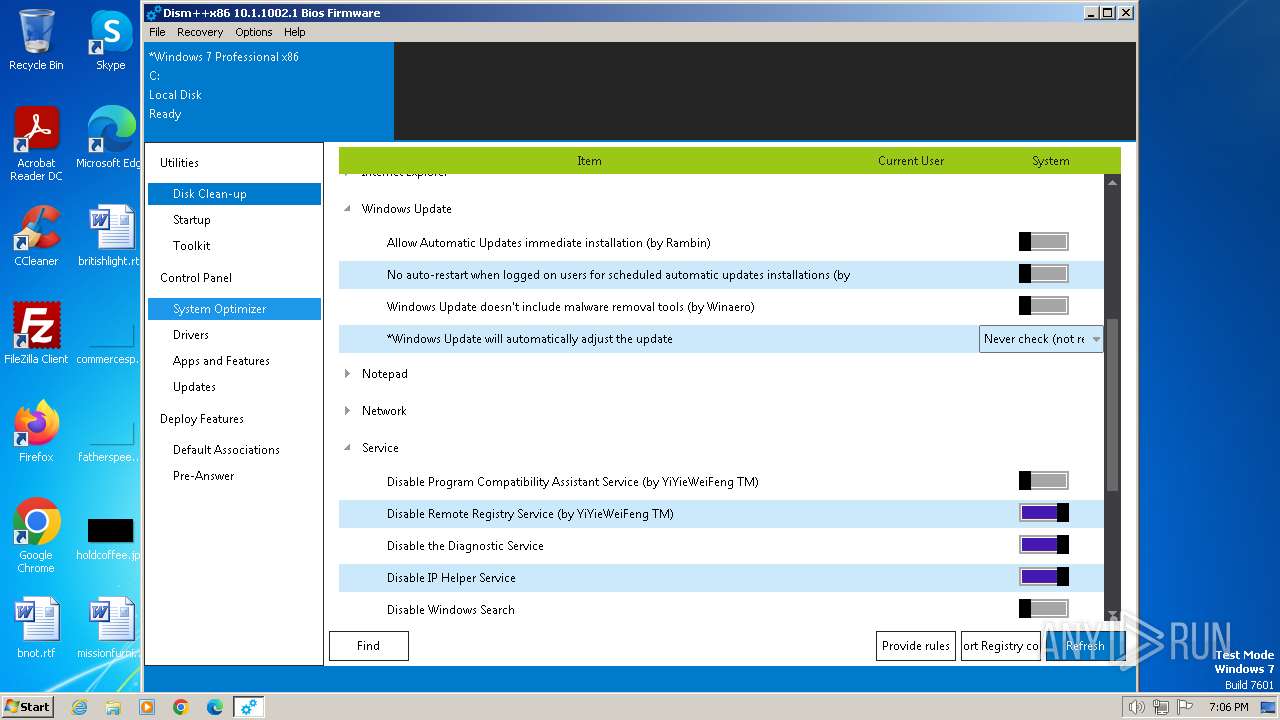
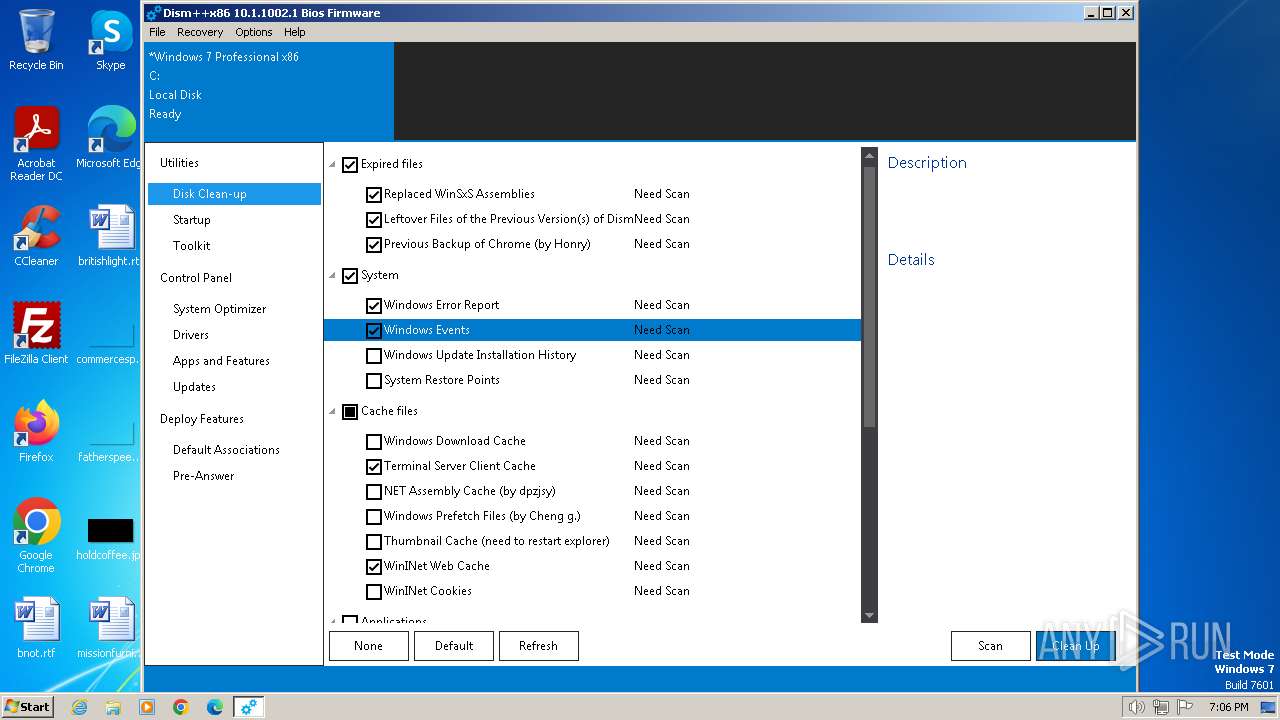
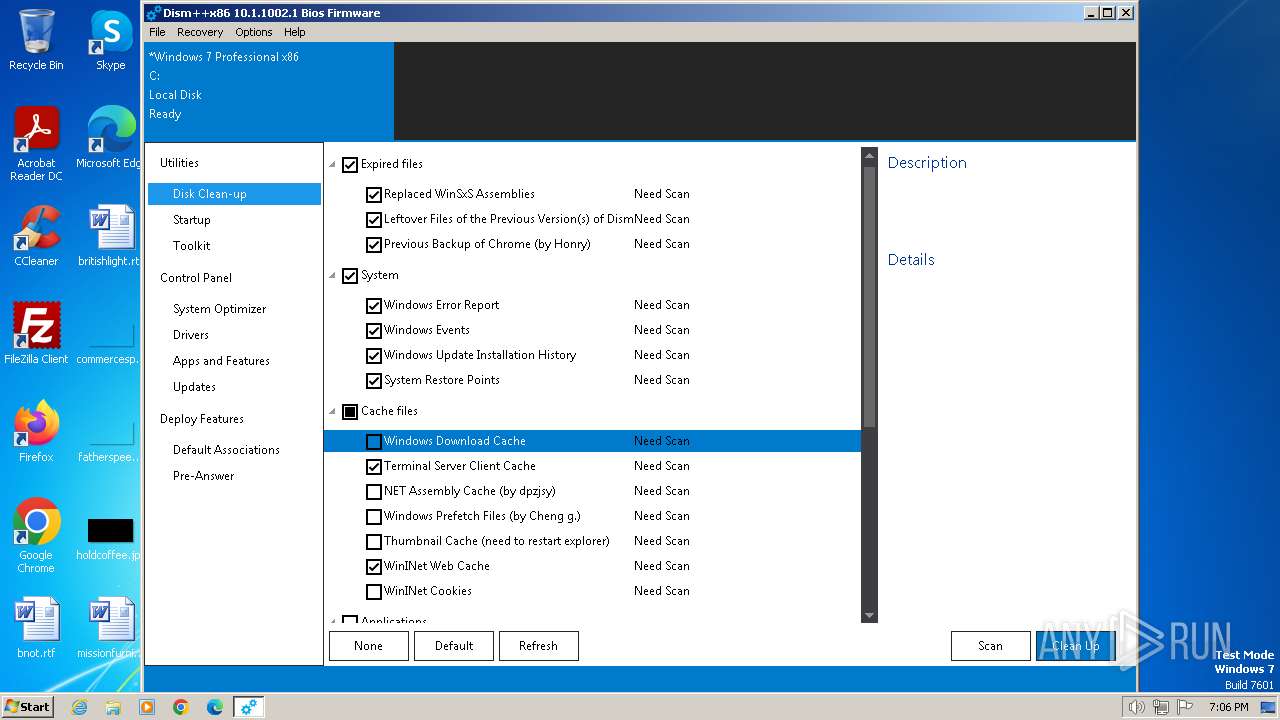
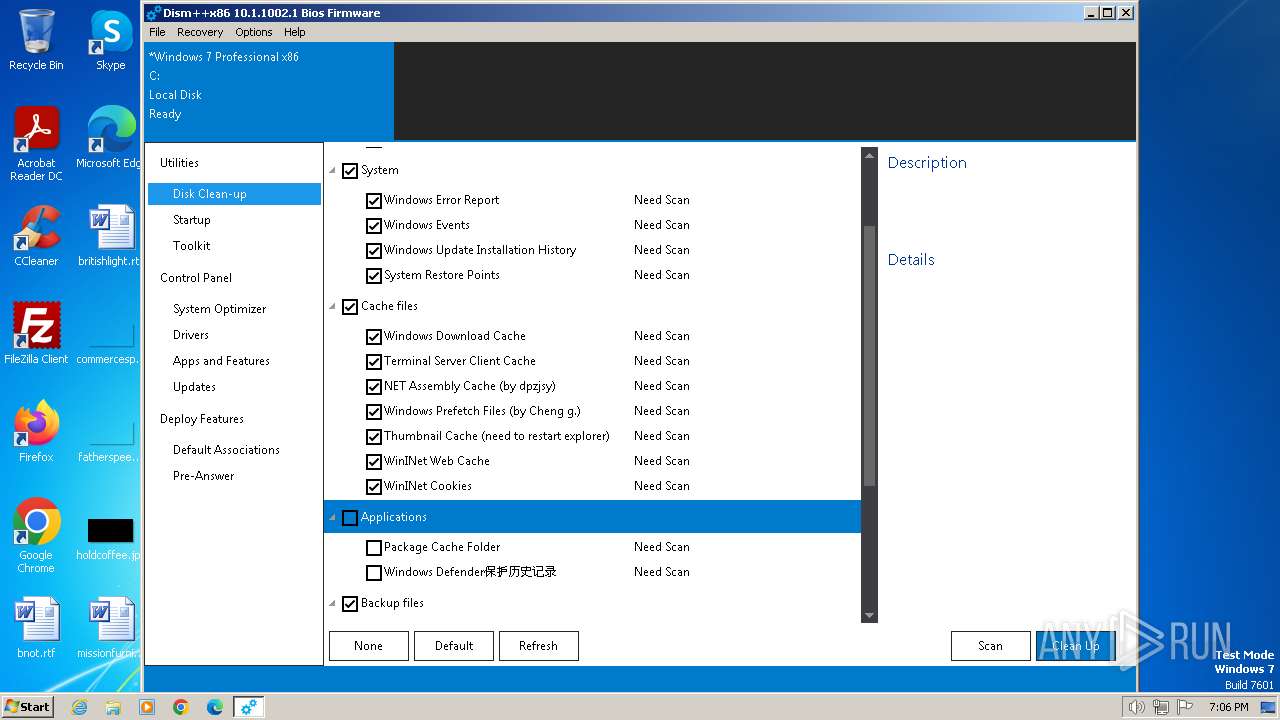
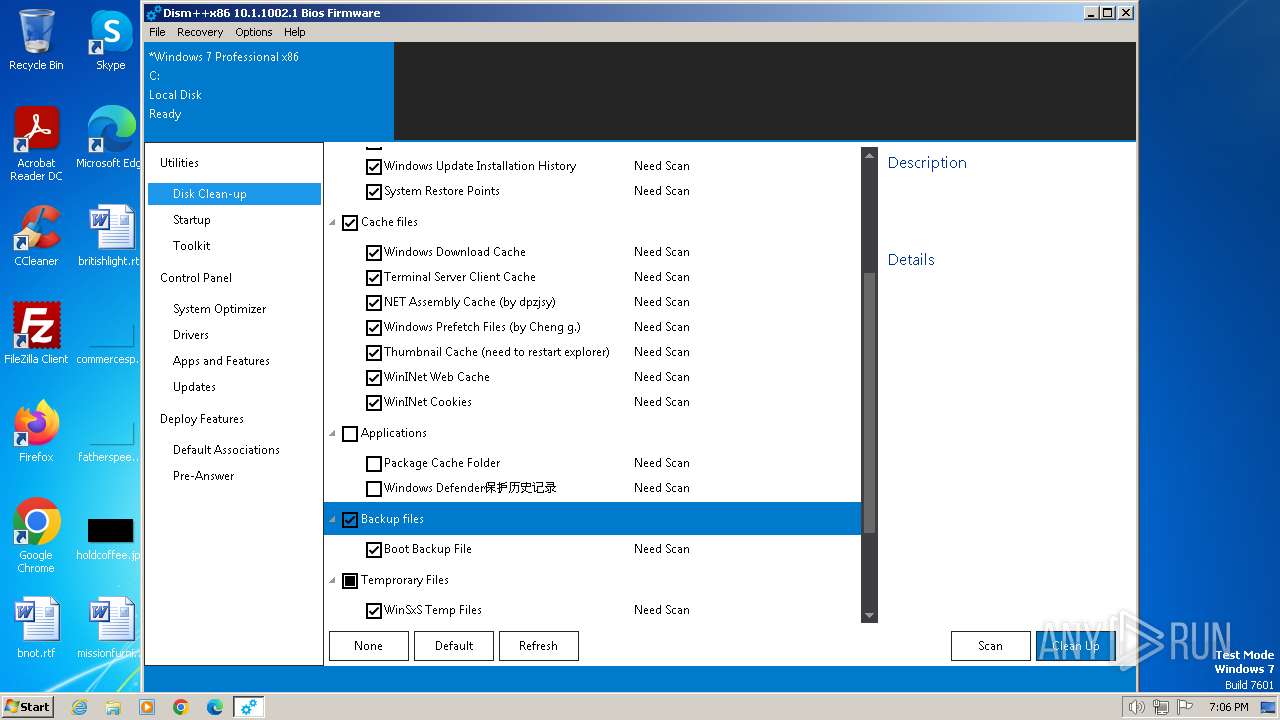
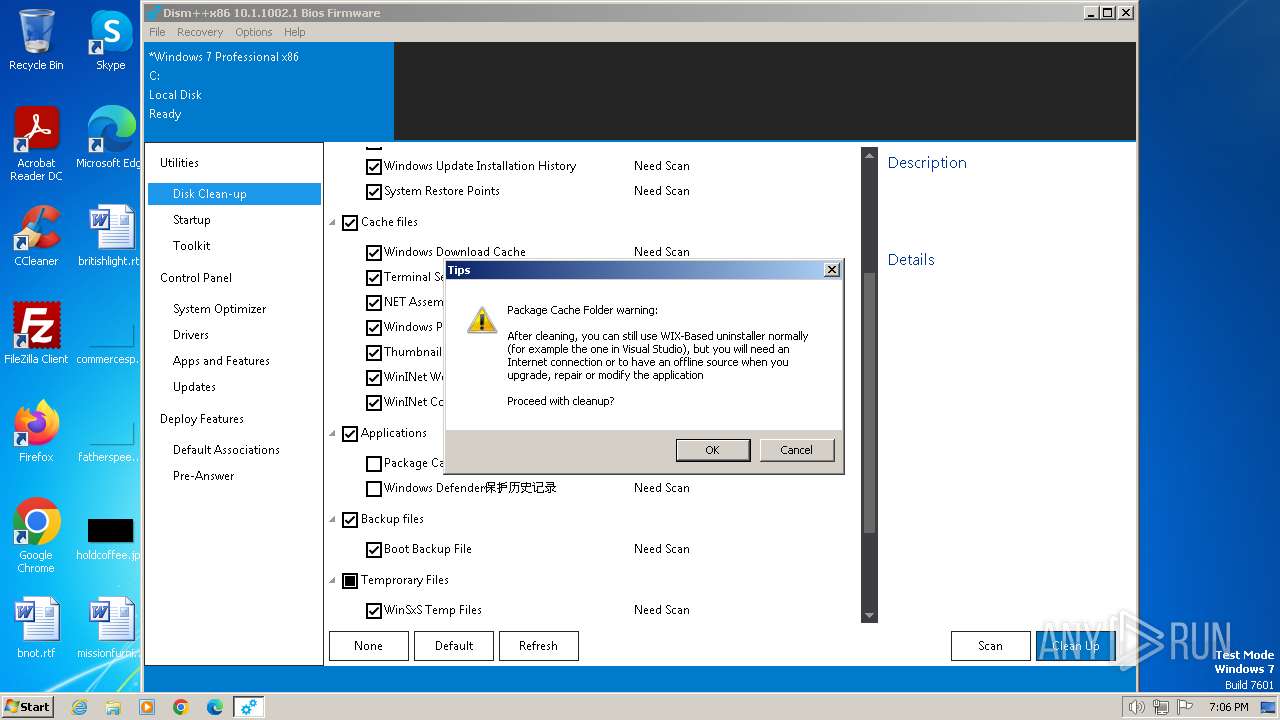
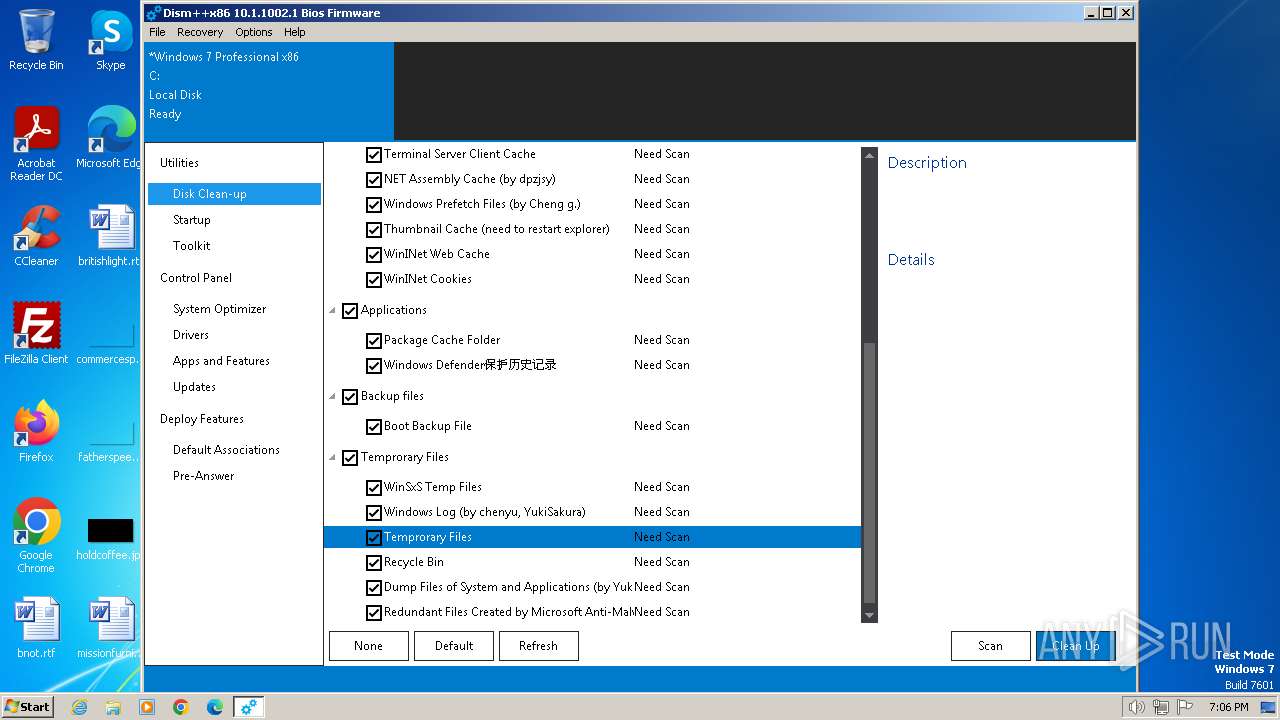
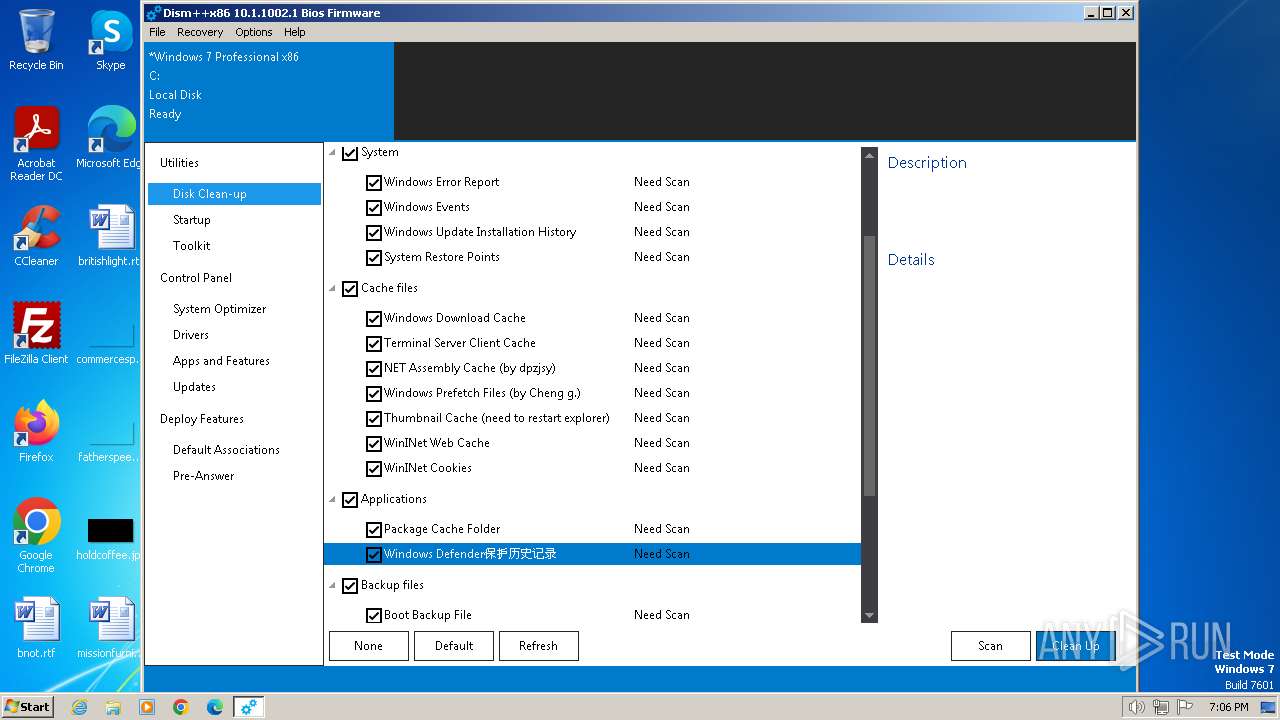
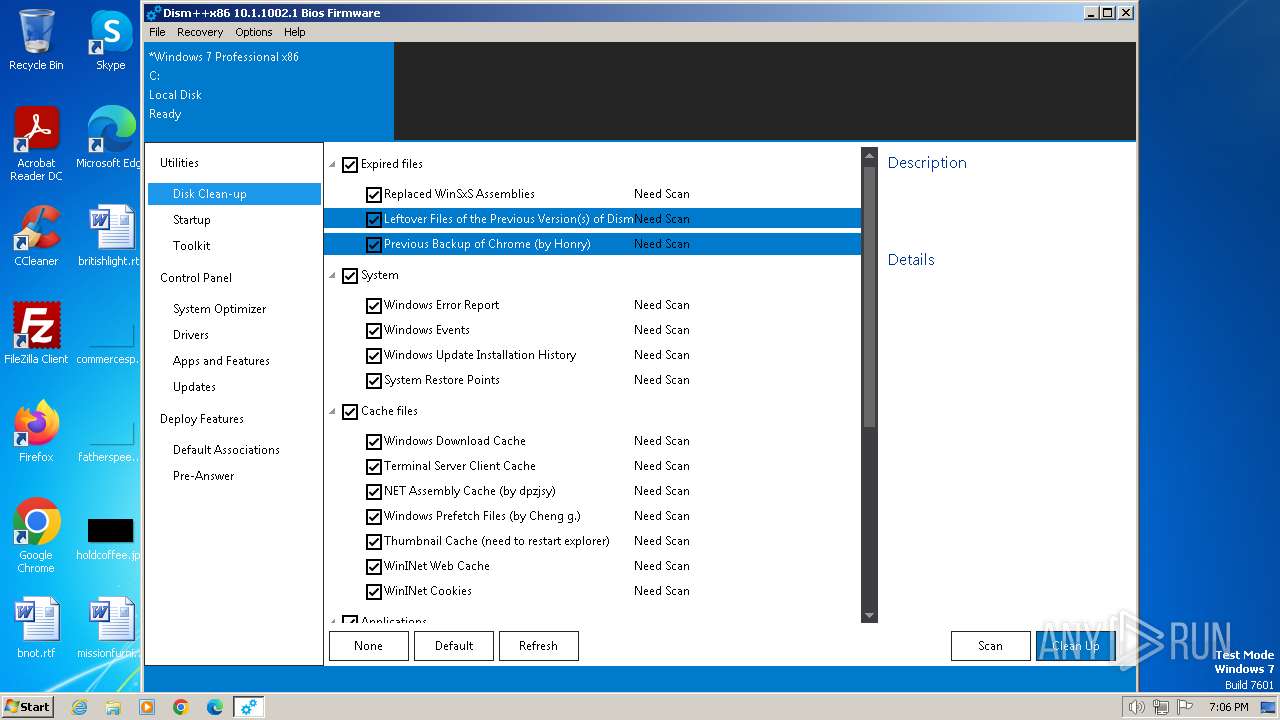
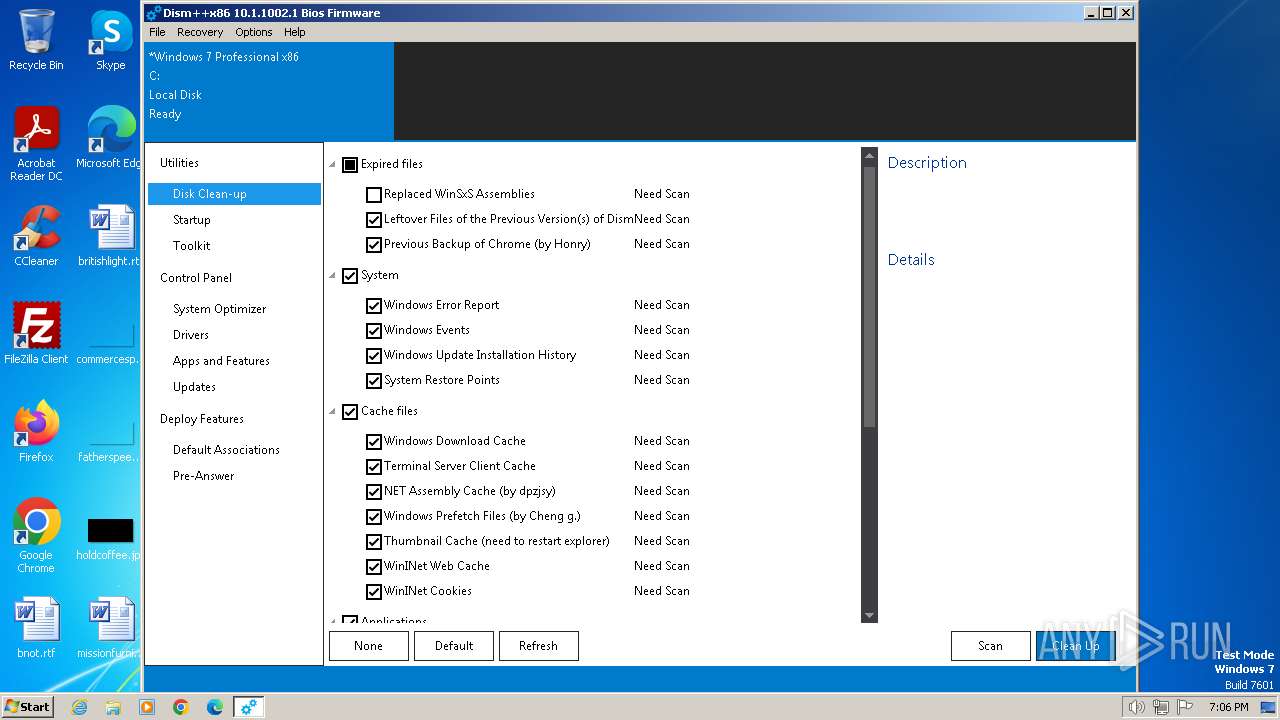
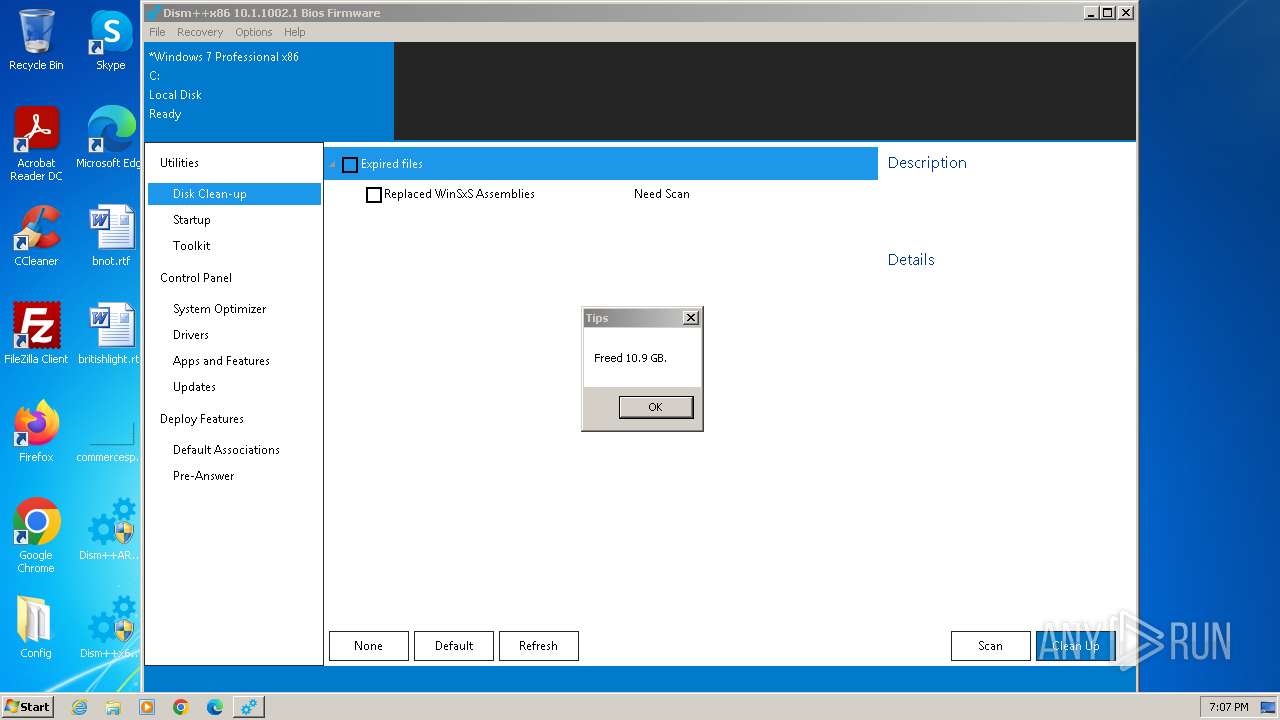
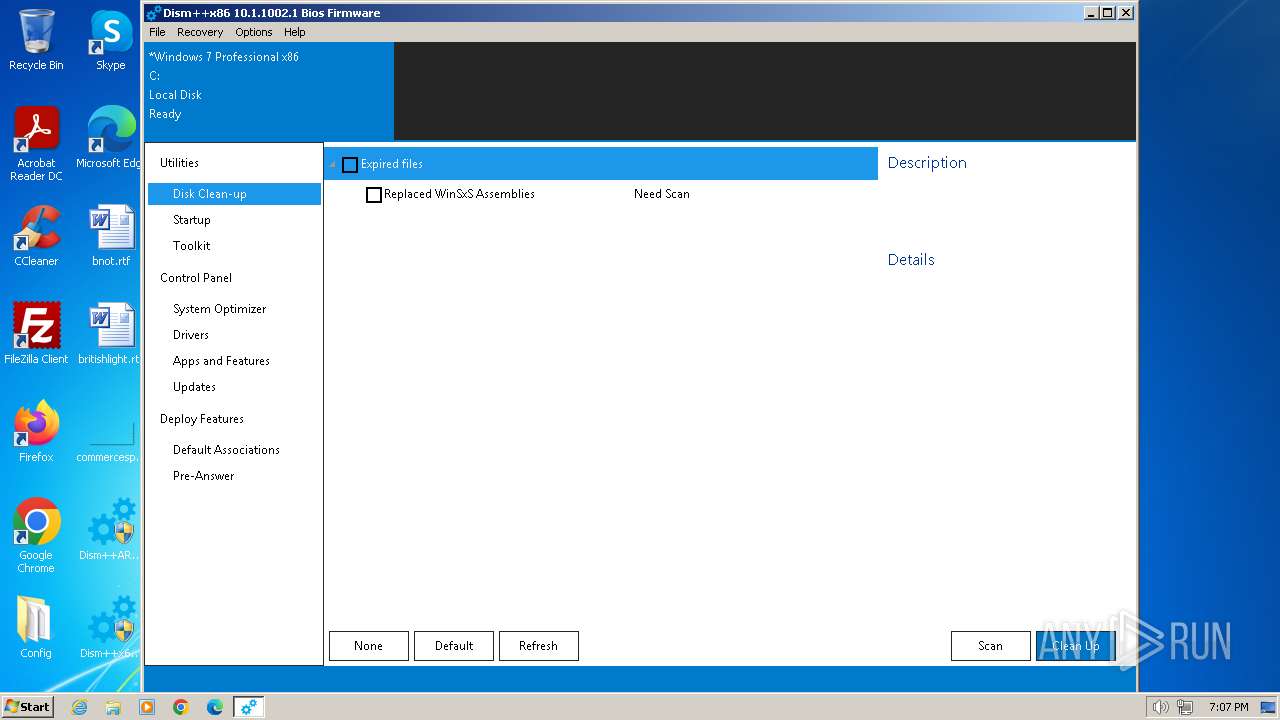
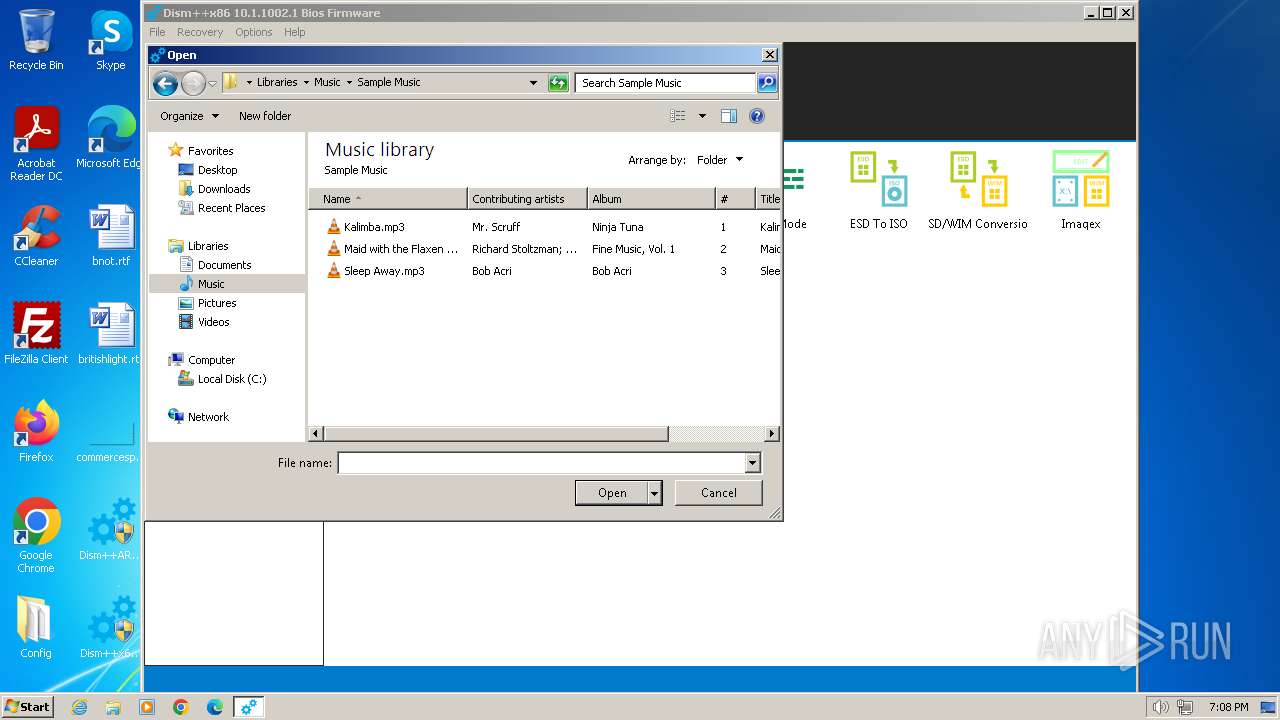
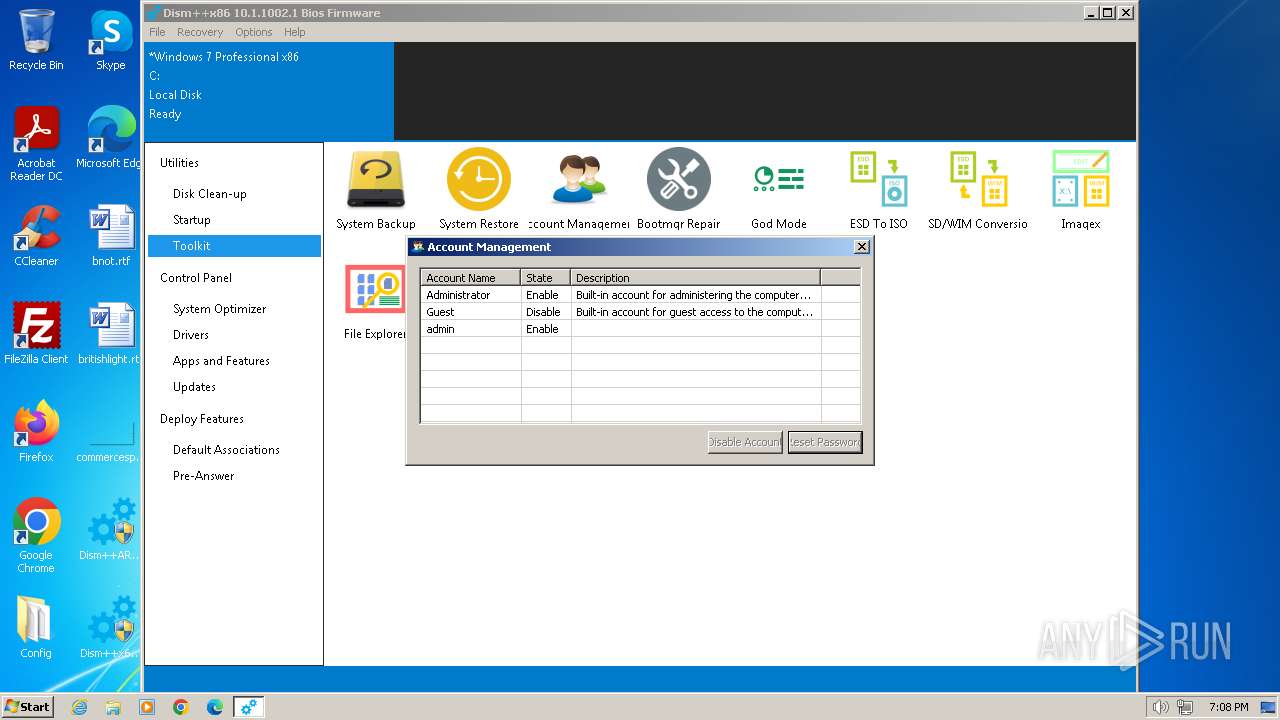
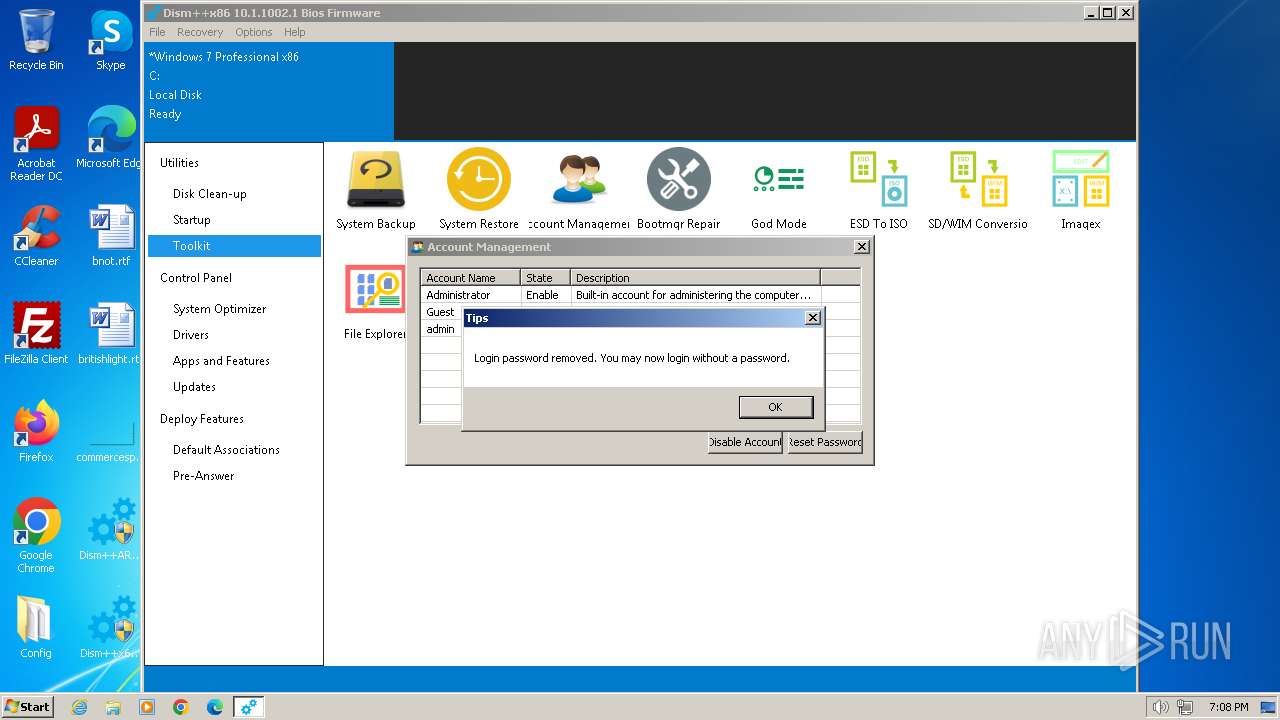
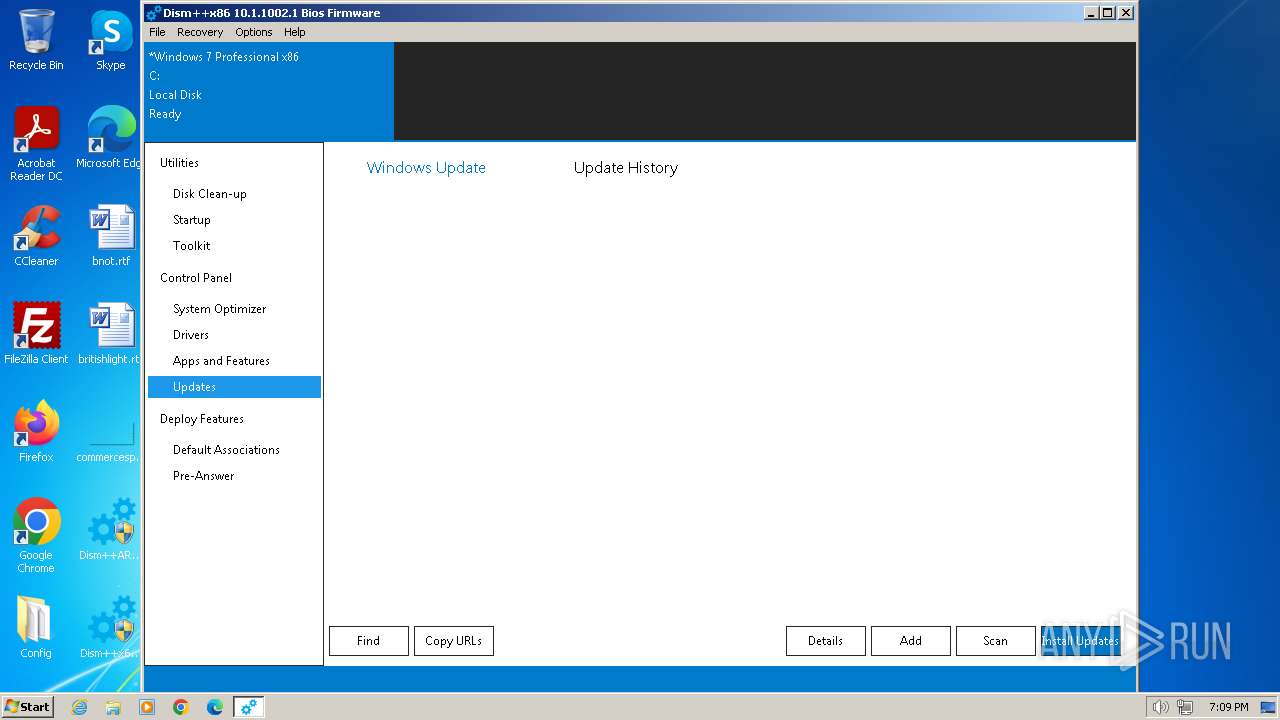
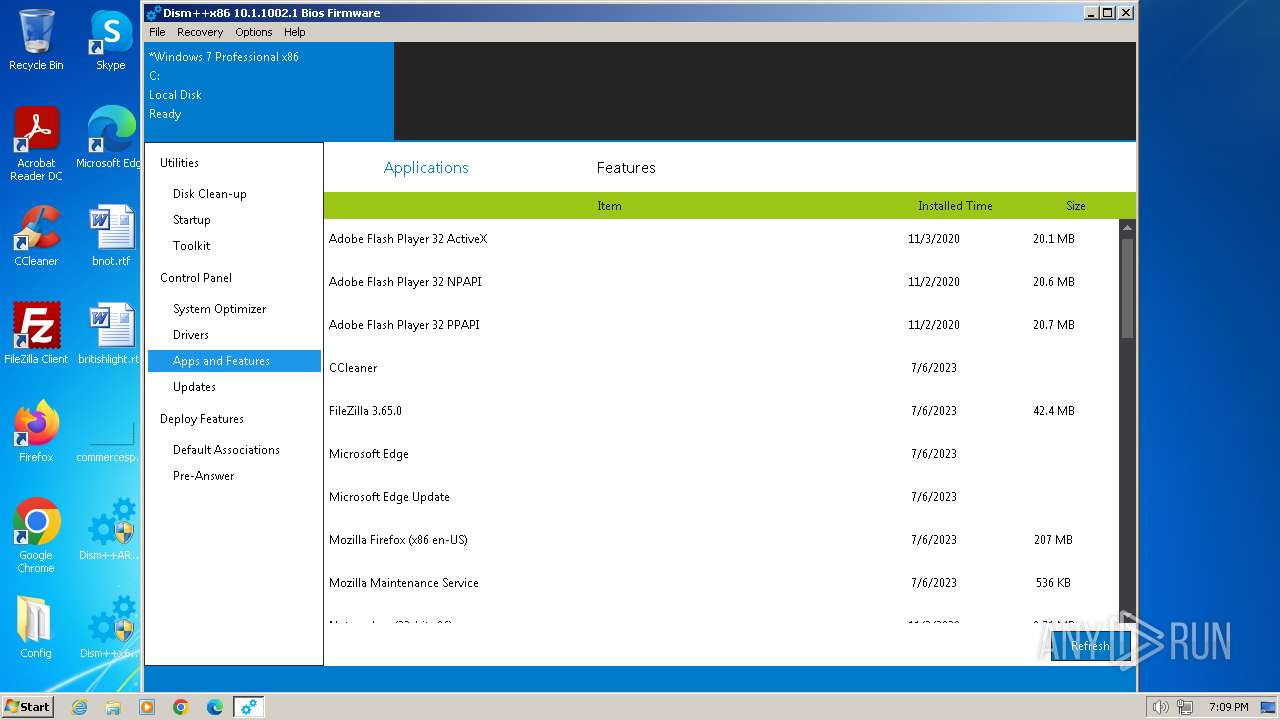
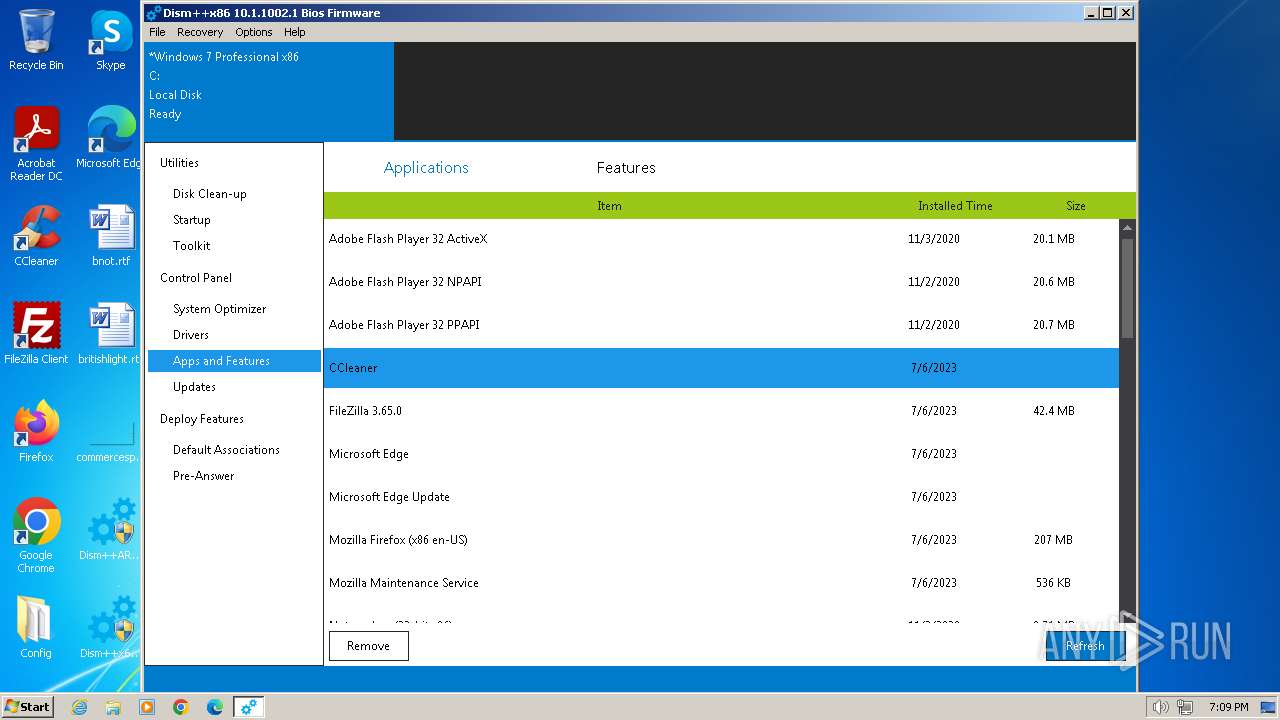
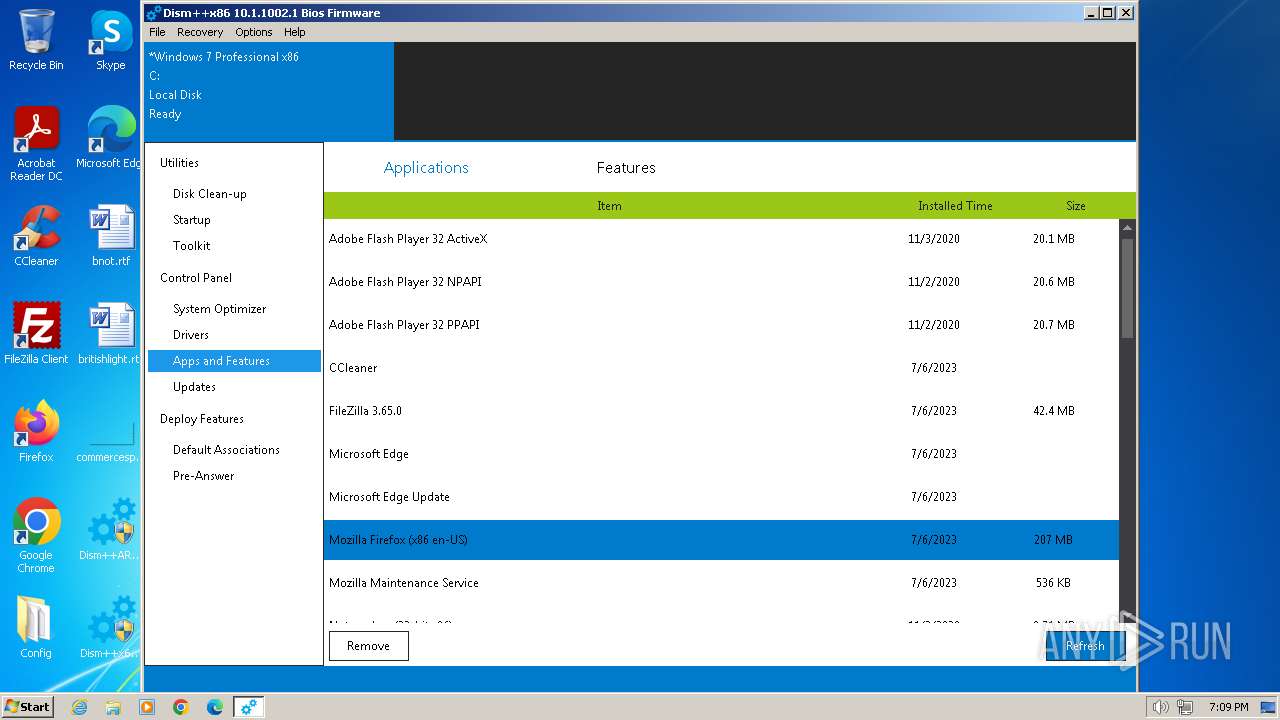
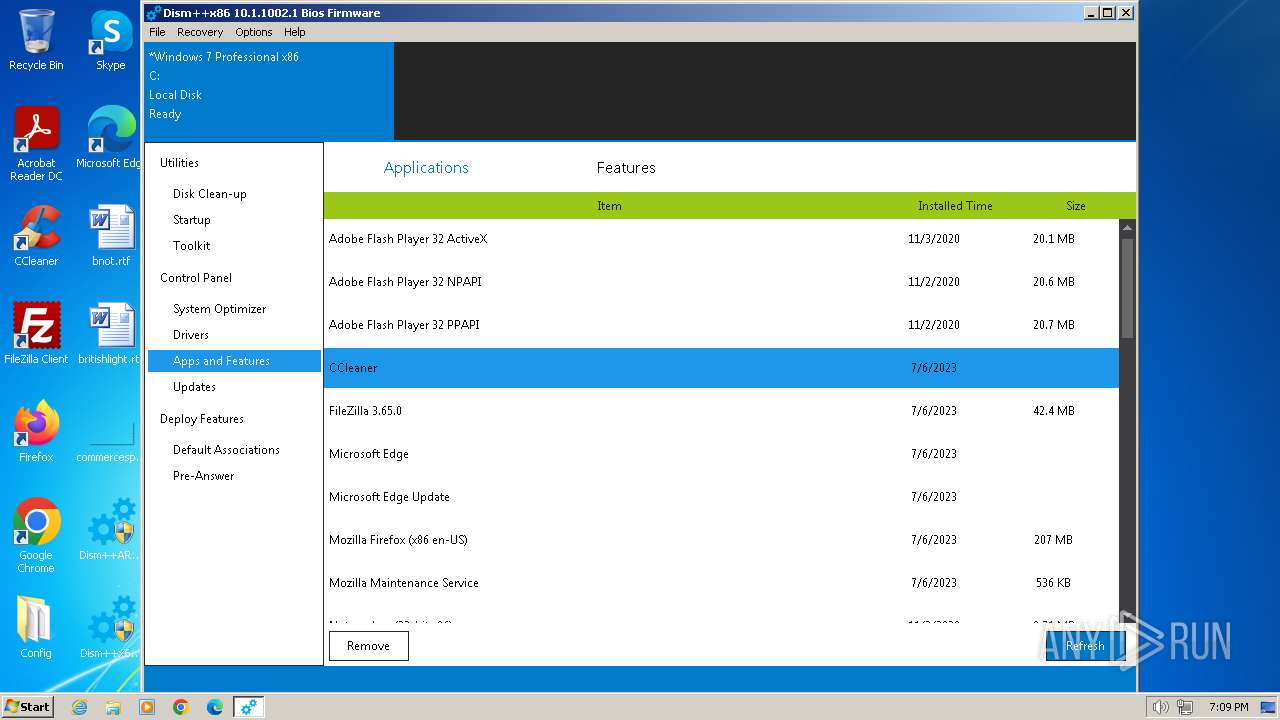
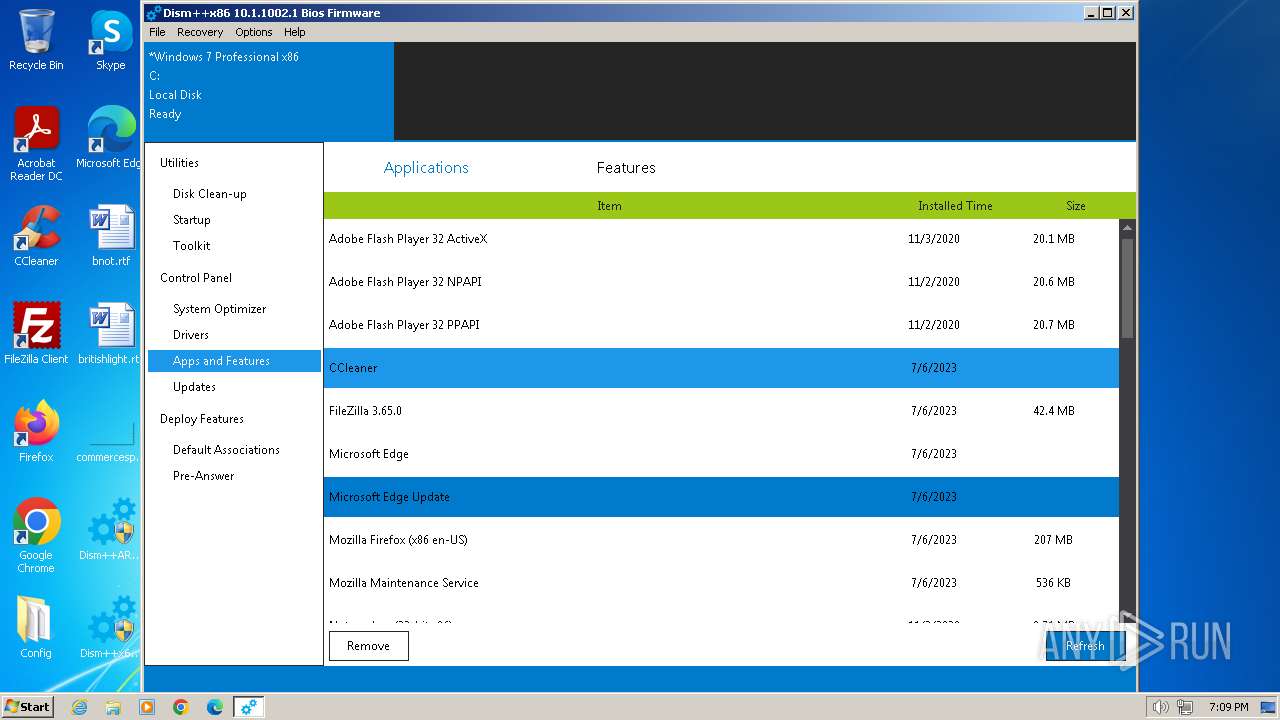
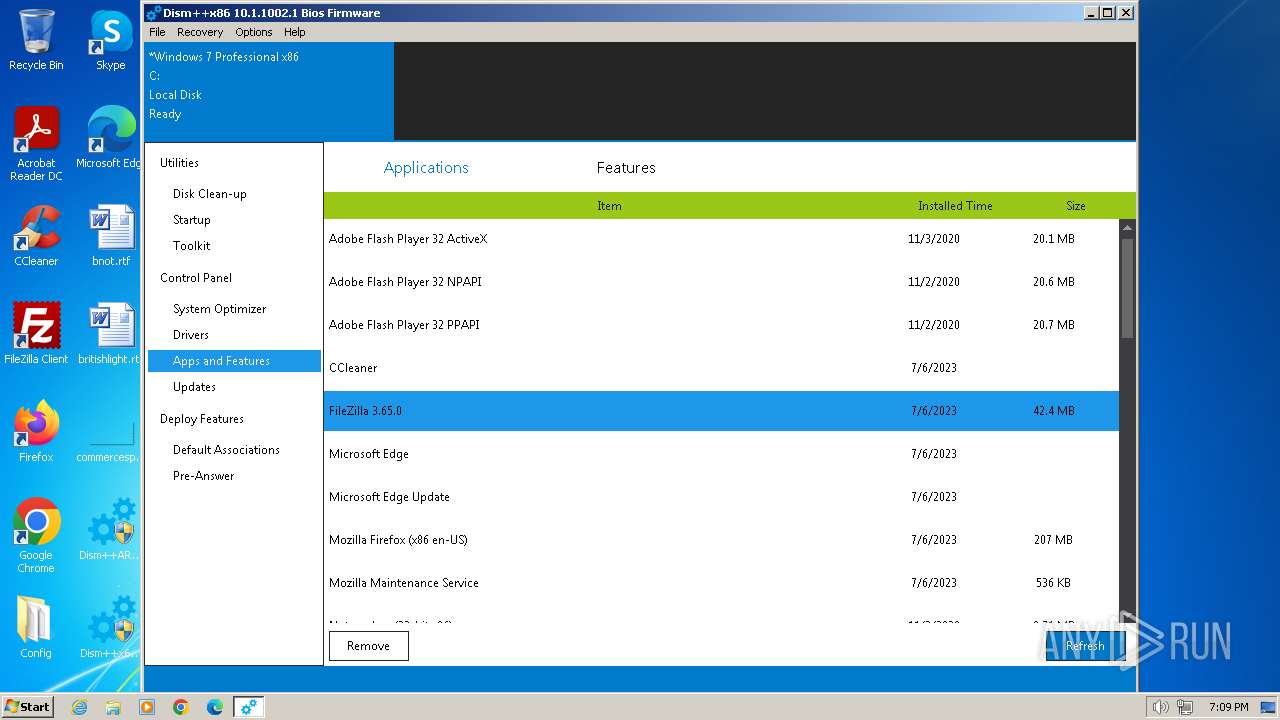
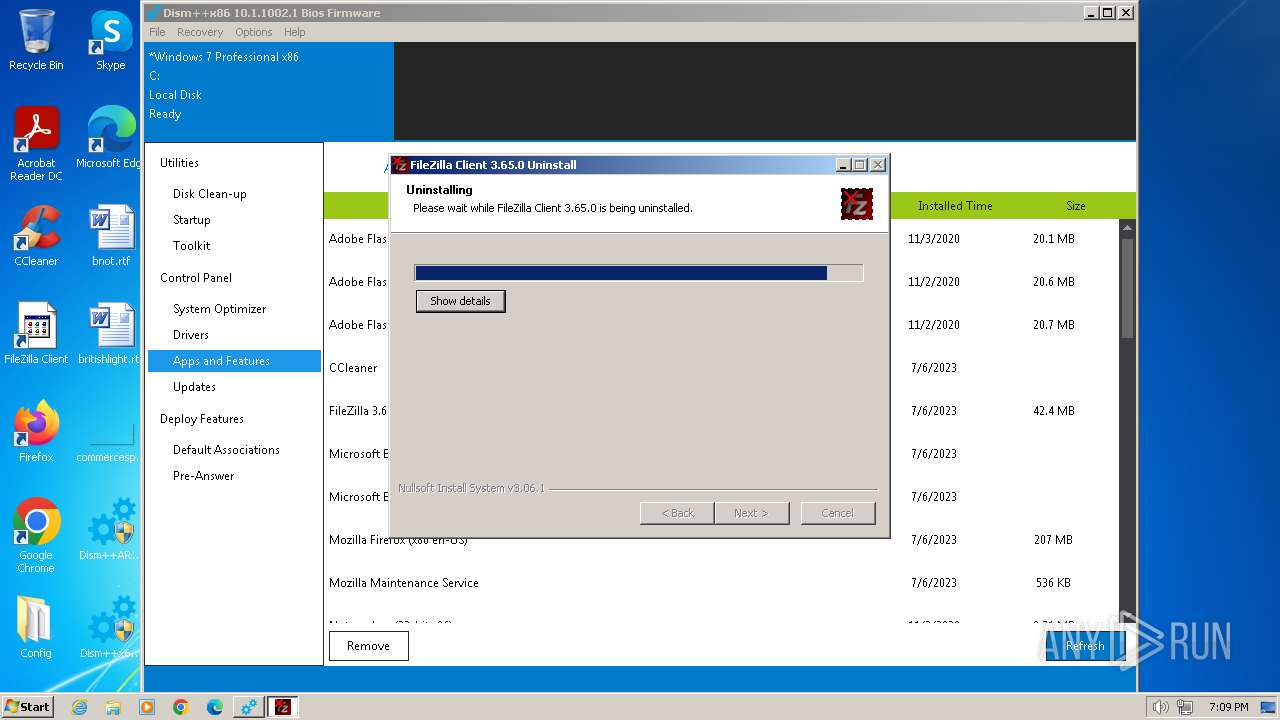
Searches for installed software
- Dism++x86.exe (PID: 2944)
- dllhost.exe (PID: 4012)
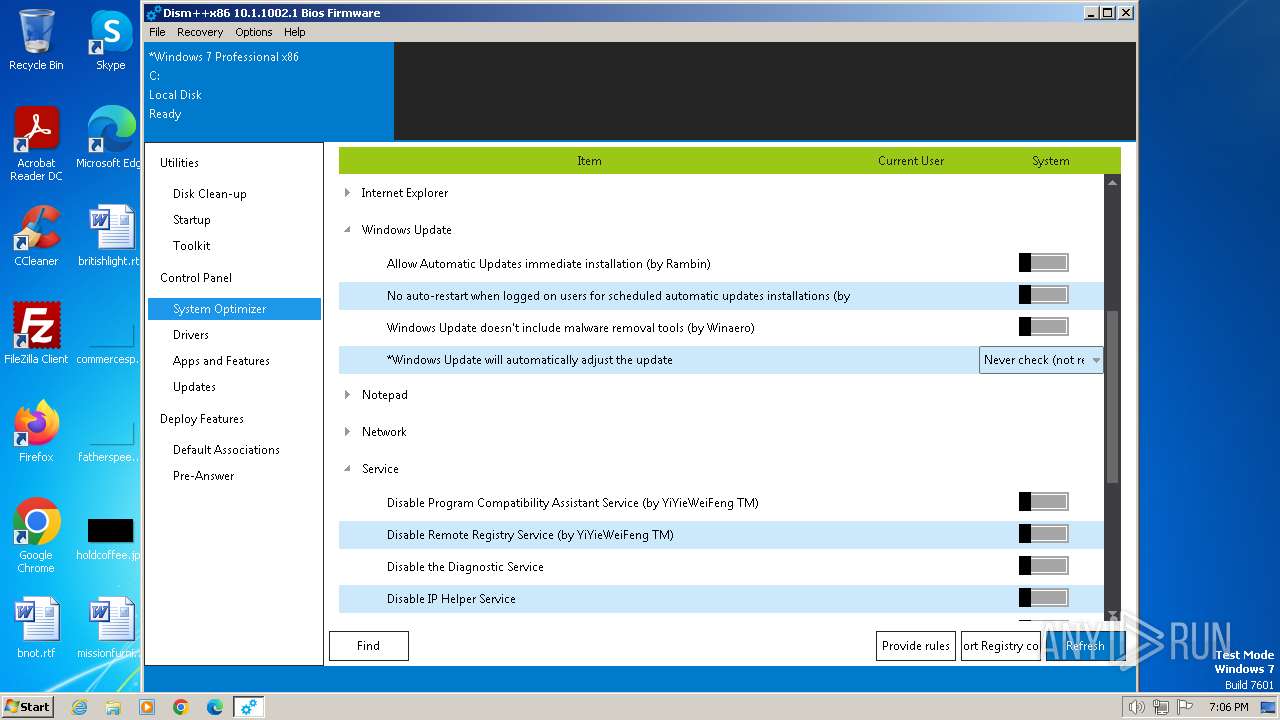
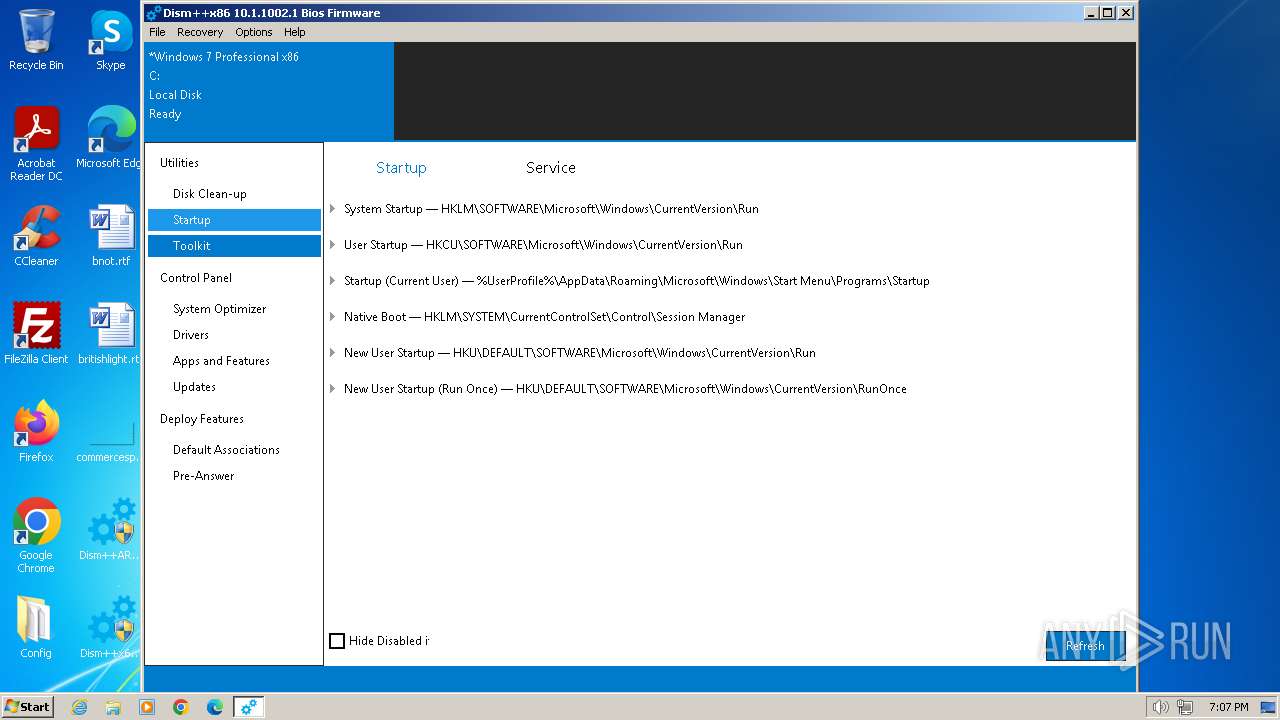
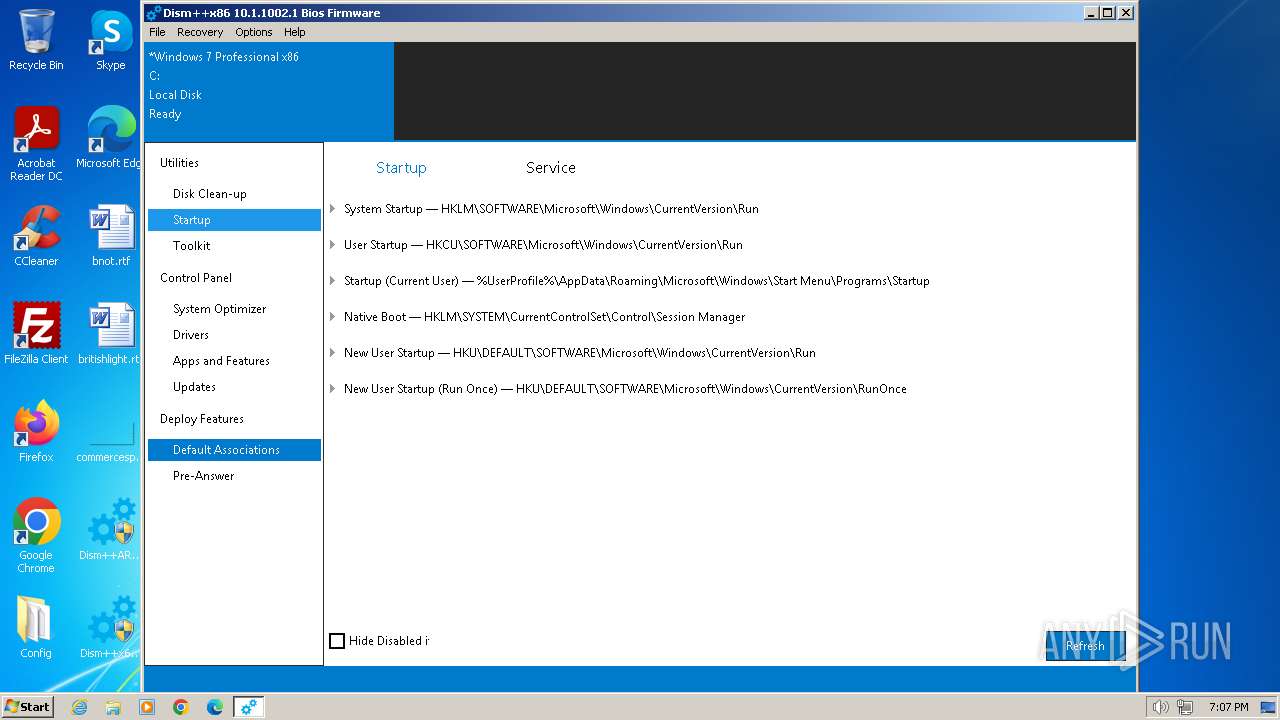
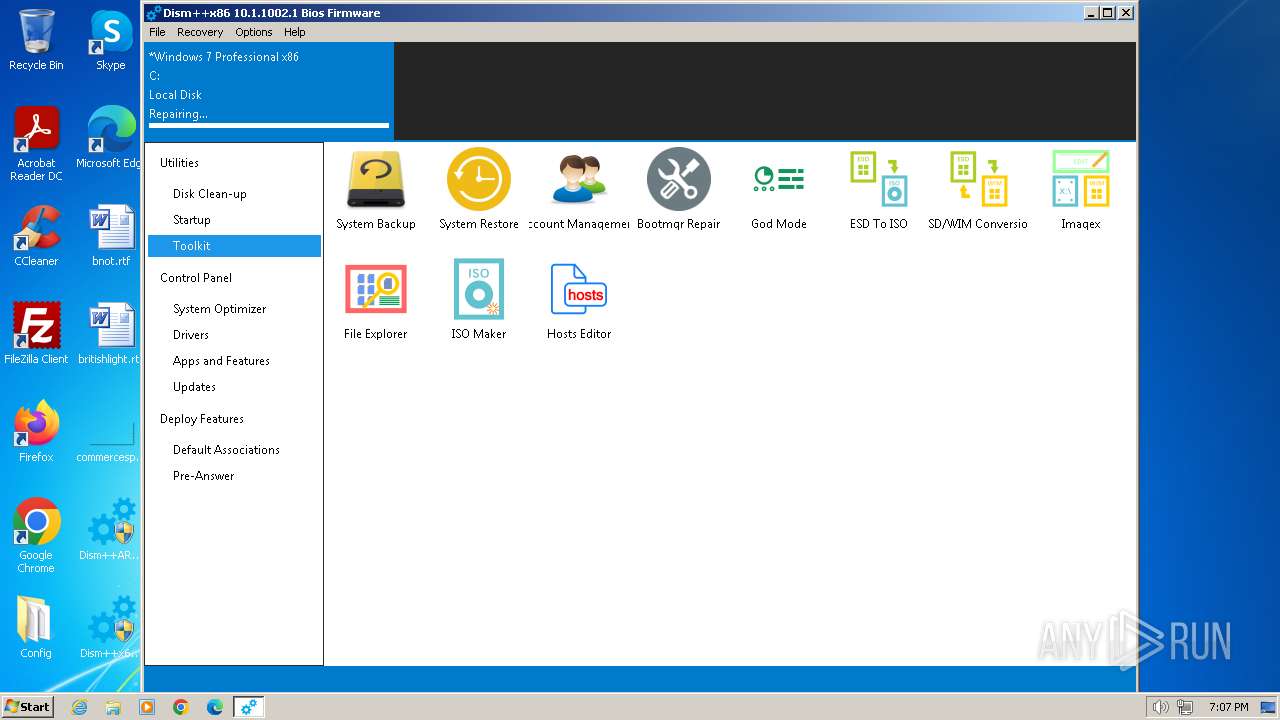
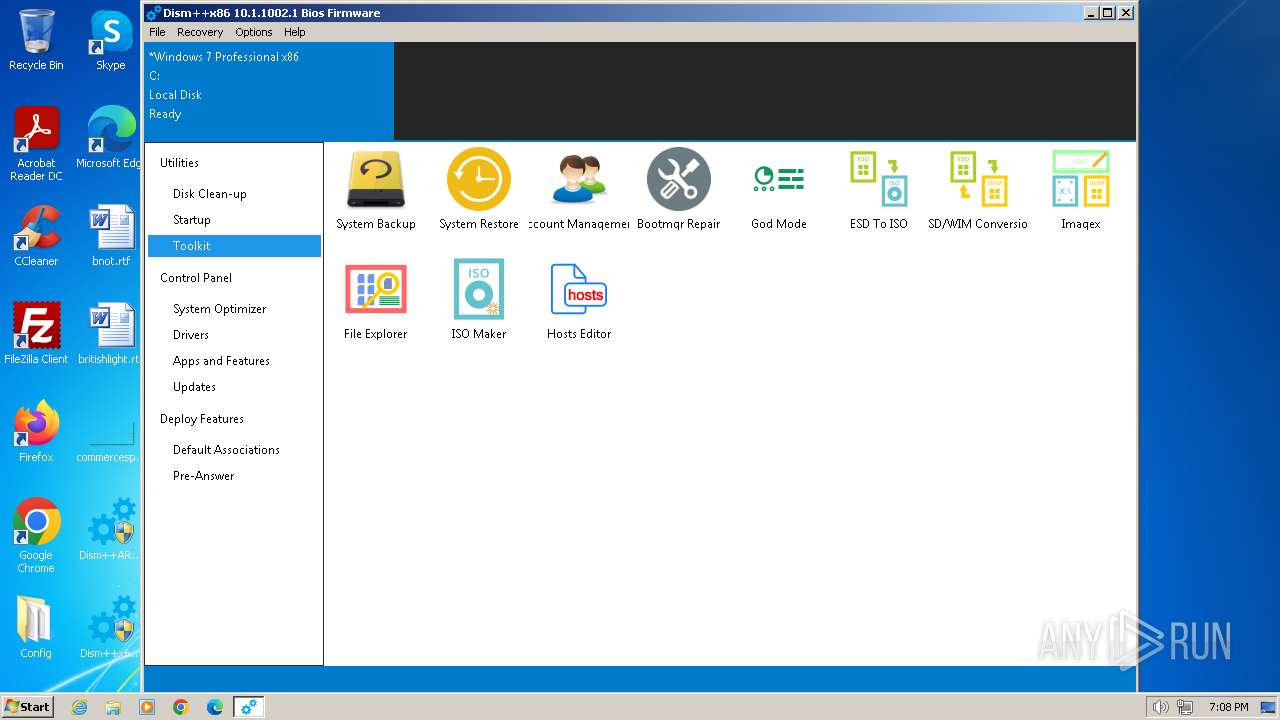
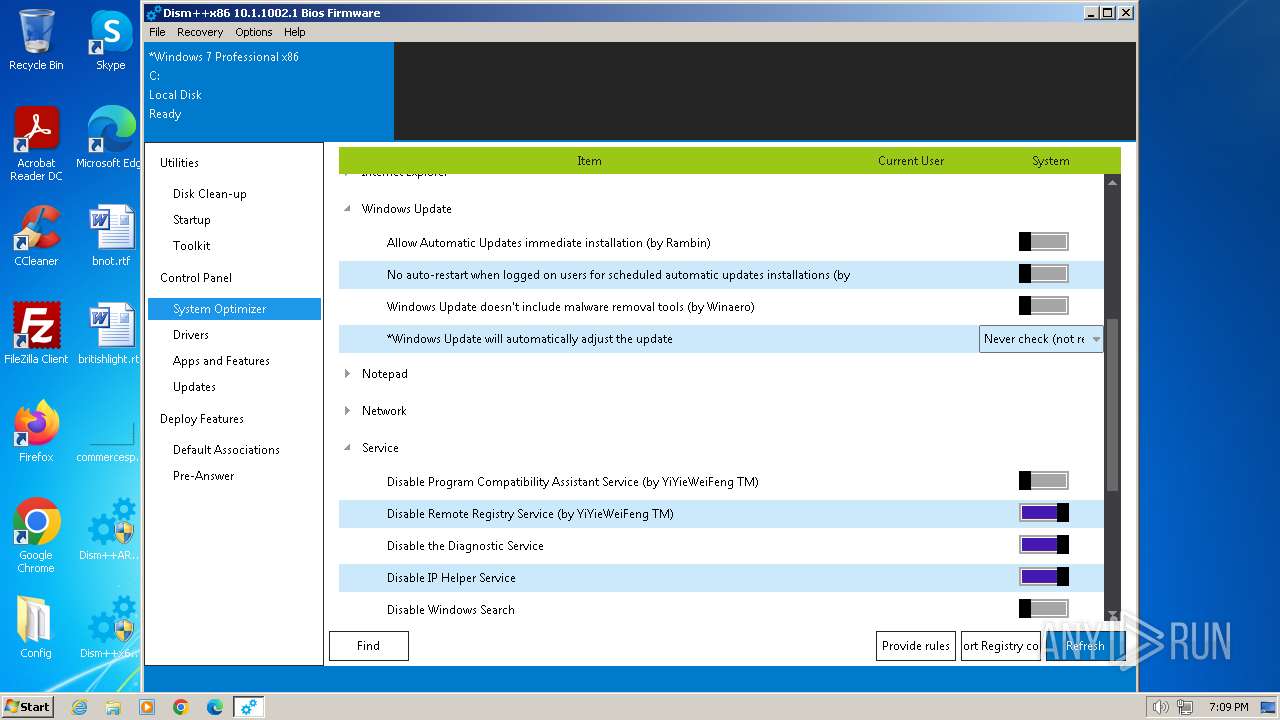
Creates or modifies Windows services
- Dism++x86.exe (PID: 2944)
Executes as Windows Service
- VSSVC.exe (PID: 3788)
Reads the Internet Settings
- Dism++x86.exe (PID: 2944)
Detected use of alternative data streams (AltDS)
- Dism++x86.exe (PID: 2944)
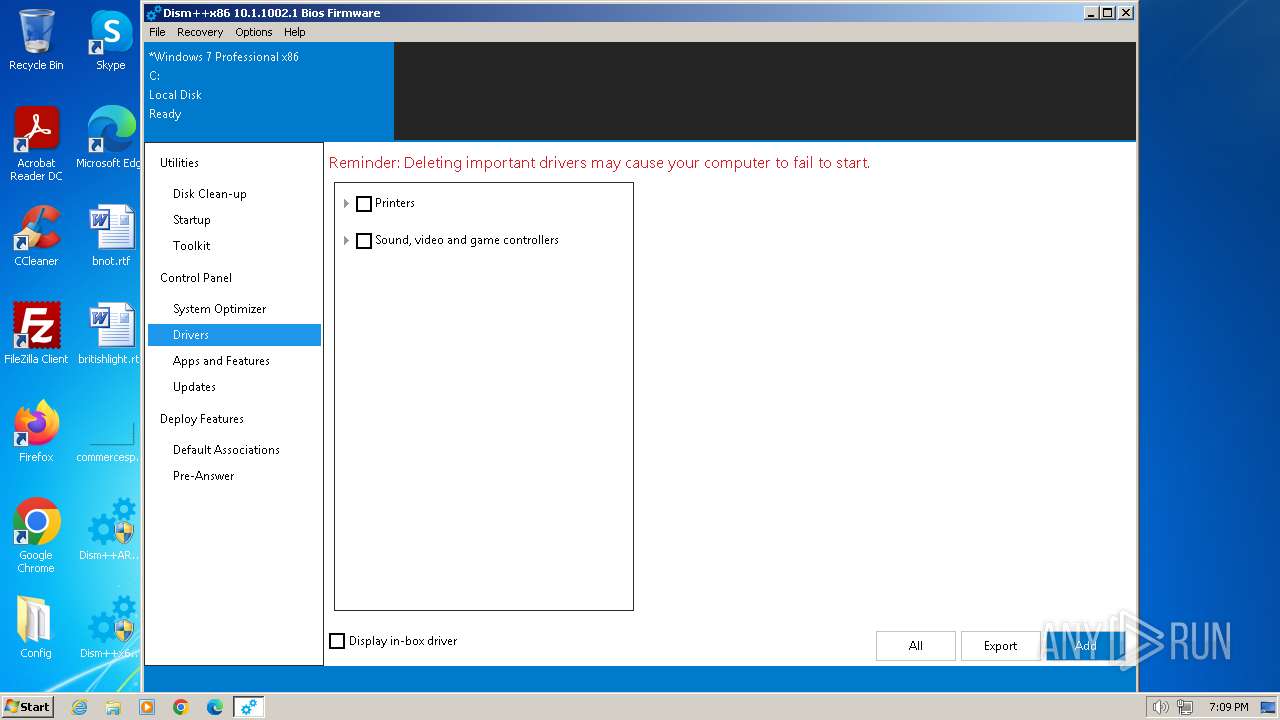
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 1504)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1504)
- Un_A.exe (PID: 392)
Process drops legitimate windows executable
- WinRAR.exe (PID: 1504)
- bcdboot.exe (PID: 1808)
Starts itself from another location
- uninstall.exe (PID: 1316)
Write to the desktop.ini file (may be used to cloak folders)
- explorer.exe (PID: 3460)
Starts a Microsoft application from unusual location
- bcdboot.exe (PID: 1808)
Executable content was dropped or overwritten
- bcdboot.exe (PID: 1808)
- uninstall.exe (PID: 1316)
- Un_A.exe (PID: 392)
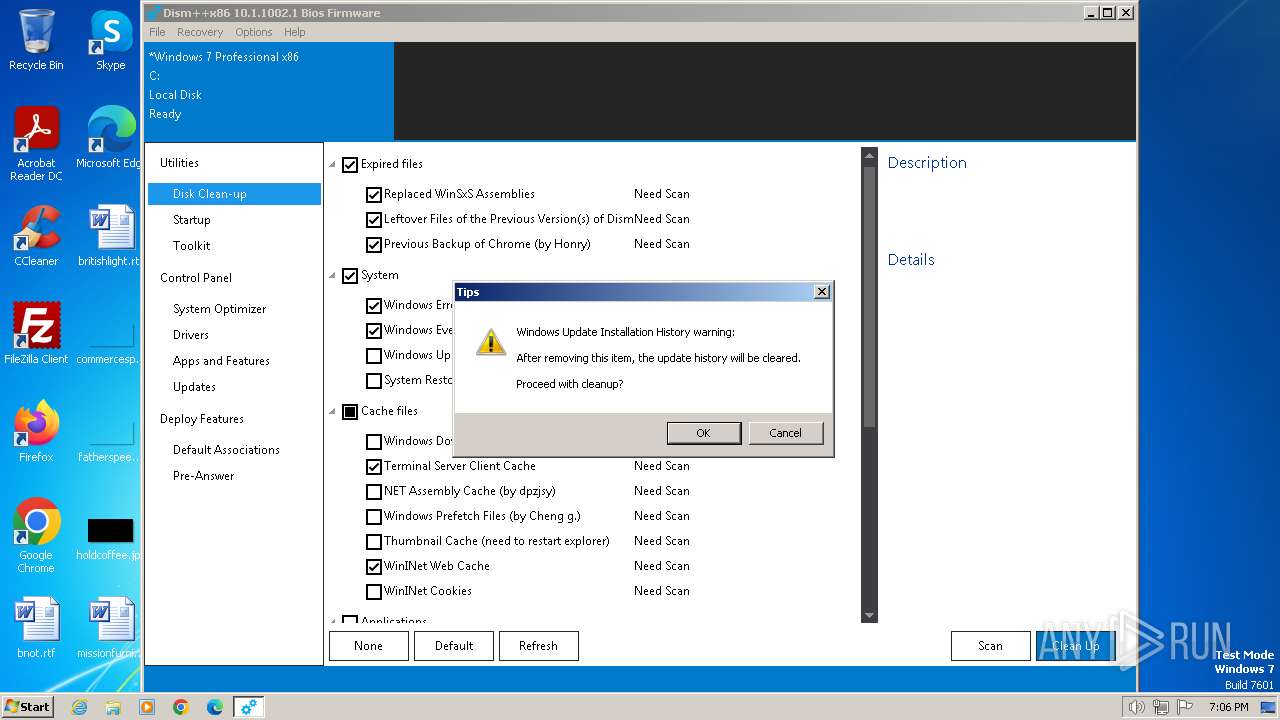
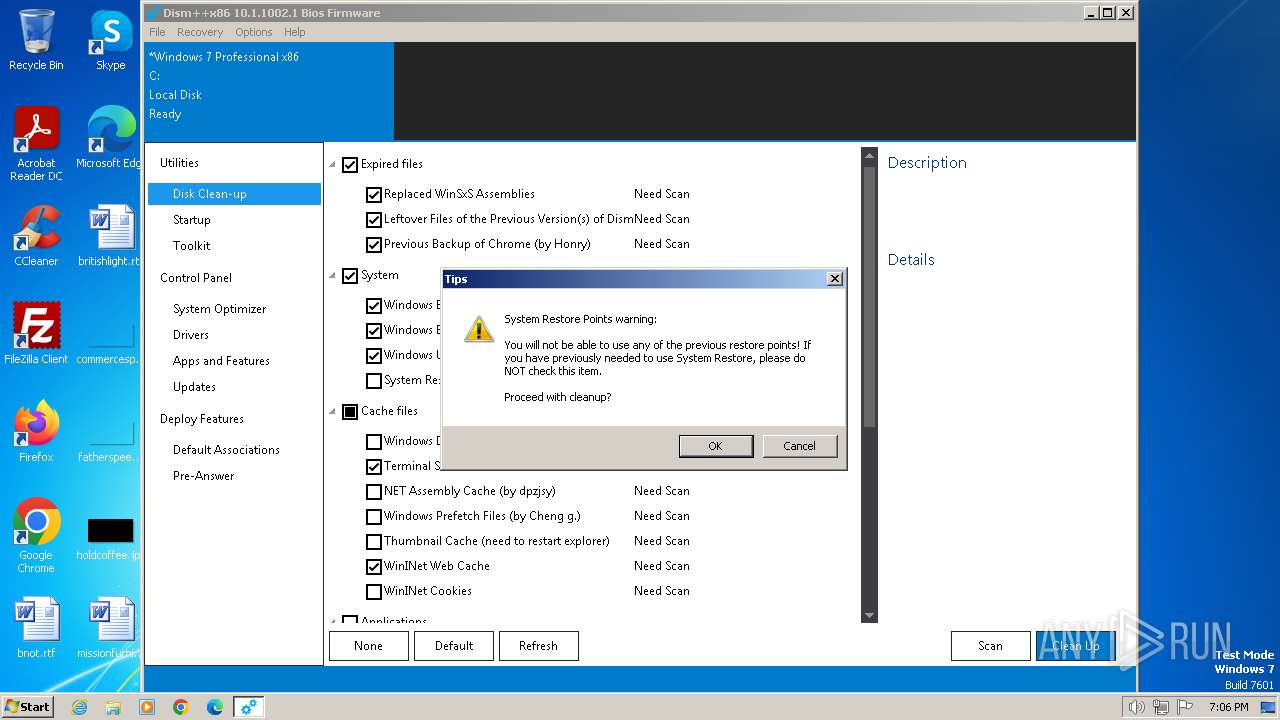
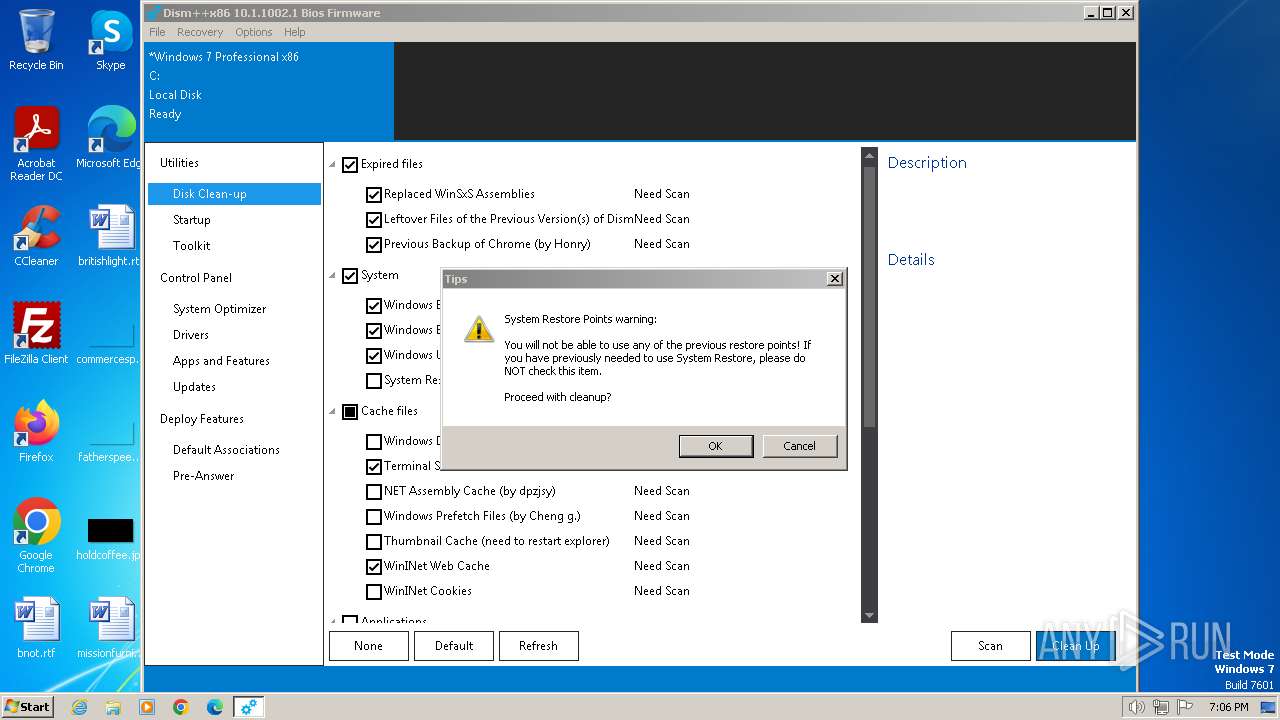
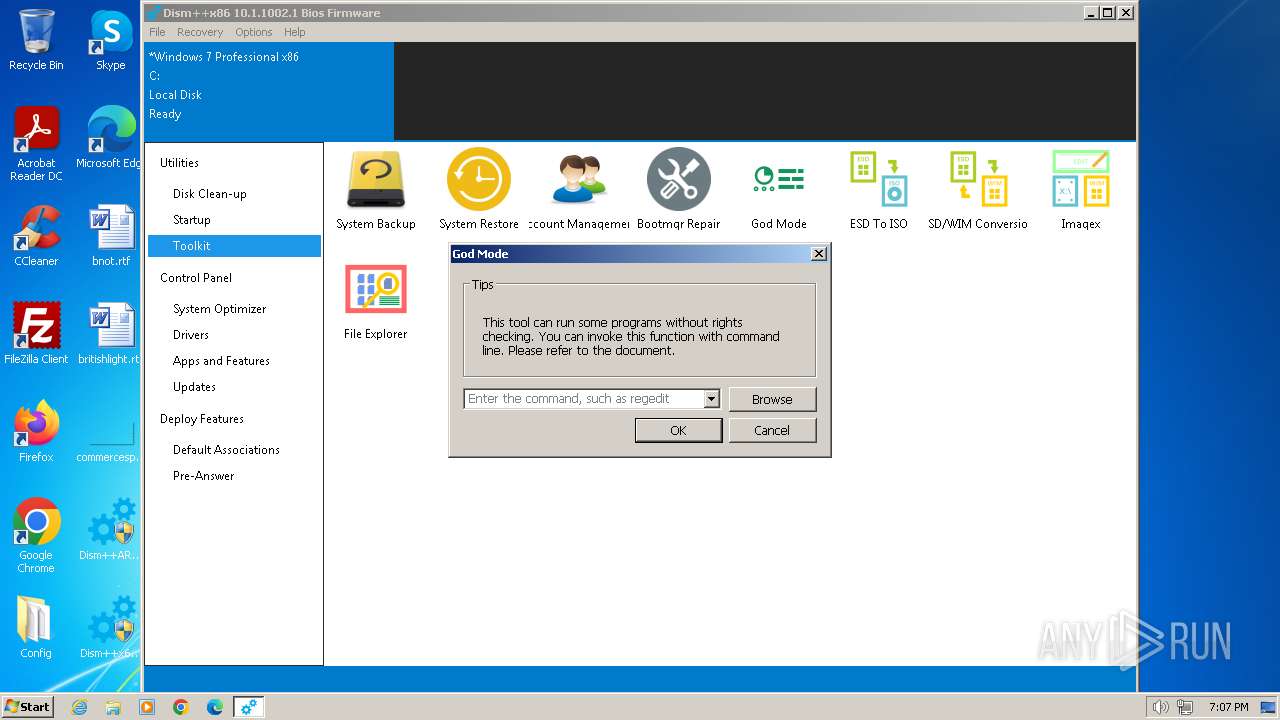
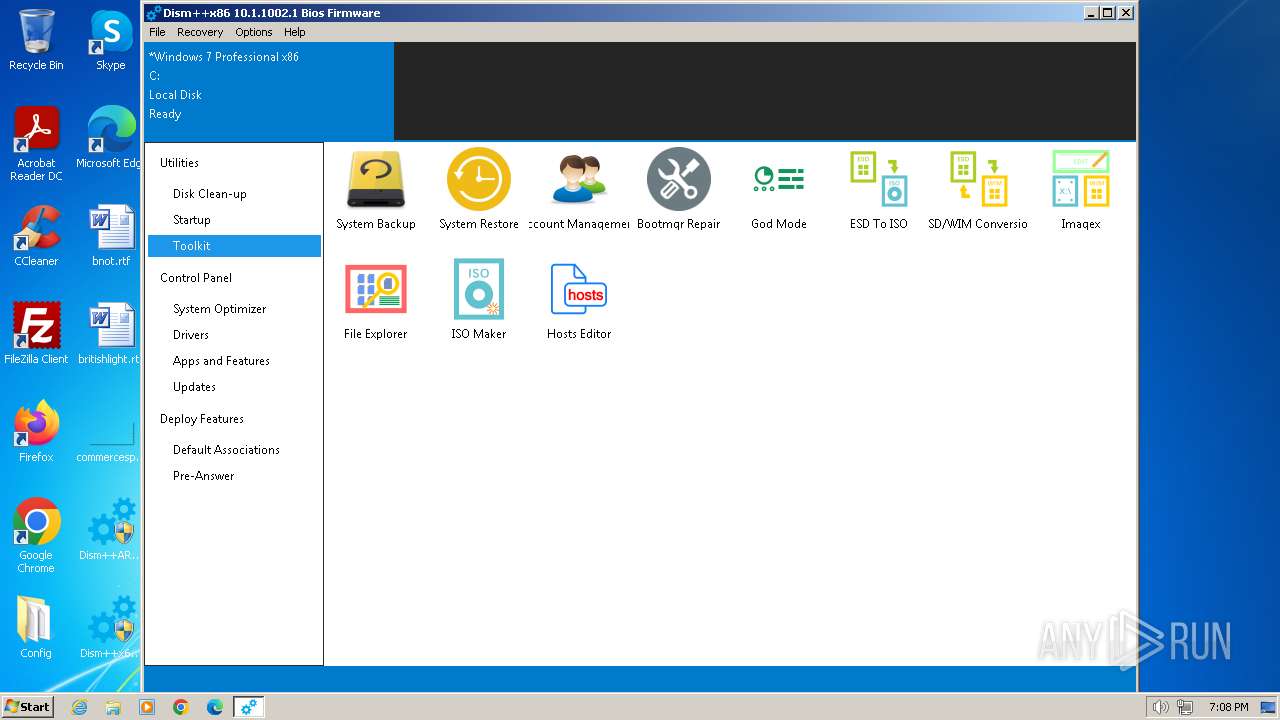
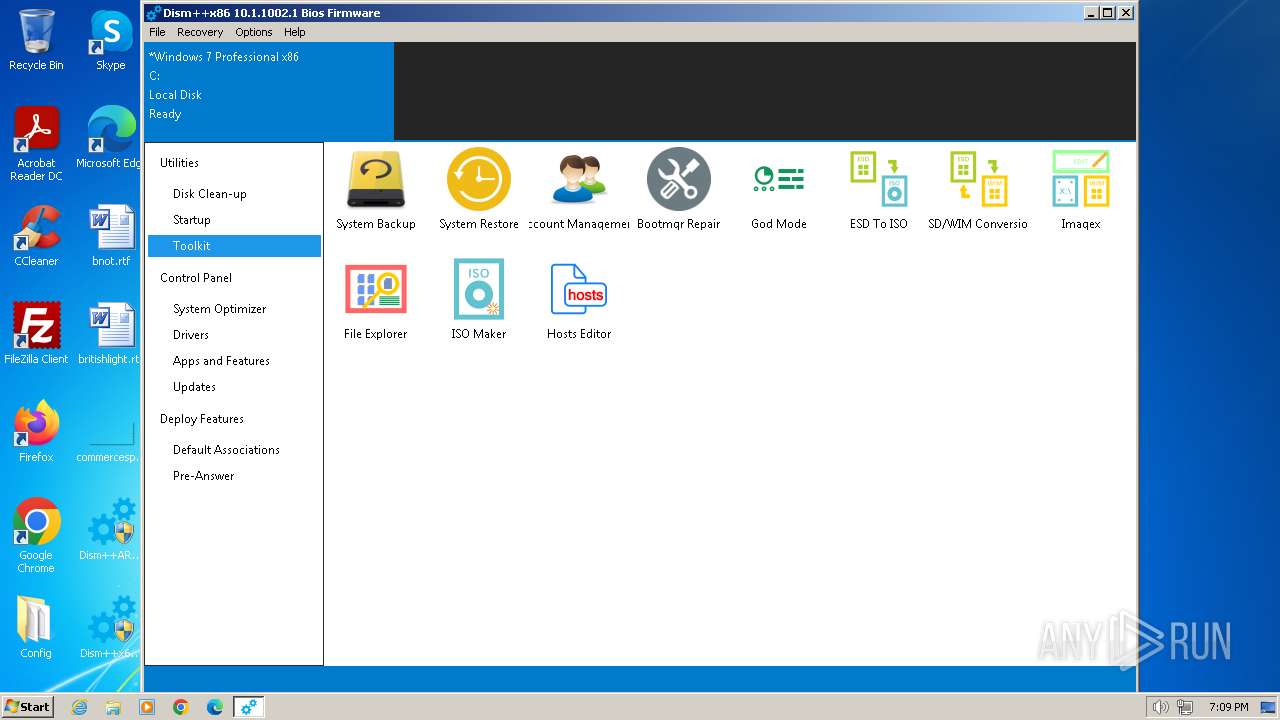
Start notepad (likely ransomware note)
- Dism++x86.exe (PID: 2944)
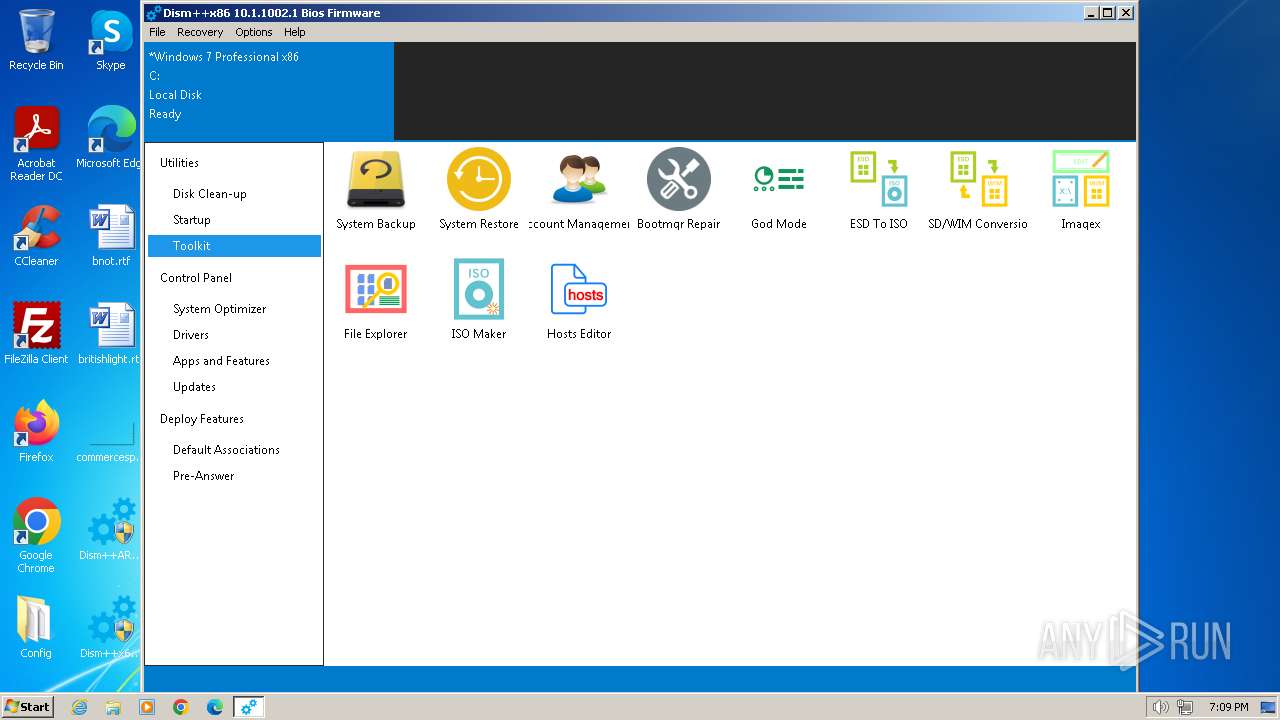
Uses RUNDLL32.EXE to load library
- Dism++x86.exe (PID: 2944)
Malware-specific behavior (creating "System.dll" in Temp)
- Un_A.exe (PID: 392)
INFO
Reads the computer name
- Dism++x86.exe (PID: 2944)
- wmpnscfg.exe (PID: 2372)
- wmpnscfg.exe (PID: 748)
- bcdboot.exe (PID: 1808)
- uninstall.exe (PID: 1316)
- Un_A.exe (PID: 392)
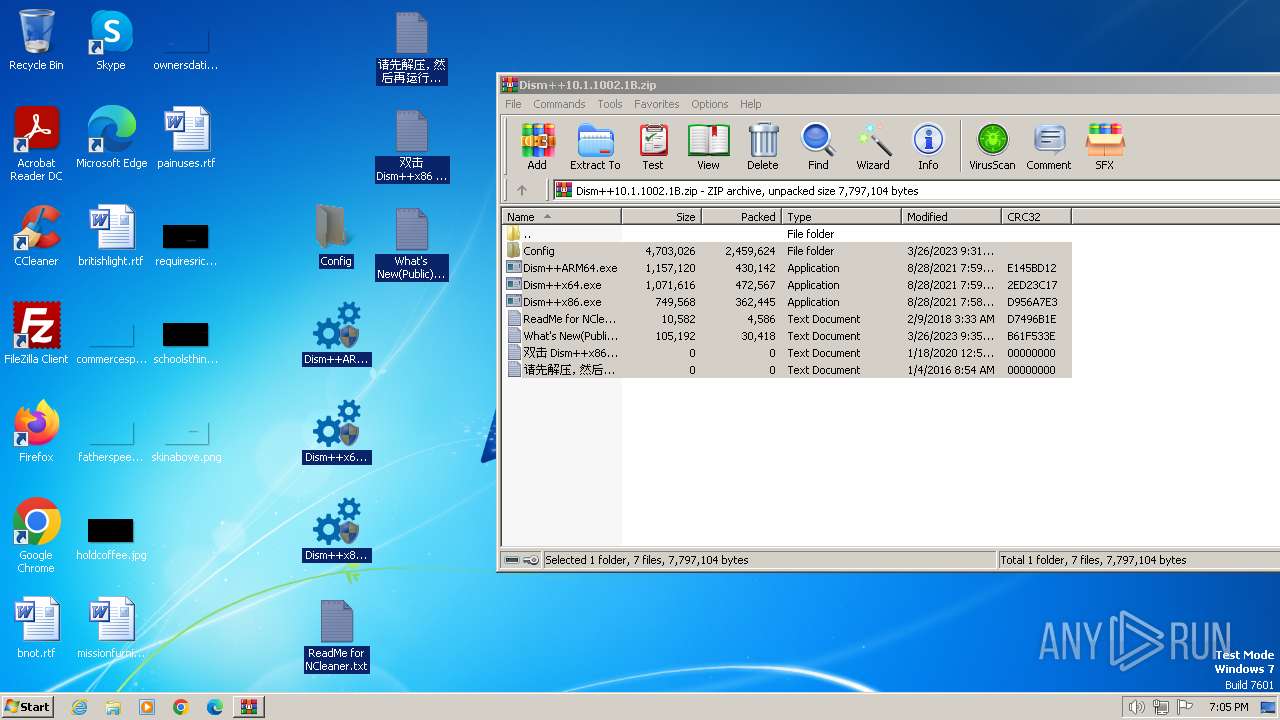
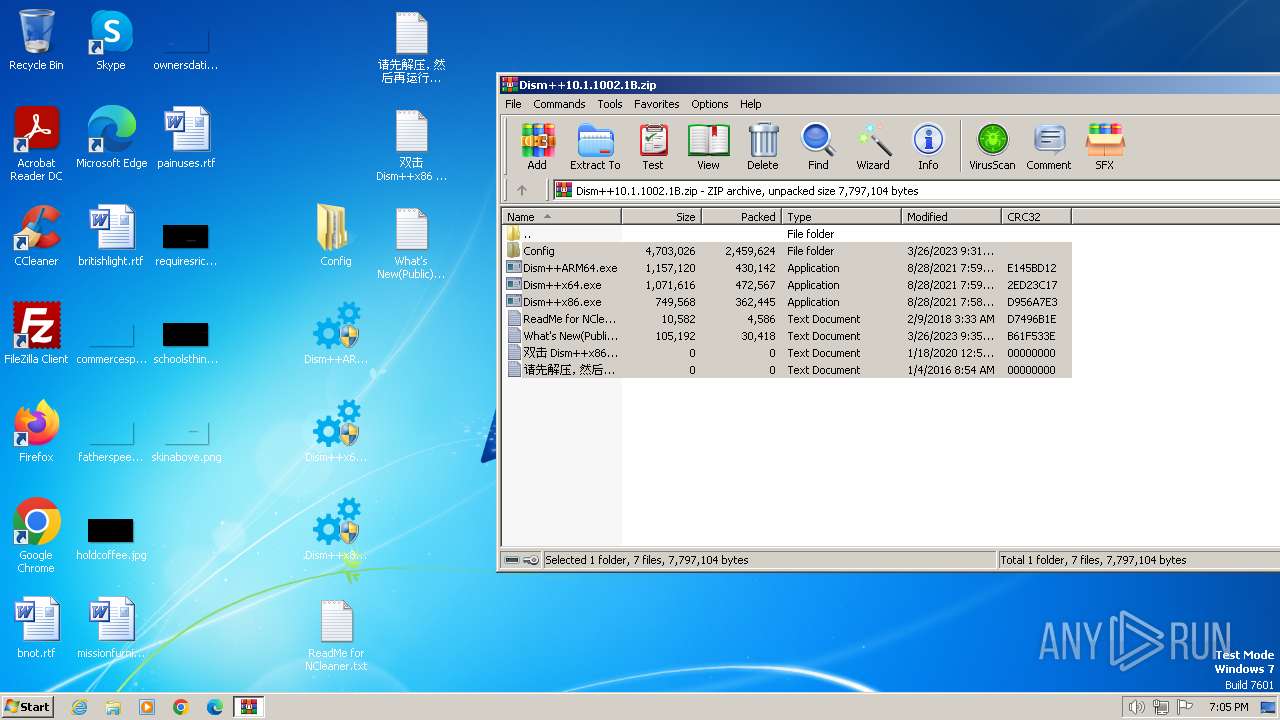
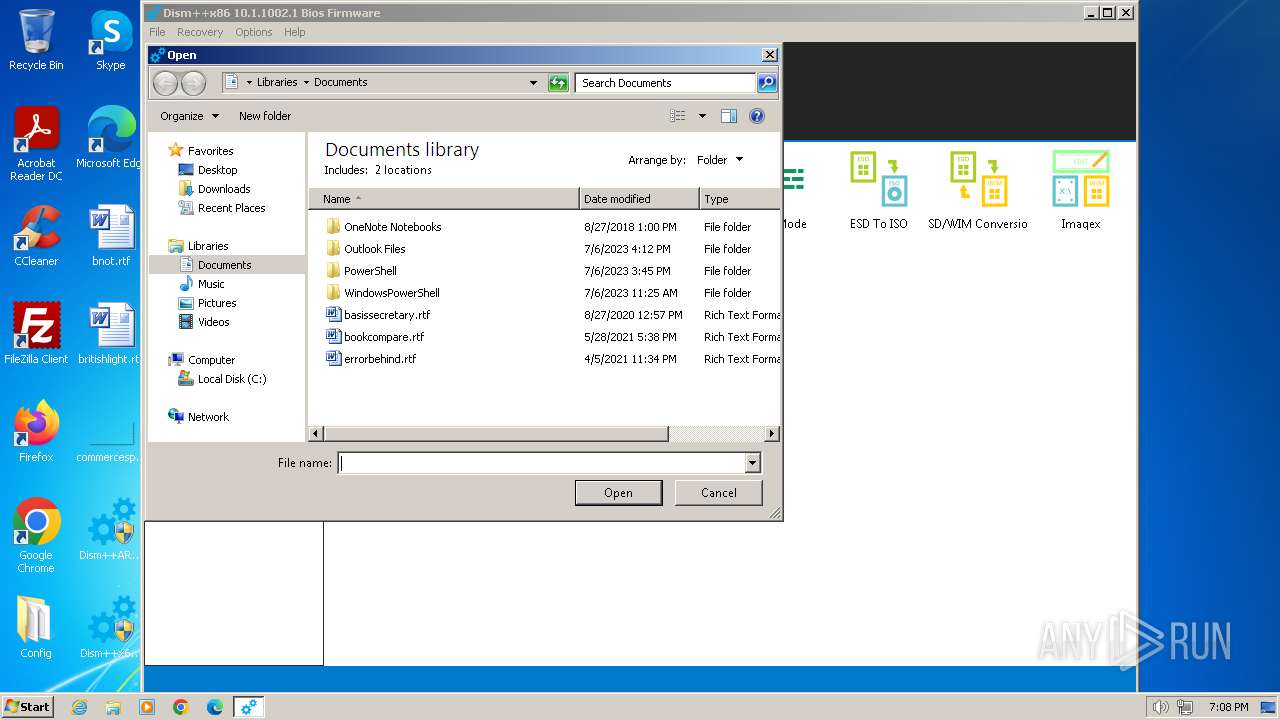
Creates files or folders in the user directory
- explorer.exe (PID: 3460)
Process checks whether UAC notifications are on
- Dism++x86.exe (PID: 2944)
Reads Environment values
- Dism++x86.exe (PID: 2944)
Reads the machine GUID from the registry
- Dism++x86.exe (PID: 2944)
Checks proxy server information
- Dism++x86.exe (PID: 2944)
Checks Windows language
- Dism++x86.exe (PID: 2944)
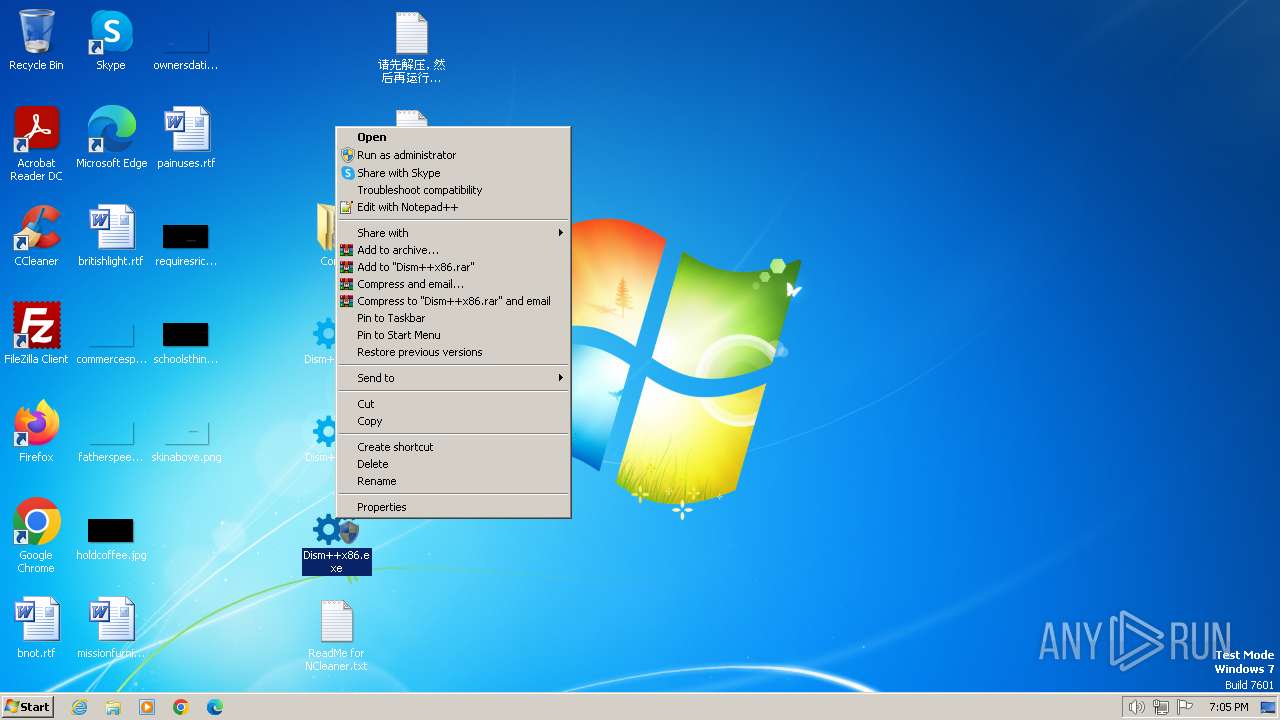
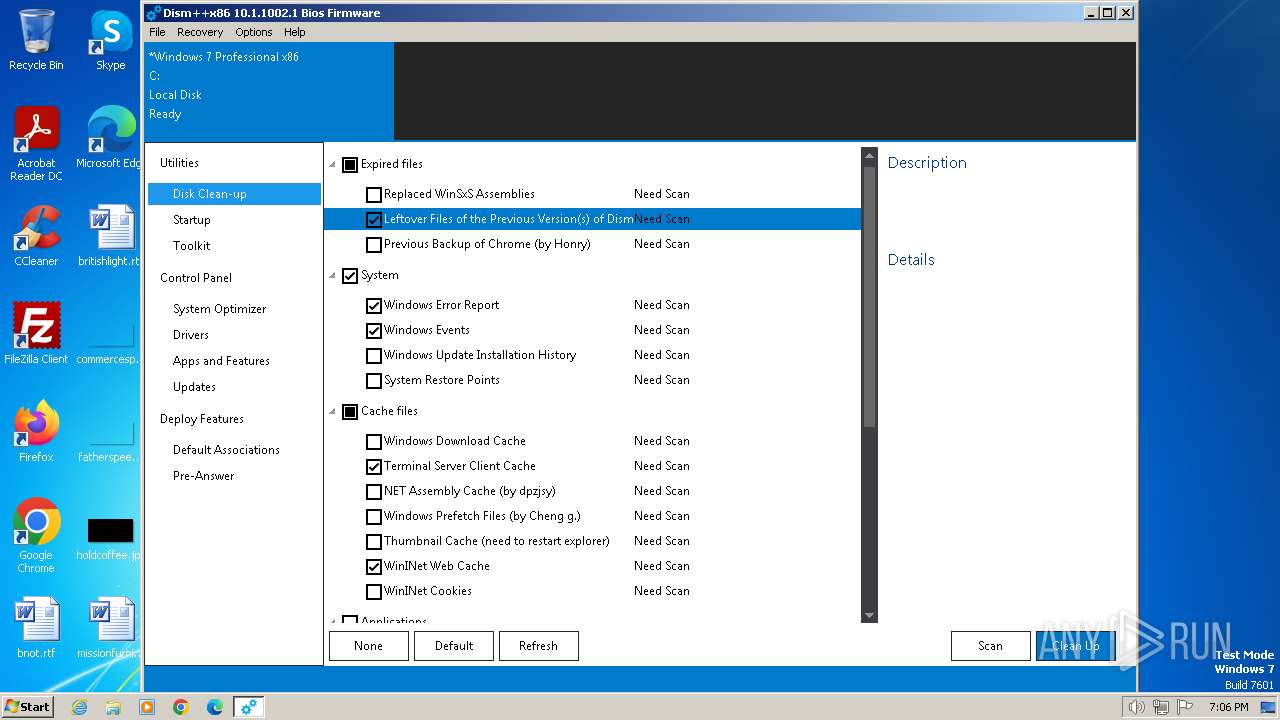
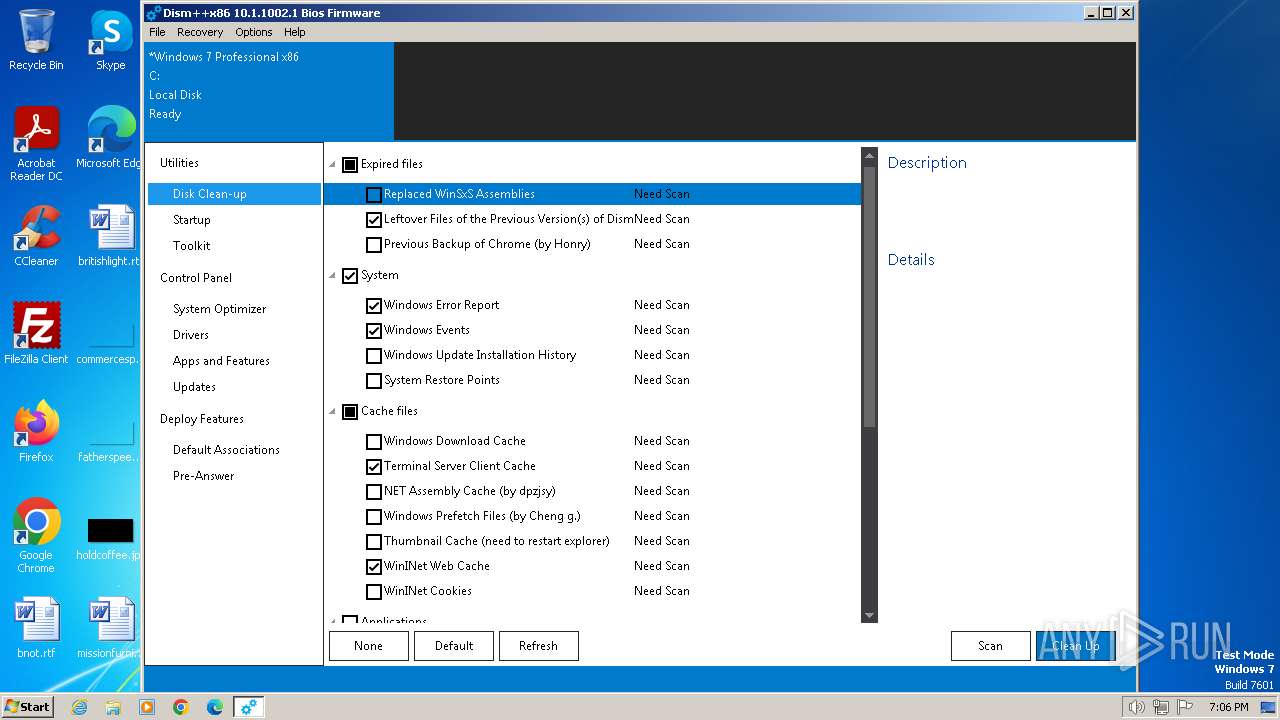
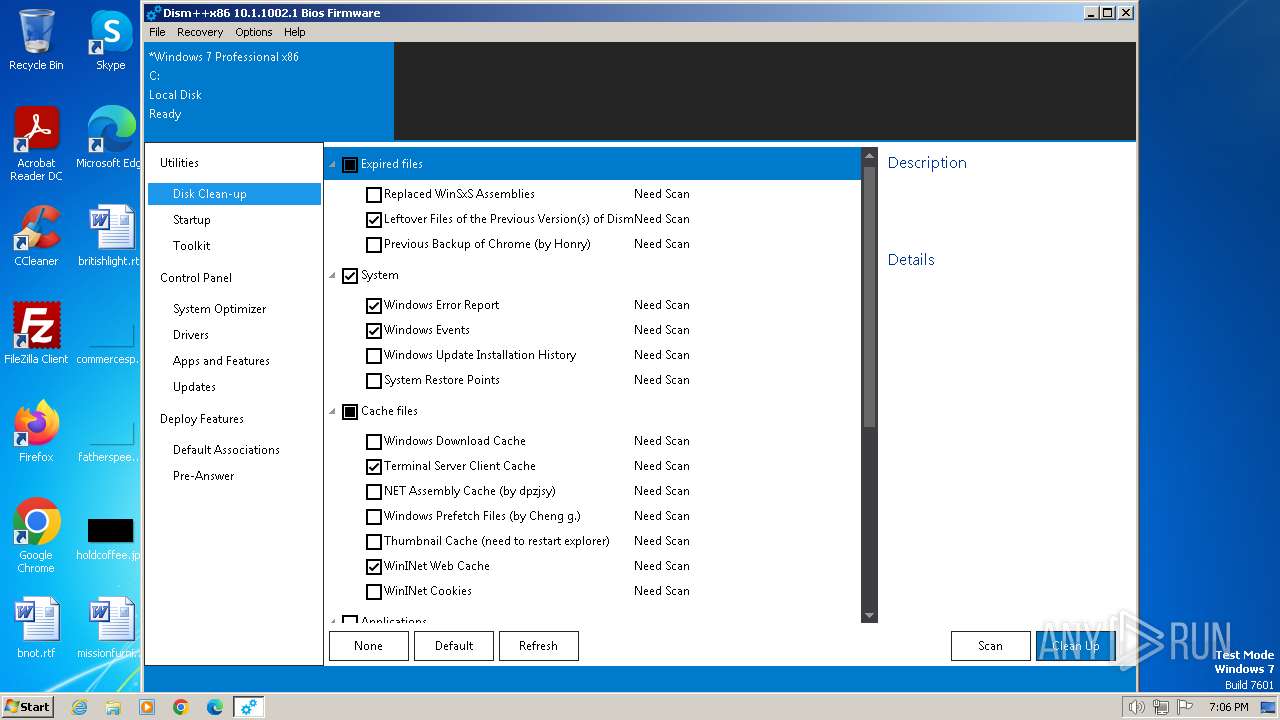
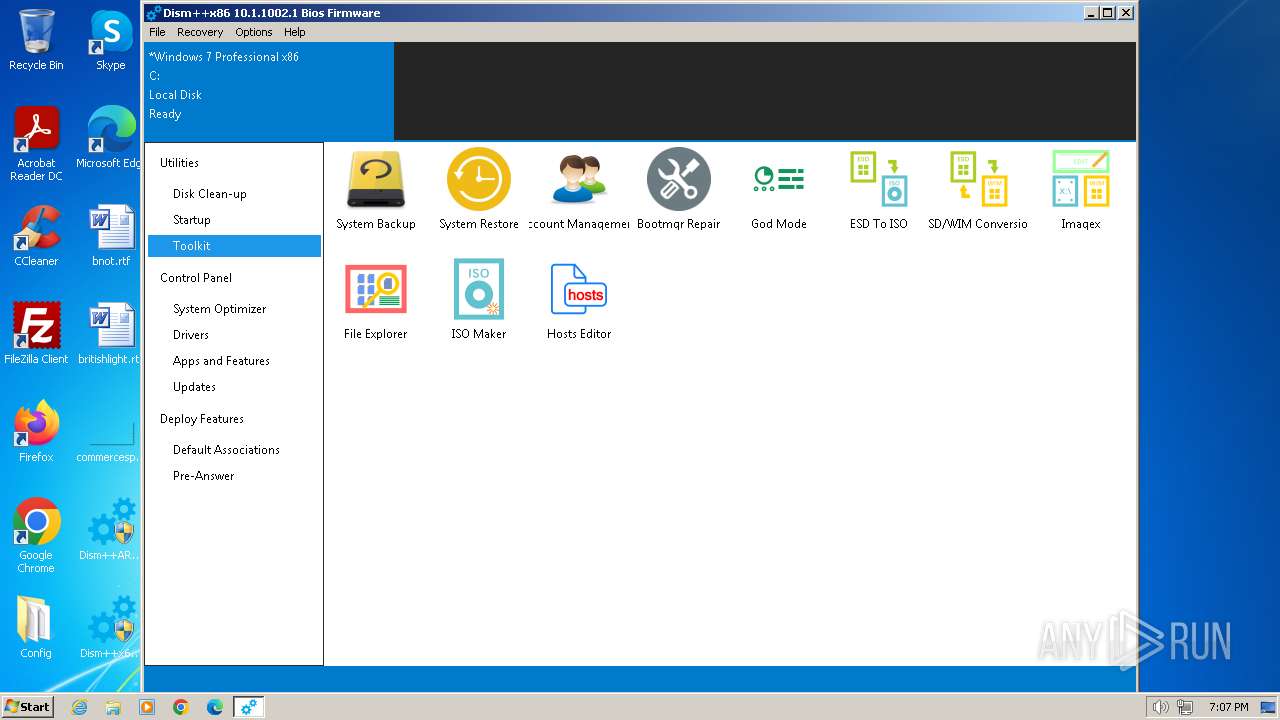
Manual execution by a user
- Dism++x86.exe (PID: 2944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1504)
Checks supported languages
- Dism++x86.exe (PID: 2944)
- wmpnscfg.exe (PID: 2372)
- bcdboot.exe (PID: 1808)
- wmpnscfg.exe (PID: 748)
- uninstall.exe (PID: 1316)
- Un_A.exe (PID: 392)
Create files in a temporary directory
- explorer.exe (PID: 3460)
- uninstall.exe (PID: 1316)
- Un_A.exe (PID: 392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:03:26 16:31:38 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Config/ |
Total processes
62
Monitored processes
13
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
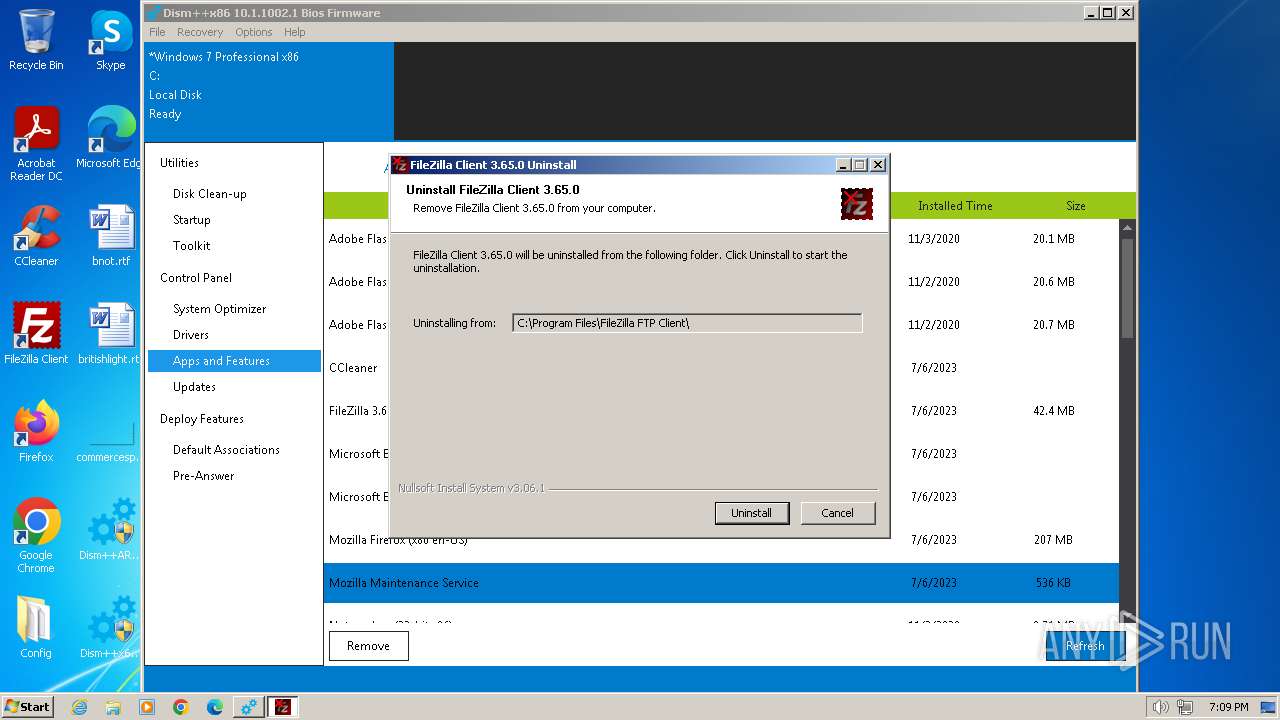
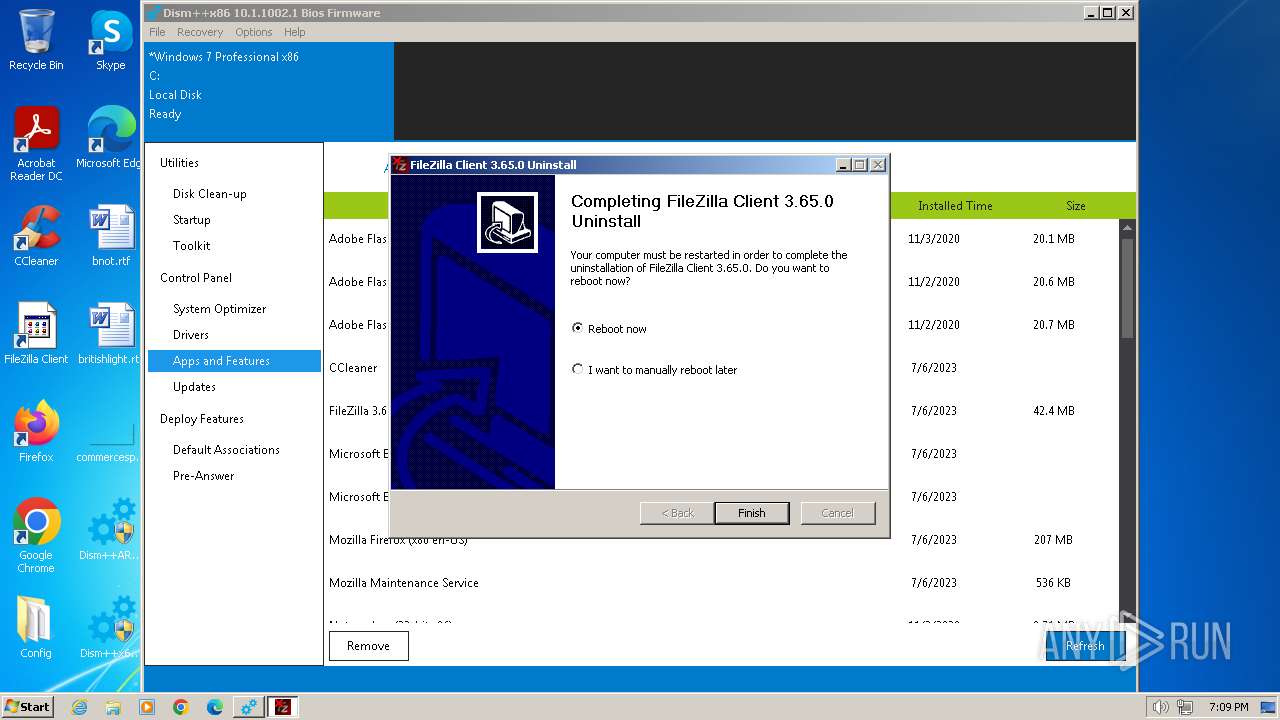
| 392 | "C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe" _?=C:\Program Files\FileZilla FTP Client\ | C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe | uninstall.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.65.0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | "C:\Program Files\FileZilla FTP Client\uninstall.exe" | C:\Program Files\FileZilla FTP Client\uninstall.exe | Dism++x86.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.65.0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dism++10.1.1002.1B.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
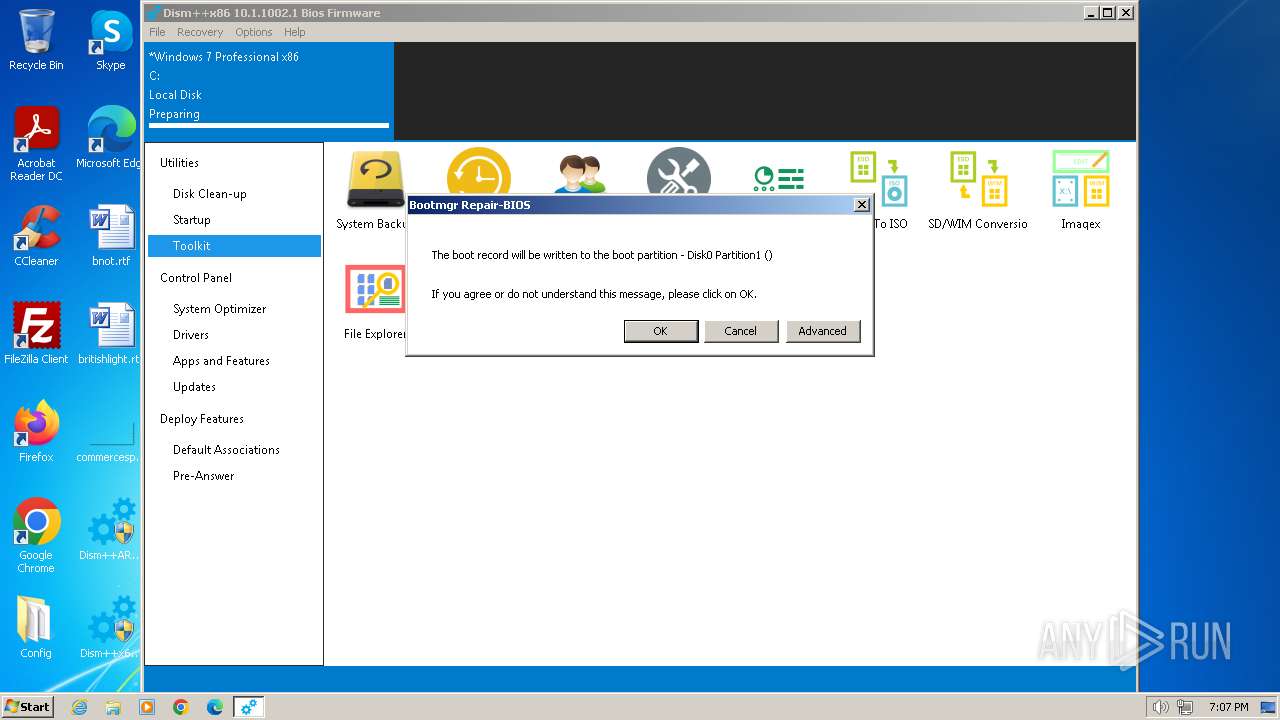
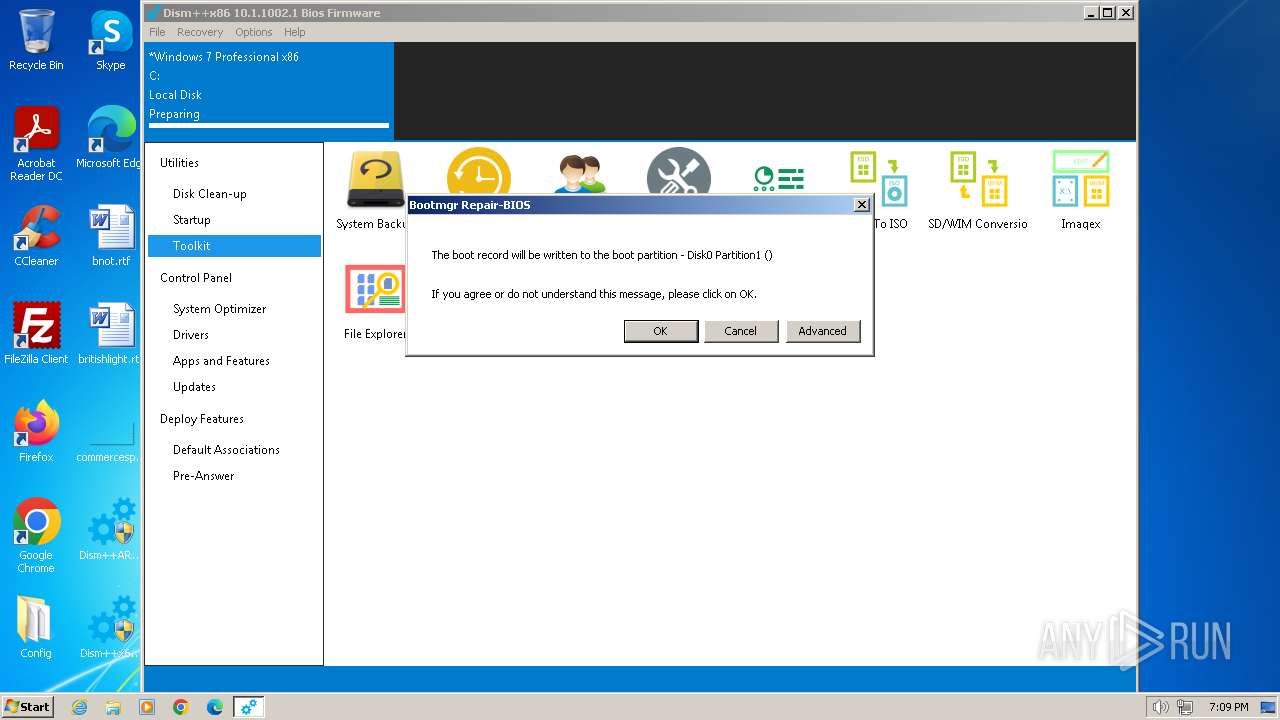
| 1808 | Bcdboot C:\Windows /l en-US /s \Device\Harddisk0\Partition1 | C:\Users\admin\Desktop\Config\x86\bcdboot.exe | Dism++x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Bcdboot utility Exit code: 0 Version: 10.0.10586.0 (th2_release.151029-1700) Modules
| |||||||||||||||
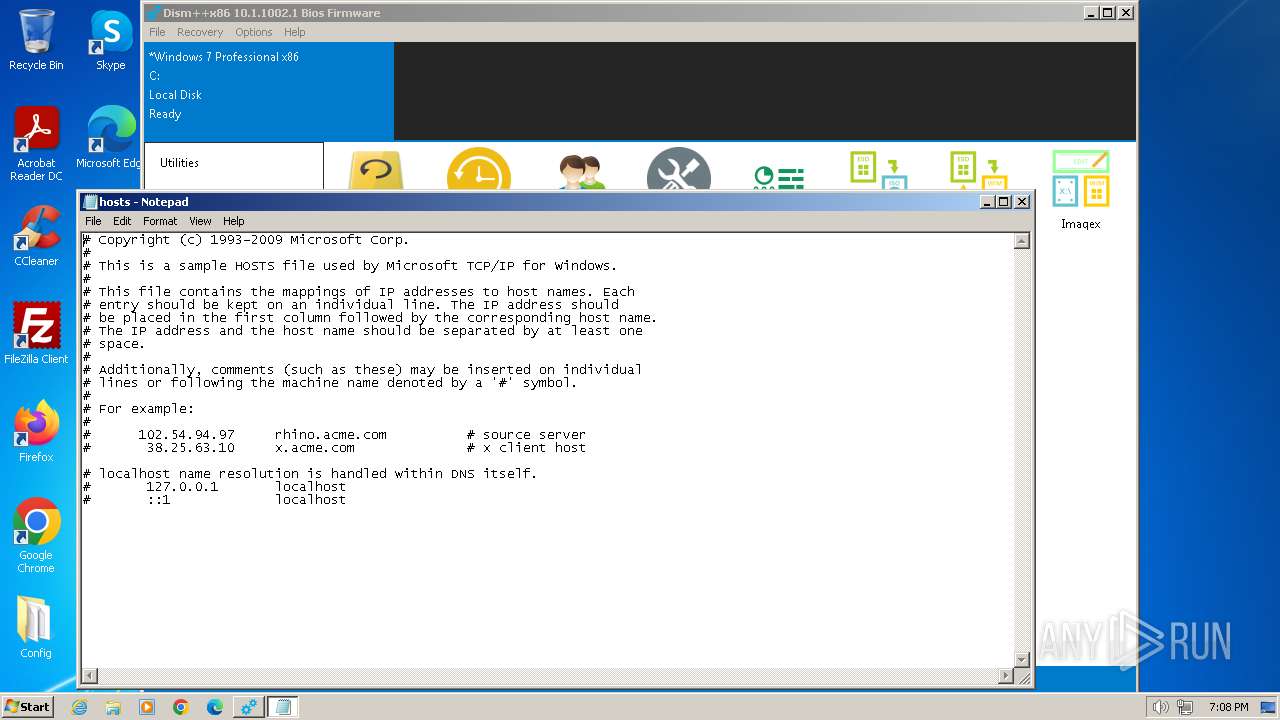
| 1832 | notepad "C:\Windows\System32\drivers\etc\hosts" | C:\Windows\System32\notepad.exe | — | Dism++x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | rundll32 "C:\Users\admin\Desktop\Config\x86\CBSHost.dll",RunCbsHost {af6d2177-bb05-44b9-949d-e2dfa9e1ea99} "C:" "\\?\C:\Windows\Temp\\" 000000C8 4 | C:\Windows\System32\rundll32.exe | — | Dism++x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
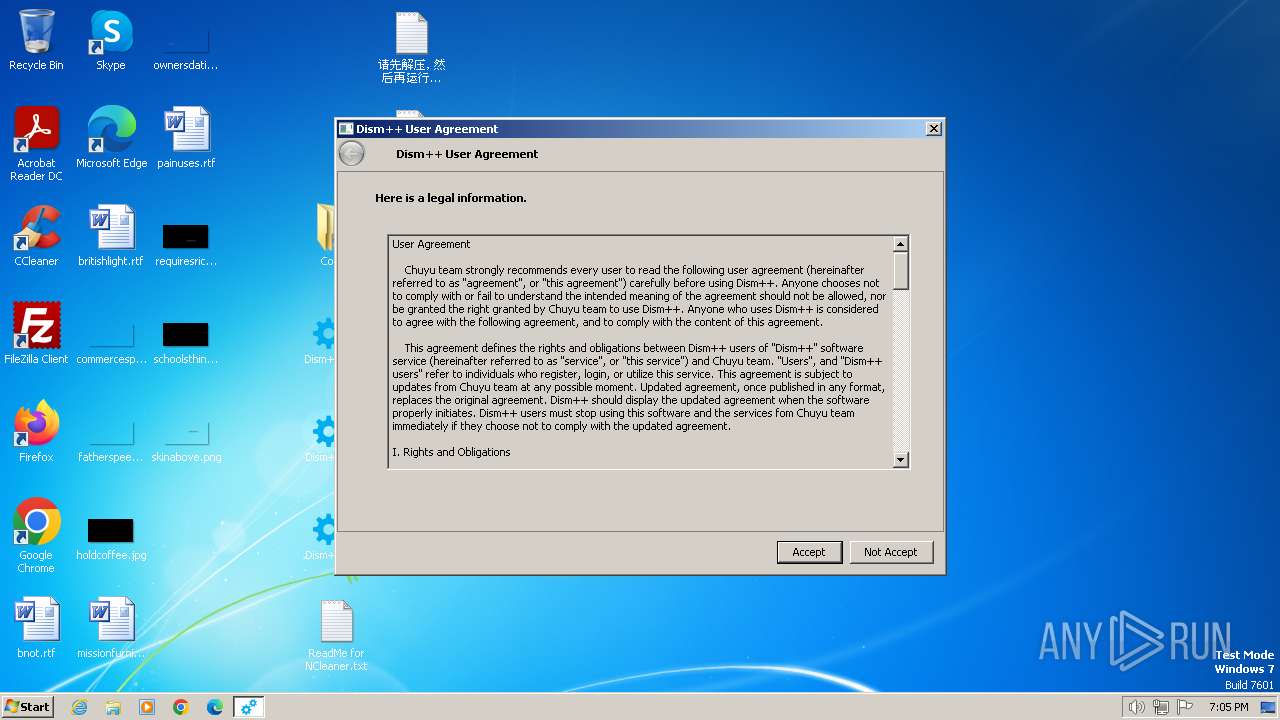
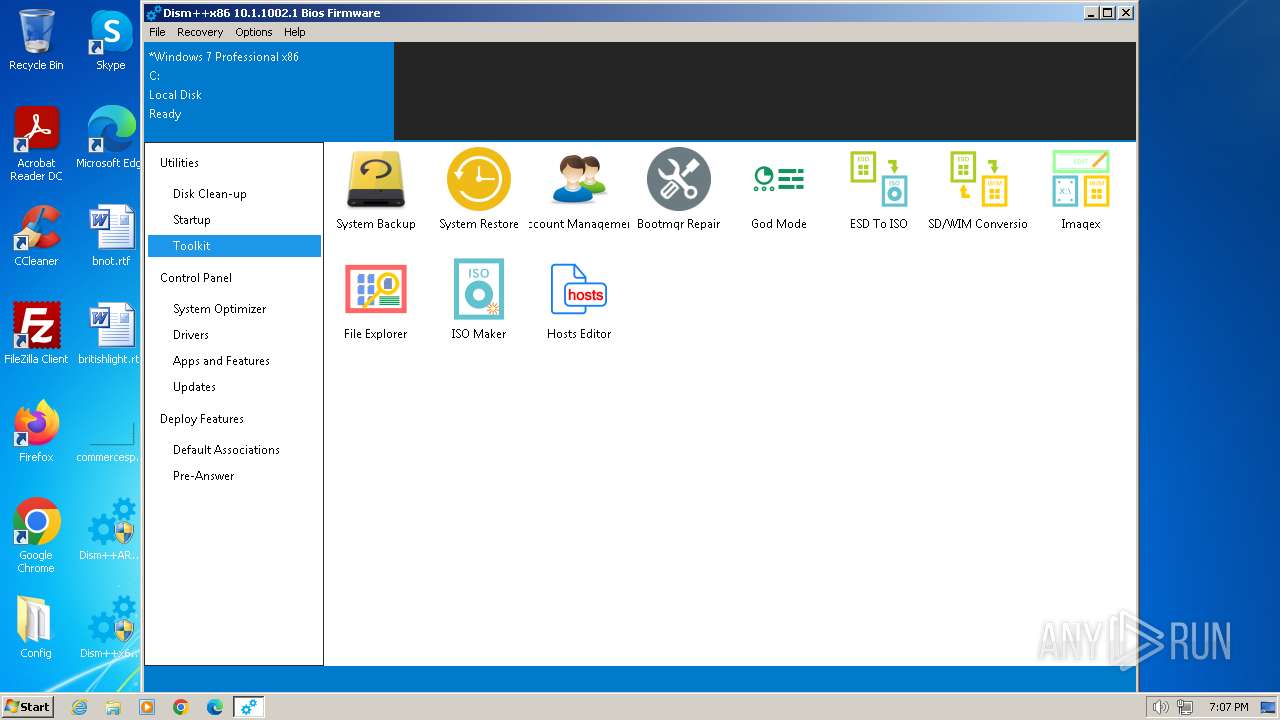
| 2944 | "C:\Users\admin\Desktop\Dism++x86.exe" | C:\Users\admin\Desktop\Dism++x86.exe | explorer.exe | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Exit code: 1073807364 Version: 10.1.1002.1 Modules
| |||||||||||||||
| 3460 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | Dism++x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 358
Read events
13 626
Write events
486
Delete events
246
Modification events
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
75
Suspicious files
45
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\amd64\wofadk.sys | executable | |
MD5:FBA28D5AC166714737D1D8CDF0AEF078 | SHA256:54FBA1CC80E820B462229FCB987FB8DF2321ED85D9450F3F4A81D0982E5D289F | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\Languages\bg.zip | compressed | |
MD5:D2EFE76E6991016EA78D7E65DB60A640 | SHA256:A9A1C127DF4BC6A7D420F209FD3D5BEEBD01454CF0CAFFC486D7509A9C50B7F2 | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\amd64\NCleaner.dll | executable | |
MD5:C2058BCB1607FFB1A9FEFD67C2E8F94A | SHA256:141587AD11529D238DC7B63D7F30002FF042C3B06282D075E44E9C5AF07CCC17 | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\amd64\CBSHost.dll | executable | |
MD5:DD139DF87A896B894335E03ECE2973BF | SHA256:6A1075F4FAB4ACD2722E8946CBA7B23508D120367C84AAE3E83284124227013A | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\amd64\bcdboot.exe | executable | |
MD5:BE14BE7C8F7F0F4E397B89979CB9CF6B | SHA256:309F3ECCB0093CC6CC98F858BD3CE67B00BB810728FFB177B7BD287FB3C92B97 | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\Languages\es.zip | compressed | |
MD5:7722877E0A3B724B1AB8376B15C55CDE | SHA256:B4CC3650EB42E53788E5D84FB79256AE8E140D843F7A47BF0710C99927E4302B | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\default.ui.zip | compressed | |
MD5:E4B7BEF45A8F48832BA59396509DCB76 | SHA256:1A90365AC33C37EEAE4DD712F84062466C10948CF5B567574055E0B8B0F70534 | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\Data.zip | compressed | |
MD5:C3DF4642551B01EE38BC10BC4A06BAD6 | SHA256:8D524539F83A6416DBB4FDDE697A4BD8D870DDF25B162E874BFC9C56122A03DC | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\amd64\wimgapi.dll | executable | |
MD5:80826A2374B051468FFBD6E85993137D | SHA256:E51344884512B486FF1DE3C30E554B0E1CB6FFB8ED4E3BDD31A29A76454F5562 | |||
| 1504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1504.21321\Config\arm64\CBSHost.dll | executable | |
MD5:D81098BEC9F475C3A86E0FA38AEAA537 | SHA256:9CAEBB88BA8F4087273BDC07F37B260A15DC2C7B4058FFAC77A147ED1A27C032 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 23.206.114.114:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133513746089530000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.chuyu.me |
| unknown |
query.prod.cms.rt.microsoft.com |
| whitelisted |