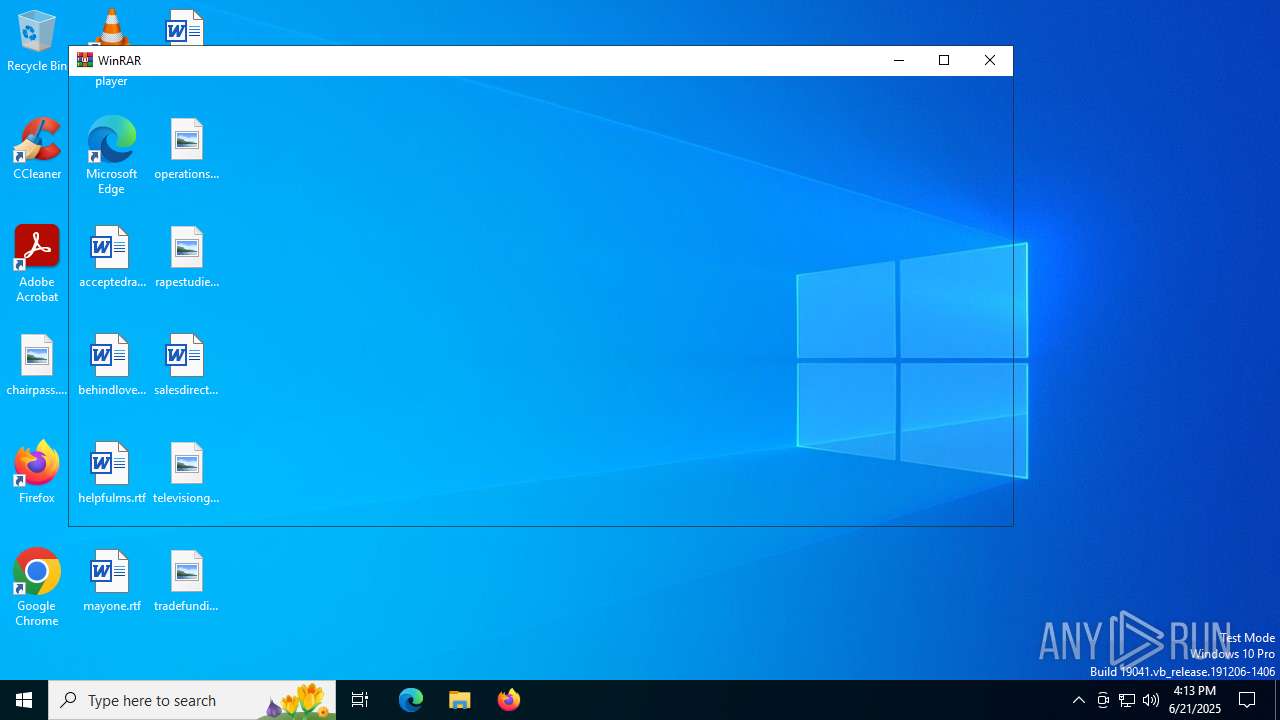
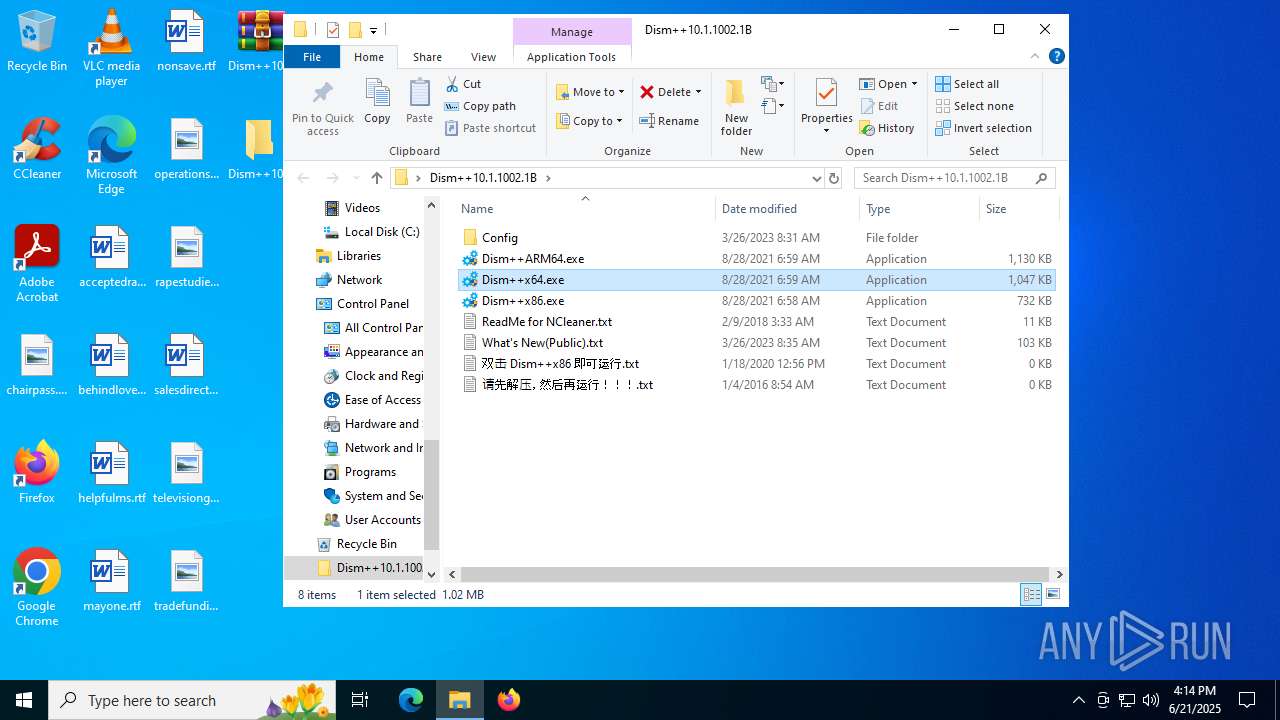
| File name: | Dism++10.1.1002.1B.zip |
| Full analysis: | https://app.any.run/tasks/63bc4889-2630-4b78-90a3-6496f20b7dca |
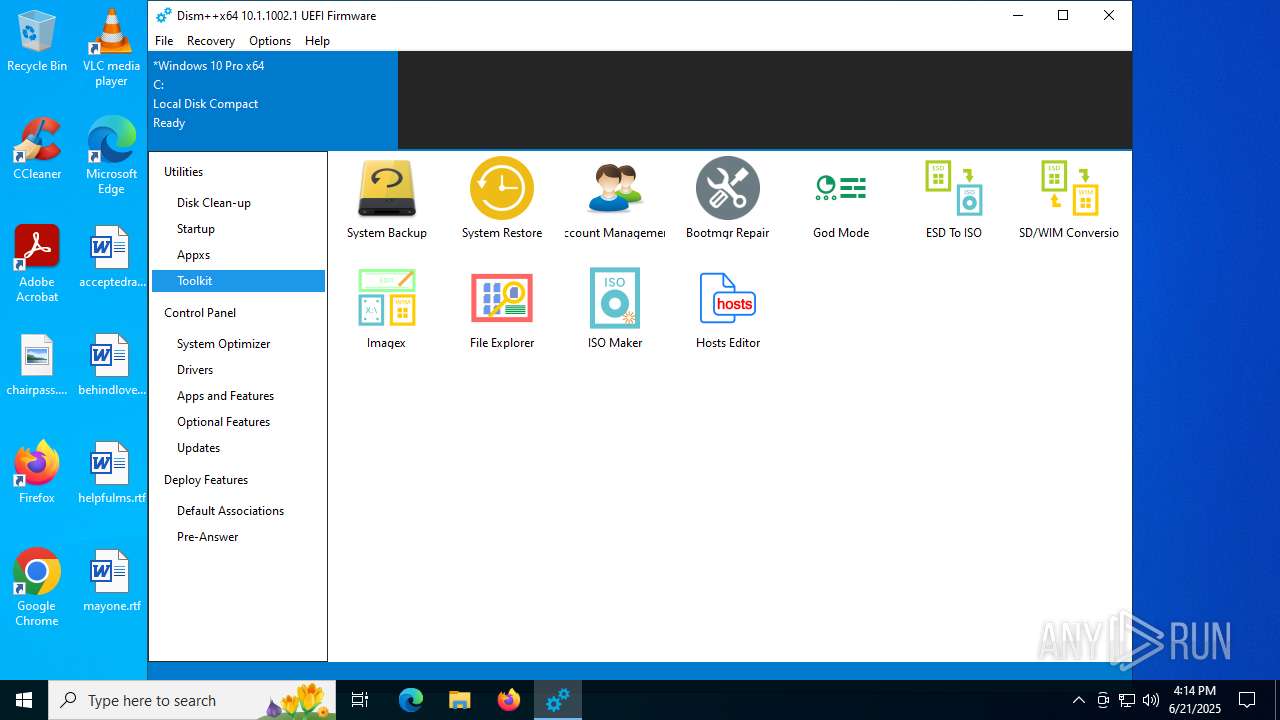
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 16:13:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | F5485E418DA631B6289E4A51495BCA87 |
| SHA1: | 2ECB84172BF12FEC7C9E1F378466DB53589660FB |
| SHA256: | 5BBAB96D60704854EFD8246A7D9371688B9102261544827FC8884126D70BCB3B |
| SSDEEP: | 98304:vKBqv2ChMWSVDy+Q8YOUoYqeYfsuK0sTILg6ixyeXmziSTPB+u8:SB82KMWqyJfoEY0l0sUAxp2WIPB+u8 |
MALICIOUS
Generic archive extractor
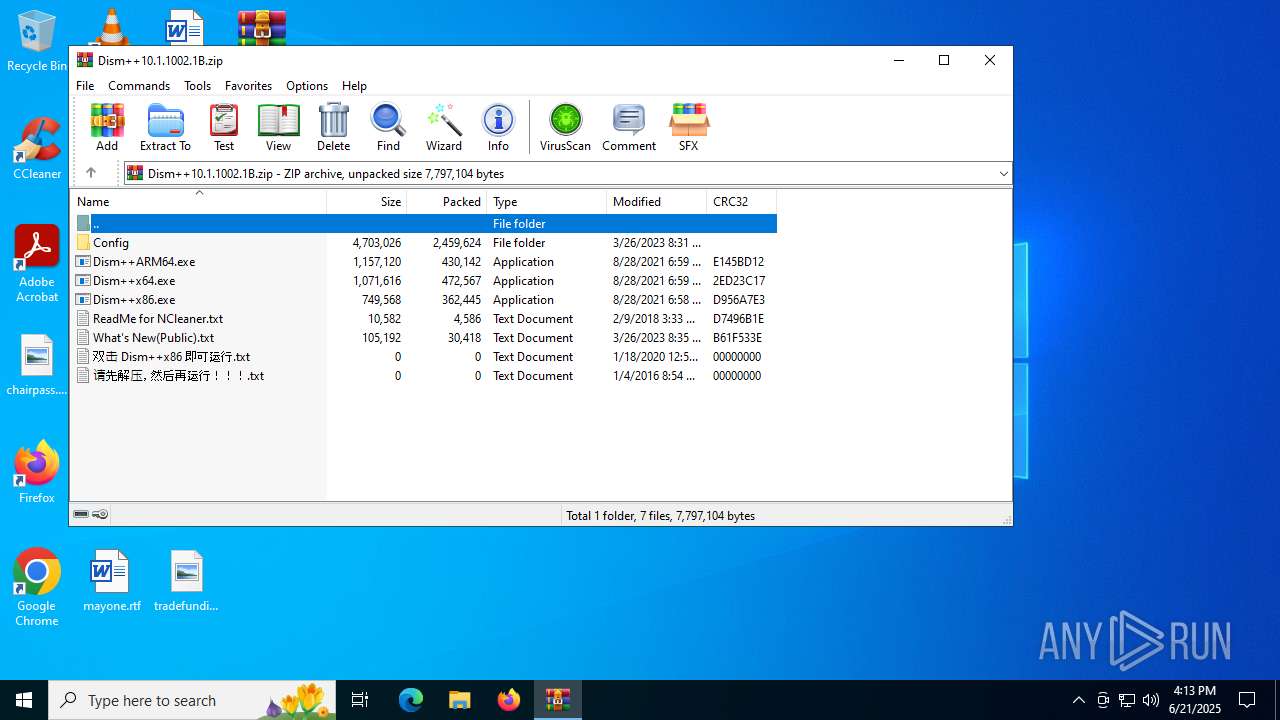
- WinRAR.exe (PID: 1068)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1068)
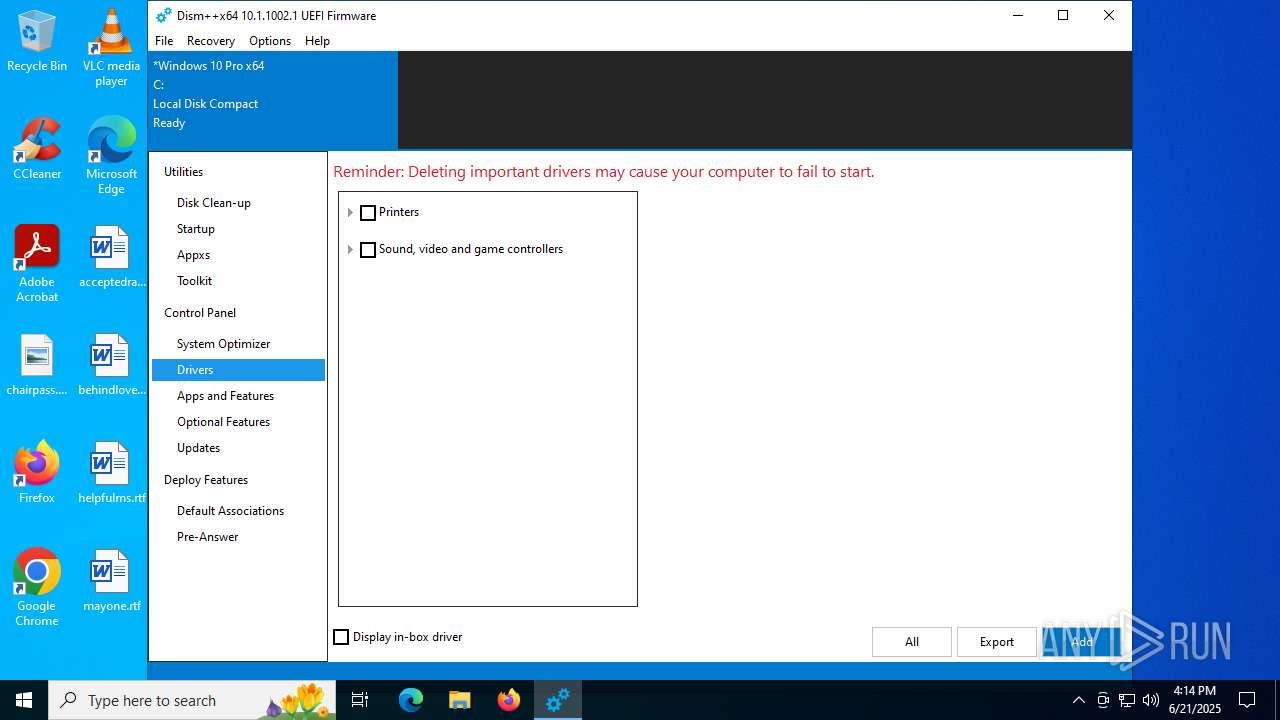
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 1068)
Detected use of alternative data streams (AltDS)
- Dism++x64.exe (PID: 6264)
Process drops legitimate windows executable
- WinRAR.exe (PID: 1068)
Reads security settings of Internet Explorer
- Dism++x64.exe (PID: 6264)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 1068)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1068)
The sample compiled with chinese language support
- WinRAR.exe (PID: 1068)
Checks supported languages
- Dism++x64.exe (PID: 6264)
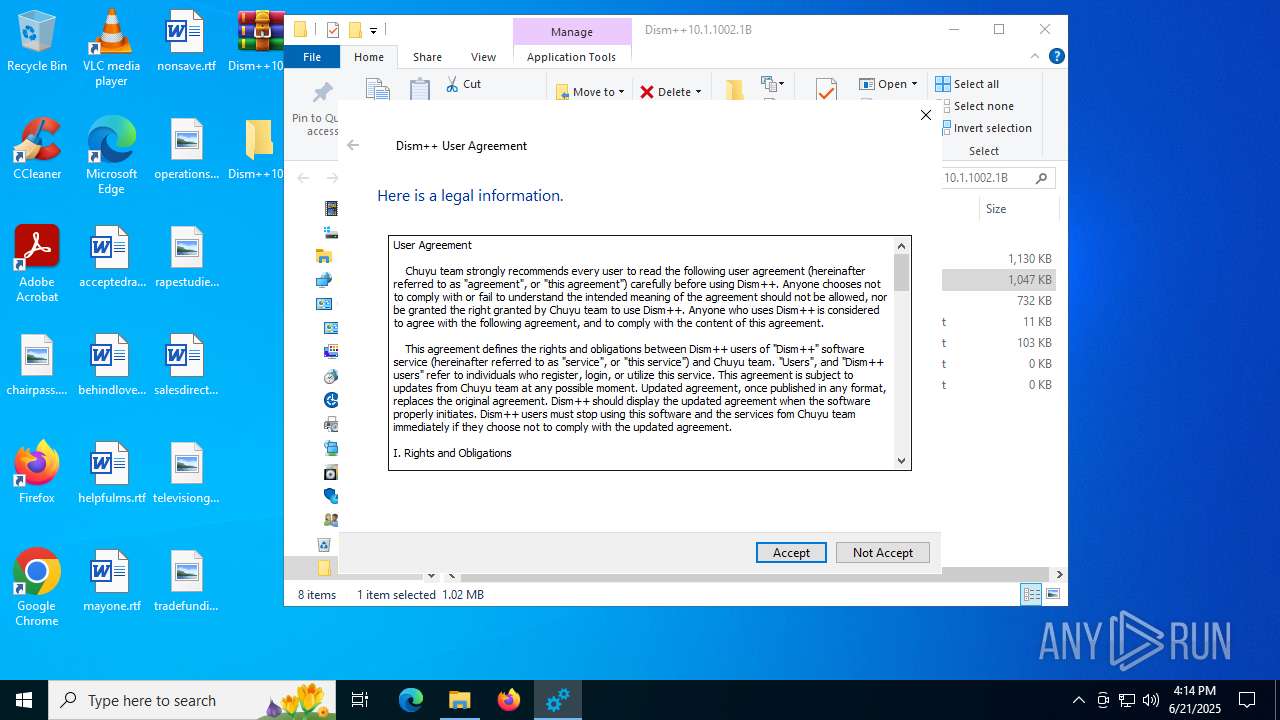
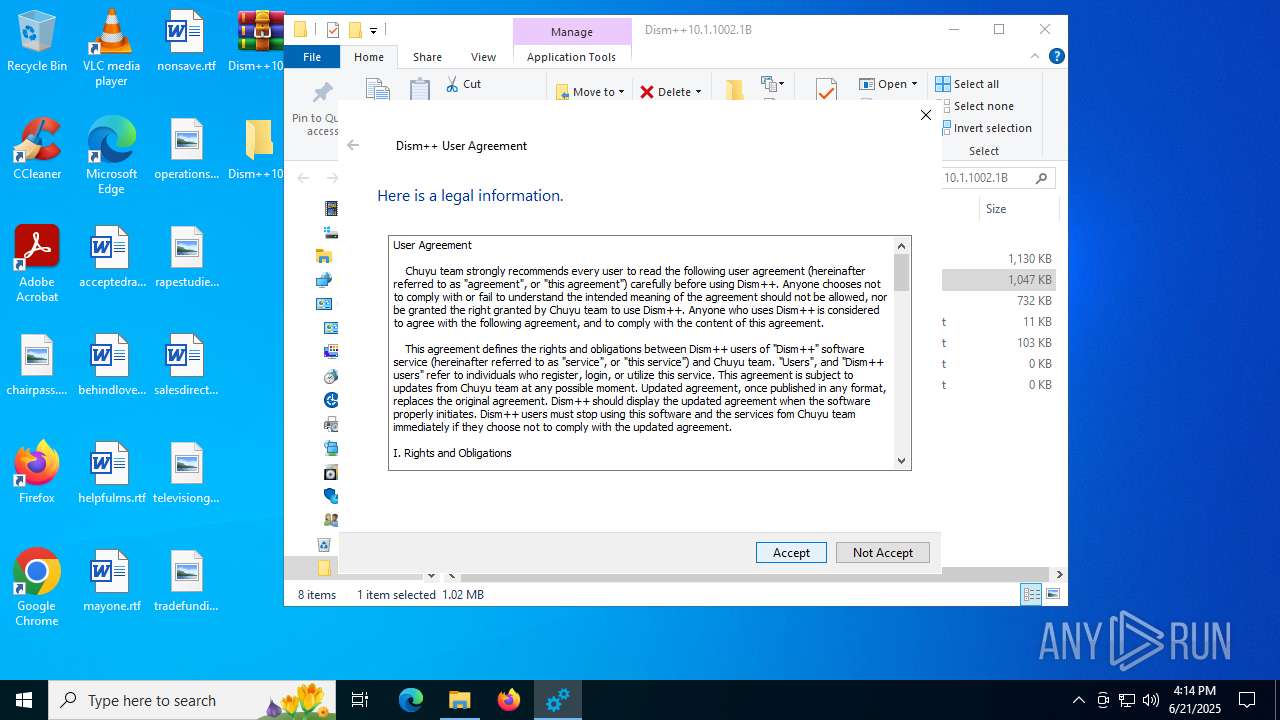
Manual execution by a user
- Dism++x64.exe (PID: 6264)
- Dism++x64.exe (PID: 4196)
Reads the computer name
- Dism++x64.exe (PID: 6264)
Reads the machine GUID from the registry
- Dism++x64.exe (PID: 6264)
Reads Environment values
- Dism++x64.exe (PID: 6264)
Checks proxy server information
- Dism++x64.exe (PID: 6264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:03:26 16:31:38 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Config/ |
Total processes
142
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
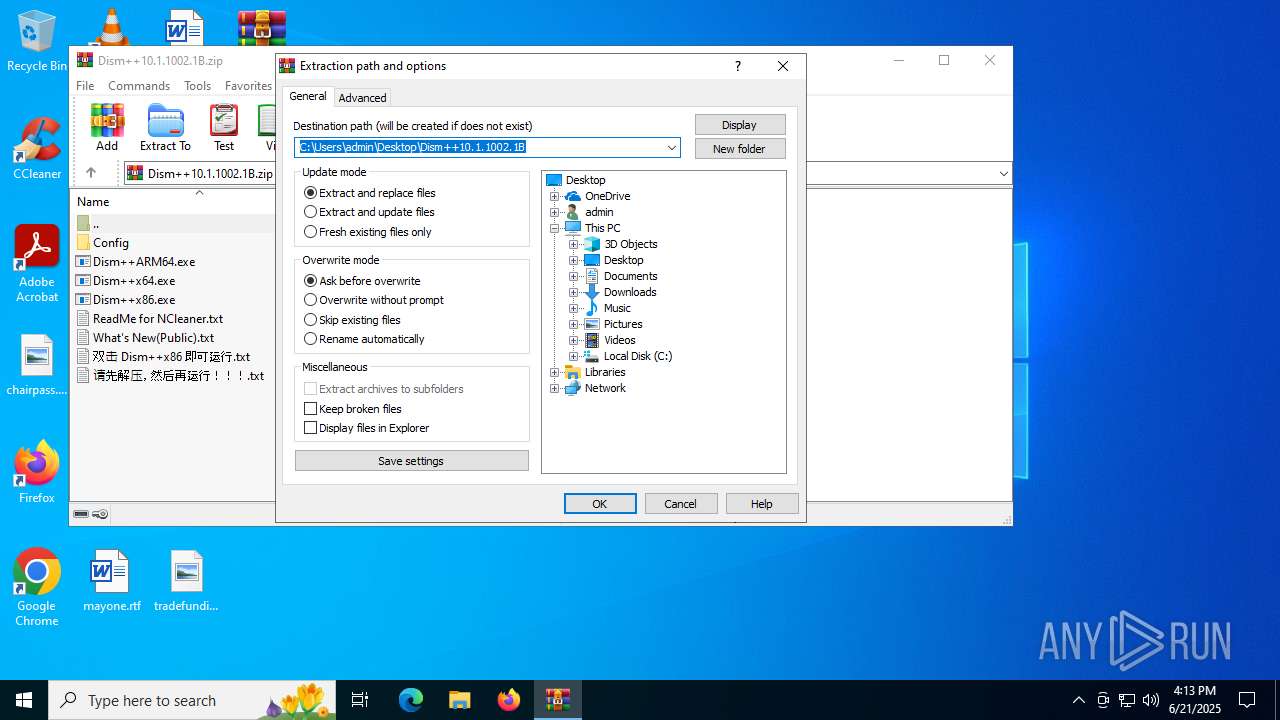
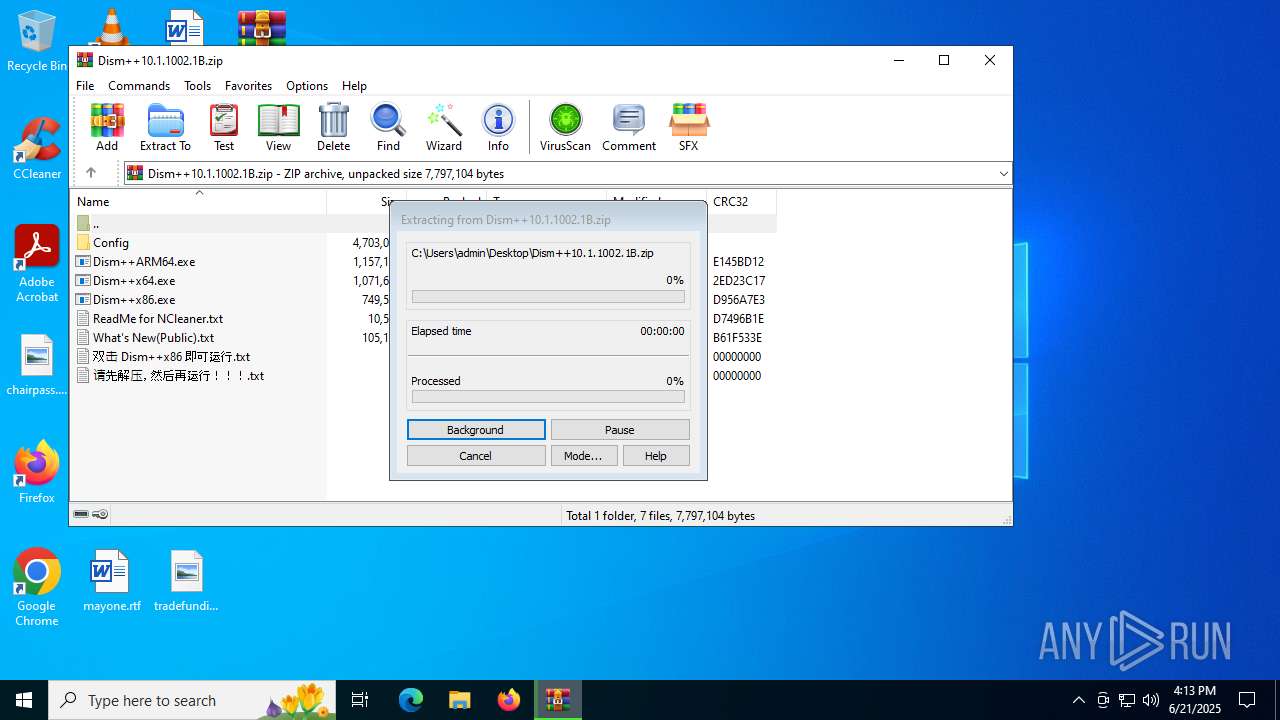
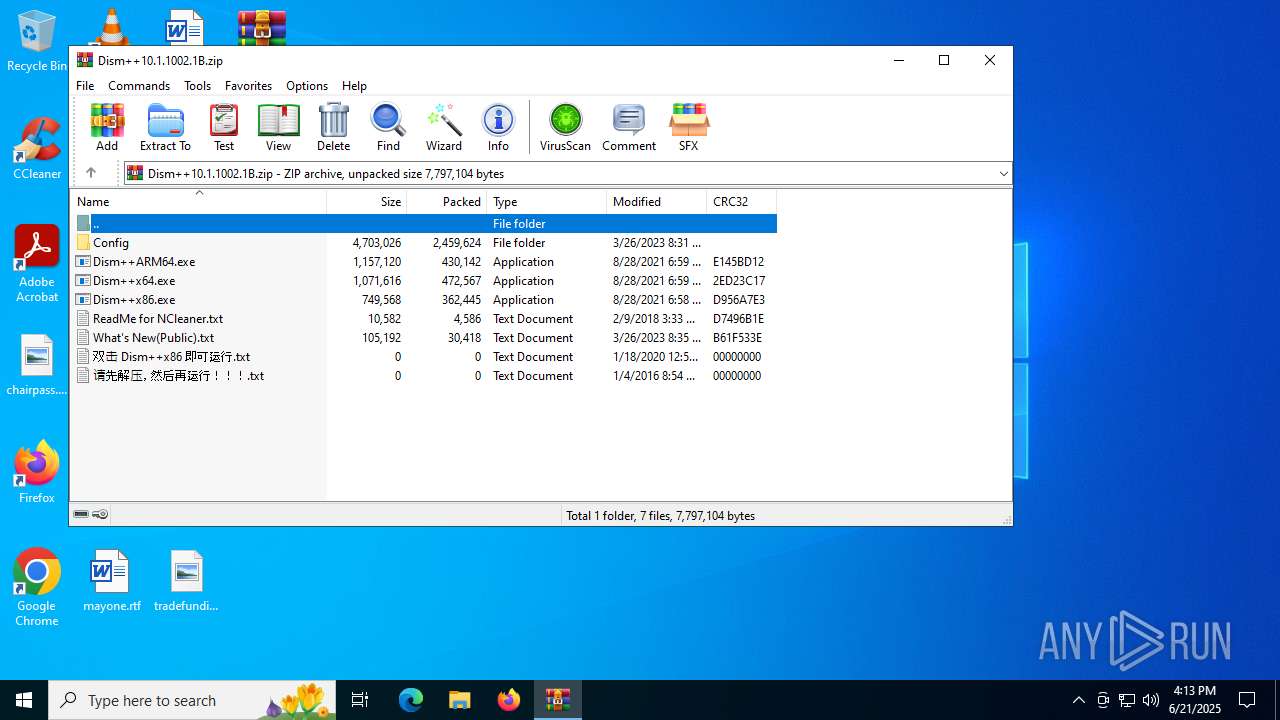
| 1068 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Dism++10.1.1002.1B.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
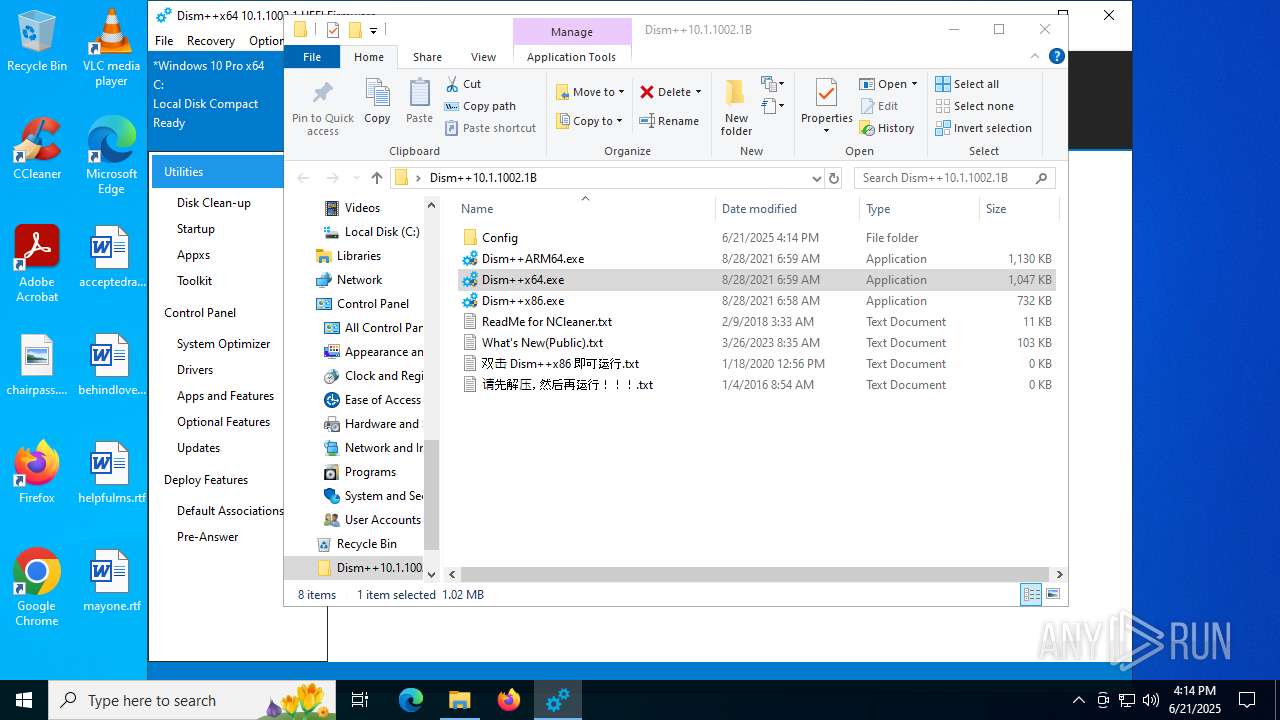
| 4196 | "C:\Users\admin\Desktop\Dism++10.1.1002.1B\Dism++x64.exe" | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Dism++x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Chuyu Team Integrity Level: MEDIUM Description: Dism++主程序 Exit code: 3221226540 Version: 10.1.1002.1 Modules
| |||||||||||||||
| 6232 | rundll32 "C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\amd64\CBSHost.dll",RunCbsHost {bbd473d3-2e10-4514-b9ba-f60339a7e844} "C:" "\\?\C:\Windows\Temp\\" 000000000000020C 4 | C:\Windows\System32\rundll32.exe | — | Dism++x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | "C:\Users\admin\Desktop\Dism++10.1.1002.1B\Dism++x64.exe" | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Dism++x64.exe | explorer.exe | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Version: 10.1.1002.1 Modules
| |||||||||||||||
Total events
2 649
Read events
2 611
Write events
24
Delete events
14
Modification events
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Dism++10.1.1002.1B.zip | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1068) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
19
Suspicious files
18
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
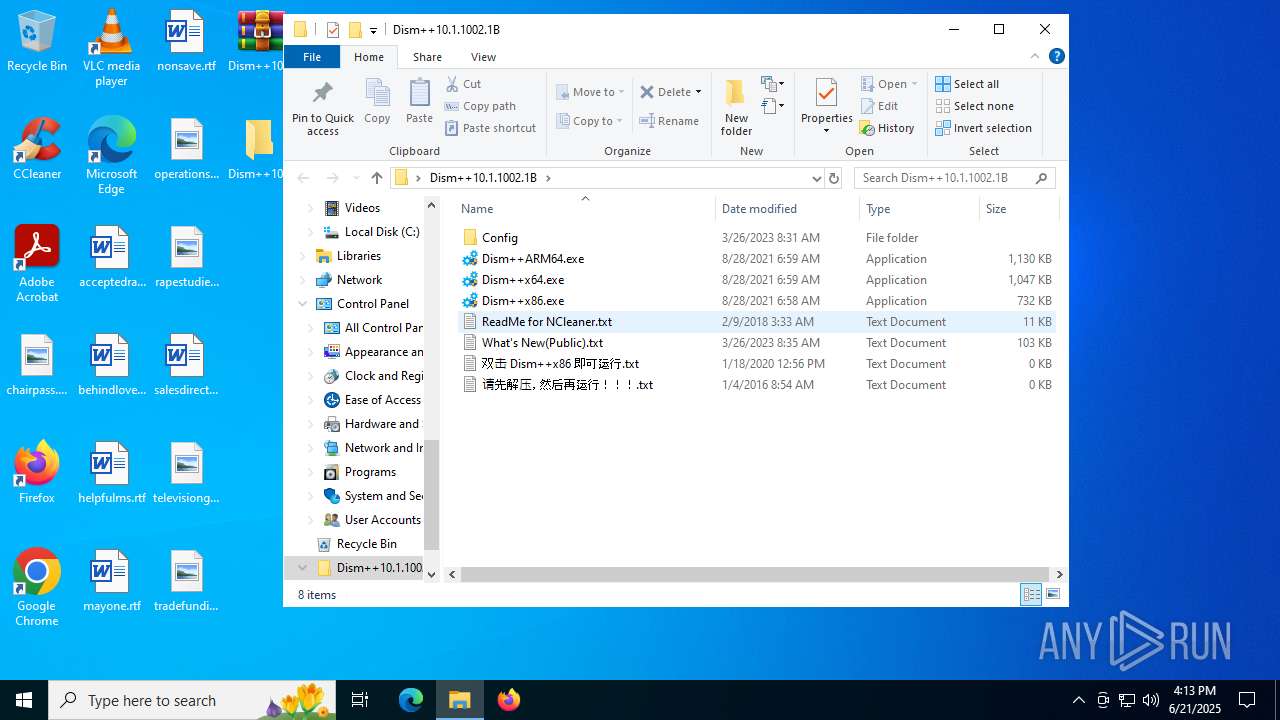
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\amd64\bcdboot.exe | executable | |
MD5:BE14BE7C8F7F0F4E397B89979CB9CF6B | SHA256:309F3ECCB0093CC6CC98F858BD3CE67B00BB810728FFB177B7BD287FB3C92B97 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\arm64\CBSHost.dll | executable | |
MD5:D81098BEC9F475C3A86E0FA38AEAA537 | SHA256:9CAEBB88BA8F4087273BDC07F37B260A15DC2C7B4058FFAC77A147ED1A27C032 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\arm64\NCleaner.dll | executable | |
MD5:6F7A31F96E95D9467F755EC806B768EC | SHA256:62BF4BCD3B3207E9BB8A4097684605A732E820968A9A8835A0F39E9BB67B26F7 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\amd64\NCleaner.dll | executable | |
MD5:C2058BCB1607FFB1A9FEFD67C2E8F94A | SHA256:141587AD11529D238DC7B63D7F30002FF042C3B06282D075E44E9C5AF07CCC17 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\default.ui.zip | compressed | |
MD5:E4B7BEF45A8F48832BA59396509DCB76 | SHA256:1A90365AC33C37EEAE4DD712F84062466C10948CF5B567574055E0B8B0F70534 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\amd64\wofadk.sys | executable | |
MD5:FBA28D5AC166714737D1D8CDF0AEF078 | SHA256:54FBA1CC80E820B462229FCB987FB8DF2321ED85D9450F3F4A81D0982E5D289F | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\Languages\bg.zip | compressed | |
MD5:D2EFE76E6991016EA78D7E65DB60A640 | SHA256:A9A1C127DF4BC6A7D420F209FD3D5BEEBD01454CF0CAFFC486D7509A9C50B7F2 | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\Data.zip | compressed | |
MD5:C3DF4642551B01EE38BC10BC4A06BAD6 | SHA256:8D524539F83A6416DBB4FDDE697A4BD8D870DDF25B162E874BFC9C56122A03DC | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\amd64\CBSHost.dll | executable | |
MD5:DD139DF87A896B894335E03ECE2973BF | SHA256:6A1075F4FAB4ACD2722E8946CBA7B23508D120367C84AAE3E83284124227013A | |||
| 1068 | WinRAR.exe | C:\Users\admin\Desktop\Dism++10.1.1002.1B\Config\Languages\hu.zip | compressed | |
MD5:41A6E34AE471CC90B9726944F7A62EA1 | SHA256:0842FEC9C602D3B2C265C575EB9DCD019E3754F5E0DD8AB1D21F360942BFD636 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5012 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5744 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5744 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3876 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5012 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5012 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 184.24.77.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |