| File name: | sm64pcBuilder2.exe |
| Full analysis: | https://app.any.run/tasks/48098940-1afb-4abb-ba6e-9f0c1bc8d8c5 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 11:14:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A609598CB83EB5D5BFA4CD5A60F14E07 |
| SHA1: | 11F6E226E3319F1FF46FC75E3D95D14DA1FC56DE |
| SHA256: | 5BB9B2F82FB416F957545F8F17C5114FAE4B8AEC6711A567A4DC5B86829D2AC7 |
| SSDEEP: | 49152:yR7zG2tHLpTeGowQeCPYdnQtD3KiWXmNE:yRpVTewQeM/tD6dXv |
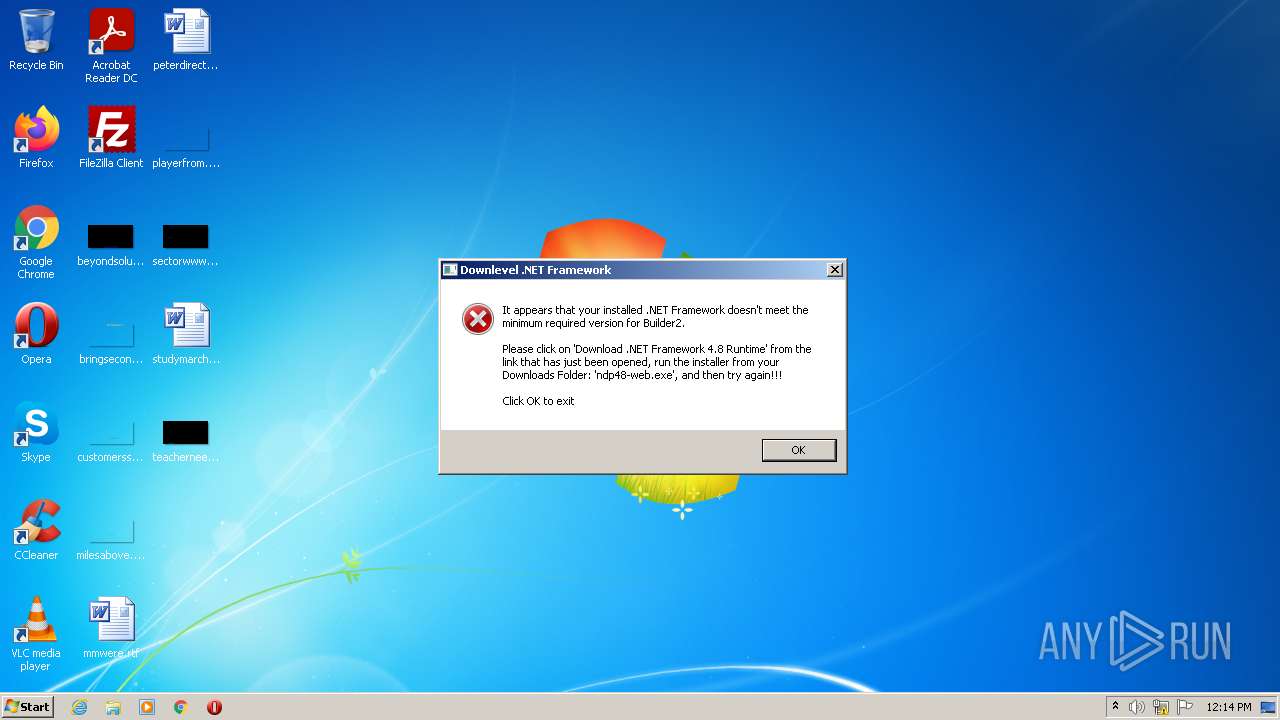
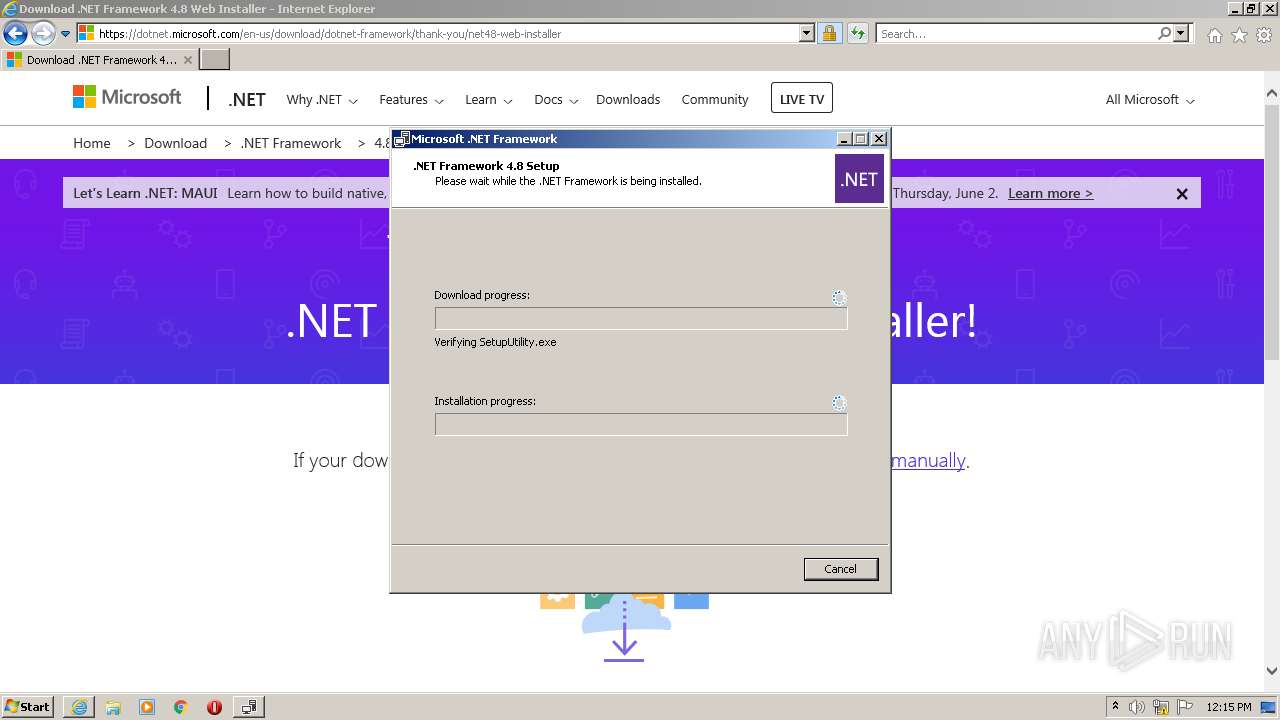
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 920)
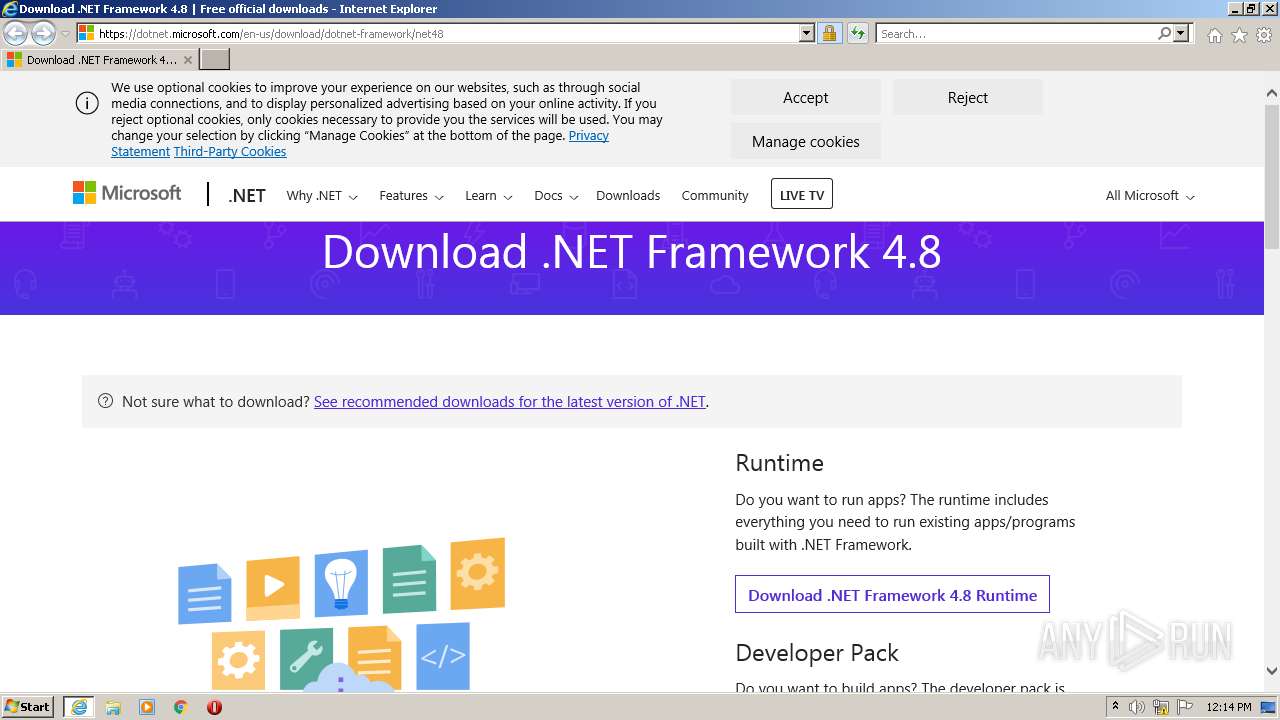
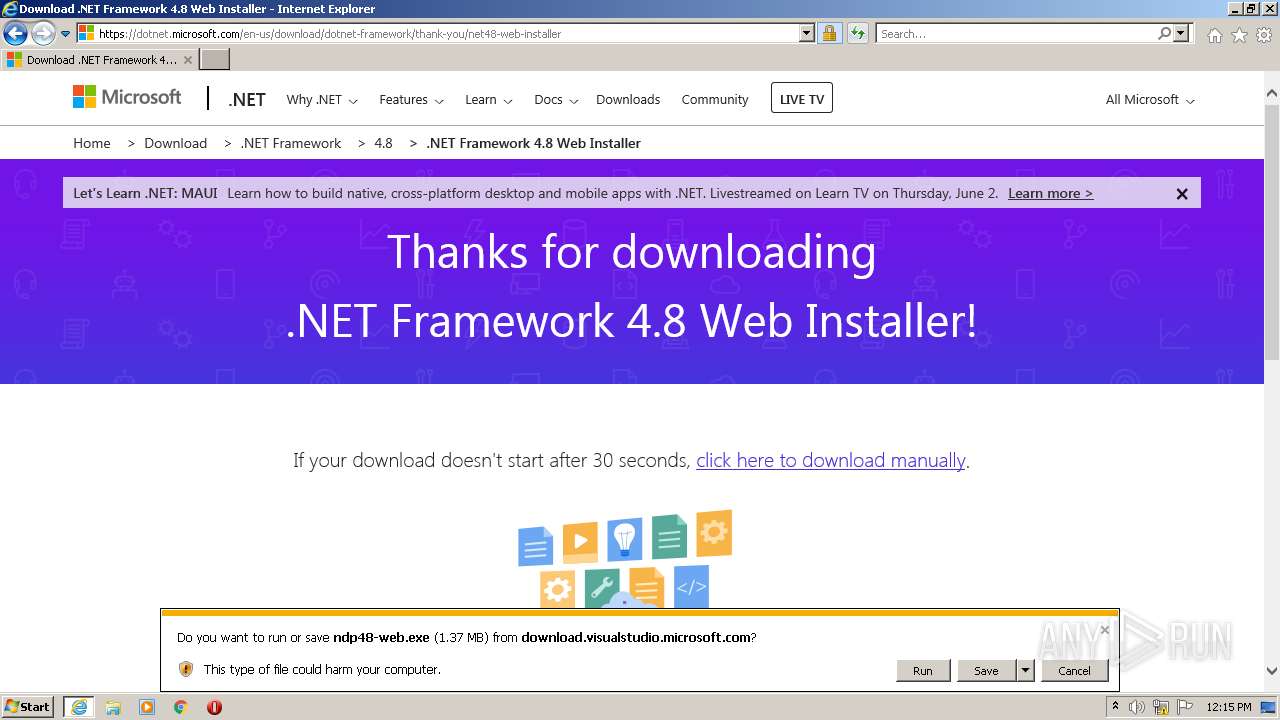
- ndp48-web.exe (PID: 924)
Application was dropped or rewritten from another process
- ndp48-web.exe (PID: 924)
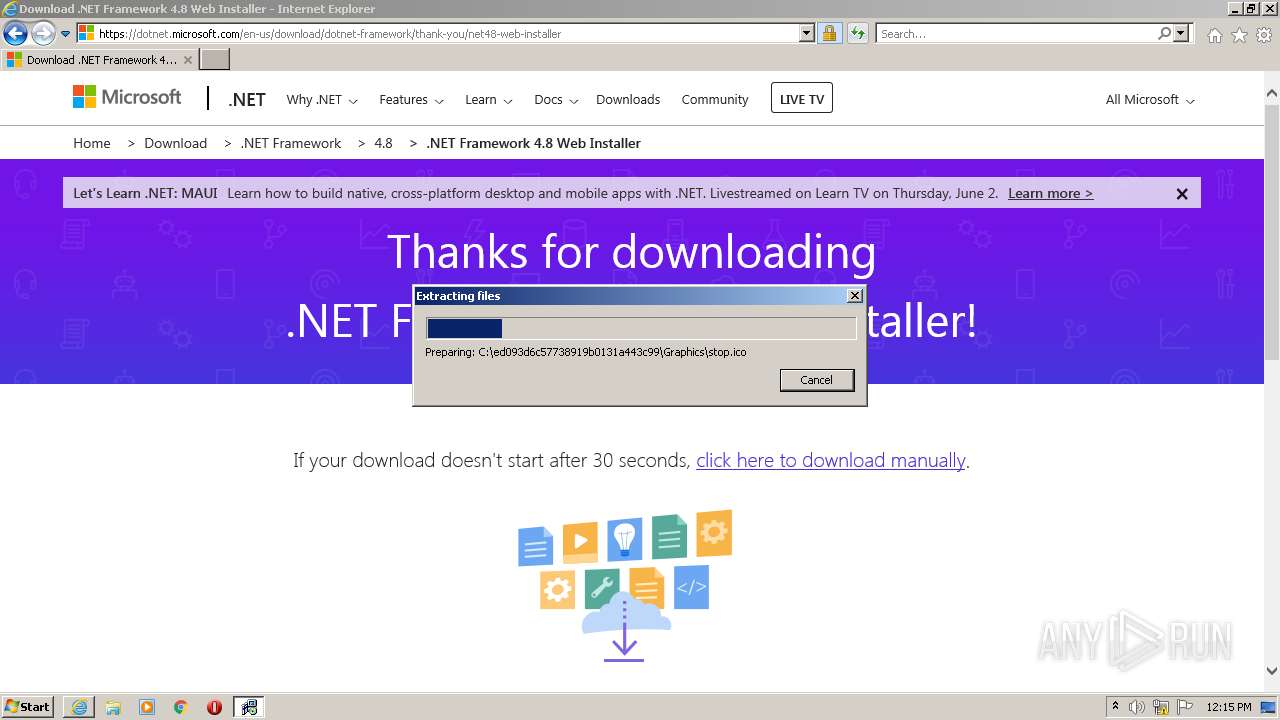
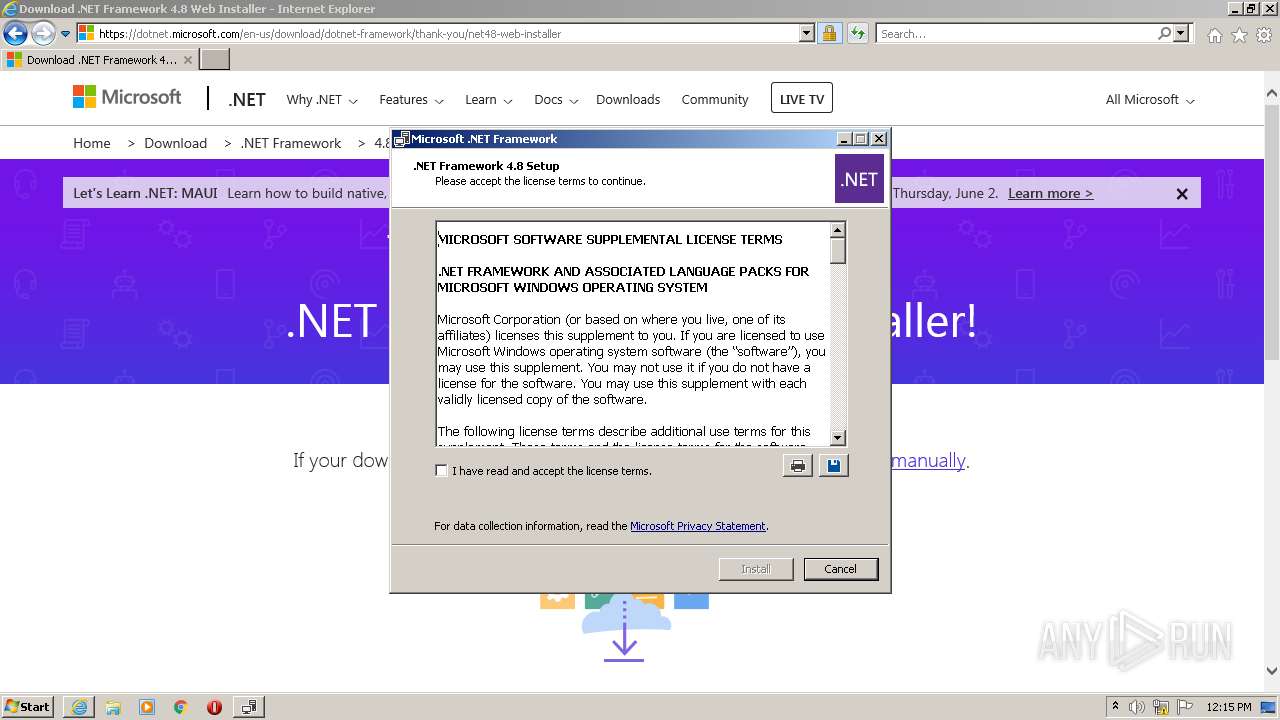
- Setup.exe (PID: 3700)
- SetupUtility.exe (PID: 3872)
- SetupUtility.exe (PID: 3148)
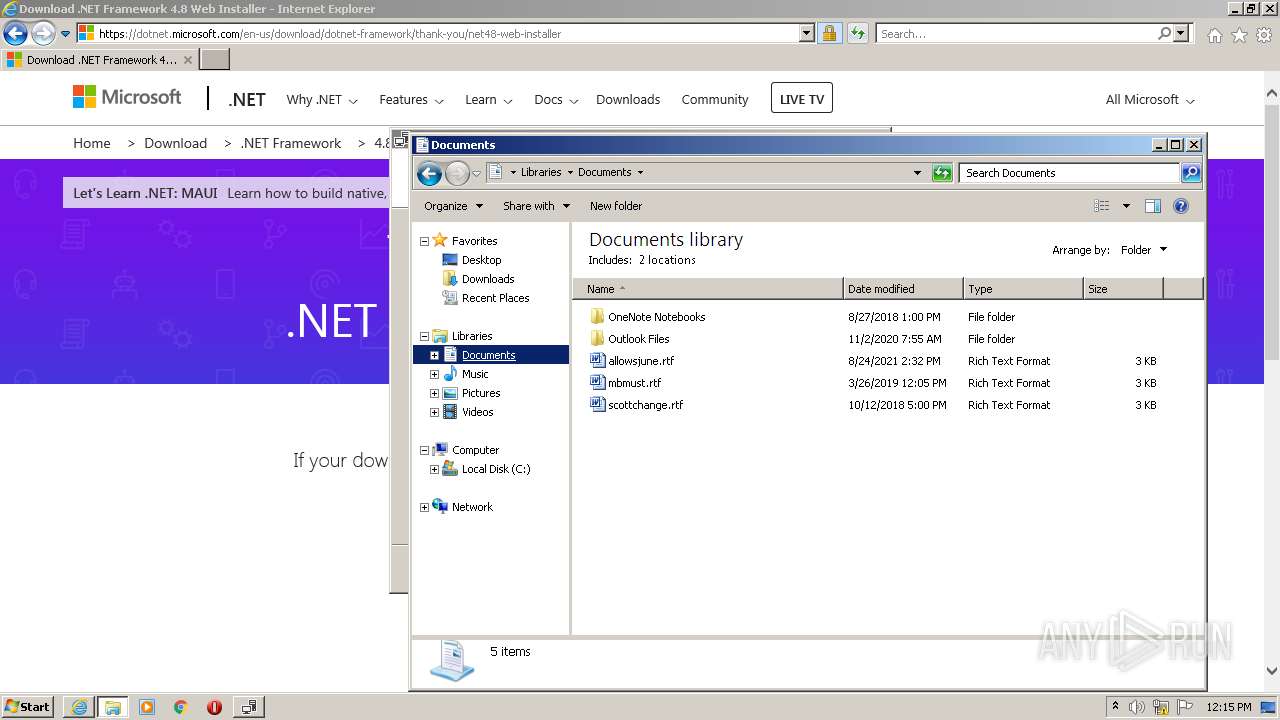
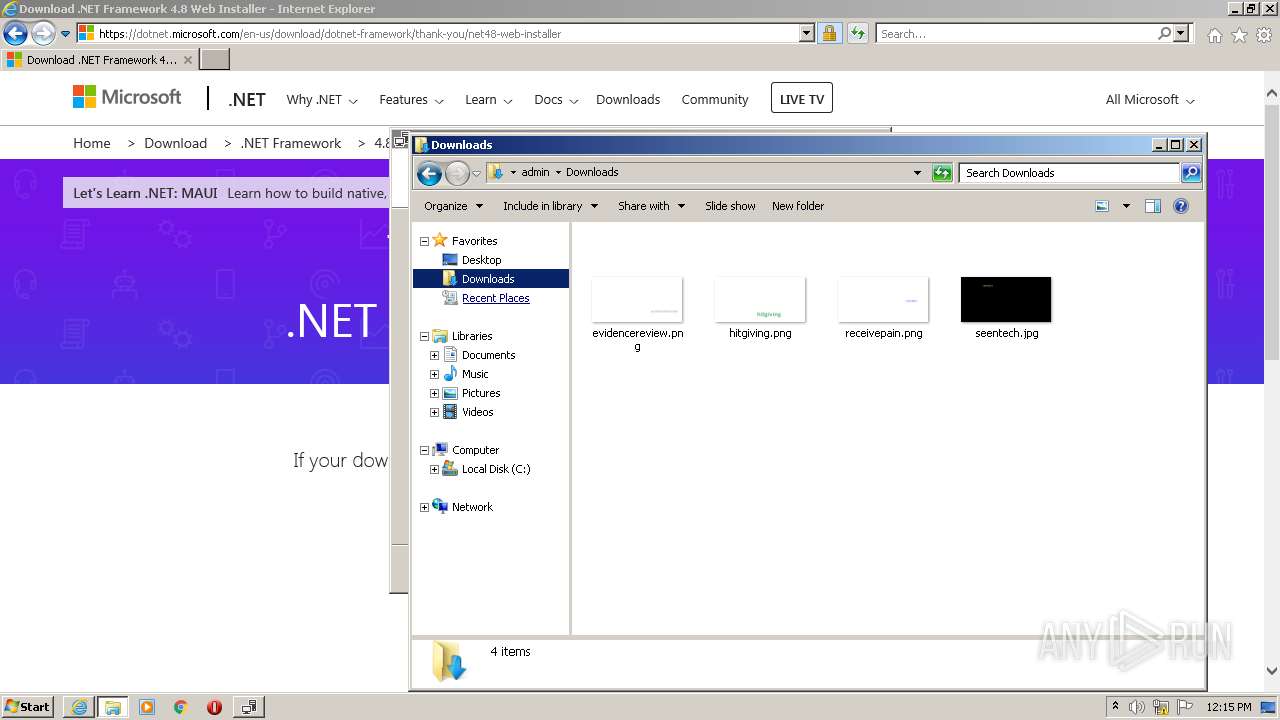
Actions looks like stealing of personal data
- ndp48-web.exe (PID: 924)
Loads dropped or rewritten executable
- Setup.exe (PID: 3700)
SUSPICIOUS
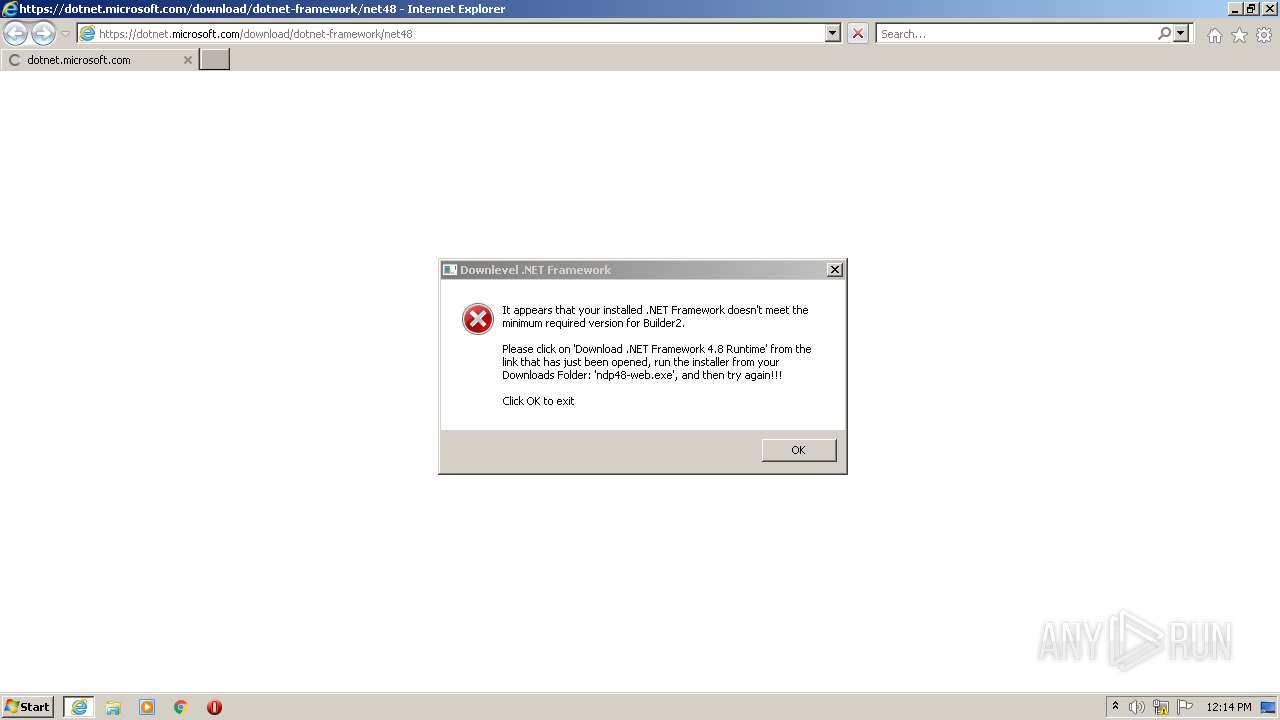
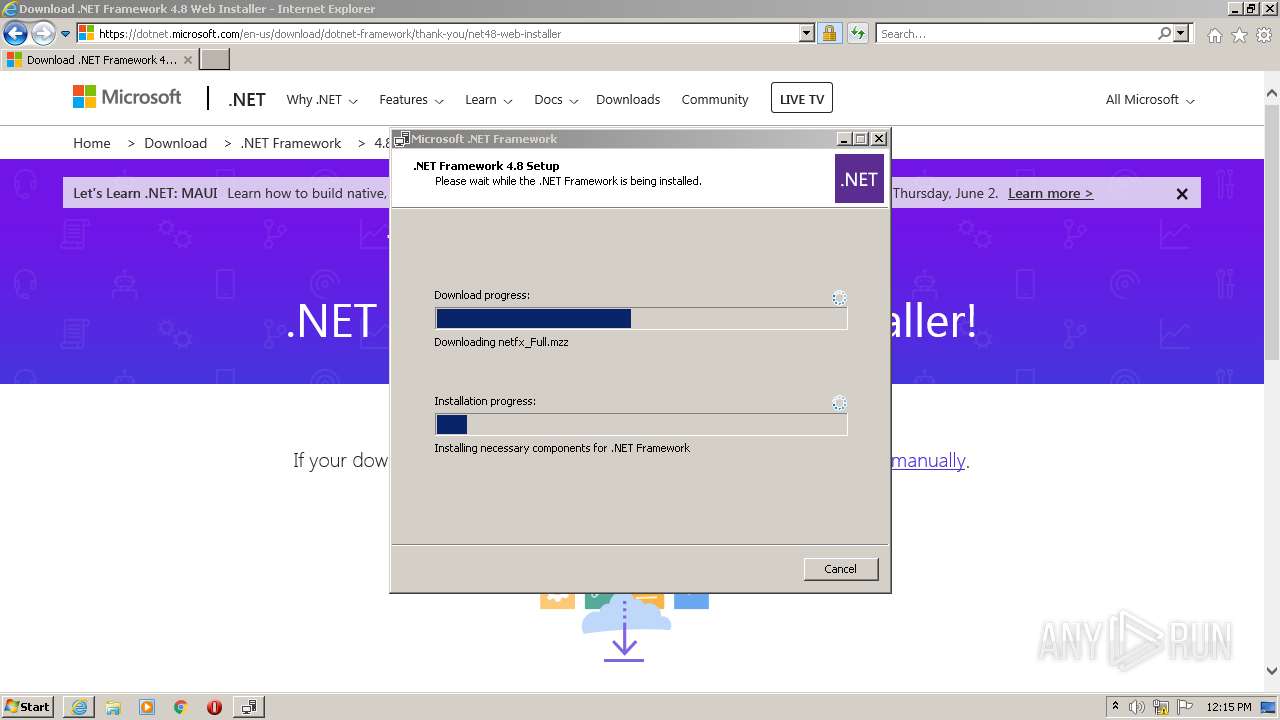
Starts Internet Explorer
- sm64pcBuilder2.exe (PID: 2492)
Checks supported languages
- sm64pcBuilder2.exe (PID: 2492)
- Setup.exe (PID: 3700)
- ndp48-web.exe (PID: 924)
- SetupUtility.exe (PID: 3872)
- SetupUtility.exe (PID: 3148)
Reads the computer name
- sm64pcBuilder2.exe (PID: 2492)
- ndp48-web.exe (PID: 924)
- Setup.exe (PID: 3700)
- SetupUtility.exe (PID: 3872)
- SetupUtility.exe (PID: 3148)
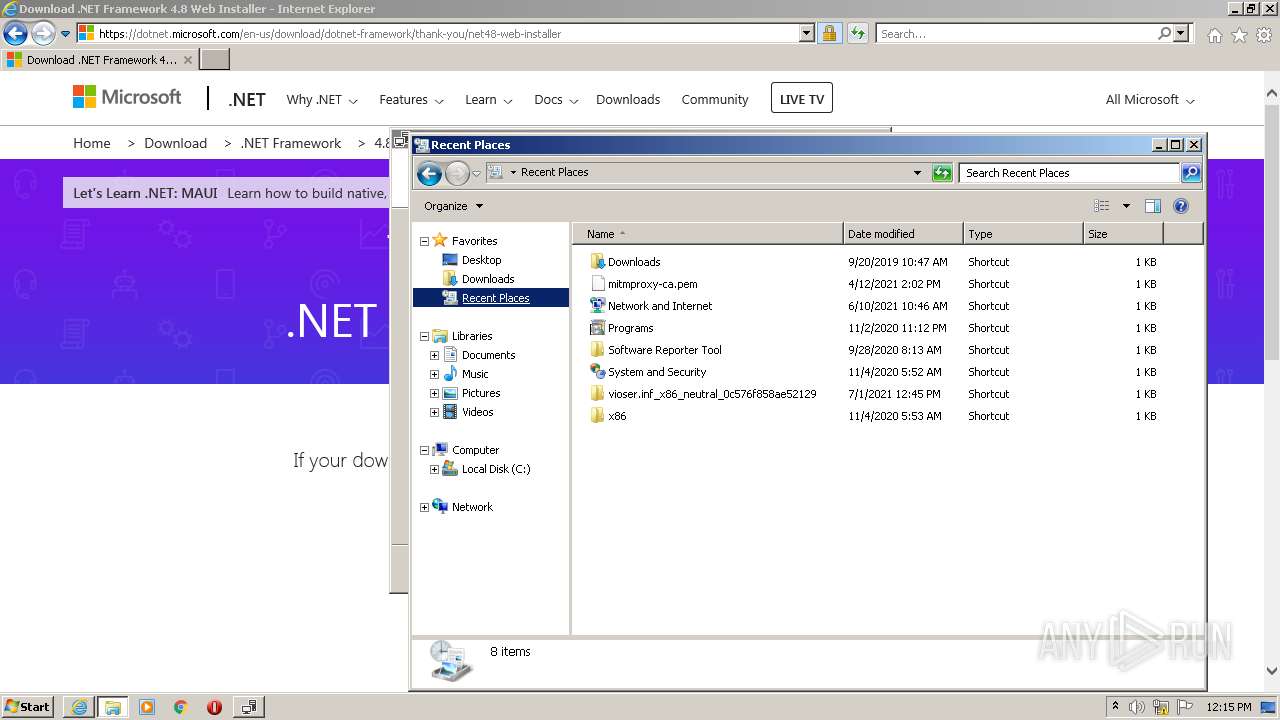
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1548)
Executable content was dropped or overwritten
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 920)
- ndp48-web.exe (PID: 924)
Drops a file with a compile date too recent
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 920)
- ndp48-web.exe (PID: 924)
Reads CPU info
- Setup.exe (PID: 3700)
Reads Environment values
- Setup.exe (PID: 3700)
INFO
Checks supported languages
- iexplore.exe (PID: 920)
- iexplore.exe (PID: 1548)
- explorer.exe (PID: 2100)
Reads the computer name
- iexplore.exe (PID: 920)
- iexplore.exe (PID: 1548)
- explorer.exe (PID: 2100)
Application launched itself
- iexplore.exe (PID: 920)
Changes internet zones settings
- iexplore.exe (PID: 920)
Reads settings of System Certificates
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 920)
- Setup.exe (PID: 3700)
Changes settings of System certificates
- iexplore.exe (PID: 1548)
Checks Windows Trust Settings
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 920)
- Setup.exe (PID: 3700)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1548)
Creates files in the user directory
- iexplore.exe (PID: 1548)
Reads internet explorer settings
- iexplore.exe (PID: 1548)
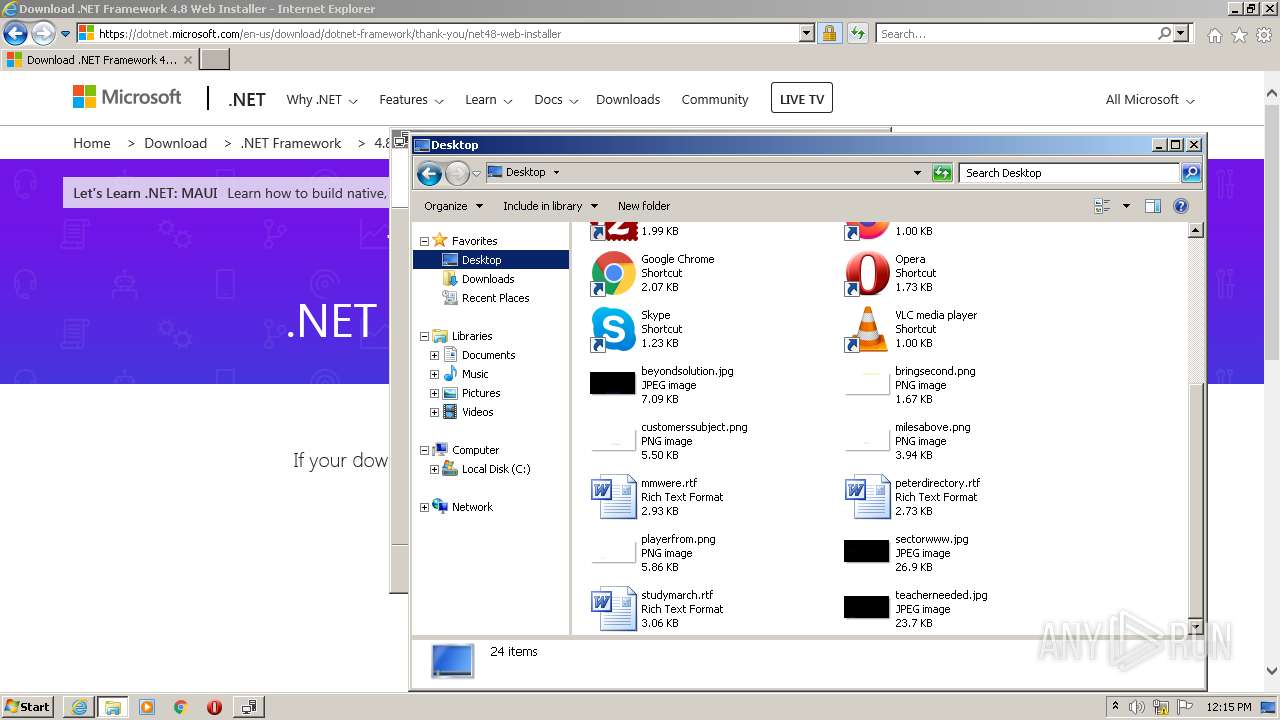
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1548)
- SetupUtility.exe (PID: 3872)
Modifies the phishing filter of IE
- iexplore.exe (PID: 920)
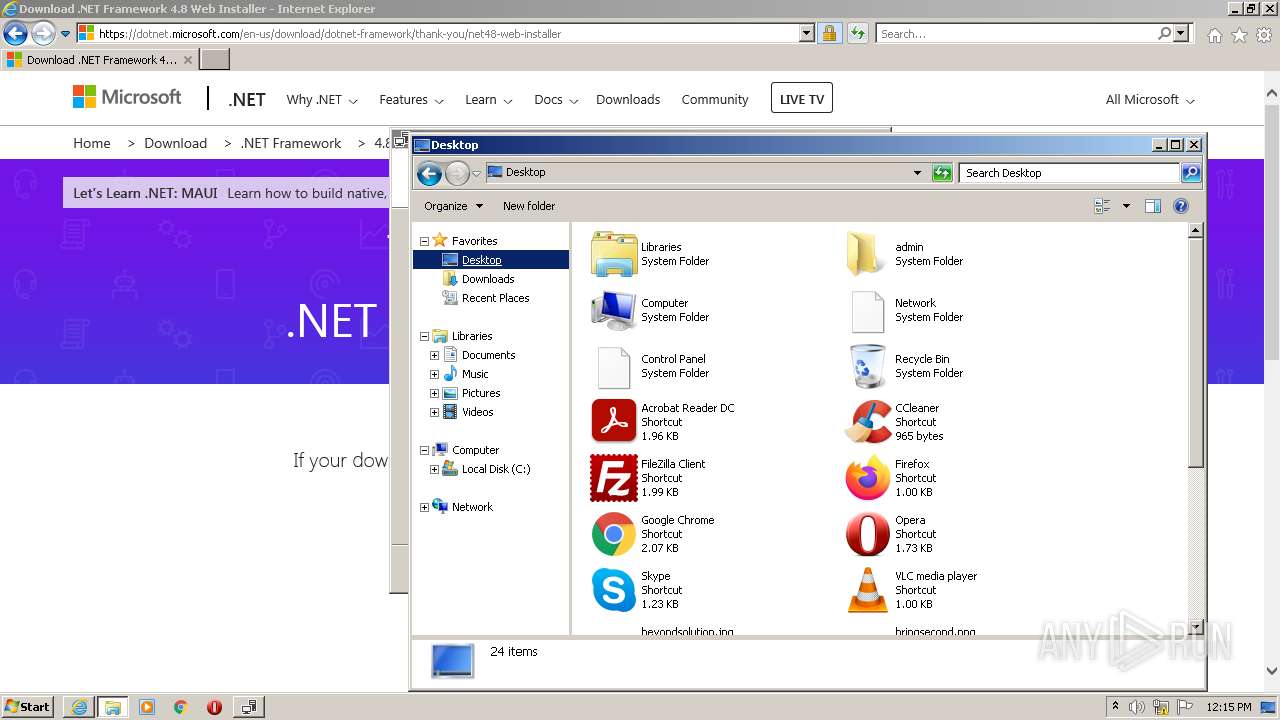
Manual execution by user
- explorer.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (46) |
|---|---|---|
| .exe | | | InstallShield setup (27) |
| .exe | | | Win64 Executable (generic) (17.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
EXIF
EXE
| ProductVersion: | 1.19.17.0 |
|---|---|
| ProductName: | sm64pcBuilder2 |
| OriginalFileName: | sm64pcBuilder2.exe |
| LegalCopyright: | Copyright © 2020-2022 |
| InternalName: | sm64pcBuilder2.exe |
| FileVersion: | 1.19.17.0 |
| FileDescription: | sm64pcBuilder2 |
| CompanyName: | gunvalk-Filipianosol-GTN |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.19.17.0 |
| FileVersionNumber: | 1.19.17.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1c323a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 467456 |
| CodeSize: | 1841152 |
| LinkerVersion: | 80 |
| PEType: | PE32 |
| TimeStamp: | 2057:09:18 01:43:56+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Aug-1921 17:15:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | gunvalk-Filipianosol-GTN |
| FileDescription: | sm64pcBuilder2 |
| FileVersion: | 1.19.17.0 |
| InternalName: | sm64pcBuilder2.exe |
| LegalCopyright: | Copyright © 2020-2022 |
| OriginalFilename: | sm64pcBuilder2.exe |
| ProductName: | sm64pcBuilder2 |
| ProductVersion: | 1.19.17.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Aug-1921 17:15:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x001C16F0 | 0x001C1800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.58034 |
.rsrc | 0x001C4000 | 0x00071ED0 | 0x00072000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37725 |
.reloc | 0x00236000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 3.07474 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
1 | 5.00018 | 3107 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.10923 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 3.14528 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
4 | 3.01731 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.71468 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.97868 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 7.88402 | 15041 | UNKNOWN | English - United States | RT_ICON |
8 | 3.53255 | 67624 | UNKNOWN | English - United States | RT_ICON |
9 | 4.05082 | 16936 | UNKNOWN | English - United States | RT_ICON |
Imports
mscoree.dll |
Total processes
50
Monitored processes
9
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
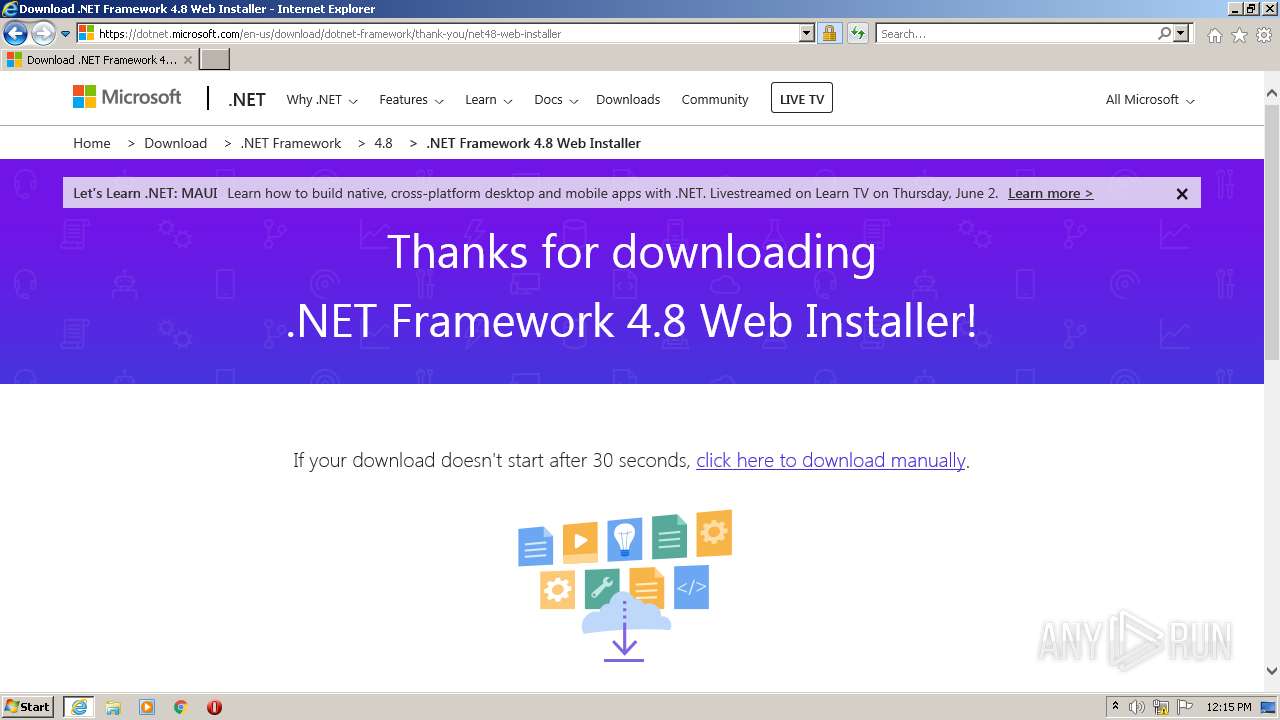
| 920 | "C:\Program Files\Internet Explorer\iexplore.exe" https://dotnet.microsoft.com/download/dotnet-framework/net48 | C:\Program Files\Internet Explorer\iexplore.exe | sm64pcBuilder2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 924 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ndp48-web.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ndp48-web.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.04115.00 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\sm64pcBuilder2.exe" | C:\Users\admin\AppData\Local\Temp\sm64pcBuilder2.exe | — | Explorer.EXE | |||||||||||
User: admin Company: gunvalk-Filipianosol-GTN Integrity Level: MEDIUM Description: sm64pcBuilder2 Exit code: 3221226540 Version: 1.19.17.0 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:920 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2100 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\AppData\Local\Temp\sm64pcBuilder2.exe" | C:\Users\admin\AppData\Local\Temp\sm64pcBuilder2.exe | Explorer.EXE | ||||||||||||
User: admin Company: gunvalk-Filipianosol-GTN Integrity Level: HIGH Description: sm64pcBuilder2 Exit code: 0 Version: 1.19.17.0 Modules
| |||||||||||||||
| 3148 | SetupUtility.exe /screboot | C:\ed093d6c57738919b0131a443c99\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 3700 | C:\ed093d6c57738919b0131a443c99\\Setup.exe /x86 /x64 /web | C:\ed093d6c57738919b0131a443c99\Setup.exe | ndp48-web.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 3872 | SetupUtility.exe /aupause | C:\ed093d6c57738919b0131a443c99\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
Total events
23 175
Read events
22 961
Write events
214
Delete events
0
Modification events
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960899 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 226749850 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960900 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
32
Suspicious files
15
Text files
121
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\net48[1].htm | html | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | der | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8PZQ55XO.txt | text | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\bootstrap-custom.min[1].css | text | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_AD319D6DA1A11BC83AC8B4E4D3638231 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
43
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 104.89.38.104:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | NL | — | — | whitelisted |
— | — | GET | 302 | 104.89.38.104:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | NL | — | — | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3700 | Setup.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 1.05 Kb | whitelisted |
3700 | Setup.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | US | der | 1.11 Kb | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1548 | iexplore.exe | 8.238.38.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
1548 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
920 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1548 | iexplore.exe | 2.18.233.62:443 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
1548 | iexplore.exe | 152.199.19.161:443 | az416426.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1548 | iexplore.exe | 23.216.77.206:443 | img-prod-cms-rt-microsoft-com.akamaized.net | NTT DOCOMO, INC. | US | whitelisted |
1548 | iexplore.exe | 23.216.77.205:443 | statics-marketingsites-wcus-ms-com.akamaized.net | NTT DOCOMO, INC. | US | suspicious |
1548 | iexplore.exe | 131.253.33.203:80 | oneocsp.microsoft.com | Microsoft Corporation | US | malicious |
920 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1548 | iexplore.exe | 52.236.186.218:443 | dc.services.visualstudio.com | Microsoft Corporation | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dotnet.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
az416426.vo.msecnd.net |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
wcpstatic.microsoft.com |
| whitelisted |