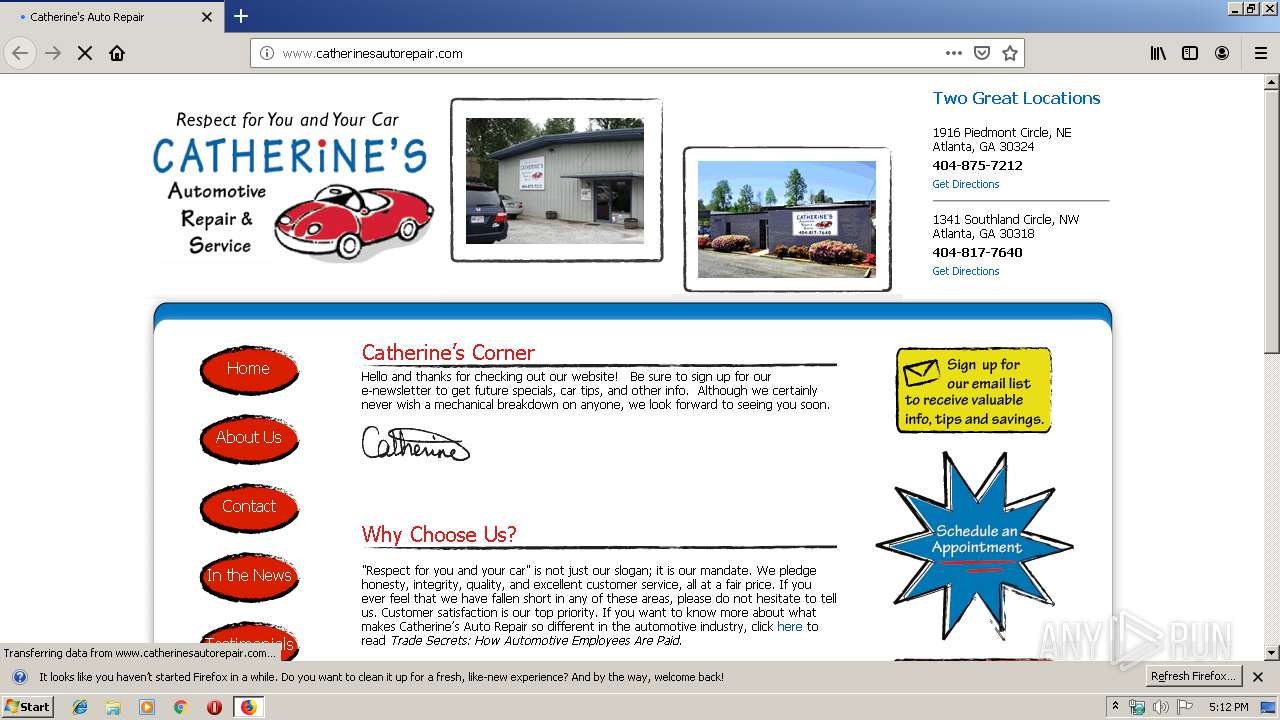
| URL: | http://www.catherinesautorepair.com/ |
| Full analysis: | https://app.any.run/tasks/5233b04c-a042-4ea7-8c24-6712fdcb35d4 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 17:11:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6C5D698C1E2ADC52DD6A0068913703CF |
| SHA1: | 388233DAB2E03ADE0A18EC3CCC1C5CE00F80AFE2 |
| SHA256: | 5BB775C6F8238AC87859A65FE5EEE026EF92A9197B905A5EEDFB91B110364305 |
| SSDEEP: | 3:N1KJS4dFLzEEKANyTKn:Cc4KAN2Kn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 408)
INFO
Application launched itself
- firefox.exe (PID: 408)
Reads Internet Cache Settings
- firefox.exe (PID: 408)
Reads CPU info
- firefox.exe (PID: 408)
Creates files in the user directory
- firefox.exe (PID: 408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://www.catherinesautorepair.com/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://www.catherinesautorepair.com/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="408.13.1389795052\815133544" -childID 2 -isForBrowser -prefsHandle 2904 -prefMapHandle 2908 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 408 "\\.\pipe\gecko-crash-server-pipe.408" 2920 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="408.0.43858104\646726711" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 408 "\\.\pipe\gecko-crash-server-pipe.408" 1152 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="408.3.1313555930\489307633" -childID 1 -isForBrowser -prefsHandle 1688 -prefMapHandle 1684 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 408 "\\.\pipe\gecko-crash-server-pipe.408" 1708 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3884 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="408.20.196278895\1372974361" -childID 3 -isForBrowser -prefsHandle 3808 -prefMapHandle 3812 -prefsLen 7297 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 408 "\\.\pipe\gecko-crash-server-pipe.408" 3824 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
699
Read events
694
Write events
5
Delete events
0
Modification events
| (PID) Process: | (944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: F86C101803000000 | |||
| (PID) Process: | (408) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 4460131803000000 | |||
| (PID) Process: | (408) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (408) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (408) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
75
Text files
37
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
40
DNS requests
98
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
408 | firefox.exe | GET | 301 | 209.104.5.212:80 | http://posting.clatl.com/images/blogimages/2014/09/18/1411054580-boa14_winner_badge145px.png | US | — | — | unknown |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/wp-content/themes/catherines-auto/images/nav.png | US | image | 1.77 Kb | unknown |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/ | US | html | 11.8 Kb | unknown |
408 | firefox.exe | GET | 200 | 104.109.71.236:80 | http://content.angieslist.com/cms/widgets/insertwebbadge.js | NL | html | 1.04 Kb | suspicious |
408 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/wp-content/uploads/2010/11/catherines-autorepair2.gif | US | image | 10.8 Kb | unknown |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/wp-content/uploads/2010/11/AAA_autoRepair.png | US | image | 6.26 Kb | unknown |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/wp-content/themes/catherines-auto/style.css | US | text | 15.0 Kb | unknown |
408 | firefox.exe | GET | 200 | 98.129.229.75:80 | http://www.catherinesautorepair.com/wp-content/uploads/2011/02/southland-circle.gif | US | image | 237 Kb | unknown |
408 | firefox.exe | GET | 200 | 104.109.71.236:80 | http://content.angieslist.com/cms/widgets/ssa-2010-award-125.png | NL | image | 3.09 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
408 | firefox.exe | 52.35.182.58:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
408 | firefox.exe | 34.210.150.241:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
408 | firefox.exe | 52.33.184.165:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
408 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
408 | firefox.exe | 209.104.5.212:80 | posting.clatl.com | Login, Inc. | US | unknown |
408 | firefox.exe | 104.109.71.236:80 | content.angieslist.com | Akamai International B.V. | NL | unknown |
408 | firefox.exe | 208.53.52.25:80 | images.iatn.net | C7 Data Centers, Inc. | US | unknown |
408 | firefox.exe | 13.32.158.23:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
408 | firefox.exe | 143.204.214.118:443 | snippets.cdn.mozilla.net | — | US | suspicious |
408 | firefox.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.catherinesautorepair.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | A Network Trojan was detected | ET WEB_CLIENT Observed DNS Query to Malicious Cookie Monster Roulette JS Cookie Stealer Exfil Domain |
1080 | svchost.exe | A Network Trojan was detected | ET WEB_CLIENT Observed DNS Query to Malicious Cookie Monster Roulette JS Cookie Stealer Exfil Domain |
1080 | svchost.exe | A Network Trojan was detected | ET WEB_CLIENT Observed DNS Query to Malicious Cookie Monster Roulette JS Cookie Stealer Exfil Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report