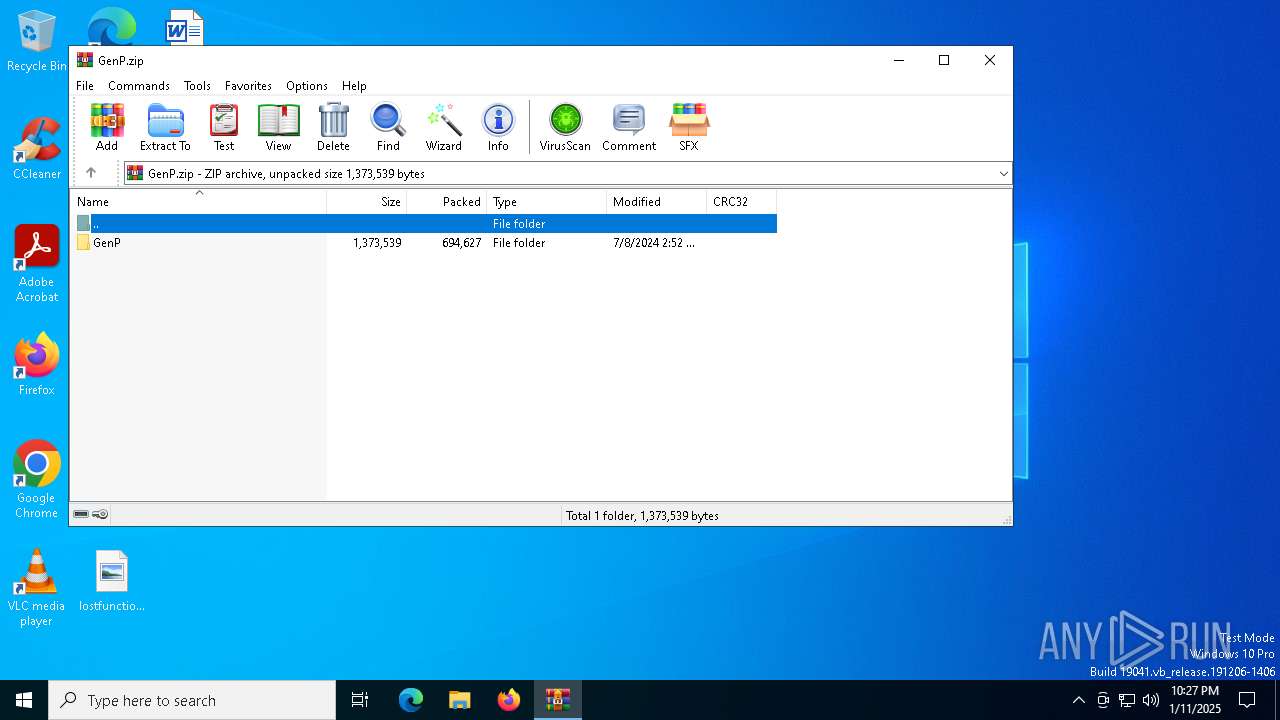
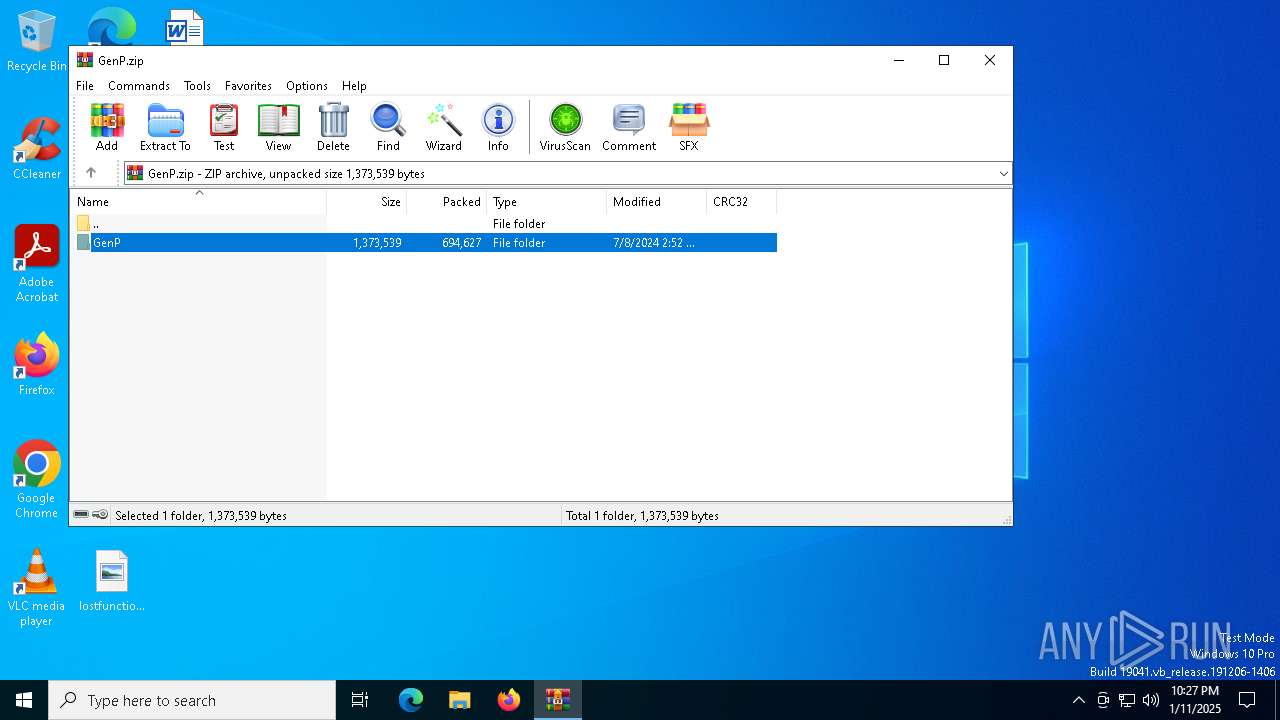
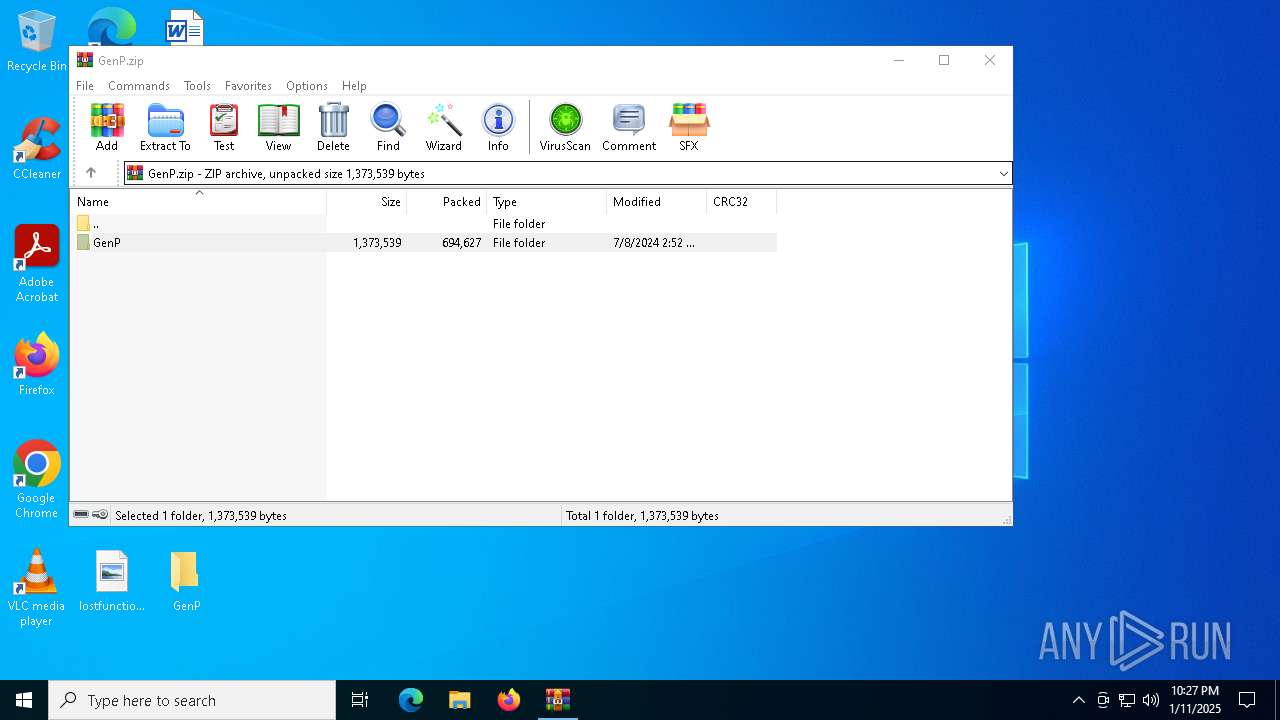
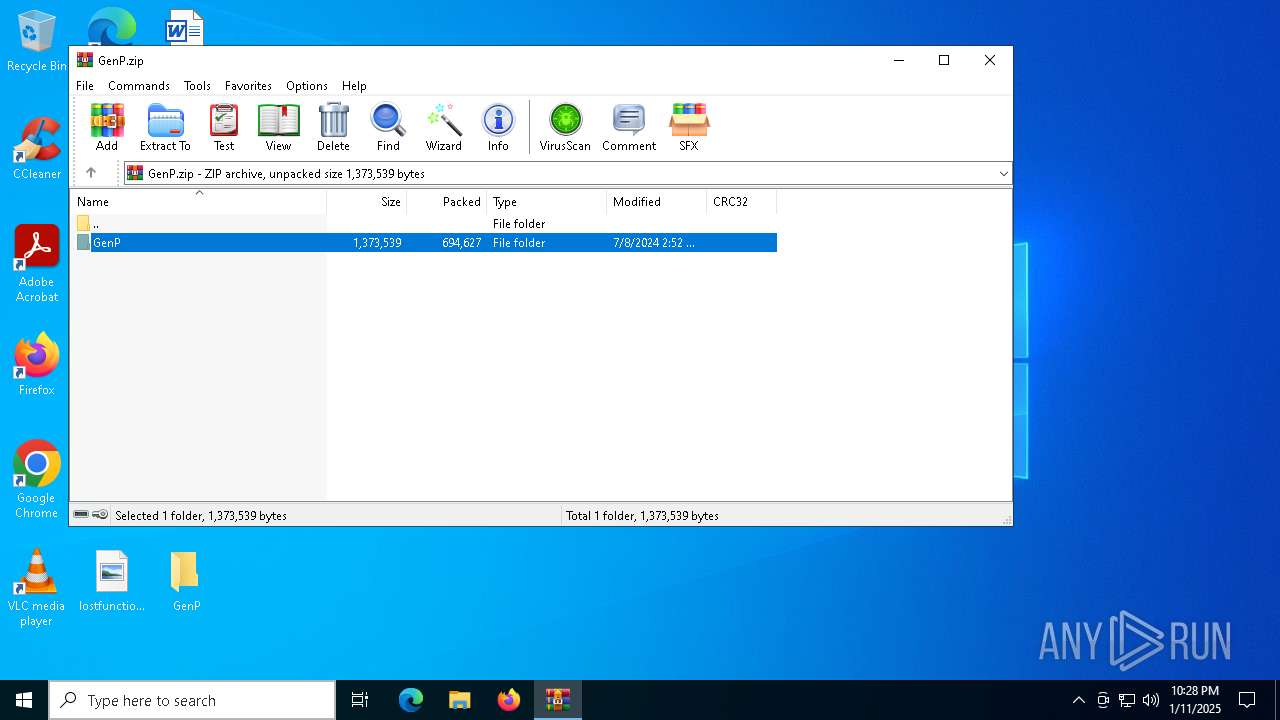
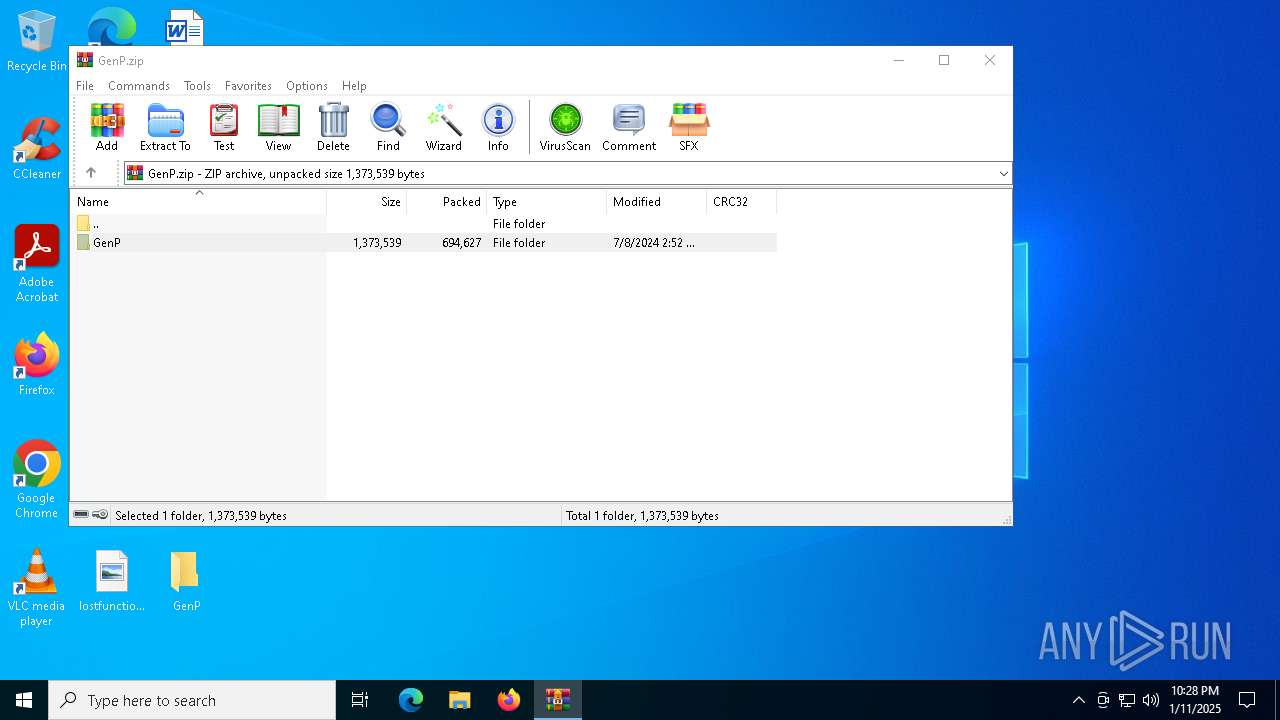
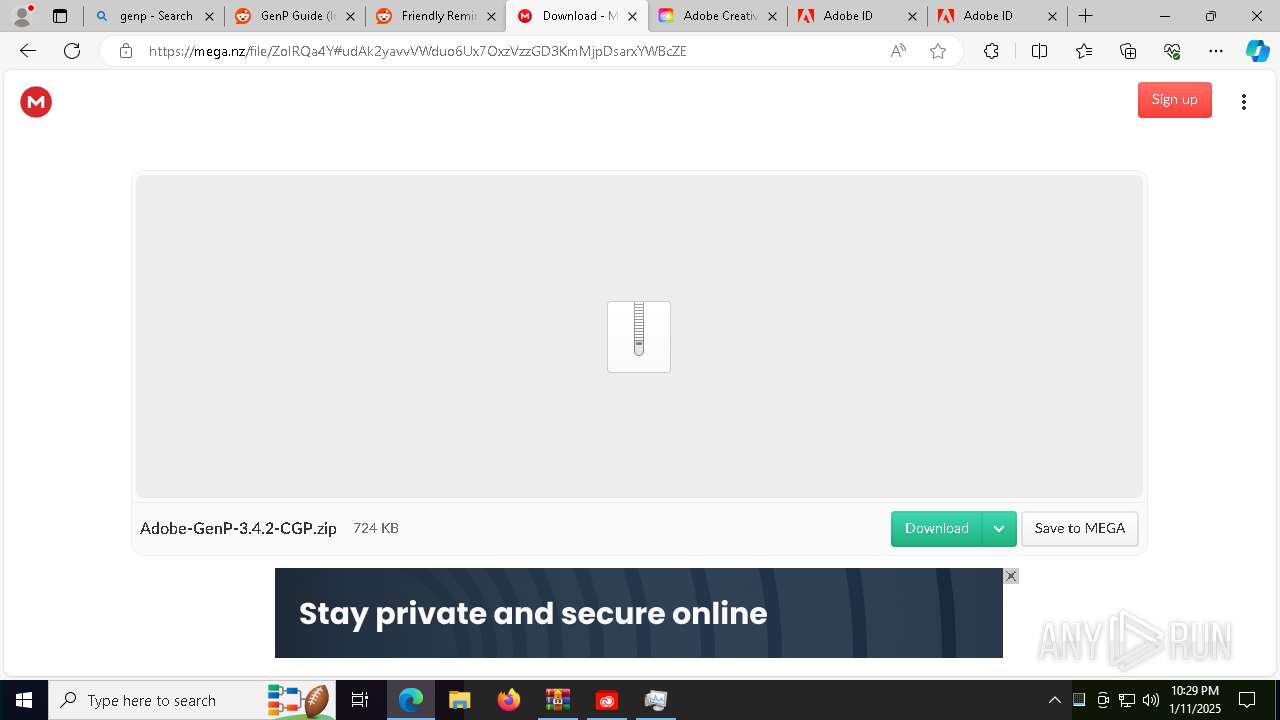
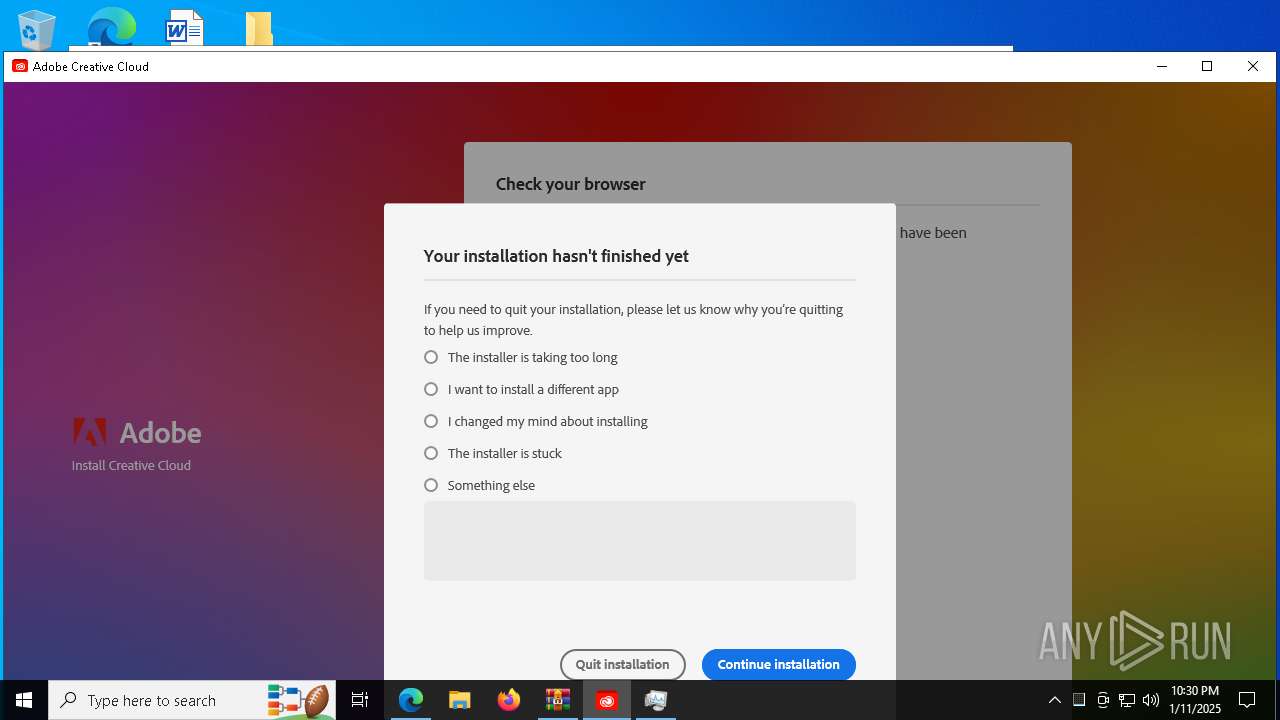
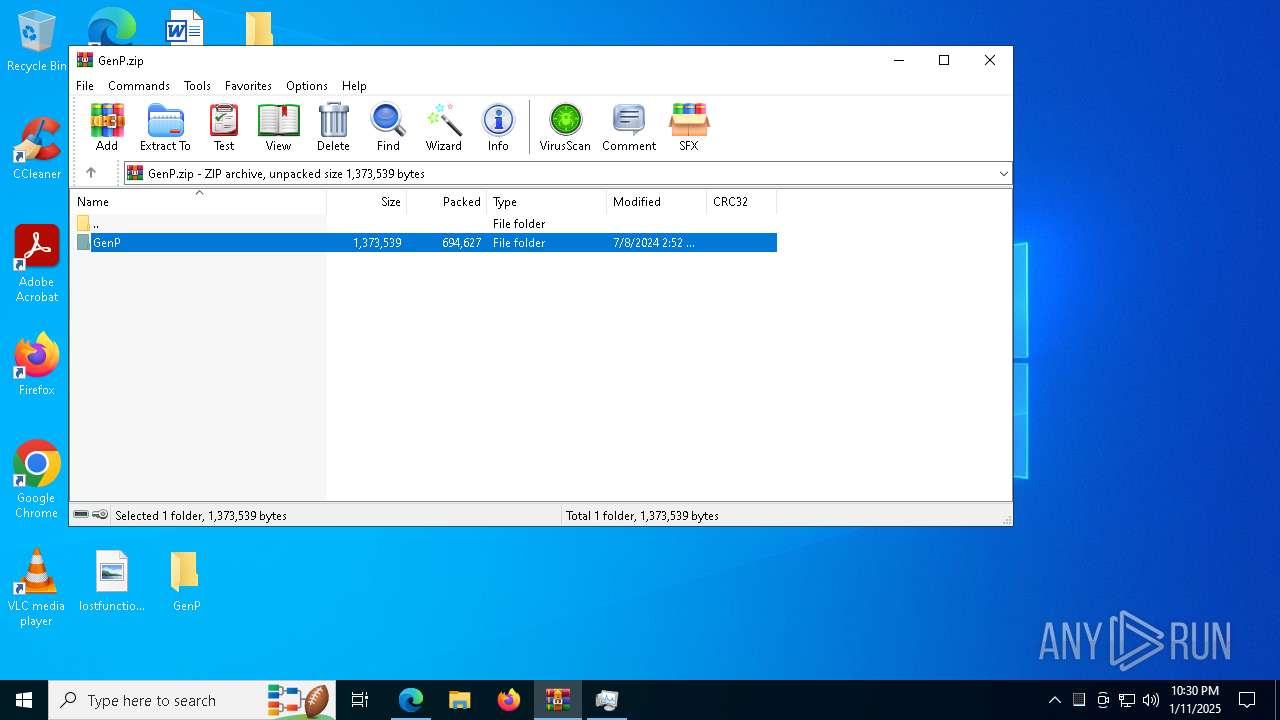
| File name: | GenP.zip |
| Full analysis: | https://app.any.run/tasks/06fea7ce-3939-490a-843b-636ba2c75b51 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2025, 22:27:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
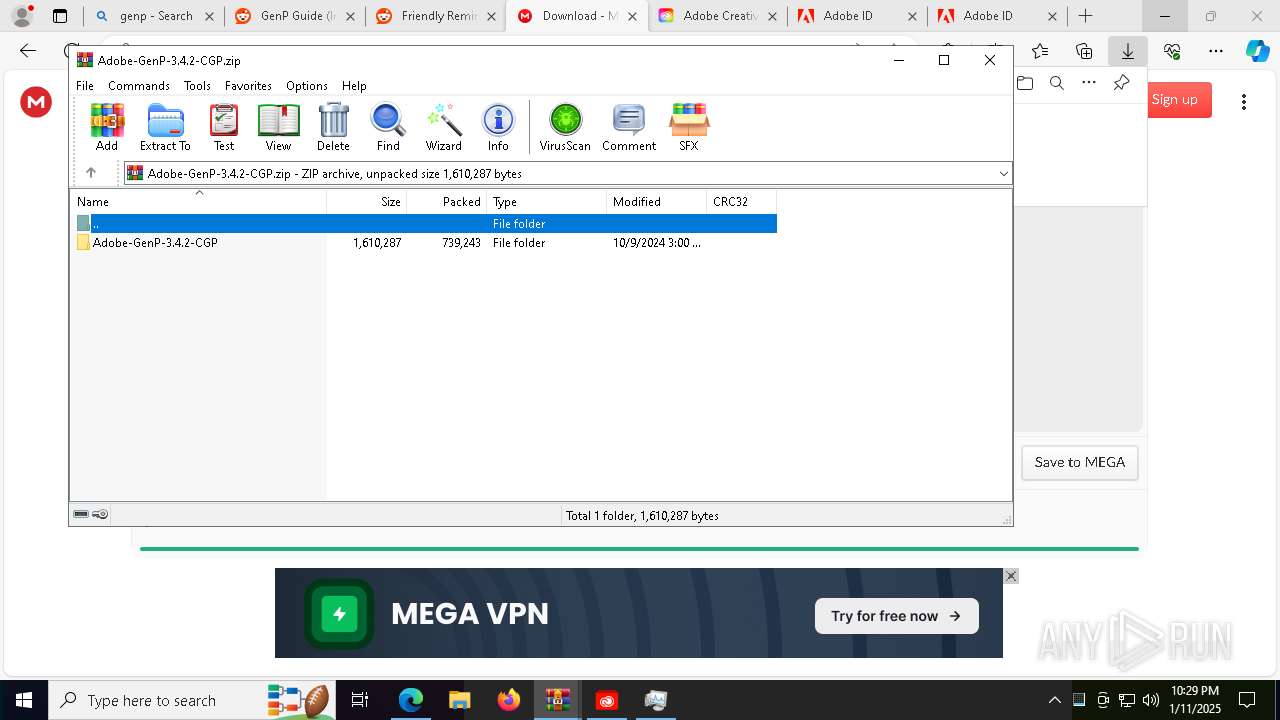
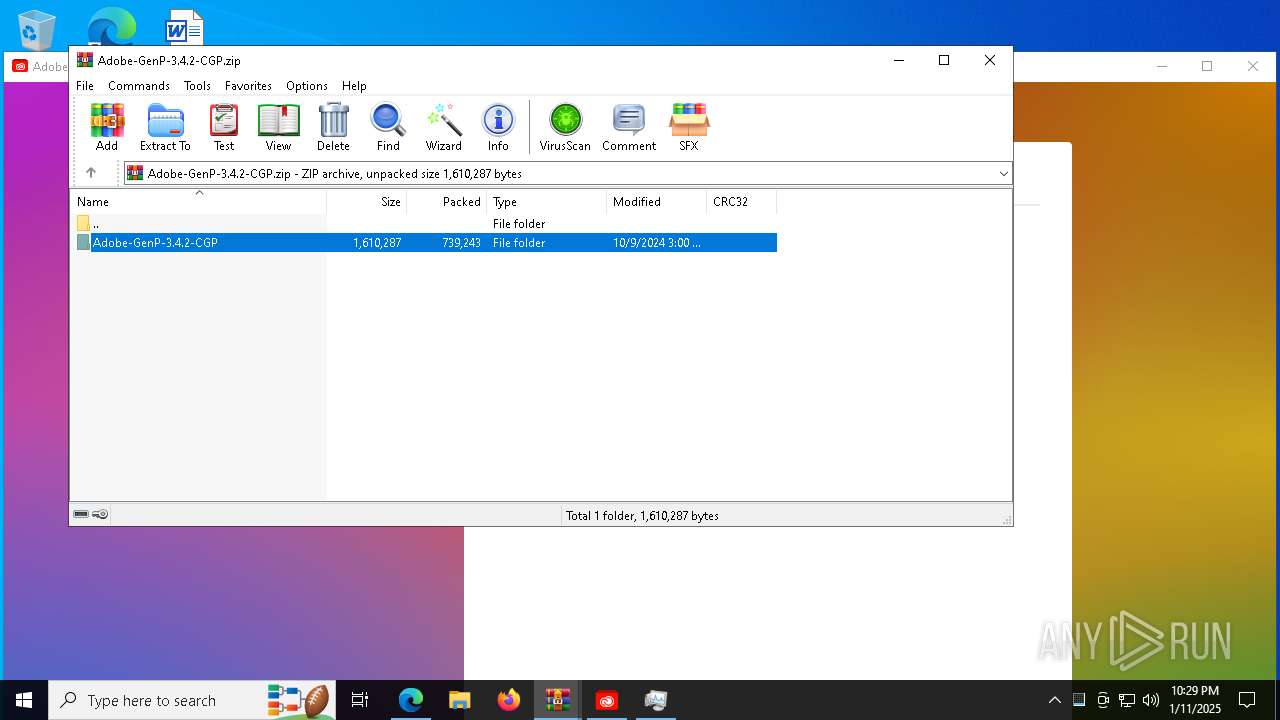
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 64D7585939C4F508CF8B5EF2D295DB3A |
| SHA1: | 3D7F5F8D9AC4BDE526CD33B37BDC1EBF034E1FDC |
| SHA256: | 5BB3C78AB4061E0E7BE78251D845EEC172D3BDED810173835E310A2FA8B729F6 |
| SSDEEP: | 24576:3JPmtvusfi8P8oARt5Vb5OO6b7p/XB604eaTn2asC9sCKCxoHcs7g15wtCqvj/YS:ZPmtvuAi8UoAX5Vb5OO6bd/XB604eaTE |
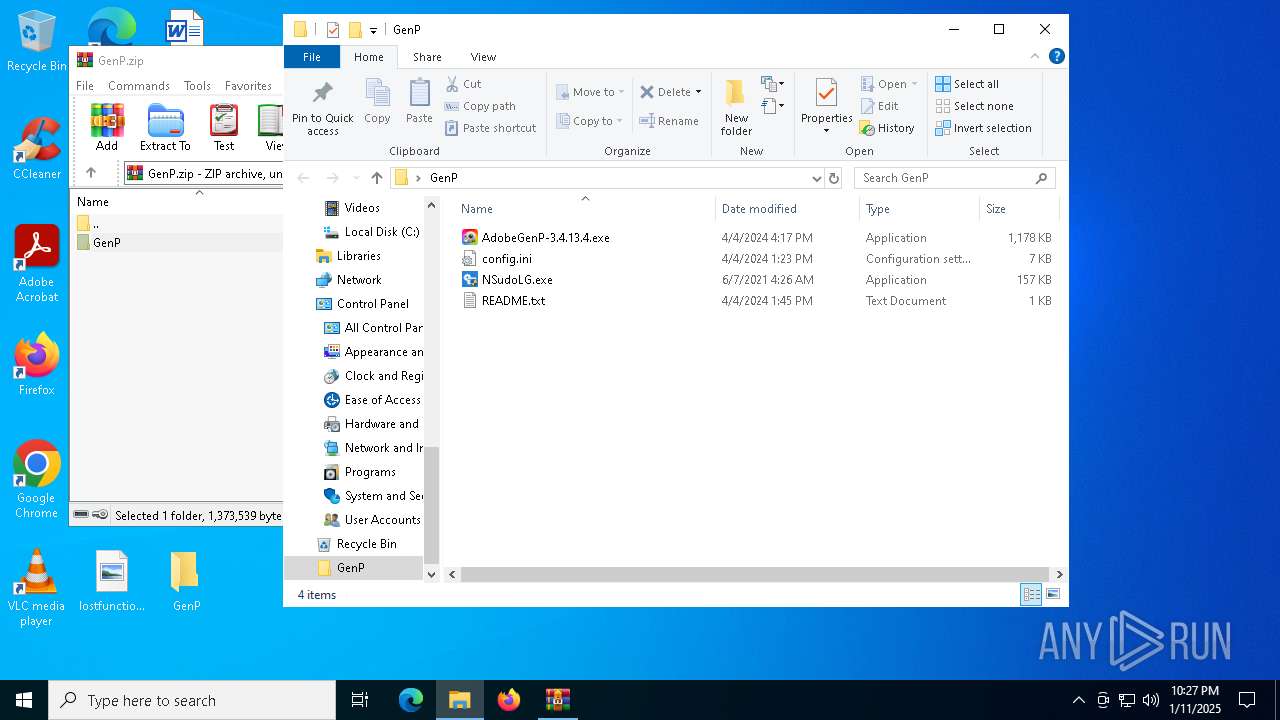
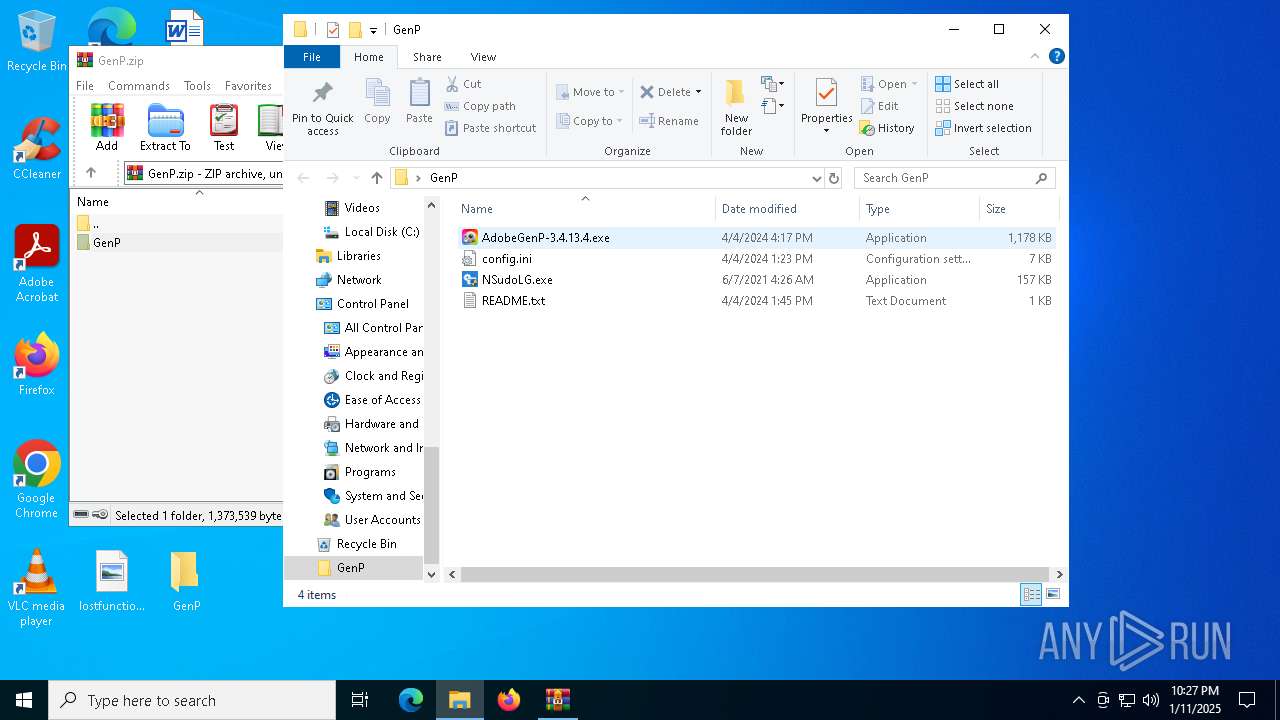
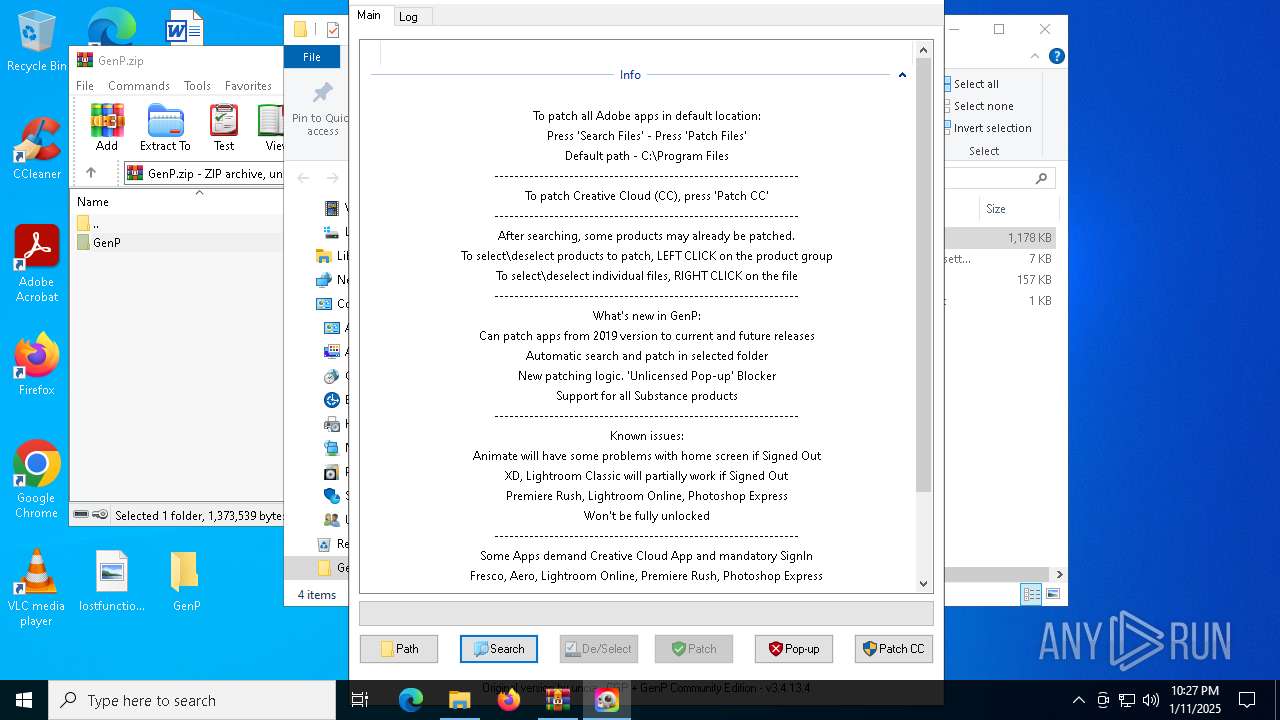
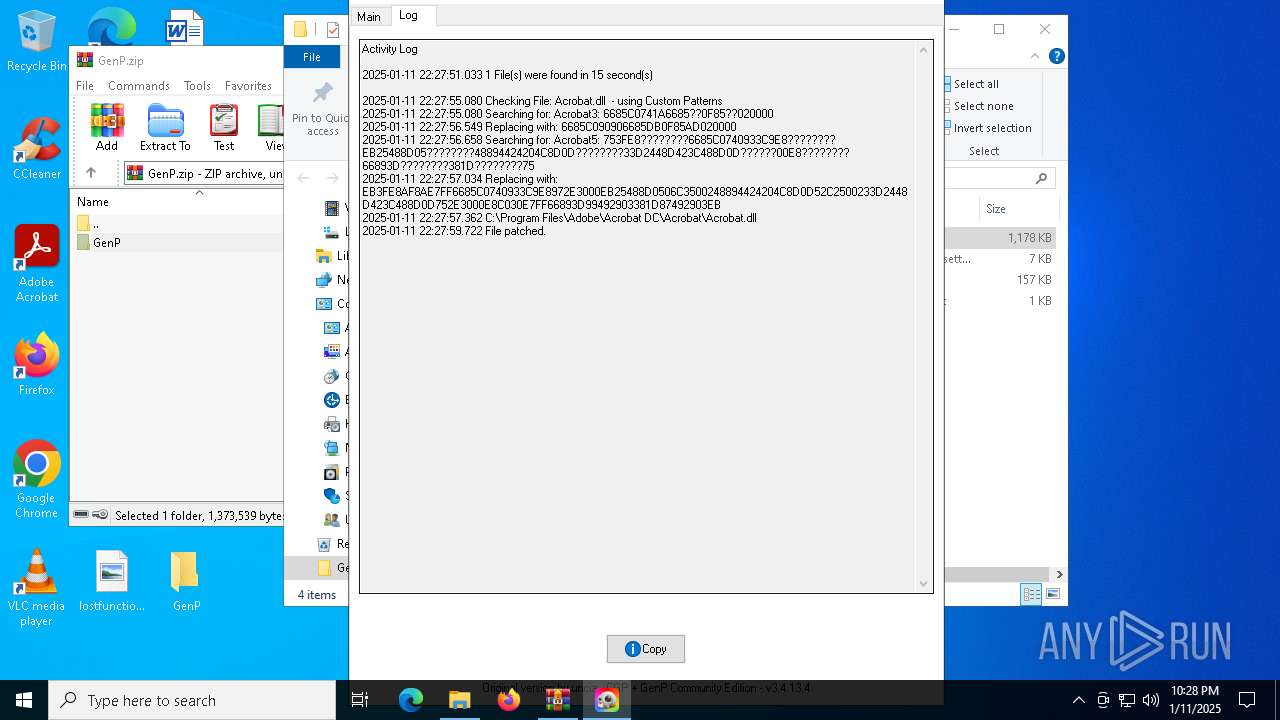
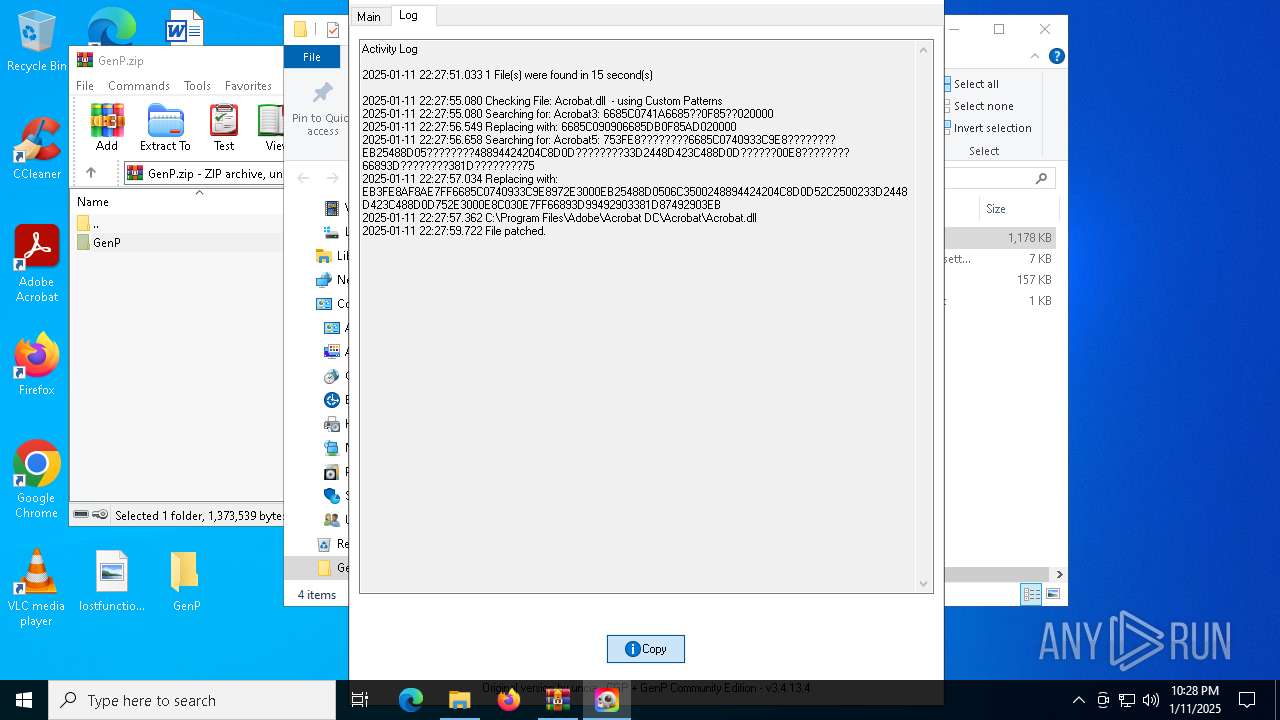
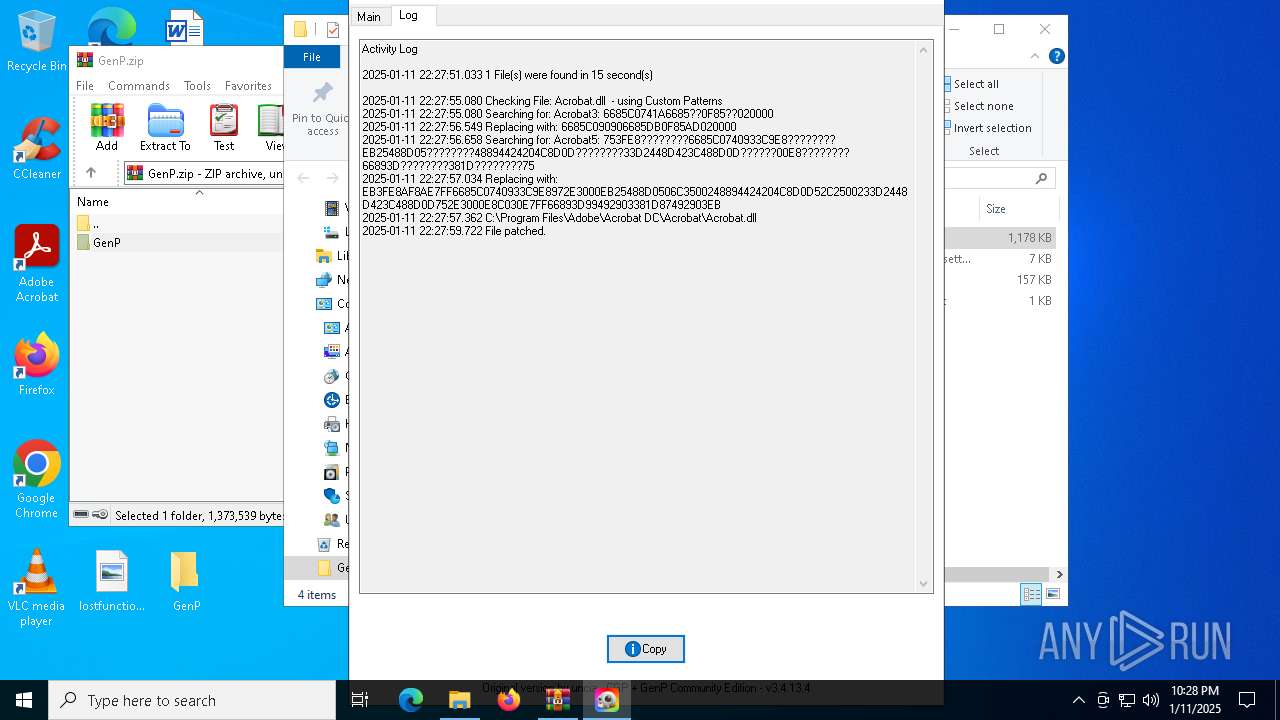
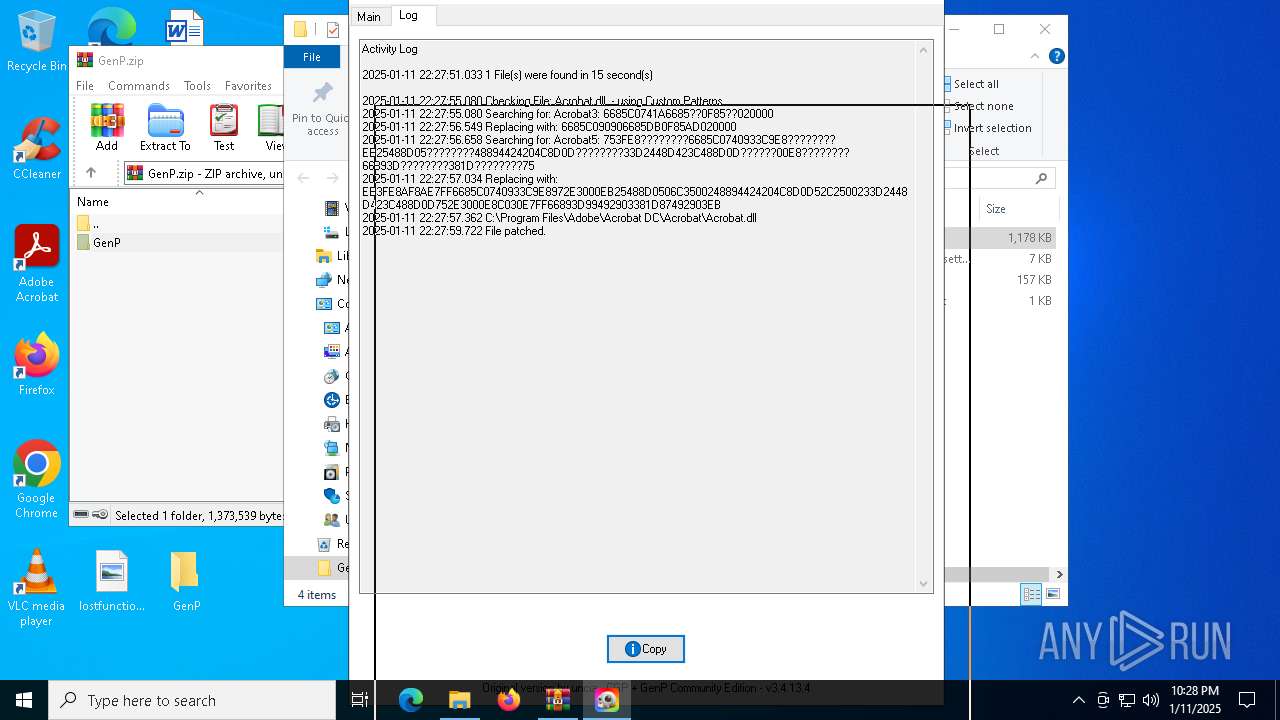
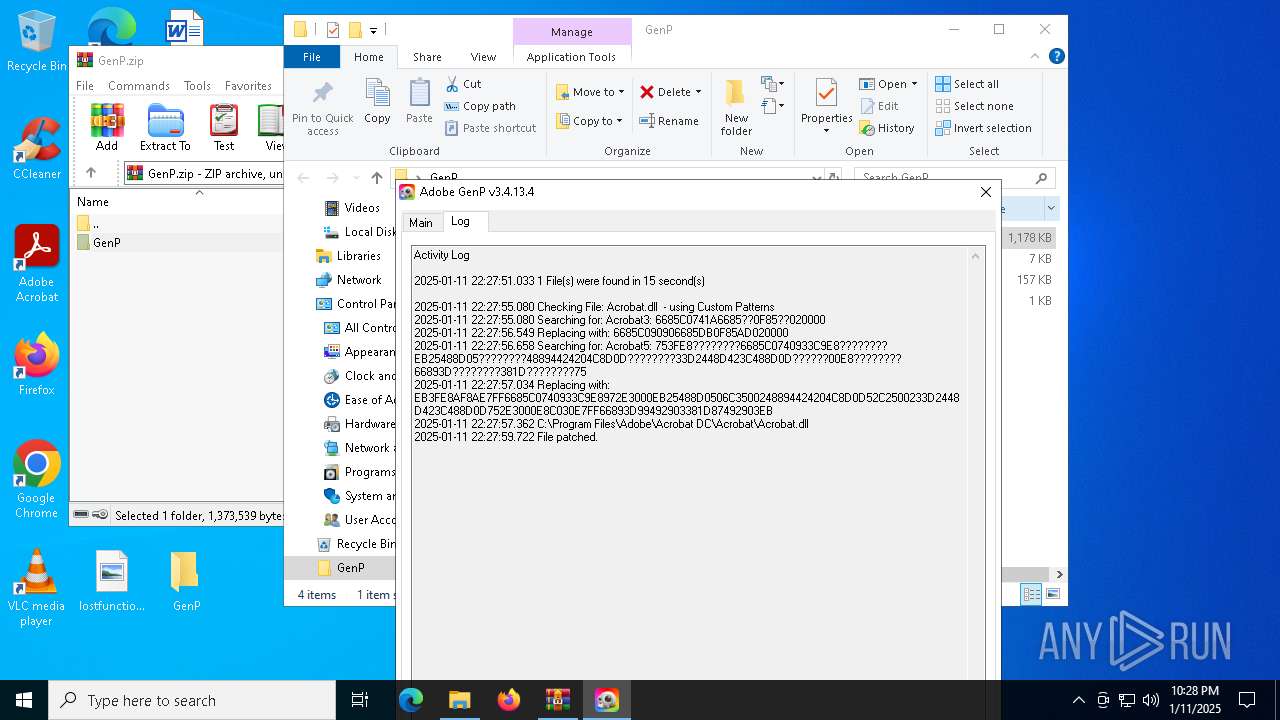
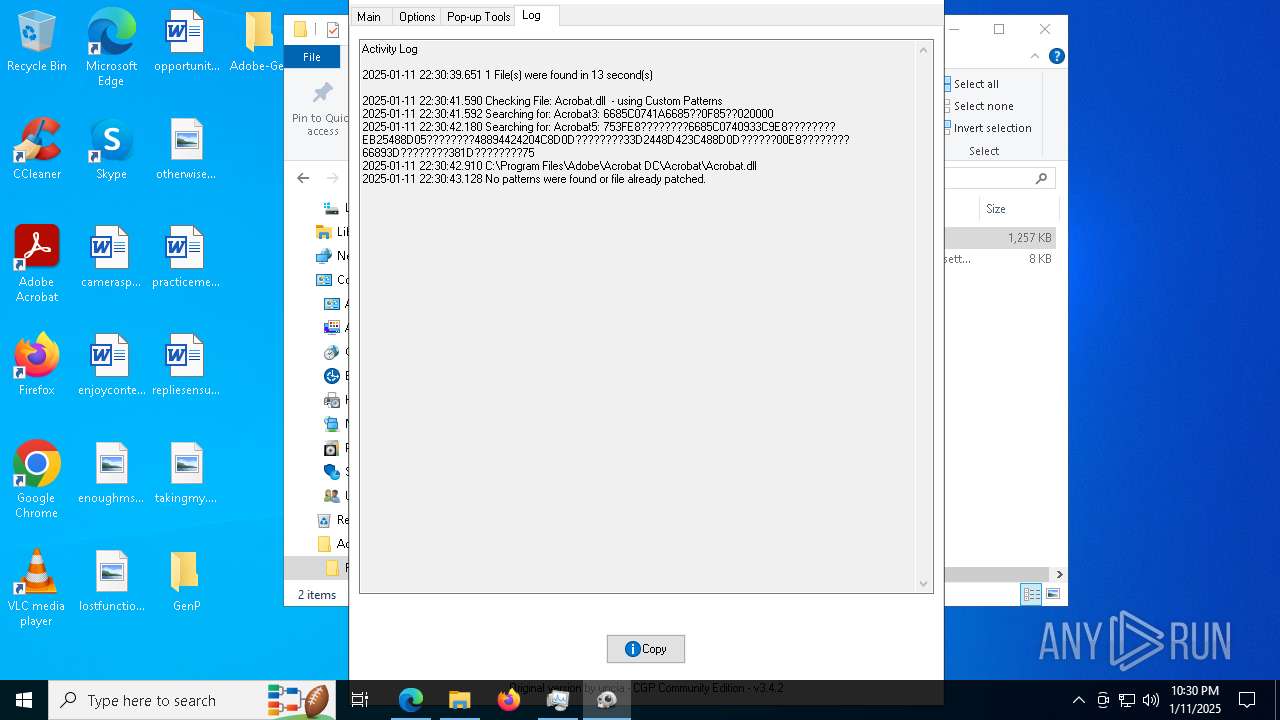
MALICIOUS
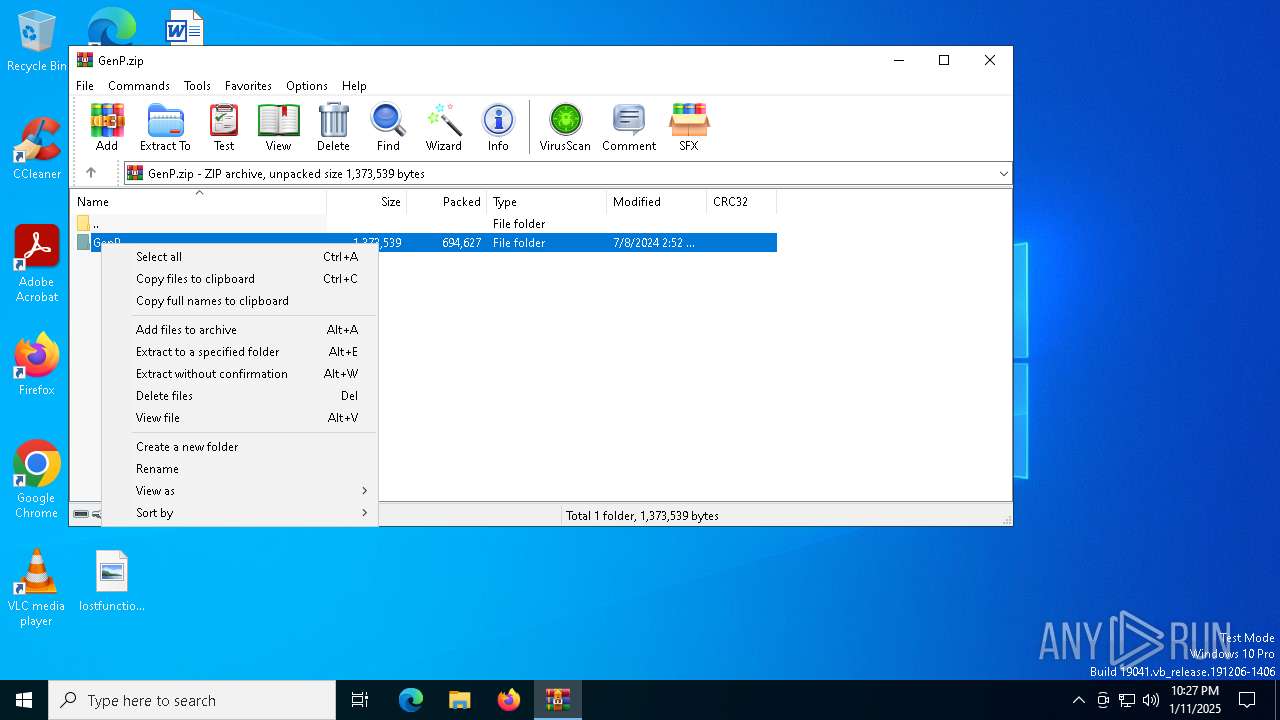
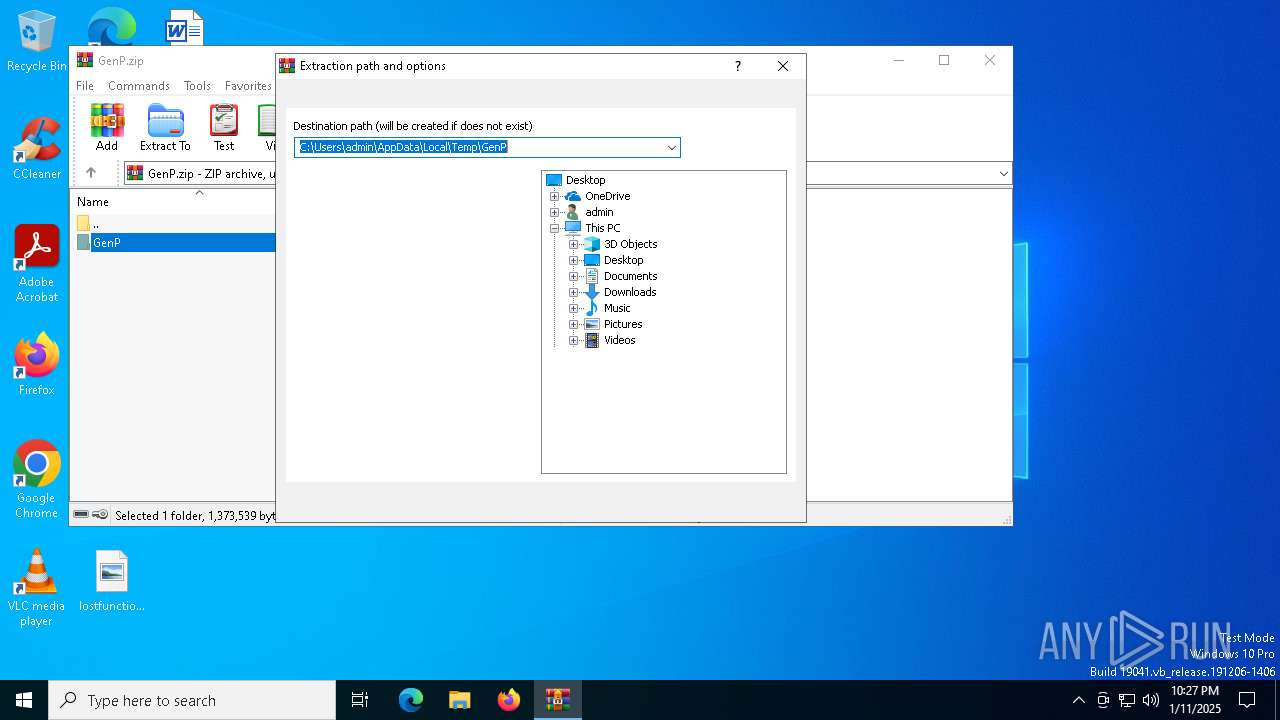
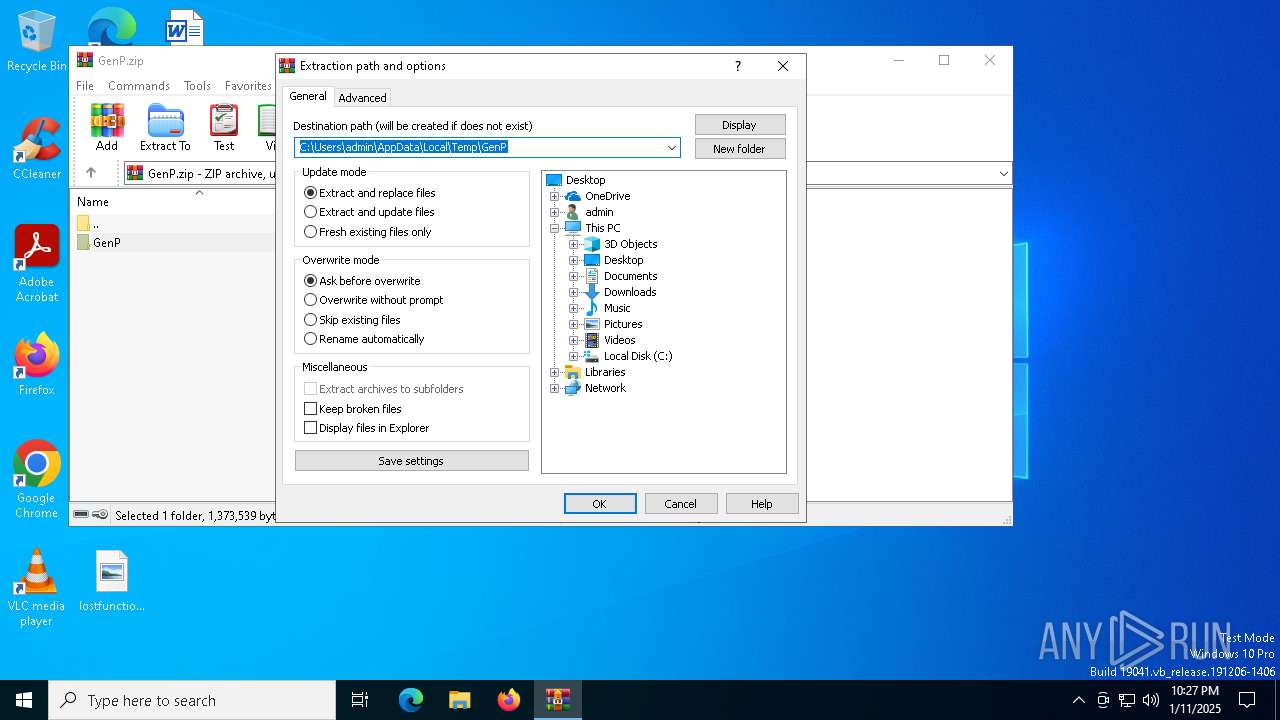
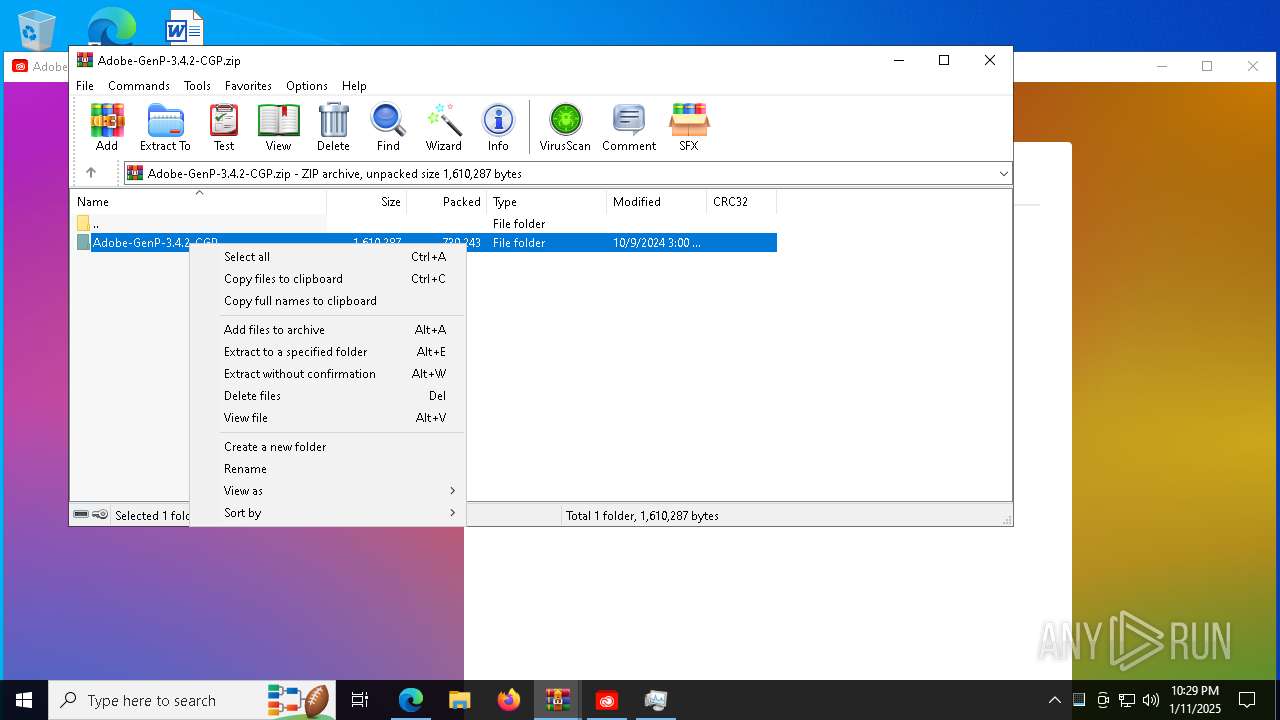
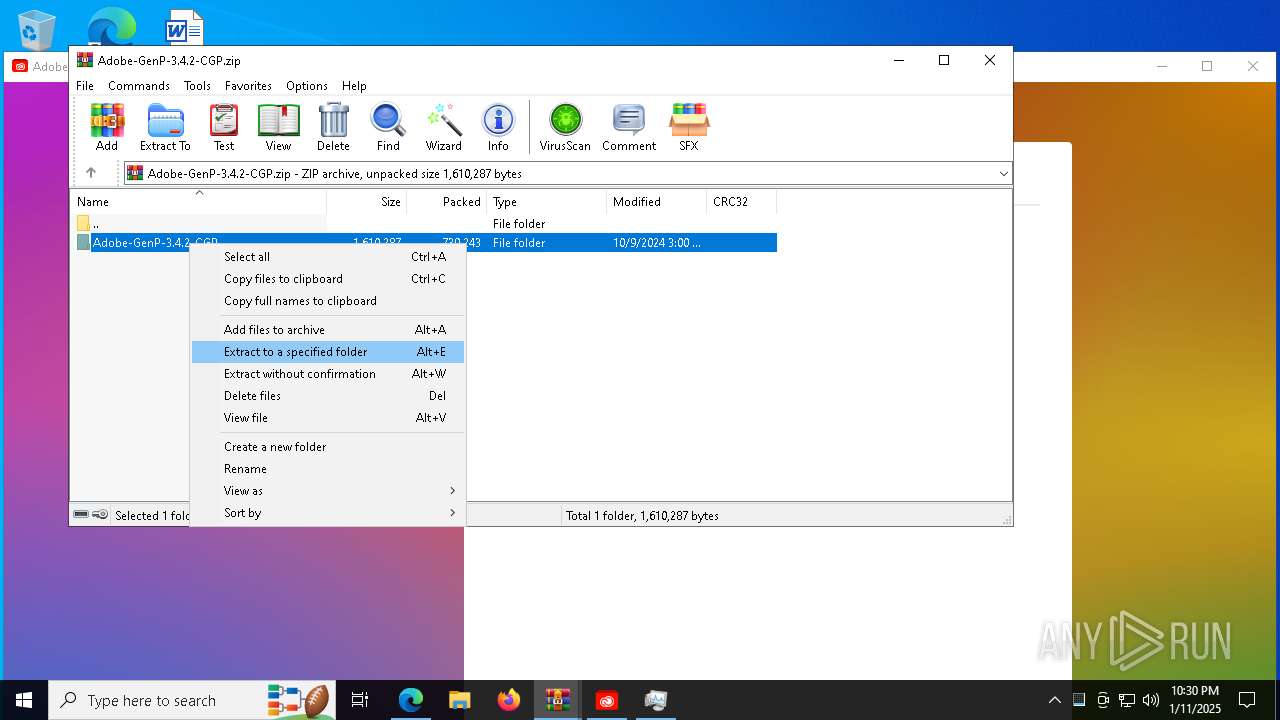
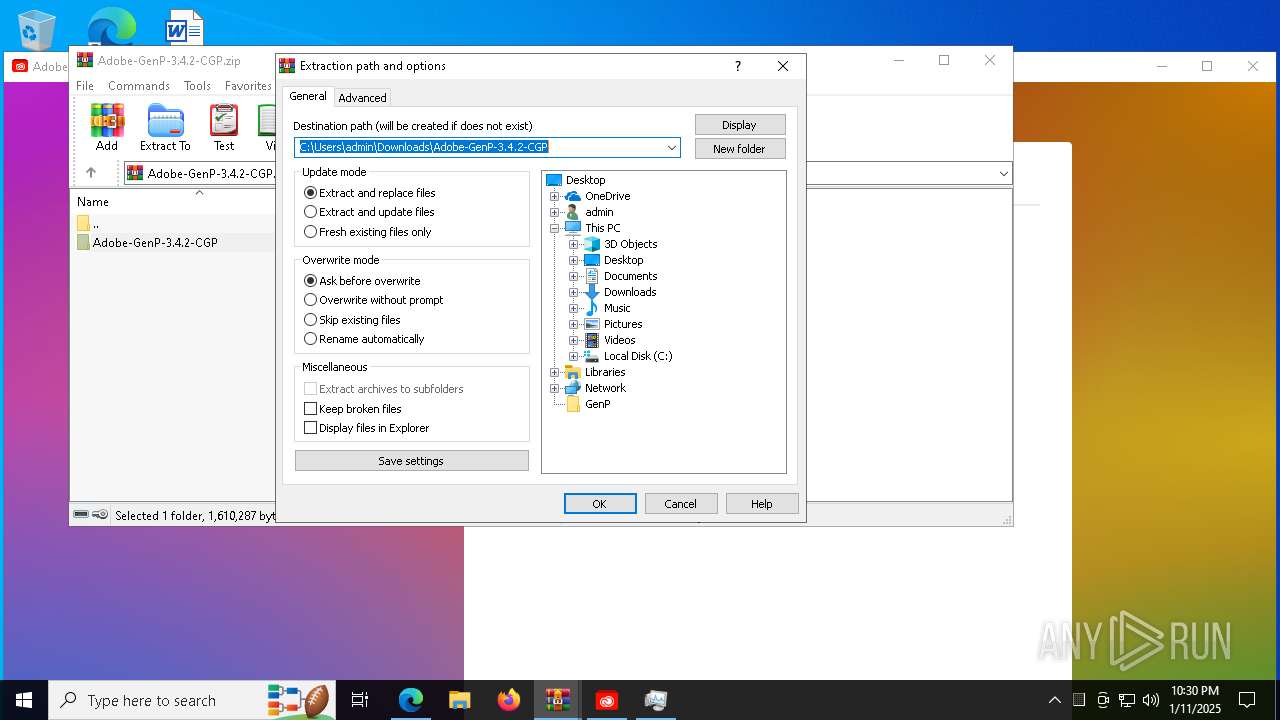
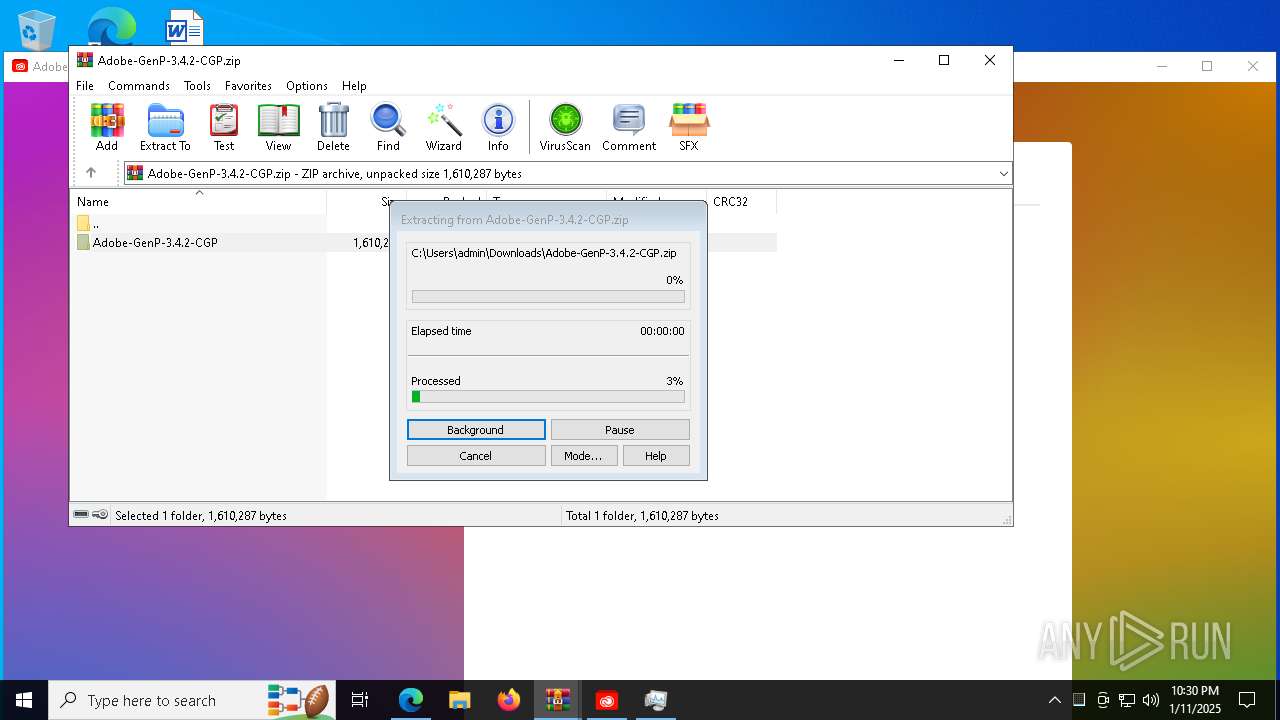
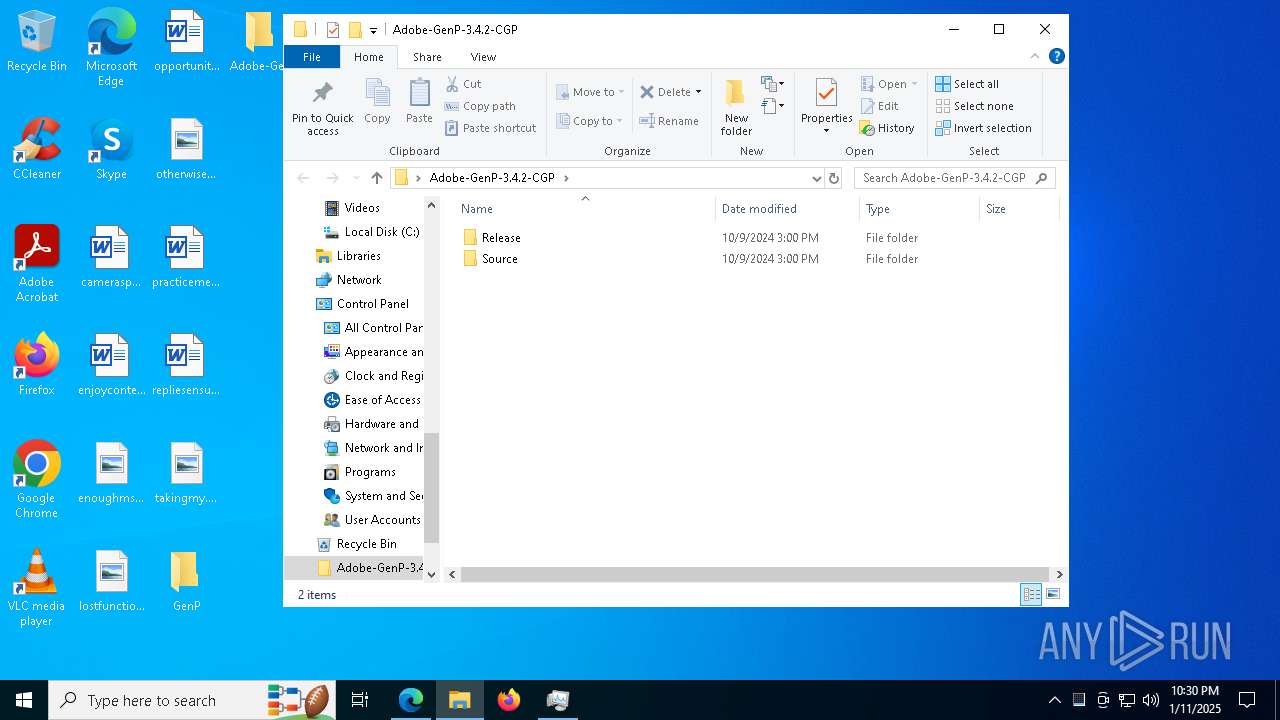
Generic archive extractor
- WinRAR.exe (PID: 6336)
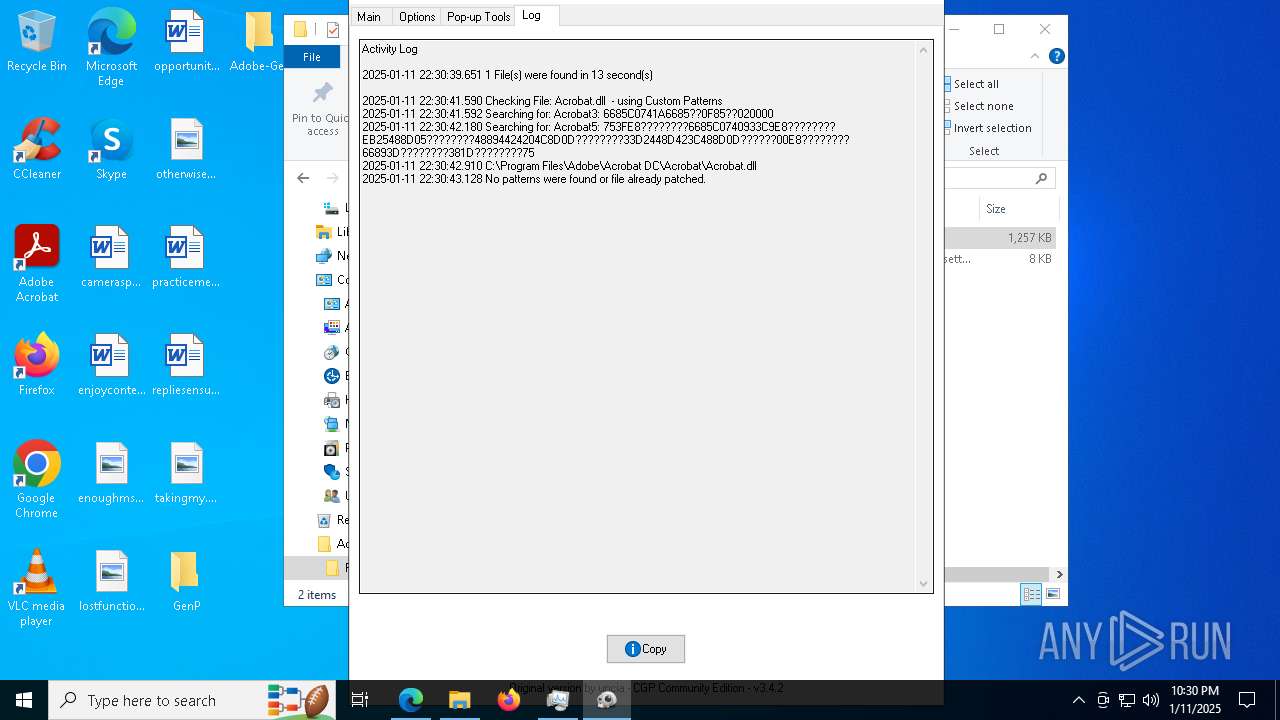
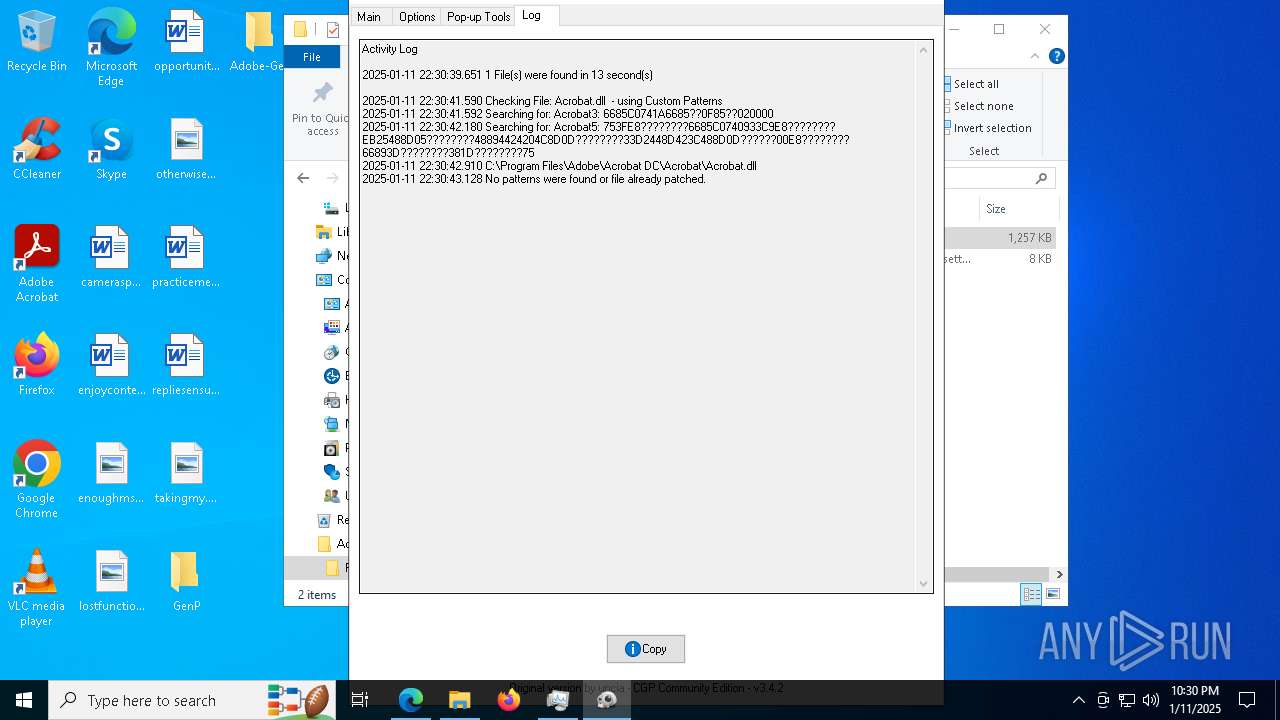
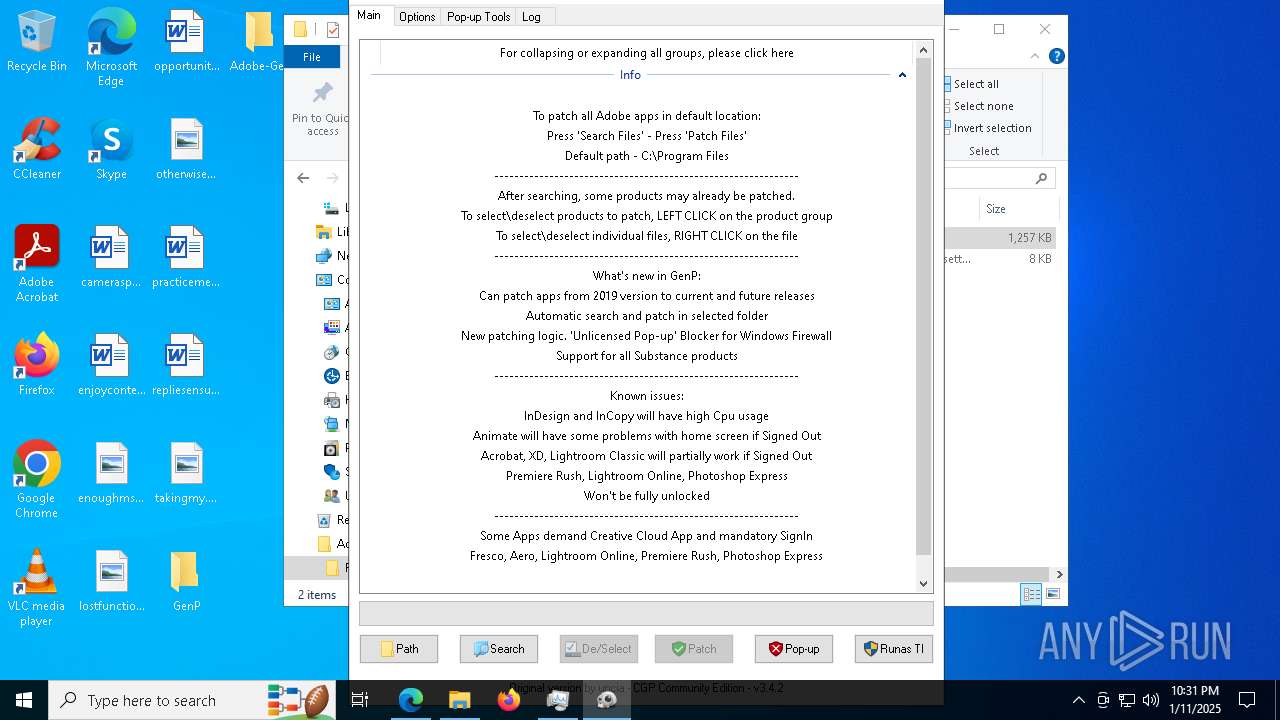
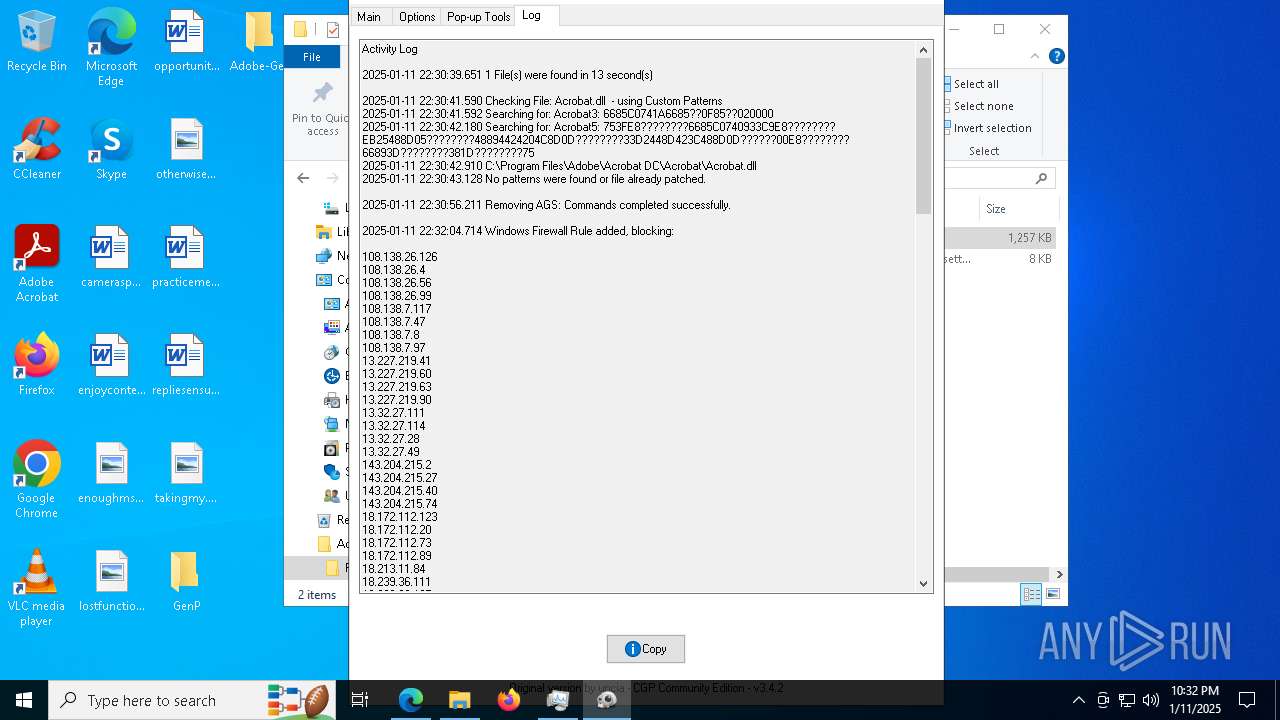
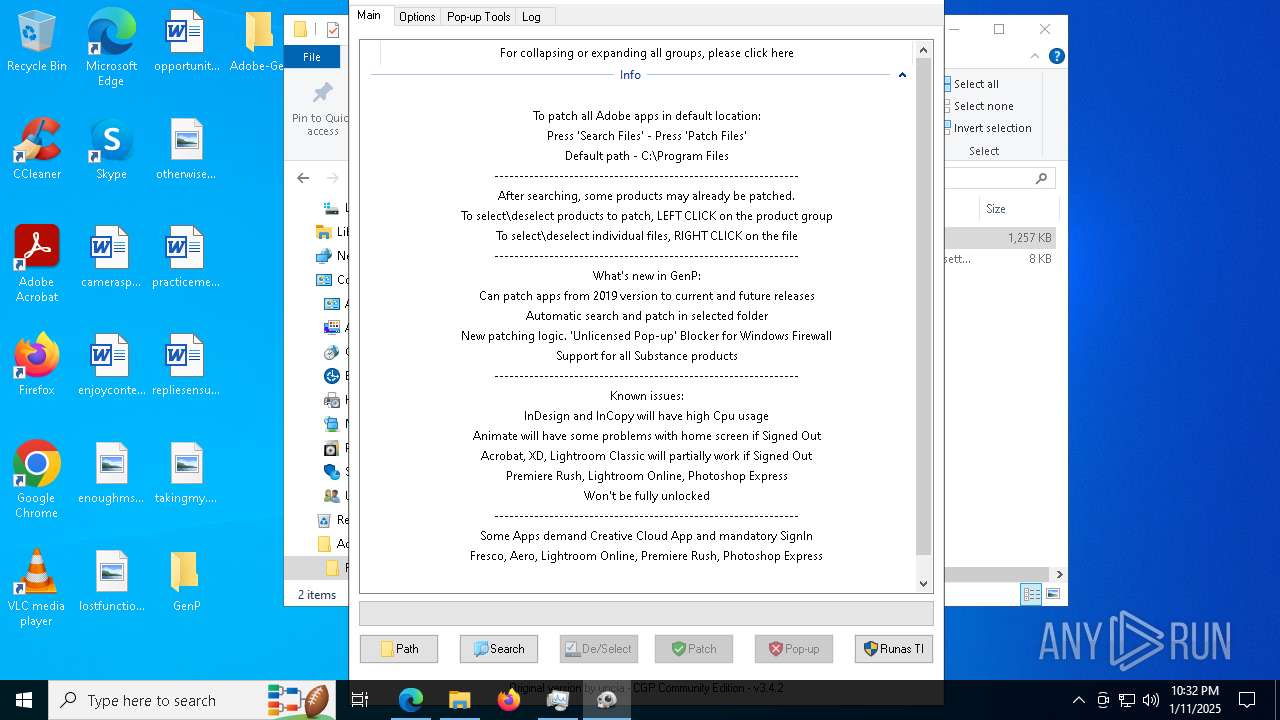
Bypass execution policy to execute commands
- powershell.exe (PID: 8496)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 3260)
- powershell.exe (PID: 3288)
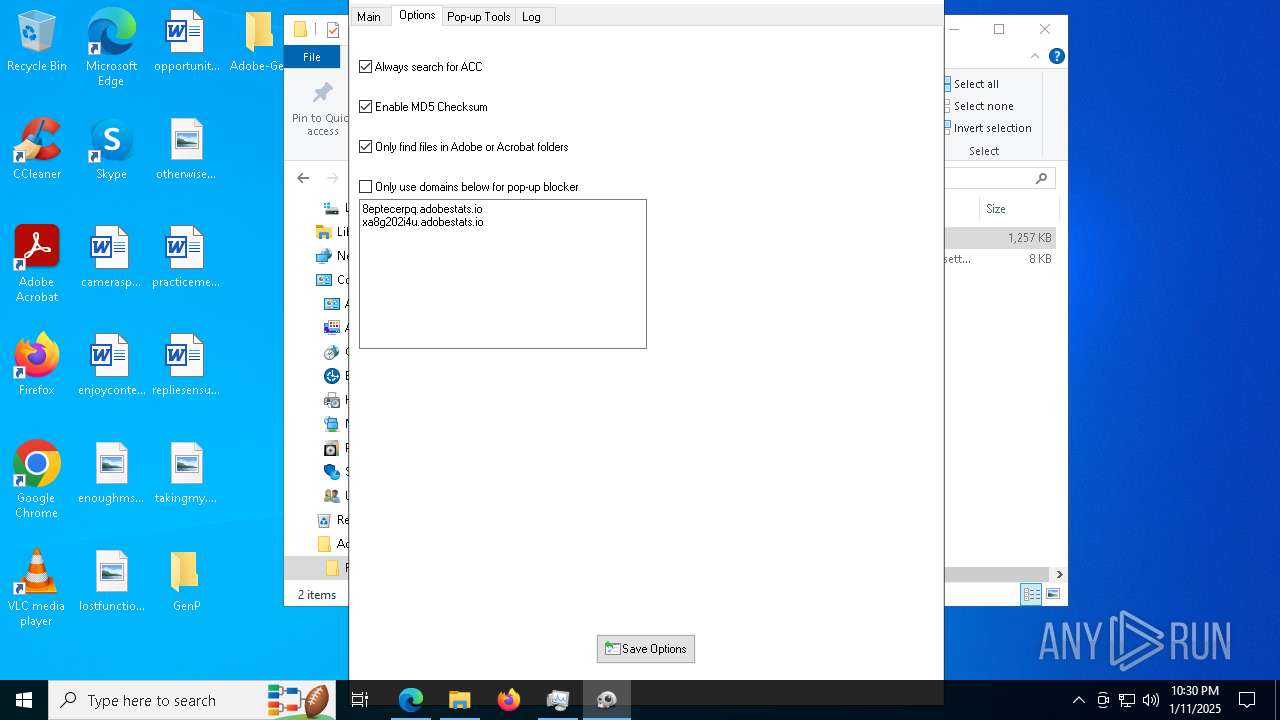
Changes powershell execution policy (Bypass)
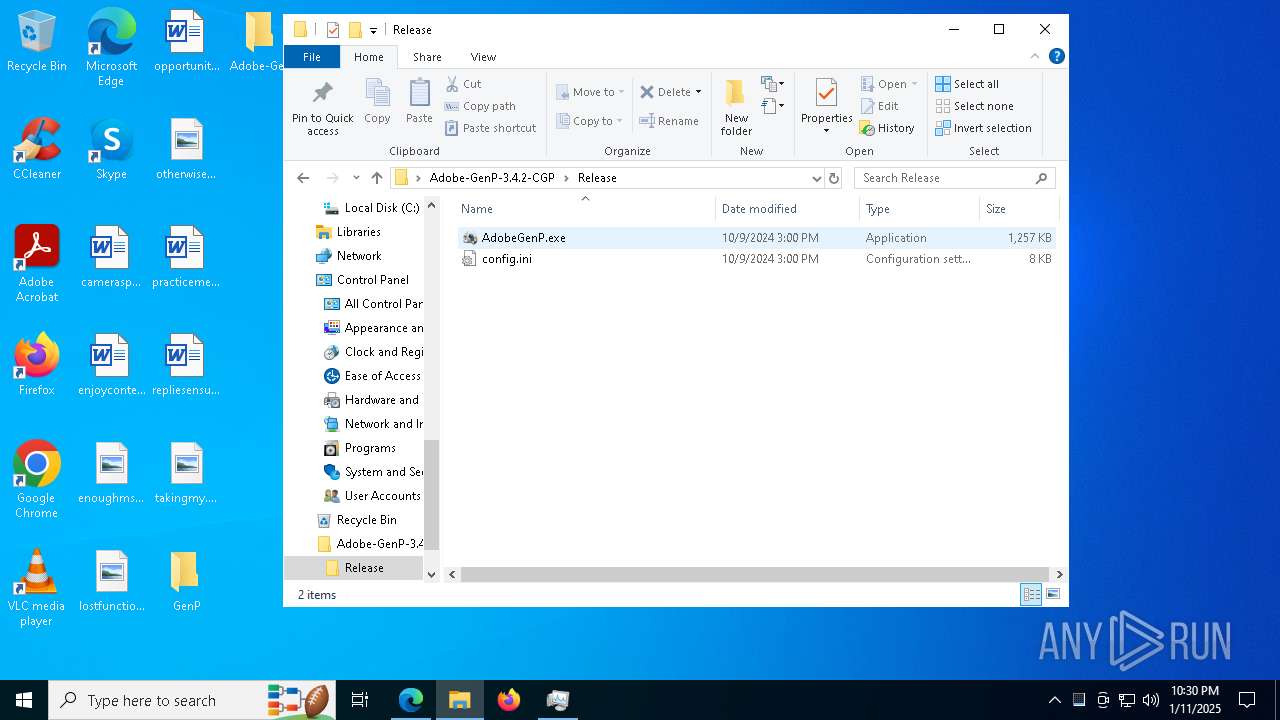
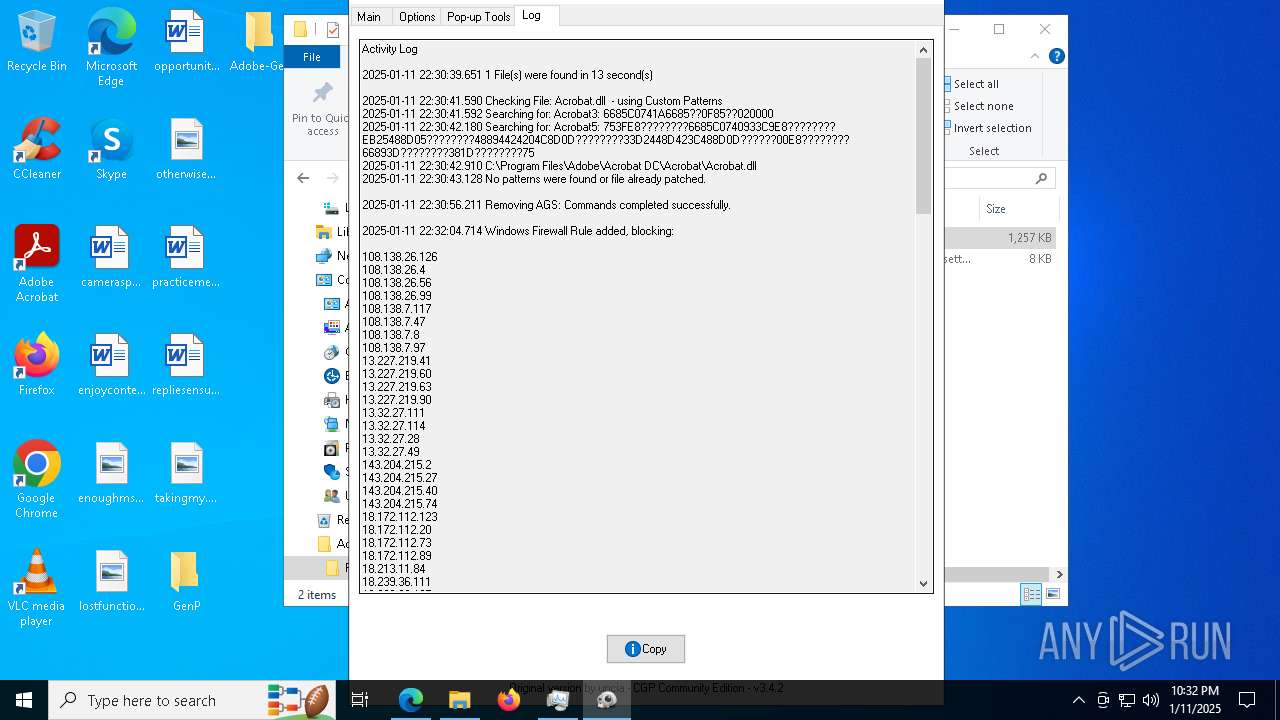
- AdobeGenP.exe (PID: 8036)
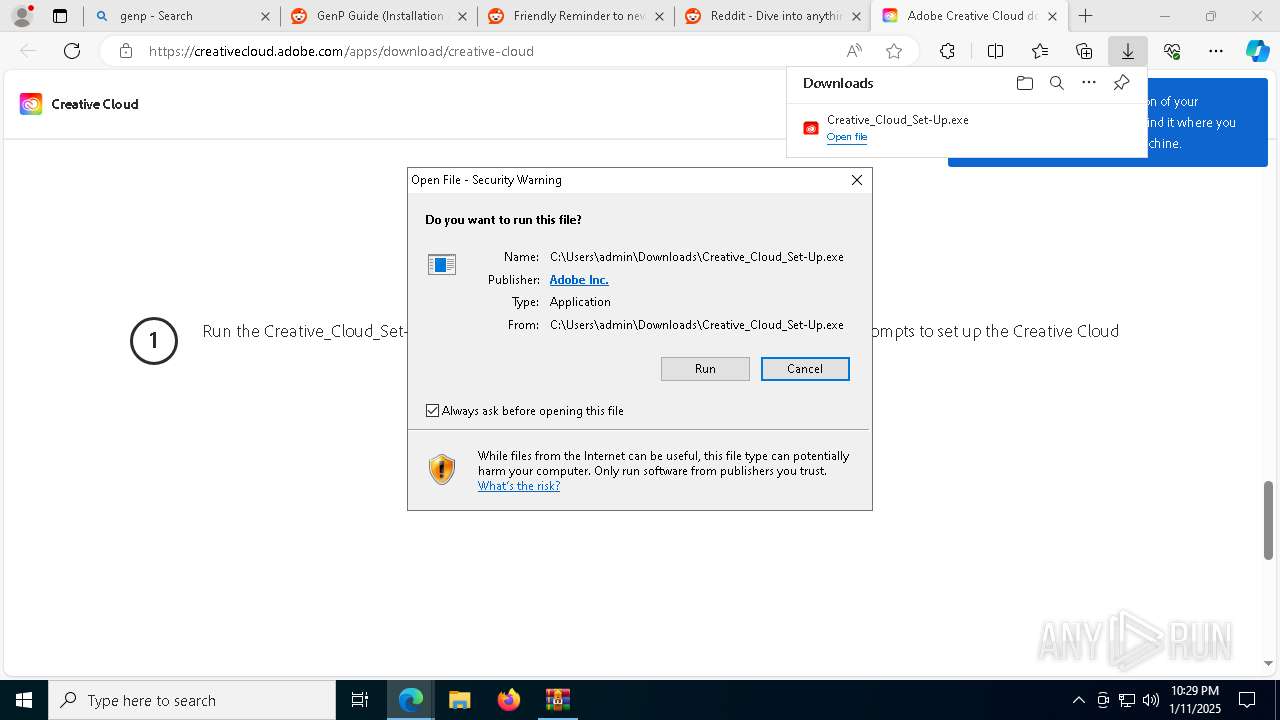
Executing a file with an untrusted certificate
- RunAsTI.exe (PID: 2736)
SUSPICIOUS
Reads security settings of Internet Explorer
- AdobeGenP-3.4.13.4.exe (PID: 5720)
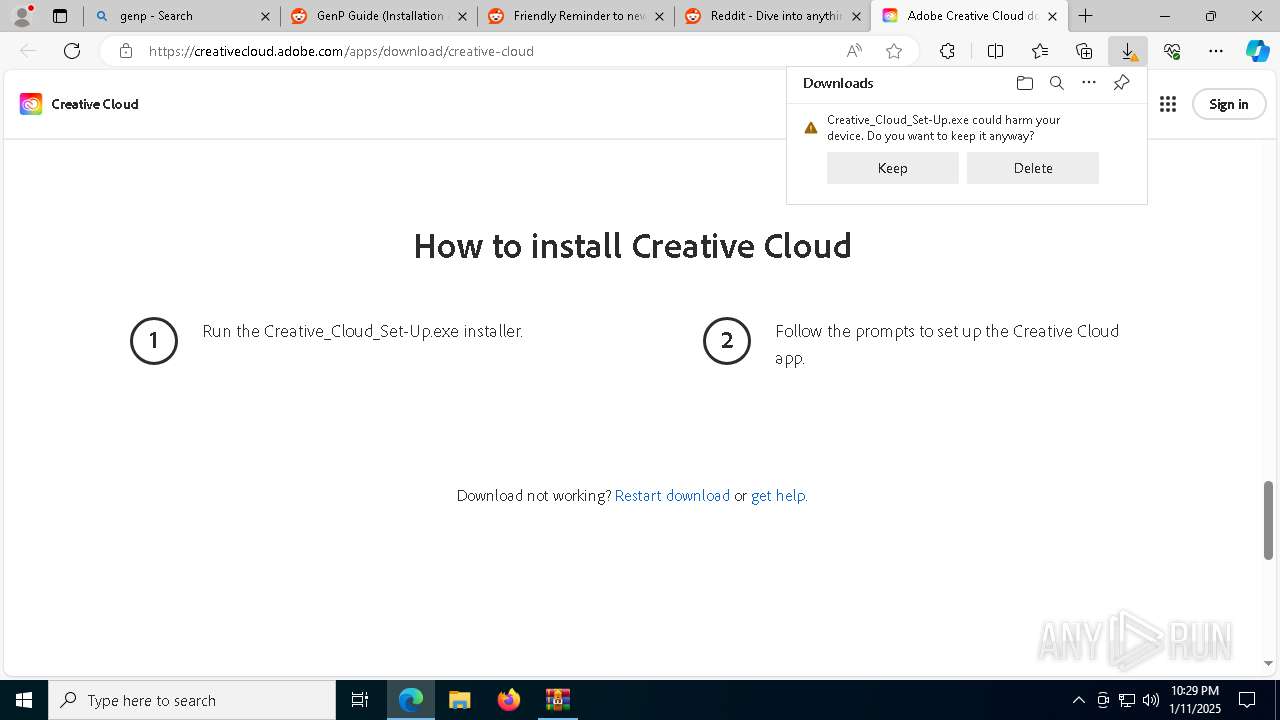
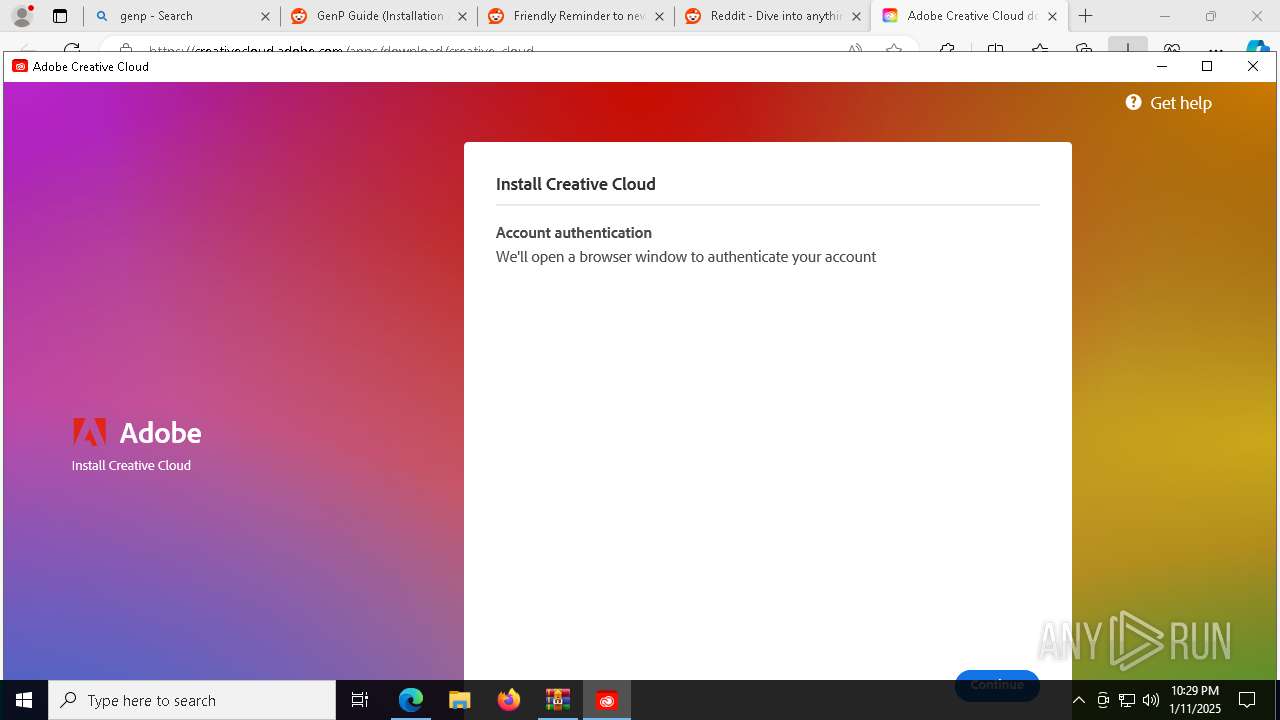
- Creative_Cloud_Set-Up.exe (PID: 7456)
Reads the date of Windows installation
- AdobeGenP-3.4.13.4.exe (PID: 5720)
Application launched itself
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- Creative_Cloud_Set-Up.exe (PID: 7456)
- RunAsTI.exe (PID: 2736)
Reads Microsoft Outlook installation path
- Creative_Cloud_Set-Up.exe (PID: 7456)
Checks Windows Trust Settings
- Creative_Cloud_Set-Up.exe (PID: 7456)
Adds/modifies Windows certificates
- Creative_Cloud_Set-Up.exe (PID: 7456)
Starts CMD.EXE for commands execution
- Creative_Cloud_Set-Up.exe (PID: 7456)
Starts POWERSHELL.EXE for commands execution
- AdobeGenP.exe (PID: 8036)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 8496)
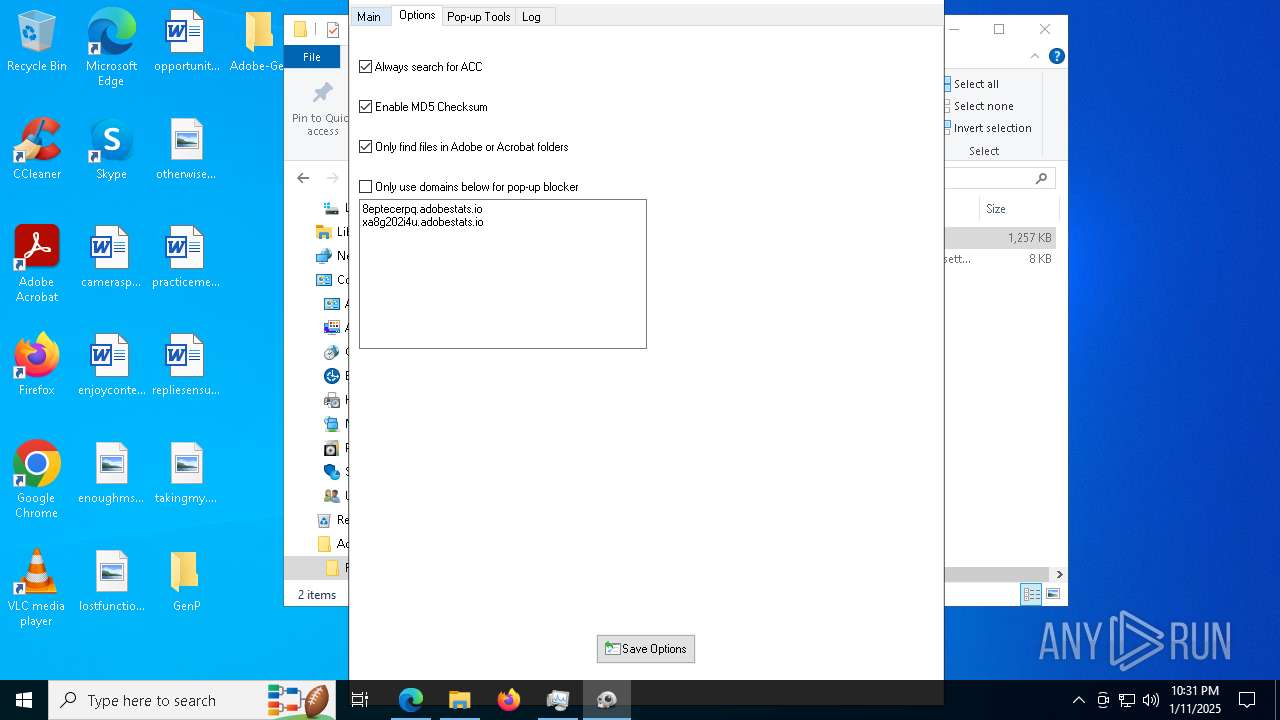
Base64-obfuscated command line is found
- AdobeGenP.exe (PID: 8036)
Kill processes via PowerShell
- powershell.exe (PID: 8496)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 8496)
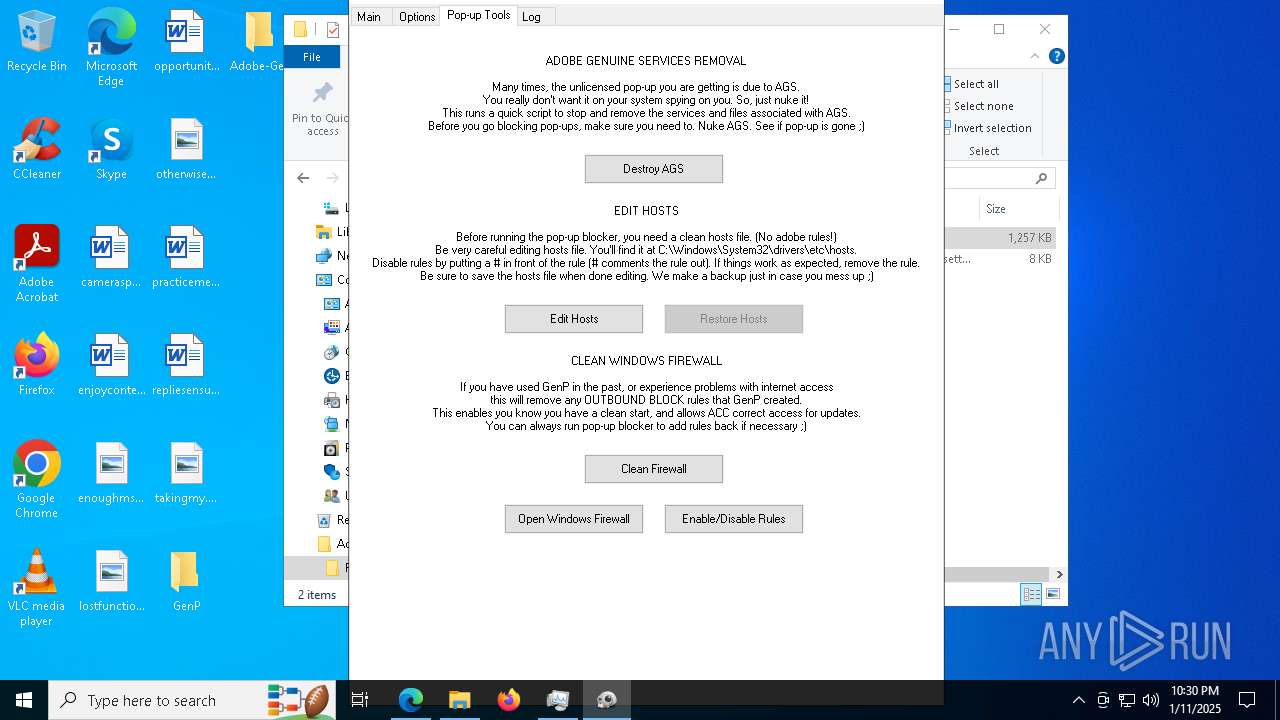
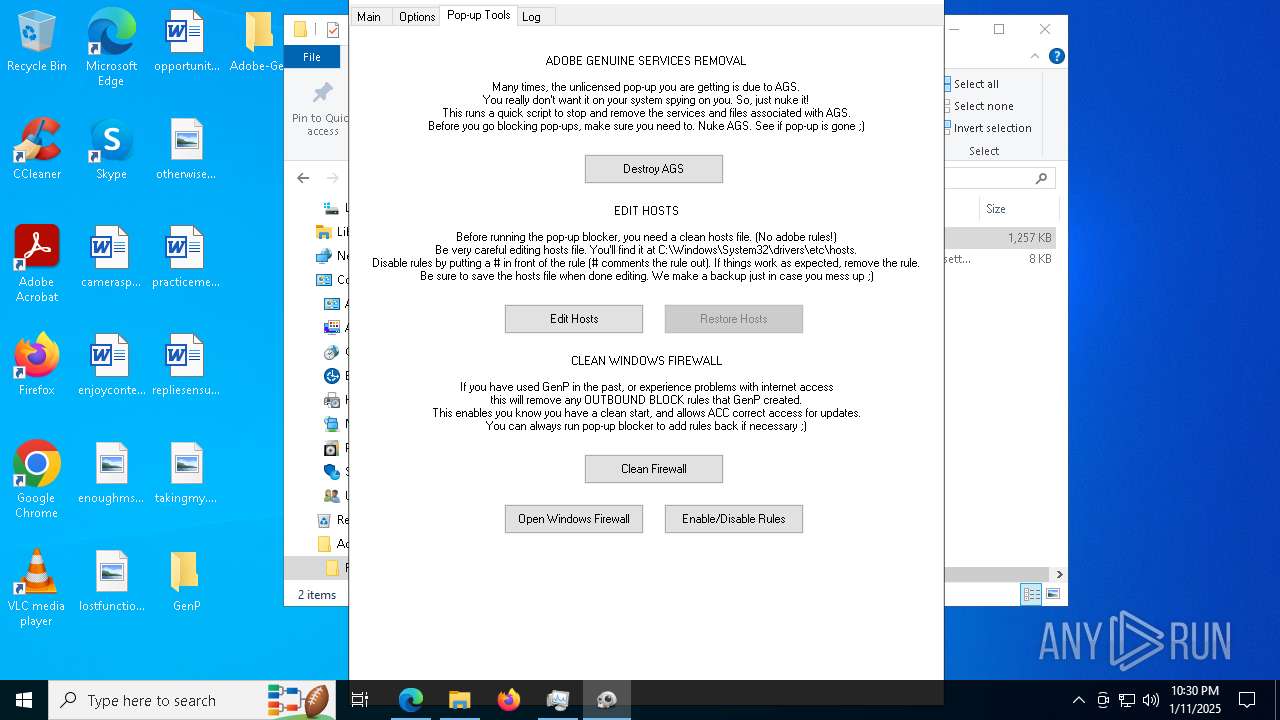
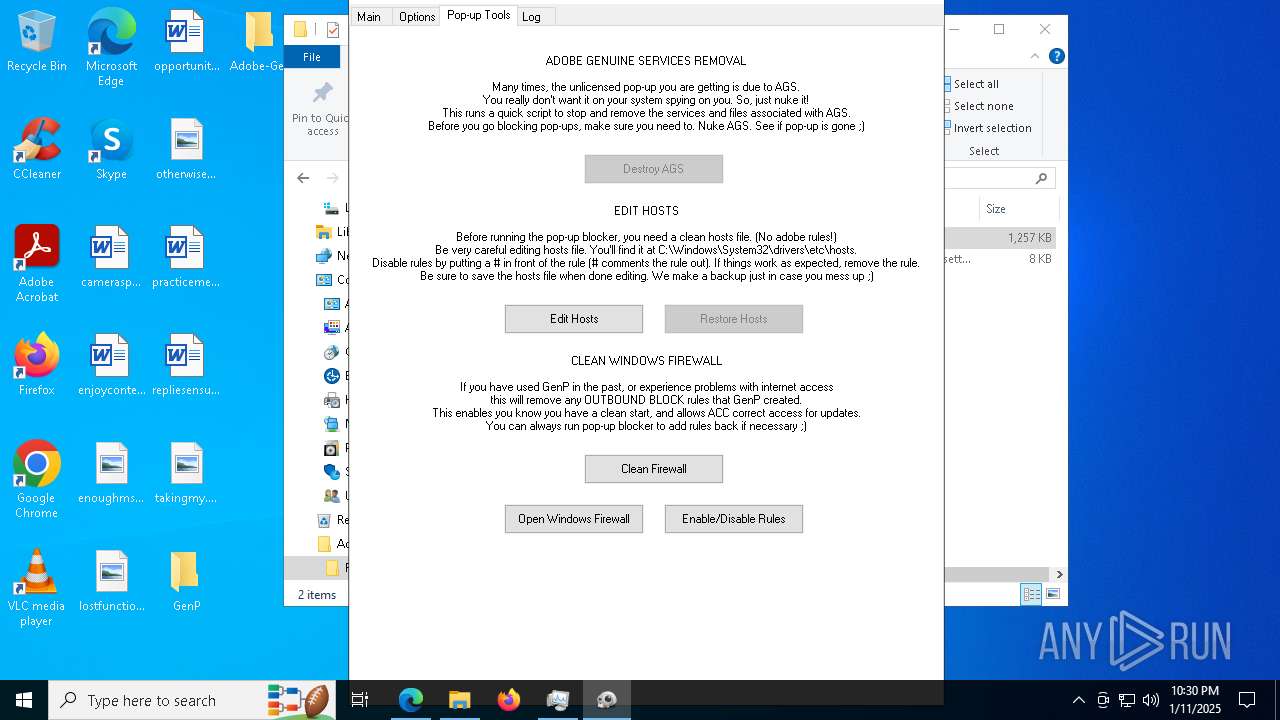
Windows service management via SC.EXE
- sc.exe (PID: 1888)
- sc.exe (PID: 3936)
Starts SC.EXE for service management
- powershell.exe (PID: 8496)
Found IP address in command line
- powershell.exe (PID: 7368)
- powershell.exe (PID: 3260)
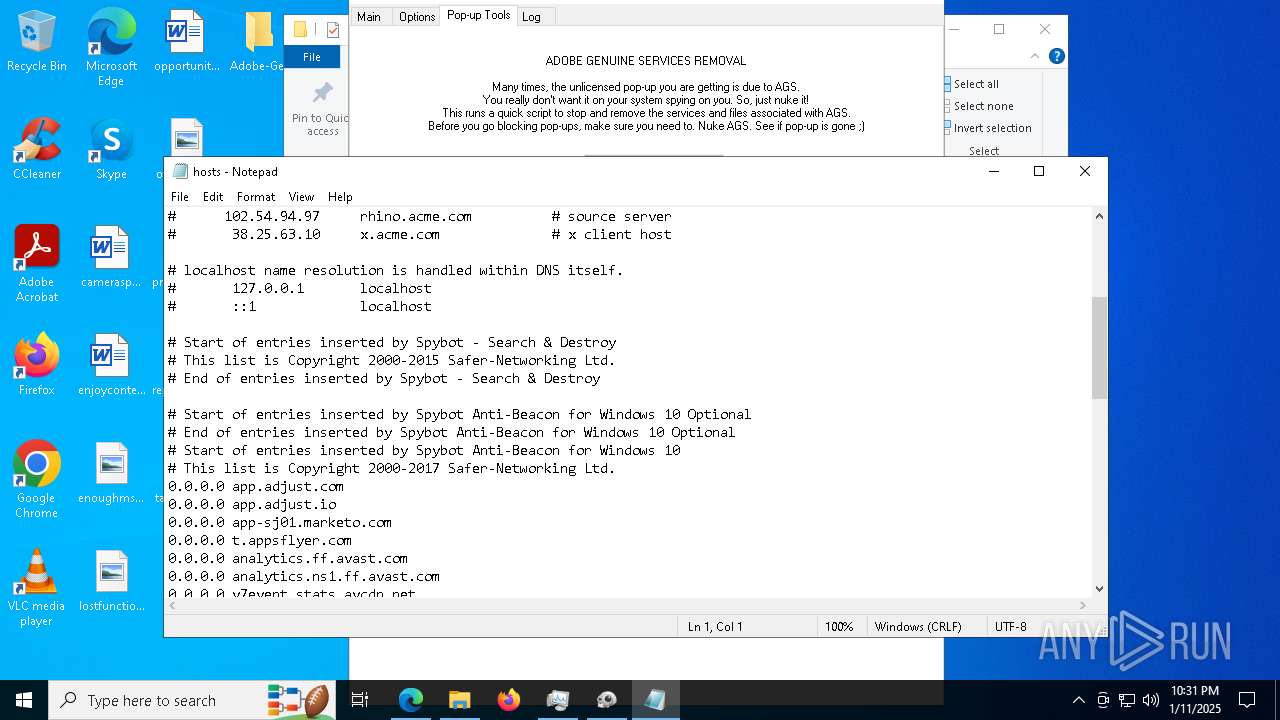
Creates files in the driver directory
- AdobeGenP.exe (PID: 8036)
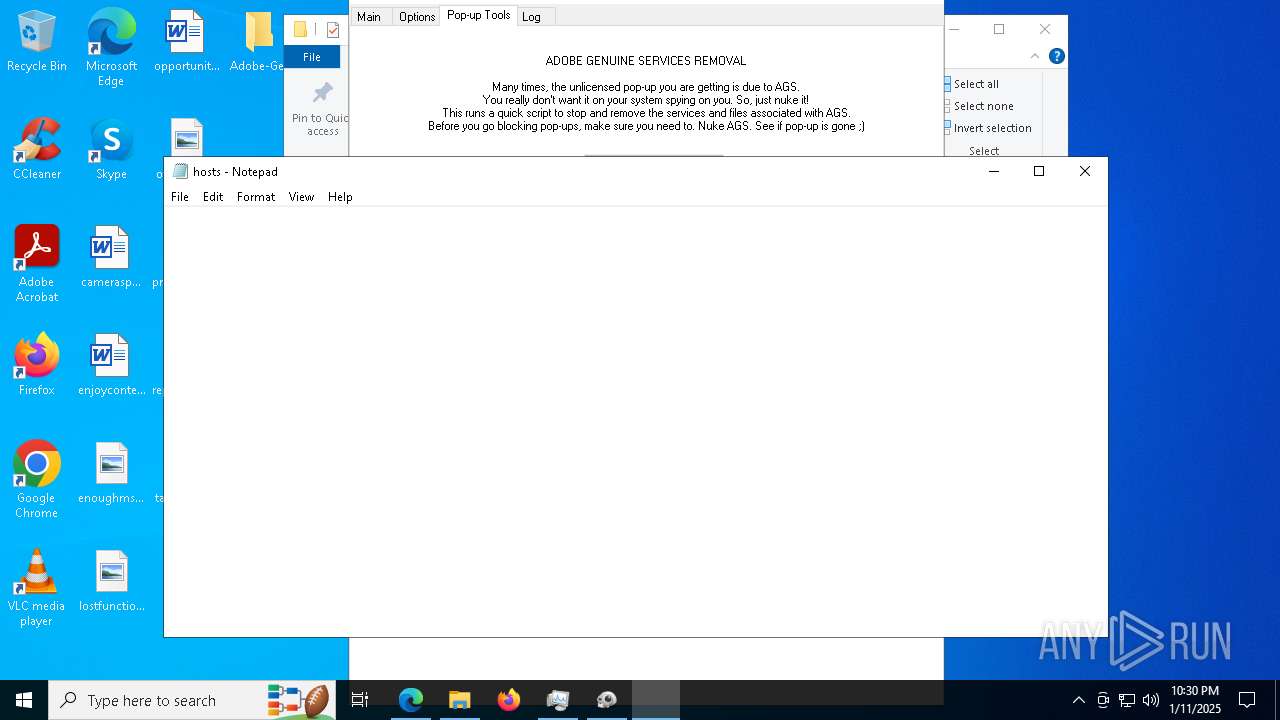
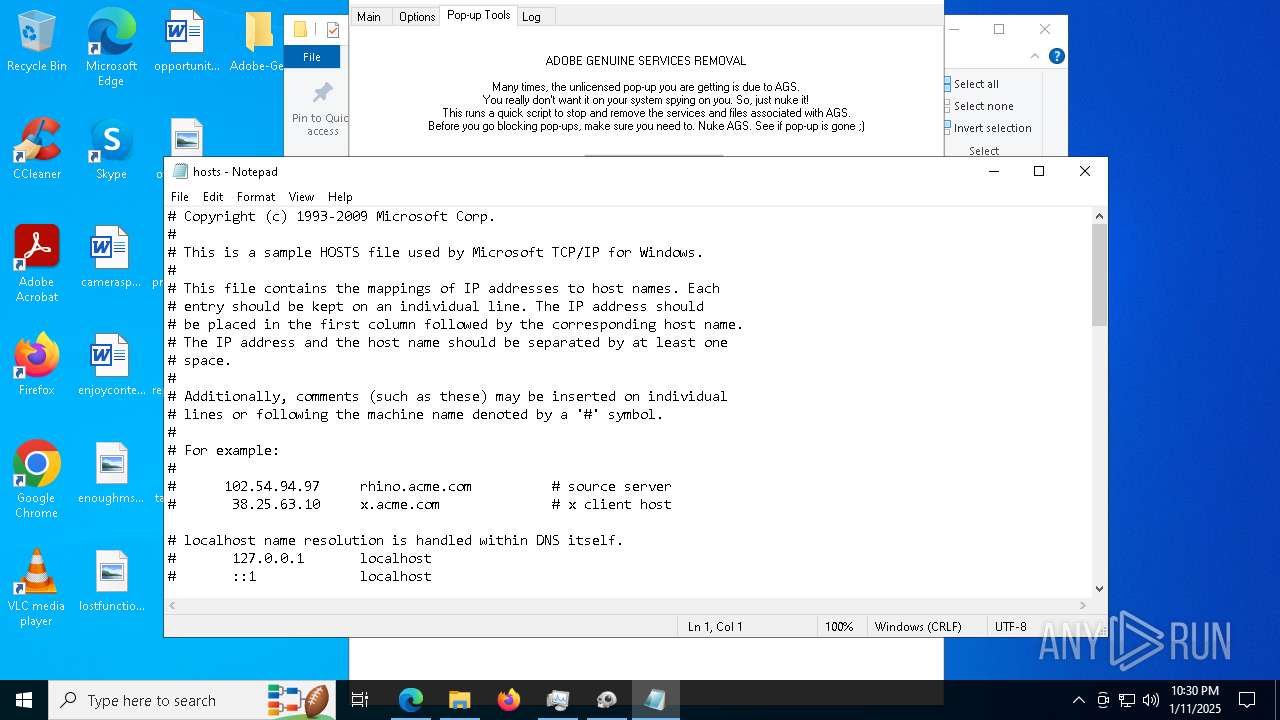
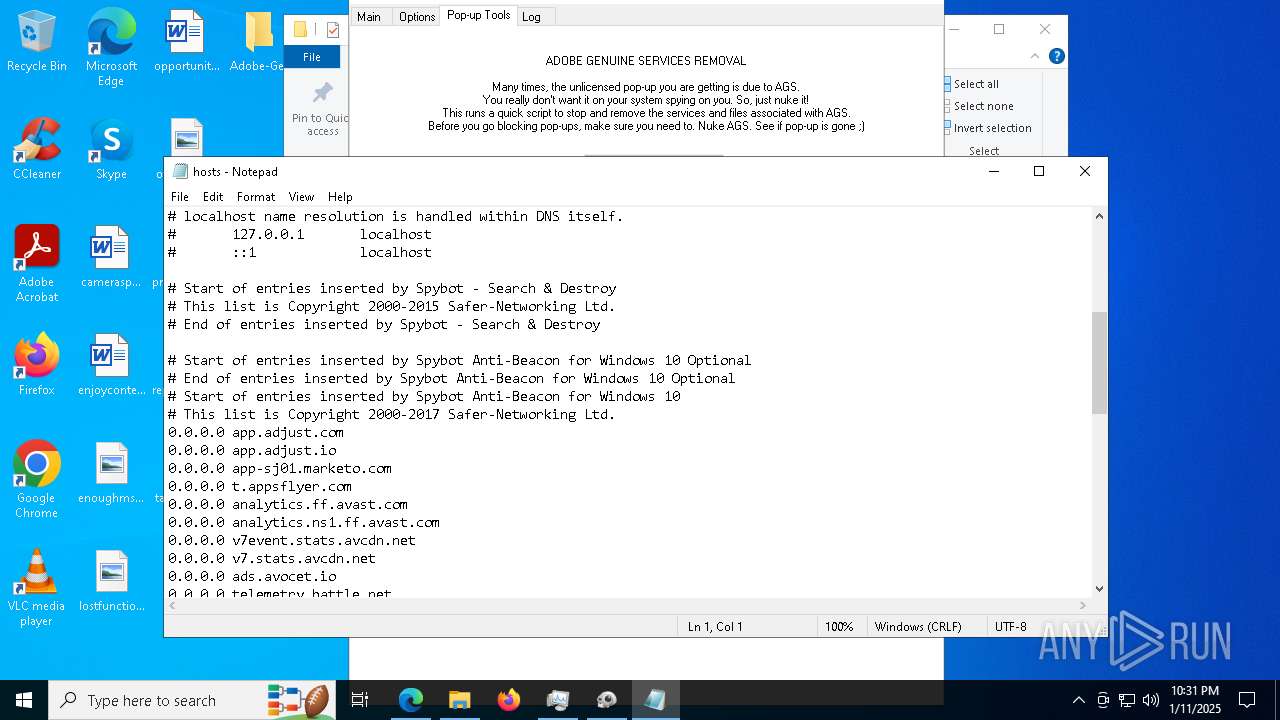
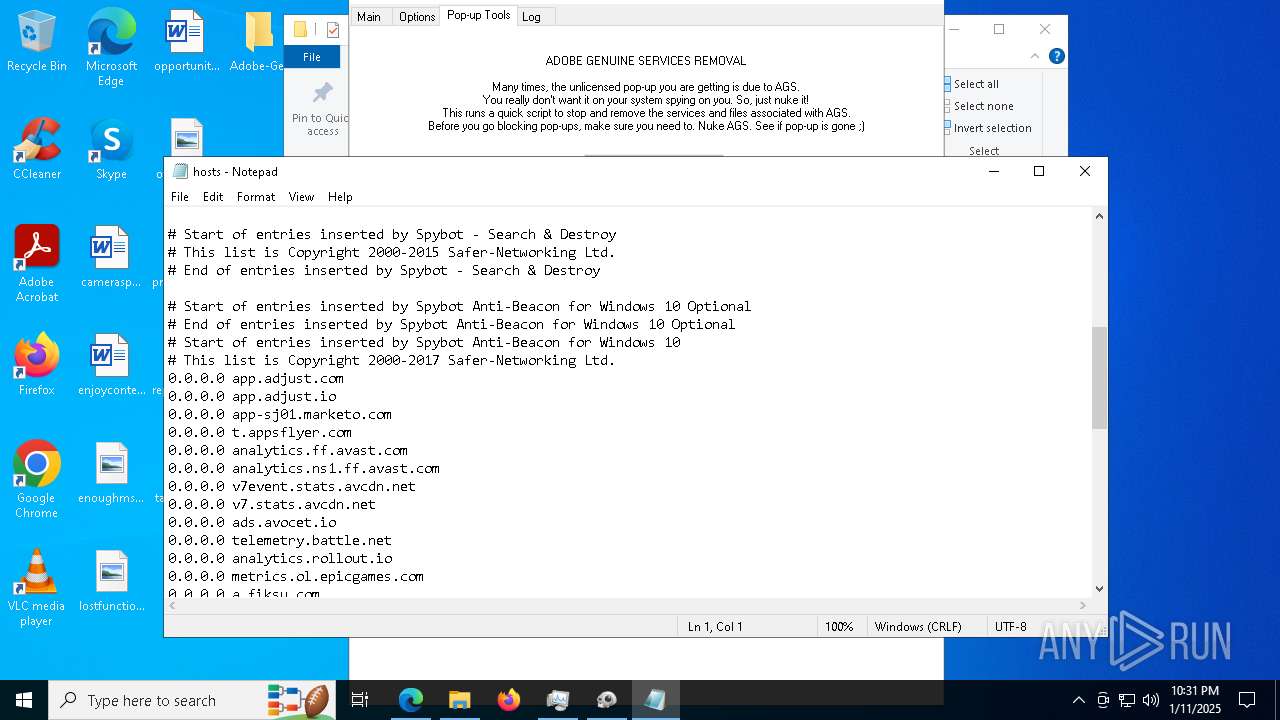
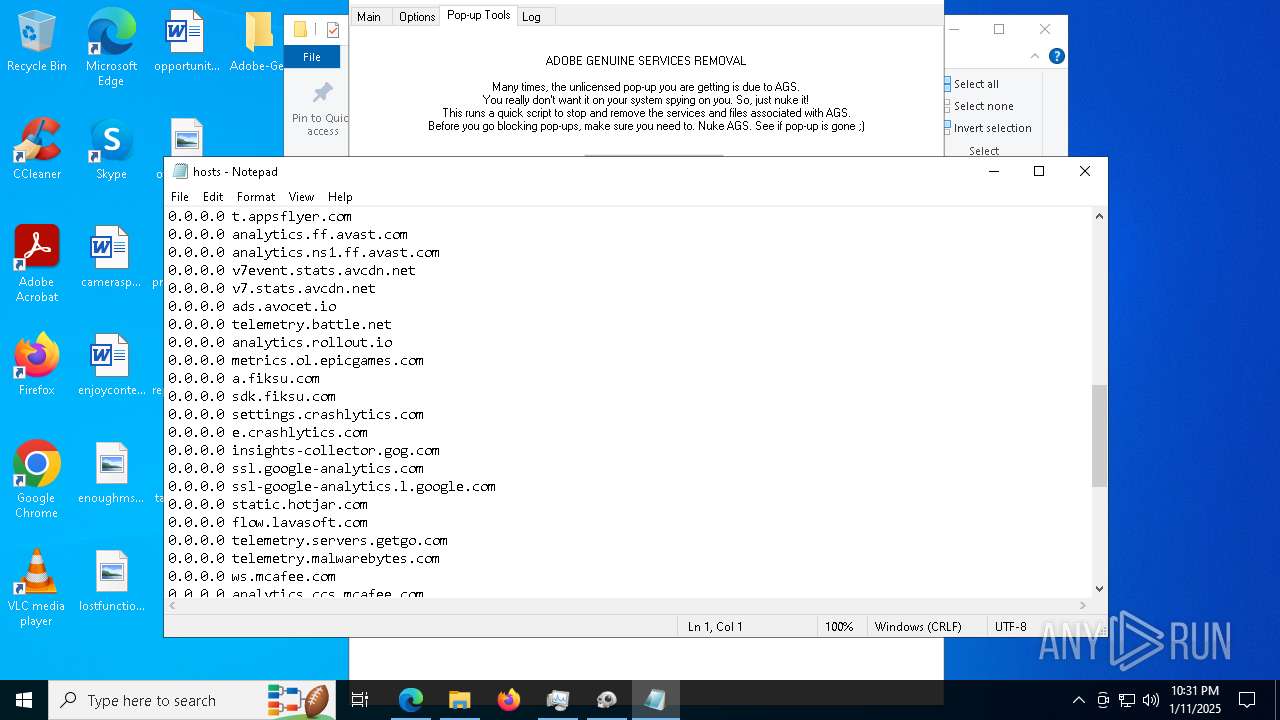
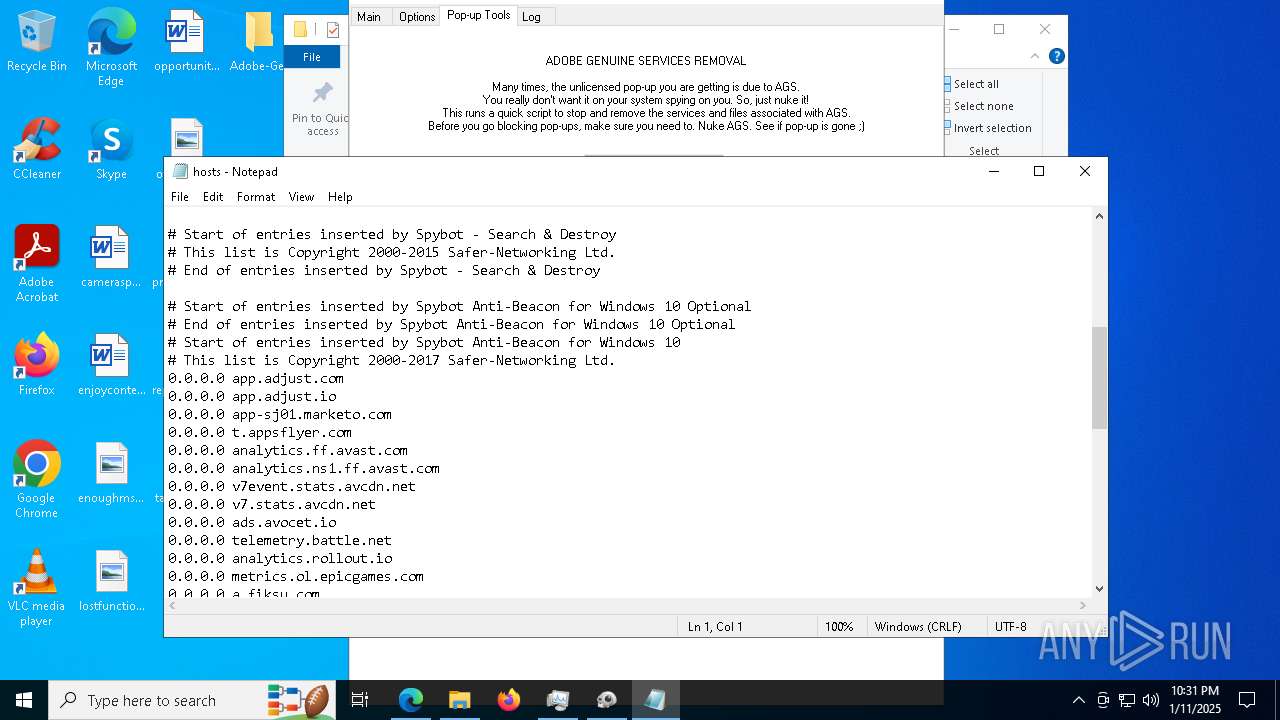
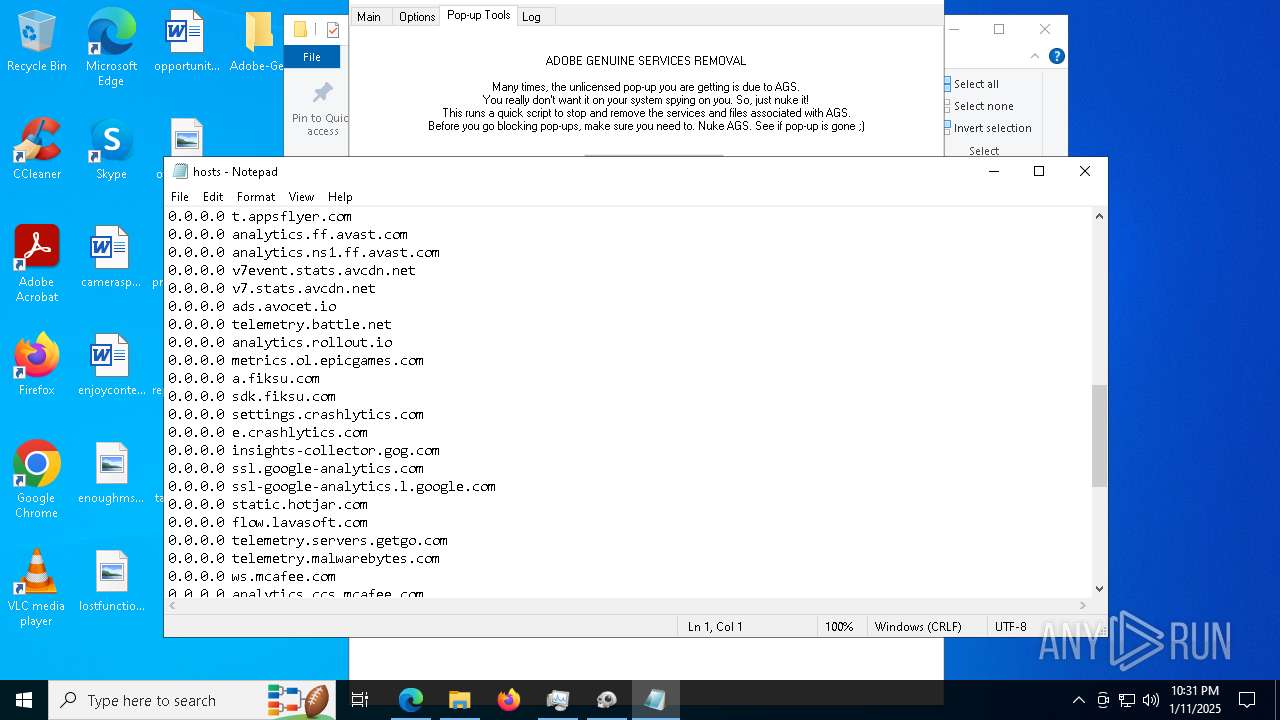
Start notepad (likely ransomware note)
- AdobeGenP.exe (PID: 8036)
Removes files via Powershell
- powershell.exe (PID: 3260)
- powershell.exe (PID: 8496)
Probably obfuscated PowerShell command line is found
- AdobeGenP.exe (PID: 8036)
Manipulates environment variables
- powershell.exe (PID: 3260)
Reads Internet Explorer settings
- Creative_Cloud_Set-Up.exe (PID: 7456)
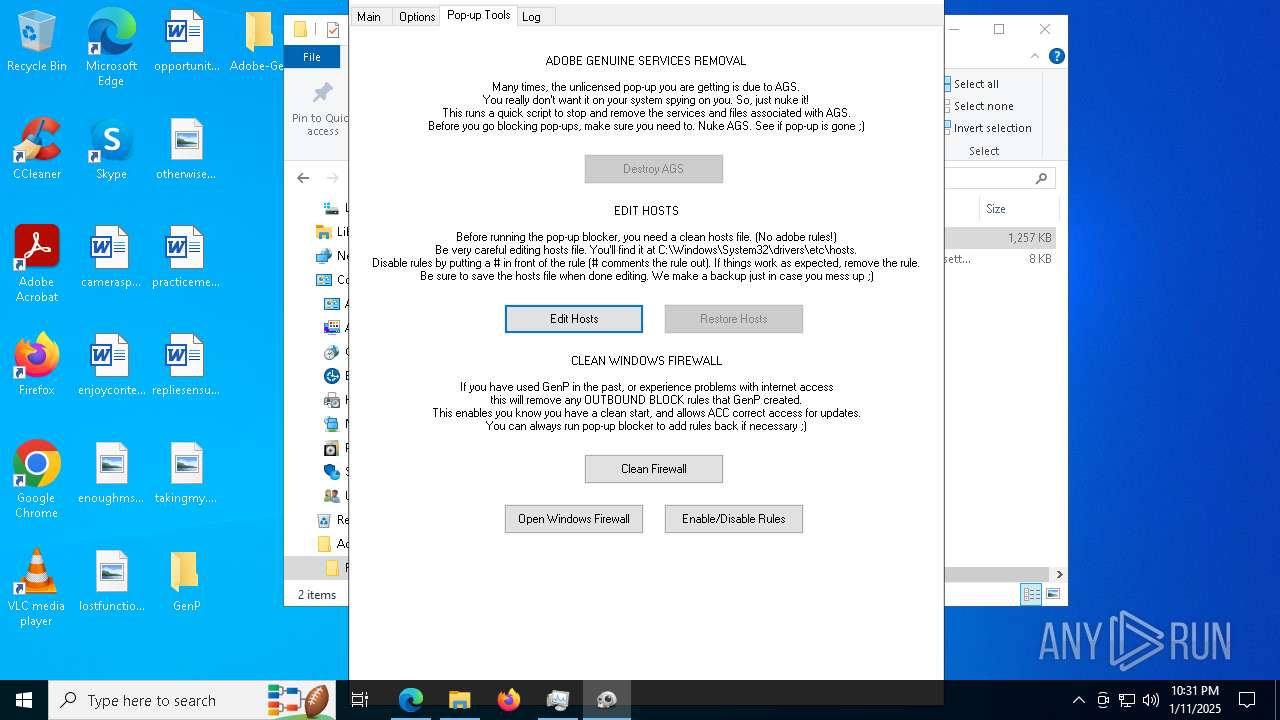
Uses NETSH.EXE to delete a firewall rule or allowed programs
- AdobeGenP.exe (PID: 8036)
Uses NETSH.EXE to add a firewall rule or allowed programs
- AdobeGenP.exe (PID: 8036)
Executable content was dropped or overwritten
- AdobeGenP.exe (PID: 8036)
INFO
Checks supported languages
- AdobeGenP-3.4.13.4.exe (PID: 3984)
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- NSudoLG.exe (PID: 128)
- AdobeGenP-3.4.13.4.exe (PID: 3812)
- Creative_Cloud_Set-Up.exe (PID: 7456)
- identity_helper.exe (PID: 1856)
- Creative_Cloud_Set-Up.exe (PID: 6888)
- AdobeGenP.exe (PID: 8036)
- RunAsTI.exe (PID: 2736)
- AdobeGenP.exe (PID: 6096)
- RunAsTI.exe (PID: 8776)
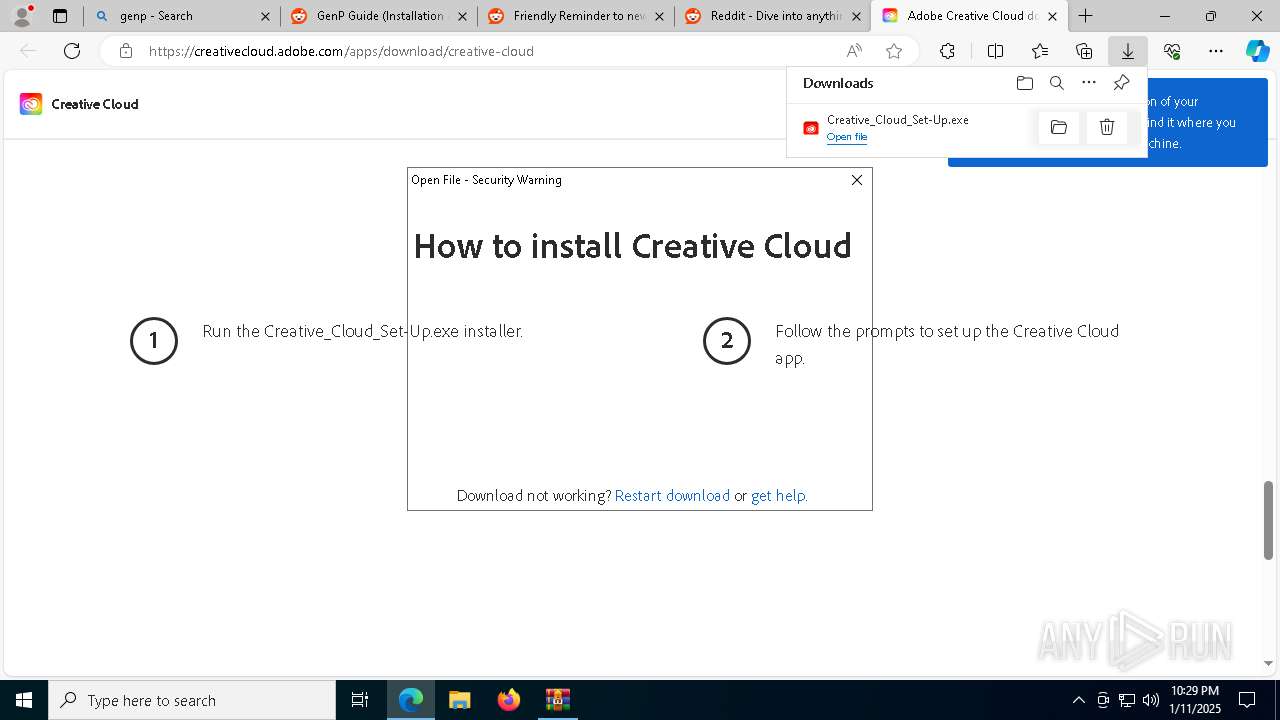
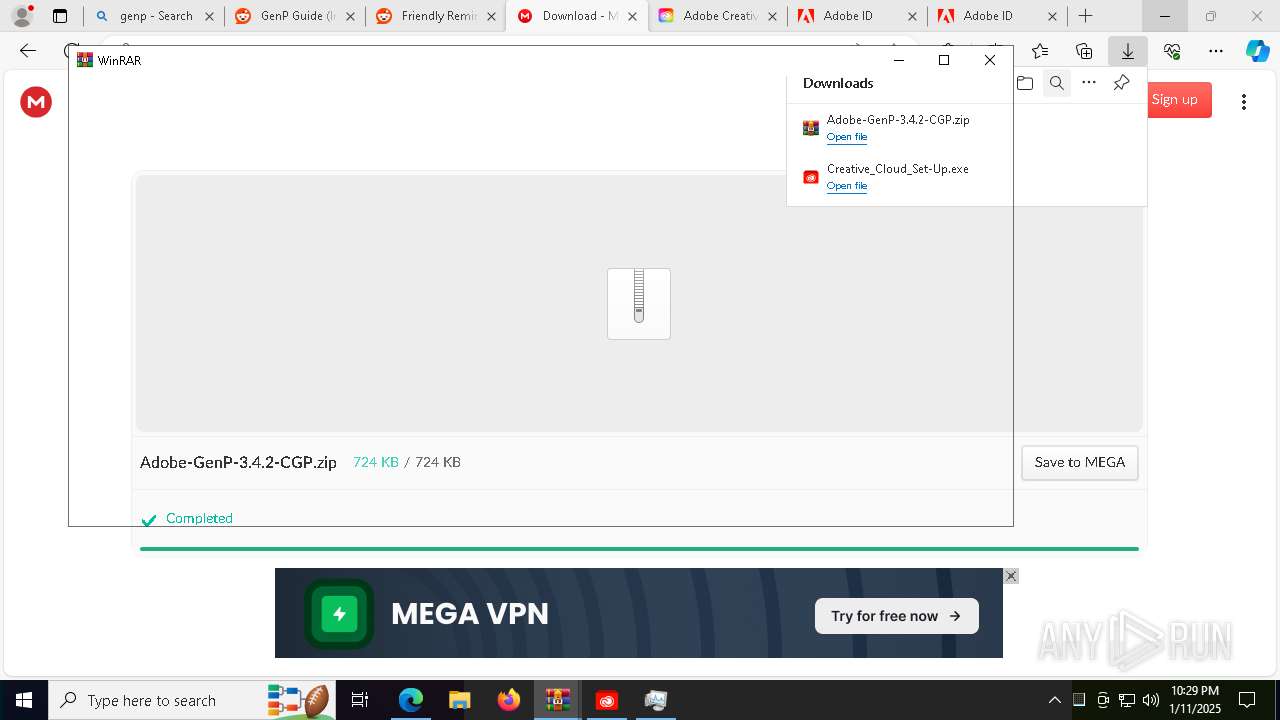
The process uses the downloaded file
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- WinRAR.exe (PID: 6336)
- msedge.exe (PID: 6580)
- Creative_Cloud_Set-Up.exe (PID: 7456)
- msedge.exe (PID: 4708)
- WinRAR.exe (PID: 8452)
- msedge.exe (PID: 9152)
- powershell.exe (PID: 3260)
Process checks computer location settings
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- Creative_Cloud_Set-Up.exe (PID: 7456)
Reads the computer name
- AdobeGenP-3.4.13.4.exe (PID: 3984)
- NSudoLG.exe (PID: 128)
- AdobeGenP-3.4.13.4.exe (PID: 3812)
- identity_helper.exe (PID: 1856)
- Creative_Cloud_Set-Up.exe (PID: 7456)
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- Creative_Cloud_Set-Up.exe (PID: 6888)
- AdobeGenP.exe (PID: 8036)
- RunAsTI.exe (PID: 2736)
- AdobeGenP.exe (PID: 6096)
- RunAsTI.exe (PID: 8776)
Reads mouse settings
- AdobeGenP-3.4.13.4.exe (PID: 3984)
- AdobeGenP-3.4.13.4.exe (PID: 3812)
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- AdobeGenP.exe (PID: 8036)
- AdobeGenP.exe (PID: 6096)
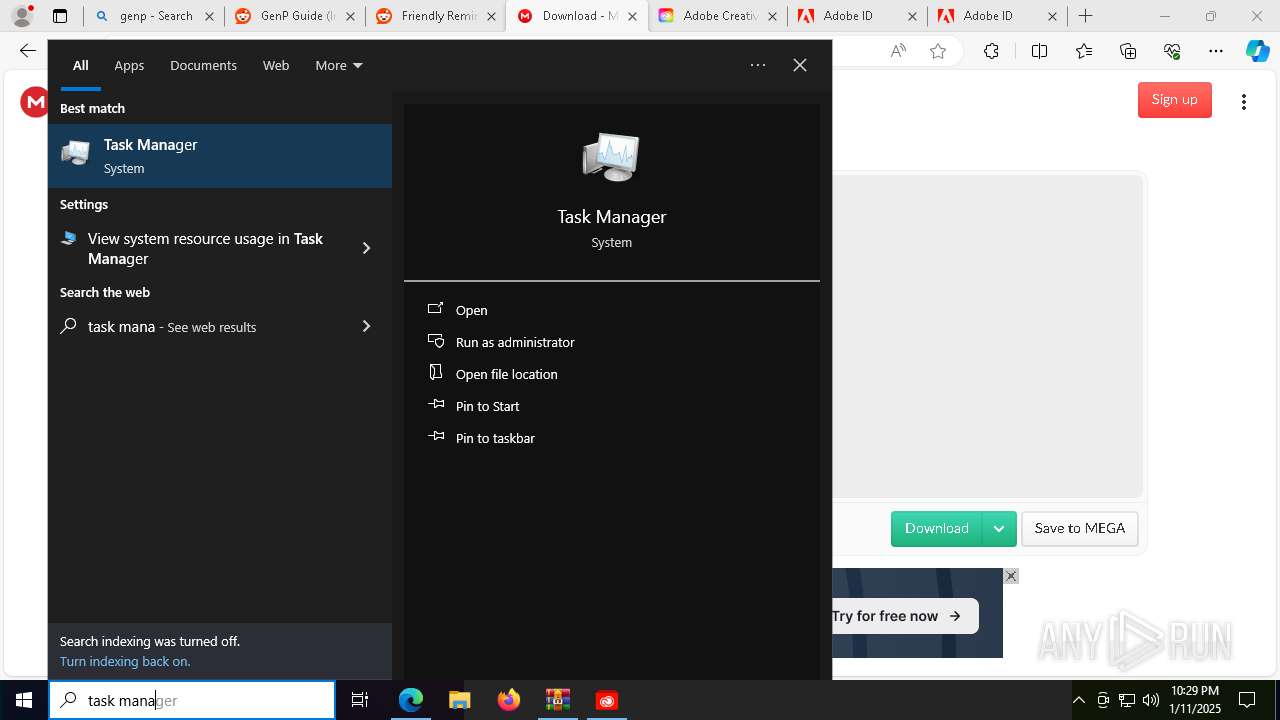
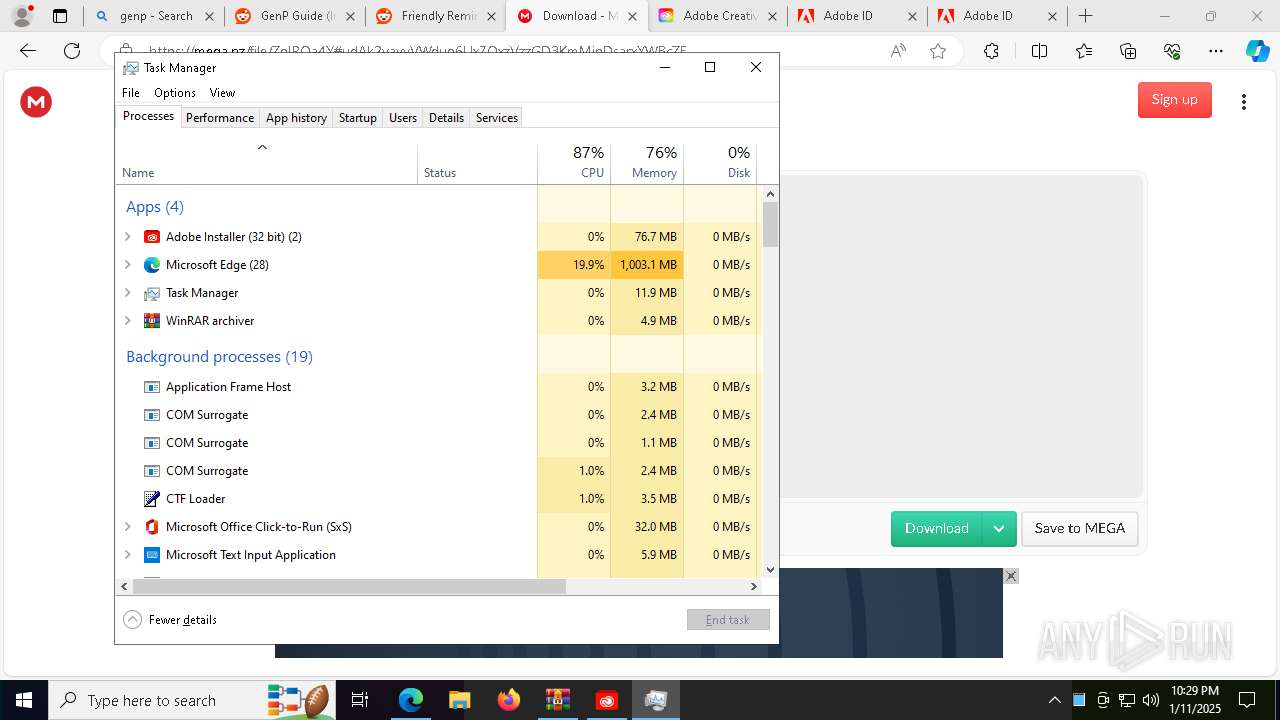
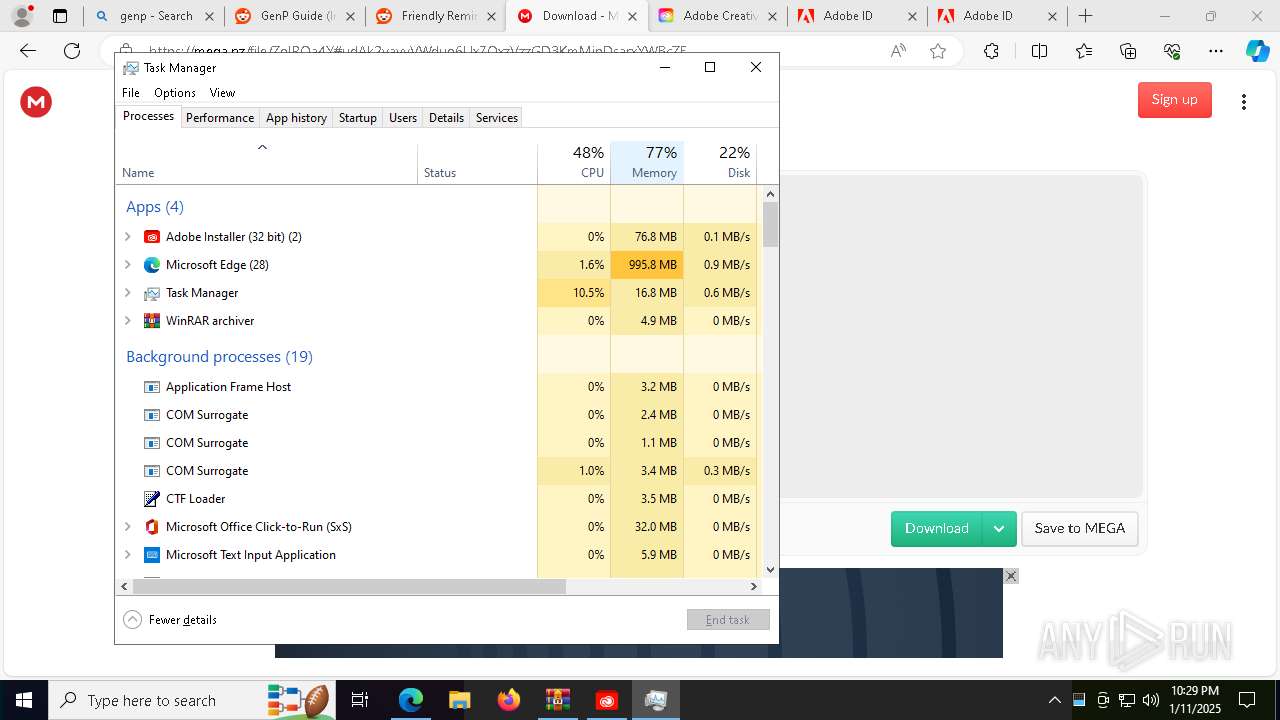
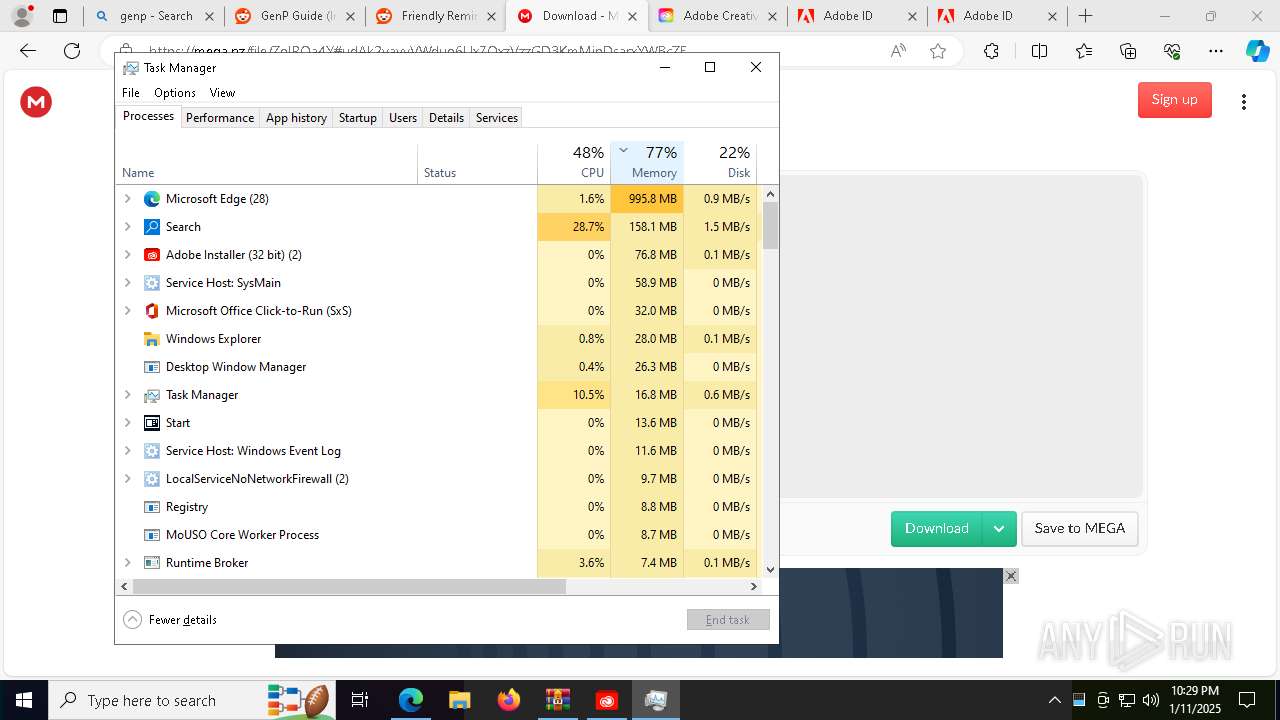
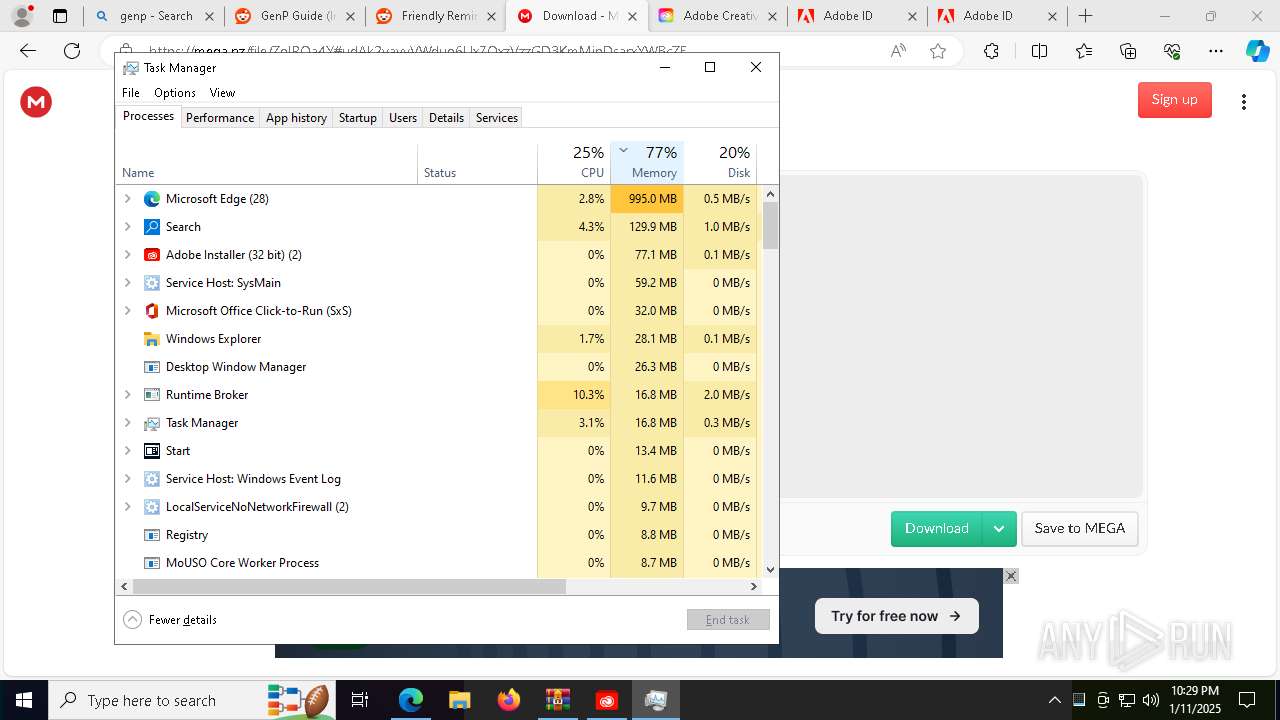
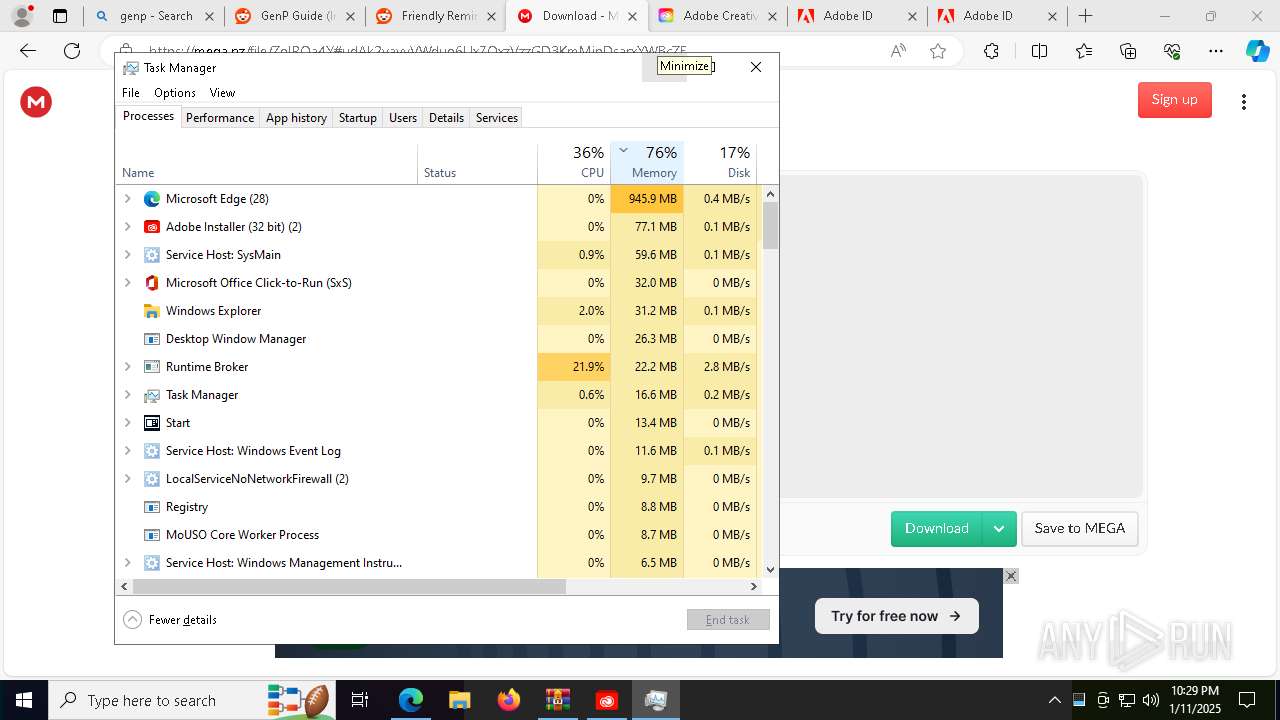
Manual execution by a user
- AdobeGenP-3.4.13.4.exe (PID: 5720)
- msedge.exe (PID: 4708)
- Taskmgr.exe (PID: 8560)
- Taskmgr.exe (PID: 8612)
- AdobeGenP.exe (PID: 8320)
- AdobeGenP.exe (PID: 8036)
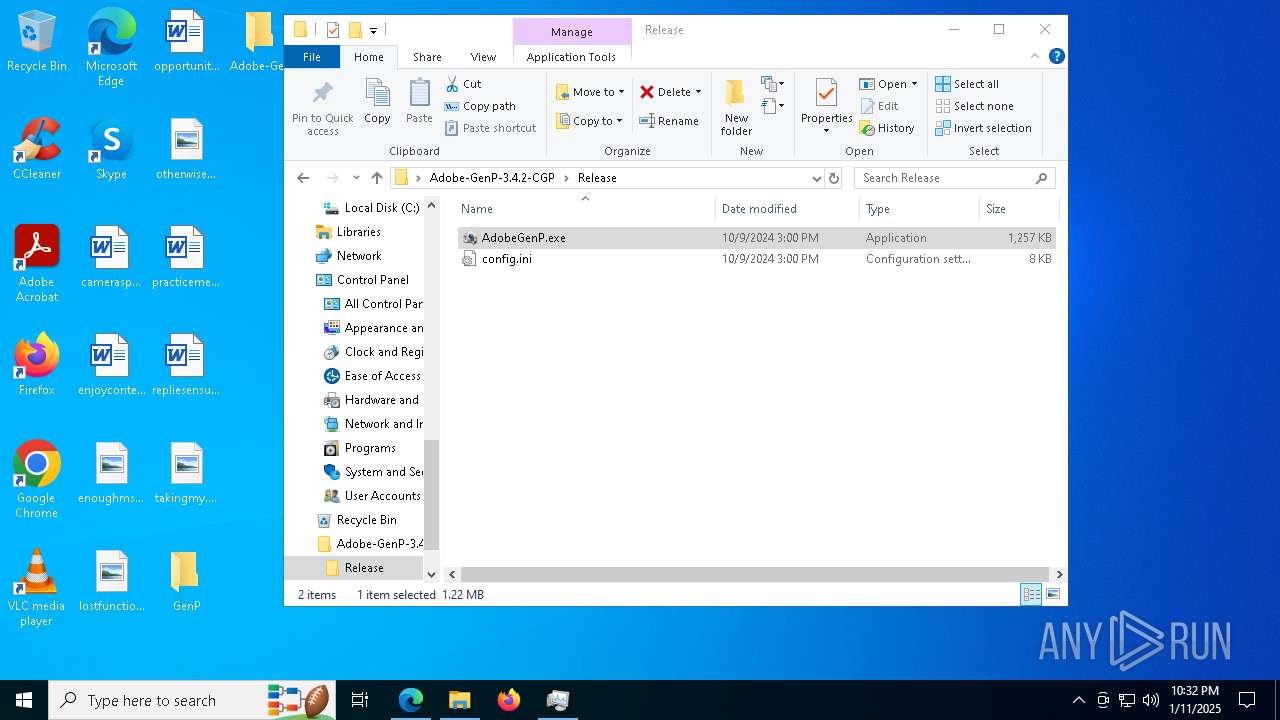
Creates files in the program directory
- AdobeGenP-3.4.13.4.exe (PID: 3812)
Application launched itself
- msedge.exe (PID: 4708)
Executable content was dropped or overwritten
- msedge.exe (PID: 6844)
- msedge.exe (PID: 4708)
- WinRAR.exe (PID: 6336)
- WinRAR.exe (PID: 8452)
- msedge.exe (PID: 1876)
Connects to unusual port
- msedge.exe (PID: 6844)
The sample compiled with english language support
- msedge.exe (PID: 6844)
- msedge.exe (PID: 4708)
- WinRAR.exe (PID: 6336)
- WinRAR.exe (PID: 8452)
- msedge.exe (PID: 1876)
The process uses AutoIt
- AdobeGenP-3.4.13.4.exe (PID: 3812)
- AdobeGenP.exe (PID: 8036)
Reads Environment values
- identity_helper.exe (PID: 1856)
Create files in a temporary directory
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
- AdobeGenP.exe (PID: 8036)
Reads CPU info
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
Creates files or folders in the user directory
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
Checks proxy server information
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
- powershell.exe (PID: 3260)
Reads the machine GUID from the registry
- Creative_Cloud_Set-Up.exe (PID: 7456)
Reads the software policy settings
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 8612)
- notepad.exe (PID: 7436)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4708)
UPX packer has been detected
- Creative_Cloud_Set-Up.exe (PID: 7456)
- Creative_Cloud_Set-Up.exe (PID: 6888)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8496)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7368)
Disables trace logs
- powershell.exe (PID: 3260)
Process checks whether UAC notifications are on
- Creative_Cloud_Set-Up.exe (PID: 7456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:07 21:52:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | GenP/ |
Total processes
265
Monitored processes
122
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Users\admin\Desktop\GenP\NSudoLG.exe -U:T -P:E -M:S "C:\Users\admin\Desktop\GenP\AdobeGenP-3.4.13.4.exe" | C:\Users\admin\Desktop\GenP\NSudoLG.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: M2-Team Integrity Level: HIGH Description: NSudo Launcher Exit code: 0 Version: 8.2.0.0 Modules
| |||||||||||||||
| 1016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5644 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5632 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7400 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7144 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=3924 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6532 --field-trial-handle=2296,i,13863860132571097797,16854680720359119477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1888 | "C:\WINDOWS\system32\sc.exe" delete AGMService | C:\Windows\System32\sc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
53 822
Read events
53 647
Write events
151
Delete events
24
Modification events
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GenP.zip | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
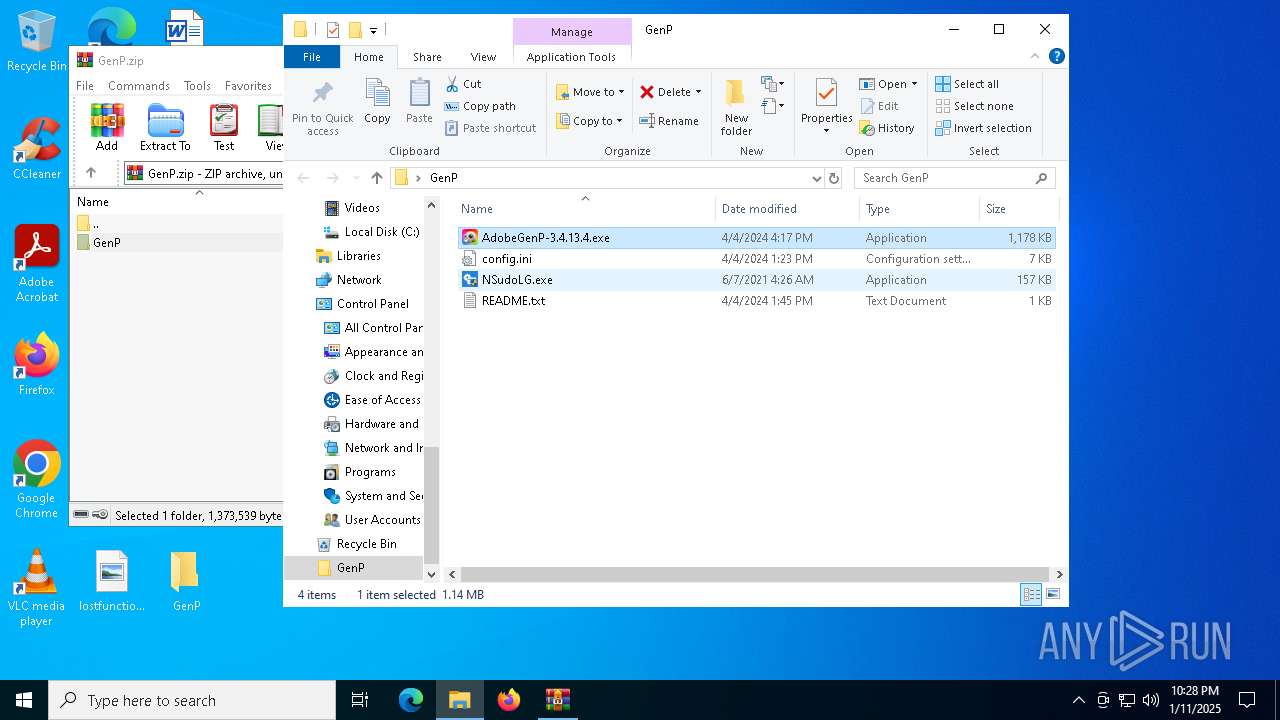
Executable files
58
Suspicious files
1 518
Text files
239
Unknown types
5
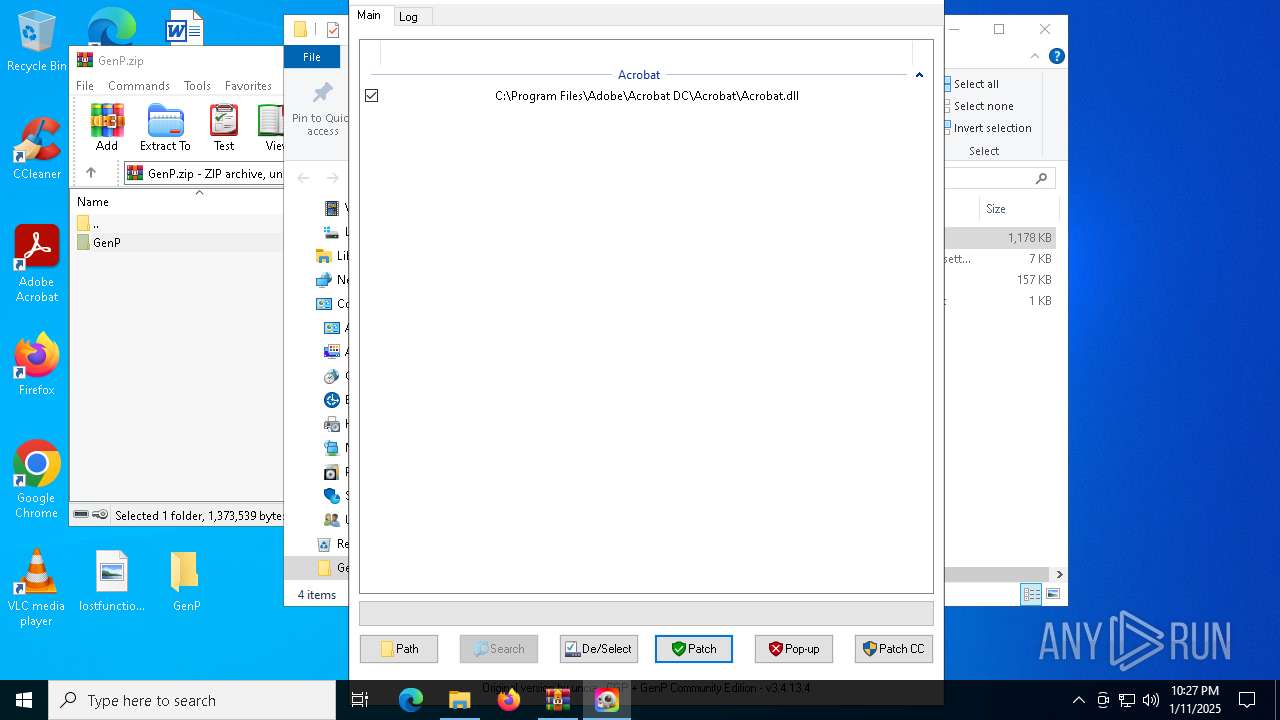
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
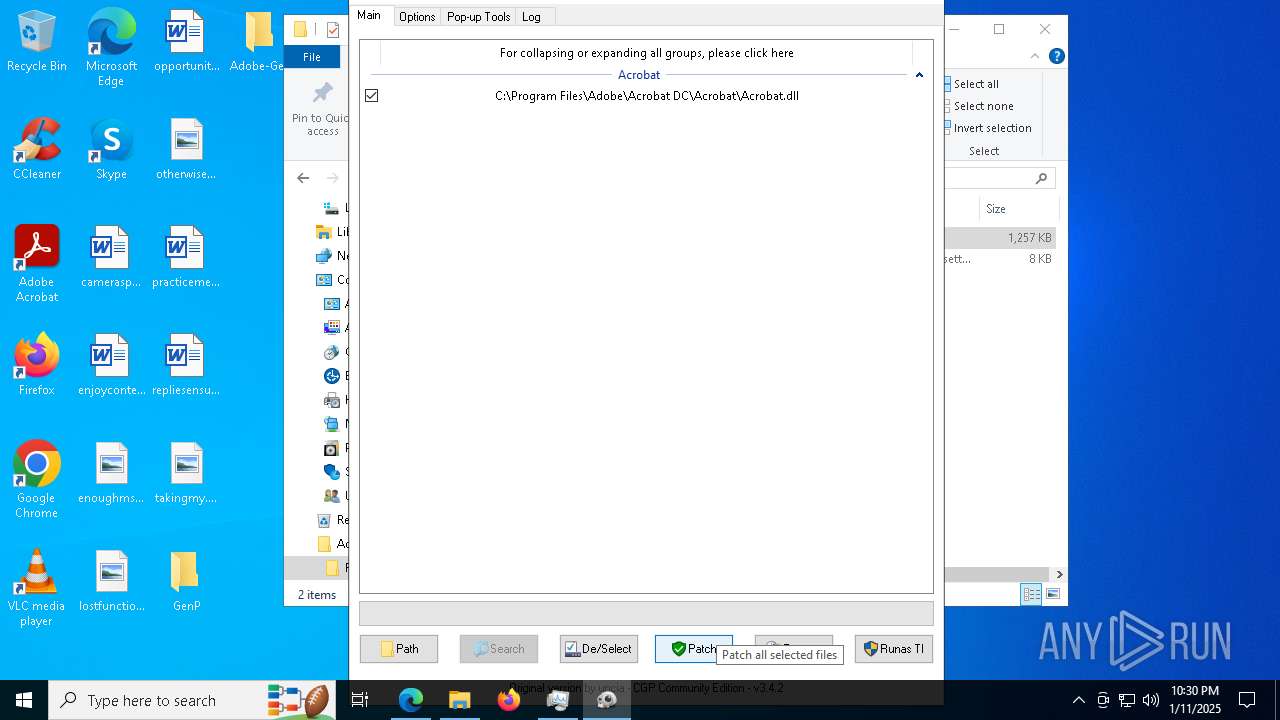
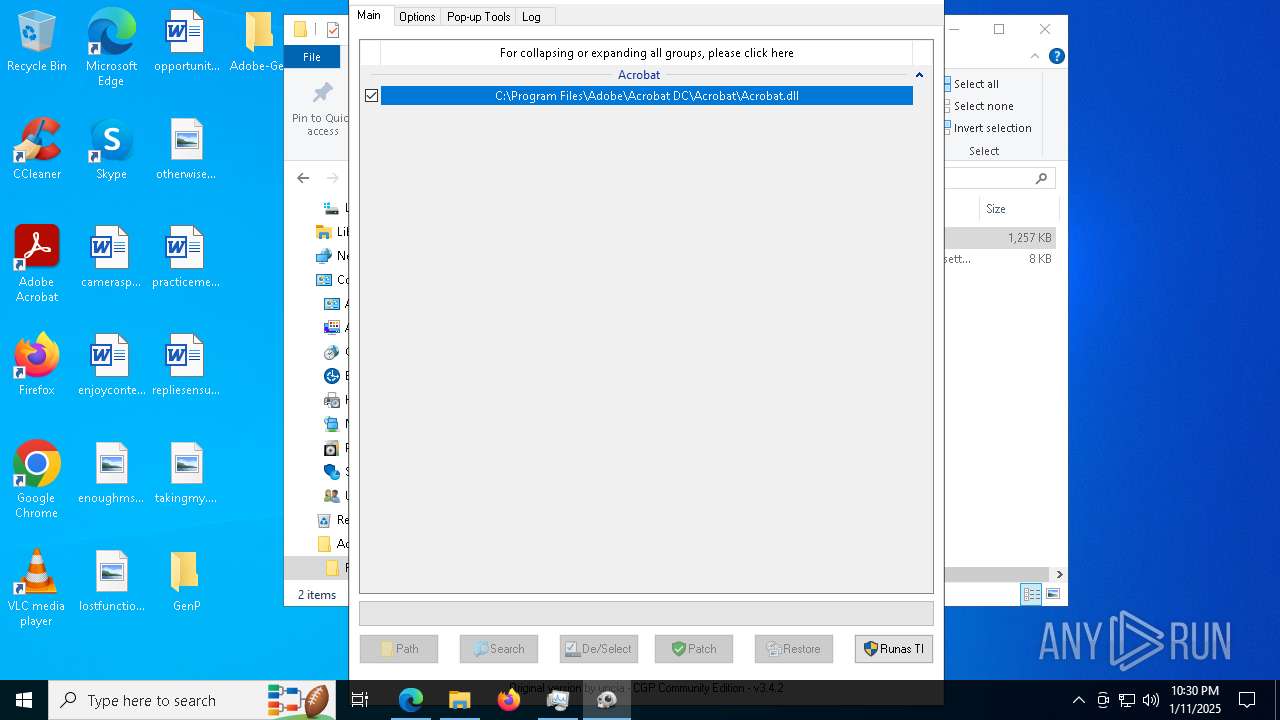
| 3812 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 3812 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF143b42.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF143b52.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF143b52.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF143b61.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF143b61.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
431
DNS requests
2 690
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4876 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.145:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4708 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4708 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAmKLzE6ssKc1CsGKg5Geww%3D | unknown | — | — | whitelisted |
7456 | Creative_Cloud_Set-Up.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
4876 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6624 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1736939538&P2=404&P3=2&P4=IL%2bh2Z85cvgImcYAQ2hvpAGJ8q9Q2%2bLb46SDgIfrt8yGkucx0nKCIgJmAxcIlzQeuVOT4JZXWF92rYS9O37yGQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5340 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.204.156:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
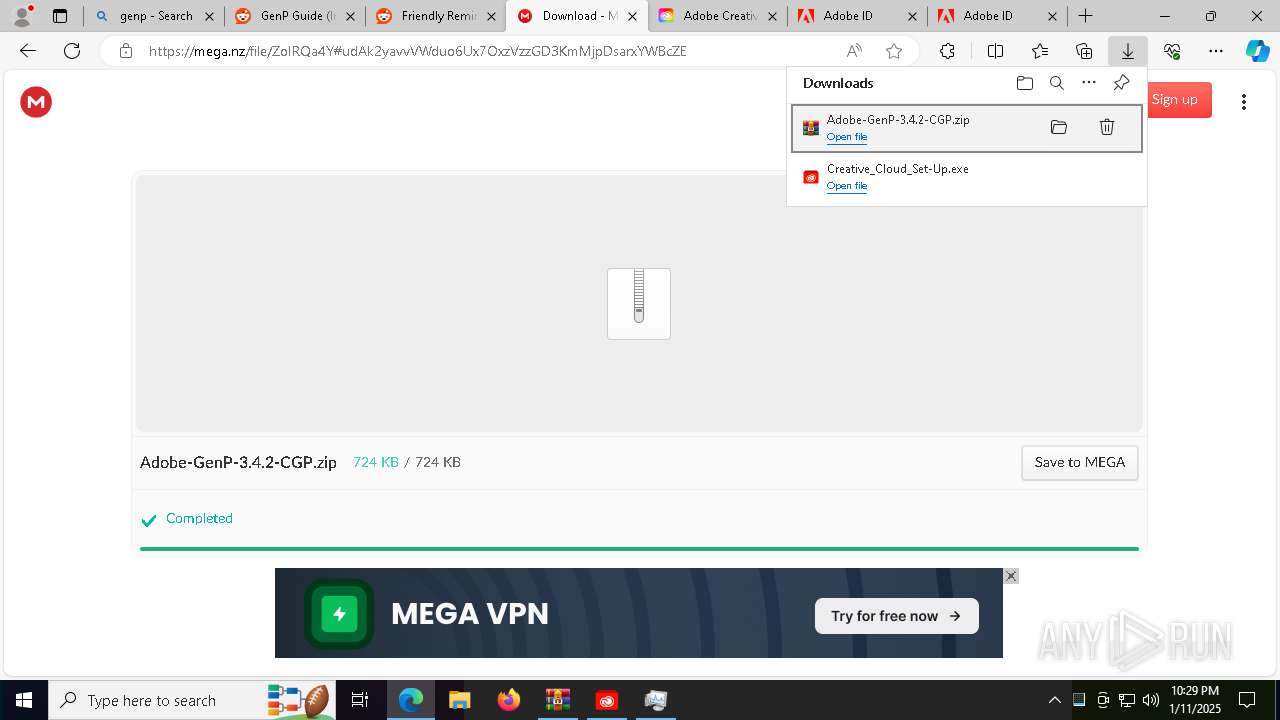
6844 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6844 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6844 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |