| File name: | bot.exe |
| Full analysis: | https://app.any.run/tasks/03c3b084-73d0-4a85-916b-5be7b6f6562b |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 16:03:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable |
| MD5: | A20FD5522E35EAE3FA566C40454E89B7 |
| SHA1: | E07EB72637B6FB99D2656610FD61EF7AF66E5D55 |
| SHA256: | 5BB1EAB89C1B5993A671FACA3F45A4BC1116D770A4BDA3BE0DC3F2D4F66CB375 |
| SSDEEP: | 3072:teqAtWZkushrKFg7BuqCGFMSPBHUj5IcfFxoRUNZTxs83Vrpr:tJA6DYl1up4BHUj5IcQUfxLrl |
MALICIOUS
Application was injected by another process
- dwm.exe (PID: 280)
- ctfmon.exe (PID: 1004)
Runs injected code in another process
- odxai.exe (PID: 1140)
Actions looks like stealing of personal data
- WinMail.exe (PID: 3892)
Changes settings of System certificates
- WinMail.exe (PID: 3892)
SUSPICIOUS
Executable content was dropped or overwritten
- bot.exe (PID: 3136)
Creates files in the user directory
- bot.exe (PID: 3136)
Reads Internet Cache Settings
- WinMail.exe (PID: 3892)
Executed via COM
- WinMail.exe (PID: 3892)
Starts itself from another location
- bot.exe (PID: 3136)
Reads internet explorer settings
- WinMail.exe (PID: 3892)
Starts CMD.EXE for commands execution
- bot.exe (PID: 3136)
Adds / modifies Windows certificates
- WinMail.exe (PID: 3892)
INFO
Reads settings of System Certificates
- WinMail.exe (PID: 3892)
- chrome.exe (PID: 1428)
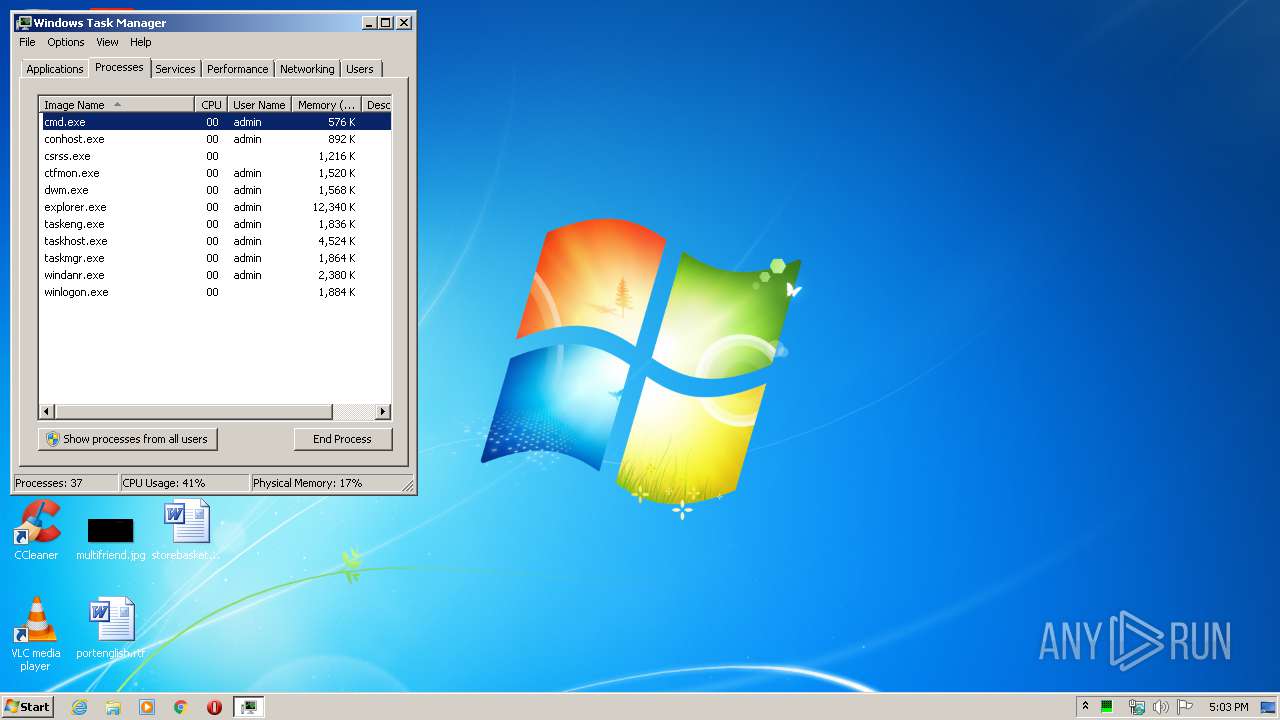
Manual execution by user
- taskmgr.exe (PID: 3252)
- chrome.exe (PID: 2688)
Reads the hosts file
- chrome.exe (PID: 2688)
- chrome.exe (PID: 1428)
Application launched itself
- chrome.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.5) |
|---|---|---|
| .exe | | | DOS Executable Borland Pascal 7.0x (19.2) |
| .exe | | | Generic Win/DOS Executable (18.8) |
| .exe | | | DOS Executable Generic (18.8) |
| .vxd | | | VXD Driver (0.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2017 14:19:31 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0000 |
| Pages in file: | 0x0000 |
| Relocations: | 0x0000 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jul-2017 14:19:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00020584 | 0x00020600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70201 |
.data | 0x00022000 | 0x00002050 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.61502 |
.reloc | 0x00025000 | 0x00001664 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.63384 |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Secur32.dll |
USER32.dll |
Total processes
67
Monitored processes
31
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5808679750318794377 --mojo-platform-channel-handle=4568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14193873396130219728 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1140 | "C:\Users\admin\AppData\Roaming\Opohzu\odxai.exe" | C:\Users\admin\AppData\Roaming\Opohzu\odxai.exe | — | bot.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4969737824932302005 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10732992754081669075 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17154651469981430627 --mojo-platform-channel-handle=4164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\tmpde376081.bat" | C:\Windows\system32\cmd.exe | — | bot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16872264682279525095,4477821794244330528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18275929686363907706 --mojo-platform-channel-handle=4592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 658
Read events
339
Write events
2 237
Delete events
1 082
Modification events
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IAM\Accounts |
| Operation: | write | Name: | ConnectionSettingsMigrated |
Value: 1 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail\Trident\Main |
| Operation: | write | Name: | Move System Caret |
Value: no | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail |
| Operation: | write | Name: | StoreMigratedV5 |
Value: 1 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail |
| Operation: | write | Name: | Settings Upgraded |
Value: 10 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail\Mail |
| Operation: | write | Name: | Safe Attachments |
Value: 1 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail\Mail |
| Operation: | write | Name: | Secure Safe Attachments |
Value: 1 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail |
| Operation: | write | Name: | Running |
Value: 1 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IAM |
| Operation: | write | Name: | Server ID |
Value: 2 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Identities |
| Operation: | write | Name: | Identity Ordinal |
Value: 2 | |||
| (PID) Process: | (3892) WinMail.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Mail |
| Operation: | write | Name: | LastBackup |
Value: E407050006001E00100003001B002002 | |||
Executable files
1
Suspicious files
45
Text files
205
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\edb.log | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\WindowsMail.MSMessageStore | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\Backup\old\ | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\Backup\temp\WindowsMail.MSMessageStore | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\edbtmp.log | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\Backup\temp\edb00002.log | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\Backup\temp\WindowsMail.pat | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\Backup\new | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Temp\ppcrlui_3892_2 | — | |
MD5:— | SHA256:— | |||
| 3892 | WinMail.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Mail\tmp.edb | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
21
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1428 | chrome.exe | GET | 200 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.230.125.140&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1590854595&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
1428 | chrome.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
1428 | chrome.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
1428 | chrome.exe | GET | 200 | 74.125.173.170:80 | http://r5---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.230.125.140&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1590854595&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1988 | taskhost.exe | 93.41.148.239:80 | — | Fastweb | IT | malicious |
1428 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1428 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 216.58.207.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 216.58.212.174:80 | apis.google.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 216.58.212.174:443 | apis.google.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 173.194.160.70:80 | r1---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |