| File name: | bat.bat |
| Full analysis: | https://app.any.run/tasks/80beabef-5d3f-4968-8950-3922d7e6246b |
| Verdict: | No threats detected |
| Analysis date: | November 01, 2024, 11:31:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (2032), with no line terminators |
| MD5: | B522062EE409389799B1768745929F85 |
| SHA1: | F7BE134F823F787FE6773227A589BE0729543E9F |
| SHA256: | 5BA4D21DE8871EC48BE69622A4356175899247DAA504BC381B622F3317B08D5A |
| SSDEEP: | 48:oZjnUk6yn3ylgihxykhQnsPouXUt8Zwv2CxxuTalIbU5h0vMvwn8Y9:oZjOynUgiHhoswuEt8ZexxuT1bU8Eq82 |
MALICIOUS
No malicious indicators.SUSPICIOUS
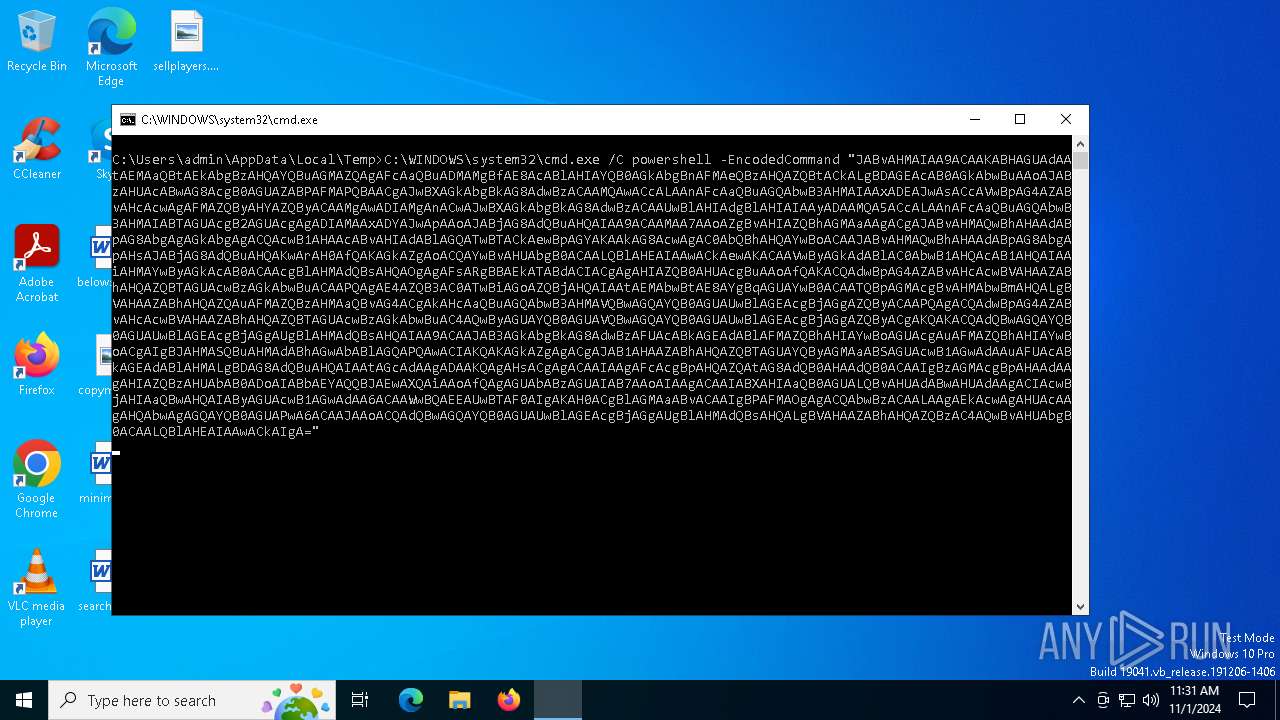
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6264)
Base64-obfuscated command line is found
- cmd.exe (PID: 6024)
Application launched itself
- cmd.exe (PID: 6264)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6024)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6024)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
136
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4348 | powershell -EncodedCommand "JABvAHMAIAA9ACAAKABHAGUAdAAtAEMAaQBtAEkAbgBzAHQAYQBuAGMAZQAgAFcAaQBuADMAMgBfAE8AcABlAHIAYQB0AGkAbgBnAFMAeQBzAHQAZQBtACkALgBDAGEAcAB0AGkAbwBuAAoAJABzAHUAcABwAG8AcgB0AGUAZABPAFMAPQBAACgAJwBXAGkAbgBkAG8AdwBzACAAMQAwACcALAAnAFcAaQBuAGQAbwB3AHMAIAAxADEAJwAsACcAVwBpAG4AZABvAHcAcwAgAFMAZQByAHYAZQByACAAMgAwADIAMgAnACwAJwBXAGkAbgBkAG8AdwBzACAAUwBlAHIAdgBlAHIAIAAyADAAMQA5ACcALAAnAFcAaQBuAGQAbwB3AHMAIABTAGUAcgB2AGUAcgAgADIAMAAxADYAJwApAAoAJABjAG8AdQBuAHQAIAA9ACAAMAA7AAoAZgBvAHIAZQBhAGMAaAAgACgAJABvAHMAQwBhAHAAdABpAG8AbgAgAGkAbgAgACQAcwB1AHAAcABvAHIAdABlAGQATwBTACkAewBpAGYAKAAkAG8AcwAgAC0AbQBhAHQAYwBoACAAJABvAHMAQwBhAHAAdABpAG8AbgApAHsAJABjAG8AdQBuAHQAKwArAH0AfQAKAGkAZgAoACQAYwBvAHUAbgB0ACAALQBlAHEAIAAwACkAewAKACAAVwByAGkAdABlAC0AbwB1AHQAcAB1AHQAIAAiAHMAYwByAGkAcAB0ACAAcgBlAHMAdQBsAHQAOgAgAFsARgBBAEkATABdACIACgAgAHIAZQB0AHUAcgBuAAoAfQAKACQAdwBpAG4AZABvAHcAcwBVAHAAZABhAHQAZQBTAGUAcwBzAGkAbwBuACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIAAtAEMAbwBtAE8AYgBqAGUAYwB0ACAATQBpAGMAcgBvAHMAbwBmAHQALgBVAHAAZABhAHQAZQAuAFMAZQBzAHMAaQBvAG4ACgAkAHcAaQBuAGQAbwB3AHMAVQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAZQByACAAPQAgACQAdwBpAG4AZABvAHcAcwBVAHAAZABhAHQAZQBTAGUAcwBzAGkAbwBuAC4AQwByAGUAYQB0AGUAVQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAZQByACgAKQAKACQAdQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAUgBlAHMAdQBsAHQAIAA9ACAAJAB3AGkAbgBkAG8AdwBzAFUAcABkAGEAdABlAFMAZQBhAHIAYwBoAGUAcgAuAFMAZQBhAHIAYwBoACgAIgBJAHMASQBuAHMAdABhAGwAbABlAGQAPQAwACIAKQAKAGkAZgAgACgAJAB1AHAAZABhAHQAZQBTAGUAYQByAGMAaABSAGUAcwB1AGwAdAAuAFUAcABkAGEAdABlAHMALgBDAG8AdQBuAHQAIAAtAGcAdAAgADAAKQAgAHsACgAgACAAIAAgAFcAcgBpAHQAZQAtAG8AdQB0AHAAdQB0ACAAIgBzAGMAcgBpAHAAdAAgAHIAZQBzAHUAbAB0ADoAIABbAEYAQQBJAEwAXQAiAAoAfQAgAGUAbABzAGUAIAB7AAoAIAAgACAAIABXAHIAaQB0AGUALQBvAHUAdABwAHUAdAAgACIAcwBjAHIAaQBwAHQAIAByAGUAcwB1AGwAdAA6ACAAWwBQAEEAUwBTAF0AIgAKAH0ACgBlAGMAaABvACAAIgBPAFMAOgAgACQAbwBzACAALAAgAEkAcwAgAHUAcAAgAHQAbwAgAGQAYQB0AGUAPwA6ACAAJAAoACQAdQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAUgBlAHMAdQBsAHQALgBVAHAAZABhAHQAZQBzAC4AQwBvAHUAbgB0ACAALQBlAHEAIAAwACkAIgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6024 | C:\WINDOWS\system32\cmd.exe /C powershell -EncodedCommand "JABvAHMAIAA9ACAAKABHAGUAdAAtAEMAaQBtAEkAbgBzAHQAYQBuAGMAZQAgAFcAaQBuADMAMgBfAE8AcABlAHIAYQB0AGkAbgBnAFMAeQBzAHQAZQBtACkALgBDAGEAcAB0AGkAbwBuAAoAJABzAHUAcABwAG8AcgB0AGUAZABPAFMAPQBAACgAJwBXAGkAbgBkAG8AdwBzACAAMQAwACcALAAnAFcAaQBuAGQAbwB3AHMAIAAxADEAJwAsACcAVwBpAG4AZABvAHcAcwAgAFMAZQByAHYAZQByACAAMgAwADIAMgAnACwAJwBXAGkAbgBkAG8AdwBzACAAUwBlAHIAdgBlAHIAIAAyADAAMQA5ACcALAAnAFcAaQBuAGQAbwB3AHMAIABTAGUAcgB2AGUAcgAgADIAMAAxADYAJwApAAoAJABjAG8AdQBuAHQAIAA9ACAAMAA7AAoAZgBvAHIAZQBhAGMAaAAgACgAJABvAHMAQwBhAHAAdABpAG8AbgAgAGkAbgAgACQAcwB1AHAAcABvAHIAdABlAGQATwBTACkAewBpAGYAKAAkAG8AcwAgAC0AbQBhAHQAYwBoACAAJABvAHMAQwBhAHAAdABpAG8AbgApAHsAJABjAG8AdQBuAHQAKwArAH0AfQAKAGkAZgAoACQAYwBvAHUAbgB0ACAALQBlAHEAIAAwACkAewAKACAAVwByAGkAdABlAC0AbwB1AHQAcAB1AHQAIAAiAHMAYwByAGkAcAB0ACAAcgBlAHMAdQBsAHQAOgAgAFsARgBBAEkATABdACIACgAgAHIAZQB0AHUAcgBuAAoAfQAKACQAdwBpAG4AZABvAHcAcwBVAHAAZABhAHQAZQBTAGUAcwBzAGkAbwBuACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIAAtAEMAbwBtAE8AYgBqAGUAYwB0ACAATQBpAGMAcgBvAHMAbwBmAHQALgBVAHAAZABhAHQAZQAuAFMAZQBzAHMAaQBvAG4ACgAkAHcAaQBuAGQAbwB3AHMAVQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAZQByACAAPQAgACQAdwBpAG4AZABvAHcAcwBVAHAAZABhAHQAZQBTAGUAcwBzAGkAbwBuAC4AQwByAGUAYQB0AGUAVQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAZQByACgAKQAKACQAdQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAUgBlAHMAdQBsAHQAIAA9ACAAJAB3AGkAbgBkAG8AdwBzAFUAcABkAGEAdABlAFMAZQBhAHIAYwBoAGUAcgAuAFMAZQBhAHIAYwBoACgAIgBJAHMASQBuAHMAdABhAGwAbABlAGQAPQAwACIAKQAKAGkAZgAgACgAJAB1AHAAZABhAHQAZQBTAGUAYQByAGMAaABSAGUAcwB1AGwAdAAuAFUAcABkAGEAdABlAHMALgBDAG8AdQBuAHQAIAAtAGcAdAAgADAAKQAgAHsACgAgACAAIAAgAFcAcgBpAHQAZQAtAG8AdQB0AHAAdQB0ACAAIgBzAGMAcgBpAHAAdAAgAHIAZQBzAHUAbAB0ADoAIABbAEYAQQBJAEwAXQAiAAoAfQAgAGUAbABzAGUAIAB7AAoAIAAgACAAIABXAHIAaQB0AGUALQBvAHUAdABwAHUAdAAgACIAcwBjAHIAaQBwAHQAIAByAGUAcwB1AGwAdAA6ACAAWwBQAEEAUwBTAF0AIgAKAH0ACgBlAGMAaABvACAAIgBPAFMAOgAgACQAbwBzACAALAAgAEkAcwAgAHUAcAAgAHQAbwAgAGQAYQB0AGUAPwA6ACAAJAAoACQAdQBwAGQAYQB0AGUAUwBlAGEAcgBjAGgAUgBlAHMAdQBsAHQALgBVAHAAZABhAHQAZQBzAC4AQwBvAHUAbgB0ACAALQBlAHEAIAAwACkAIgA=" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\bat.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 556
Read events
4 556
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sdccmt5o.3gw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4348 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E82A714991353335C40EB710F7BD9A9C | SHA256:C75BD696F43C7CB1018608E6694F2F2BC5522C06B1B71D67C0C02840A73CC4C2 | |||
| 4348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_idiefi51.lly.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
38
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2312 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4080 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |