| File name: | action1_agent(My_Organization).msi |
| Full analysis: | https://app.any.run/tasks/eedb955d-6a80-498b-b198-30dca673b324 |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2025, 19:03:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
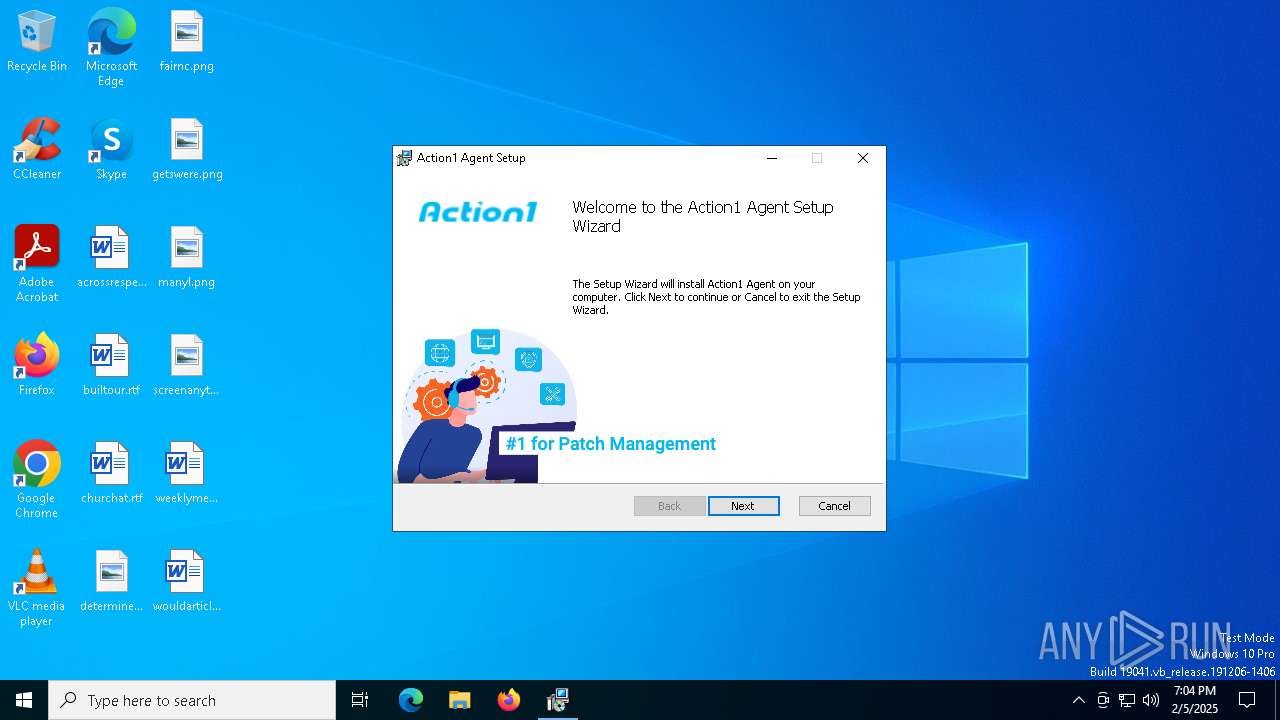
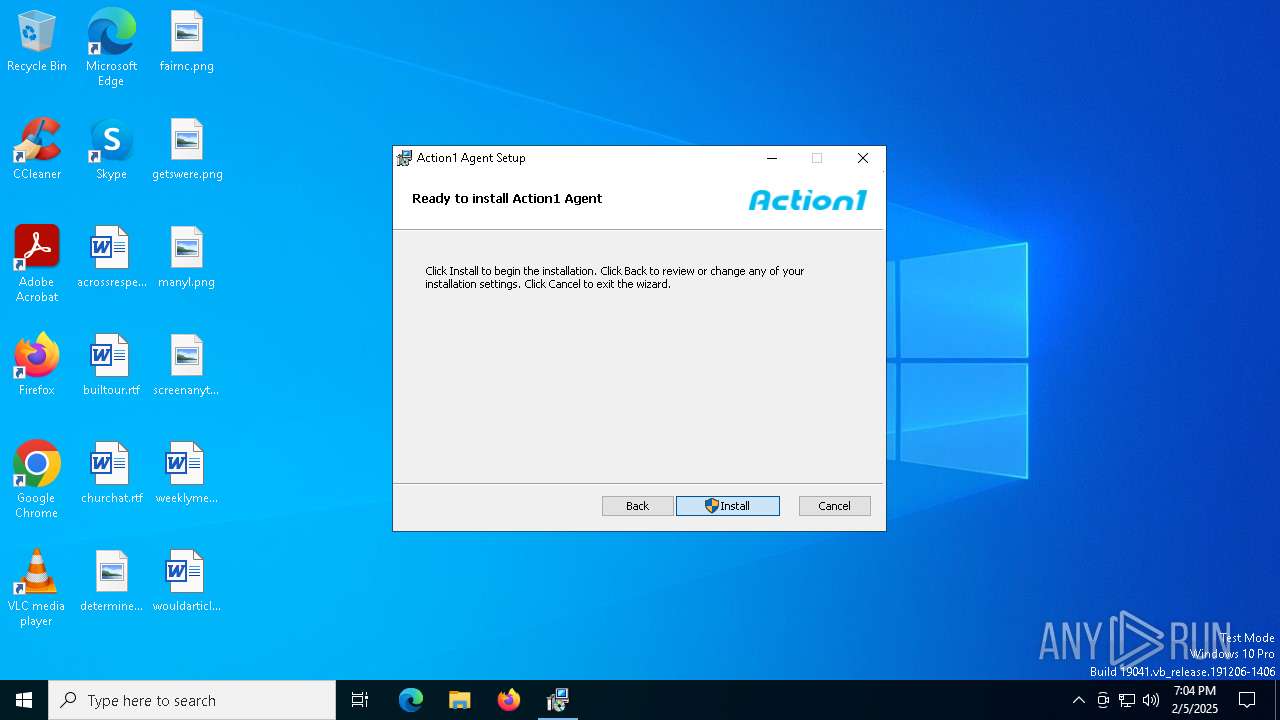
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Action1 Agent provides the ability to remotely manage computers using Action1 Platform, Author: Action1 Corporation, Keywords: Action1,Agent, Comments: Version: 5.213.614.1. Copyright (C) 2021 Action1 Corporation, Template: Intel;1033, Revision Number: {93CBCBB1-BFE5-44AF-9851-12AB61B1A154}, Create Time/Date: Mon Dec 16 17:27:58 2024, Last Saved Time/Date: Mon Dec 16 17:27:58 2024, Number of Pages: 400, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | A76B3BAE2A2A4DA1F82040E98A4300C3 |
| SHA1: | F2798E9D3CC1409ABD5C8FD41182B68FA97C2831 |
| SHA256: | 5B9B5E4FCCC07A2BBFB1C076786872F0B87E82ECA58038BC4724A722A0B99CFA |
| SSDEEP: | 98304:709tWD+72IXgMzx8Th7PIrrOjoqoE3SL9sMfR7t00vaWEaGfAmf29tjCSEU9ag/X:KhIVsEDo |
MALICIOUS
Changes powershell execution policy (Bypass)
- action1_agent.exe (PID: 2136)
Bypass execution policy to execute commands
- powershell.exe (PID: 6436)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7104)
- action1_agent.exe (PID: 2136)
Checks Windows Trust Settings
- msiexec.exe (PID: 6572)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6572)
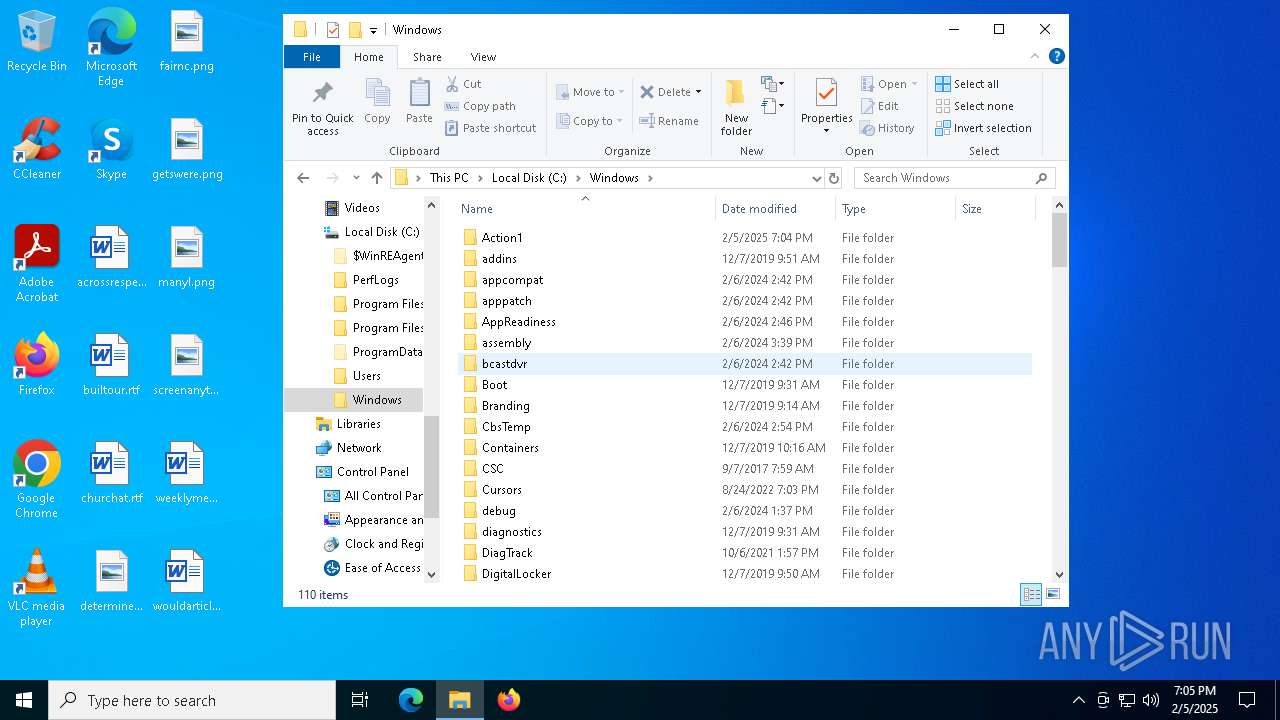
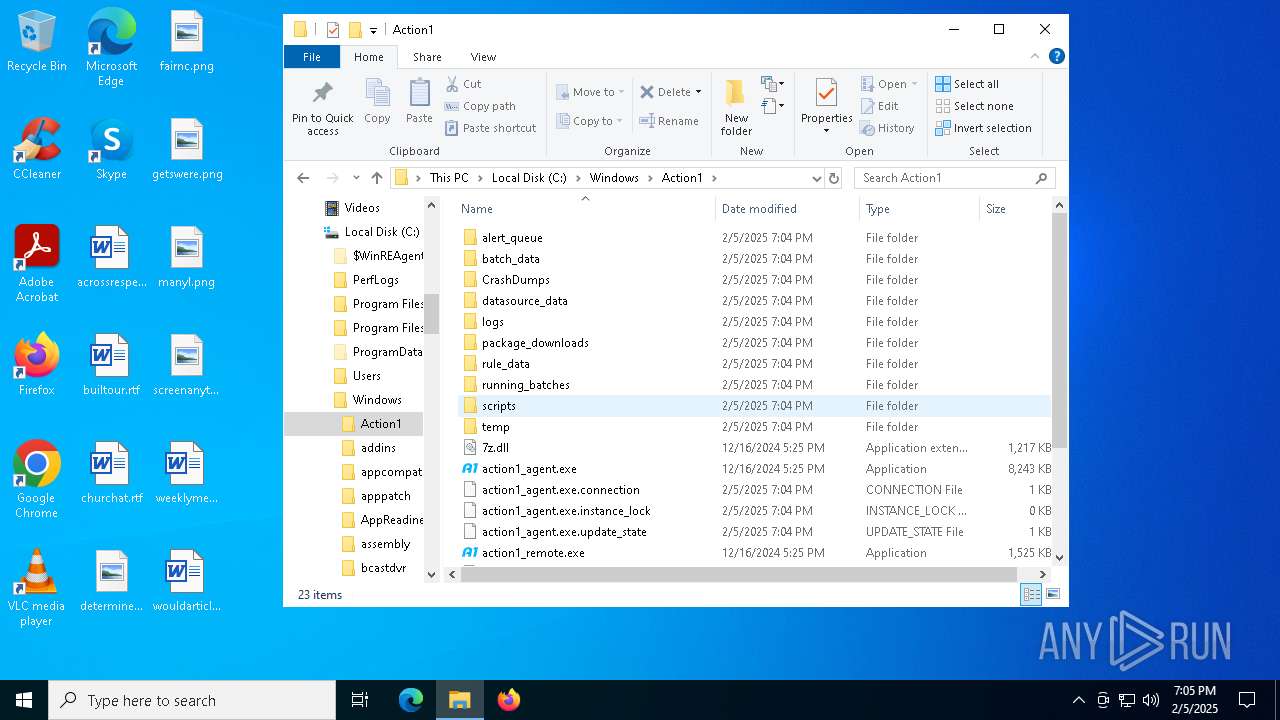
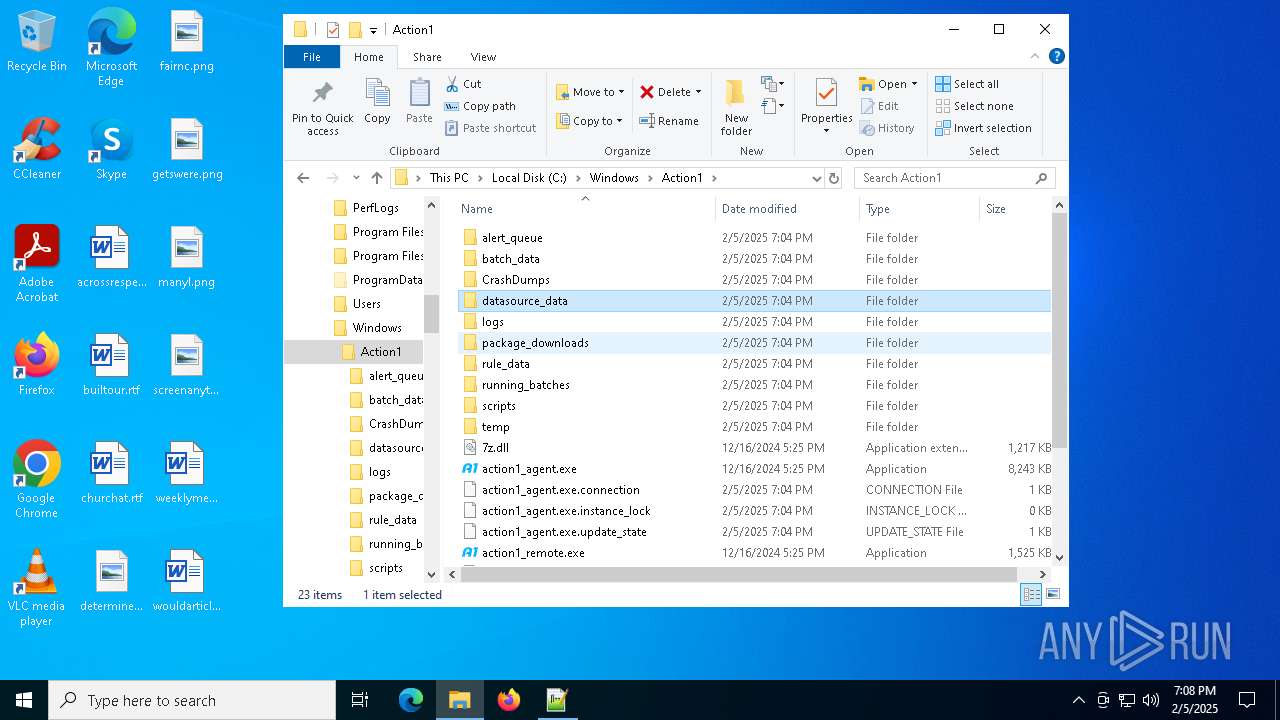
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 6572)
Process drops legitimate windows executable
- msiexec.exe (PID: 6572)
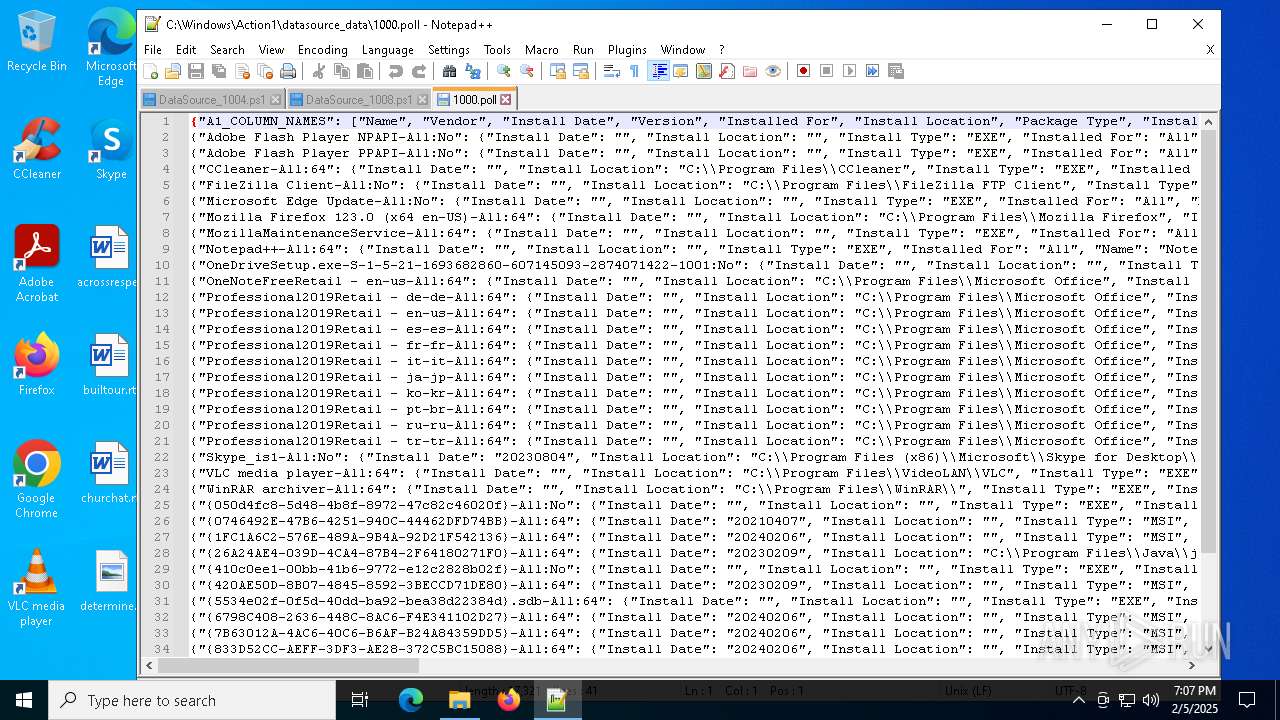
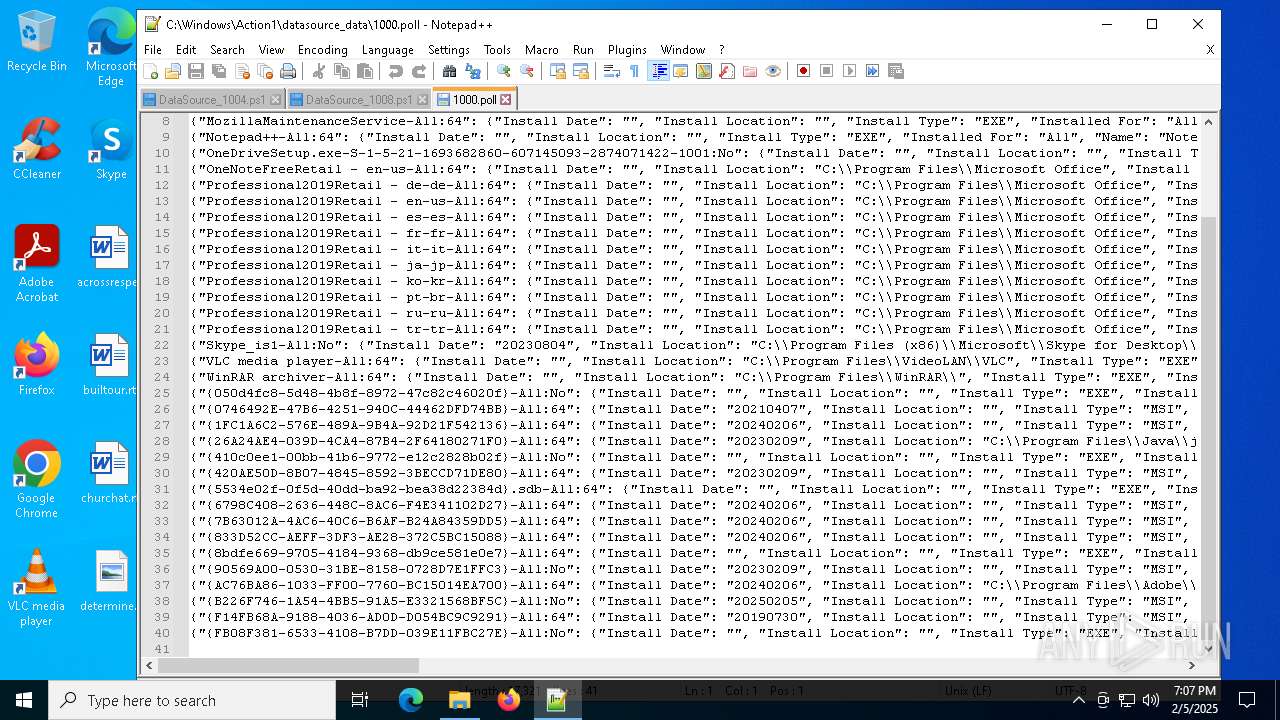
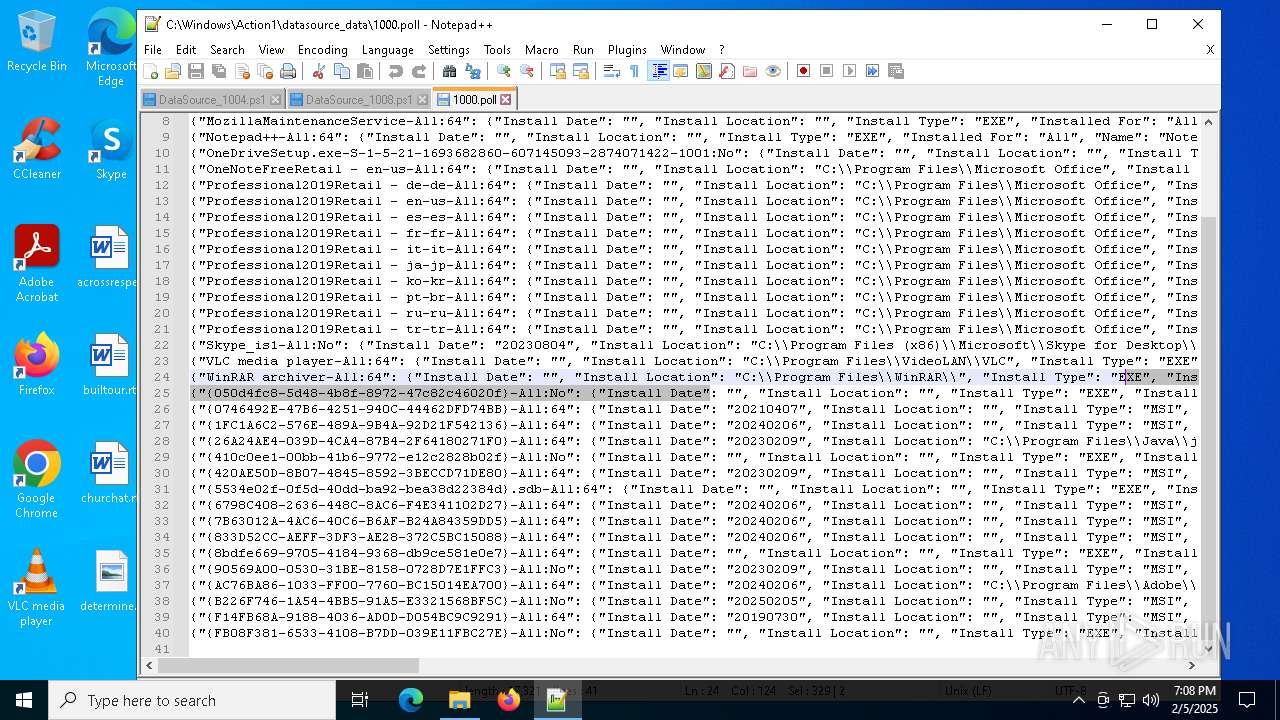
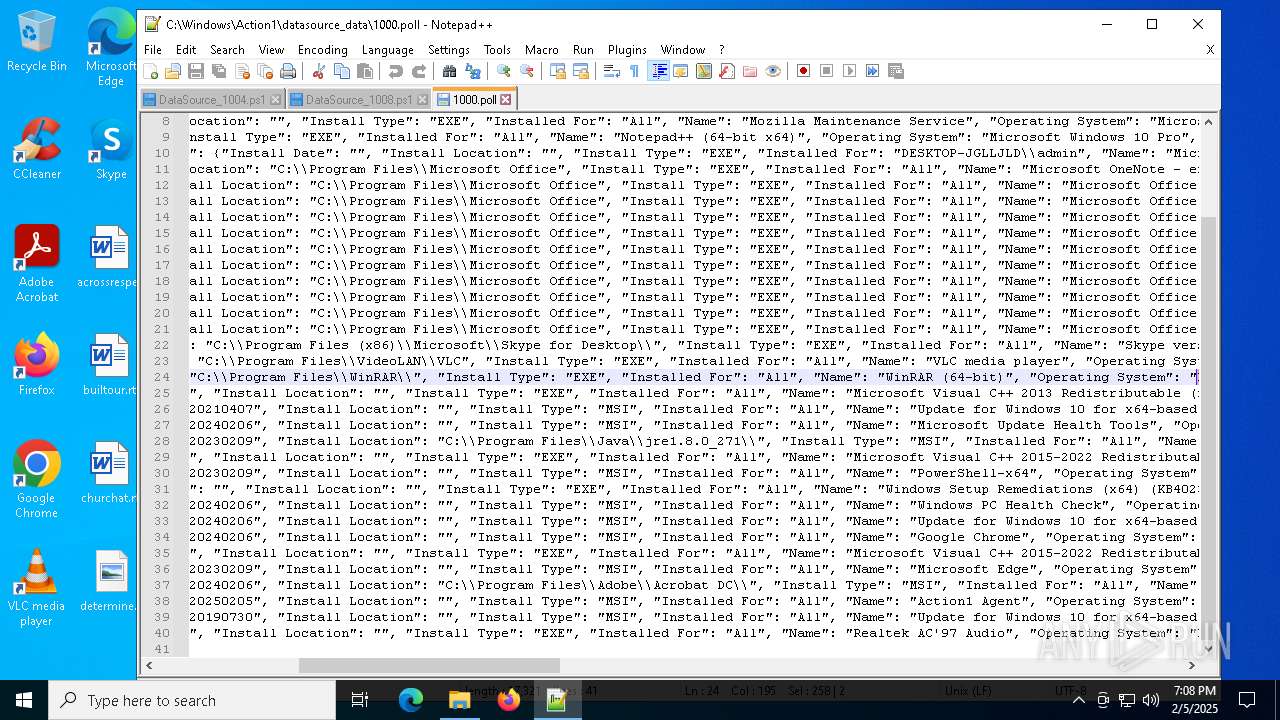
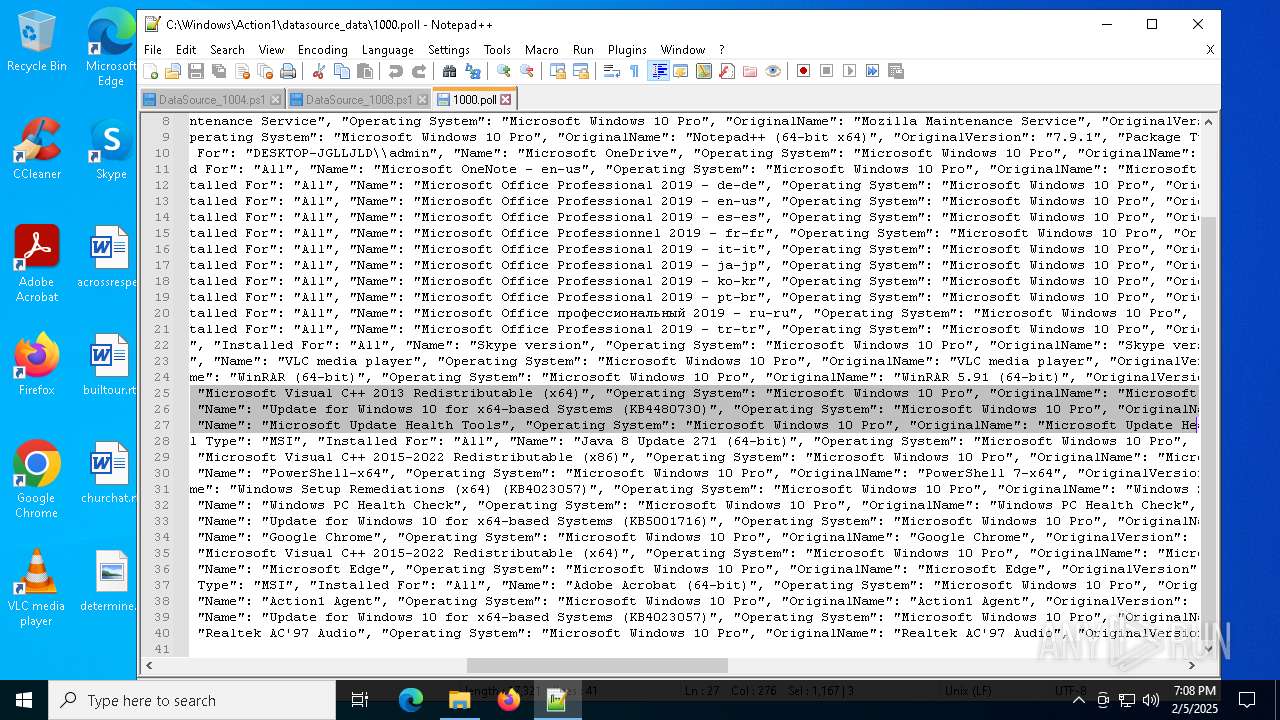
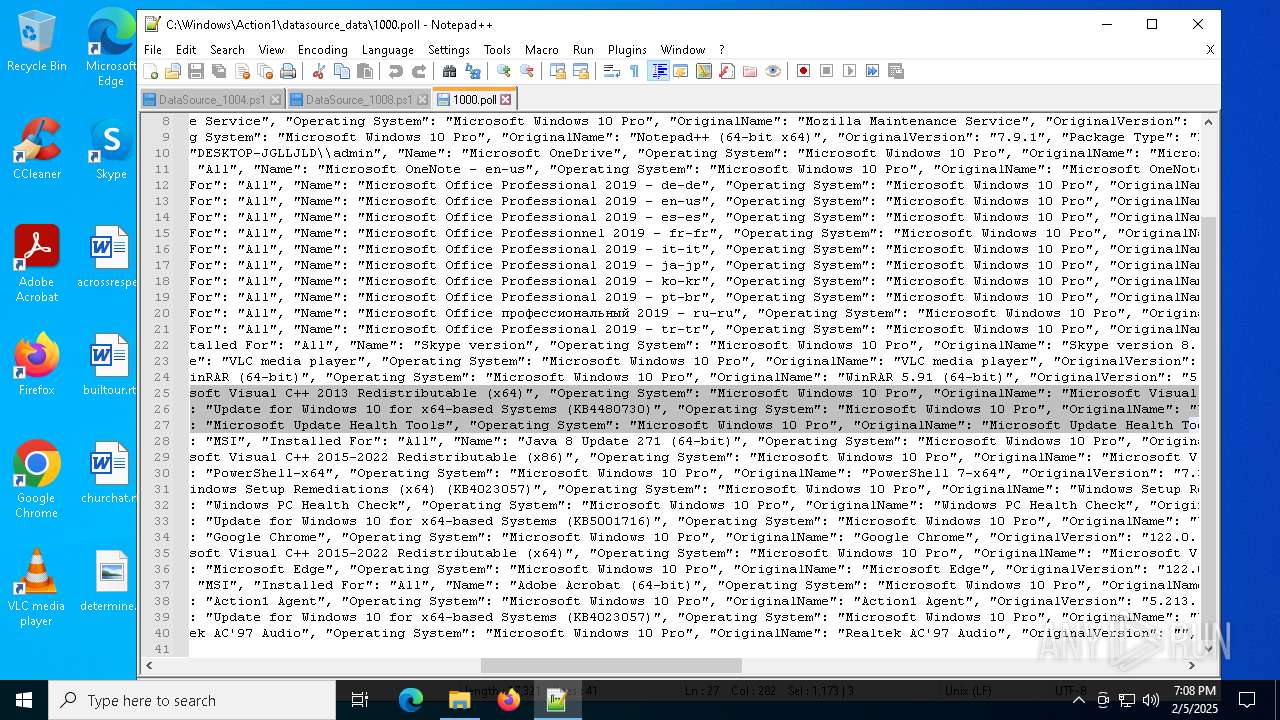
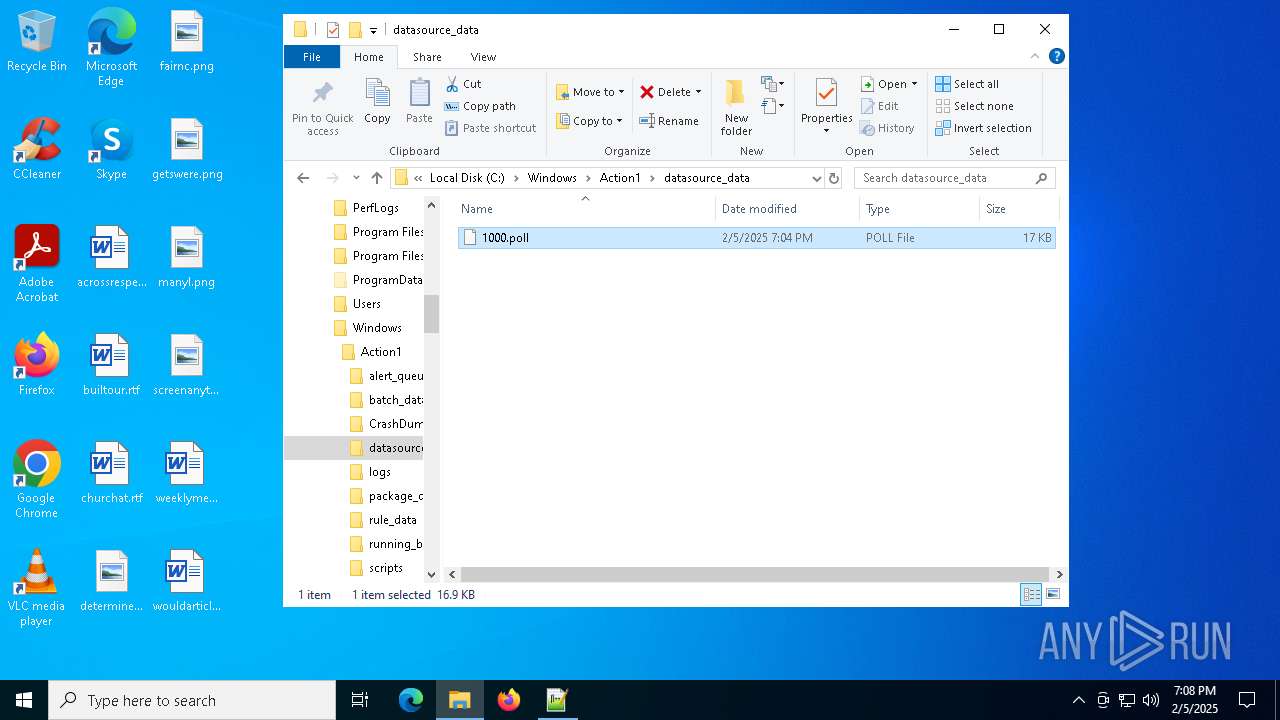
Searches for installed software
- action1_agent.exe (PID: 2136)
Reads security settings of Internet Explorer
- action1_agent.exe (PID: 2136)
Connects to unusual port
- action1_agent.exe (PID: 2136)
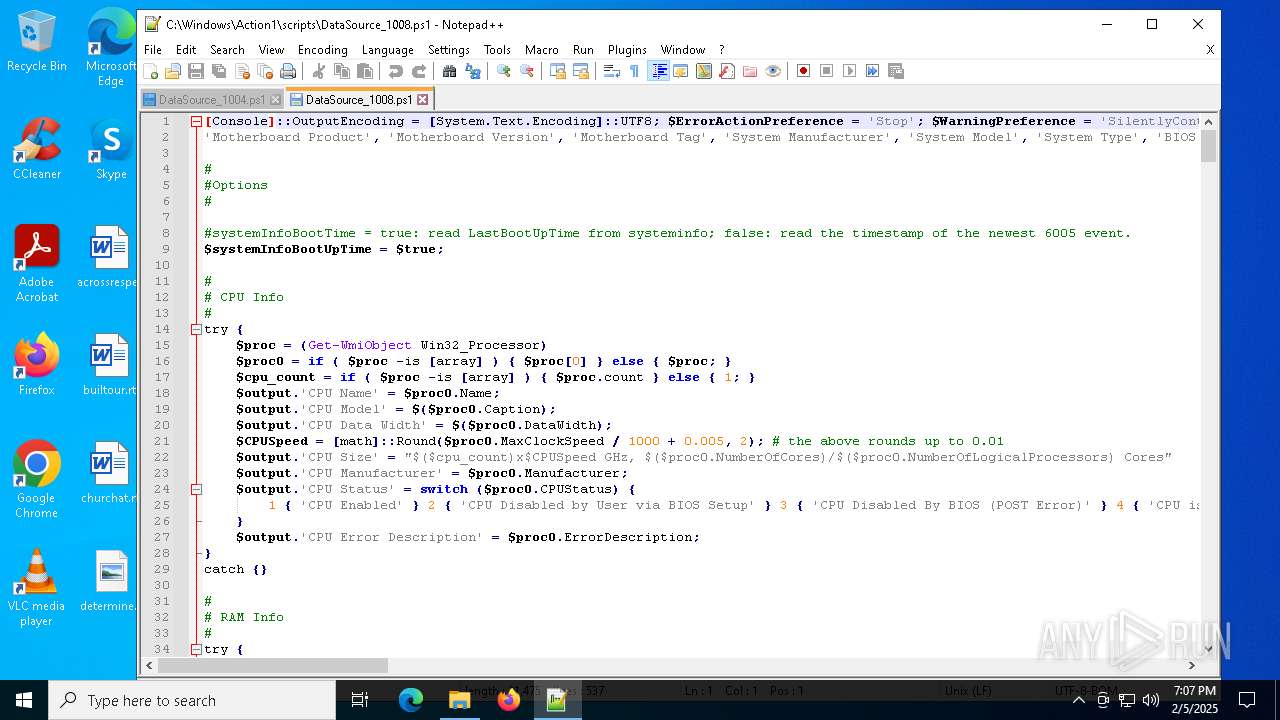
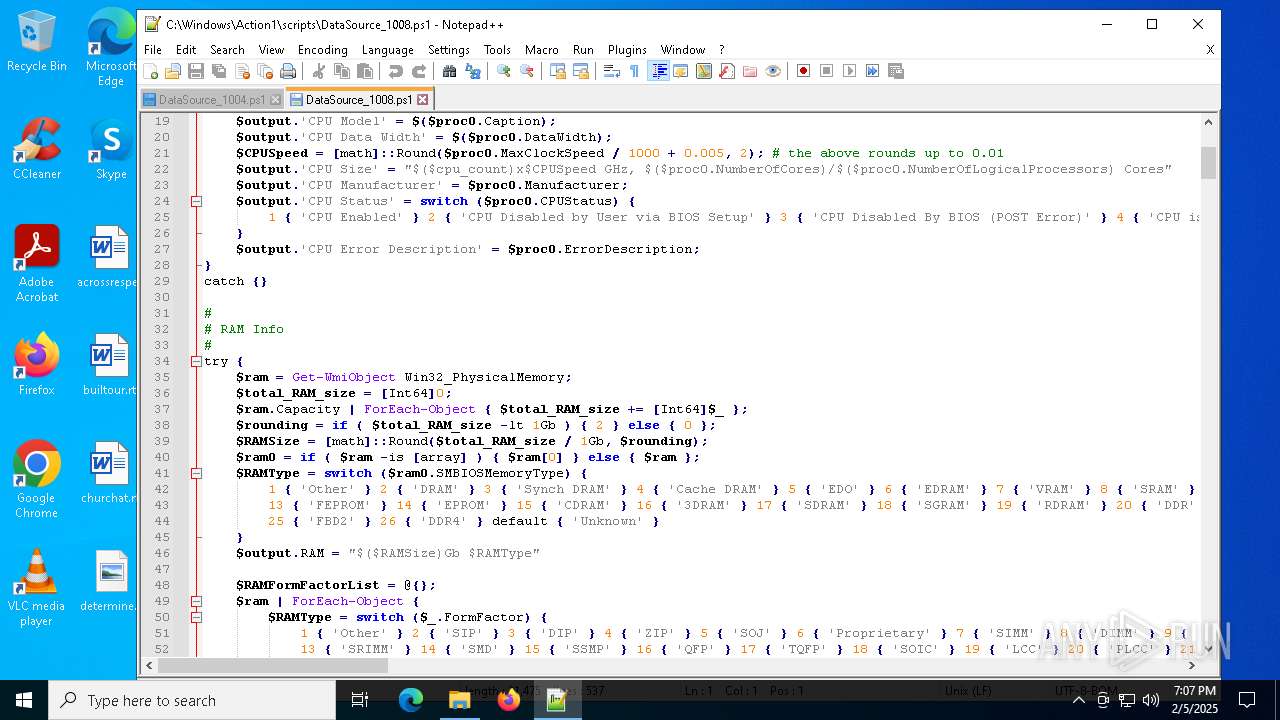
Starts POWERSHELL.EXE for commands execution
- action1_agent.exe (PID: 2136)
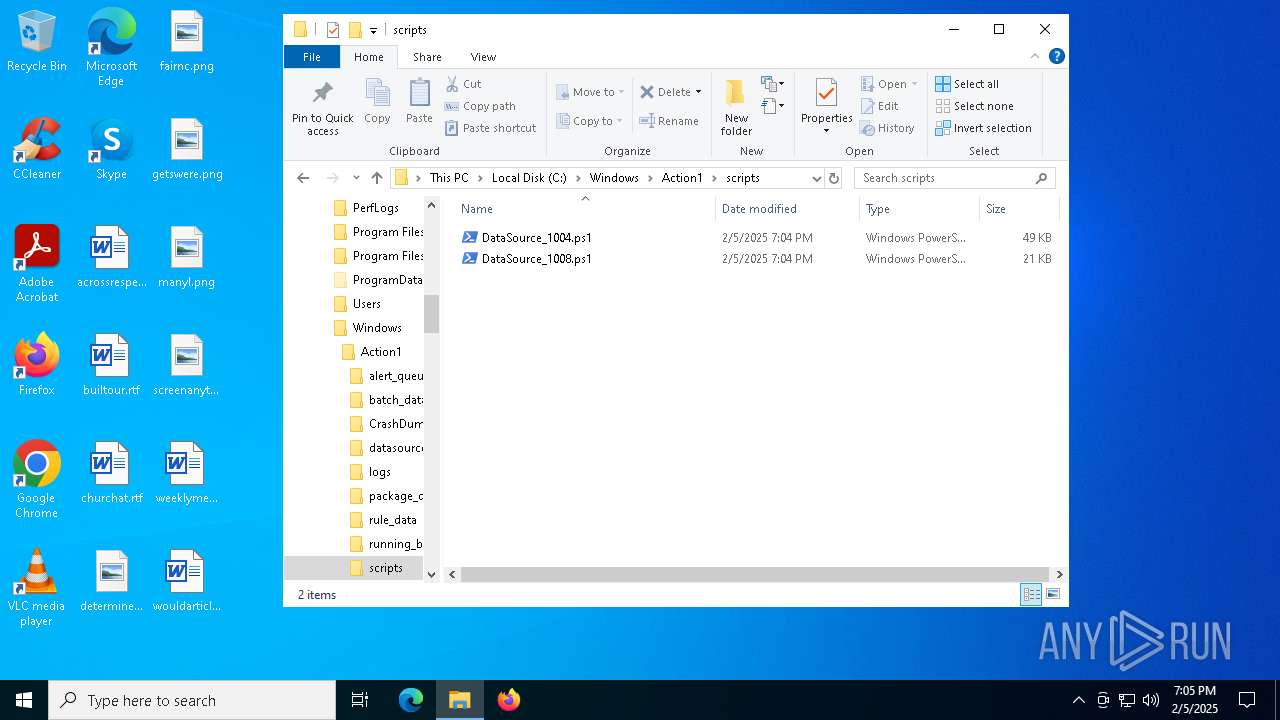
The process executes Powershell scripts
- action1_agent.exe (PID: 2136)
The process hides Powershell's copyright startup banner
- action1_agent.exe (PID: 2136)
The process bypasses the loading of PowerShell profile settings
- action1_agent.exe (PID: 2136)
The process hide an interactive prompt from the user
- action1_agent.exe (PID: 2136)
There is functionality for taking screenshot (YARA)
- action1_agent.exe (PID: 2136)
INFO
Reads the software policy settings
- msiexec.exe (PID: 6244)
- msiexec.exe (PID: 6572)
- powershell.exe (PID: 6436)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6244)
- powershell.exe (PID: 6436)
Checks proxy server information
- msiexec.exe (PID: 6244)
The sample compiled with english language support
- msiexec.exe (PID: 6244)
- msiexec.exe (PID: 6572)
Creates files or folders in the user directory
- msiexec.exe (PID: 6244)
Reads the computer name
- msiexec.exe (PID: 6572)
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 4144)
- action1_agent.exe (PID: 2136)
Checks supported languages
- msiexec.exe (PID: 6572)
- msiexec.exe (PID: 4052)
- action1_agent.exe (PID: 2136)
- msiexec.exe (PID: 4144)
Manages system restore points
- SrTasks.exe (PID: 3988)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6572)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6572)
Reads Environment values
- action1_agent.exe (PID: 2136)
Creates a software uninstall entry
- msiexec.exe (PID: 6572)
Process checks computer location settings
- action1_agent.exe (PID: 2136)
Detects Fody packer (YARA)
- powershell.exe (PID: 6436)
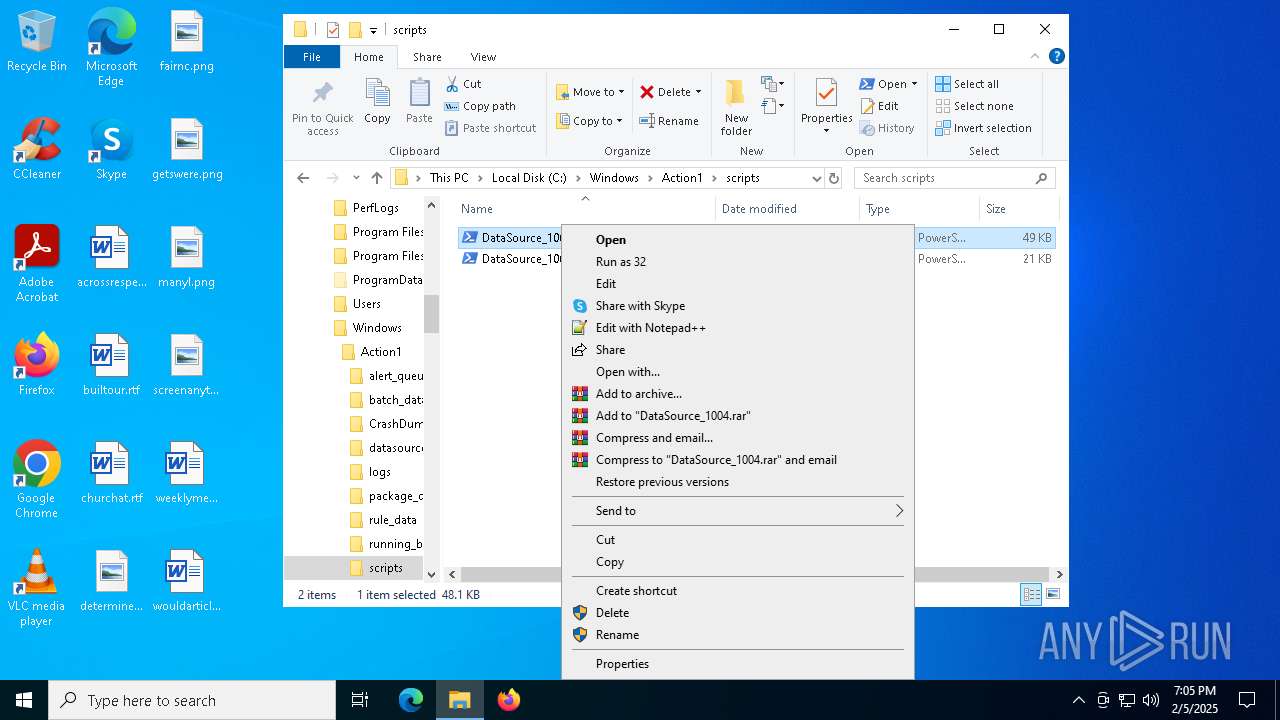
Manual execution by a user
- notepad++.exe (PID: 1704)
- notepad.exe (PID: 768)
- notepad++.exe (PID: 2624)
- notepad++.exe (PID: 748)
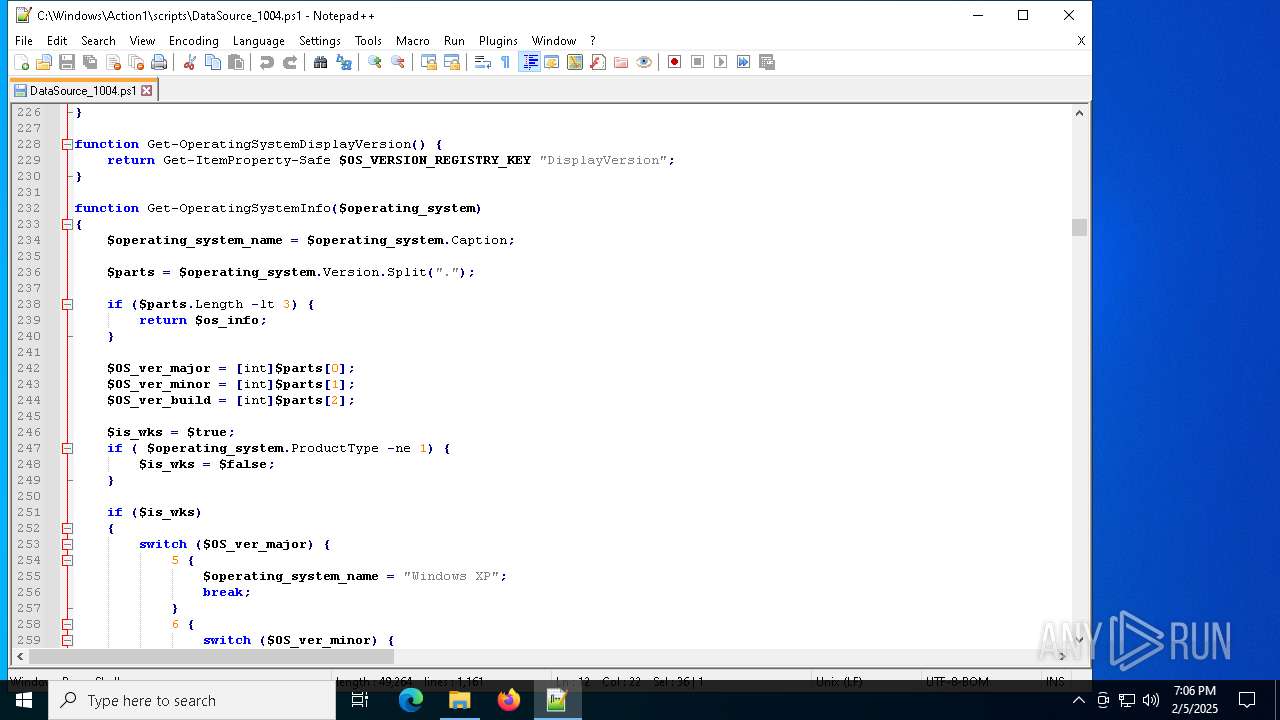
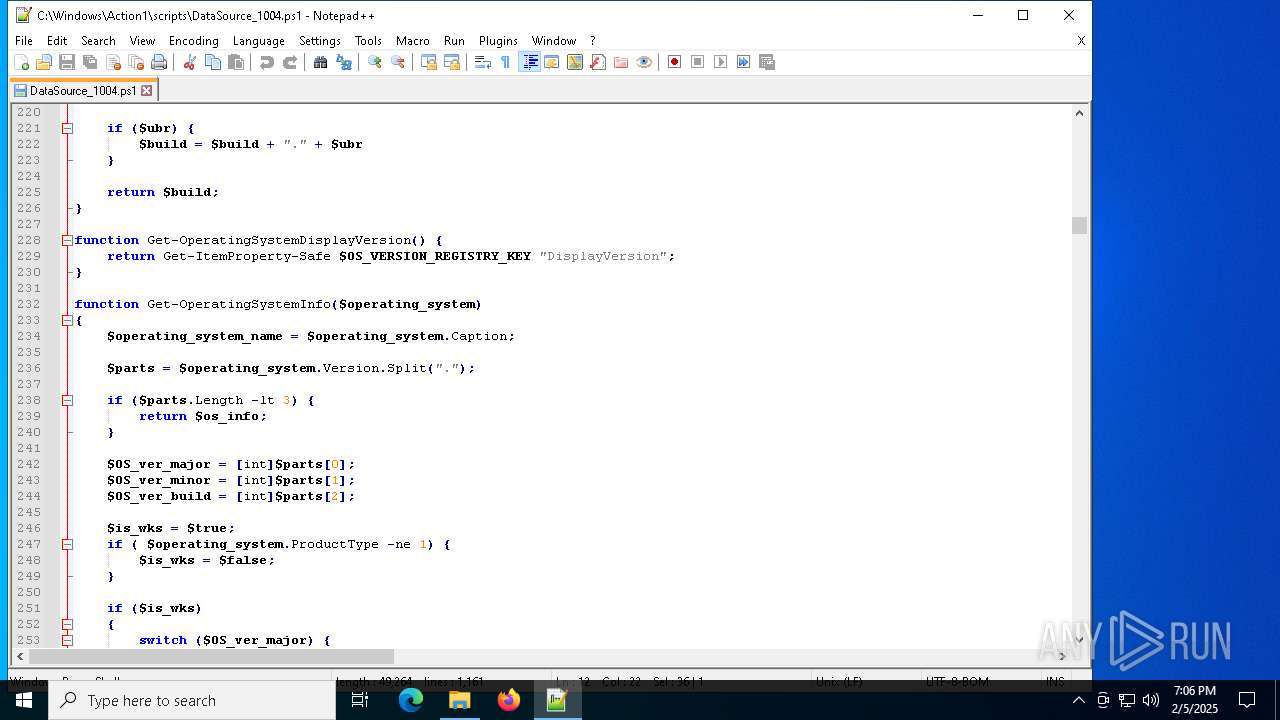
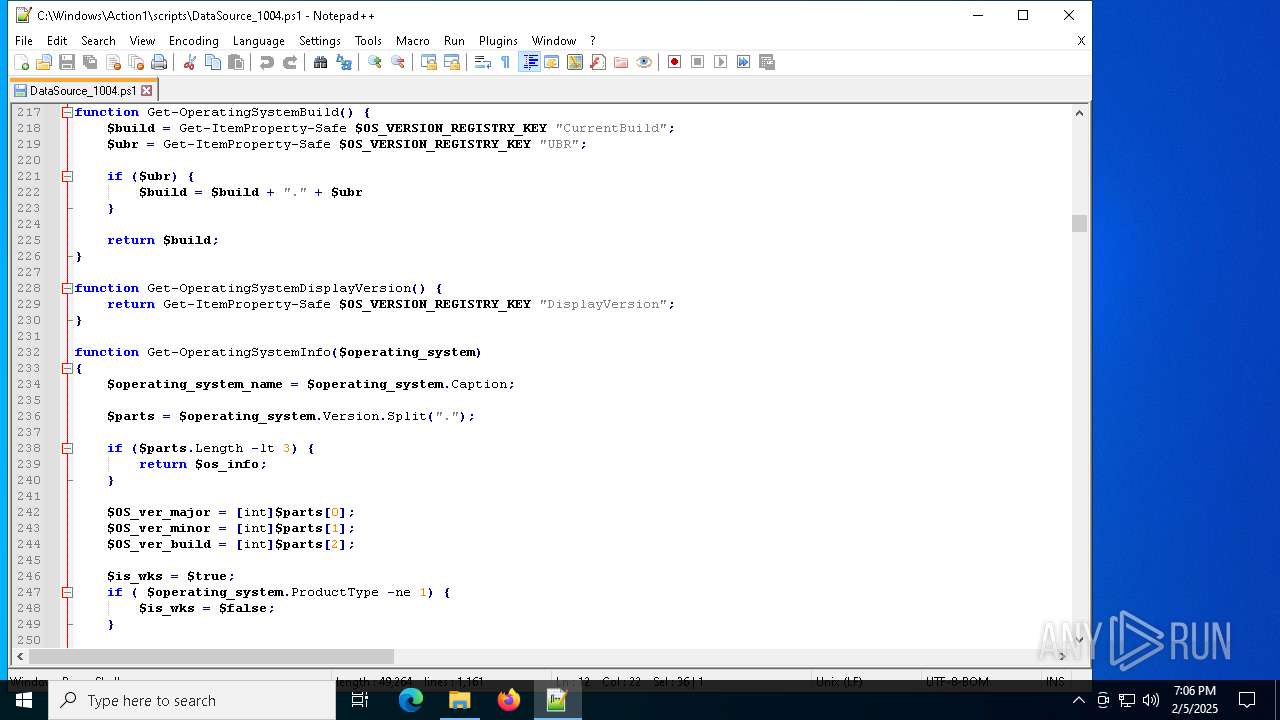
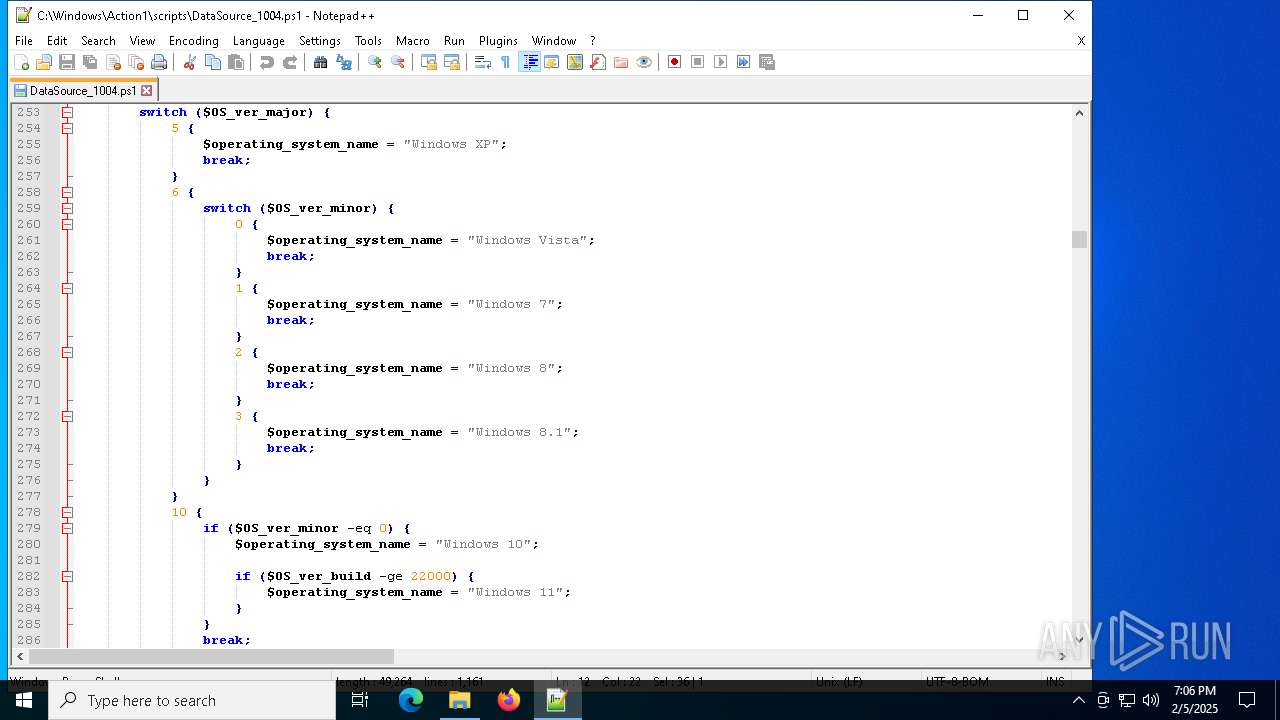
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
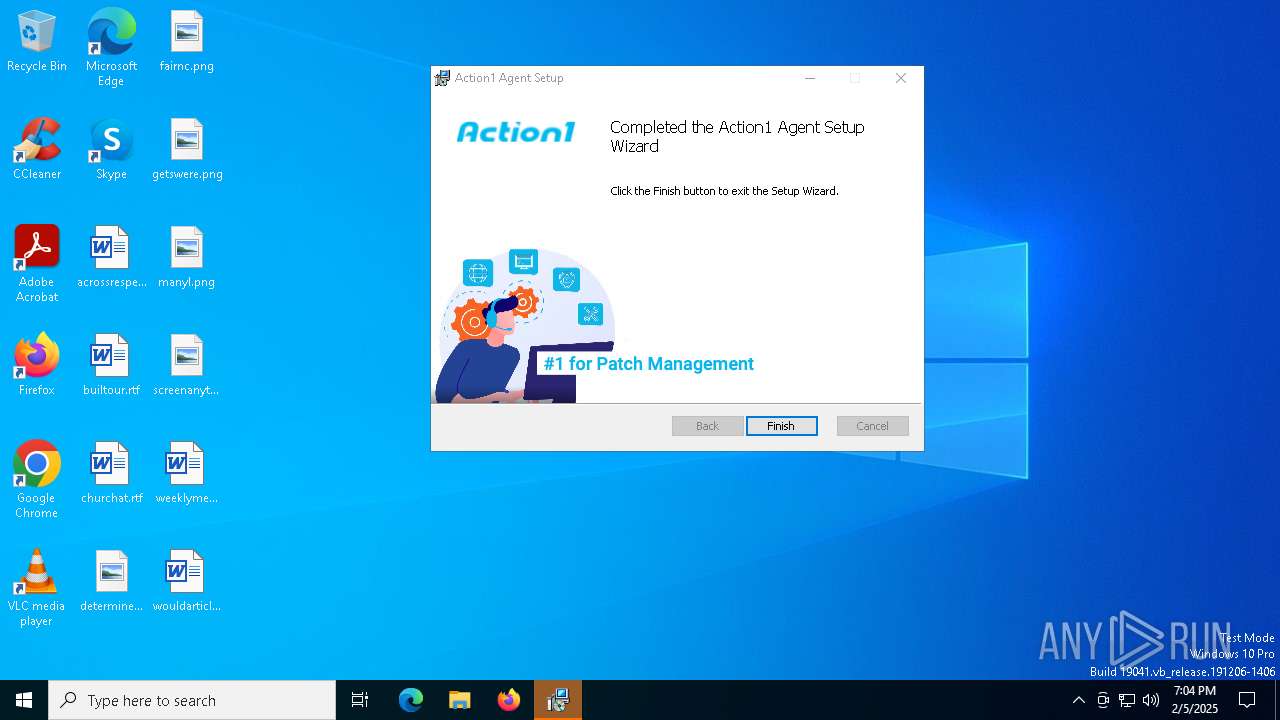
| Title: | Installation Database |
| Subject: | Action1 Agent provides the ability to remotely manage computers using Action1 Platform |
| Author: | Action1 Corporation |
| Keywords: | Action1,Agent |
| Comments: | Version: 5.213.614.1. Copyright (C) 2021 Action1 Corporation |
| Template: | Intel;1033 |
| RevisionNumber: | {93CBCBB1-BFE5-44AF-9851-12AB61B1A154} |
| CreateDate: | 2024:12:16 17:27:58 |
| ModifyDate: | 2024:12:16 17:27:58 |
| Pages: | 400 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
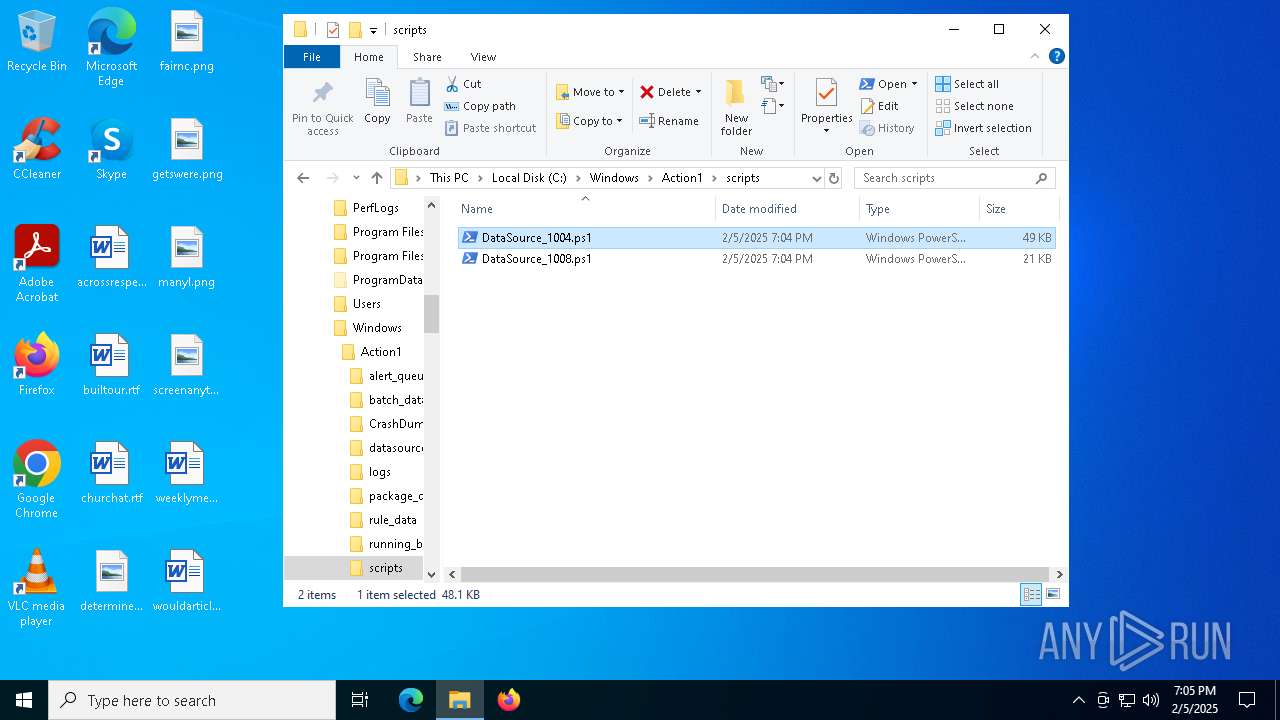
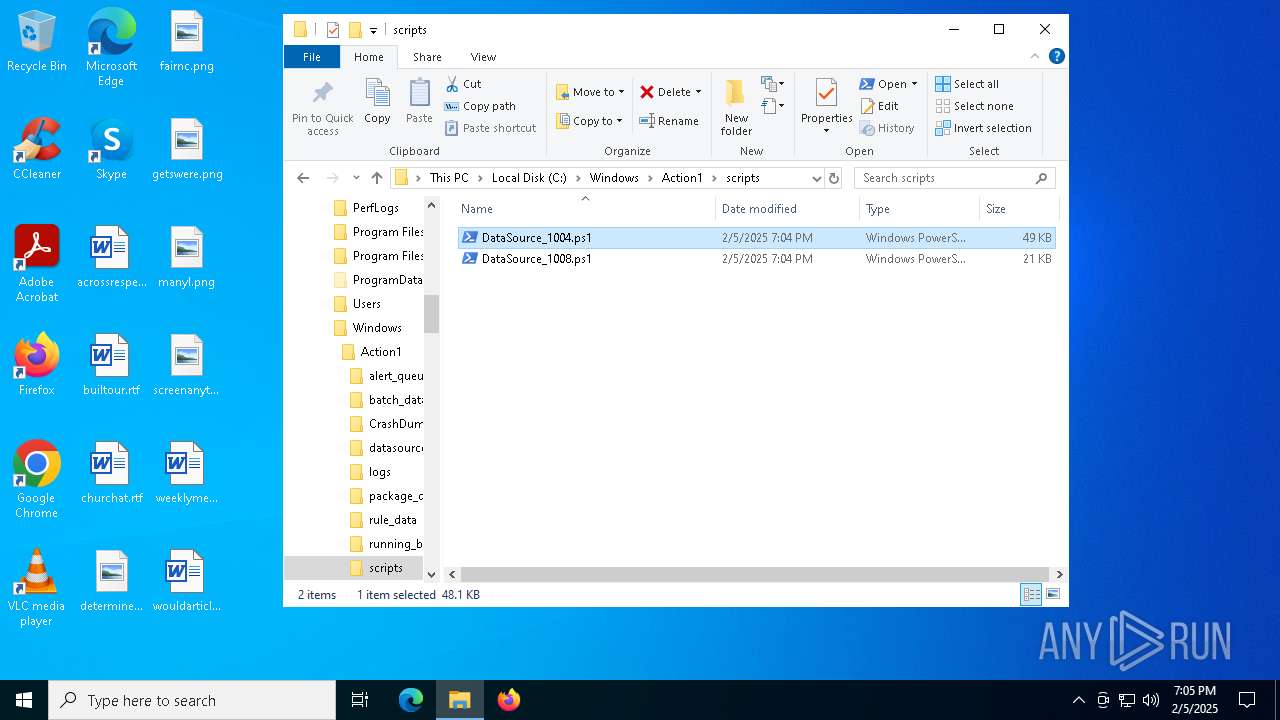
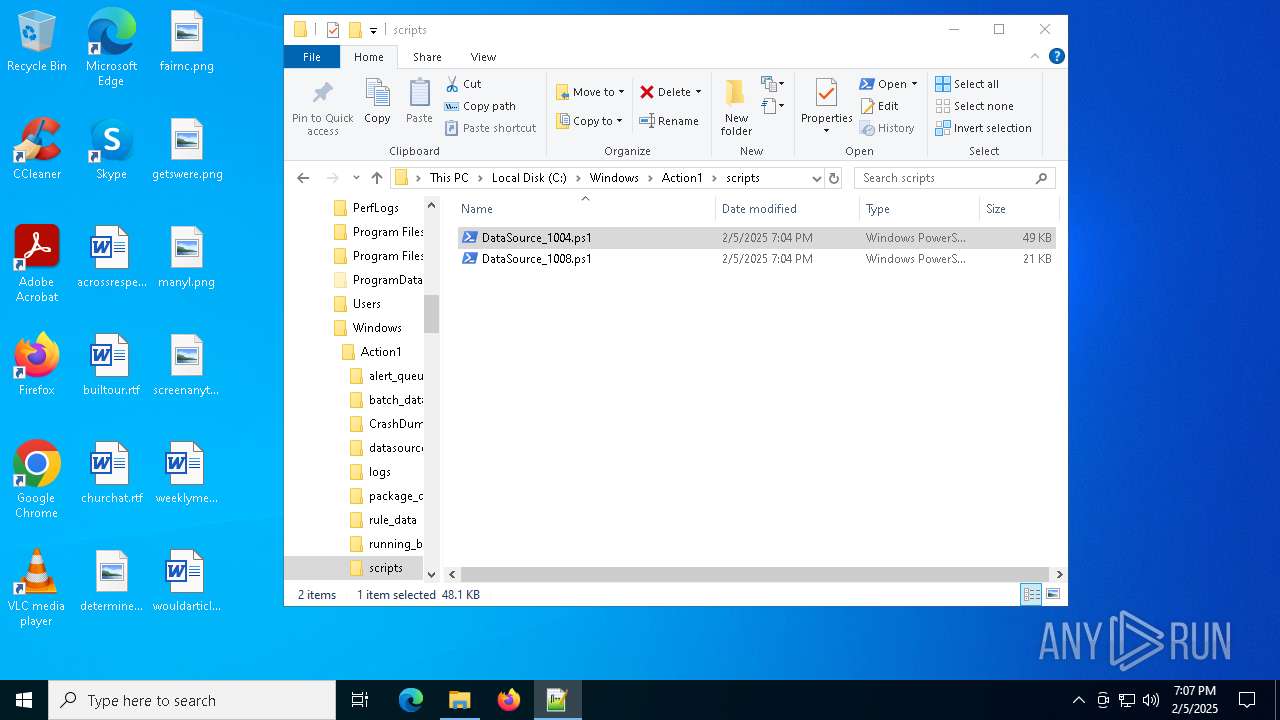
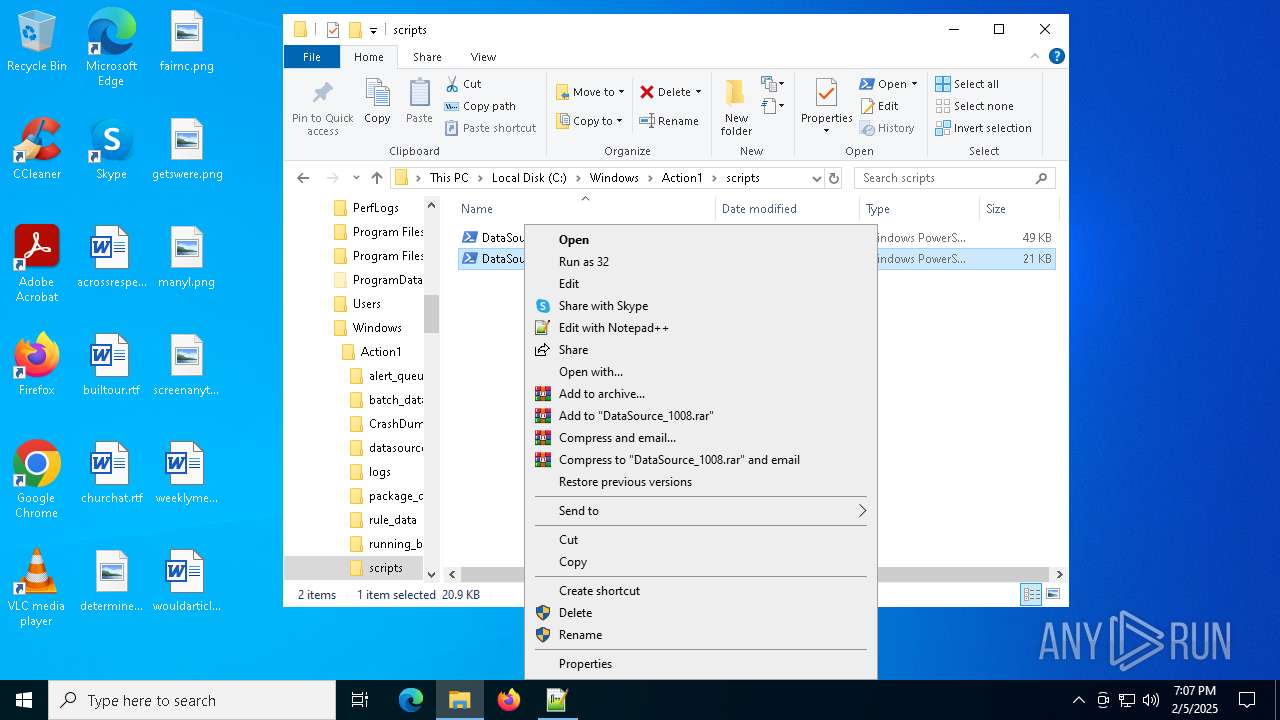
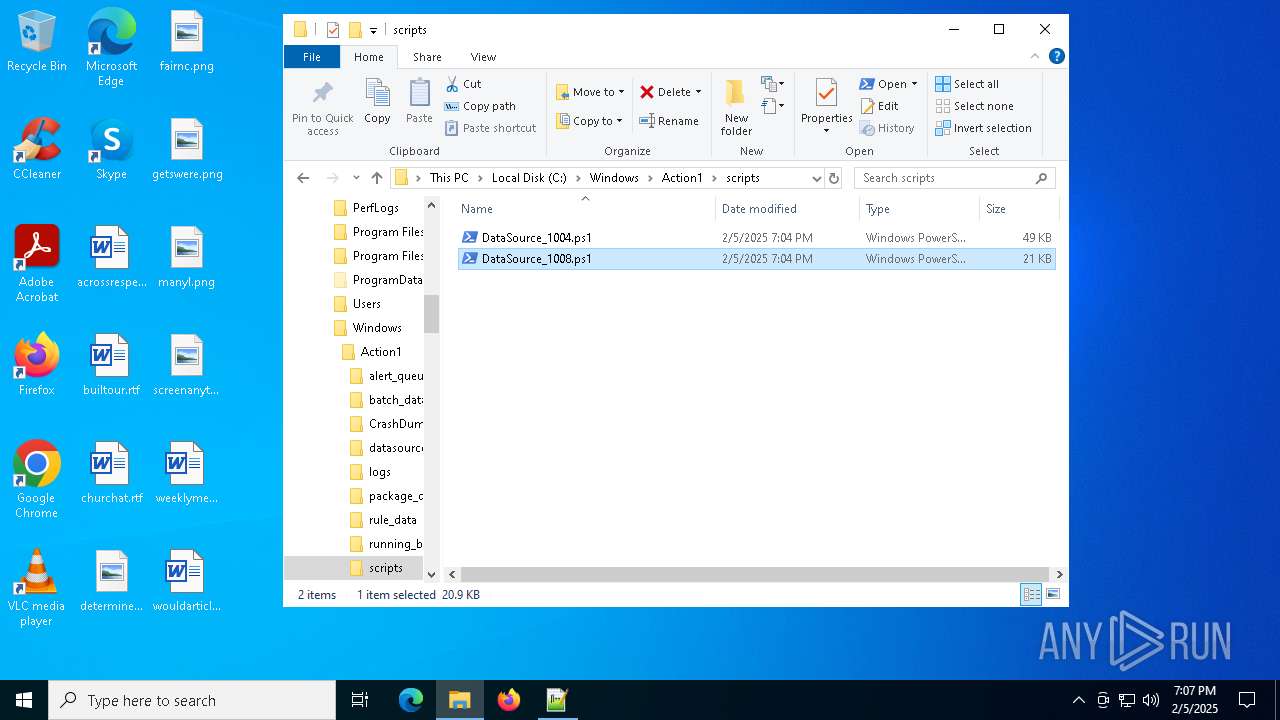
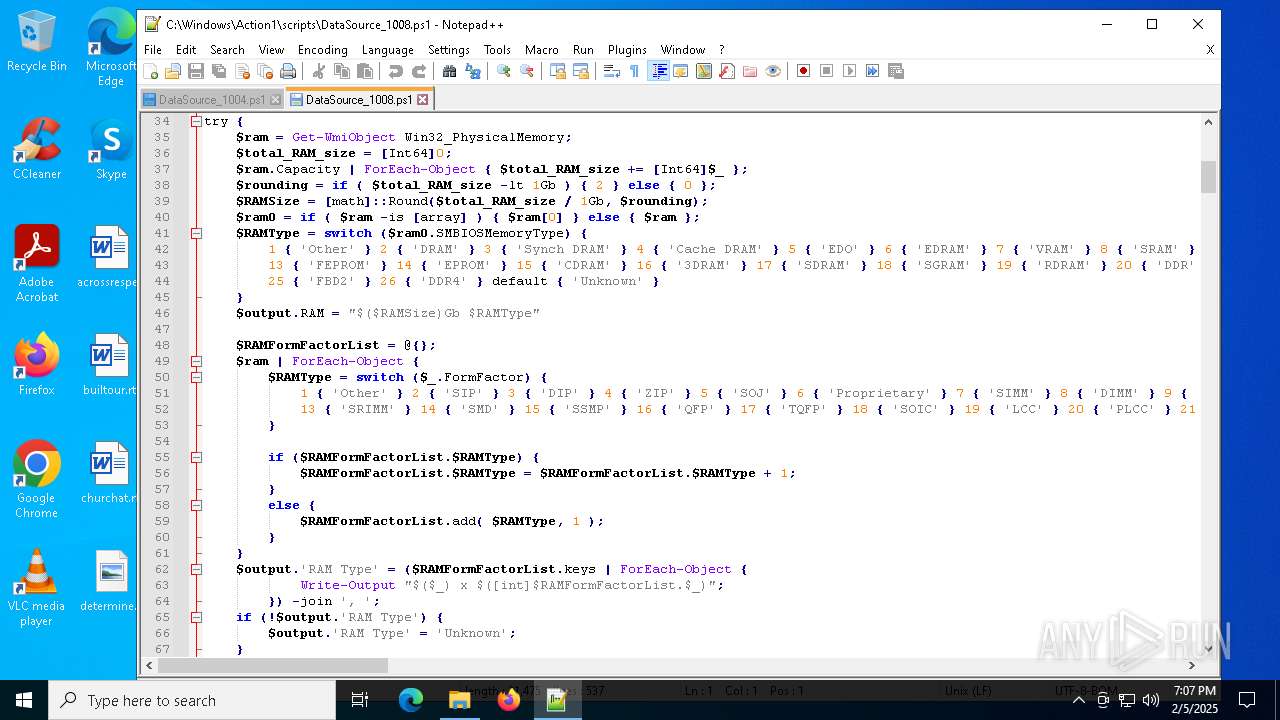
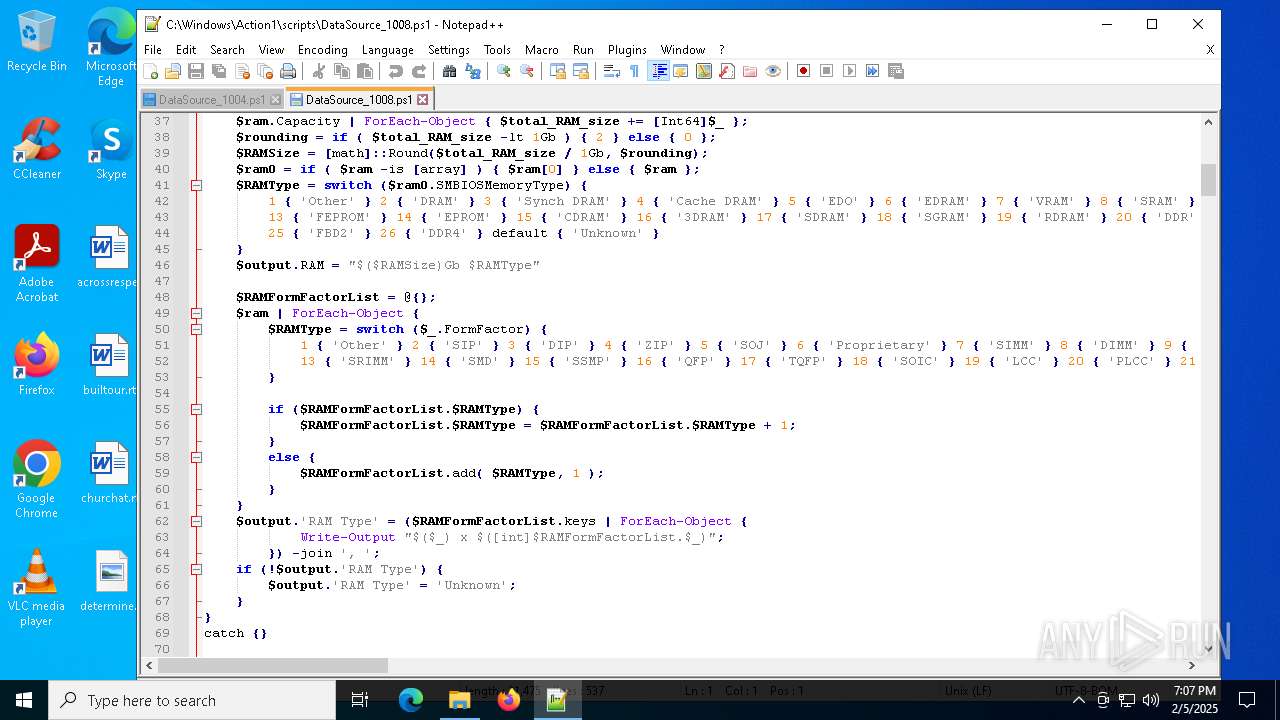
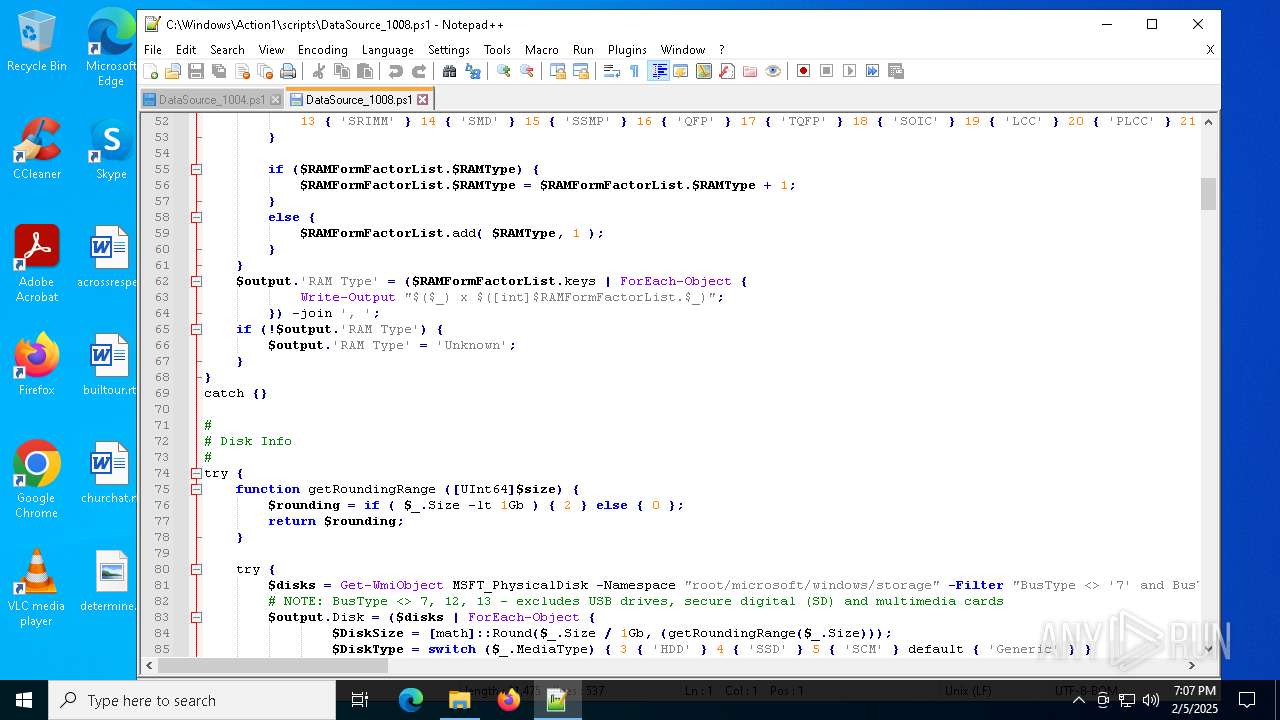
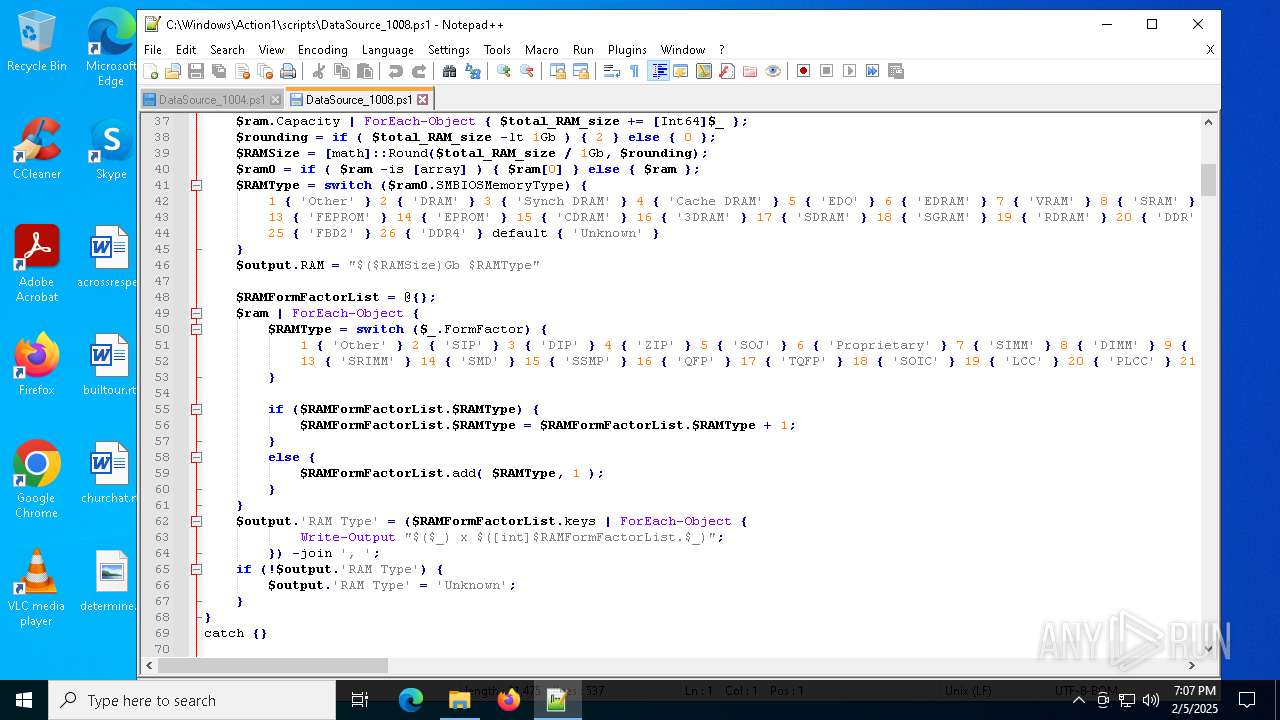
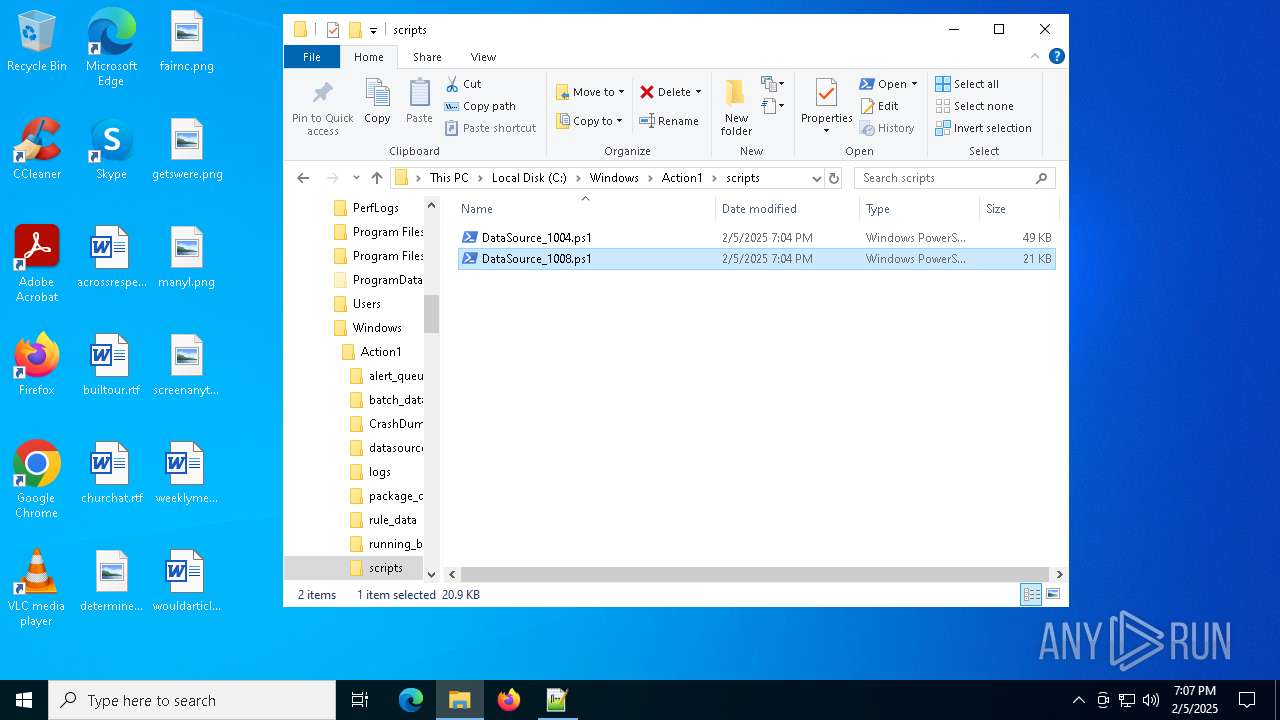
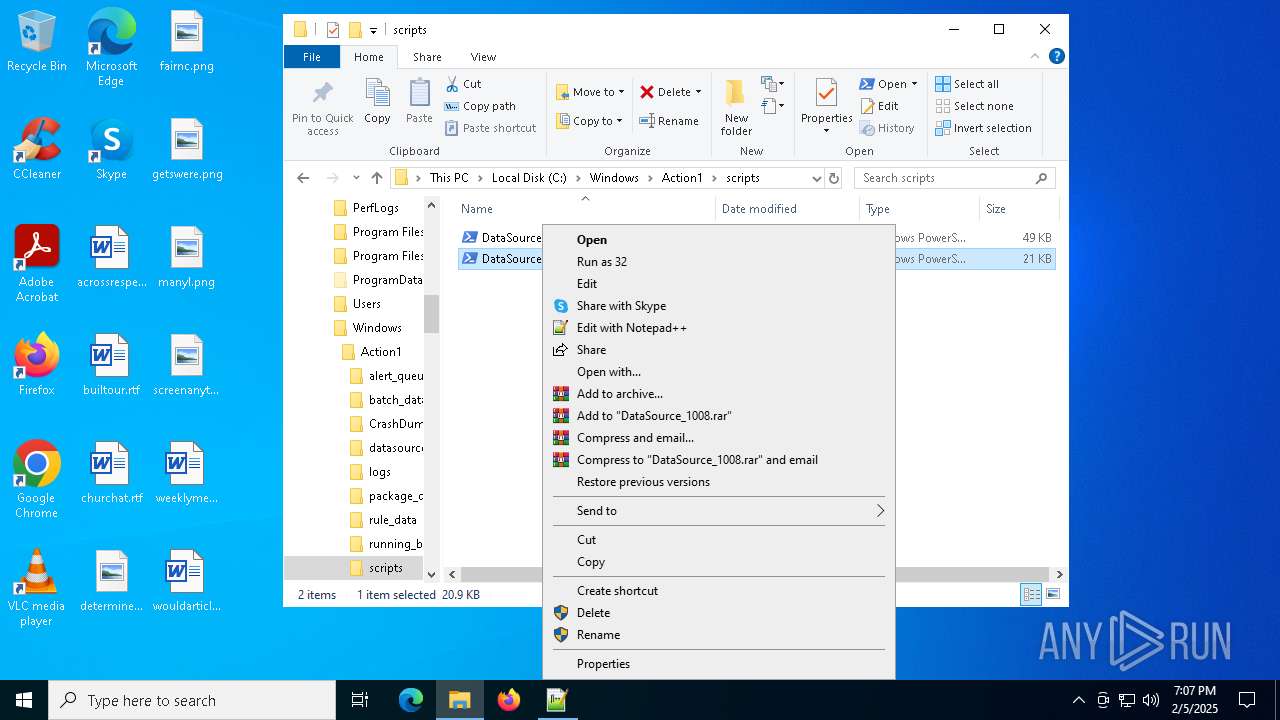
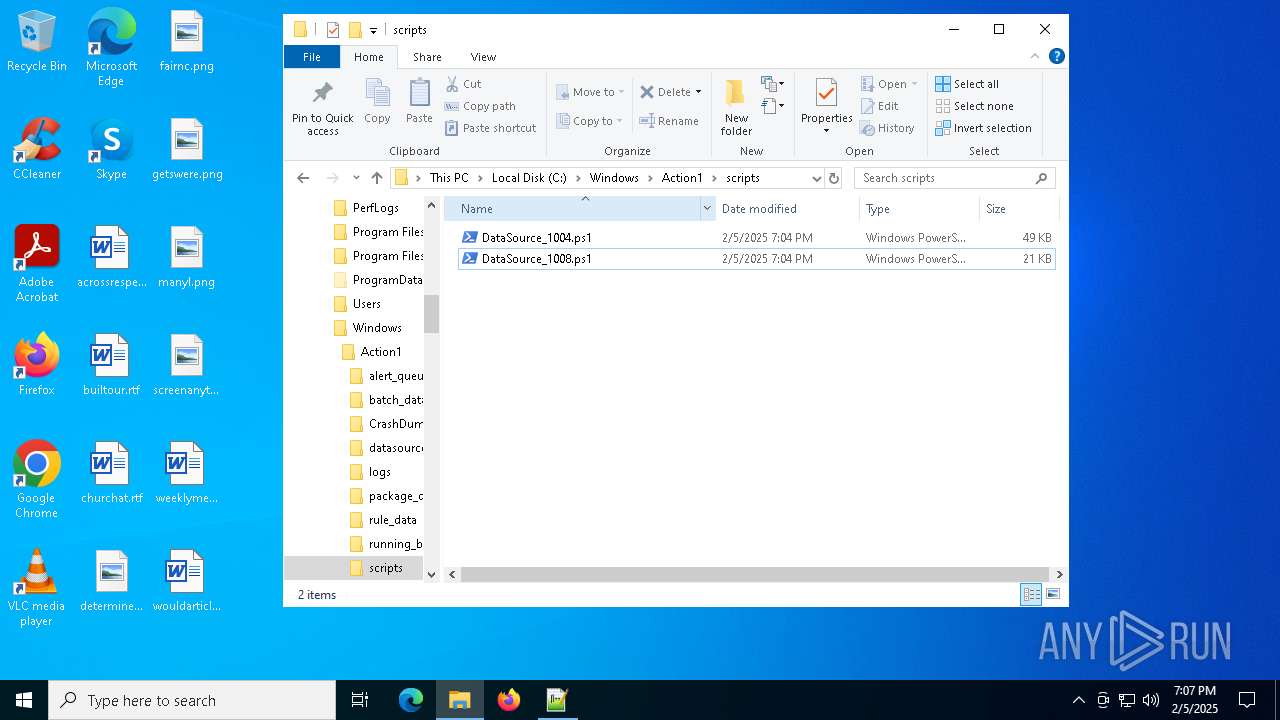
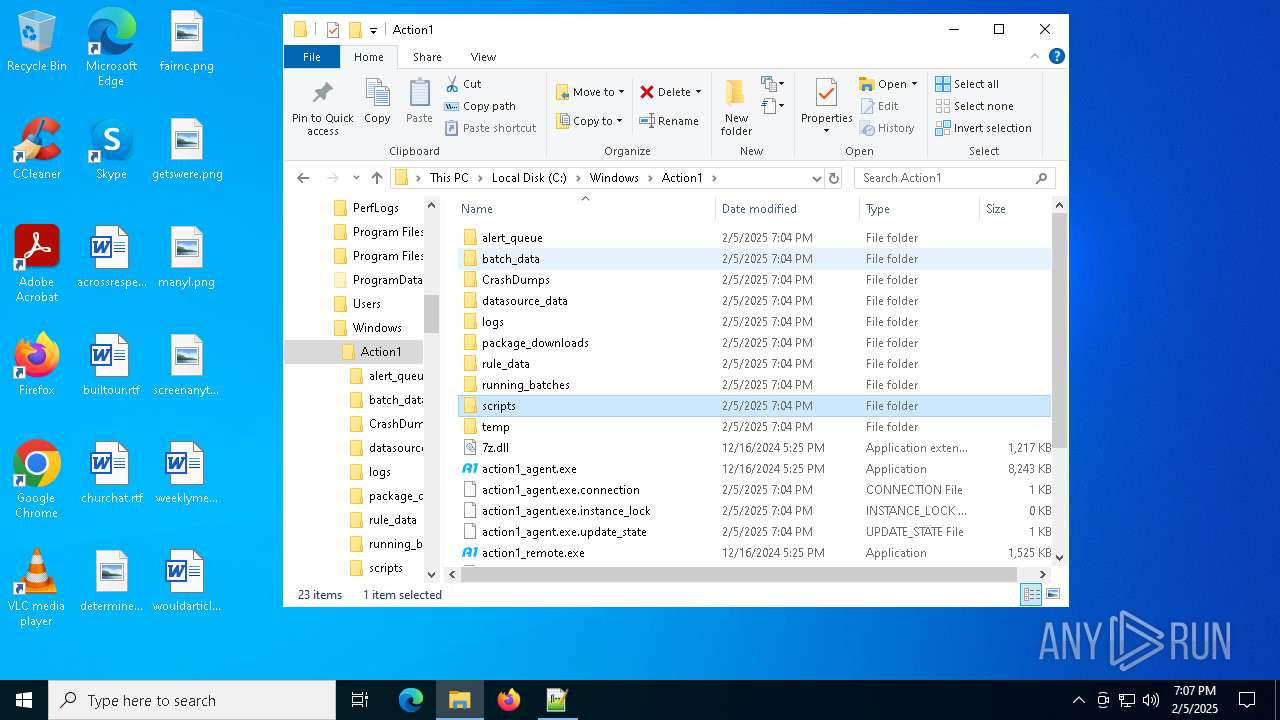
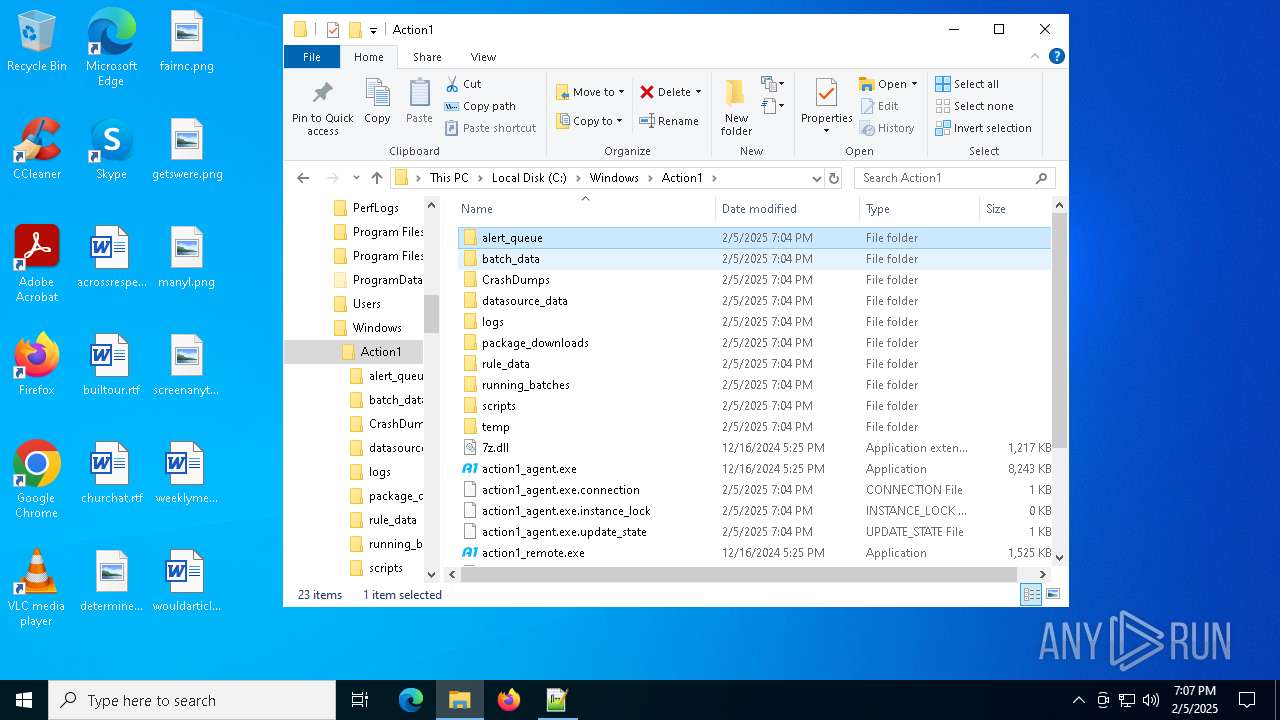
| 748 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\Action1\scripts\DataSource_1008.ps1" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
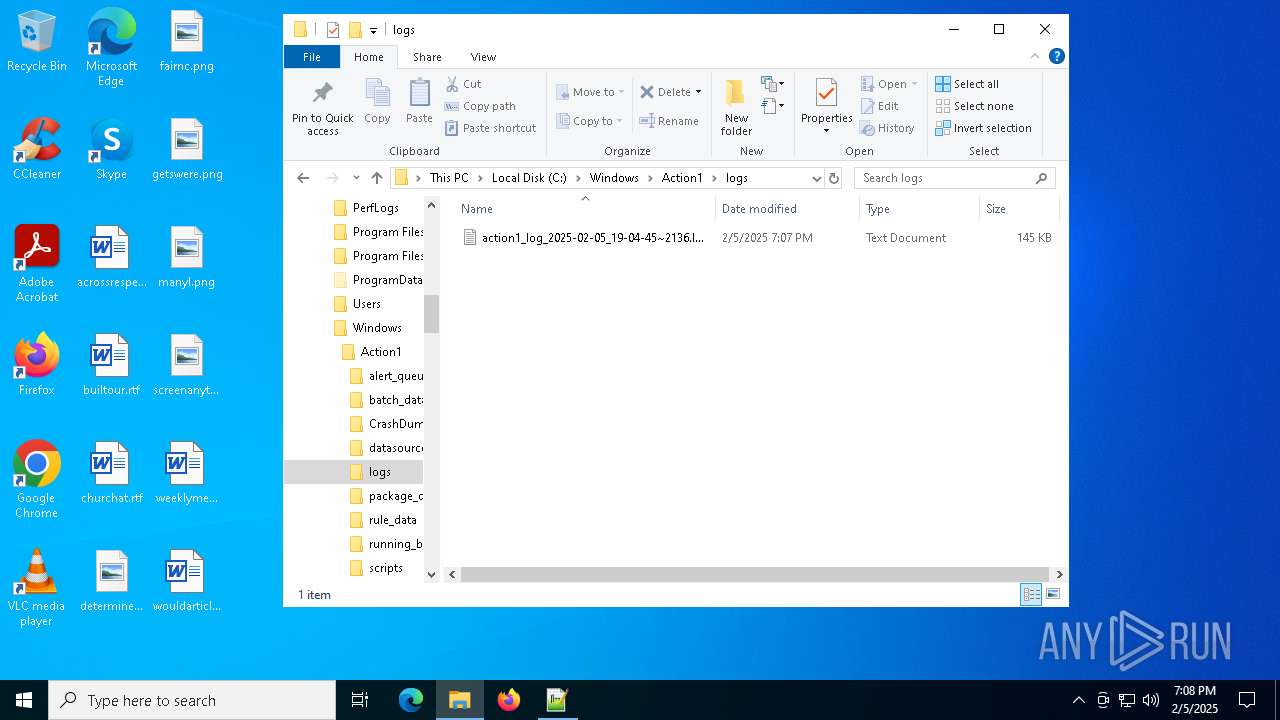
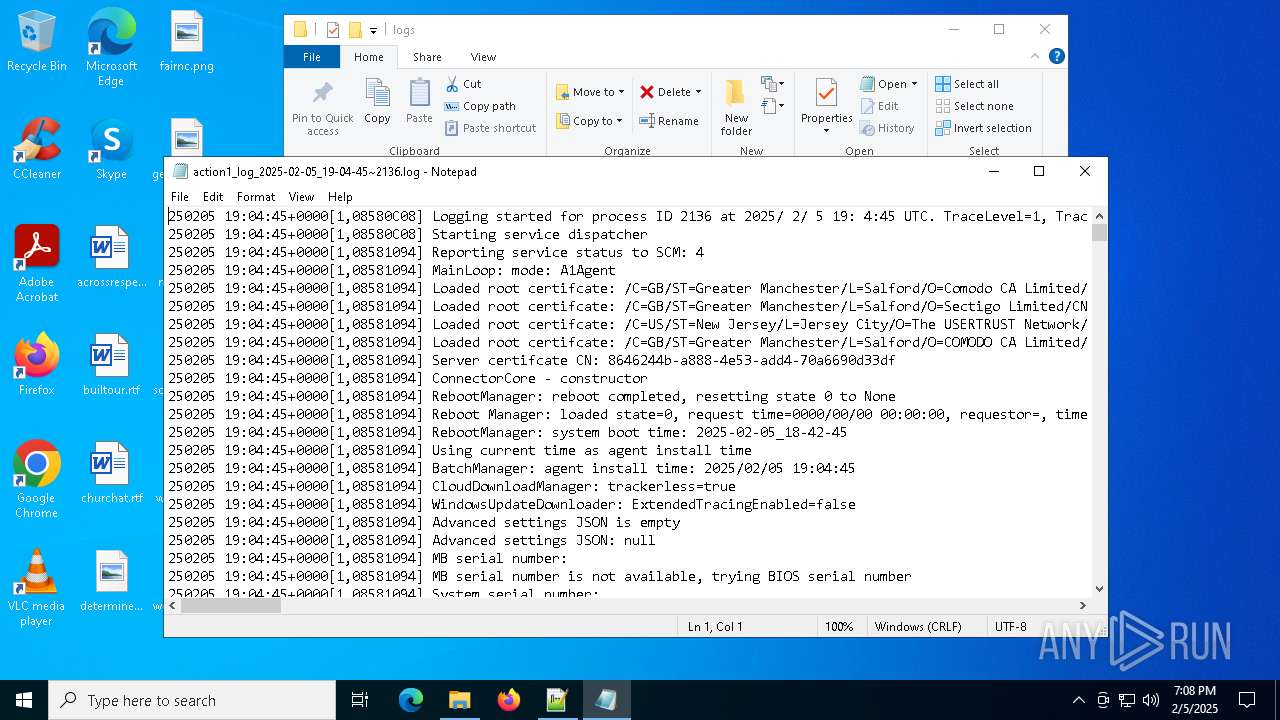
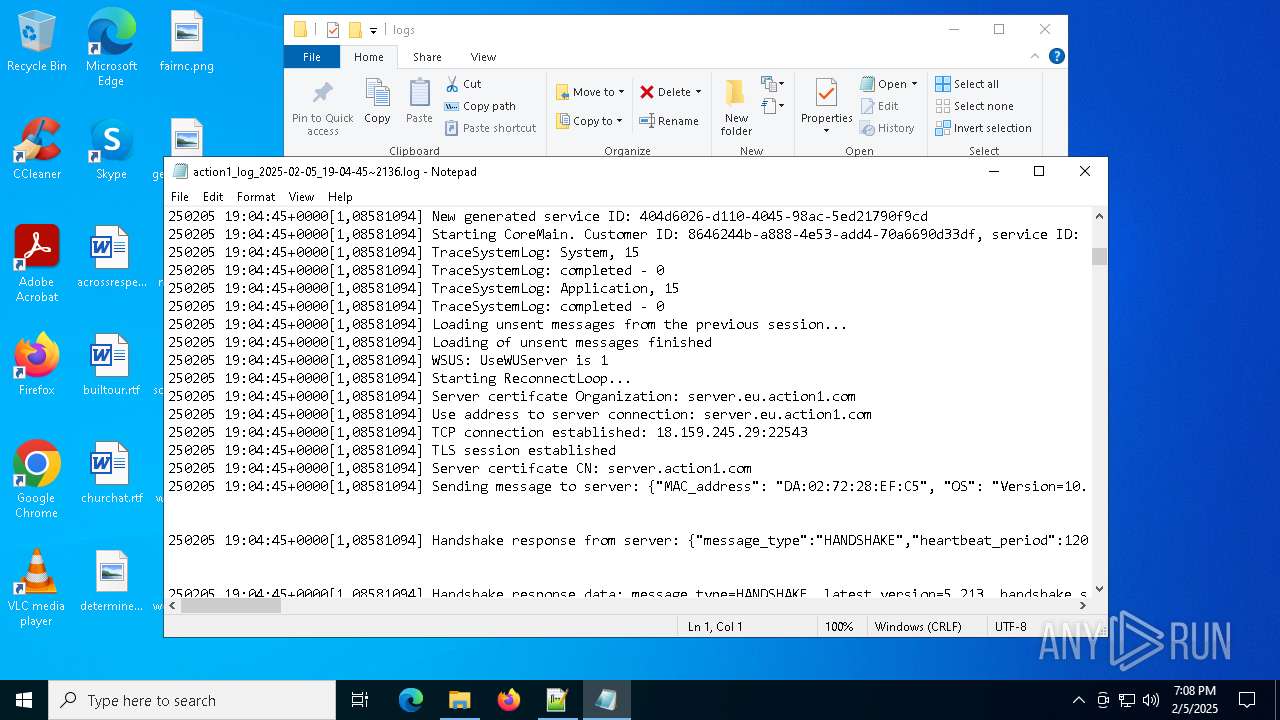
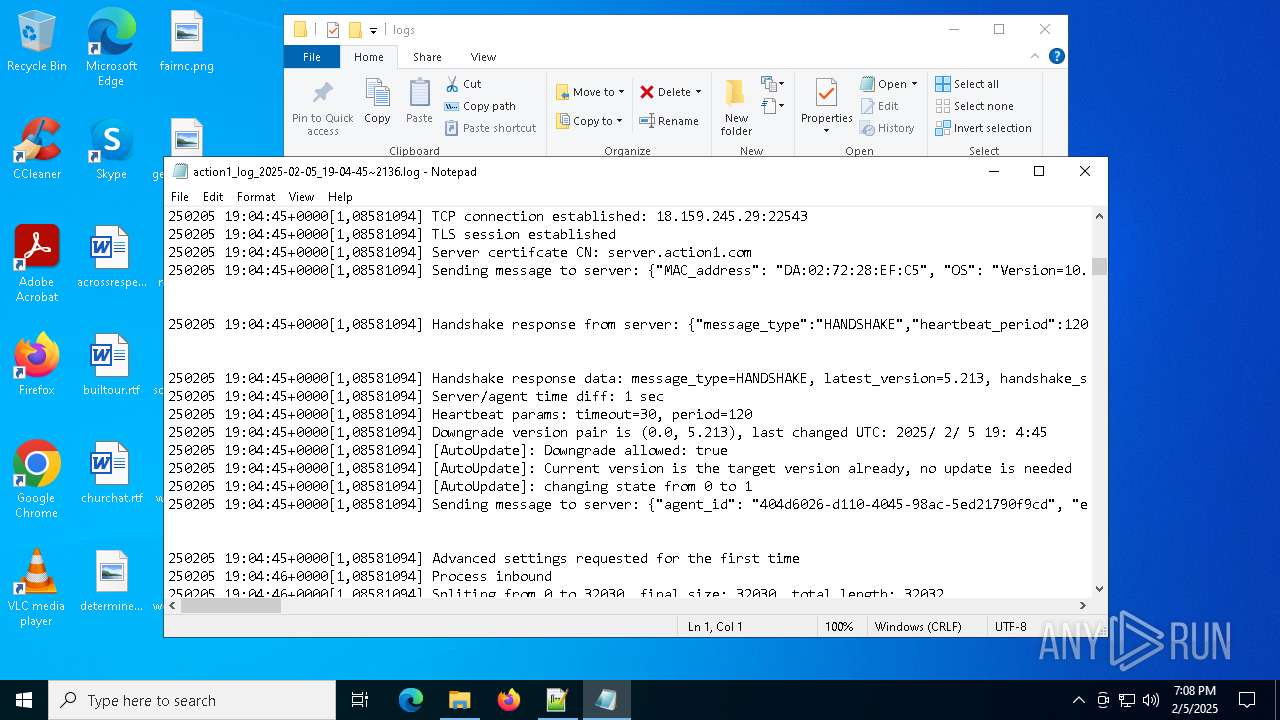
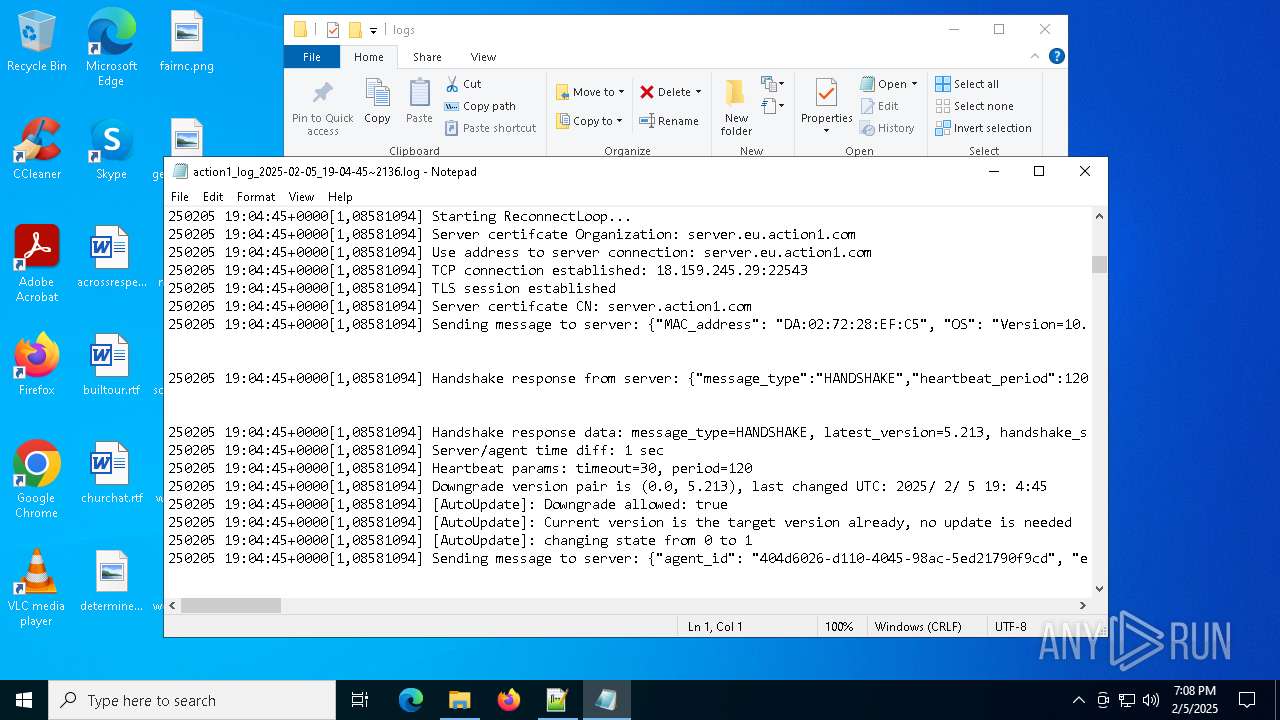
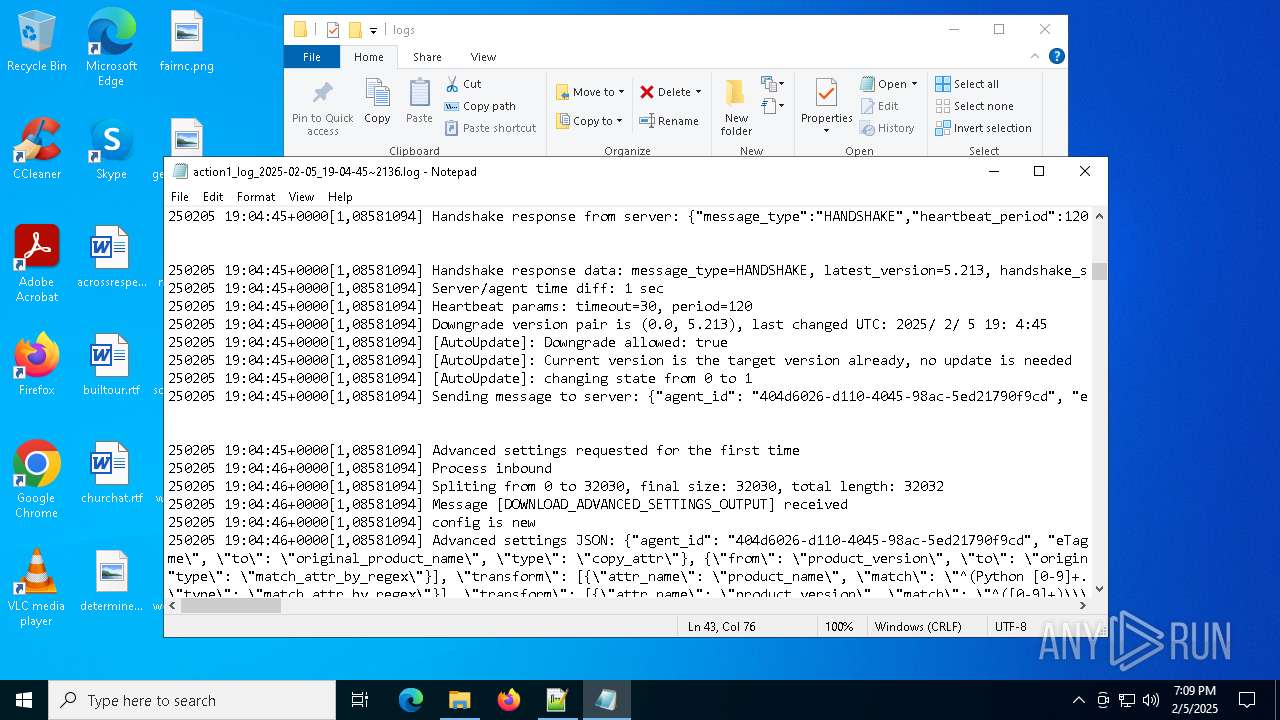
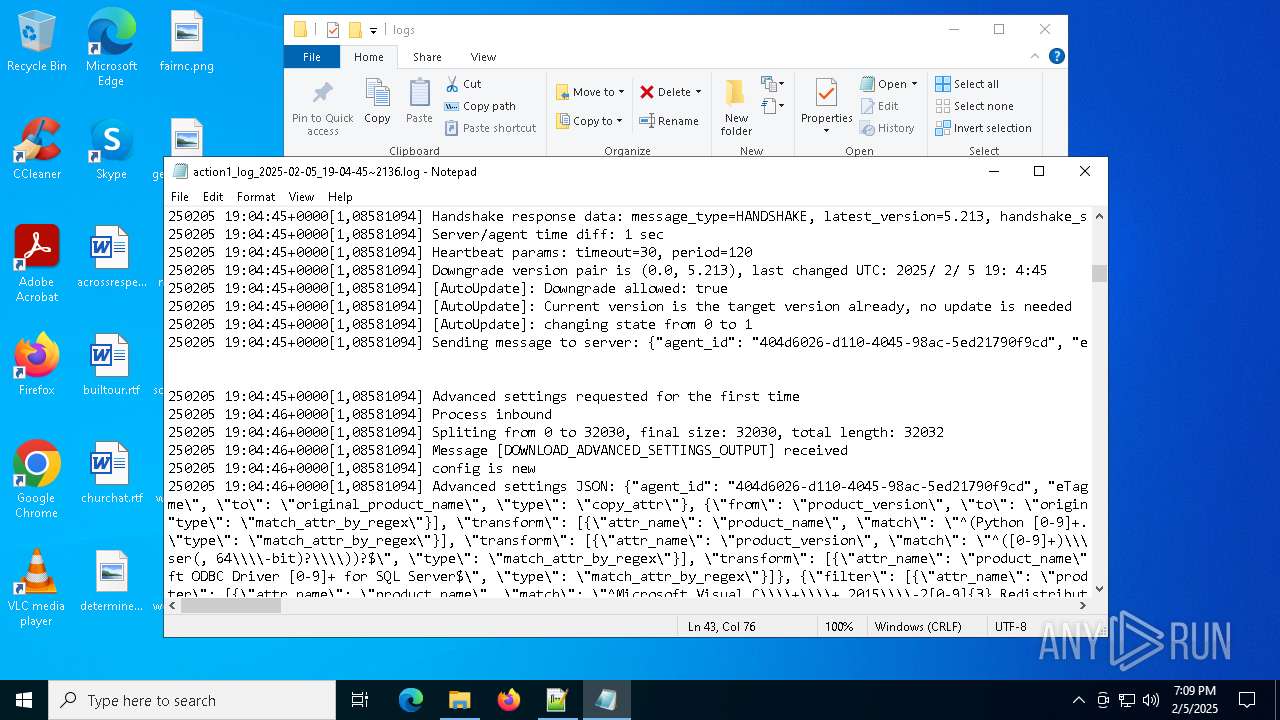
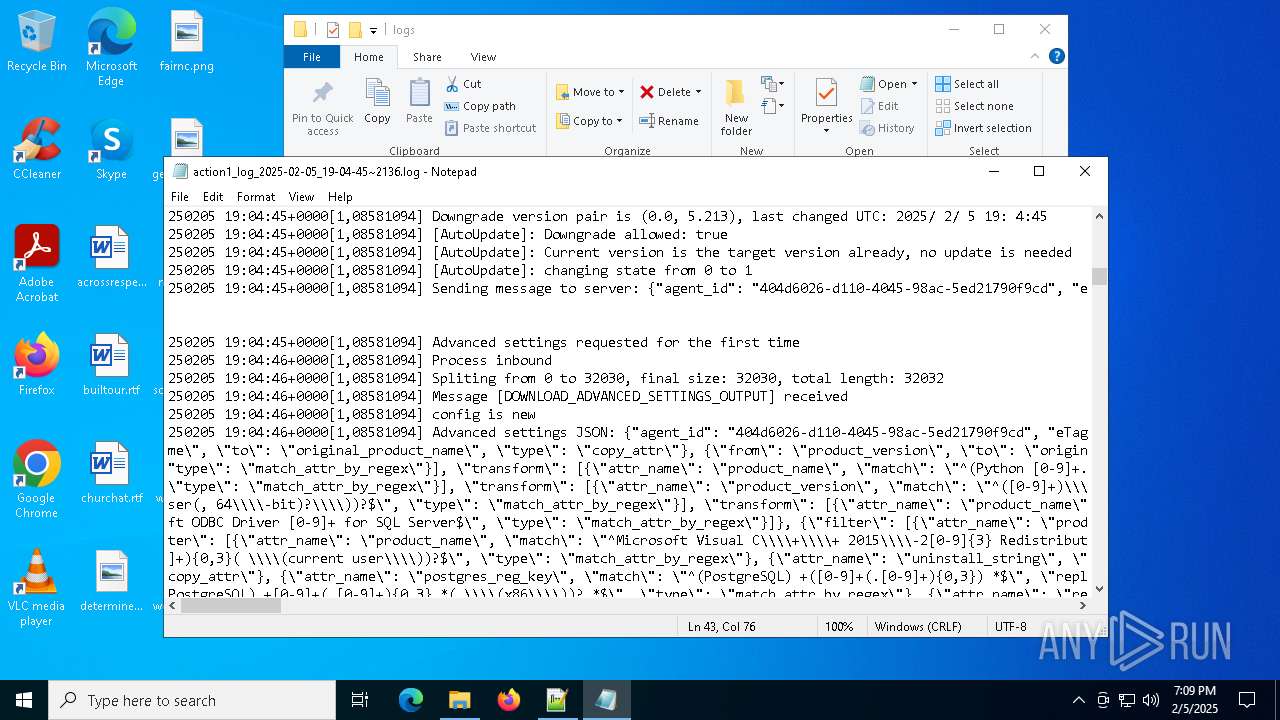
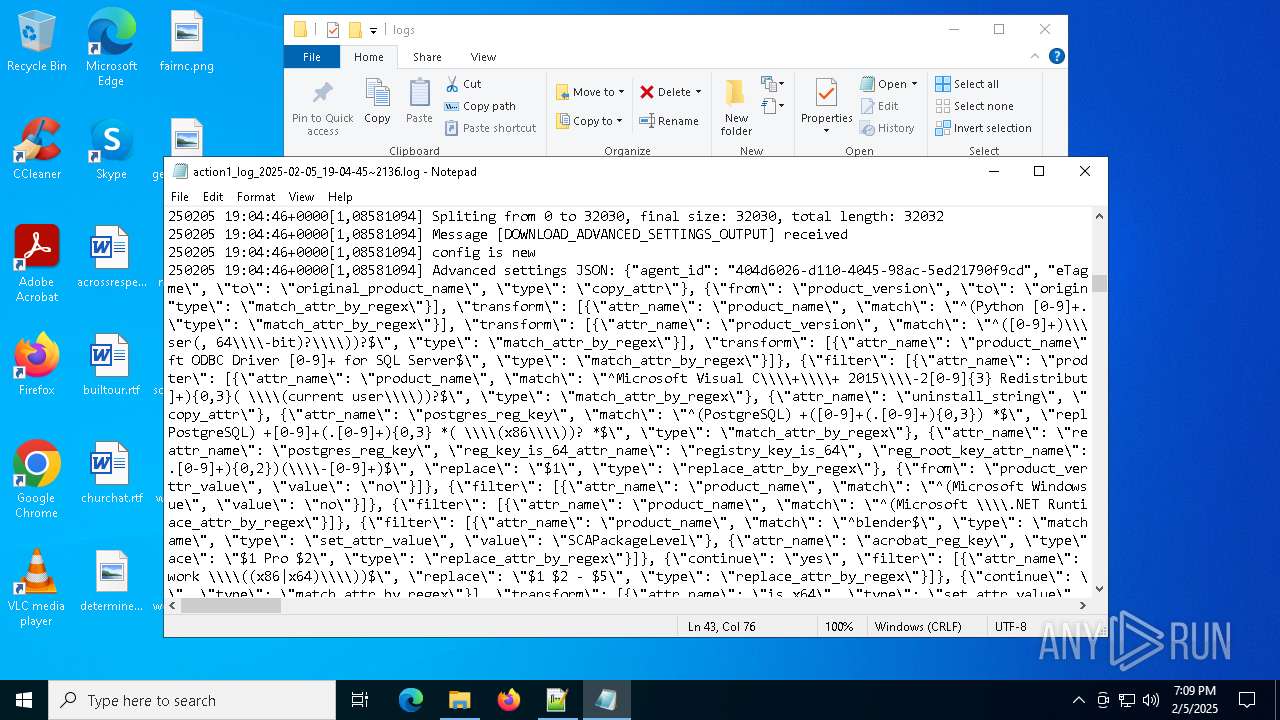
| 768 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Windows\Action1\logs\action1_log_2025-02-05_19-04-45~2136.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
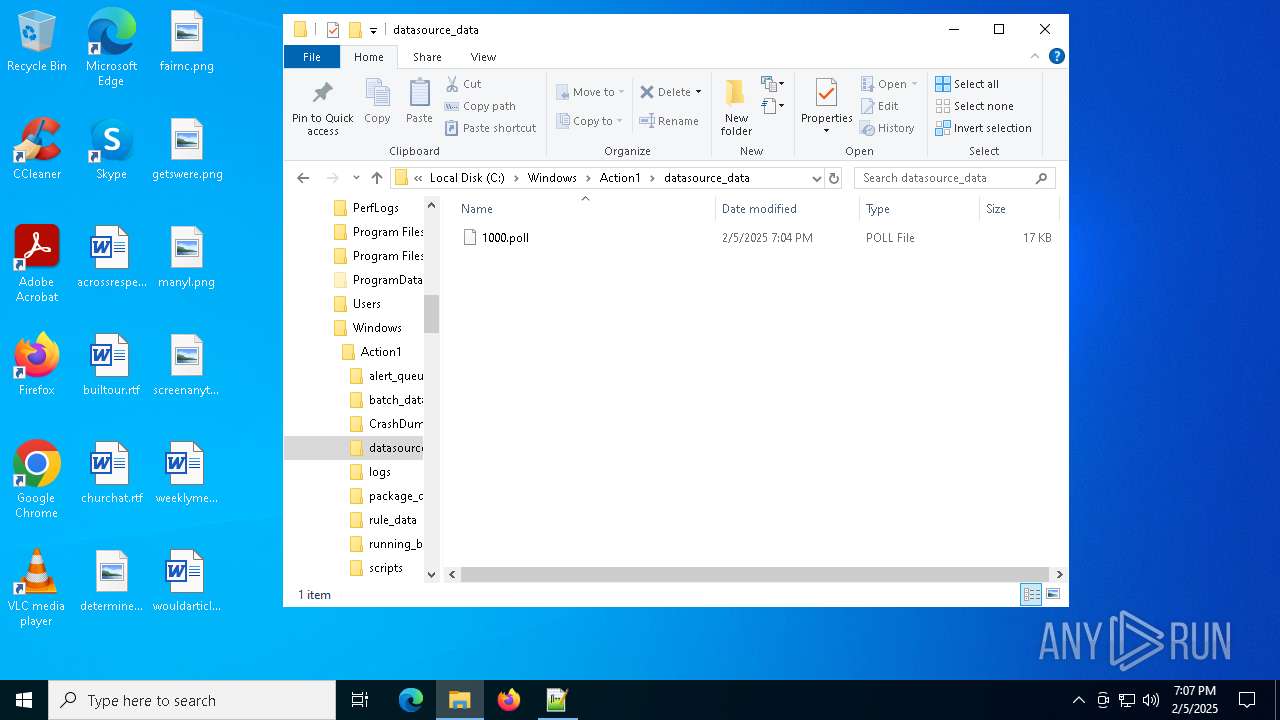
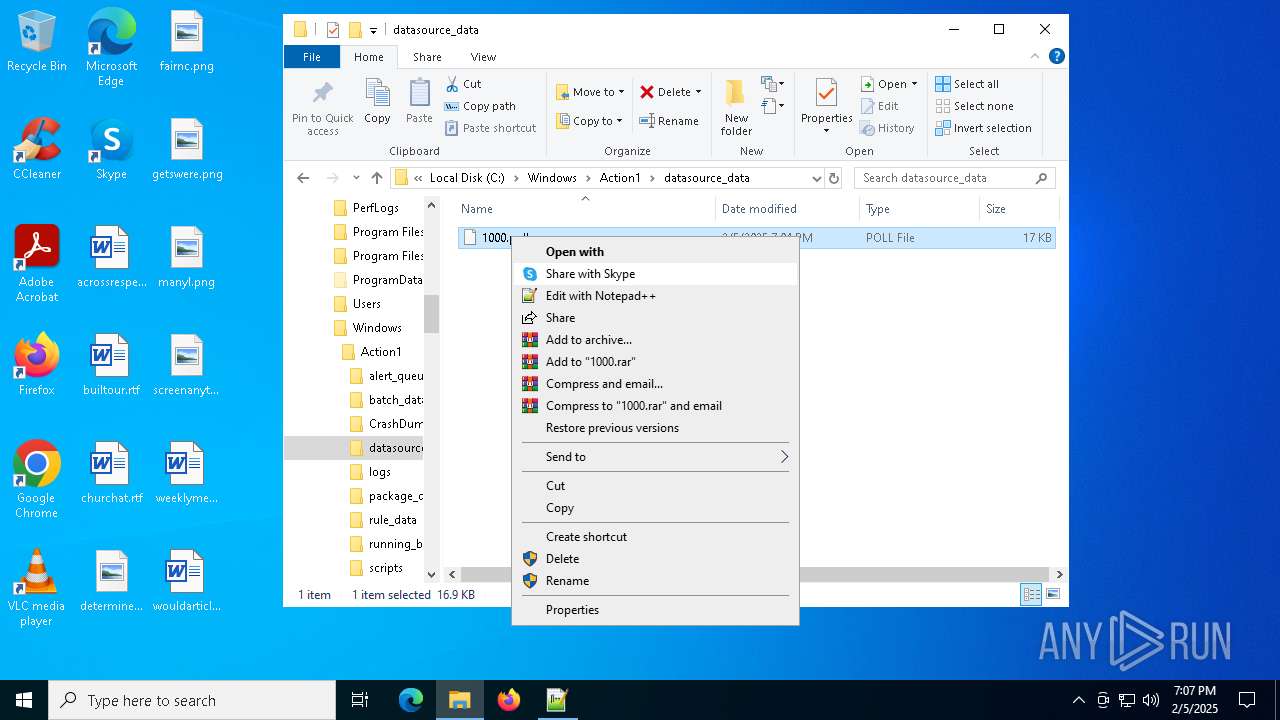
| 1704 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\Action1\datasource_data\1000.poll" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
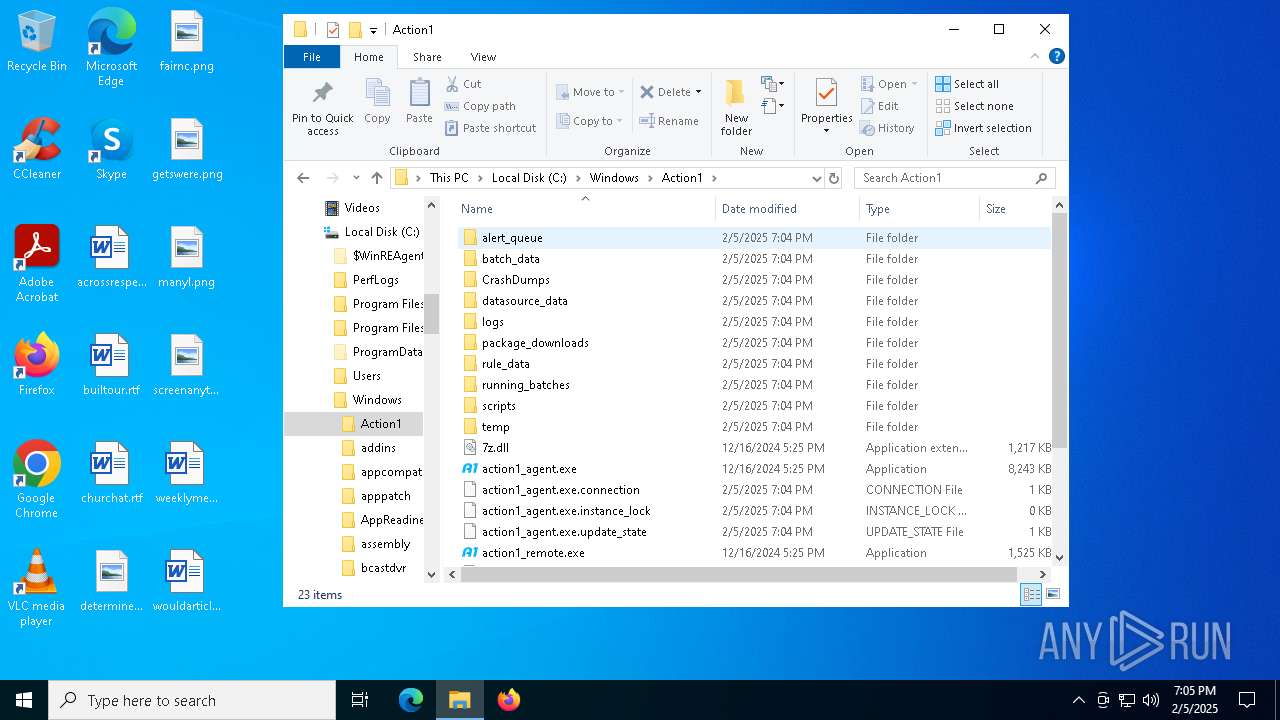
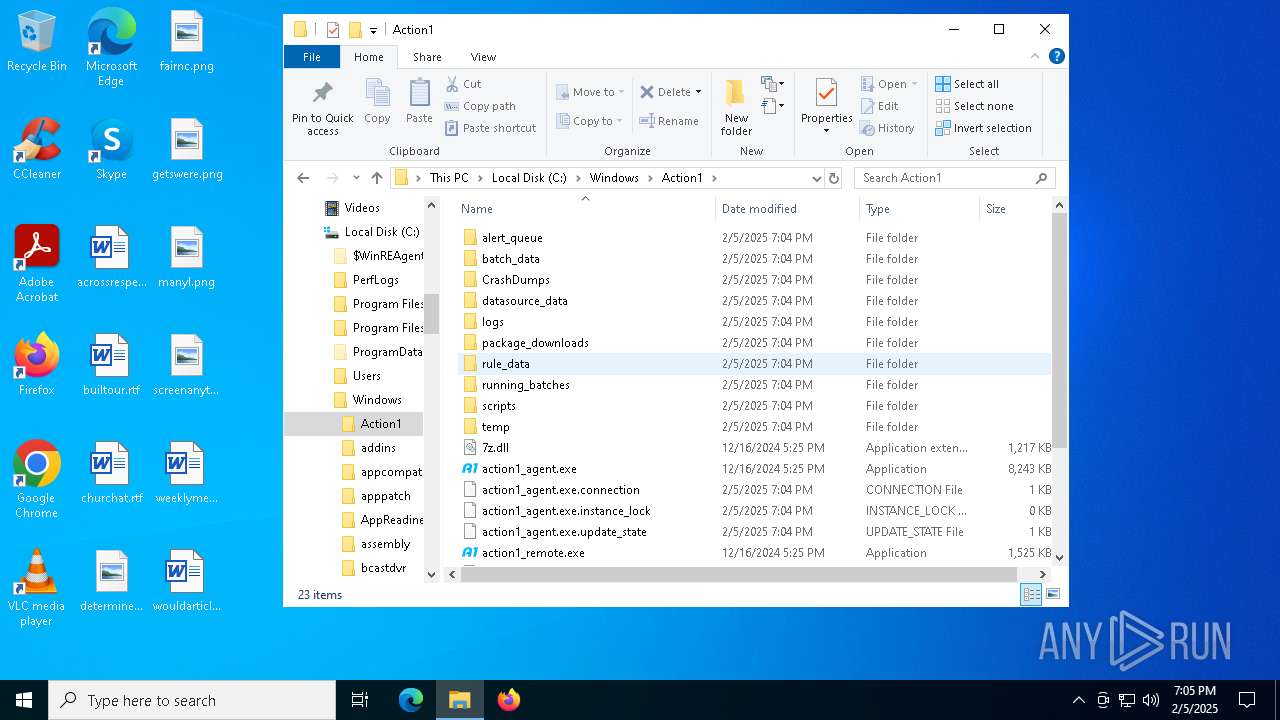
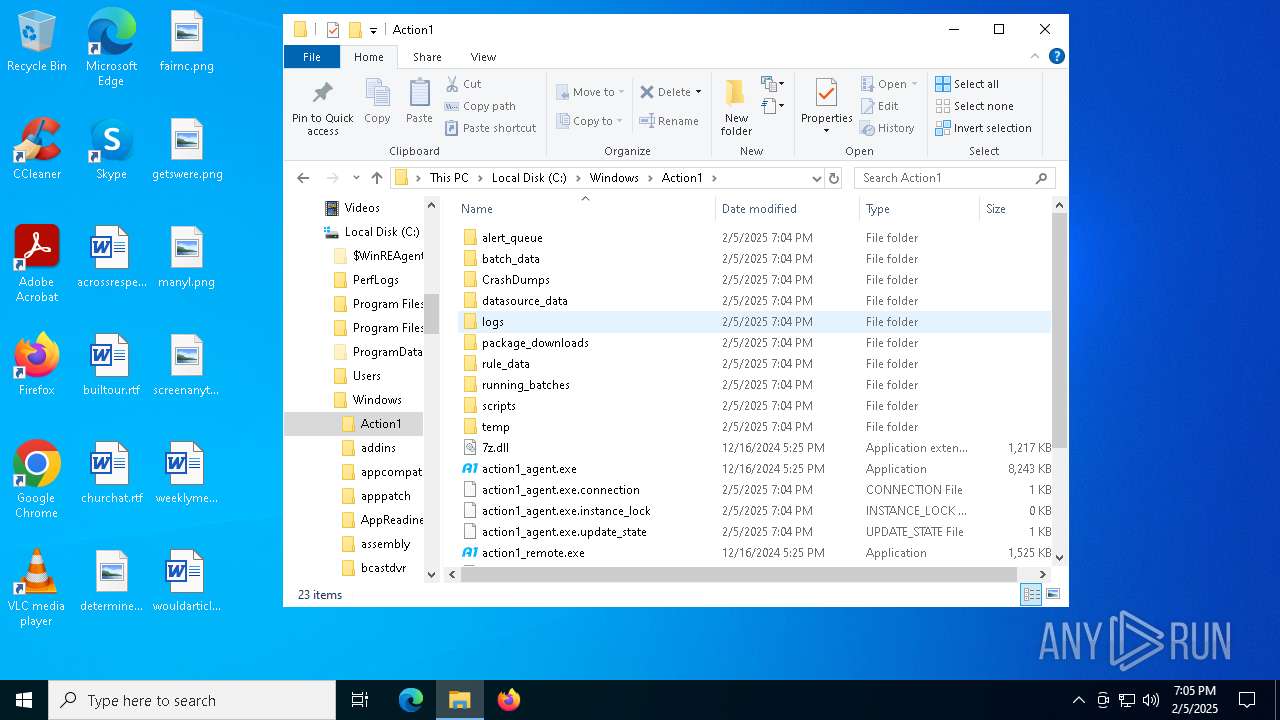
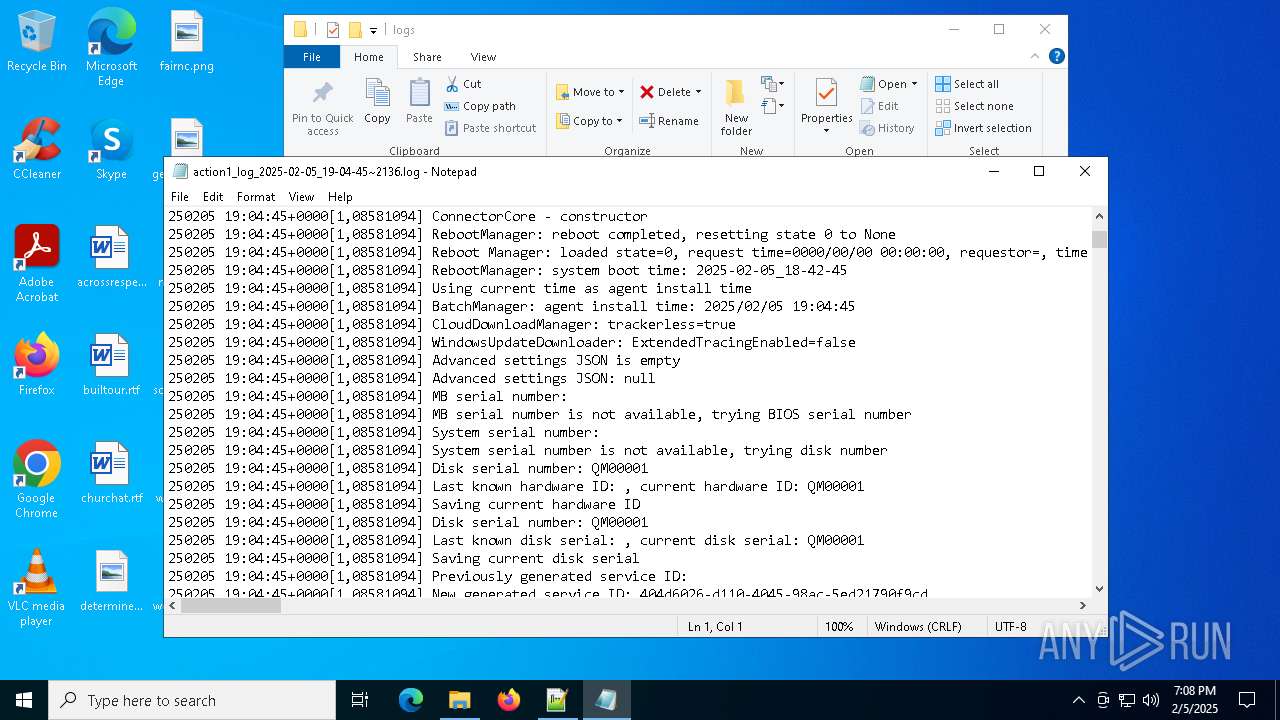
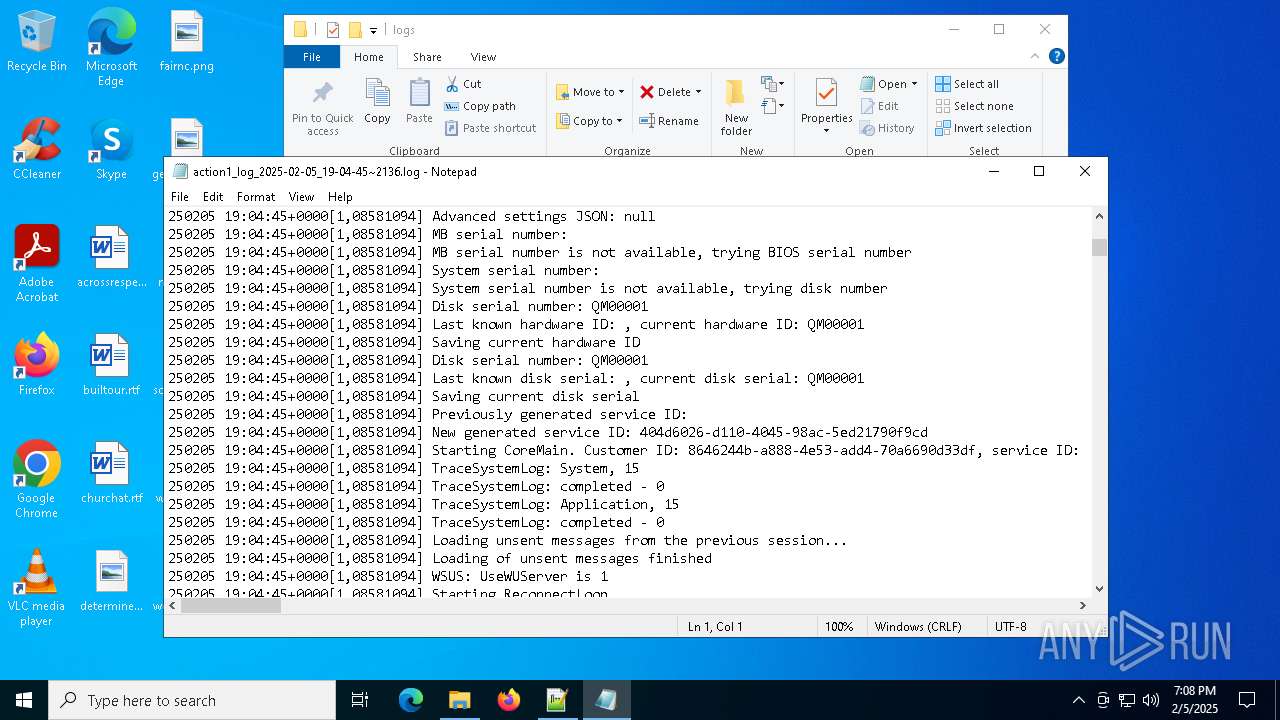
| 2136 | C:\WINDOWS\Action1\action1_agent.exe service | C:\Windows\Action1\action1_agent.exe | services.exe | ||||||||||||
User: SYSTEM Company: Action1 Corporation Integrity Level: SYSTEM Description: Endpoint Agent Version: 5.213.614.1 Modules
| |||||||||||||||
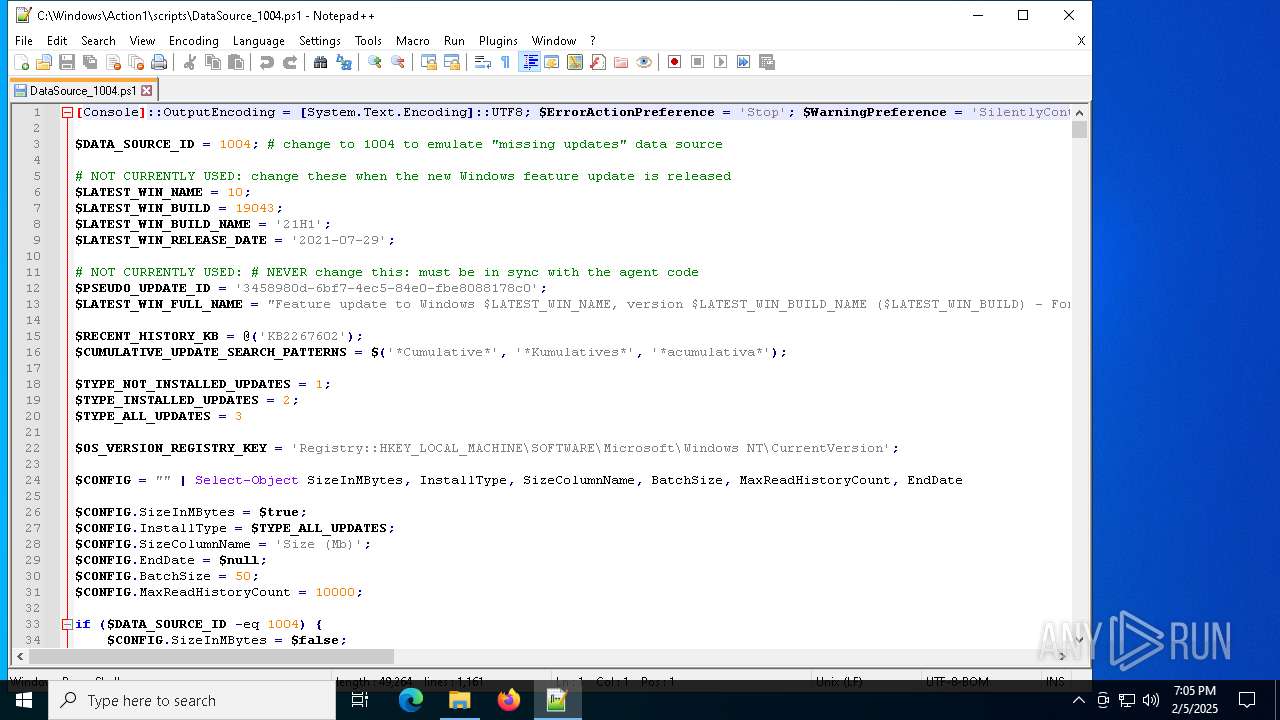
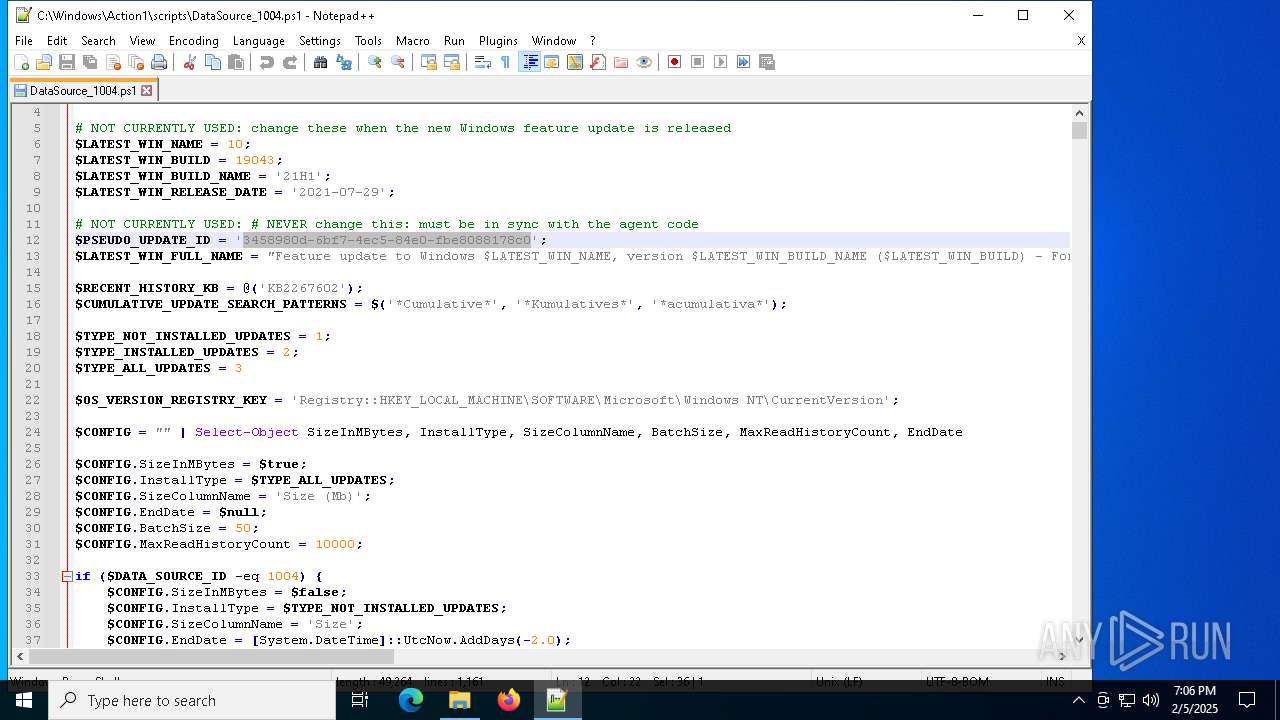
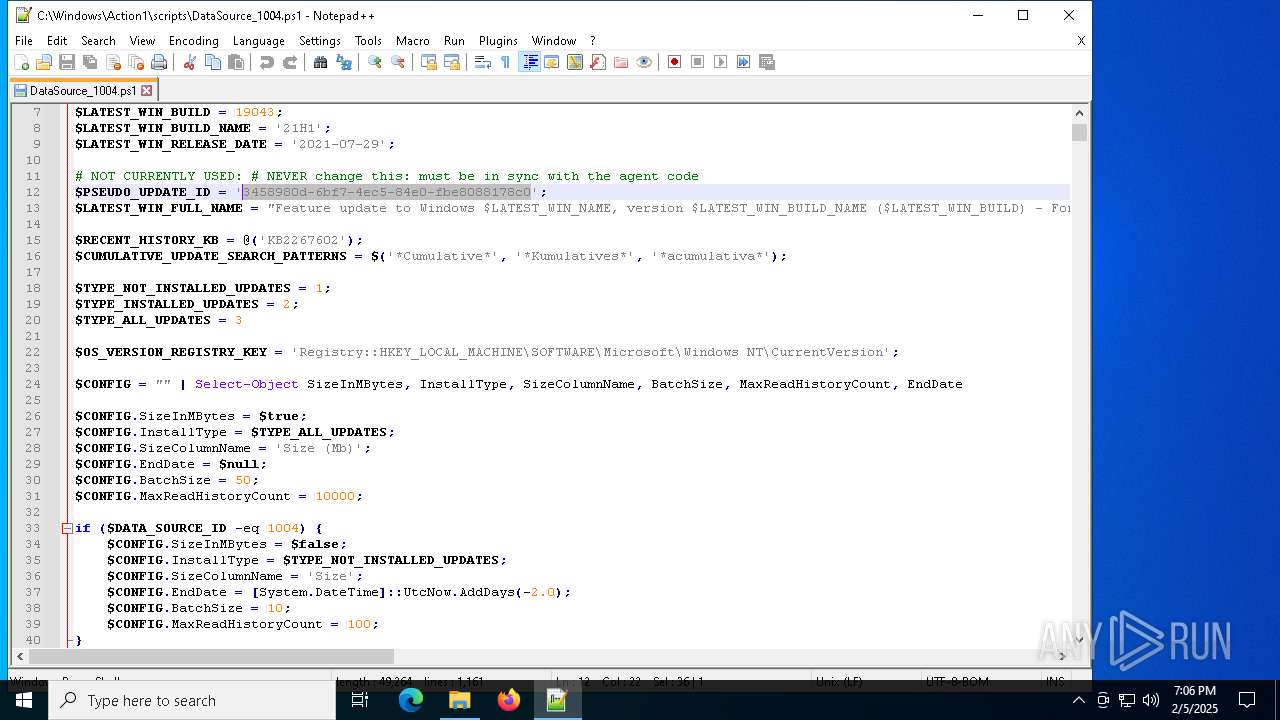
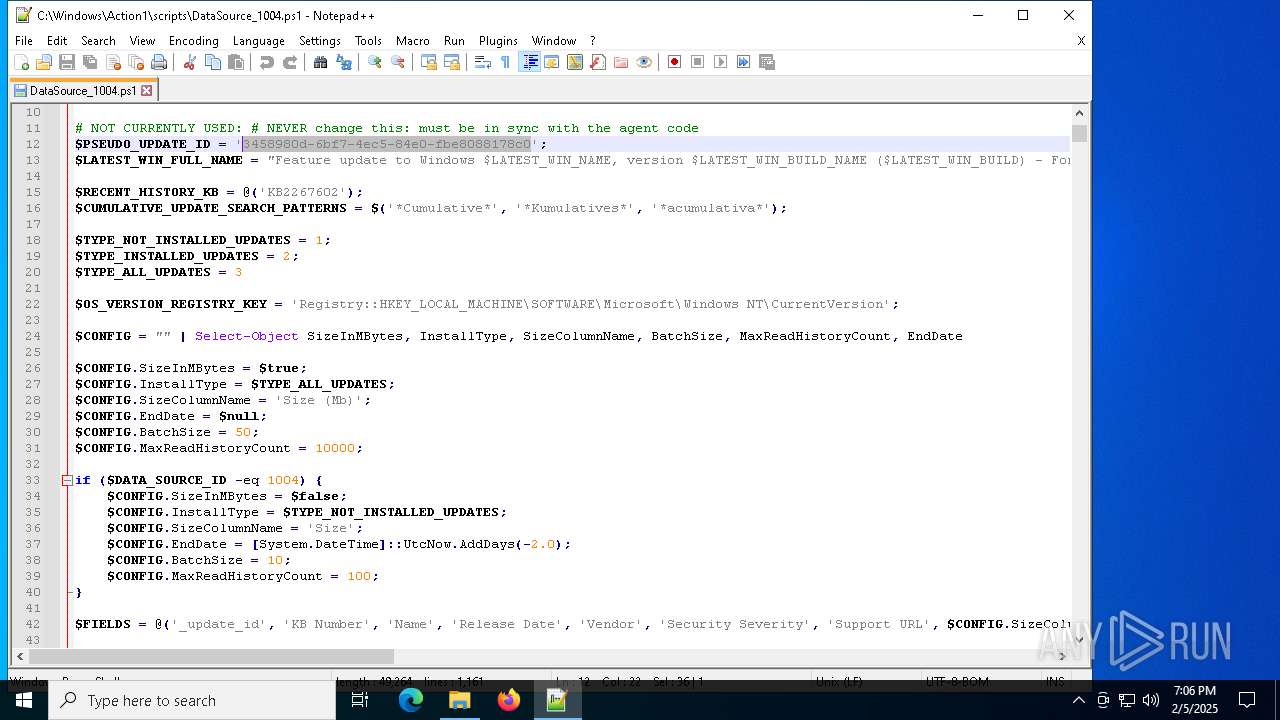
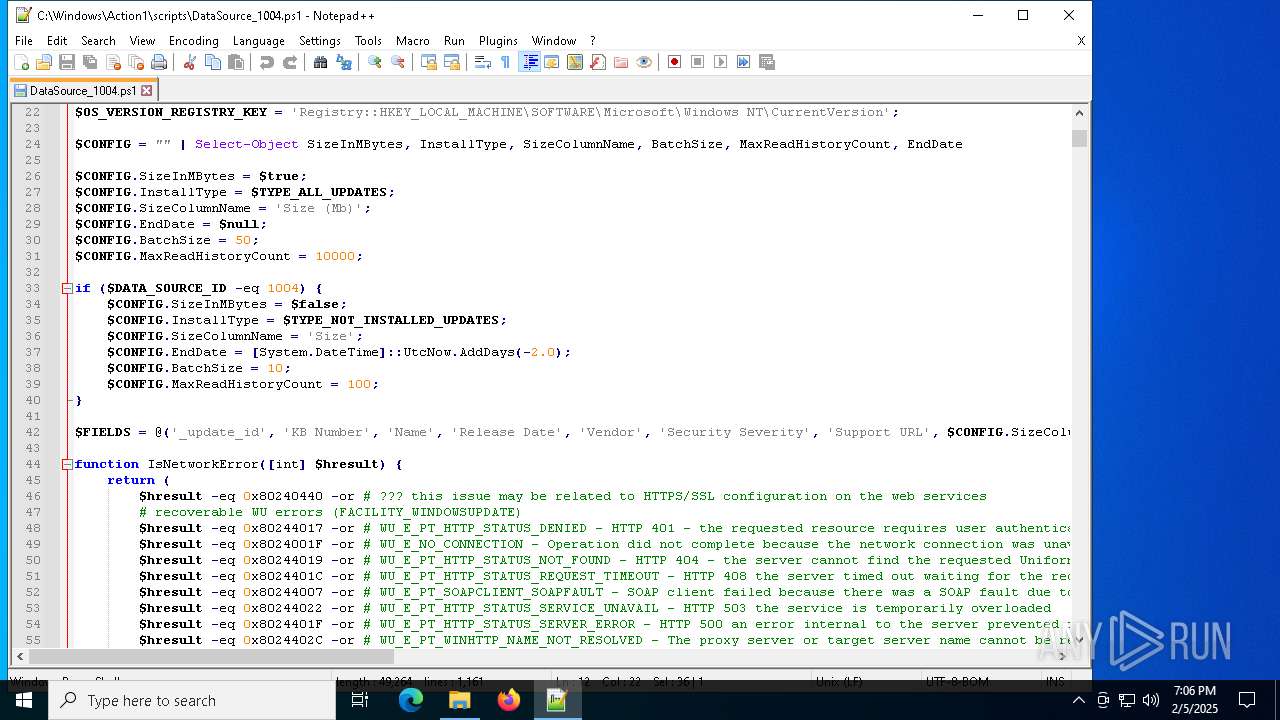
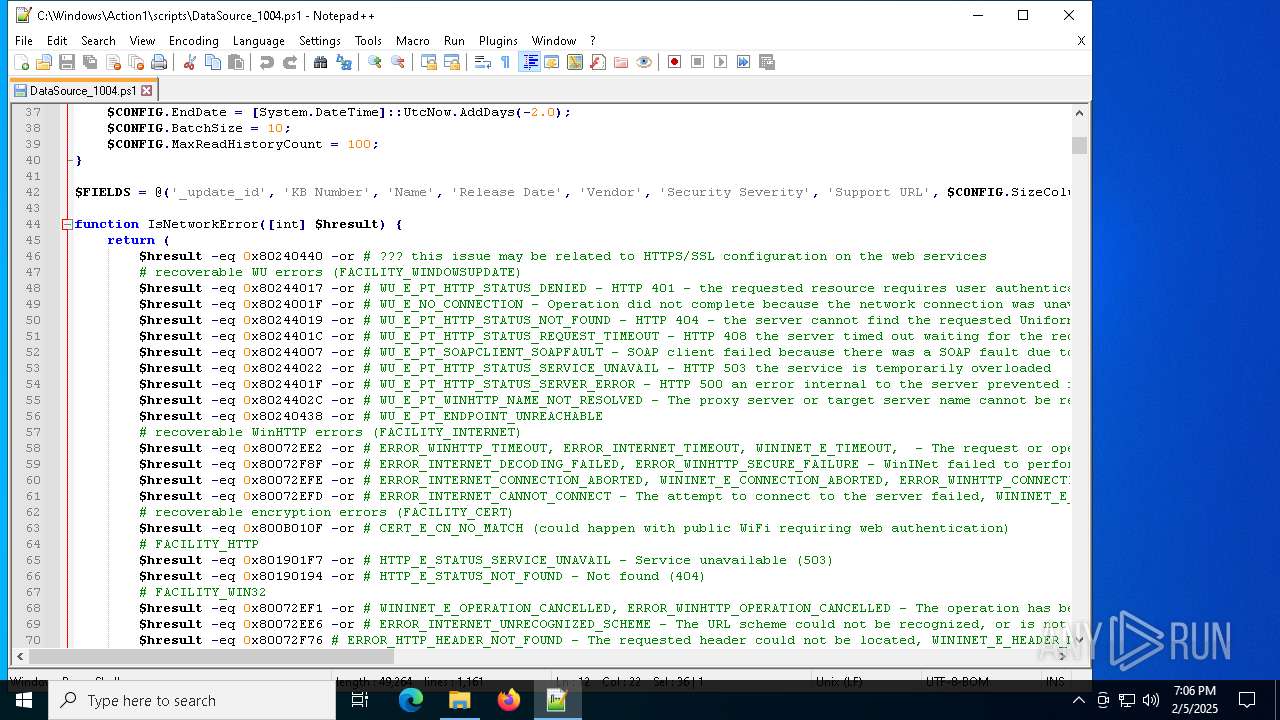
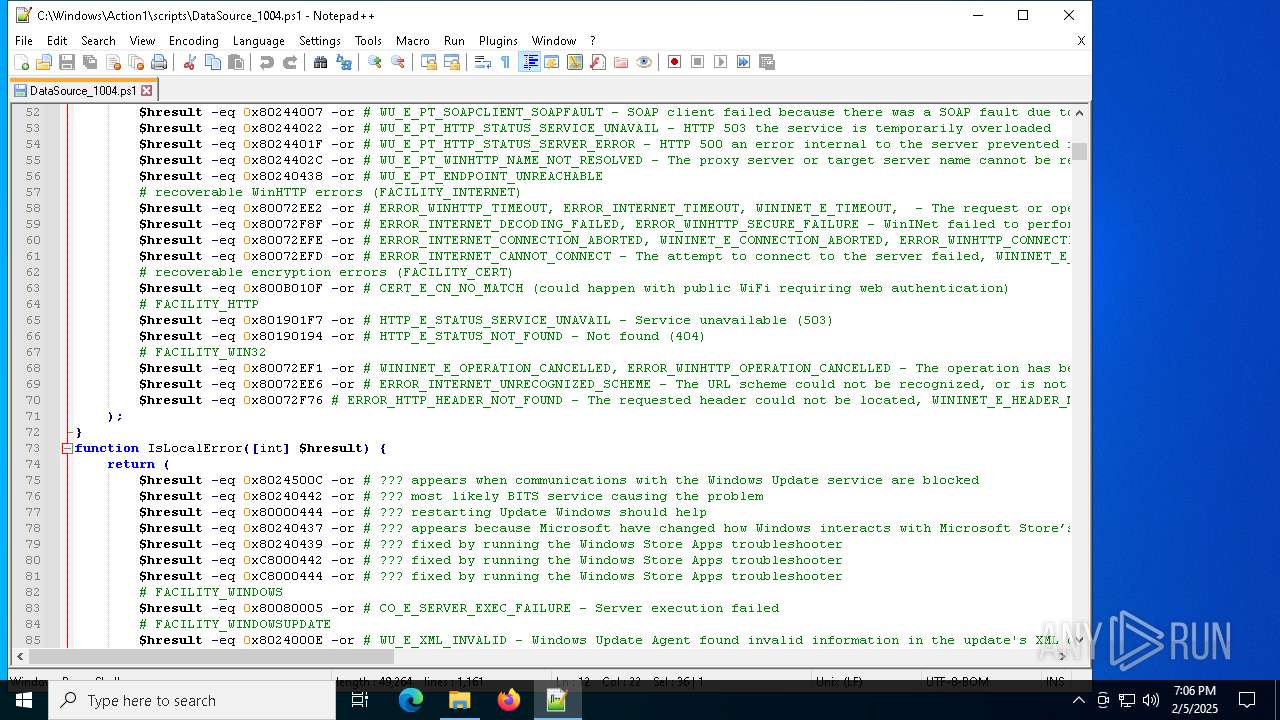
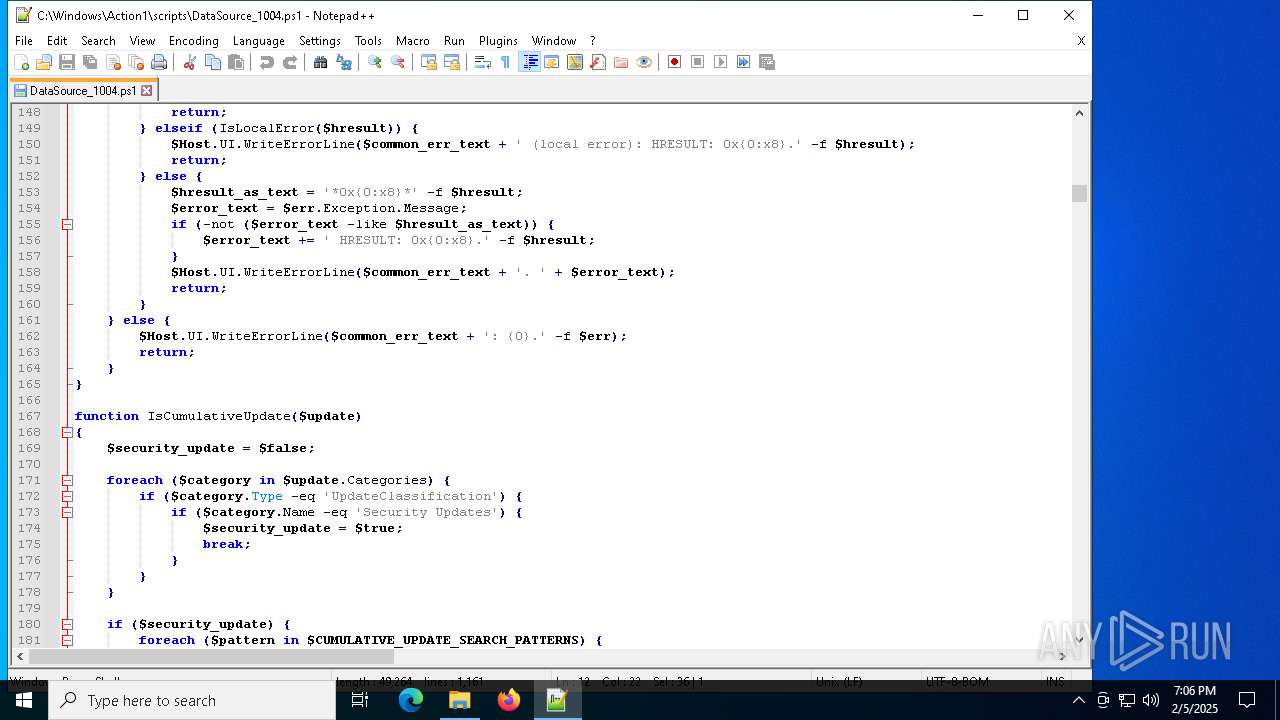
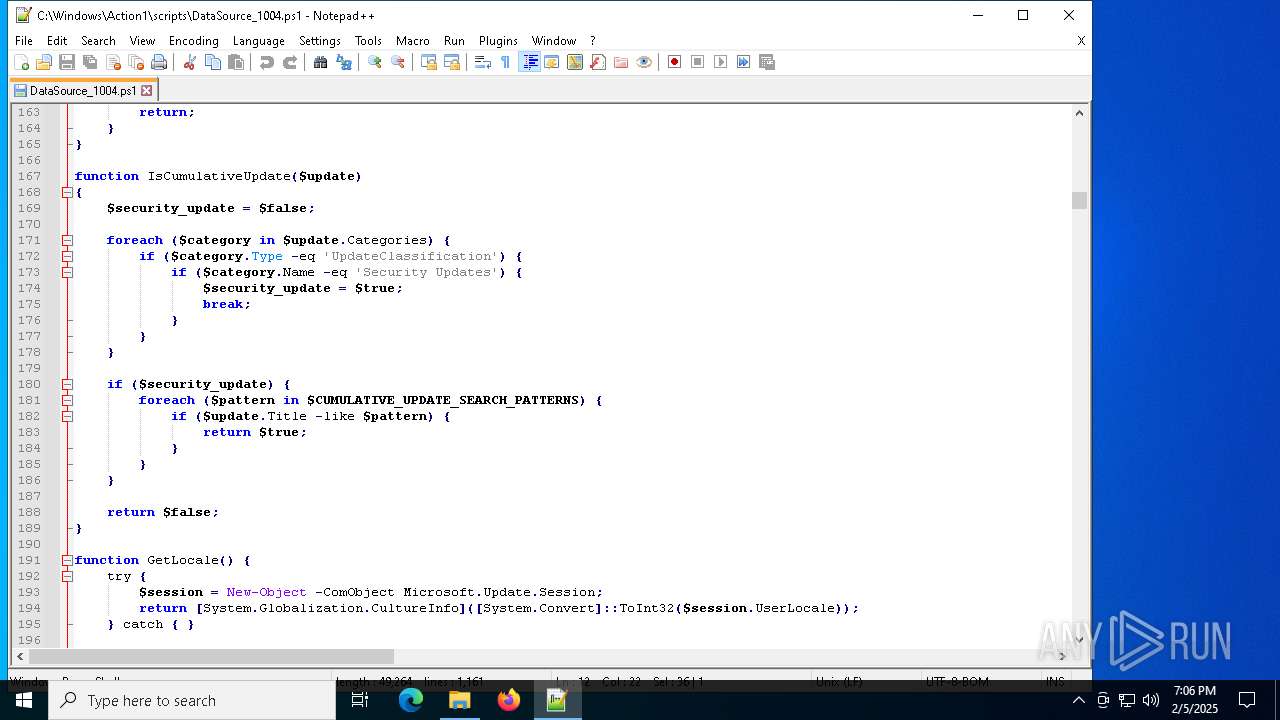
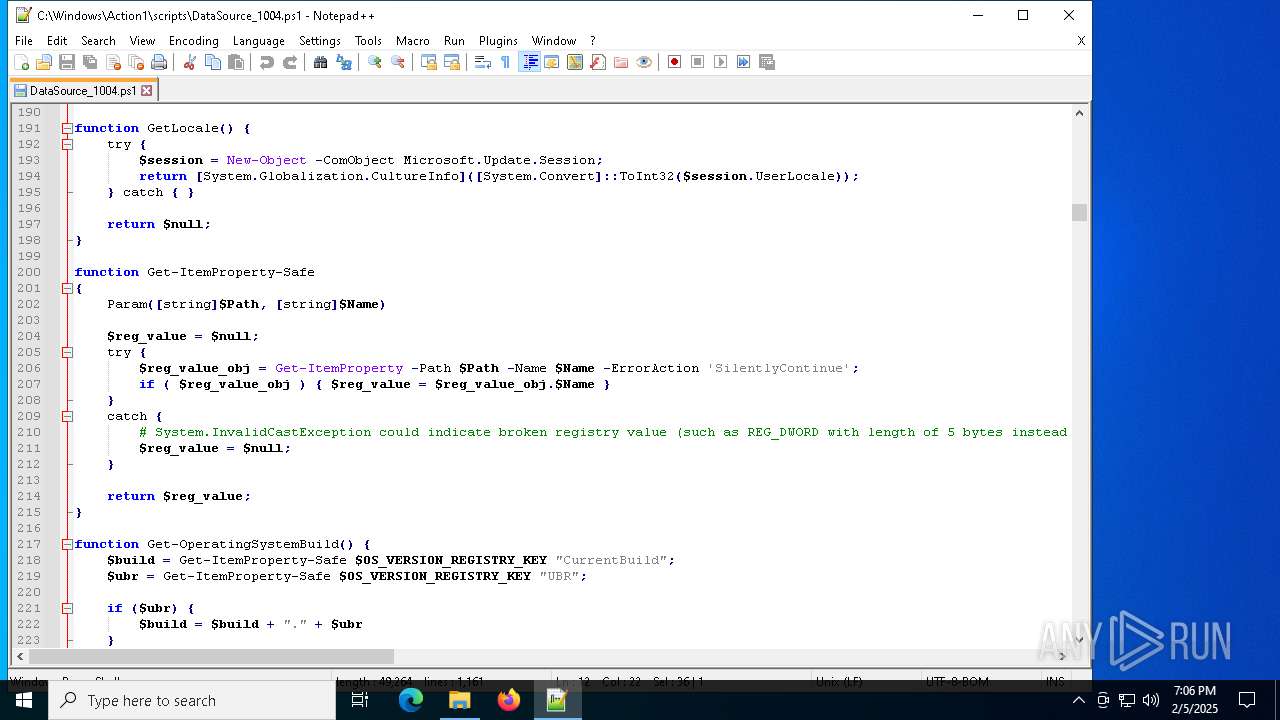
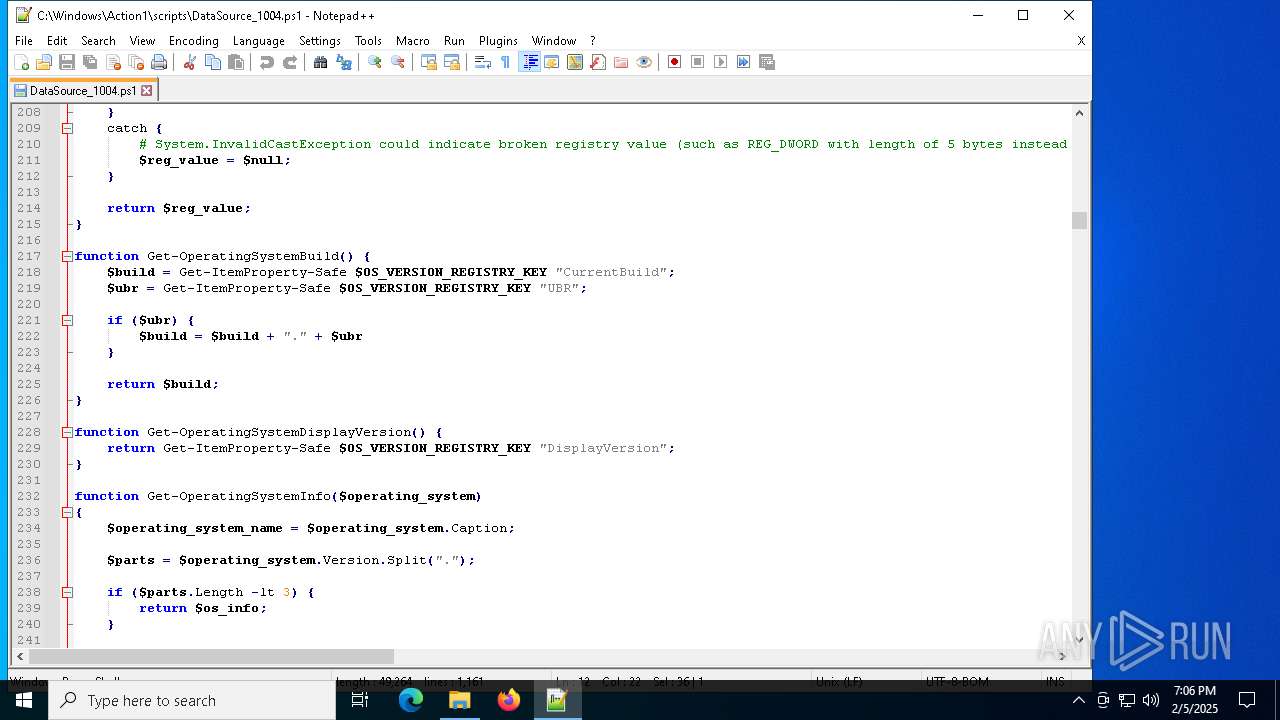
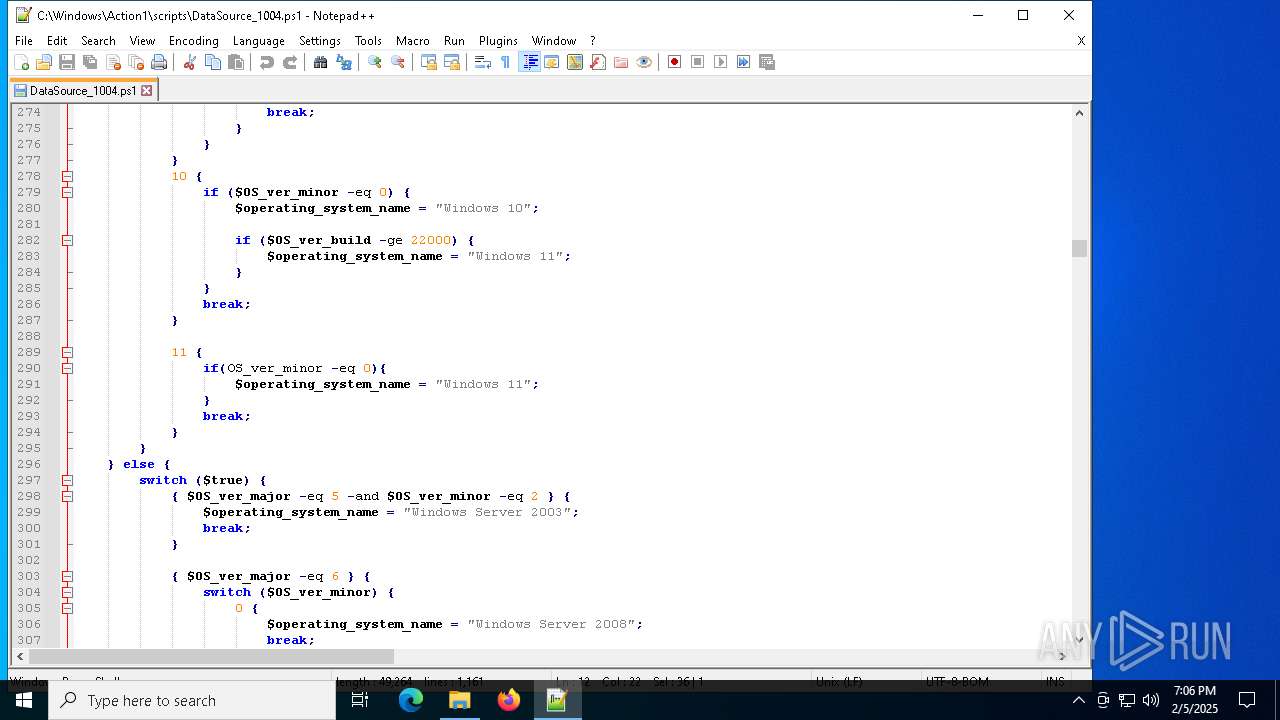
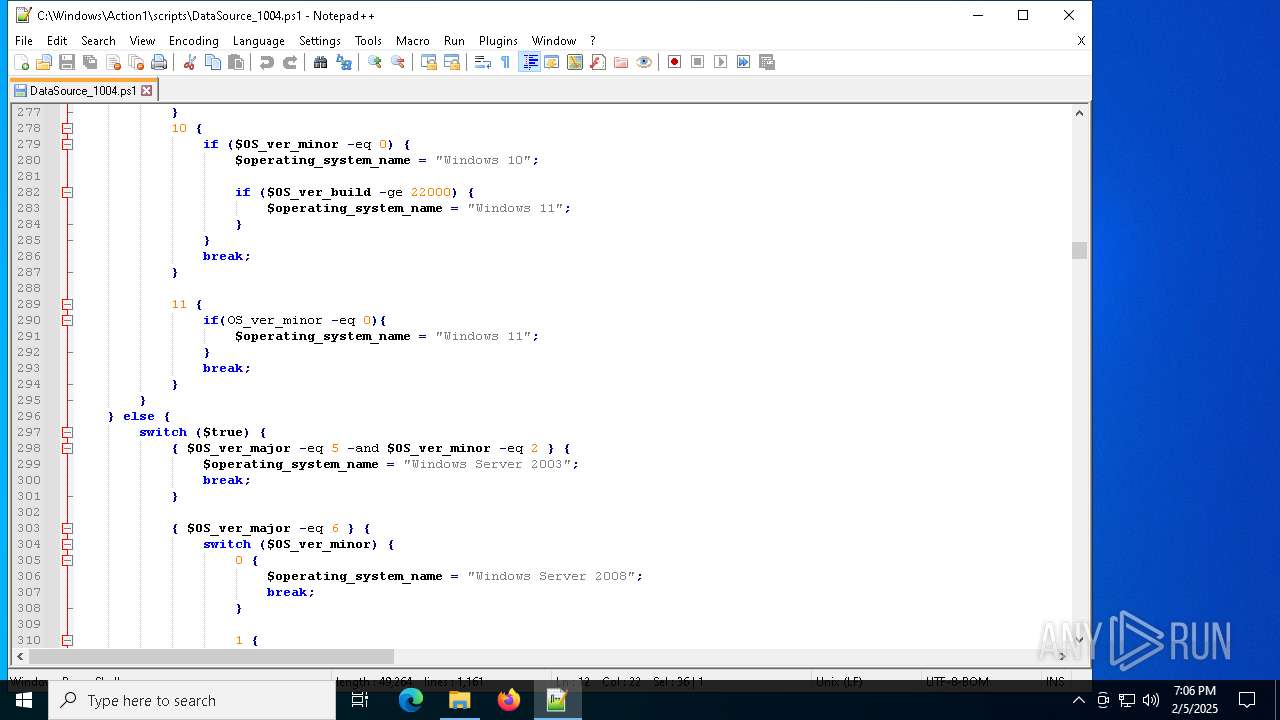
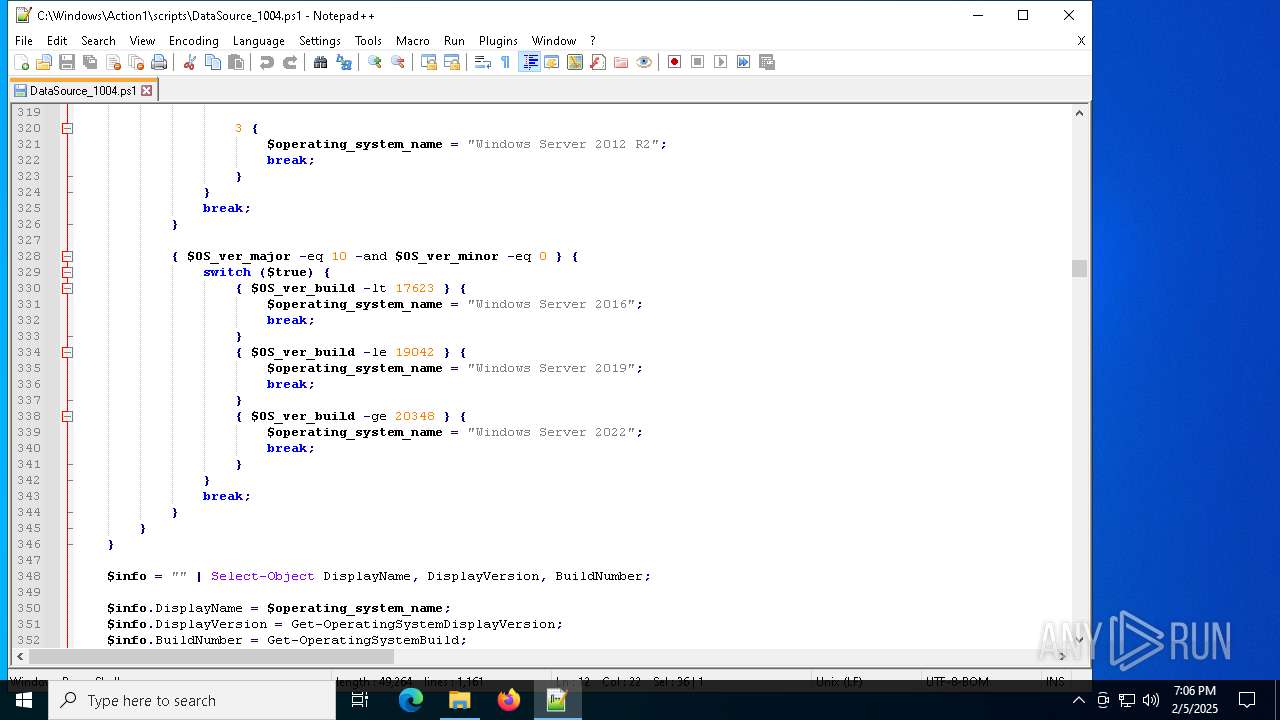
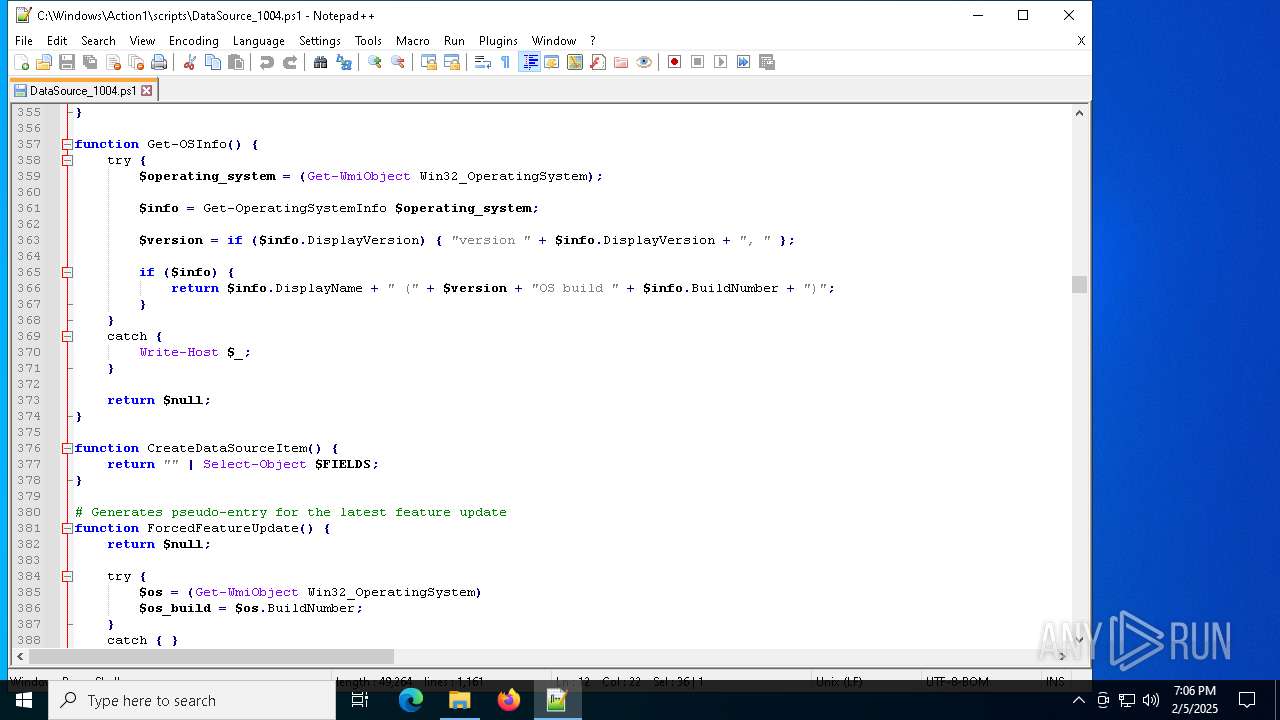
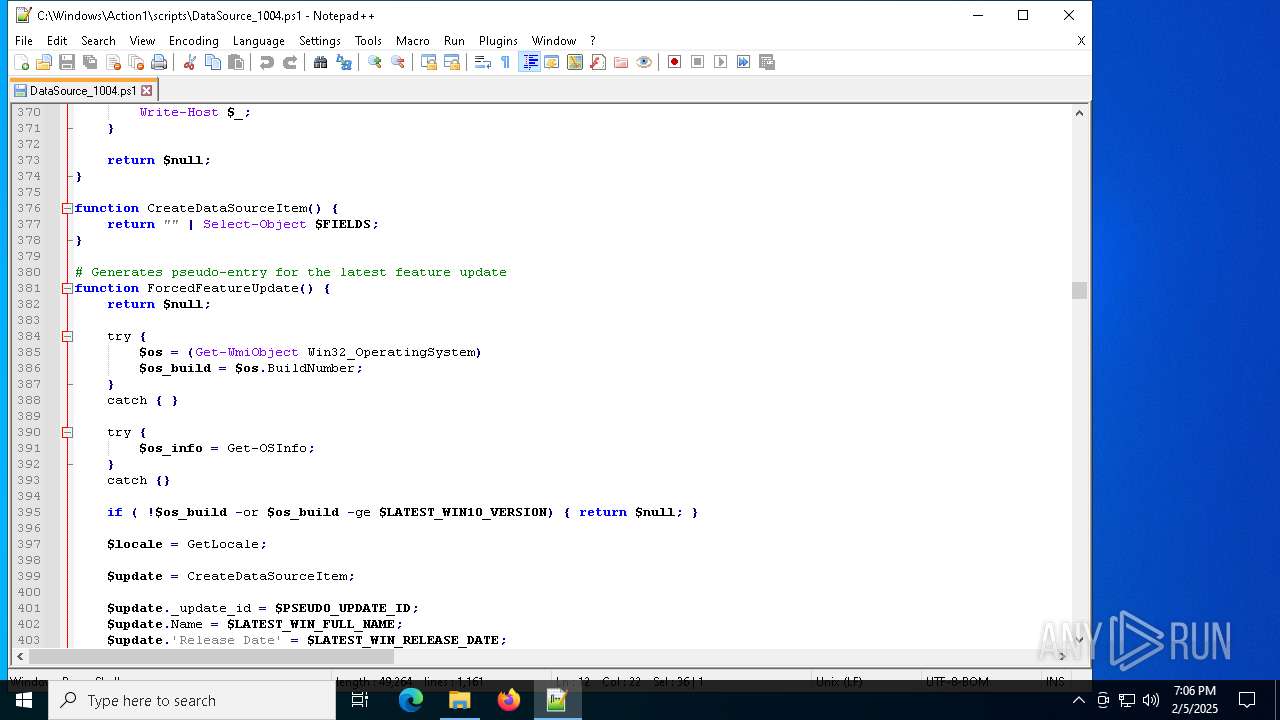
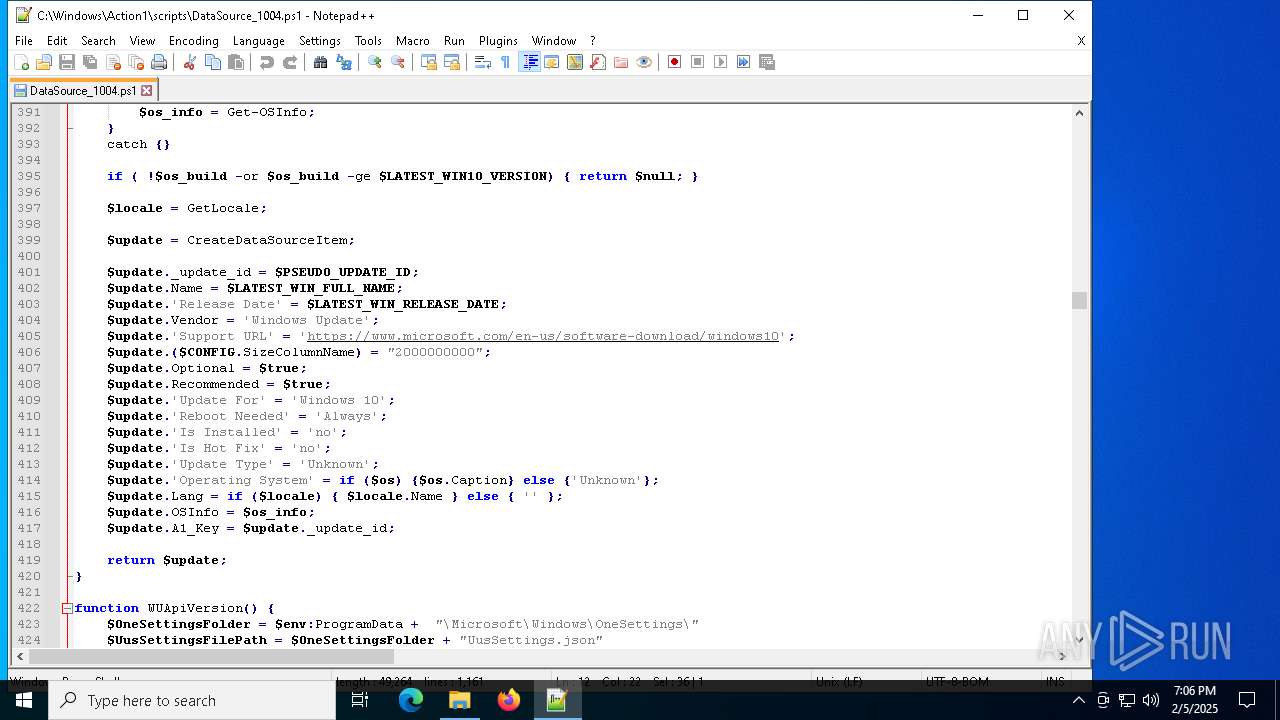
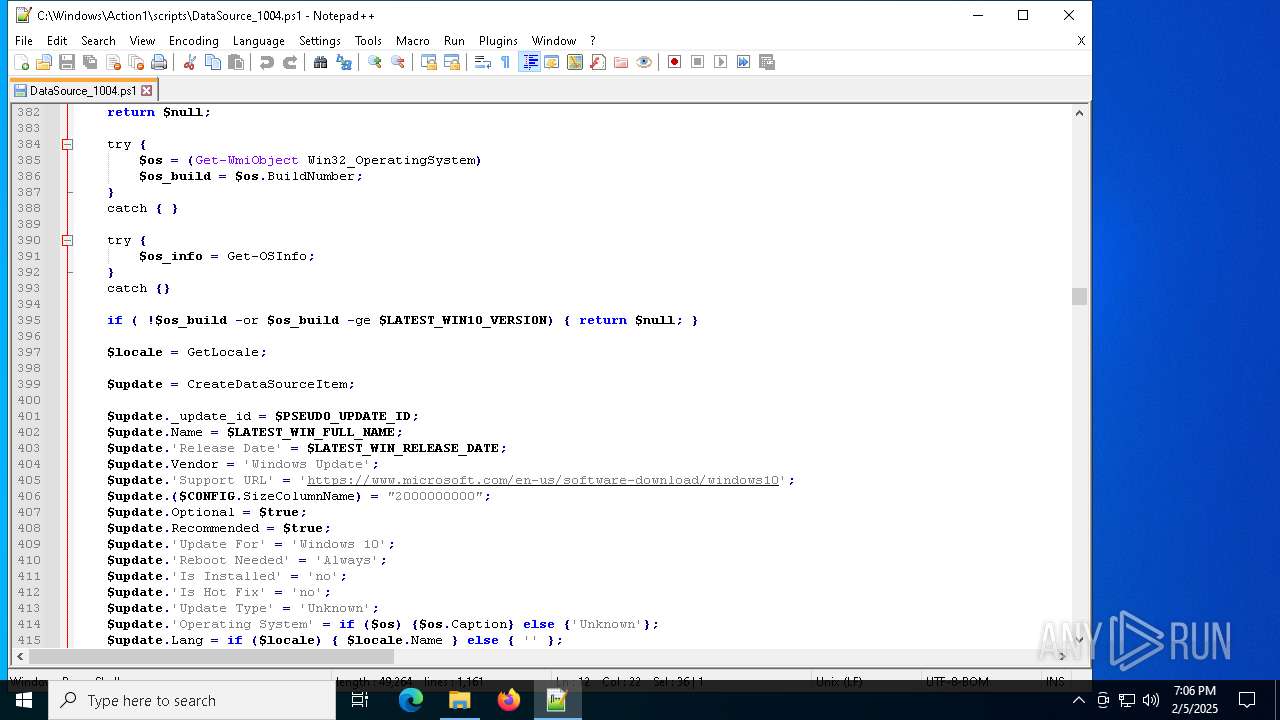
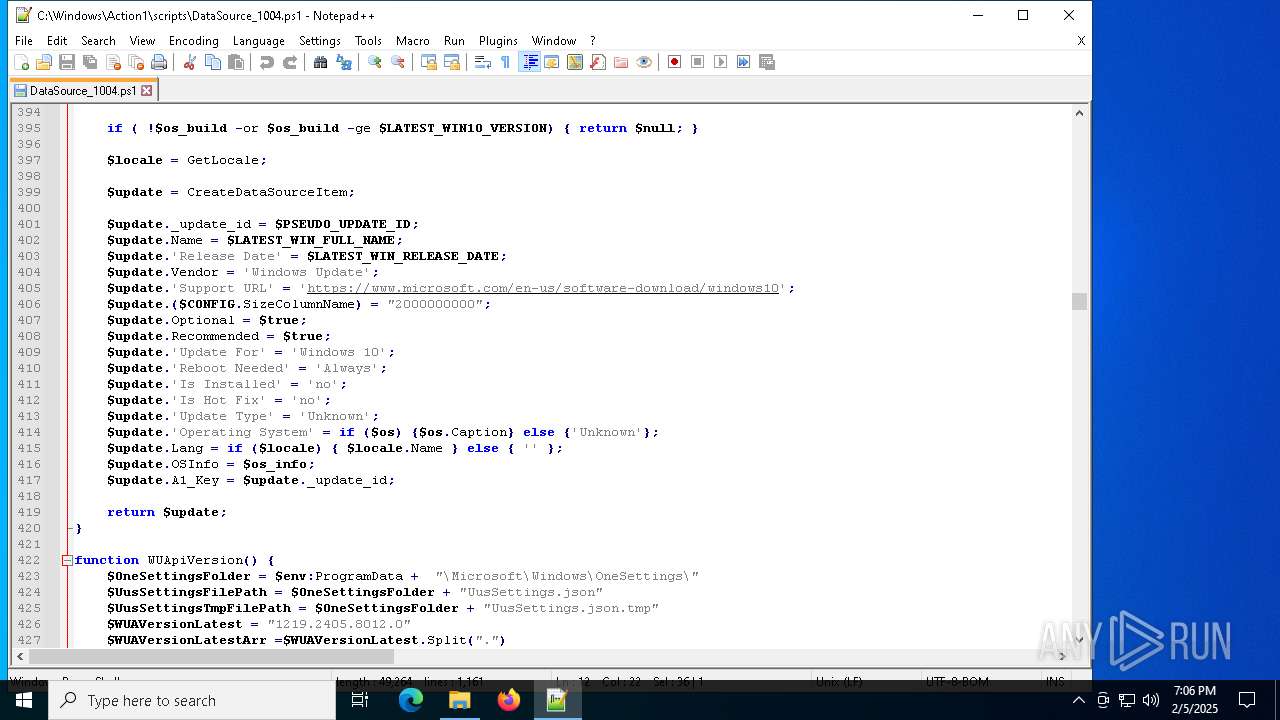
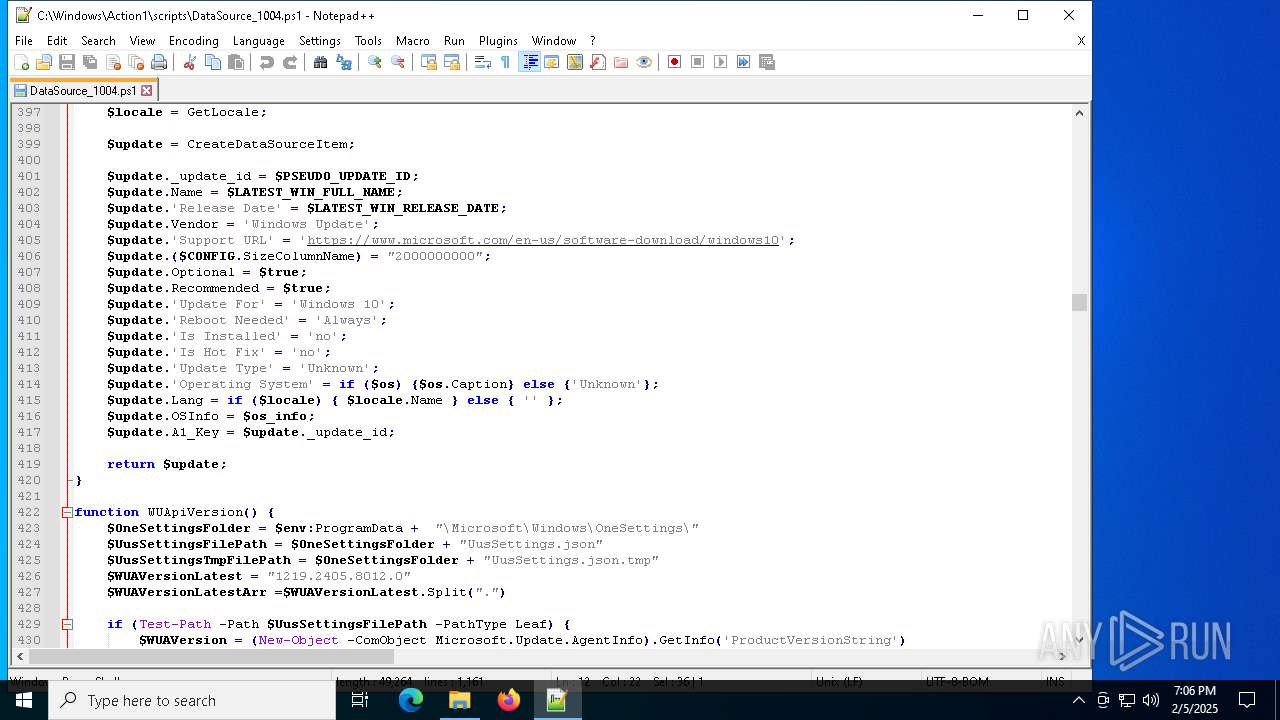
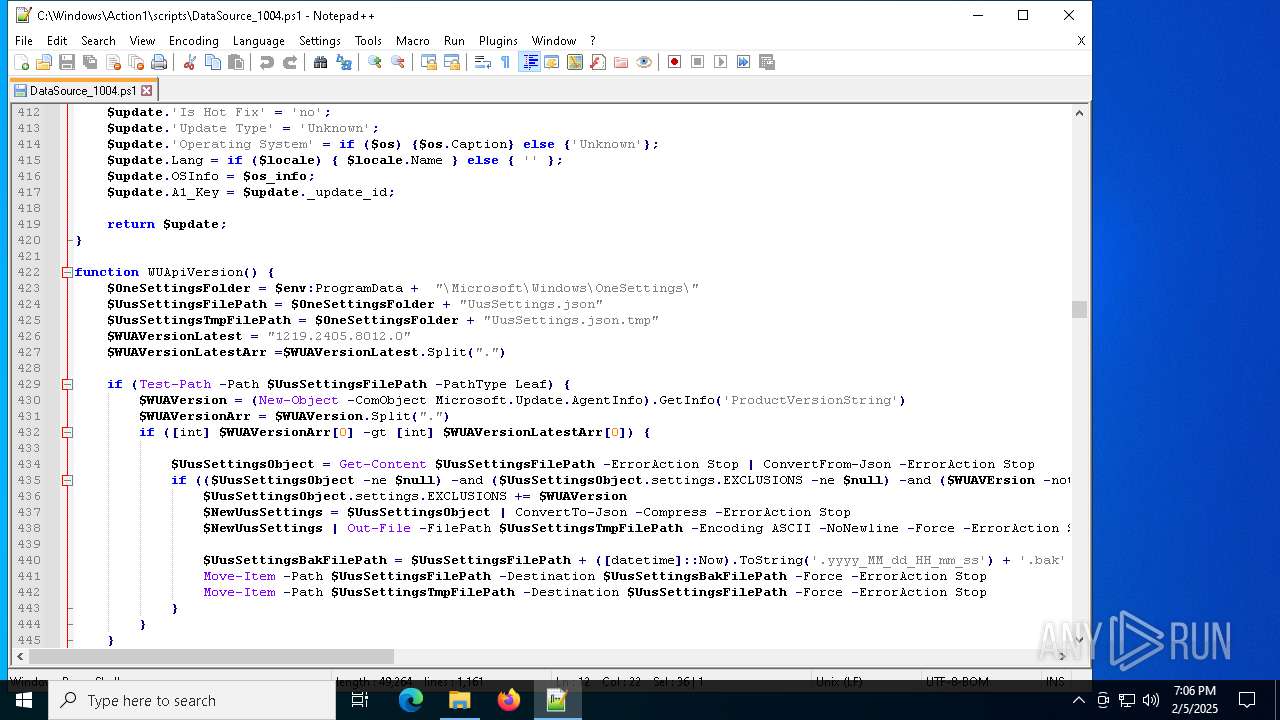
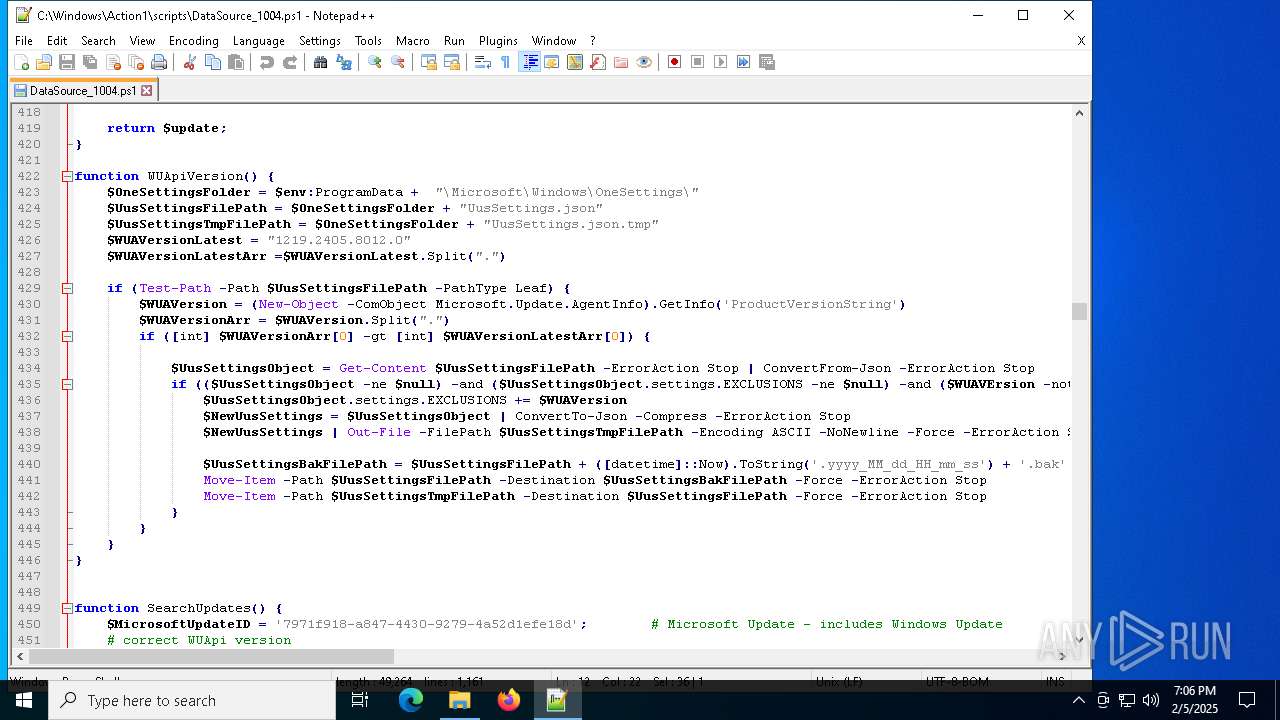
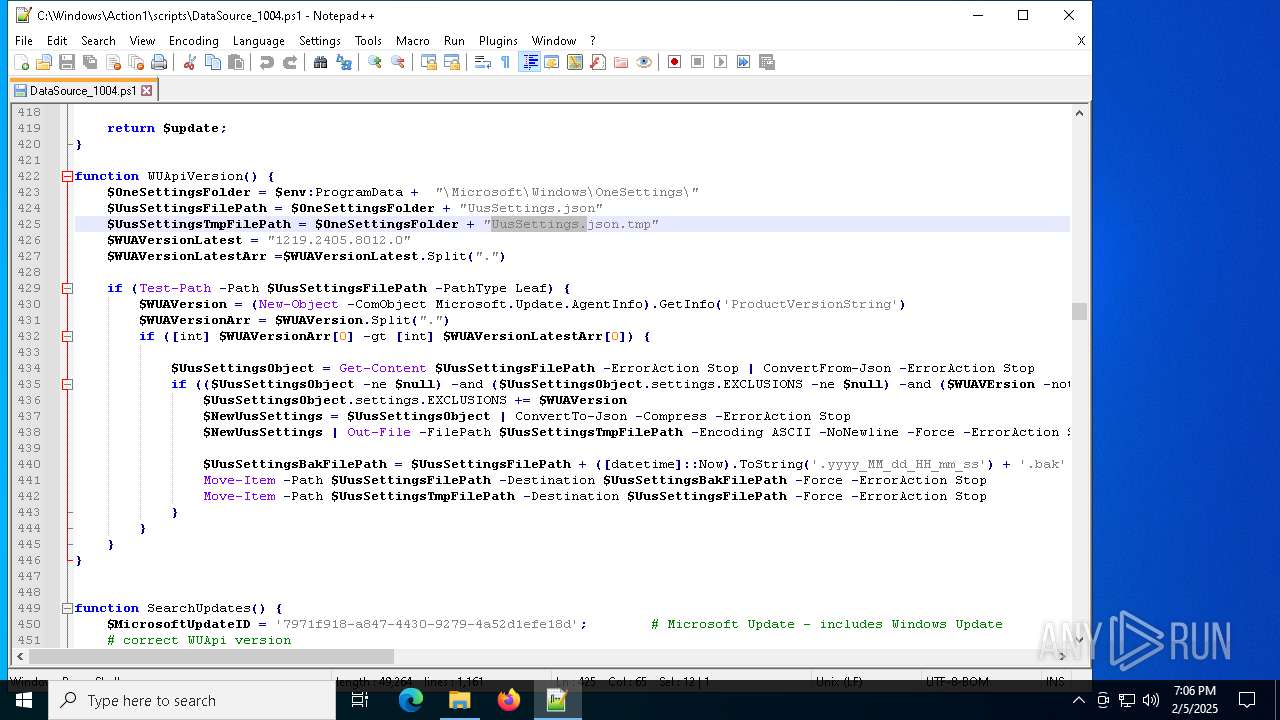
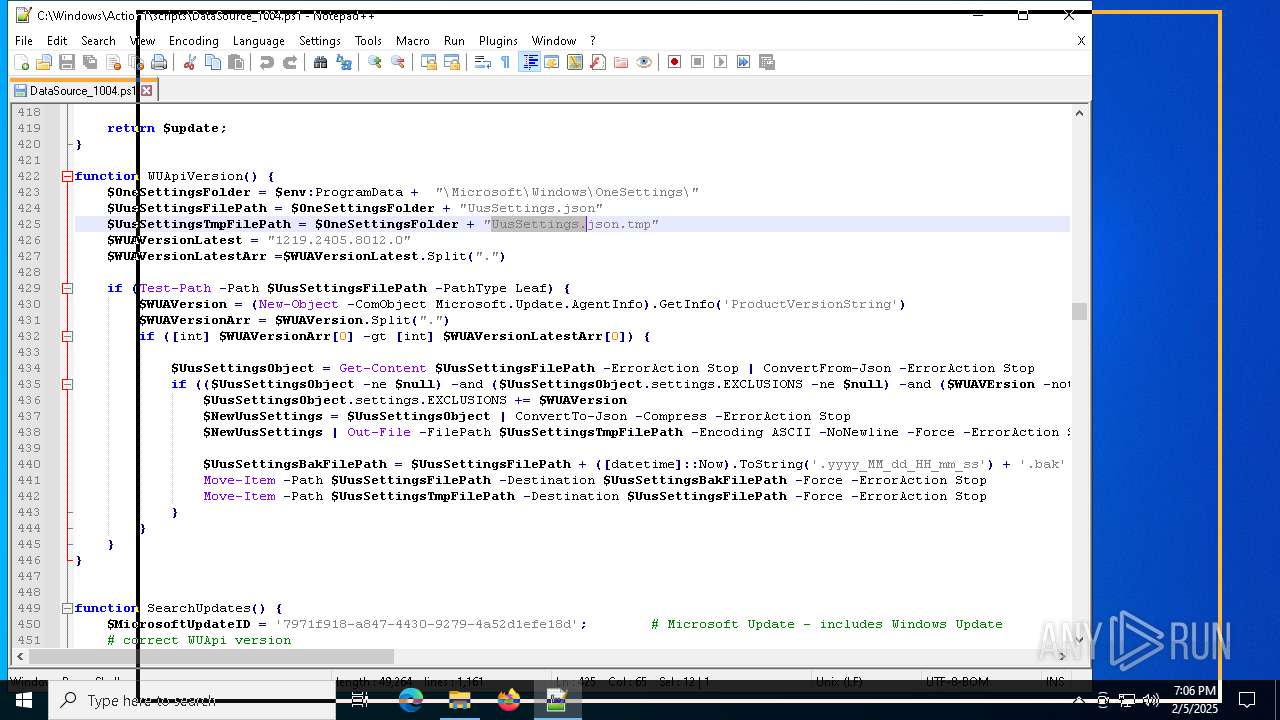
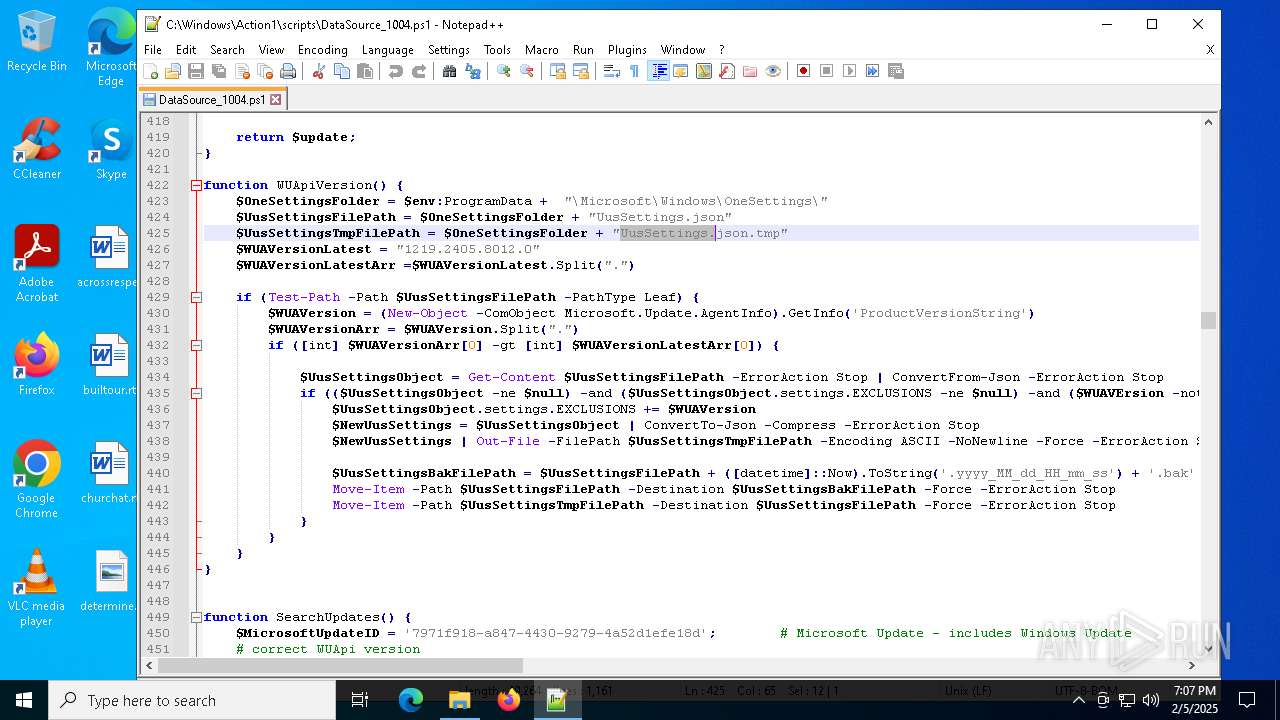
| 2624 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\Action1\scripts\DataSource_1004.ps1" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 3820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | C:\Windows\syswow64\MsiExec.exe -Embedding CE2C01646C49E7C3021DDE7619C8CA4E | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4144 | C:\Windows\syswow64\MsiExec.exe -Embedding 1663E99450C231964C0D01A323A08005 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 989
Read events
16 644
Write events
325
Delete events
20
Modification events
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000D7D7F5BF0078DB01AC190000B01B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000D7D7F5BF0078DB01AC190000B01B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000082BA3FC00078DB01AC190000B01B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000531D42C00078DB01AC190000B01B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000060E446C00078DB01AC190000B01B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000068144C00078DB01AC190000B01B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000003375FEC00078DB01AC190000B01B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7104) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000040B205C10078DB01C01B0000D8120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7104) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000040B205C10078DB01C01B0000E01B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7104) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000040B205C10078DB01C01B0000900F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
39
Text files
14
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6572 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6572 | msiexec.exe | C:\Windows\Installer\141b27.msi | — | |
MD5:— | SHA256:— | |||
| 6572 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:99AF0A41BB8DCEB15BF2E872F8F6B992 | SHA256:E6CB772774D708BD9D0FD3F7CCDE99AA95230E12E2681B868F932A25F92F1C5B | |||
| 6572 | msiexec.exe | C:\Windows\Action1\sas.dll | executable | |
MD5:969D1F85151E0156D51A664E59A50213 | SHA256:996B01E15F85E165899630721A141B178A9C372B6E878012180EC9E9D4E7BD06 | |||
| 6572 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7470a403-5d90-48c5-b5e6-d8e8a689494f}_OnDiskSnapshotProp | binary | |
MD5:9101B2A4C7E36BA47709FBF641F6B784 | SHA256:6A770D01D7DCB4EBA66D1FD0657209BC36756588810876FCBFB10C8705E58FEE | |||
| 6572 | msiexec.exe | C:\Windows\Action1\7z.dll | executable | |
MD5:26ACF2E068A715BD449A1CFCB9074AE4 | SHA256:F9762180D733B0AFDEBD33869DA91B96623A439A70E27573E71974AFB39B436B | |||
| 6572 | msiexec.exe | C:\Windows\Temp\~DF123582F083C03C5C.TMP | binary | |
MD5:99AF0A41BB8DCEB15BF2E872F8F6B992 | SHA256:E6CB772774D708BD9D0FD3F7CCDE99AA95230E12E2681B868F932A25F92F1C5B | |||
| 6572 | msiexec.exe | C:\Windows\Action1\action1_remote.exe | executable | |
MD5:BF7777B3D04D9E29B6FDC5699E254DB4 | SHA256:BCA6CD6F28C4774655BE9BAA32D630C737BEBF56E56AFE597843B3B632571430 | |||
| 6244 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3AA0DCD5A74331FBD6F344550EC48B87_FAB5A9F6C6BE3394975FF948CA40CA87 | binary | |
MD5:C62958256E44DC0DF147715C1162E4EC | SHA256:FD0AEBCABC56B2F41099A5212C535A010677D3986C2BA4196E7EE14890A62294 | |||
| 6572 | msiexec.exe | C:\Windows\Installer\MSI24EF.tmp | executable | |
MD5:8EDC1557E9FC7F25F89AD384D01BCEC4 | SHA256:78860E15E474CC2AF7AD6E499A8971B6B8197AFB8E49A1B9EAAA392E4378F3A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
30
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6244 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6244 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
6244 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEEV%2F6oPpCGe%2BJ43kKfDM9ME%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.130:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | — | Akamai International B.V. | DE | unknown |
6244 | msiexec.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6152 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
server.eu.action1.com |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|