| File name: | 5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e |
| Full analysis: | https://app.any.run/tasks/d9d7d355-0f1d-4a6a-9f2d-a479afa9e263 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2020, 04:09:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | 0C54AEFAC127381AD1C1AB7581EE794A |
| SHA1: | 8F86181298E6B0C170A74EB533B3DEA650E566C7 |
| SHA256: | 5B9B238B3C4E8C69E7EE3E02D4B2061BF2C816293FDD3C427231D17C177DFA5E |
| SSDEEP: | 768:enHKmM0qauedFQFtxTXKXAx6ZQgZOgRT77D1O4ymg:eqmMyTcTXfxhgZzTZOrmg |
MALICIOUS
Loads dropped or rewritten executable
- windanr.exe (PID: 2396)
- cmd.exe (PID: 3096)
- find.exe (PID: 1696)
- wmiprvse.exe (PID: 2604)
- find.exe (PID: 1928)
- cmd.exe (PID: 2272)
- tasklist.exe (PID: 2944)
- conhost.exe (PID: 2480)
- extrac32.exe (PID: 4064)
- cmd.exe (PID: 3324)
- svchost.exe (PID: 796)
- regsvr32.exe (PID: 3684)
- regsvr32.exe (PID: 1116)
- regsvr32.exe (PID: 3108)
- regsvr32.exe (PID: 3992)
- findstr.exe (PID: 3388)
- findstr.exe (PID: 3196)
- findstr.exe (PID: 2228)
- 5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e.exe (PID: 1516)
- reg.exe (PID: 3492)
- regsvr32.exe (PID: 2488)
- regsvr32.exe (PID: 2936)
- regsvr32.exe (PID: 3552)
- explorer.exe (PID: 372)
- svchost.exe (PID: 824)
- svchost.exe (PID: 756)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 3096)
Application was dropped or rewritten from another process
- extrac32.exe (PID: 4064)
- conhost.exe (PID: 2480)
- find.exe (PID: 1928)
- regsvr32.exe (PID: 3108)
- find.exe (PID: 1696)
- findstr.exe (PID: 3196)
- findstr.exe (PID: 3388)
- regsvr32.exe (PID: 2488)
- reg.exe (PID: 3492)
- regsvr32.exe (PID: 1116)
- regsvr32.exe (PID: 3684)
- regsvr32.exe (PID: 3992)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 2272)
- findstr.exe (PID: 2228)
- regsvr32.exe (PID: 3552)
- svchost.exe (PID: 756)
- svchost.exe (PID: 796)
- svchost.exe (PID: 824)
- tasklist.exe (PID: 2944)
- windanr.exe (PID: 2396)
- regsvr32.exe (PID: 2936)
SUSPICIOUS
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3096)
Application launched itself
- cmd.exe (PID: 3096)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3096)
- 5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e.exe (PID: 1516)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3096)
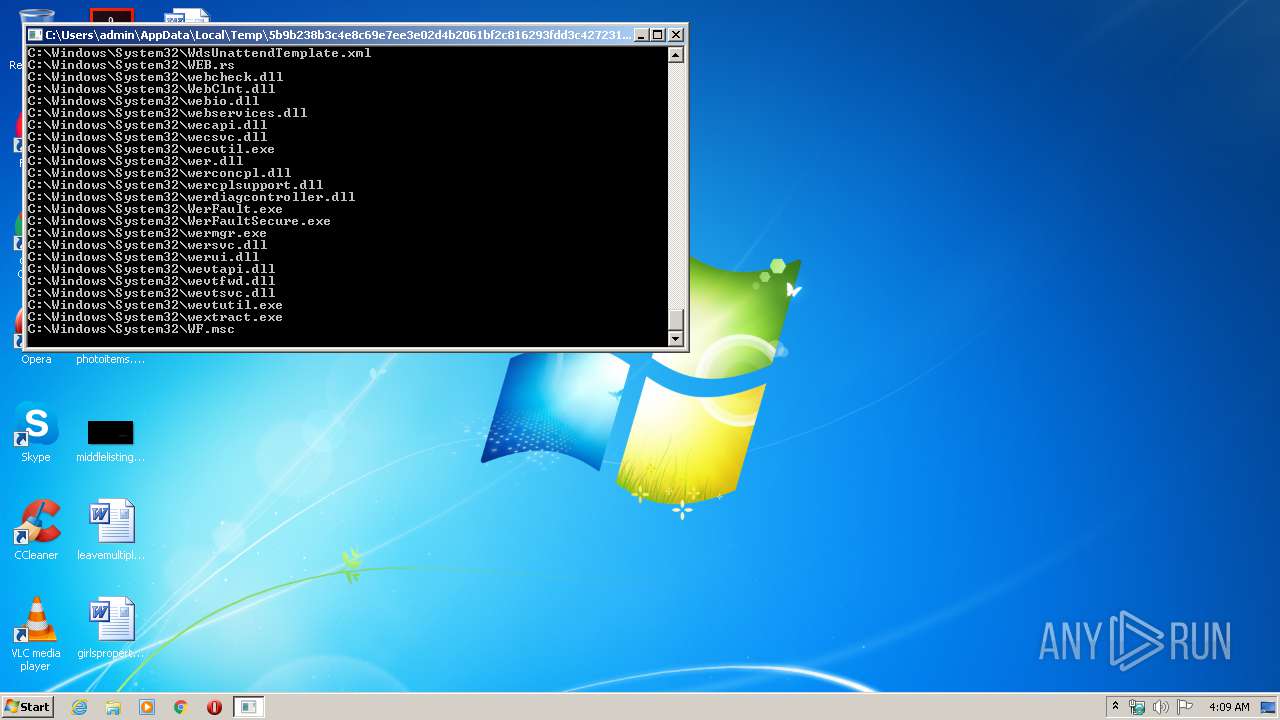
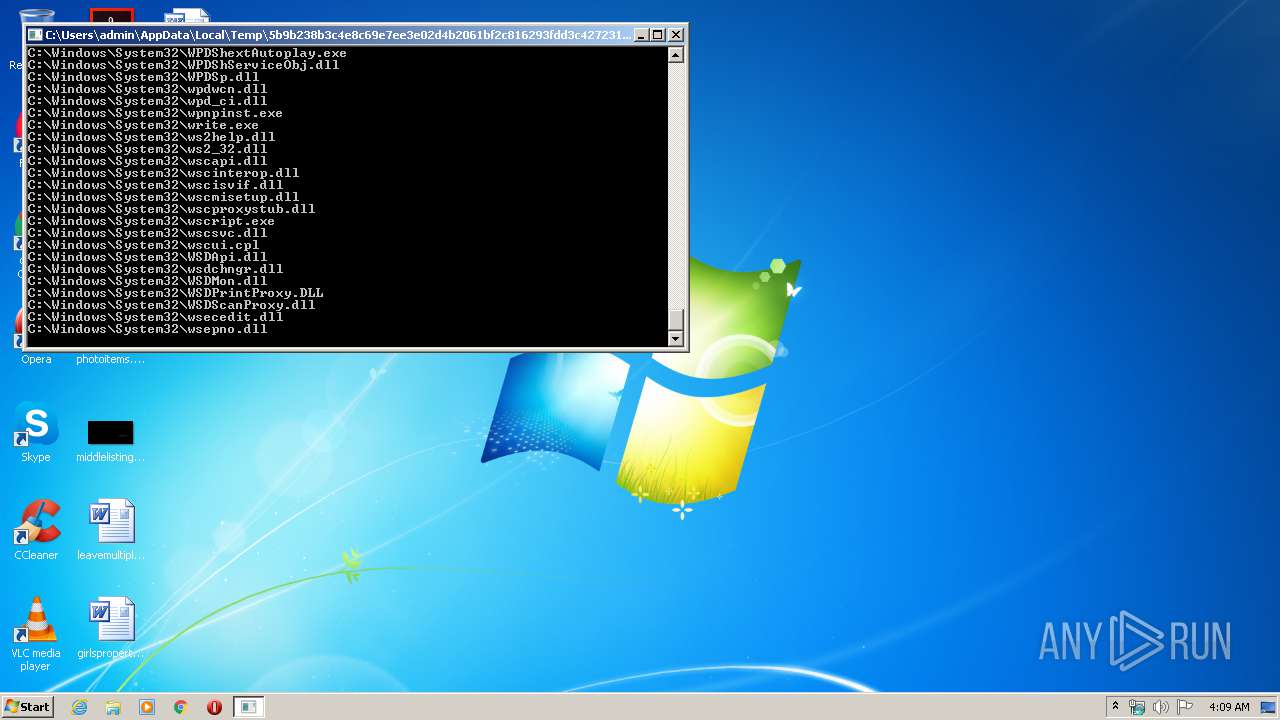
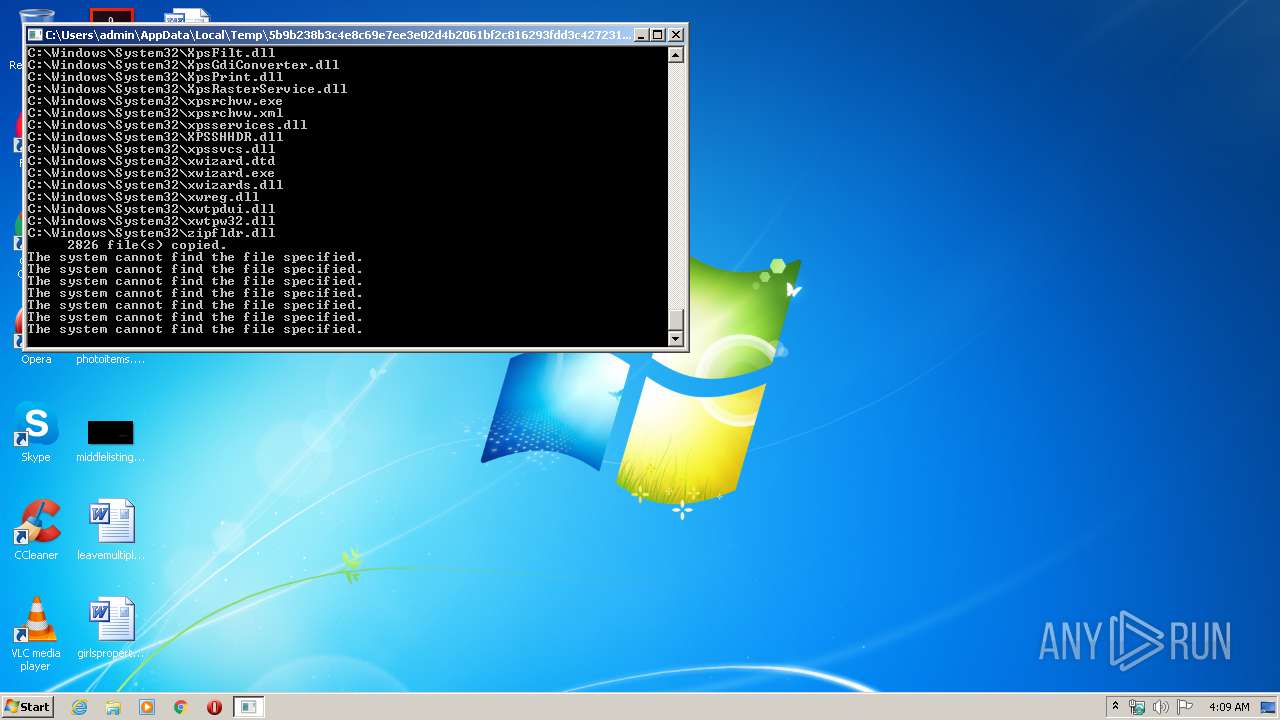
Creates executable files which already exist in Windows
- cmd.exe (PID: 3096)
Executable content was dropped or overwritten
- cmd.exe (PID: 3096)
INFO
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:03:25 14:17:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 33792 |
| InitializedDataSize: | 10240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe1e7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 25-Mar-2011 13:17:51 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Mar-2011 13:17:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.MPRESS1 | 0x00001000 | 0x0000D000 | 0x00005400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99215 |
.MPRESS2Q\x0d | 0x0000E000 | 0x00000D51 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.81133 |
.rsrc | 0x0000F000 | 0x00000370 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.40884 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 0 | 2680 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 0 | 9 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
Total processes
55
Monitored processes
26
Malicious processes
24
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | C:\Windows\System32\regsvr32.exe /s C:\Windows\System32\ | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\AppData\Local\Temp\5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e.exe" | C:\Users\admin\AppData\Local\Temp\5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1696 | find /i "SelfPlayer.exe" temp.txt | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | find /i "iexplore.exe" temp.txt | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | FINDSTR "IE.._H264.ocx" temp.txt | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | C:\Windows\system32\cmd.exe /c FINDSTR "HEM_OCX.._H264.ocx" temp.txt | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
140
Read events
110
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2396) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
2 580
Suspicious files
148
Text files
72
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\temp.txt | — | |
MD5:— | SHA256:— | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\aaclient.dll | executable | |
MD5:— | SHA256:— | |||
| 1516 | 5b9b238b3c4e8c69e7ee3e02d4b2061bf2c816293fdd3c427231d17c177dfa5e.exe | C:\Users\admin\AppData\Local\Temp\6A3B.tmp\Setup.bat | text | |
MD5:— | SHA256:— | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\acledit.dll | executable | |
MD5:76828928A893D595EF5CA2C53B2B48C0 | SHA256:7FC551E7874FE11563805D205630ADC2B88CB9B9FCC83B020A313108A5F3929A | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\12520850.cpx | text | |
MD5:D69AE057CD82D04EE7D311809ABEFB2A | SHA256:DF45B91D9BDD852F49CF043CBD2408C8E139643B413071FF2FA87BFB45940216 | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\acproxy.dll | executable | |
MD5:3A9FC5D24053769ED9B710B576DEEB8A | SHA256:F6409D4AB94399429266A926821EDB5AB3DF3D8F9FB99BD0675781A8637054C0 | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\ACCTRES.dll | executable | |
MD5:494E31F87662C486EF2F2048D599AC46 | SHA256:770FC0C01D7B705278282C7A010BA34EDF26ABD81AD04879E3383BC9F07C90AB | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\acppage.dll | executable | |
MD5:B57053CD59114D36952461EE638D3784 | SHA256:F5C54321A7A8119215E525CAD44B723DD9699A13F754669D29761833C3936575 | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\aclui.dll | executable | |
MD5:DAB5808E0C26740577AE67878A87136E | SHA256:780F077D9818776CE53055A06E9ABB578816C15442FBCF21052E6784BC6AEB1A | |||
| 3096 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IEPlugin\actxprxy.dll | executable | |
MD5:D2958325C1AE1AE37A83334C6229E3BC | SHA256:D8263CB39A25447442B75A8D8E8111DF671D645DA90A33865C089DEDA9706904 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report