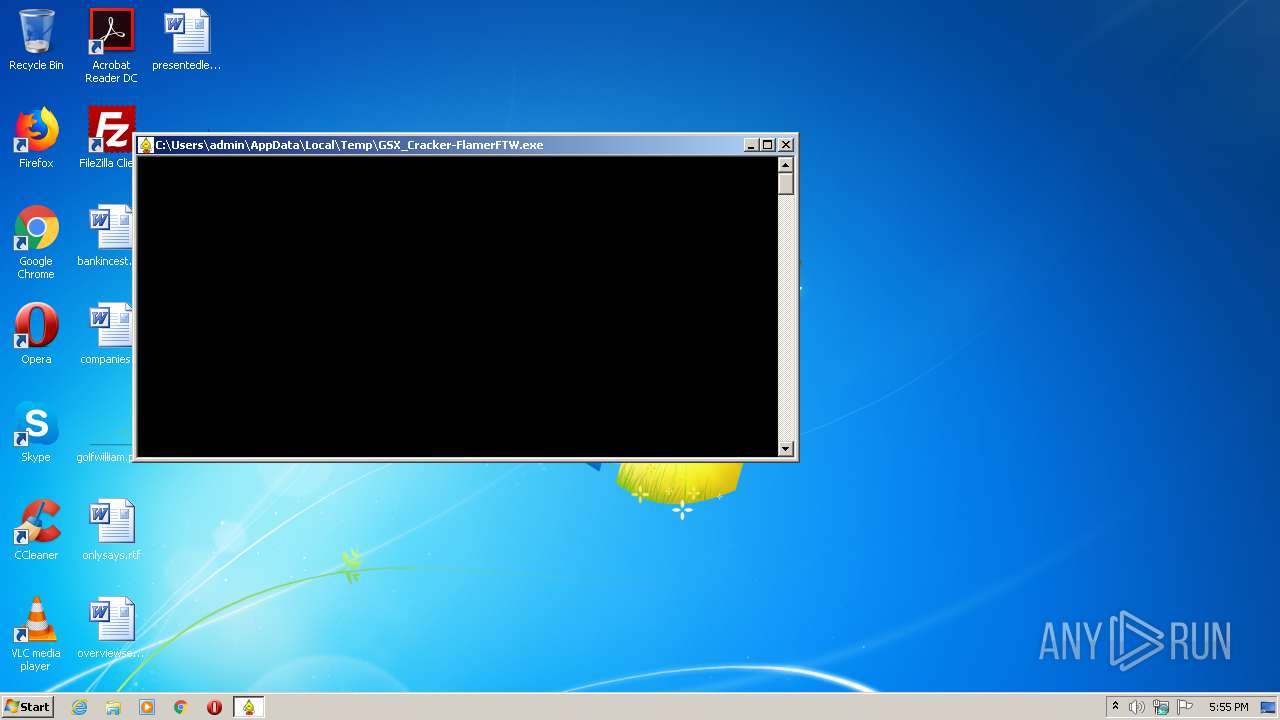
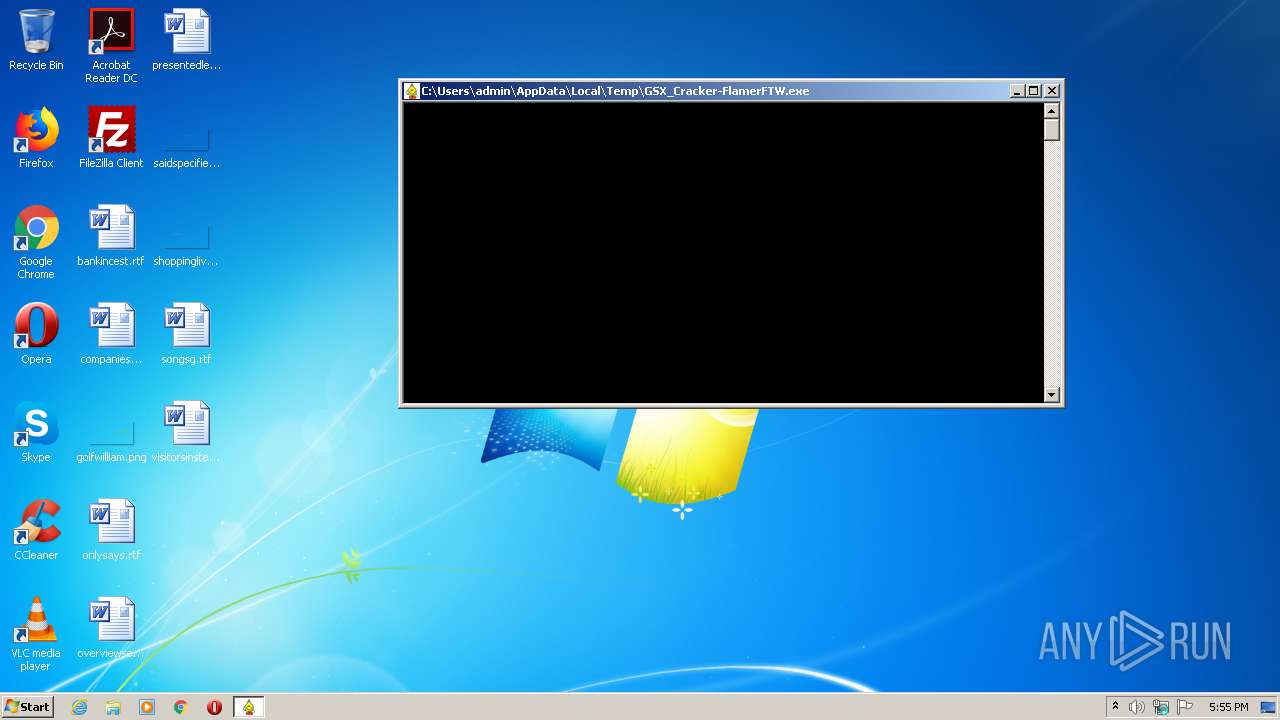
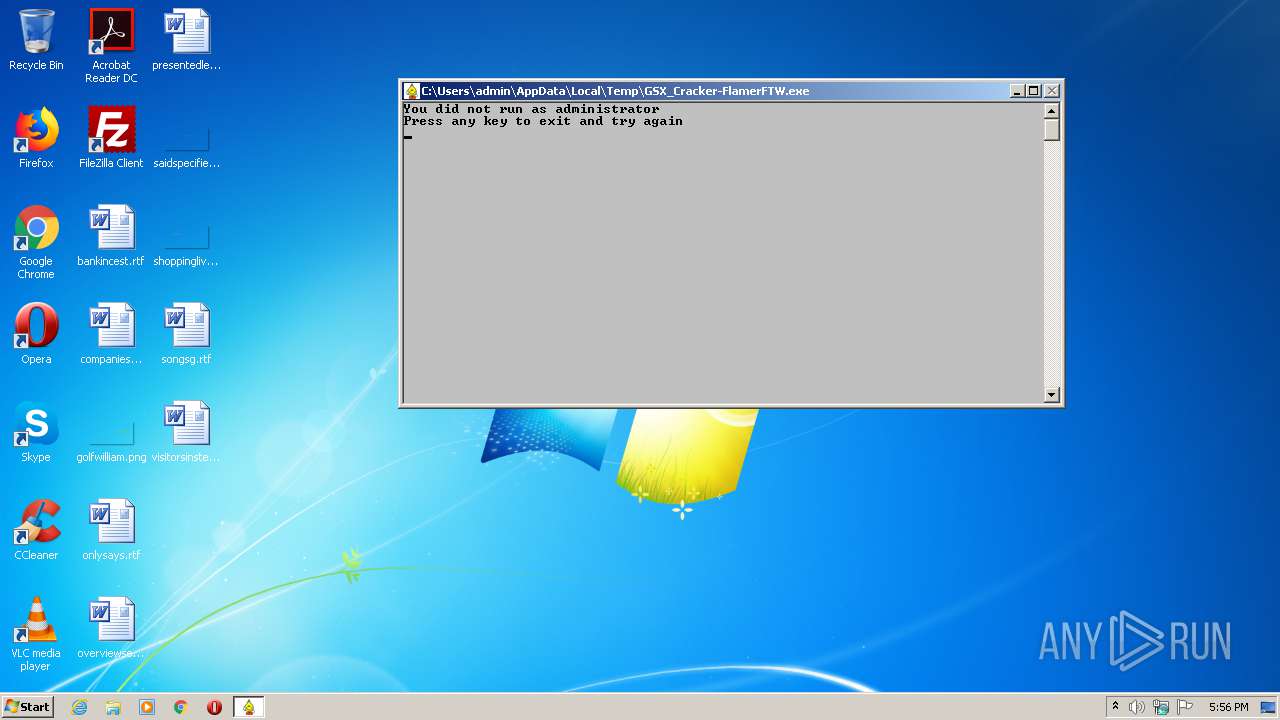
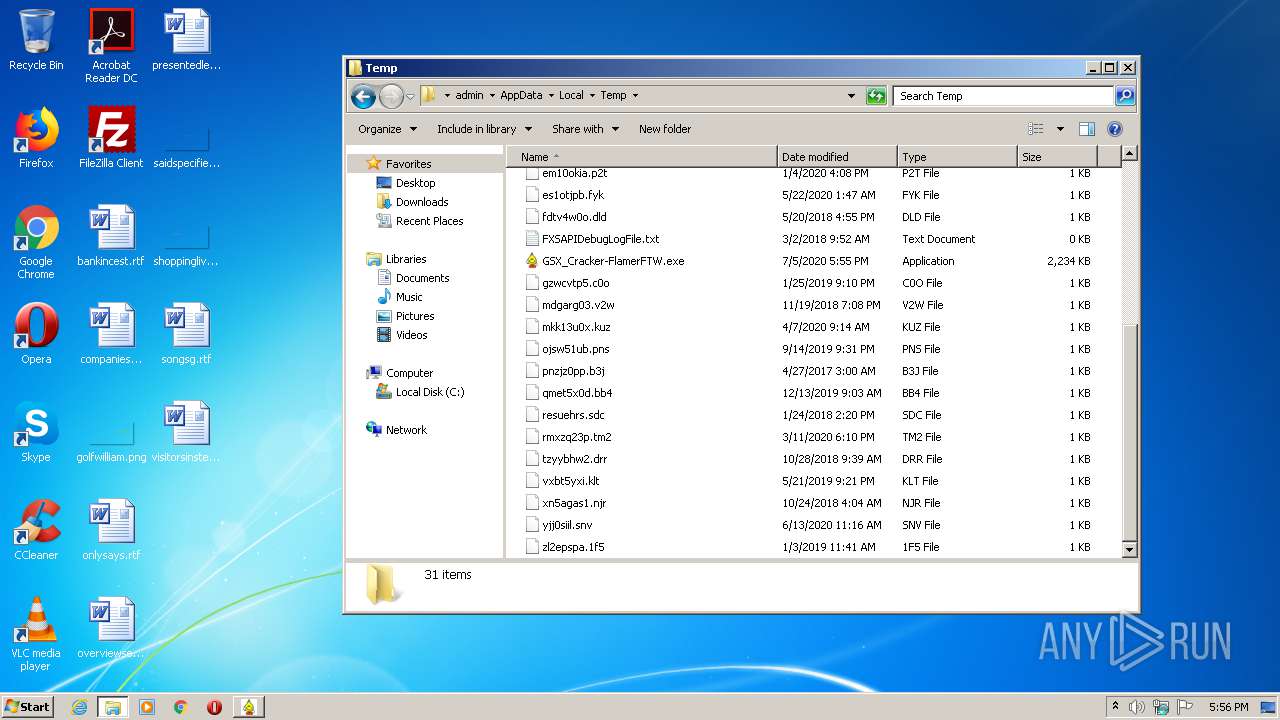
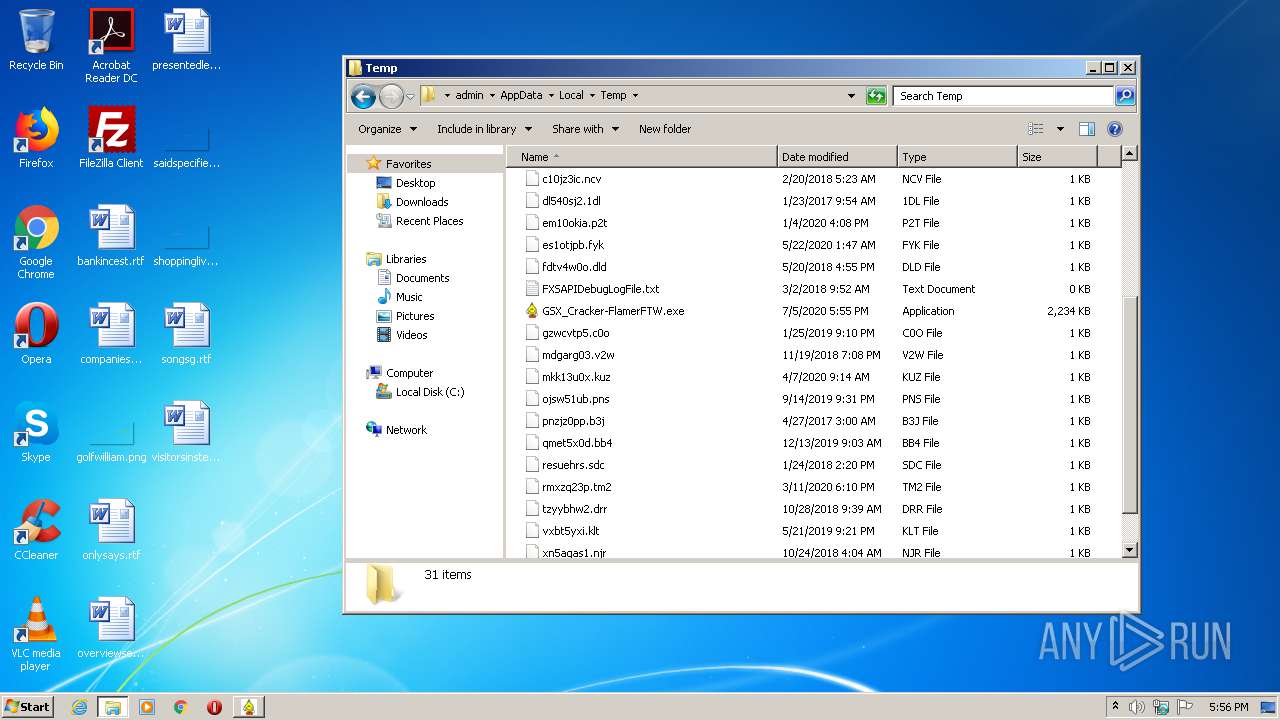
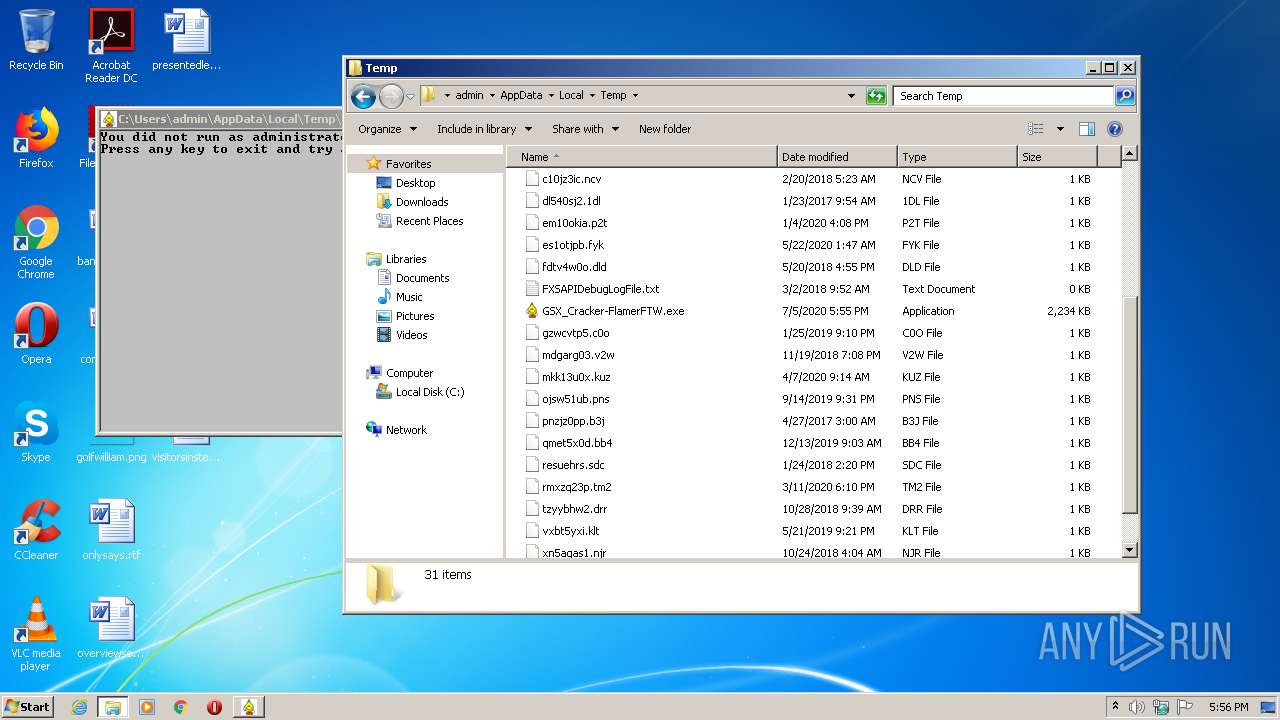
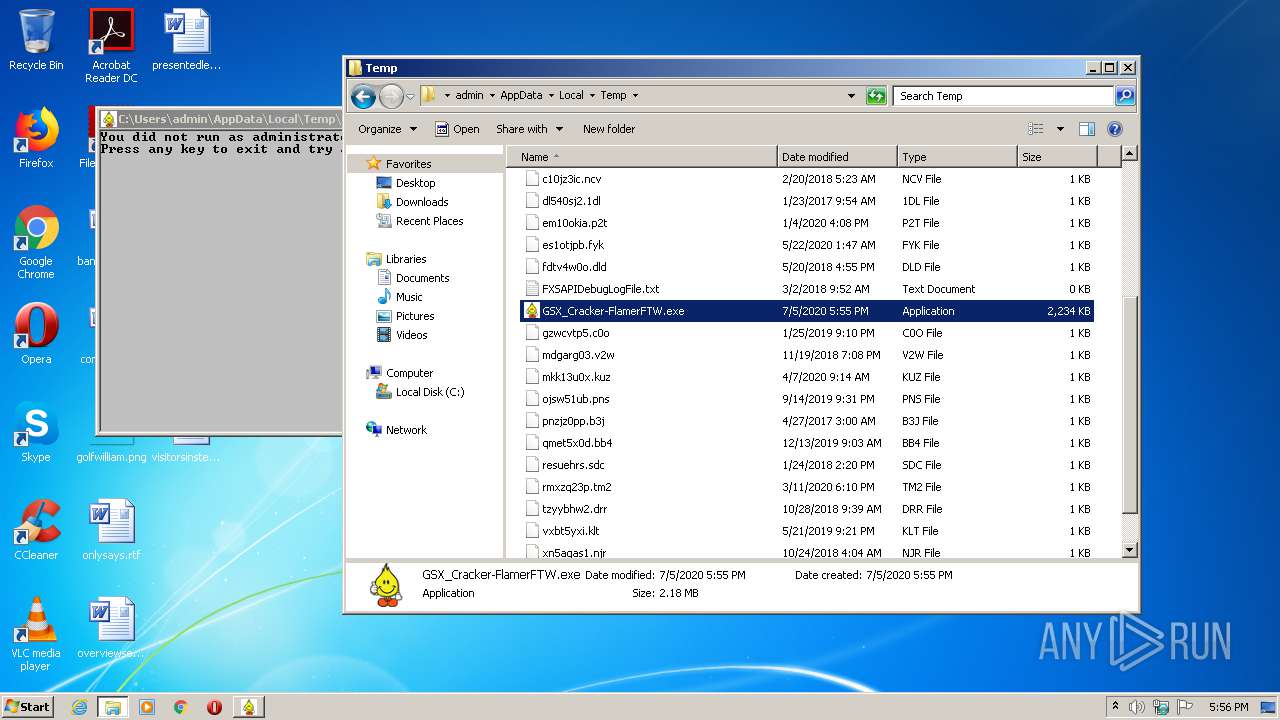
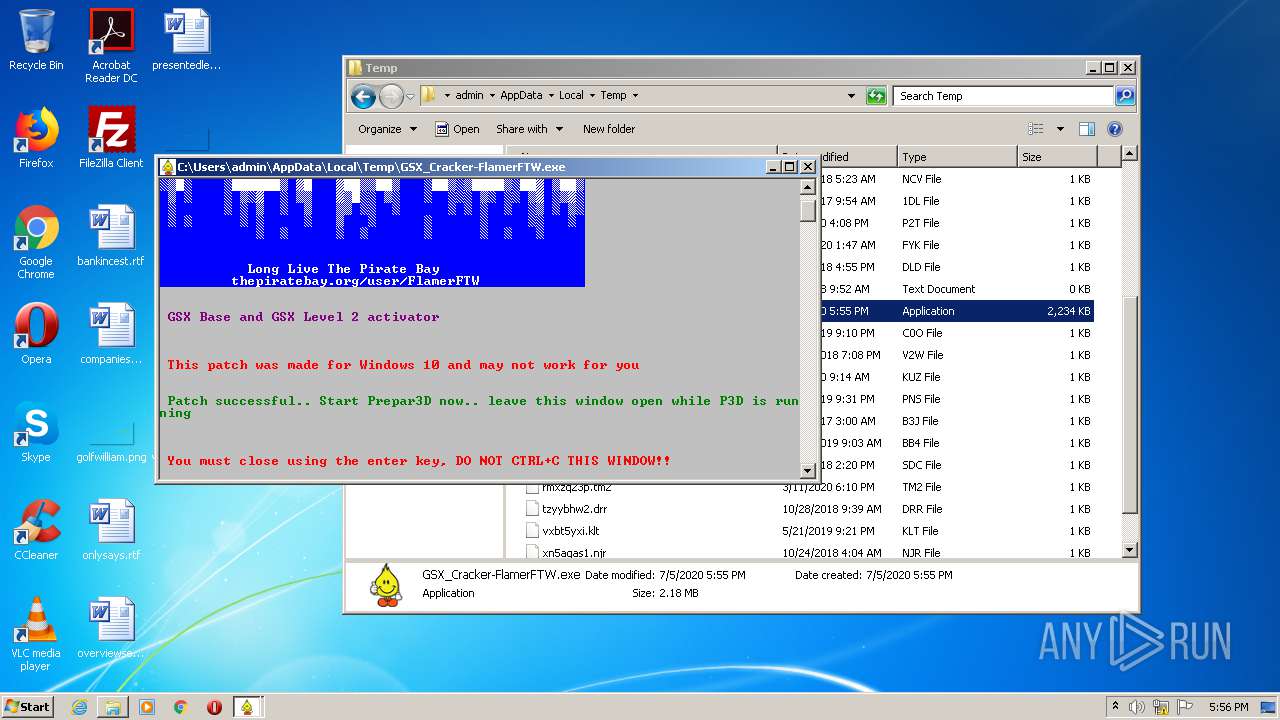
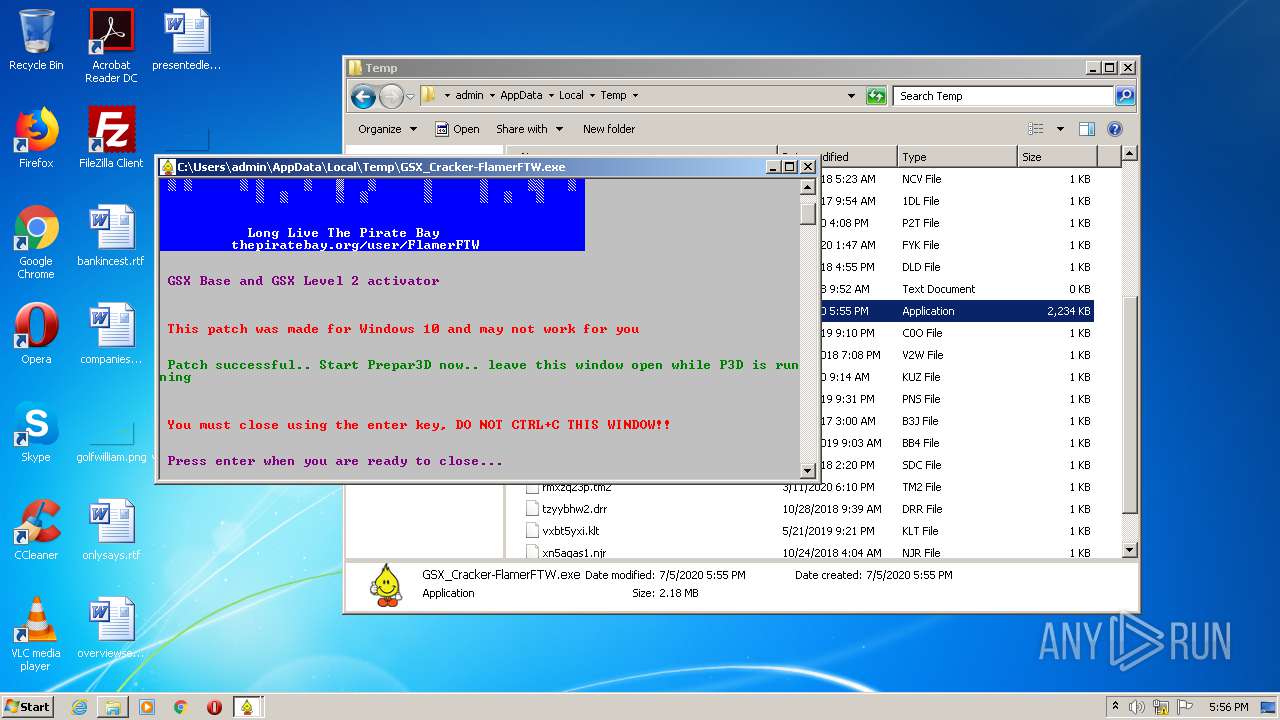
| File name: | GSX_Cracker-FlamerFTW.exe |
| Full analysis: | https://app.any.run/tasks/60f2a572-d2ba-4b23-a4a5-448f2f186daa |
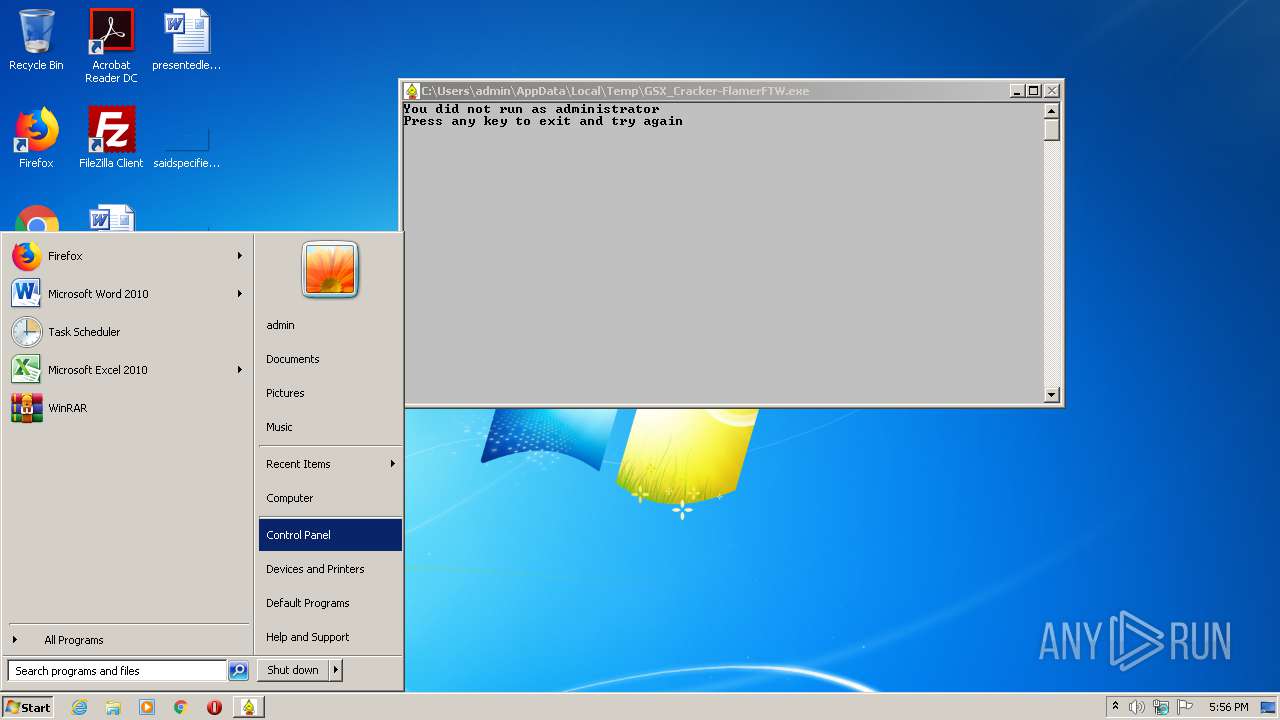
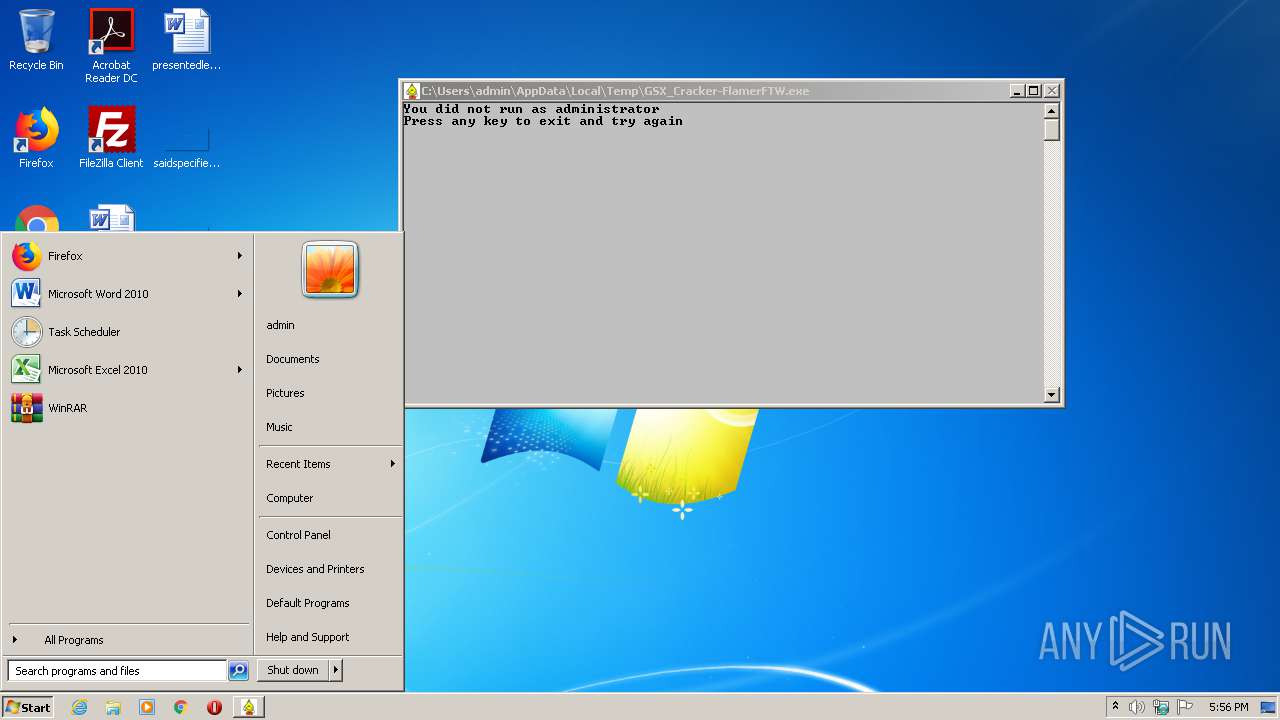
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2020, 16:55:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | F8DCDC938A80AFA2915E4309C4867E37 |
| SHA1: | 5B26E8E7F7FFC0236CA72E82896B5253C0F97FA5 |
| SHA256: | 5B91C3779D20FFB4627AE4C6515161BAECAFA5AA836982AC42786BDBF647F751 |
| SSDEEP: | 49152:1ODL3LhZpABVTydmR+h7wT/mtd9+sxcIQHRdF1wCy:1qL3tZu8dmS7wT/mYsiZTFny |
MALICIOUS
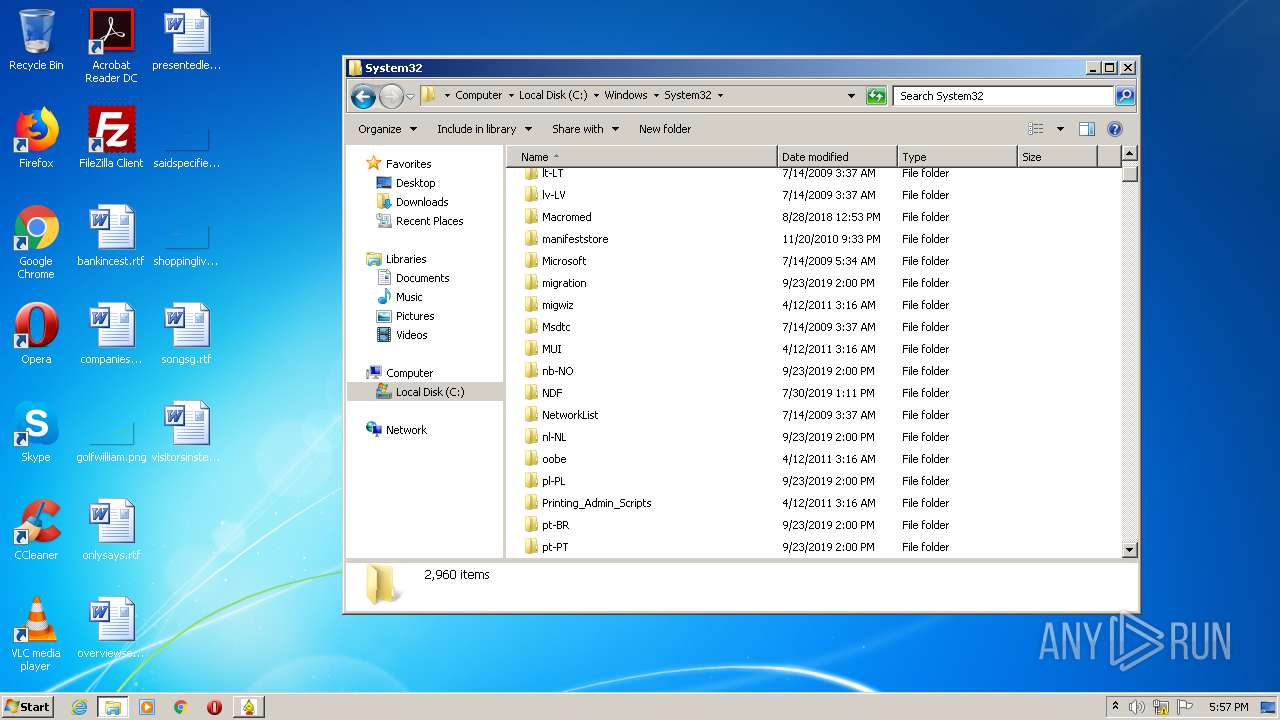
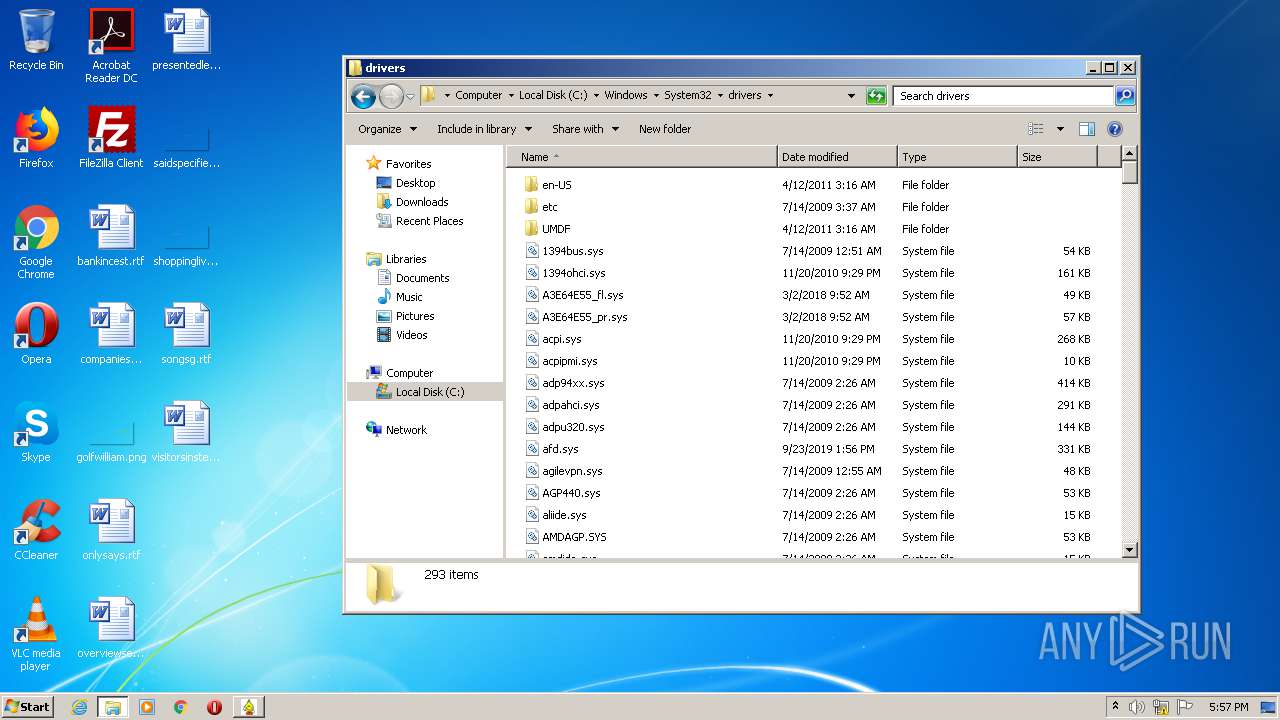
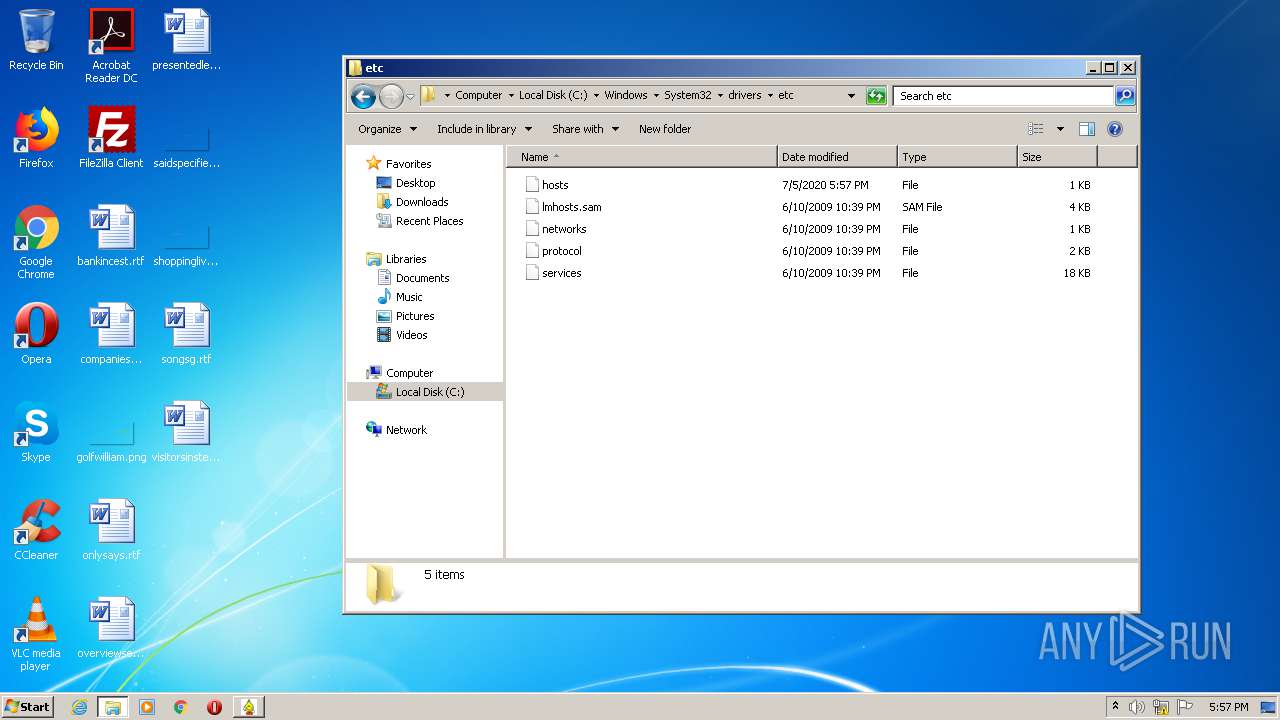
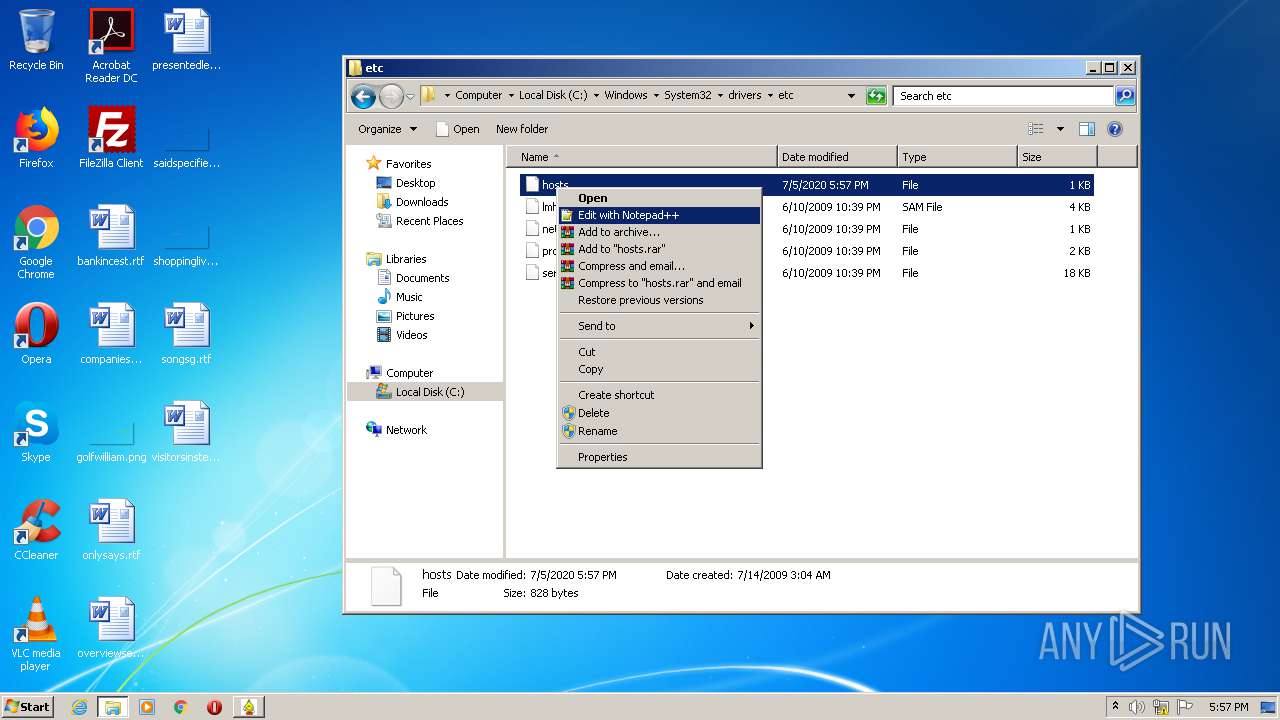
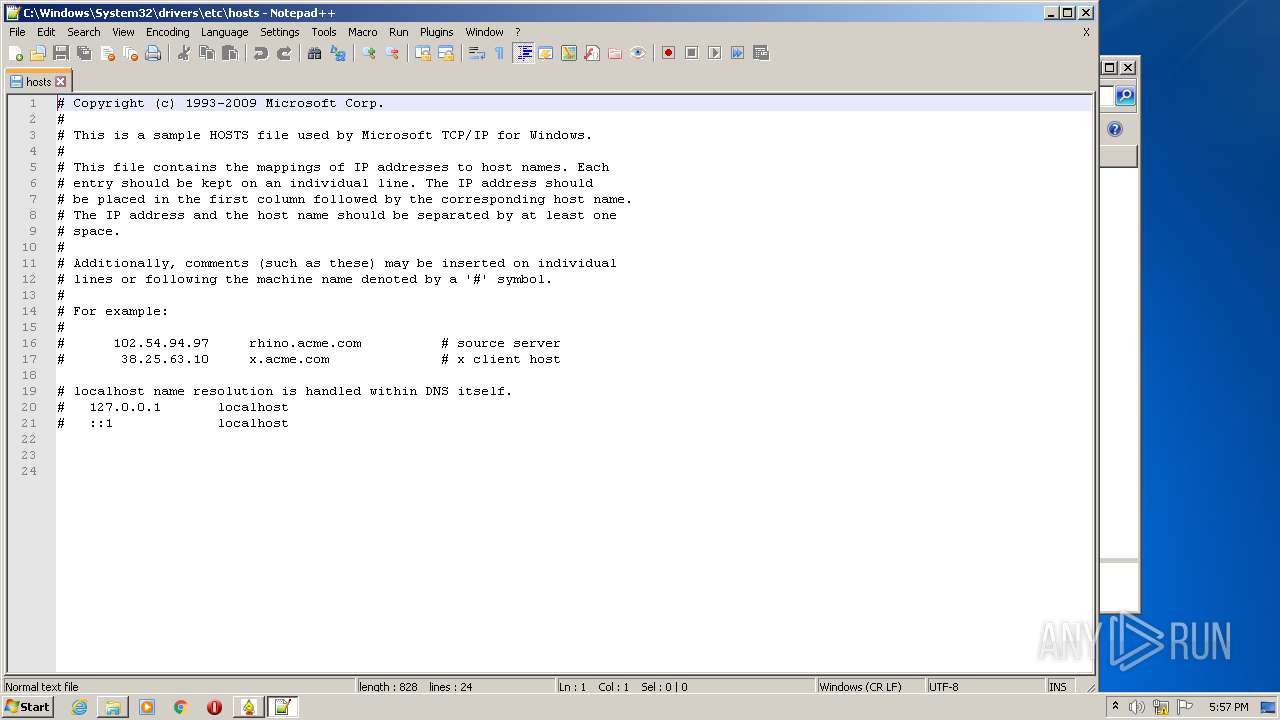
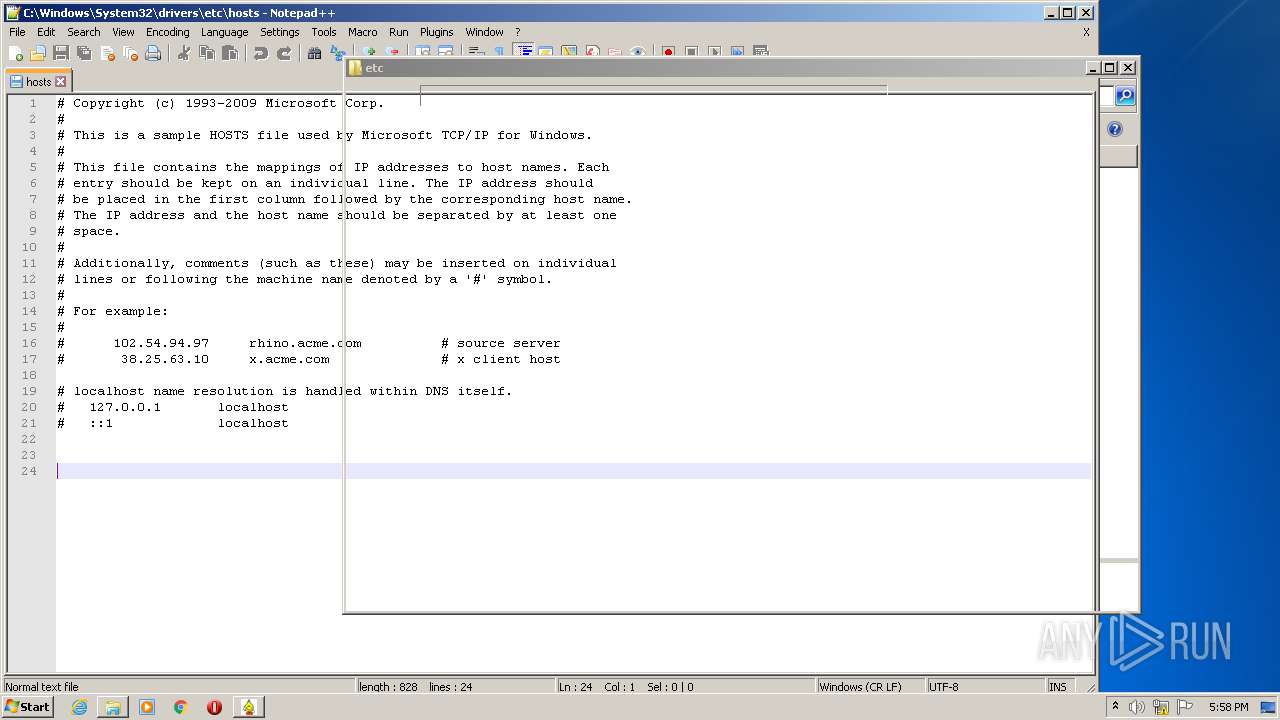
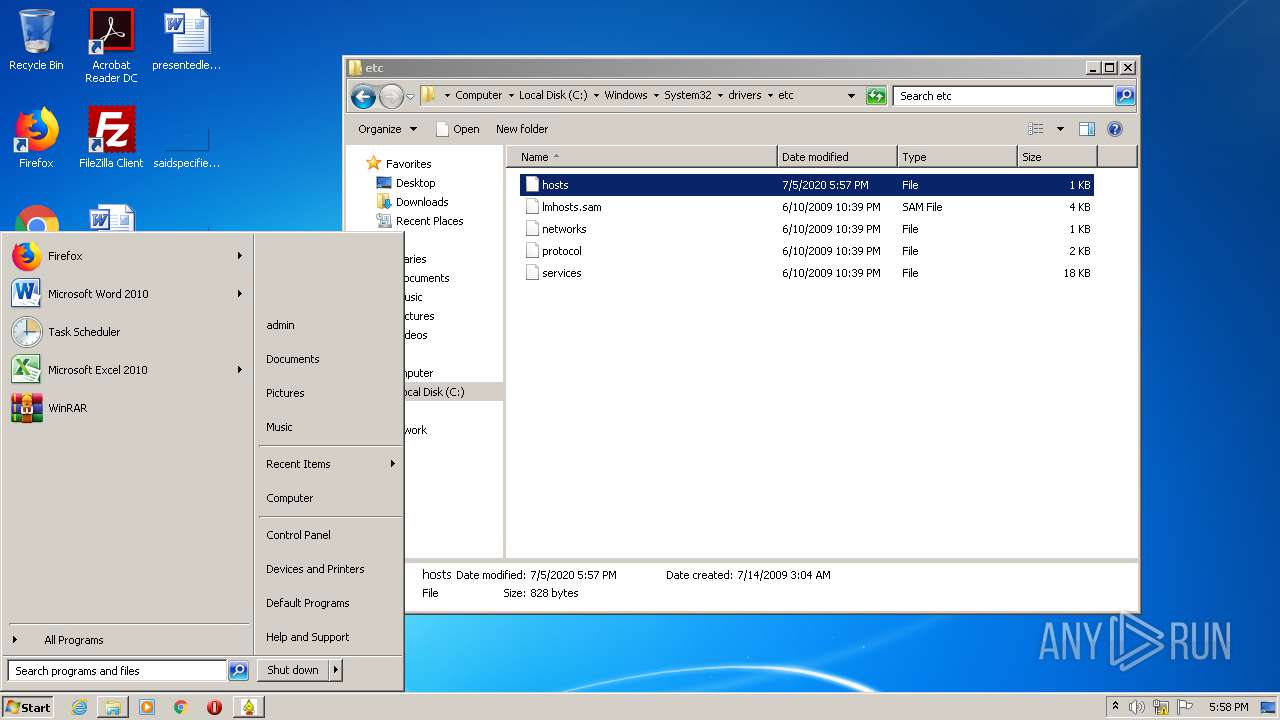
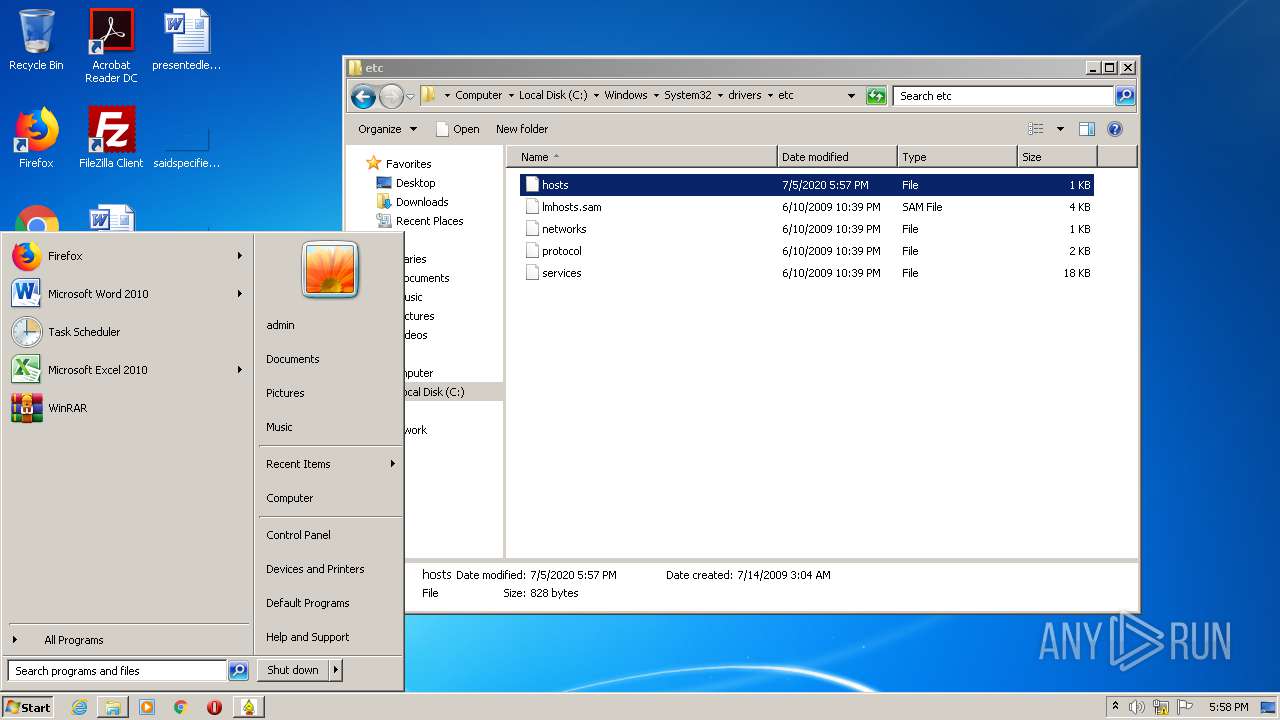
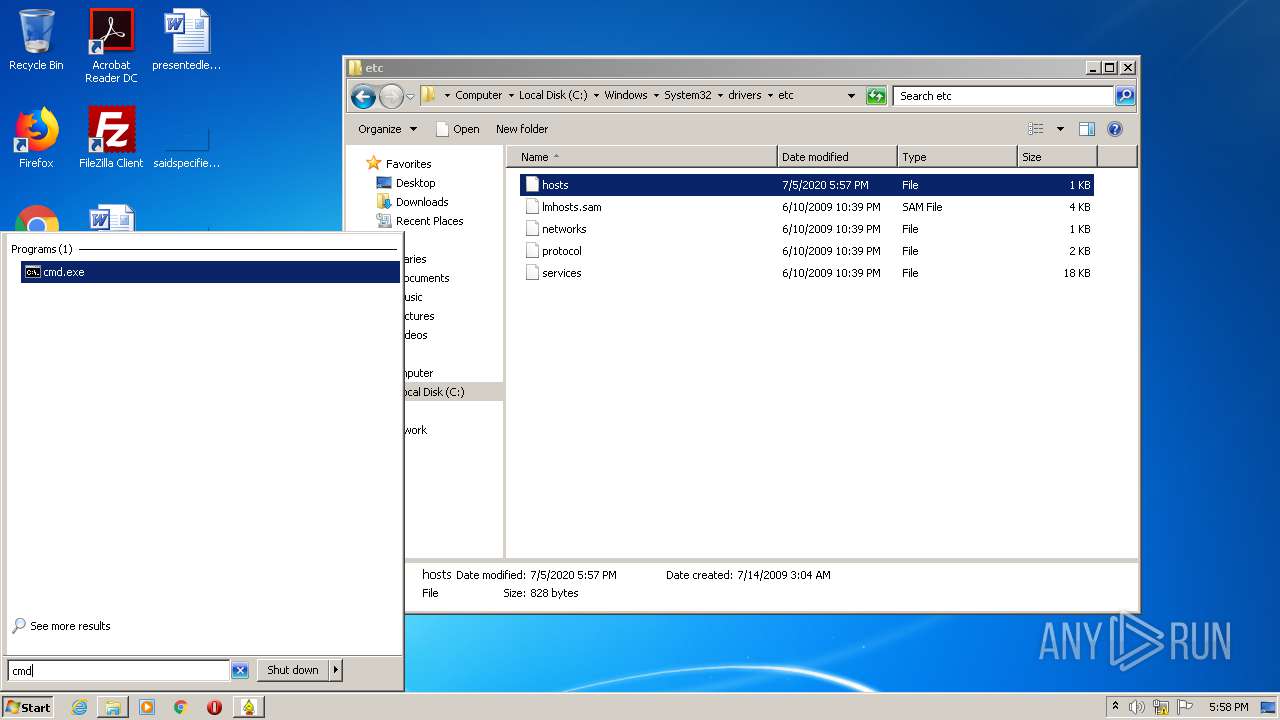
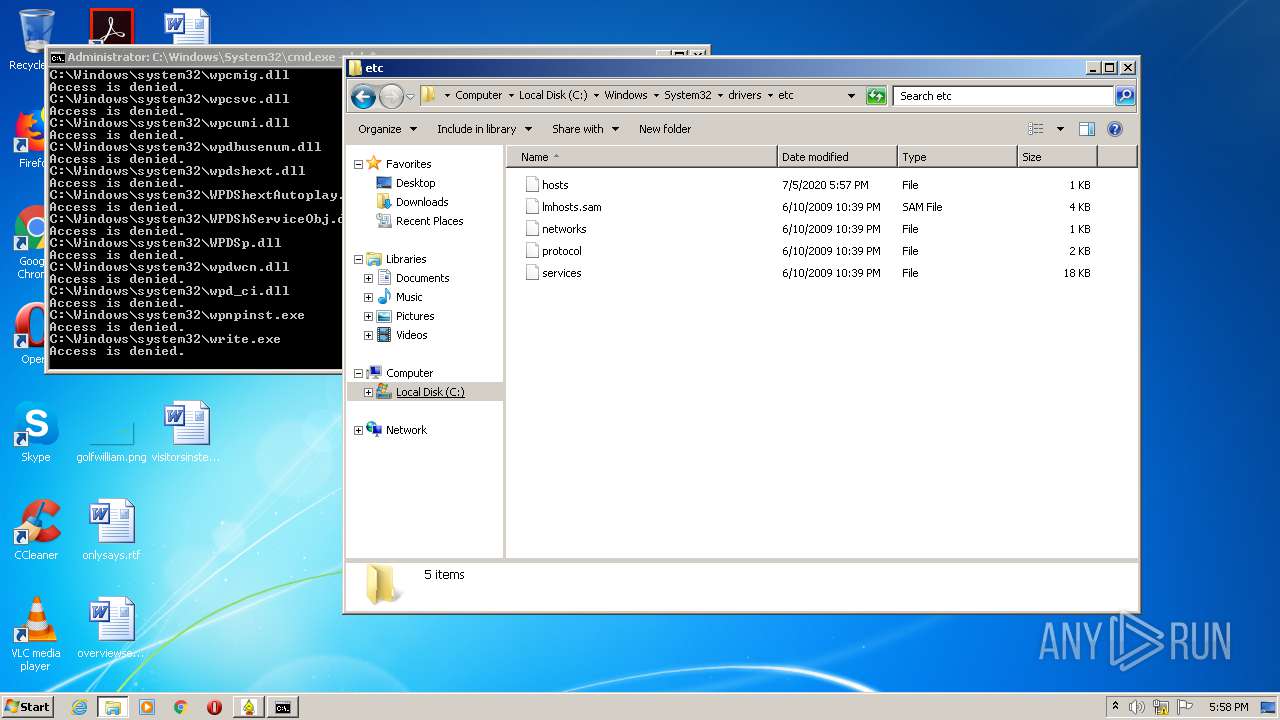
Writes to the hosts file
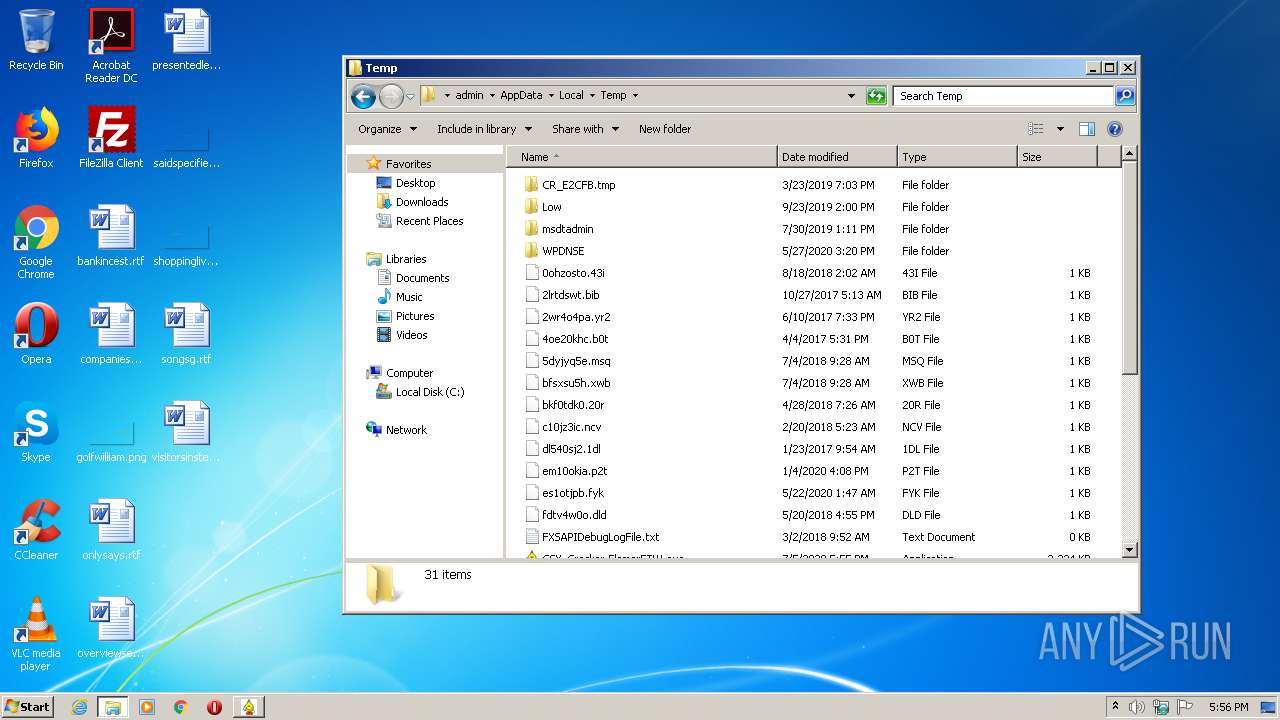
- GSX_Cracker-FlamerFTW.exe (PID: 2720)
Tries to delete the host file
- DllHost.exe (PID: 2684)
SUSPICIOUS
Reads CPU info
- GSX_Cracker-FlamerFTW.exe (PID: 2720)
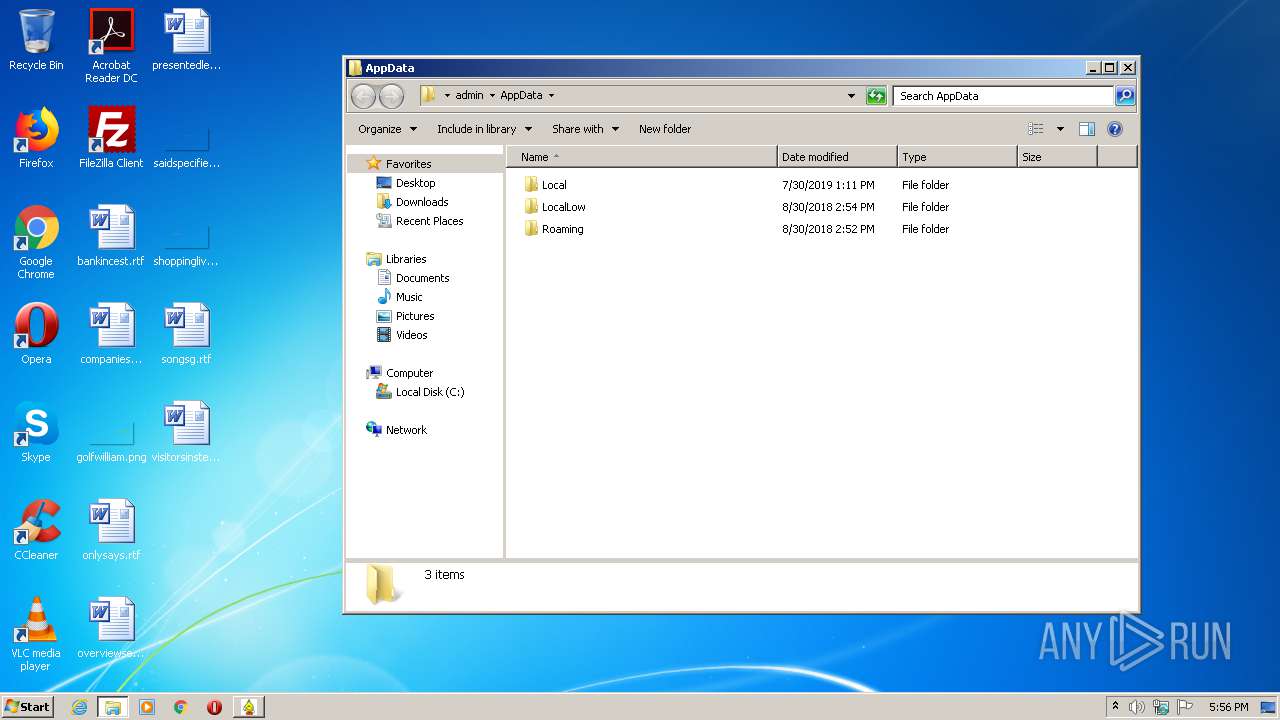
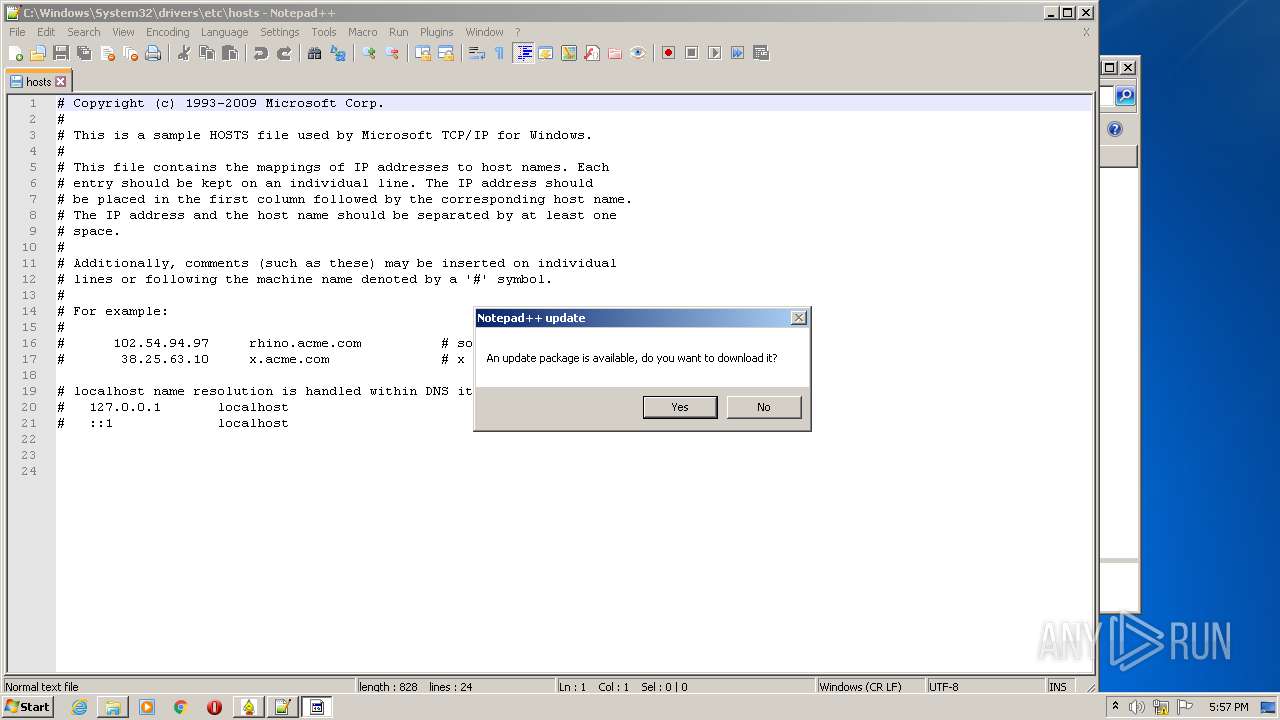
Creates files in the user directory
- notepad++.exe (PID: 552)
Executed via COM
- DllHost.exe (PID: 2684)
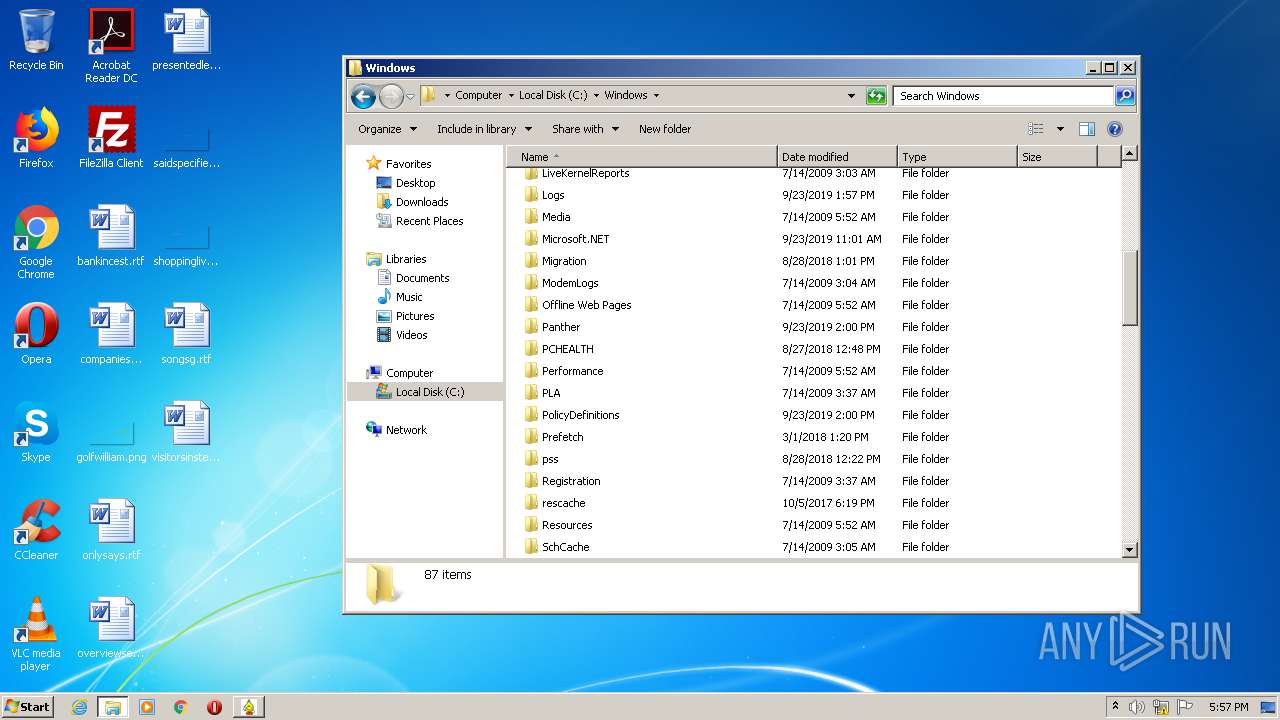
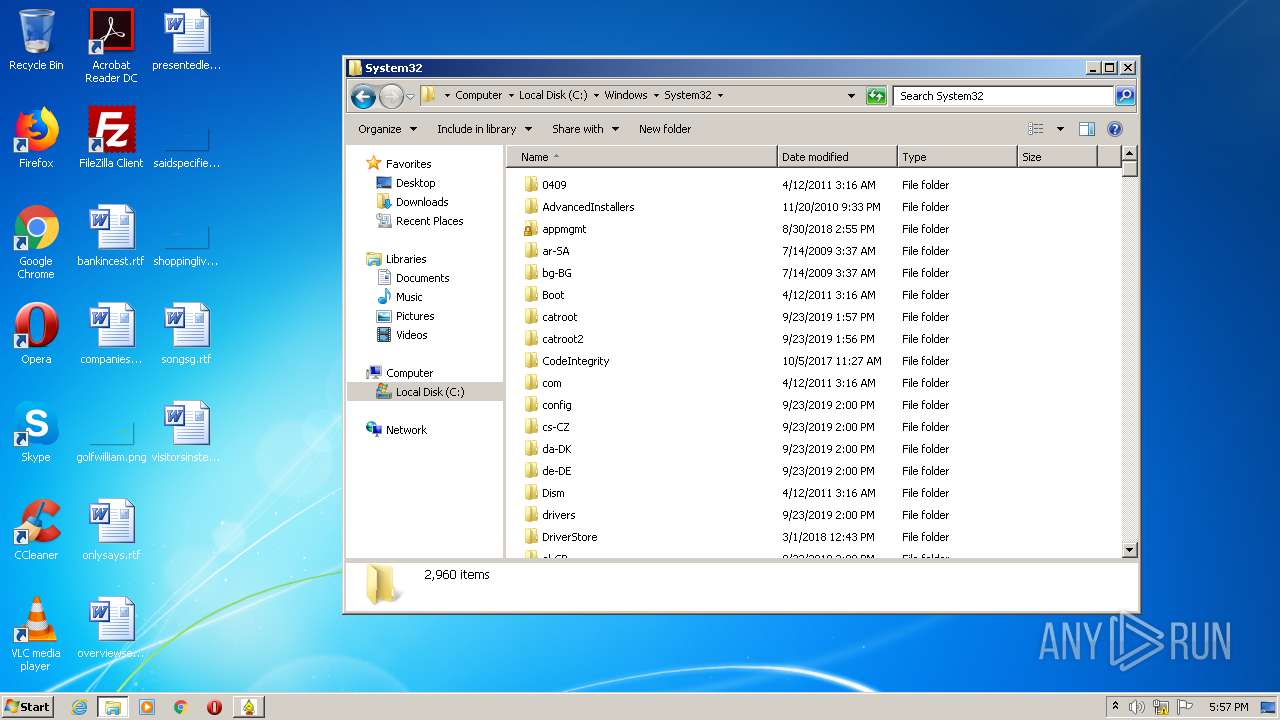
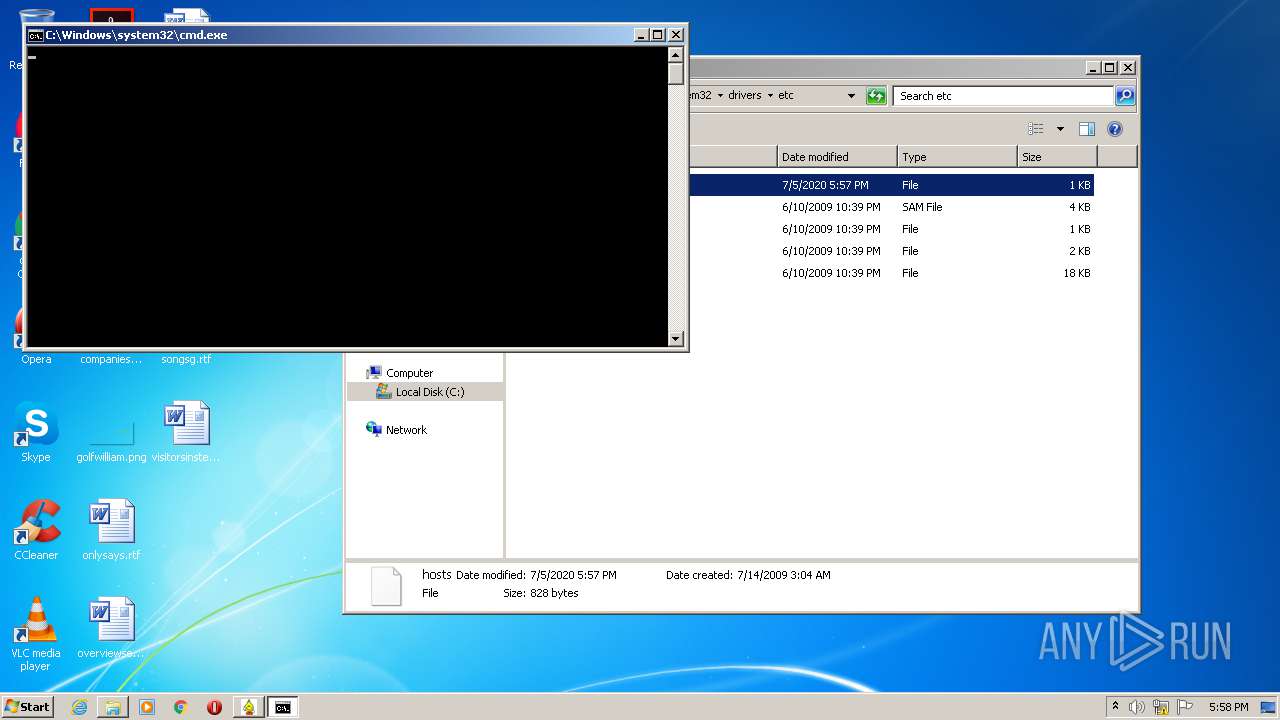
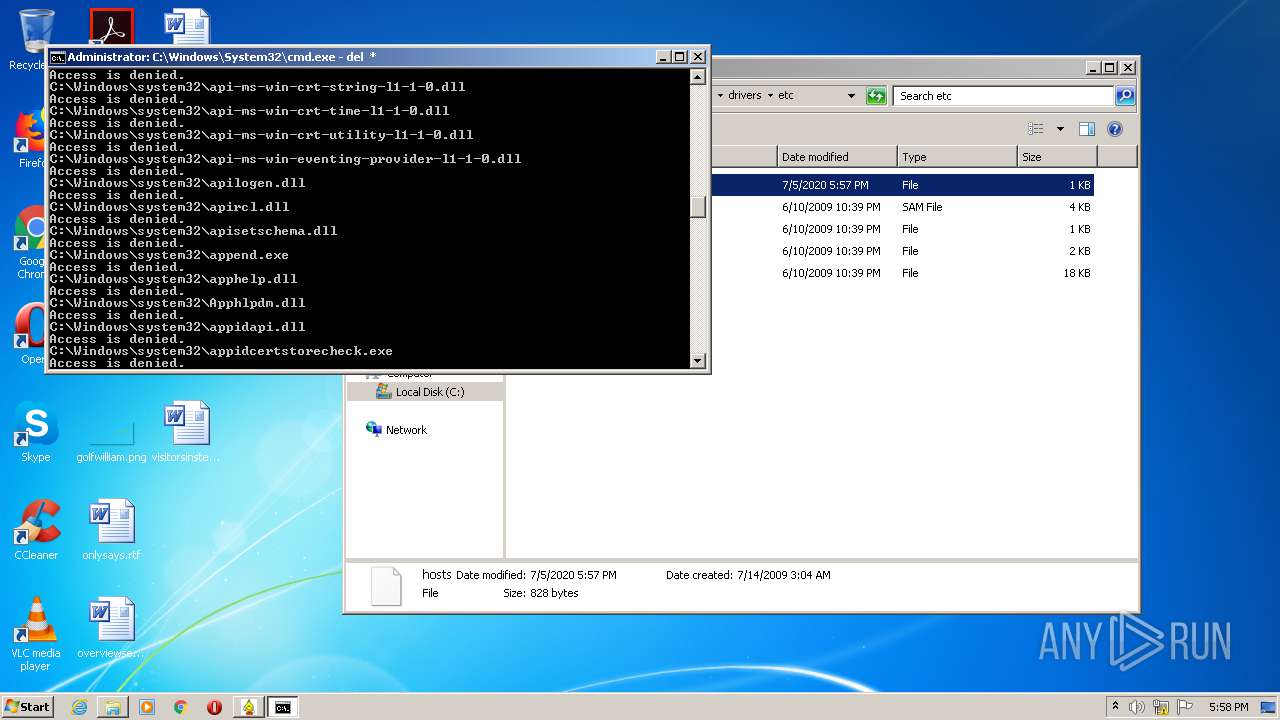
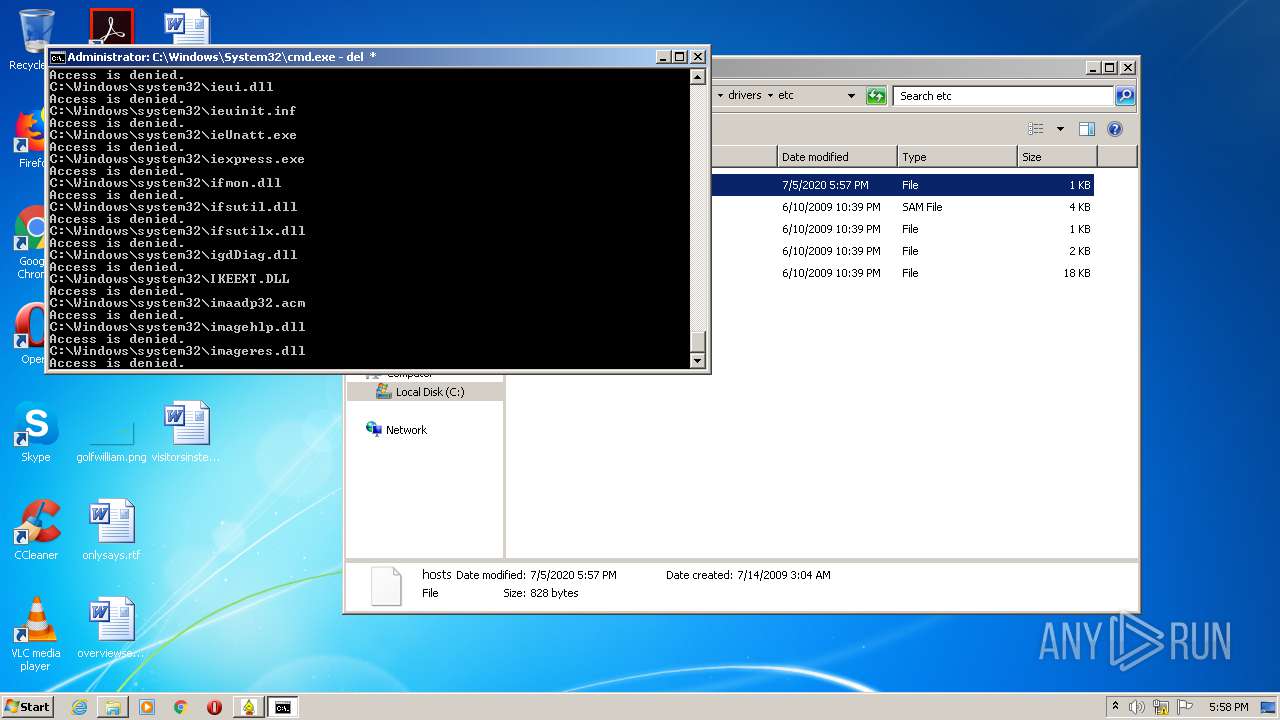
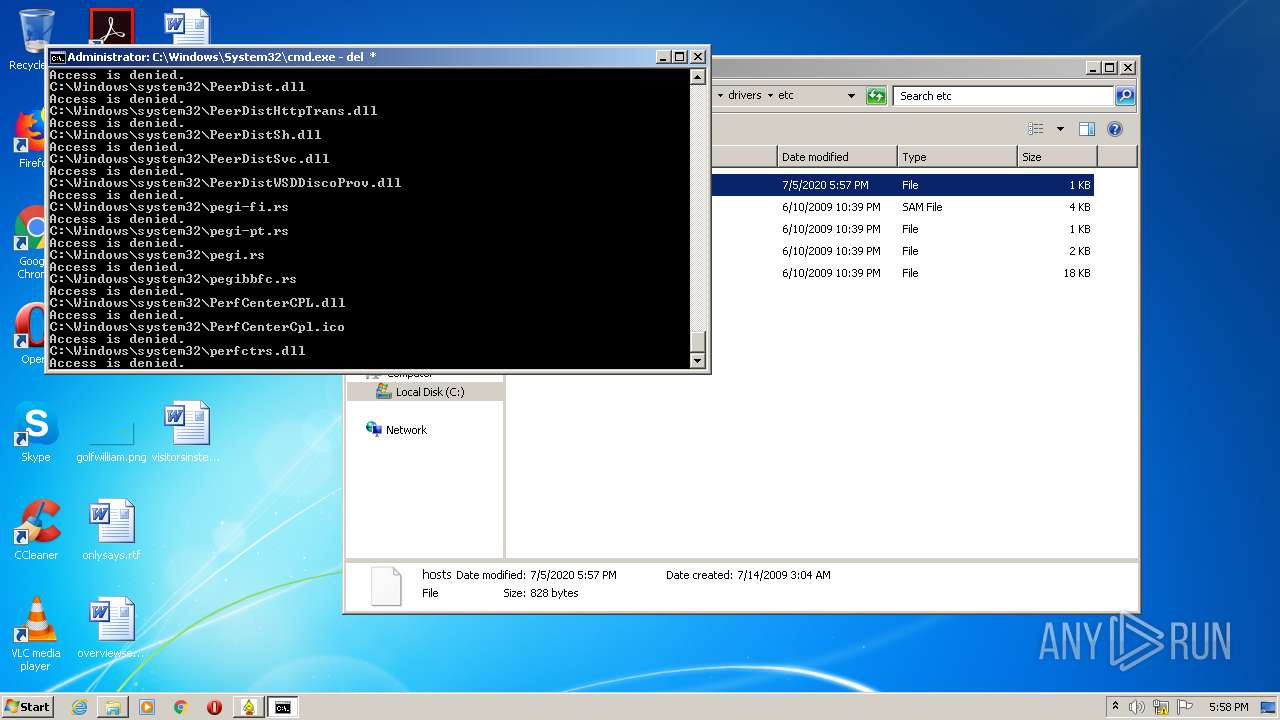
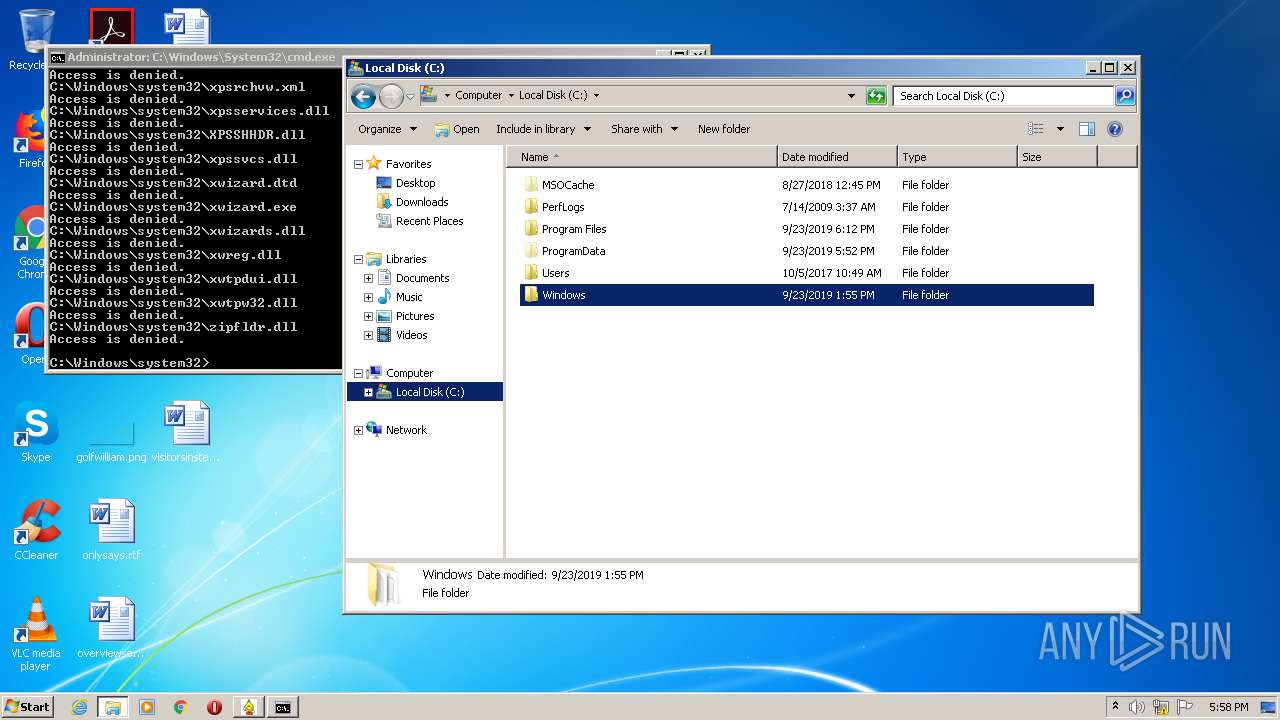
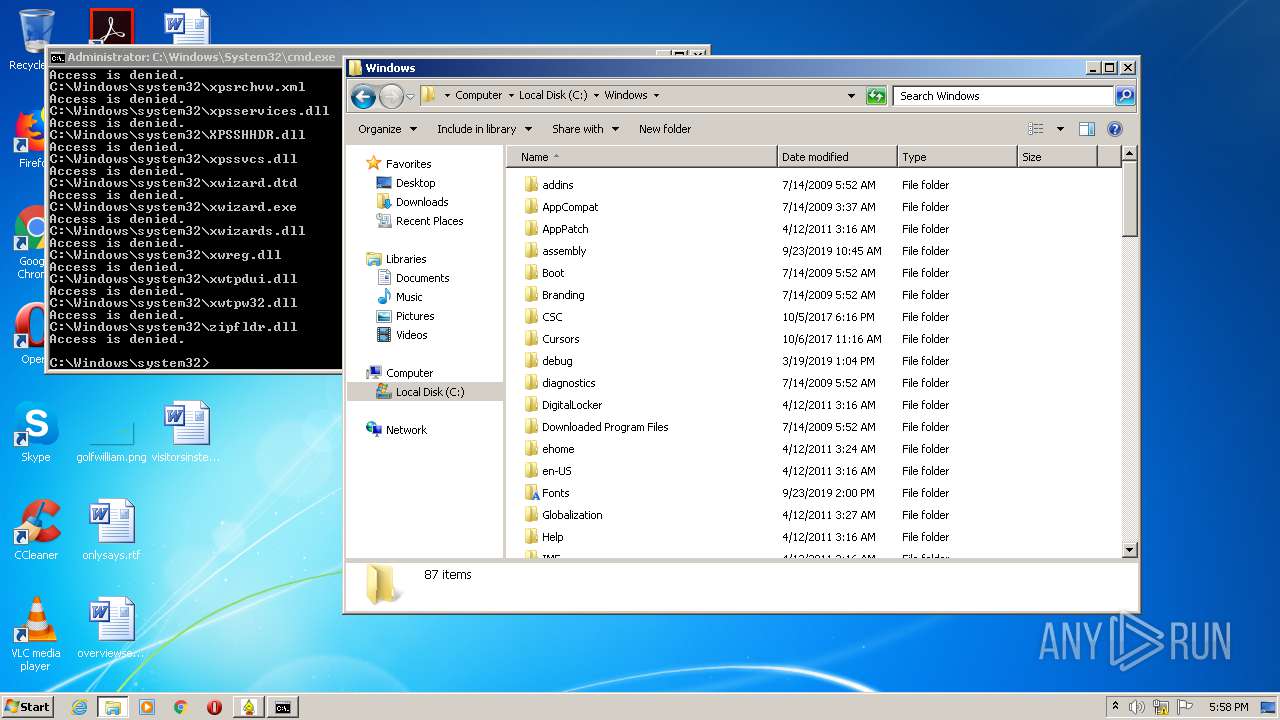
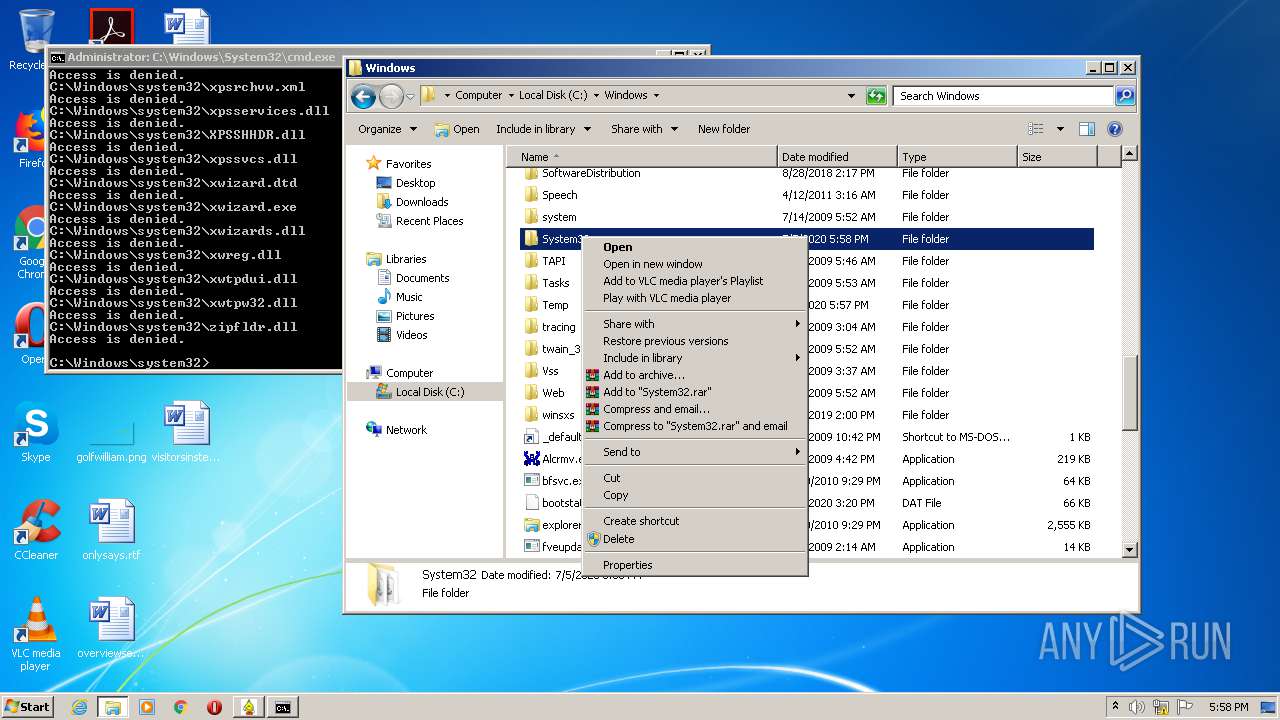
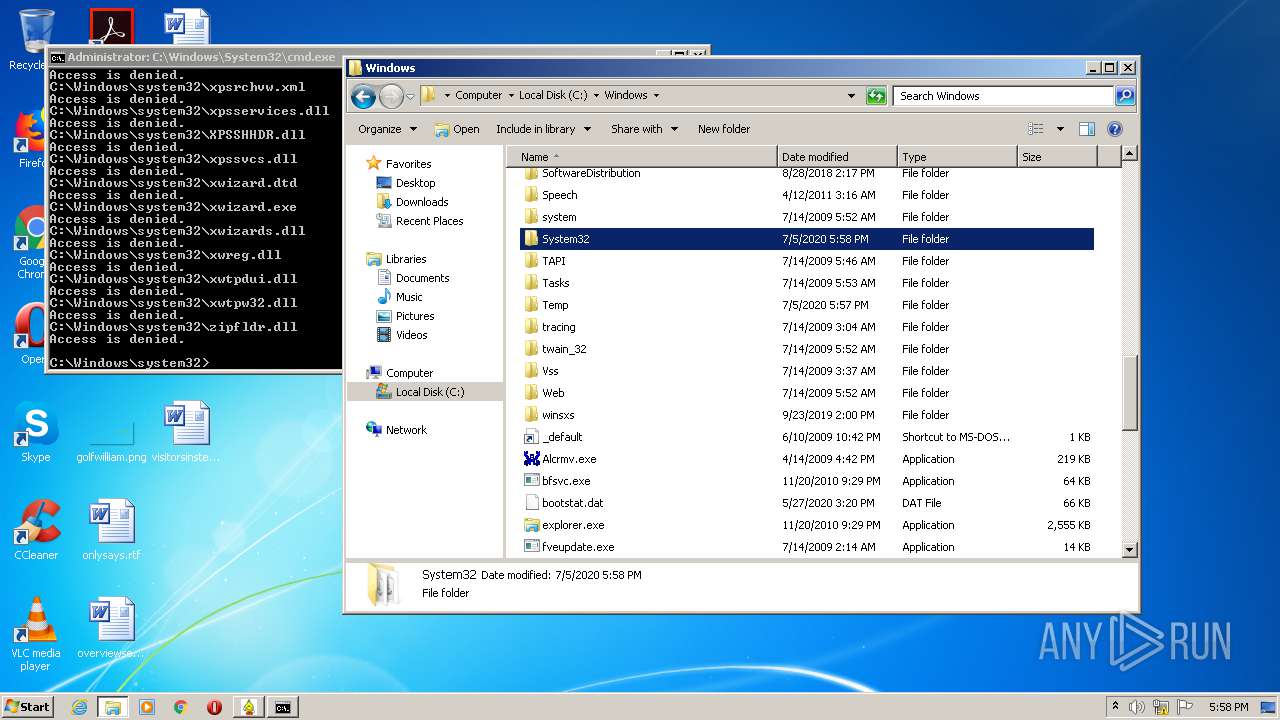
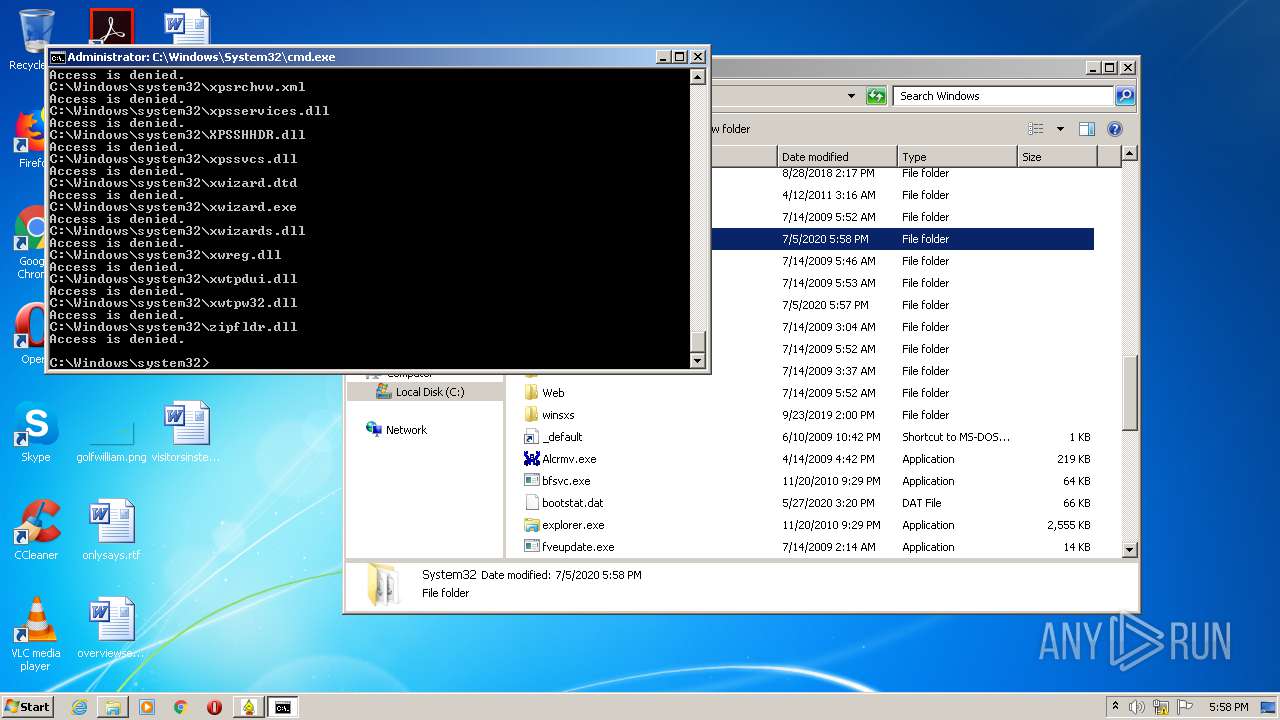
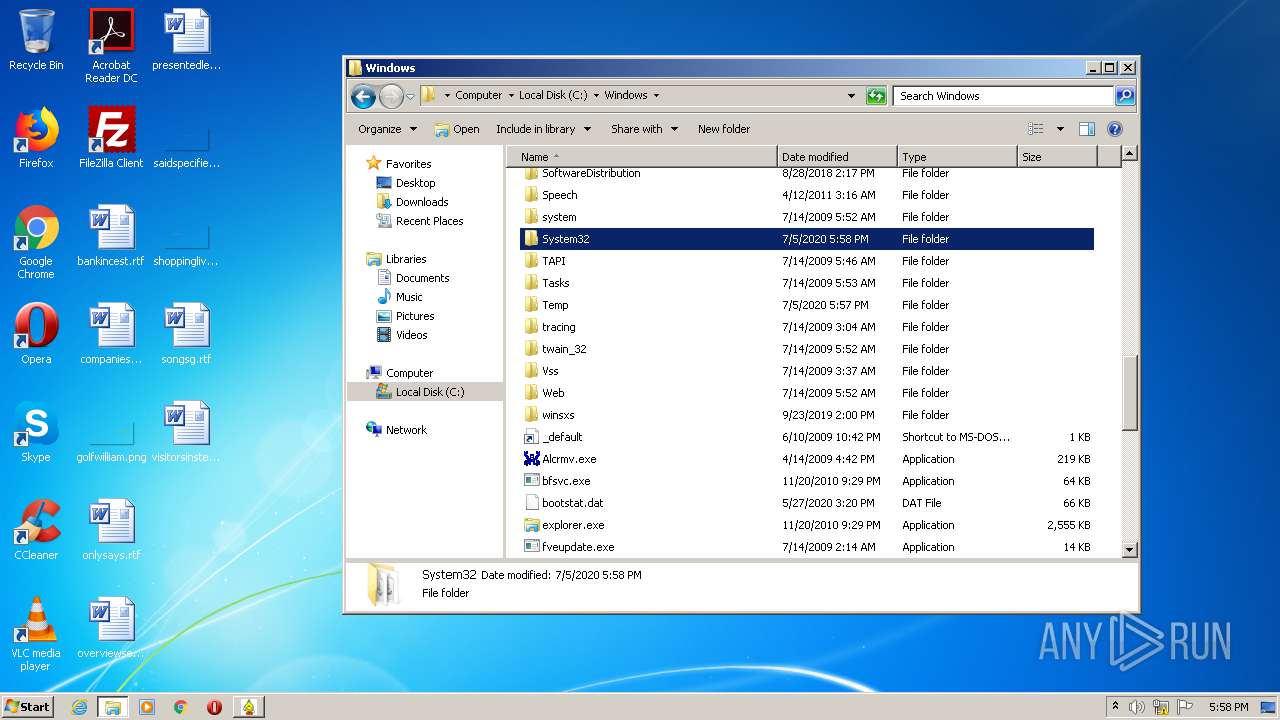
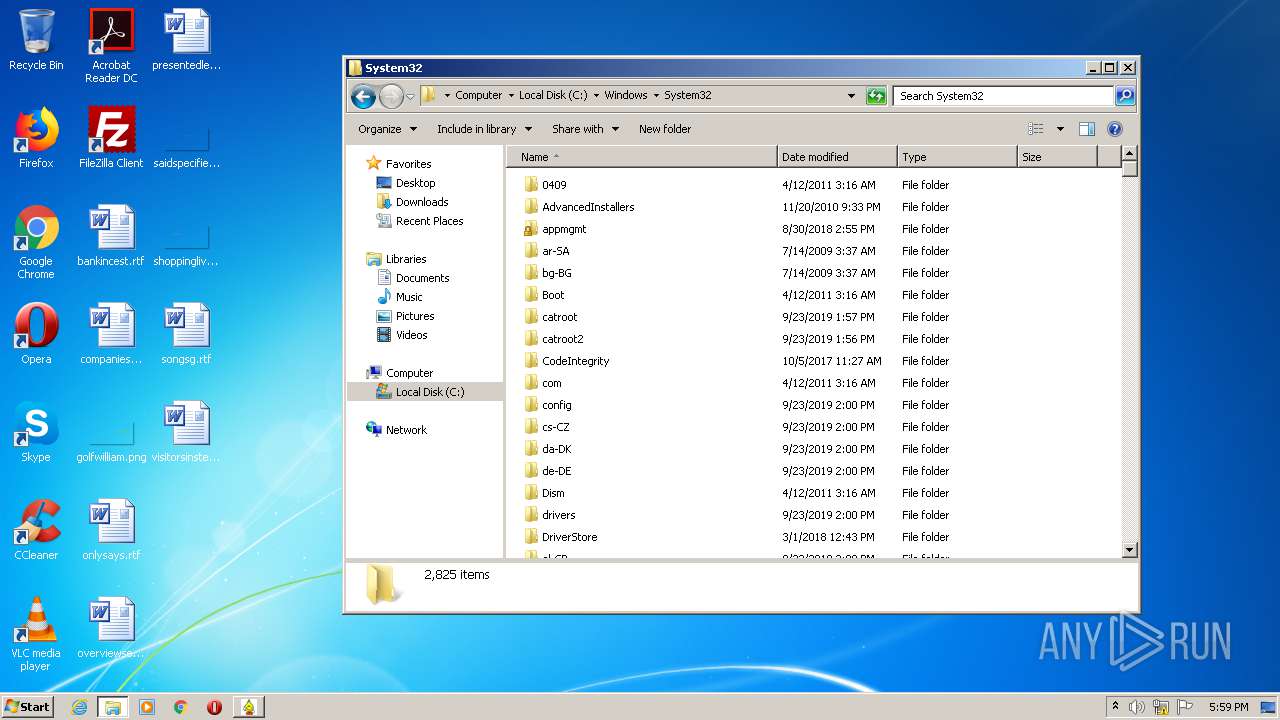
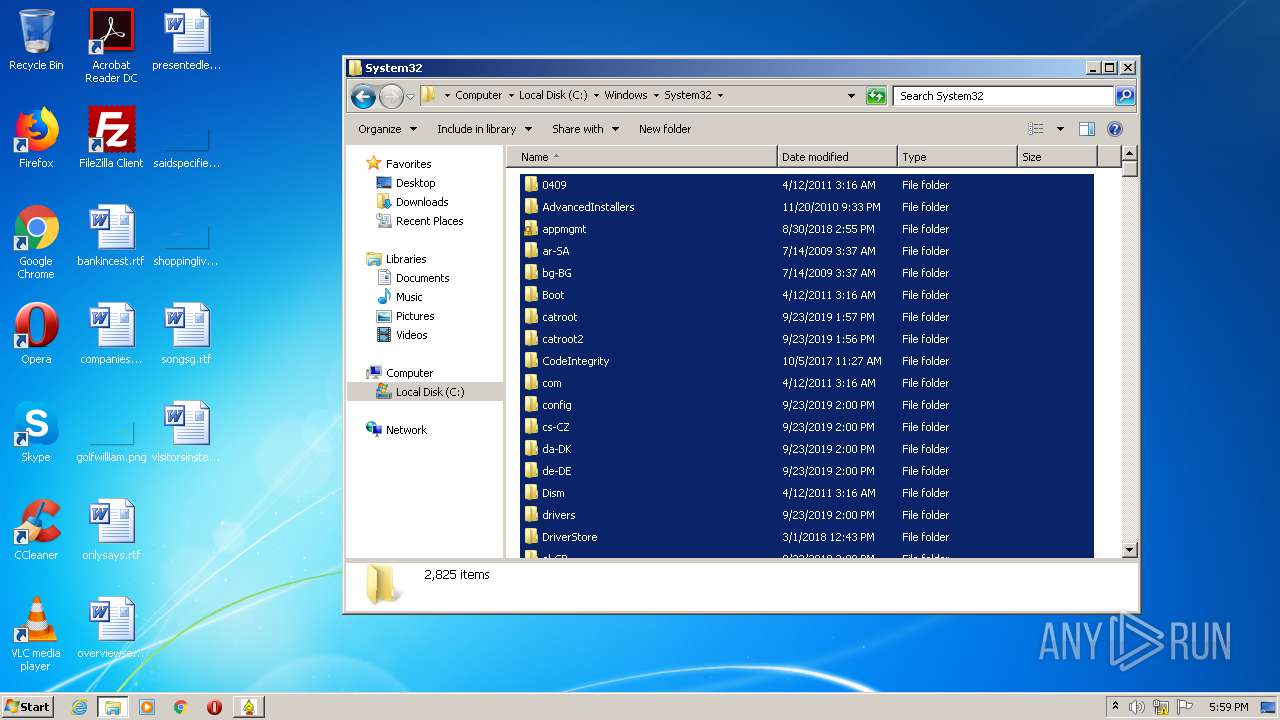
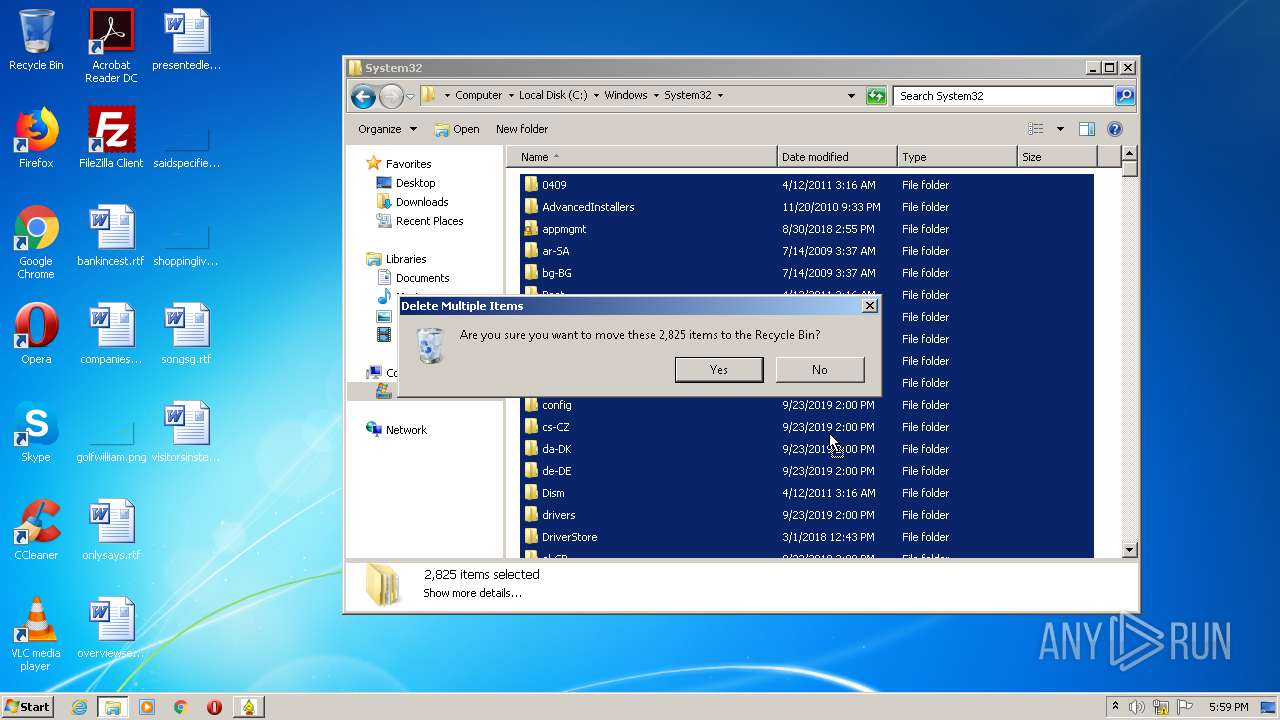
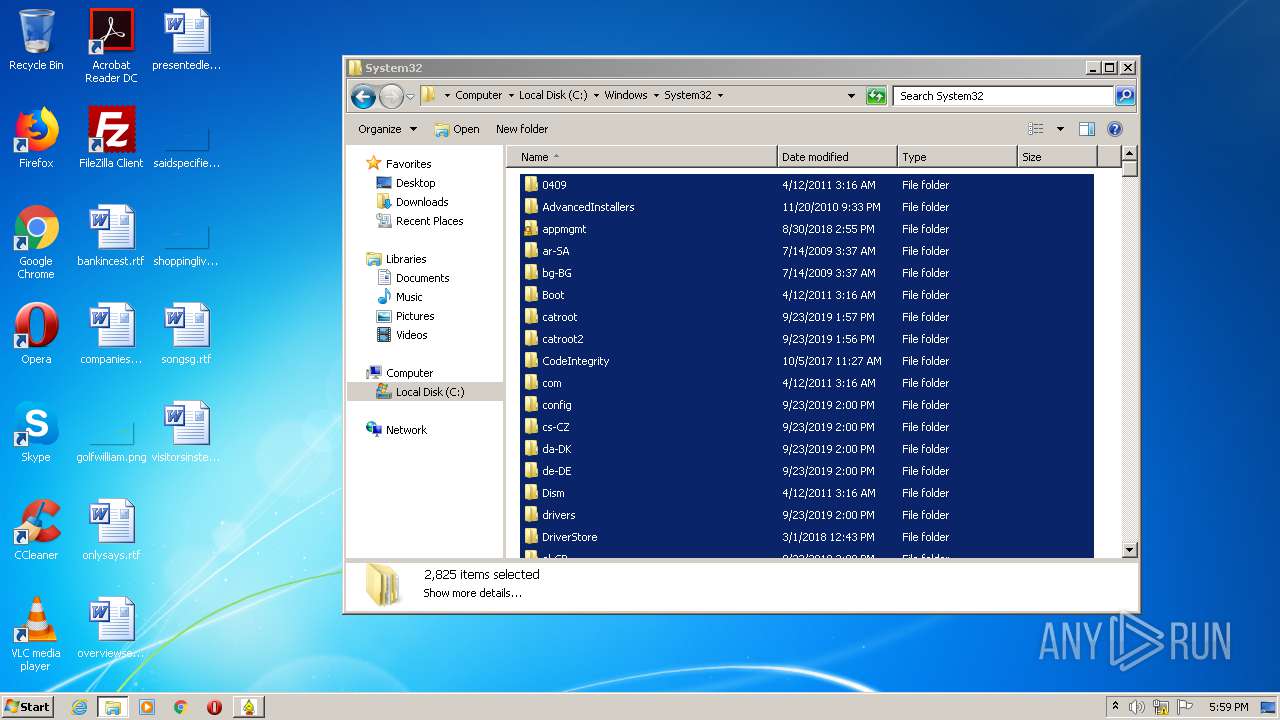
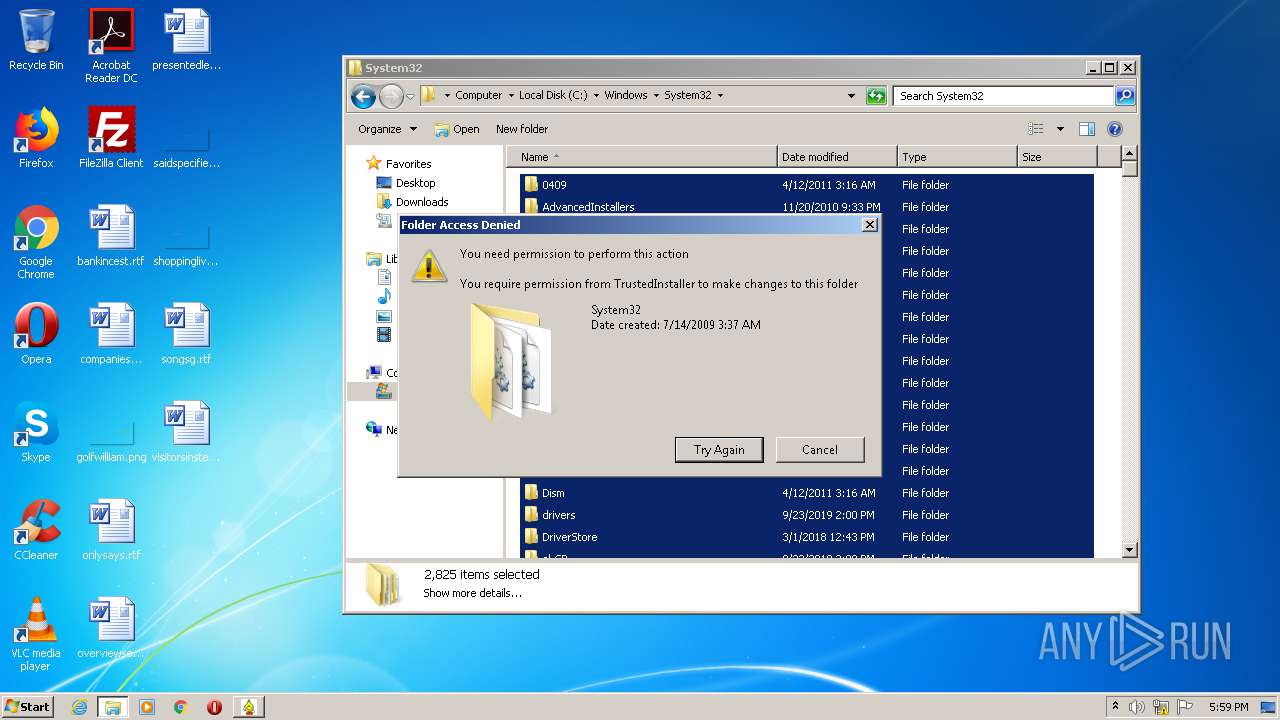
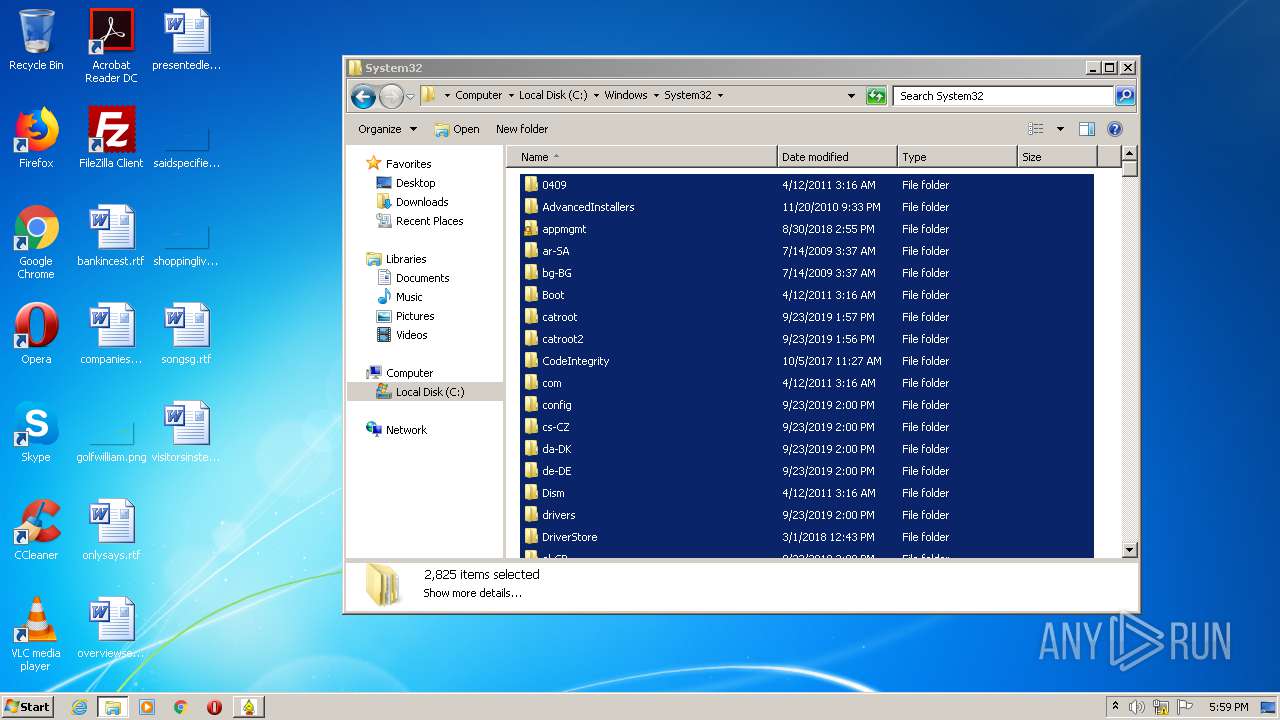
Removes files from Windows directory
- cmd.exe (PID: 3980)
- DllHost.exe (PID: 2684)
INFO
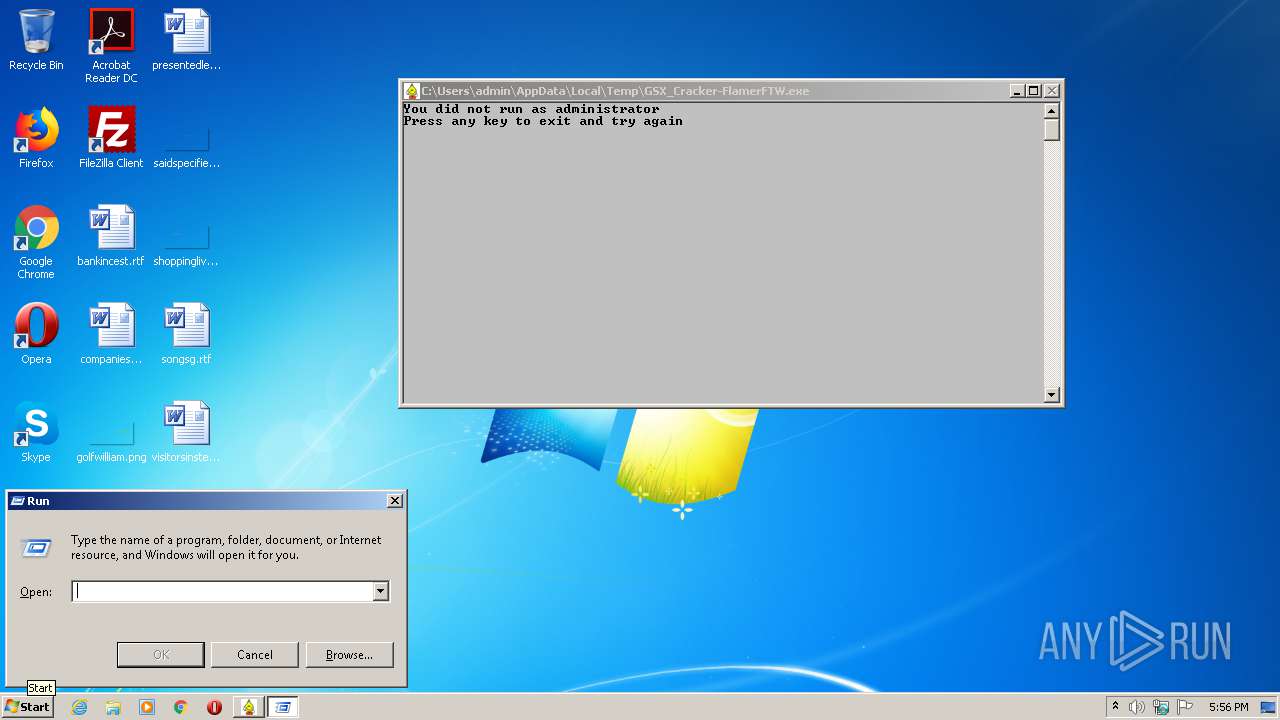
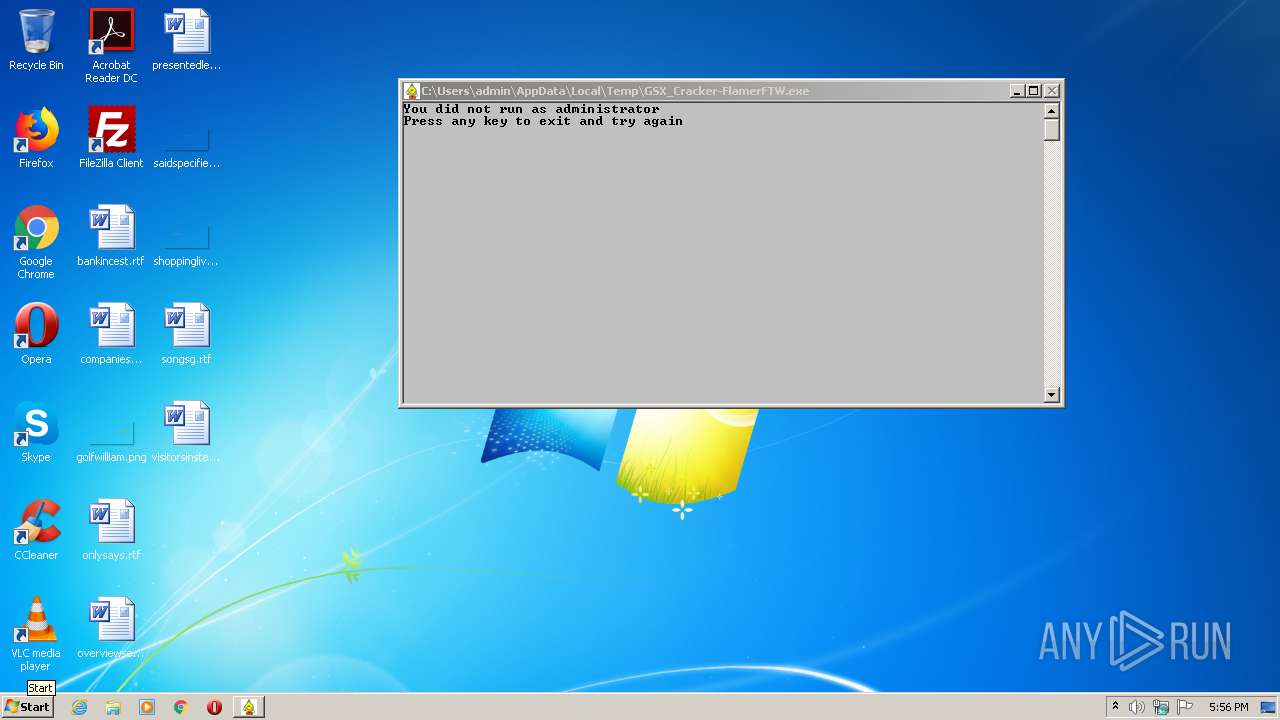
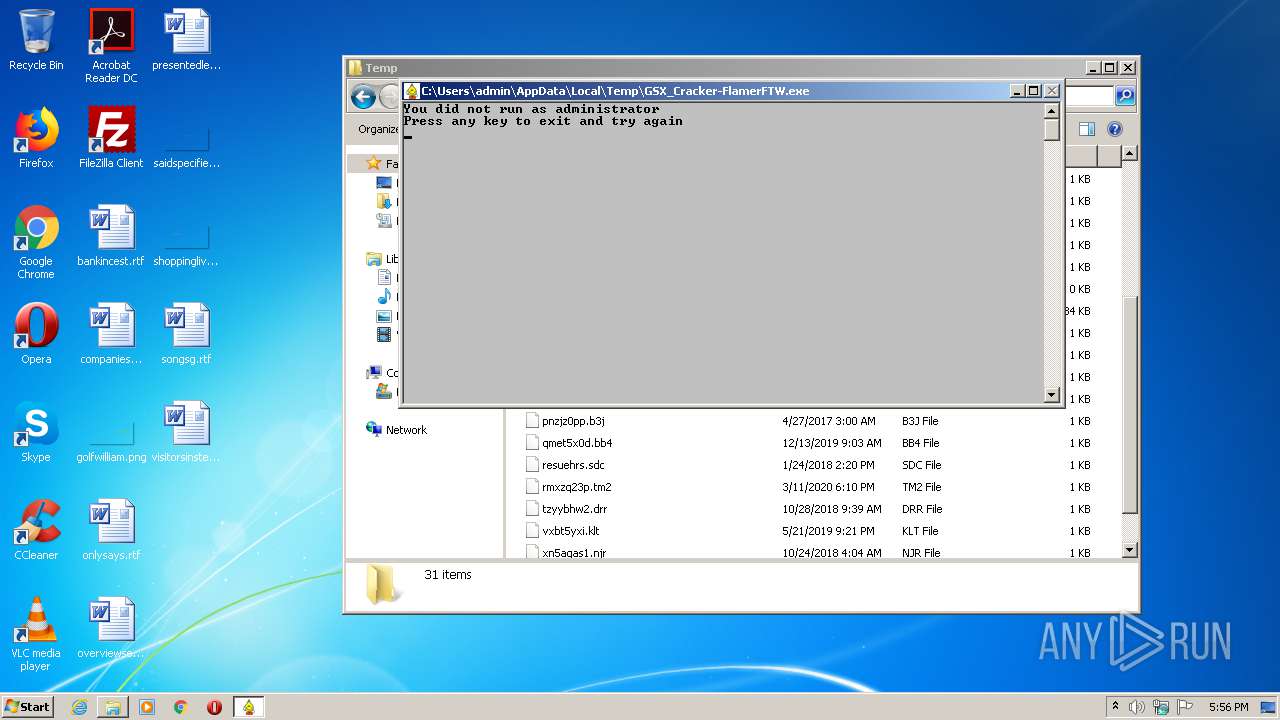
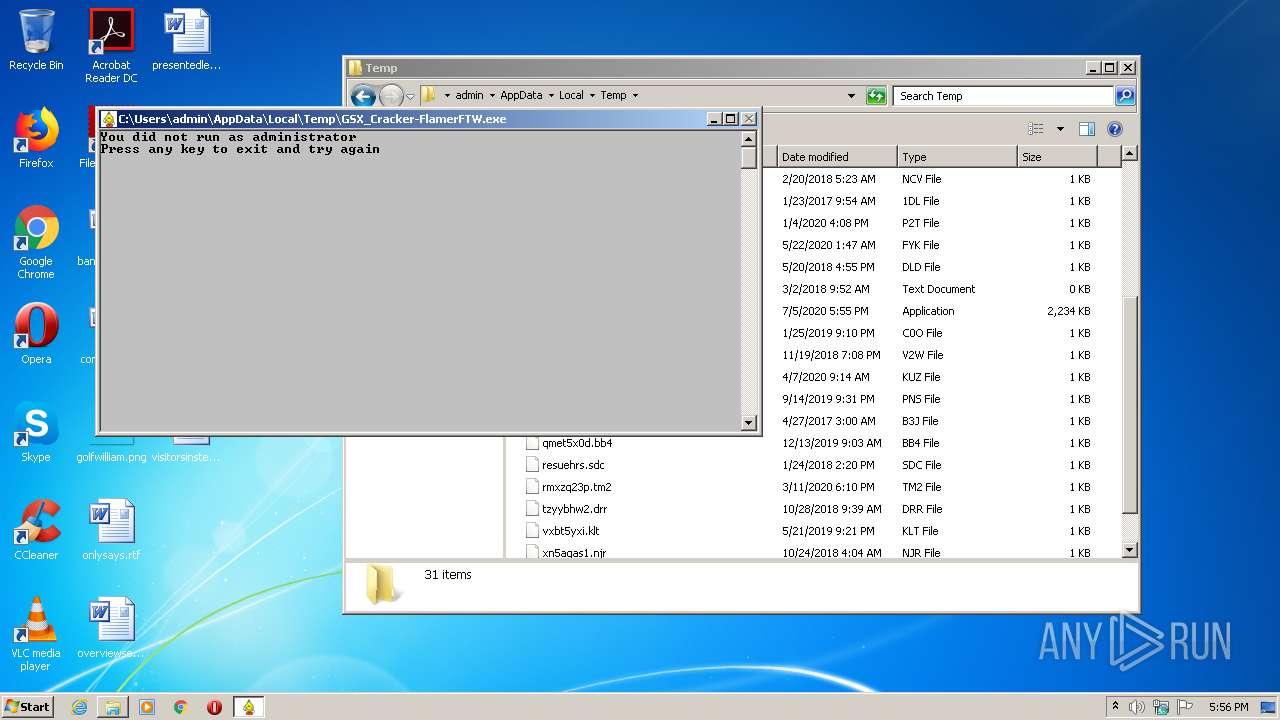
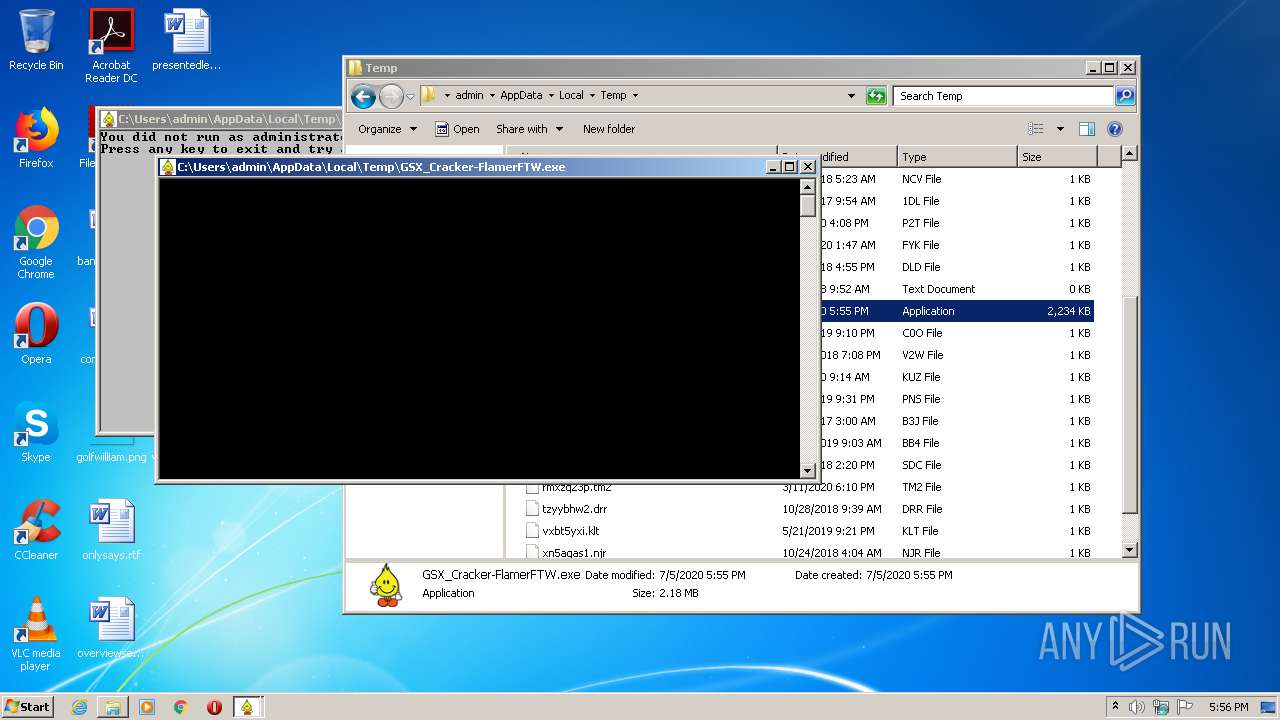
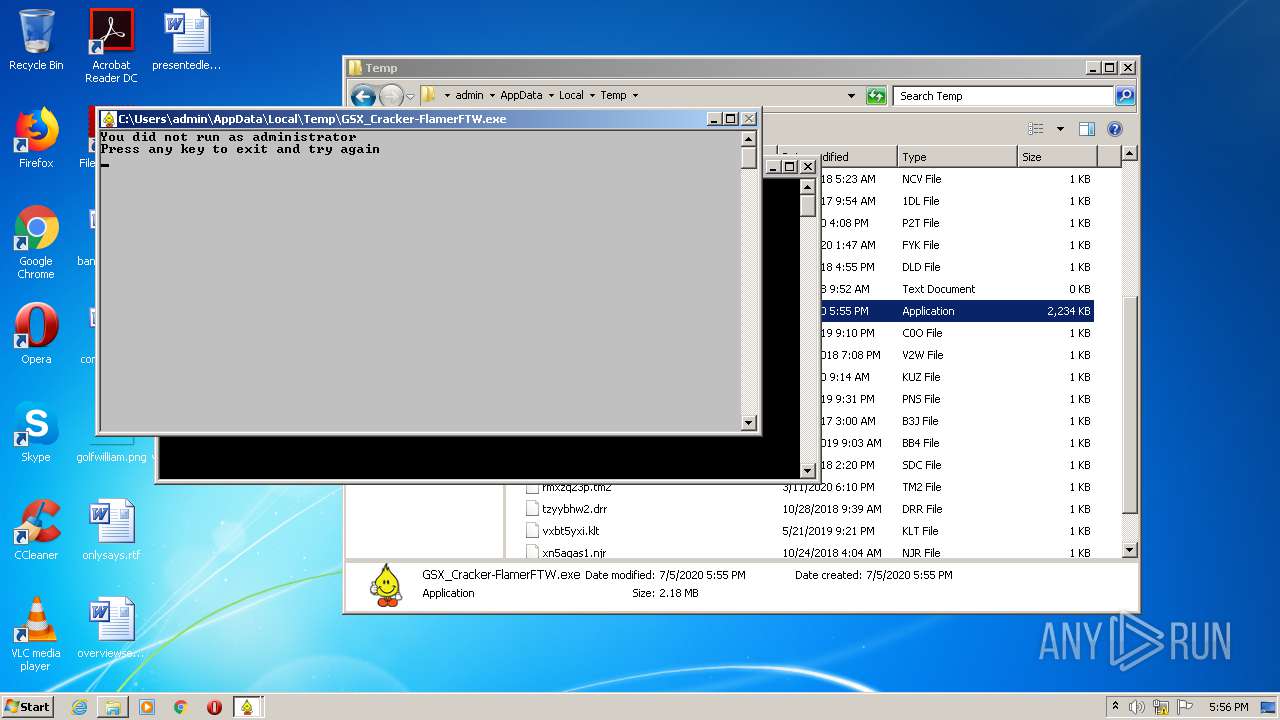
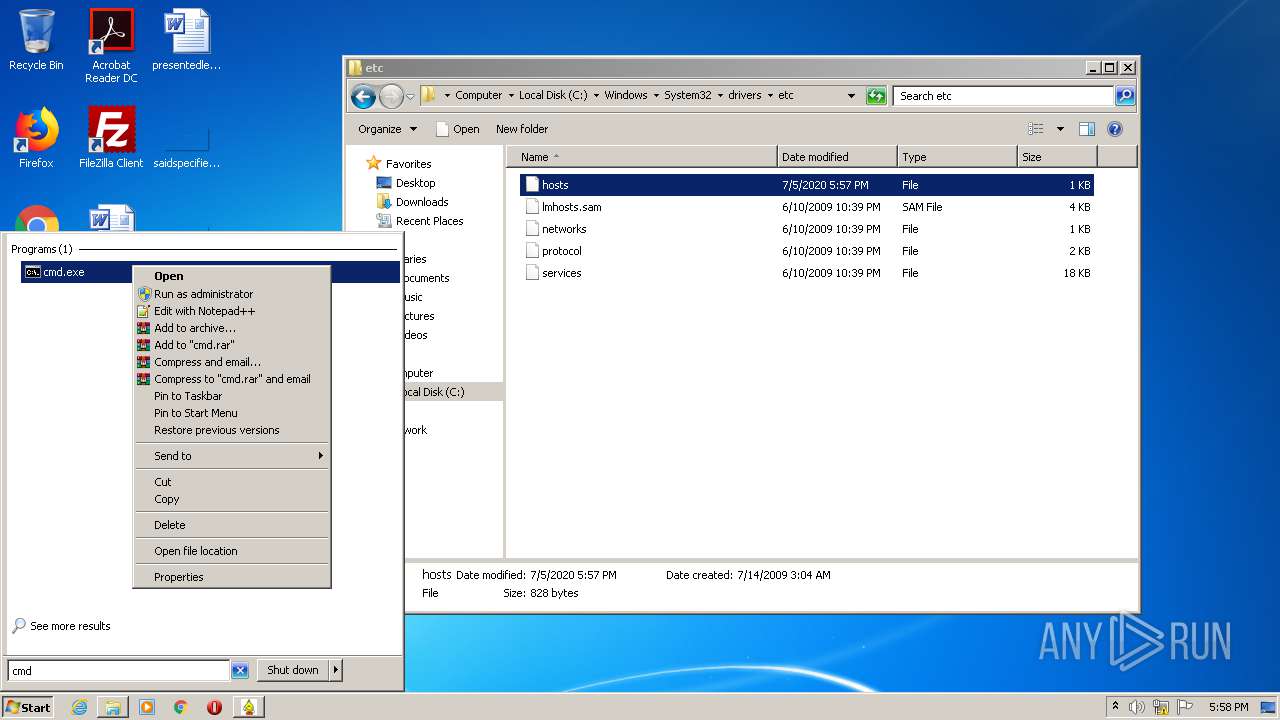
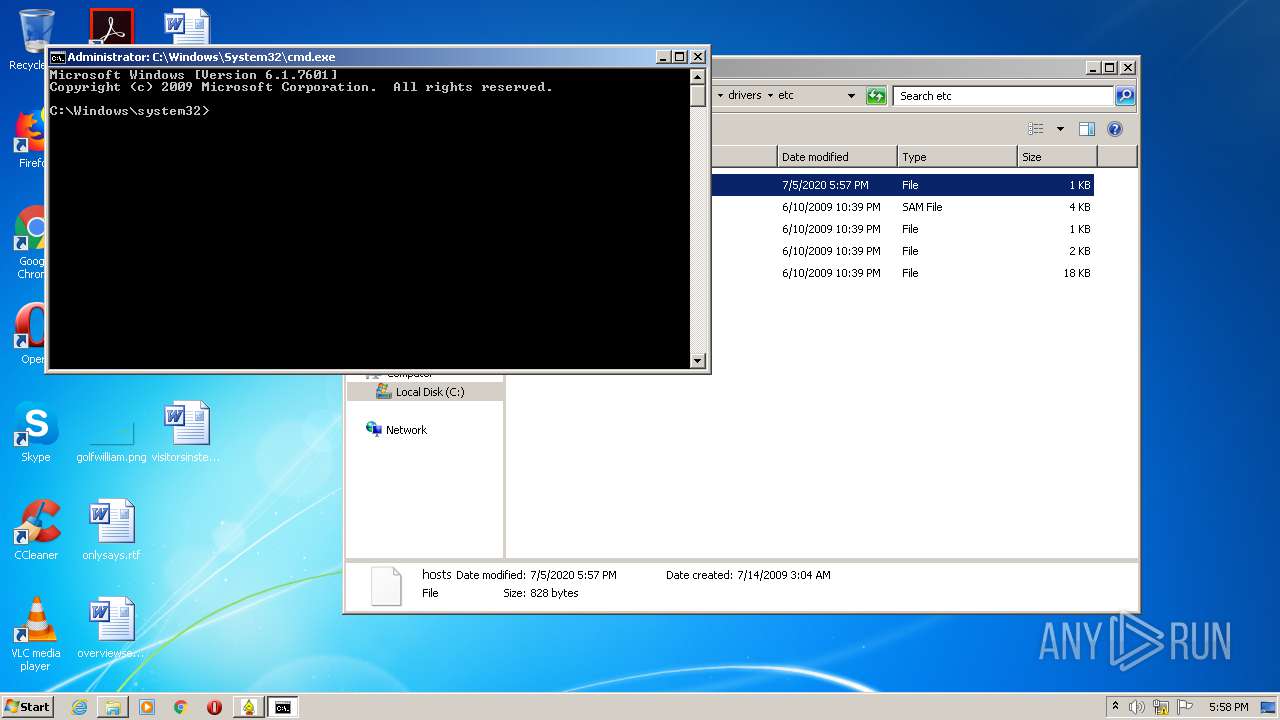
Manual execution by user
- cmd.exe (PID: 3980)
- GSX_Cracker-FlamerFTW.exe (PID: 2720)
- cmd.exe (PID: 3464)
- notepad++.exe (PID: 552)
Reads the hosts file
- notepad++.exe (PID: 552)
- GSX_Cracker-FlamerFTW.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2063:07:01 07:04:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 11264 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5ae000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | GSX_Cracker-FlamerFTW |
| CompanyName: | ThePirateBay.org |
| FileDescription: | GSX_Cracker-FlamerFTW |
| FileVersion: | 1.01 |
| InternalName: | GSX_Cracker-FlamerFTW.exe |
| LegalCopyright: | Copyright © 2069 |
| LegalTrademarks: | - |
| OriginalFileName: | GSX_Cracker-FlamerFTW.exe |
| ProductName: | GSX_Cracker-FlamerFTW |
| ProductVersion: | 1.01 |
| AssemblyVersion: | 1.1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 25-May-1927 22:36:22 |
| Comments: | GSX_Cracker-FlamerFTW |
| CompanyName: | ThePirateBay.org |
| FileDescription: | GSX_Cracker-FlamerFTW |
| FileVersion: | 1.01 |
| InternalName: | GSX_Cracker-FlamerFTW.exe |
| LegalCopyright: | Copyright © 2069 |
| LegalTrademarks: | - |
| OriginalFilename: | GSX_Cracker-FlamerFTW.exe |
| ProductName: | GSX_Cracker-FlamerFTW |
| ProductVersion: | 1.01 |
| Assembly Version: | 1.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x867A |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 25-May-1927 22:36:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00002000 | 0x00004000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.83385 | |
.rsrc | 0x00006000 | 0x00004224 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.95358 |
.idata | 0x0000C000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.17411 |
0x0000E000 | 0x00378000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.251484 | |
nnvutyks | 0x00386000 | 0x00226000 | 0x00224800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95384 |
iahiekhu | 0x005AC000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.33466 |
.taggant | 0x005AE000 | 0x00004000 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.68409 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.68927 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.43005 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.45849 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
comctl32.dll |
kernel32.dll |
Total processes
58
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\System32\drivers\etc\hosts" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2684 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
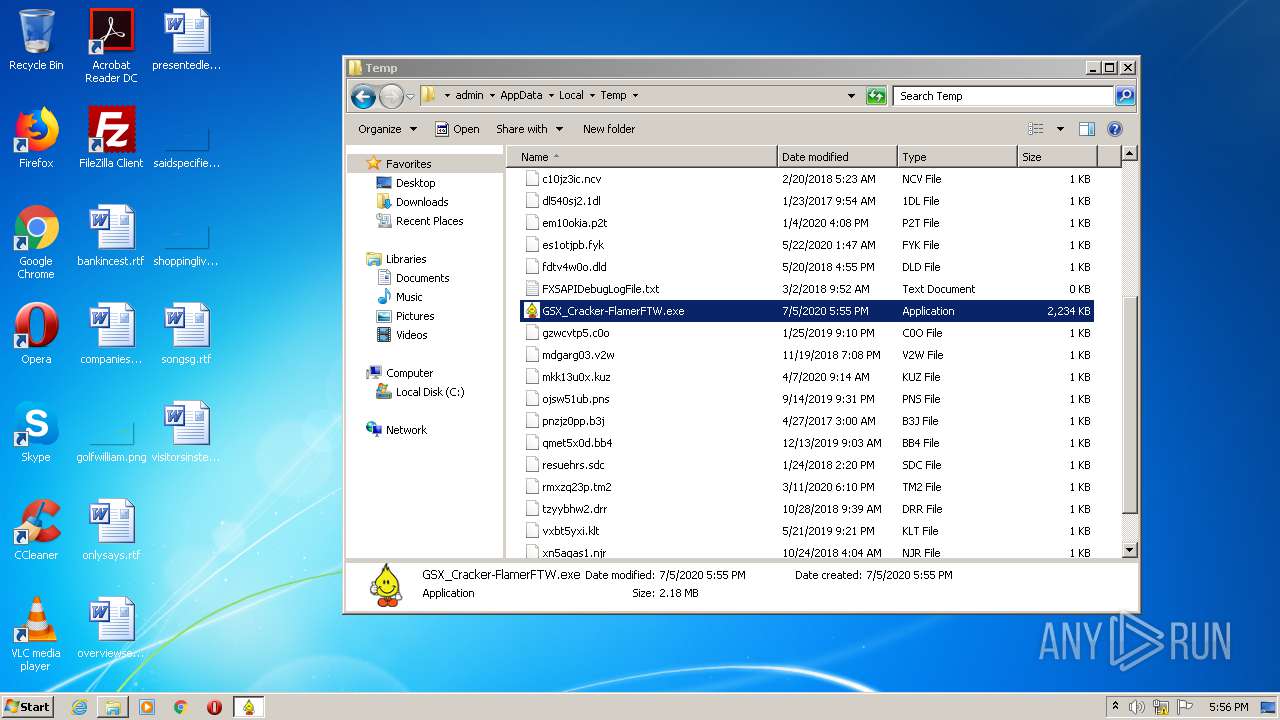
| 2720 | "C:\Users\admin\AppData\Local\Temp\GSX_Cracker-FlamerFTW.exe" | C:\Users\admin\AppData\Local\Temp\GSX_Cracker-FlamerFTW.exe | explorer.exe | ||||||||||||
User: admin Company: ThePirateBay.org Integrity Level: HIGH Description: GSX_Cracker-FlamerFTW Exit code: 0 Version: 1.01 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\GSX_Cracker-FlamerFTW.exe" | C:\Users\admin\AppData\Local\Temp\GSX_Cracker-FlamerFTW.exe | explorer.exe | ||||||||||||
User: admin Company: ThePirateBay.org Integrity Level: MEDIUM Description: GSX_Cracker-FlamerFTW Exit code: 0 Version: 1.01 Modules
| |||||||||||||||
| 3464 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3480 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 3980 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
157
Read events
114
Write events
37
Delete events
6
Modification events
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\CentralProcessor\0 |
| Operation: | write | Name: | Identifier |
Value: Intel64 Family 6 Model 158 Stepping 10 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\CentralProcessor\0 |
| Operation: | write | Name: | VendorIdentifier |
Value: GenuineIntel | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System |
| Operation: | write | Name: | SystemBiosVersion |
Value: ALASKA - 1072009 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Disk\Enum |
| Operation: | write | Name: | 0 |
Value: SCSI\Disk&Ven_NVMe&Prod_Samsung_SSD_960\5&87ca3f&0&000000 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\CentralProcessor\0 |
| Operation: | write | Name: | ~MHz |
Value: 3600 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip\Linkage |
| Operation: | write | Name: | bind |
Value: \Device\{63F47244-9922-44AE-BC5C-3F7ABF6C720E} | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\cdrom\Enum |
| Operation: | write | Name: | 0 |
Value: SCSI\CdRom&Ven_ATAPI&Prod_iHAS324___B\4&240534ba&0&000500 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\IDConfigDB\CurrentDockInfo |
| Operation: | write | Name: | DockingState |
Value: 1 | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System |
| Operation: | write | Name: | SystemBiosDate |
Value: | |||
| (PID) Process: | (2720) GSX_Cracker-FlamerFTW.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\eSellerate\Activations\PUB9932588035\ACT725435328 |
| Operation: | write | Name: | FSDTGSX-9EDN-PFWN-K2Q9-VL11-7K21 |
Value: 5RX5TC-GN16-WHK03F-6H6Y-993U3H-X4FP9T-LWRL-2CF04E-U0JZ-287Q24 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 2720 | GSX_Cracker-FlamerFTW.exe | C:\Windows\system32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
| 552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | gup.exe | 172.67.218.84:443 | notepad-plus-plus.org | — | US | malicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GSX_Cracker-FlamerFTW.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
GSX_Cracker-FlamerFTW.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|