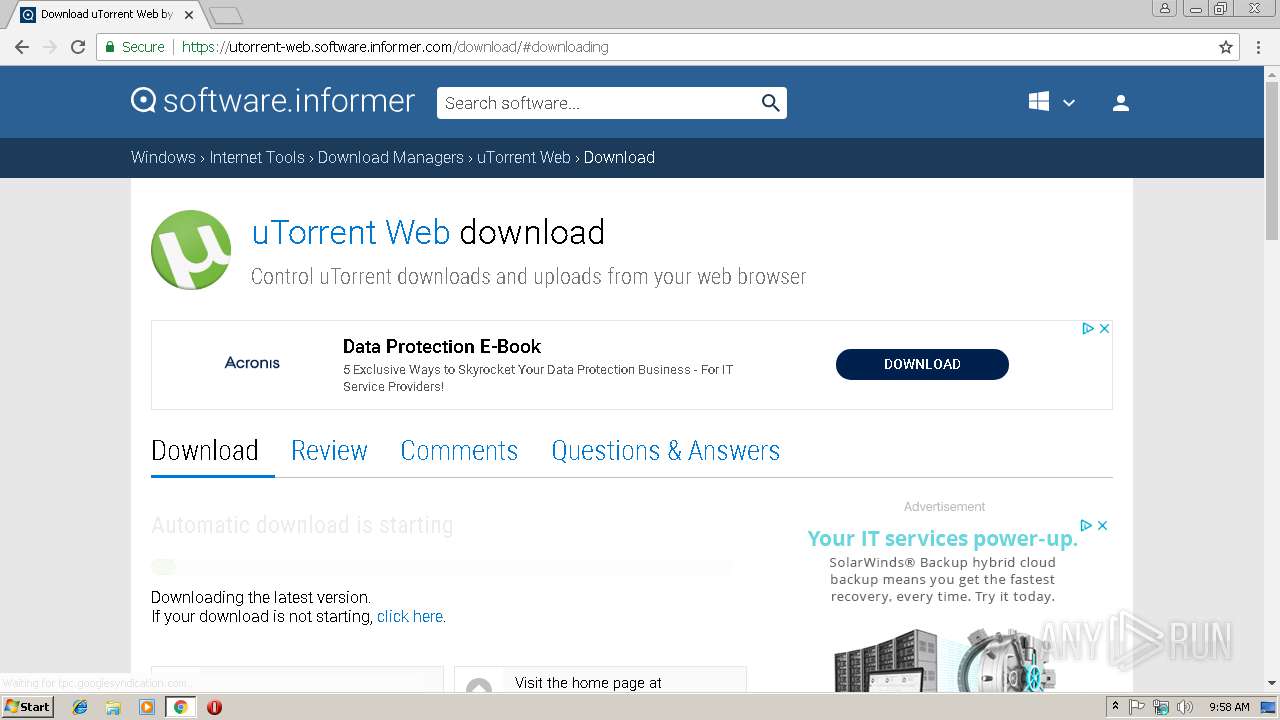
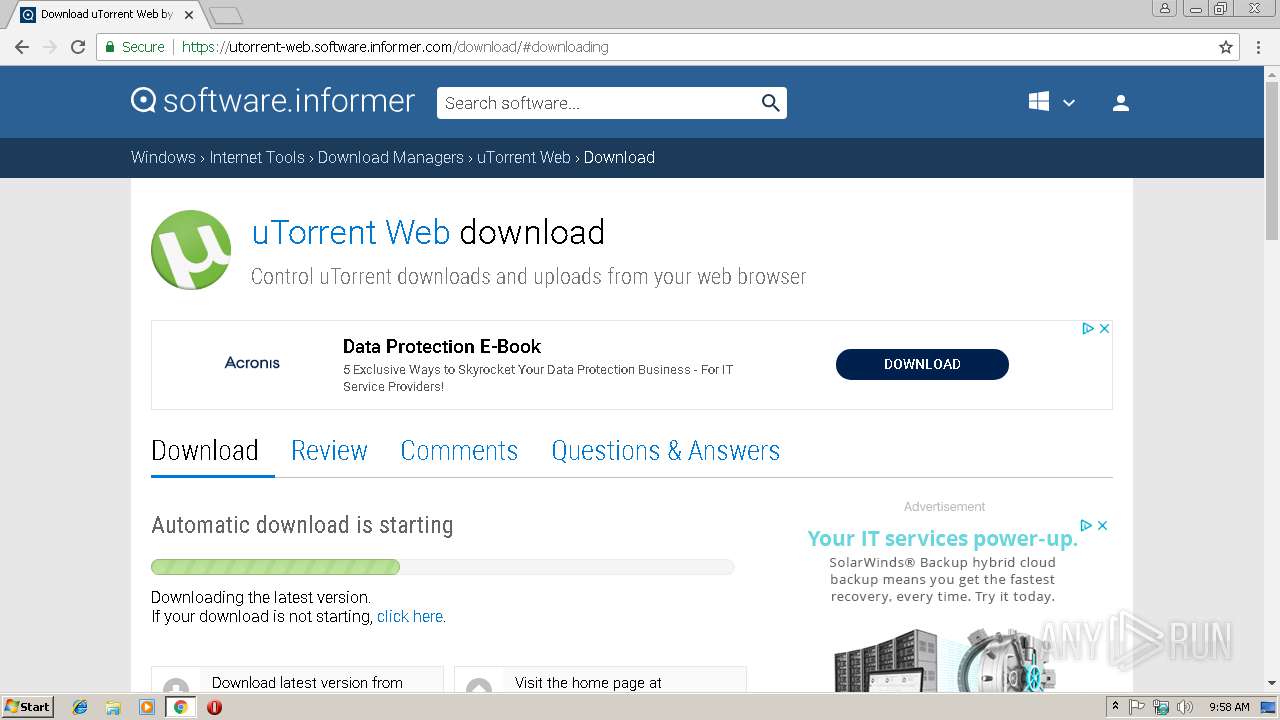
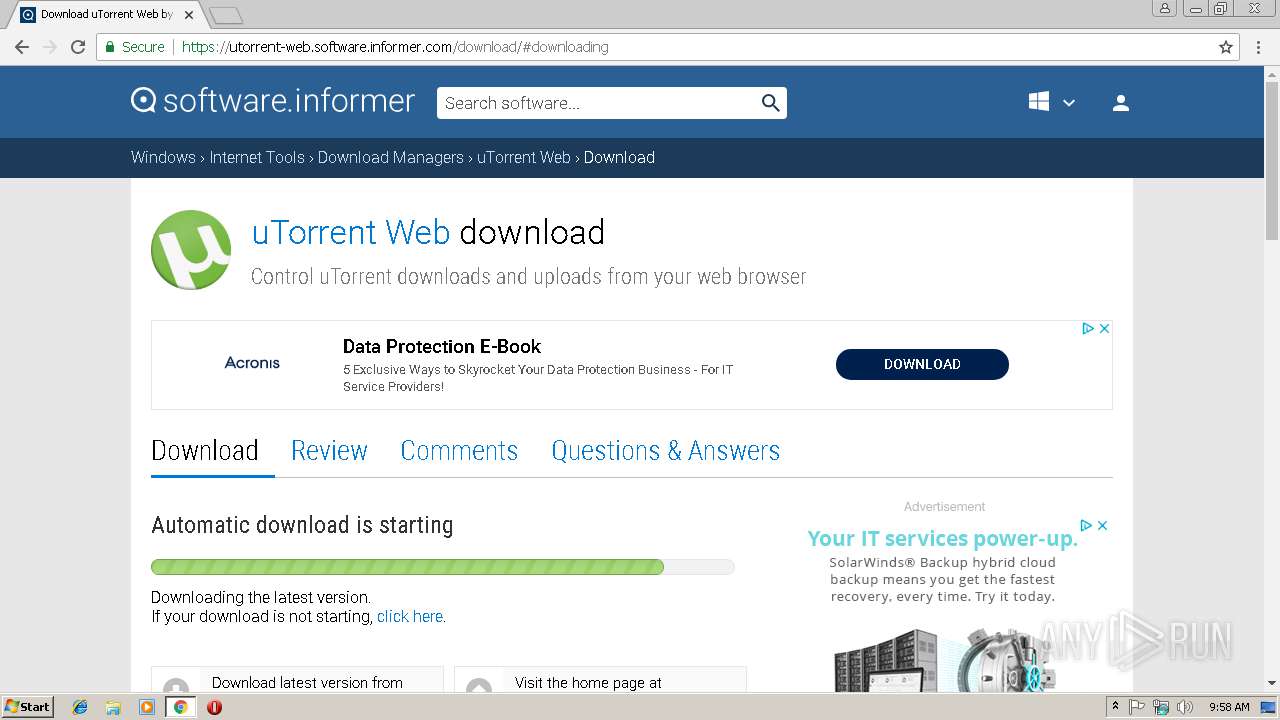
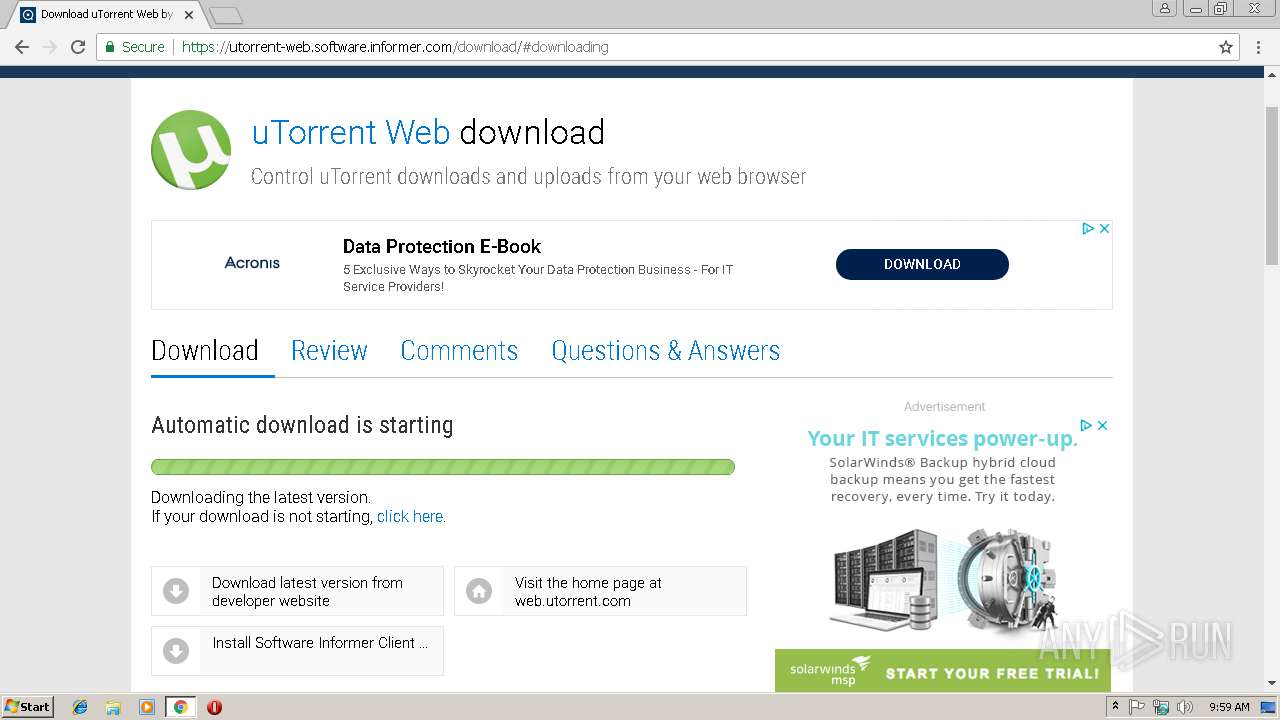
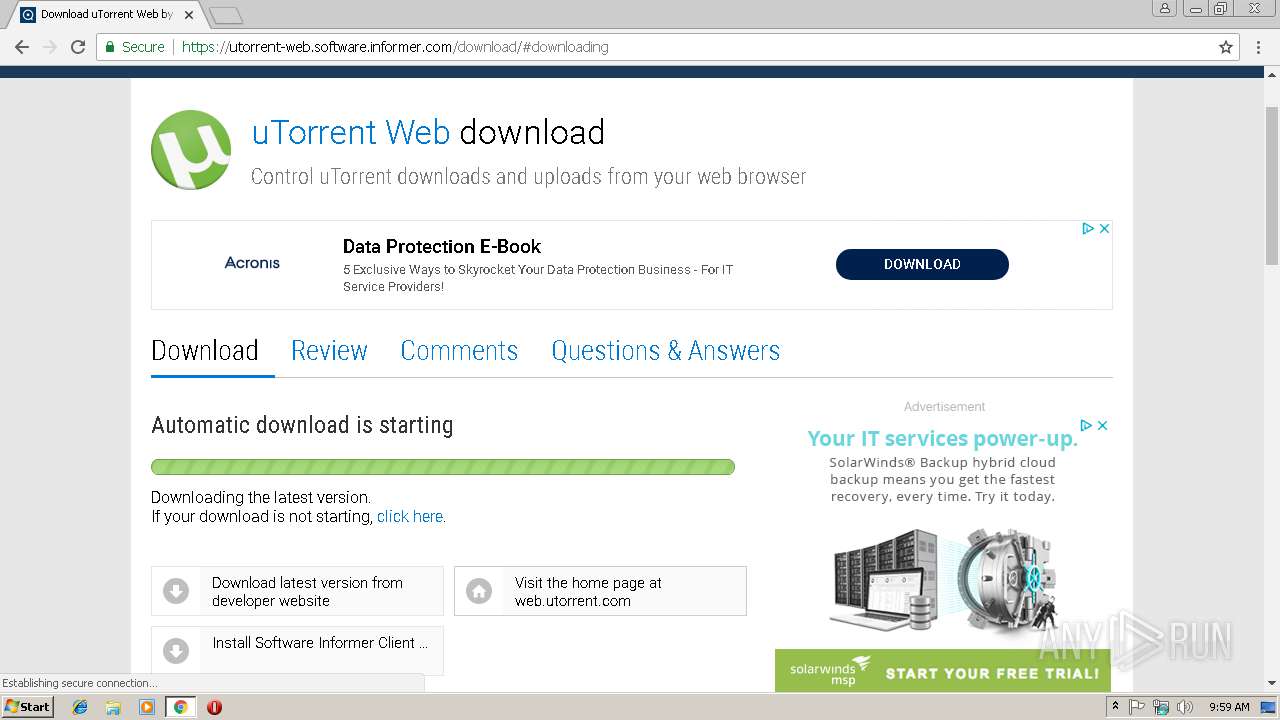
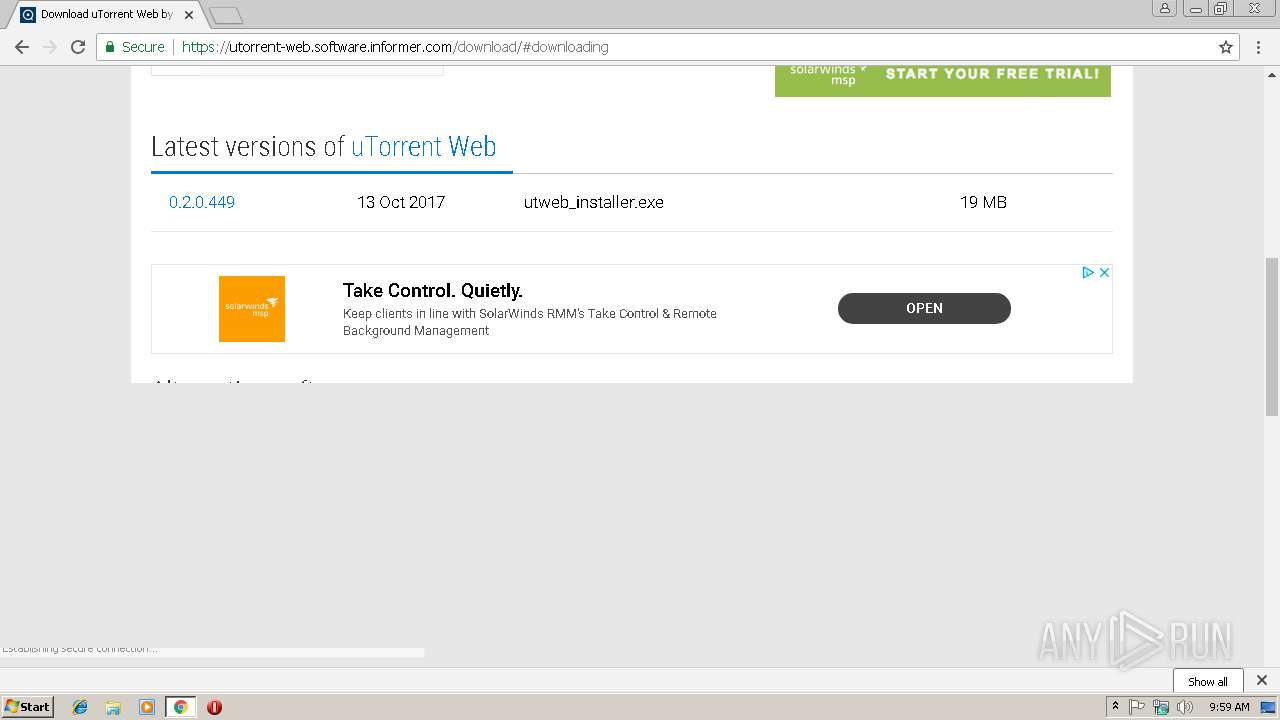
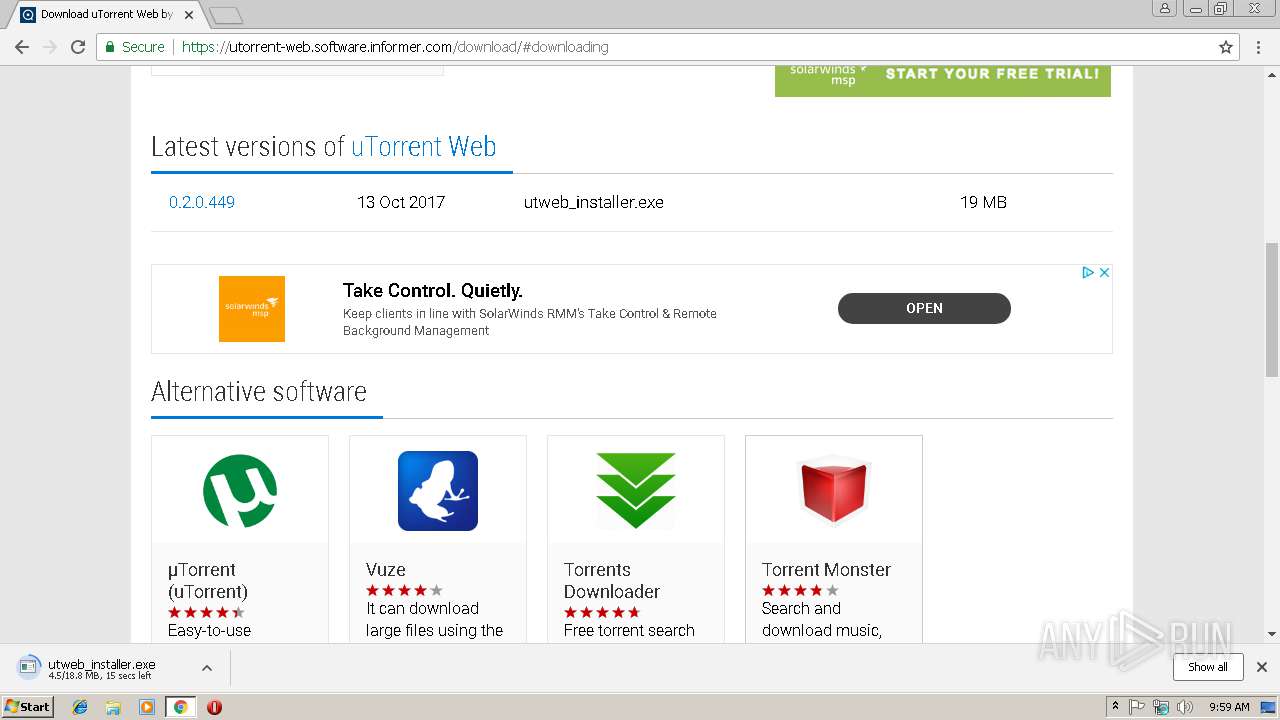
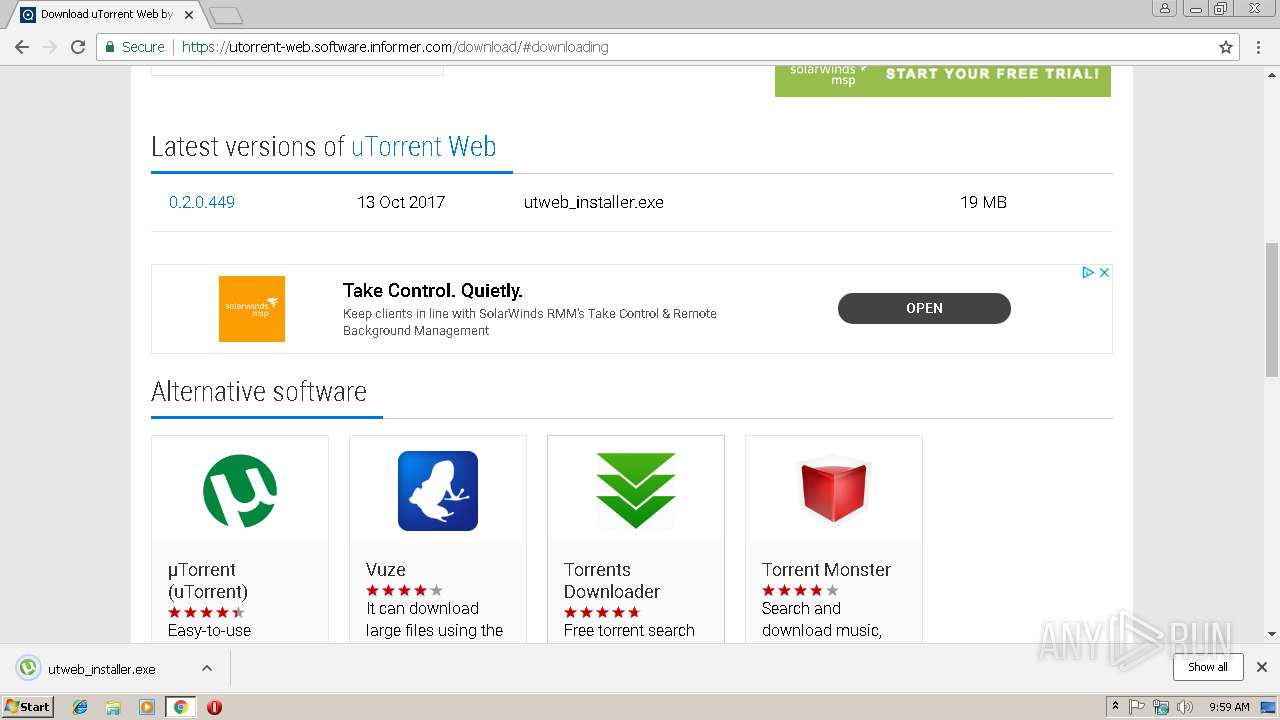
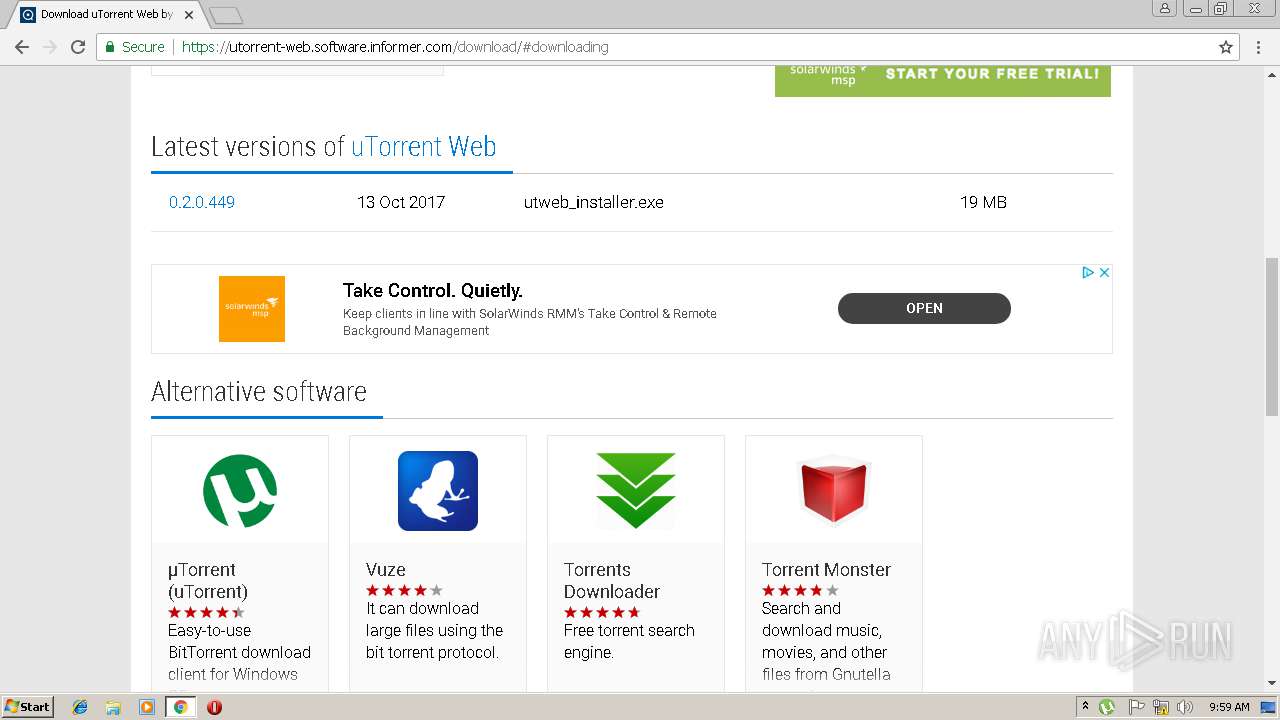
| URL: | https://utorrent-web.software.informer.com/0.1/ |
| Full analysis: | https://app.any.run/tasks/c7431a5c-b5f0-4166-bafa-7546fd1a320b |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2019, 09:58:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7BFC3EDE9231E7EAD7297348161B658B |
| SHA1: | 1EBA521CC5C644FCFF1642B6811FE39499EE2091 |
| SHA256: | 5B7FD358007B4176FAF329016186713CB9F6456825689E73F18FE4081DFC8372 |
| SSDEEP: | 3:N8ARISLY9j4P:2ARjY0P |
MALICIOUS
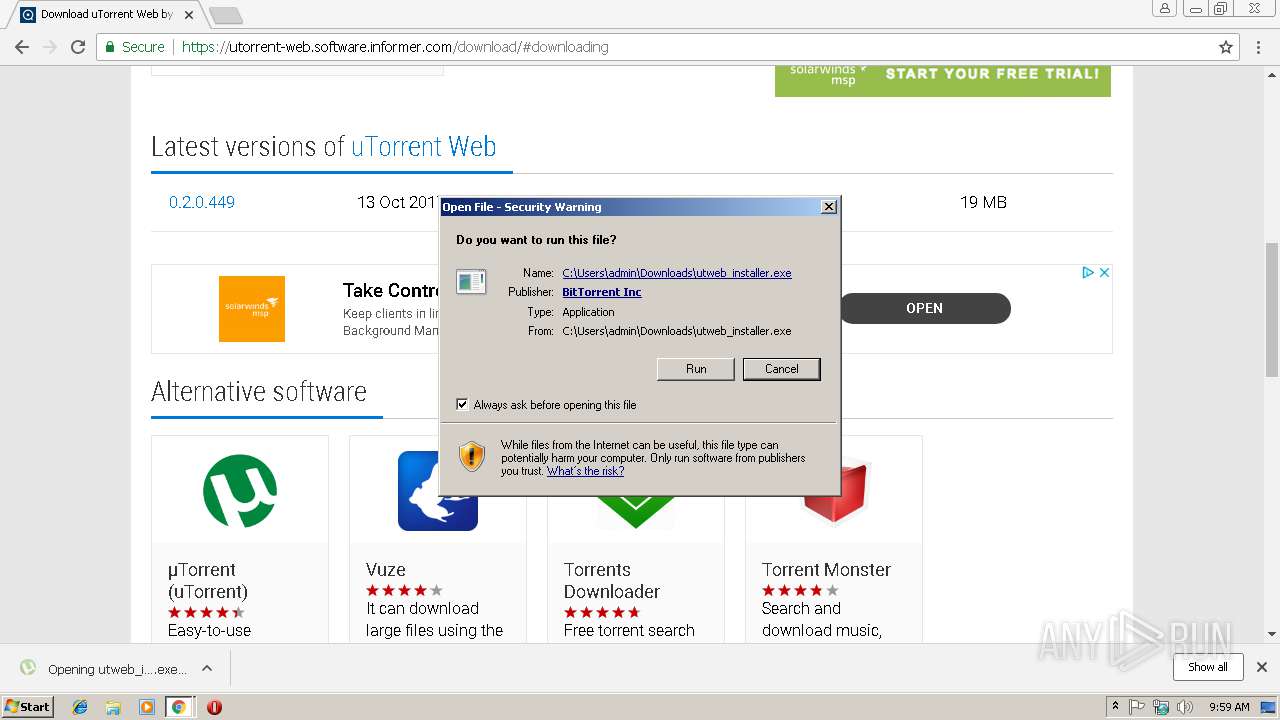
Application was dropped or rewritten from another process
- utweb_installer.exe (PID: 3380)
- utweb.exe (PID: 3444)
- utweb_installer.exe (PID: 4012)
- utweb.exe (PID: 4020)
Loads dropped or rewritten executable
- utweb_installer.exe (PID: 4012)
- utweb_installer.exe (PID: 3380)
- utweb.exe (PID: 3444)
- utweb.exe (PID: 4020)
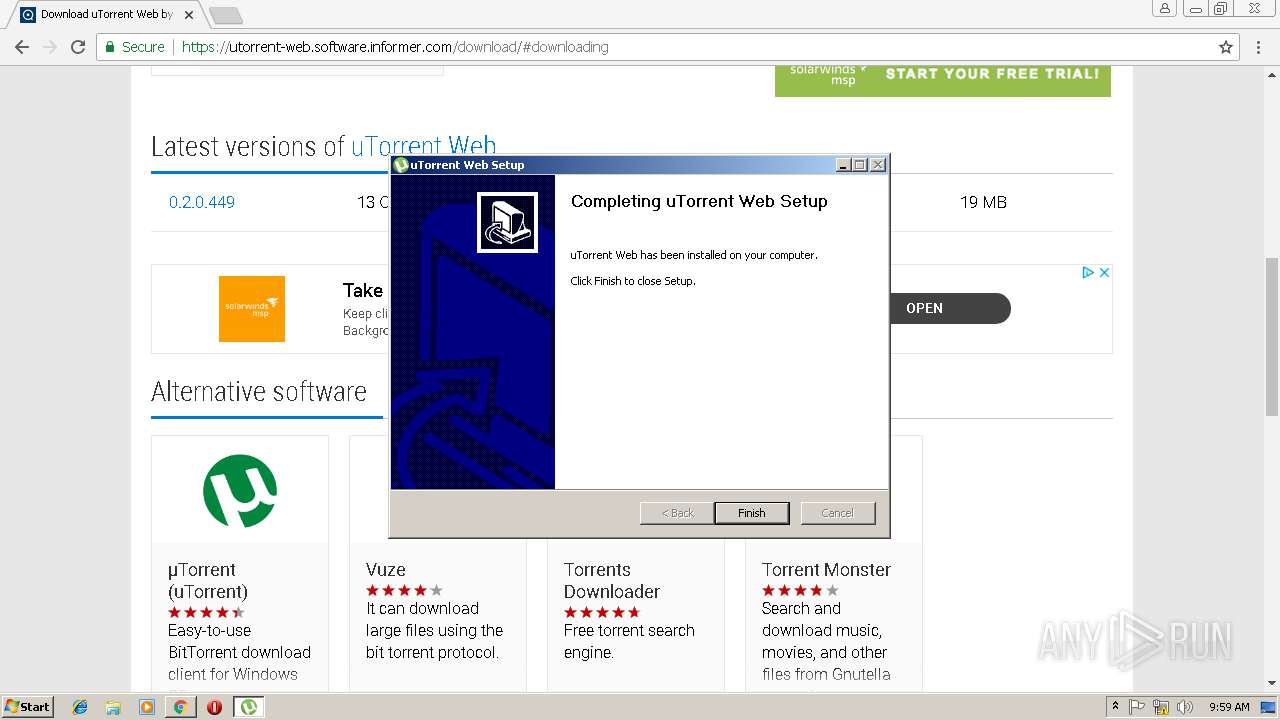
Changes the autorun value in the registry
- utweb.exe (PID: 3444)
SUSPICIOUS
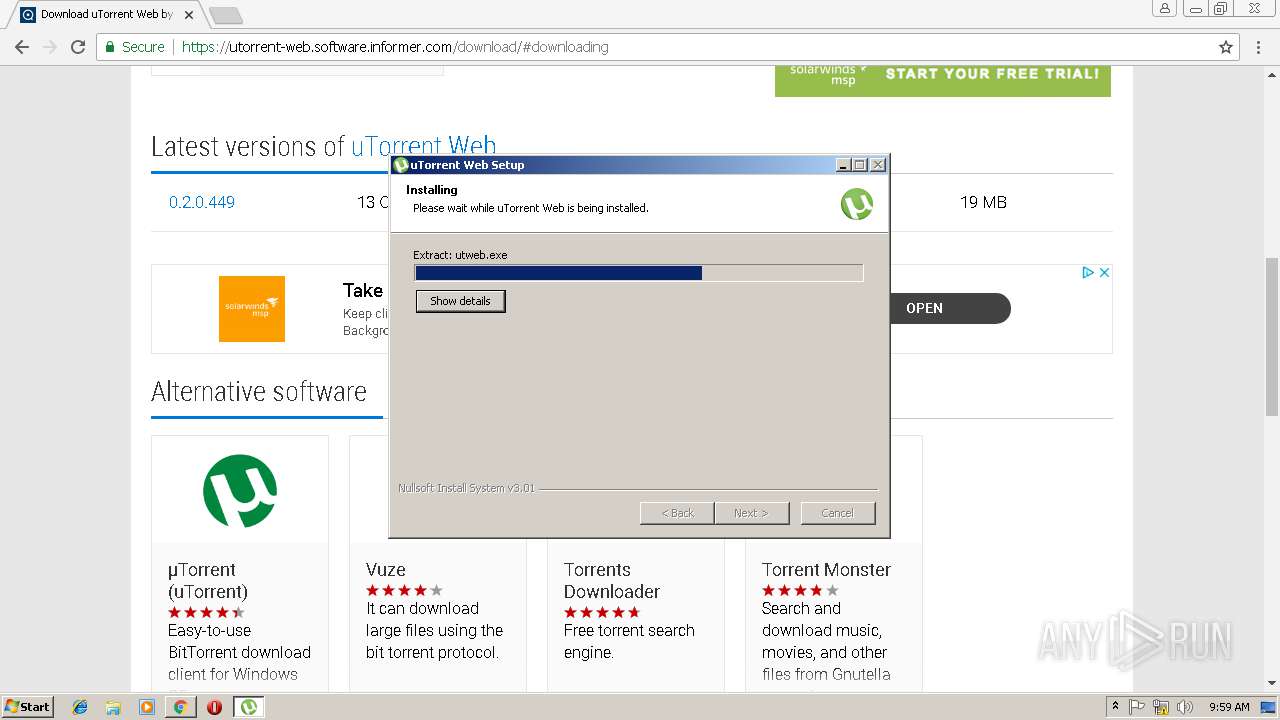
Executable content was dropped or overwritten
- utweb_installer.exe (PID: 3380)
- utweb_installer.exe (PID: 4012)
- chrome.exe (PID: 3000)
- utweb.exe (PID: 3444)
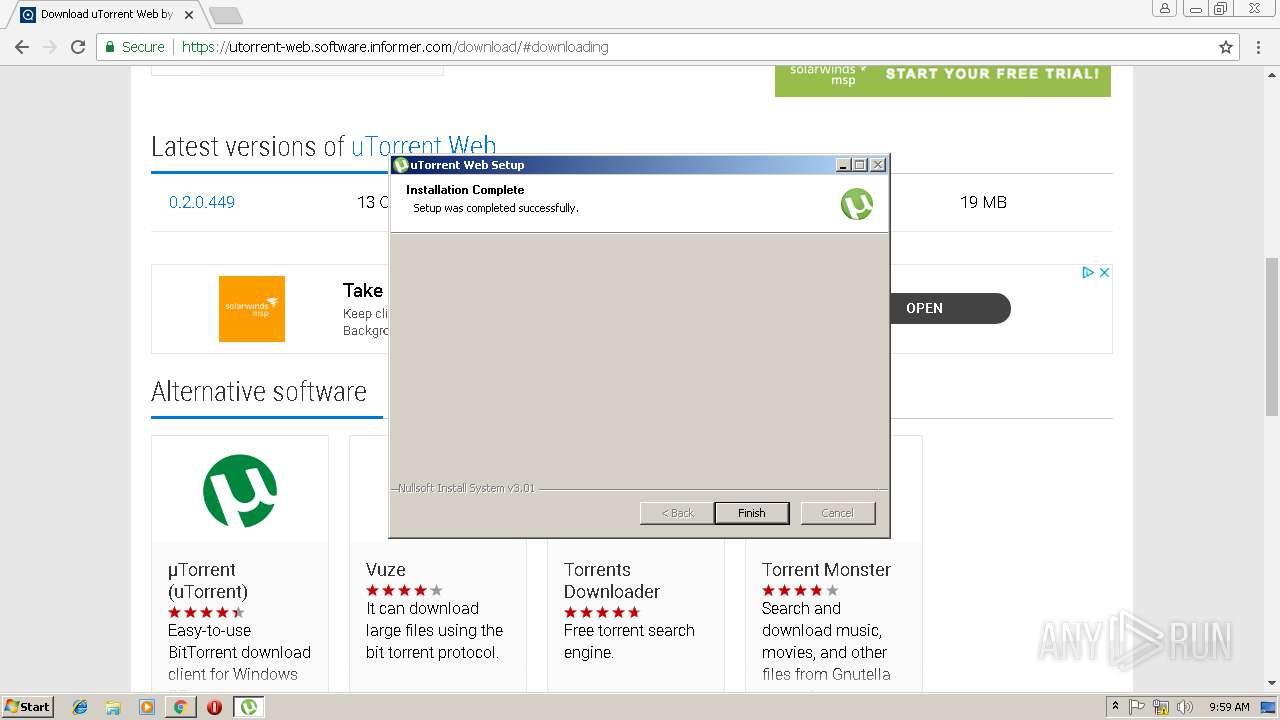
Creates a software uninstall entry
- utweb_installer.exe (PID: 4012)
Modifies the open verb of a shell class
- utweb_installer.exe (PID: 4012)
Reads Internet Cache Settings
- utweb_installer.exe (PID: 4012)
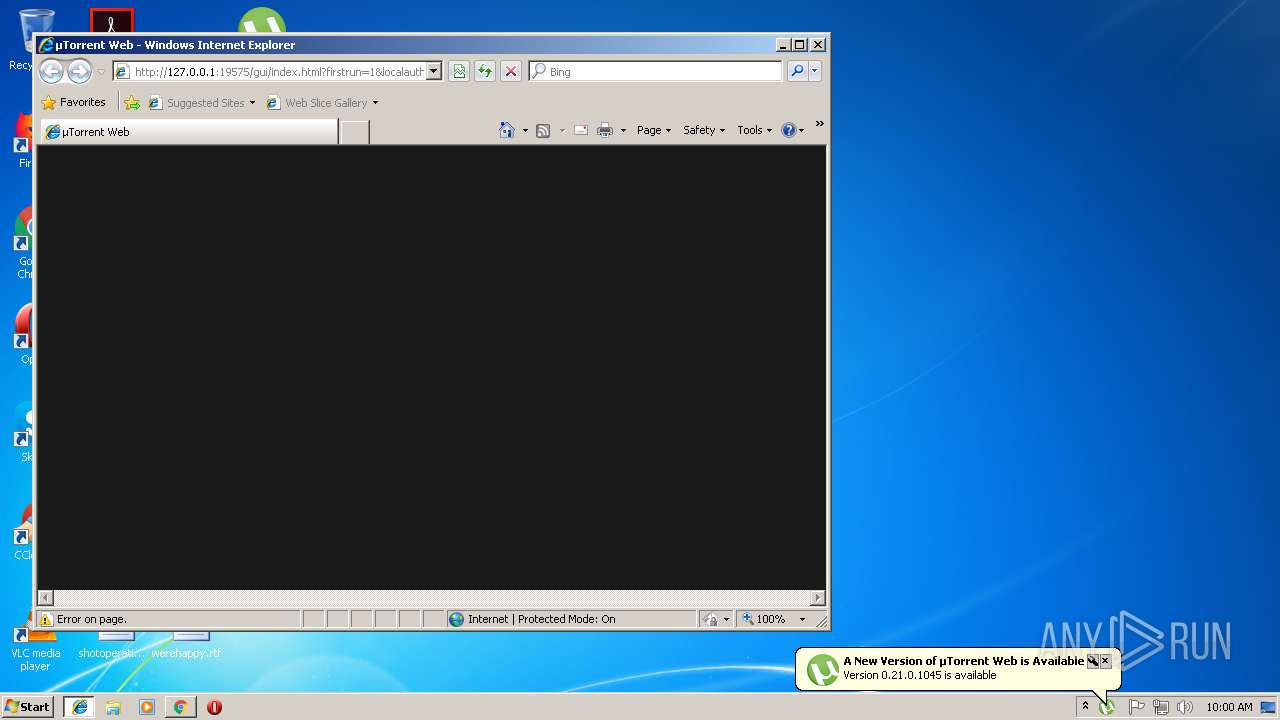
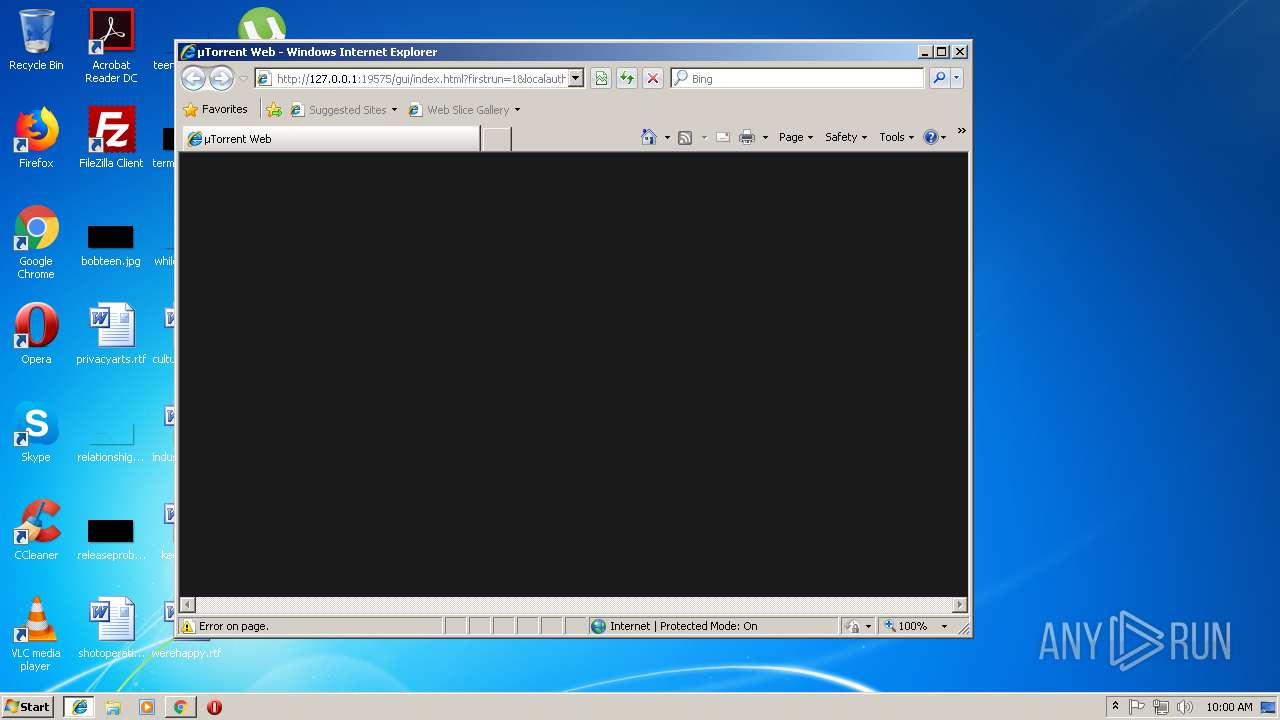
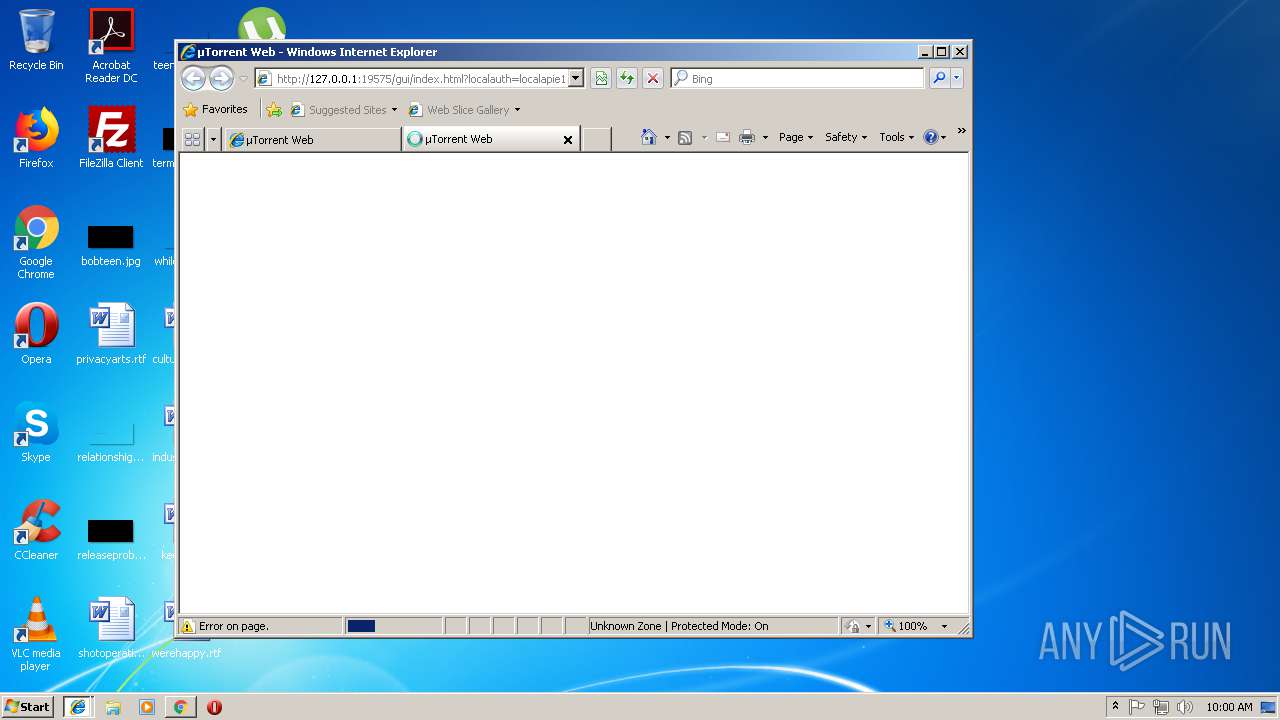
Starts Internet Explorer
- utweb.exe (PID: 3444)
Application launched itself
- utweb_installer.exe (PID: 3380)
Creates files in the user directory
- utweb_installer.exe (PID: 4012)
- utweb.exe (PID: 3444)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3000)
- utweb.exe (PID: 3444)
Reads Internet Cache Settings
- chrome.exe (PID: 3000)
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 1888)
- iexplore.exe (PID: 2276)
Application launched itself
- chrome.exe (PID: 3000)
- iexplore.exe (PID: 1888)
Changes internet zones settings
- iexplore.exe (PID: 1888)
Reads internet explorer settings
- iexplore.exe (PID: 2276)
- iexplore.exe (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
16
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1888 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | utweb.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=856 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1888 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=B9455384F4EF6E8F385C1B9E92958DF9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B9455384F4EF6E8F385C1B9E92958DF9 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3004 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://utorrent-web.software.informer.com/0.1/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=C01CDCD5B404F38C7AB4E28FC043E4AB --mojo-platform-channel-handle=3588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
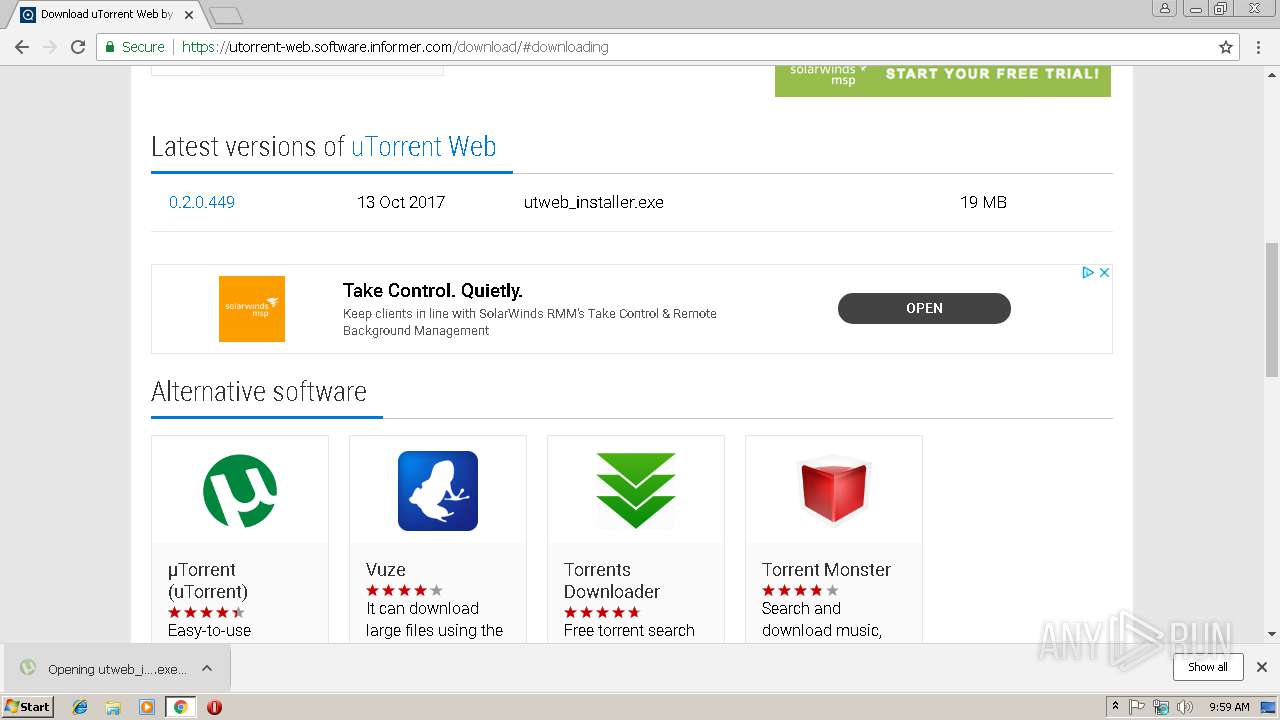
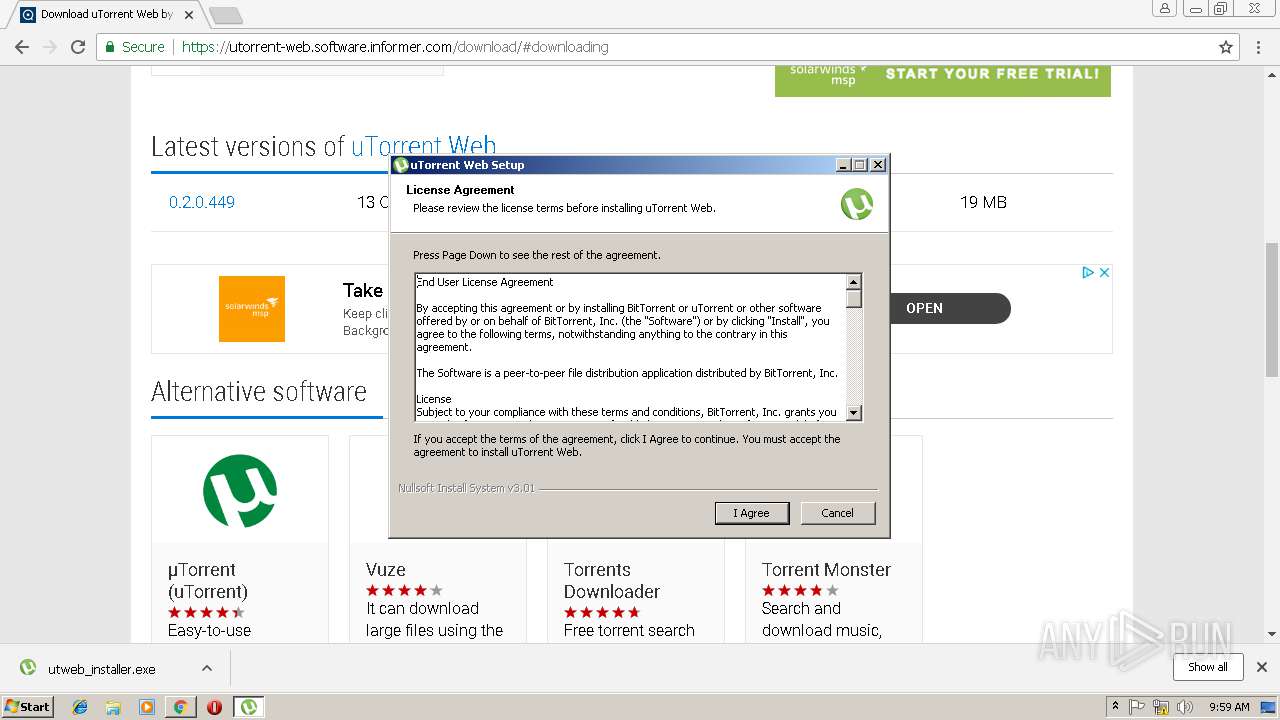
| 3380 | "C:\Users\admin\Downloads\utweb_installer.exe" | C:\Users\admin\Downloads\utweb_installer.exe | chrome.exe | ||||||||||||
User: admin Company: BitTorrent, Inc. Integrity Level: MEDIUM Description: uTorrent Web Exit code: 0 Version: 0.18.2.652 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=276349CDFD0799BCF6C37BDAF7D47659 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=276349CDFD0799BCF6C37BDAF7D47659 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\AppData\Roaming\uTorrent Web\utweb.exe" /RUNONSTARTUP | C:\Users\admin\AppData\Roaming\uTorrent Web\utweb.exe | utweb_installer.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Web Exit code: 0 Version: 0.18.2.652 Modules
| |||||||||||||||
Total events
2 221
Read events
2 034
Write events
179
Delete events
8
Modification events
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13194179903392000 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13194179903392000 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
22
Suspicious files
42
Text files
127
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\83f5afba-a556-4815-9882-34b2f247f92e.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF246d32.TMP | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a291d3ca-0127-4aac-a32c-3f4fb30885f9.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246c86.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF246cb5.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
129
DNS requests
70
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
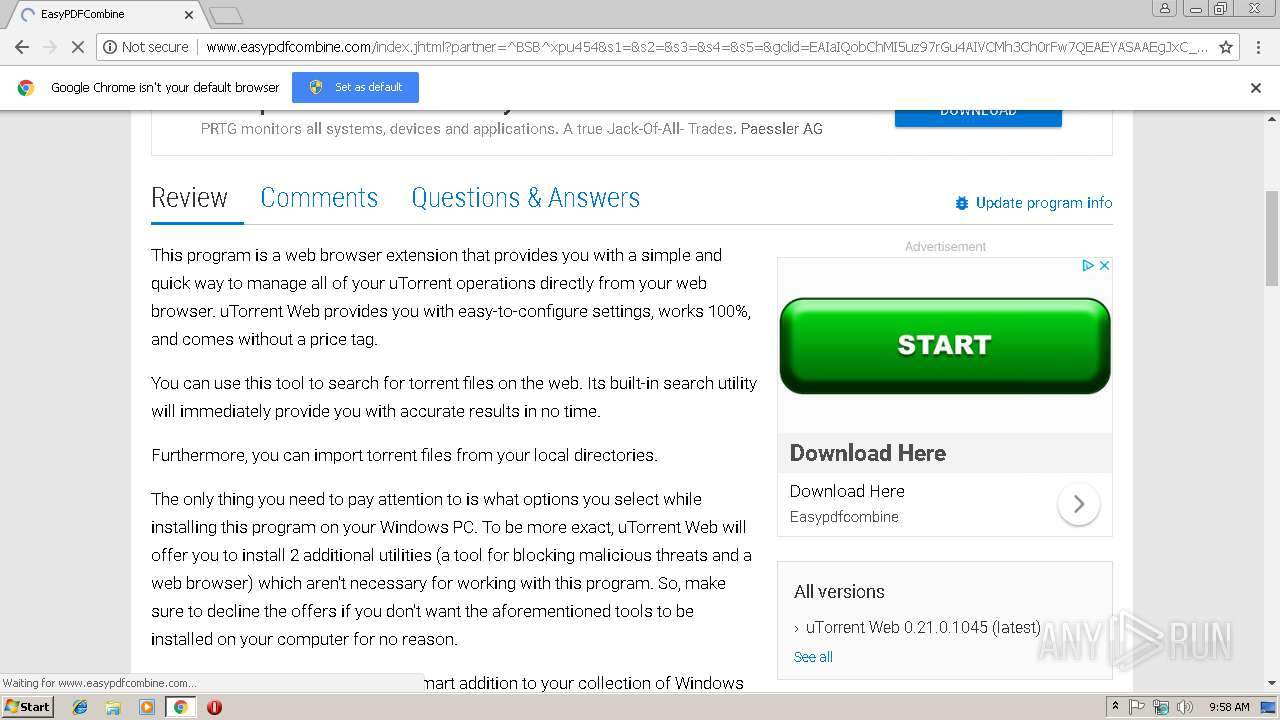
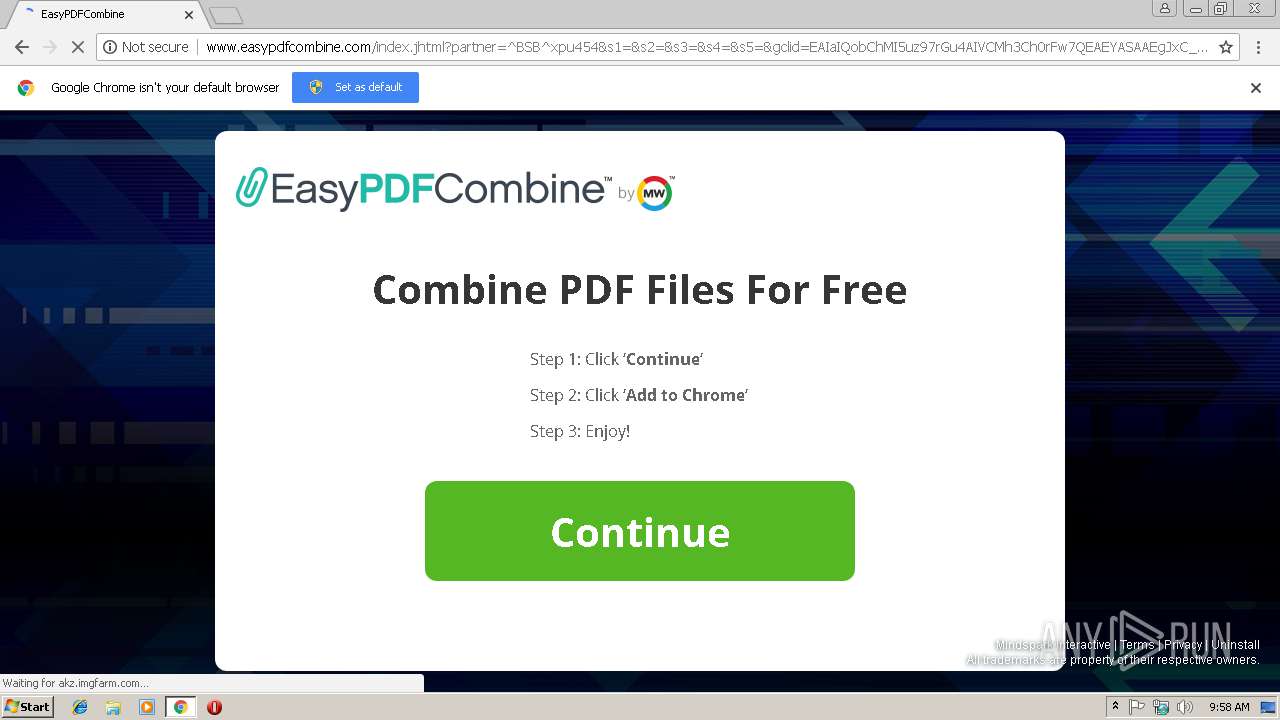
3000 | chrome.exe | GET | 200 | 74.113.235.138:80 | http://easypdfcombine.dl.tb.ask.com/localStorage.jhtml | IE | html | 2.20 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttDetectUtil.js | unknown | text | 3.81 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 74.113.235.138:80 | http://www.easypdfcombine.com/index.jhtml?partner=^BSB^xpu454&s1=&s2=&s3=&s4=&s5=&gclid=EAIaIQobChMI5uz97rGu4AIVCMh3Ch0rFw7QEAEYASAAEgJxC_D_BwE | IE | html | 45.8 Kb | whitelisted |
3000 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://www.easypdfcombine.com/anemone.jhtml?anxuu=B50D038B-34B1-4C10-8501-05944B763BEC&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe24.dub.jabodo.com&anxu=http%3A%2F%2Fwww.easypdfcombine.com%2Findex.jhtml&anxl=en-US&anxlv=1549706311692&anxsq=5&cookiesEnabled=1&pageLoad=1327&anxe=SplashLanding&anxr=891989056 | IE | — | — | whitelisted |
3000 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://www.easypdfcombine.com/anemone.jhtml?anxuu=B50D038B-34B1-4C10-8501-05944B763BEC&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe24.dub.jabodo.com&anxu=http%3A%2F%2Fwww.easypdfcombine.com%2Findex.jhtml&anxl=en-US&anxlv=1549706311529&anxsq=3&present=false&anxe=ToolbarDetect&anxr=184380195 | IE | compressed | 45.8 Kb | whitelisted |
3000 | chrome.exe | GET | 302 | 178.250.0.163:80 | http://widget.criteo.com/event?a=%5B48692%2C54320%2C54462%2C54317%2C54452%2C54447%2C54463%2C54450%2C54502%2C54498%2C54507%5D&rt=gif&v=4.8.3&p0=e%3Dvh&p1=e%3Dvp%26p%3D1&p2=e%3Dvb%26p%3D%255Bi%25253D1%252526pr%25253D0%252526q%25253D1%255D&p3=e%3Ddis&adce=1&lwid=da6cba87-85c4-447f-849d-94b729295a6c&tld=easypdfcombine.com&dtycbr=58201 | FR | — | — | whitelisted |
3000 | chrome.exe | POST | 200 | 74.113.235.138:80 | http://easypdfcombine.dl.myway.com/mirrorCookies.jhtml | IE | html | 93 b | whitelisted |
3000 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://www.easypdfcombine.com/anemone.jhtml?anxuu=B50D038B-34B1-4C10-8501-05944B763BEC&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe24.dub.jabodo.com&anxu=http%3A%2F%2Fwww.easypdfcombine.com%2Findex.jhtml&anxl=en-US&anxlv=1549706311511&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=B2D7D55F-8BD4-444E-8CCF-96182633235C&anxe=backFill&anxr=1681342396 | IE | compressed | 45.8 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/download/assist_21.gif | unknown | image | 6.25 Kb | whitelisted |
3000 | chrome.exe | GET | 302 | 185.31.128.129:80 | http://20787046p.rfihub.com/ca.gif?rb=32555&ca=20787046&_o=32555&_t=20787046&ra=REPLACE_ME_WITH_YOUR_CACHE_BUSTING | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 204.155.159.109:443 | hits.informer.com | WZ Communications Inc. | US | unknown |
3000 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 74.117.179.70:443 | img.informer.com | WZ Communications Inc. | US | suspicious |
3000 | chrome.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 74.117.179.74:443 | art-u1.infcdn.net | WZ Communications Inc. | US | unknown |
3000 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.208.34:443 | adservice.google.nl | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.22.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
utorrent-web.software.informer.com |
| suspicious |
accounts.google.com |
| shared |
img.informer.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
i.informer.com |
| whitelisted |
art-u1.infcdn.net |
| suspicious |
hits.informer.com |
| unknown |
art-u3.infcdn.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4012 | utweb_installer.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
4012 | utweb_installer.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |