| File name: | Ransomware.exe |
| Full analysis: | https://app.any.run/tasks/8aa2c49c-3200-4948-adcc-a74c62244b1e |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 18:02:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9F3BFD6CCA828C8AA52BB64175D1F969 |
| SHA1: | C64B16CABF5E1C61F2E62944C8AF6AC6401D83A2 |
| SHA256: | 5B7B0ECB3A5E00F75E1A1CDA76232457DA5952ABC448E010D6A6B0CDF19FDAB9 |
| SSDEEP: | 192:OOJJq+h2oygP8Xo77gwtD8a4W+xXYKCaHU2xRNUKYsIvrJuMB9lgz5tHPwmVmdkV:Jq9XBwtAaaxXD0oIFuMB9lgz5tHoc |
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 1220)
SUSPICIOUS
Checks supported languages
- Ransomware.exe (PID: 804)
Reads the computer name
- Ransomware.exe (PID: 804)
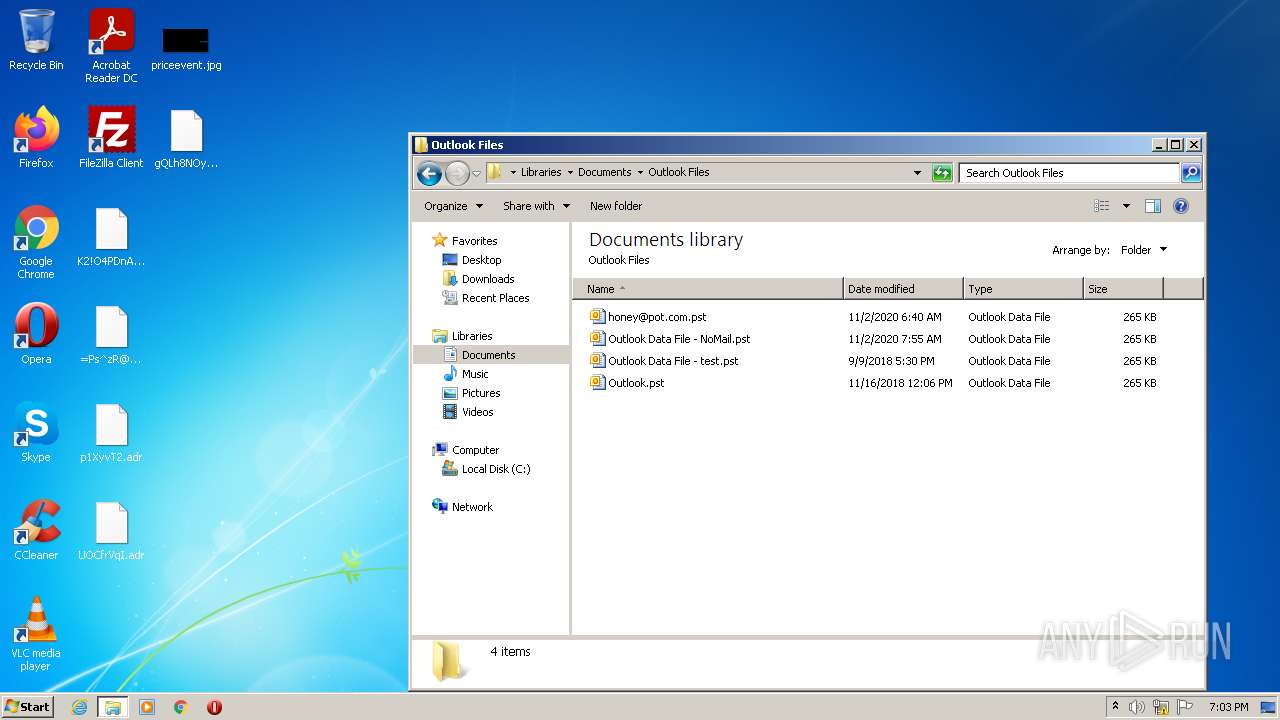
Reads Microsoft Outlook installation path
- rundll32.exe (PID: 1220)
Creates files in the user directory
- Ransomware.exe (PID: 804)
Uses RUNDLL32.EXE to load library
- Ransomware.exe (PID: 804)
Reads internet explorer settings
- rundll32.exe (PID: 1220)
INFO
Checks supported languages
- rundll32.exe (PID: 1220)
- explorer.exe (PID: 3464)
- rundll32.exe (PID: 2376)
Reads the computer name
- rundll32.exe (PID: 1220)
- explorer.exe (PID: 3464)
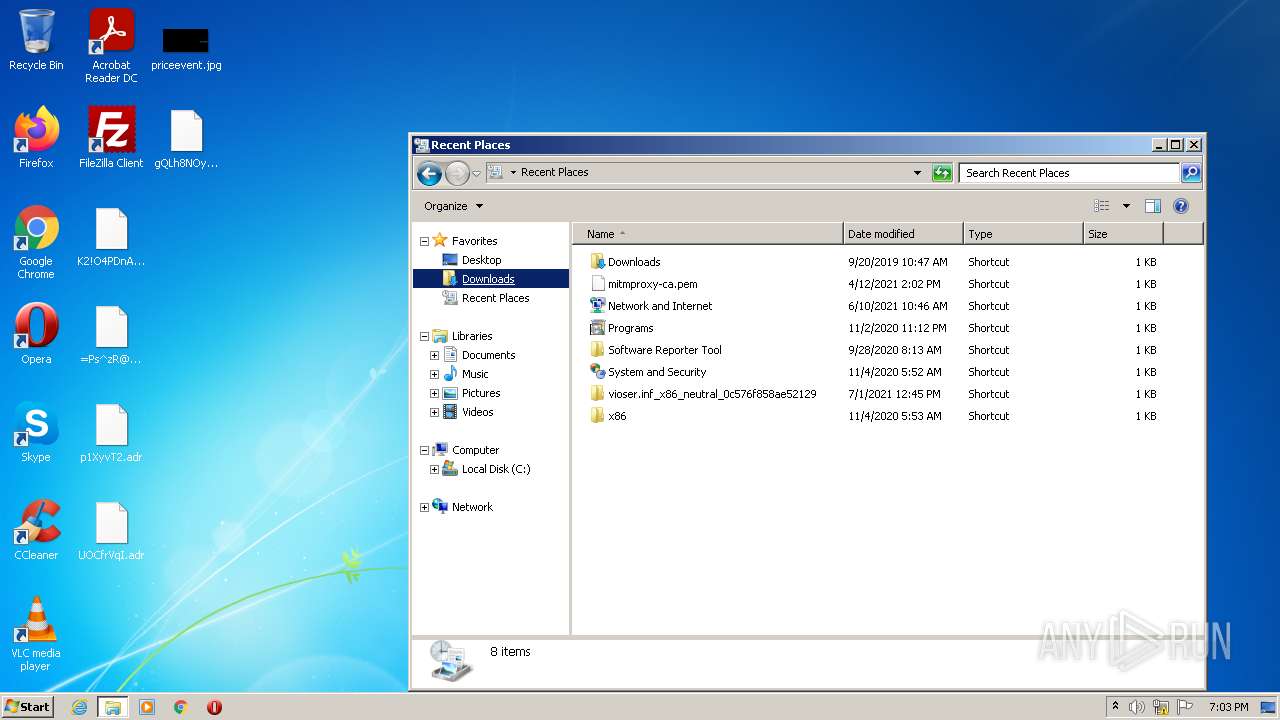
Manual execution by user
- explorer.exe (PID: 3464)
- rundll32.exe (PID: 2376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Ransomware |
| OriginalFileName: | Ransomware.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2016 |
| InternalName: | Ransomware.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Ransomware |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x46d6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 10240 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:20 20:00:53+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-2022 18:00:53 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Ransomware |
| FileVersion: | 1.0.0.0 |
| InternalName: | Ransomware.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | Ransomware.exe |
| ProductName: | Ransomware |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-May-2022 18:00:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000026DC | 0x00002800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.21054 |
.rsrc | 0x00006000 | 0x00000E98 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.43187 |
.reloc | 0x00008000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.94718 | 2757 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | "C:\Users\admin\AppData\Local\Temp\Ransomware.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Ransomware Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1220 | "C:\Windows\System32\rundll32.exe" javascript:"\..\mshtml,RunHTMLApplication ";document.write();shell=new%20ActiveXObject("wscript.shell");shell.regwrite("HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\RunOnce\\adr","C:\\Users\\admin\\AppData\\Local\\Temp\\Ransomware.exe"); | C:\Windows\System32\rundll32.exe | Ransomware.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
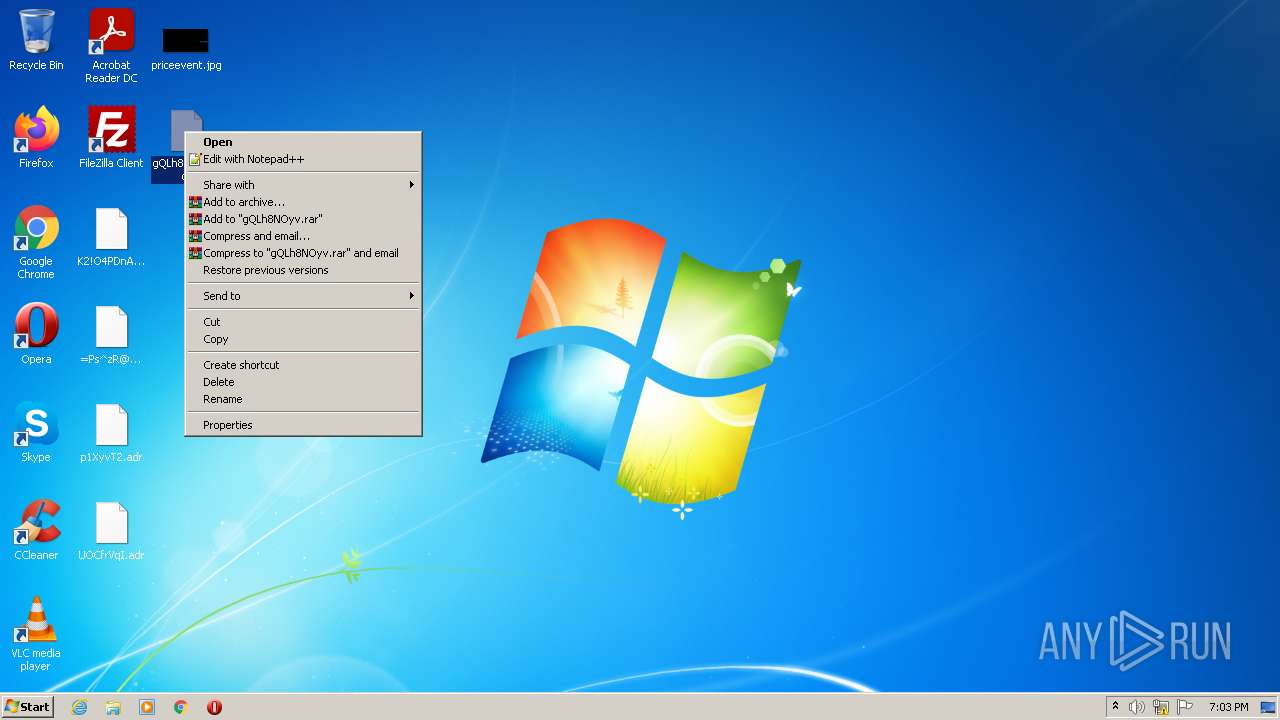
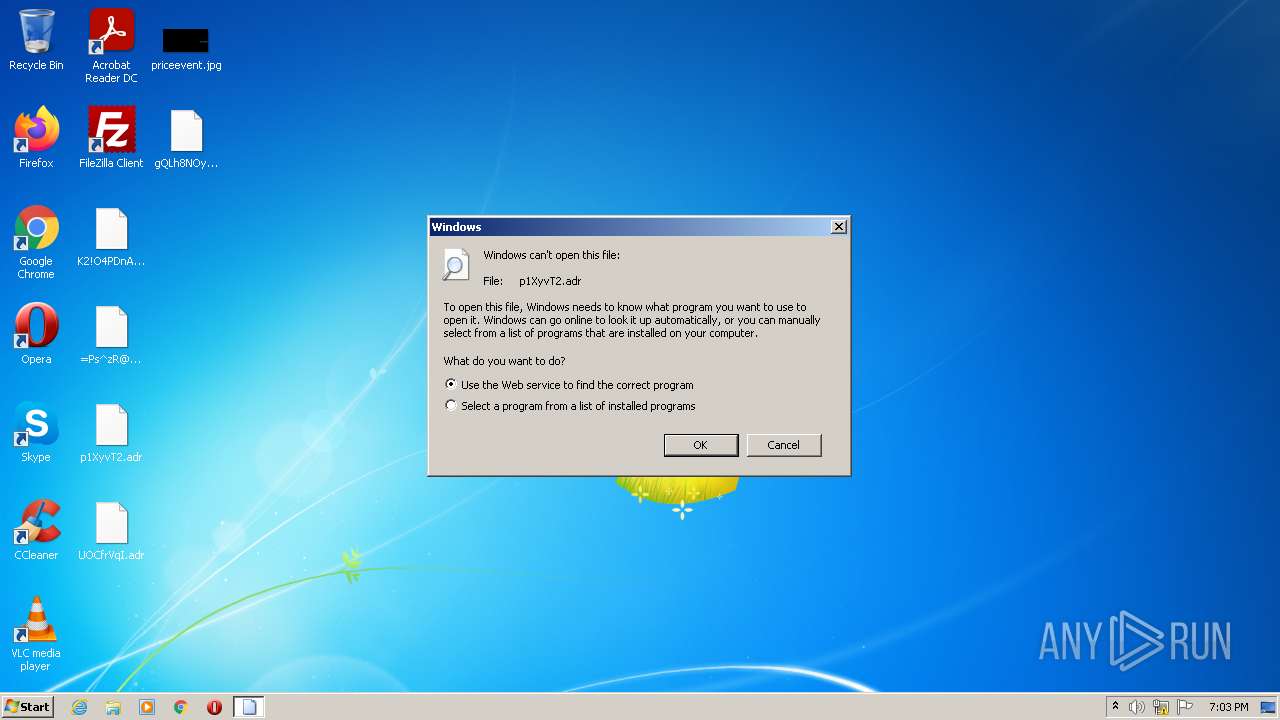
| 2376 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\p1XyvT2.adr | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
644
Read events
627
Write events
17
Delete events
0
Modification events
| (PID) Process: | (804) Ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (804) Ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (804) Ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (804) Ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1220) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1220) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1220) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1220) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1220) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | adr |
Value: C:\Users\admin\AppData\Local\Temp\Ransomware.exe | |||
Executable files
0
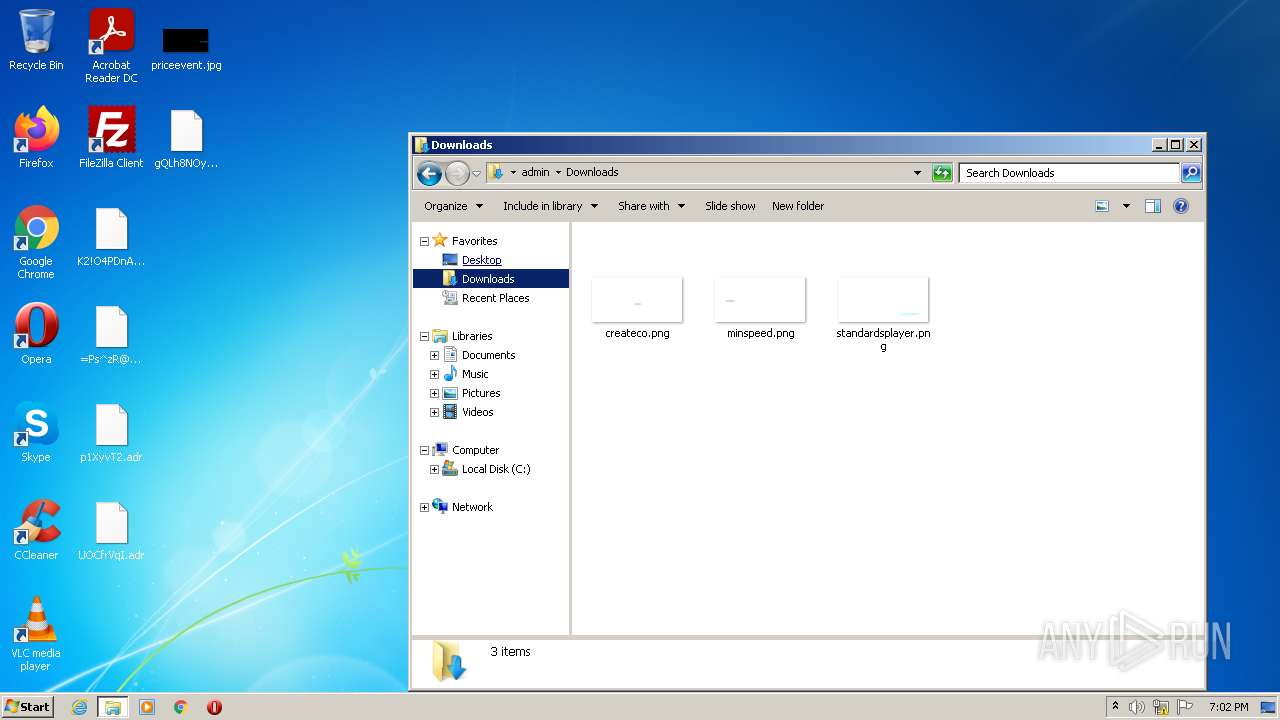
Suspicious files
6
Text files
3
Unknown types
1
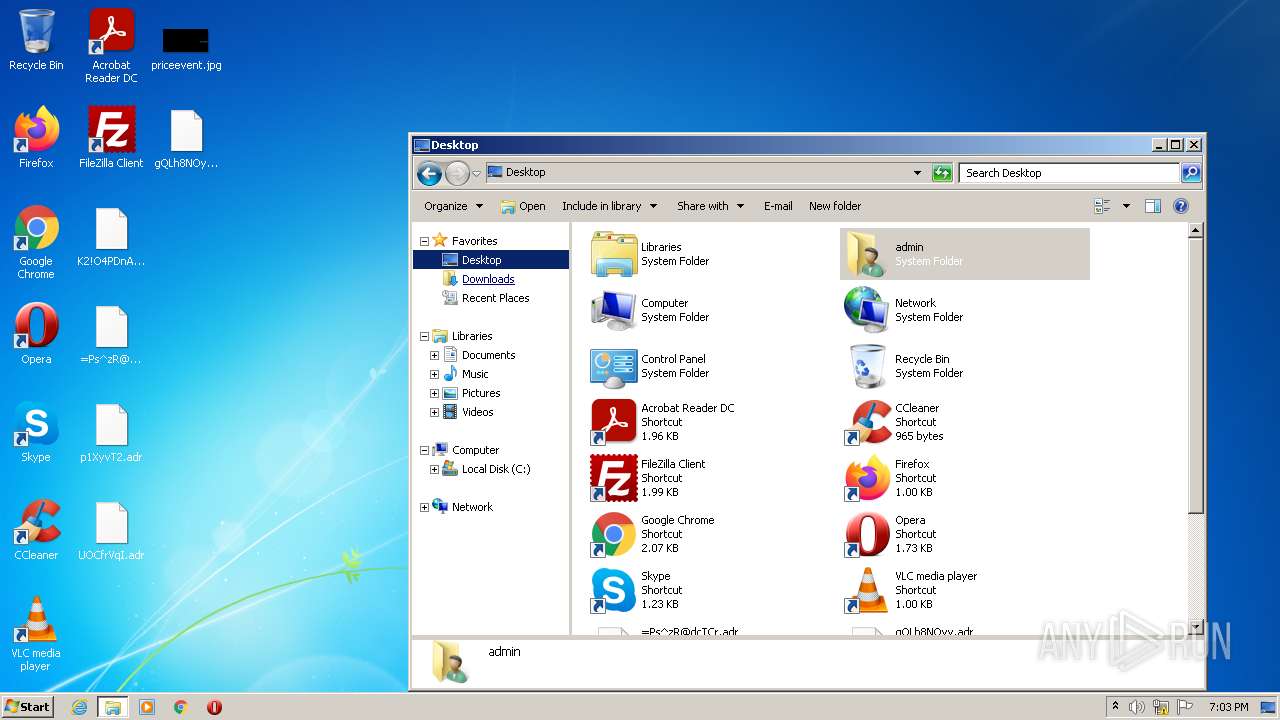
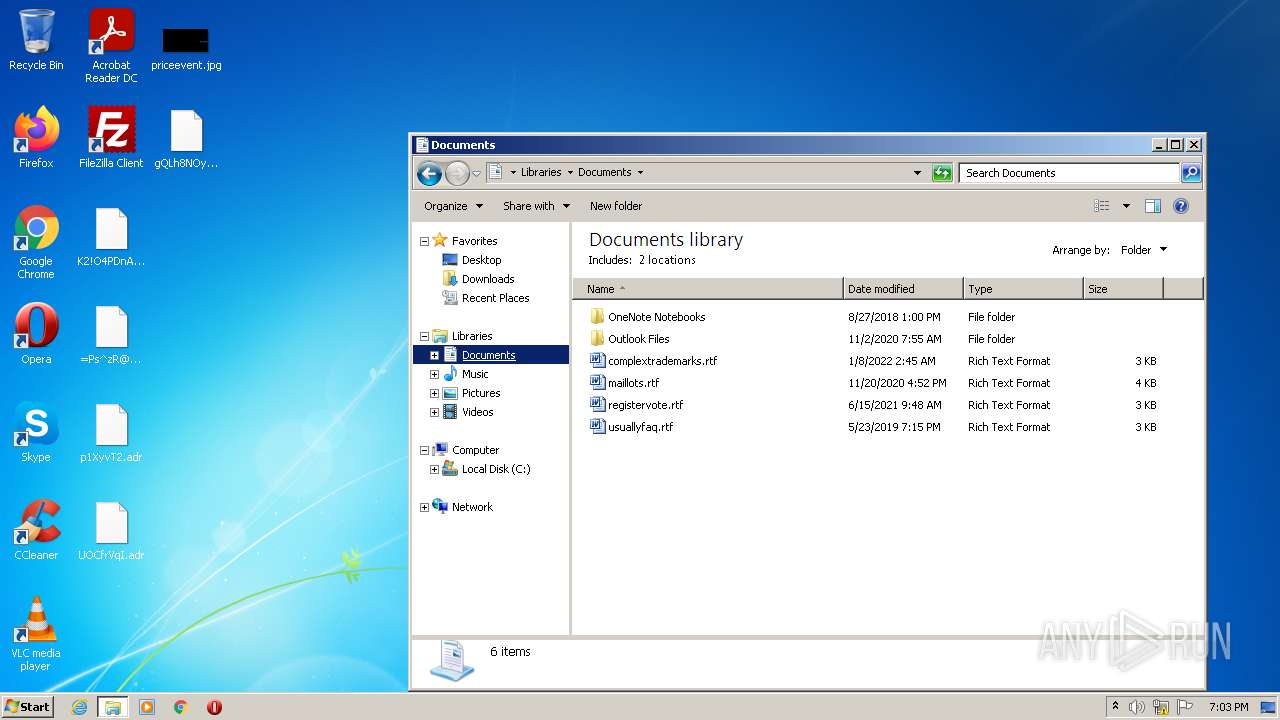
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 804 | Ransomware.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\7d25443fb0d0d0ba922fbf8118fef114_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:— | SHA256:— | |||
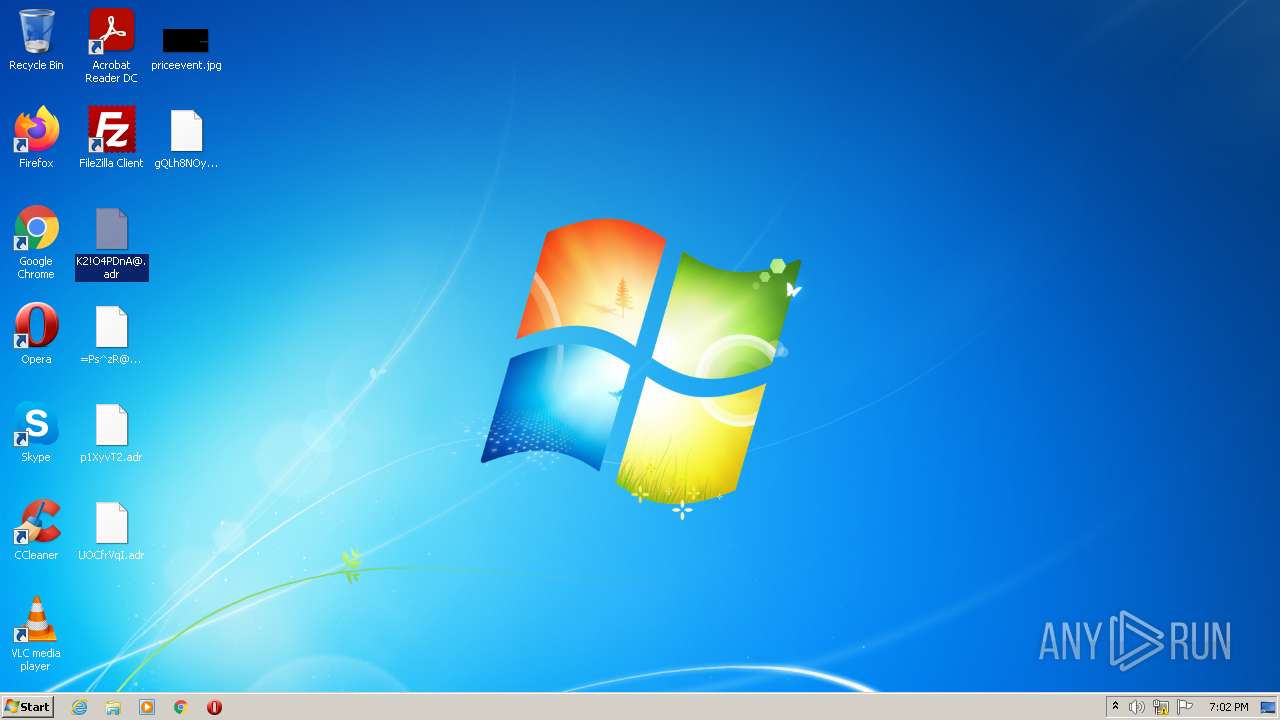
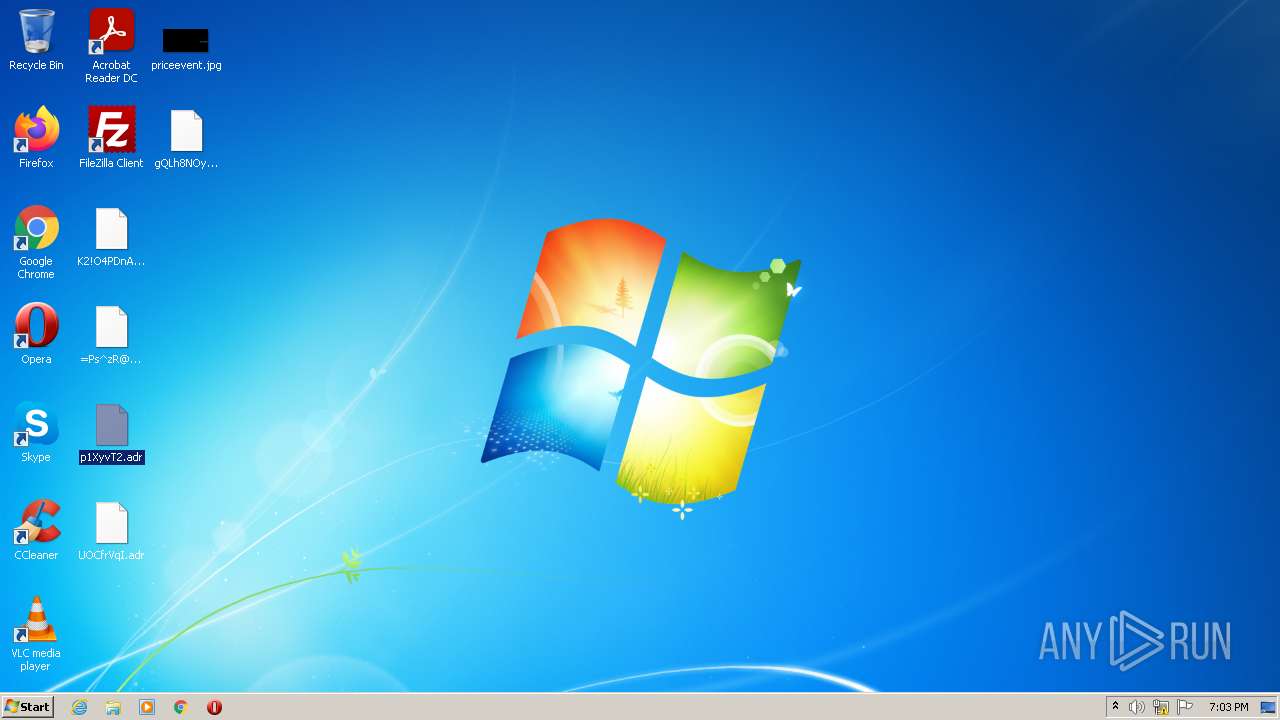
| 804 | Ransomware.exe | C:\Users\admin\Desktop\gQLh8NOyv.adr | binary | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\AppData\Local\Temp\sendBack.txt | text | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\AppData\Local\Temp\secretAES.txt | binary | |
MD5:— | SHA256:— | |||
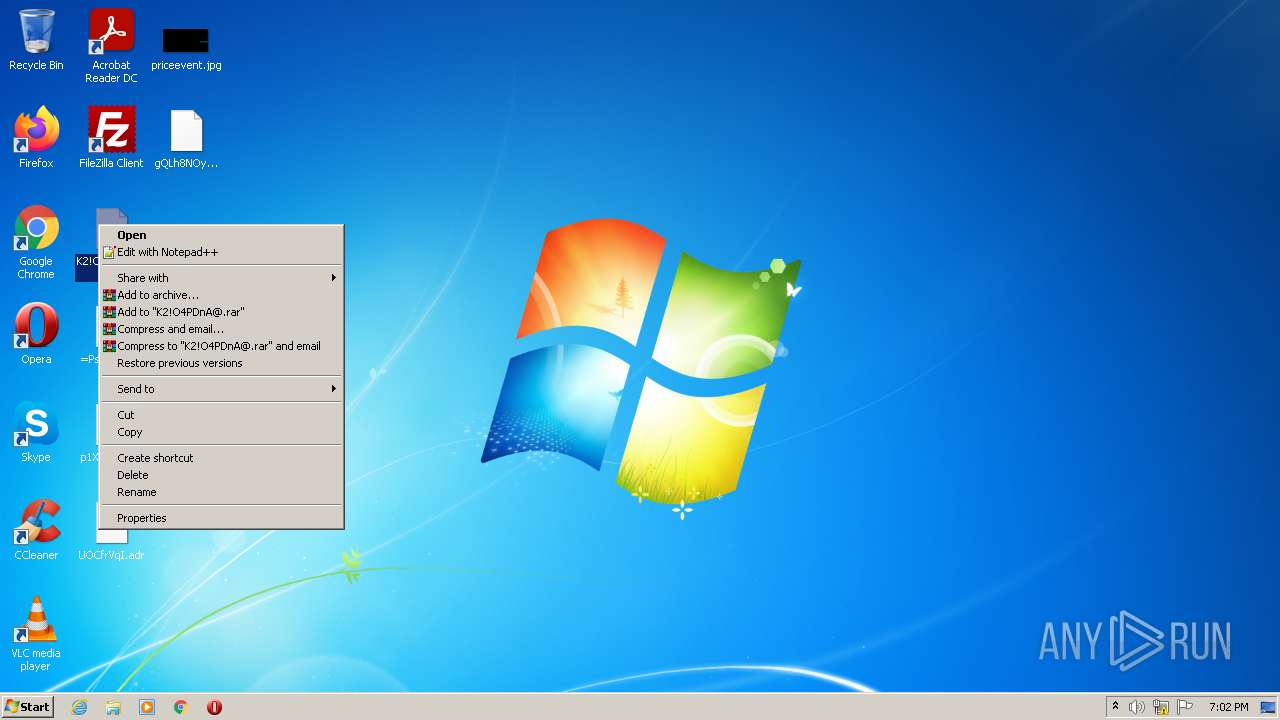
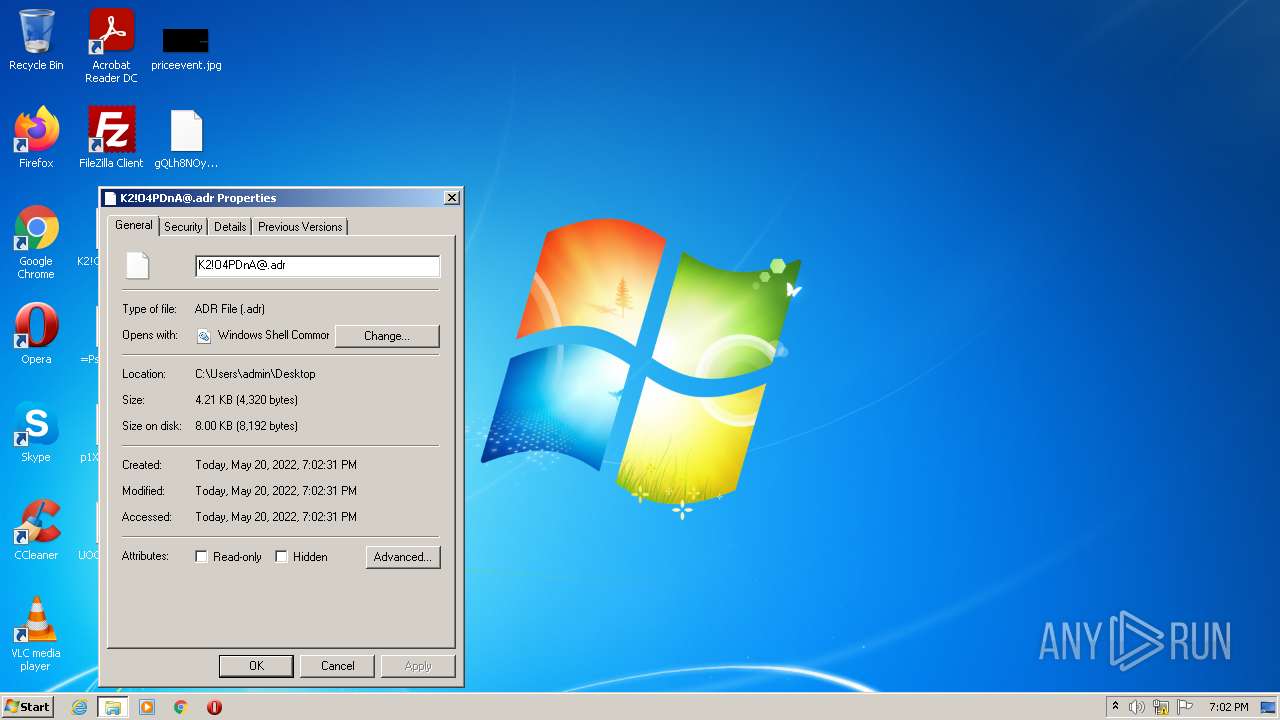
| 804 | Ransomware.exe | C:\Users\admin\Desktop\K2!O4PDnA@.adr | binary | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\AppData\Local\Temp\data recive | text | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\AppData\Local\Temp\secret.txt | text | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\Desktop\=Ps^zR@dcTCr.adr | binary | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\Desktop\UOCfrVqI.adr | binary | |
MD5:— | SHA256:— | |||
| 804 | Ransomware.exe | C:\Users\admin\Desktop\p1XyvT2.adr | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report