| File name: | testuuu.exe |
| Full analysis: | https://app.any.run/tasks/08e82290-be94-4d8c-a79c-72935a46ebb1 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
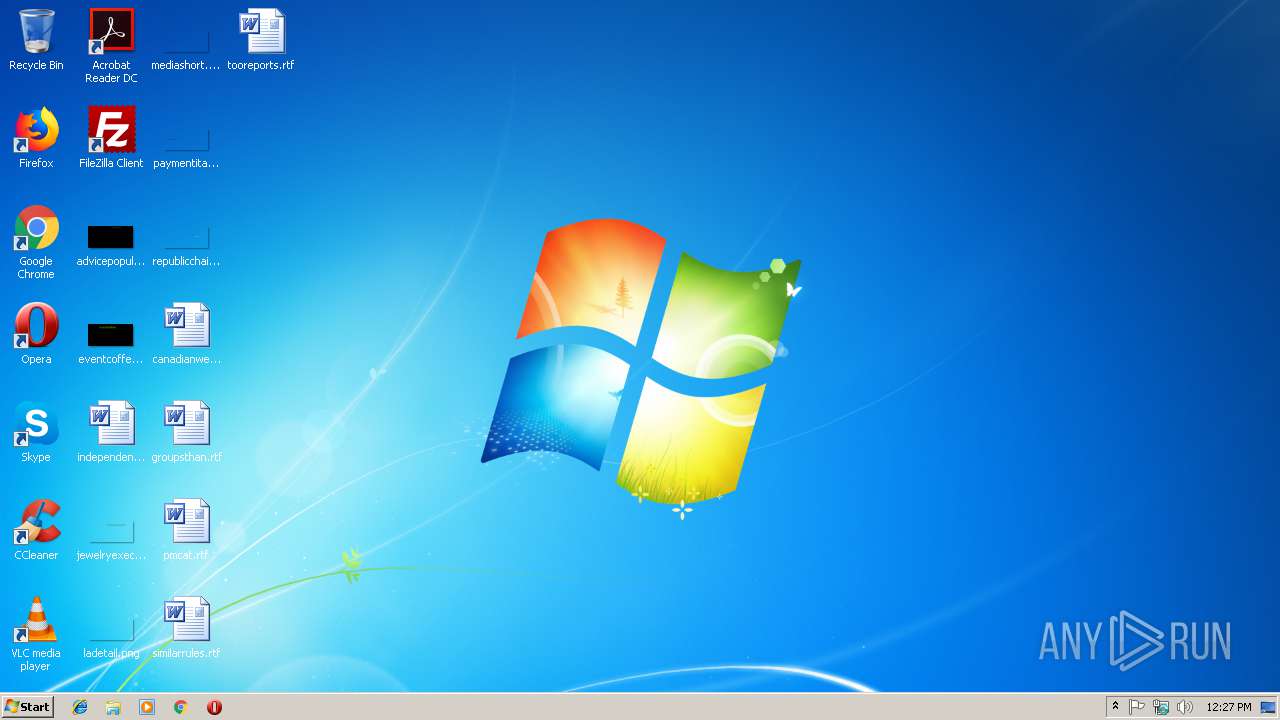
| Analysis date: | January 22, 2019, 12:27:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C70CCCC83EDC3F6C757C267CD08D4687 |
| SHA1: | 0D747483B316A7125AC8C4EADD365FA6D914C380 |
| SHA256: | 5B73019C232ADBD1627B986BFC476DE96C230AD54A9A014932F3F32D814FC744 |
| SSDEEP: | 6144:xuBE0jQFX+/tHjxsyg7BoHgKyWpY/gQpImg9R:xufjWXKtH27CTyK4fpIm8 |
MALICIOUS
GandCrab keys found
- testuuu.exe (PID: 2844)
Actions looks like stealing of personal data
- testuuu.exe (PID: 2844)
Writes file to Word startup folder
- testuuu.exe (PID: 2844)
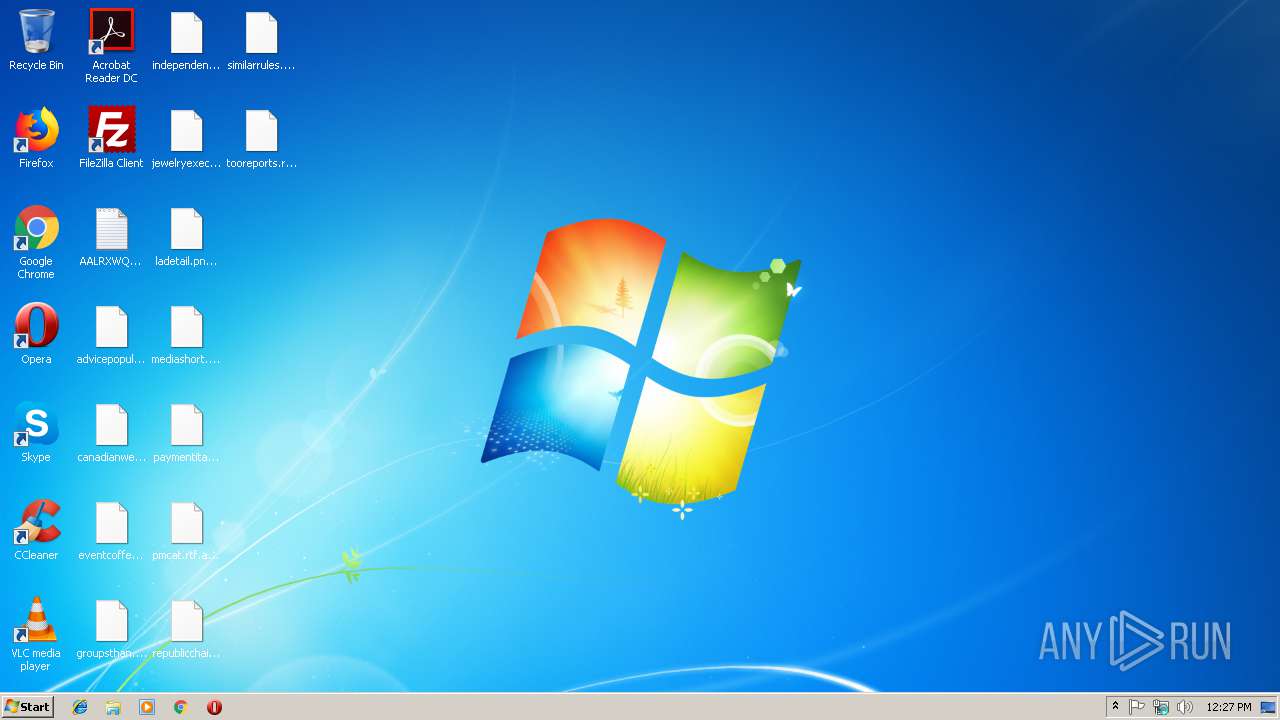
Renames files like Ransomware
- testuuu.exe (PID: 2844)
Deletes shadow copies
- testuuu.exe (PID: 2844)
Dropped file may contain instructions of ransomware
- testuuu.exe (PID: 2844)
Changes settings of System certificates
- testuuu.exe (PID: 2844)
SUSPICIOUS
Creates files in the program directory
- testuuu.exe (PID: 2844)
Reads the cookies of Mozilla Firefox
- testuuu.exe (PID: 2844)
Creates files like Ransomware instruction
- testuuu.exe (PID: 2844)
Adds / modifies Windows certificates
- testuuu.exe (PID: 2844)
Creates files in the user directory
- testuuu.exe (PID: 2844)
INFO
Dropped object may contain TOR URL's
- testuuu.exe (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:17 17:31:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 136192 |
| InitializedDataSize: | 210432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf6d0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.5.6 |
| ProductVersionNumber: | 5.2.5.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | IBE Software |
| FileDescription: | Contention One Vs |
| OriginalFileName: | Safer.exe |
| LegalCopyright: | IBE Software Copyright (c) |
| InternalName: | Safer |
| ProductName: | Safer |
| ProductVersion: | 5.2.5.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2019 16:31:47 |
| Detected languages: |
|
| CompanyName: | IBE Software |
| FileDescription: | Contention One Vs |
| OriginalFilename: | Safer.exe |
| LegalCopyright: | IBE Software Copyright (c) |
| InternalName: | Safer |
| ProductName: | Safer |
| ProductVersion: | 5.2.5.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Jan-2019 16:31:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000213E1 | 0x00021400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6802 |
.rdata | 0x00023000 | 0x000078A4 | 0x00007A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.16623 |
.data | 0x0002B000 | 0x000036A4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66505 |
.rsrc | 0x0002F000 | 0x0002A358 | 0x0002A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.9376 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01596 | 957 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.84011 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.04327 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.31284 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.15052 | 10344 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.02131 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 1.82697 | 62 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 2.14675 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.93257 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.14675 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OPENGL32.dll |
SHLWAPI.dll |
Secur32.dll |
TAPI32.dll |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2744 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\testuuu.exe" | C:\Users\admin\AppData\Local\Temp\testuuu.exe | explorer.exe | ||||||||||||
User: admin Company: IBE Software Integrity Level: MEDIUM Description: Contention One Vs Exit code: 1073807364 Modules
| |||||||||||||||
| 3252 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | testuuu.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
130
Read events
96
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00610061006C00720078007700710070000000 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001009D9360FC02FA8EA909DE835E69189F79AF8B556FA34F5B1928F078B3A671284AFD720B0E00E4FC2CF43C51E24E2A8A0C0BDD540F99F8B3A9BE9EBF3F66D60CF12170EF61188873788AE5199AAEA4D5104E86D2212D2AC6AB59F2163045F4082A00CEAE9AD522B3EDC0D8D4CA1C344EA25CCA8F0EDF2FD094FA9E360985E224F9074591C925F8FF1123CB2BAEE49292E409D30D59BEB64322A4252AC71F2D97590B3236CFC0067FB6B5F47C85F67A927CBC986F1AD3797D6FF3EB72F0E1A3C0233A0F49710E9605625DC8DDF5F38542CEF98AC2EB165C9842D1108DF7C7D91FA2066BDBB42288CC4885C4FE91C4C9D7A9933AE8700703000E68FC1D4A121871D9 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000F57E8942A7DB9F3105094924338CF8C13994966712F64767446393C32FF904A26BDE1622DBC4265BDB7EF8A8C3AC3D6628F58F2A85EC5B2C927CABCBAD2D64C93376053C5DD3E8E9CE39220E839ADF3C0BC581B3CB5F478629ECB675022532E2ED1495ABCEE73BD9DCCE3A09AAC80066FB0DB504E887BCEA061C01B95BE517D378105C93EC9DC15E961EBA91CCB83DD4A1FB8CF38825223292F9240FA73AEE4669B467CC5B6E7784C383895B32FB84D8B2E21BFBCD48764F7E416C06093AB6CE68FDC6E853BFC0E40F58DD90CD8262778D5DE35BD642DF477038EEDB530A8FDAA4AD26D8C4B5A7251F04C0A4826F020441005E383D837D6E9988189CAFDDC400F902608F3493318FB1711E5FF2F9462ADD11849630E3D50536371802FC73EB3480A8FE2655F61A7FA1A449A1B45CE520482C62F56FA0CA961CC985653D4421F8691B60FFF04B55EE48C117FF32D6B44C94BA203DD7D461E1BA80350569D8CF33387B4946D66109D3D936B0F390A6FB72F406A4A211542F80E87A5DF1DE9DECDB35352978839603AAEBBC58C2FA617D82D71392B7C0B1F95DAC550B9908DE9803C901E9D24238D4E194147A17766AE4E6322476D4BD3217AAEE4633D9B0A72DD839B25264A3059D14F69D8180CBFA41689226A0ABE346EE7FBAC3B52510EF6216B72D3691A927190FF8B9C60934BEA4D3D5FE445AF05D513D2E4E1F4031CB3F08872DA173079A66EF8AA9E24AC319C714FE781FB8757FC9C80CA919C42E8A4D43A992AE0FDDB3263C760D39F54729F83FCA26E9BD6C9A6E21273DE0F31F939792BBF16DB83492FF528906E34139F4AFCA94BB8A95FDCF9816F1F4560E8C7A120E534C6B3B3C0CD630021576C56FE8BA620392FBAFC40DC13A2716E0DDAB46E7F13C81A2AA3ECCA541857E55ABD6CDC26374765A8087924612E21A9A04C1B3FFB9190B2D171CEB67D14A3E44D499B61FA35A2B3B0D7F619E28B22CFF1C0CEA1FF6B2A686A117B5765AA0BD36FEE80F479D8A1A75C681E70E8466394F3BB30A90464A7FF23578BFA13BC7DA38B66B3F7D9F323E37798069D3A7E312C8FB4B425EC65FEED1E8C377A009F1709169DA0D2B637D1337DF4050962B12A6B31903D89E783701729C003D2239C22177F2ED150AAAA6A4D5A14720C5DBB83B03EF55532B3518C5E42924821C754802BA41B3F45EF1A2F0FAFEAE4602E005A14D7C020D1769B1B749A6C2AF3563C3EC45B180CBC3F9DD7B170BF3E56A744CB0DD809AA68354DB9D76BA2765EA45B6AEC36D464B9666F8B638587ADC6145B6625BA227044D8A7F5566F3378775E01B5CDD3B97E404DED5D55239E3C2752E2EDF07FA25CB151B900803E47141DF1D1FFE981BE9B6A9C35B86887366C781A7F00C8618F3E676888E181F026E86D3160A573CD63B298627D90D267F3E990B25B3811B2079E371FFE76B3F3DD831CB3342EAF4E6736C727DD8B944732141CFA19BB22CFC5C5732E3769004086881C46296FF12A28B0A8332661EFA53D0A3EC4CFBB609CF68210DE1D97F8B5F7BDBA8D089C13F08DDE128C06408875AFE006CAA435169C21718ED894879FE37C8BD174010E4E2A5845FE316360A16CC151A4A8D360086CC69D9A0643C43BB35F0BC1E438E8211D0AAC0103E771D14C75AD9AF2E7F6D564C02363EC15D5E9AE8D9255C970ADB2052A90BDAED51A5B6189E0434300B4F1DB1DC0137A85914B09DED55D395920CC26C41FF9E78C627D55EA16079CF40004051BC40DC2F745ED2B326E4B9EFE57D4FAC953357C17419276C625F16630339139657143231F34257EC5583A1A899B25CFE8D867D63ADE5A7430A2772643A88B4176359B0C85A4A7ADFF7FA45B3F28F1DB07E74136E2BED50CD96B48FBEEB6052396F9839B6C7EC758C16423E9AFF5E2848A8EEE180C5DF28AA9273D098C46D1B03F18E15E6D4EBAA84328646BA9FB9285FDB6CD131AD7B7E4F3B731E9B337B6F13DA80FF363A4FEBF468C64FC1A1E854BED541561E75CE0C2FD96095D4ED5FE0516B6DD39CDD4458B36B19D226138F1A7E2F3C97787646C04F2F60D5FACA0070858CE8E96DEA6B385C54006B0B8FE4DC4F30A8B3BDE983BA0A362ECCC54AA9BBF971DA20FEEACBE81045EBB652A82984C7DF857D031F84BD3F0C9CC6067A5B8B566ADFF9CB47ABF78E5C8073A9A83864C1E161C32BAB94B759599AC35BFF76D8423BA81857D7E5AA6ECF7BF90B746D9368440613A8BB8E1864BB0F5B676B657ACFE06A097461BD93C430B854C97B145E870F67C01C8B25377ACFE8B1FF4EB40A5B218FFB76695F868D1EFC72E6748DCEA2AC6DE9006BC0F2CA020FBB913BD800CAB3B87C8F08AC1EA9504B9764BBBAD71AA425B67708B8DBB9 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\testuuu_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\testuuu_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\testuuu_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\testuuu_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2844) testuuu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\testuuu_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
424
Text files
323
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | testuuu.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.aalrxwqp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\AALRXWQP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2844 | testuuu.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\AALRXWQP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | testuuu.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | testuuu.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2844 | testuuu.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |