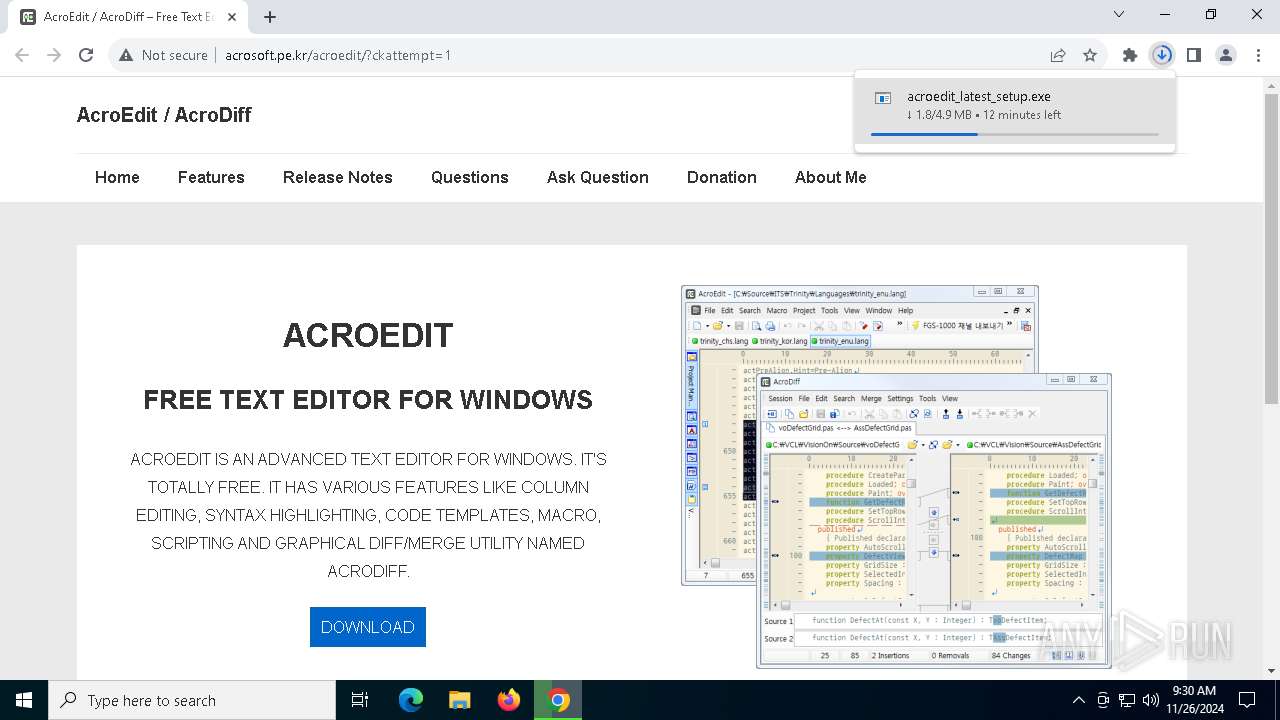
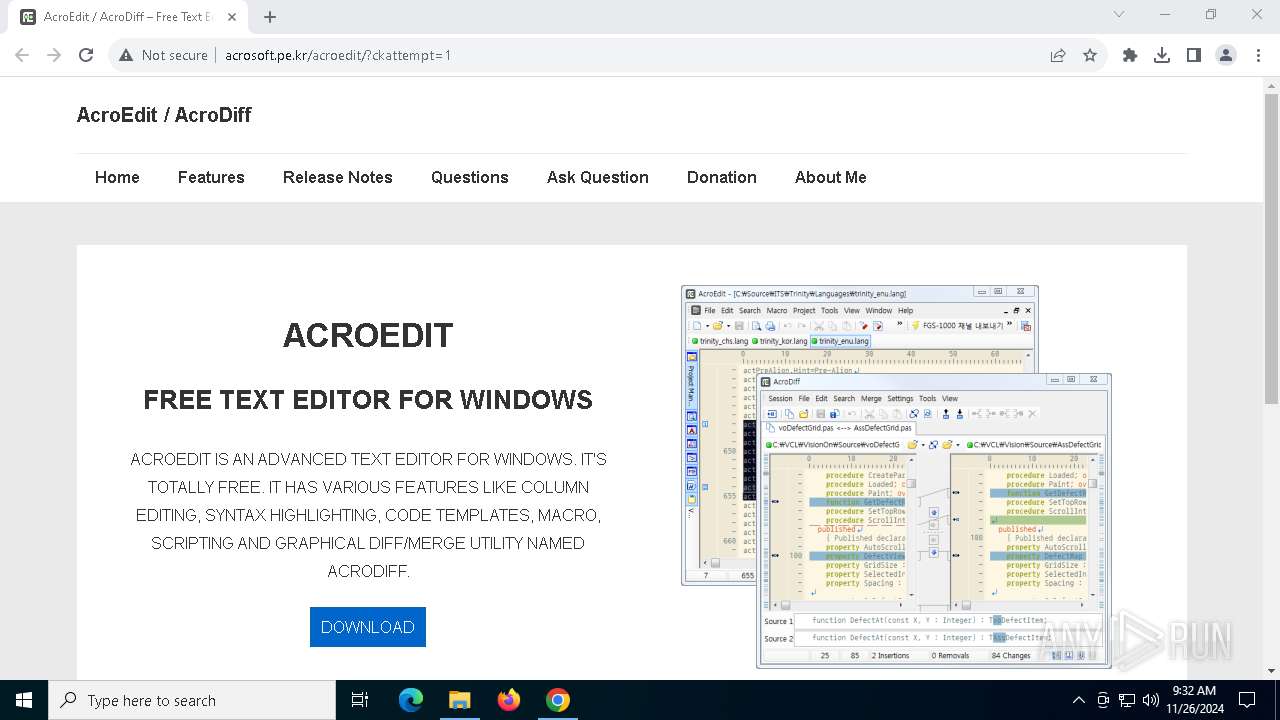
| URL: | http://www.acrosoft.pe.kr/acroedit/ |
| Full analysis: | https://app.any.run/tasks/8cdf2f25-e0db-4729-a985-07778045239a |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2024, 09:28:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 65307566B41B7D119DB924FDC69E8D73 |
| SHA1: | 8E2504DAC95E2AE01F42A3B22BA6206E67E14642 |
| SHA256: | 5B6228680F4183F344608181071A73887EAA819709DE02903E16B015D1696B0D |
| SSDEEP: | 3:N1KJS4PYZ7aEGXbBQKn:Cc4w9aPN |
MALICIOUS
No malicious indicators.SUSPICIOUS
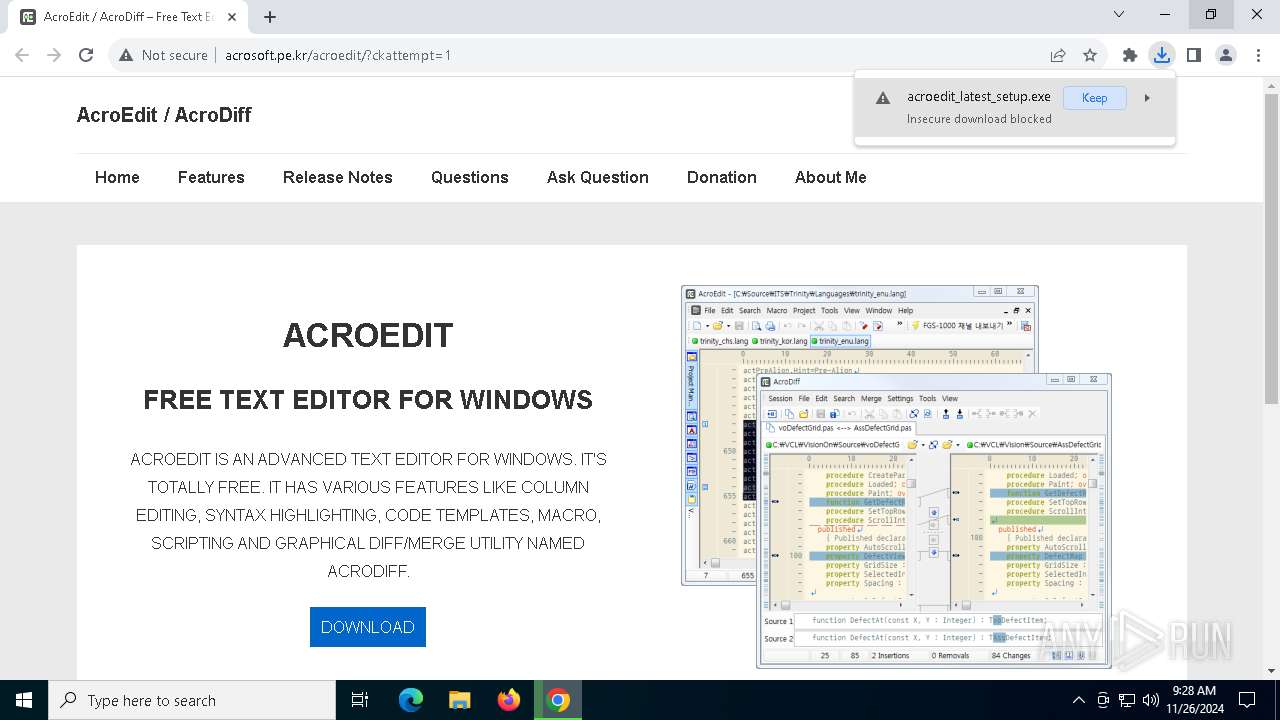
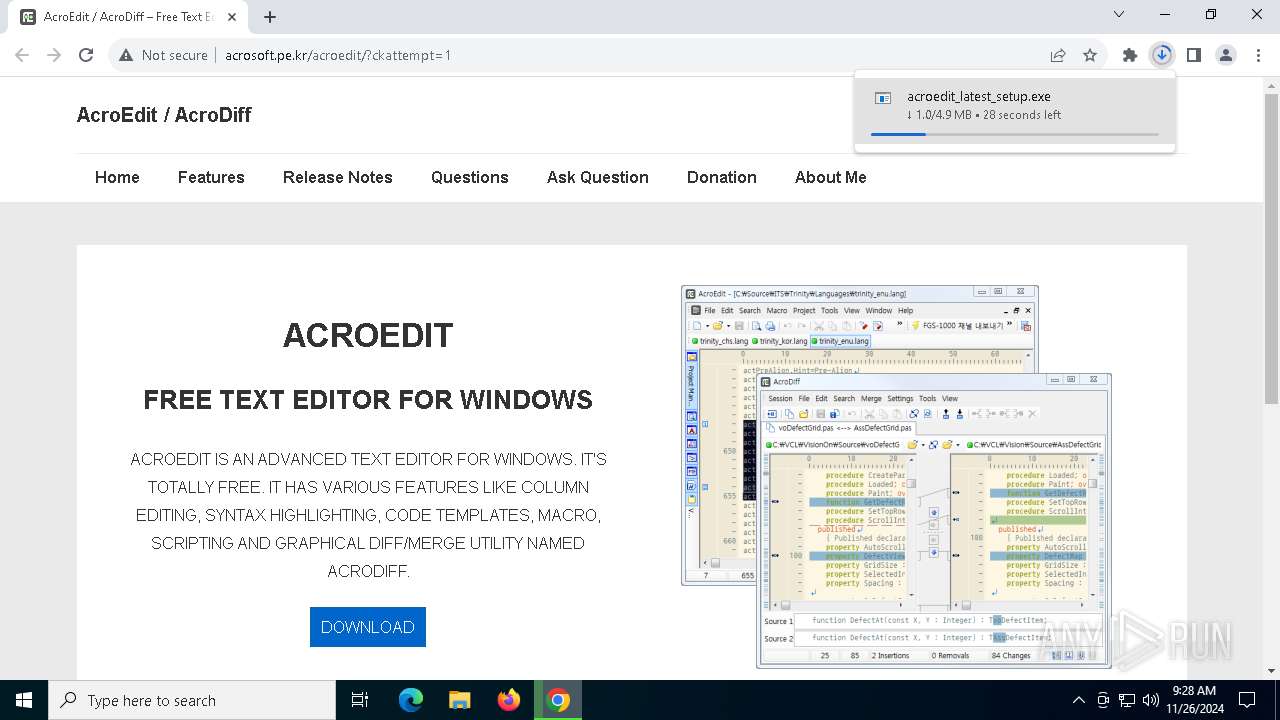
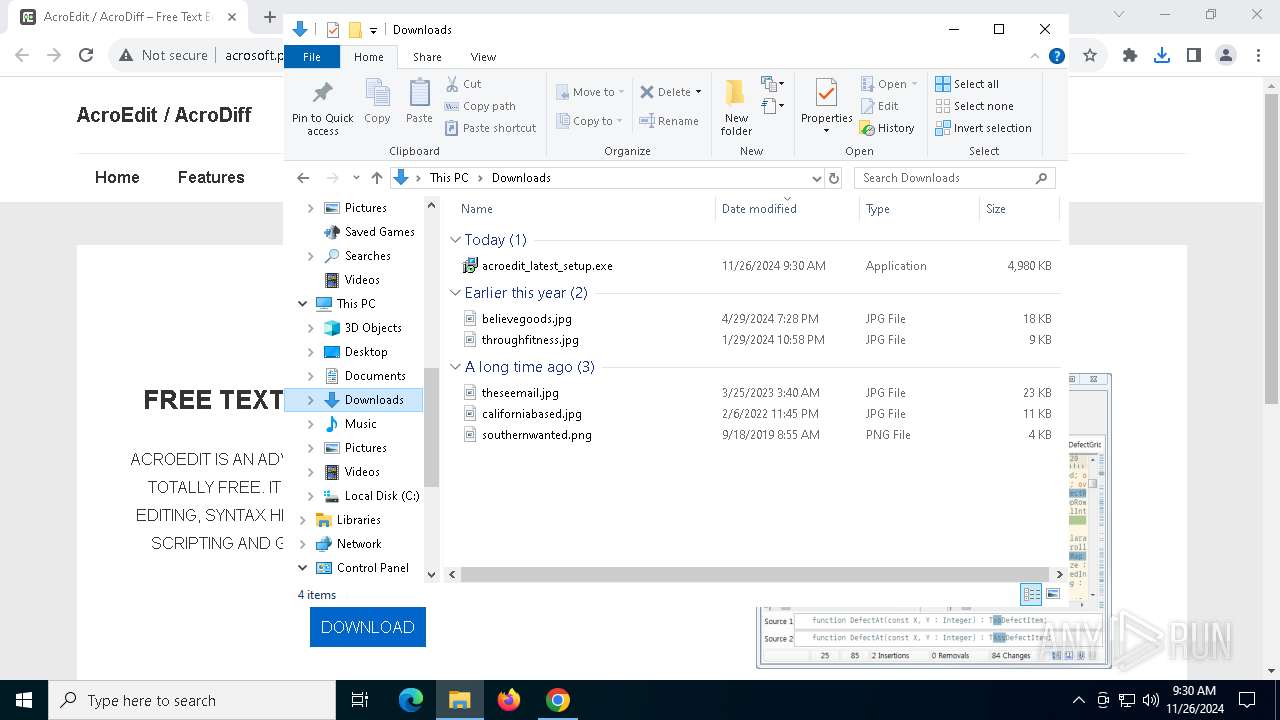
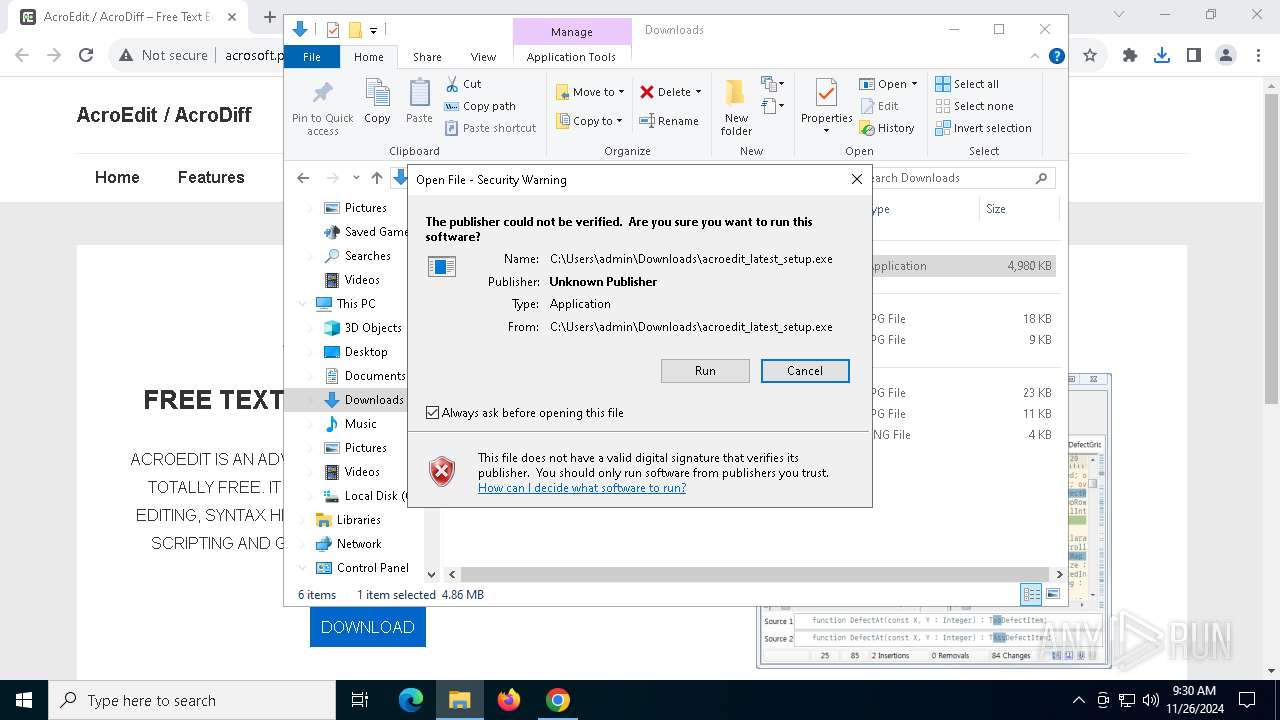
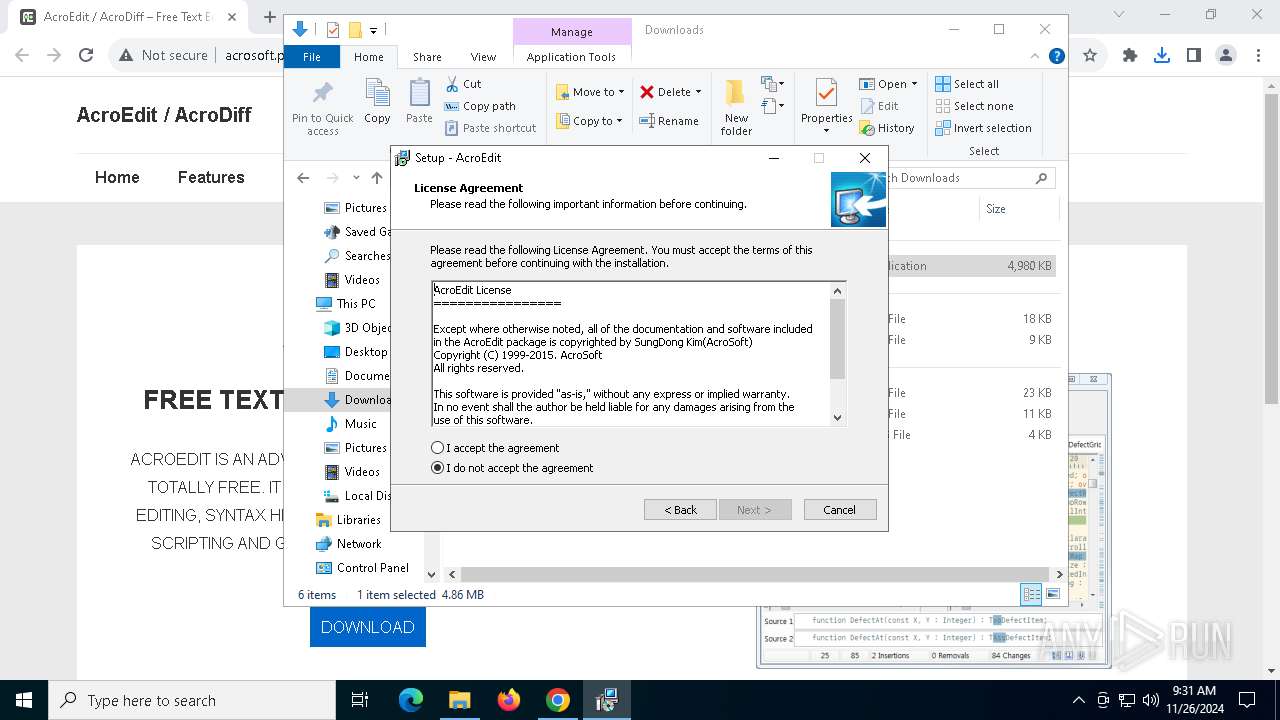
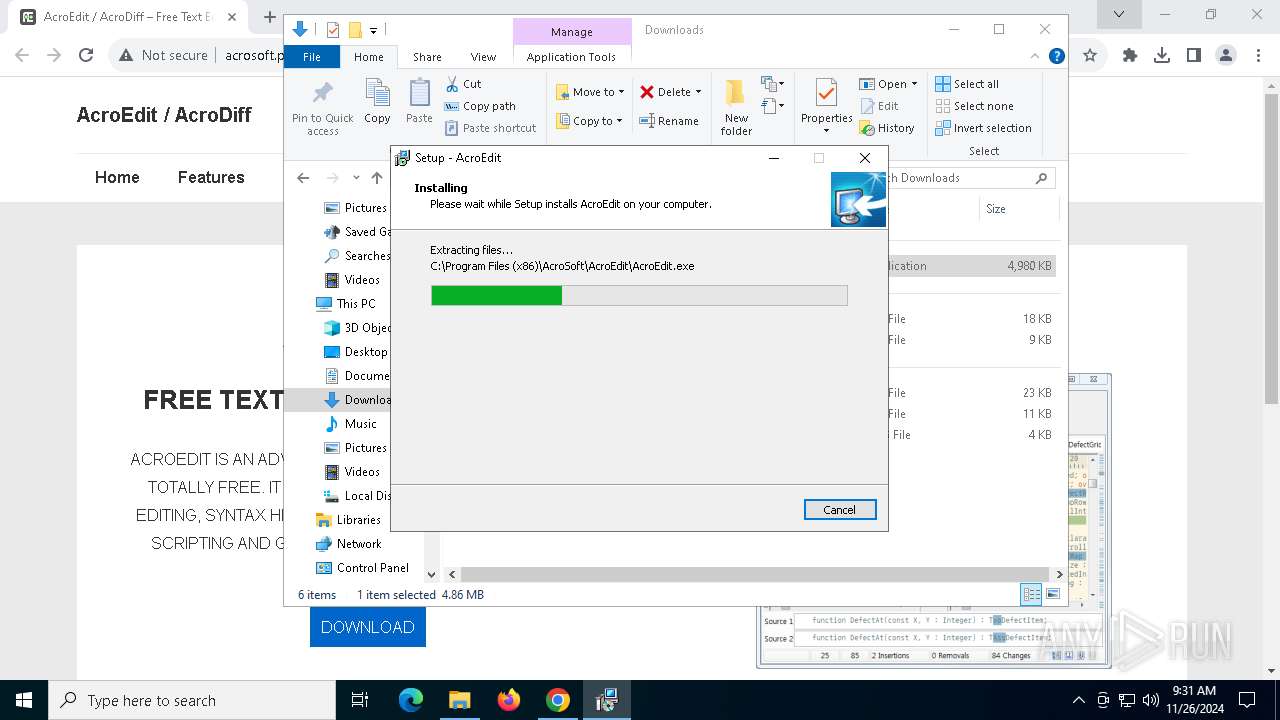
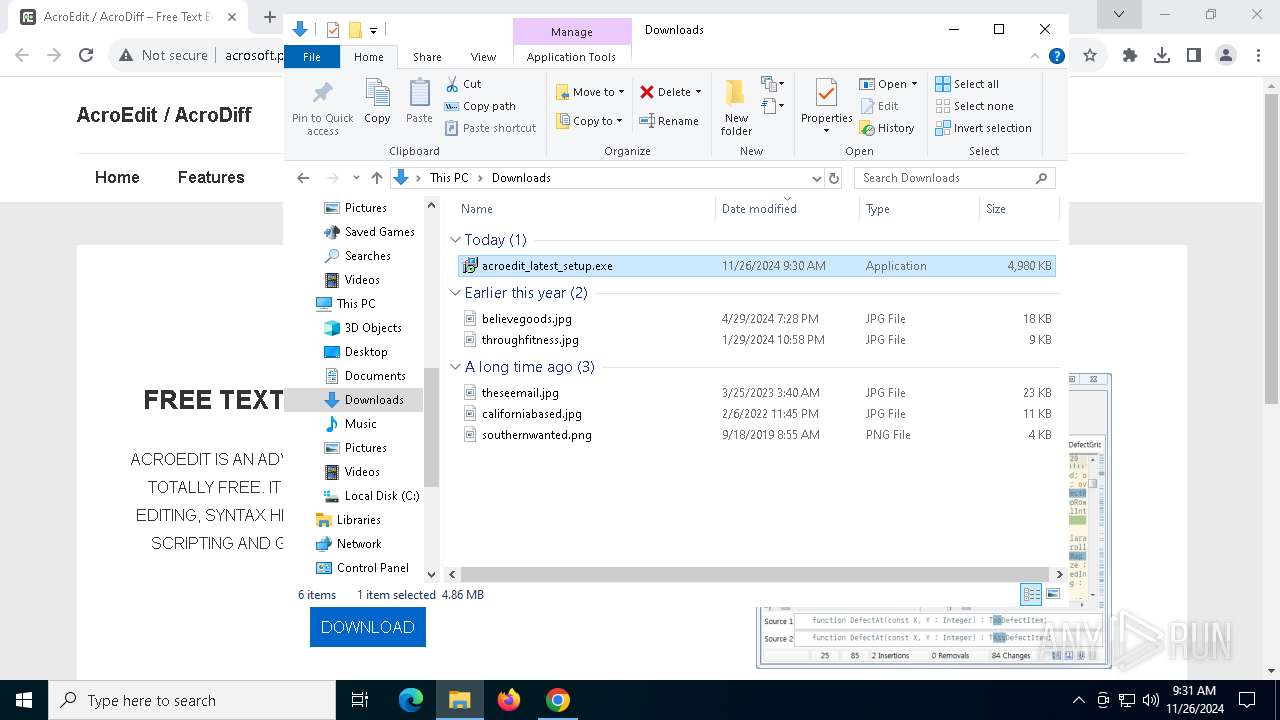
Process drops legitimate windows executable
- acroedit_latest_setup.tmp (PID: 1412)
Executable content was dropped or overwritten
- acroedit_latest_setup.exe (PID: 3780)
- acroedit_latest_setup.exe (PID: 3224)
- acroedit_latest_setup.tmp (PID: 1412)
Potential Corporate Privacy Violation
- chrome.exe (PID: 6684)
INFO
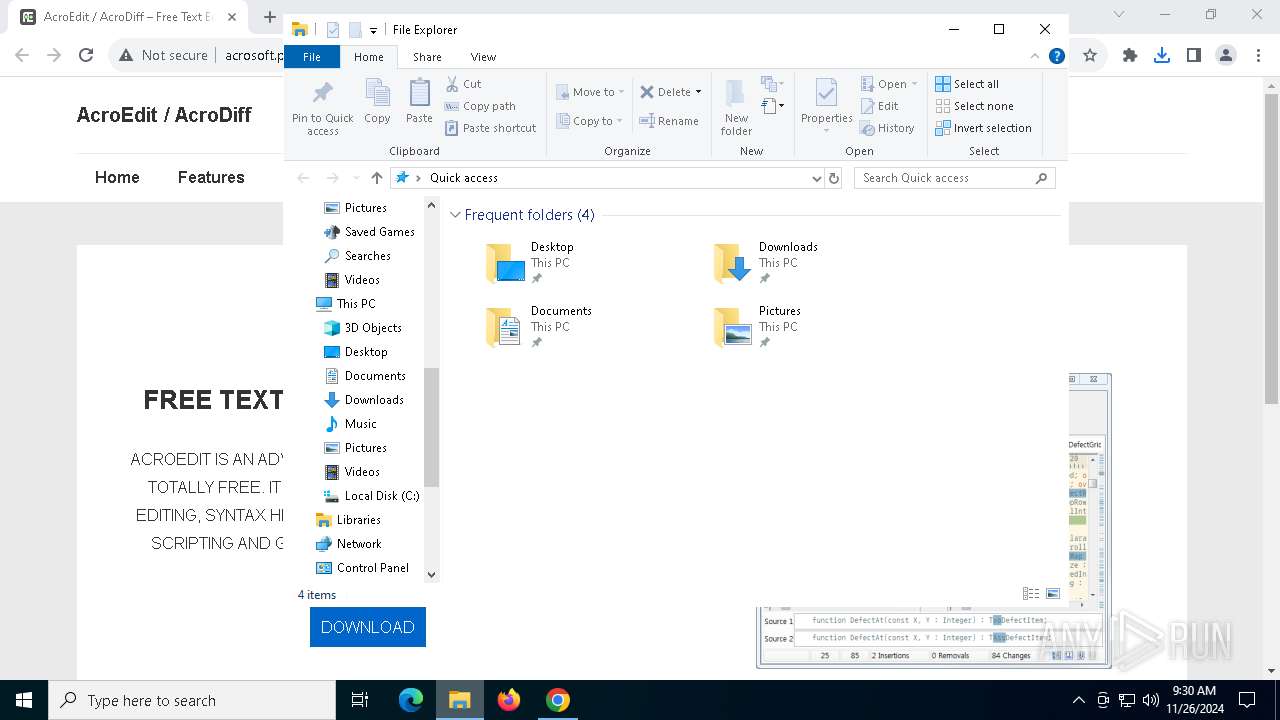
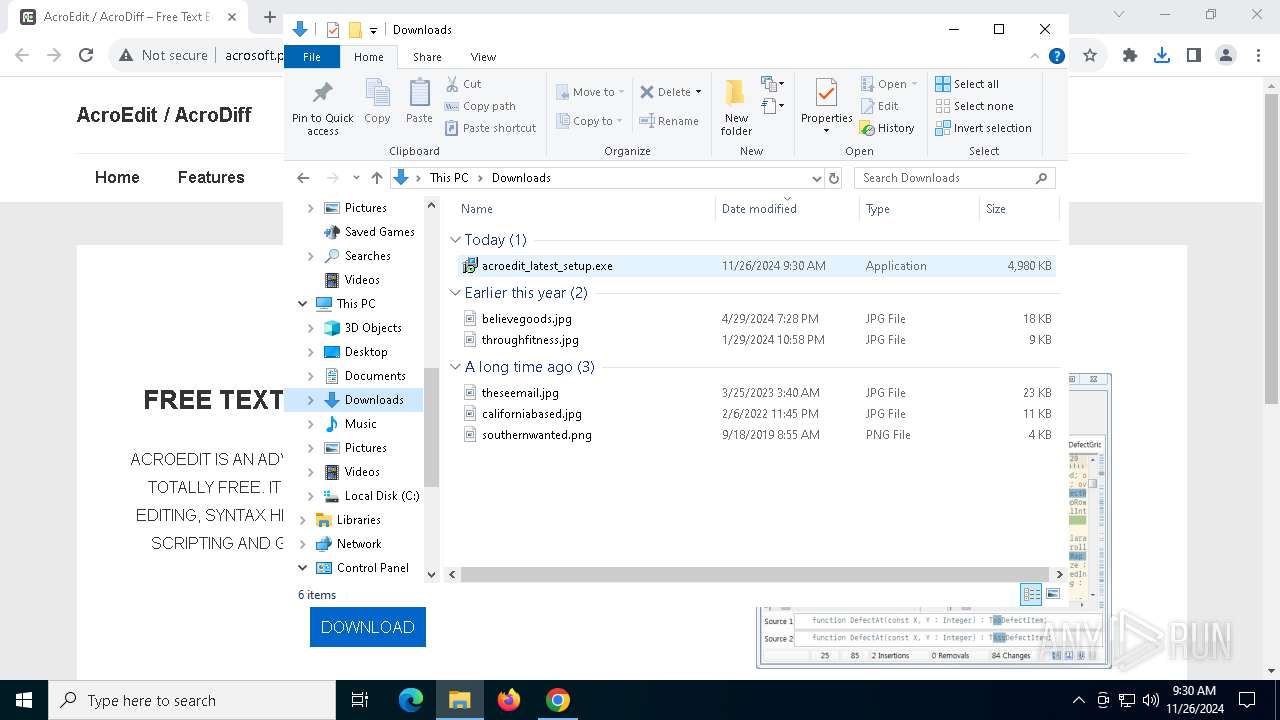
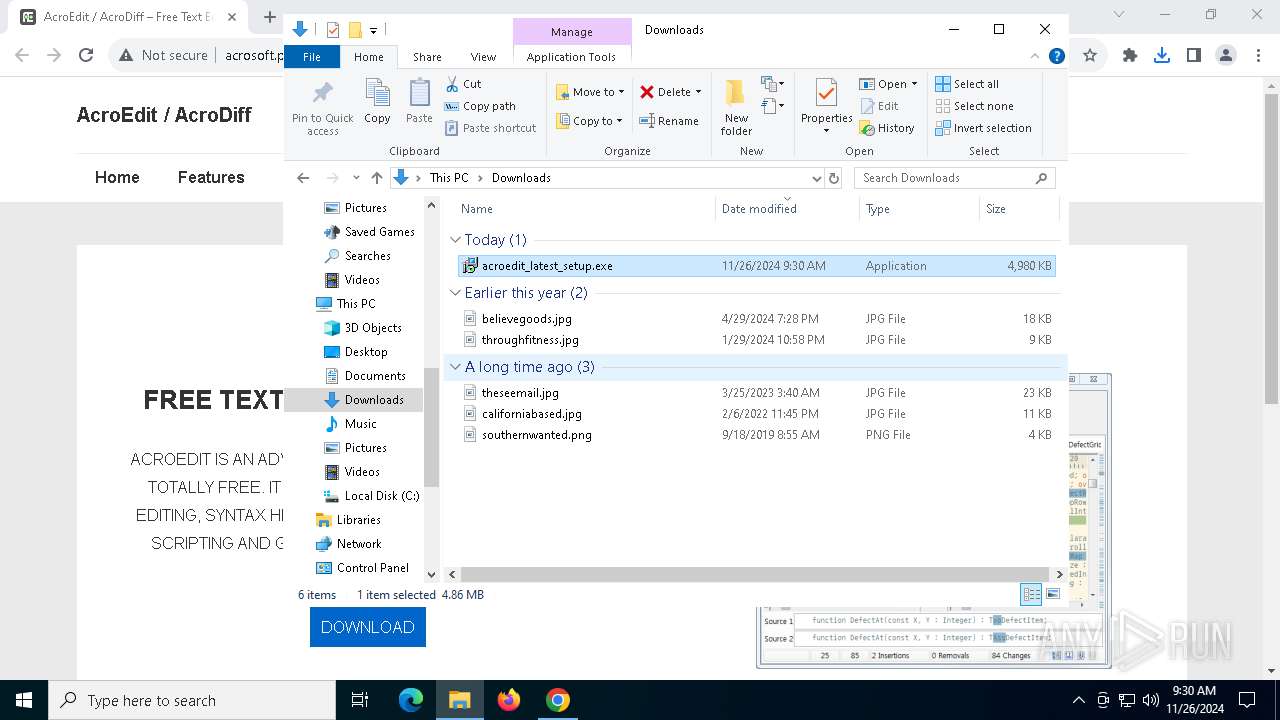
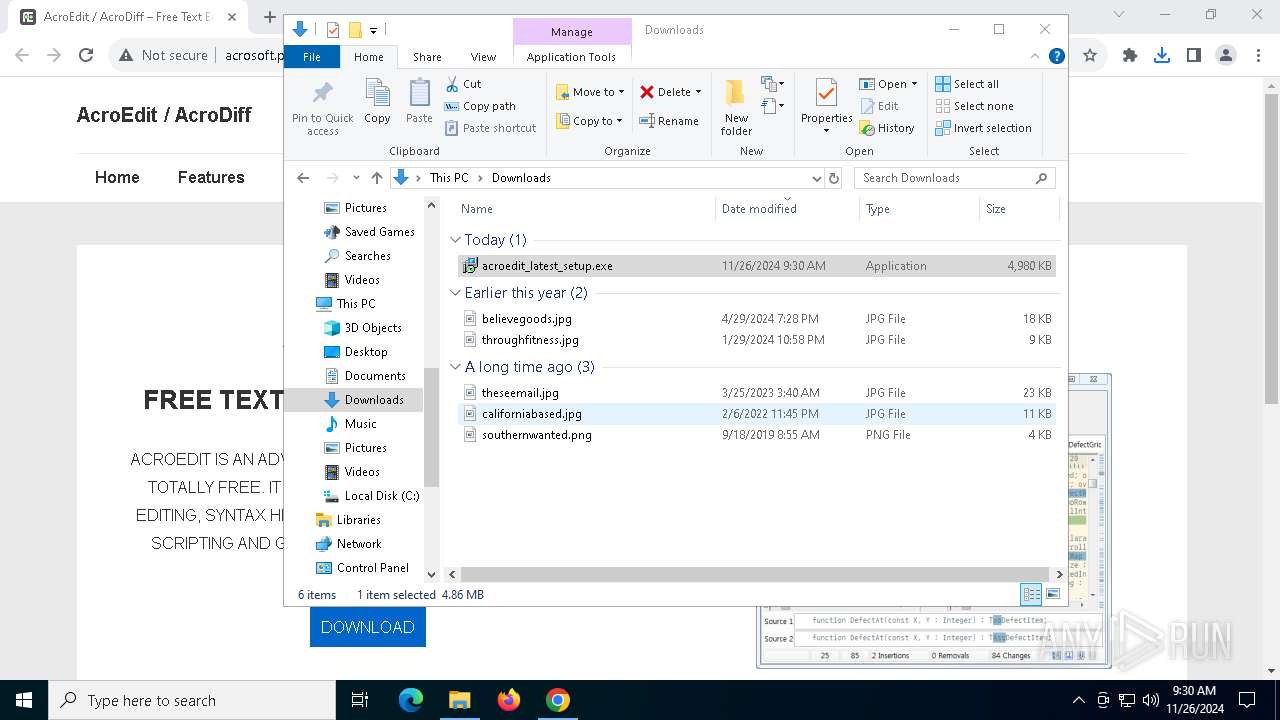
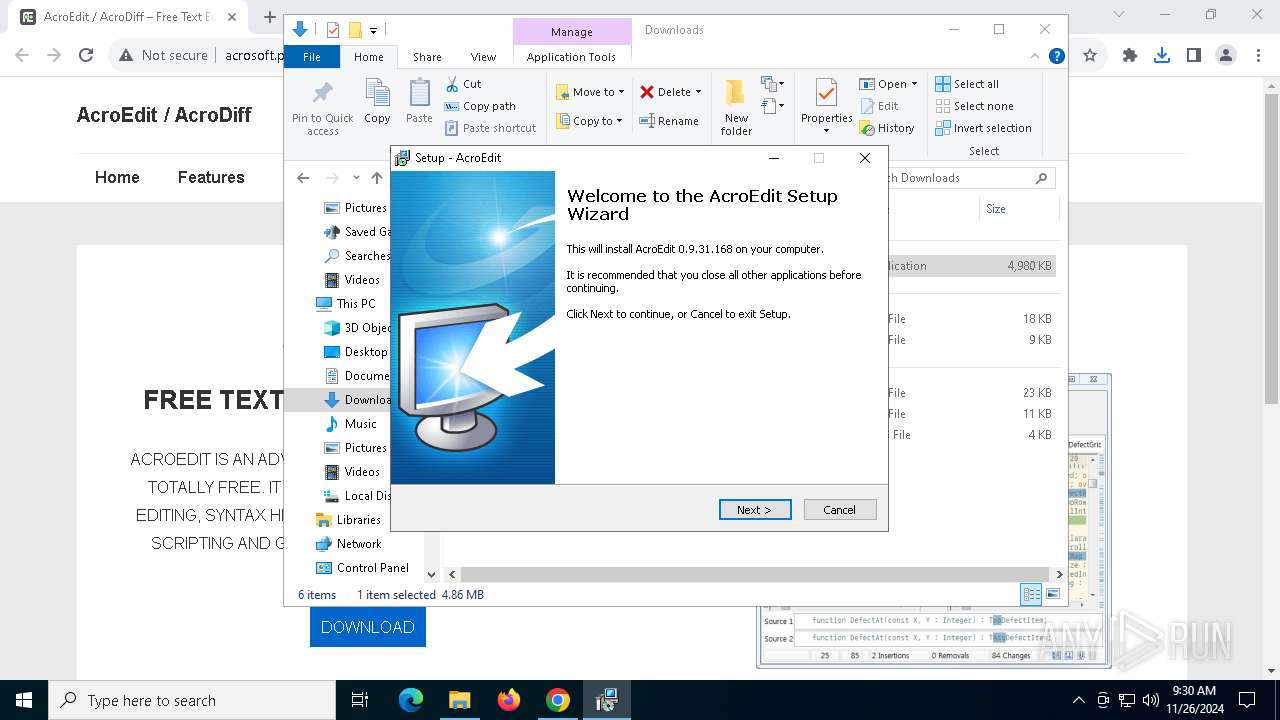
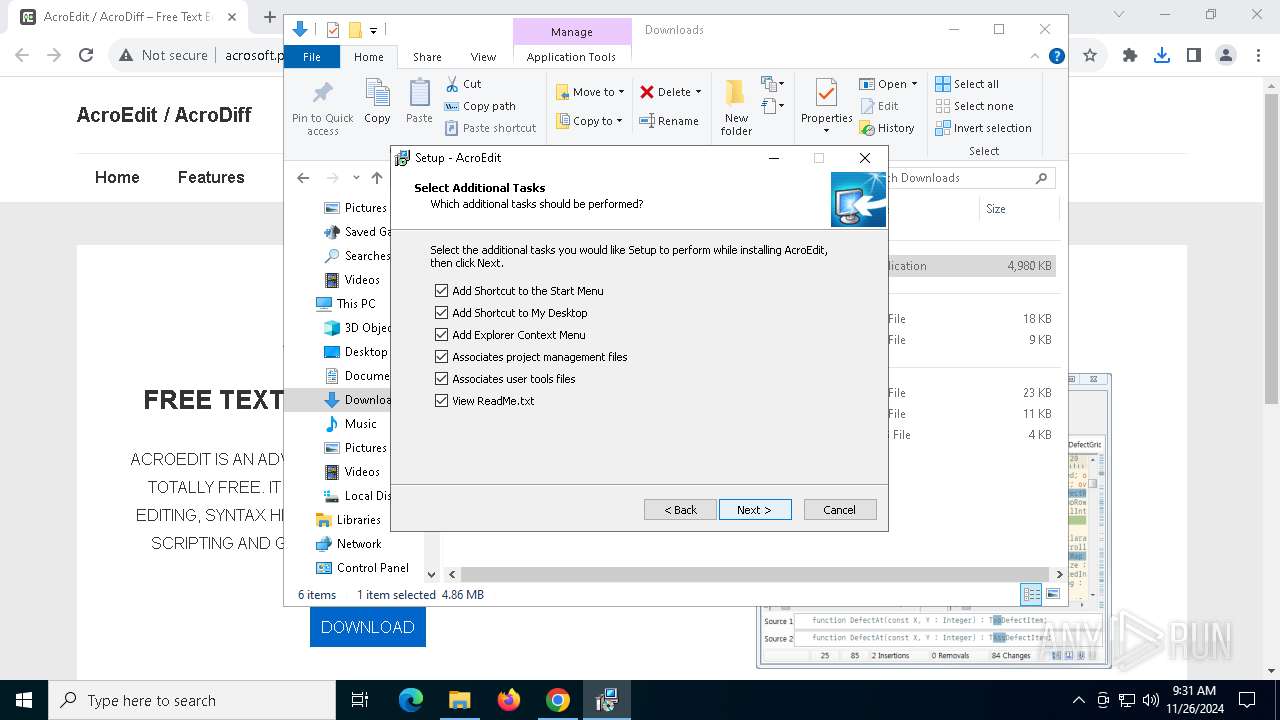
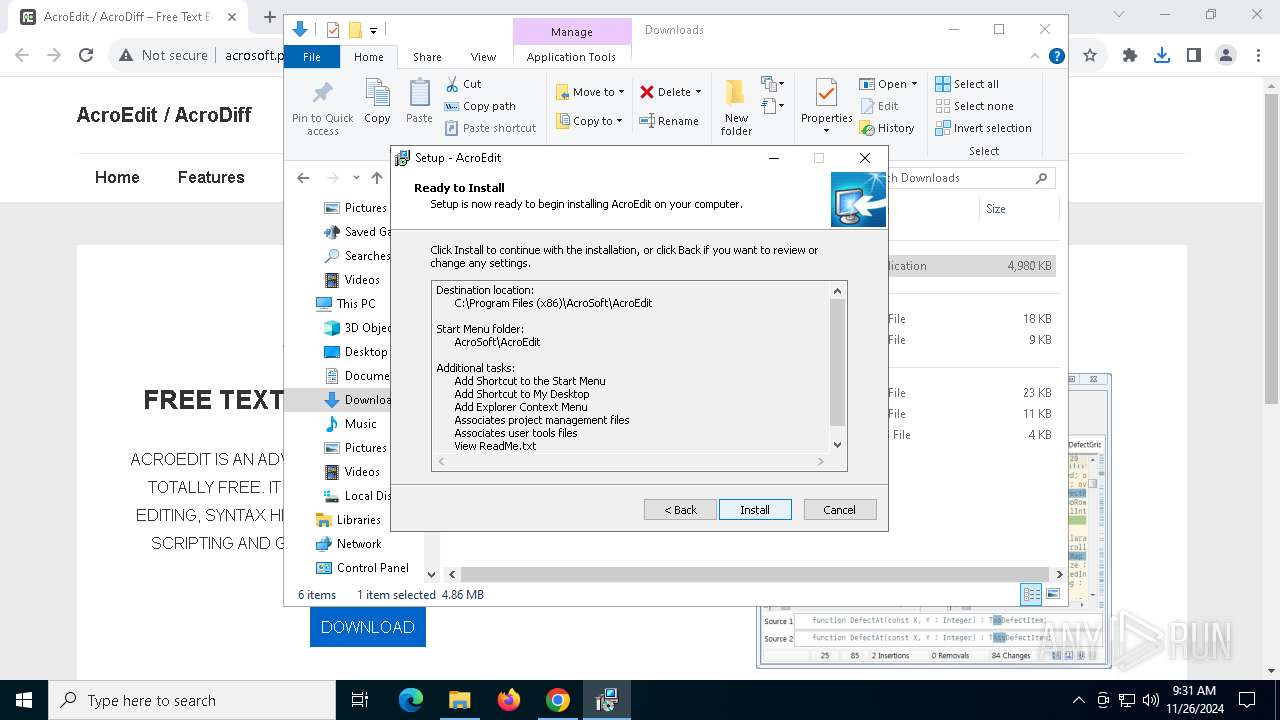
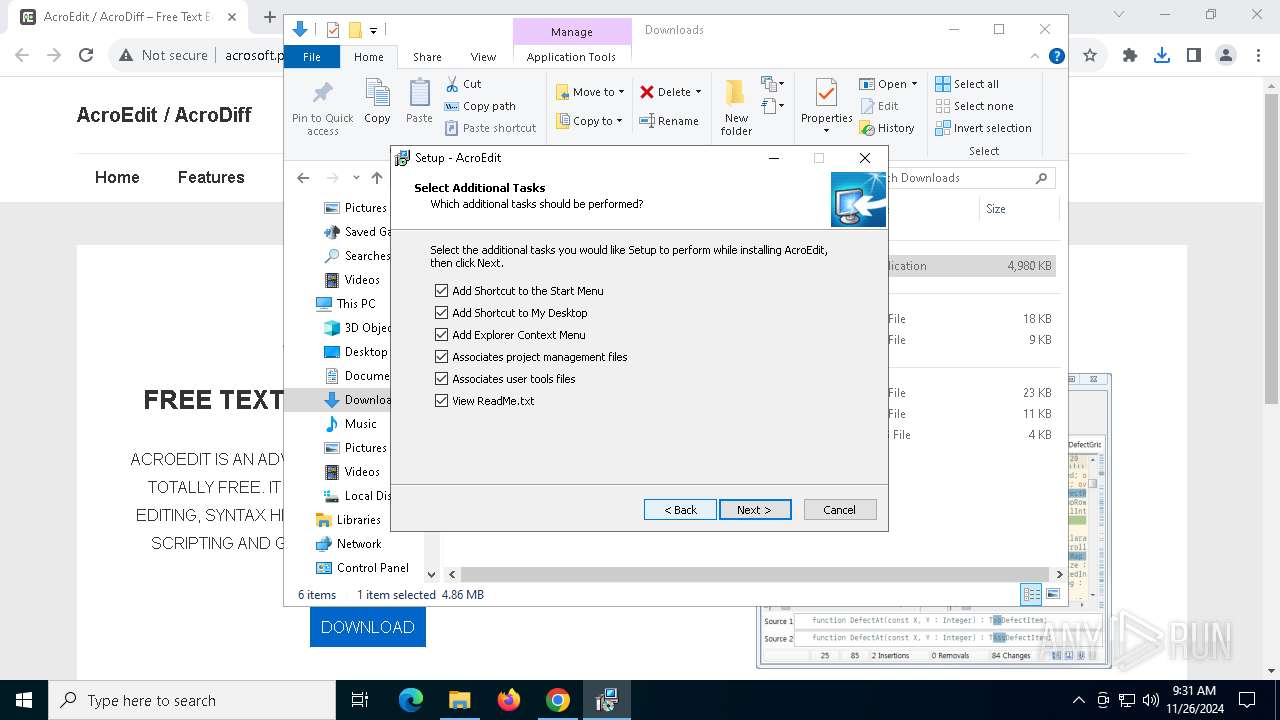
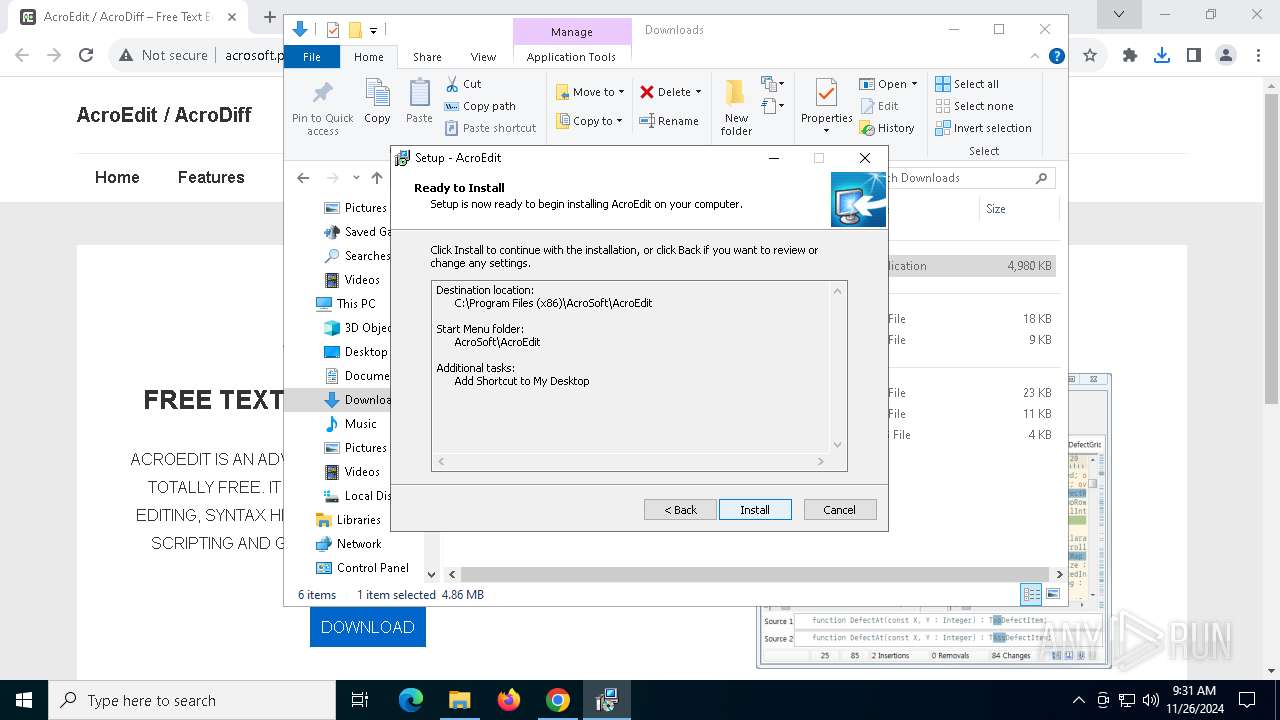
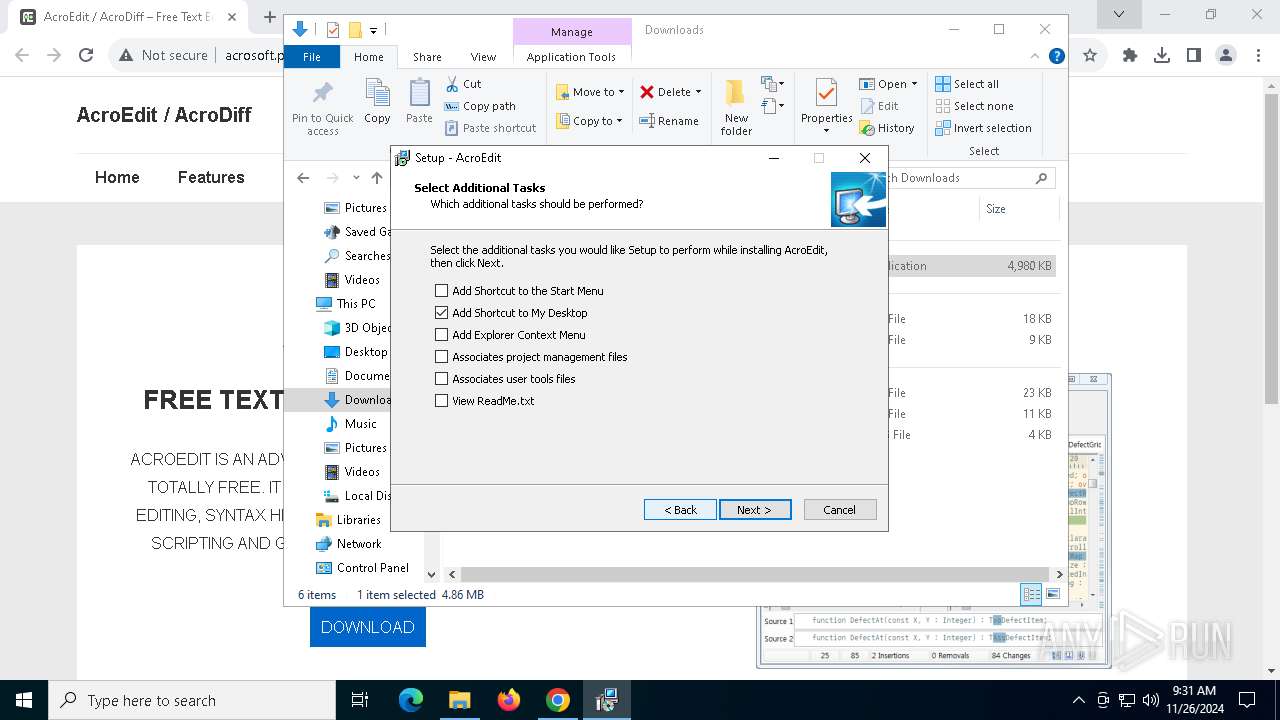
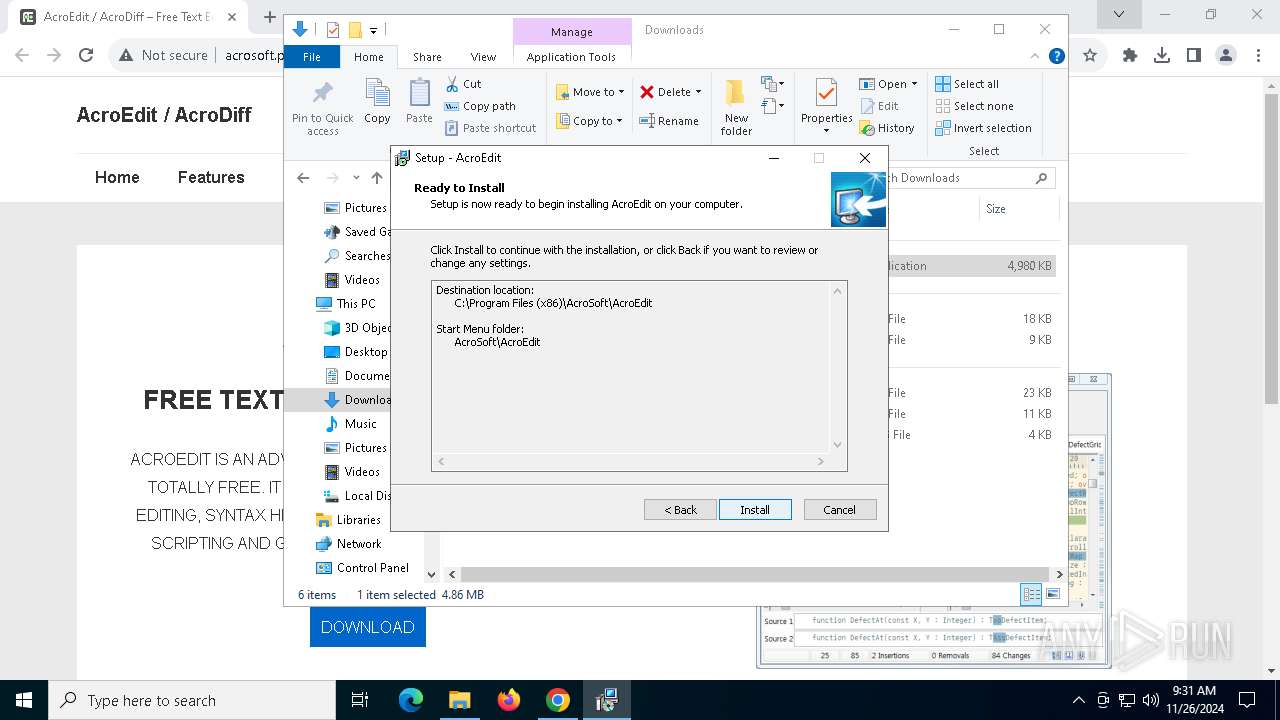
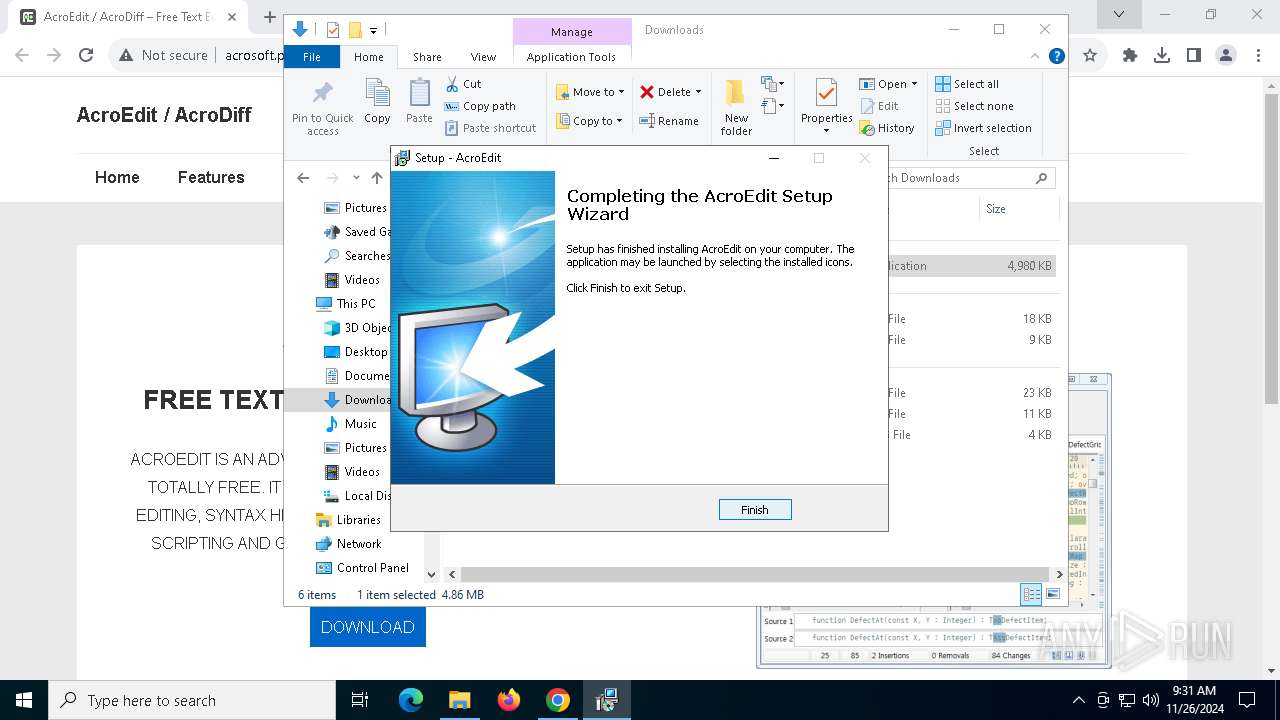
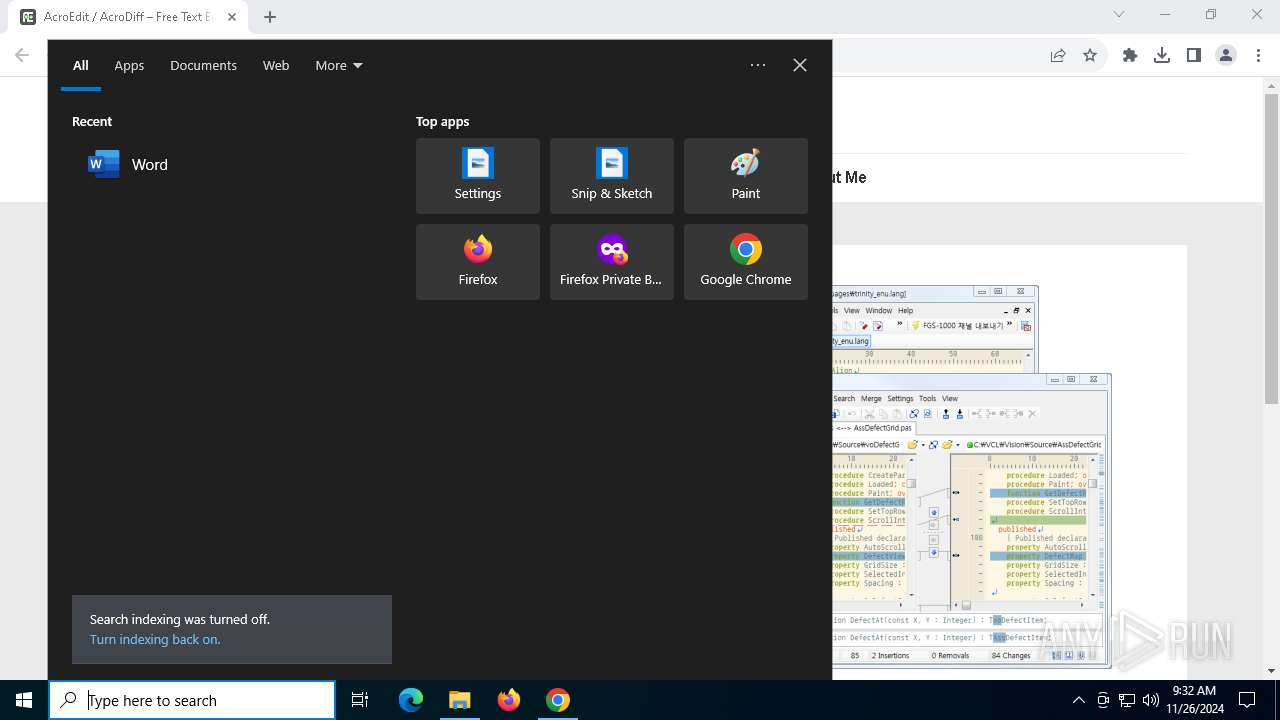
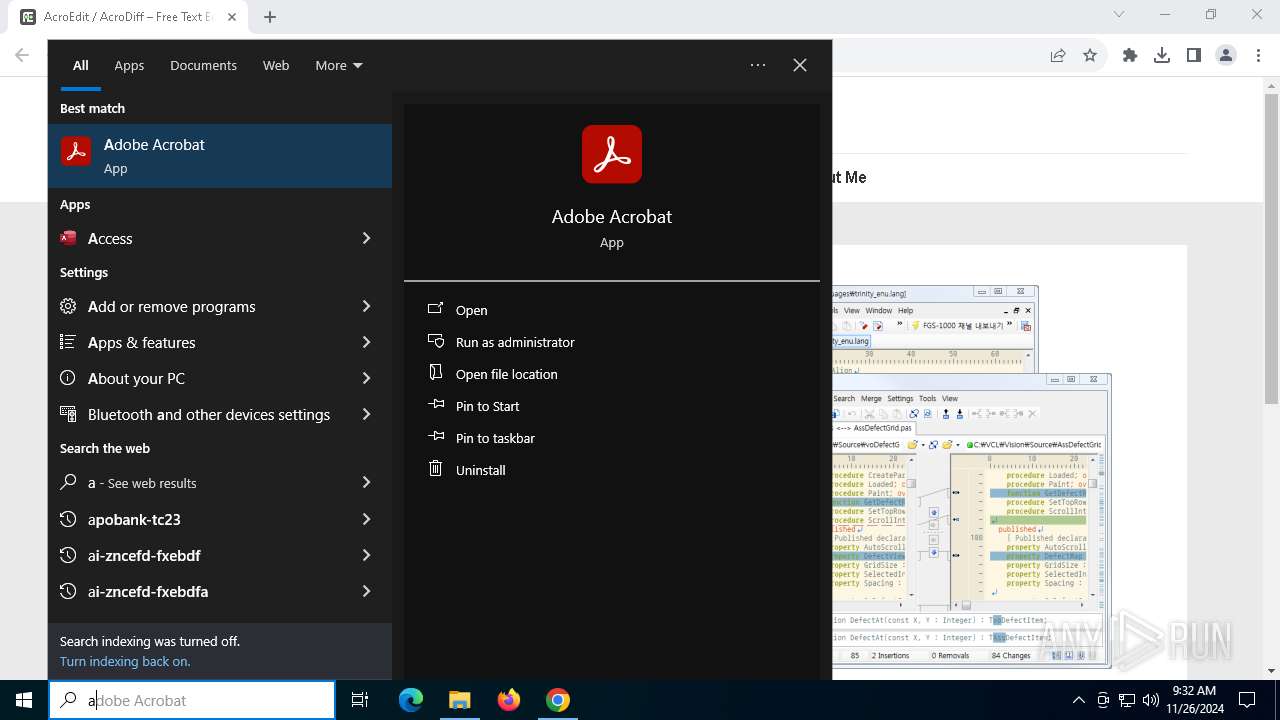
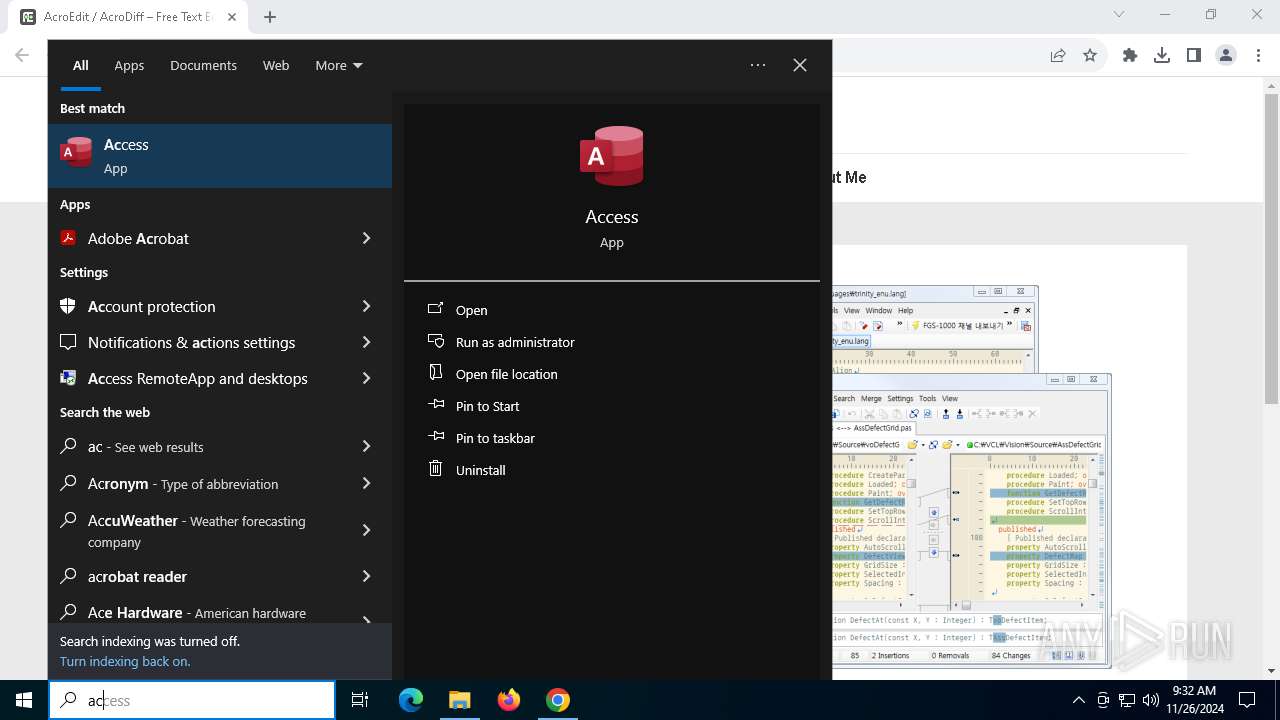
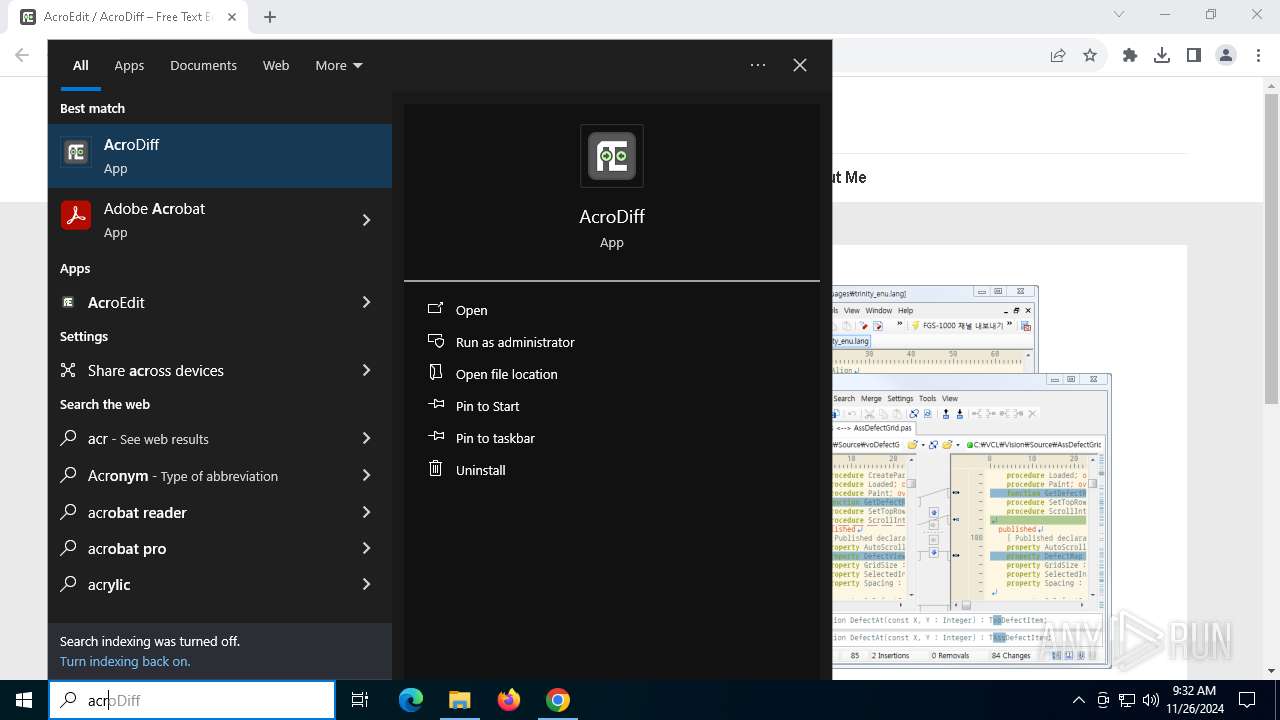
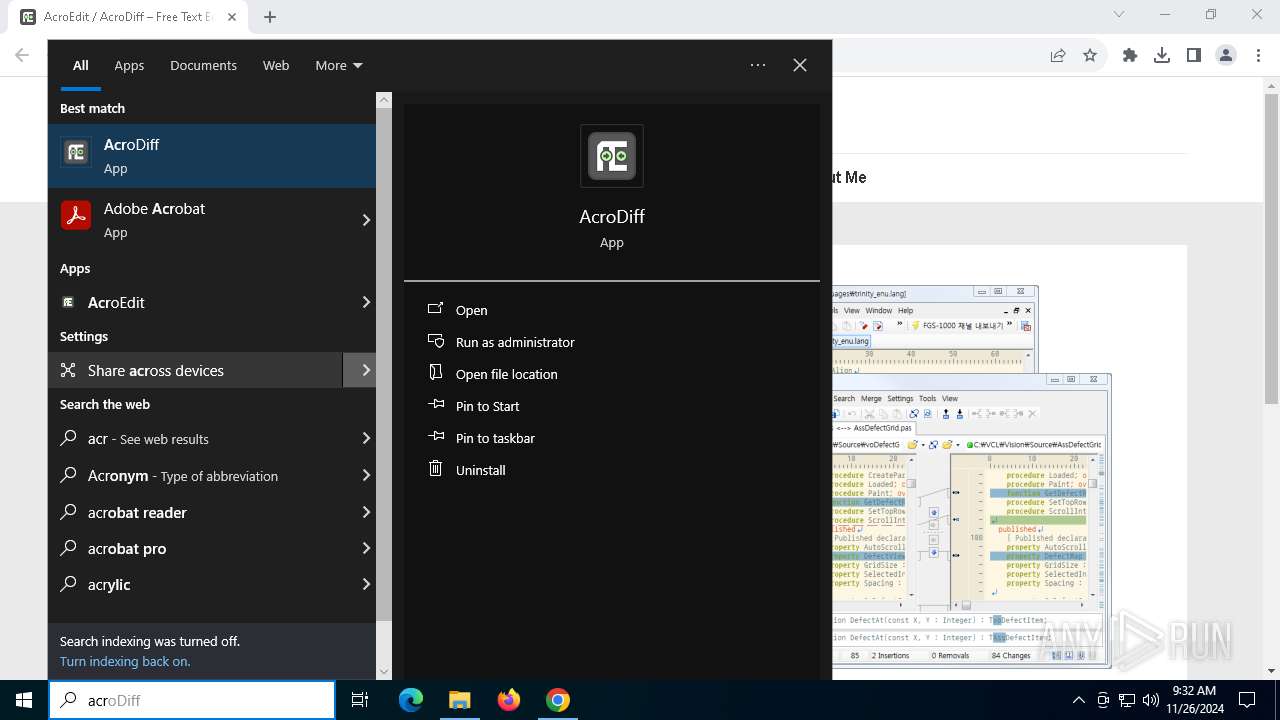
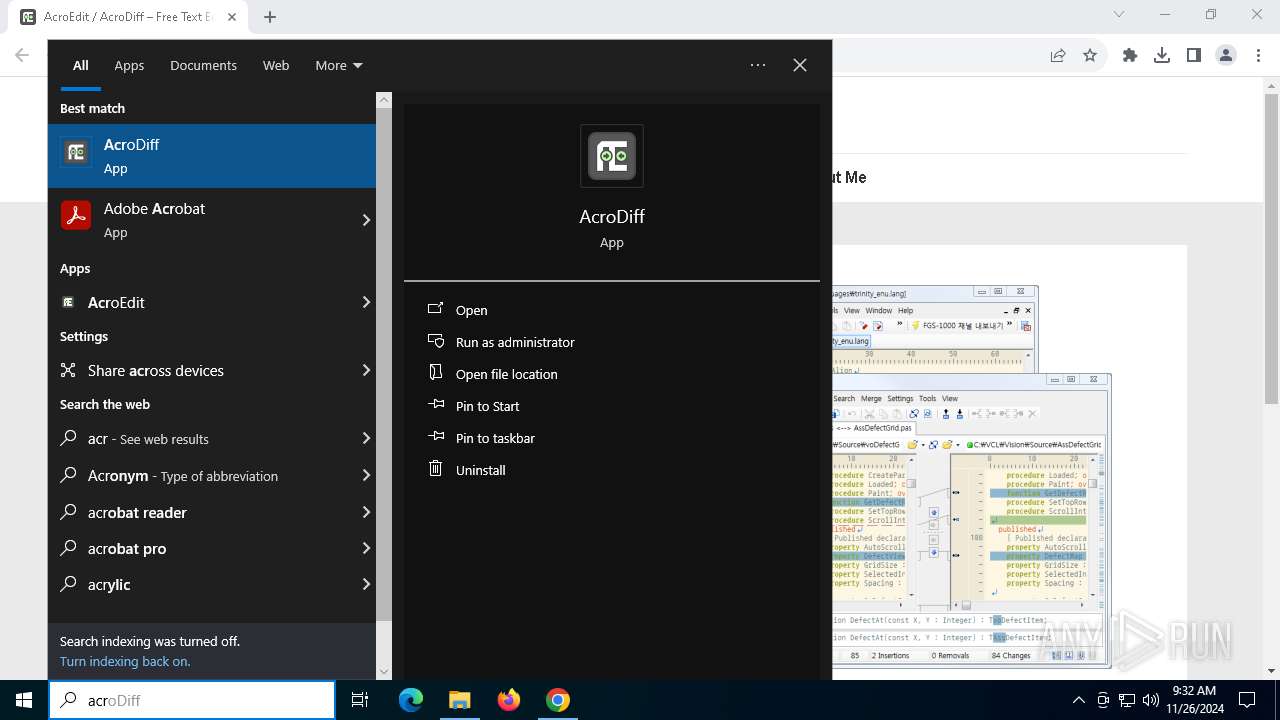
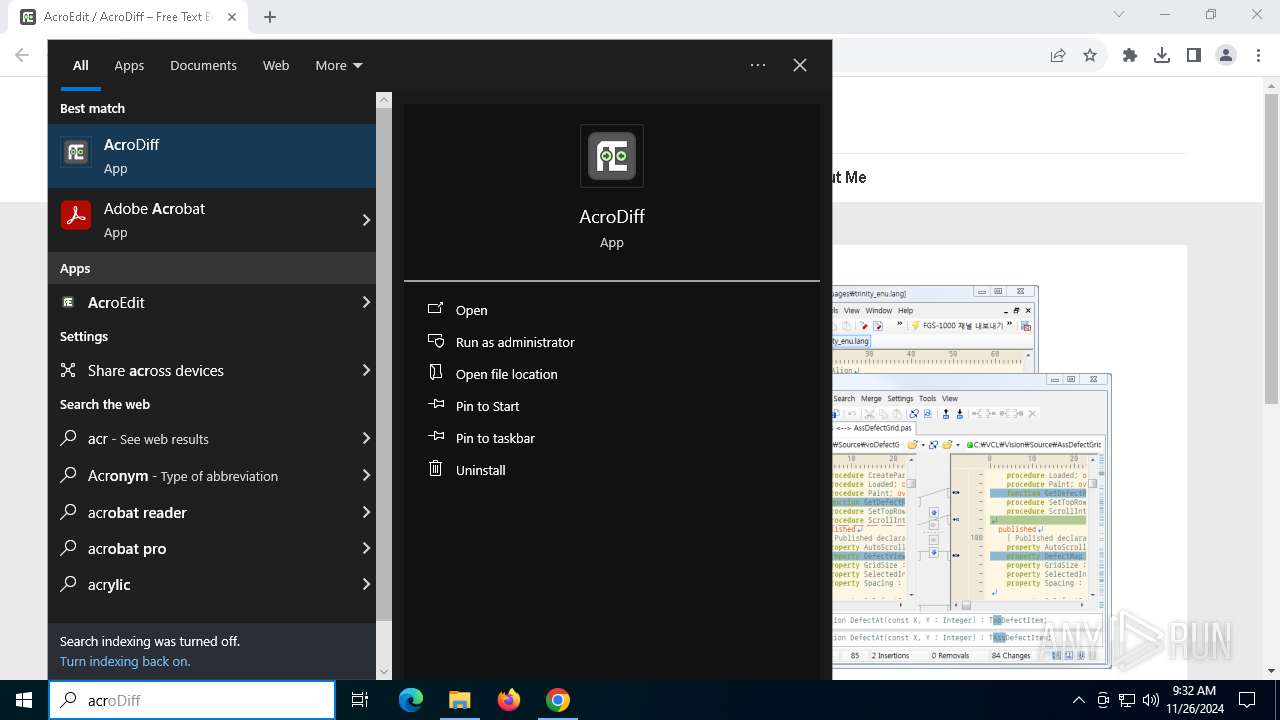
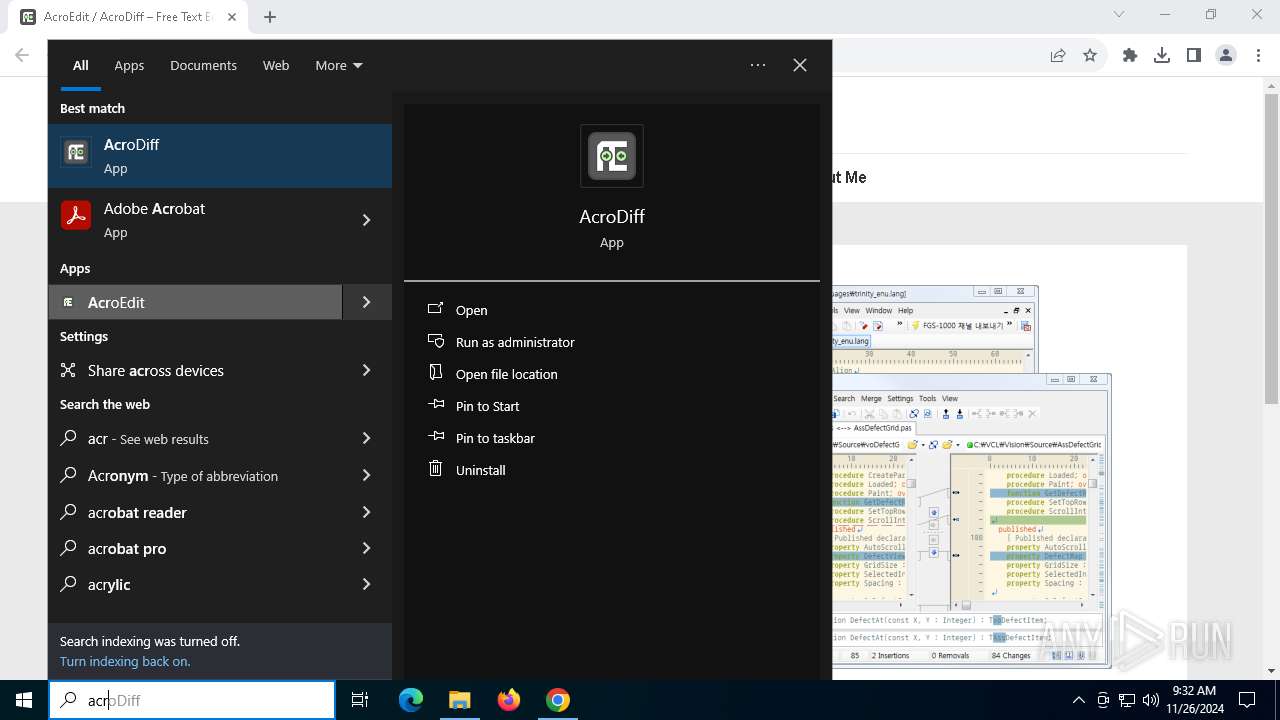
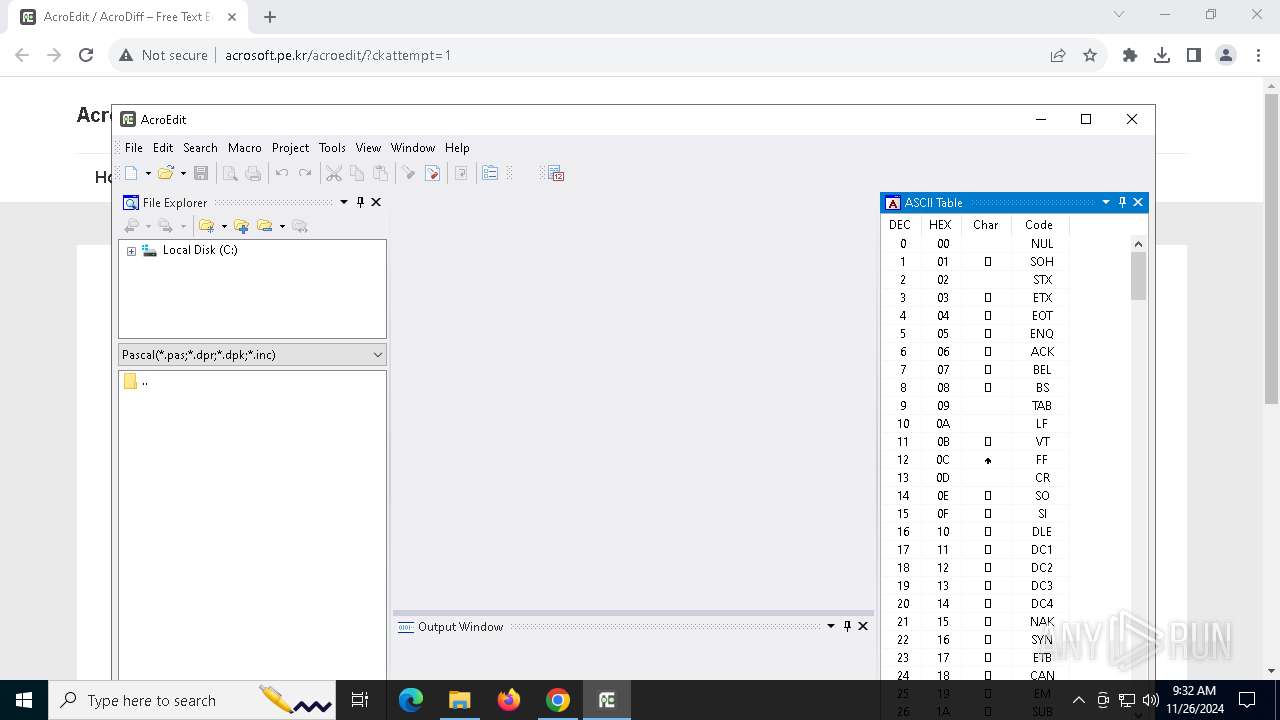
Manual execution by a user
- acroedit_latest_setup.exe (PID: 3780)
- AcroEdit.exe (PID: 4444)
Executable content was dropped or overwritten
- chrome.exe (PID: 3912)
- chrome.exe (PID: 6400)
Application launched itself
- chrome.exe (PID: 6400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5548 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3600 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5576 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
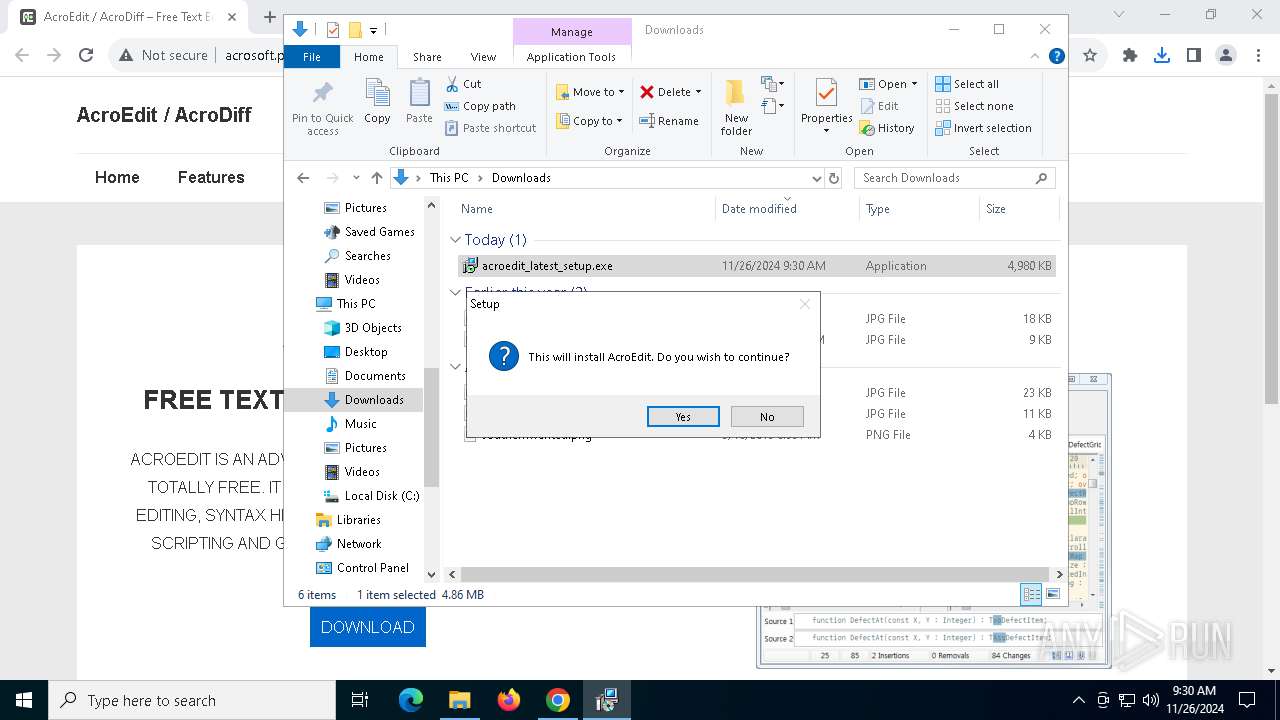
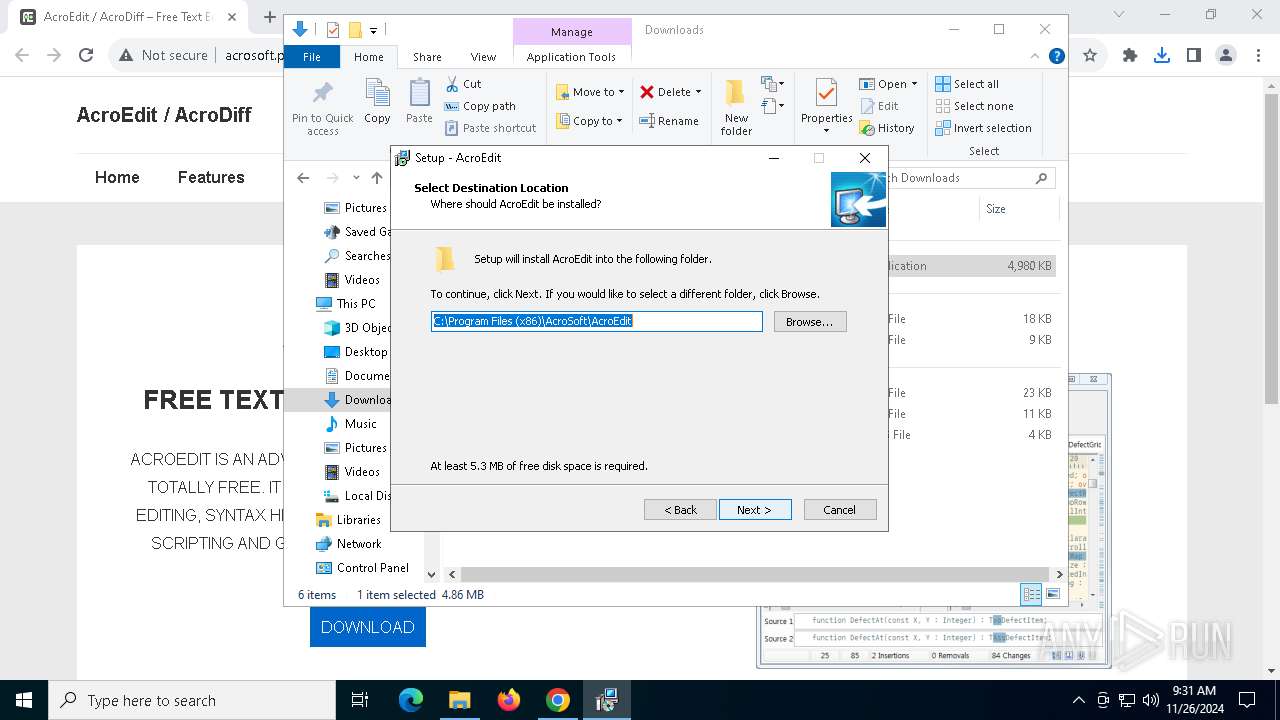
| 1412 | "C:\Users\admin\AppData\Local\Temp\is-F7A0F.tmp\acroedit_latest_setup.tmp" /SL5="$40232,4687616,119296,C:\Users\admin\Downloads\acroedit_latest_setup.exe" /SPAWNWND=$50226 /NOTIFYWND=$60254 | C:\Users\admin\AppData\Local\Temp\is-F7A0F.tmp\acroedit_latest_setup.tmp | acroedit_latest_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5700 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4880 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1888 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4652 --field-trial-handle=1788,i,10130850675050766112,8149669504487456210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\Downloads\acroedit_latest_setup.exe" /SPAWNWND=$50226 /NOTIFYWND=$60254 | C:\Users\admin\Downloads\acroedit_latest_setup.exe | acroedit_latest_setup.tmp | ||||||||||||
User: admin Company: AcroSoft Integrity Level: HIGH Description: AcroEdit Installation Program Exit code: 0 Version: 0.9.31.168 Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\Downloads\acroedit_latest_setup.exe" | C:\Users\admin\Downloads\acroedit_latest_setup.exe | explorer.exe | ||||||||||||
User: admin Company: AcroSoft Integrity Level: MEDIUM Description: AcroEdit Installation Program Exit code: 0 Version: 0.9.31.168 Modules
| |||||||||||||||
Total events
8 413
Read events
8 364
Write events
43
Delete events
6
Modification events
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6400) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
35
Suspicious files
123
Text files
77
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137a54.TMP | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137a54.TMP | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF137a54.TMP | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137a54.TMP | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF137a92.TMP | — | |
MD5:— | SHA256:— | |||
| 6400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
86
DNS requests
84
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
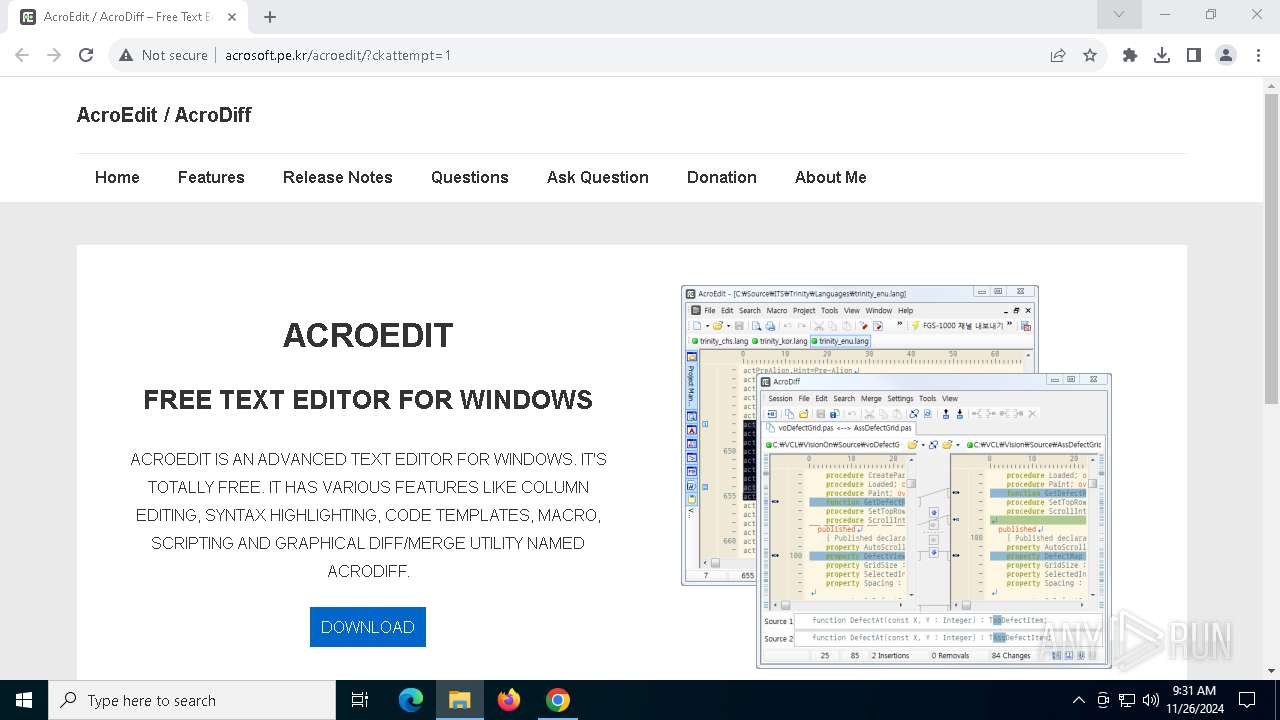
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/?ckattempt=1 | KR | html | 14.2 Kb | unknown |
3040 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/cupid.js | KR | text | 8.70 Kb | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/ | KR | html | 774 b | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/wp-content/plugins/dw-question-answer/templates/assets/css/style.css?ver=180720161357 | KR | text | 2.26 Kb | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/wp-content/plugins/dw-question-answer/templates/assets/css/rtl.css?ver=180720161357 | KR | text | 1.00 Kb | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/wp-content/plugins/responsive-add-ons/includes/megamenu/assets/megamenu.css?ver=3.1.2 | KR | text | 339 b | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/wp-content/themes/responsive/core/css/style.min.css?ver=6.0.1 | KR | text | 39.8 Kb | unknown |
6684 | chrome.exe | GET | 200 | 183.111.199.215:80 | http://www.acrosoft.pe.kr/acroedit/wp-content/themes/responsive/core/css/icomoon/style.min.css?ver=6.0.1 | KR | text | 1.28 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3040 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3040 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6400 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6684 | chrome.exe | 108.177.96.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6684 | chrome.exe | 183.111.199.215:443 | www.acrosoft.pe.kr | Korea Telecom | KR | unknown |
6684 | chrome.exe | 183.111.199.215:80 | www.acrosoft.pe.kr | Korea Telecom | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.acrosoft.pe.kr |
| unknown |
accounts.google.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
stats.wp.com |
| whitelisted |
v0.wordpress.com |
| whitelisted |
2.gravatar.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6684 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Self Signed SSL Certificate to 'My Company Ltd' |
6684 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Self Signed SSL Certificate to 'My Company Ltd' |
6684 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |