| File name: | ransomware.exe |
| Full analysis: | https://app.any.run/tasks/fde8527f-a2ad-48e6-b030-23bc6f52736c |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2024, 13:33:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
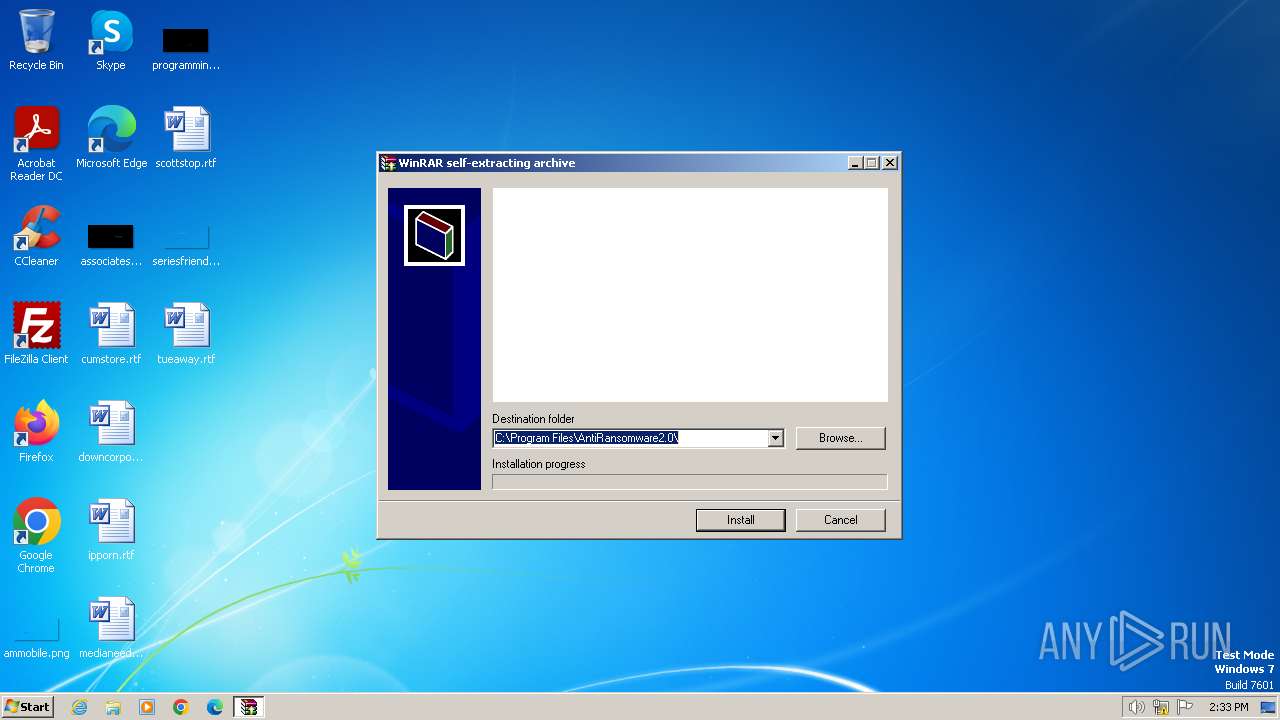
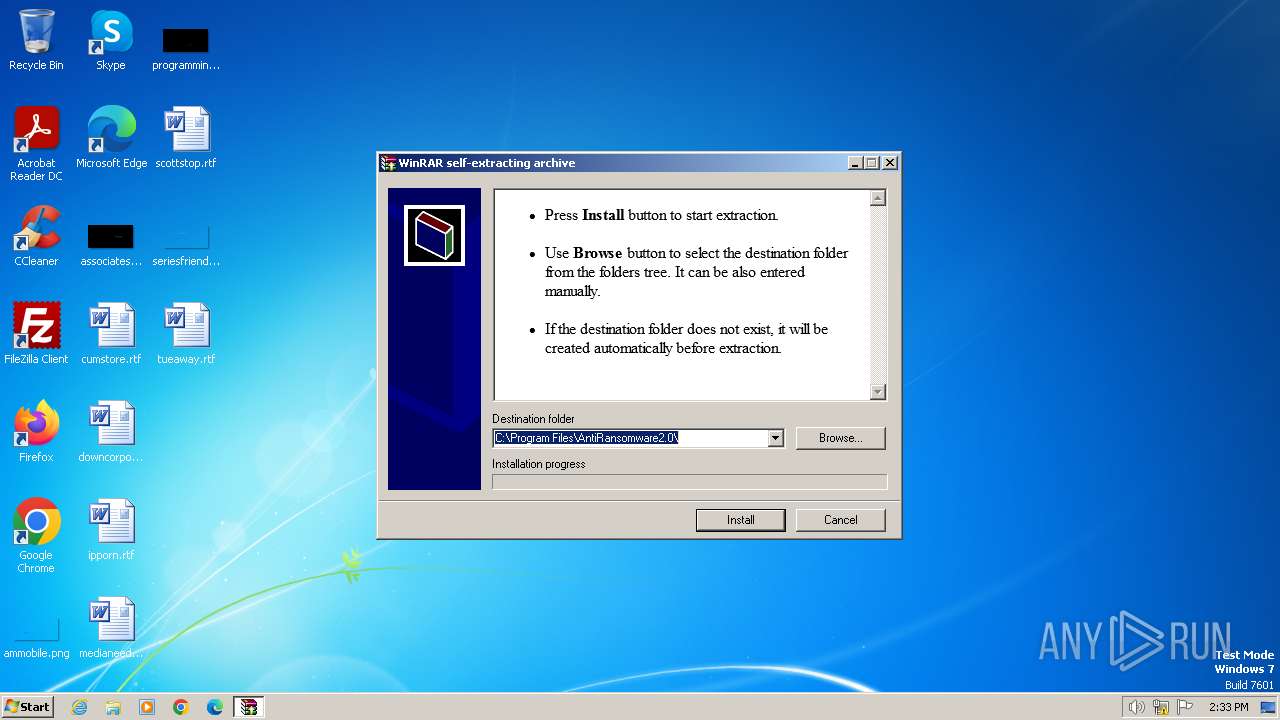
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 6906FECE4E593A51C7F3C61B1A464868 |
| SHA1: | 8A1F2FBA9D9C232CD7B3A3AC9D6648645657D774 |
| SHA256: | 5B55725BFDC2C7A82AB9057A5403D48AA212DEC18FA4D6B2181481A8376D63D6 |
| SSDEEP: | 98304:Zvmsej3qYeftWdpVeztb4AhSGSjBMJ7l5VEH1MoYRIwtmiAPf4O47iWk3eOdvxKr:nRIIYRczi1q |
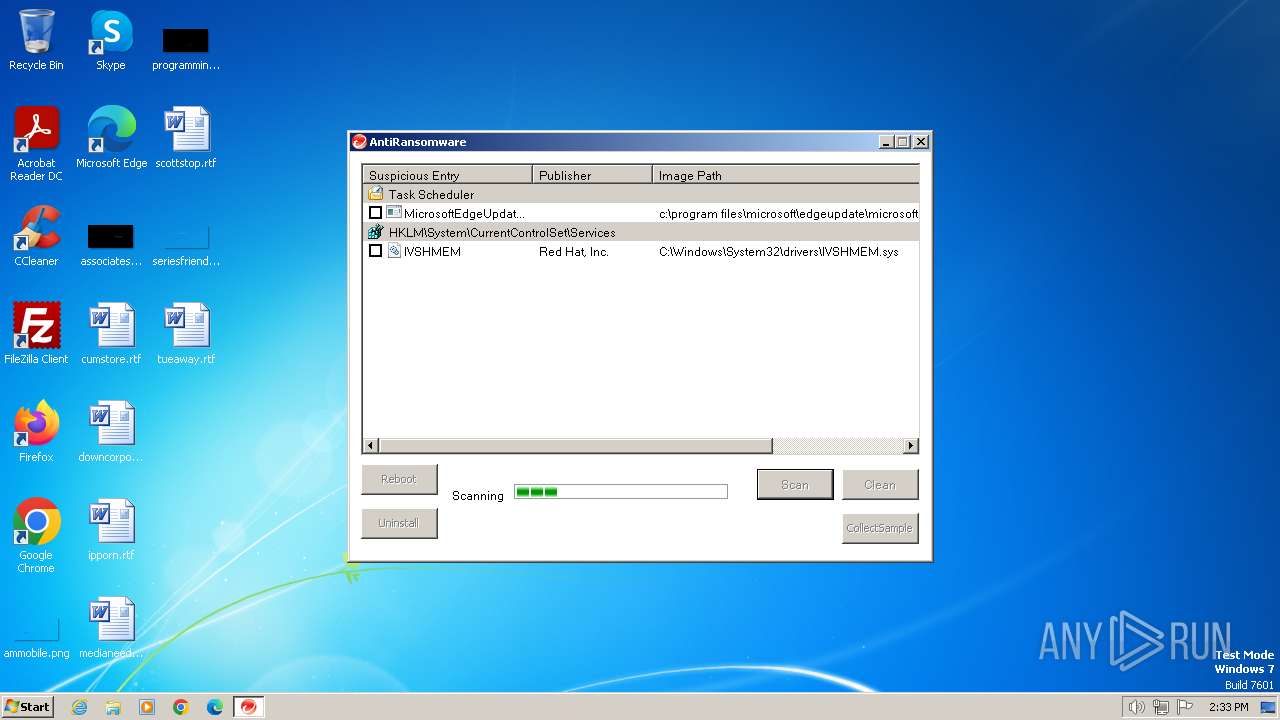
MALICIOUS
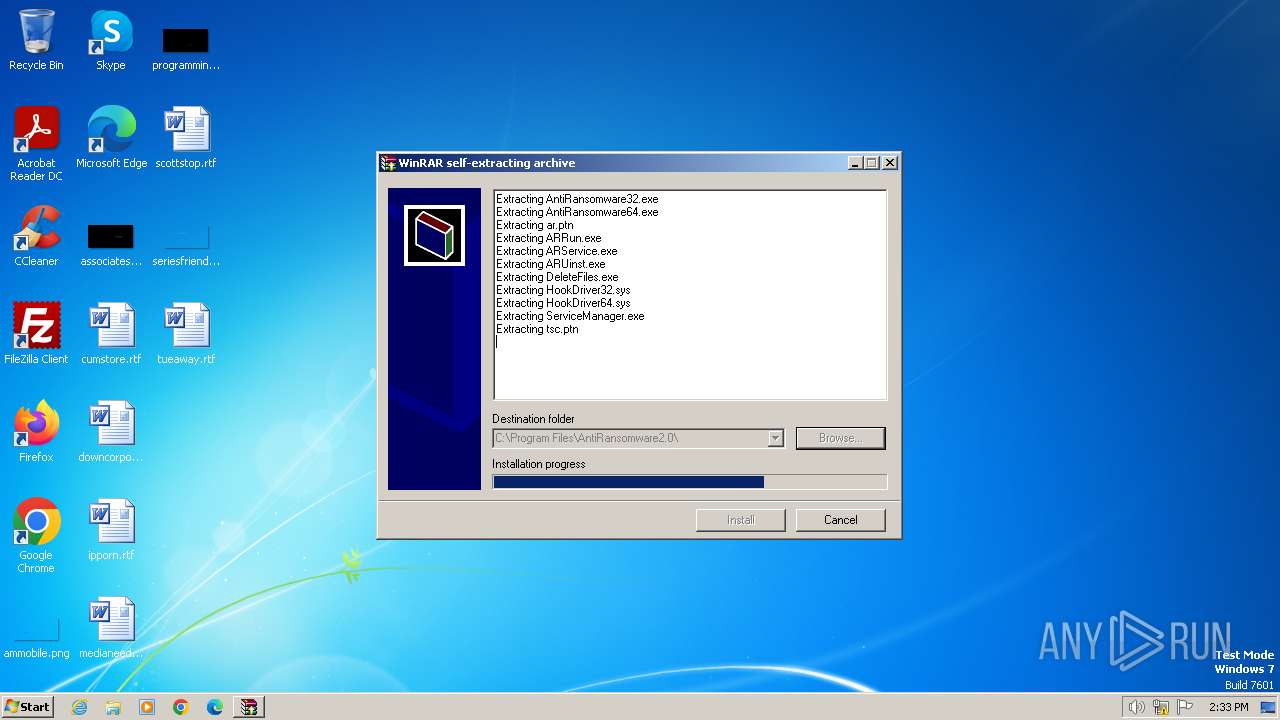
SFX dropper has been detected
- ransomware.exe (PID: 3320)
SUSPICIOUS
Reads the Internet Settings
- ransomware.exe (PID: 3320)
- ARRun.exe (PID: 1008)
- ransomware.exe (PID: 1920)
Creates file in the systems drive root
- ransomware.exe (PID: 3320)
- ransomware.exe (PID: 1920)
Reads security settings of Internet Explorer
- ransomware.exe (PID: 3320)
- ARRun.exe (PID: 1008)
- ransomware.exe (PID: 1920)
Reads Microsoft Outlook installation path
- ransomware.exe (PID: 3320)
Application launched itself
- ransomware.exe (PID: 3320)
Reads Internet Explorer settings
- ransomware.exe (PID: 3320)
Drops a system driver (possible attempt to evade defenses)
- ransomware.exe (PID: 1920)
Executable content was dropped or overwritten
- ransomware.exe (PID: 1920)
Executes as Windows Service
- ARService.exe (PID: 3160)
INFO
Checks supported languages
- ransomware.exe (PID: 3320)
- ransomware.exe (PID: 1920)
- ARRun.exe (PID: 1008)
- ARService.exe (PID: 3160)
- ServiceManager.exe (PID: 3696)
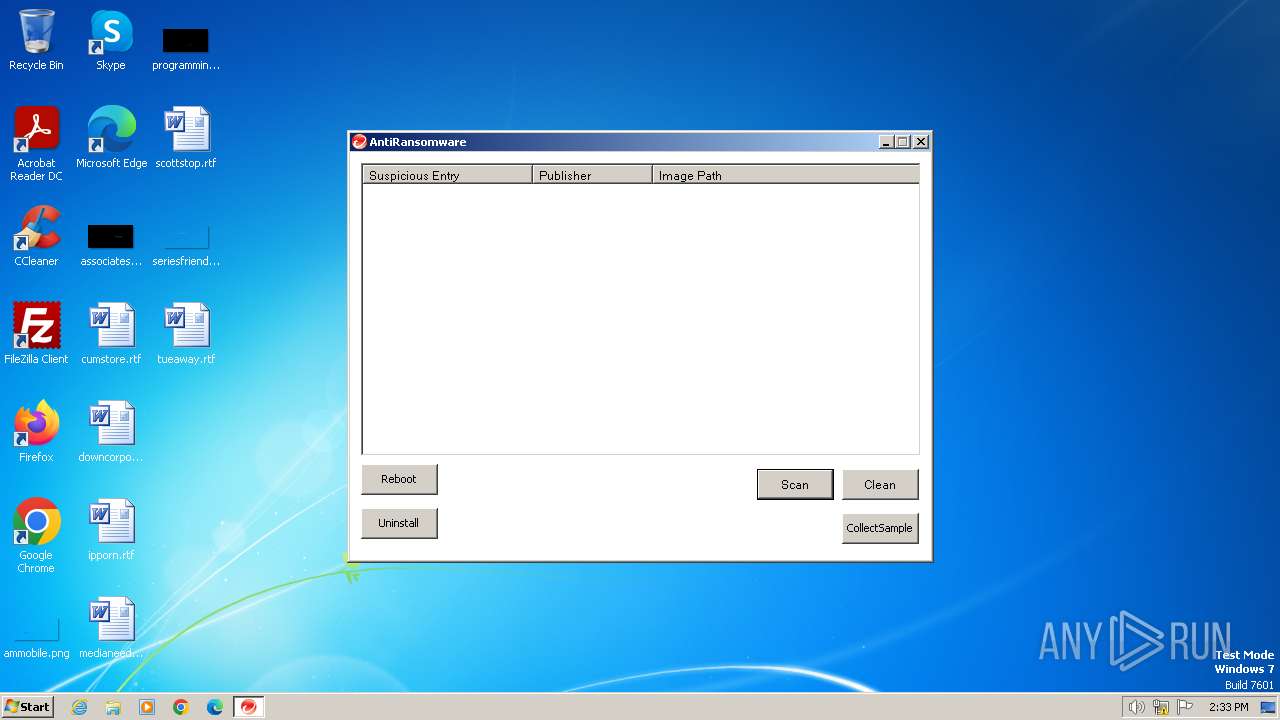
- AntiRansomware32.exe (PID: 1832)
Reads the computer name
- ransomware.exe (PID: 3320)
- ARRun.exe (PID: 1008)
- ServiceManager.exe (PID: 3696)
- ARService.exe (PID: 3160)
- ransomware.exe (PID: 1920)
- AntiRansomware32.exe (PID: 1832)
Checks proxy server information
- ransomware.exe (PID: 3320)
Reads the machine GUID from the registry
- ransomware.exe (PID: 3320)
The process uses the downloaded file
- ransomware.exe (PID: 3320)
- ARRun.exe (PID: 1008)
- ransomware.exe (PID: 1920)
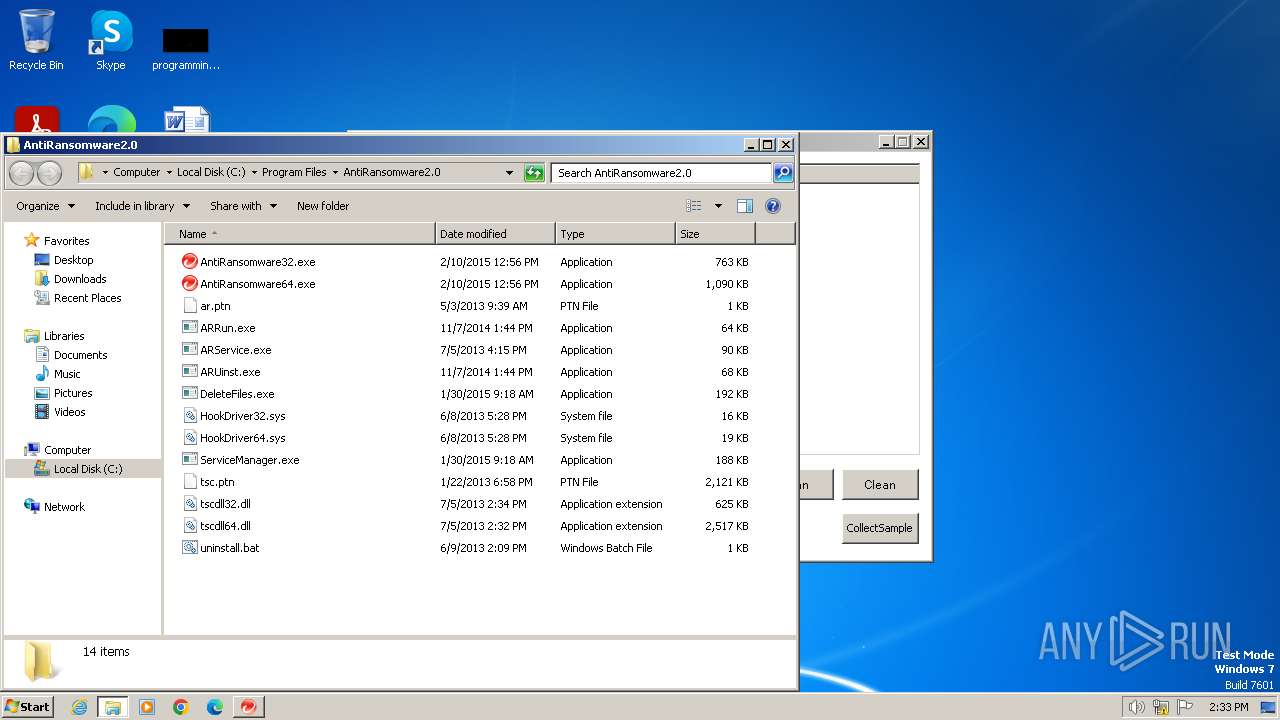
Creates files in the program directory
- ransomware.exe (PID: 1920)
- ServiceManager.exe (PID: 3696)
- ARService.exe (PID: 3160)
- AntiRansomware32.exe (PID: 1832)
Sends debugging messages
- ARService.exe (PID: 3160)
Manual execution by a user
- wmpnscfg.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.3) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Win32 Executable Watcom C++ (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:22 04:59:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 81920 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
46
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Program Files\AntiRansomware2.0\ARRun.exe" | C:\Program Files\AntiRansomware2.0\ARRun.exe | — | ransomware.exe | |||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: ARLoad Application Exit code: 0 Version: 2, 0, 0, 1001 Modules
| |||||||||||||||
| 1572 | "C:\Windows\explorer.exe" "C:\Program Files\AntiRansomware2.0" | C:\Windows\explorer.exe | — | AntiRansomware32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | "C:\Program Files\AntiRansomware2.0\antiransomware32.exe" | C:\Program Files\AntiRansomware2.0\AntiRansomware32.exe | ARRun.exe | ||||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: Trend Micro AntiRansomware Tool Version: 2.0.0.1013 Modules
| |||||||||||||||
| 1920 | "C:\ransomware.exe" -el -s2 "-dC:\Program Files\AntiRansomware2.0\" "-p" "-sp" | C:\ransomware.exe | ransomware.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\AntiRansomware2.0\arservice.exe" | C:\Program Files\AntiRansomware2.0\ARService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Trend Micro Inc. Integrity Level: SYSTEM Description: ARServic Application Version: 2, 0, 0, 1001 Modules
| |||||||||||||||
| 3320 | "C:\ransomware.exe" | C:\ransomware.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3504 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3696 | "C:\Program Files\AntiRansomware2.0\servicemanager.exe" -i | C:\Program Files\AntiRansomware2.0\ServiceManager.exe | — | ARRun.exe | |||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: Service Manager Application Exit code: 0 Version: 2, 0, 0, 1001 Modules
| |||||||||||||||
Total events
101 231
Read events
101 093
Write events
124
Delete events
14
Modification events
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3320) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
11
Suspicious files
5
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\AntiRansomware32.exe | executable | |
MD5:7EDF77D5D2CEFC2A9DA831B0689D7A5F | SHA256:42DF46FDE6DF9A243B4F7EA130C5E59DFA31144021D1A7A26F01E41622EF0E96 | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\ARService.exe | executable | |
MD5:F36B5FA003FE7EAB5380845ACFF15FED | SHA256:57403D8B090904B983A4C97C461F9109A4BC1F2B6003FA07AE6712586EBC8912 | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\HookDriver64.sys | executable | |
MD5:7339ACD1FAD38BD97C550BADEE8F98C9 | SHA256:5AF7629F07EDE929E6E655CB72FE6756BA7A4FD3C3B196F1D2E26F129D218657 | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\ARUinst.exe | executable | |
MD5:C7B5990CAC119F1E68AC22D25C2B7DAB | SHA256:78BB5C0F1122FA65BC0E63F35ECCA2A3FD50314D7E7E4610B82BD2898B6B24FF | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\DeleteFiles.exe | executable | |
MD5:C0CBA6A8CB94DF18ED537A512D9DAACA | SHA256:1EE42C7BB92B88EFE2B5293D37DBA2BFE9AE14742E89001E9743876E92416425 | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\uninstall.bat | text | |
MD5:86A74DE4BB5B49E32B24048FE9A5C584 | SHA256:A293E4E79B5B12C98F6E835D4534E3C120C66286D65DCE325E5C3683B6228BAC | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\HookDriver32.sys | executable | |
MD5:103FD50F3255B5EB51ABFEDDCF817146 | SHA256:C884AF03495CD0C10CD621BC7D91855ADDA86CCEEF359ED82166044223DB305F | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\tsc.ptn | ptn | |
MD5:91579E7604ACD27CDA70B73C43116C1C | SHA256:CD6895EED246F92A4D938030989F462E499DFFC16042E13B00B9E31C48E6B744 | |||
| 1832 | AntiRansomware32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:2CD7858B552D50076A58997428610CD2 | SHA256:777C996358B99A3B31C9D3170302E72AA8600085E305F7713B16EC978D8848A5 | |||
| 1920 | ransomware.exe | C:\Program Files\AntiRansomware2.0\ServiceManager.exe | executable | |
MD5:2EA57429D207D737C53FFD8CCB3E825E | SHA256:D370618906316C6AB2BF705C56E6ACE9A0C32637A30161CE24D53083F4A5D8AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1832 | AntiRansomware32.exe | GET | 200 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?578ef341f98f0ac4 | unknown | — | — | whitelisted |
1832 | AntiRansomware32.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/certs/Microsoft%20Development%20Root%20Certificate%20Authority%202014.crt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
— | — | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1832 | AntiRansomware32.exe | 2.19.126.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
1832 | AntiRansomware32.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ARService.exe | My Sample Service: Main: Entry
|
ARService.exe | My Sample Service: ServiceMain: Entry
|
ARService.exe | My Sample Service: ServiceMain: Performing Service Start Operations
|
ARService.exe | My Sample Service: ServiceMain: Waiting for Worker Thread to complete
|
ARService.exe | My Sample Service: ServiceWorkerThread: Entry
|