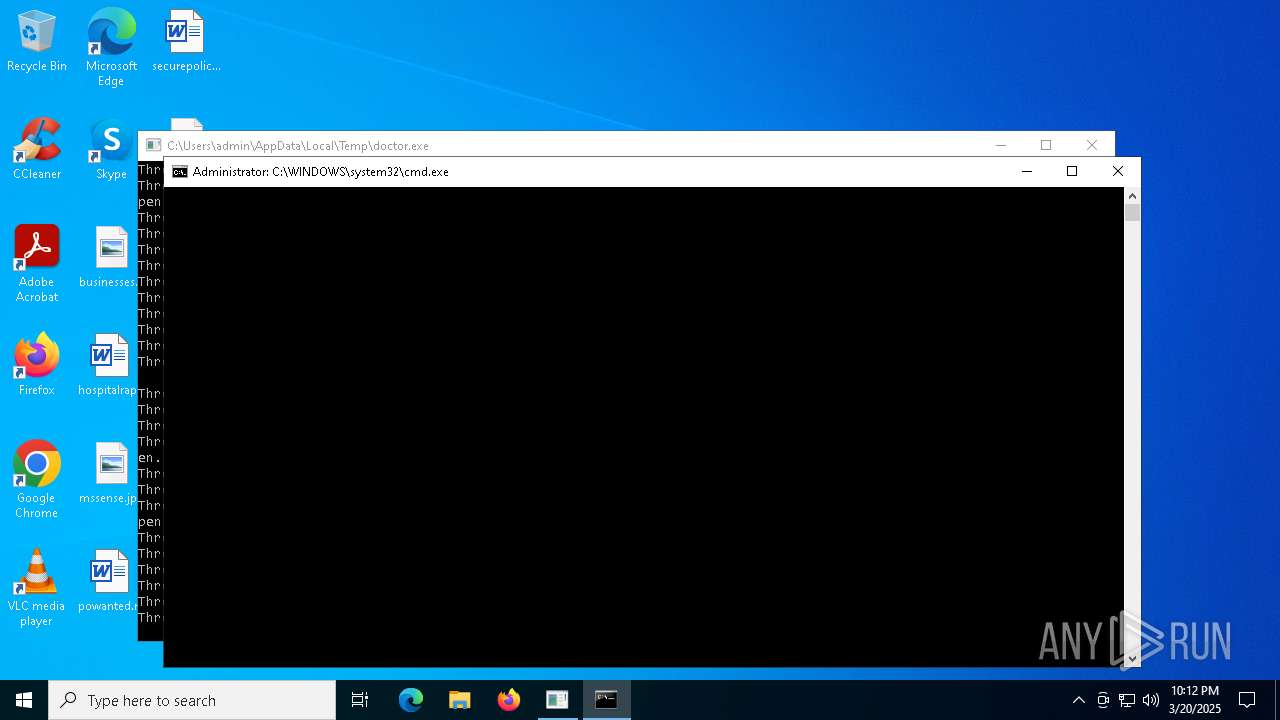
| File name: | doctor.exe |
| Full analysis: | https://app.any.run/tasks/83c302e3-3f58-4181-a5bf-de054c5c7814 |
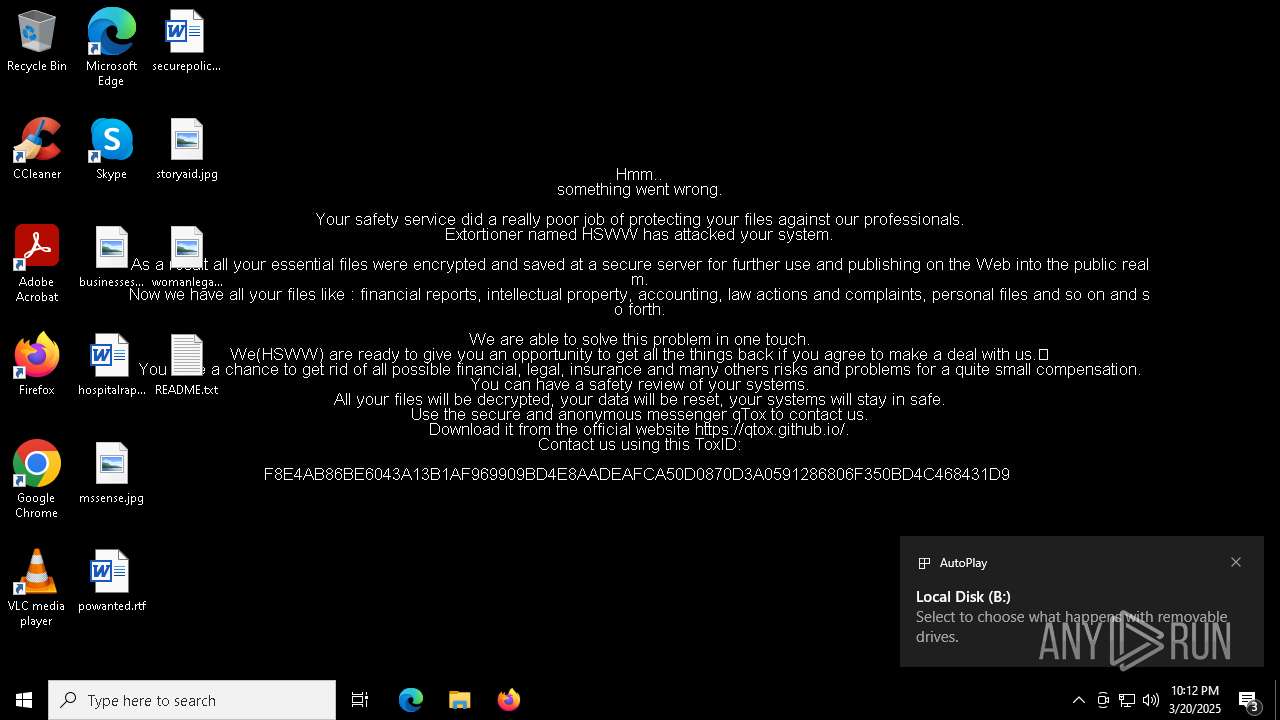
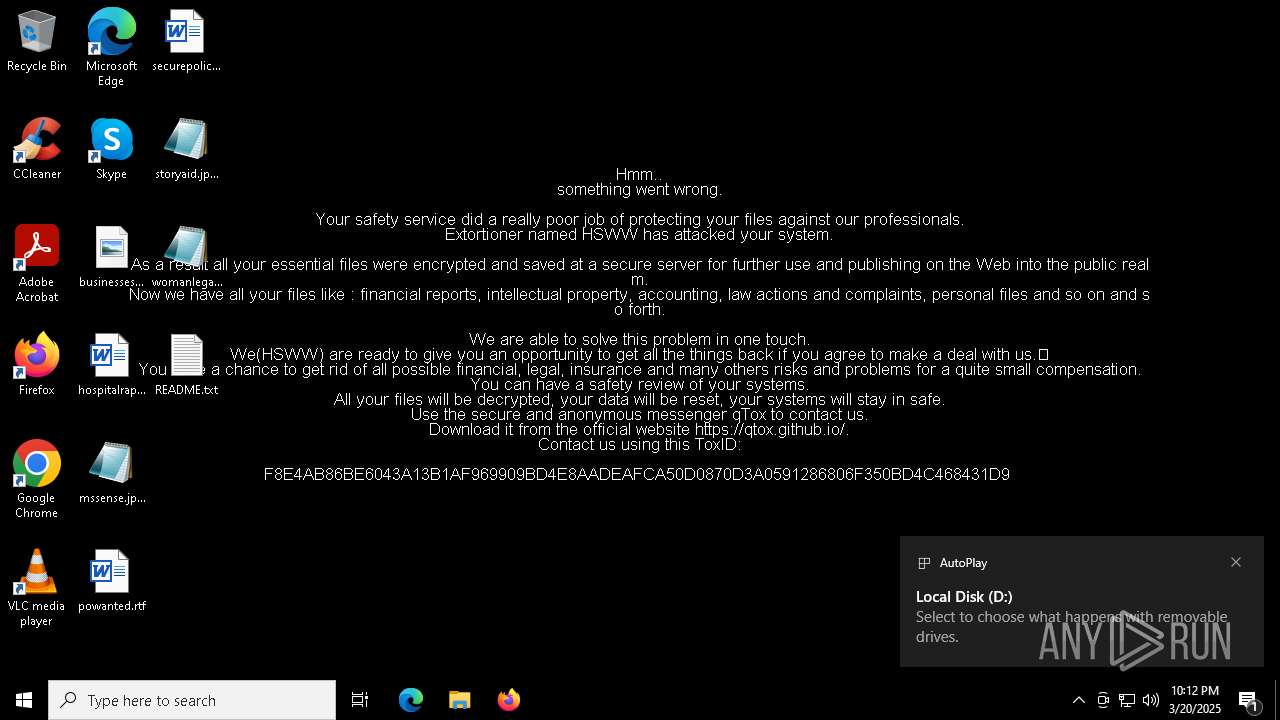
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2025, 22:11:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | FF8DDFFC1F59A2D6E97AD21CCE2C507C |
| SHA1: | 4E40DBD646F55169DEFA72C0F482F11437033803 |
| SHA256: | 5B4535B3A064CEA8C97F4330917725FD343CCFA05827B4A69825EFC7DAD35CA0 |
| SSDEEP: | 24576:pGrJAEq+4Lm9y7JMNCiktD9gBb9/sx7SKDrl:HEqm9y7JMgiktD9gBb9Ex7SKDr |
MALICIOUS
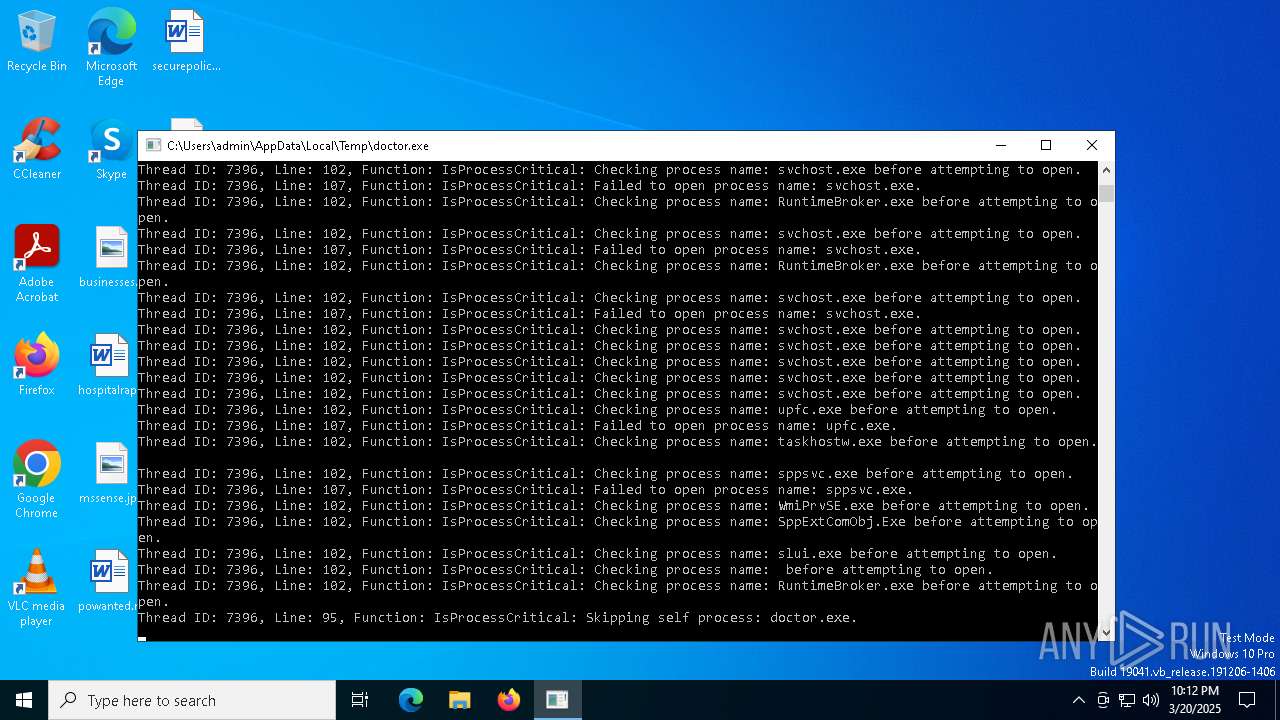
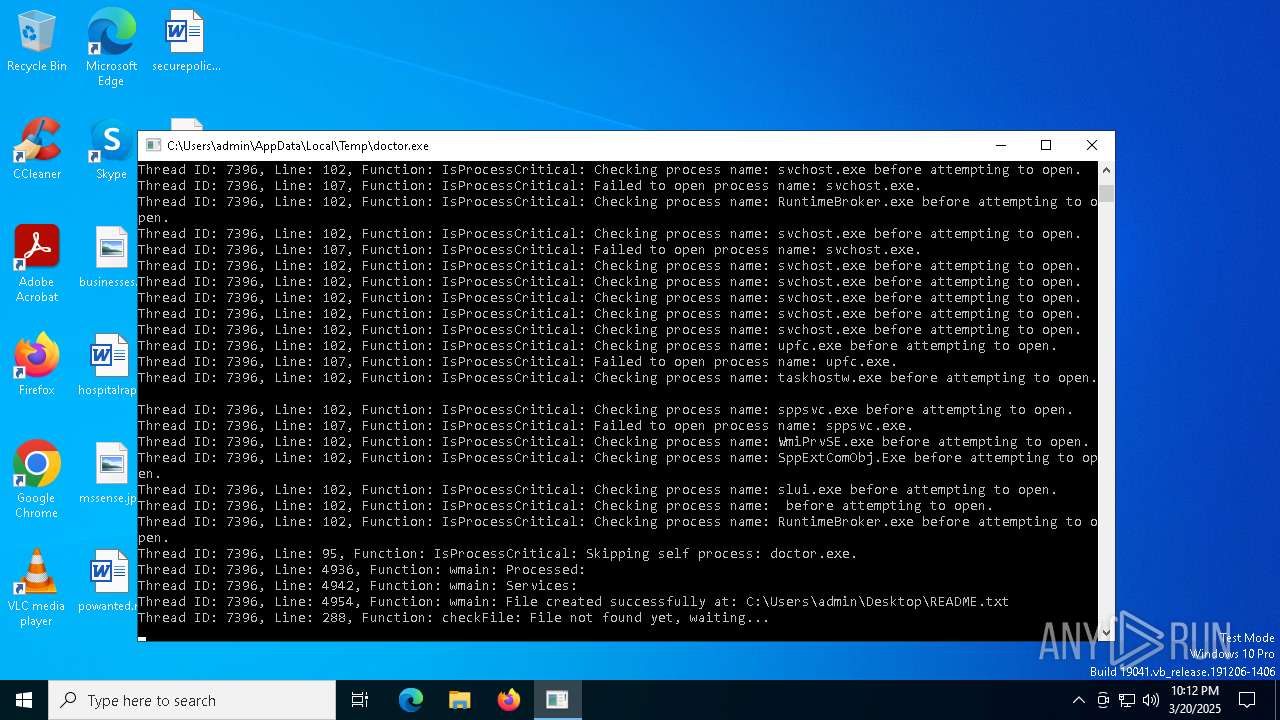
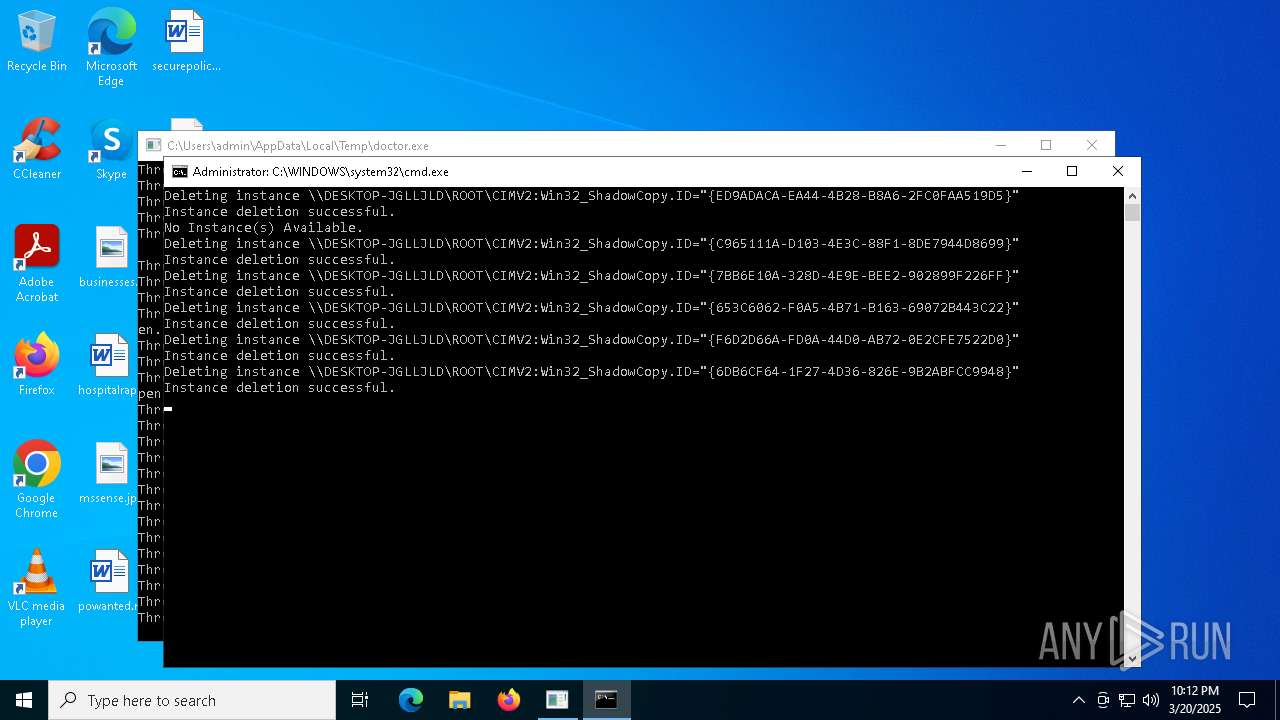
Deletes shadow copies
- powershell.exe (PID: 7944)
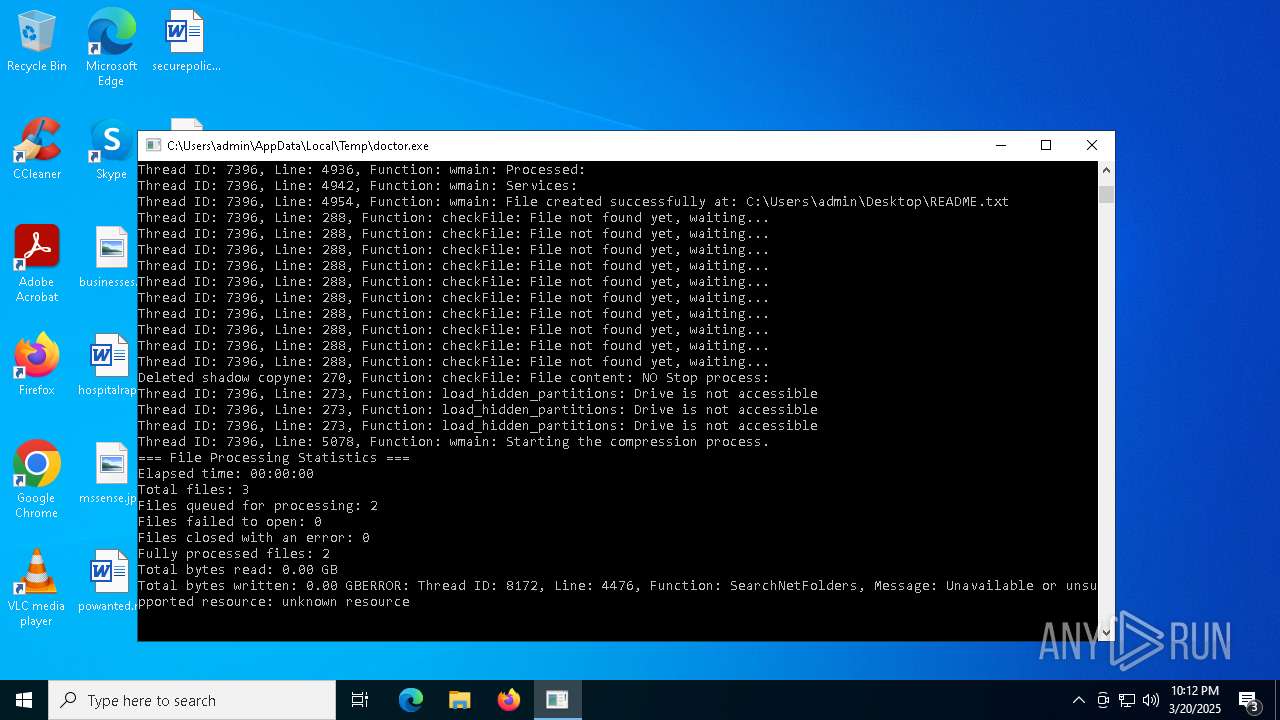
Renames files like ransomware
- doctor.exe (PID: 7400)
Starts CMD.EXE for self-deleting
- doctor.exe (PID: 7400)
SUSPICIOUS
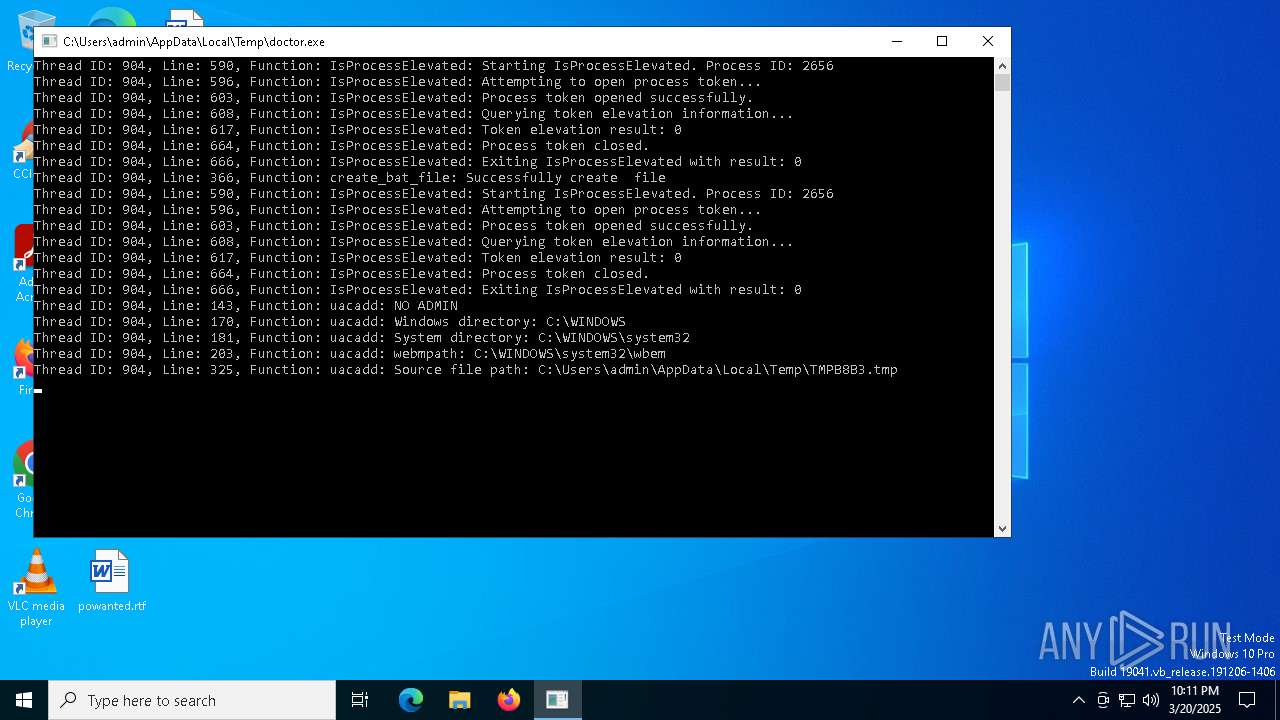
Reads the date of Windows installation
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
Executable content was dropped or overwritten
- dllhost.exe (PID: 960)
- doctor.exe (PID: 2656)
Hides command output
- cmd.exe (PID: 4224)
- cmd.exe (PID: 7156)
Starts CMD.EXE for commands execution
- doctor.exe (PID: 2656)
- mmc.exe (PID: 7448)
- mmc.exe (PID: 2564)
- doctor.exe (PID: 7400)
Reads security settings of Internet Explorer
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4224)
Executing commands from a ".bat" file
- mmc.exe (PID: 7448)
- mmc.exe (PID: 2564)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7404)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7504)
- powershell.exe (PID: 7576)
- cmd.exe (PID: 7404)
- powershell.exe (PID: 7308)
Application launched itself
- powershell.exe (PID: 7576)
- powershell.exe (PID: 7308)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7308)
Uses WMIC.EXE to obtain shadow copy information
- powershell.exe (PID: 7944)
Executes as Windows Service
- VSSVC.exe (PID: 6044)
INFO
Reads the computer name
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
- ShellExperienceHost.exe (PID: 920)
Checks supported languages
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
- ShellExperienceHost.exe (PID: 920)
Reads the machine GUID from the registry
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
Create files in a temporary directory
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 960)
- BackgroundTransferHost.exe (PID: 4920)
- mmc.exe (PID: 7448)
- BackgroundTransferHost.exe (PID: 7612)
- BackgroundTransferHost.exe (PID: 7772)
- BackgroundTransferHost.exe (PID: 7200)
- mmc.exe (PID: 2564)
- WMIC.exe (PID: 3008)
- WMIC.exe (PID: 4040)
- WMIC.exe (PID: 7676)
- WMIC.exe (PID: 7792)
- WMIC.exe (PID: 6512)
- WMIC.exe (PID: 6576)
- WMIC.exe (PID: 1096)
- WMIC.exe (PID: 7924)
- WMIC.exe (PID: 7788)
- WMIC.exe (PID: 8048)
Checks transactions between databases Windows and Oracle
- doctor.exe (PID: 2656)
Process checks computer location settings
- doctor.exe (PID: 2656)
- doctor.exe (PID: 7400)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7612)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7612)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7612)
The executable file from the user directory is run by the Powershell process
- doctor.exe (PID: 7400)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7944)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7308)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:20 11:07:15+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 853504 |
| InitializedDataSize: | 173056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9dfe0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
179
Monitored processes
43
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\WINDOWS\System32\Wbem\WMIC.exe" shadowcopy where ID='{F6D2D66A-FD0A-44D0-AB72-0E2CFE7522D0}' delete | C:\Windows\System32\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | "C:\Windows\System32\mmc.exe" WmiMgmt.msc | C:\Windows\System32\mmc.exe | — | doctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 3221225547 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2656 | "C:\Users\admin\AppData\Local\Temp\doctor.exe" | C:\Users\admin\AppData\Local\Temp\doctor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3008 | "C:\WINDOWS\System32\Wbem\WMIC.exe" shadowcopy where ID='{653C6062-F0A5-4B71-B163-69072B443C22}' delete | C:\Windows\System32\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\WINDOWS\System32\Wbem\WMIC.exe" shadowcopy list brief /format:list | C:\Windows\System32\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | "C:\Windows\System32\cmd.exe" /C ping 127.0.0.1 -n 6 > nul & start mmc.exe WmiMgmt.msc | C:\Windows\System32\cmd.exe | — | doctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | ping 127.0.0.1 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4784 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 579
Read events
26 556
Write events
23
Delete events
0
Modification events
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7772) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7772) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7772) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7996) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
56
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b06676f2-398d-43d4-90c4-2260c9d9507d.down_data | — | |
MD5:— | SHA256:— | |||
| 7308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0cq1sl2u.k05.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7612 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:F95A197EE4145A3B48CBFAAA81A78C2F | SHA256:9F1337BF8806F9EAE5204CE368A7F6375BE713ED66B9116012497B069B3055EA | |||
| 7576 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_abeoyhlt.yzb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7576 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ctfwqar3.unt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7612 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\cf20883f-9f41-4387-8e74-1bc02aa3f56b.8dadbca9-5533-4a3a-9a0f-22e77bf8312e.down_meta | binary | |
MD5:97BDA97CC37BE8801C6FB3C46EE61E2F | SHA256:C23CFAF7B1A52E0817EB86A80F77C7D7F85571EA642253C2EDD937176E40F201 | |||
| 7612 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:16819BF408313D19C4BB1CF4F9684243 | SHA256:9FE4EF7DD94022F24F6ECF635FF62058CBCDCBA156568F5F3FD9D98767180C22 | |||
| 7308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jvdlr004.al0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7296 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:65AC756E81FB637A4E9F9988C2E4AAF1 | SHA256:34EB39D1AD78AFC36C7D3F0DDA345D48078B5ABD56C9E726B966F664EC0C7D8F | |||
| 7612 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b06676f2-398d-43d4-90c4-2260c9d9507d.8dadbca9-5533-4a3a-9a0f-22e77bf8312e.down_meta | binary | |
MD5:97BDA97CC37BE8801C6FB3C46EE61E2F | SHA256:C23CFAF7B1A52E0817EB86A80F77C7D7F85571EA642253C2EDD937176E40F201 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7612 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1184 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
736 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
736 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.24.77.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1184 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |