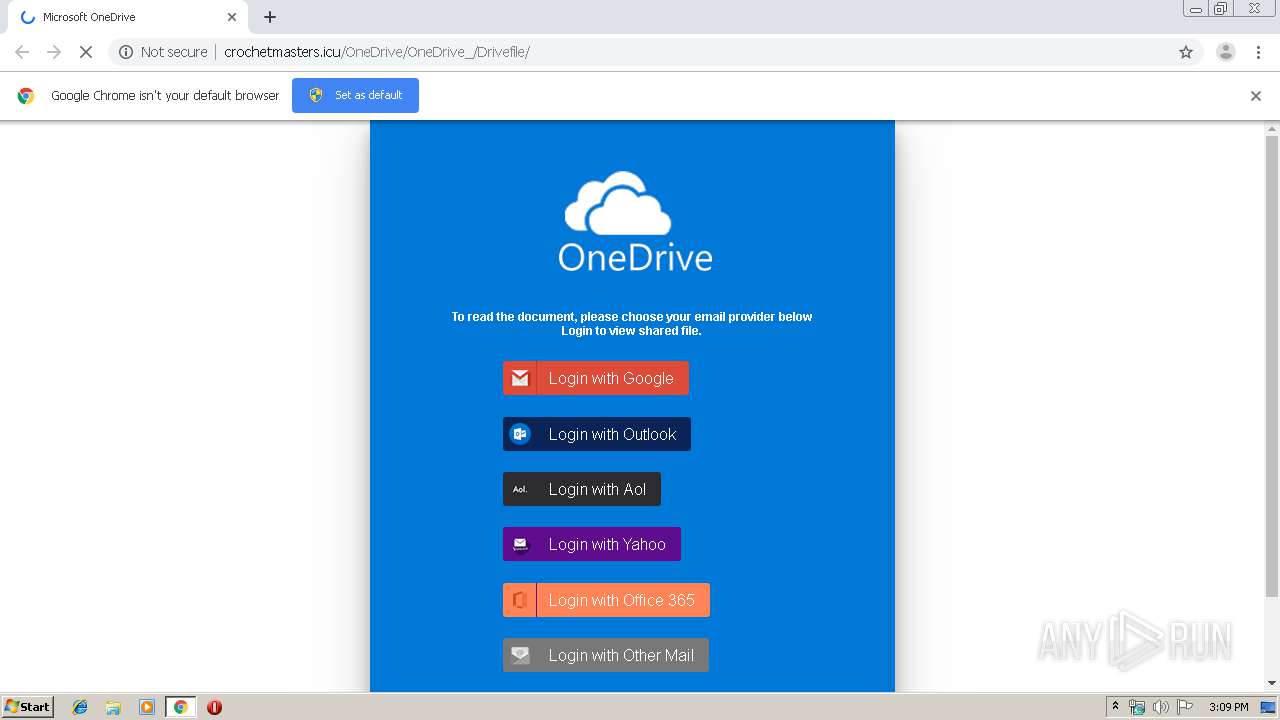
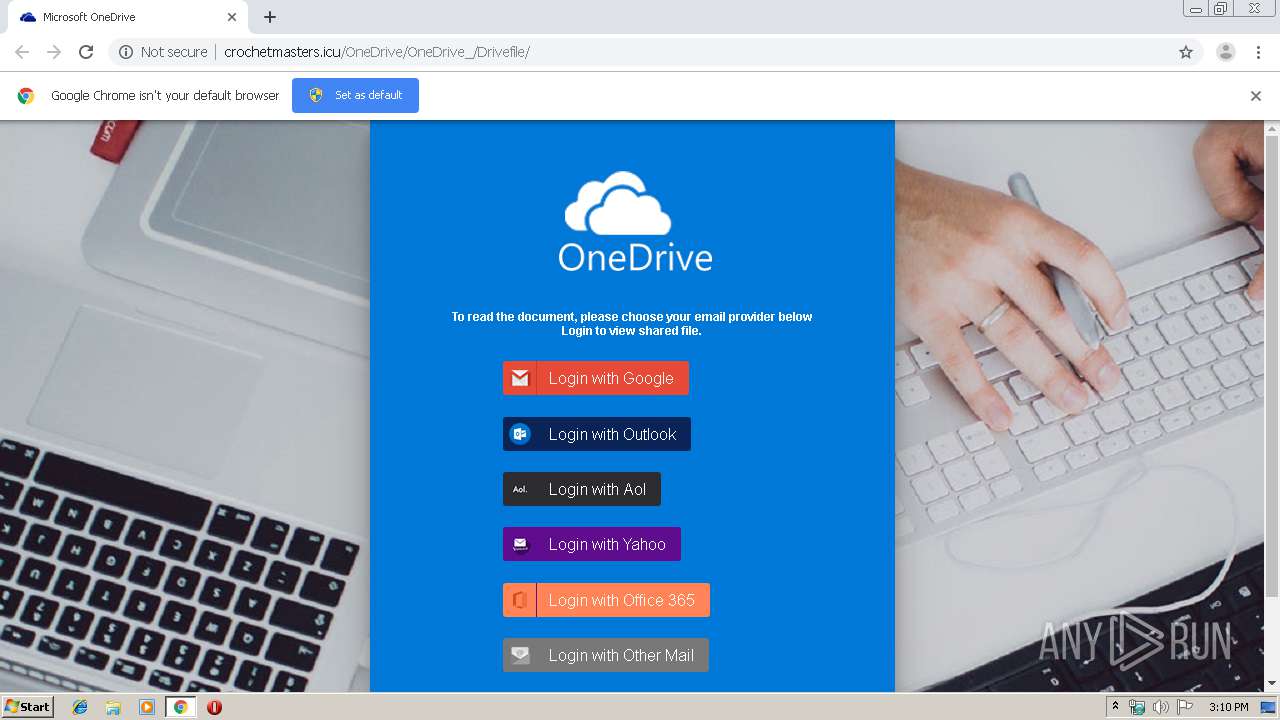
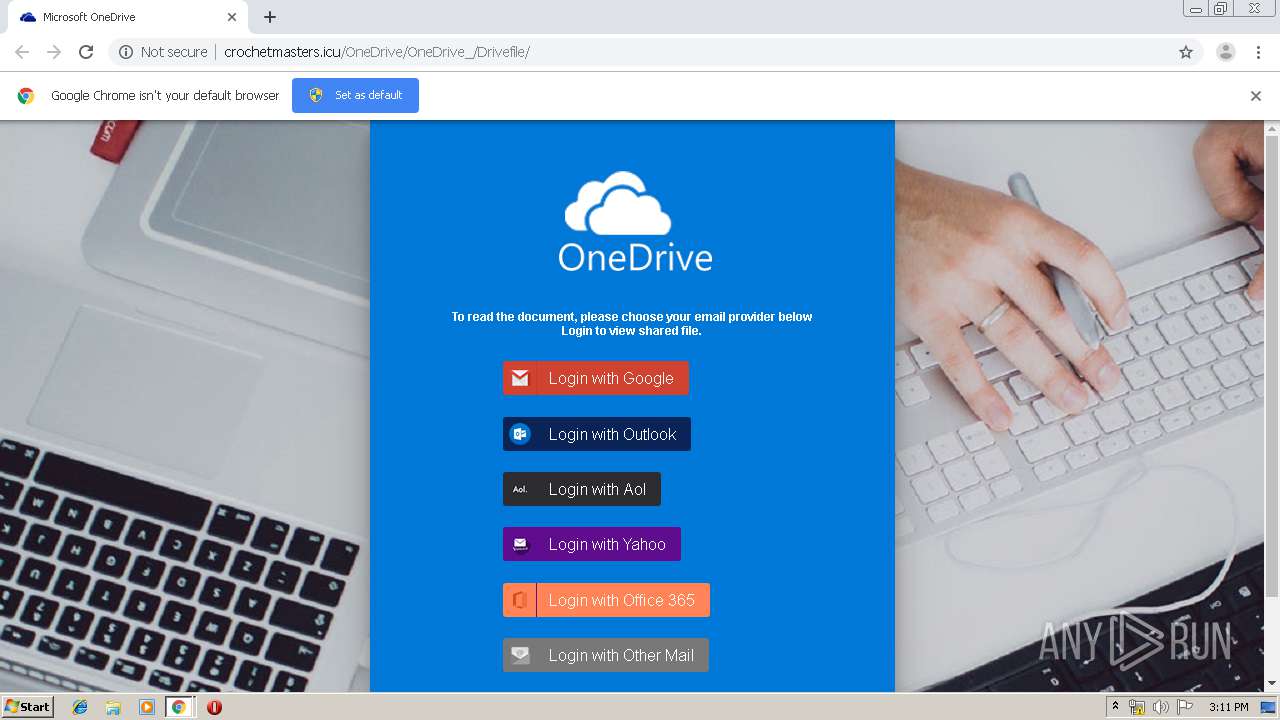
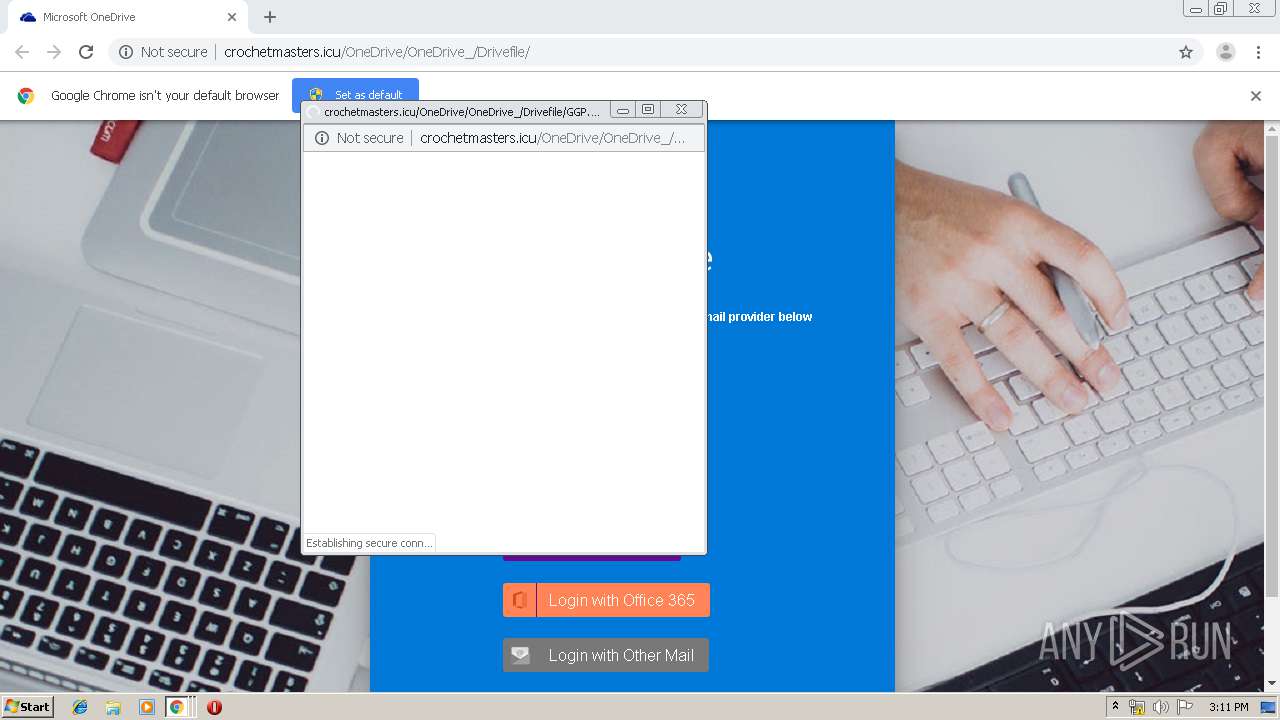
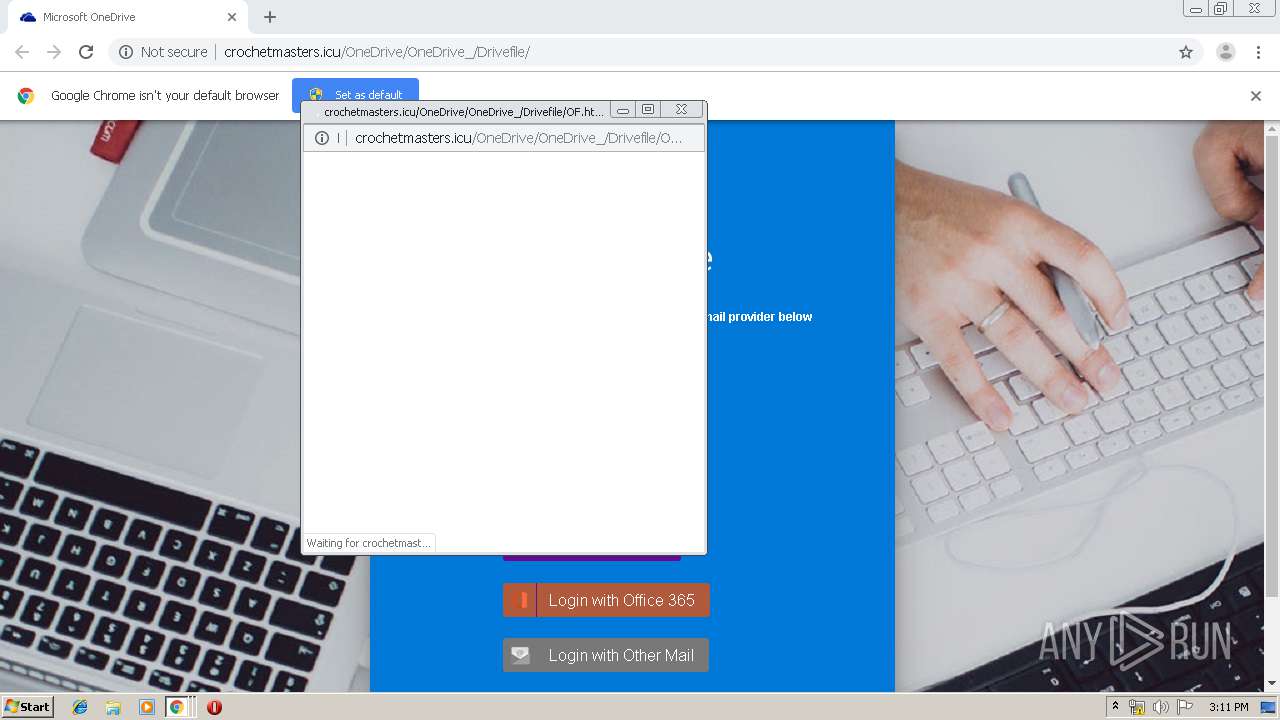
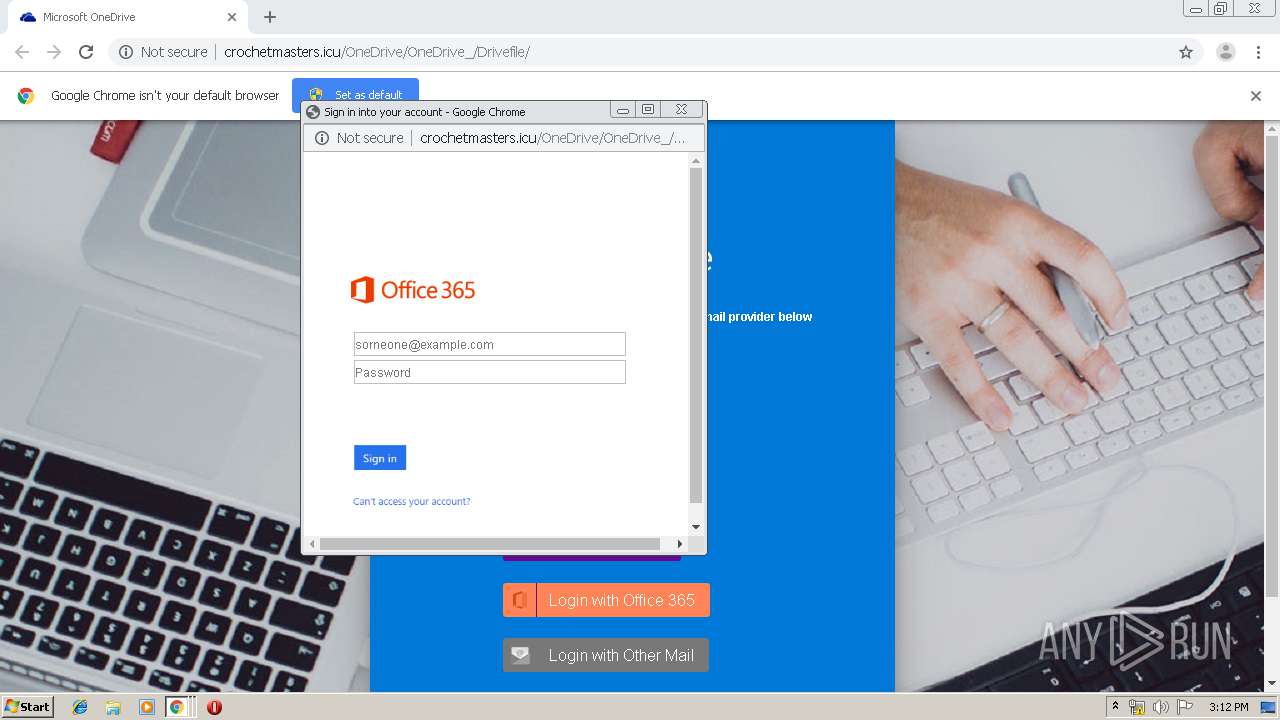
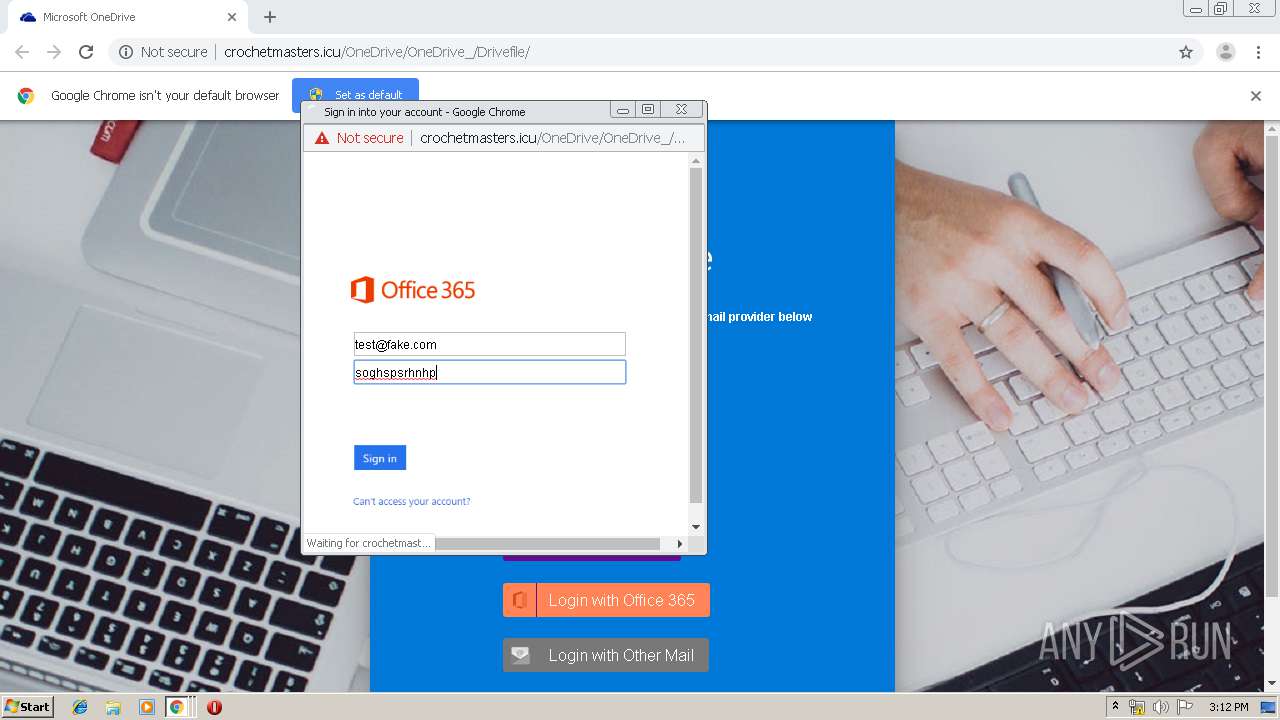
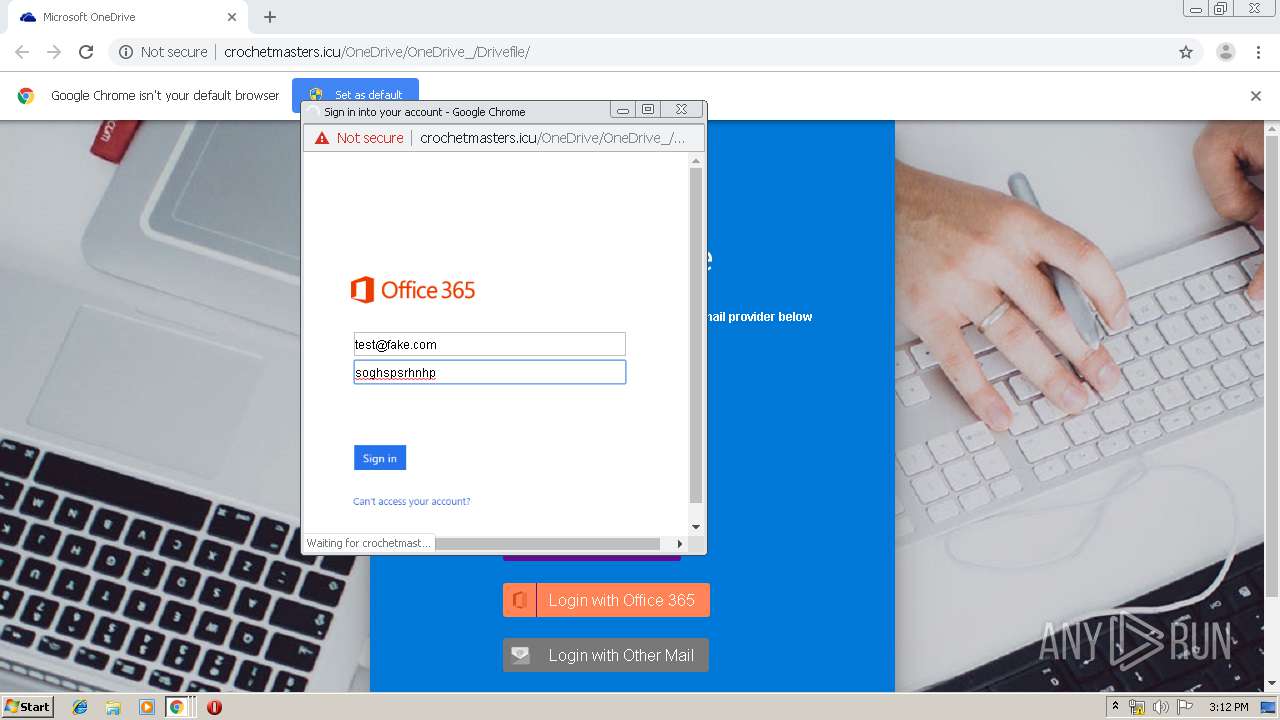
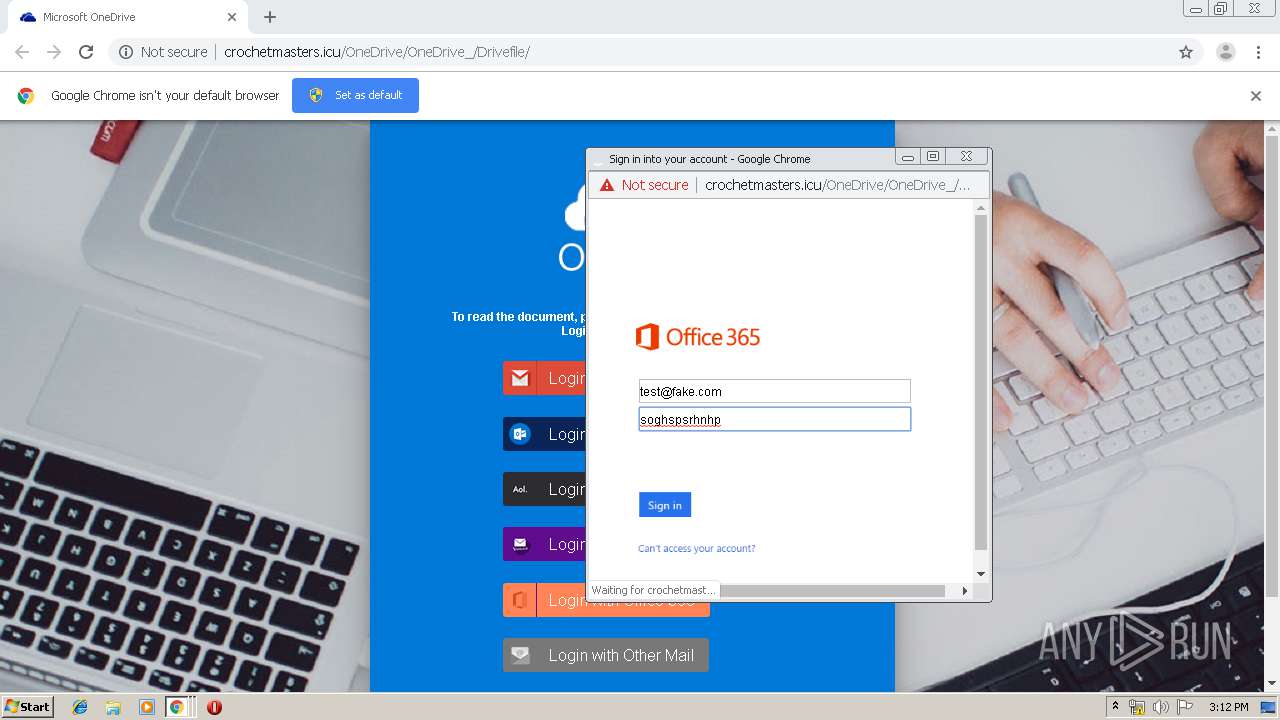
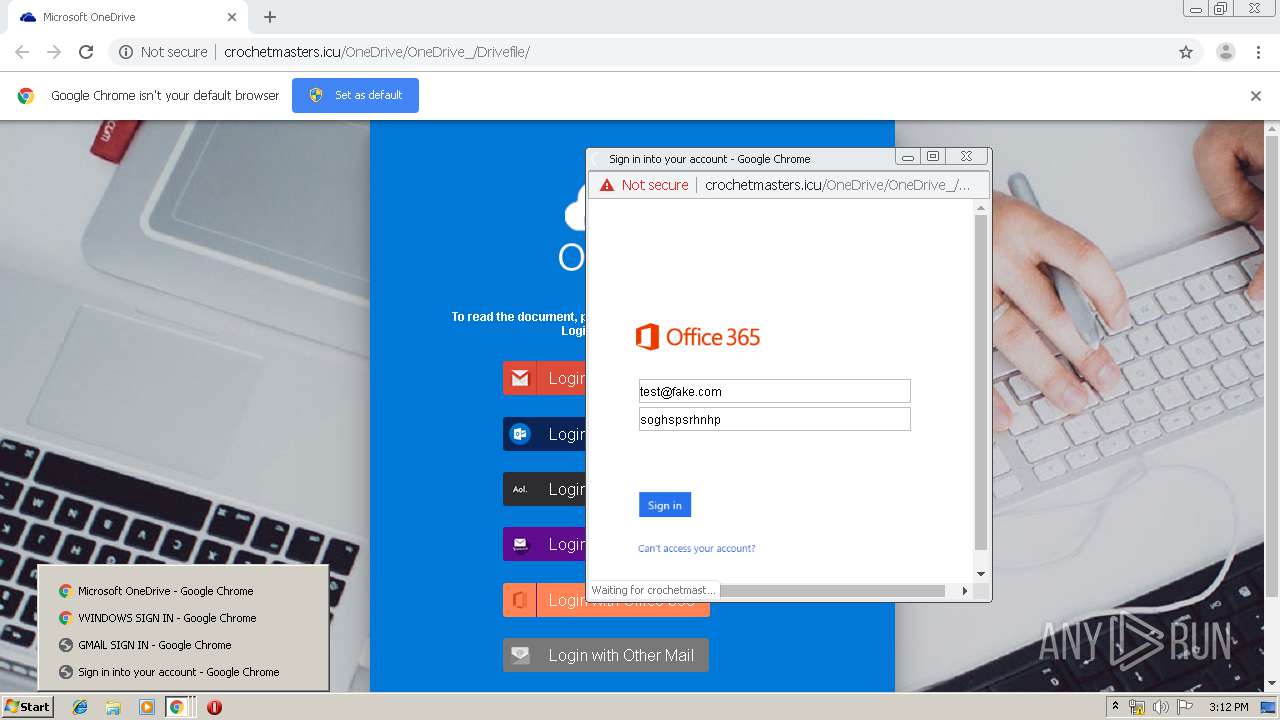
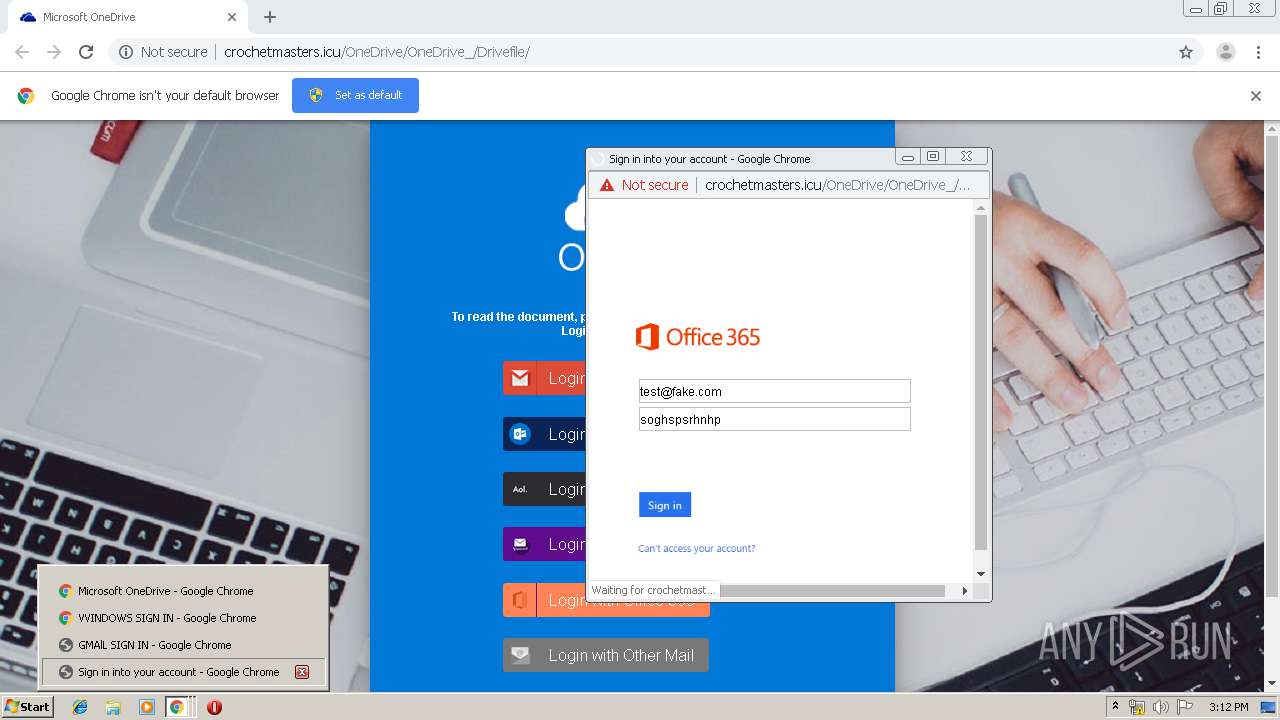
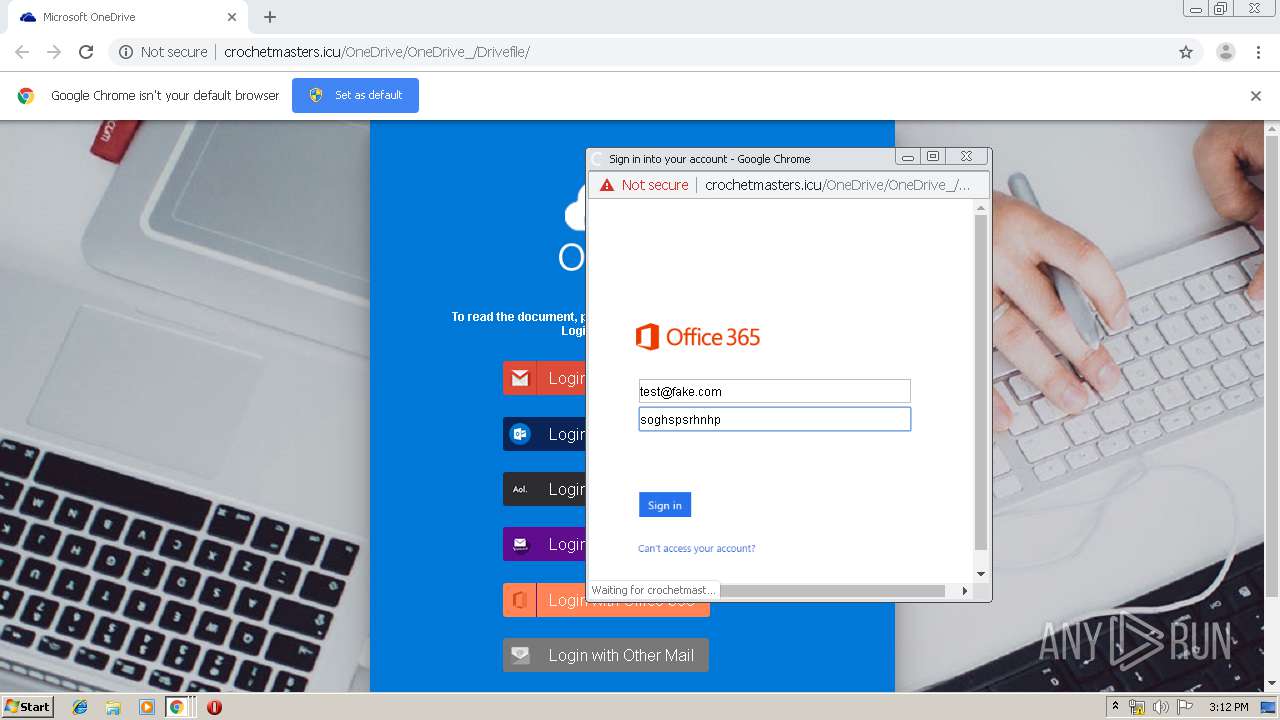
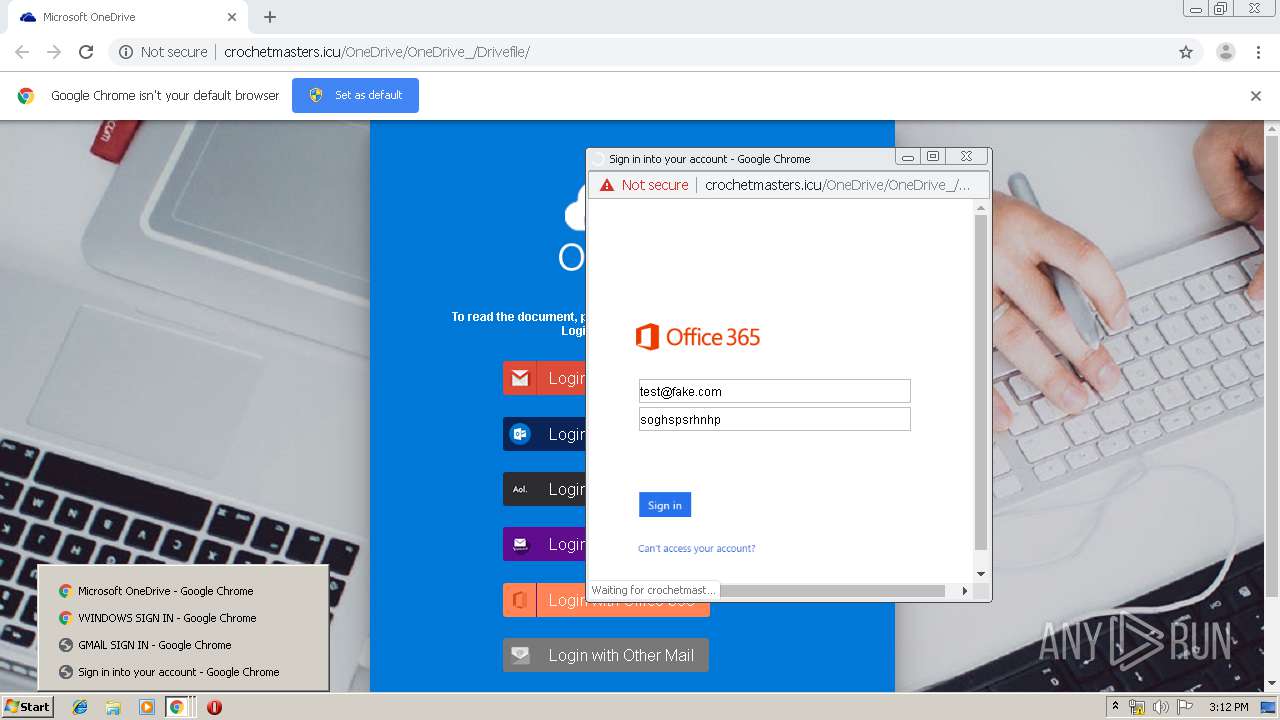
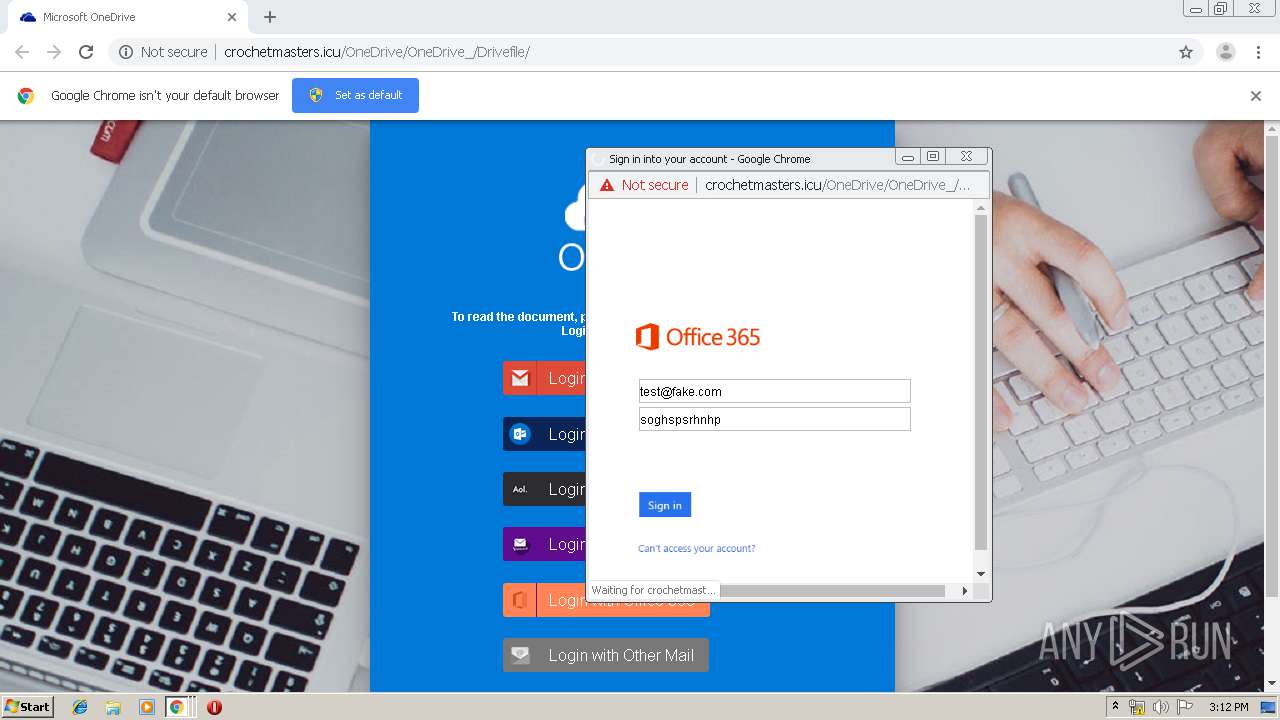
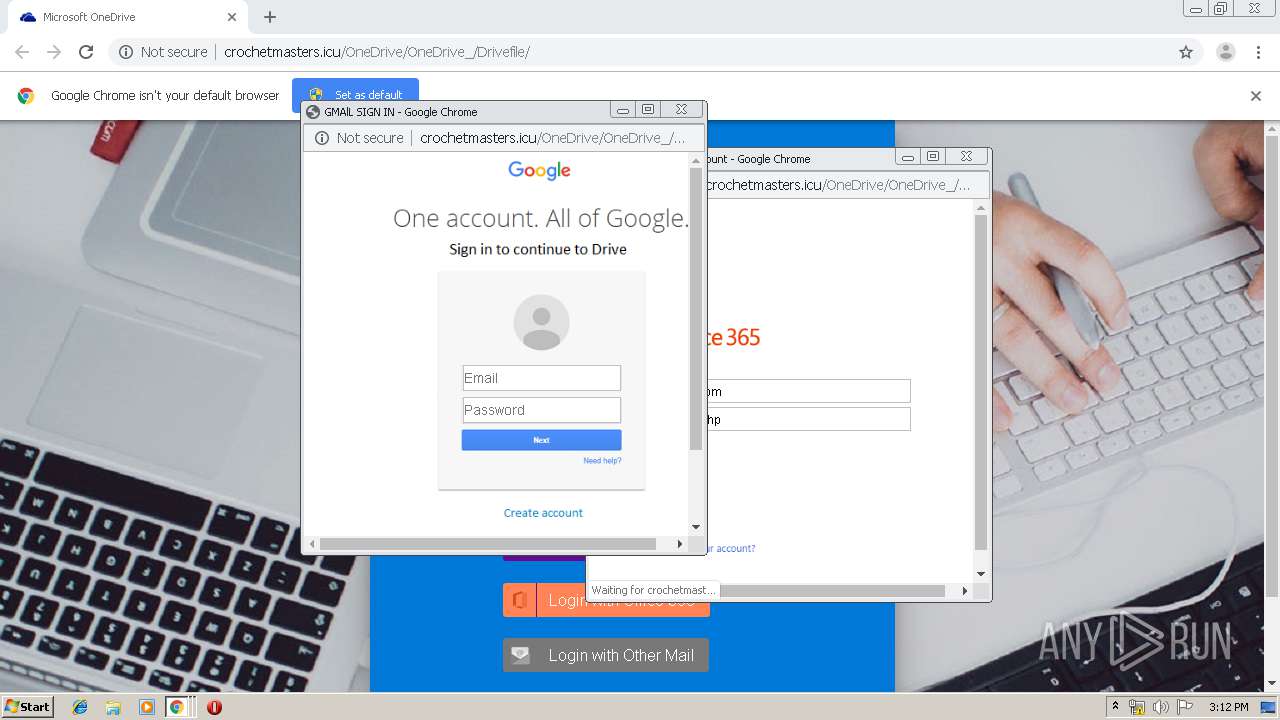
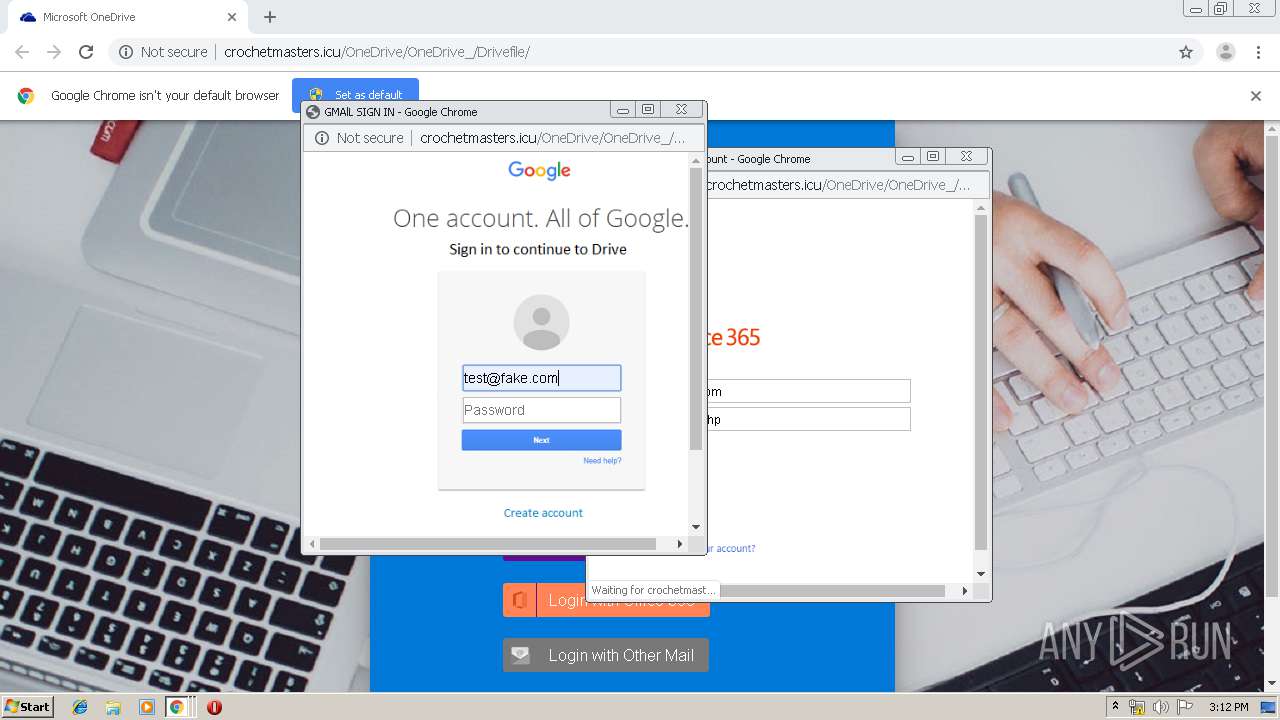
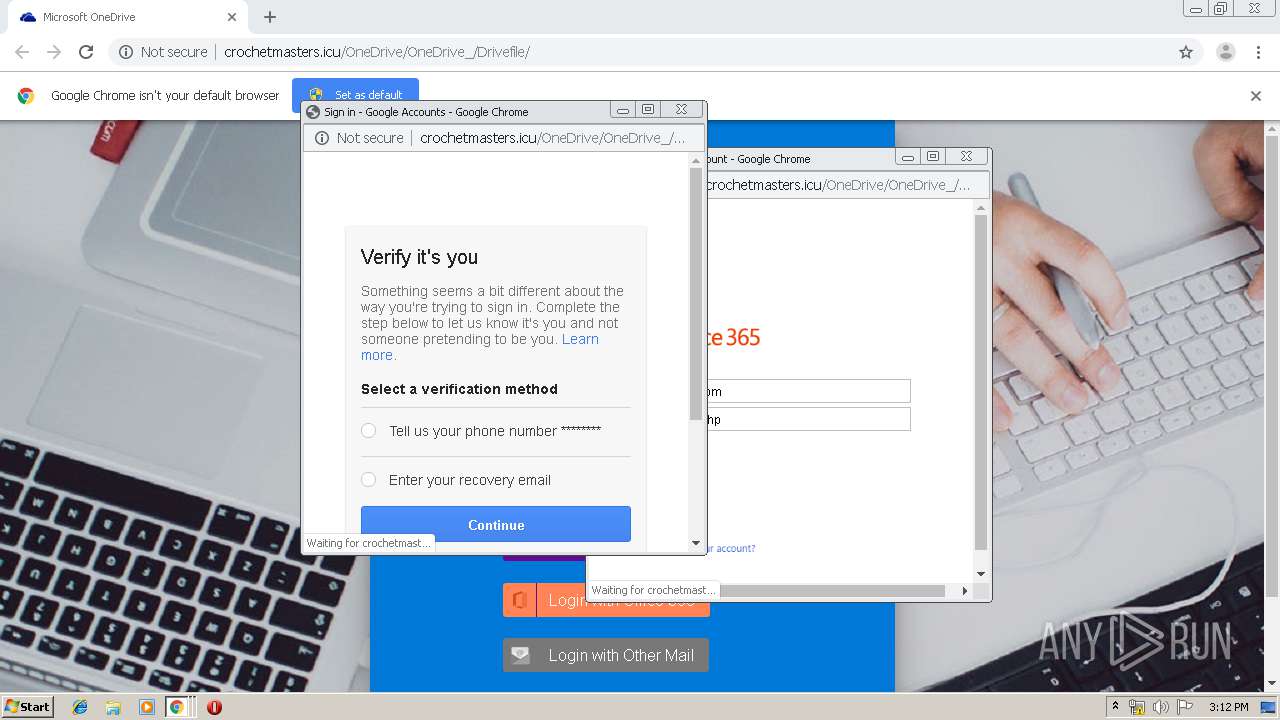
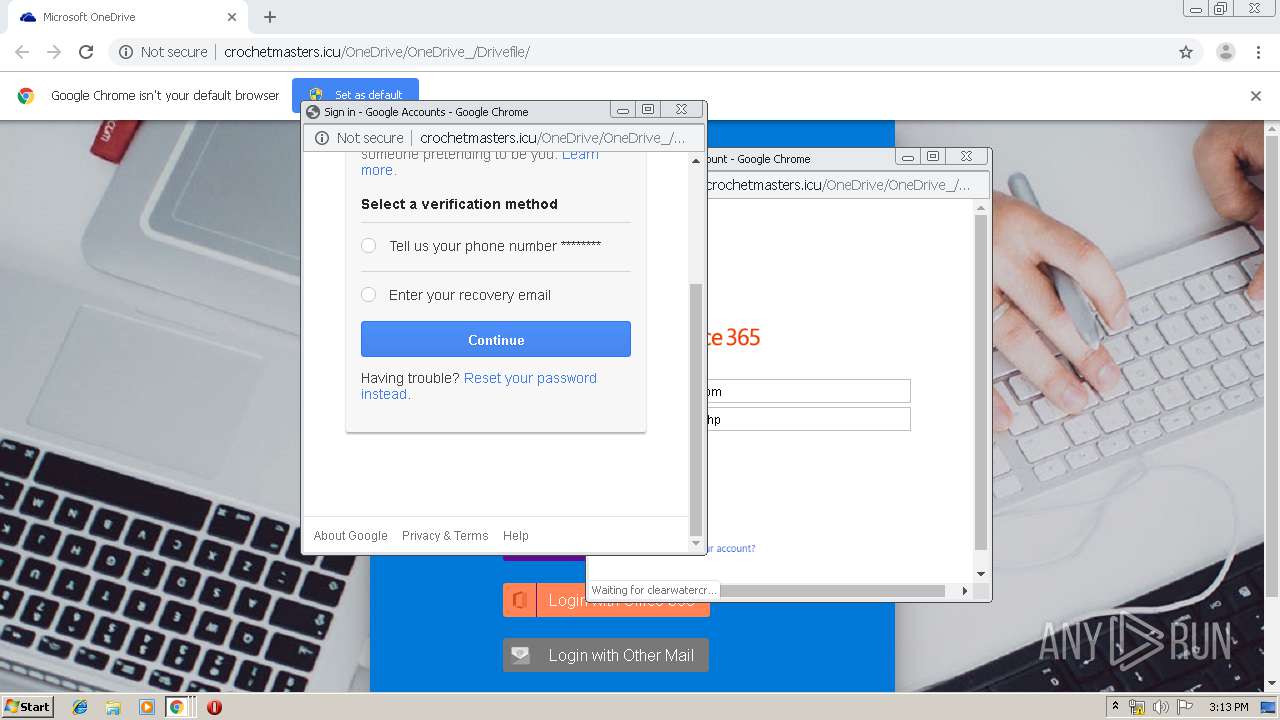
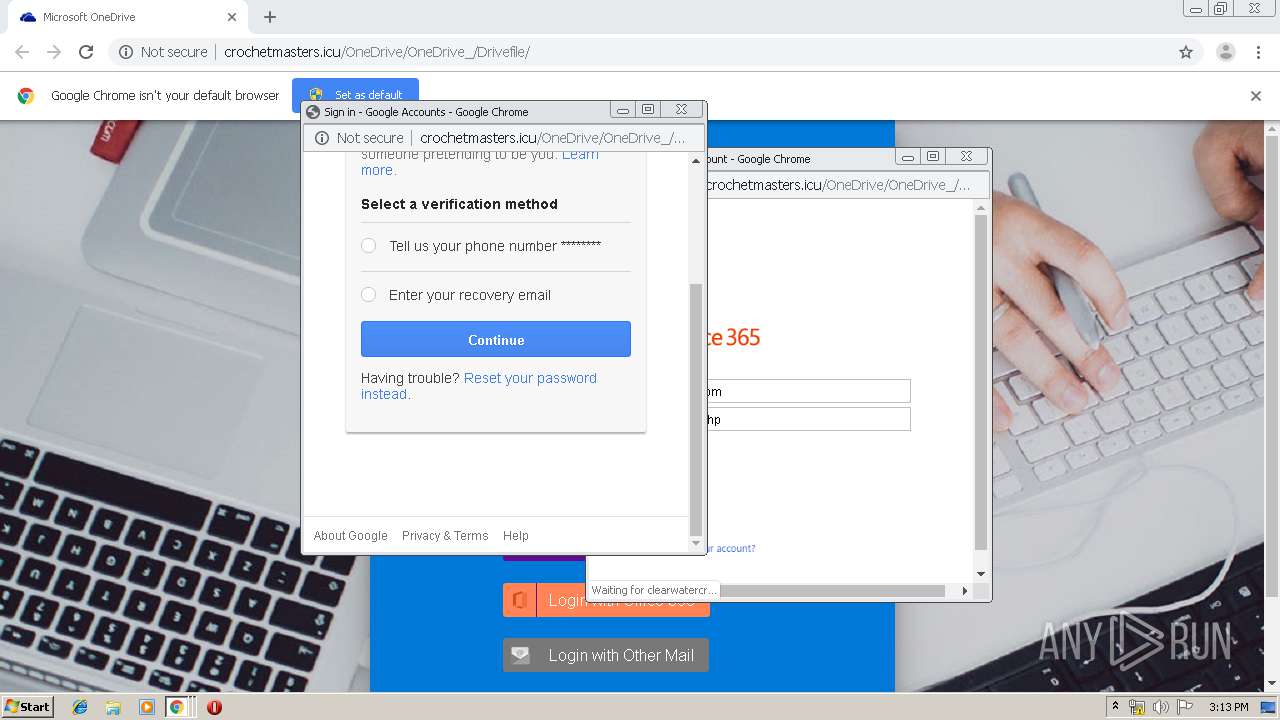
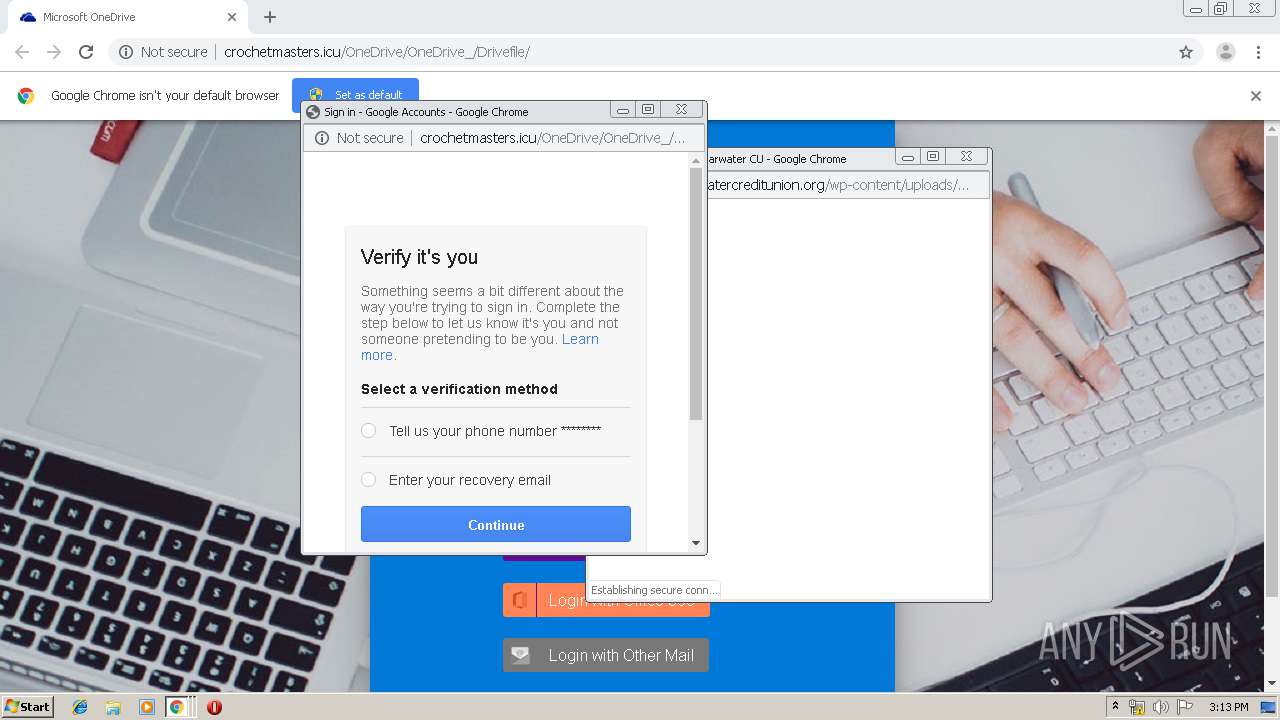
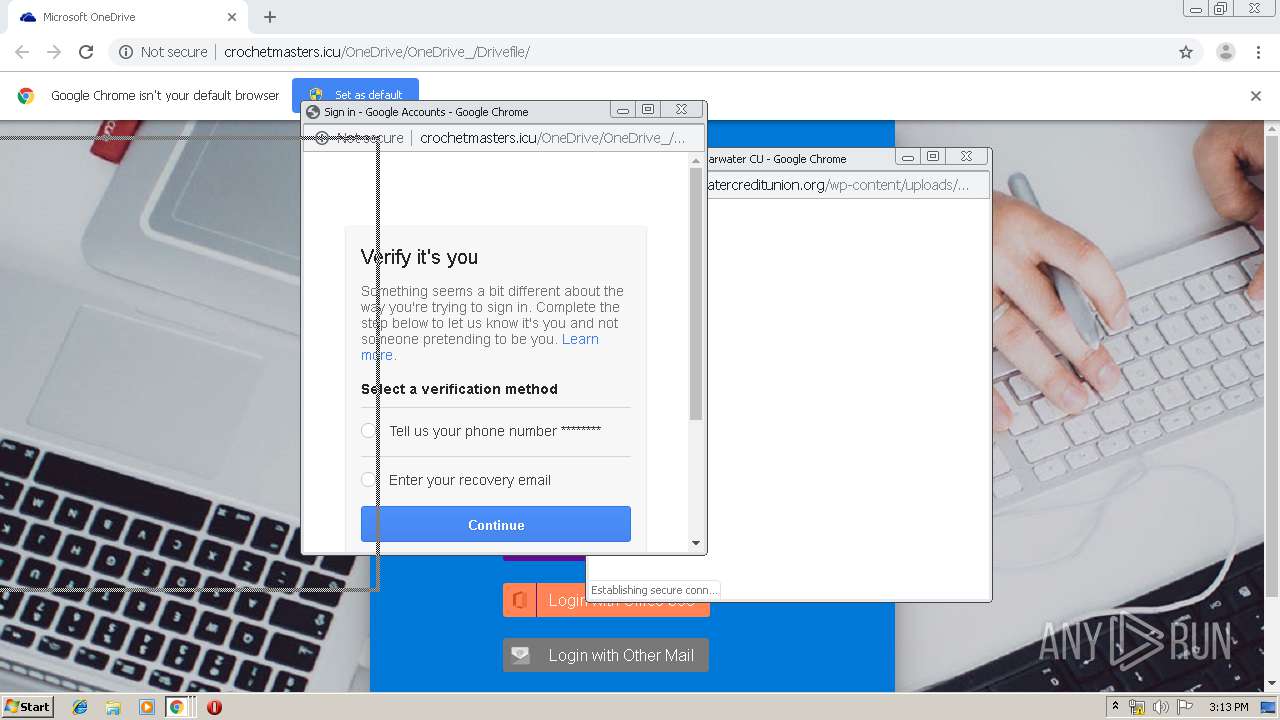
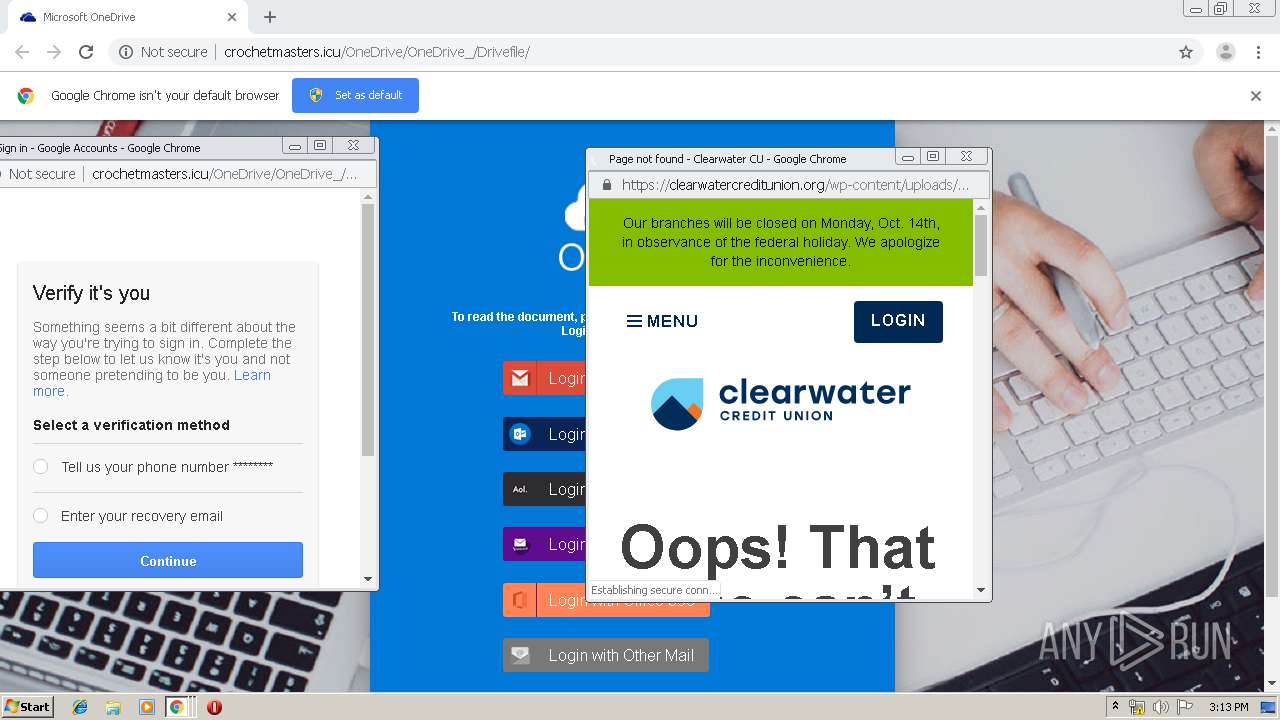
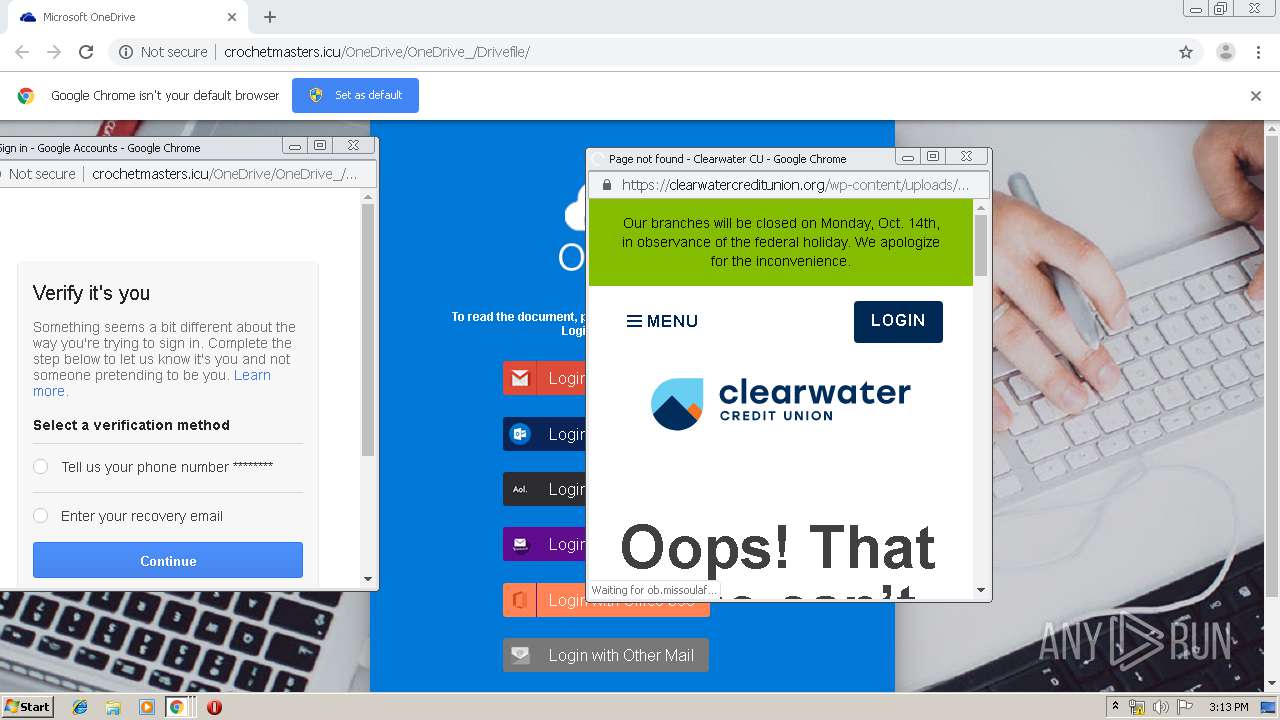
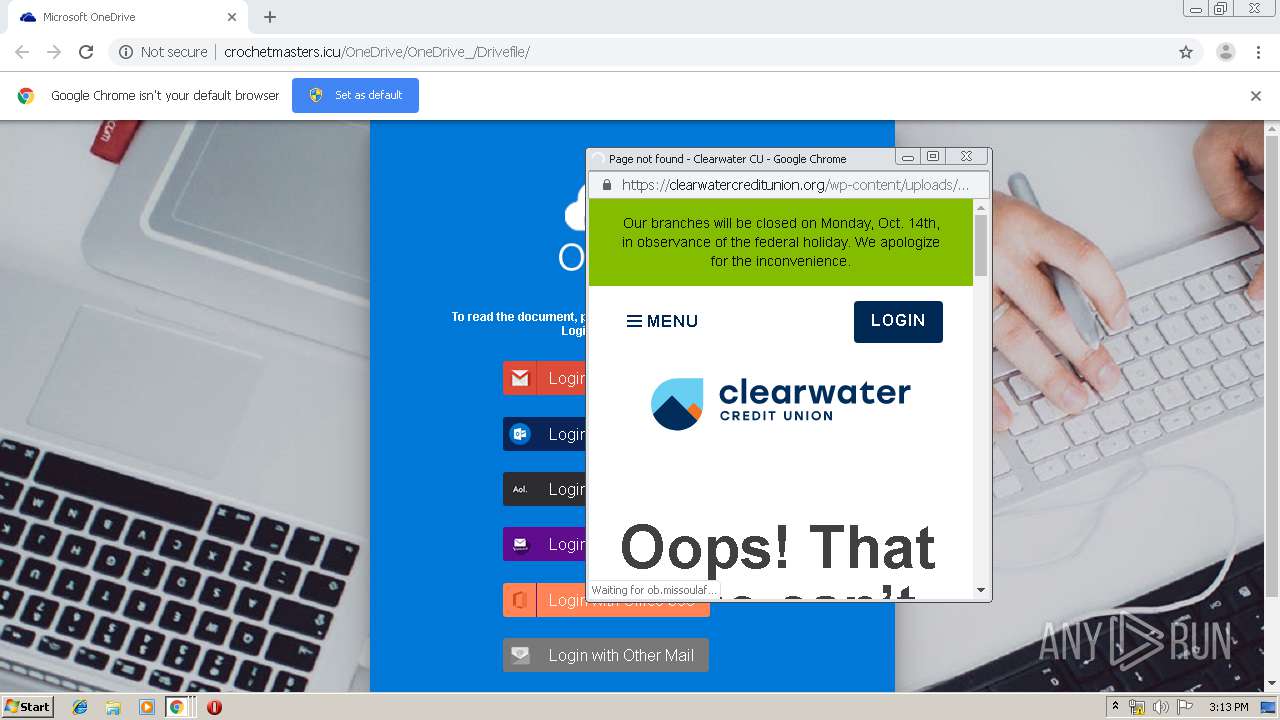
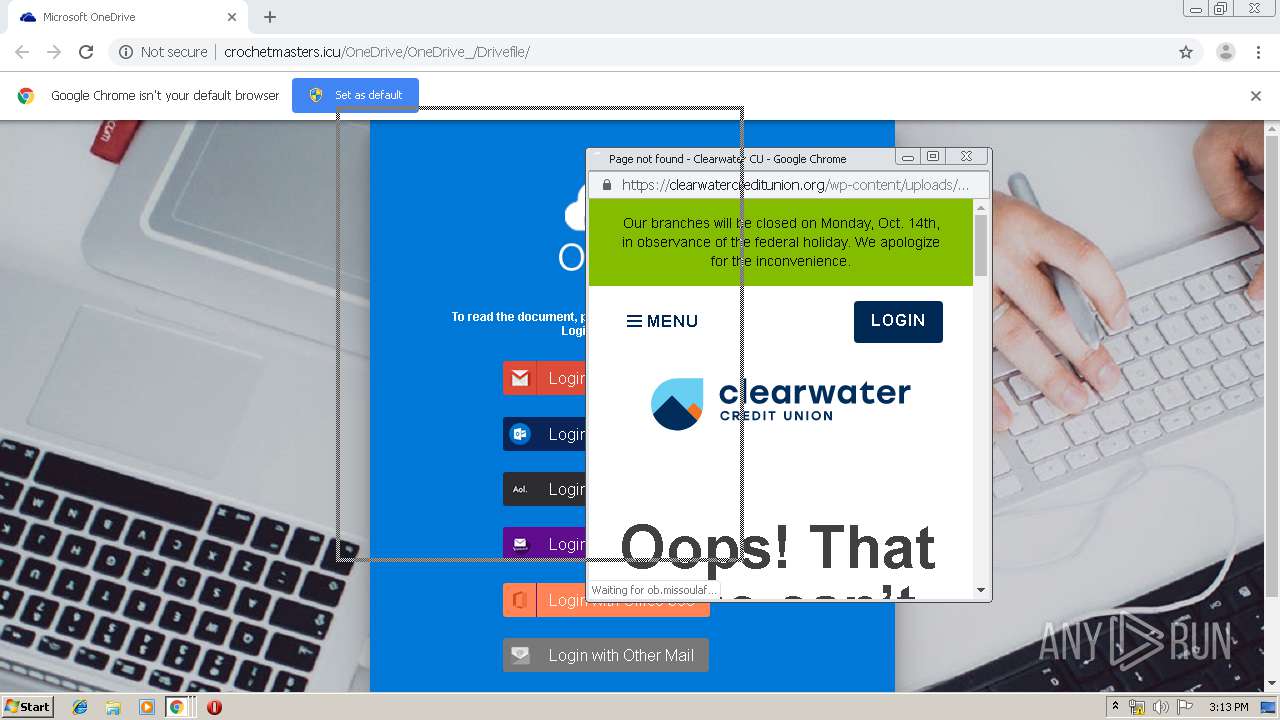
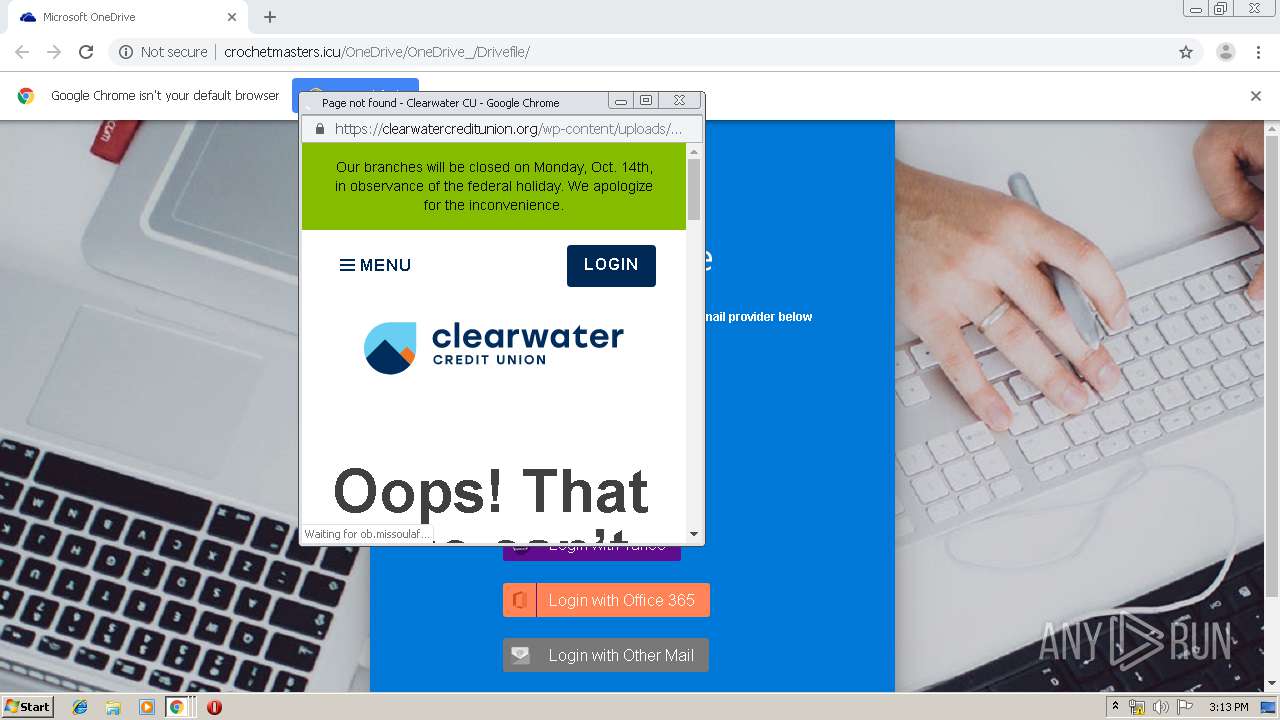
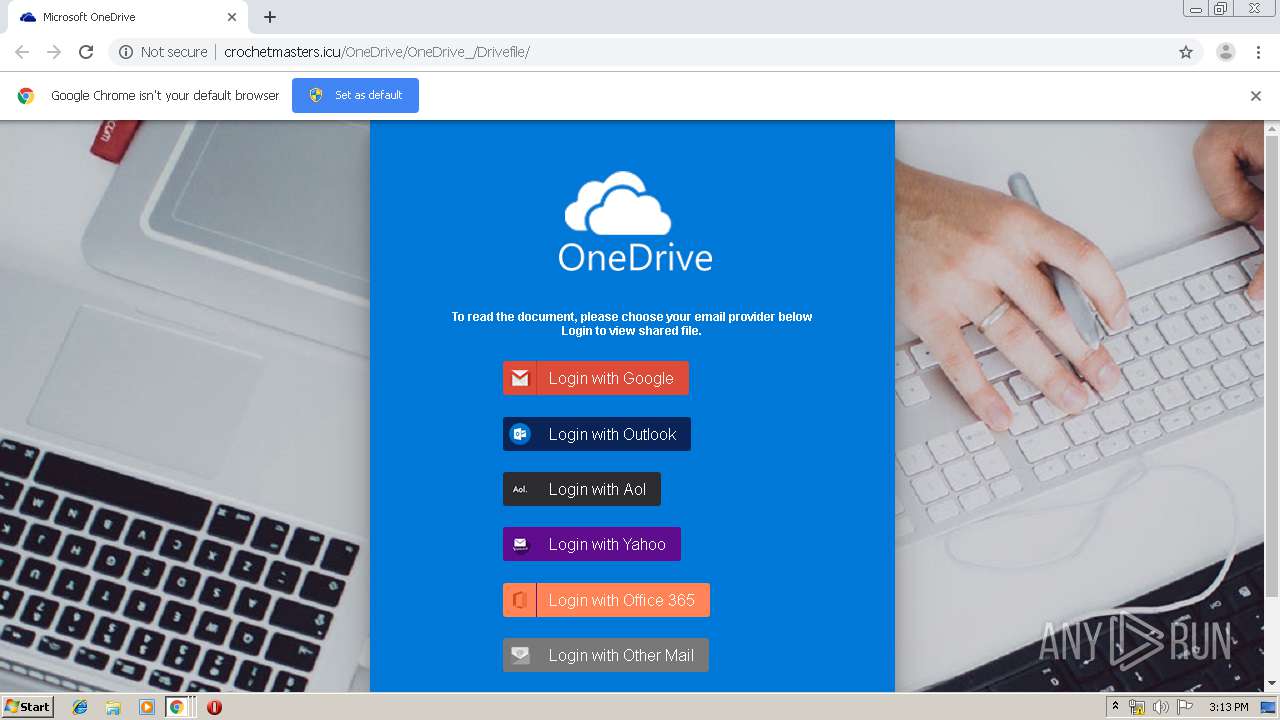
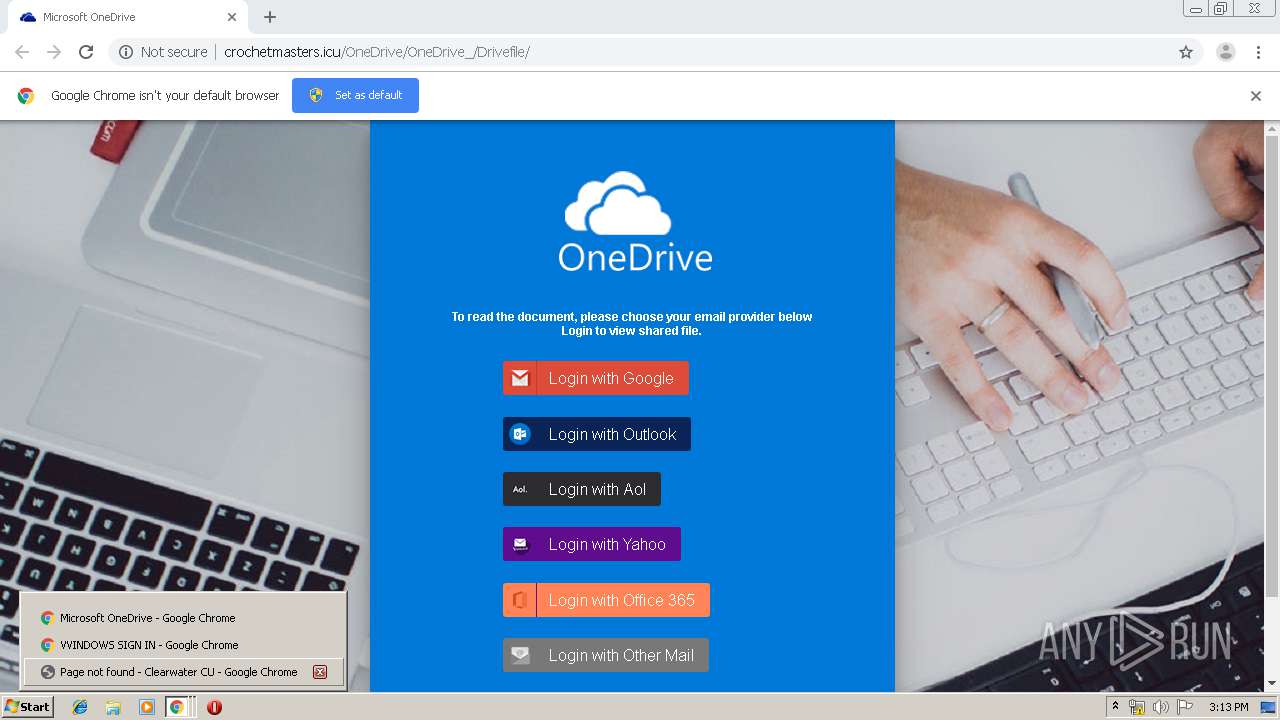
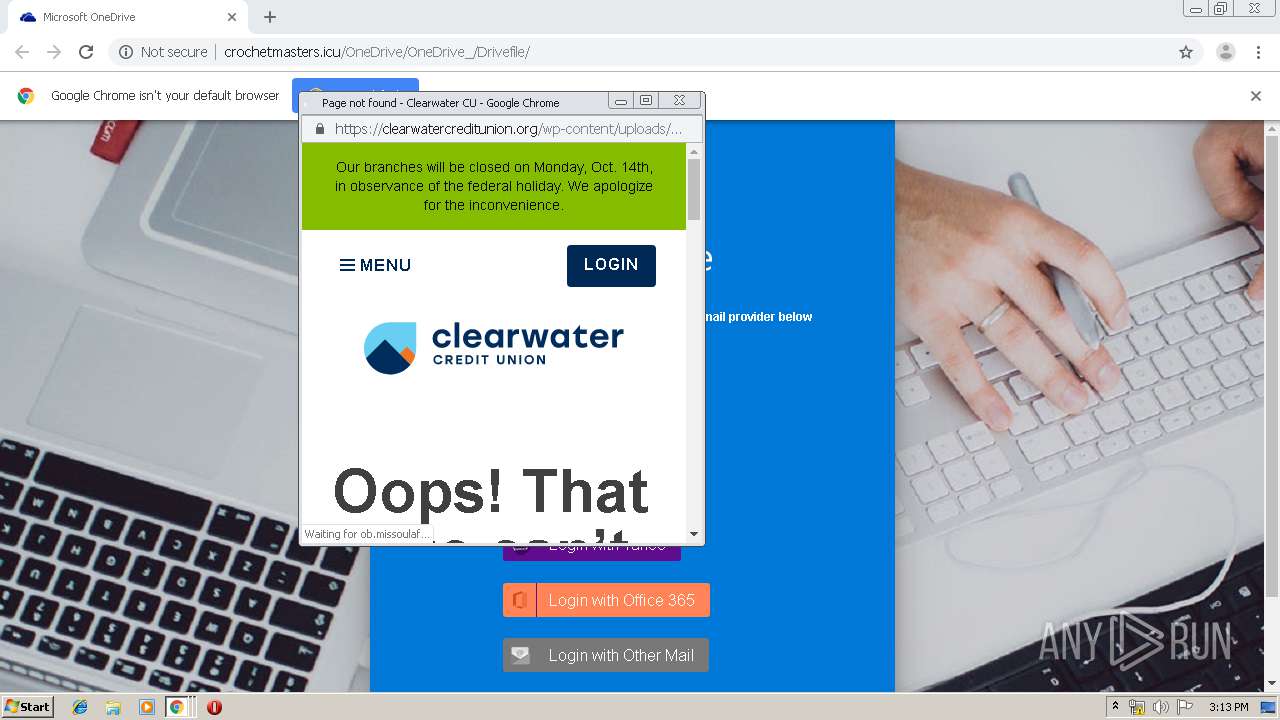
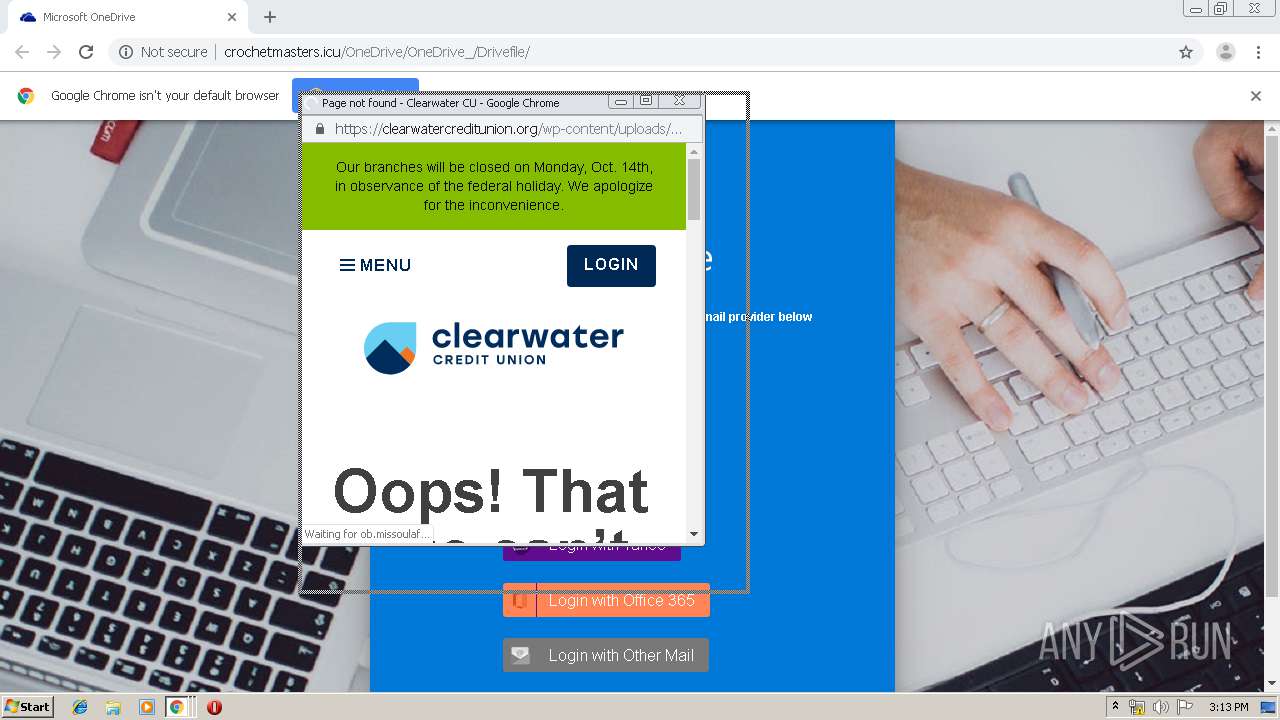
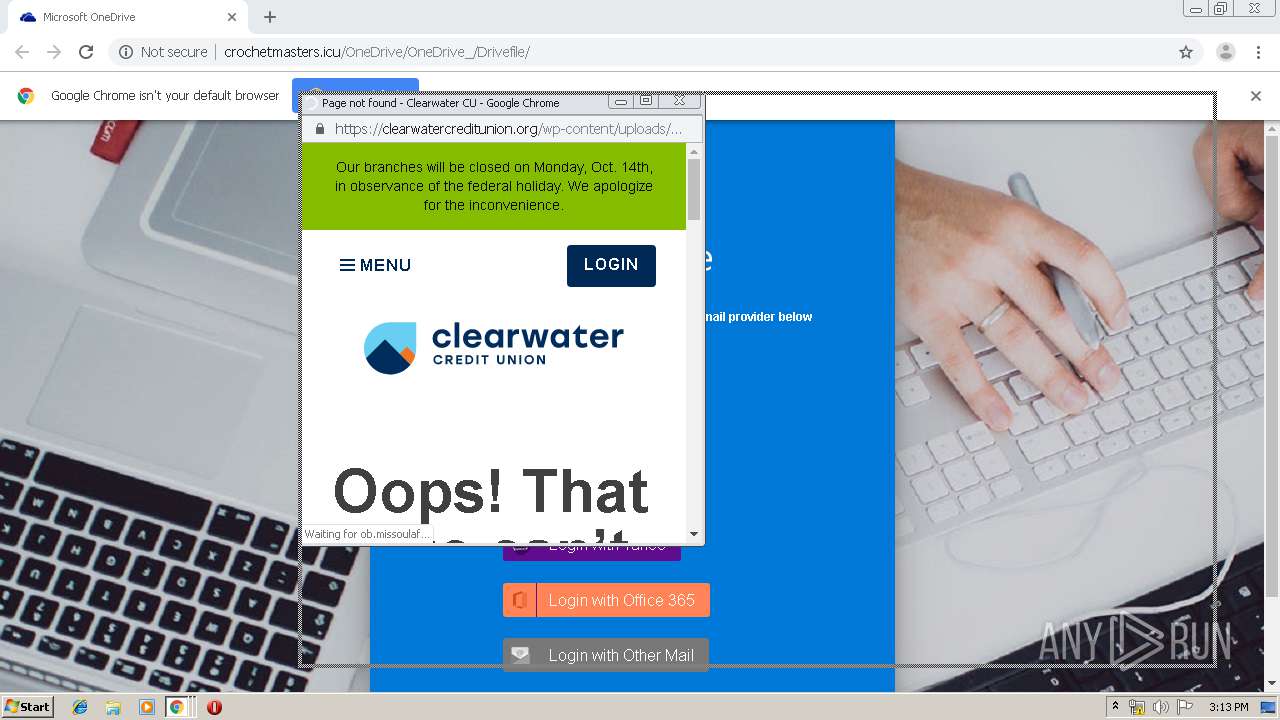
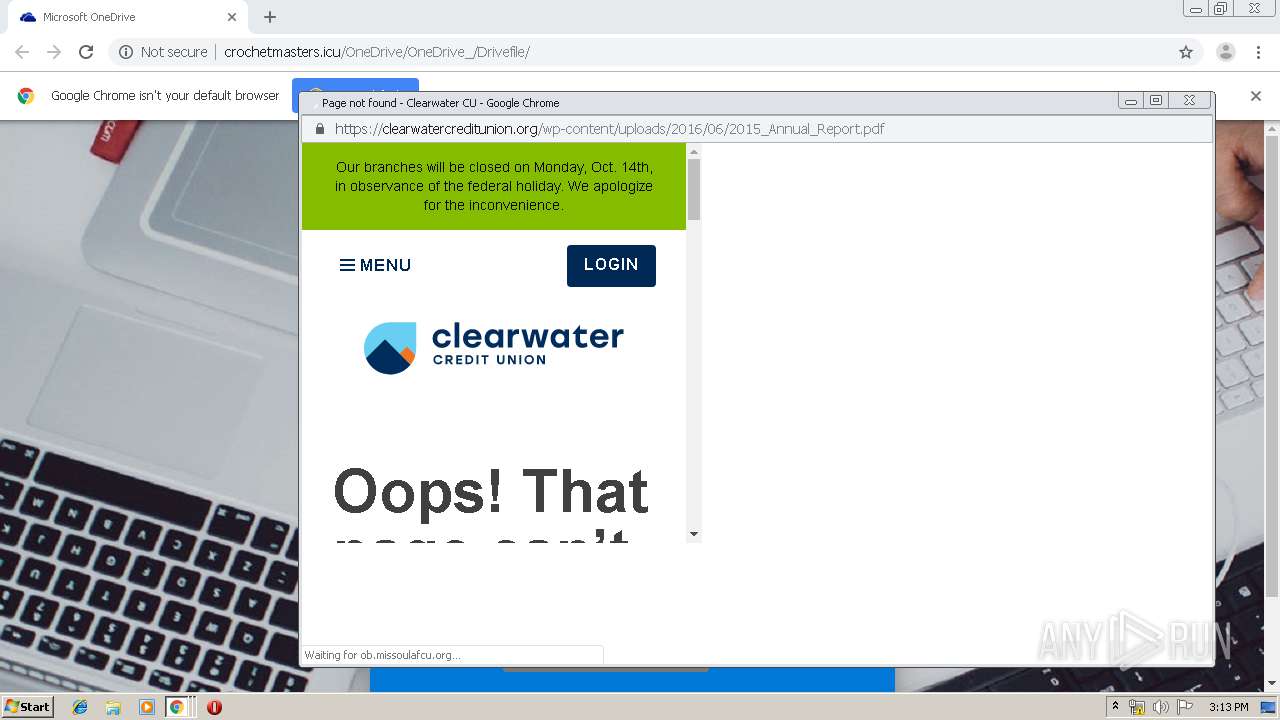
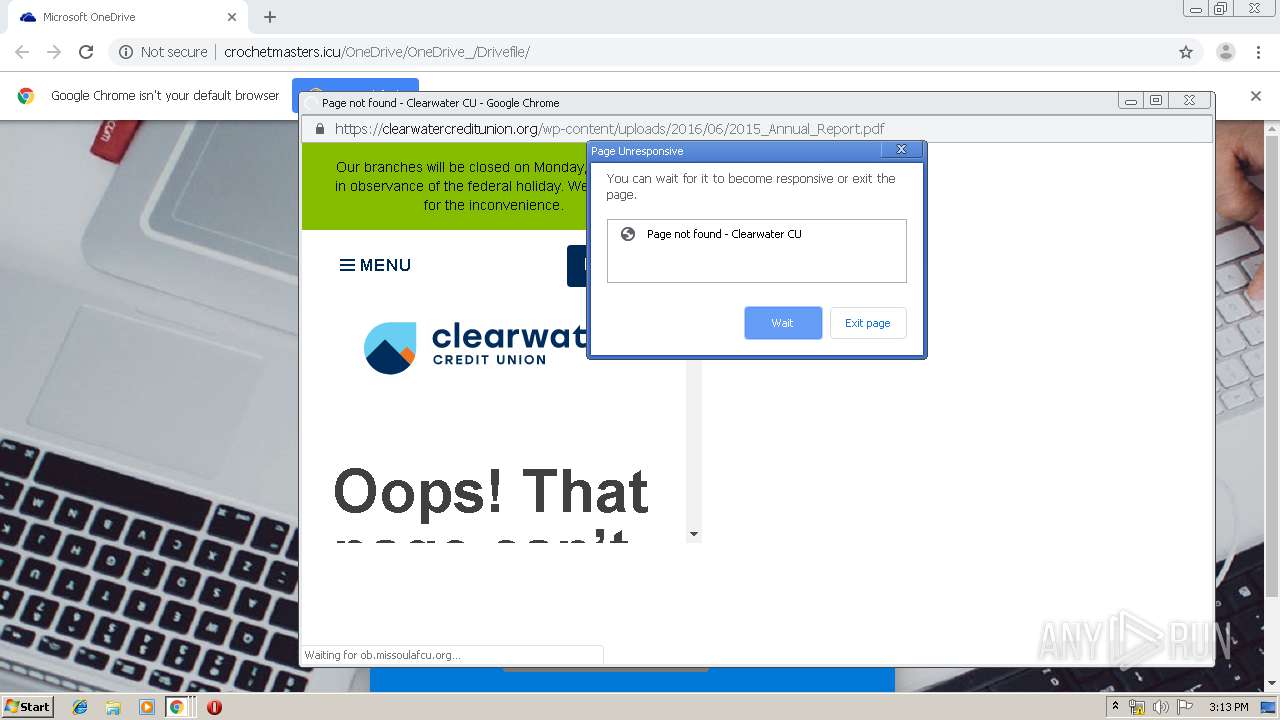
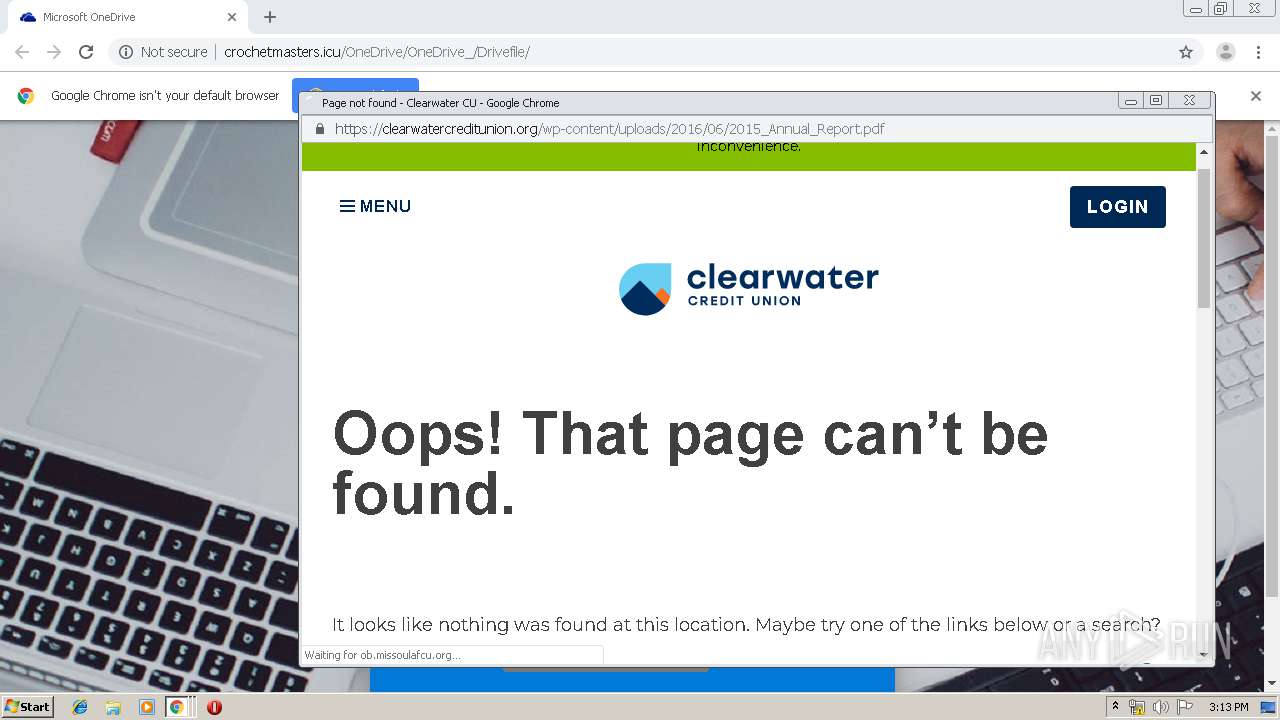
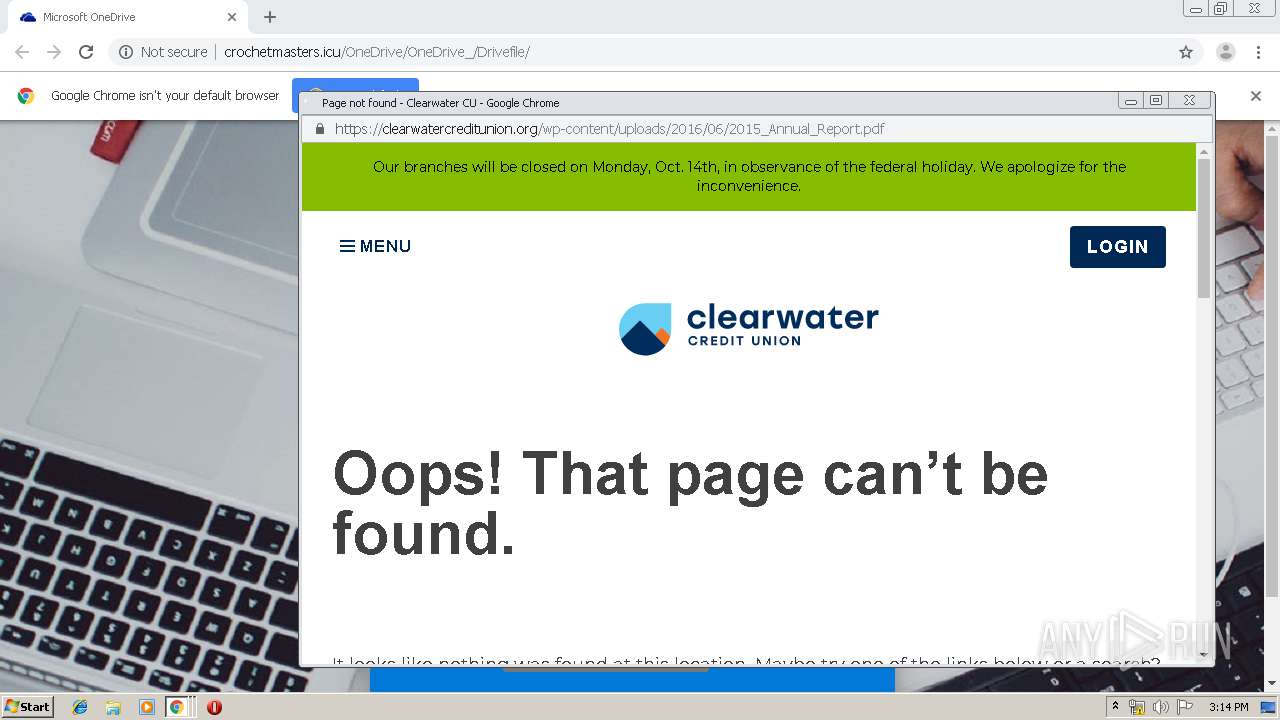
| URL: | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/ |
| Full analysis: | https://app.any.run/tasks/5eb1b8f3-440f-440c-899b-7a6d1e341607 |
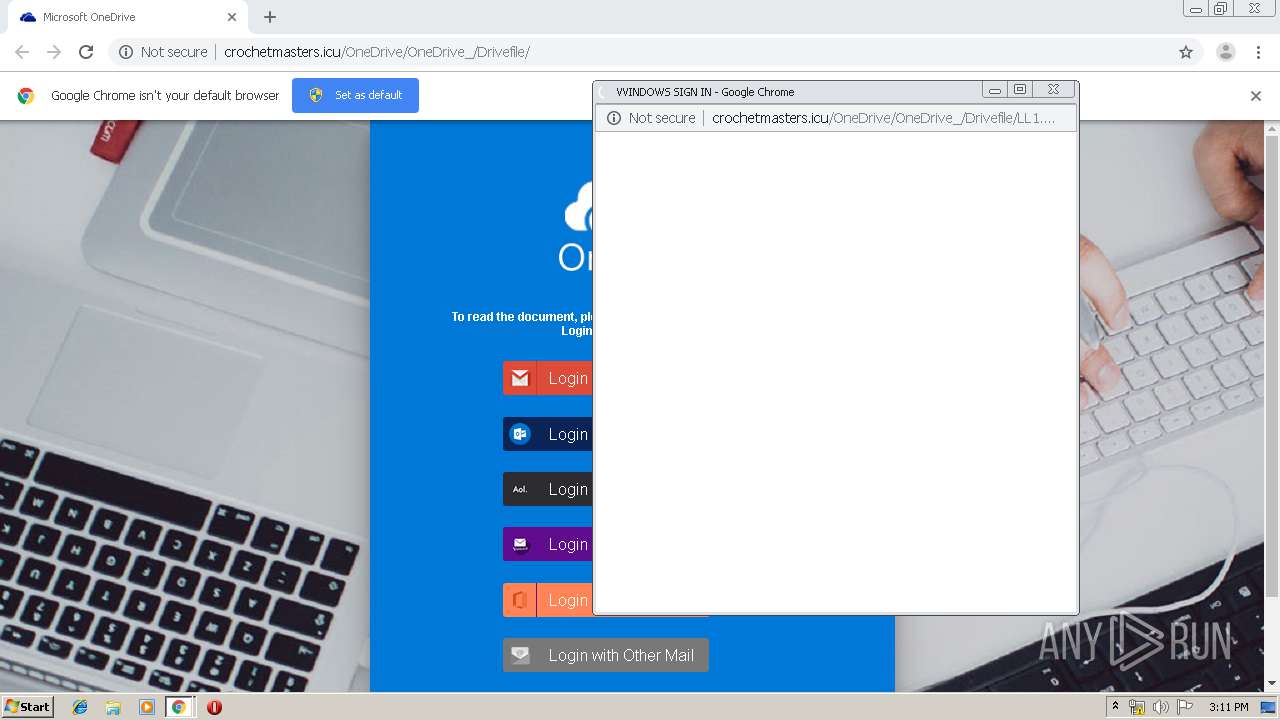
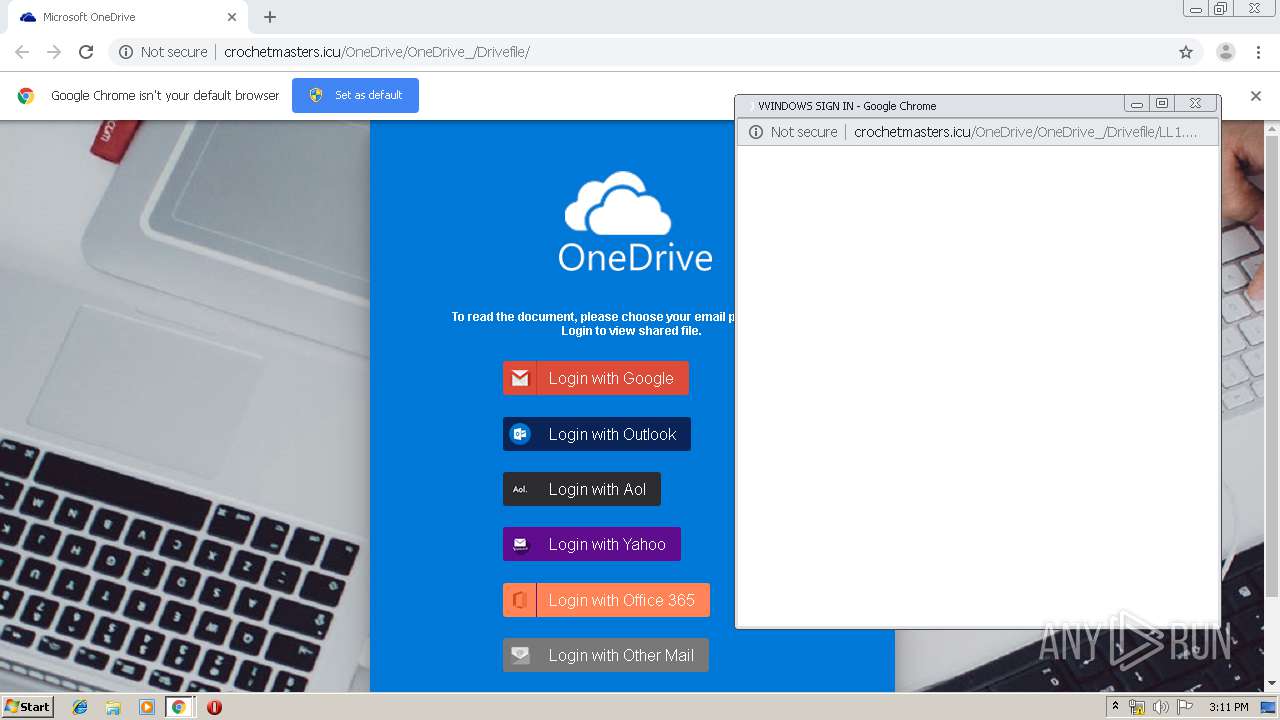
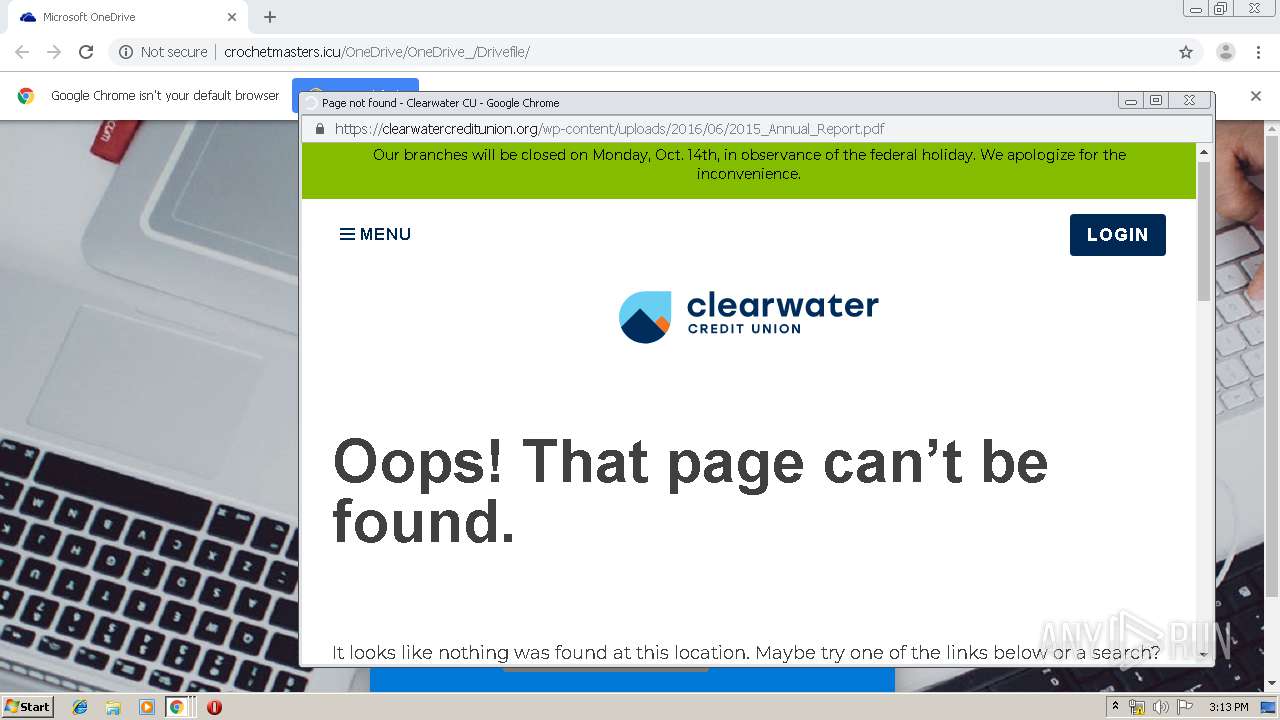
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 14:09:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 14D9812DAAED4038DA688A80AE643149 |
| SHA1: | 78A49E34AD378ECE4068C7119E991D7EDCE0DA1E |
| SHA256: | 5B41E369DDCAA784A1280B86886490D14F87A06FFE0703AA687CB2DDA4F9E67A |
| SSDEEP: | 3:N1KdXchkIABSTiUSAM:CYABSTiUg |
MALICIOUS
OneDrive phishing page detected
- chrome.exe (PID: 1880)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1296)
INFO
Reads the hosts file
- chrome.exe (PID: 1296)
- chrome.exe (PID: 1880)
Application launched itself
- chrome.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11997997038972612495 --mojo-platform-channel-handle=3660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3276863922609622775 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2658349455112509639 --mojo-platform-channel-handle=2080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9951746506352827377 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8960981289490562561 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16577827282143944218 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14942888719428217691 --mojo-platform-channel-handle=2908 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18092098360242592269 --mojo-platform-channel-handle=1952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2428 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
700
Read events
598
Write events
97
Delete events
5
Modification events
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1296-13215535787673875 |
Value: 259 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
46
Text files
272
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2fe3fe34-35e3-429c-ac2c-539bff1ee472.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a60e.TMP | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a5d0.TMP | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a5ef.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
52
DNS requests
27
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
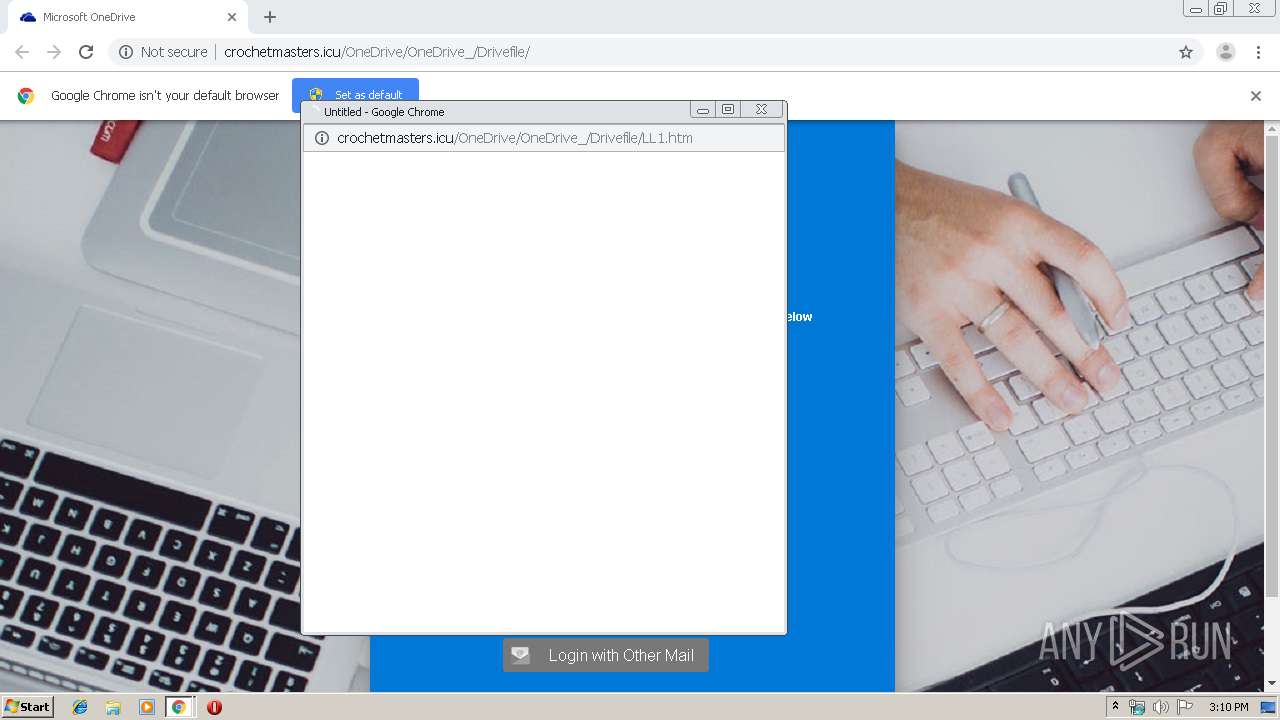
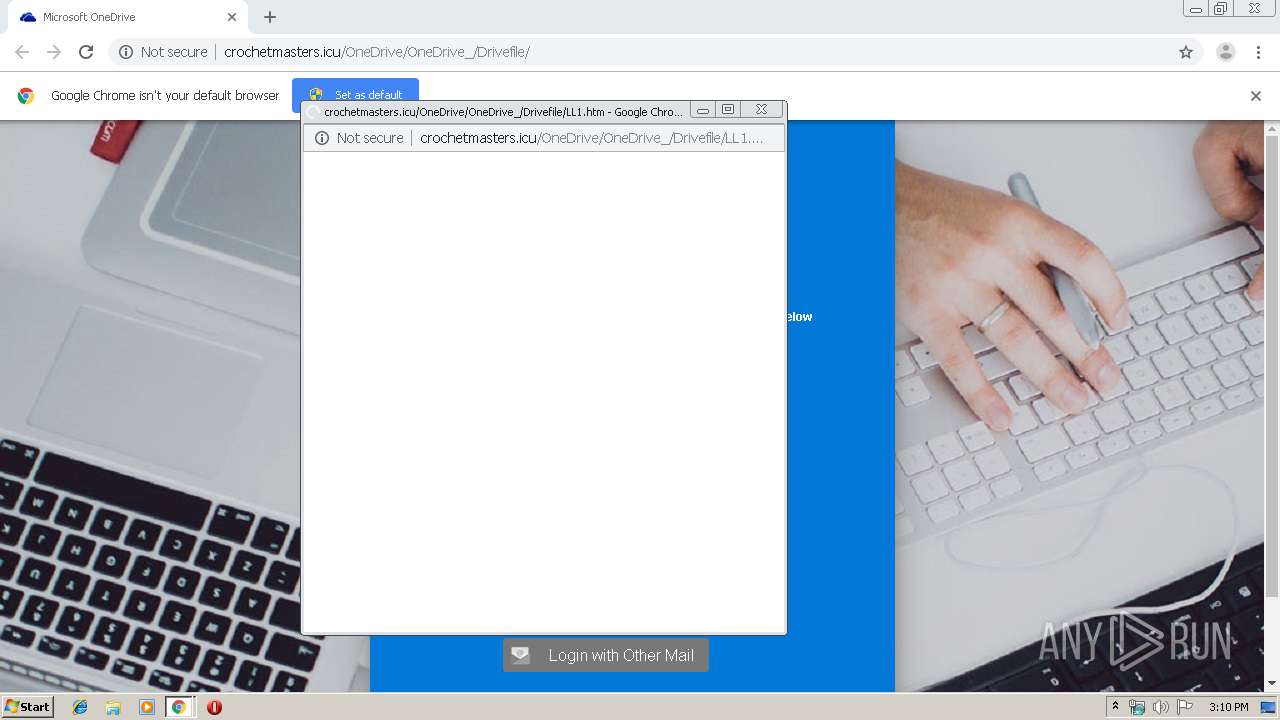
1880 | chrome.exe | GET | — | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/LL1.htm | RU | — | — | suspicious |
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/ | RU | html | 2.92 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/css/style.css | RU | text | 6.74 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/images/landing-devices-bg.jpg | RU | image | 230 Kb | suspicious |
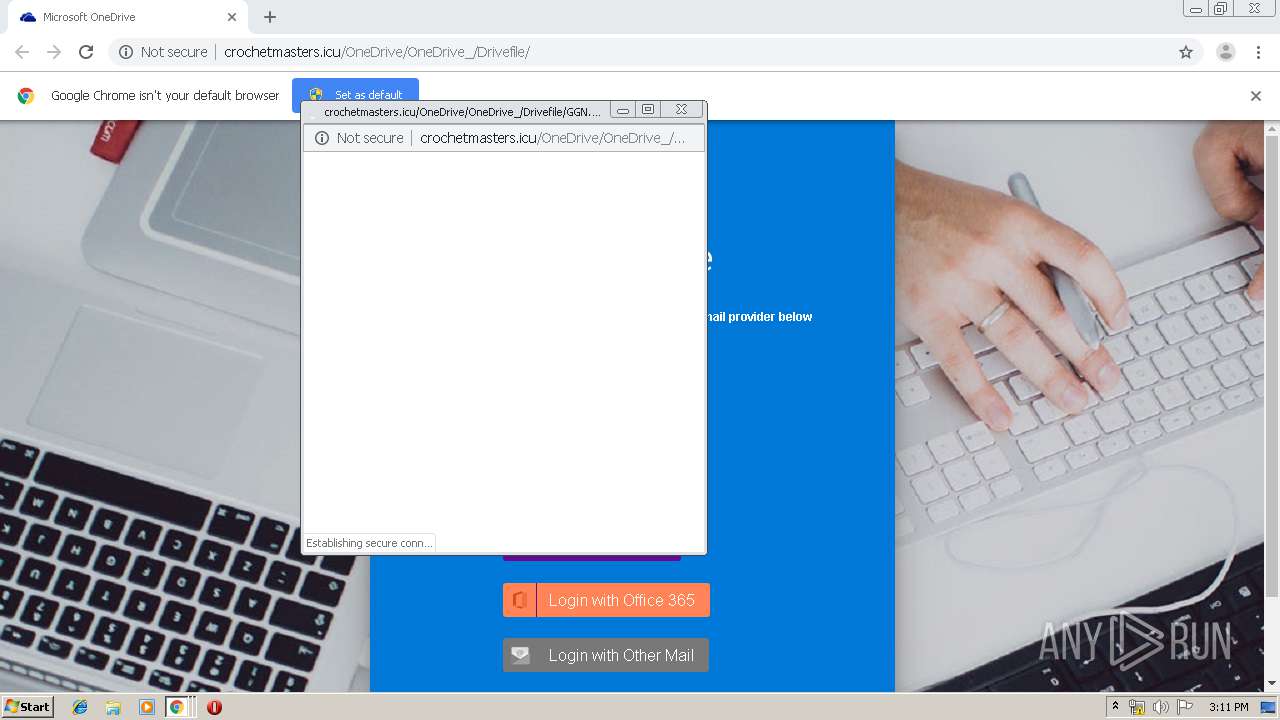
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/GGN.html | RU | html | 1.63 Kb | suspicious |
1880 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
1880 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/images/yahooMail.png | RU | image | 1.95 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/images/oneDrive.png | RU | image | 14.6 Kb | suspicious |
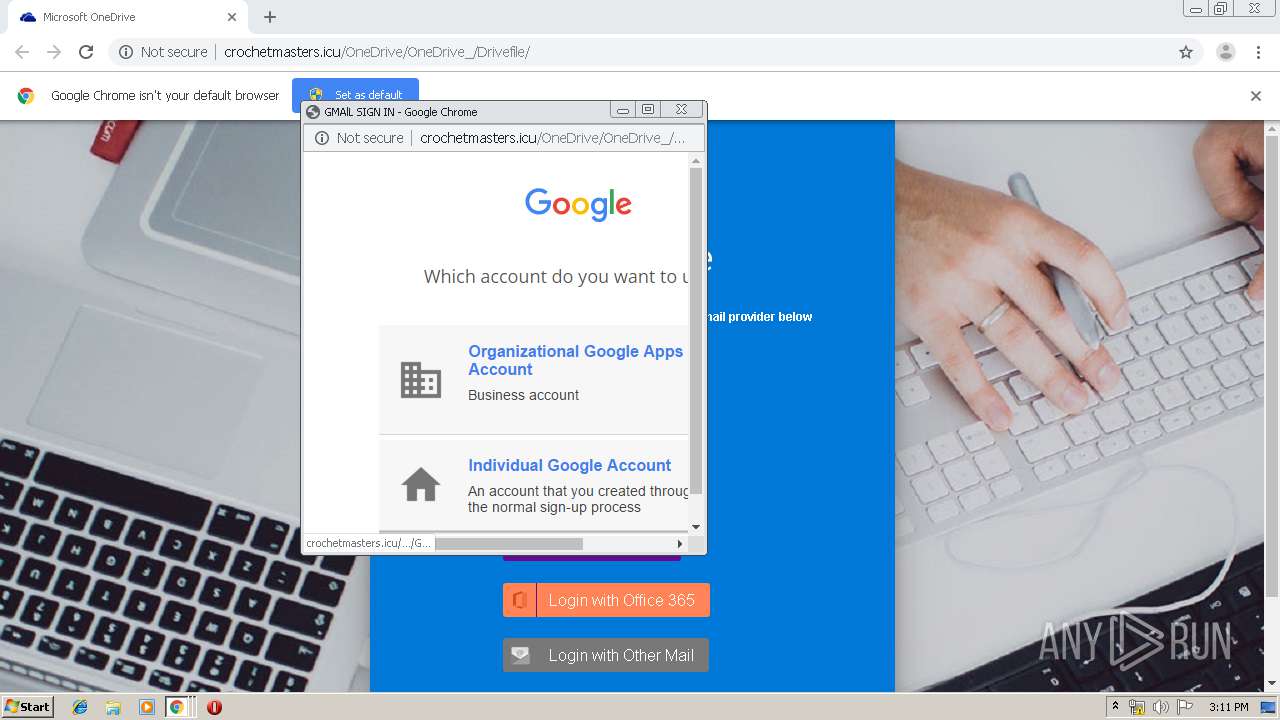
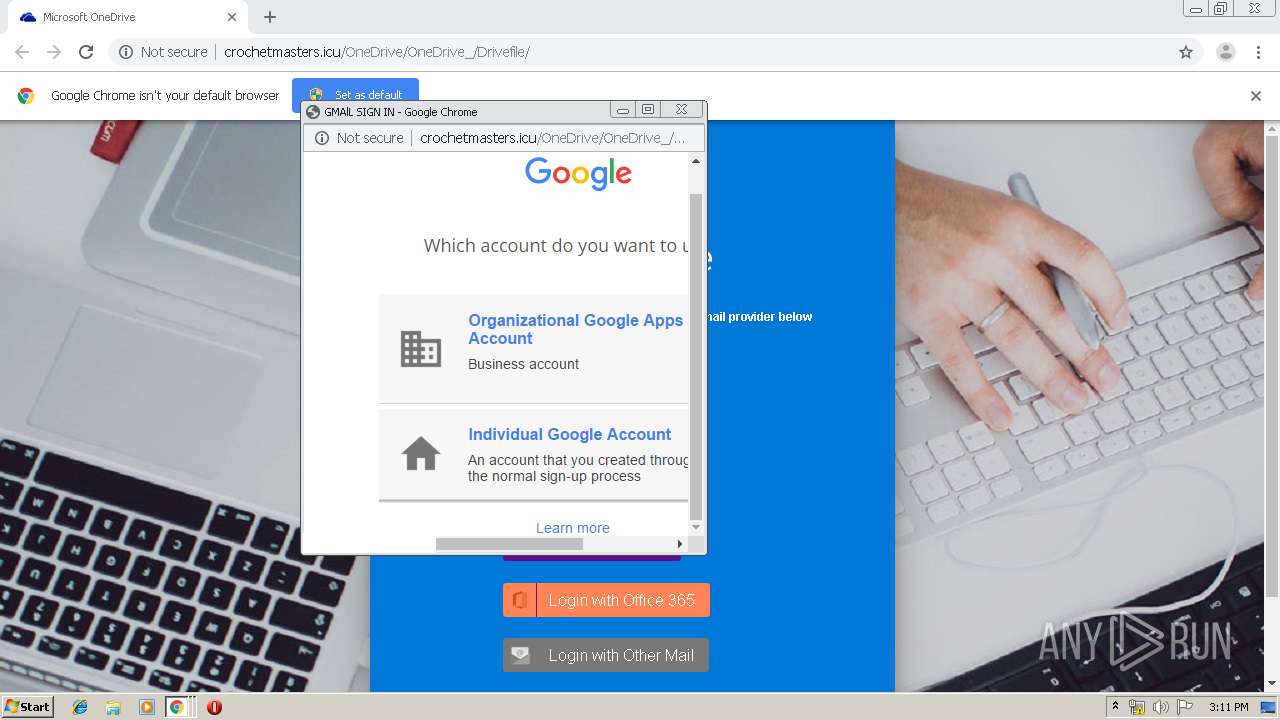
1880 | chrome.exe | GET | 200 | 178.159.36.146:80 | http://crochetmasters.icu/OneDrive/OneDrive_/Drivefile/g_files/which%202.png | RU | image | 5.64 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1880 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 178.159.36.146:80 | crochetmasters.icu | MAROSNET Telecommunication Company LLC | RU | suspicious |
1880 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 104.156.59.104:80 | www.icons101.com | HIVELOCITY VENTURES CORP | US | unknown |
1880 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 54.148.84.95:443 | www.sitepoint.com | Amazon.com, Inc. | US | unknown |
1880 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 104.25.96.109:443 | missoulafcu.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crochetmasters.icu |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.icons101.com |
| unknown |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.sitepoint.com |
| shared |
www.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
1880 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Popupwnd Phishing Landing 2018-01-25 |
1880 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Phishing Landing 2018-08-30 |
1880 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish to .icu Domain 2019-02-06 |
1880 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
1880 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish to .icu Domain 2019-02-06 |
1880 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
7 ETPRO signatures available at the full report