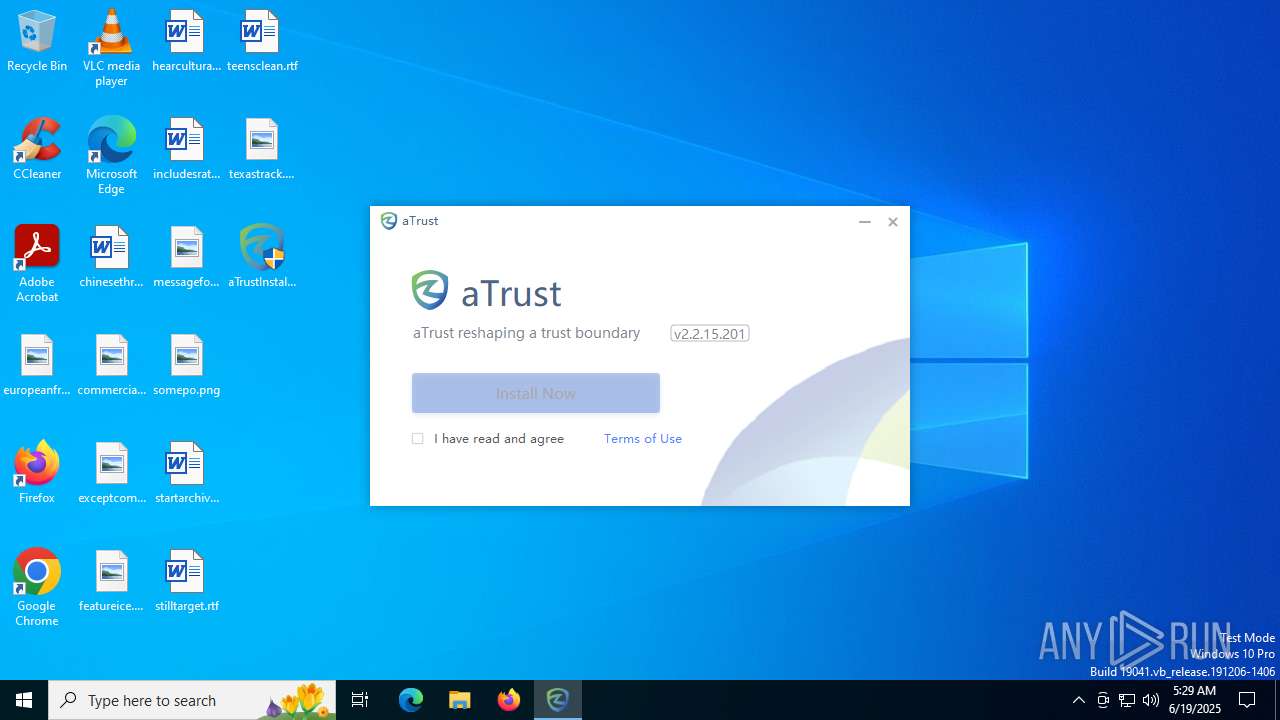
| File name: | aTrustInstaller.exe |
| Full analysis: | https://app.any.run/tasks/5d9119be-4a00-4417-a1cc-b013af85861f |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 05:29:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | B3B29C19D2260C42EB3BC78413A078EA |
| SHA1: | 6E946550A28CB5142210A13239EFEB343EB6857E |
| SHA256: | 5B403B24BC4D0E6A106A9CDDA114E4E219104DF0A491420A6A8C6078E0A103A6 |
| SSDEEP: | 786432:MJg7C/Wekh18V0LBuGvkqhQ+3kbQEMscfZV/ZFjJjWBSW:MJg7C/WeksVMNvkqhQ+3jCcff/jcBSW |
MALICIOUS
Executing a file with an untrusted certificate
- rootcert.exe (PID: 2188)
Changes the autorun value in the registry
- rootcert.exe (PID: 2188)
- aTrustTrayInstaller.exe (PID: 6408)
Changes the Windows auto-update feature
- aTrustAgent.exe (PID: 5772)
SUSPICIOUS
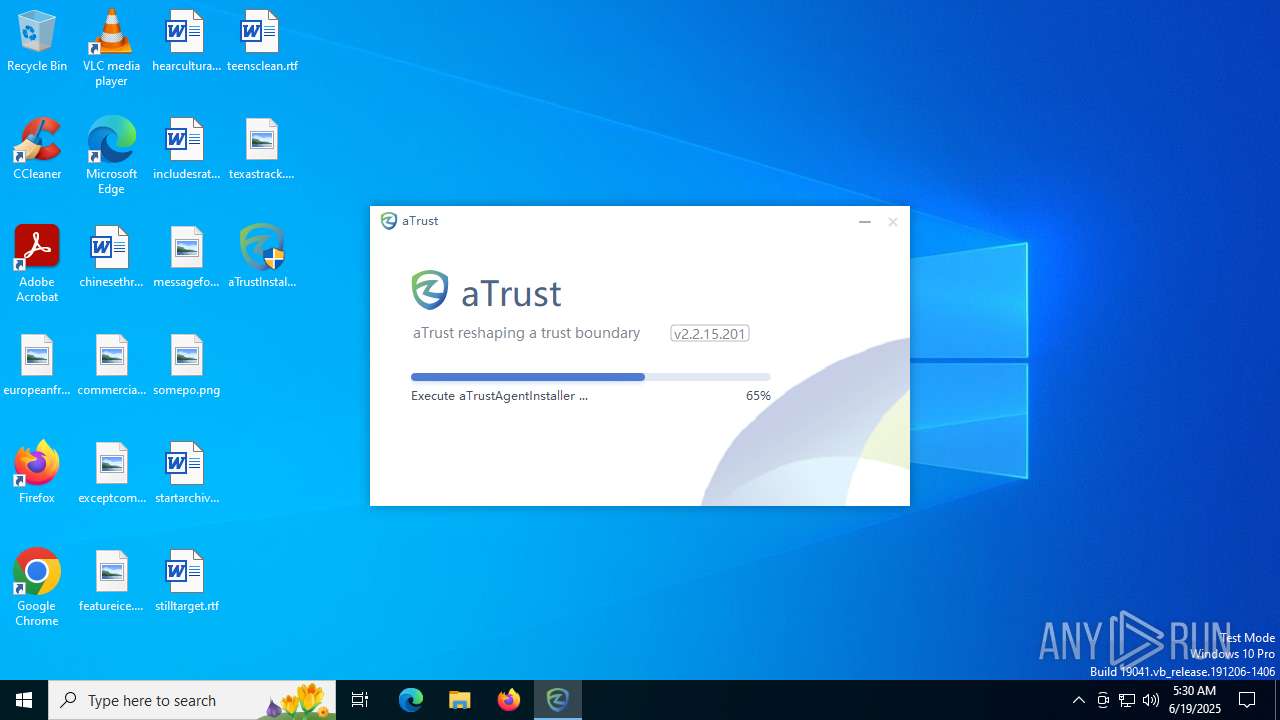
Malware-specific behavior (creating "System.dll" in Temp)
- aTrustInstaller.exe (PID: 4804)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustInstaller.exe (PID: 6264)
- aTrustTrayInstaller.exe (PID: 6408)
Executable content was dropped or overwritten
- aTrustInstaller.exe (PID: 4804)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- rootcert.exe (PID: 2188)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- drvinst.exe (PID: 1760)
- vacon.exe (PID: 4664)
- aTrustInstaller.exe (PID: 6264)
- drvinst.exe (PID: 1964)
- aTrustAgentInstaller.exe (PID: 5692)
- aTrustTrayInstaller.exe (PID: 6408)
The process creates files with name similar to system file names
- aTrustInstaller.exe (PID: 4804)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustInstaller.exe (PID: 6264)
- aTrustTrayInstaller.exe (PID: 6408)
Process drops legitimate windows executable
- aTrustInstaller.exe (PID: 6264)
- aTrustDefenserInstaller.exe (PID: 1096)
- rootcert.exe (PID: 2188)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- aTrustTrayInstaller.exe (PID: 6408)
The process drops C-runtime libraries
- aTrustInstaller.exe (PID: 6264)
- aTrustTrayInstaller.exe (PID: 6408)
Drops 7-zip archiver for unpacking
- aTrustInstaller.exe (PID: 6264)
There is functionality for taking screenshot (YARA)
- aTrustInstaller.exe (PID: 4804)
- aTrustInstaller.exe (PID: 6264)
Drops a system driver (possible attempt to evade defenses)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- vacon.exe (PID: 4664)
- drvinst.exe (PID: 1760)
- drvinst.exe (PID: 1964)
Adds/modifies Windows certificates
- updroots.exe (PID: 4156)
- updroots.exe (PID: 6828)
- updroots.exe (PID: 888)
- vacon.exe (PID: 4664)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 1688)
Starts a Microsoft application from unusual location
- updroots.exe (PID: 4156)
- updroots.exe (PID: 6828)
- updroots.exe (PID: 7092)
- updroots.exe (PID: 888)
Creates files in the driver directory
- drvinst.exe (PID: 1760)
- drvinst.exe (PID: 1964)
Reads security settings of Internet Explorer
- vacon.exe (PID: 4664)
- aTrustAgent.exe (PID: 6472)
- aTrustTrayInstaller.exe (PID: 6408)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 2324)
- aTrustInstaller.exe (PID: 4804)
Application launched itself
- aTrustInstaller.exe (PID: 4804)
- aTrustAgent.exe (PID: 5952)
- aTrustTray.exe (PID: 6172)
Creates or modifies Windows services
- drvinst.exe (PID: 1964)
Windows service management via SC.EXE
- sc.exe (PID: 1604)
- sc.exe (PID: 1204)
- sc.exe (PID: 5416)
Restarts service on failure
- sc.exe (PID: 6652)
Executes as Windows Service
- aTrustAgent.exe (PID: 5952)
Modifies hosts file to alter network resolution
- aTrustAgent.exe (PID: 1688)
Reads the date of Windows installation
- aTrustAgent.exe (PID: 1688)
- aTrustAgent.exe (PID: 5772)
Searches for installed software
- aTrustAgent.exe (PID: 1688)
Creates a software uninstall entry
- aTrustInstaller.exe (PID: 4804)
INFO
Creates files or folders in the user directory
- aTrustInstaller.exe (PID: 6892)
- aTrustInstaller.exe (PID: 4804)
- vacon.exe (PID: 4664)
- ConfigUpgrade.exe (PID: 4060)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5772)
- aTrustAgent.exe (PID: 1688)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 4308)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 1560)
The sample compiled with chinese language support
- aTrustInstaller.exe (PID: 6892)
- aTrustInstaller.exe (PID: 4804)
- aTrustInstaller.exe (PID: 6264)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustDnsDriverInstaller.exe (PID: 3720)
Reads the computer name
- aTrustInstaller.exe (PID: 6264)
- aTrustDefenserInstaller.exe (PID: 1096)
- Install.exe (PID: 6852)
- ndiscleanup.x64.exe (PID: 6224)
- vacon.exe (PID: 4664)
- aTrustInstaller.exe (PID: 4804)
- drvinst.exe (PID: 1760)
- drvinst.exe (PID: 1964)
- aTrustAgent.exe (PID: 5952)
- aTrustAgentInstaller.exe (PID: 5692)
- aTrustAgent.exe (PID: 1688)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5772)
- aTrustTrayInstaller.exe (PID: 6408)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 3780)
- aTrustTray.exe (PID: 1560)
- aTrustTray.exe (PID: 1388)
Create files in a temporary directory
- aTrustInstaller.exe (PID: 6264)
- aTrustInstaller.exe (PID: 4804)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- rootcert.exe (PID: 2188)
- vacon.exe (PID: 4664)
- aTrustAgentInstaller.exe (PID: 5692)
- aTrustTrayInstaller.exe (PID: 6408)
- aTrustTray.exe (PID: 6172)
Creates files in the program directory
- aTrustInstaller.exe (PID: 6264)
- aTrustInstaller.exe (PID: 4804)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustDefenserInstaller.exe (PID: 1096)
- Remove.exe (PID: 3624)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- aTrustAgentInstaller.exe (PID: 5692)
- ConfigUpgrade.exe (PID: 4060)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5952)
- aTrustAgent.exe (PID: 1688)
- aTrustTrayInstaller.exe (PID: 6408)
- aTrustAgent.exe (PID: 5772)
Checks supported languages
- aTrustInstaller.exe (PID: 6892)
- aTrustInstaller.exe (PID: 4804)
- aTrustInstaller.exe (PID: 6264)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- Remove.exe (PID: 3624)
- rootcert.exe (PID: 2188)
- Install.exe (PID: 6852)
- updroots.exe (PID: 4156)
- ndiscleanup.x64.exe (PID: 6224)
- updroots.exe (PID: 6828)
- vacon.exe (PID: 4664)
- updroots.exe (PID: 888)
- updroots.exe (PID: 7092)
- drvinst.exe (PID: 1760)
- drvinst.exe (PID: 1964)
- aTrustAgentInstaller.exe (PID: 5692)
- ConfigUpgrade.exe (PID: 4060)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5952)
- aTrustAgent.exe (PID: 5772)
- aTrustAgent.exe (PID: 1688)
- aTrustTrayInstaller.exe (PID: 6408)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 3780)
- aTrustTray.exe (PID: 1560)
- aTrustTray.exe (PID: 2044)
- aTrustTray.exe (PID: 4308)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 7192)
- aTrustTray.exe (PID: 7472)
- aTrustTray.exe (PID: 1388)
The sample compiled with english language support
- aTrustInstaller.exe (PID: 6264)
- aTrustDefenserInstaller.exe (PID: 1096)
- aTrustVNICInstaller_X86_X64.exe (PID: 1496)
- aTrustDnsDriverInstaller.exe (PID: 3720)
- rootcert.exe (PID: 2188)
- aTrustVNICInstaller_X64.exe (PID: 5252)
- vacon.exe (PID: 4664)
- drvinst.exe (PID: 1760)
- drvinst.exe (PID: 1964)
- aTrustTrayInstaller.exe (PID: 6408)
Launching a file from a Registry key
- rootcert.exe (PID: 2188)
- aTrustTrayInstaller.exe (PID: 6408)
Reads the software policy settings
- vacon.exe (PID: 4664)
- drvinst.exe (PID: 1760)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5952)
- aTrustAgent.exe (PID: 5772)
- aTrustAgent.exe (PID: 1688)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 1560)
- slui.exe (PID: 3756)
Reads the machine GUID from the registry
- vacon.exe (PID: 4664)
- drvinst.exe (PID: 1760)
- aTrustAgent.exe (PID: 6472)
- aTrustAgent.exe (PID: 5952)
- aTrustAgent.exe (PID: 1688)
- aTrustAgent.exe (PID: 5772)
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 1560)
Reads Windows Product ID
- aTrustAgent.exe (PID: 1688)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6772)
Manual execution by a user
- aTrustTray.exe (PID: 2324)
Process checks computer location settings
- aTrustTray.exe (PID: 6172)
- aTrustTray.exe (PID: 2324)
- aTrustTray.exe (PID: 2044)
- aTrustTray.exe (PID: 7472)
- aTrustTray.exe (PID: 7192)
Checks proxy server information
- aTrustTray.exe (PID: 6172)
- slui.exe (PID: 3756)
ELECTRON JS mutex has been found
- aTrustTray.exe (PID: 6172)
Node.js compiler has been detected
- aTrustTray.exe (PID: 6172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:04:27 08:53:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 241664 |
| InitializedDataSize: | 97483264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20cf |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.15.201 |
| ProductVersionNumber: | 2.2.15.201 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | Sangfor Technologies Inc. |
| FileDescription: | aTrustInstaller |
| FileVersion: | 2.2.15.201 |
| InternalName: | aTrustInstaller |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | aTrustInstaller.exe |
| ProductName: | aTrust |
| ProductVersion: | 2.2.15.201 |
Total processes
185
Monitored processes
55
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe -l roots.sst | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe | — | rootcert.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UPDROOTS Exit code: 0 Version: 5.1.2484.0 (main.010529-2005) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CheckNetIsolation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Sangfor\aTrust\aTrustDefenserInstaller.exe" | C:\Program Files (x86)\Sangfor\aTrust\aTrustDefenserInstaller.exe | aTrustInstaller.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: HIGH Description: Defenser Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1204 | sc start aTrustService | C:\Windows\SysWOW64\sc.exe | — | aTrustAgentInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | C:\Windows\System32\CompPkgSrv.exe -Embedding | C:\Windows\System32\CompPkgSrv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Component Package Support Server Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Sangfor\aTrust\aTrustTray\aTrustTray.exe" --type=gpu-process --field-trial-handle=2384,6645808423348772074,5313726620999555860,131072 --disable-features=SpareRendererForSitePerProcess --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADoAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --service-request-channel-token=258398722138784713 --mojo-platform-channel-handle=3920 /prefetch:2 | C:\Program Files (x86)\Sangfor\aTrust\aTrustTray\aTrustTray.exe | — | aTrustTray.exe | |||||||||||
User: admin Company: Sangfor Integrity Level: MEDIUM Description: aTrustTray Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Sangfor\aTrust\aTrustVNICInstaller_X86_X64.exe" | C:\Program Files (x86)\Sangfor\aTrust\aTrustVNICInstaller_X86_X64.exe | aTrustInstaller.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: HIGH Description: VNIC Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1560 | "C:\Program Files (x86)\Sangfor\aTrust\aTrustTray\aTrustTray.exe" --type=utility --field-trial-handle=2384,6645808423348772074,5313726620999555860,131072 --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --ignore-certificate-errors --proxy-server=127.0.0.1:54321 --ignore-certificate-errors --service-request-channel-token=8595037437660730645 --mojo-platform-channel-handle=2840 /prefetch:8 | C:\Program Files (x86)\Sangfor\aTrust\aTrustTray\aTrustTray.exe | — | aTrustTray.exe | |||||||||||
User: admin Company: Sangfor Integrity Level: MEDIUM Description: aTrustTray Version: 1.0.1.0 Modules
| |||||||||||||||
| 1604 | sc query aTrustService | C:\Windows\SysWOW64\sc.exe | — | aTrustAgentInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
100 666
Read events
97 103
Write events
1 694
Delete events
1 869
Modification events
| (PID) Process: | (4804) aTrustInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip6\Parameters |
| Operation: | write | Name: | DisabledComponents |
Value: 32 | |||
| (PID) Process: | (5252) aTrustVNICInstaller_X64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NewNetworkWindowOff |
| Operation: | write | Name: | showNetworkLocation |
Value: 0 | |||
| (PID) Process: | (1096) aTrustDefenserInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\Defenser |
| Operation: | write | Name: | UnInstall |
Value: C:\Program Files (x86)\Sangfor\aTrust\uninstall.exe | |||
| (PID) Process: | (1096) aTrustDefenserInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\Defenser |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files (x86)\Sangfor\aTrust\aTrustDefenser\aTrustDefenser.dll | |||
| (PID) Process: | (1096) aTrustDefenserInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\Defenser |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.3 | |||
| (PID) Process: | (1096) aTrustDefenserInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\Defenser |
| Operation: | write | Name: | path |
Value: C:\Program Files (x86)\Sangfor\aTrust\aTrustDefenser | |||
| (PID) Process: | (1096) aTrustDefenserInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sangfor\aTrust\Defenser |
| Operation: | write | Name: | Path |
Value: C:\Program Files (x86)\Sangfor\aTrust\aTrustDefenser | |||
| (PID) Process: | (3720) aTrustDnsDriverInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\DnsDriver |
| Operation: | write | Name: | UnInstall |
Value: C:\Program Files (x86)\Sangfor\aTrust\DnsDriver\uninstall.exe | |||
| (PID) Process: | (3720) aTrustDnsDriverInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\DnsDriver |
| Operation: | write | Name: | Path |
Value: C:\Program Files (x86)\Sangfor\aTrust\DnsDriver\aTrustDnsDriver.sys | |||
| (PID) Process: | (3720) aTrustDnsDriverInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Sangfor\aTrust\DnsDriver |
| Operation: | write | Name: | Version |
Value: 1.0.0.4 | |||
Executable files
234
Suspicious files
179
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6892 | aTrustInstaller.exe | C:\Users\admin\AppData\Roaming\aTrustInstall_242315\aTrustInstaller.exe | — | |
MD5:— | SHA256:— | |||
| 6264 | aTrustInstaller.exe | C:\Program Files (x86)\Sangfor\aTrust\app.7z | — | |
MD5:— | SHA256:— | |||
| 4804 | aTrustInstaller.exe | C:\Program Files (x86)\Sangfor\aTrust\install.log | binary | |
MD5:0D6297A98269E206E3BC7254DFAB66C0 | SHA256:C5E7B30C044EBEDF4CD7402076406246E45AE1FC868FE5D1DD63002FFE55C965 | |||
| 6264 | aTrustInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsyCA17.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 6264 | aTrustInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsyCA17.tmp\nsProcess.dll | executable | |
MD5:88D3E48D1C1A051C702D47046ADE7B4C | SHA256:51DA07DA18A5486B11E0D51EBFF77A3F2FCBB4D66B5665D212CC6BDA480C4257 | |||
| 6264 | aTrustInstaller.exe | C:\Program Files (x86)\Sangfor\aTrust\aTrustAgent\script\low_vnic_priority.bat | text | |
MD5:359766A2FC3C60A692081BFCEF8E6D44 | SHA256:C1B778350212B9C0D4E27FF0B7C68E49C5944C4899FE766F6965B4FD12B24A03 | |||
| 6264 | aTrustInstaller.exe | C:\Program Files (x86)\Sangfor\aTrust\version | binary | |
MD5:92632638E8E8B25D15BD5BF0C0CE55B3 | SHA256:3B733C25603D6DD15BB5D4D83ECB8F82C045137FB8F9F4C1A21F64A3E1FA3481 | |||
| 4804 | aTrustInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsyBCC9.tmp\UserInfo.dll | executable | |
MD5:DC90F96B169DCC9151EE6E93B47446EA | SHA256:AFC939EBFD66A6C972D2D6BBCB978559AB3427D1582935E45392F9912EF186AD | |||
| 6264 | aTrustInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsyCA17.tmp\UserInfo.dll | executable | |
MD5:DC90F96B169DCC9151EE6E93B47446EA | SHA256:AFC939EBFD66A6C972D2D6BBCB978559AB3427D1582935E45392F9912EF186AD | |||
| 6264 | aTrustInstaller.exe | C:\Program Files (x86)\Sangfor\aTrust\aTrustTray\icudtl.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
24
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 138.113.20.168:443 | https://atrustcdn.sangfor.com/resource/client/static/certificate.json?platform=Windows&clientType=SDPClient | unknown | binary | 16.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
— | — | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
atrustcdn.sangfor.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
aTrustInstaller.exe | [aTrustInstallWrapper] [RegWritePca] RegOpenKeyEx Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Persisted failed:2 |
aTrustInstaller.exe | [aTrustInstallWrapper] [GetTempFilePath] szFilePath=C:\Users\admin\AppData\Roaming\aTrustInstall_242315\aTrustInstaller.exe |
aTrustInstaller.exe | [aTrustInstallWrapper] [ExecCommand] ExecCommand "C:\Users\admin\AppData\Roaming\aTrustInstall_242315\aTrustInstaller.exe" |
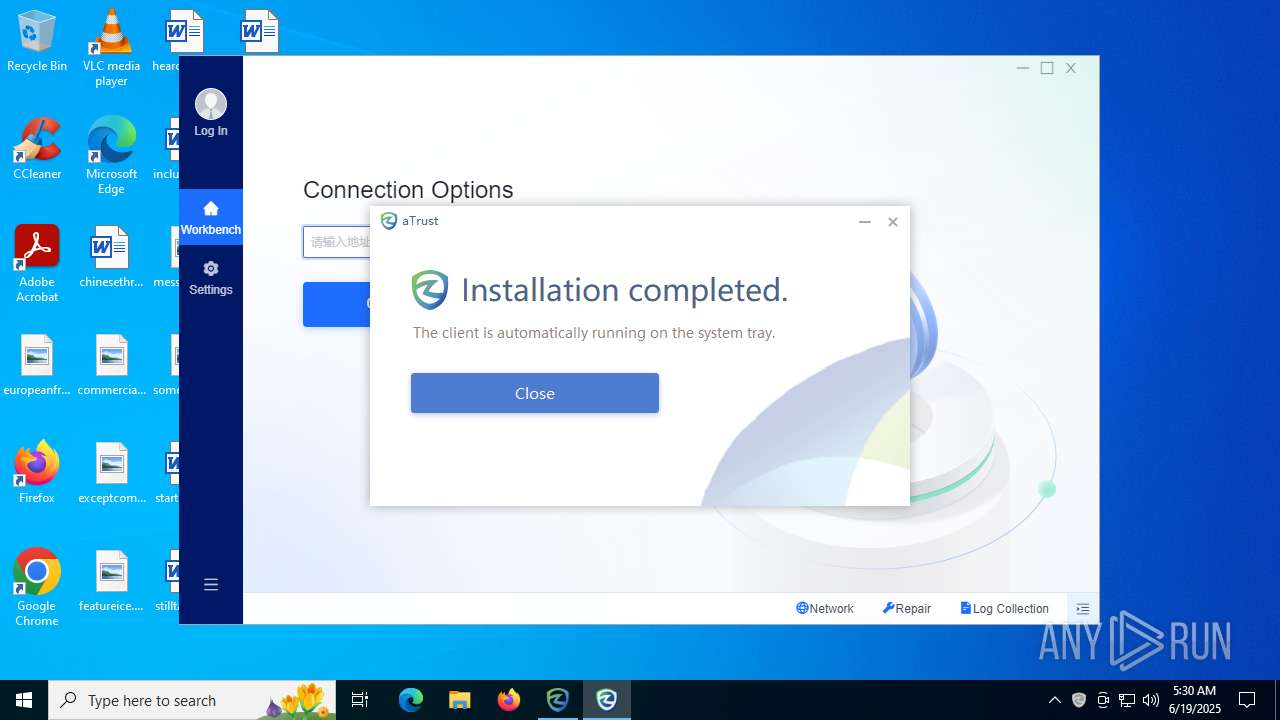
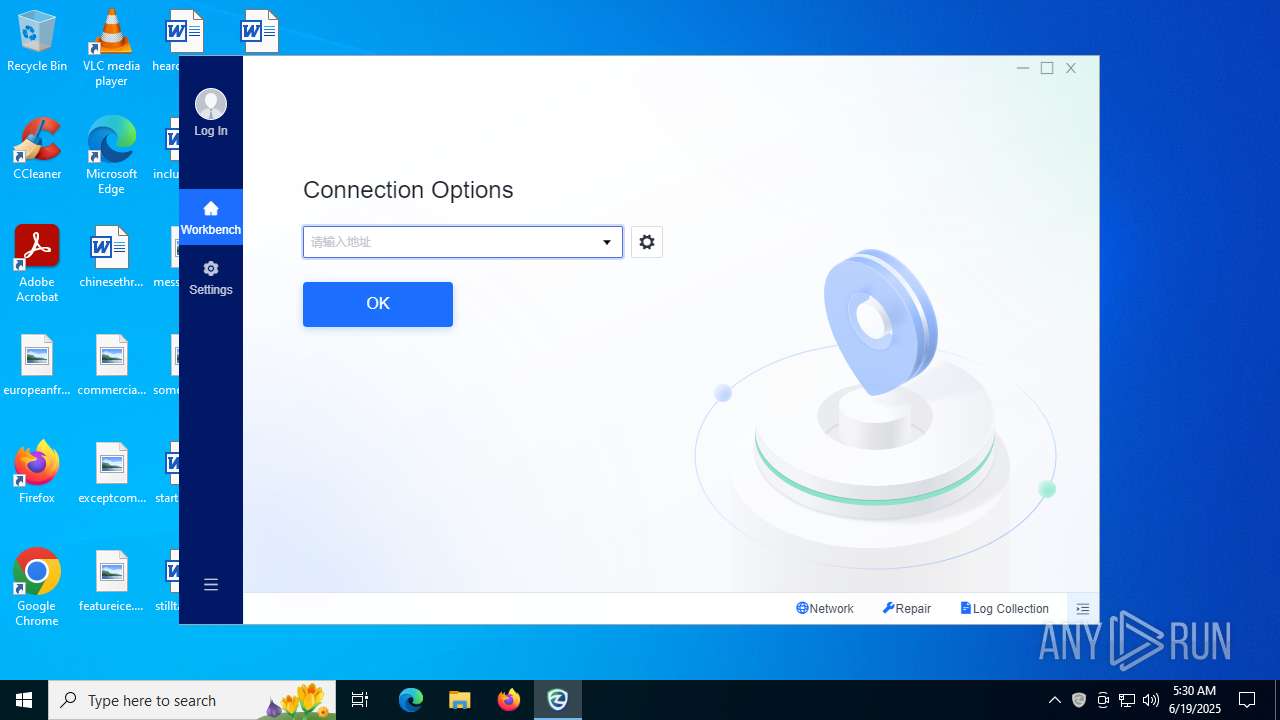
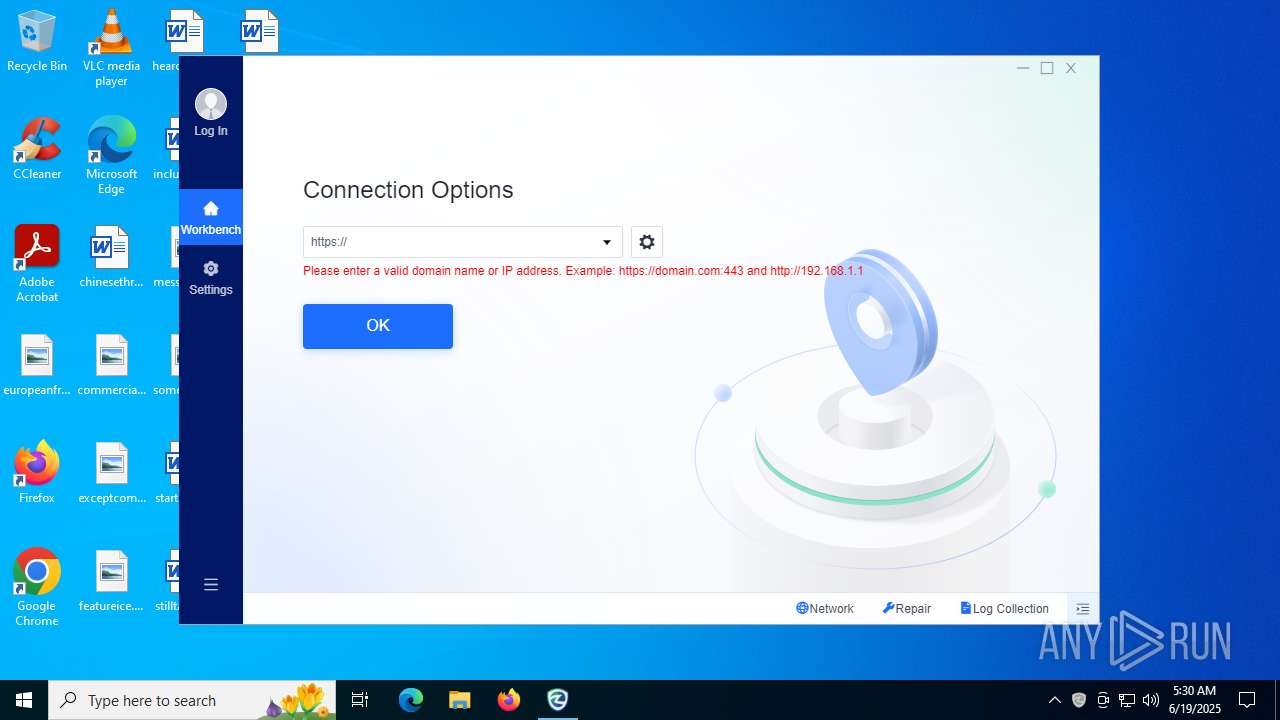
aTrustInstaller.exe | Window, size, 540,300
|
aTrustInstaller.exe | Window, caption, 0,0,0,300
|
aTrustInstaller.exe | Window, bktrans, false
|
aTrustInstaller.exe | Window, shadowcorner, 12,12,12,12
|
aTrustInstaller.exe | Window, shadowsize, 12
|
aTrustInstaller.exe | Window, showshadow, true
|
aTrustInstaller.exe | Window, sizebox, 0,0,0,0
|