| File name: | 5b3a41ed8a9a619b4aa18cef611c94b3273671ad464847cbfa600a6571c64431.msi |
| Full analysis: | https://app.any.run/tasks/72152193-6a3b-4cd0-afdb-8b8fc03cda7f |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2024, 05:23:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
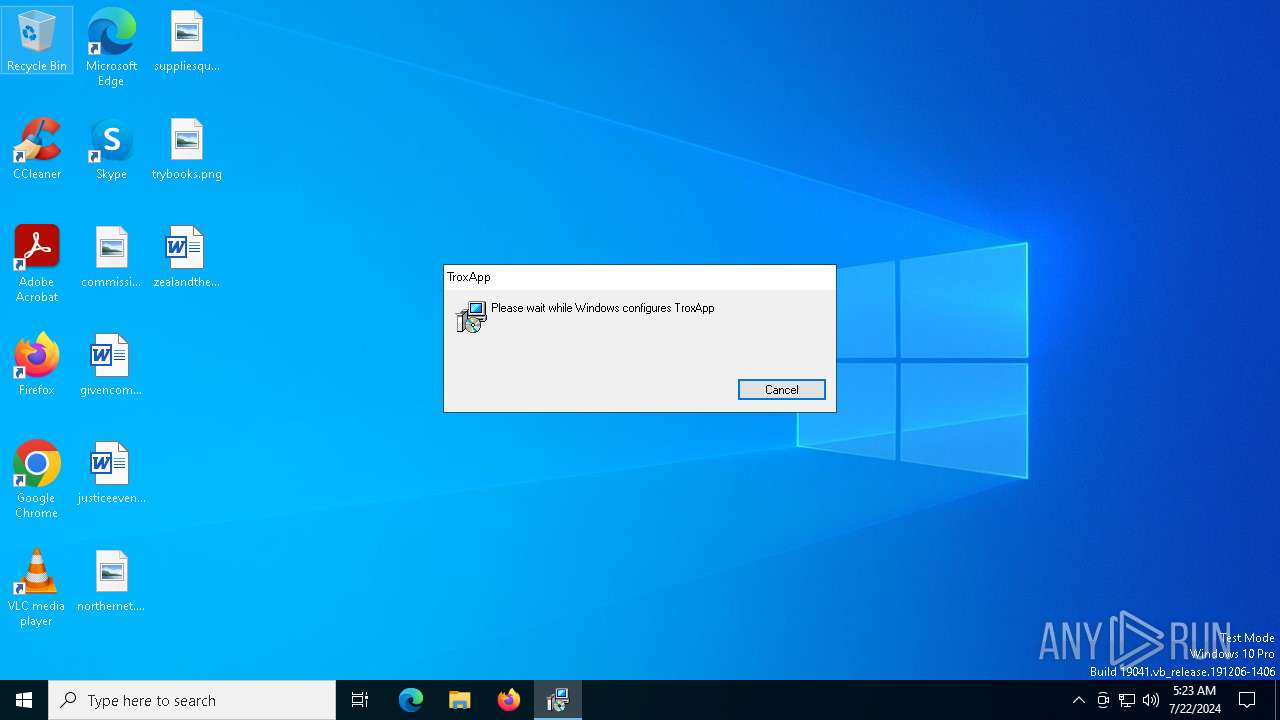
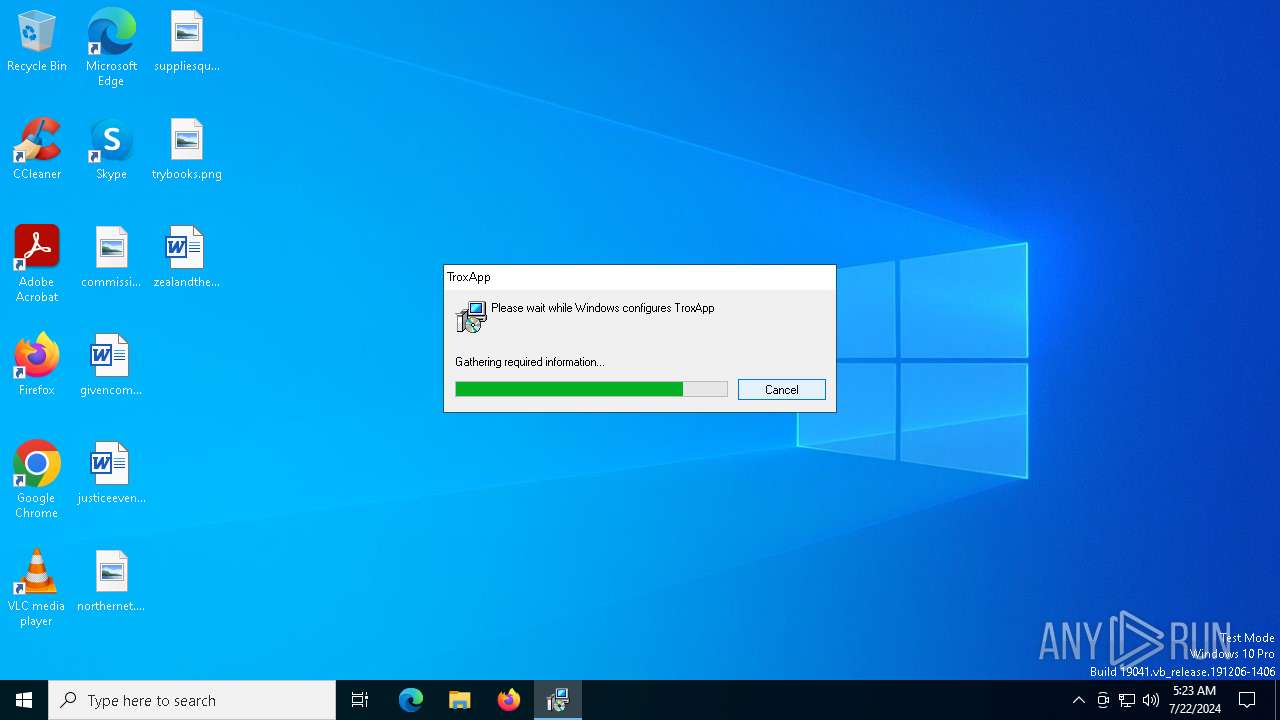
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {A3B69905-389C-4777-92FB-F2E072712230}, Number of Words: 10, Subject: TroxApp, Author: Troxbox Publish, Name of Creating Application: TroxApp, Template: x64;1033, Comments: This installer database contains the logic and data required to install TroxApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Mon Jul 8 17:55:21 2024, Last Saved Time/Date: Mon Jul 8 17:55:21 2024, Last Printed: Mon Jul 8 17:55:21 2024, Number of Pages: 450 |
| MD5: | 6E619D3D24F58BFB7BD7E76A4756E258 |
| SHA1: | 890359E1E86525C4C14E975E762239878134B32D |
| SHA256: | 5B3A41ED8A9A619B4AA18CEF611C94B3273671AD464847CBFA600A6571C64431 |
| SSDEEP: | 393216:U88/NM3eBSTDiwDnsVznaoDtACBF2iILPmq:k6tu+nKnrDqCqtLP |
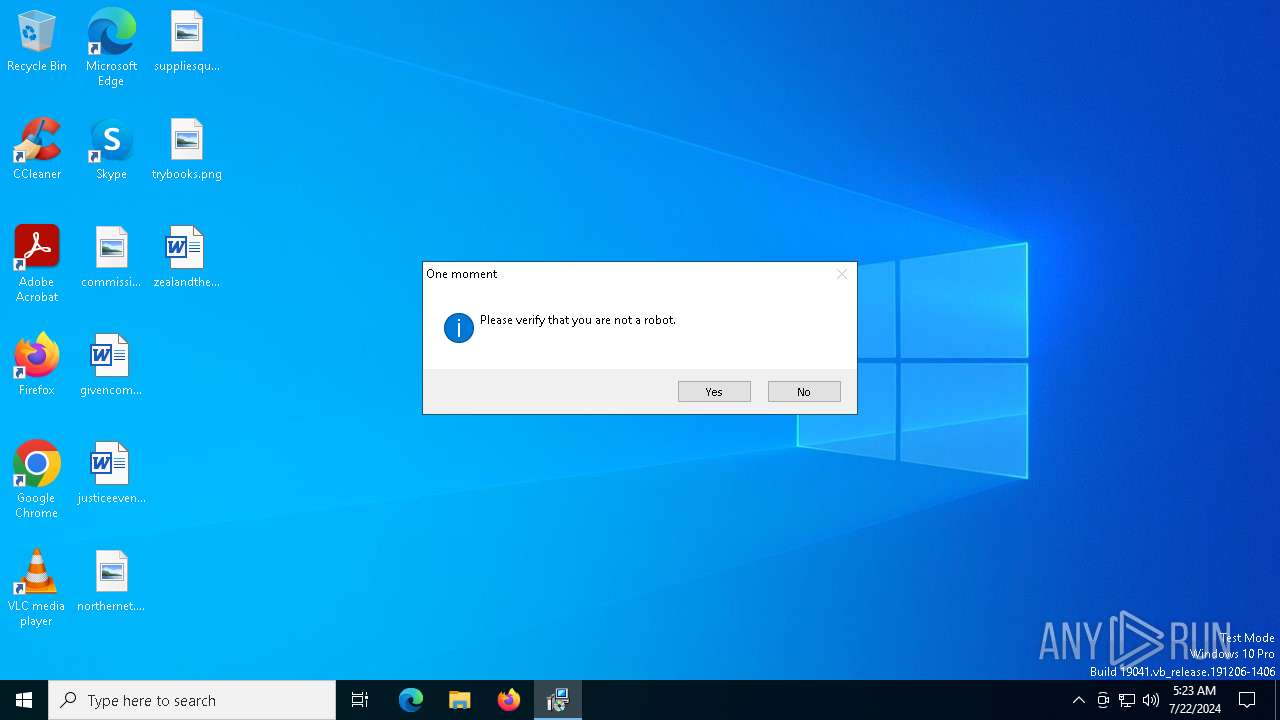
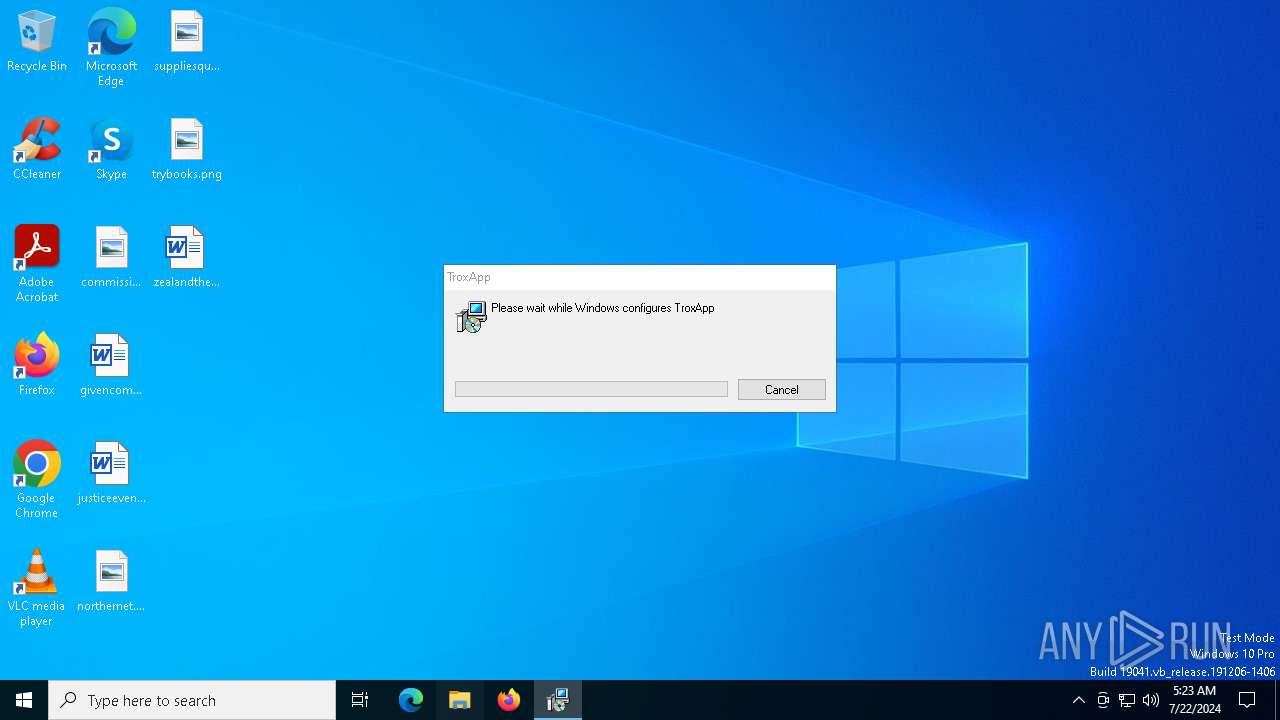
MALICIOUS
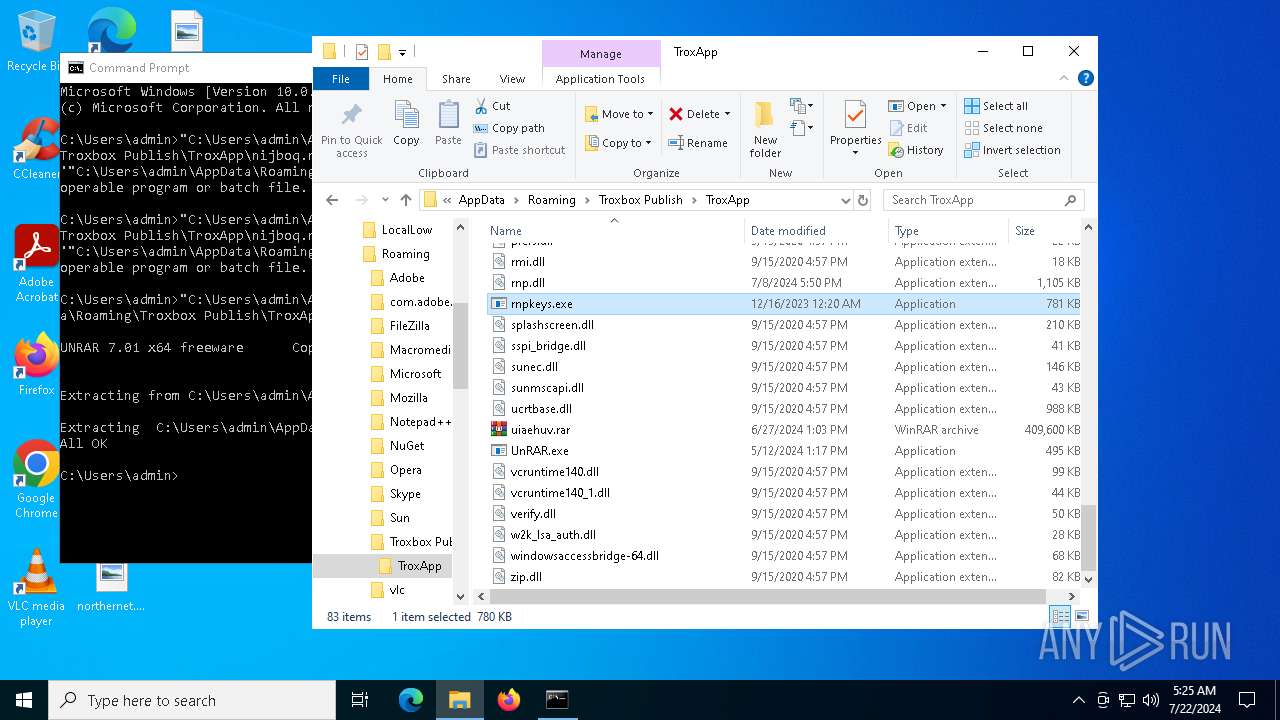
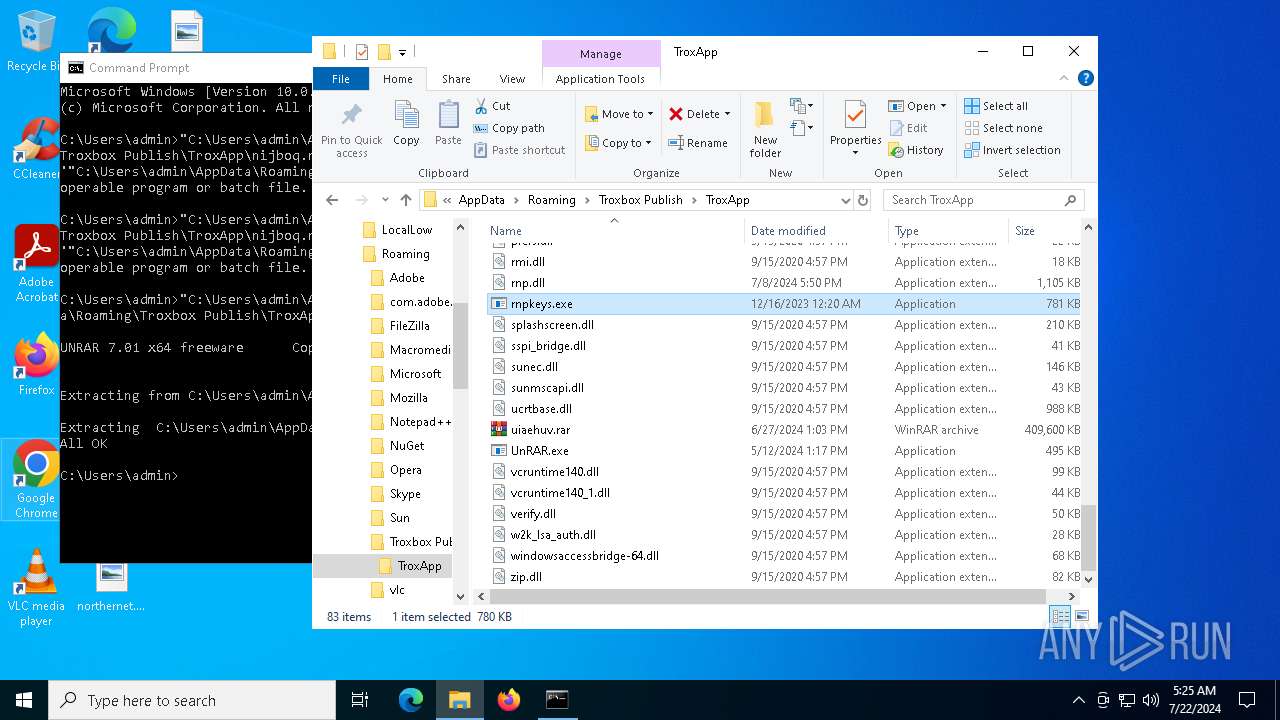
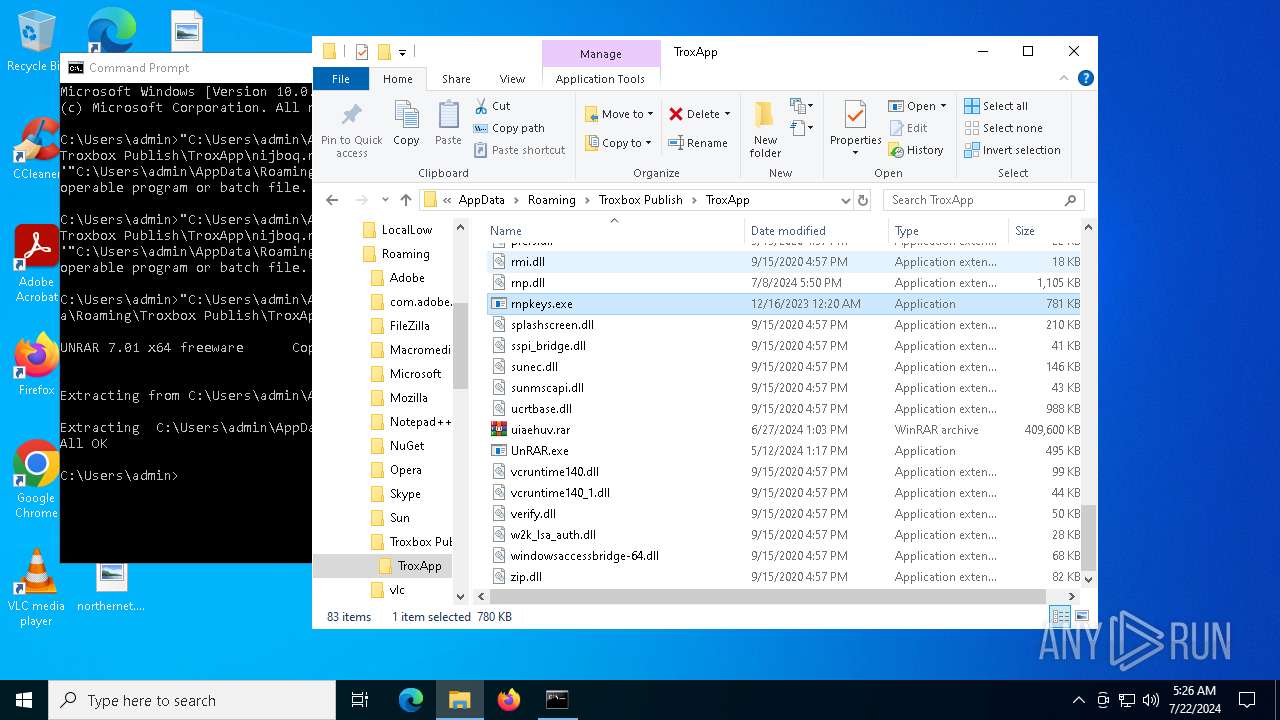
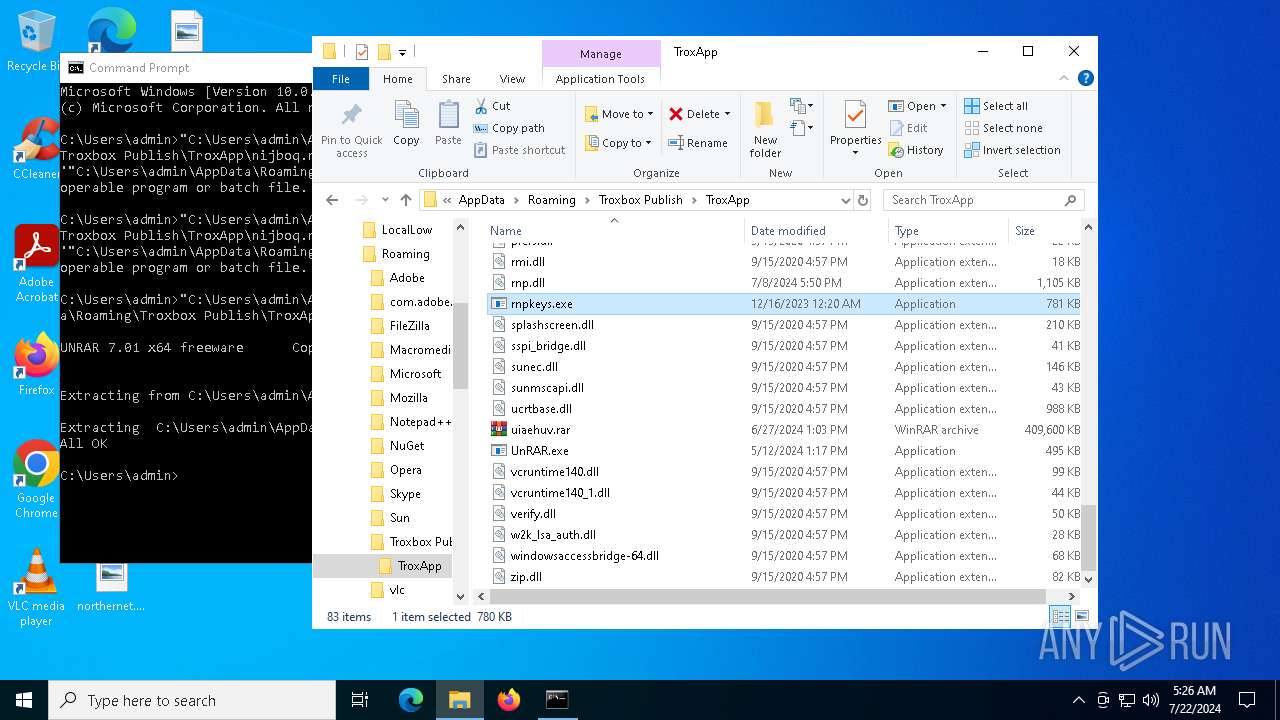
Drops the executable file immediately after the start
- msiexec.exe (PID: 7096)
- UnRAR.exe (PID: 3920)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7096)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2344)
Checks Windows Trust Settings
- msiexec.exe (PID: 2344)
Process drops legitimate windows executable
- msiexec.exe (PID: 7096)
The process drops C-runtime libraries
- msiexec.exe (PID: 7096)
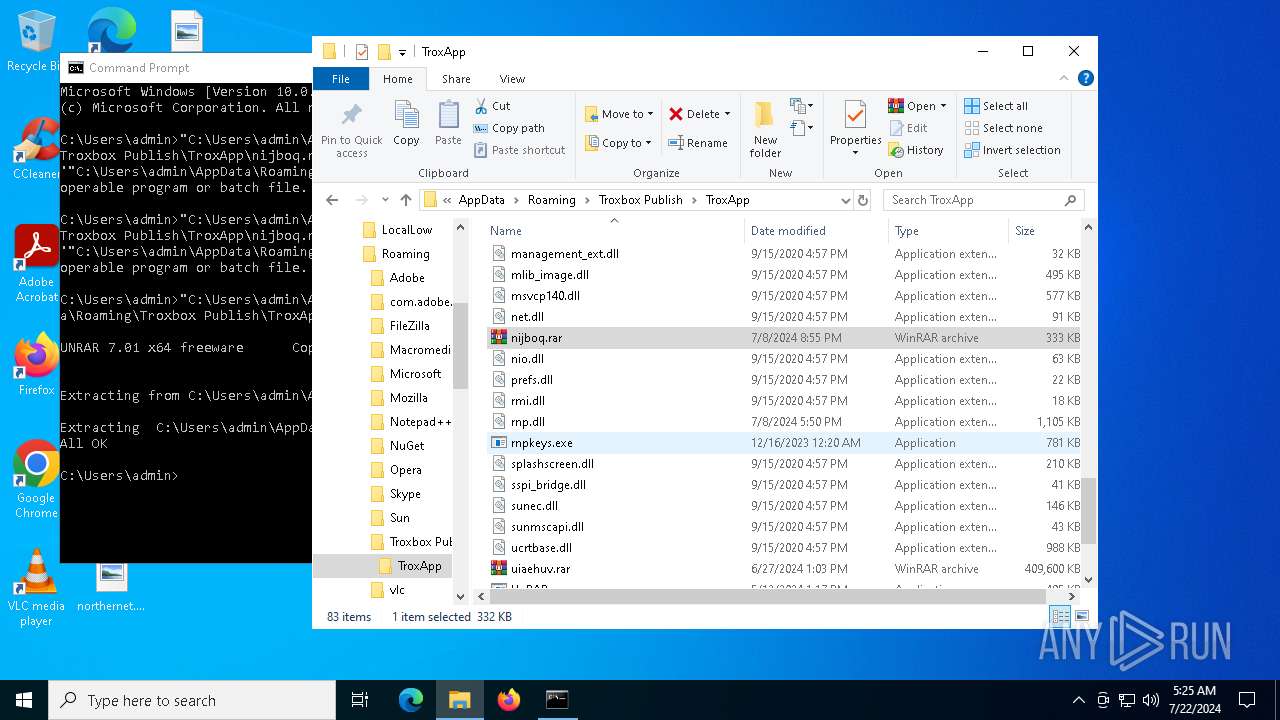
Executes application which crashes
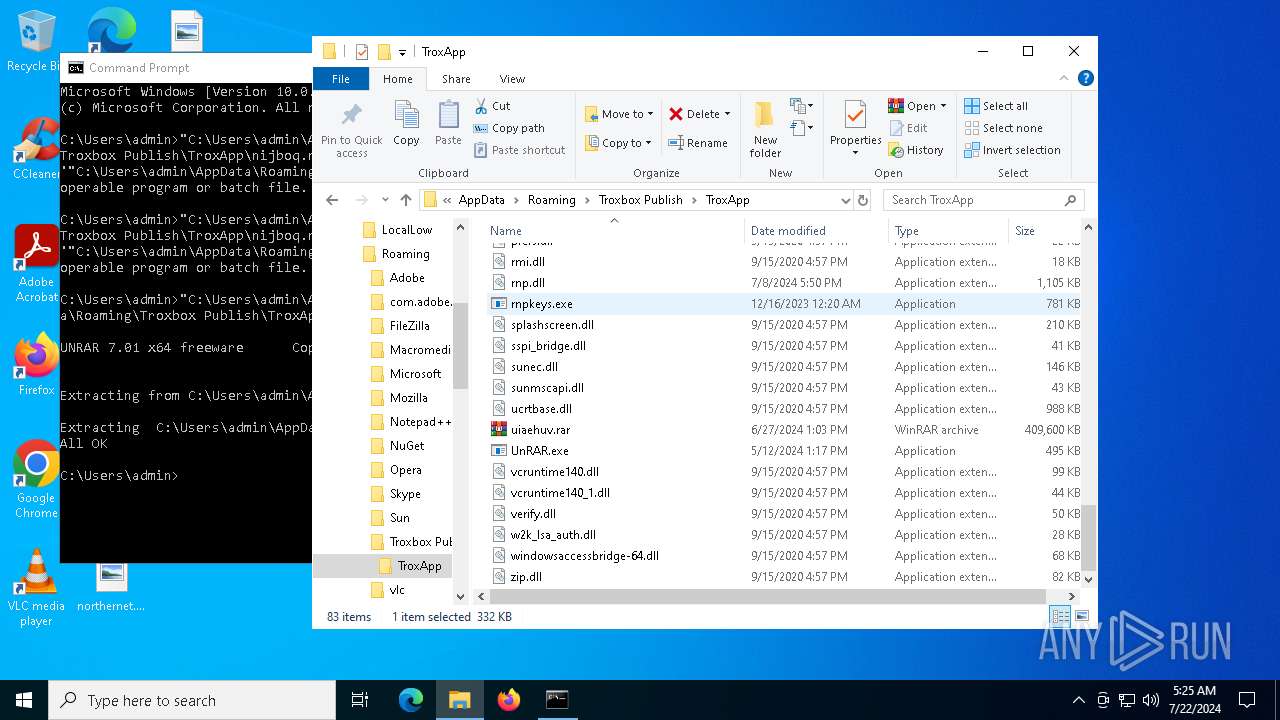
- rnpkeys.exe (PID: 7796)
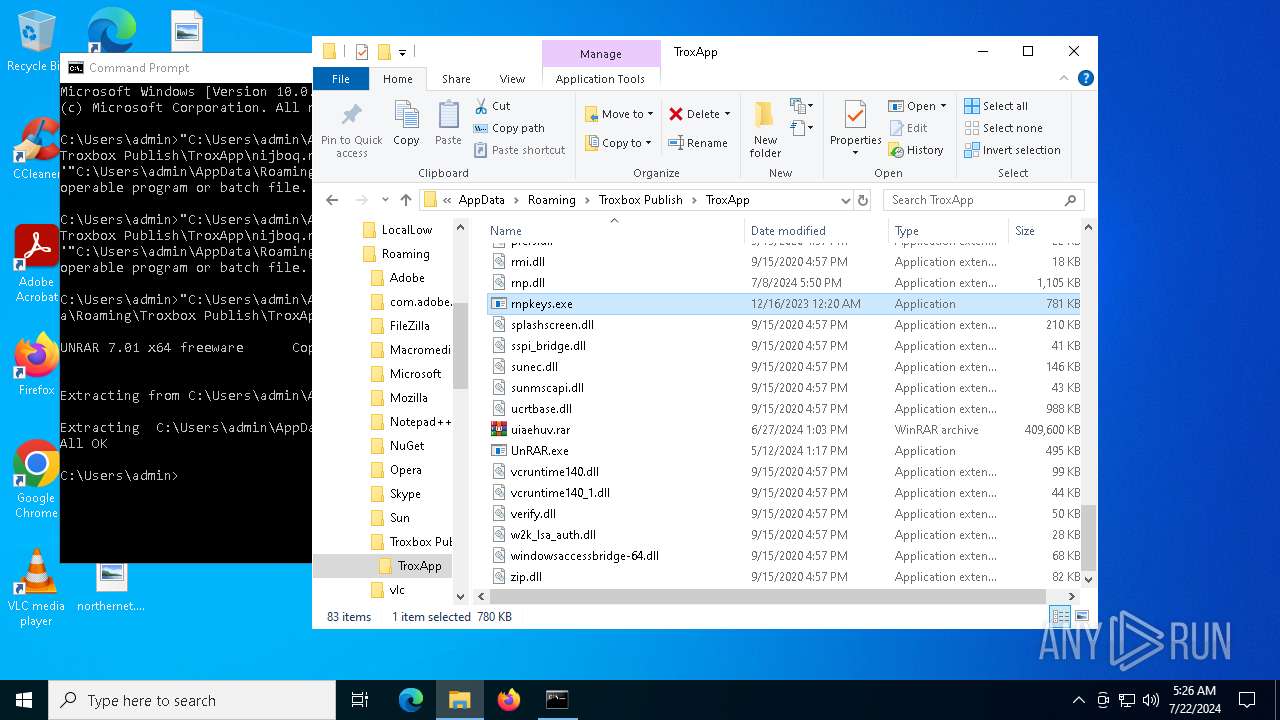
Executable content was dropped or overwritten
- UnRAR.exe (PID: 3920)
INFO
An automatically generated document
- msiexec.exe (PID: 5724)
Reads the computer name
- msiexec.exe (PID: 7096)
- msiexec.exe (PID: 2344)
Checks supported languages
- msiexec.exe (PID: 2344)
- msiexec.exe (PID: 7096)
- UnRAR.exe (PID: 3920)
- rnpkeys.exe (PID: 7796)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7096)
Reads Environment values
- msiexec.exe (PID: 2344)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2344)
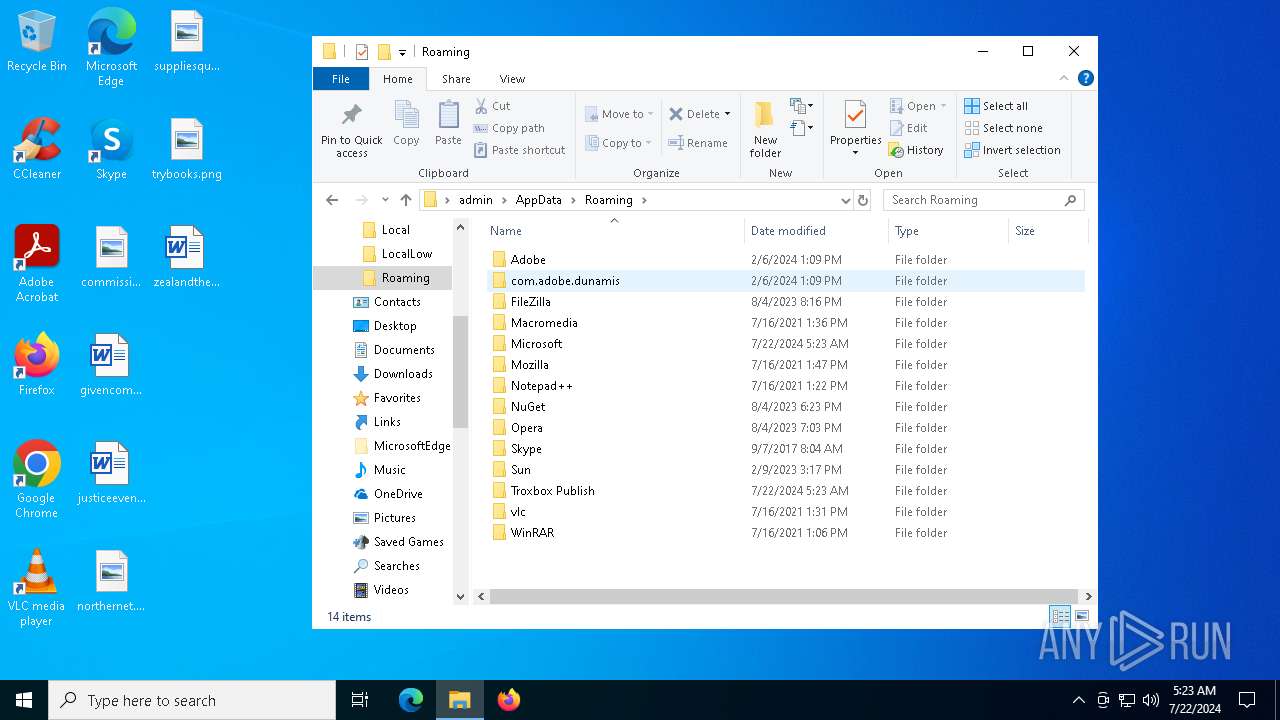
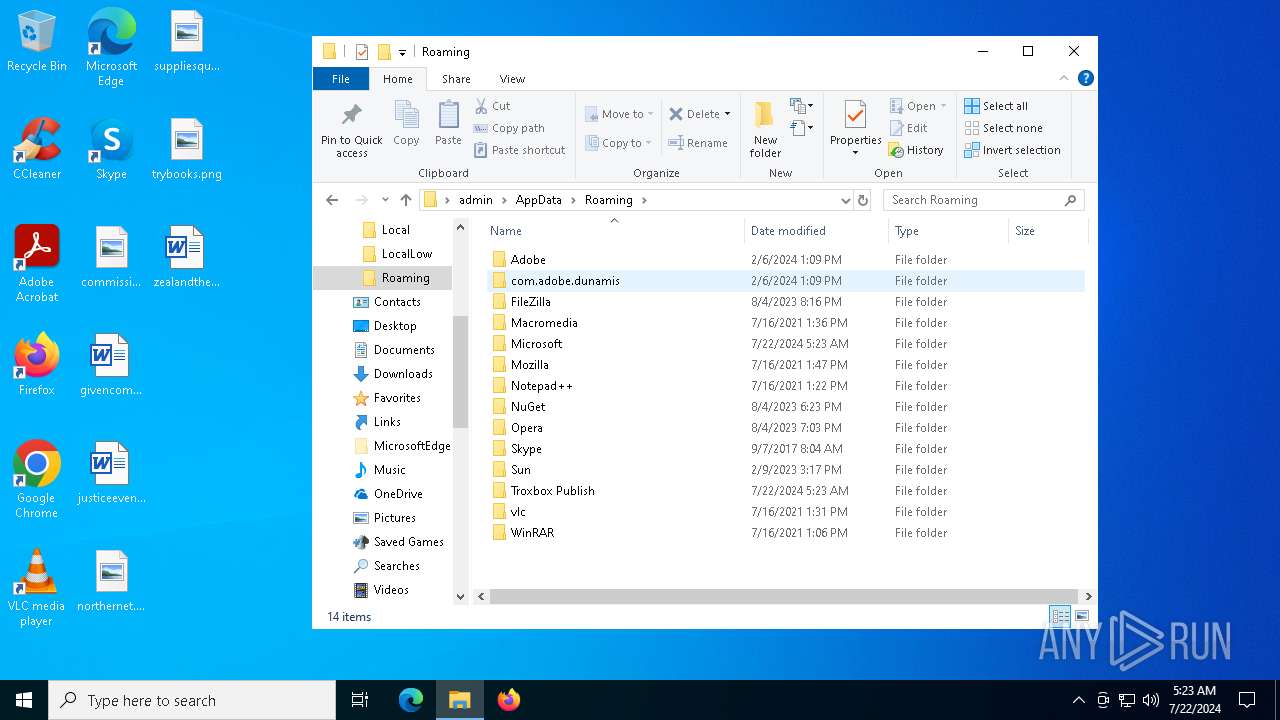
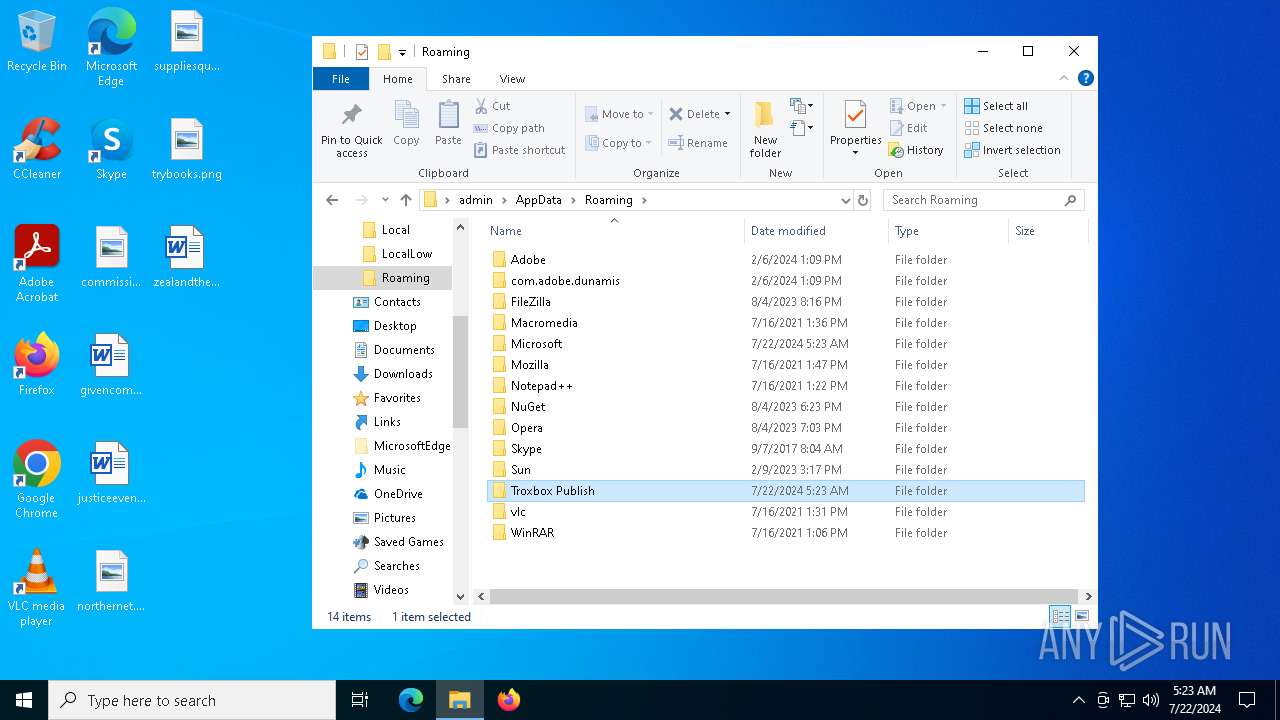
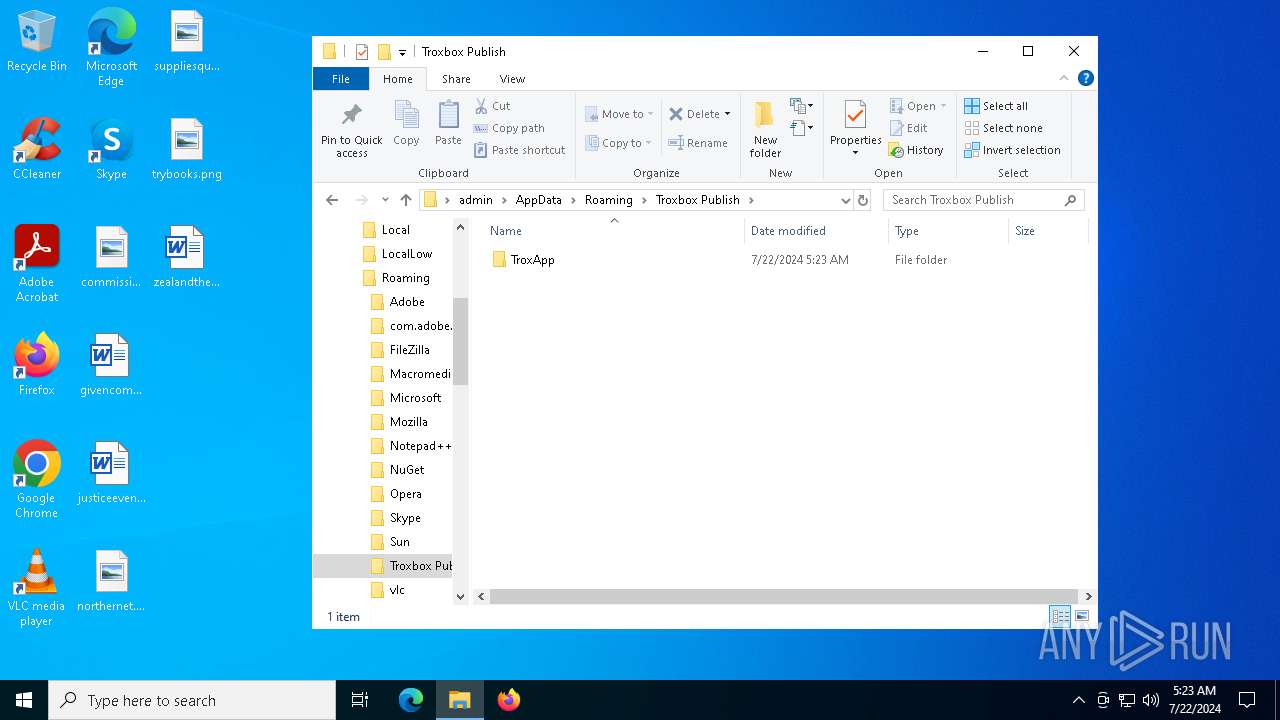
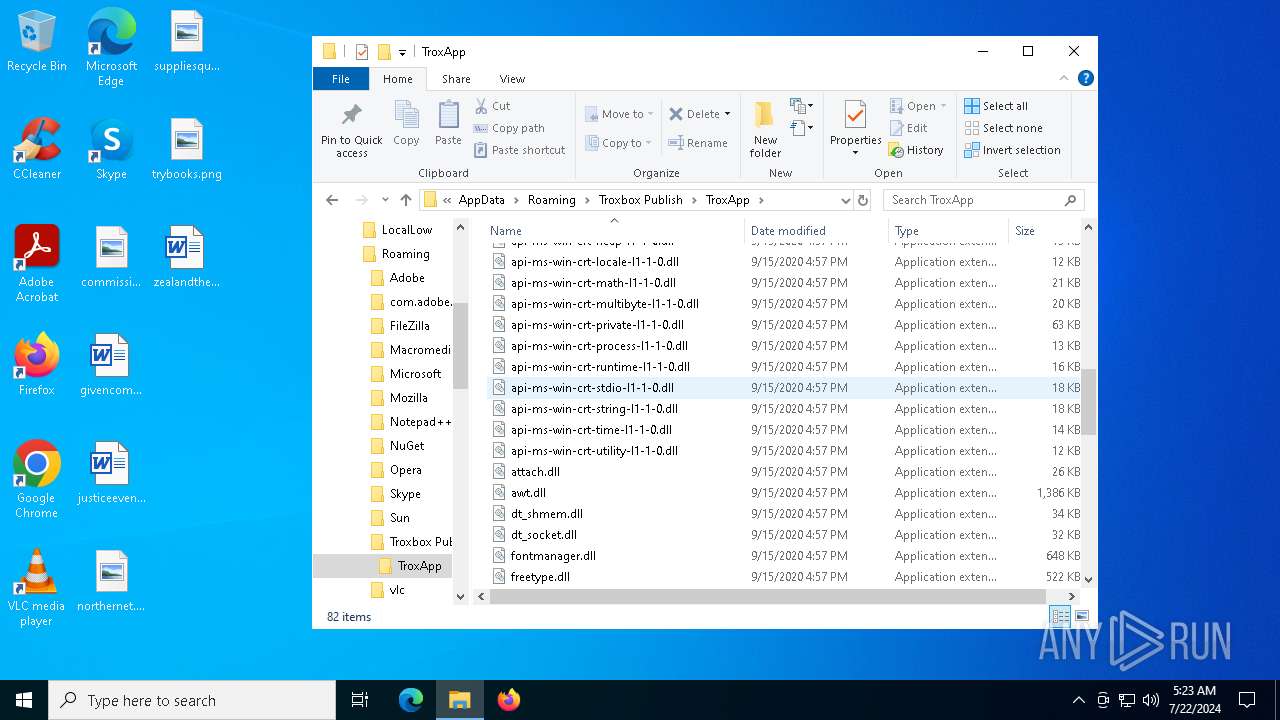
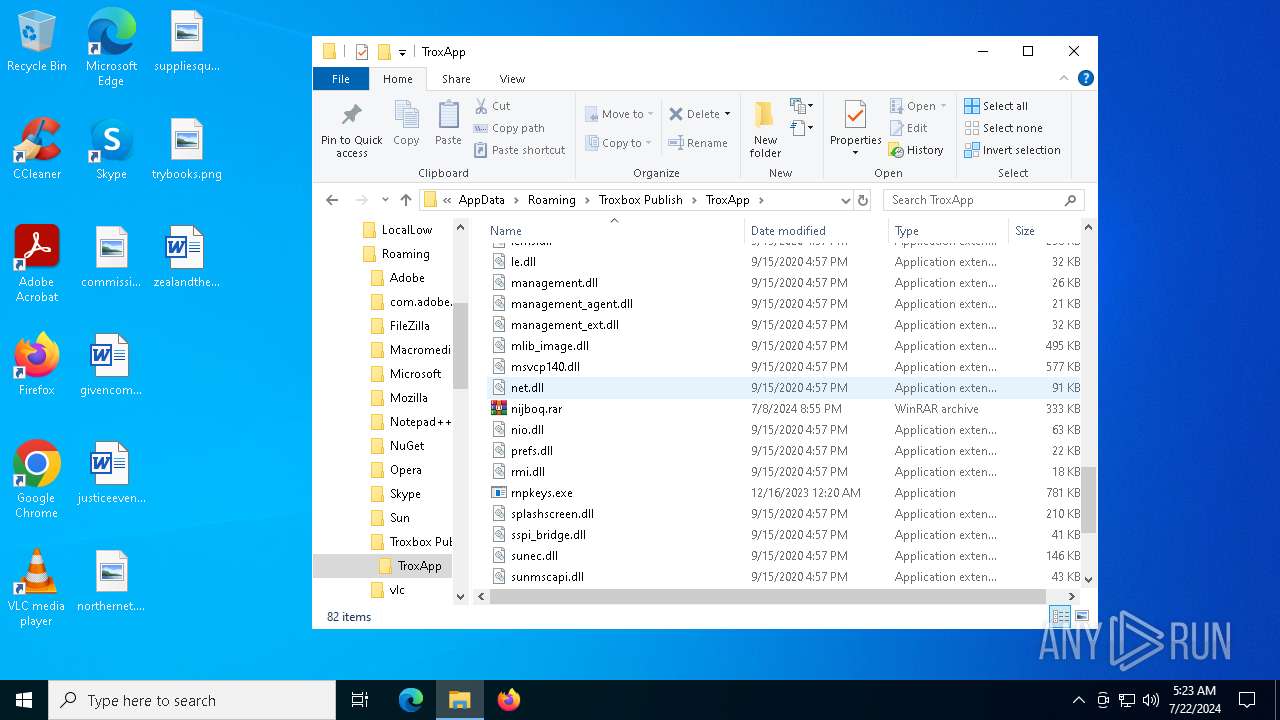
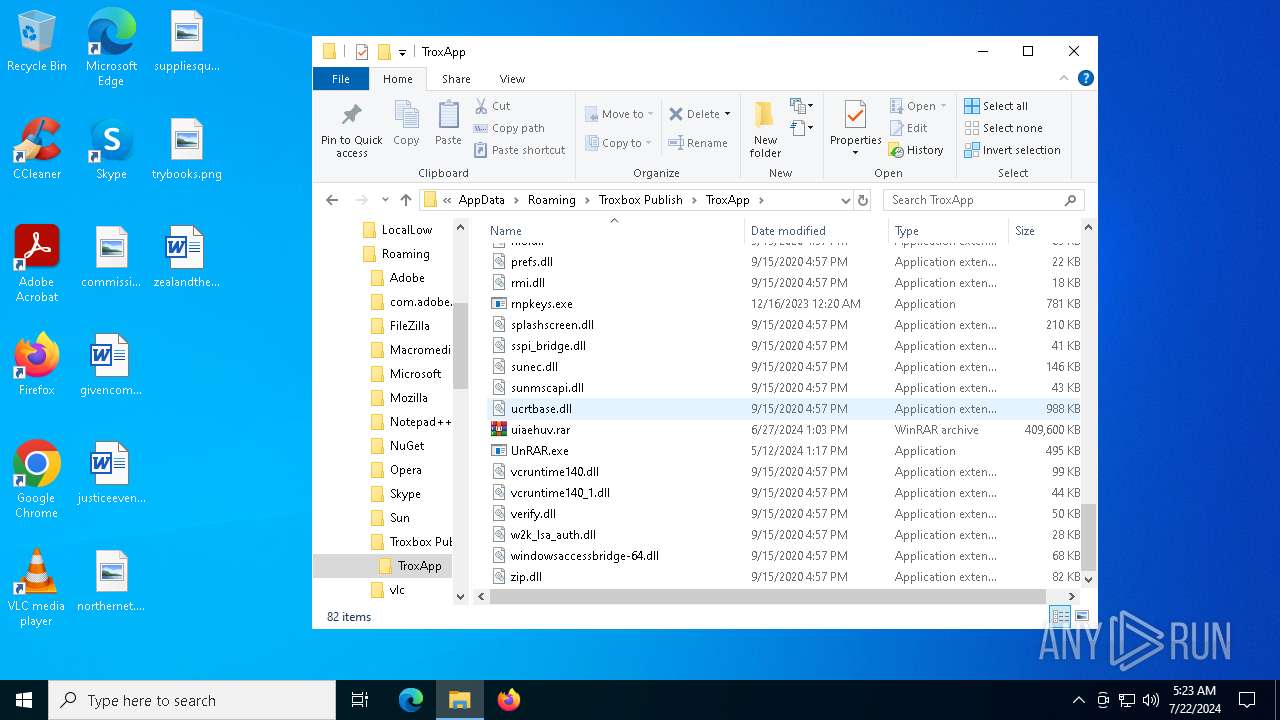
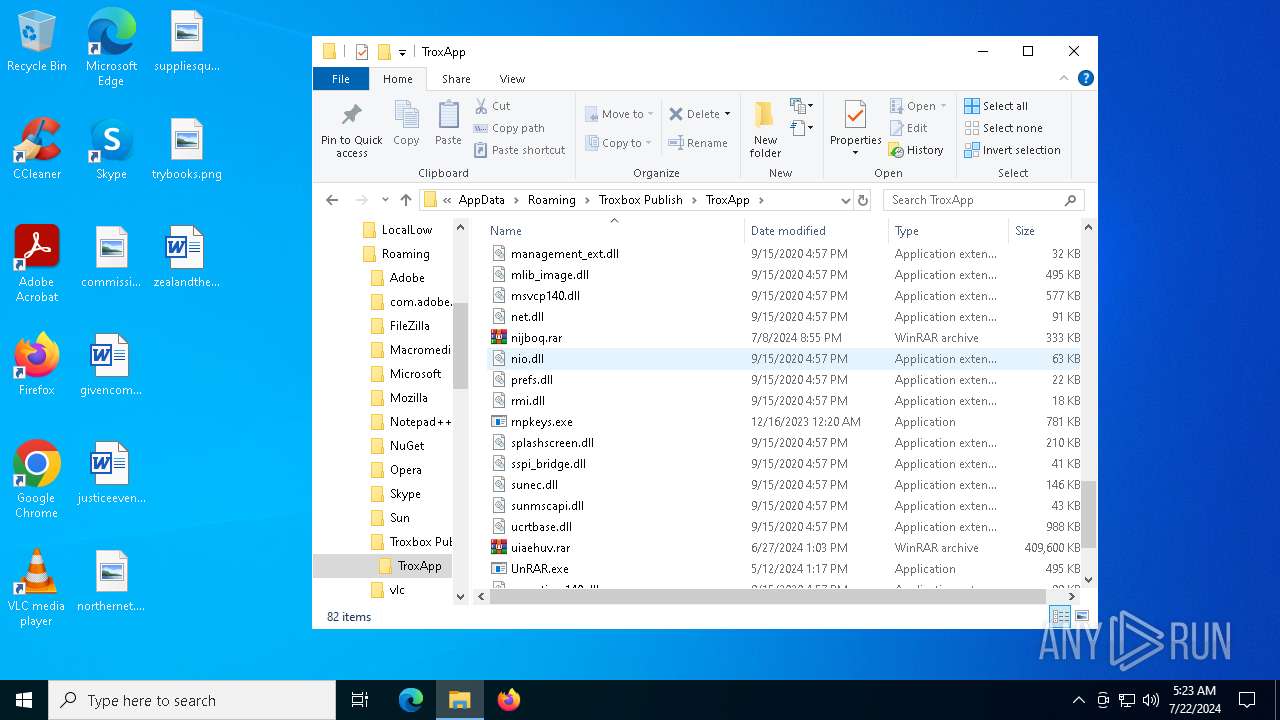
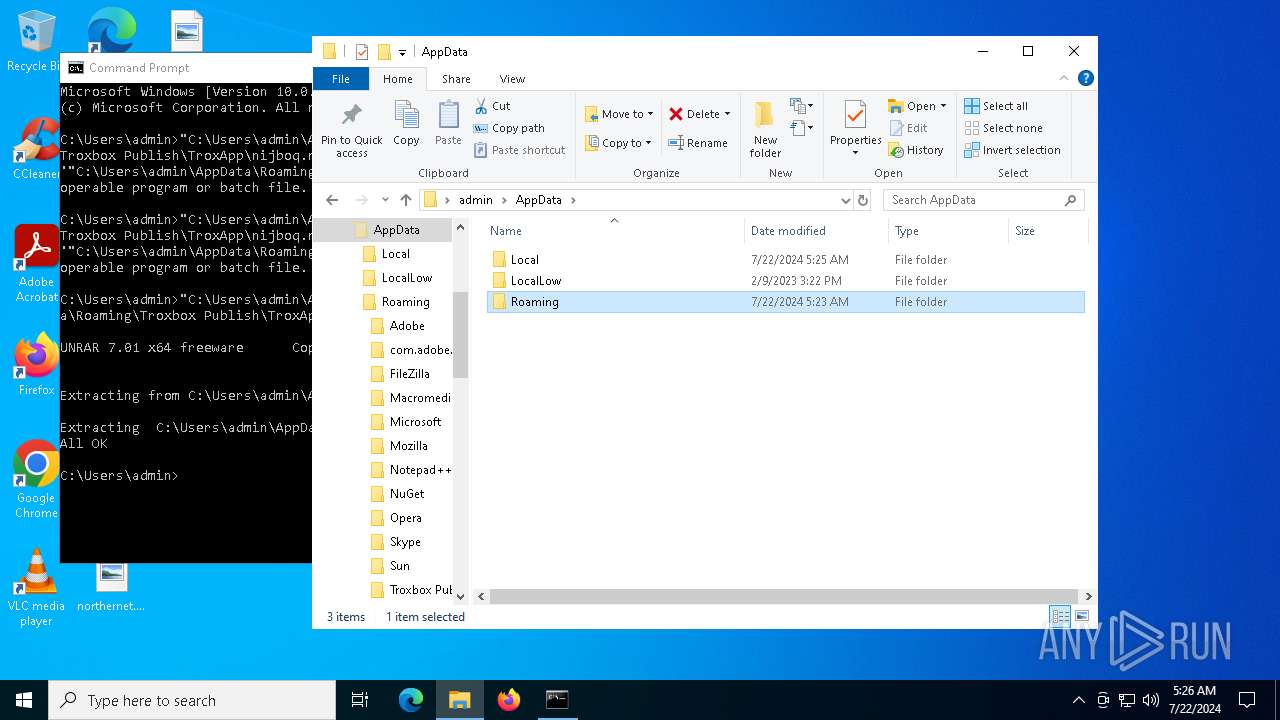
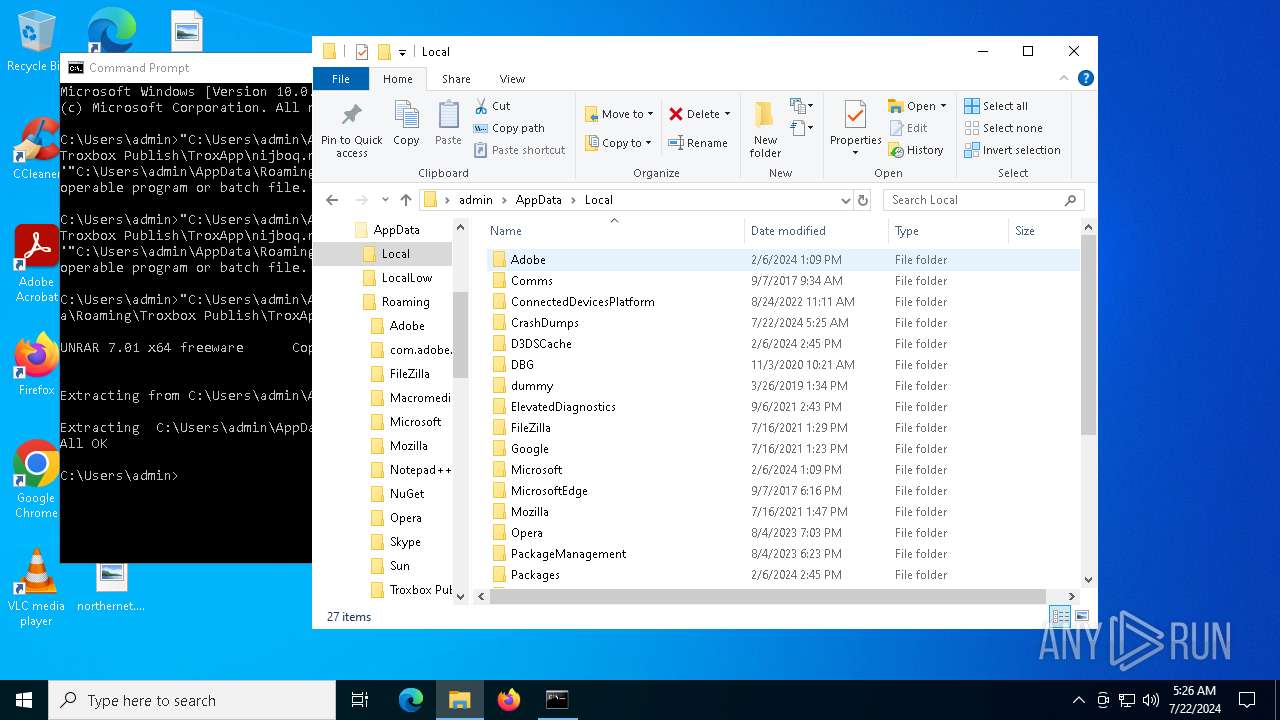
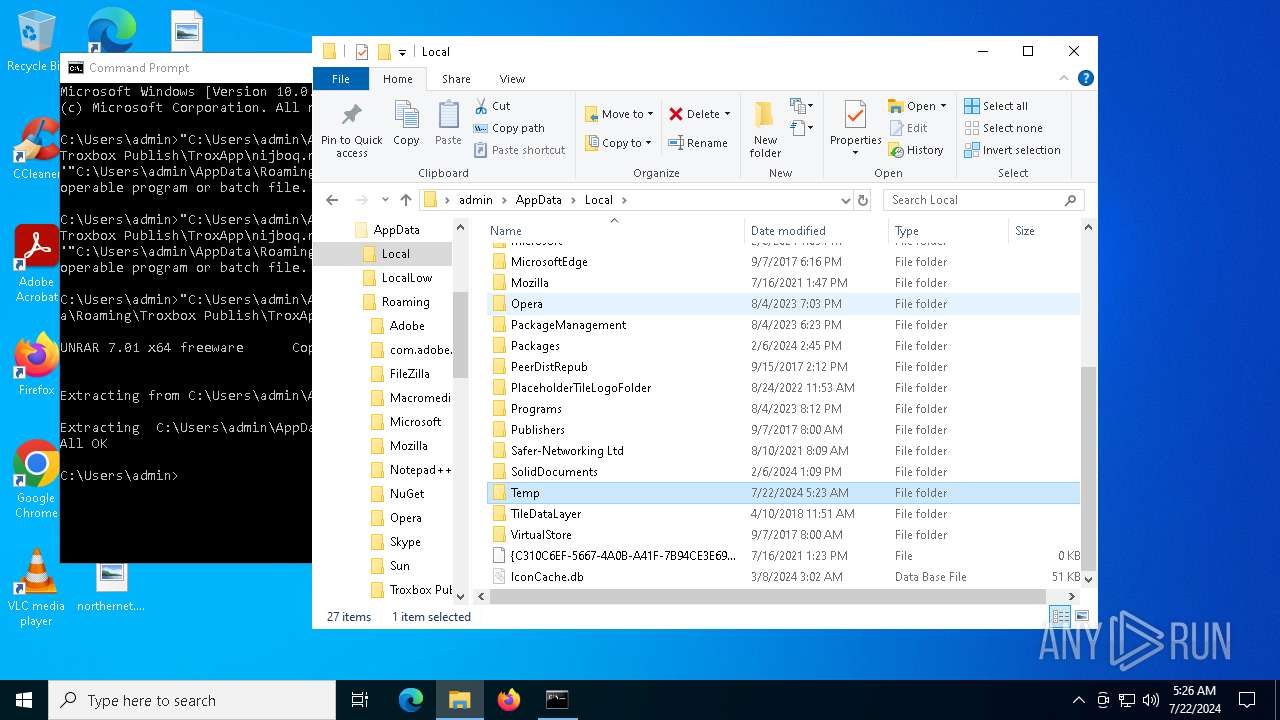
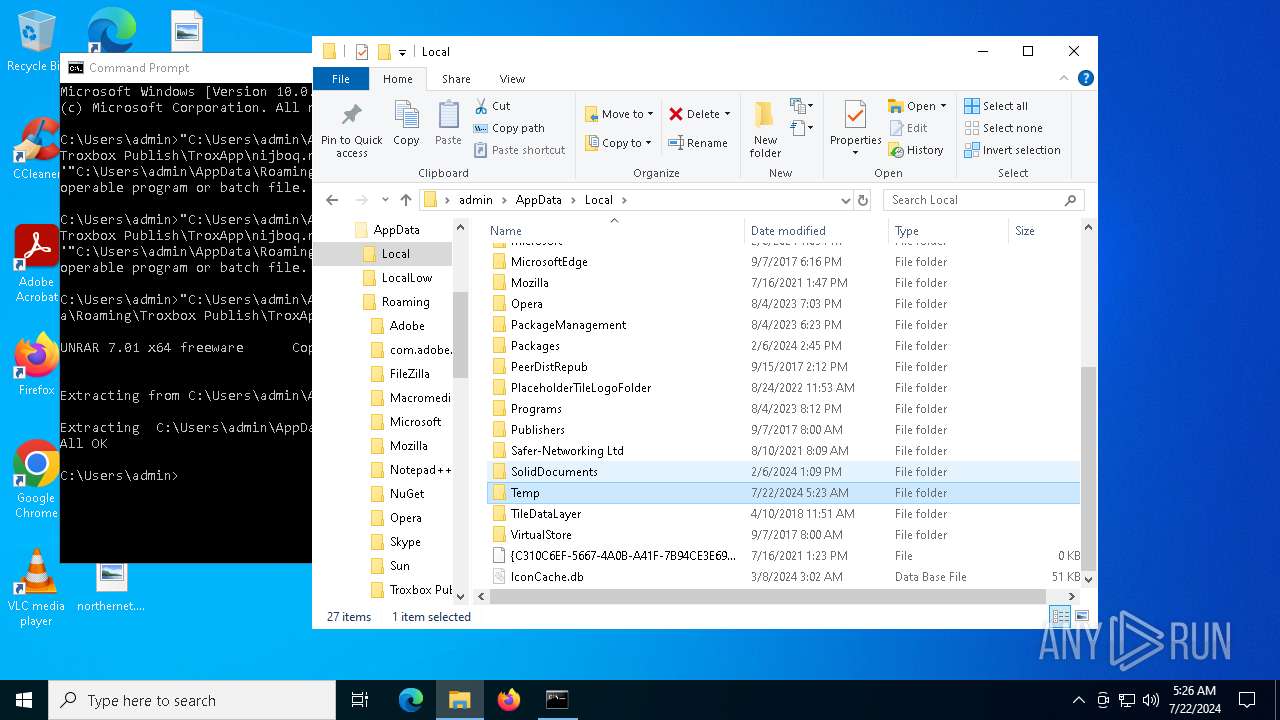
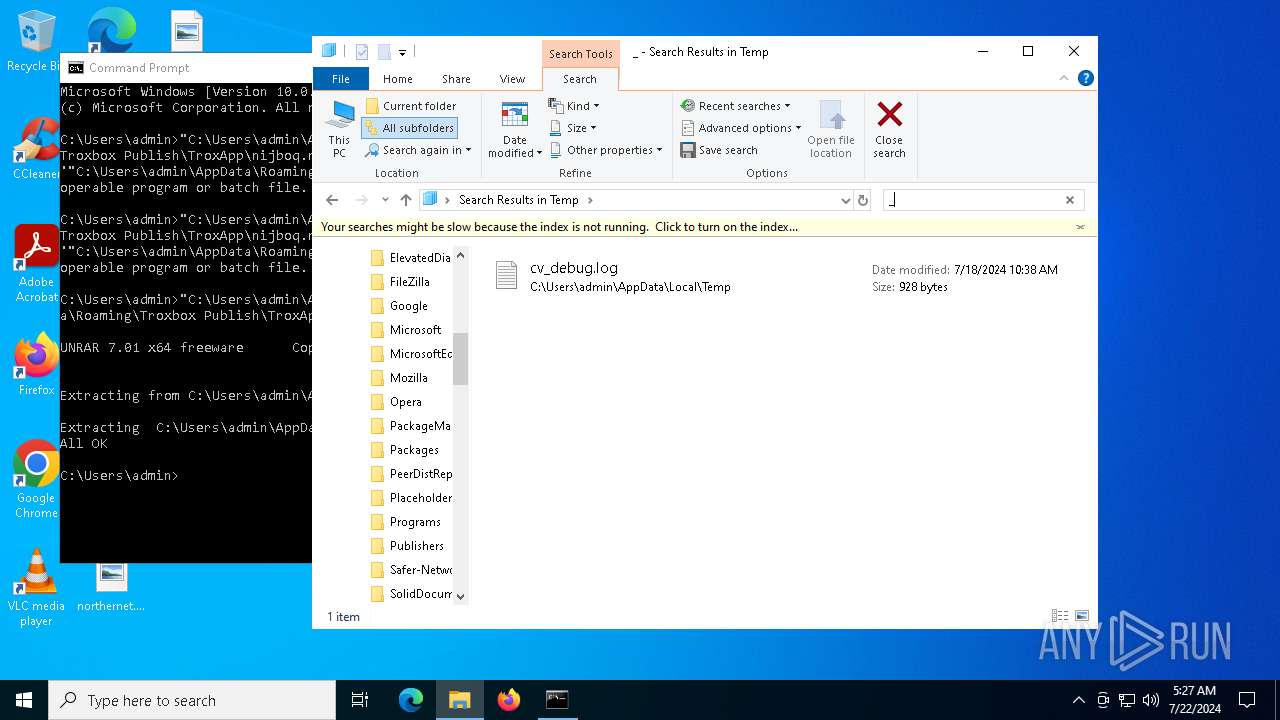
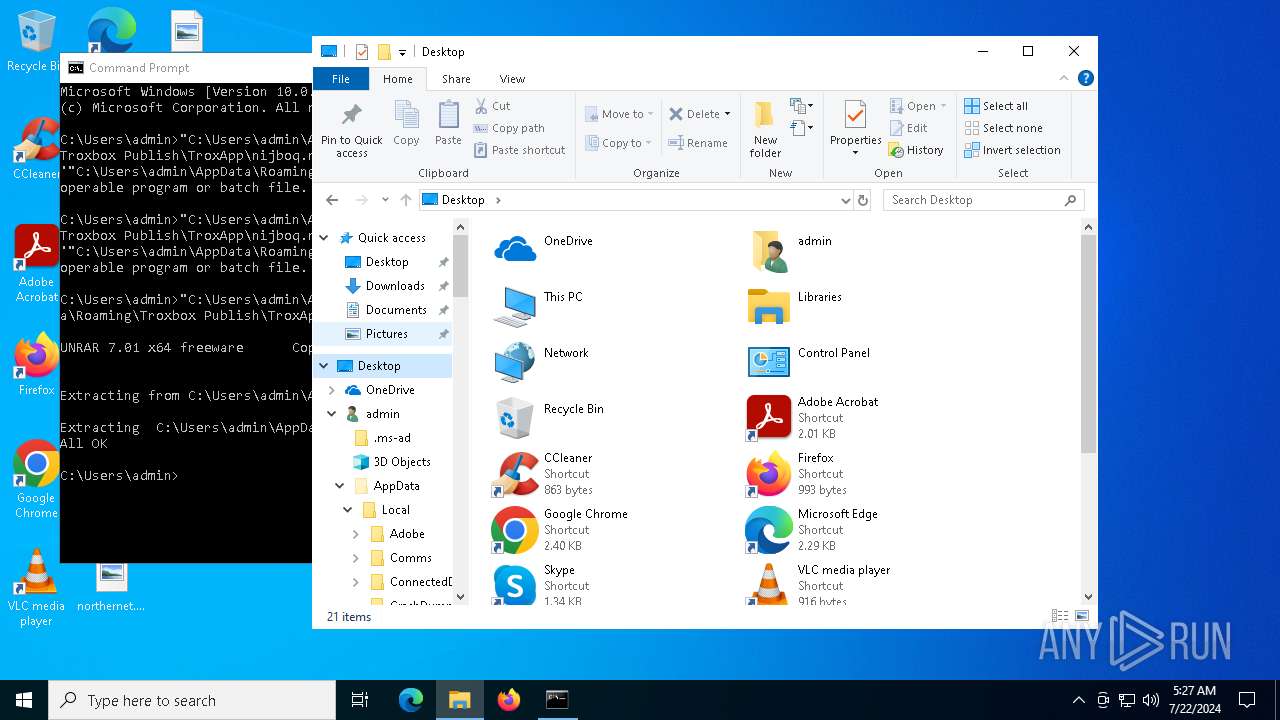
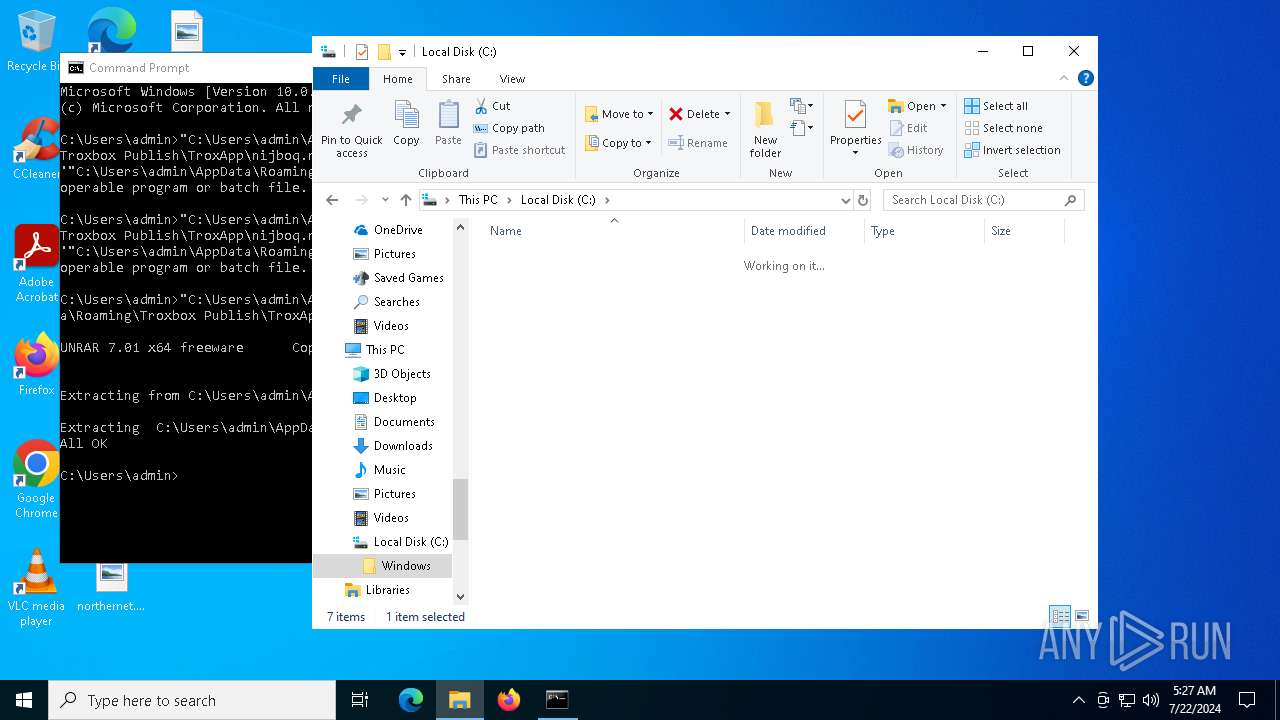
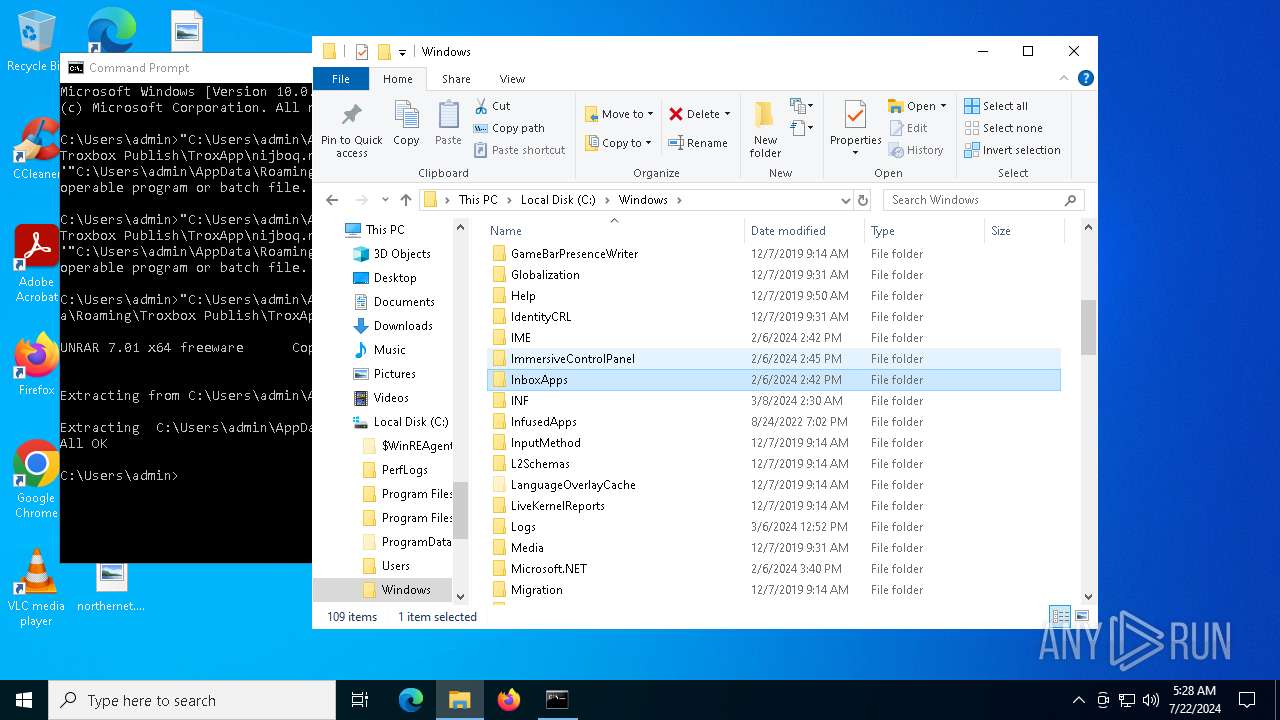
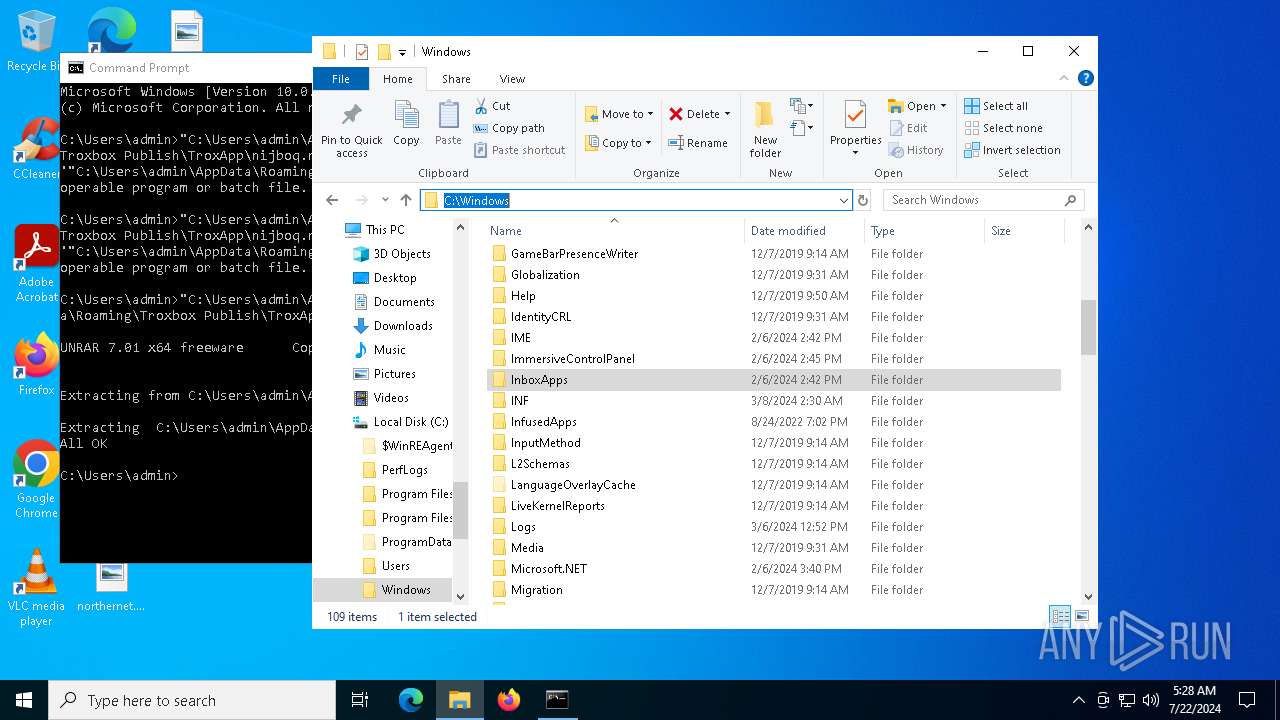
Creates files or folders in the user directory
- msiexec.exe (PID: 7096)
- msiexec.exe (PID: 2344)
- WerFault.exe (PID: 5748)
- UnRAR.exe (PID: 3920)
- WerFault.exe (PID: 7012)
Checks proxy server information
- msiexec.exe (PID: 2344)
Reads the software policy settings
- msiexec.exe (PID: 2344)
Creates a software uninstall entry
- msiexec.exe (PID: 7096)
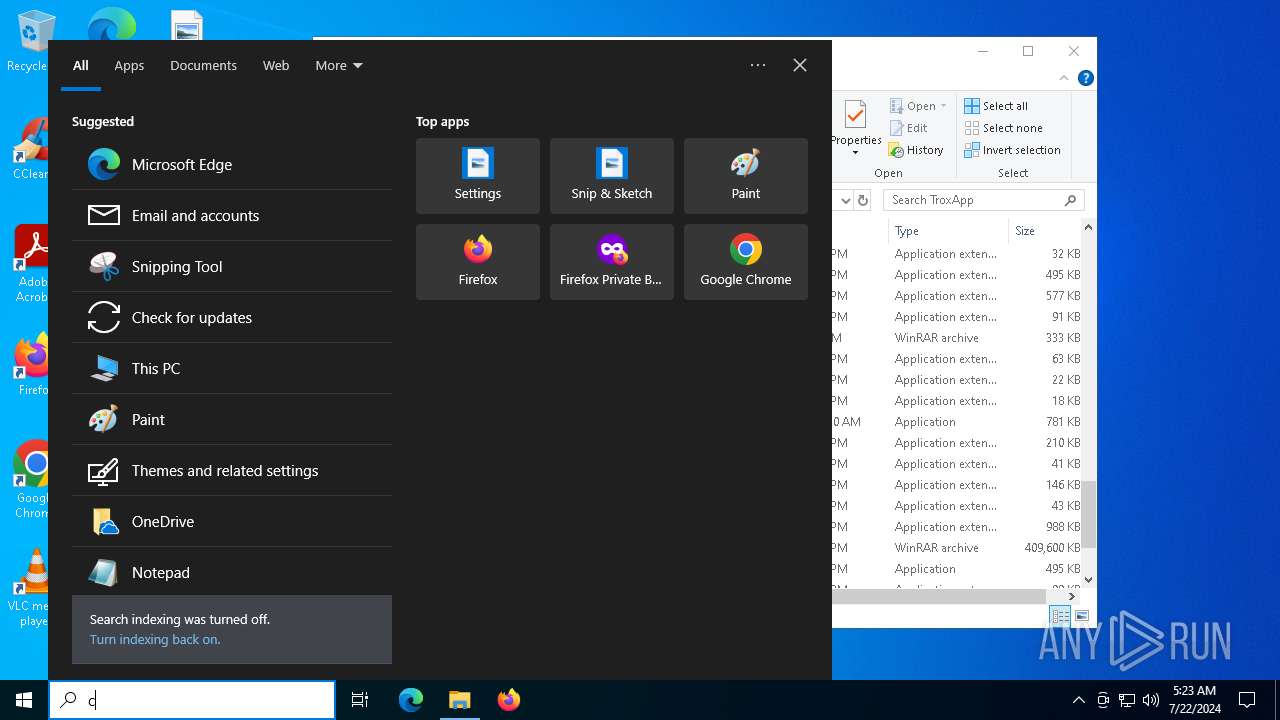
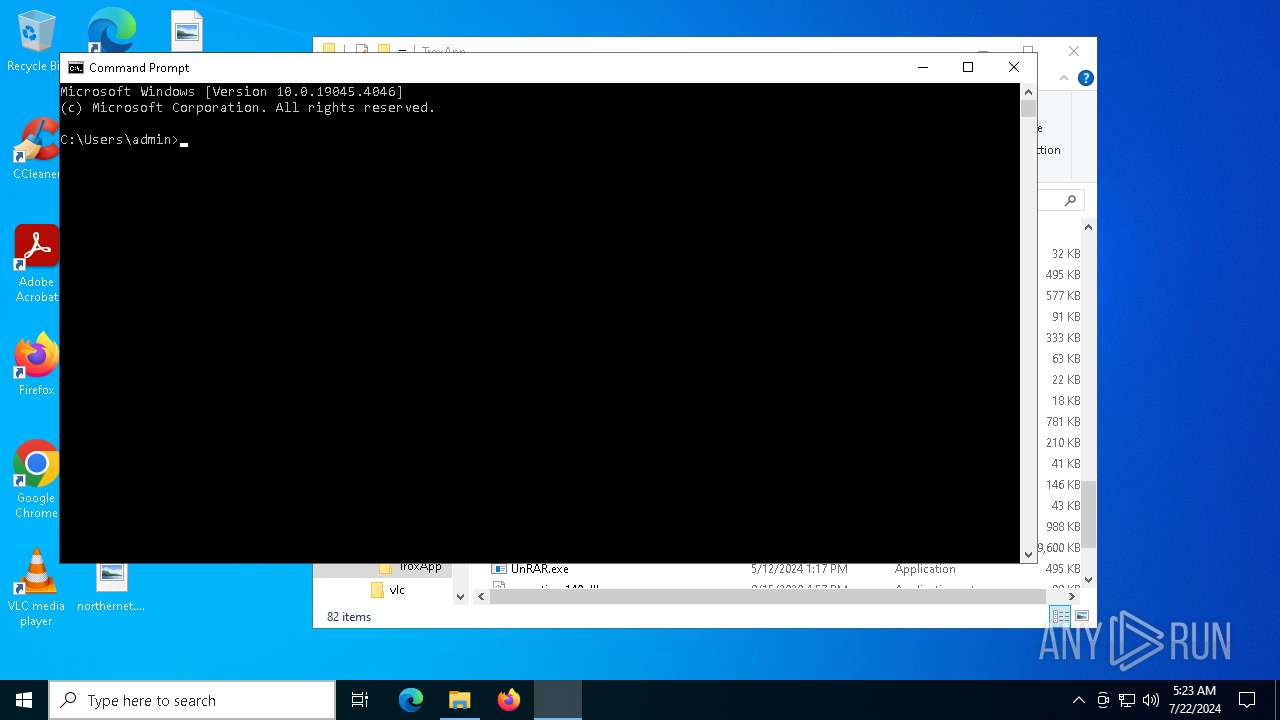
Manual execution by a user
- cmd.exe (PID: 4504)
- rnpkeys.exe (PID: 7796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {A3B69905-389C-4777-92FB-F2E072712230} |
| Words: | 10 |
| Subject: | TroxApp |
| Author: | Troxbox Publish |
| LastModifiedBy: | - |
| Software: | TroxApp |
| Template: | x64;1033 |
| Comments: | This installer database contains the logic and data required to install TroxApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:07:08 17:55:21 |
| ModifyDate: | 2024:07:08 17:55:21 |
| LastPrinted: | 2024:07:08 17:55:21 |
| Pages: | 450 |
Total processes
153
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2344 | C:\Windows\syswow64\MsiExec.exe -Embedding 46524EF9D8D0E902449E2BDB6B5B9E22 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
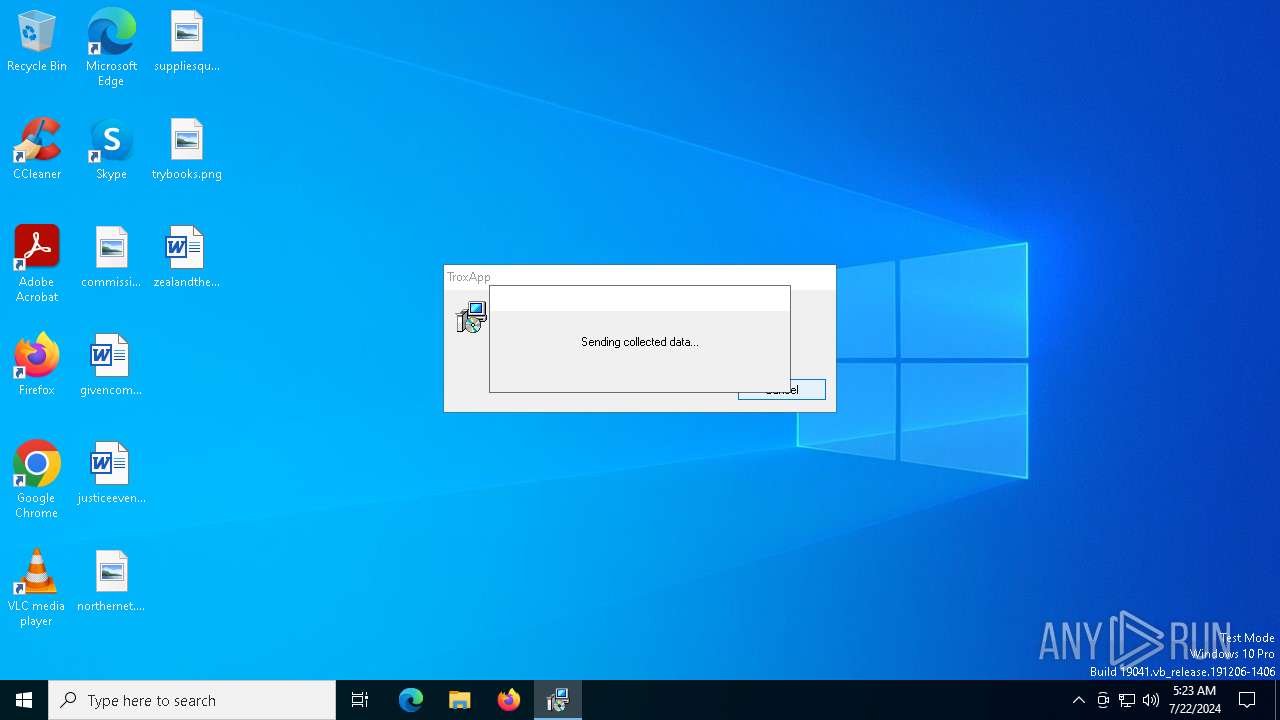
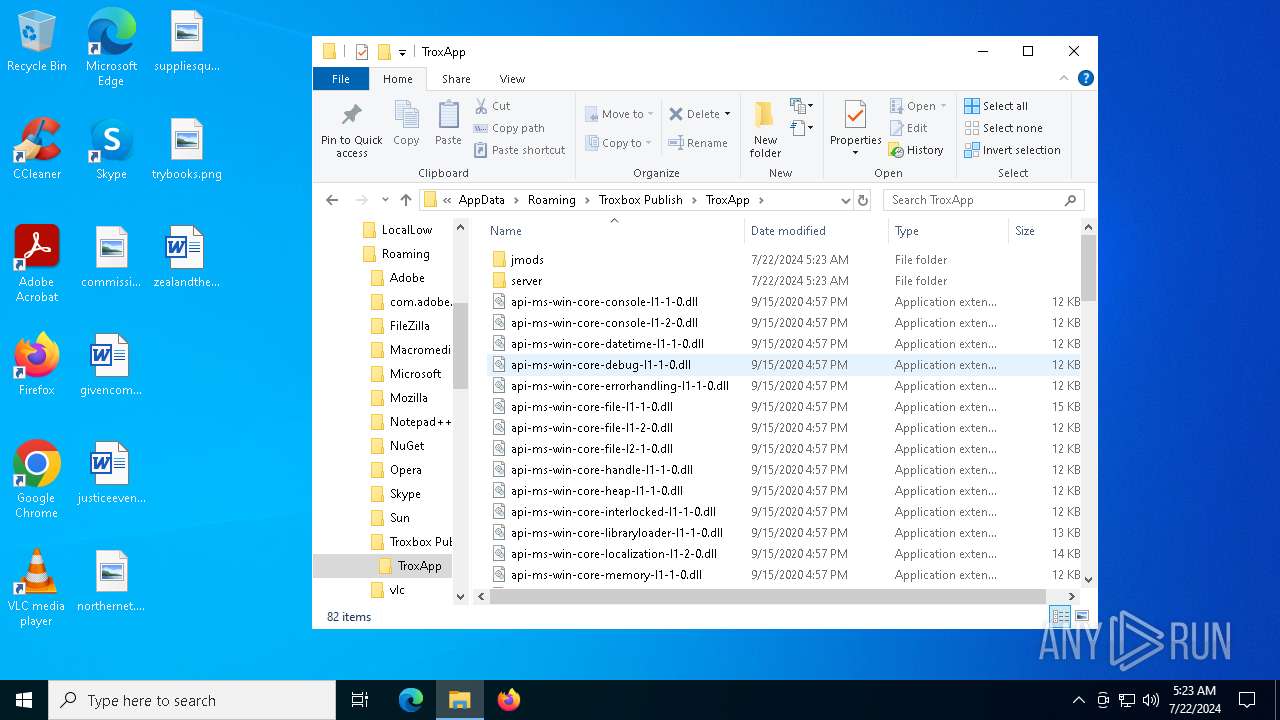
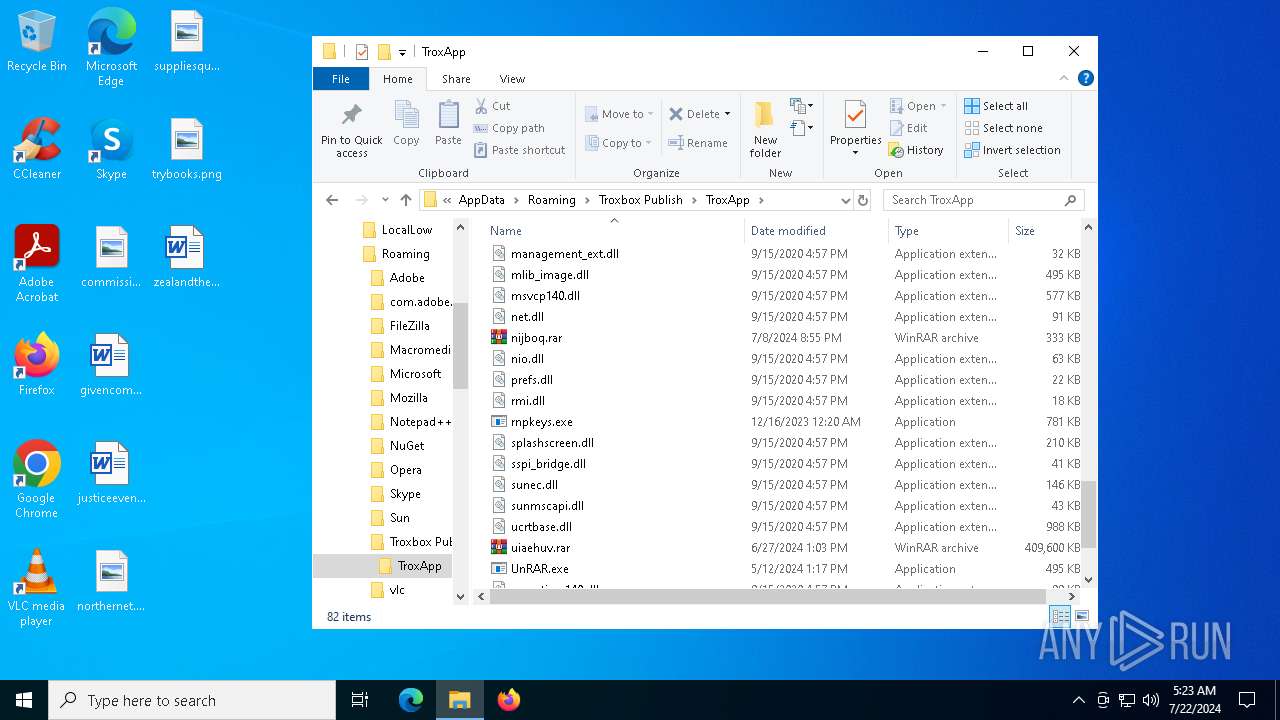
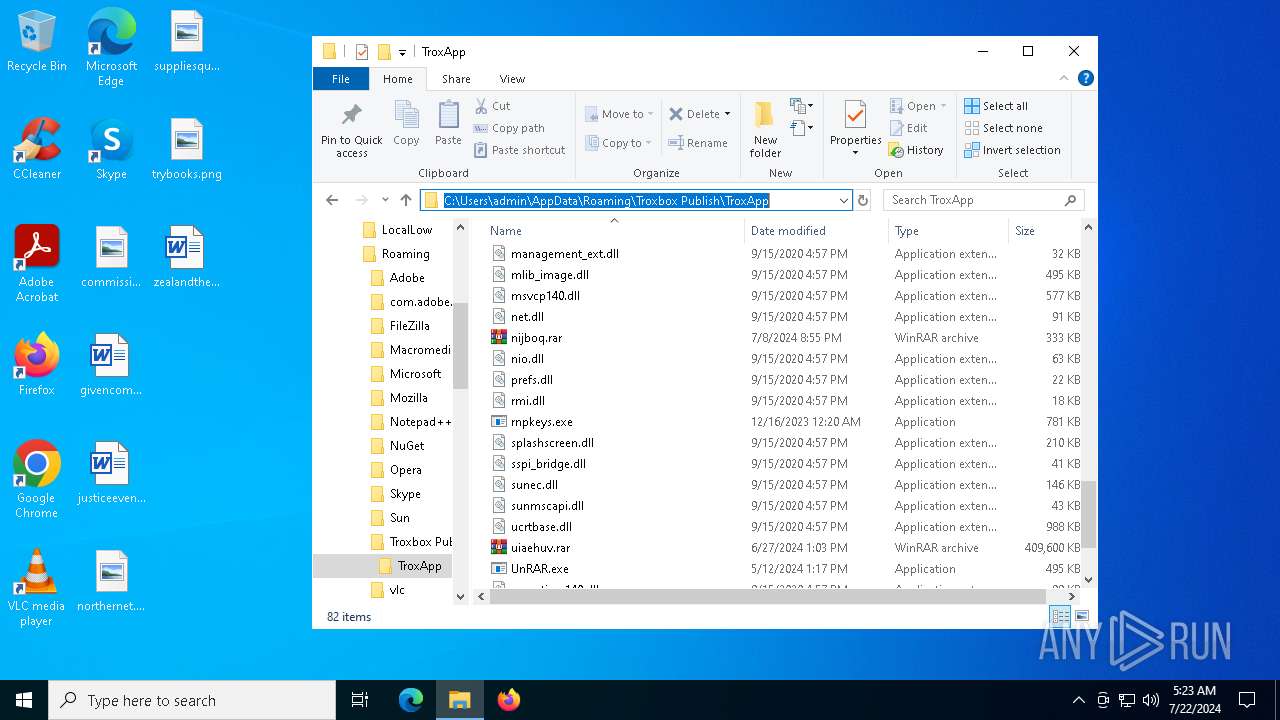
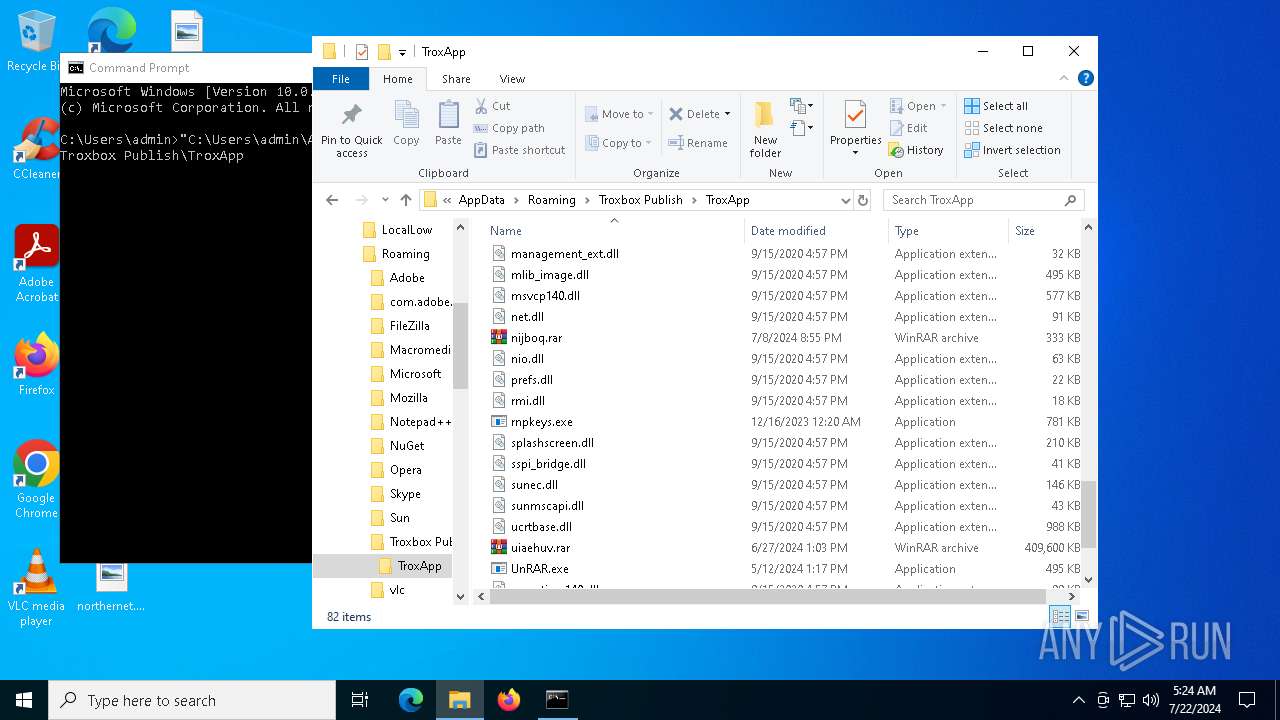
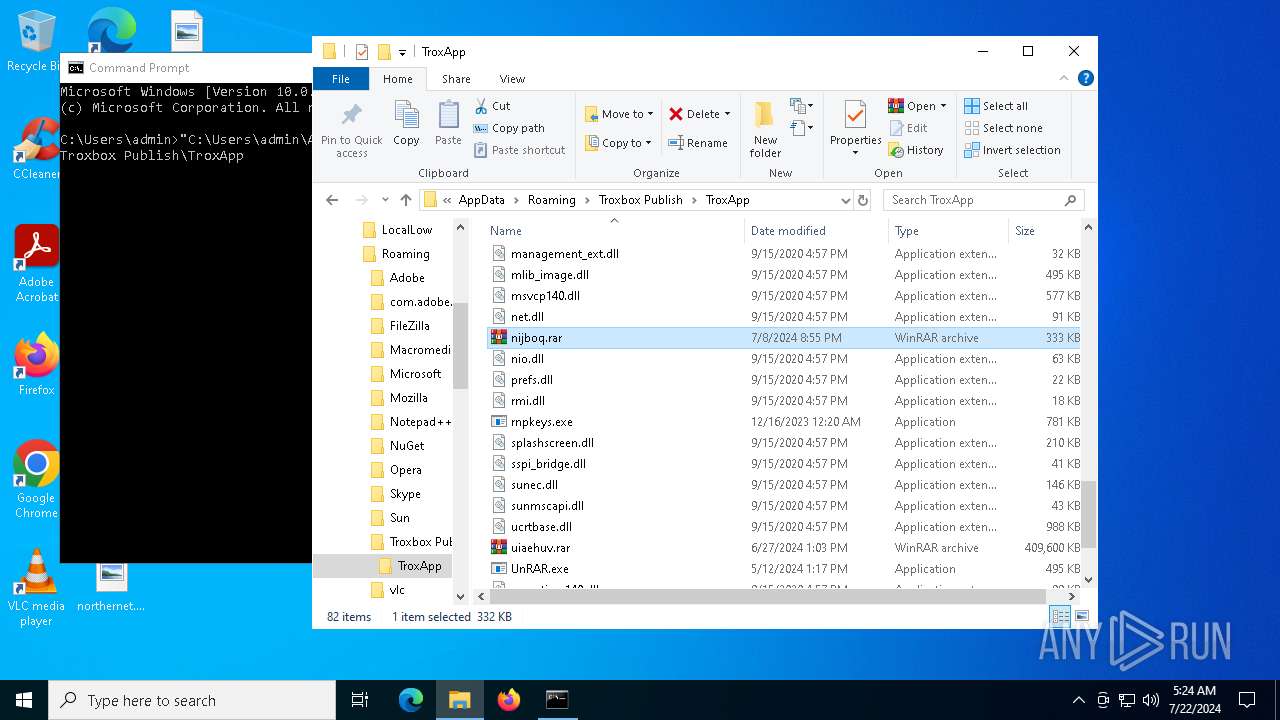
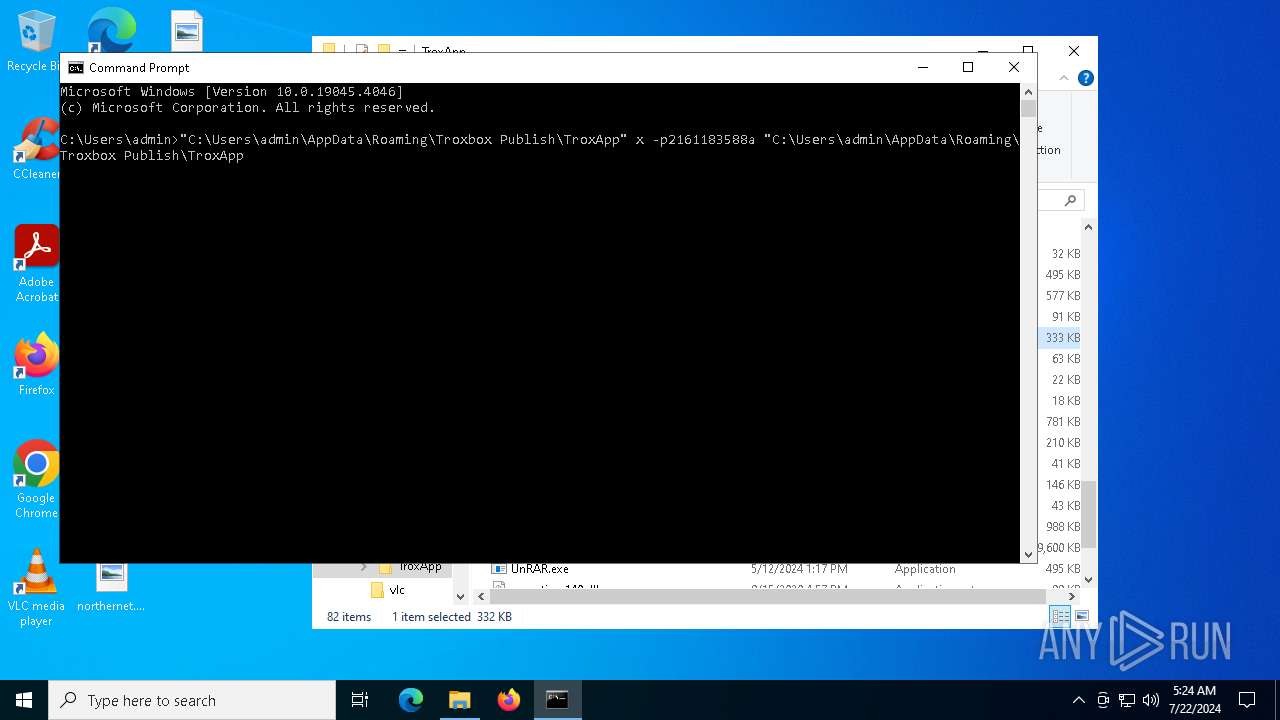
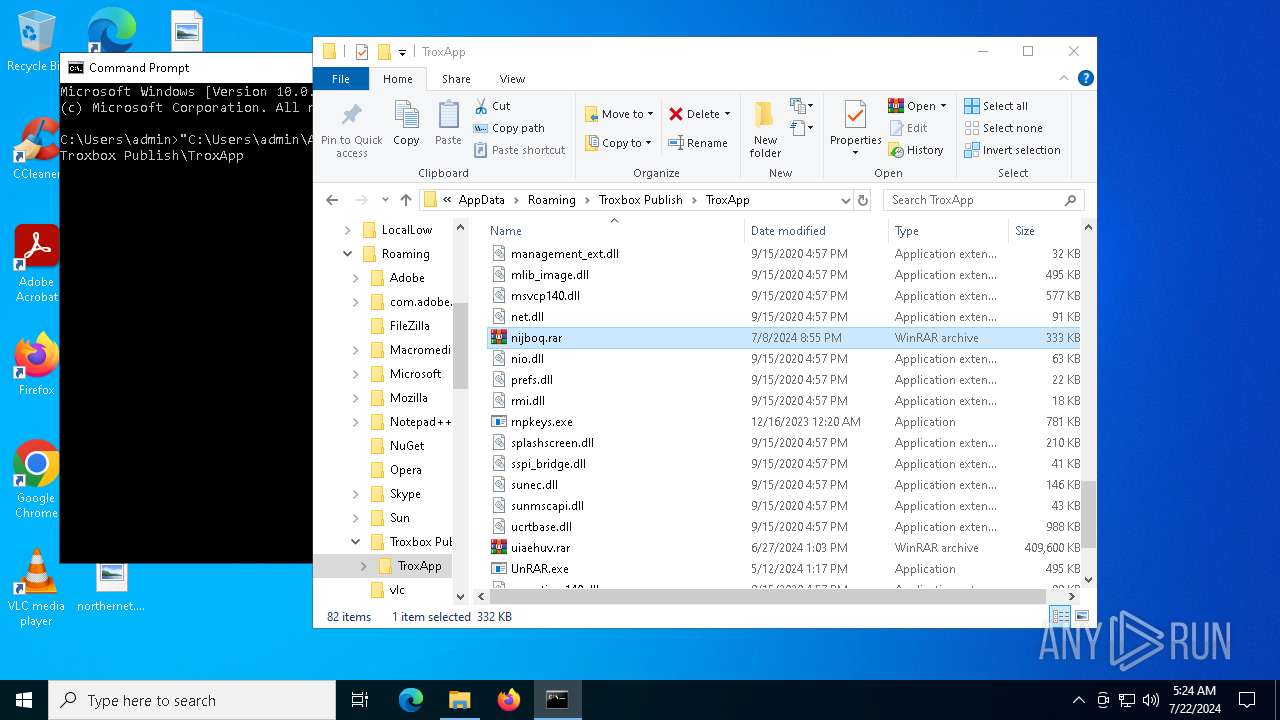
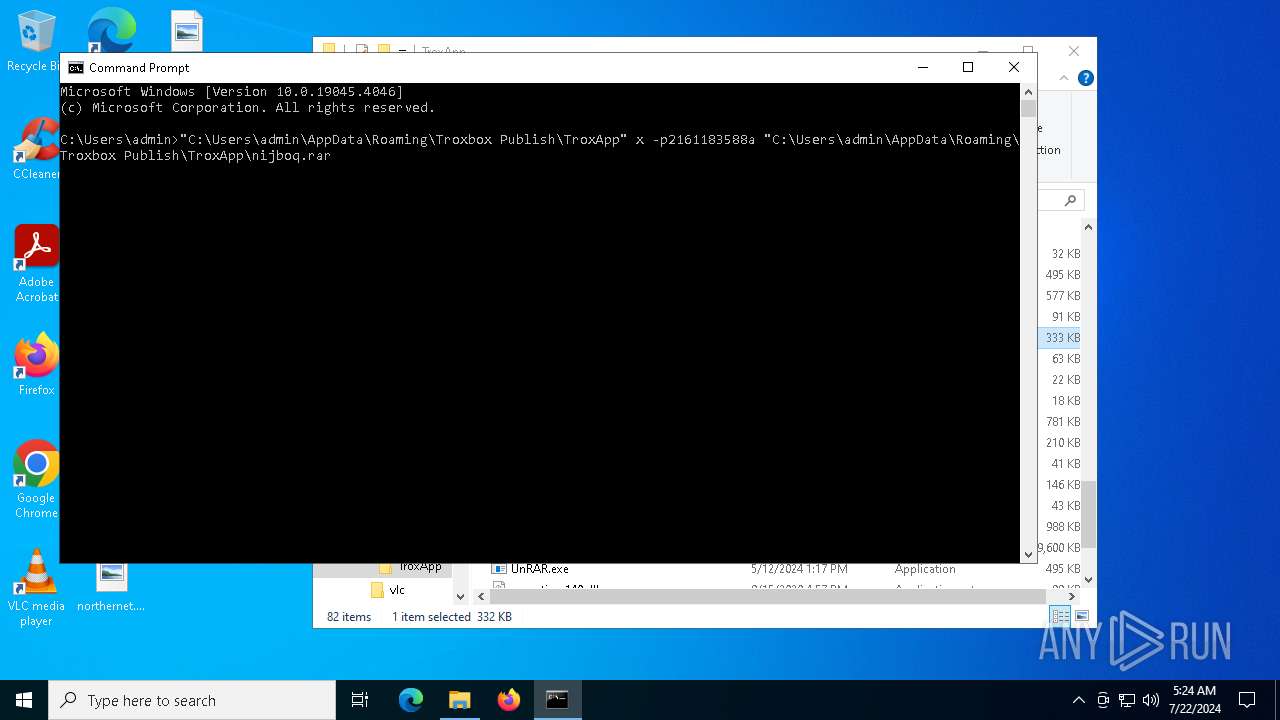
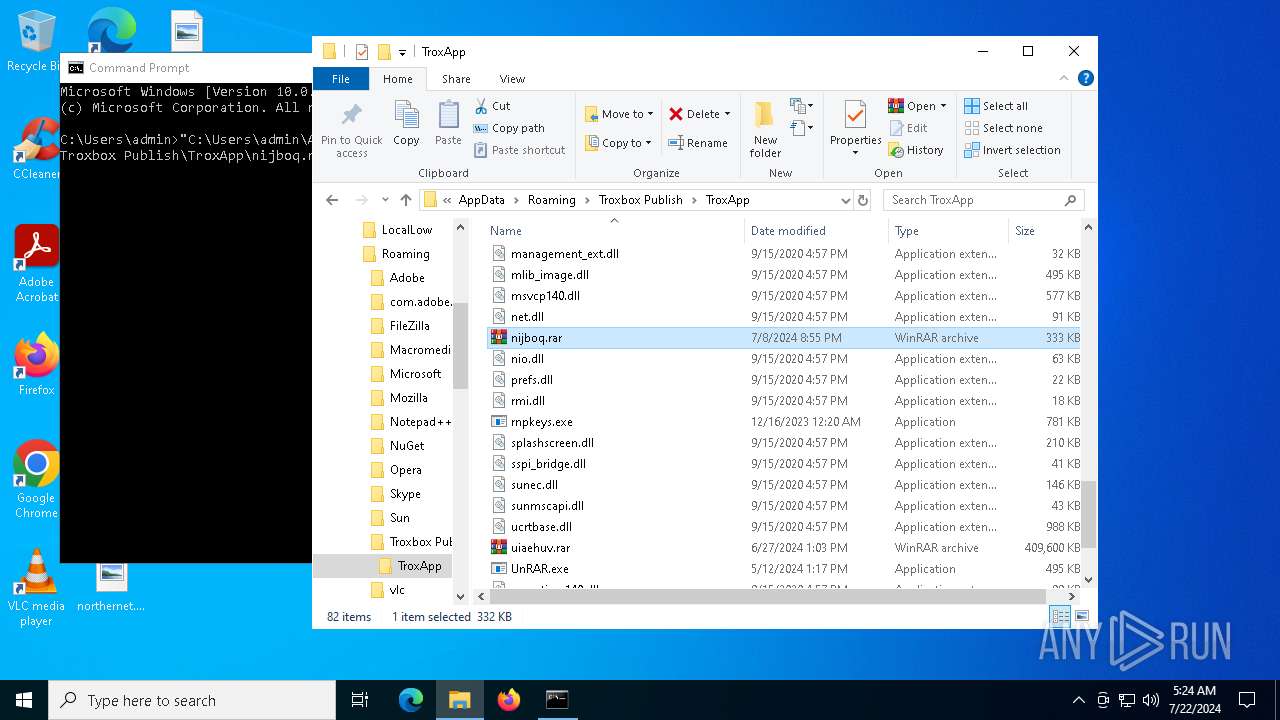
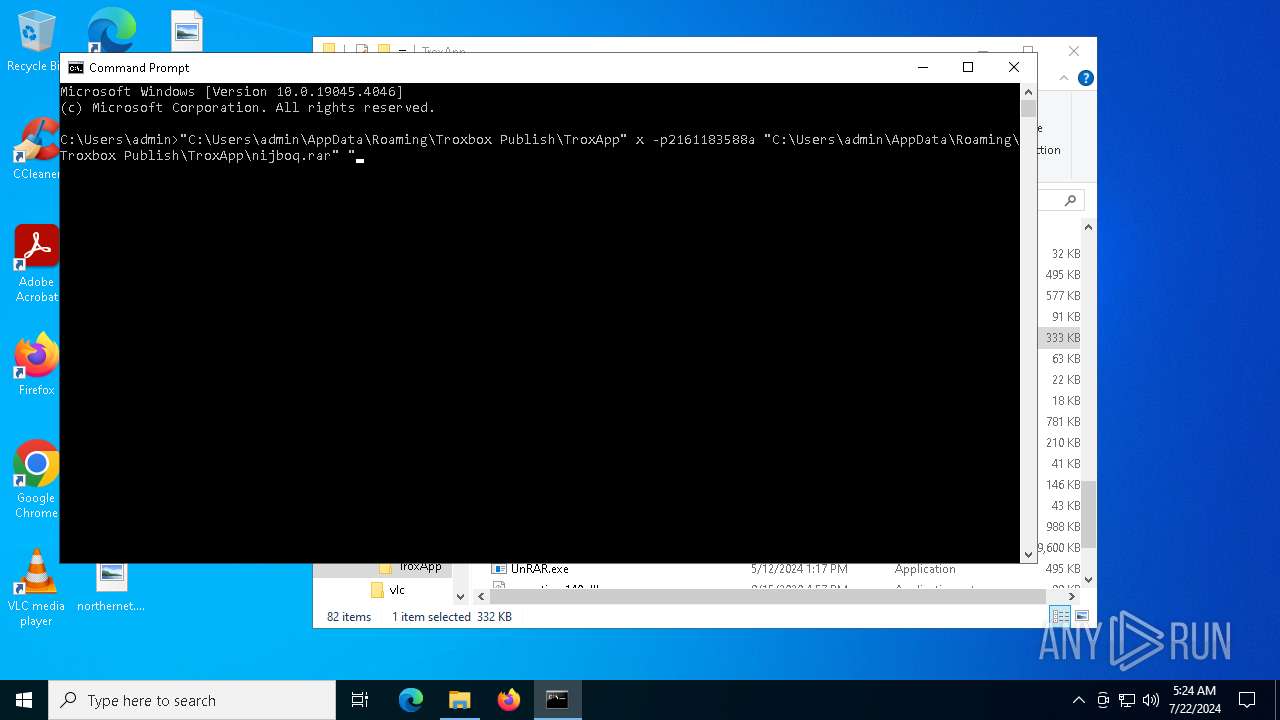
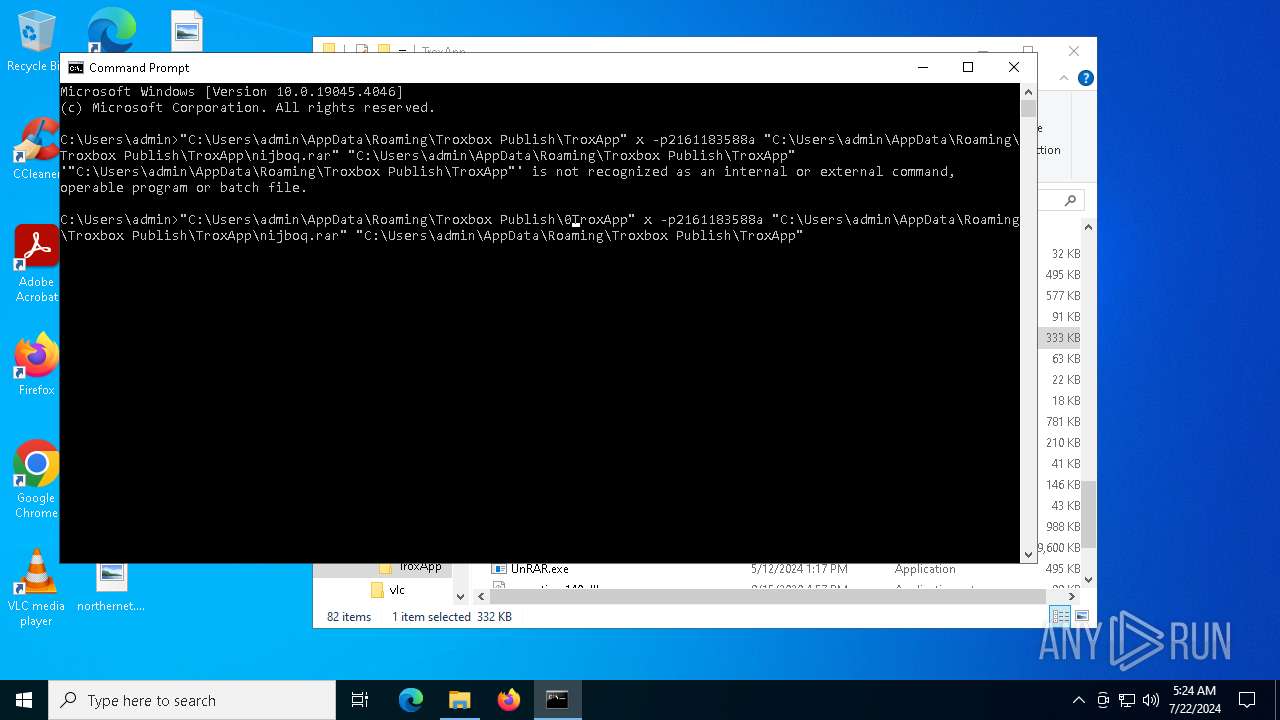
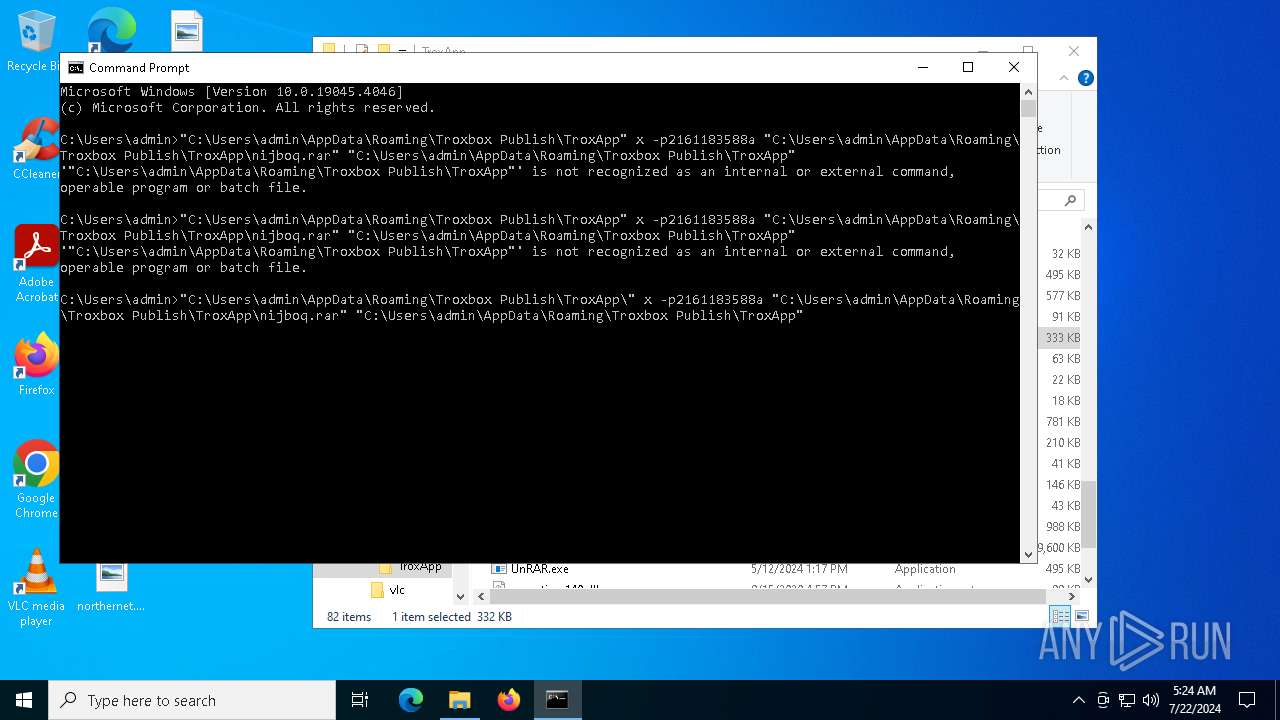
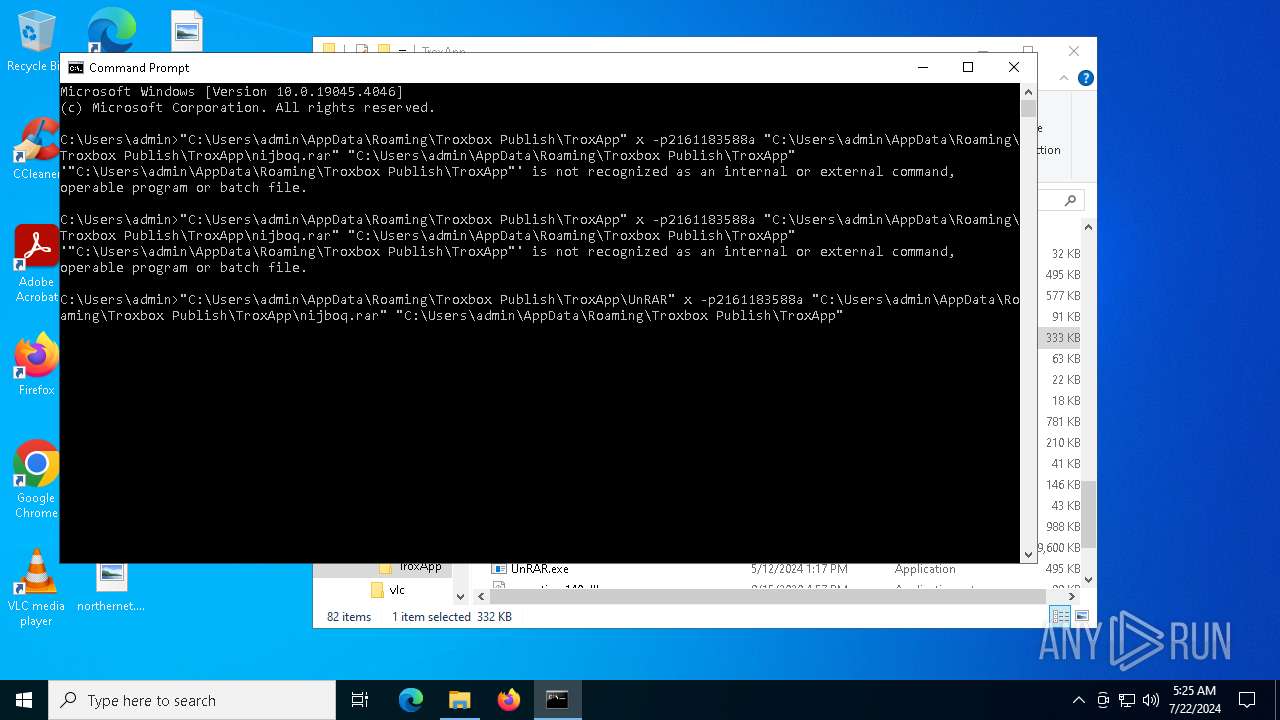
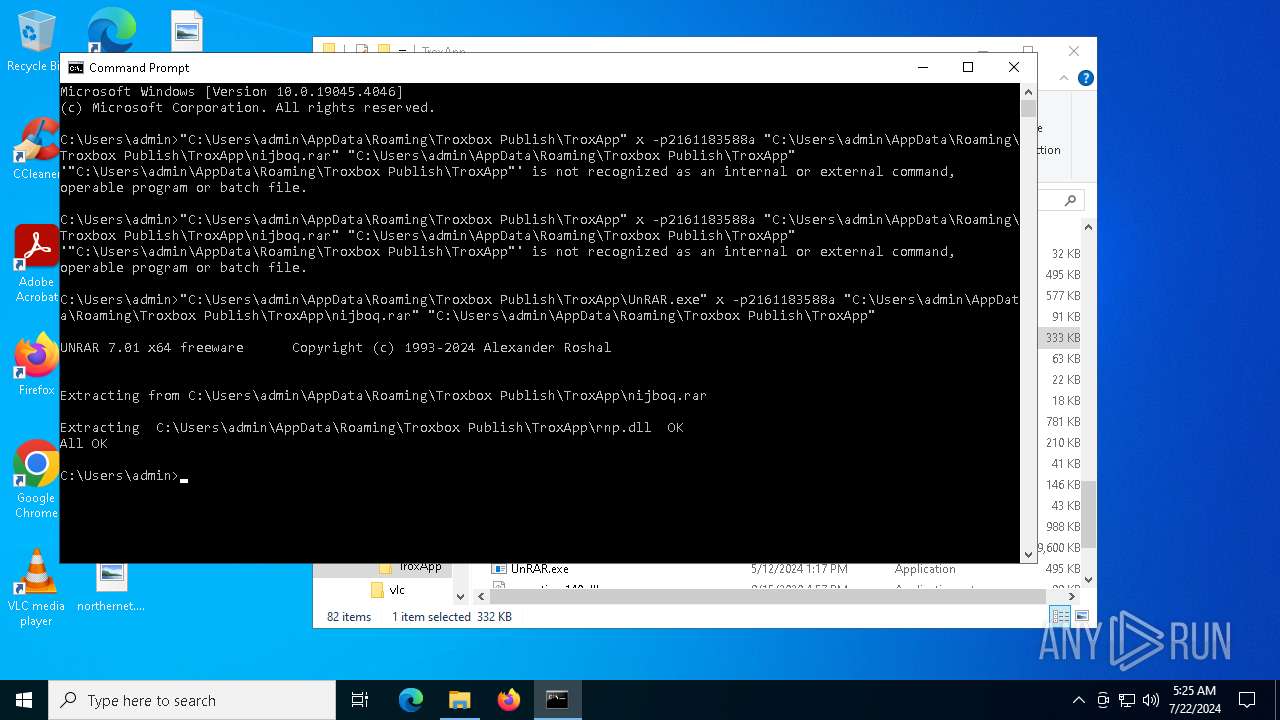
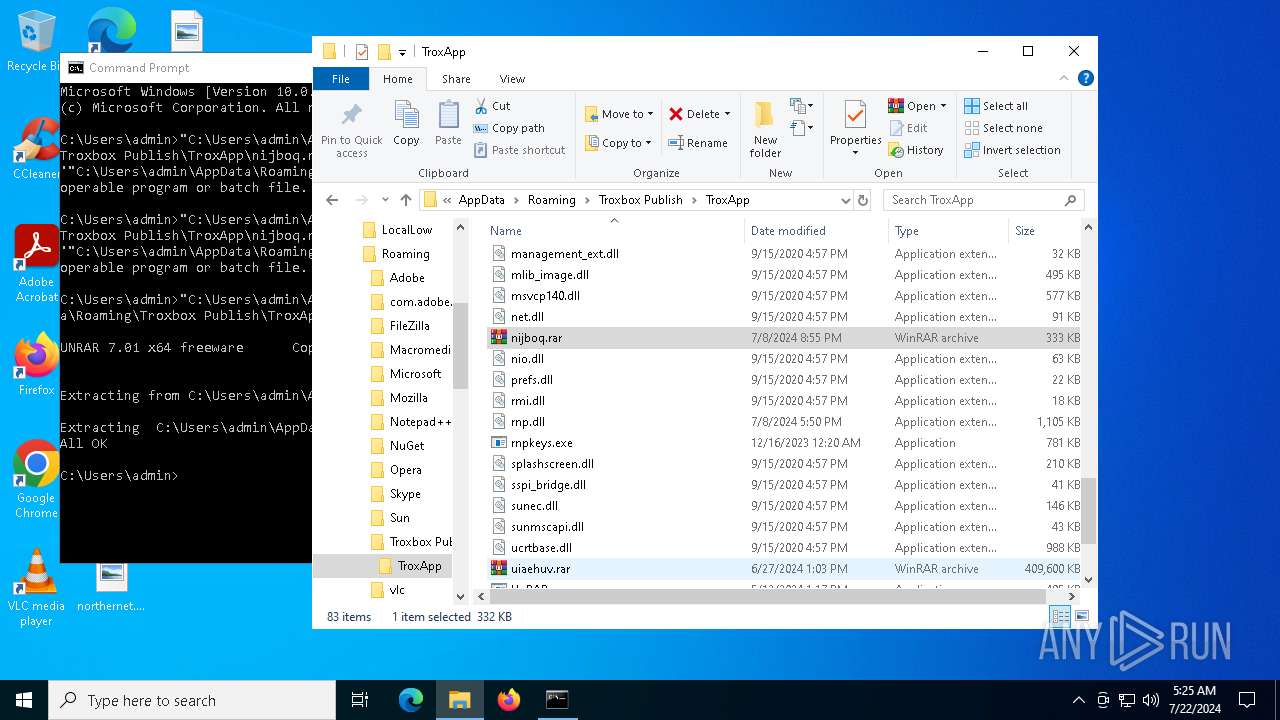
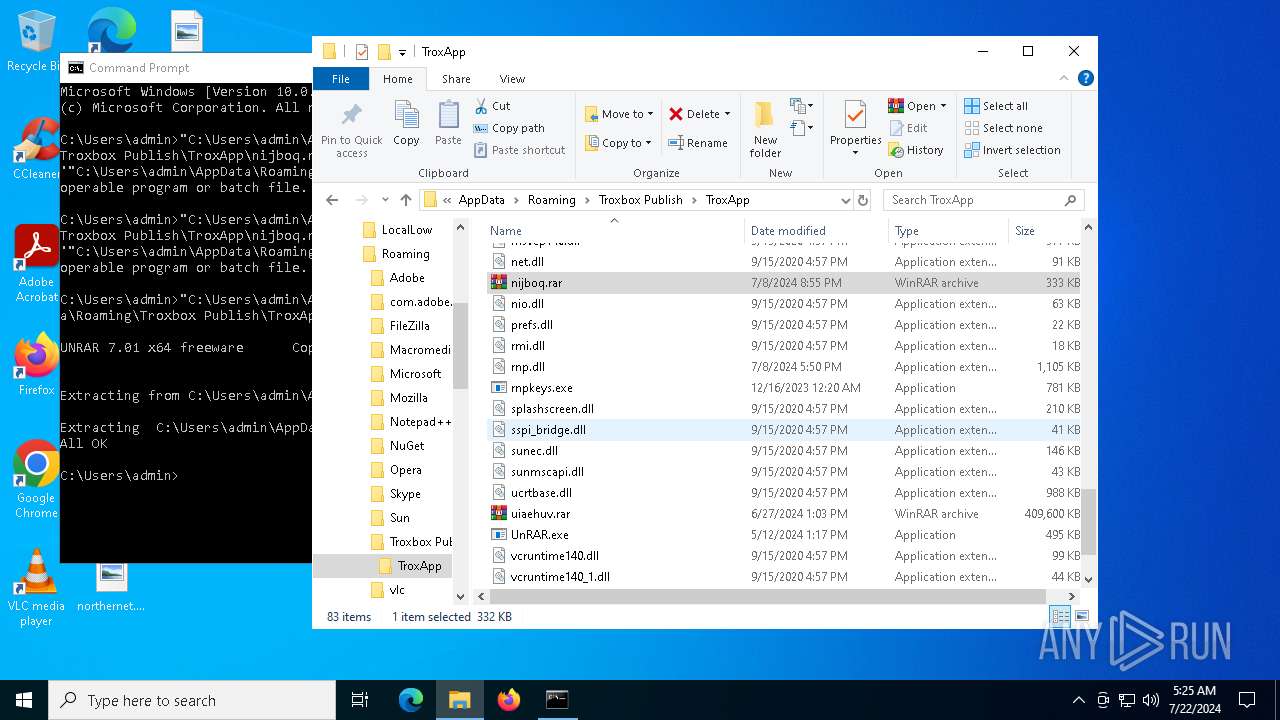
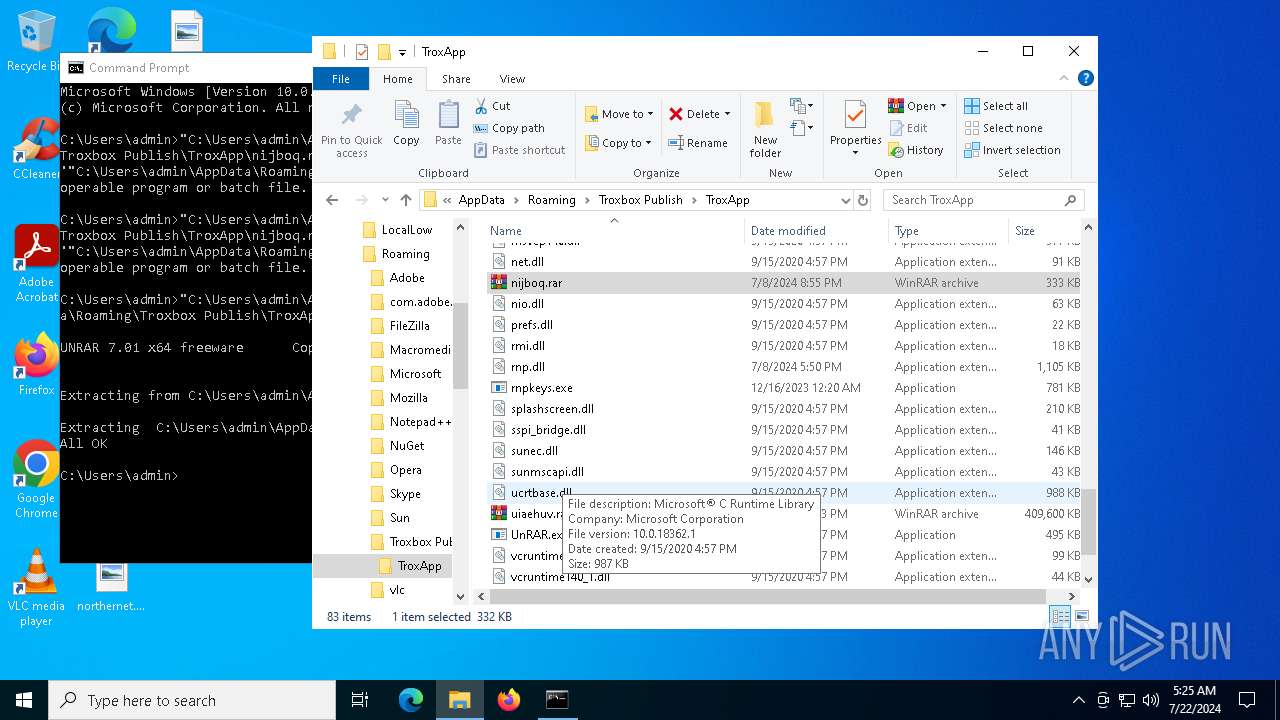
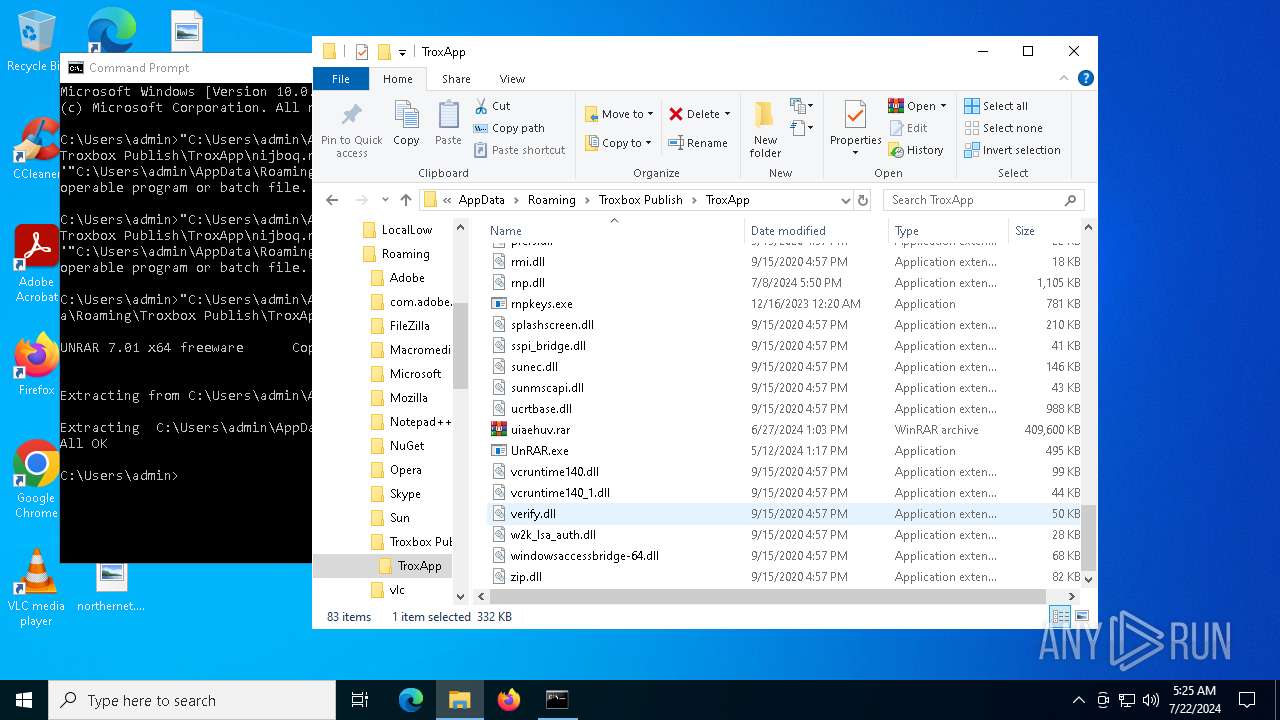
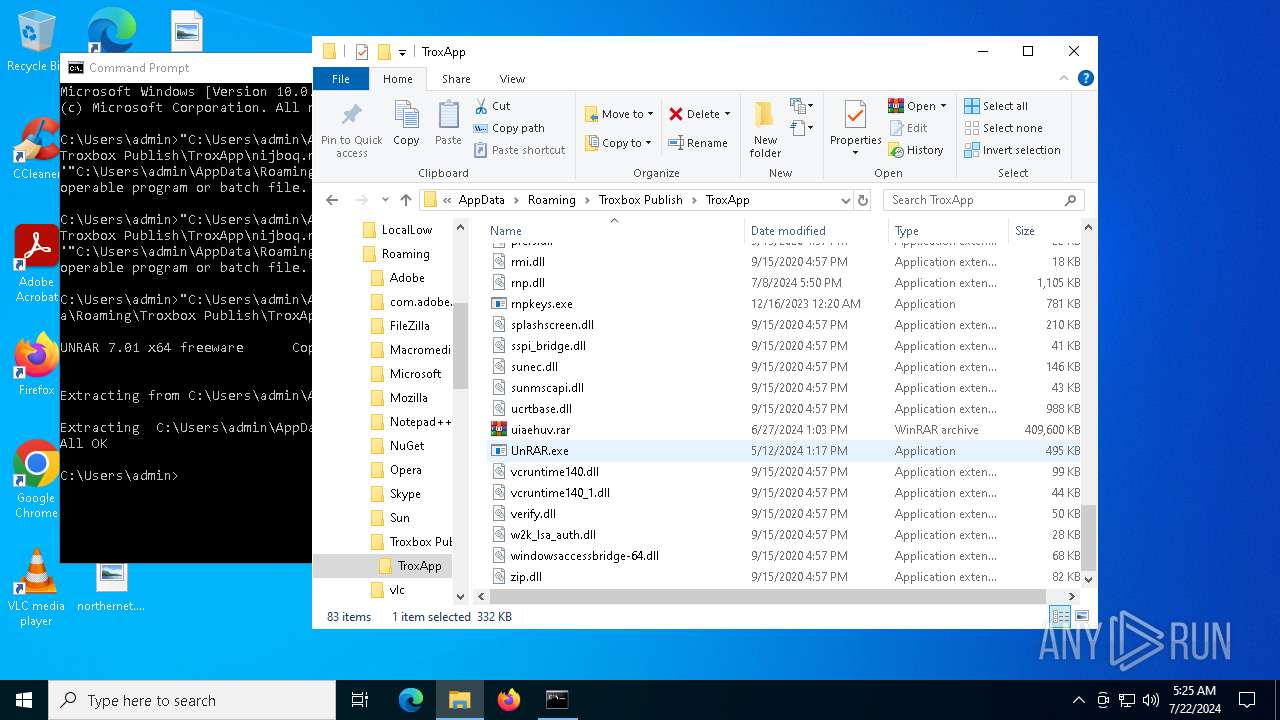
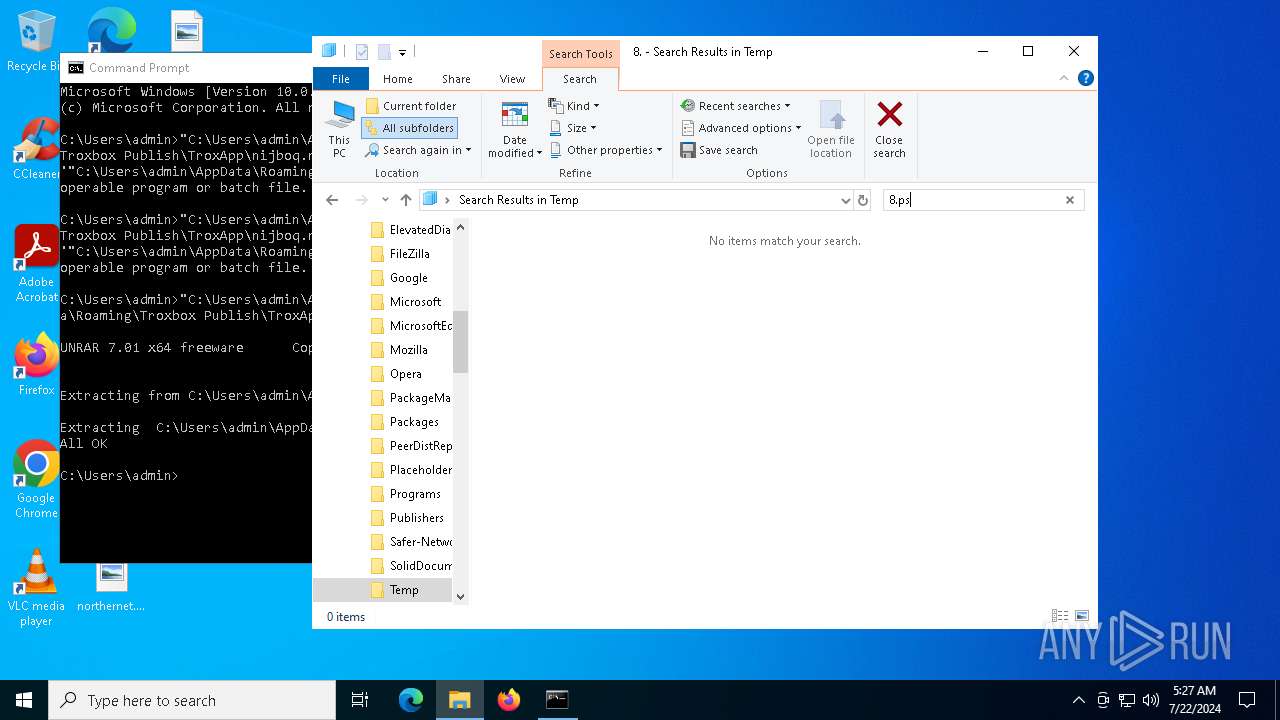
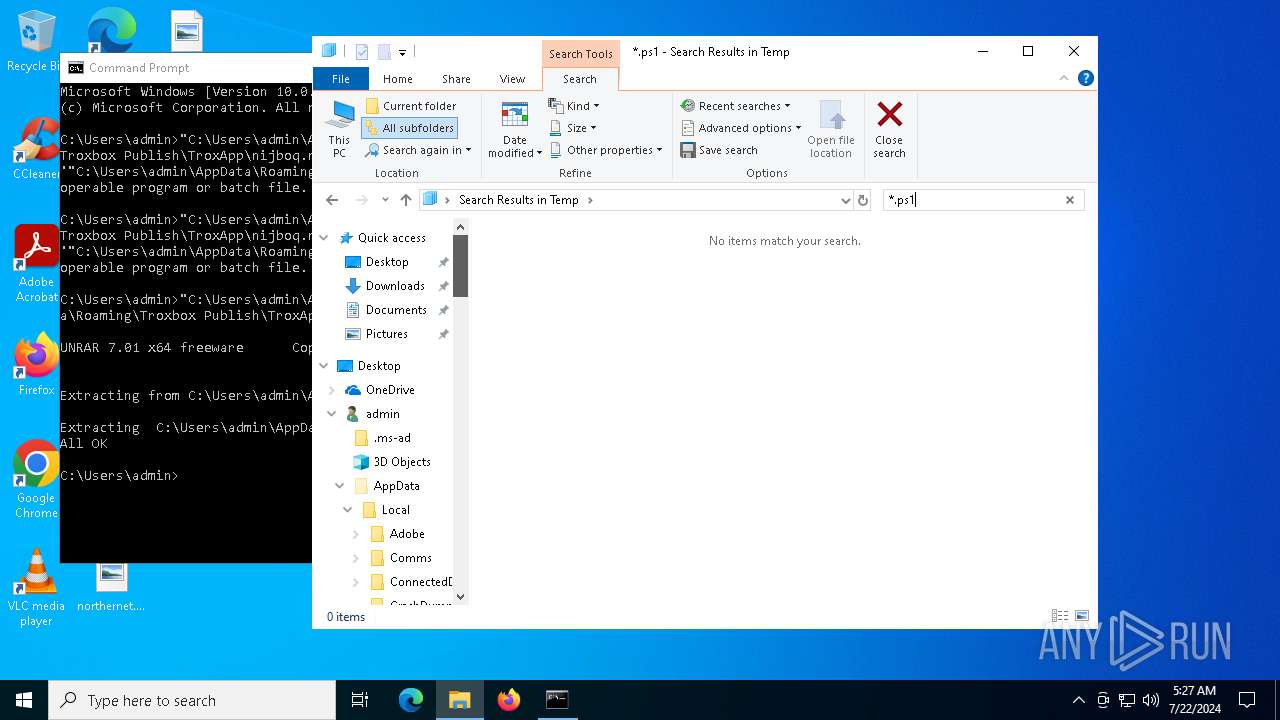
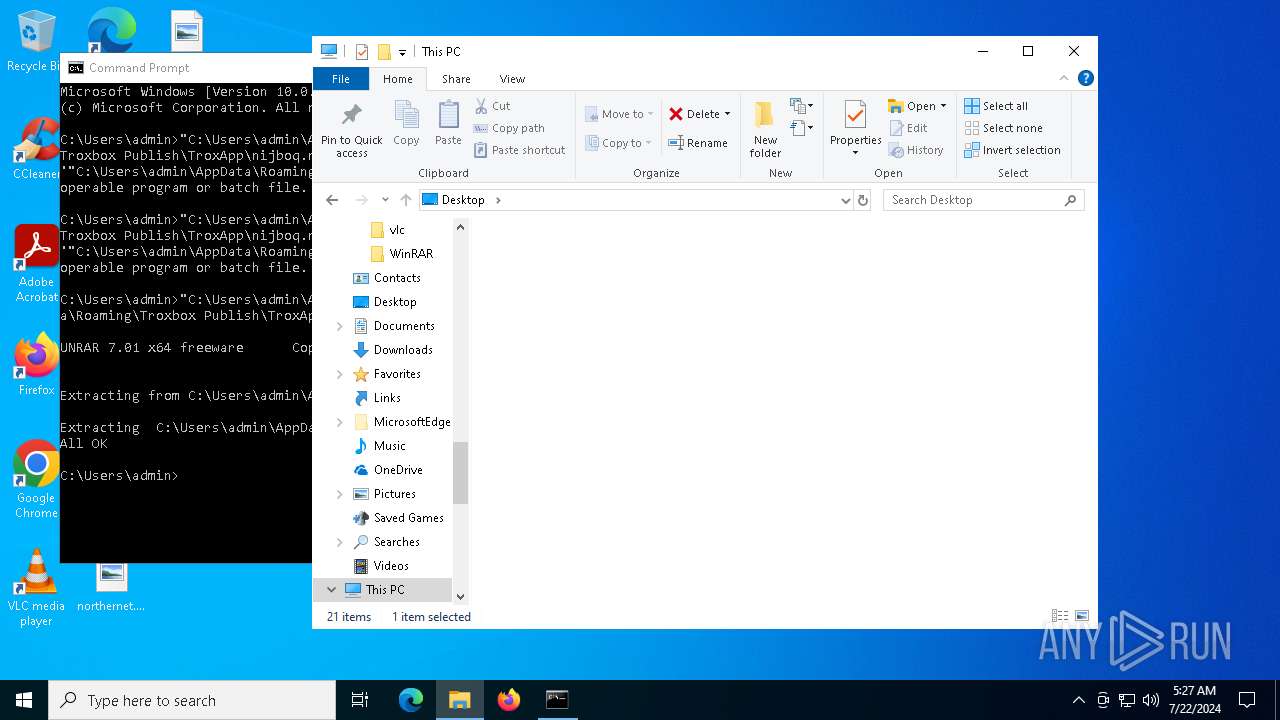
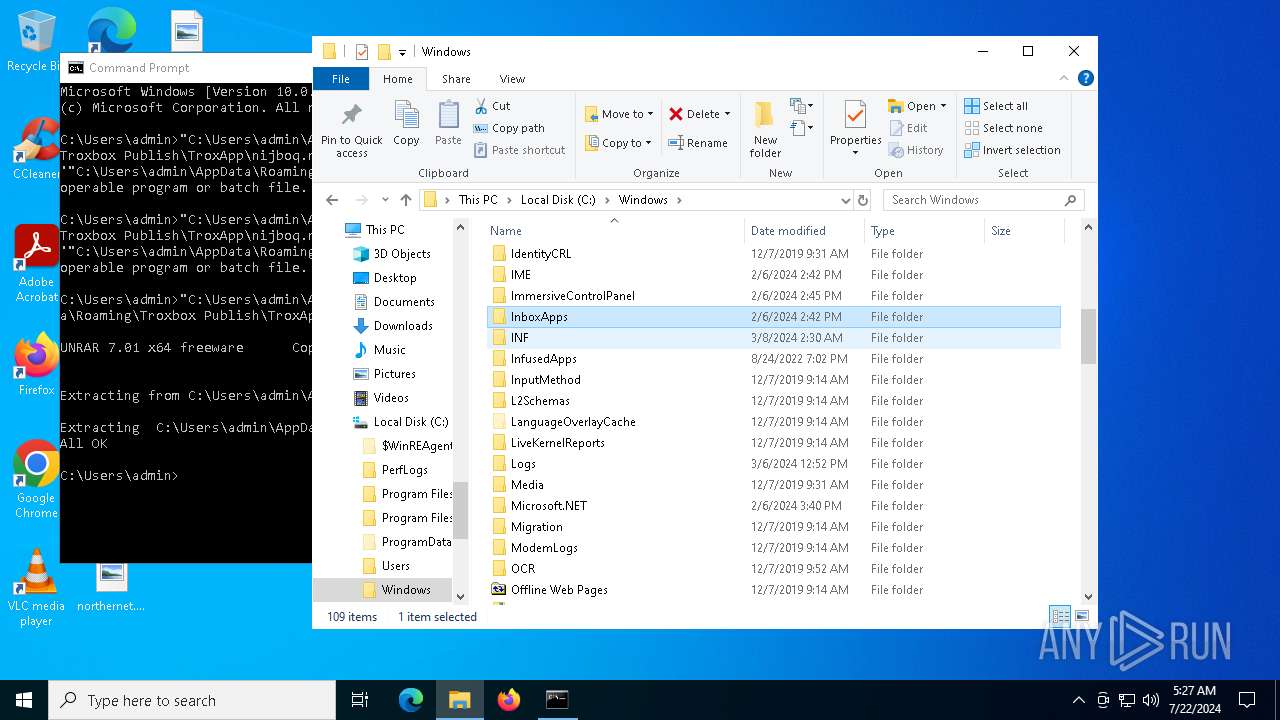
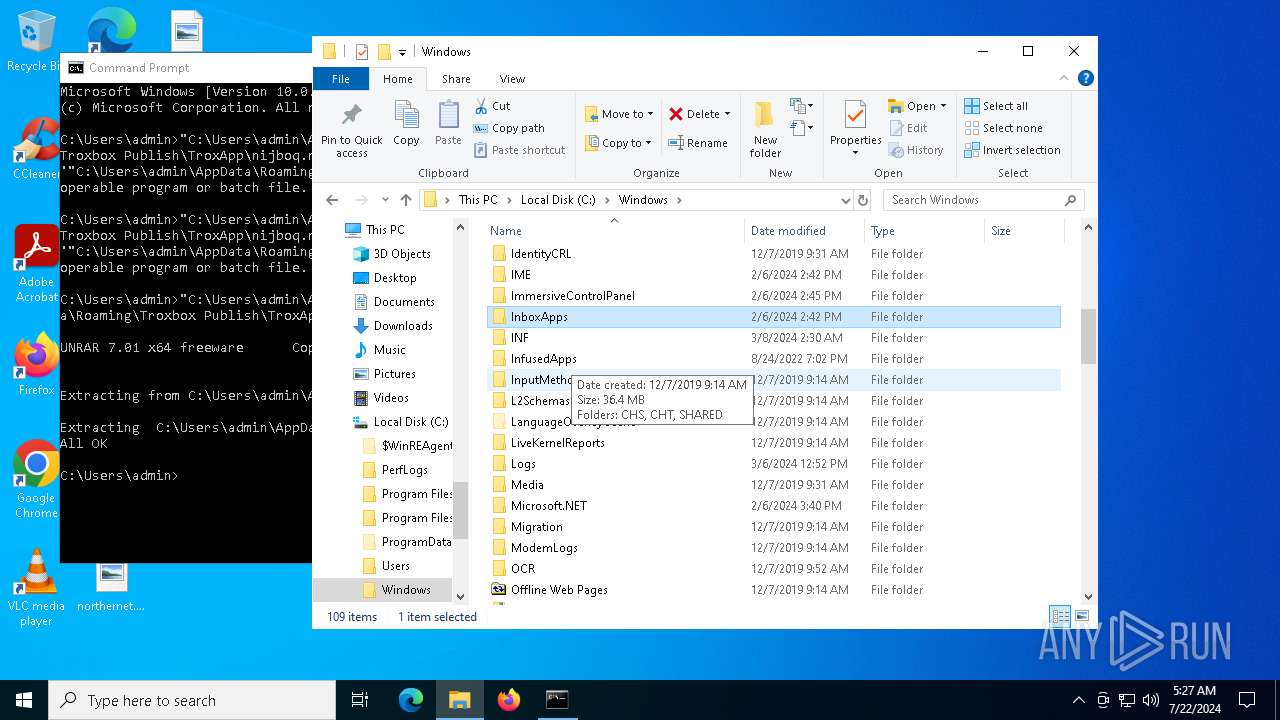
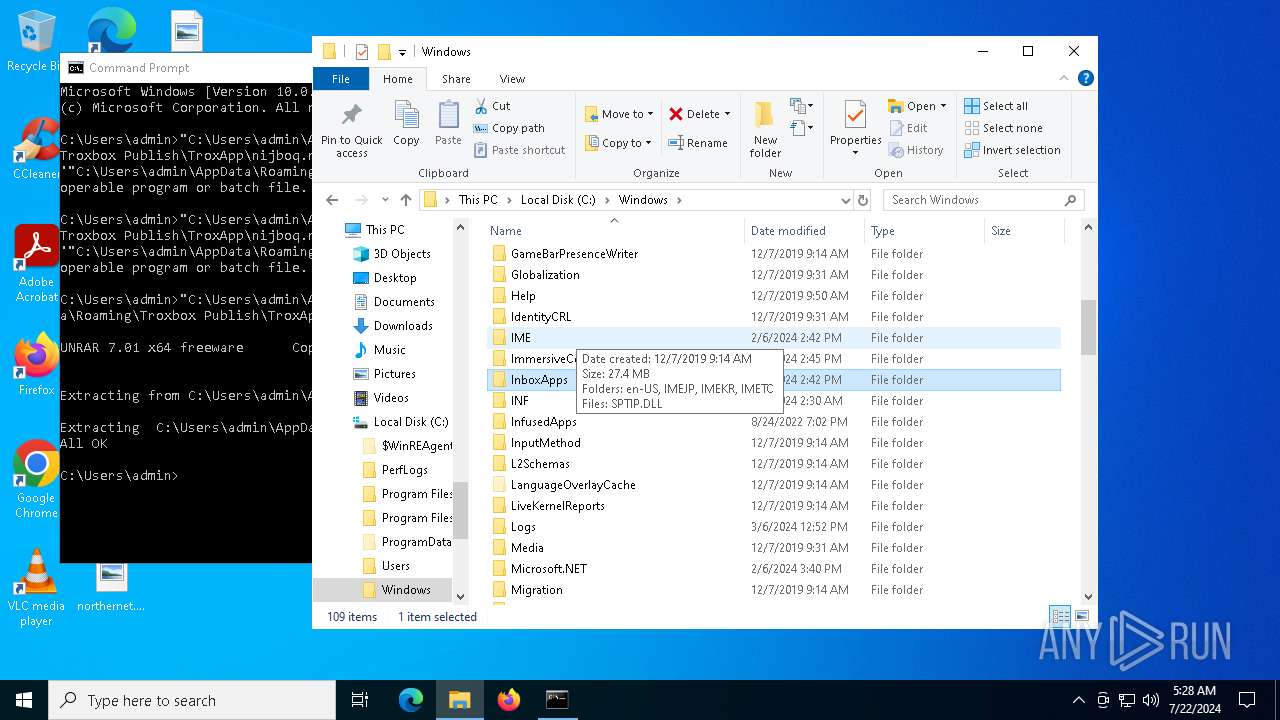
| 3920 | "C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\UnRAR.exe" x -p2161183588a "C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\nijboq.rar" "C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp" | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\UnRAR.exe | cmd.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 4228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
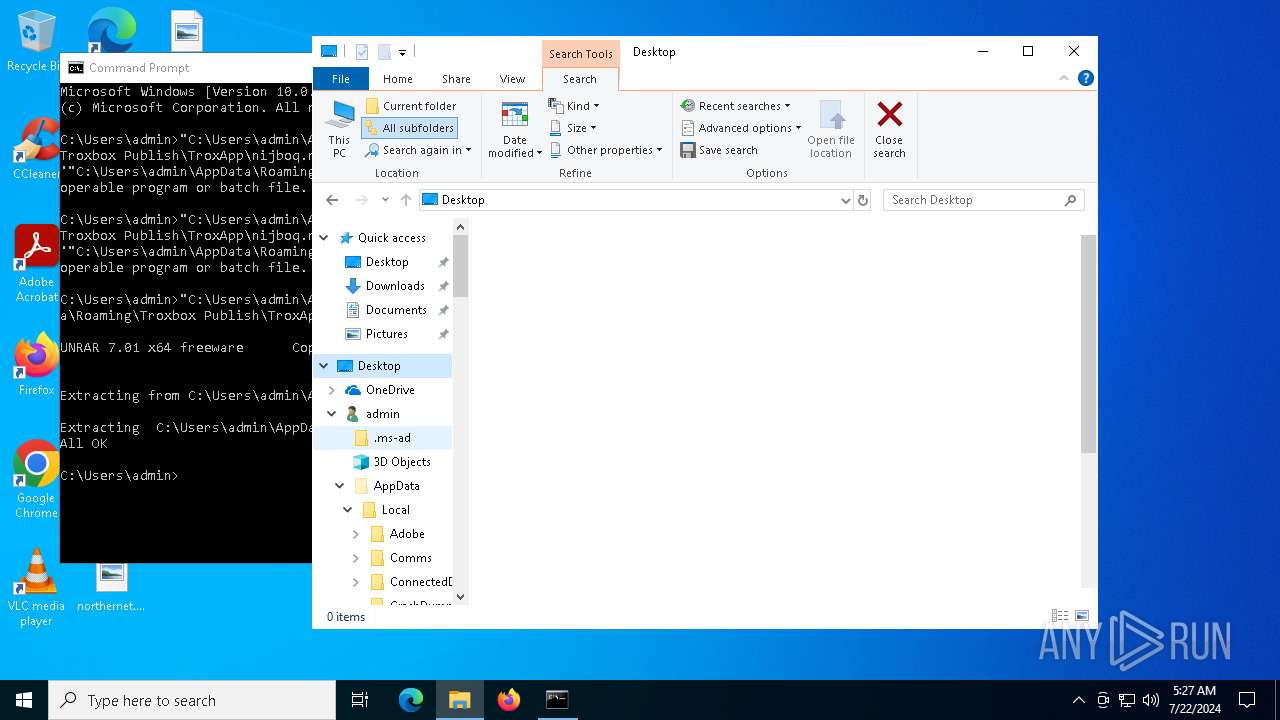
| 4504 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5724 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\5b3a41ed8a9a619b4aa18cef611c94b3273671ad464847cbfa600a6571c64431.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5748 | C:\WINDOWS\system32\WerFault.exe -u -p 7796 -s 336 | C:\Windows\System32\WerFault.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6500 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | C:\WINDOWS\system32\WerFault.exe -u -p 7796 -s 340 | C:\Windows\System32\WerFault.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7096 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 545
Read events
17 350
Write events
186
Delete events
9
Modification events
| (PID) Process: | (7096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B81B0000253C1742F7DBDA01 | |||
| (PID) Process: | (7096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: BBAC910342A7550F0AF85ECCD8B36535B6B0527E537D7E5D606B317B8D7E6737 | |||
| (PID) Process: | (7096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2344) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
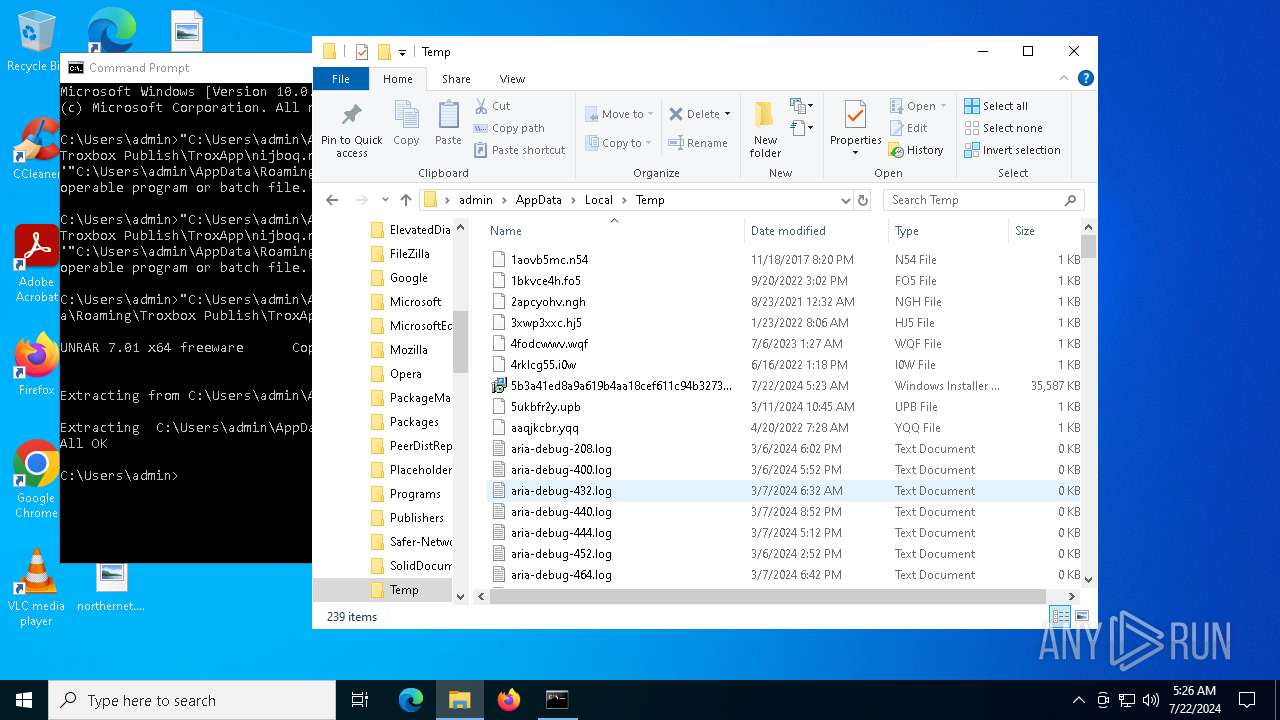
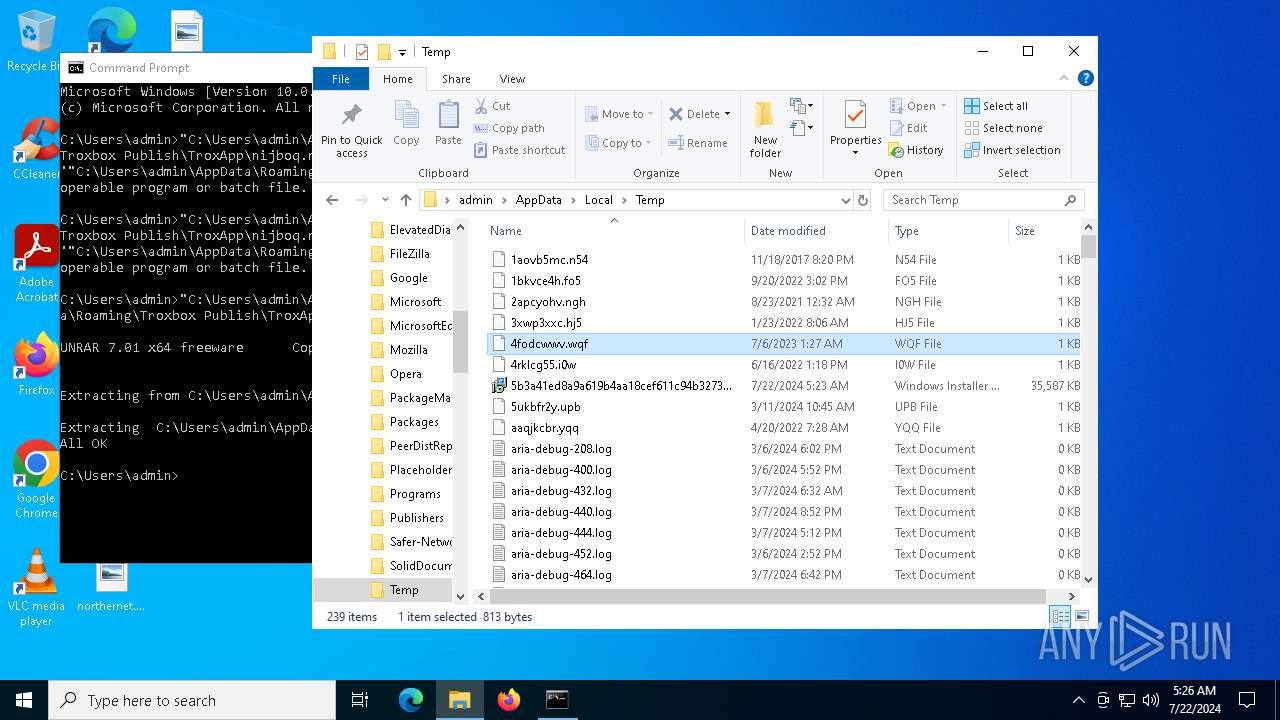
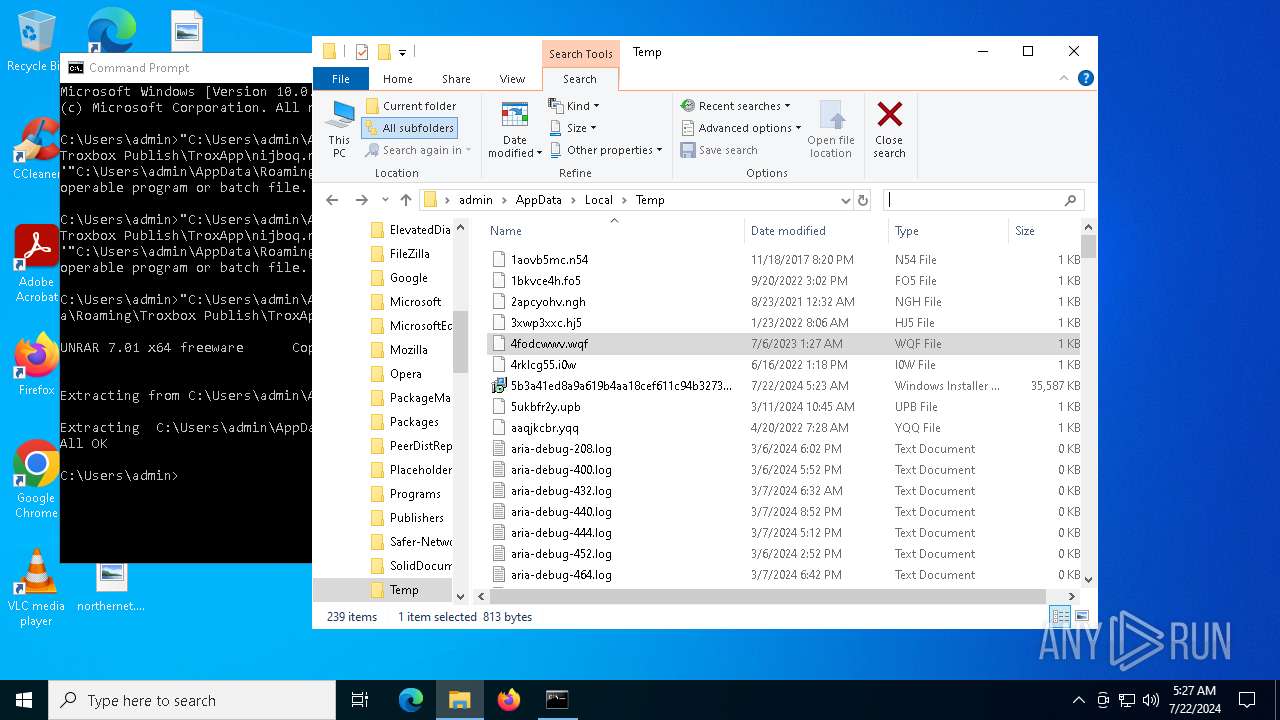
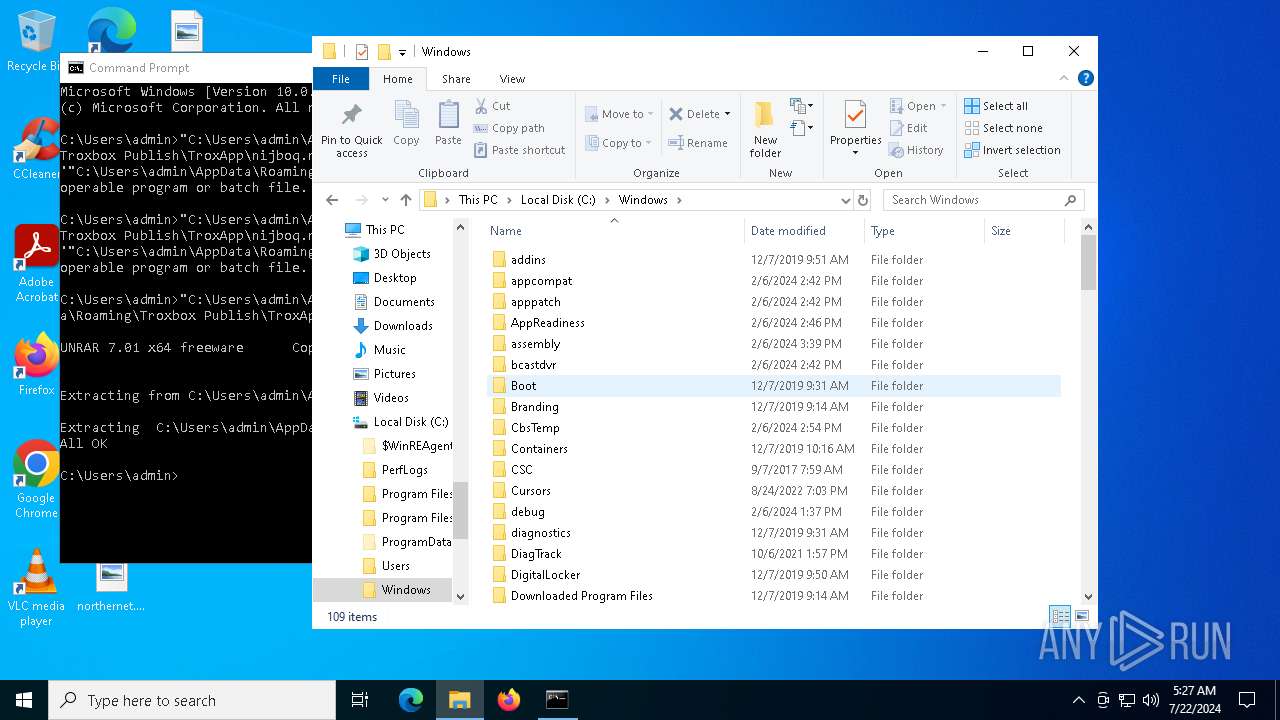
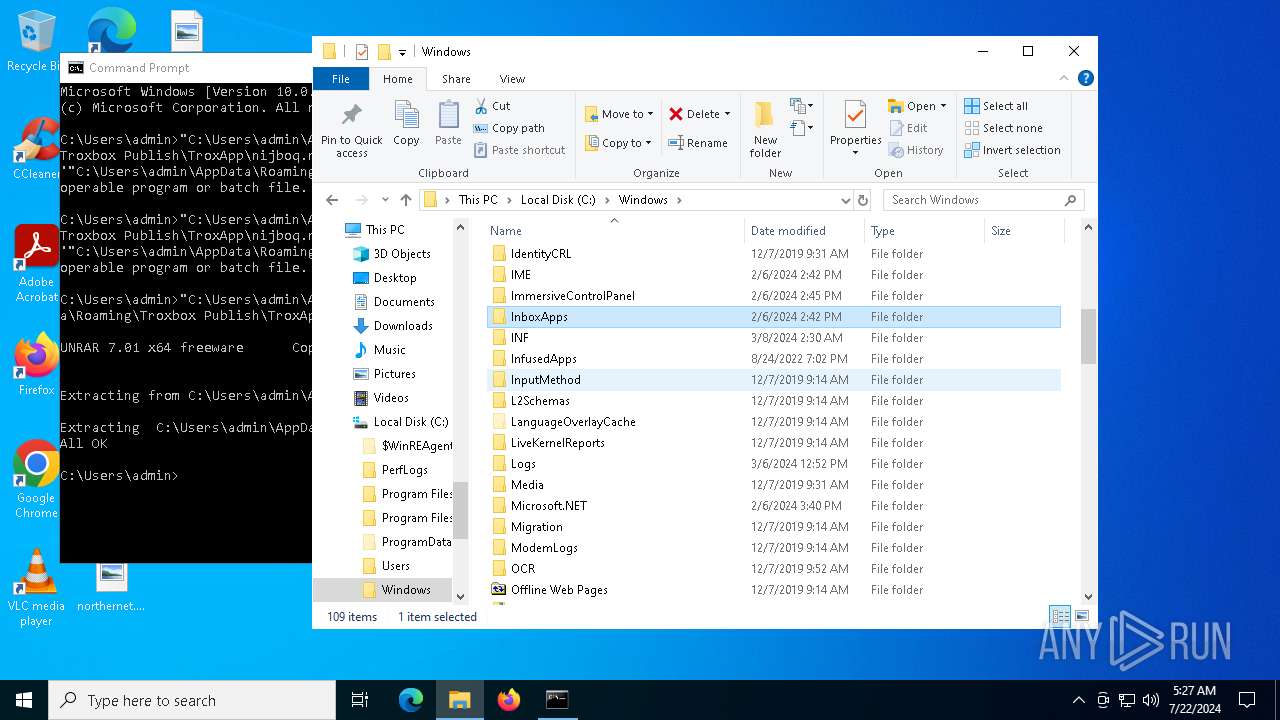
Executable files
87
Suspicious files
28
Text files
6
Unknown types
0
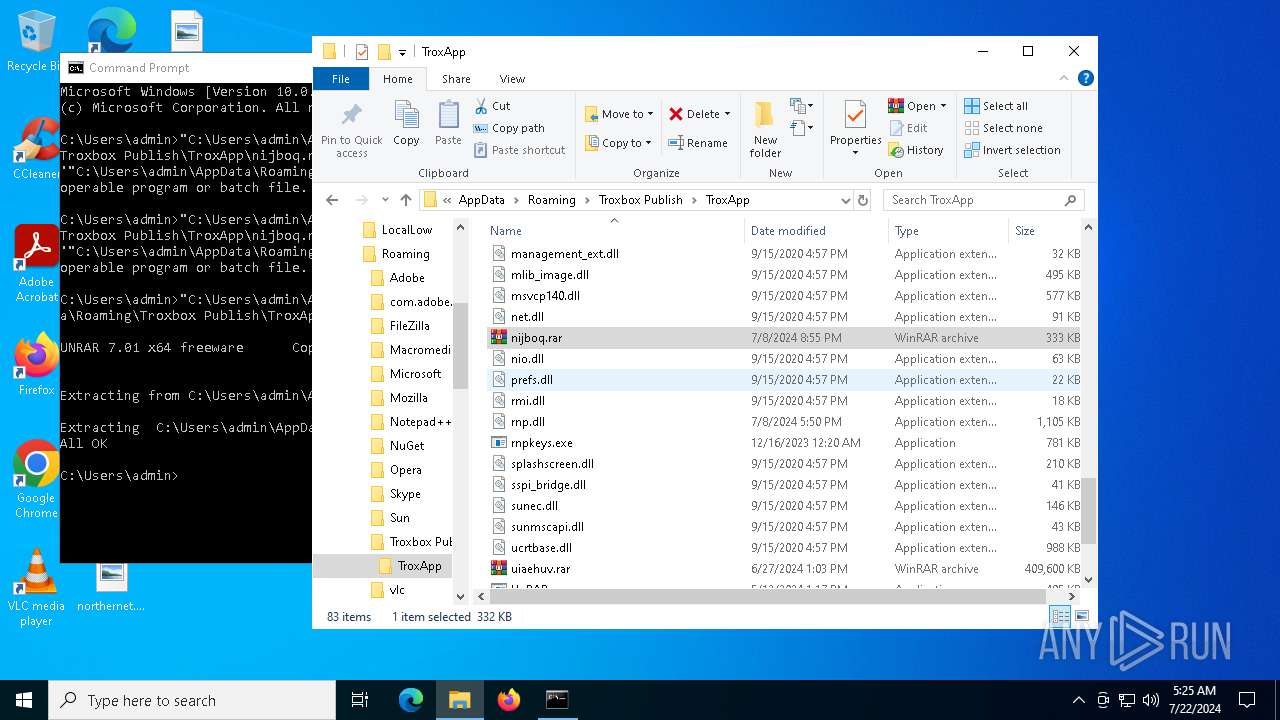
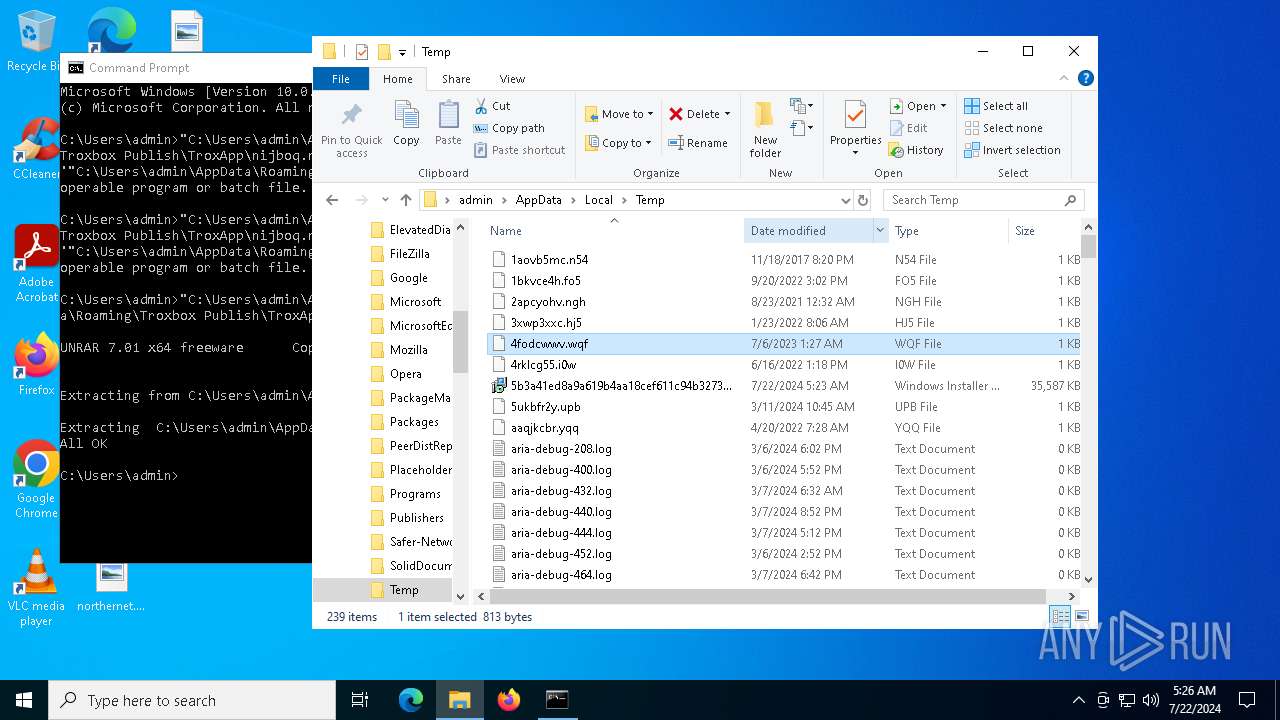
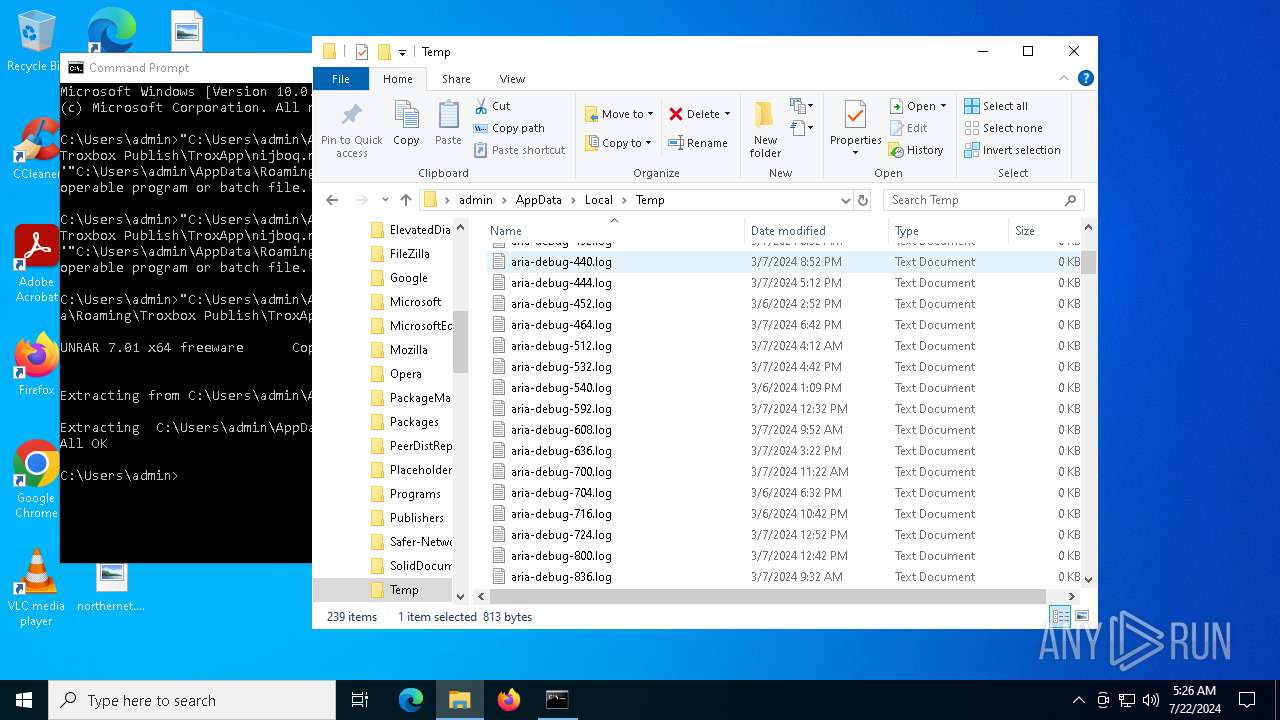
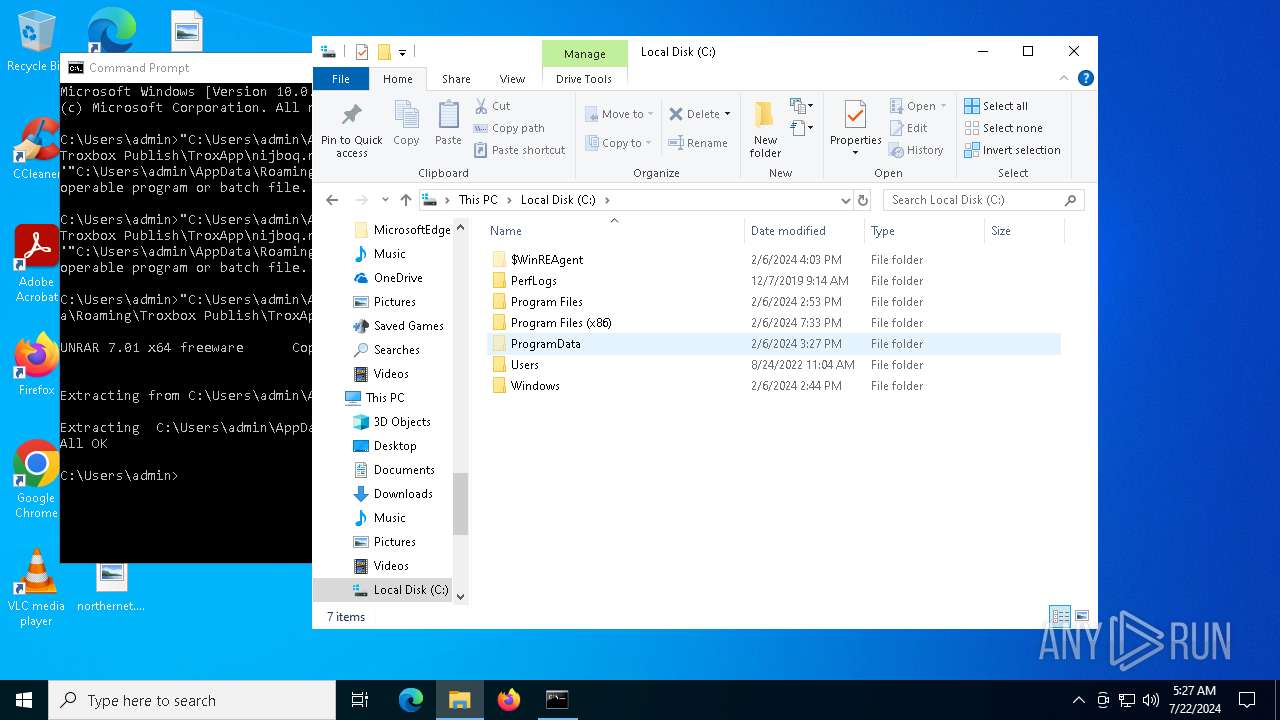
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7096 | msiexec.exe | C:\WINDOWS\Installer\42b18c.msi | — | |
MD5:— | SHA256:— | |||
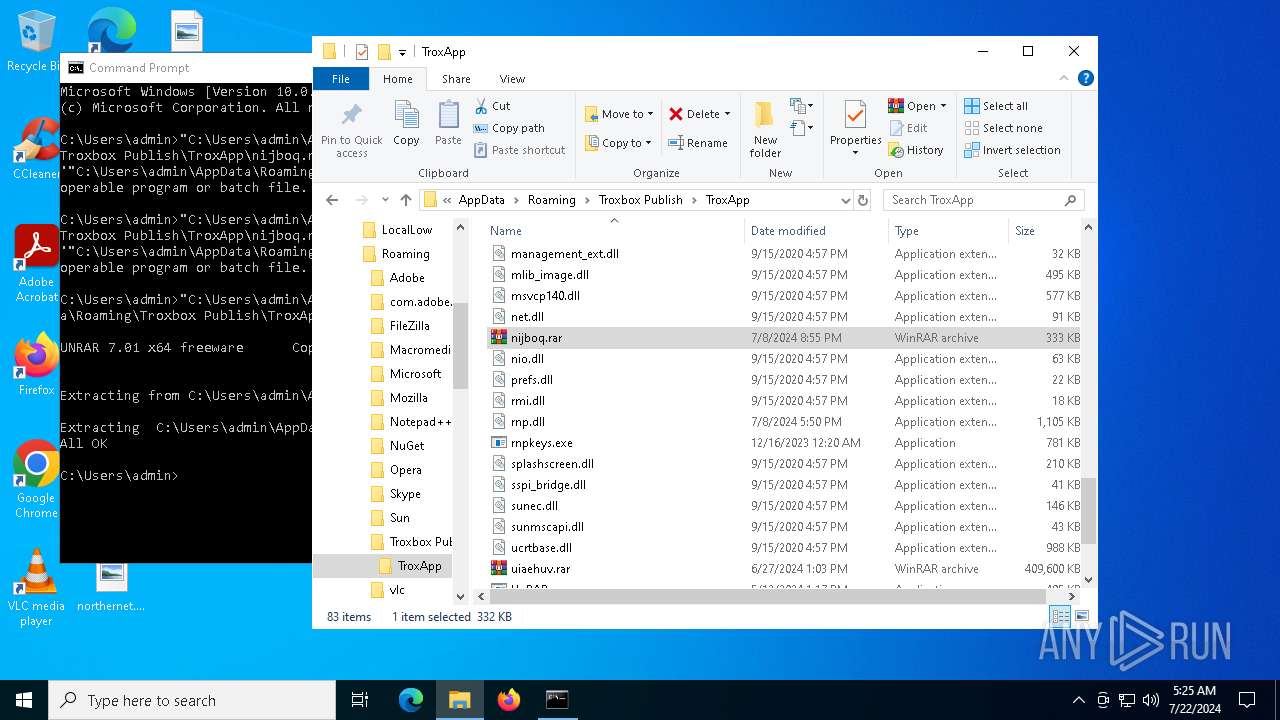
| 7096 | msiexec.exe | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\uiaehuv.rar | — | |
MD5:— | SHA256:— | |||
| 7096 | msiexec.exe | C:\WINDOWS\Installer\MSIC0E5.tmp | executable | |
MD5:54D74546C6AFE67B3D118C3C477C159A | SHA256:F9956417AF079E428631A6C921B79716D960C3B4917C6B7D17FF3CB945F18611 | |||
| 2344 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:7FB5FA1534DCF77F2125B2403B30A0EE | SHA256:33A39E9EC2133230533A686EC43760026E014A3828C703707ACBC150FE40FD6F | |||
| 7096 | msiexec.exe | C:\WINDOWS\Installer\MSIB47B.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 2344 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:D80472482352494FCA82BBC87E6CE596 | SHA256:AC89414D32B9CB1E3733411C17345BE451C012B420D023823DF7D3BE125A3493 | |||
| 7096 | msiexec.exe | C:\WINDOWS\Installer\MSIC73F.tmp | binary | |
MD5:B69B2B26F1C5983E87BBD572E80C4B35 | SHA256:5215EF020FF15CCFE972958B420039BF50F5FD9D8D3CAE16E752E904C6F898B5 | |||
| 7096 | msiexec.exe | C:\WINDOWS\Installer\MSIC057.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 7096 | msiexec.exe | C:\WINDOWS\TEMP\~DF2E950F73EC01B10F.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 2344 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:A22AD22CFDF7D5725296DEC21D0131F9 | SHA256:738501287EDFC640DEC125EB7138467158AC9DF411FF6EF01A5E84145136A239 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
43
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2344 | msiexec.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2344 | msiexec.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
5628 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.209.33.156:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2344 | msiexec.exe | 188.114.96.3:443 | get-license2.com | CLOUDFLARENET | NL | unknown |
2344 | msiexec.exe | 142.250.186.35:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
get-license2.com |
| unknown |
c.pki.goog |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |