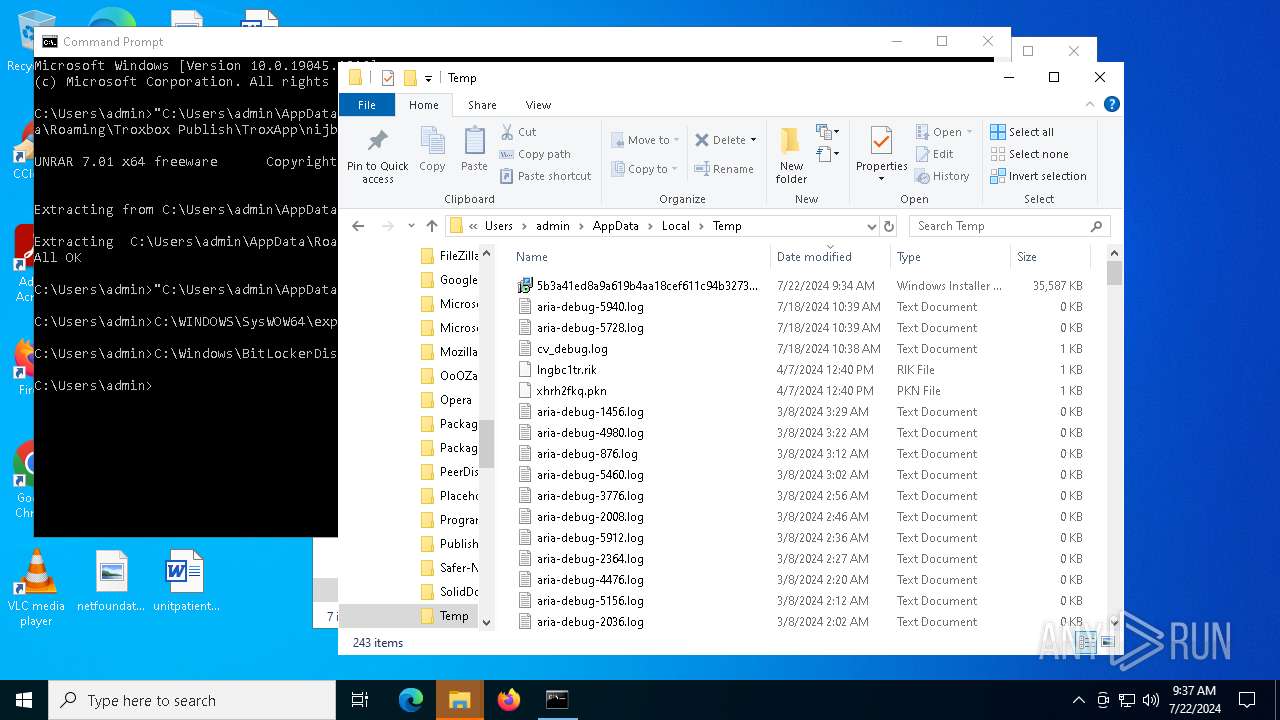
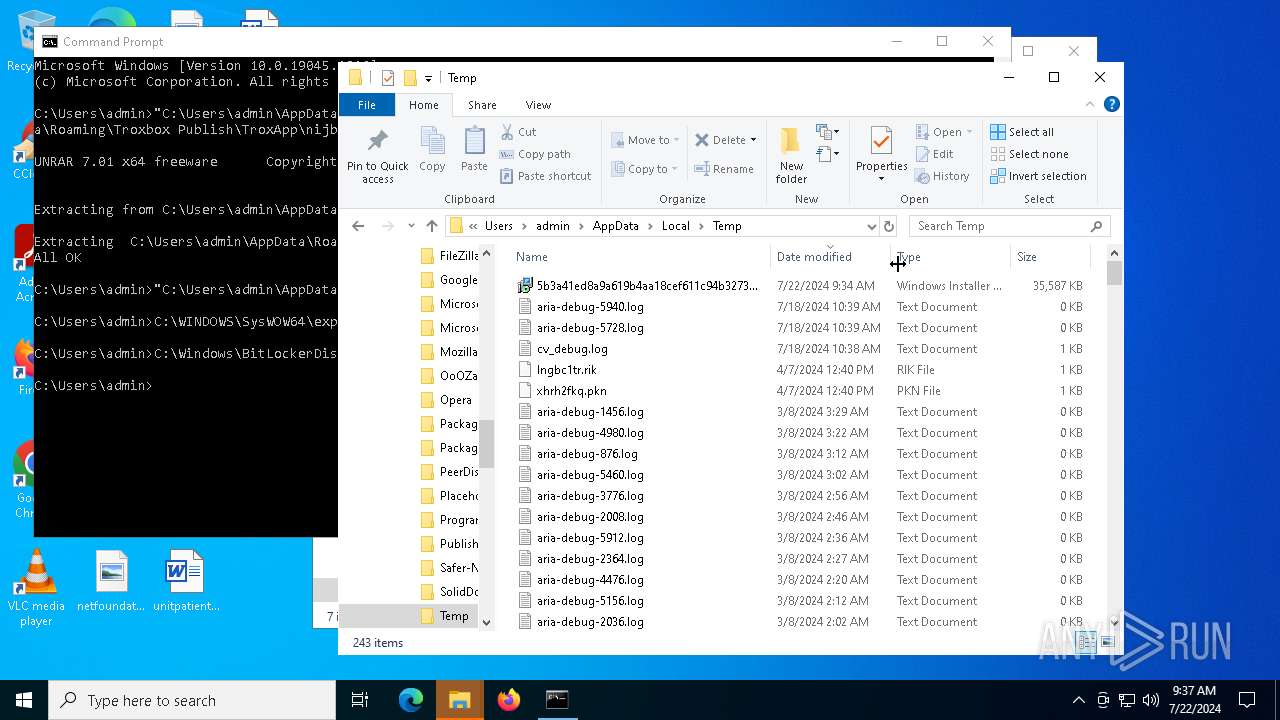
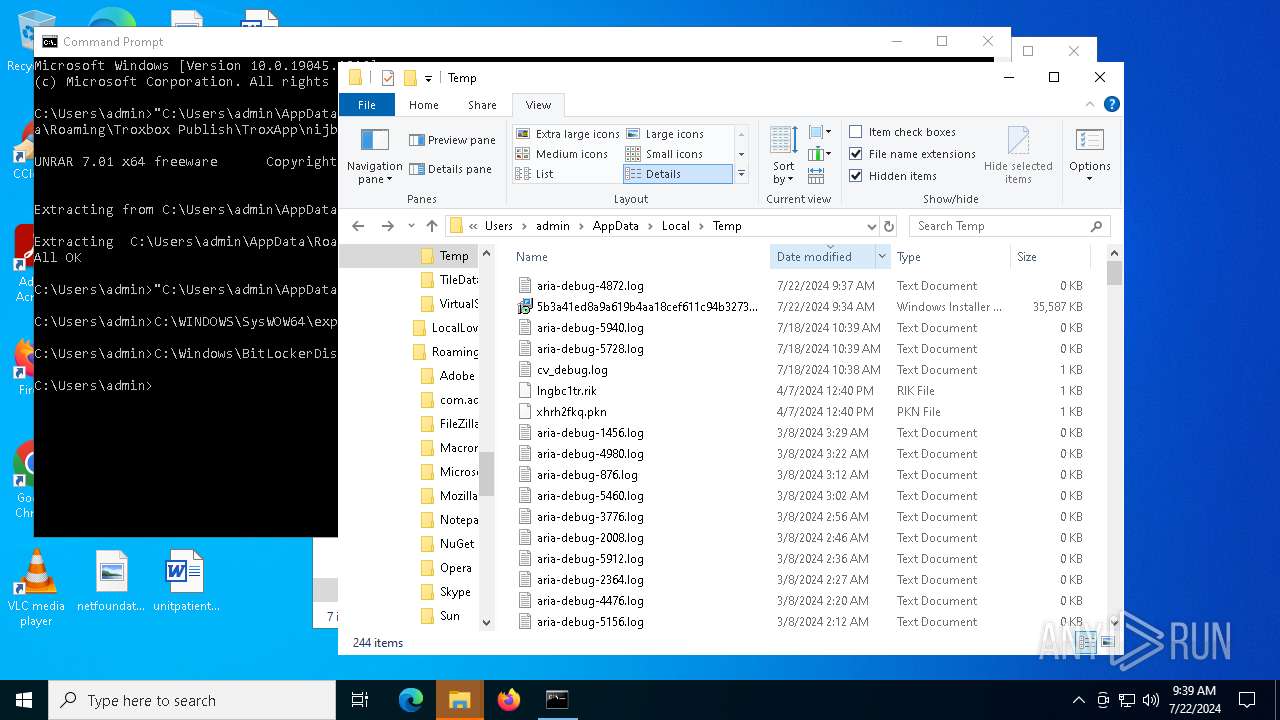
| File name: | 5b3a41ed8a9a619b4aa18cef611c94b3273671ad464847cbfa600a6571c64431.msi |
| Full analysis: | https://app.any.run/tasks/50064cfa-407c-42c6-a749-ea4c3f5ca2dd |
| Verdict: | Malicious activity |
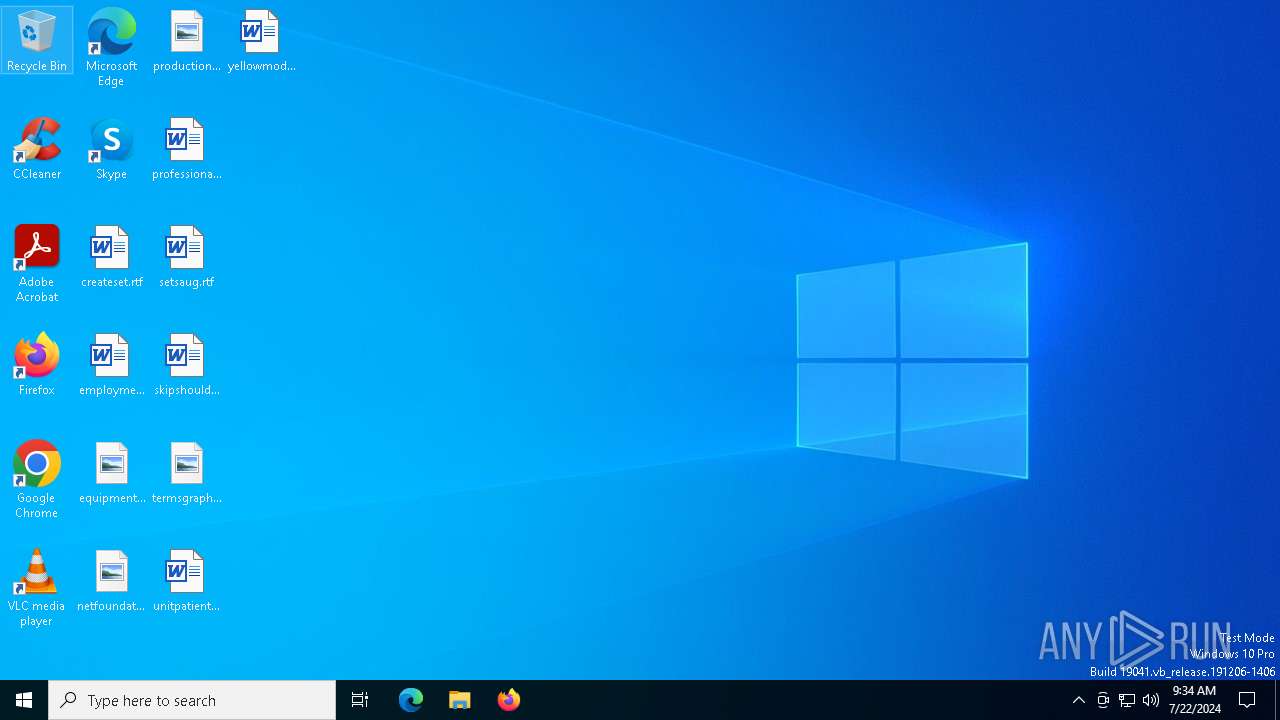
| Analysis date: | July 22, 2024, 09:34:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
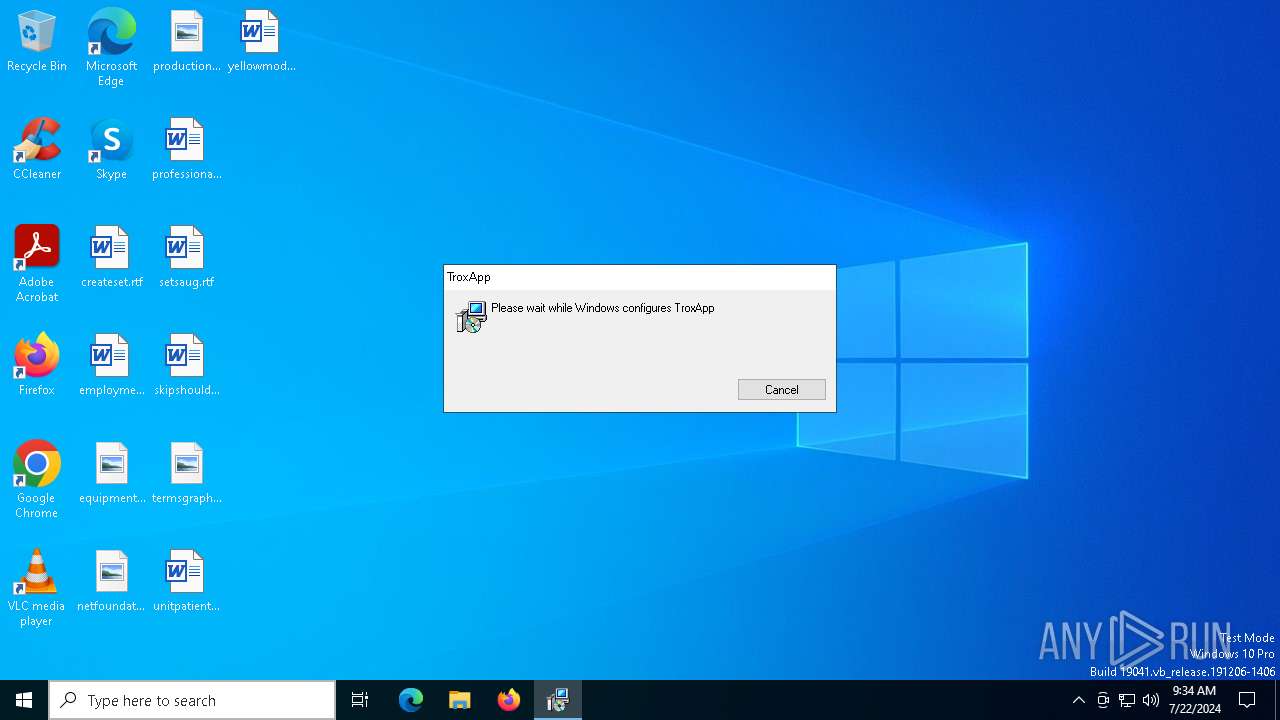
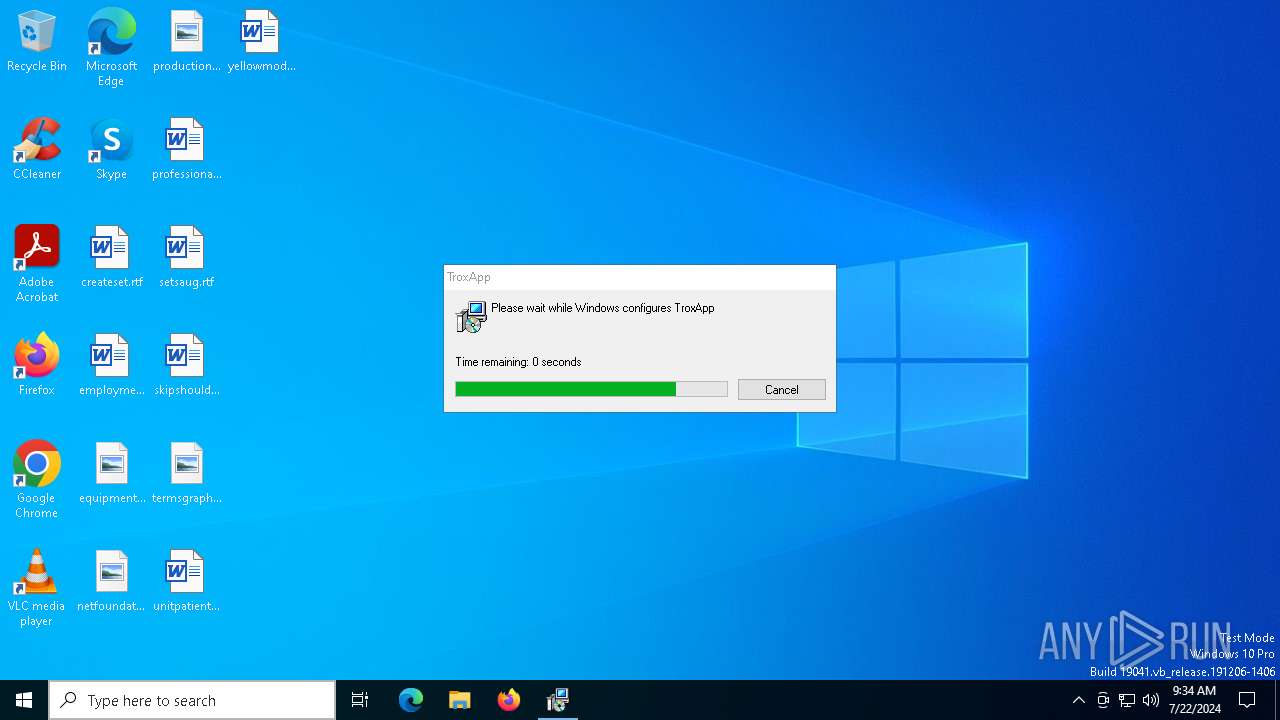
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {A3B69905-389C-4777-92FB-F2E072712230}, Number of Words: 10, Subject: TroxApp, Author: Troxbox Publish, Name of Creating Application: TroxApp, Template: x64;1033, Comments: This installer database contains the logic and data required to install TroxApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Mon Jul 8 17:55:21 2024, Last Saved Time/Date: Mon Jul 8 17:55:21 2024, Last Printed: Mon Jul 8 17:55:21 2024, Number of Pages: 450 |
| MD5: | 6E619D3D24F58BFB7BD7E76A4756E258 |
| SHA1: | 890359E1E86525C4C14E975E762239878134B32D |
| SHA256: | 5B3A41ED8A9A619B4AA18CEF611C94B3273671AD464847CBFA600A6571C64431 |
| SSDEEP: | 393216:U88/NM3eBSTDiwDnsVznaoDtACBF2iILPmq:k6tu+nKnrDqCqtLP |
MALICIOUS
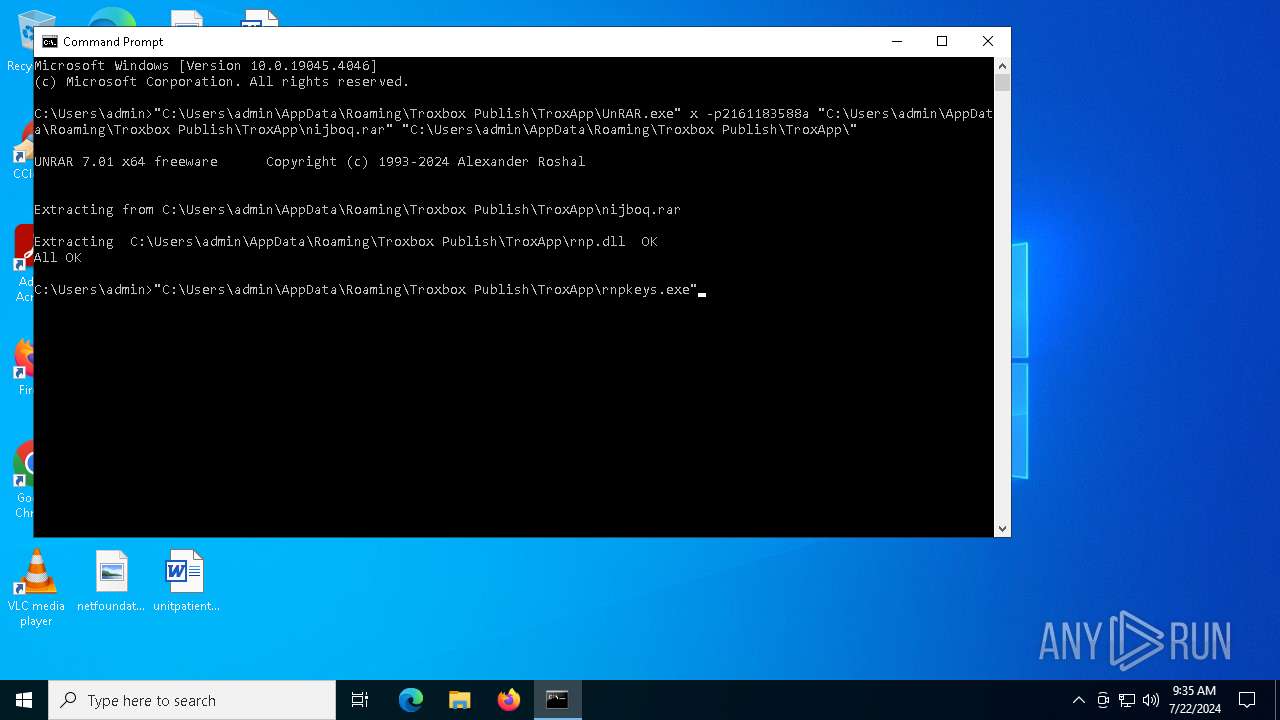
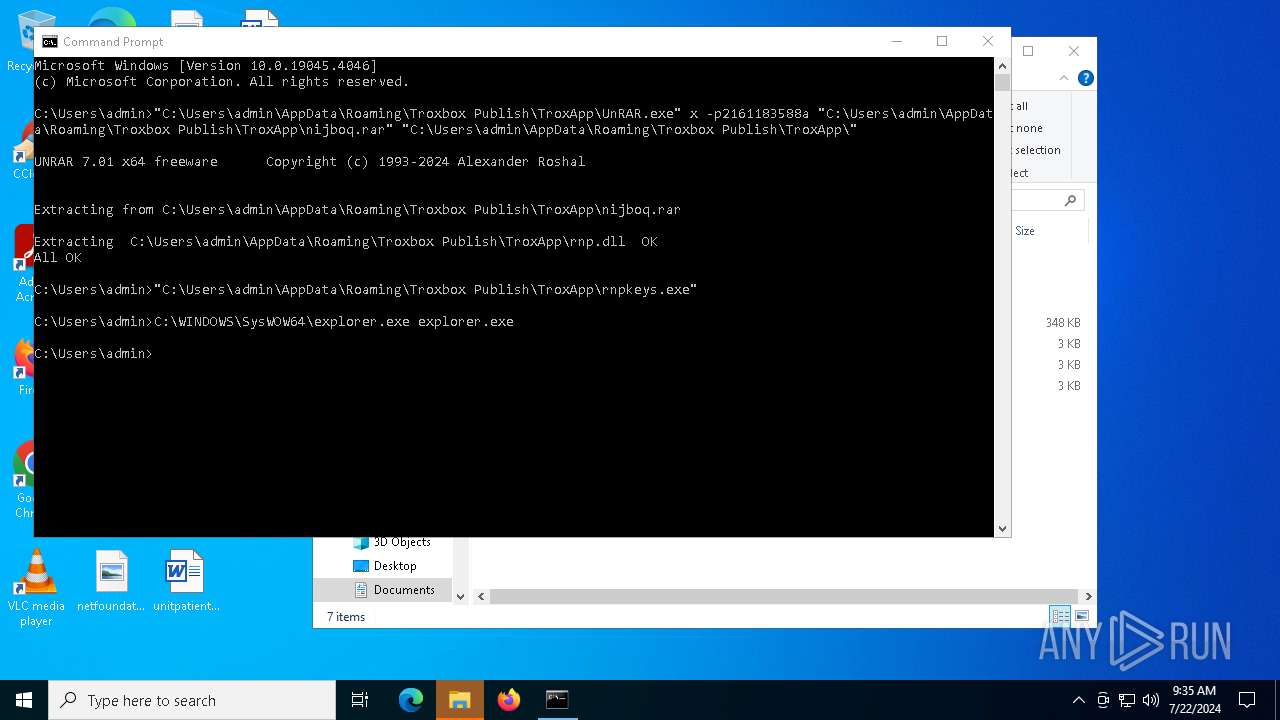
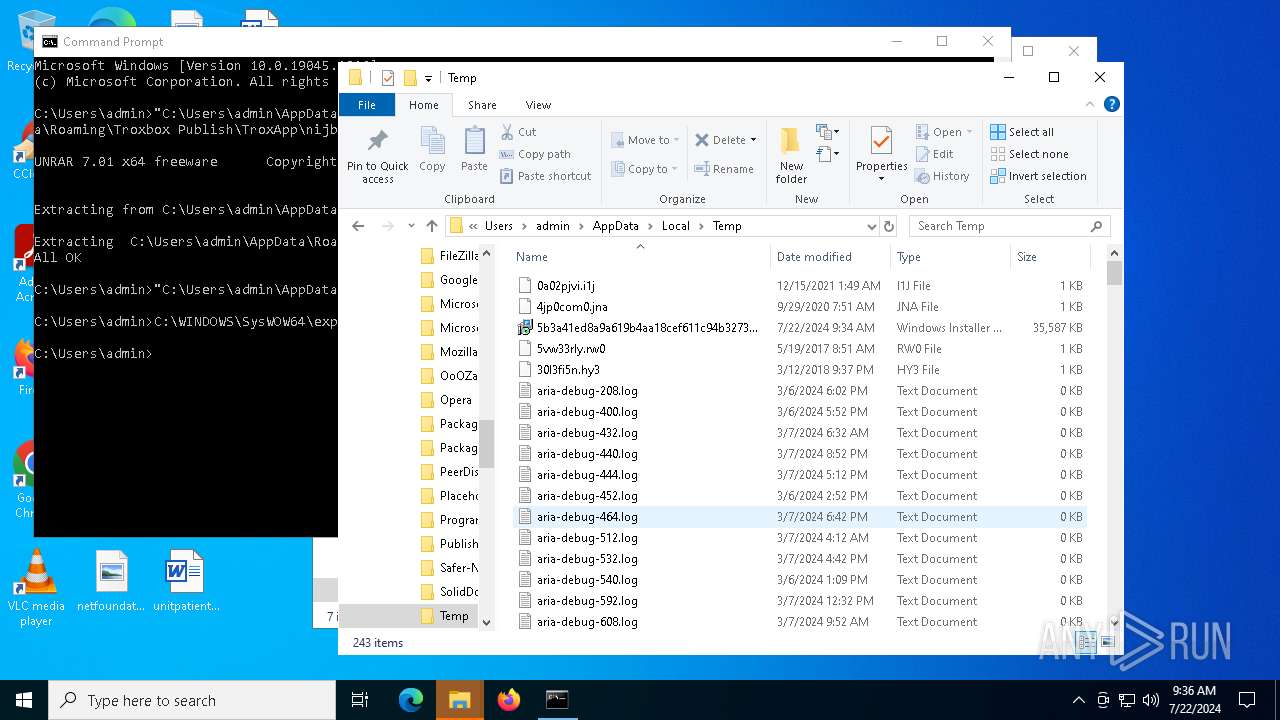
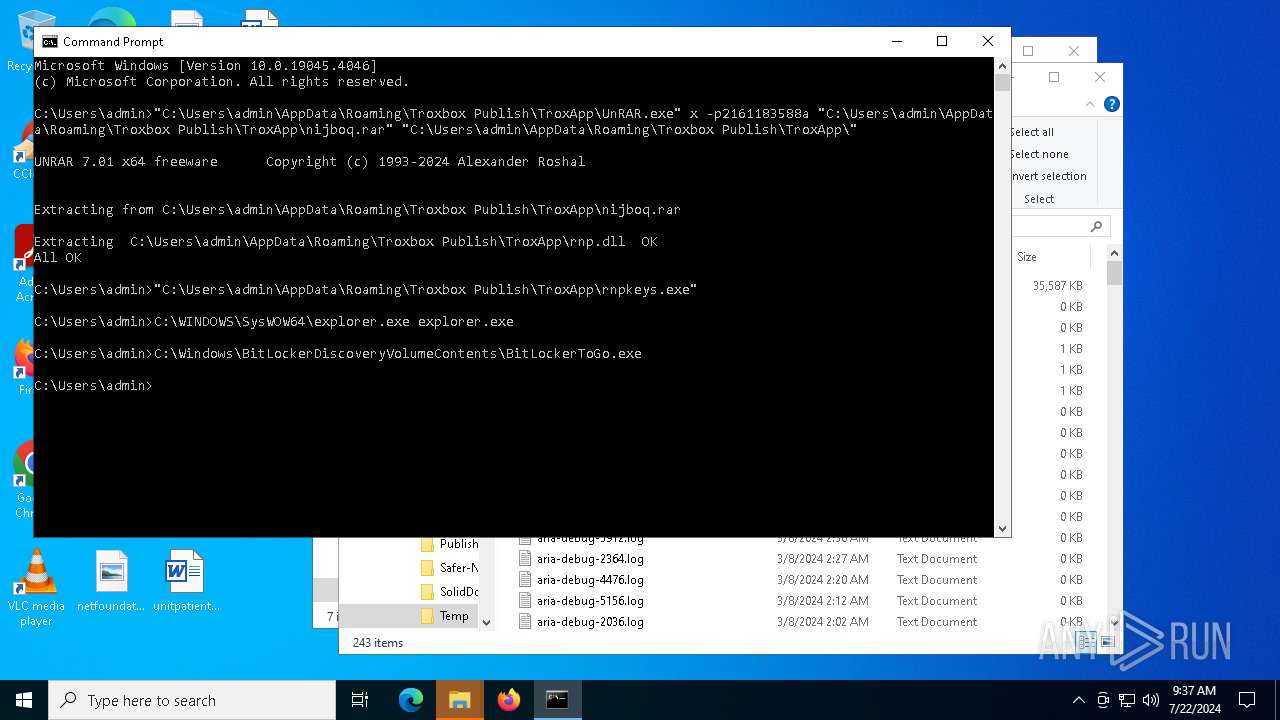
Drops the executable file immediately after the start
- msiexec.exe (PID: 6968)
- UnRAR.exe (PID: 7476)
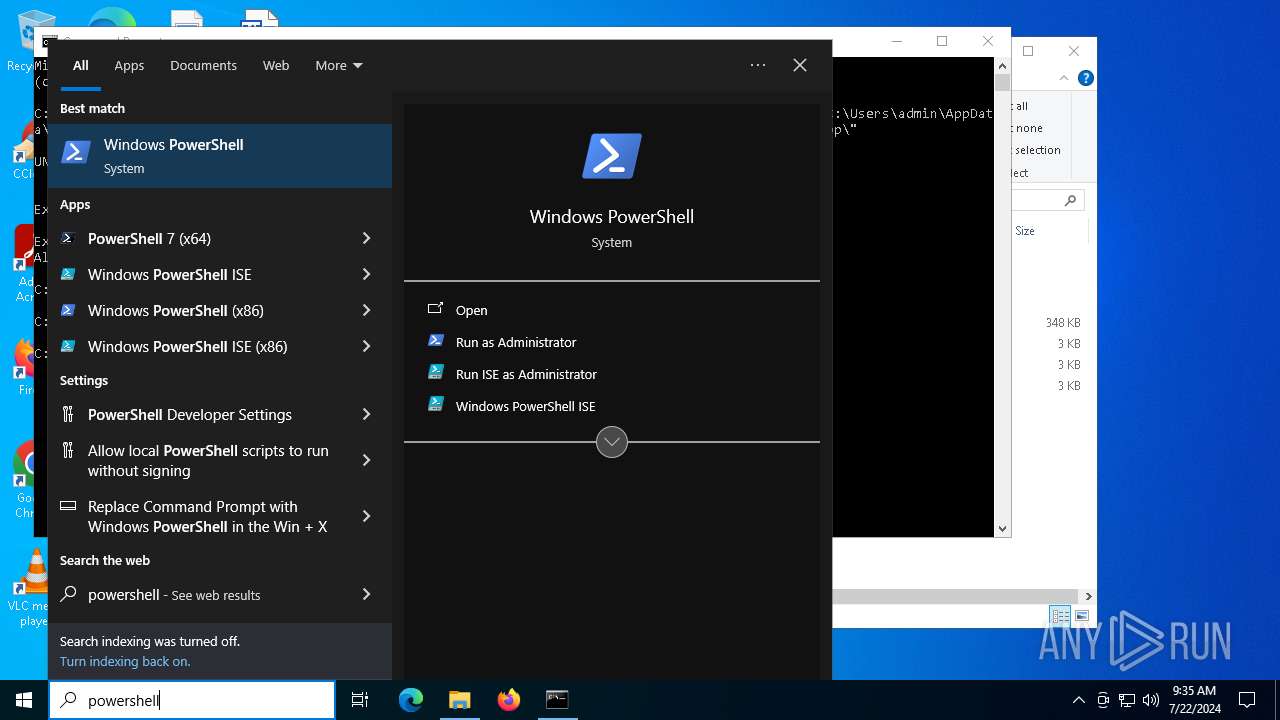
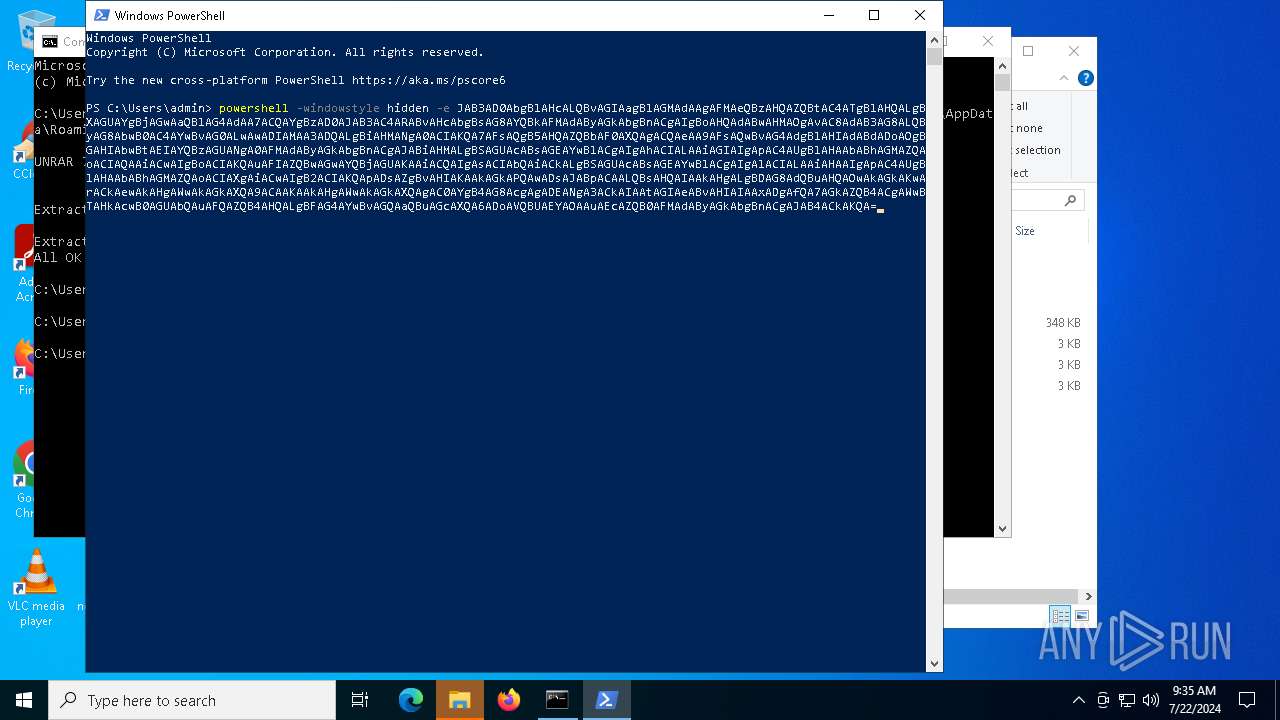
Run PowerShell with an invisible window
- powershell.exe (PID: 7588)
Actions looks like stealing of personal data
- powershell.exe (PID: 7588)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6968)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7440)
Checks Windows Trust Settings
- msiexec.exe (PID: 7440)
Process drops legitimate windows executable
- msiexec.exe (PID: 6968)
The process drops C-runtime libraries
- msiexec.exe (PID: 6968)
Base64-obfuscated command line is found
- powershell.exe (PID: 7352)
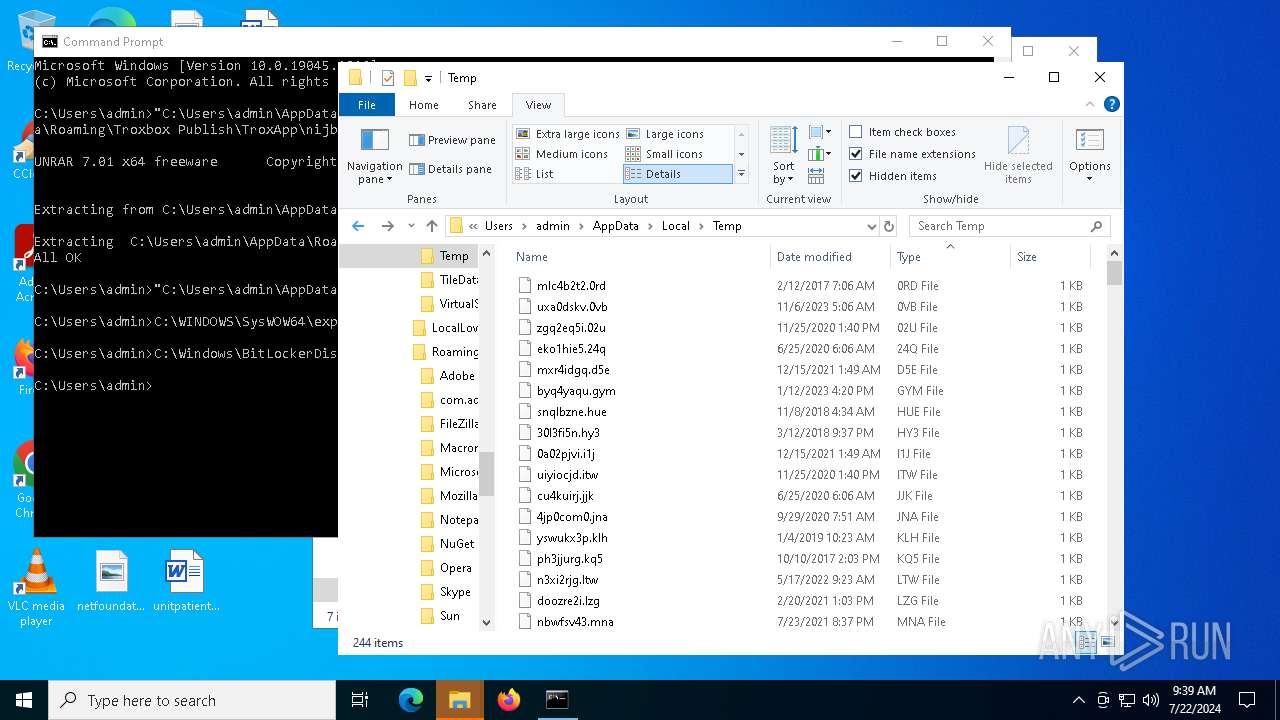
Executable content was dropped or overwritten
- UnRAR.exe (PID: 7476)
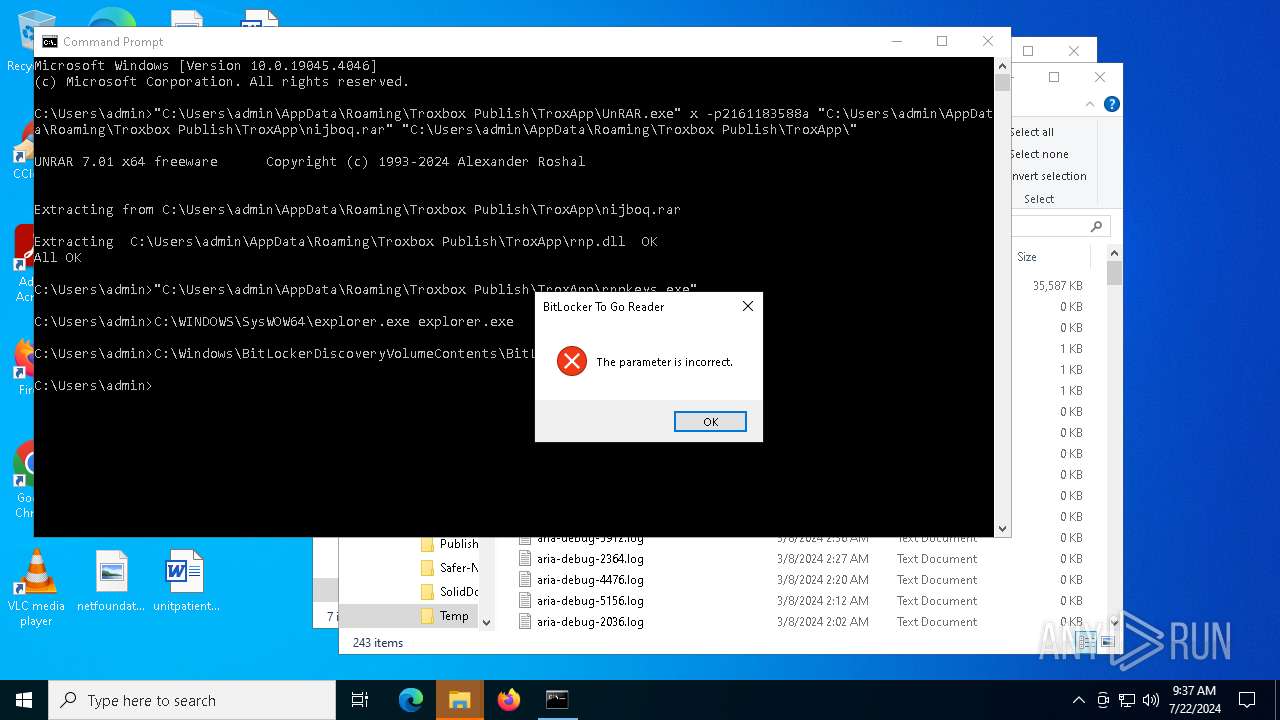
Executes application which crashes
- rnpkeys.exe (PID: 1884)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7352)
Application launched itself
- powershell.exe (PID: 7352)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7352)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7588)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7588)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7588)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7588)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7588)
INFO
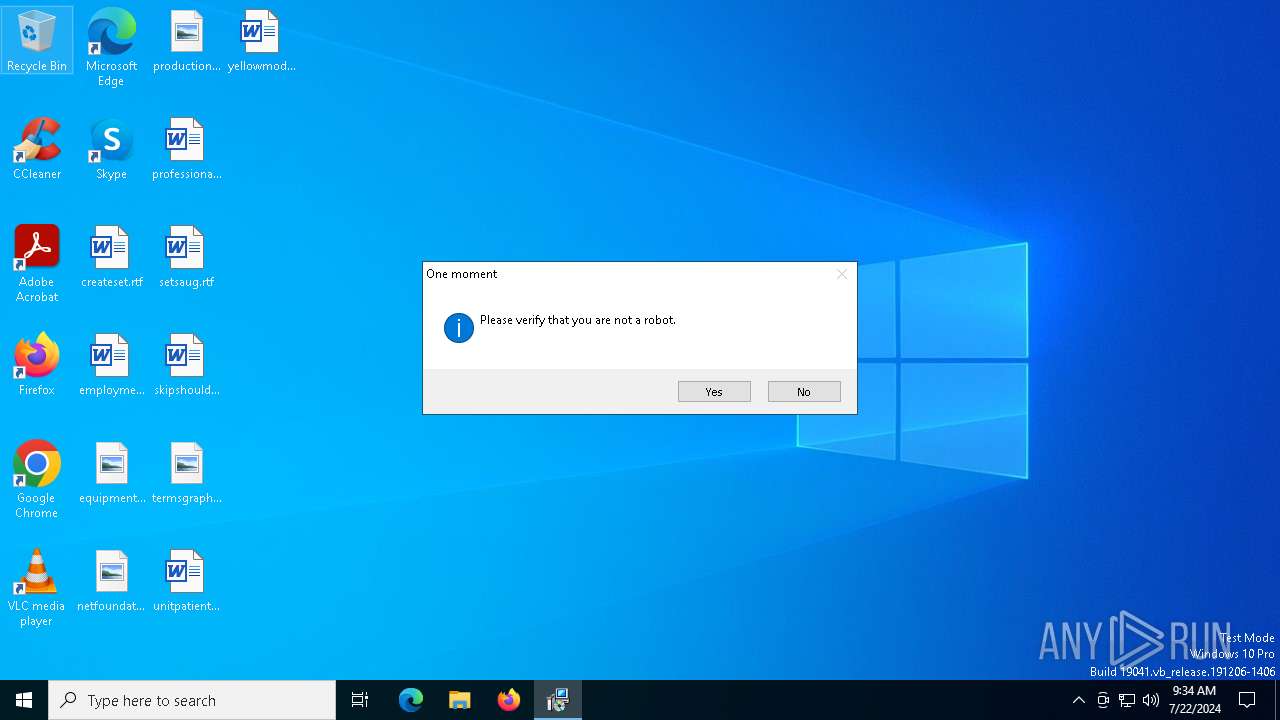
An automatically generated document
- msiexec.exe (PID: 5112)
Reads the computer name
- msiexec.exe (PID: 6968)
- msiexec.exe (PID: 7440)
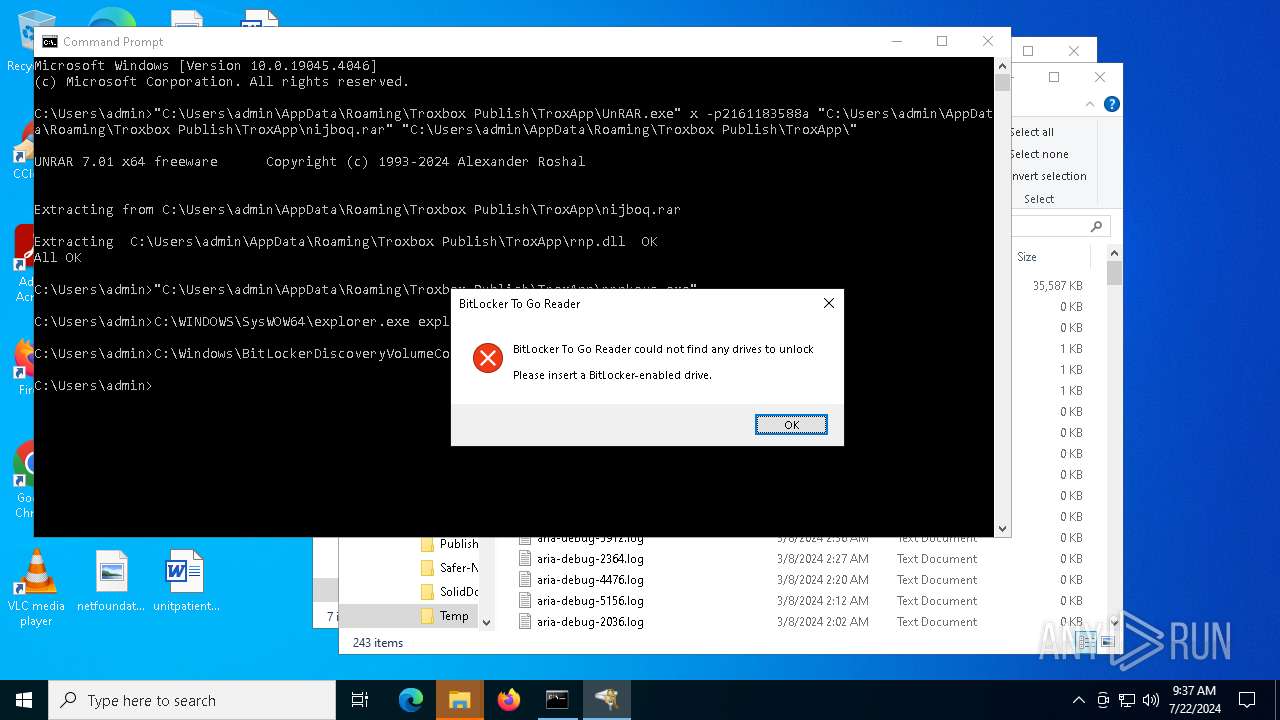
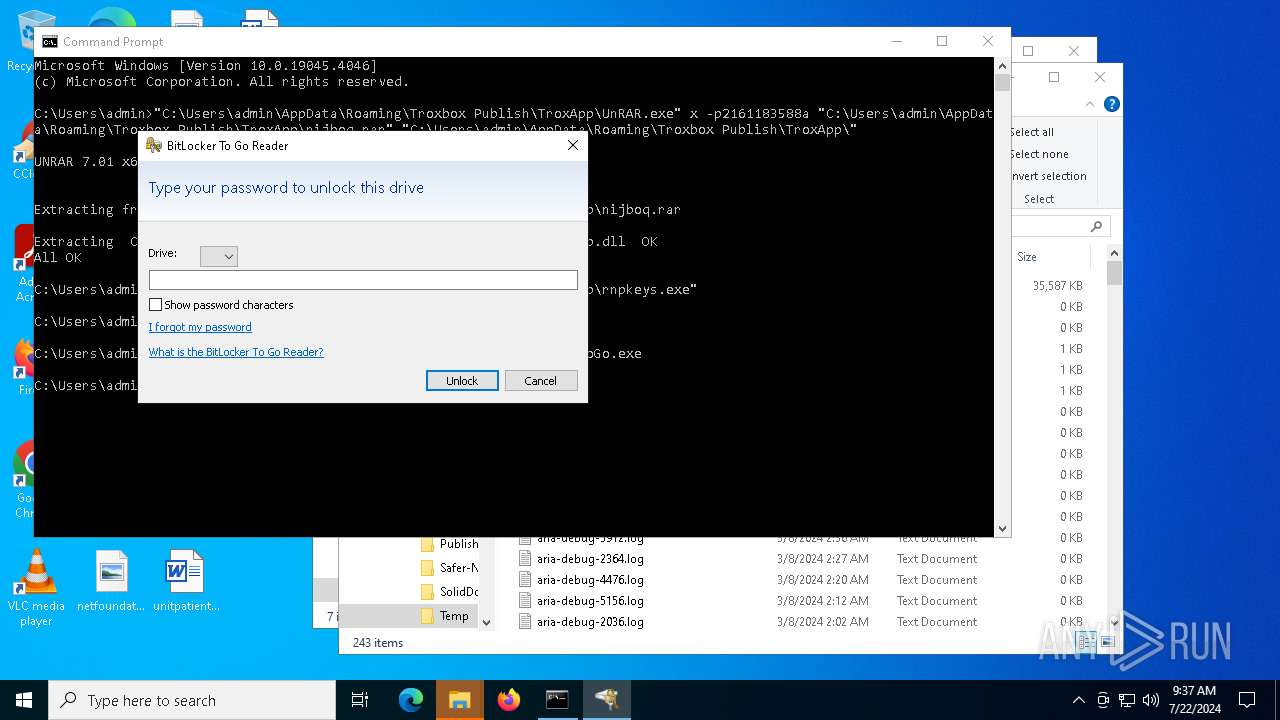
- BitLockerToGo.exe (PID: 7476)
Checks supported languages
- msiexec.exe (PID: 6968)
- msiexec.exe (PID: 7440)
- UnRAR.exe (PID: 7476)
- rnpkeys.exe (PID: 1884)
- BitLockerToGo.exe (PID: 7476)
Reads Environment values
- msiexec.exe (PID: 7440)
Checks proxy server information
- msiexec.exe (PID: 7440)
- powershell.exe (PID: 7588)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6968)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7440)
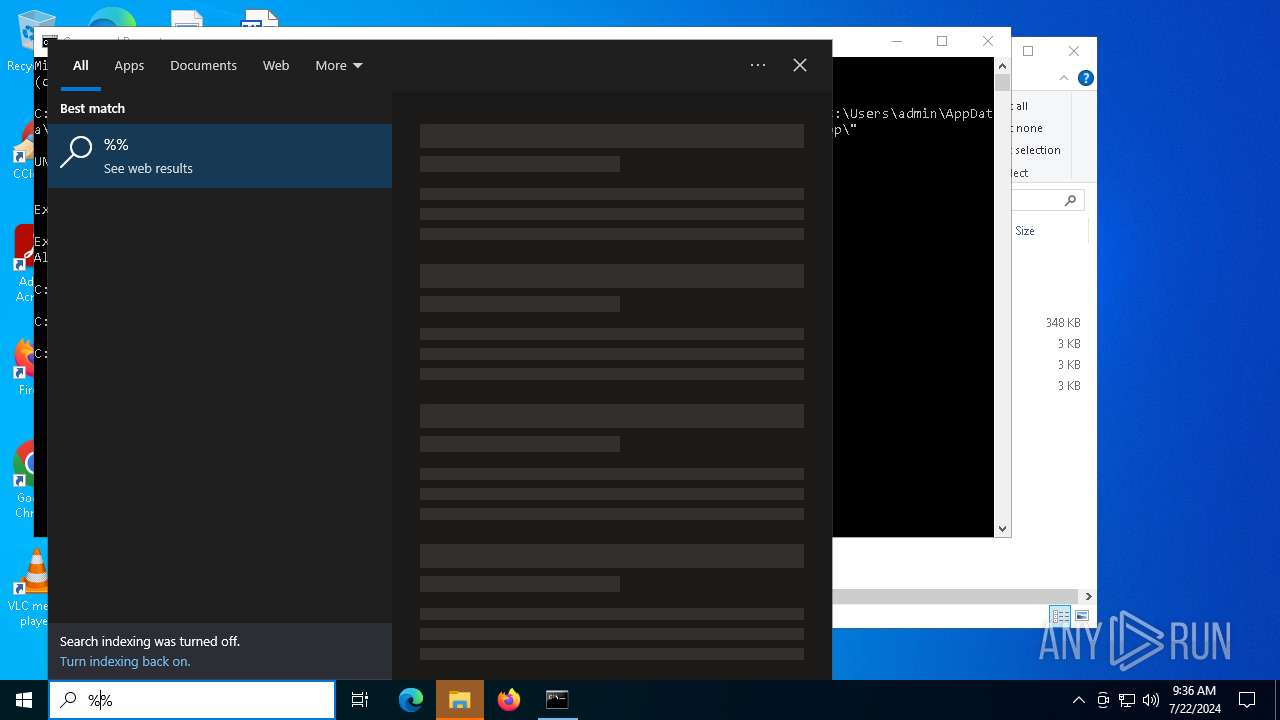
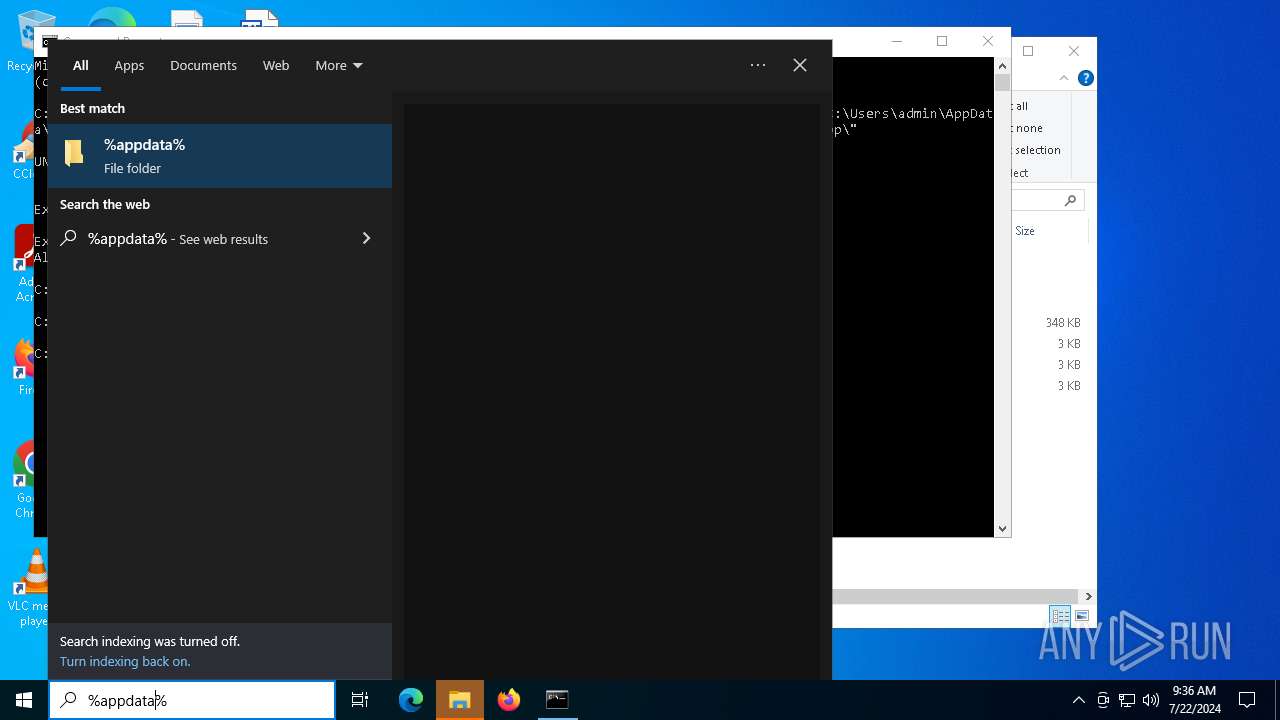
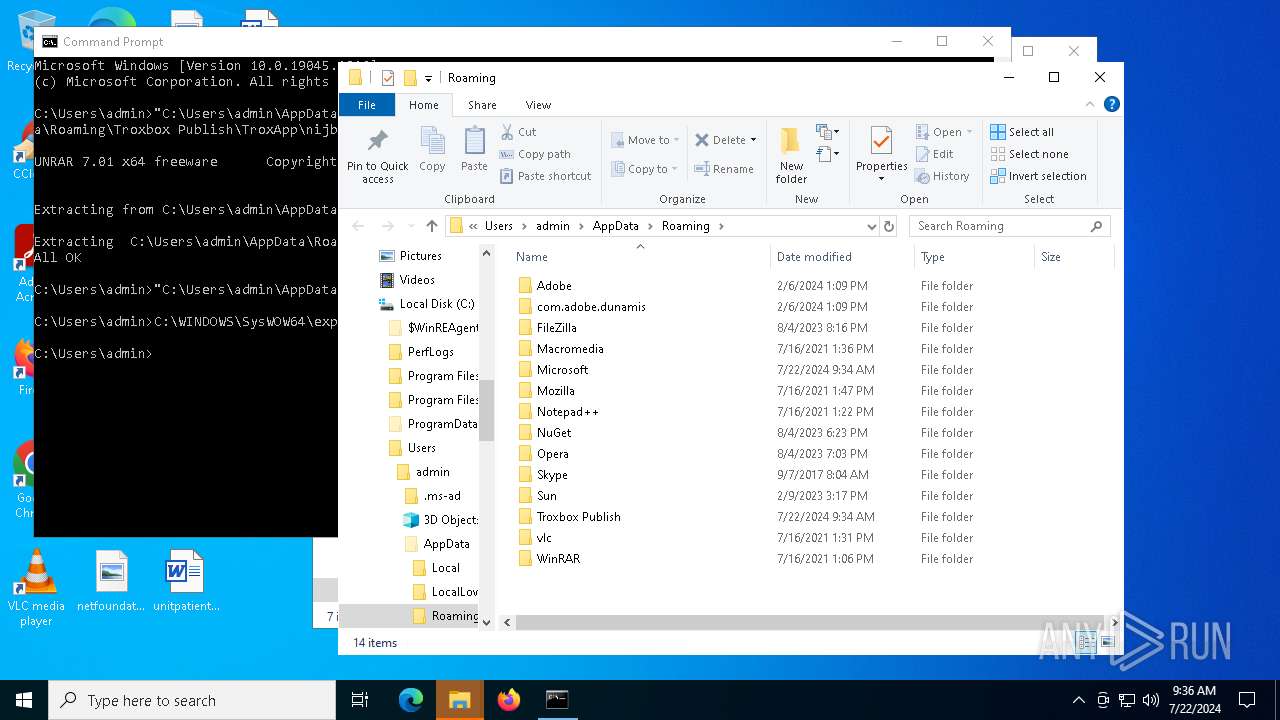
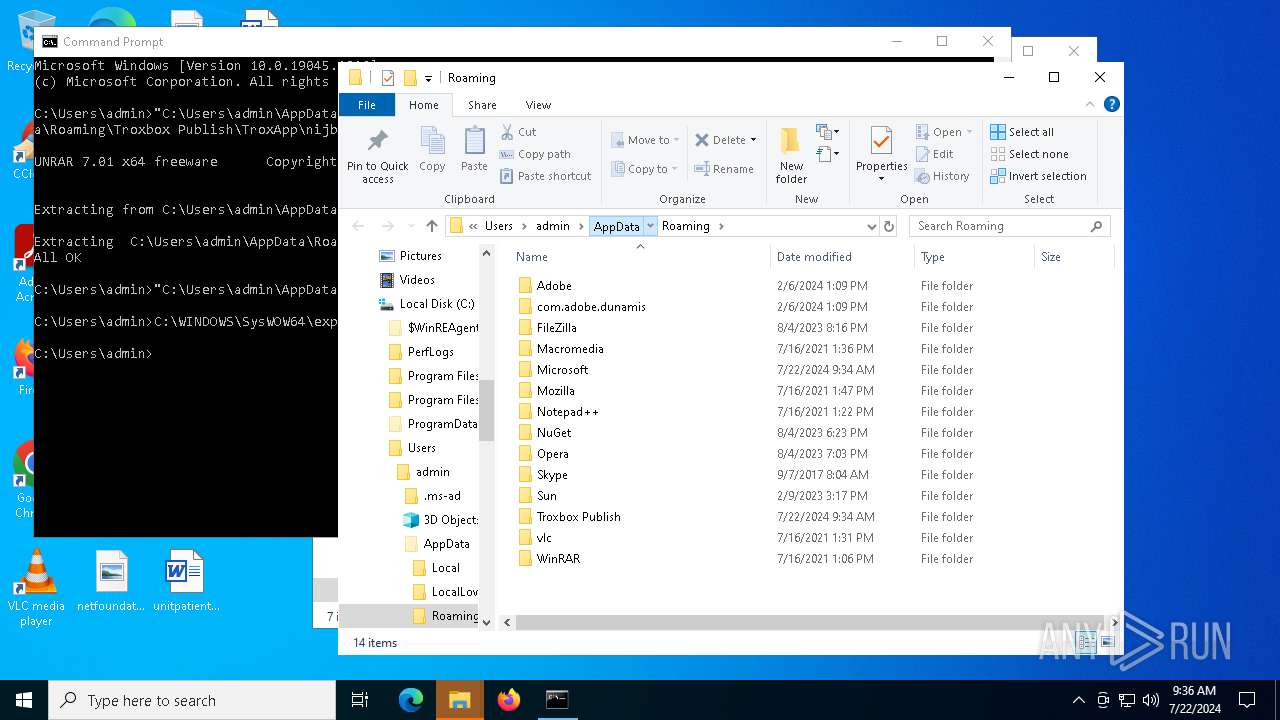
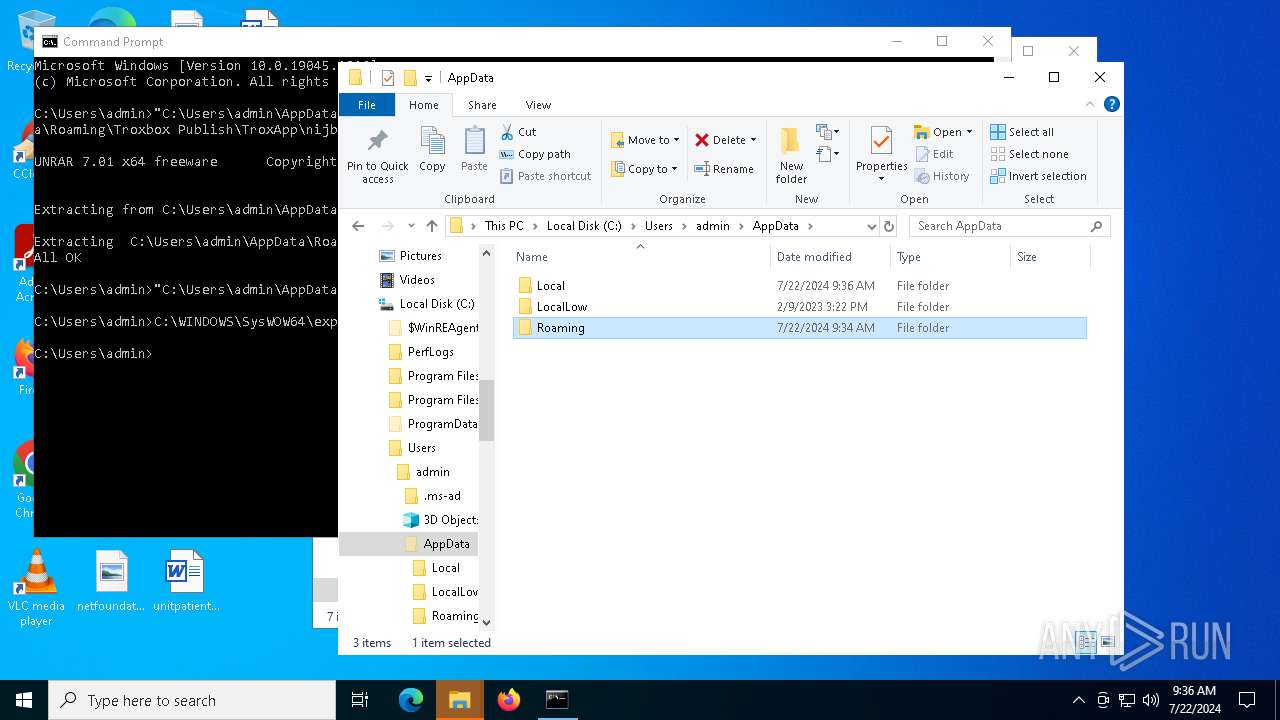
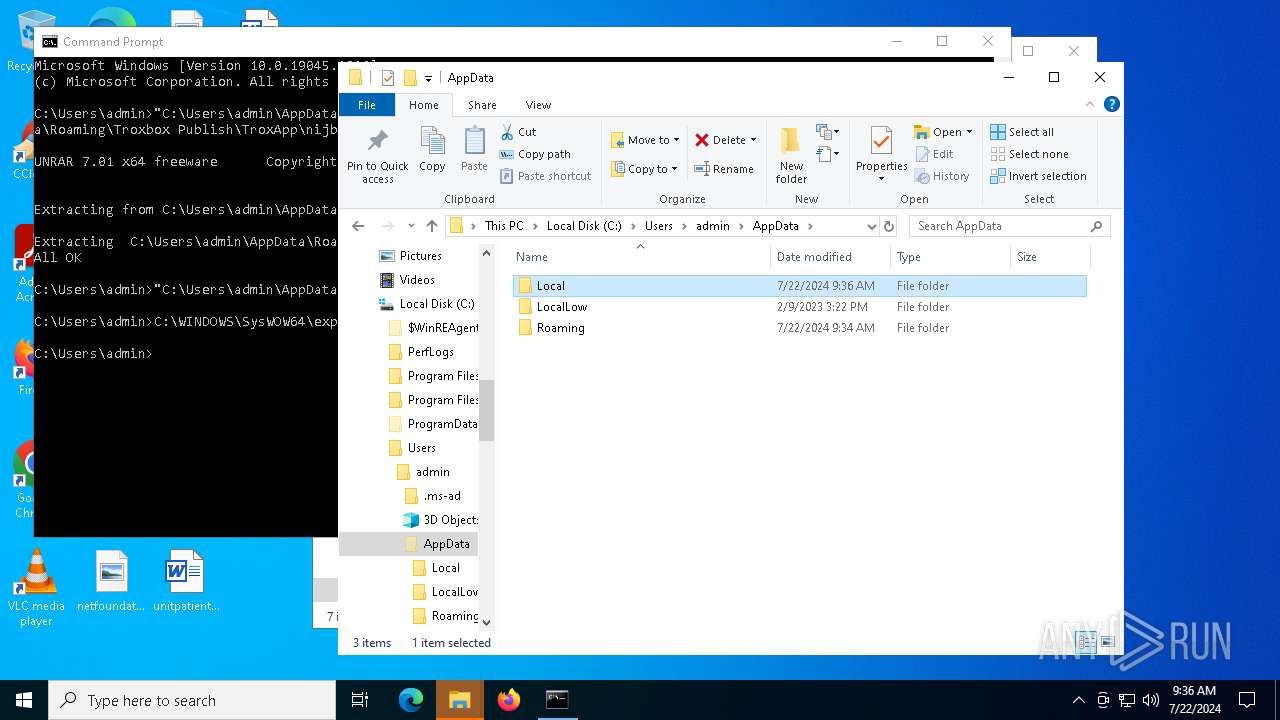
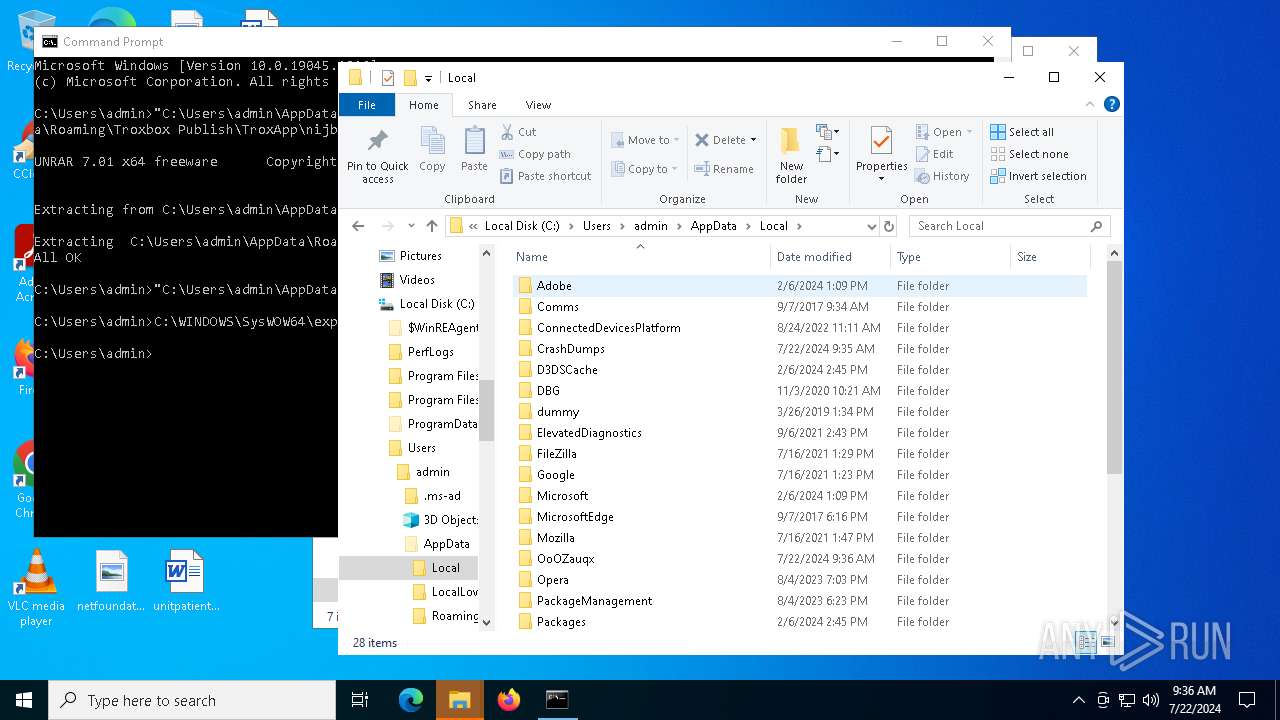
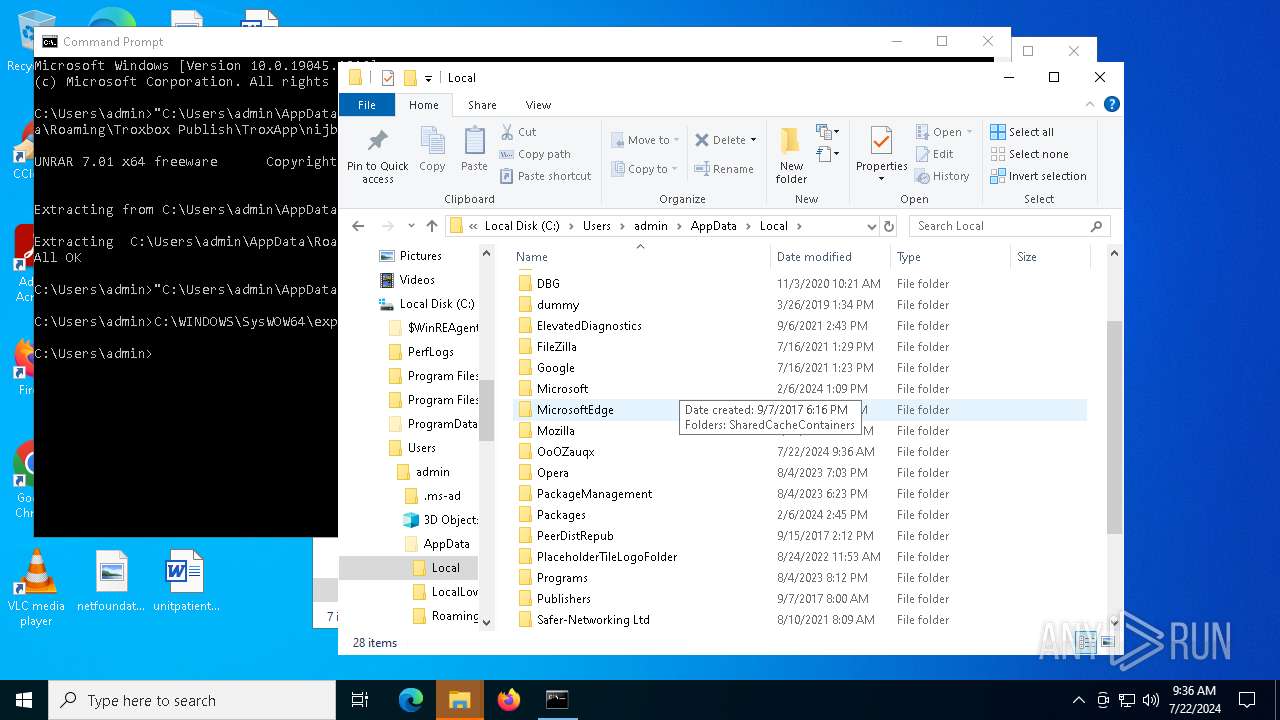
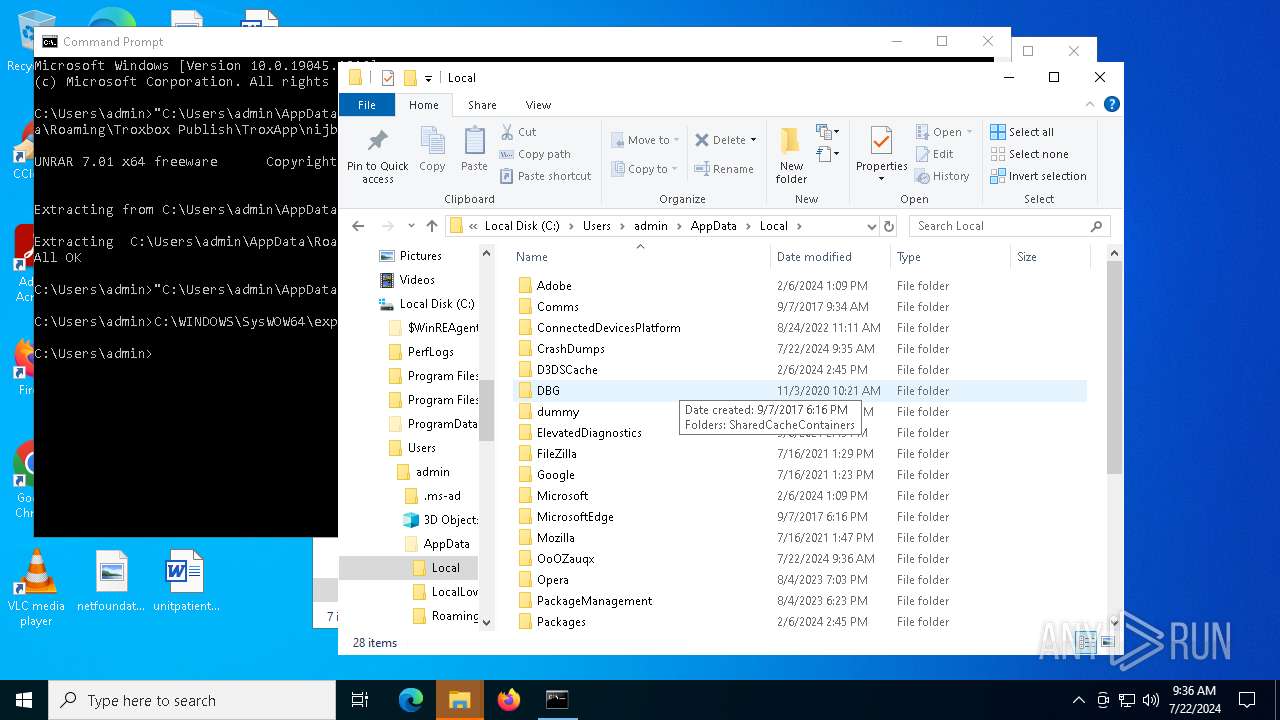
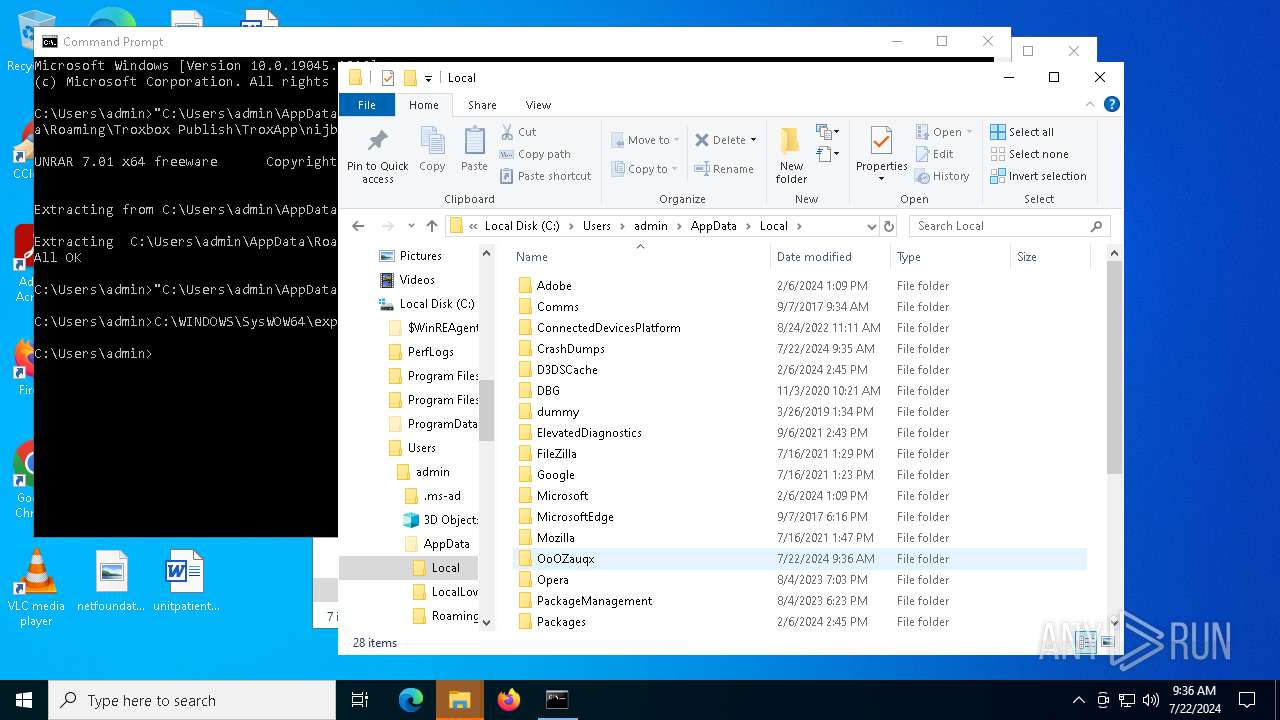
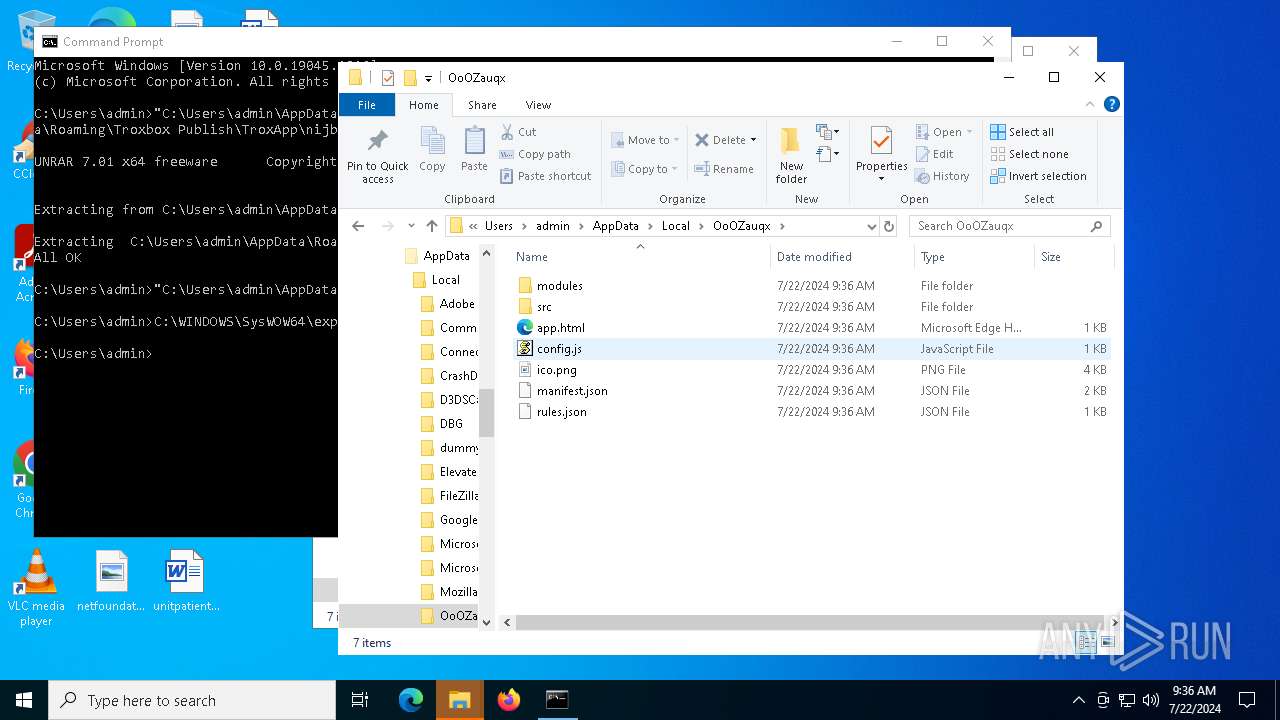
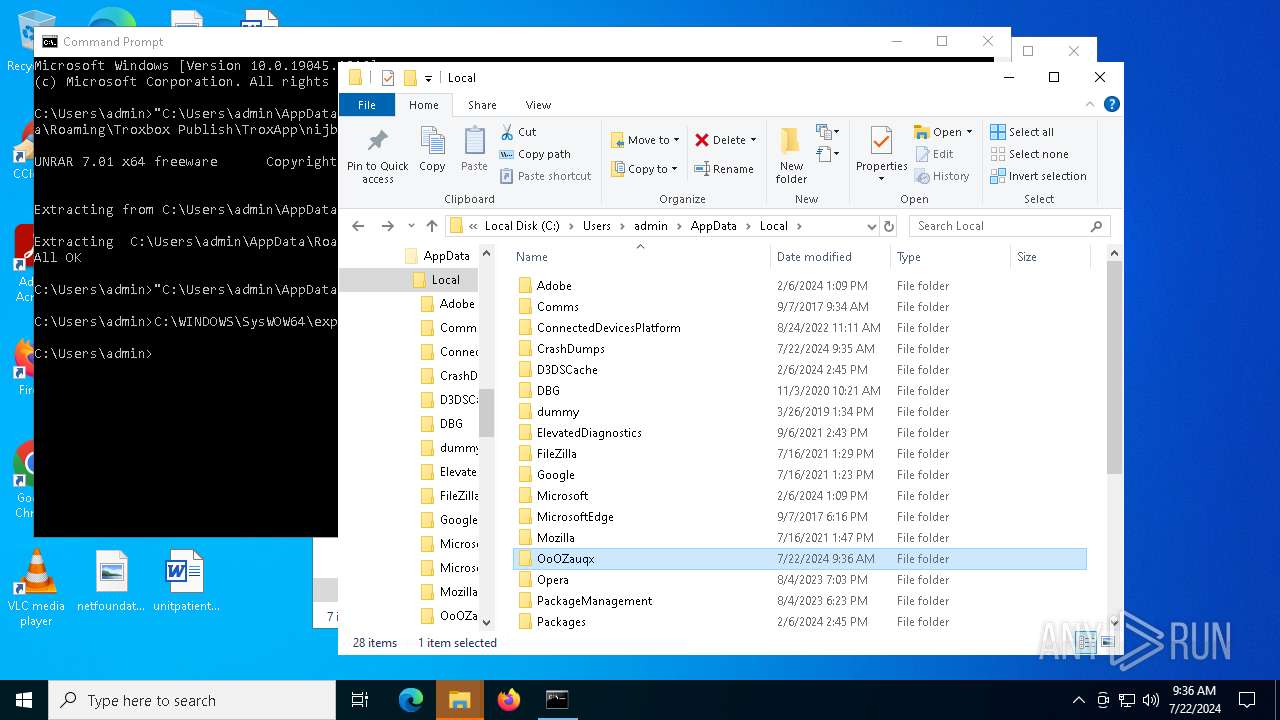
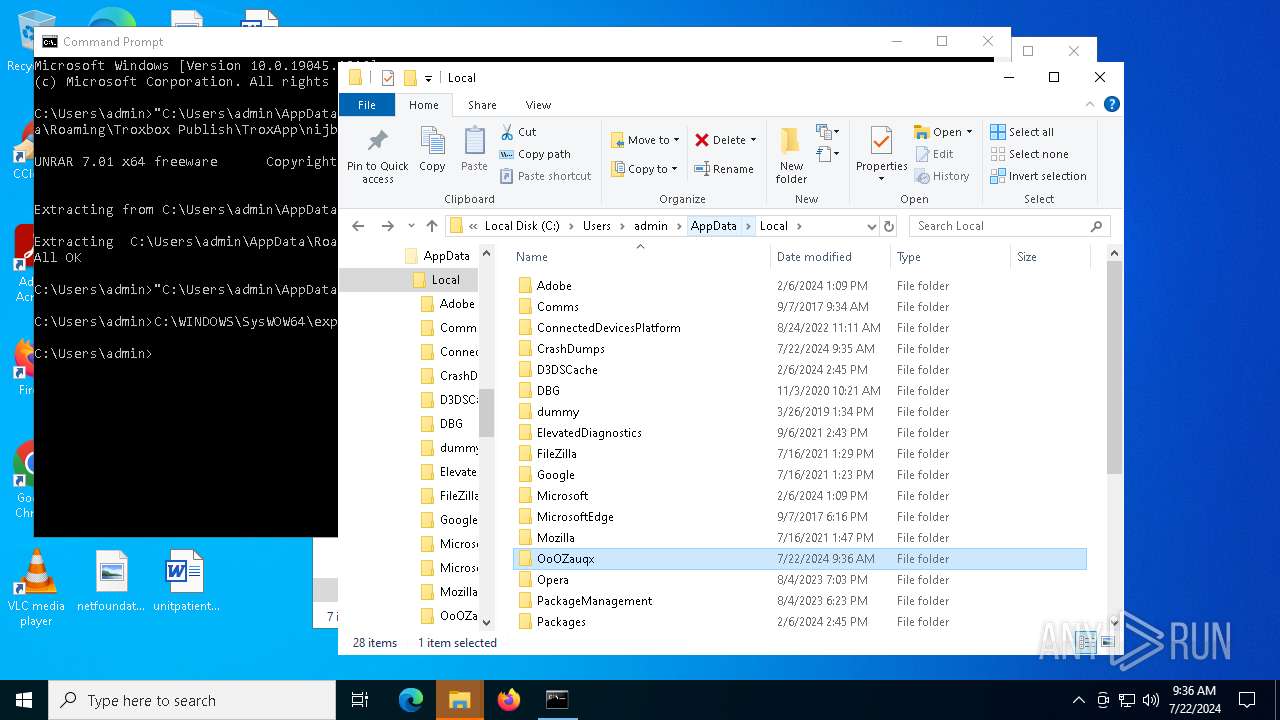
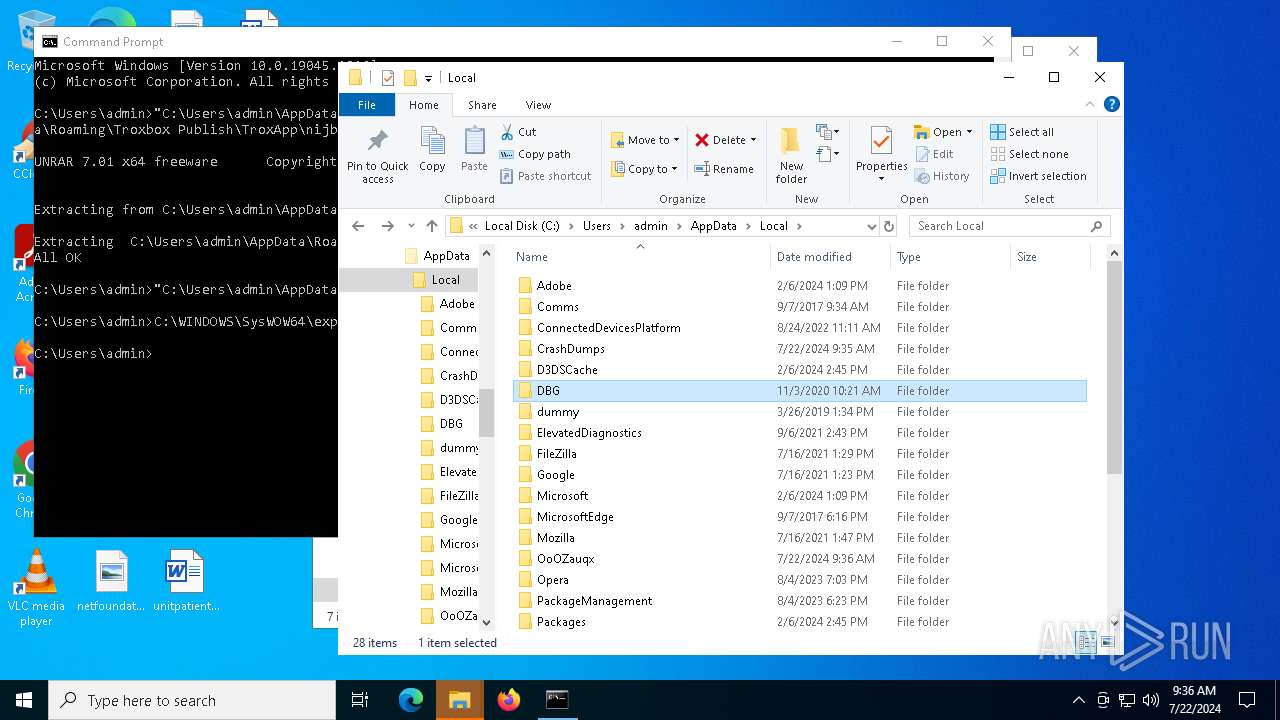
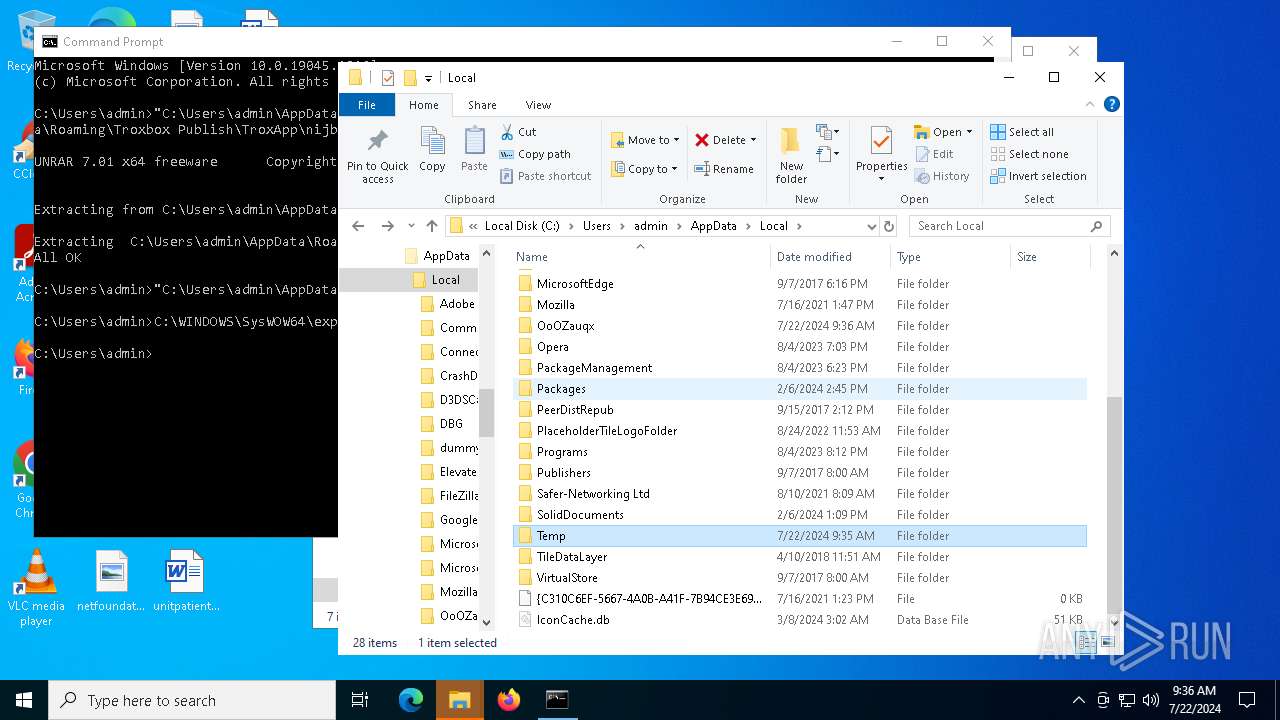
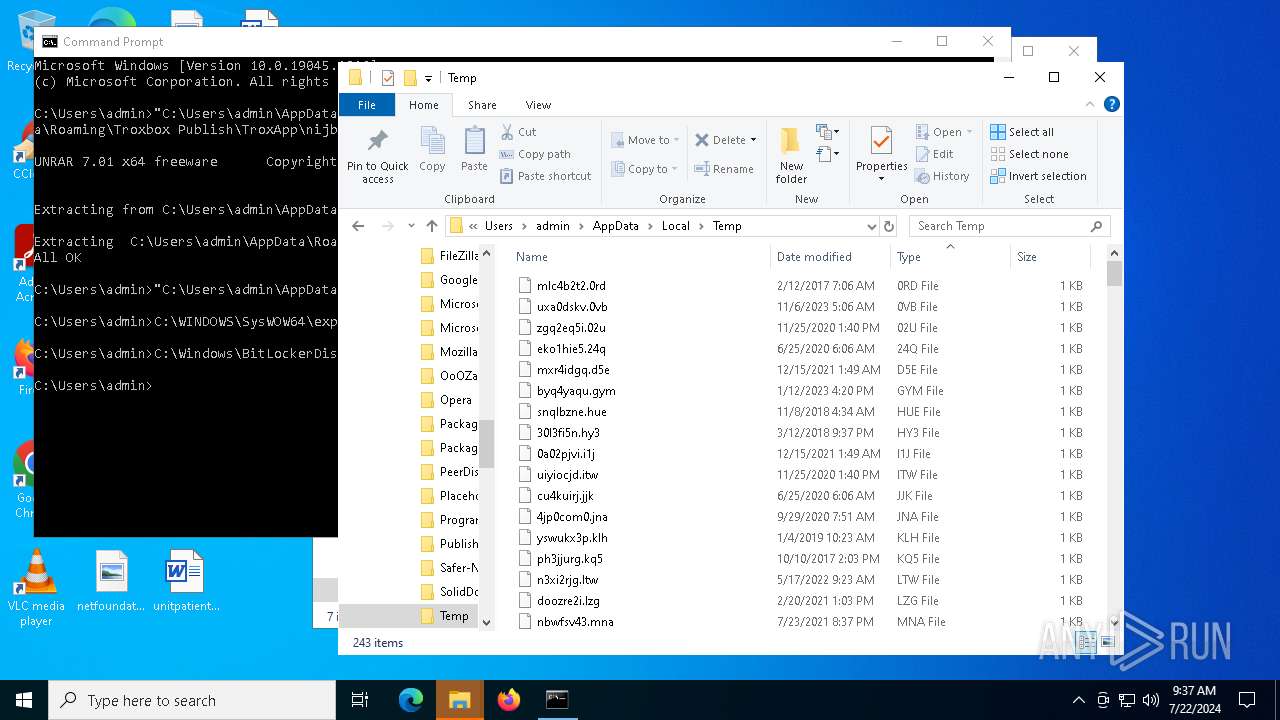
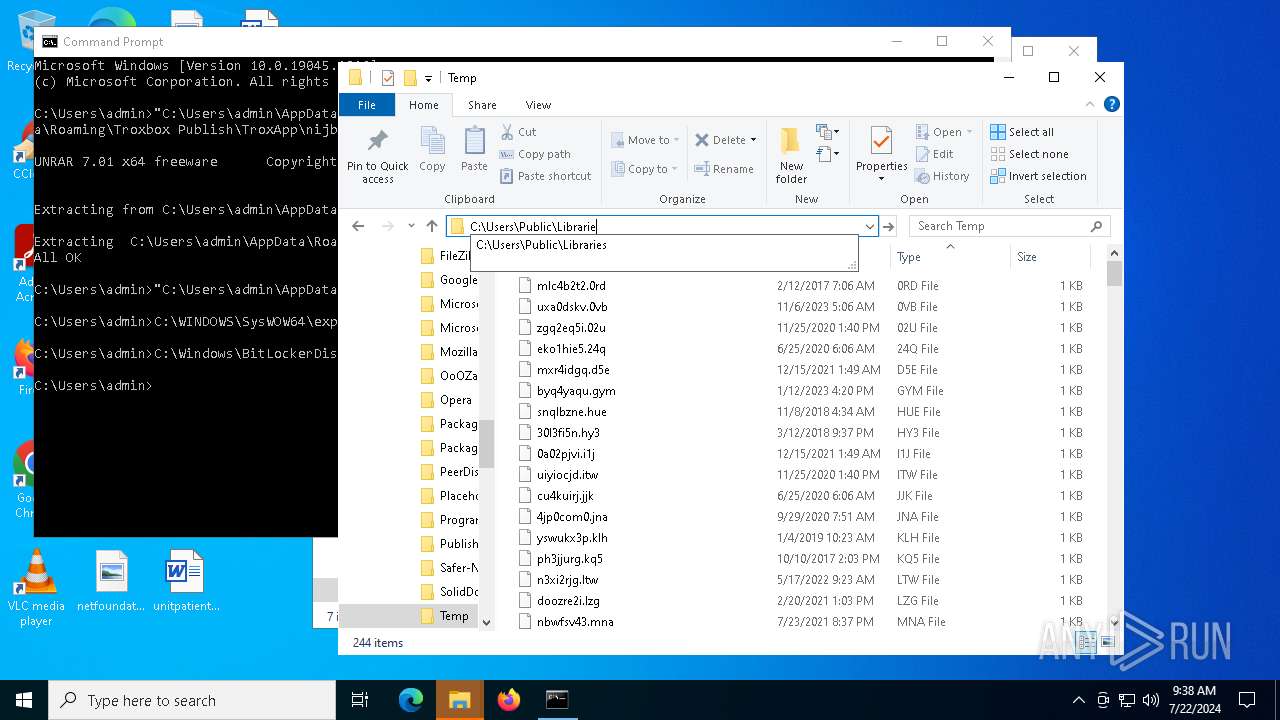
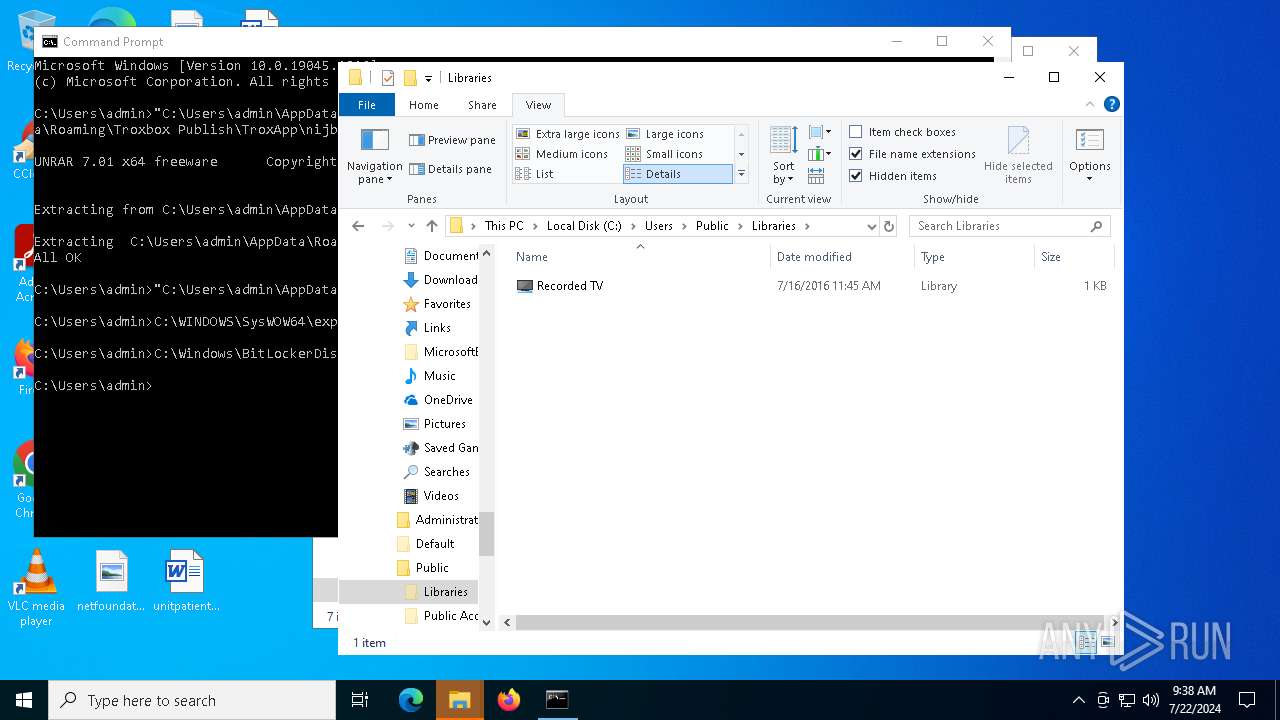
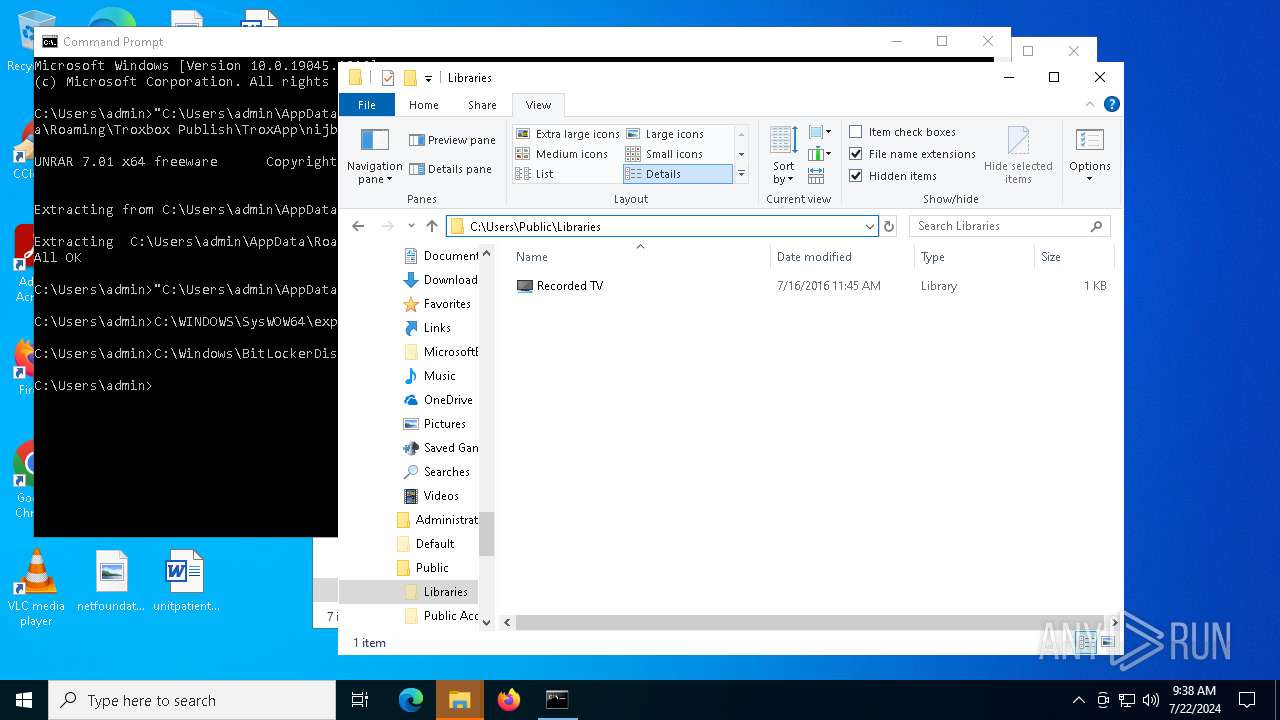
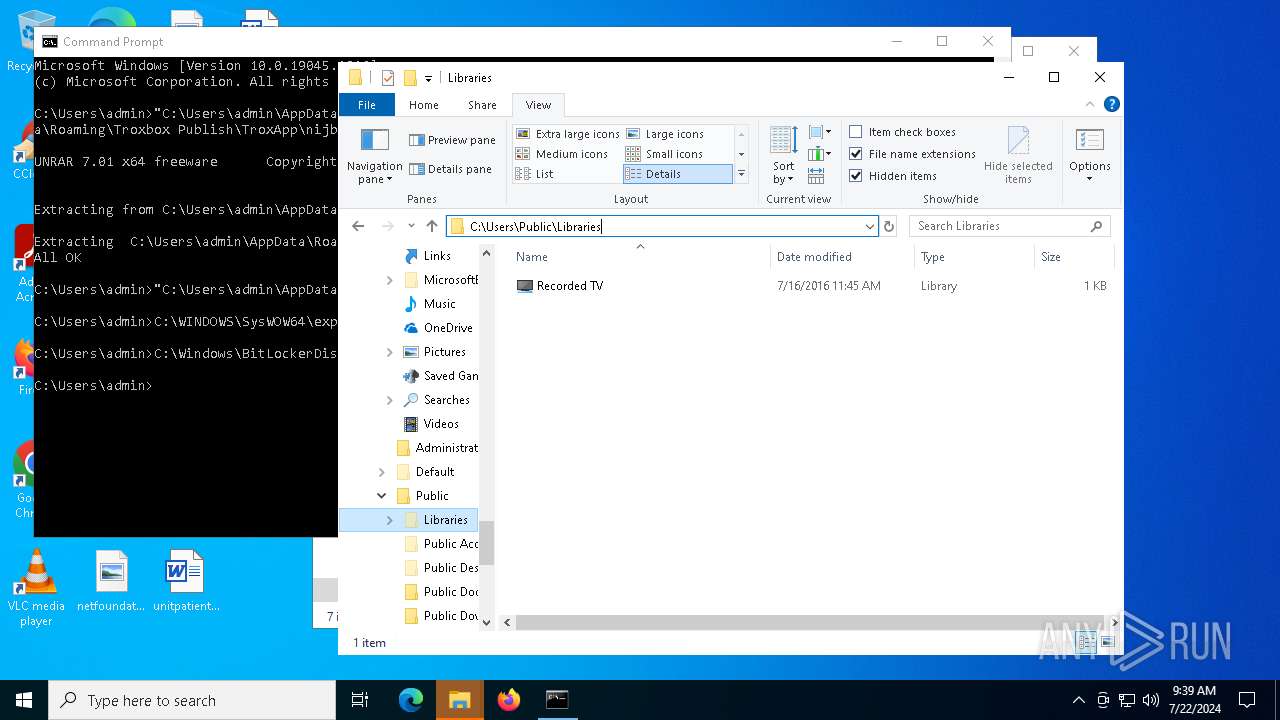
Creates files or folders in the user directory
- msiexec.exe (PID: 7440)
- msiexec.exe (PID: 6968)
- UnRAR.exe (PID: 7476)
- WerFault.exe (PID: 5444)
- WerFault.exe (PID: 7796)
Reads the software policy settings
- msiexec.exe (PID: 7440)
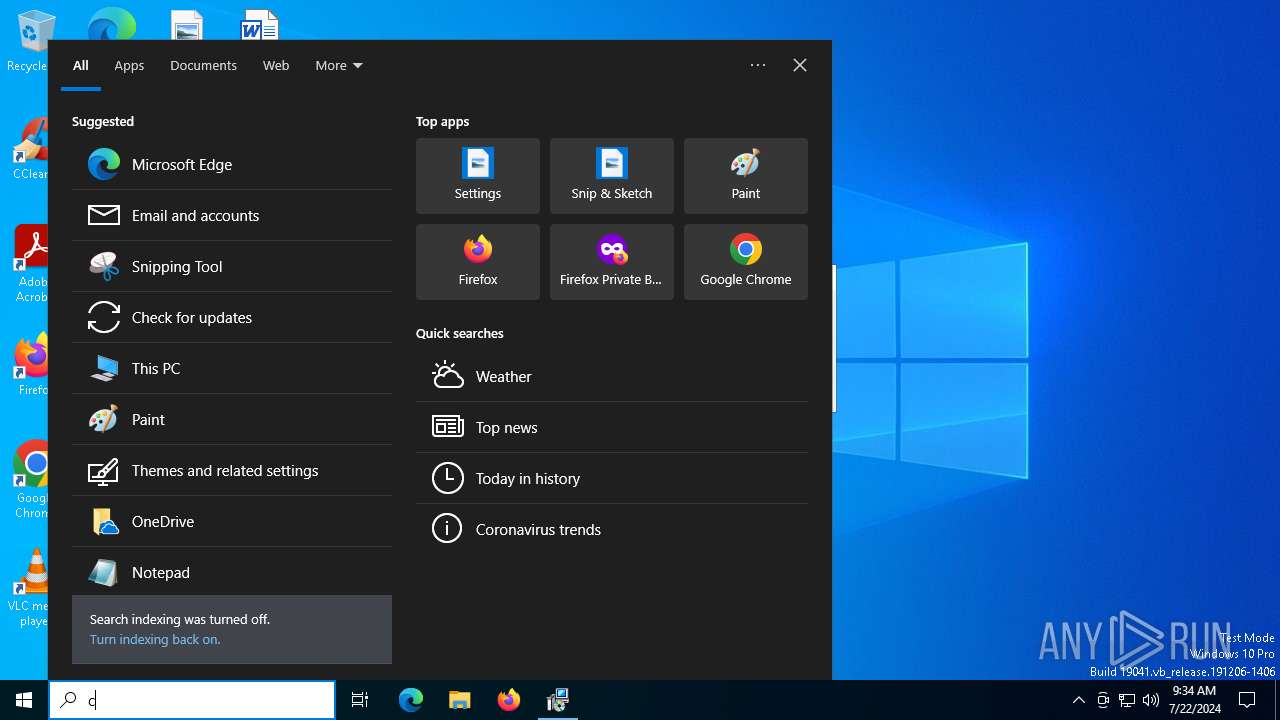
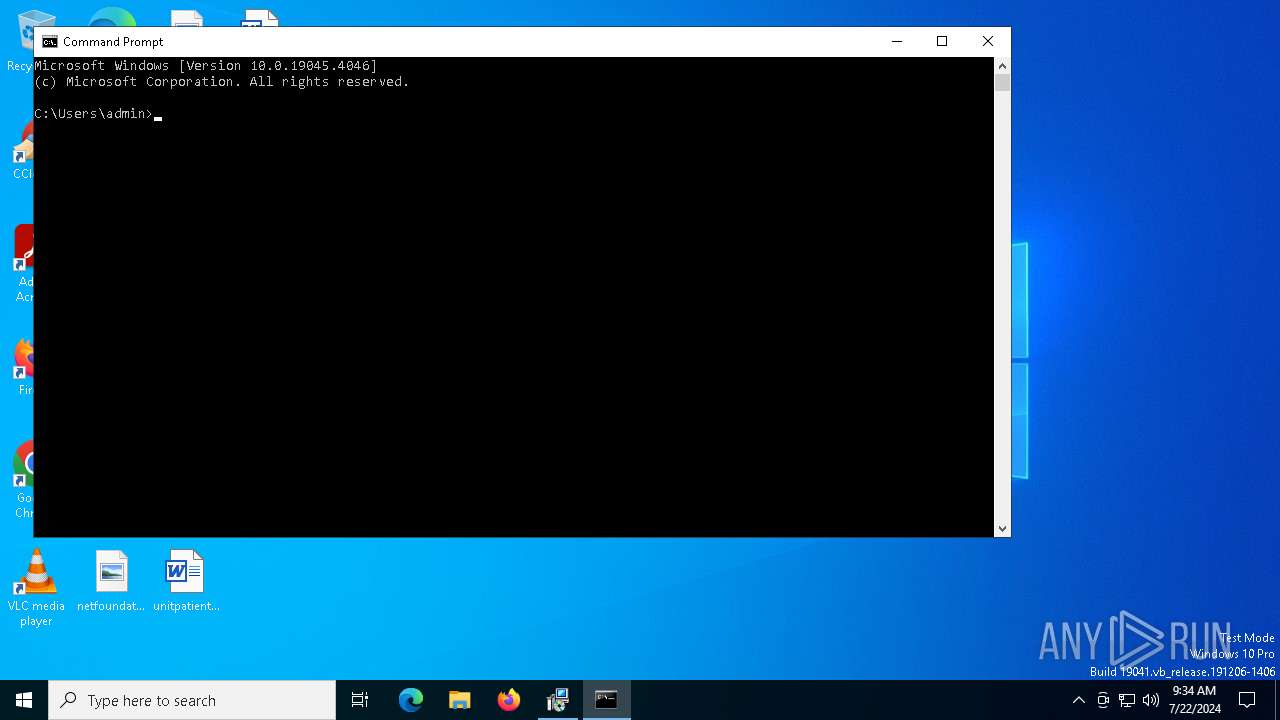
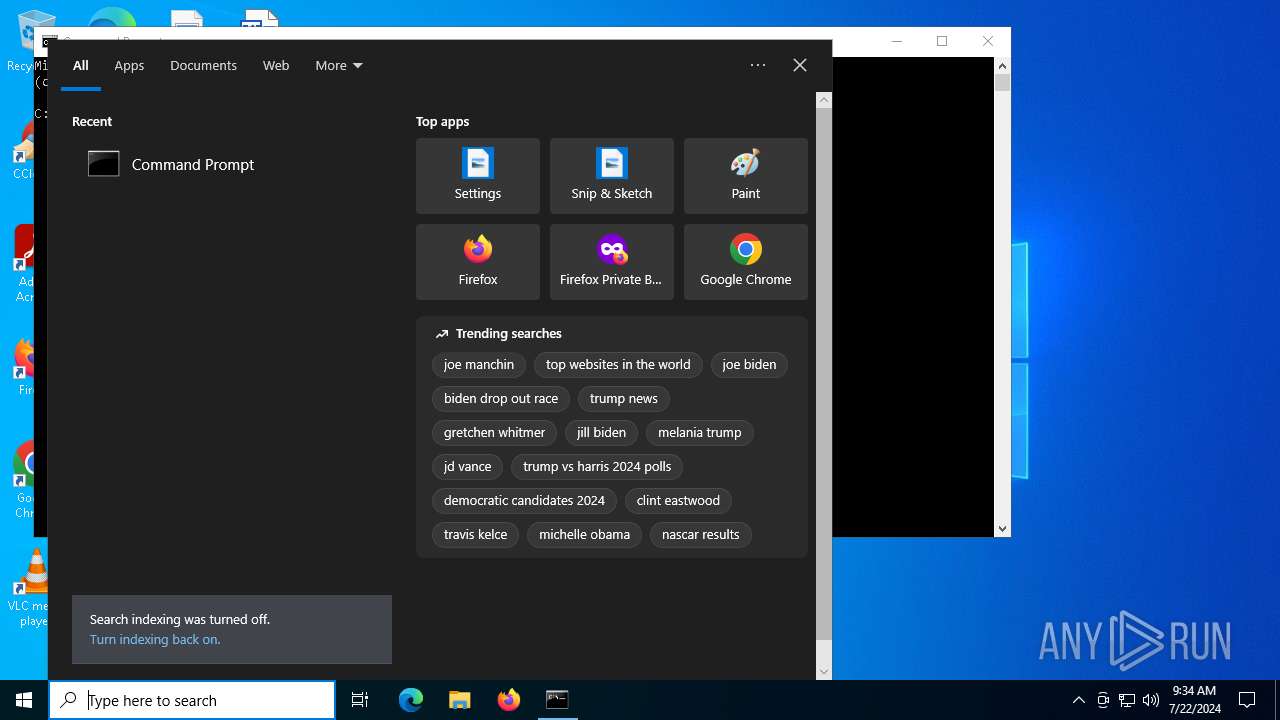
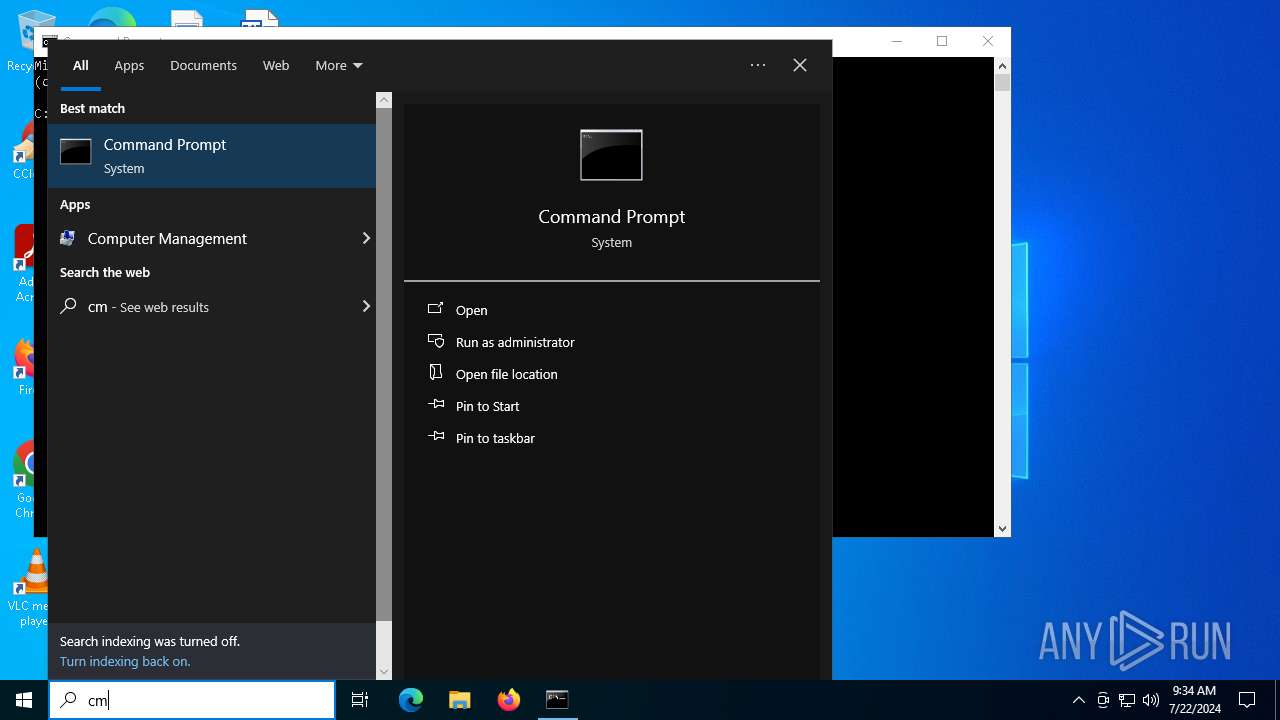
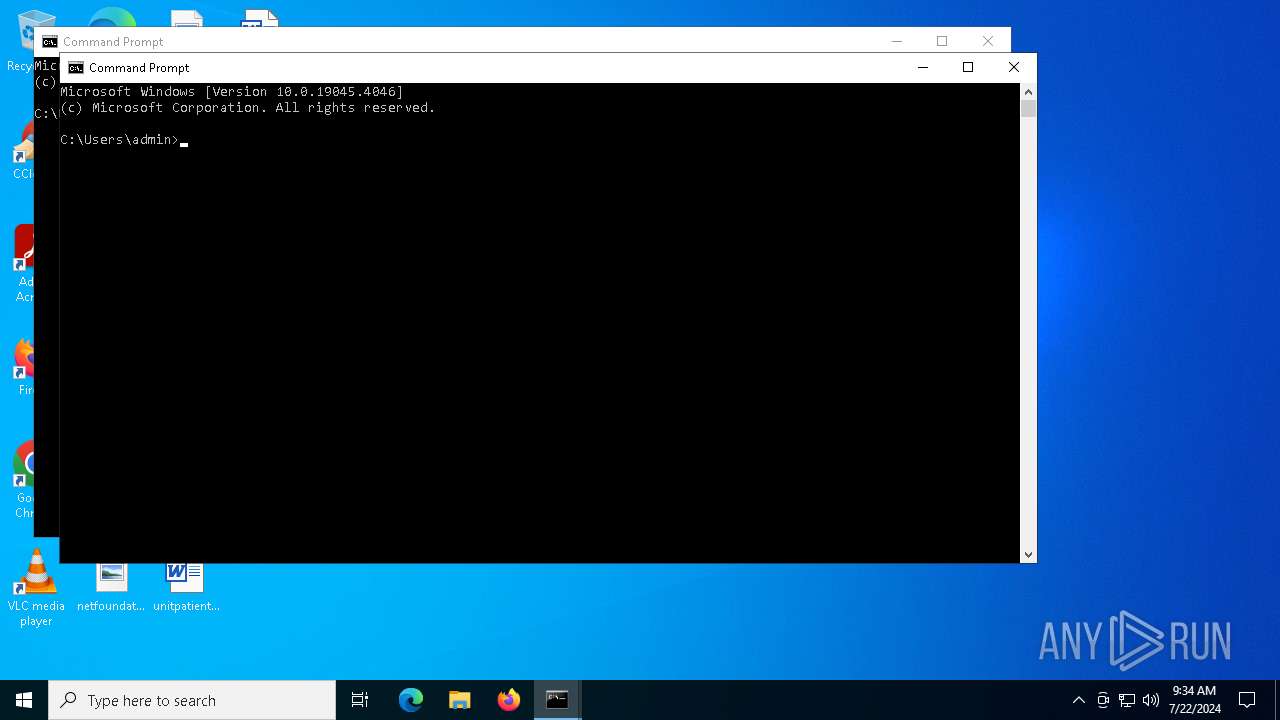
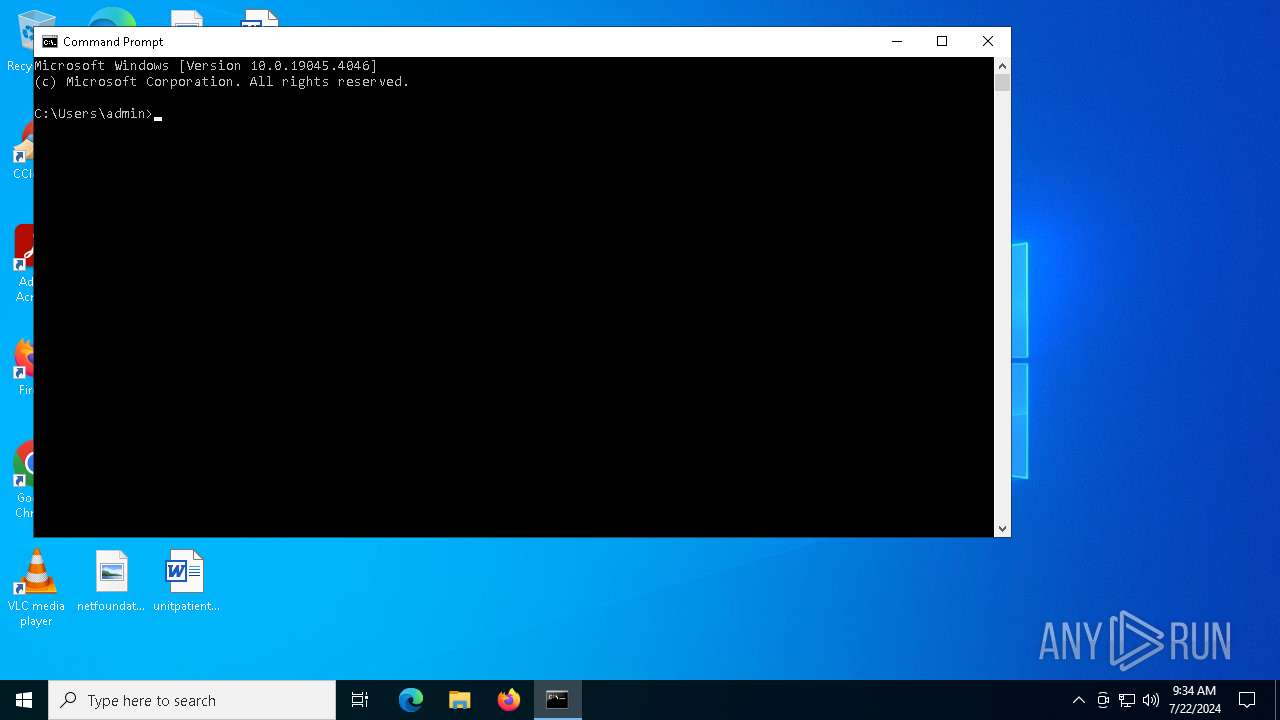
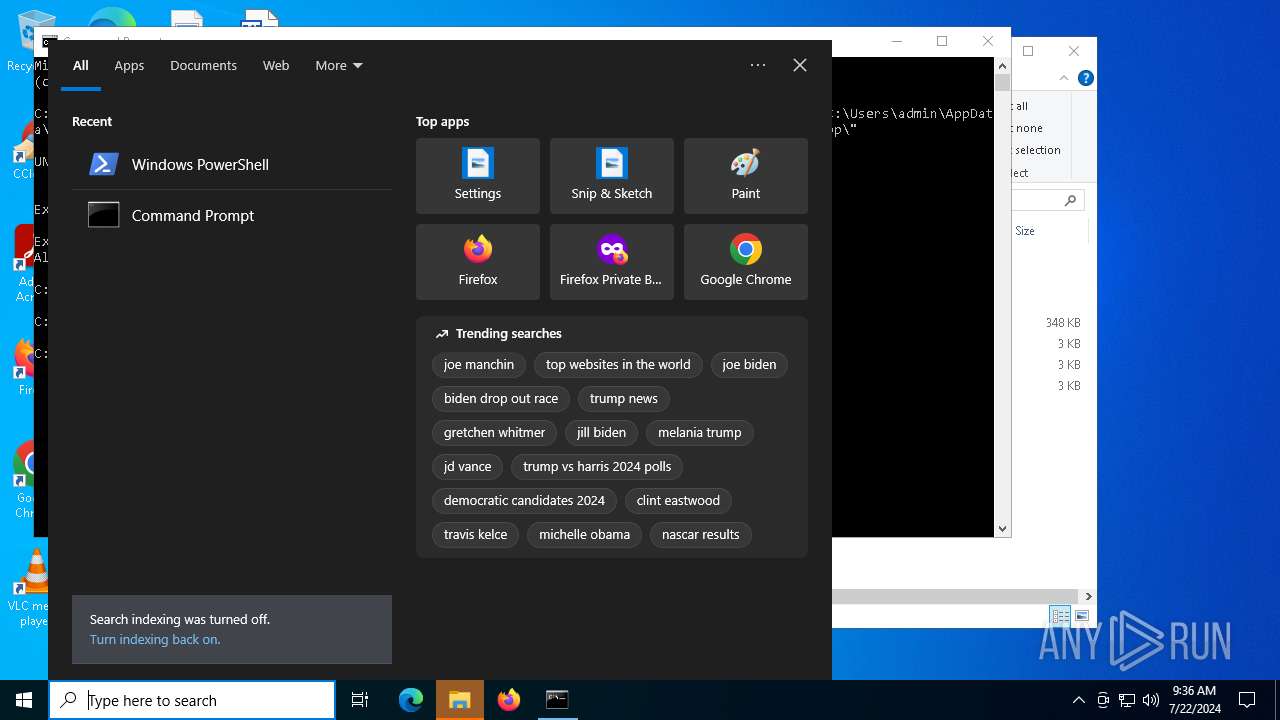
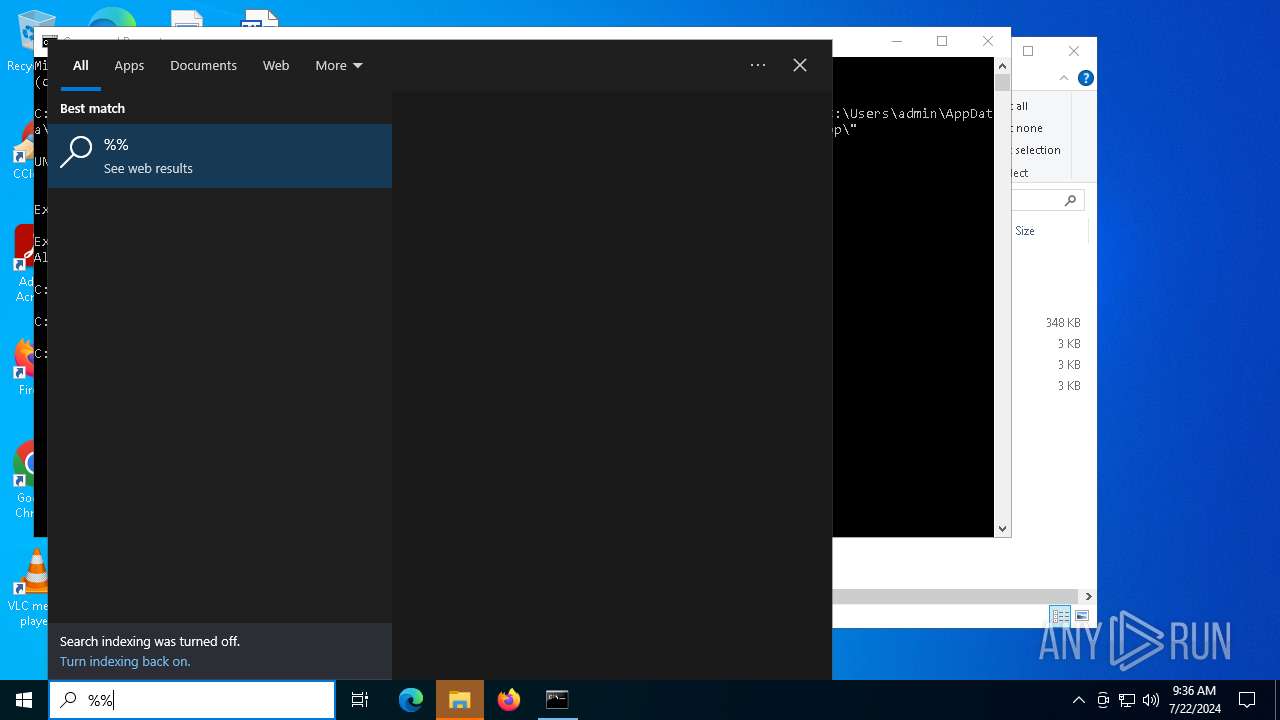
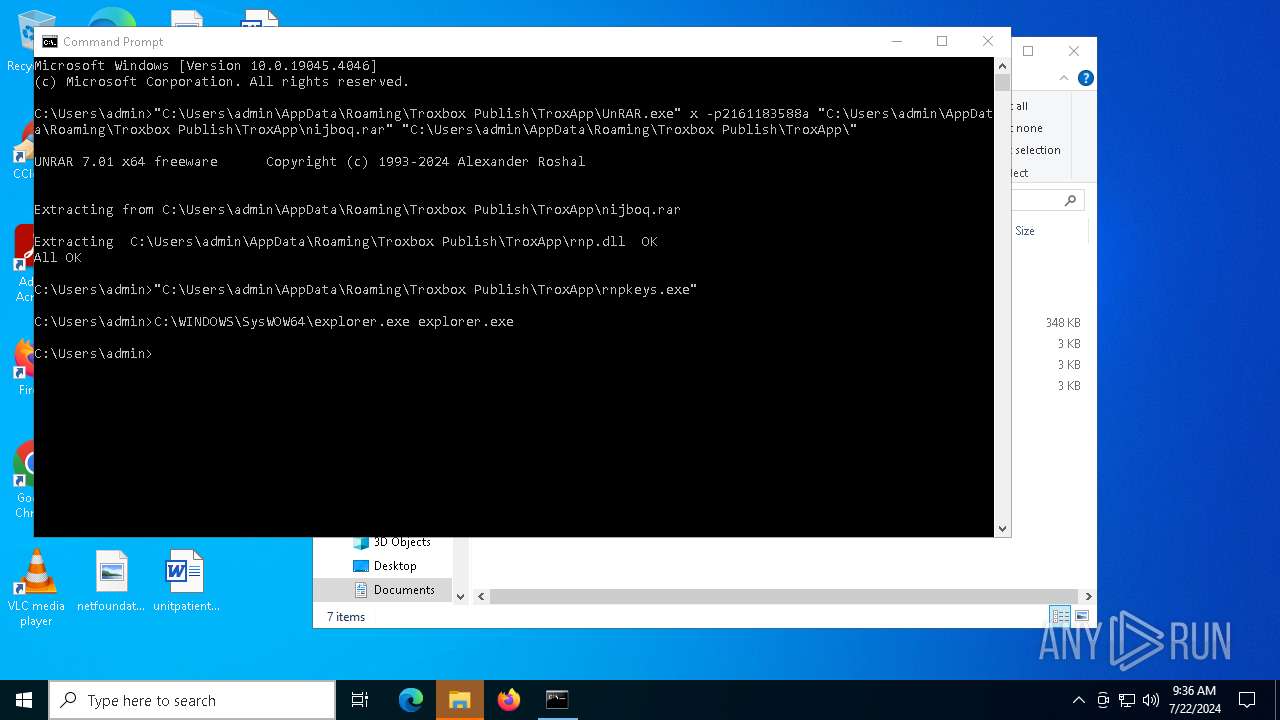
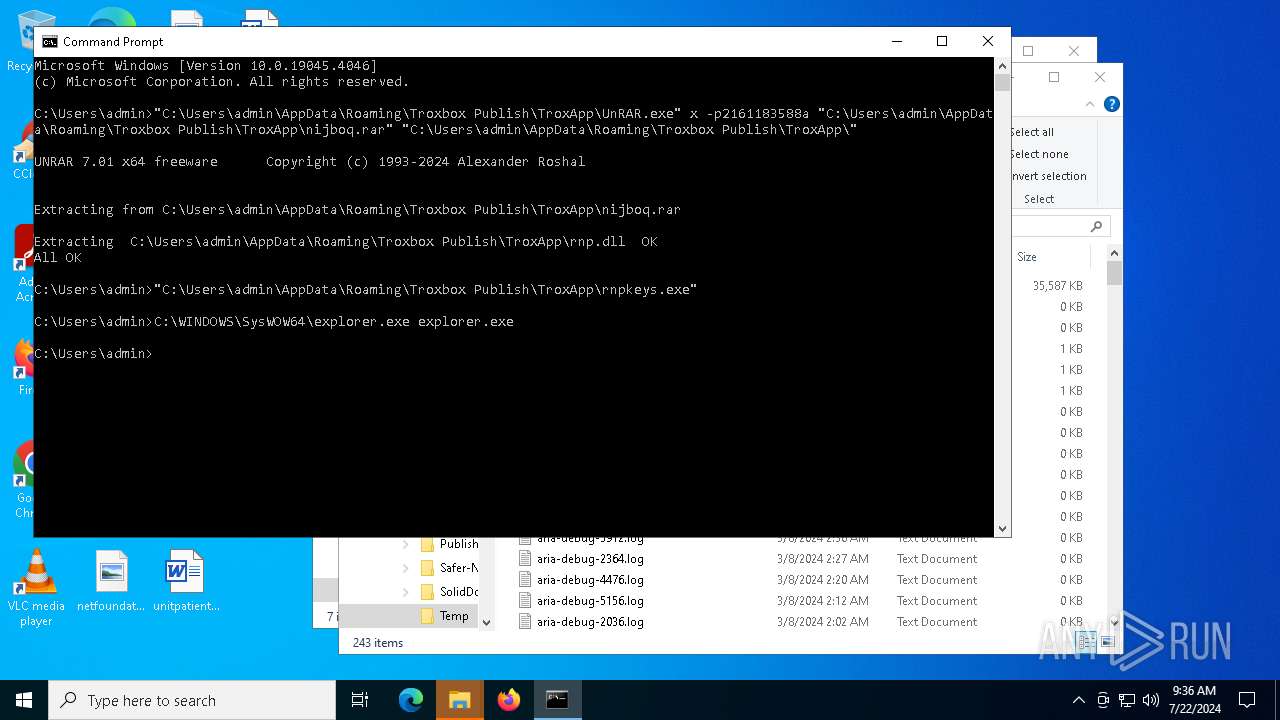
Manual execution by a user
- cmd.exe (PID: 7304)
- cmd.exe (PID: 1792)
- powershell.exe (PID: 7352)
Creates a software uninstall entry
- msiexec.exe (PID: 6968)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6692)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7352)
Disables trace logs
- powershell.exe (PID: 7588)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7588)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7588)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 7352)
- conhost.exe (PID: 908)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {A3B69905-389C-4777-92FB-F2E072712230} |
| Words: | 10 |
| Subject: | TroxApp |
| Author: | Troxbox Publish |
| LastModifiedBy: | - |
| Software: | TroxApp |
| Template: | x64;1033 |
| Comments: | This installer database contains the logic and data required to install TroxApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:07:08 17:55:21 |
| ModifyDate: | 2024:07:08 17:55:21 |
| LastPrinted: | 2024:07:08 17:55:21 |
| Pages: | 450 |
Total processes
164
Monitored processes
20
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1884 | "C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\rnpkeys.exe" | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\rnpkeys.exe | cmd.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 3221226505 Version: 115.6.0 Modules
| |||||||||||||||
| 3628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\5b3a41ed8a9a619b4aa18cef611c94b3273671ad464847cbfa600a6571c64431.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5444 | C:\WINDOWS\system32\WerFault.exe -u -p 1884 -s 188 | C:\Windows\System32\WerFault.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6692 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6968 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 214
Read events
48 952
Write events
253
Delete events
9
Modification events
| (PID) Process: | (6968) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 381B0000B3CA3C571ADCDA01 | |||
| (PID) Process: | (6968) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1107FA8588774C721E8818FA1E440E98EA69C77913155205B89B0EDF56BDB988 | |||
| (PID) Process: | (6968) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
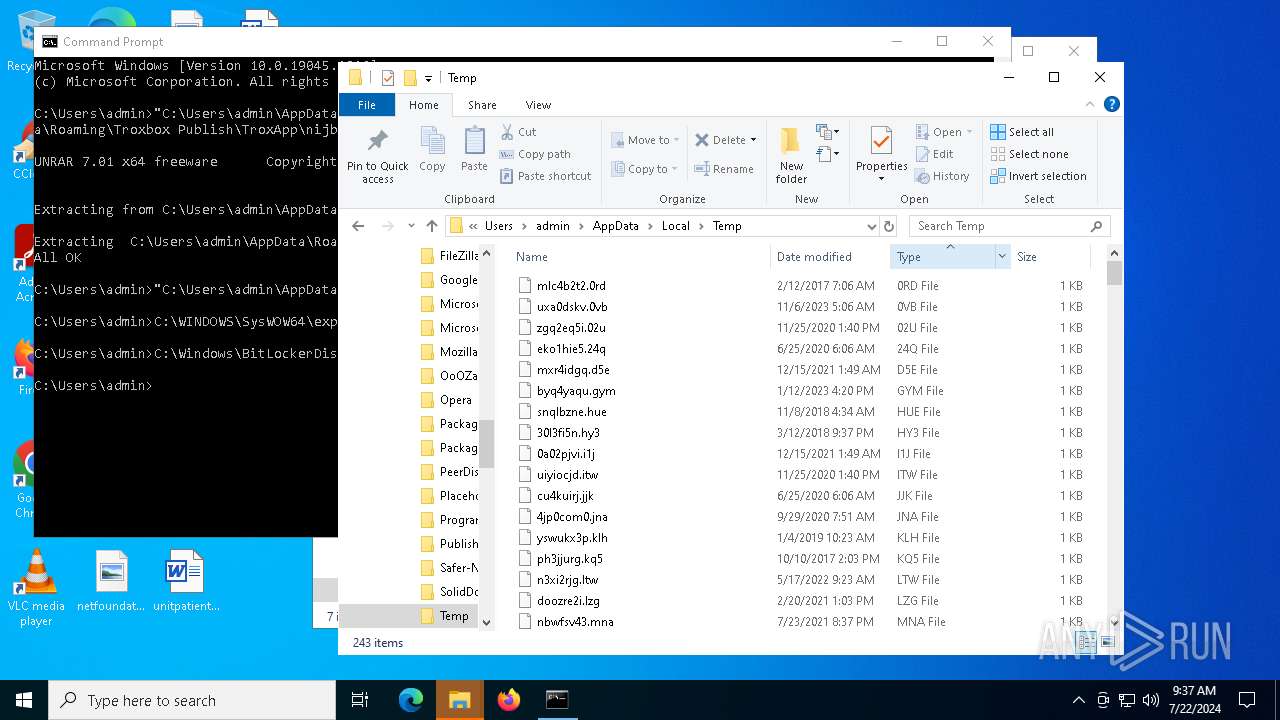
Executable files
87
Suspicious files
61
Text files
18
Unknown types
1
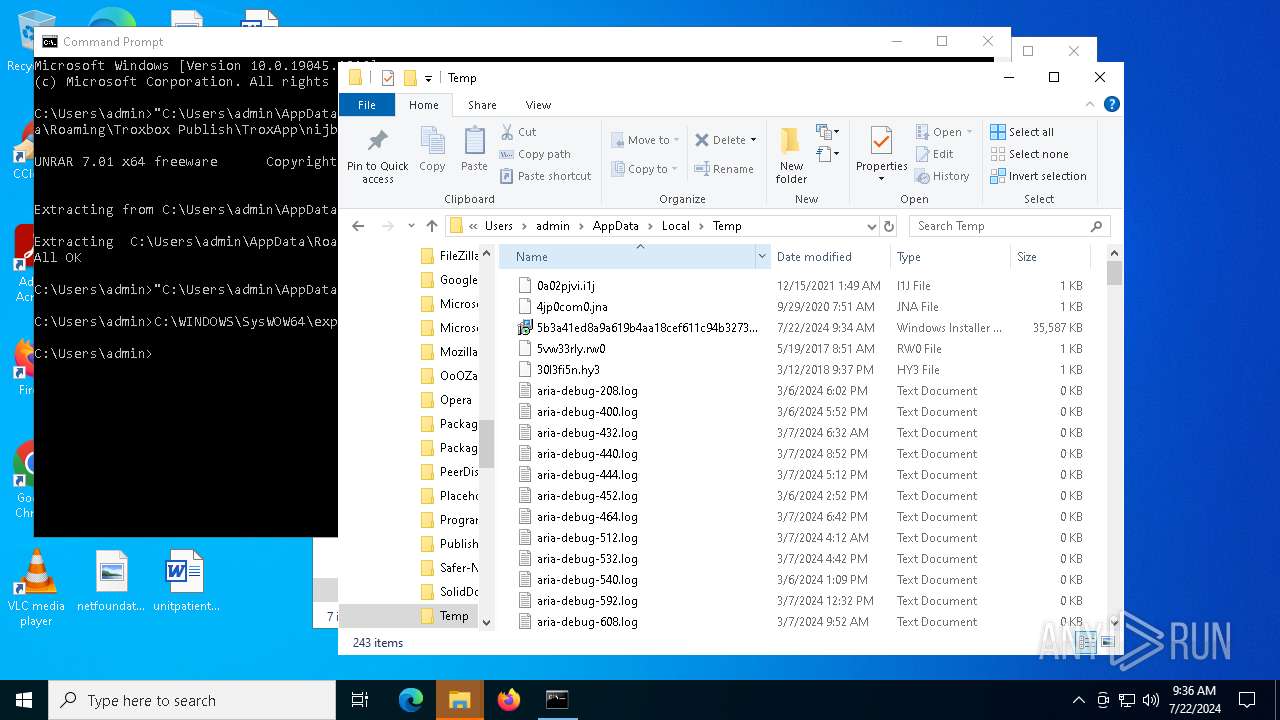
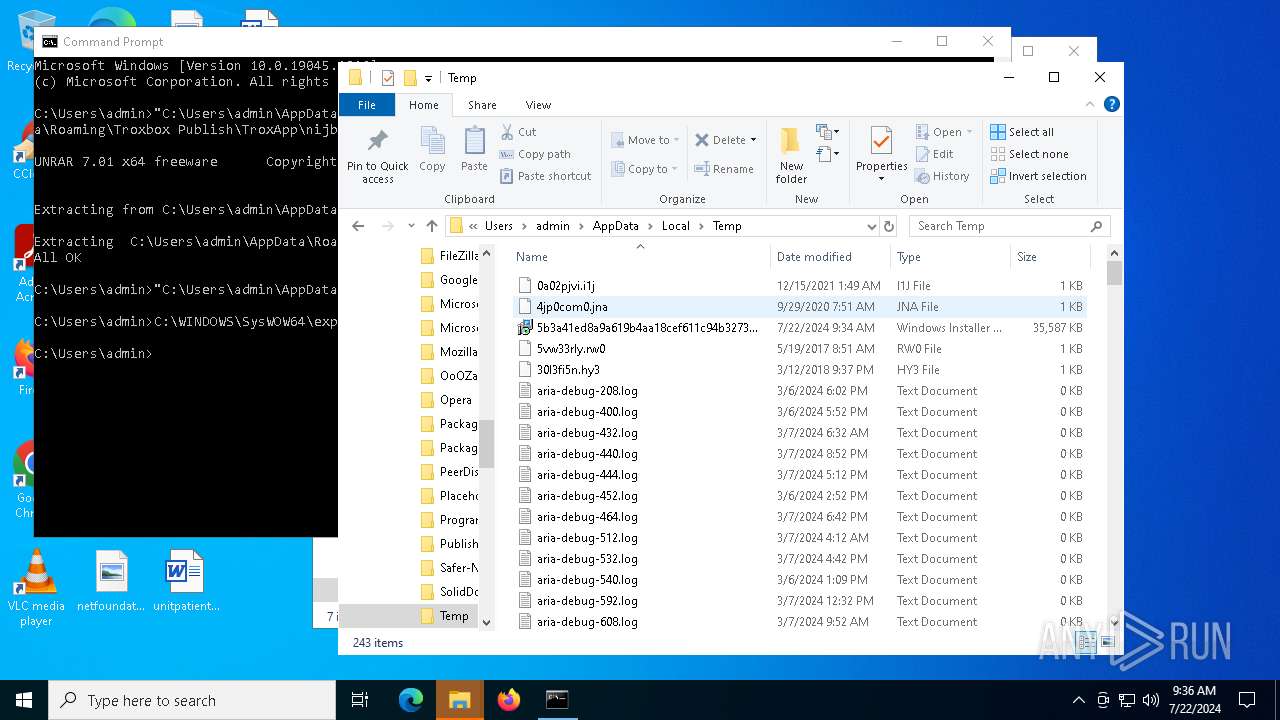
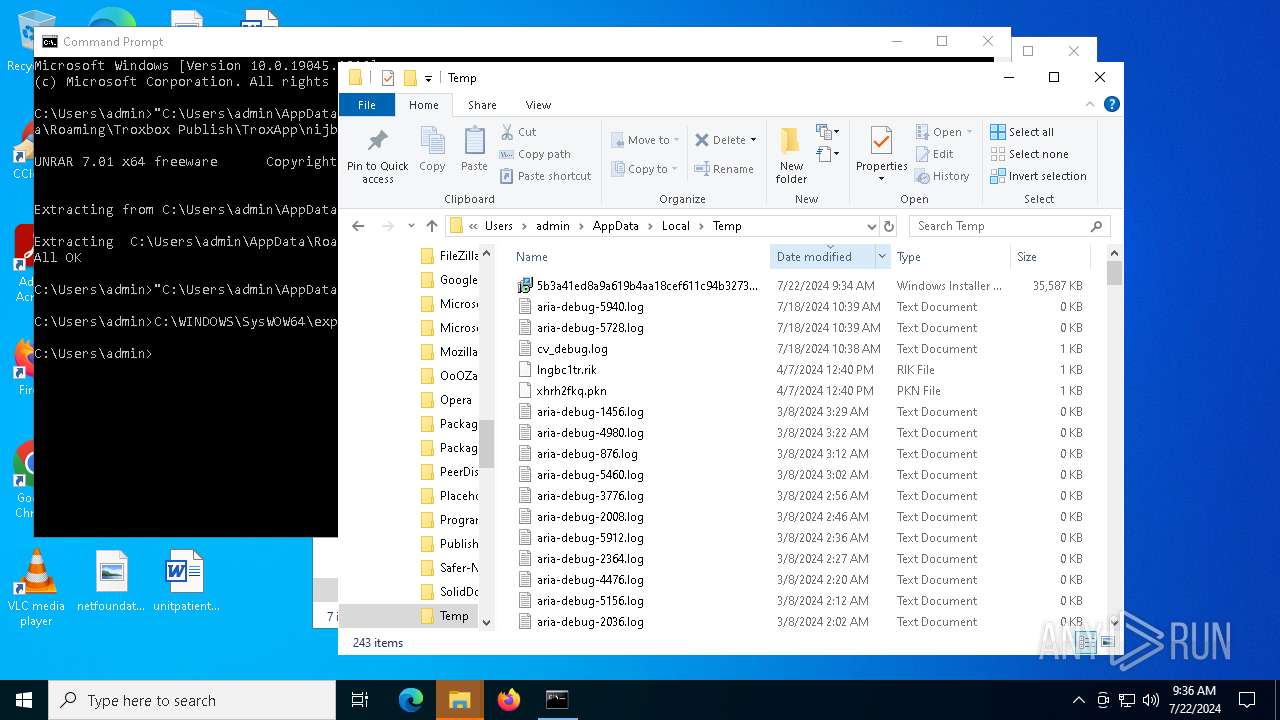
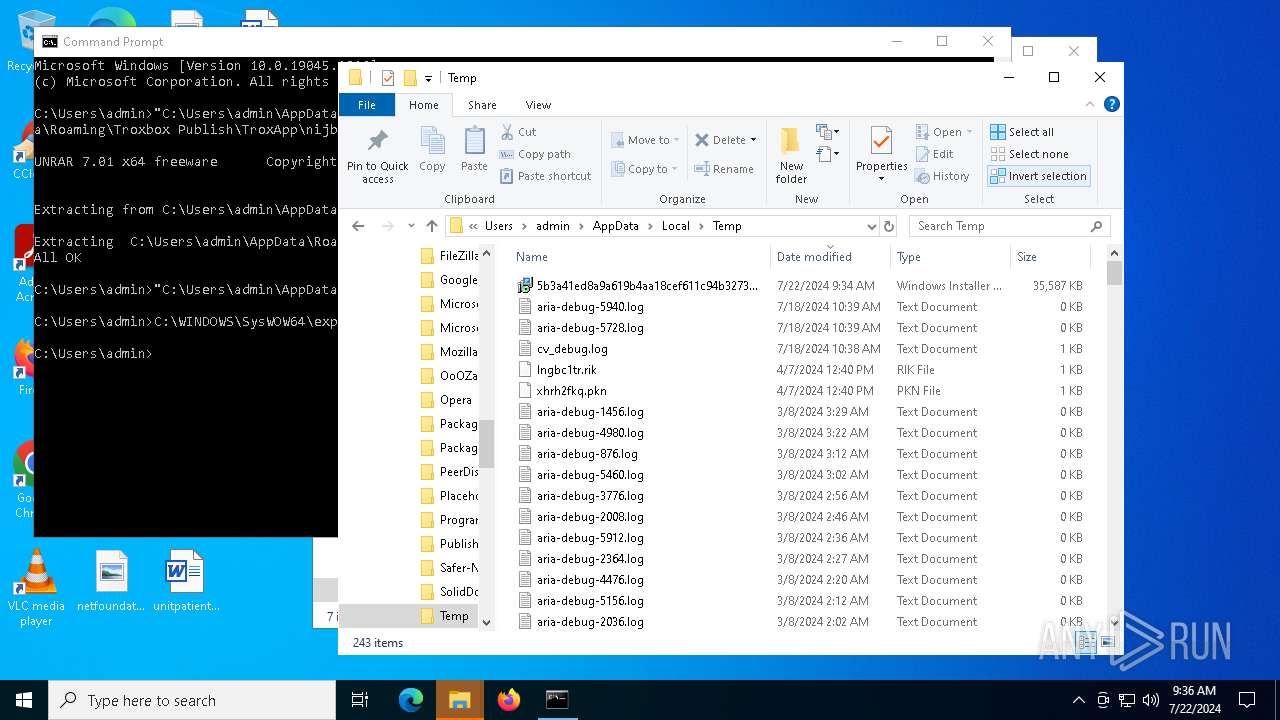
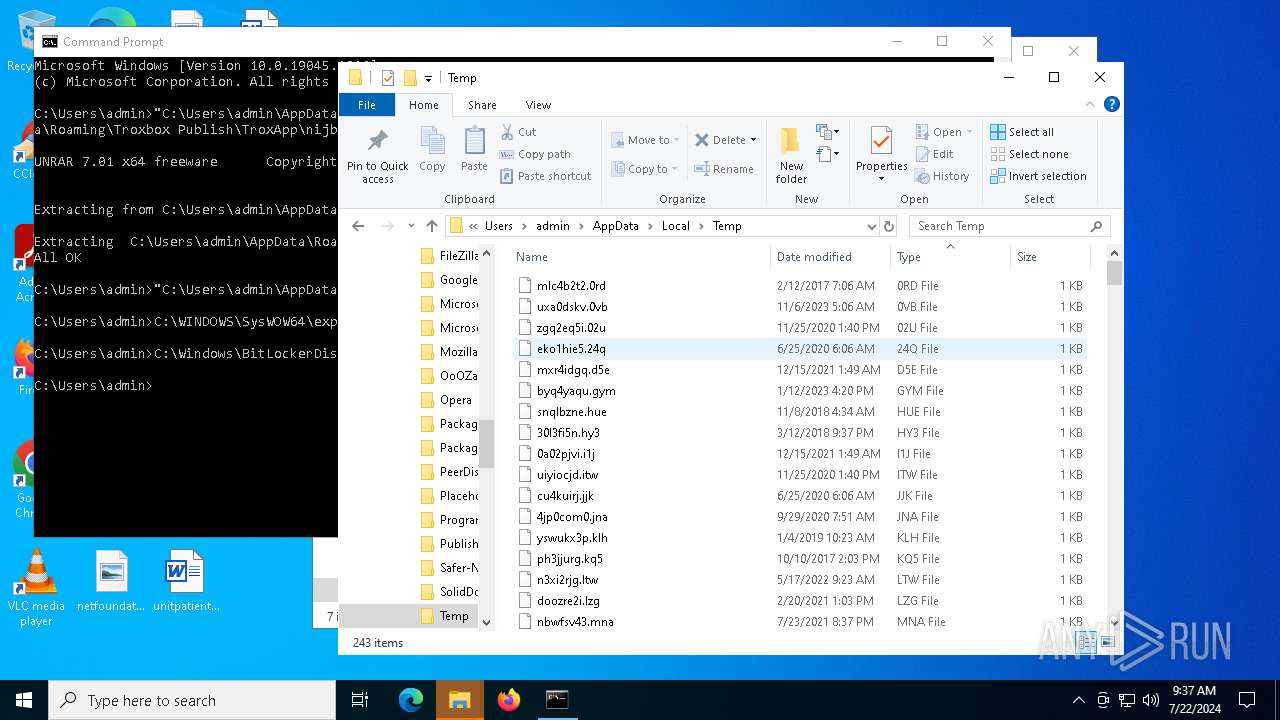
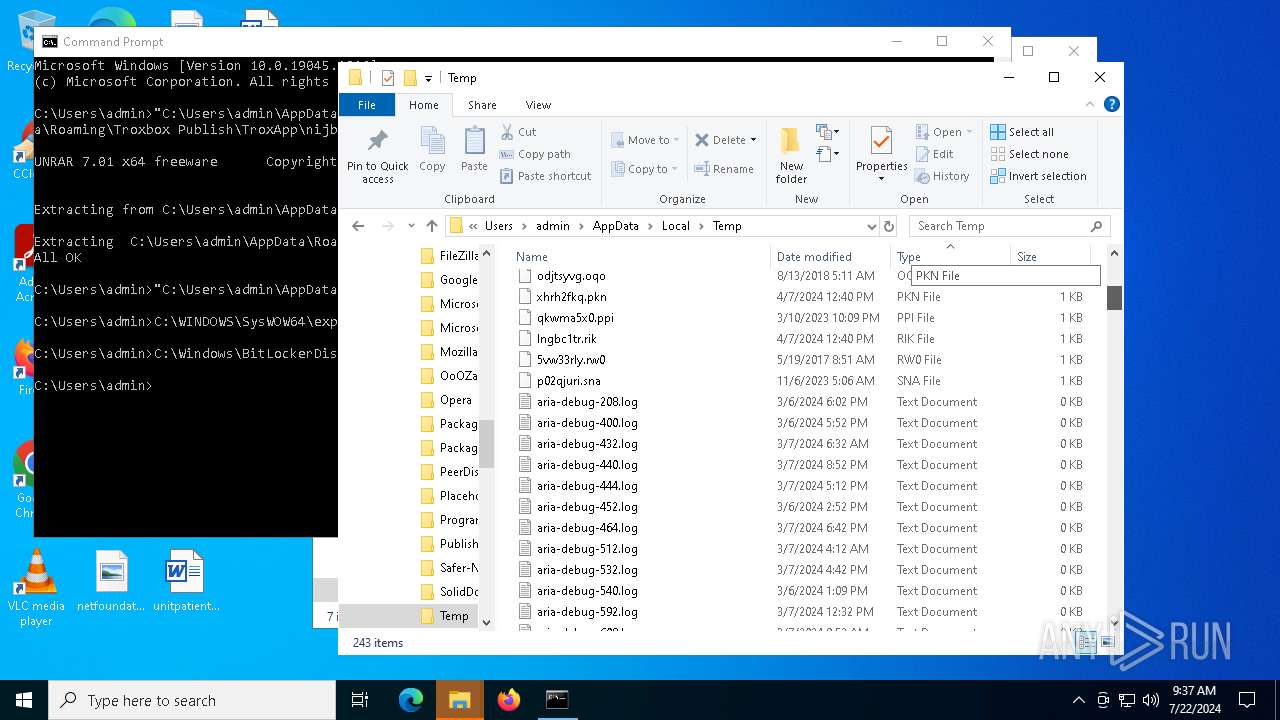
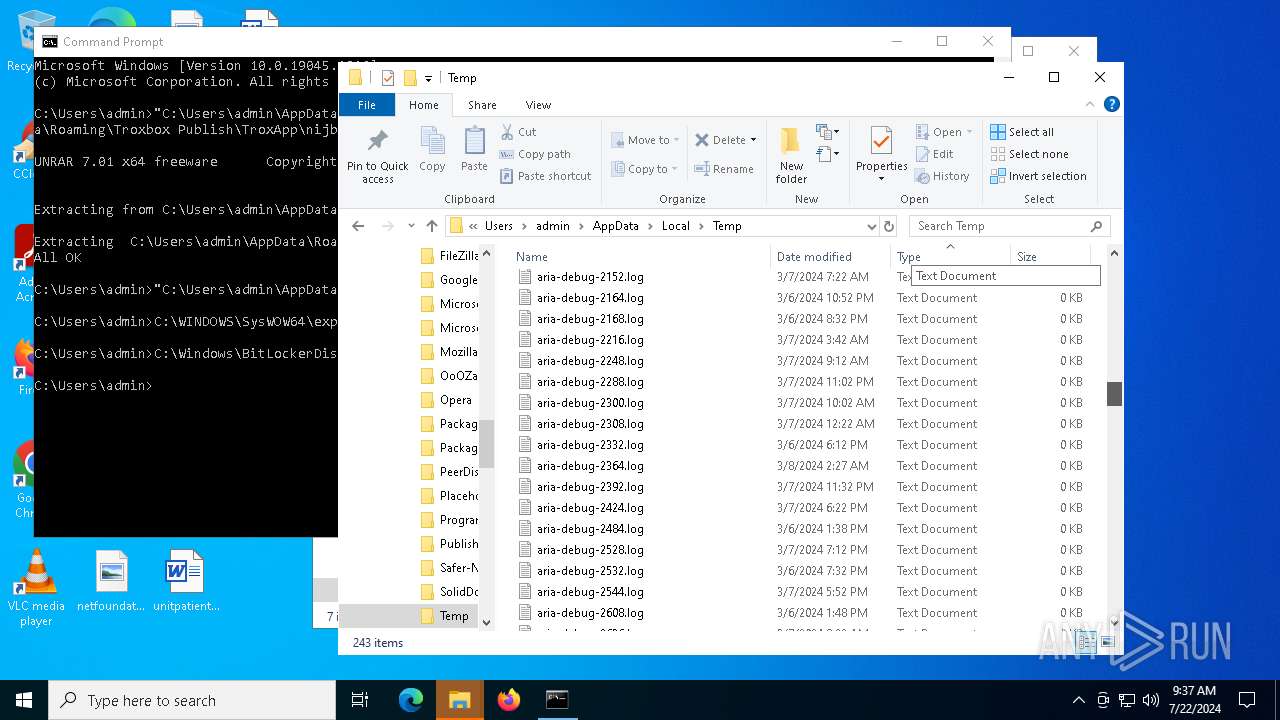
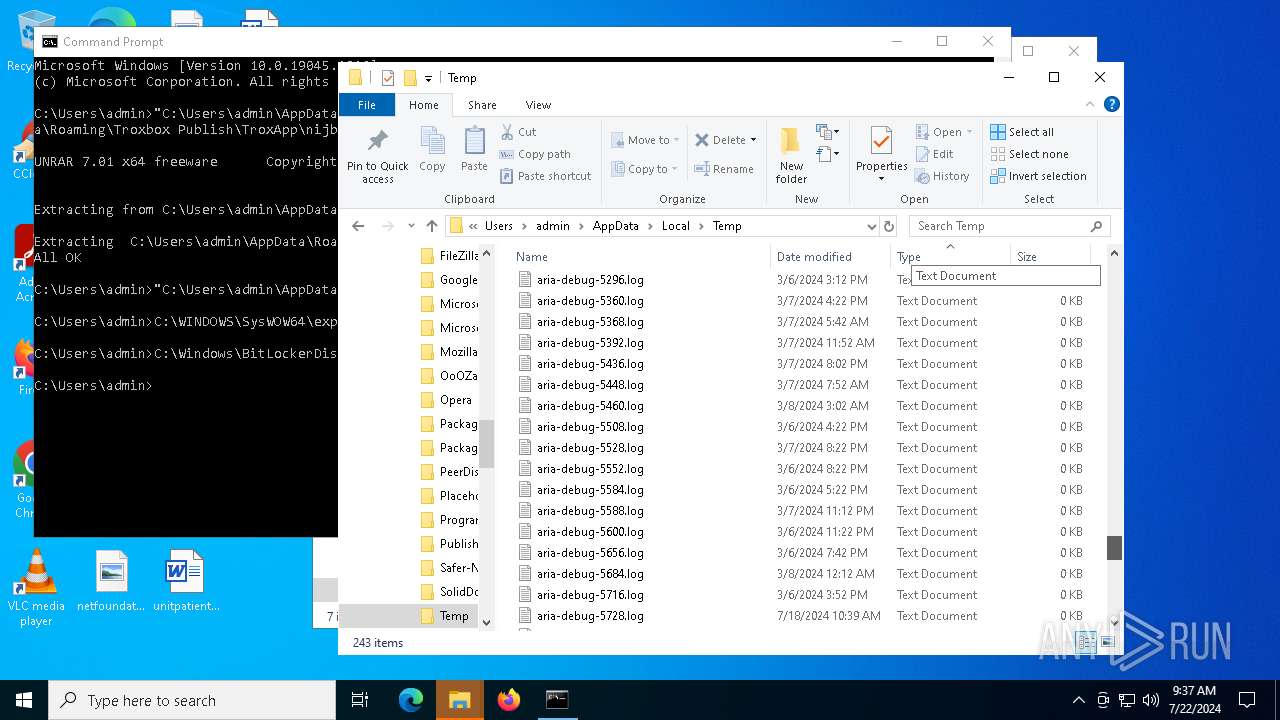
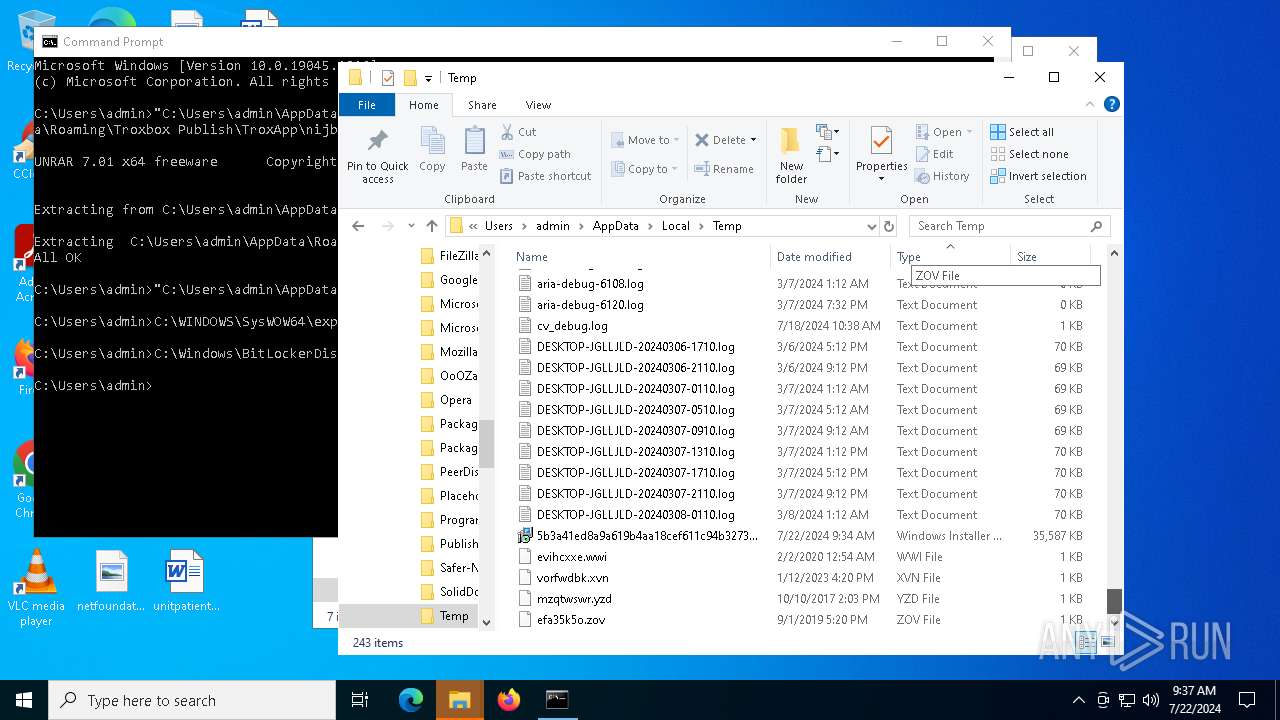
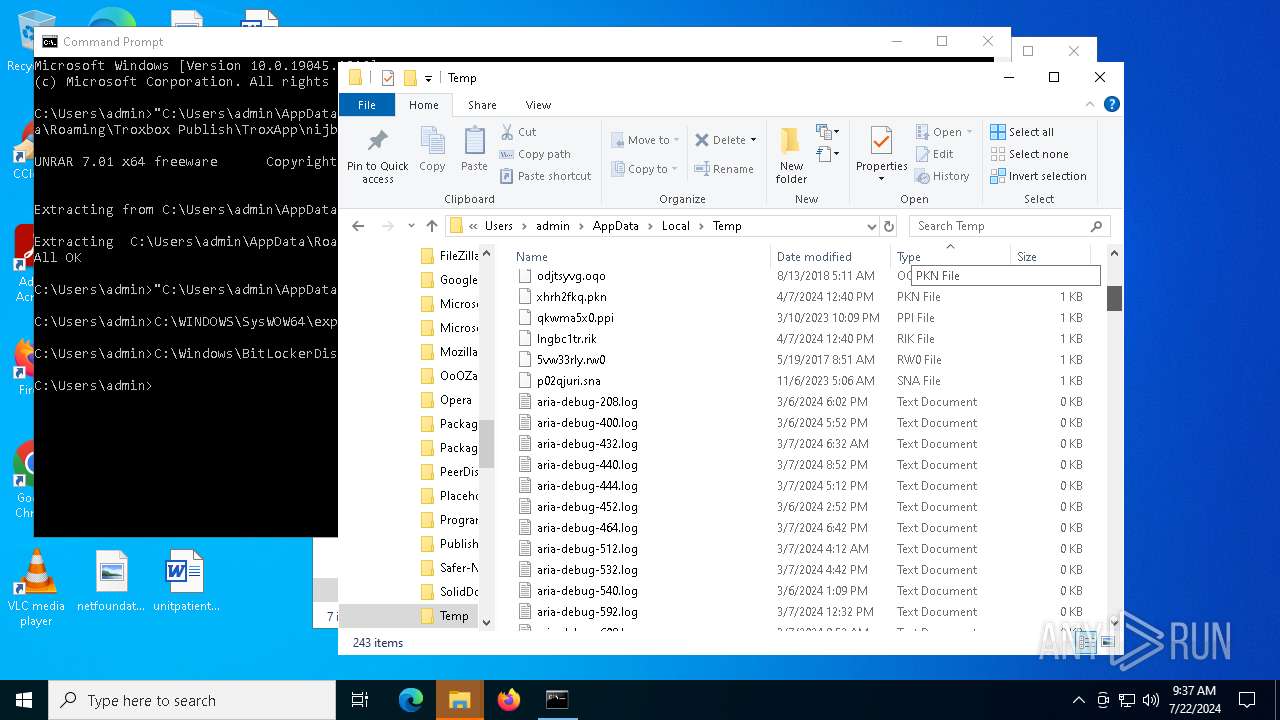
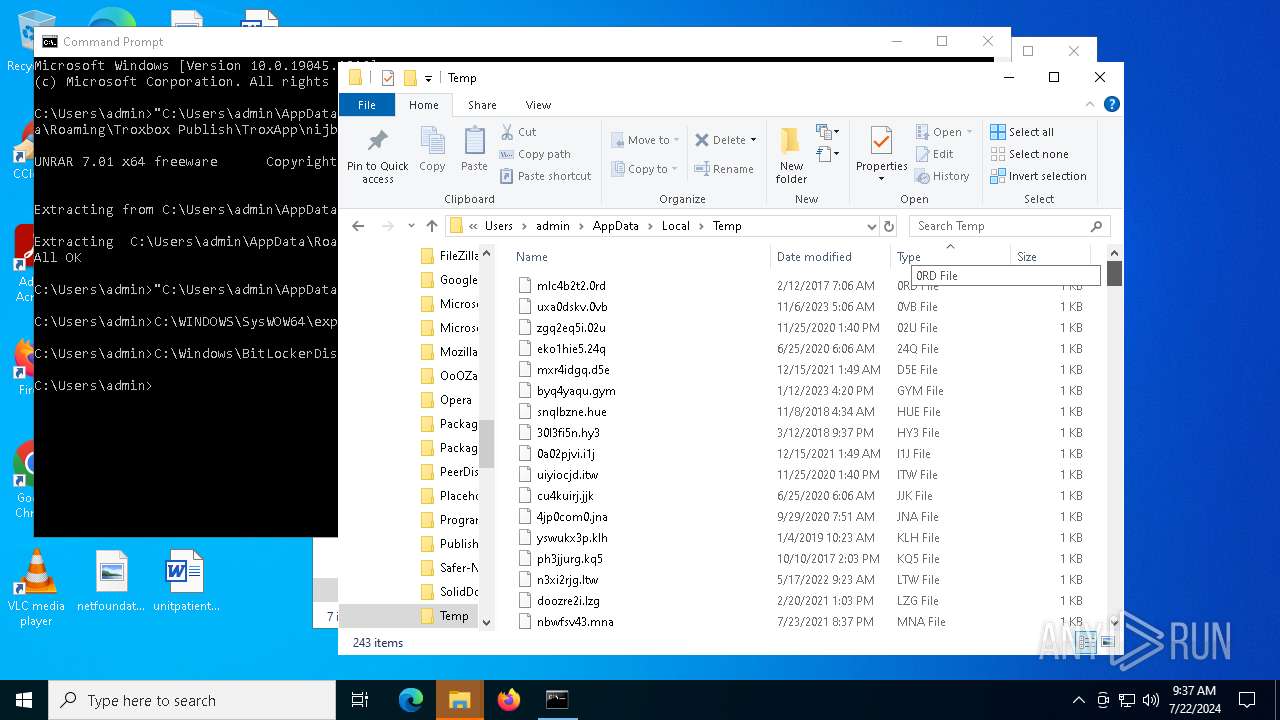
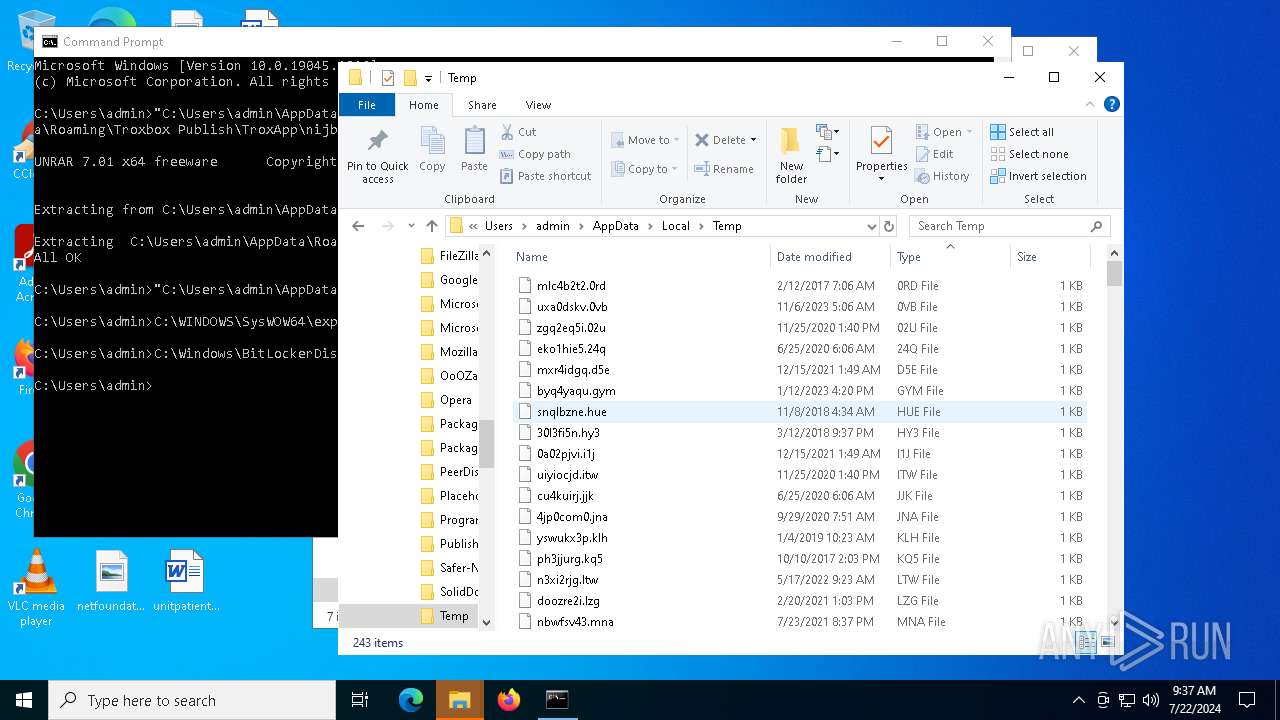
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6968 | msiexec.exe | C:\WINDOWS\Installer\42b228.msi | — | |
MD5:— | SHA256:— | |||
| 6968 | msiexec.exe | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\uiaehuv.rar | — | |
MD5:— | SHA256:— | |||
| 6968 | msiexec.exe | C:\WINDOWS\Installer\MSIB2C4.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6968 | msiexec.exe | C:\WINDOWS\Installer\MSIB4F9.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6968 | msiexec.exe | C:\WINDOWS\Installer\MSIB45B.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6968 | msiexec.exe | C:\WINDOWS\Installer\MSIB557.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6968 | msiexec.exe | C:\WINDOWS\Installer\MSIC2E9.tmp | binary | |
MD5:003EA097630E22AA82EEDD9D6F6F1559 | SHA256:E3021A5D7B755A95C15168C1B188C666C1E161DE39BBFEFB3CF9110EDFB0D381 | |||
| 6968 | msiexec.exe | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\dt_shmem.dll | executable | |
MD5:EDBAB7FE0A95FD6BB093C61AC290C408 | SHA256:7C42FFD63EE5194F514257CAEE60E0F9C5E66BB841388F33FC77446B09D6620A | |||
| 7440 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:1BFE0A81DB078EA084FF82FE545176FE | SHA256:5BA8817F13EEE00E75158BAD93076AB474A068C6B52686579E0F728FDA68499F | |||
| 6968 | msiexec.exe | C:\Users\admin\AppData\Roaming\Troxbox Publish\TroxApp\UnRAR.exe | executable | |
MD5:98CCD44353F7BC5BAD1BC6BA9AE0CD68 | SHA256:E51021F6CB20EFBD2169F2A2DA10CE1ABCA58B4F5F30FBF4BAE931E4ECAAC99B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
57
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5628 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5628 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7440 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7440 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7856 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7440 | msiexec.exe | 188.114.97.3:443 | get-license2.com | CLOUDFLARENET | NL | unknown |
7440 | msiexec.exe | 142.250.186.163:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
get-license2.com |
| unknown |
c.pki.goog |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
a-ring-fallback.msedge.net |
| unknown |
licensing.mp.microsoft.com |
| whitelisted |
t-ring-s.msedge.net |
| unknown |