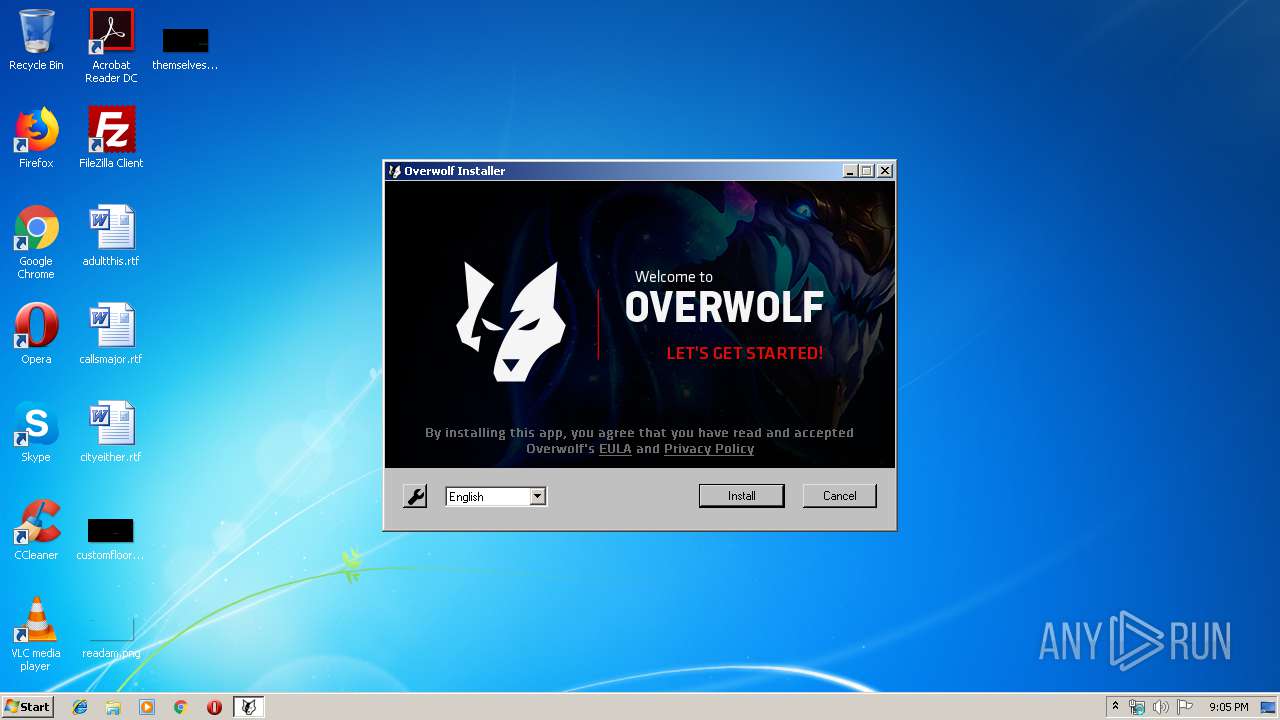
| File name: | Quarterback-OverwolfInstaller.exe |
| Full analysis: | https://app.any.run/tasks/5c1f0274-c320-4e6f-81da-2fdf56c6ff74 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2019, 20:05:11 |
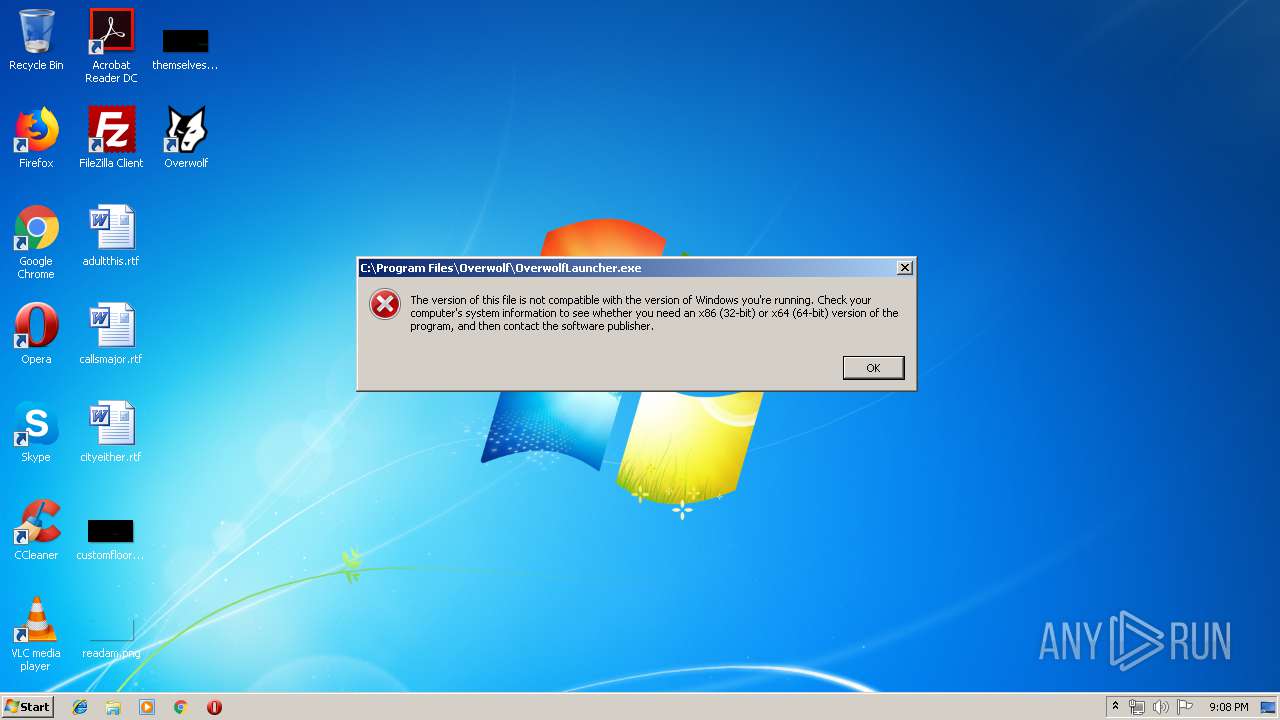
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1828046B26FCC14C48A0640FE7C47314 |
| SHA1: | 51B8DD169CA5958BD3A4C9CD9B12FA7CCAE6EDF6 |
| SHA256: | 5B2A9EF3AD440F4C649E953F48032E241B258A71B4392153265F8DC96B913A4F |
| SSDEEP: | 49152:cDgNWDMsmTZdS38WioqUxzAM7mhVGfnME5i9cB:cswD9mTC3NioqUBAN7YME56w |
MALICIOUS
Loads dropped or rewritten executable
- OWinstaller.exe (PID: 3120)
- OverwolfSetup.exe (PID: 3404)
- Quarterback-OverwolfInstaller.exe (PID: 3716)
- Quarterback-OverwolfInstaller.exe (PID: 3756)
Changes settings of System certificates
- OWinstaller.exe (PID: 3120)
- OverwolfSetup.exe (PID: 3404)
Loads the Task Scheduler COM API
- OWinstaller.exe (PID: 3120)
Changes the autorun value in the registry
- OWinstaller.exe (PID: 3120)
Application was dropped or rewritten from another process
- OWinstaller.exe (PID: 3120)
SUSPICIOUS
Executable content was dropped or overwritten
- Quarterback-OverwolfInstaller.exe (PID: 3716)
- OWinstaller.exe (PID: 3120)
- OverwolfSetup.exe (PID: 3404)
- Quarterback-OverwolfInstaller.exe (PID: 3756)
Reads internet explorer settings
- OWinstaller.exe (PID: 3120)
Adds / modifies Windows certificates
- OverwolfSetup.exe (PID: 3404)
- OWinstaller.exe (PID: 3120)
Creates a software uninstall entry
- OverwolfSetup.exe (PID: 3404)
Creates files in the program directory
- OWinstaller.exe (PID: 3120)
- OverwolfSetup.exe (PID: 3404)
Modifies the open verb of a shell class
- OverwolfSetup.exe (PID: 3404)
Application launched itself
- Quarterback-OverwolfInstaller.exe (PID: 3716)
INFO
Dropped object may contain Bitcoin addresses
- OverwolfSetup.exe (PID: 3404)
- OWinstaller.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.131.0.3 |
| ProductVersionNumber: | 2.131.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | qlub.gg |
| FileVersion: | 2.131.0.3 |
| LegalCopyright: | Copyright (C) 2019 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | qlub.gg |
| ProductVersion: | 2.131.0.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:44 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | qlub.gg |
| FileVersion: | 2.131.0.3 |
| LegalCopyright: | Copyright (C) 2019 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | qlub.gg |
| ProductVersion: | 2.131.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000606C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45707 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94596 |
.data | 0x0000A000 | 0x0002AF98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79535 |
.ndata | 0x00035000 | 0x00013000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00048000 | 0x00006A50 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.71265 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27028 | 773 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.92361 | 9369 | UNKNOWN | English - United States | RT_ICON |
3 | 3.80301 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.75459 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.44608 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
43
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3120 | "C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\OWinstaller.exe" Extension=bekkfkjdkbginihlkpegcpomdeonddjhgbhgaaeh&Name=Quarterback&Sel=1 /UAC:20128 /NCRC -exepath C:\Users\admin\AppData\Local\Temp\Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\OWinstaller.exe | Quarterback-OverwolfInstaller.exe | ||||||||||||
User: admin Company: Overwolf Integrity Level: HIGH Description: Overwolf Installer Exit code: 3221225547 Version: 2.133.0.2 Modules
| |||||||||||||||
| 3404 | "C:\ProgramData\Overwolf\Setup\0.134.0.26\OverwolfSetup.exe" /S "/TargetDir=C:\Program Files\Overwolf\" -ignoredotnet | C:\ProgramData\Overwolf\Setup\0.134.0.26\OverwolfSetup.exe | OWinstaller.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: HIGH Description: Overwolf Exit code: 0 Version: 0.134.0.26 Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Local\Temp\Quarterback-OverwolfInstaller.exe" | C:\Users\admin\AppData\Local\Temp\Quarterback-OverwolfInstaller.exe | explorer.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: MEDIUM Description: qlub.gg Exit code: 1223 Version: 2.131.0.3 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\Temp\Quarterback-OverwolfInstaller.exe" /UAC:20128 /NCRC | C:\Users\admin\AppData\Local\Temp\Quarterback-OverwolfInstaller.exe | Quarterback-OverwolfInstaller.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: HIGH Description: qlub.gg Exit code: 1223 Version: 2.131.0.3 Modules
| |||||||||||||||
Total events
1 601
Read events
1 491
Write events
110
Delete events
0
Modification events
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Quarterback-OverwolfInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Quarterback-OverwolfInstaller_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
237
Suspicious files
31
Text files
278
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\OWInstaller.exe | executable | |
MD5:— | SHA256:— | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\app\index.html | html | |
MD5:— | SHA256:— | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\app\_locales\ko\messages.json | html | |
MD5:— | SHA256:— | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\app\_locales\pt\messages.json | html | |
MD5:— | SHA256:— | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\app\_locales\en\messages.json | html | |
MD5:— | SHA256:— | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\app\manifest.json | text | |
MD5:— | SHA256:— | |||
| 3716 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse9C45.tmp\System.dll | executable | |
MD5:7399323923E3946FE9140132AC388132 | SHA256:5A1C20A3E2E2EB182976977669F2C5D9F3104477E98F74D69D2434E79B92FDC3 | |||
| 3716 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse9C45.tmp\UserInfo.dll | executable | |
MD5:9301577FF4D229347FE33259B43EF3B2 | SHA256:090C4BC8DC534E97B3877BD5115EB58B3E181495F29F231479F540BAB5C01EDC | |||
| 3756 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsrA29E.tmp\nsis7z.dll | executable | |
MD5:— | SHA256:— | |||
| 3716 | Quarterback-OverwolfInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse9C45.tmp\uac.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
25
DNS requests
16
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
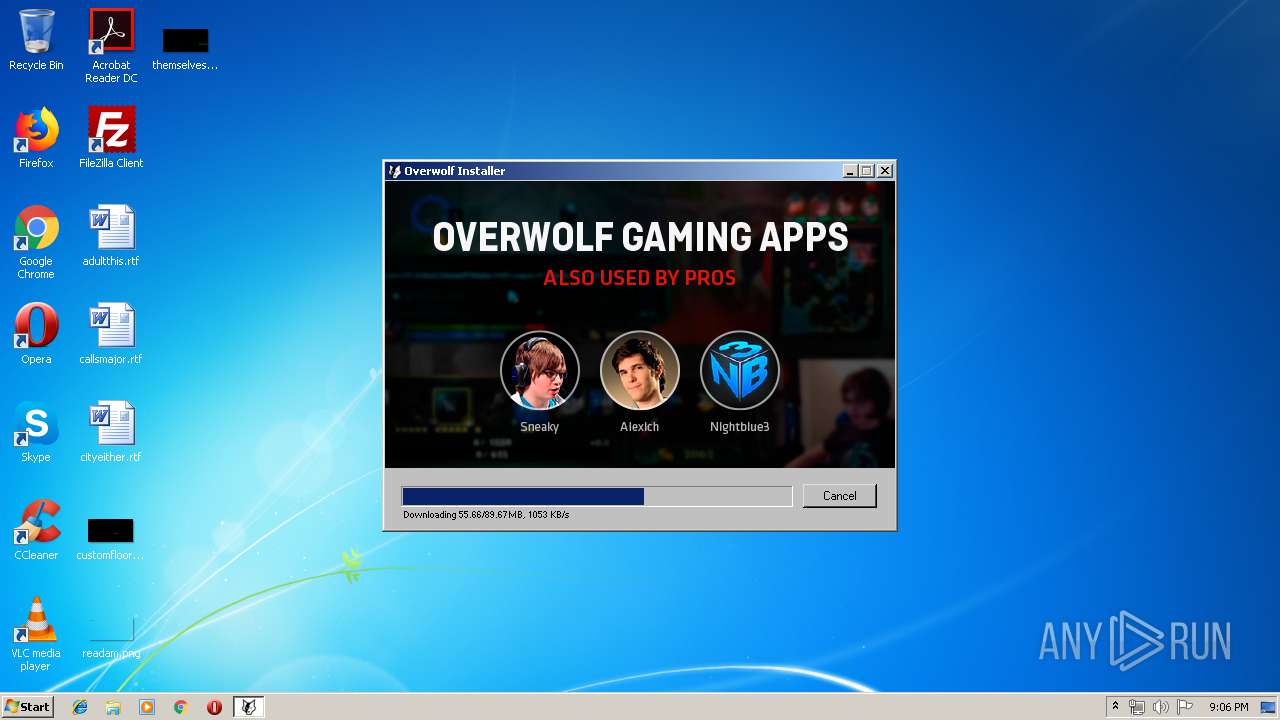
3120 | OWinstaller.exe | GET | 200 | 2.16.106.193:80 | http://setup.overwolf.com/0.134.0.26/OverwolfSetup.7z | unknown | compressed | 89.6 Mb | suspicious |
3120 | OWinstaller.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=&PartnerID=0&Name=Manual_Installer_Launched&Value=1&UserName=&GameSessionId=&owver=0.133.0.4&MUID=a743f657-82e2-4213-822f-fb2c66c8fdcf | US | text | 2 b | malicious |
3120 | OWinstaller.exe | GET | 200 | 172.217.16.206:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=579508034&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=284343452&utmr=/&utmp=/&utmac=UA-80584726-1&utmcc=__utma%3D0.1441004695.1567886730.1567886730.1567886730.2%3B%2B__utmz%3D0.1567886730.1.1.utmcsr%3D(direct)%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5(Funnel2*Installer%20Launched*2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client)()&gaq=1&utmt=event | US | image | 35 b | whitelisted |
3120 | OWinstaller.exe | GET | 200 | 143.204.214.59:80 | http://content.overwolf.com/Installer/Overwolf/default/InstallerServerPage.html?langid=en&pid=0&state=progress | US | html | 754 b | whitelisted |
3120 | OWinstaller.exe | GET | 200 | 172.217.16.206:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=77857047&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=57647796&utmr=/&utmp=/&utmac=UA-80584726-1&utmcc=__utma%3D0.1089339689.1567886730.1567886730.1567886730.2%3B%2B__utmz%3D0.1567886730.1.1.utmcsr%3D(direct)%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5(Funnel2*Installer%20Launched*2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client)()&gaq=1&utmt=event | US | image | 35 b | whitelisted |
3120 | OWinstaller.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=&PartnerID=0&Name=Manual_Funnel2_Installer_Launched&Value=1&UserName=&GameSessionId=&owver=0.133.0.4&MUID=a743f657-82e2-4213-822f-fb2c66c8fdcf | US | text | 2 b | malicious |
3756 | Quarterback-OverwolfInstaller.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?Name=installer_uac_action&Value=1&Extra=%5b%7b%22Name%22%3a%22installer_version%22%2c%22Value%22%3a%222.131.0.3%22%7d%5d | US | text | 2 b | malicious |
3120 | OWinstaller.exe | GET | 200 | 143.204.208.42:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3120 | OWinstaller.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=&PartnerID=0&Name=Manual_Installer_Launched&Value=1&UserName=&GameSessionId=&owver=0.133.0.4&MUID=a743f657-82e2-4213-822f-fb2c66c8fdcf | US | text | 2 b | malicious |
3120 | OWinstaller.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=&PartnerID=0&Name=installer_webbrowser_init&Value=1&UserName=&GameSessionId=&Extra=%255b%257b%2522Name%2522%253a%2522ver%2522%252c%2522Value%2522%253a%25228.0.7601.17514%2522%257d%255d&owver=0.133.0.4&MUID=a743f657-82e2-4213-822f-fb2c66c8fdcf | US | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | Quarterback-OverwolfInstaller.exe | 69.16.175.42:80 | analyticsnew.overwolf.com | Highwinds Network Group, Inc. | US | malicious |
3120 | OWinstaller.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3120 | OWinstaller.exe | 172.217.16.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3120 | OWinstaller.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3120 | OWinstaller.exe | 54.225.197.63:443 | api.overwolf.com | Amazon.com, Inc. | US | unknown |
3120 | OWinstaller.exe | 172.217.21.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3120 | OWinstaller.exe | 143.204.208.204:80 | gamelist.overwolf.com | — | US | unknown |
3120 | OWinstaller.exe | 143.204.214.59:80 | content.overwolf.com | — | US | suspicious |
3120 | OWinstaller.exe | 143.204.214.44:80 | content.overwolf.com | — | US | suspicious |
3120 | OWinstaller.exe | 2.16.106.211:80 | apps4.overwolf.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analyticsnew.overwolf.com |
| malicious |
www.google-analytics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.overwolf.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.overwolf.com |
| whitelisted |
setup.overwolf.com |
| suspicious |
content.overwolf.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | Quarterback-OverwolfInstaller.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3756 | Quarterback-OverwolfInstaller.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
3404 | OverwolfSetup.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3404 | OverwolfSetup.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
3404 | OverwolfSetup.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3404 | OverwolfSetup.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |