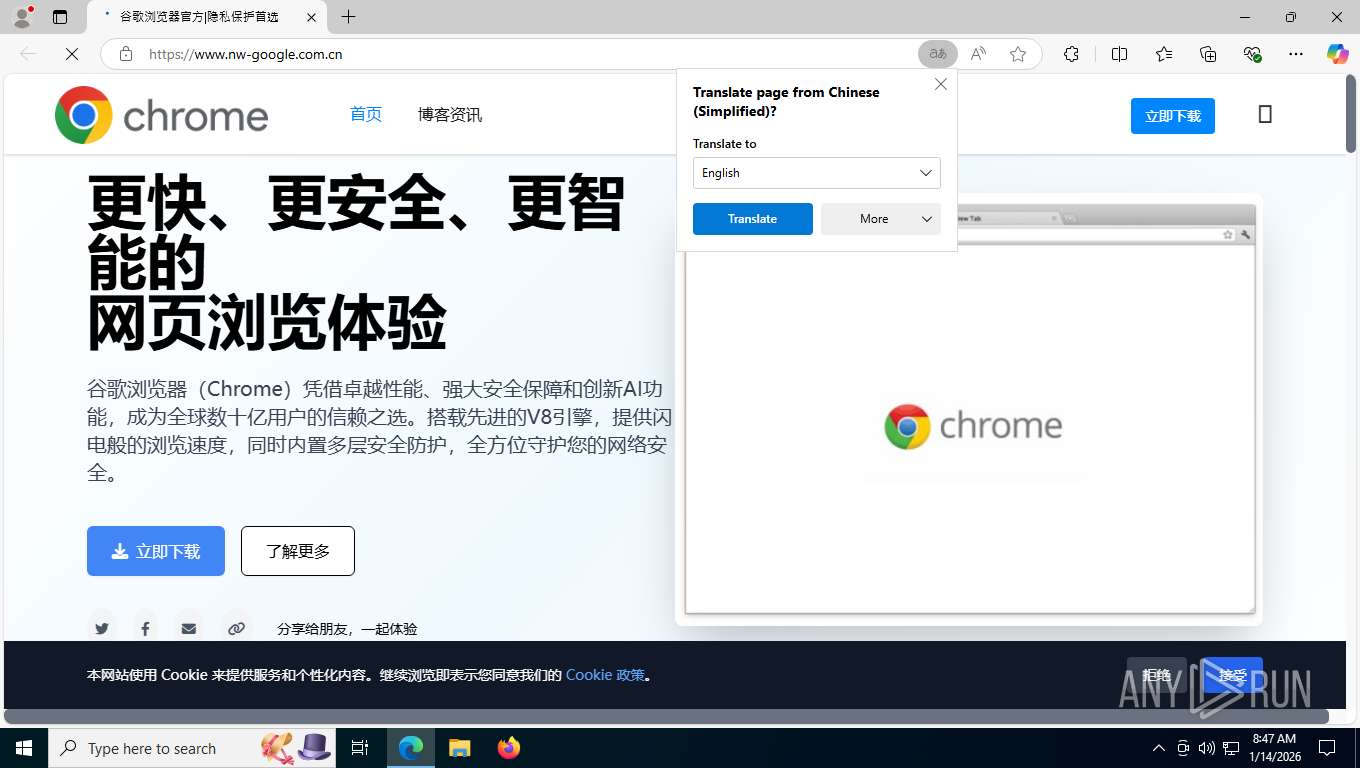
| URL: | www.nw-google.com.cn |
| Full analysis: | https://app.any.run/tasks/59fba7a1-81b2-4d68-a8e3-cf42350c800d |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2026, 13:46:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ECF60B0843C9FC62254FCC81B820FE3E |
| SHA1: | D2817F6728ECDB4E42C4734D2E646CEE5273AFCE |
| SHA256: | 5B14863510745A7F8A4CBBC8607DDDEEE4AB83AFAB3108DAE86DBDF7514BA8BF |
| SSDEEP: | 3:EuLH:VLH |
MALICIOUS
Adds path to the Windows Defender exclusion list
- irsetup.exe (PID: 6724)
- cmd.exe (PID: 8072)
Bypass execution policy to execute commands
- powershell.exe (PID: 7248)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8072)
Run PowerShell with an invisible window
- powershell.exe (PID: 7248)
Changes Windows Defender settings
- cmd.exe (PID: 8072)
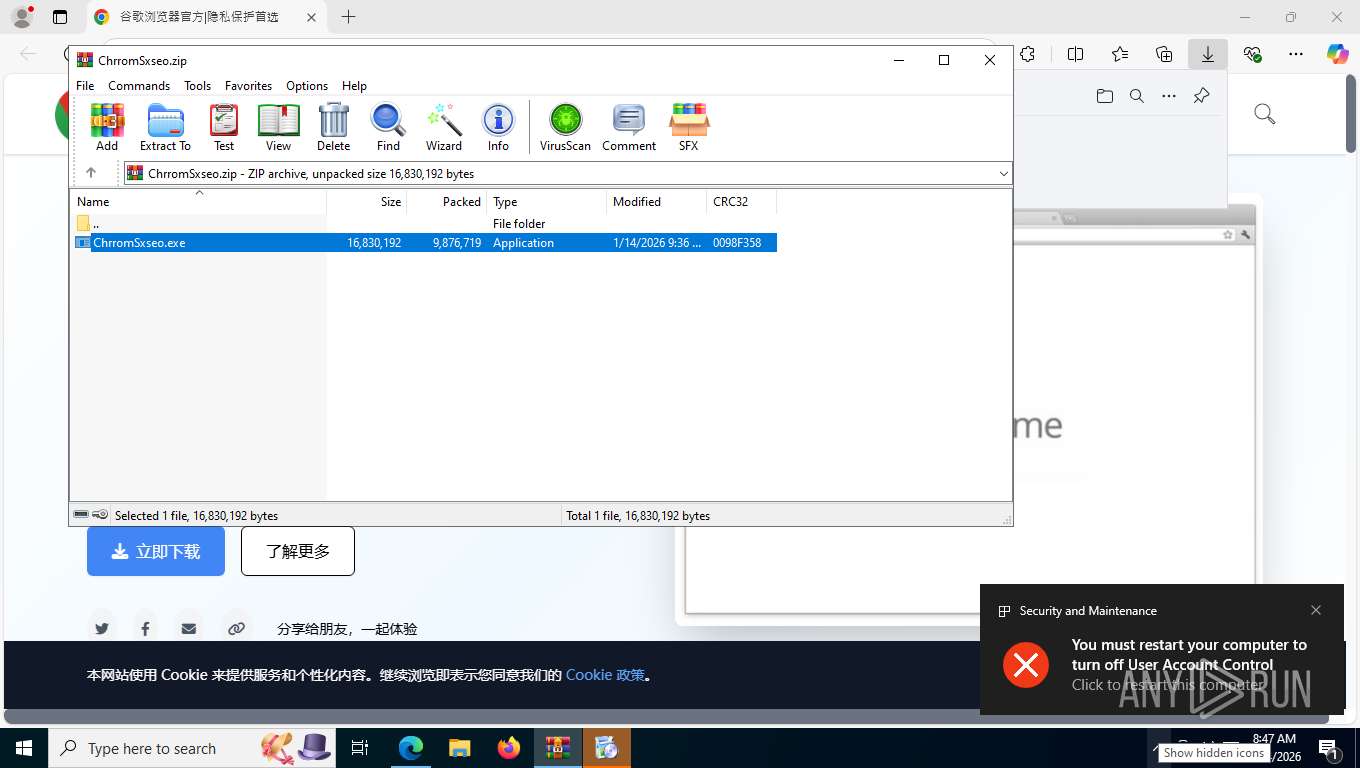
UAC/LUA settings modification
- iusb3mon.exe (PID: 8324)
Changes the autorun value in the registry
- iusb3mon.exe (PID: 8324)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2228)
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
Executable content was dropped or overwritten
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
- updater.exe (PID: 8616)
Reads the date of Windows installation
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 6724)
Starts CMD.EXE for commands execution
- irsetup.exe (PID: 6724)
Hides command output
- cmd.exe (PID: 4680)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 2680)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 2680)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8232)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 4680)
- net.exe (PID: 6936)
Get information on the list of running processes
- cmd.exe (PID: 2680)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 2680)
- irsetup.exe (PID: 6724)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 8072)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 8072)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8072)
- iusb3mon.exe (PID: 8324)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8232)
Executing commands from a ".bat" file
- irsetup.exe (PID: 6724)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8072)
- iusb3mon.exe (PID: 8324)
Application launched itself
- updater.exe (PID: 8476)
Executes as Windows Service
- updater.exe (PID: 8616)
- updater.exe (PID: 8712)
Base64-obfuscated command line is found
- iusb3mon.exe (PID: 8324)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 8964)
Manipulates environment variables
- powershell.exe (PID: 8964)
Removes files via Powershell
- powershell.exe (PID: 8964)
Probably obfuscated PowerShell command line is found
- iusb3mon.exe (PID: 8324)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8964)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8964)
Connects to unusual port
- iusb3mon.exe (PID: 8324)
INFO
Checks supported languages
- identity_helper.exe (PID: 7216)
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- iusb3mon.exe (PID: 8324)
- Ó¢ÐÛÁªÃË.exe (PID: 8348)
- updater.exe (PID: 8476)
- updater.exe (PID: 8496)
Reads Environment values
- identity_helper.exe (PID: 7216)
Application launched itself
- msedge.exe (PID: 7456)
Reads the computer name
- identity_helper.exe (PID: 7216)
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- iusb3mon.exe (PID: 8324)
- updater.exe (PID: 8476)
- Ó¢ÐÛÁªÃË.exe (PID: 8348)
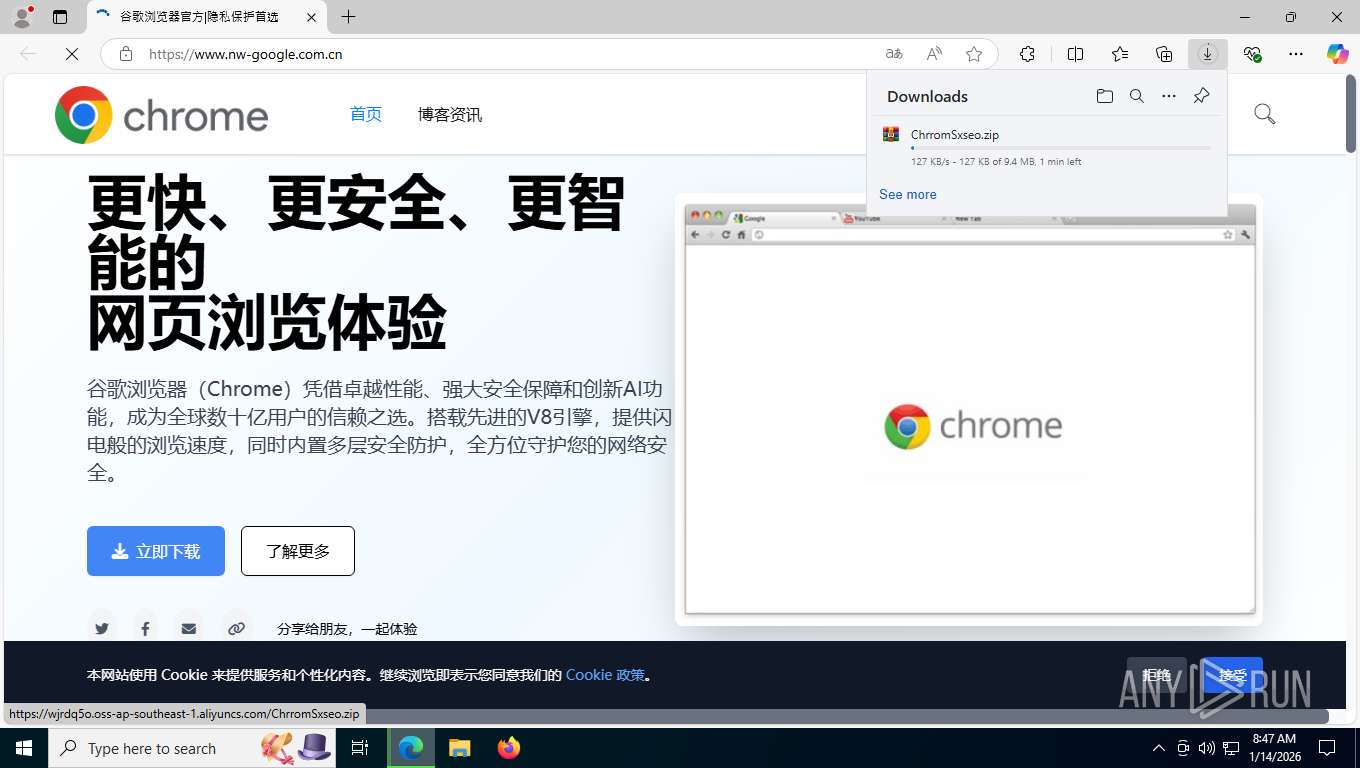
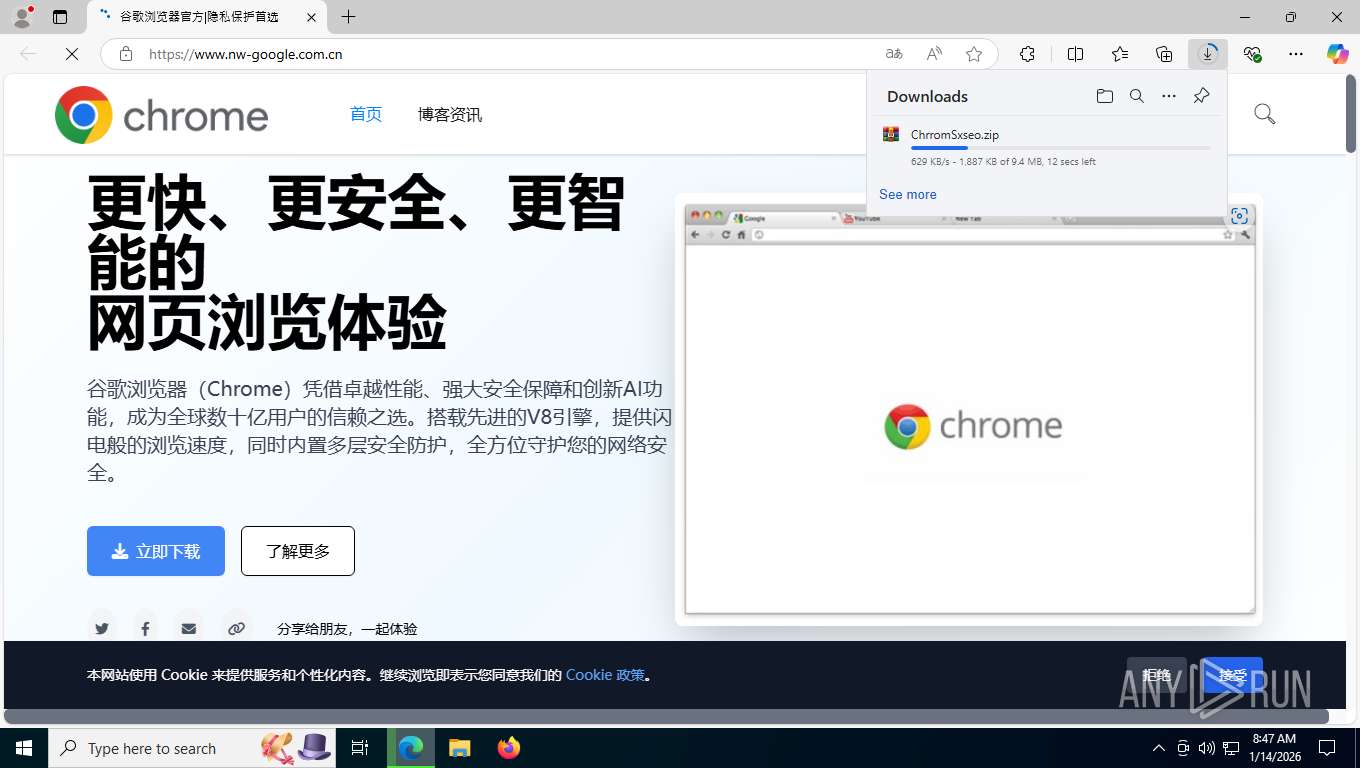
Launching a file from the Downloads directory
- msedge.exe (PID: 7456)
The sample compiled with english language support
- msedge.exe (PID: 7776)
- WinRAR.exe (PID: 2228)
- msedge.exe (PID: 7456)
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
- updater.exe (PID: 8616)
The sample compiled with portuguese language support
- ChrromSxseo.exe (PID: 1908)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2228)
Create files in a temporary directory
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
- SecEdit.exe (PID: 4404)
Process checks computer location settings
- ChrromSxseo.exe (PID: 1908)
- irsetup.exe (PID: 6724)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7248)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7248)
Creates files or folders in the user directory
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
Creates files in the program directory
- irsetup.exe (PID: 6724)
- updater.exe (PID: 8476)
- updater.exe (PID: 8496)
- updater.exe (PID: 8616)
- updater.exe (PID: 8712)
Reads the machine GUID from the registry
- updater.exe (PID: 8476)
Process checks whether UAC notifications are on
- updater.exe (PID: 8476)
- iusb3mon.exe (PID: 8324)
Checks proxy server information
- updater.exe (PID: 8476)
Launching a file from a Registry key
- iusb3mon.exe (PID: 8324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
95
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
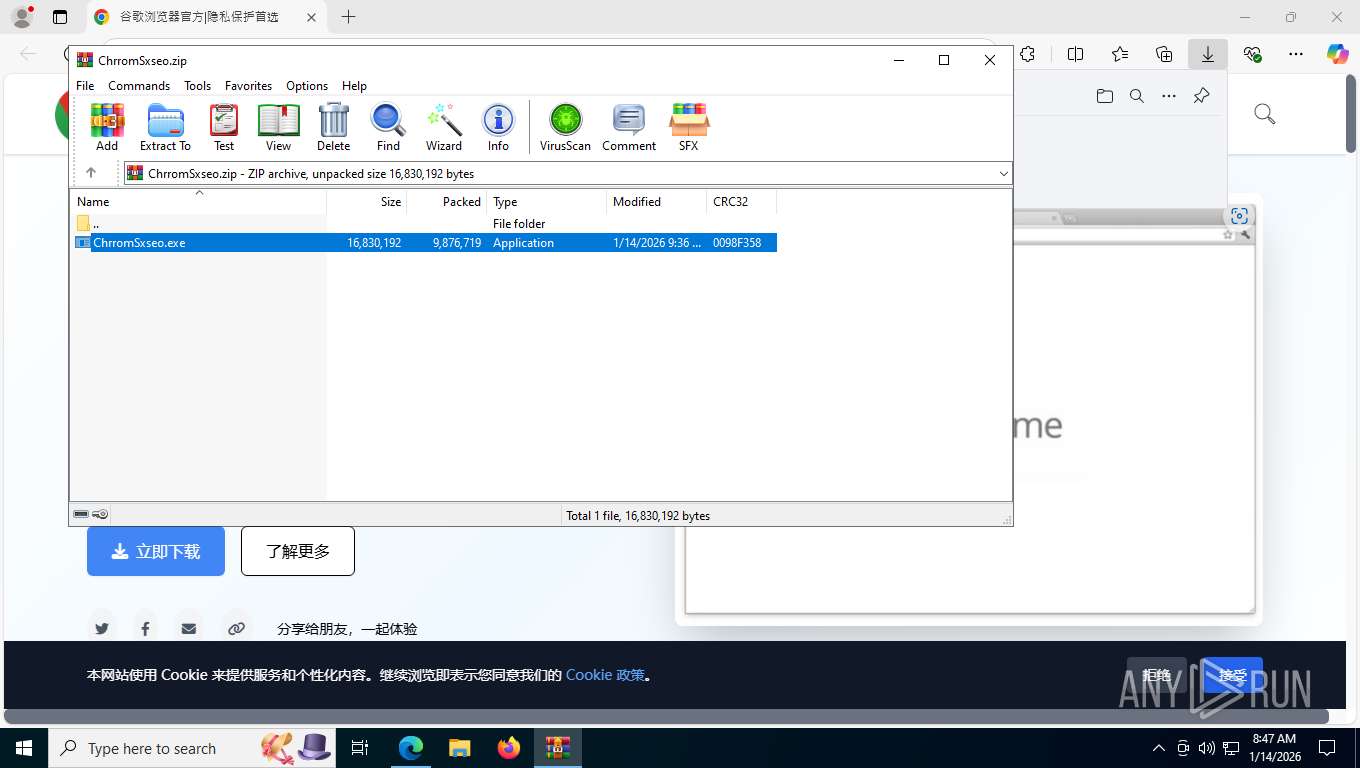
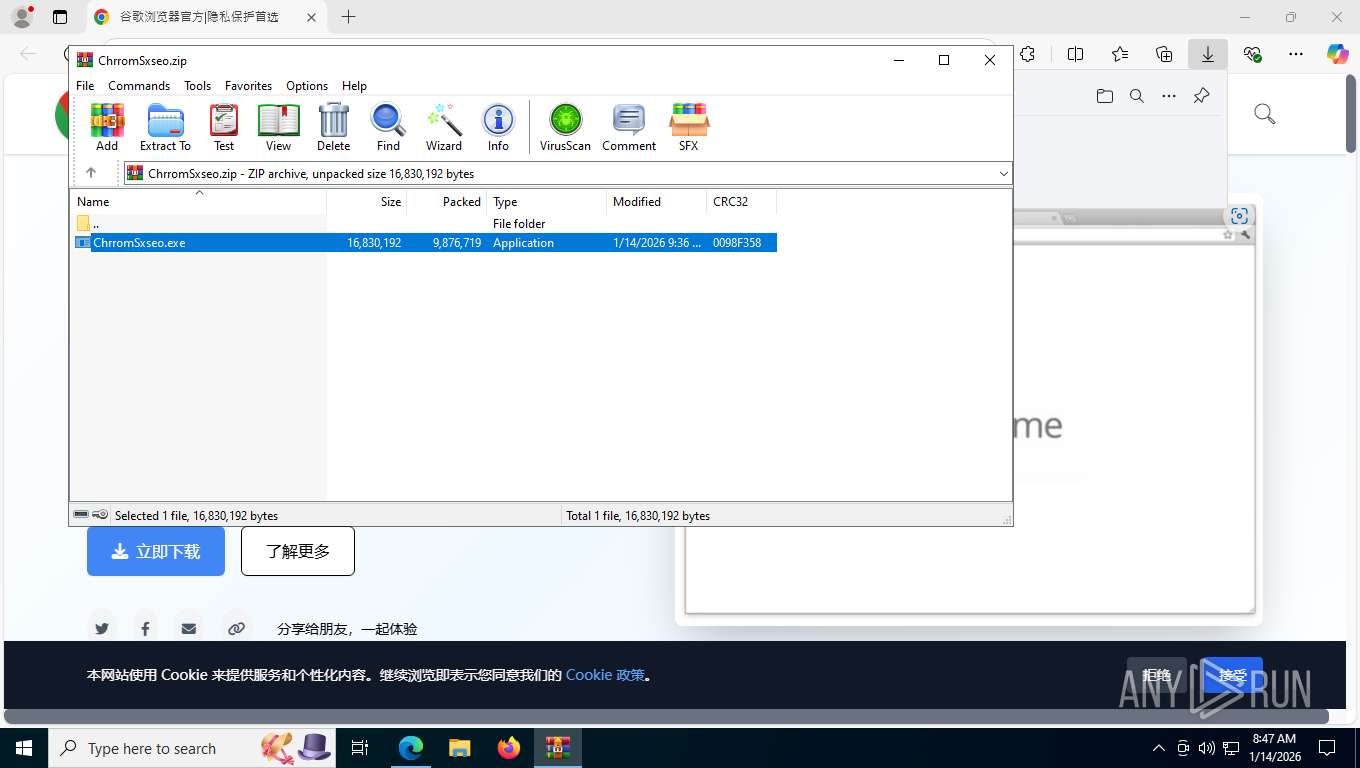
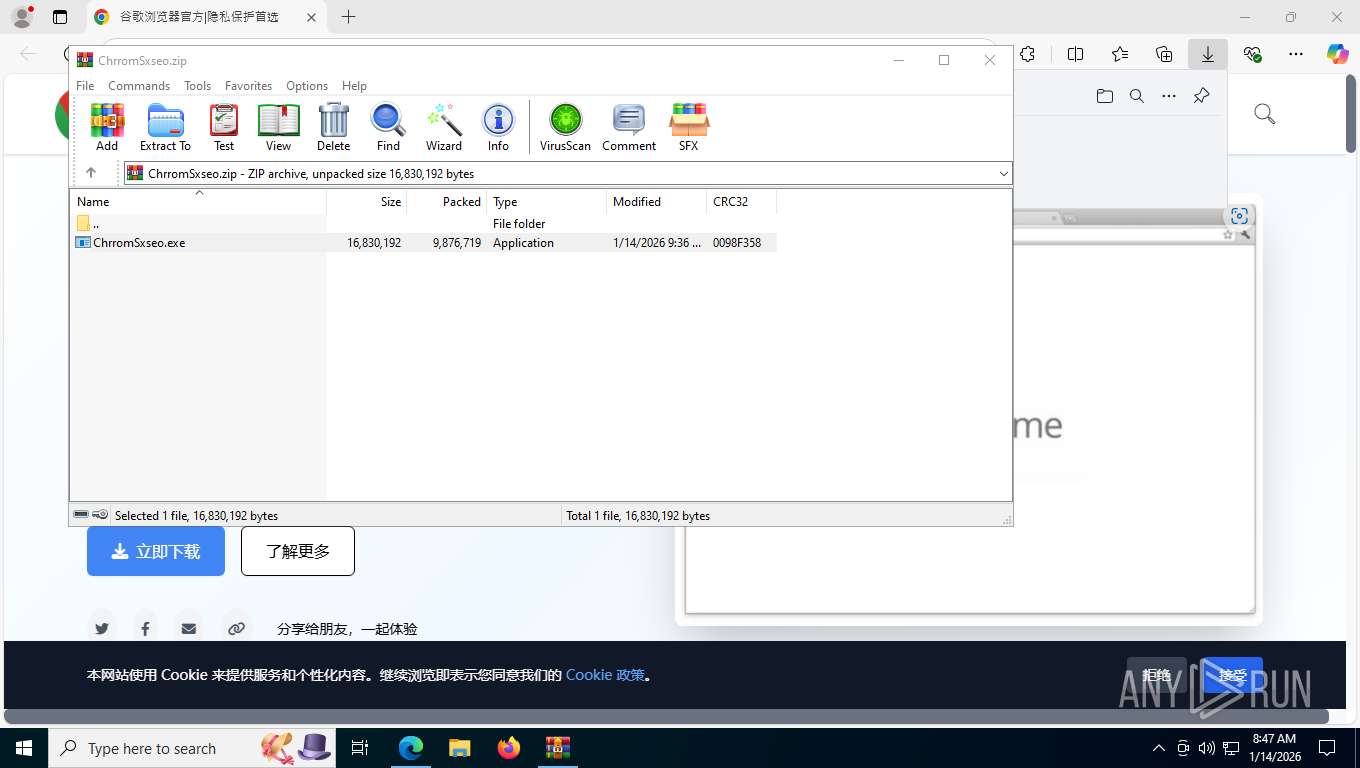
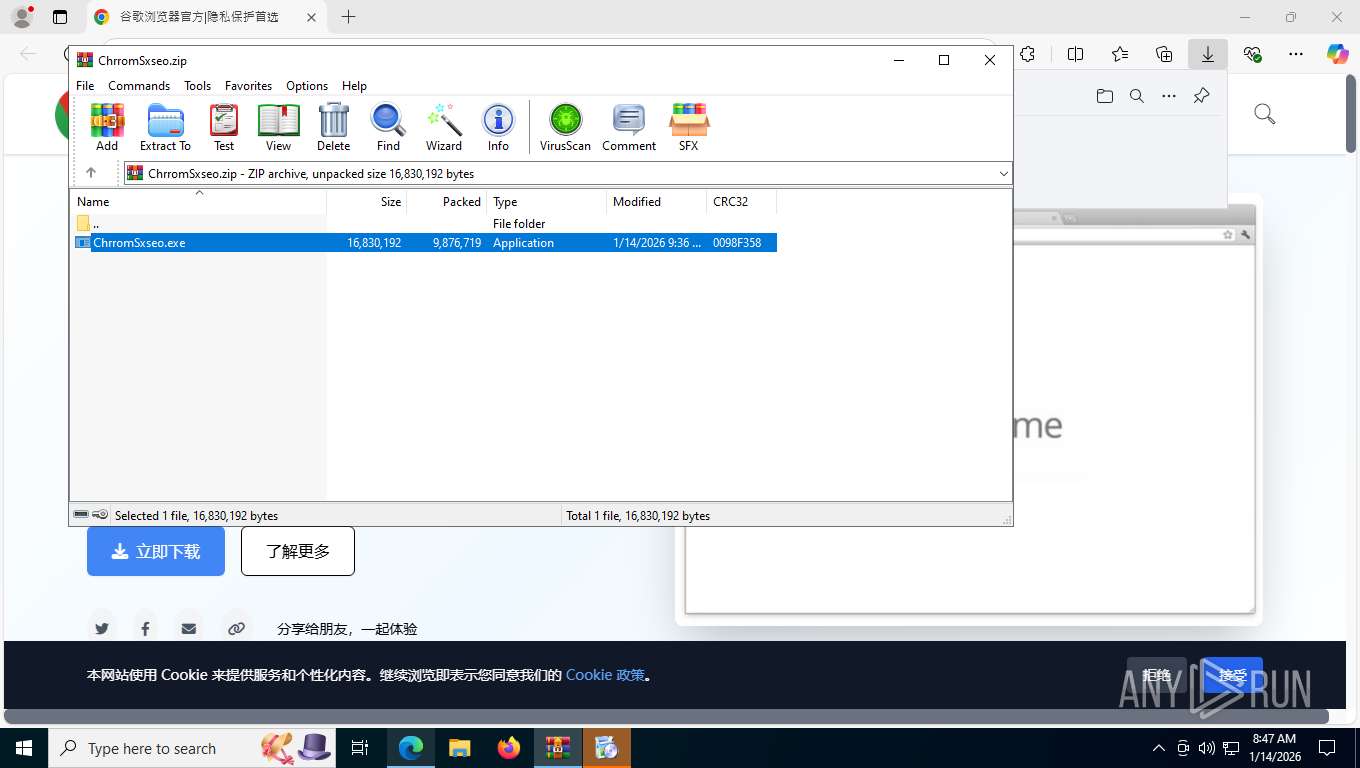
| 144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.9342\ChrromSxseo.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.9342\ChrromSxseo.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 10.1.0.0 Modules
| |||||||||||||||
| 144 | tasklist /FI "IMAGENAME eq HipsLog.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6576,i,17164554942598266788,4423862003027653600,262144 --variations-seed-version --mojo-platform-channel-handle=6616 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1780 | tasklist /FI "IMAGENAME eq 360Tray.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1780 | find /I "QQPCRTP.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1780 | find /I "HipsMain.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | find /I "360Tray.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | "C:\Windows\System32\cmd.exe" /c tasklist /FI "IMAGENAME eq QQPCRTP.exe" 2>nul | find /I "QQPCRTP.exe" >nul | C:\Windows\System32\cmd.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | "C:\Windows\System32\cmd.exe" /c tasklist /FI "IMAGENAME eq HipsMain.exe" 2>nul | find /I "HipsMain.exe" >nul | C:\Windows\System32\cmd.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1908 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.9342\ChrromSxseo.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.9342\ChrromSxseo.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 10.1.0.0 Modules
| |||||||||||||||
Total events
18 266
Read events
18 144
Write events
112
Delete events
10
Modification events
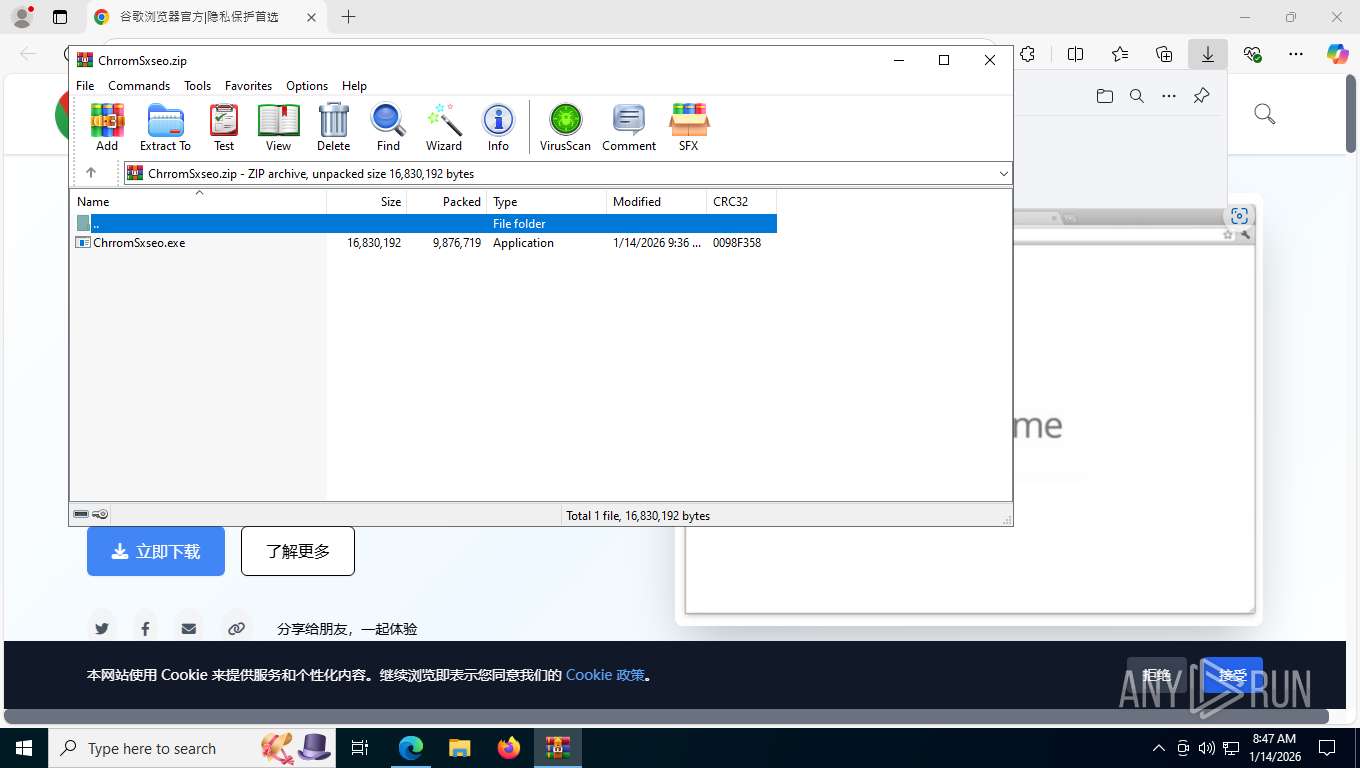
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\ChrromSxseo.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8476) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 132.0.6833.0 | |||
| (PID) Process: | (8476) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | name |
Value: GoogleUpdater | |||
Executable files
8
Suspicious files
86
Text files
110
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe565.TMP | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe575.TMP | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe575.TMP | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe584.TMP | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe594.TMP | — | |
MD5:— | SHA256:— | |||
| 7456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe594.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
130
TCP/UDP connections
99
DNS requests
88
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7776 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
7776 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:tZ5r6eOLUHe-8-Wq7u7CywPpoIxyQvIDOo6I7sgfIK0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7776 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
7776 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | text | 892 b | whitelisted |
7776 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7776 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1768398425&lafgdate=0 | unknown | text | 4.66 Kb | whitelisted |
7776 | msedge.exe | GET | 302 | 104.26.3.143:443 | https://cdn.tailwindcss.com/ | unknown | — | — | unknown |
7776 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1768398425&lafgdate=0 | unknown | text | 41.4 Kb | whitelisted |
7776 | msedge.exe | GET | 200 | 2.16.241.200:443 | https://www.bing.com/api/shopping/v1/user/shoppingsettings?EnabledServiceFeaturesv2=edgeServerUX.shopping.msEdgeShoppingCashbackDismissTimeout2s | unknown | text | 1.02 Kb | whitelisted |
7776 | msedge.exe | GET | 301 | 198.44.179.119:80 | http://www.nw-google.com.cn/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6236 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7776 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7776 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7776 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7776 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.nw-google.com.cn |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7776 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7776 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7776 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7776 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7776 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
7776 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
7776 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
7776 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
7776 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |