| download: | /wp-content/uploads/2020/12/SaveWizard.zip |
| Full analysis: | https://app.any.run/tasks/b4915d3b-d392-4ebc-8006-8629b66fc0df |
| Verdict: | Malicious activity |
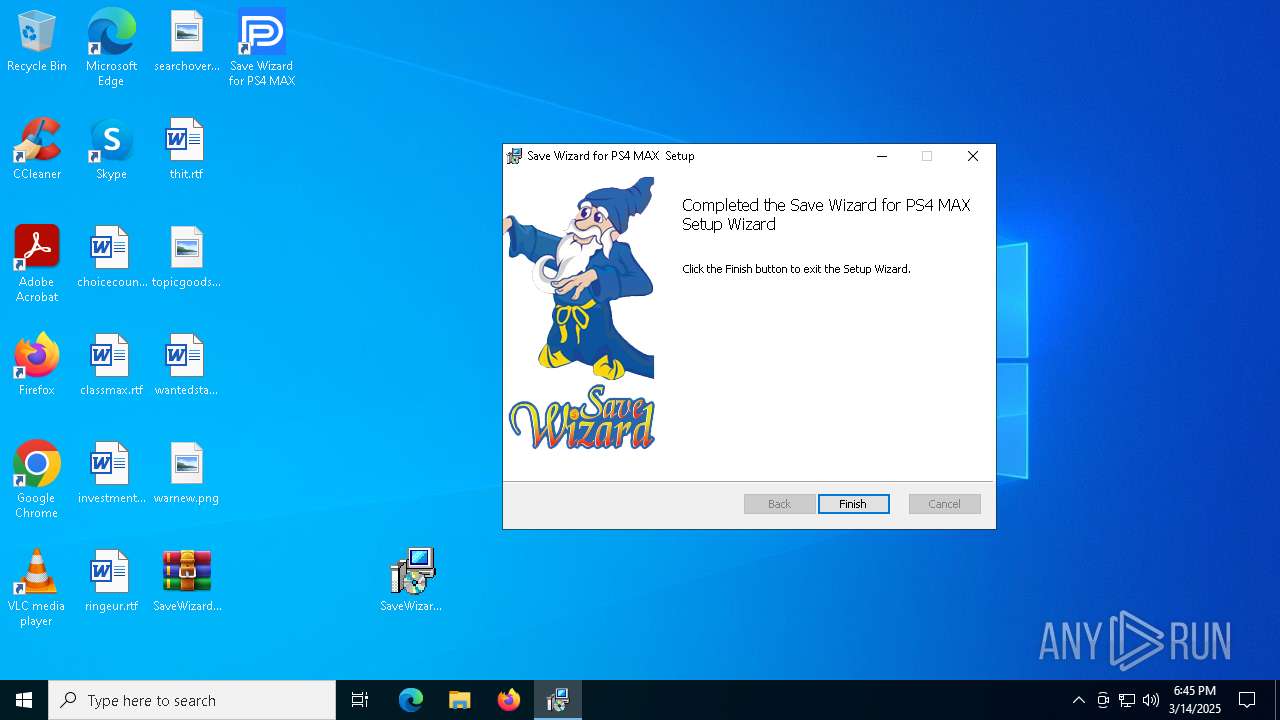
| Analysis date: | March 14, 2025, 18:45:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
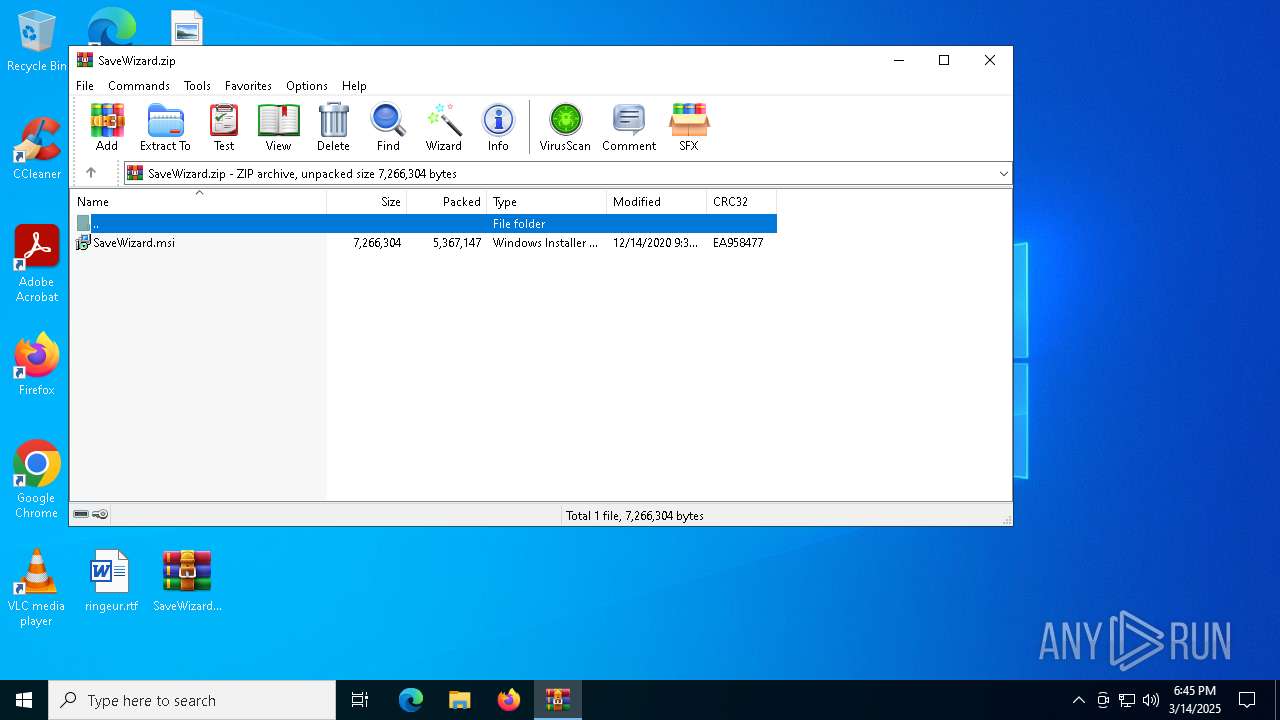
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 77F4655AF9DF808A32F8909E10C32D65 |
| SHA1: | BCE960065C6E3FFFAE9DF9A7ADC9DD82193CD681 |
| SHA256: | 5B0E541B67709FF205BE5C1540D68D5E1730B7821489FC4130B25FCDE82CA317 |
| SSDEEP: | 98304:1zMO9ERmu8DEXYOXkujVmcYORcMsRP0IRQkq/KBwMKyFaUu9LkJDZ0XPJBPpZ95X:bEc2Laz9YgxEntvX |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 3676)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1328)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4880)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3768)
- msiexec.exe (PID: 2084)
- ShellExperienceHost.exe (PID: 7036)
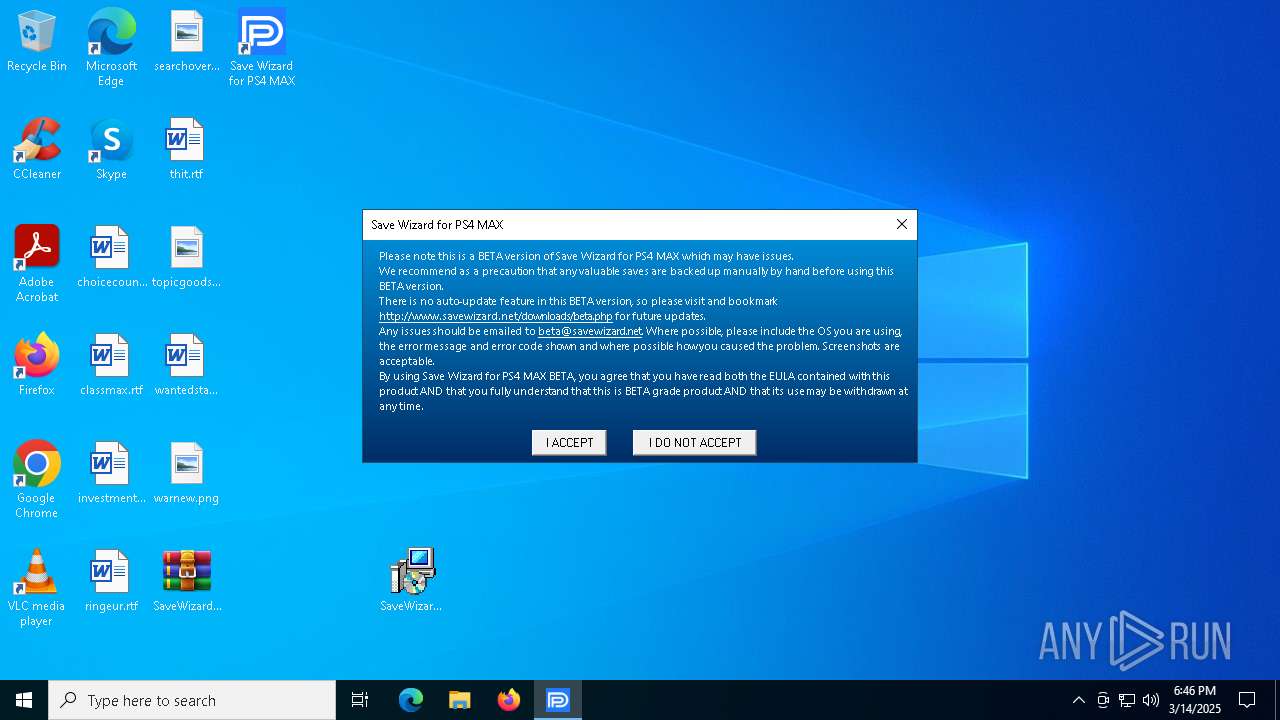
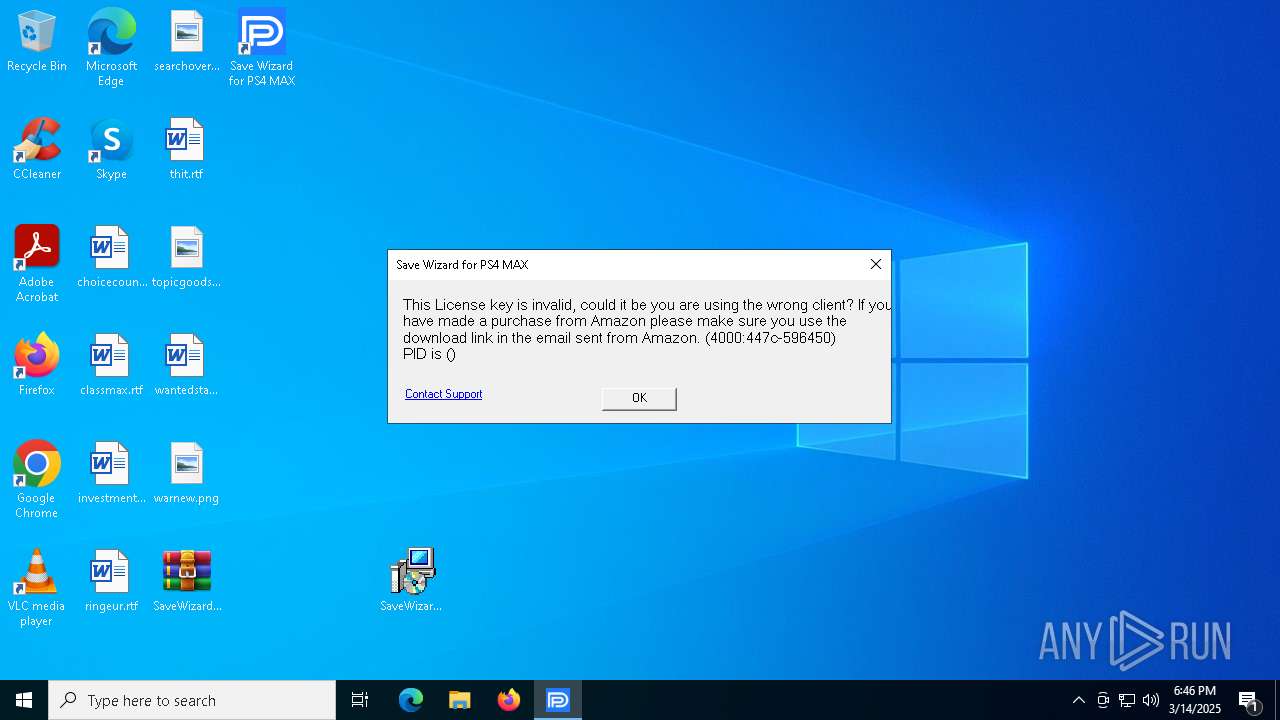
Potential Corporate Privacy Violation
- SWPS4MAX.exe (PID: 1748)
Connects to unusual port
- SWPS4MAX.exe (PID: 1748)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5868)
- BackgroundTransferHost.exe (PID: 3888)
- BackgroundTransferHost.exe (PID: 5260)
- BackgroundTransferHost.exe (PID: 1228)
- BackgroundTransferHost.exe (PID: 5956)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5868)
- slui.exe (PID: 5324)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5868)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5868)
- msiexec.exe (PID: 4880)
Reads the computer name
- msiexec.exe (PID: 4880)
- msiexec.exe (PID: 4988)
- msiexec.exe (PID: 3768)
- ShellExperienceHost.exe (PID: 7036)
- msiexec.exe (PID: 2084)
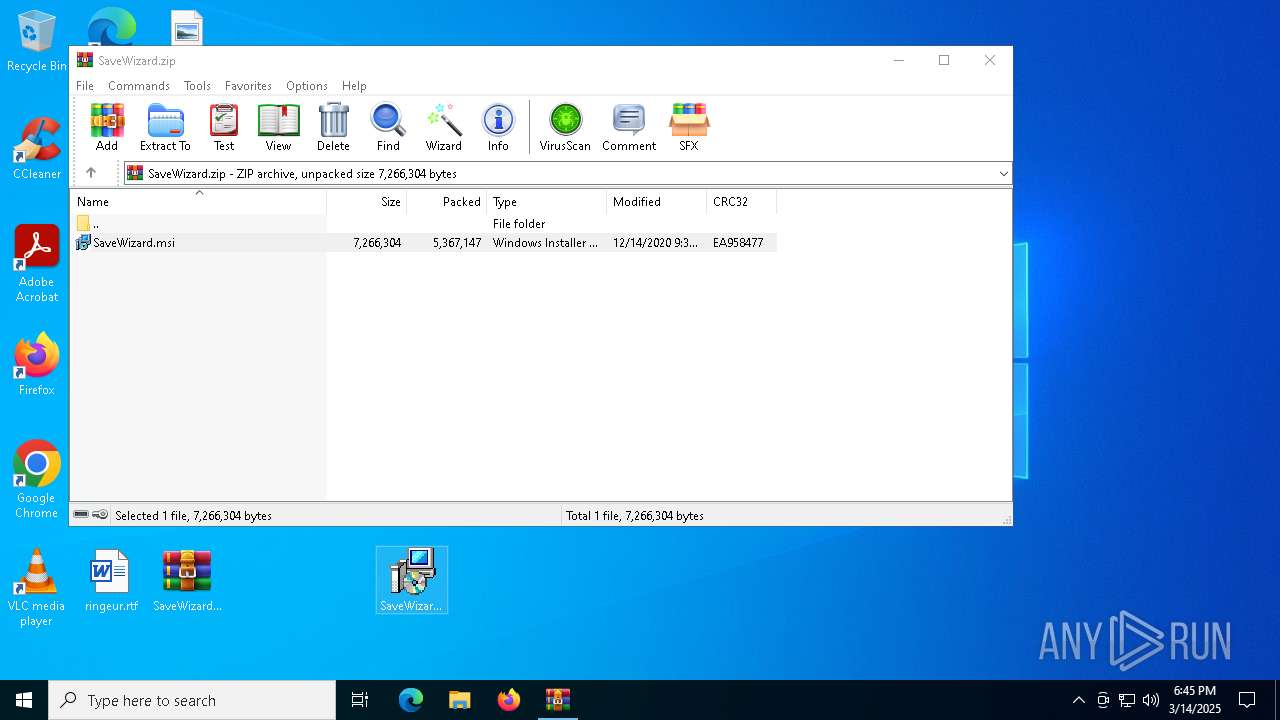
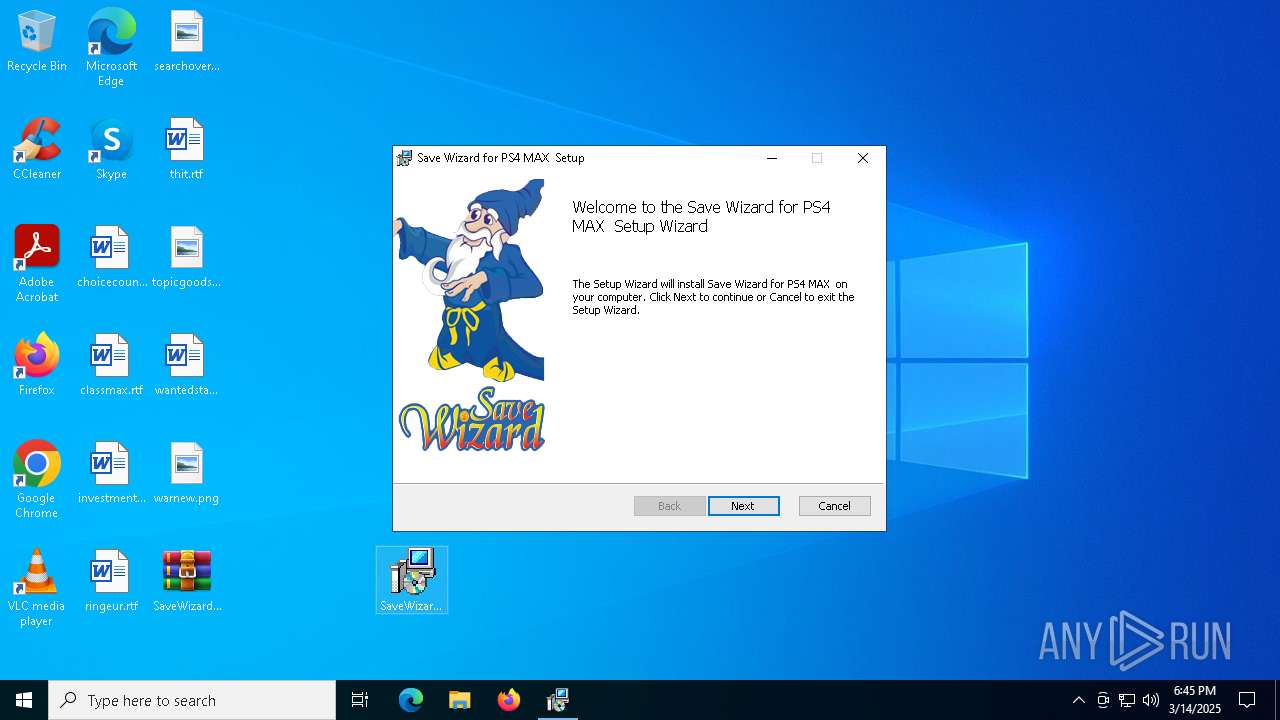
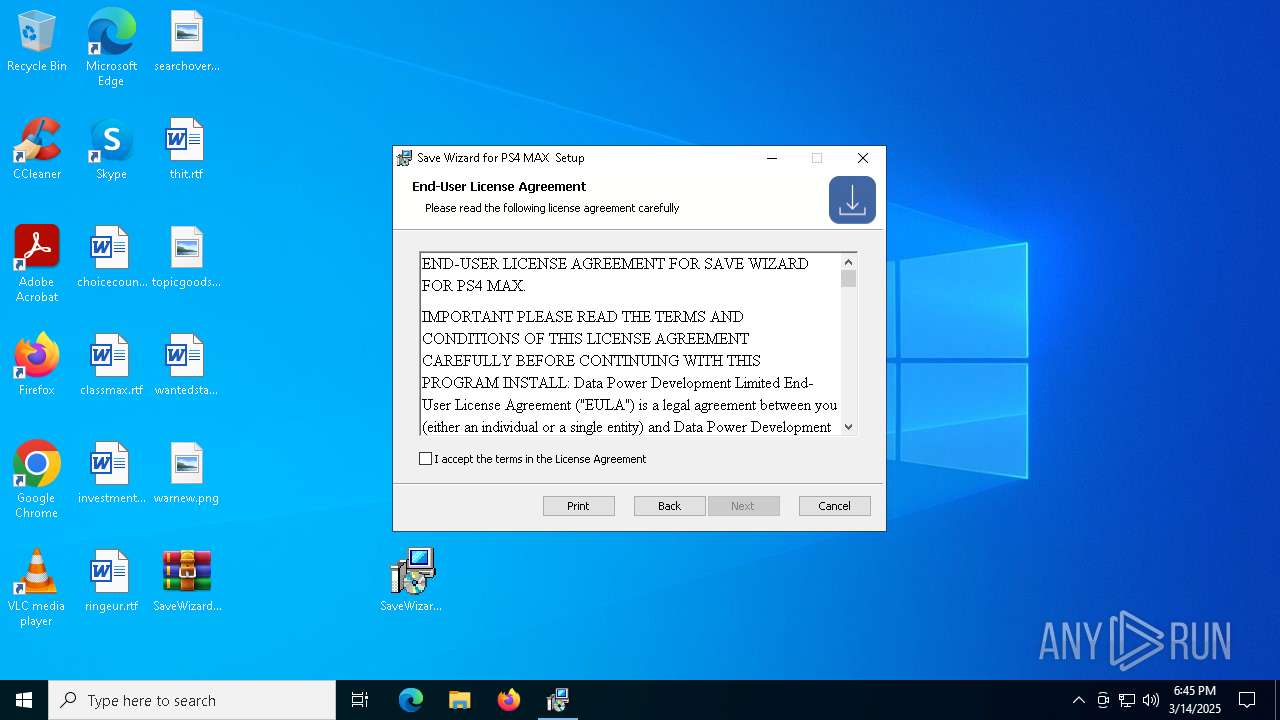
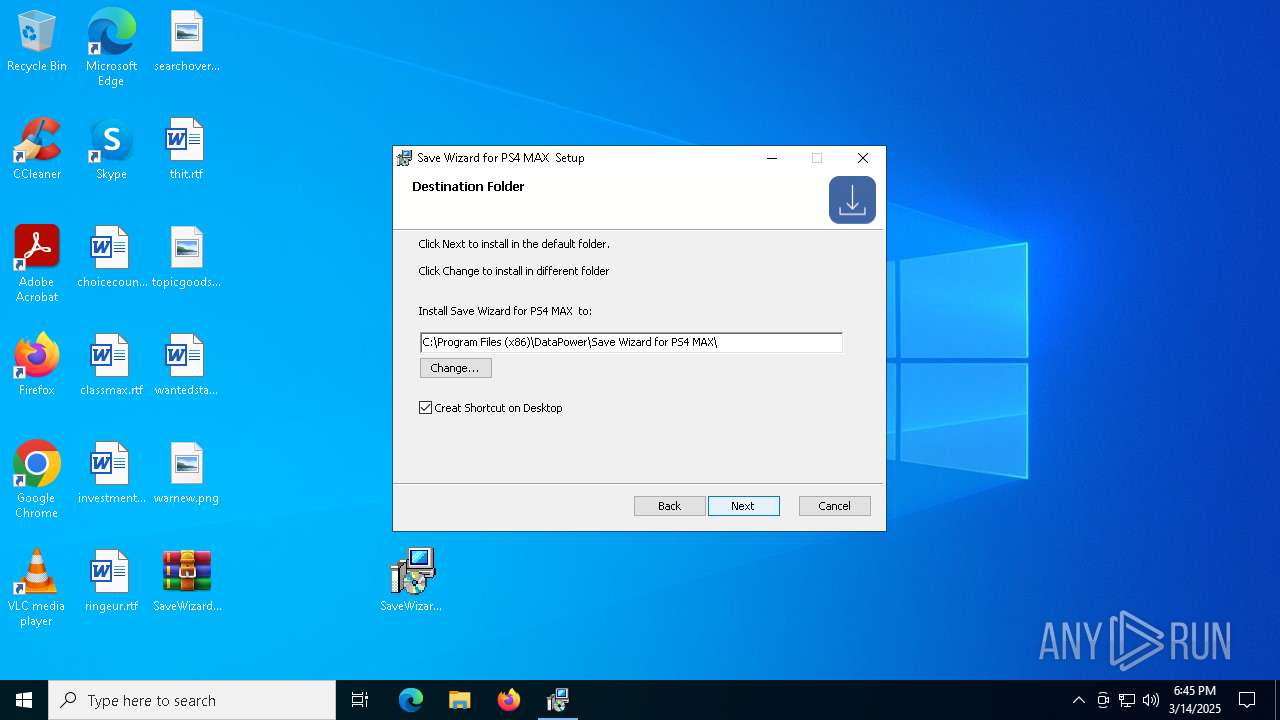
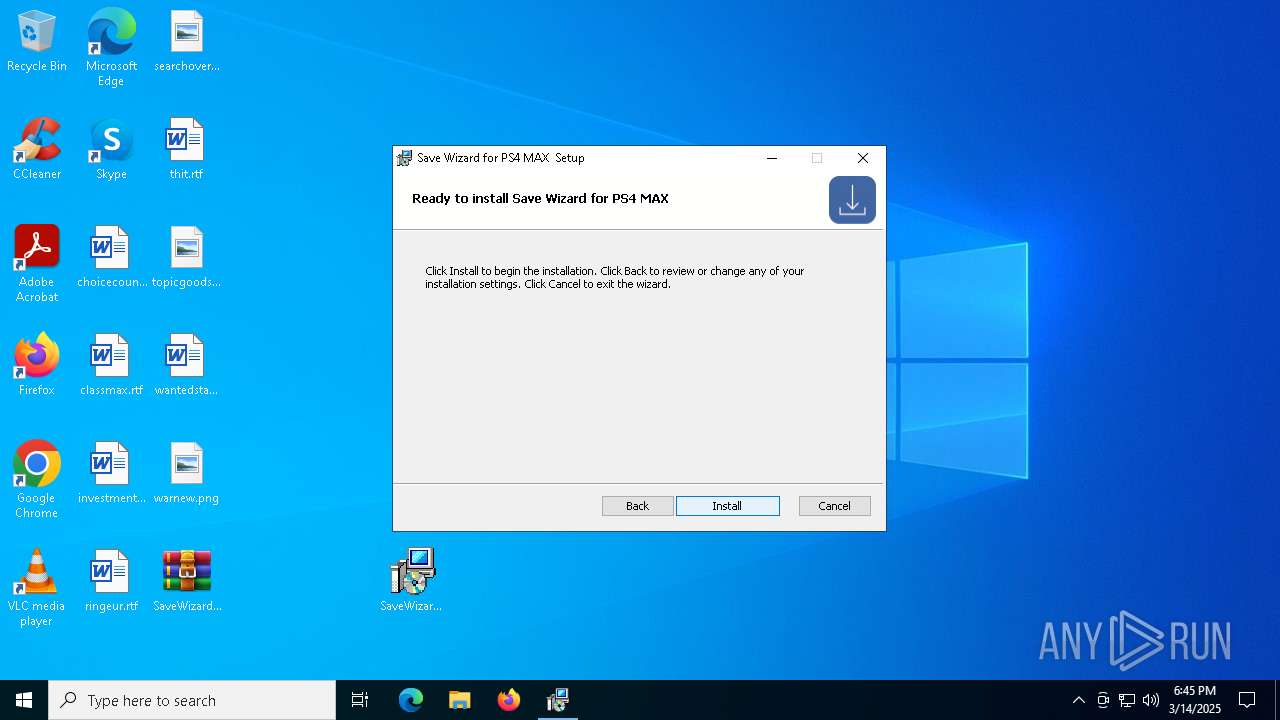
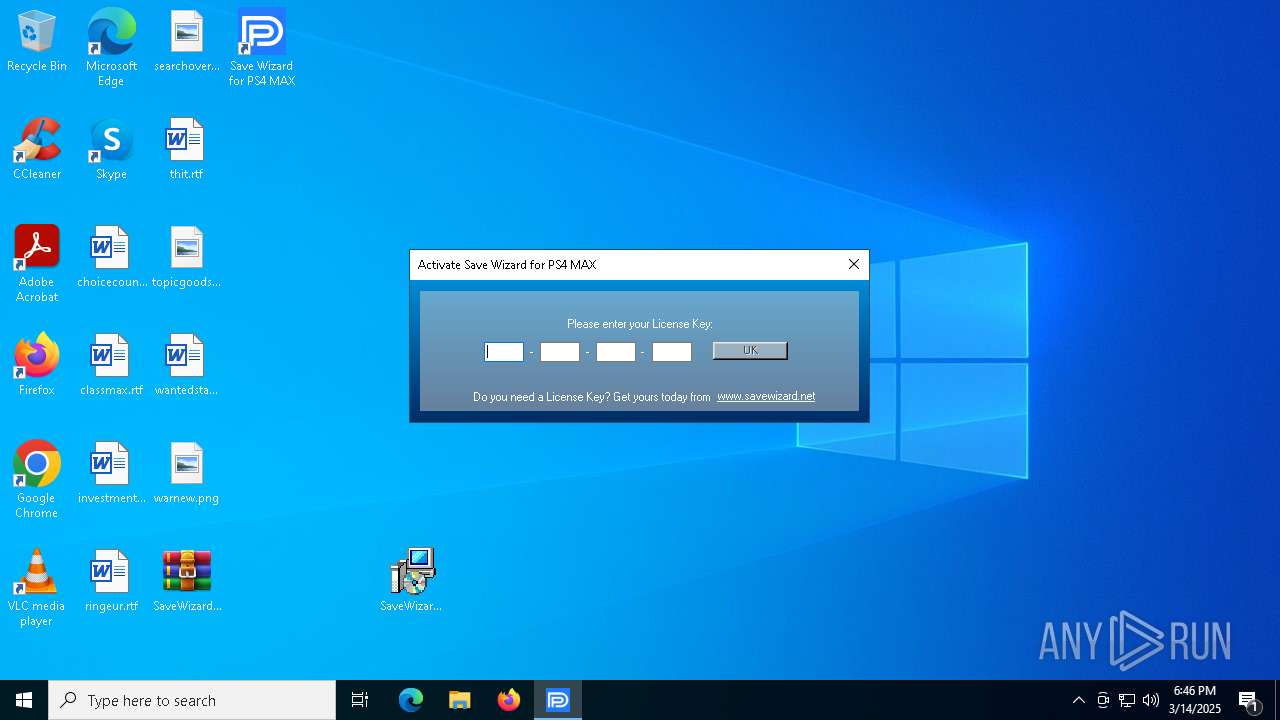
Manual execution by a user
- msiexec.exe (PID: 5756)
- SWPS4MAX.exe (PID: 1748)
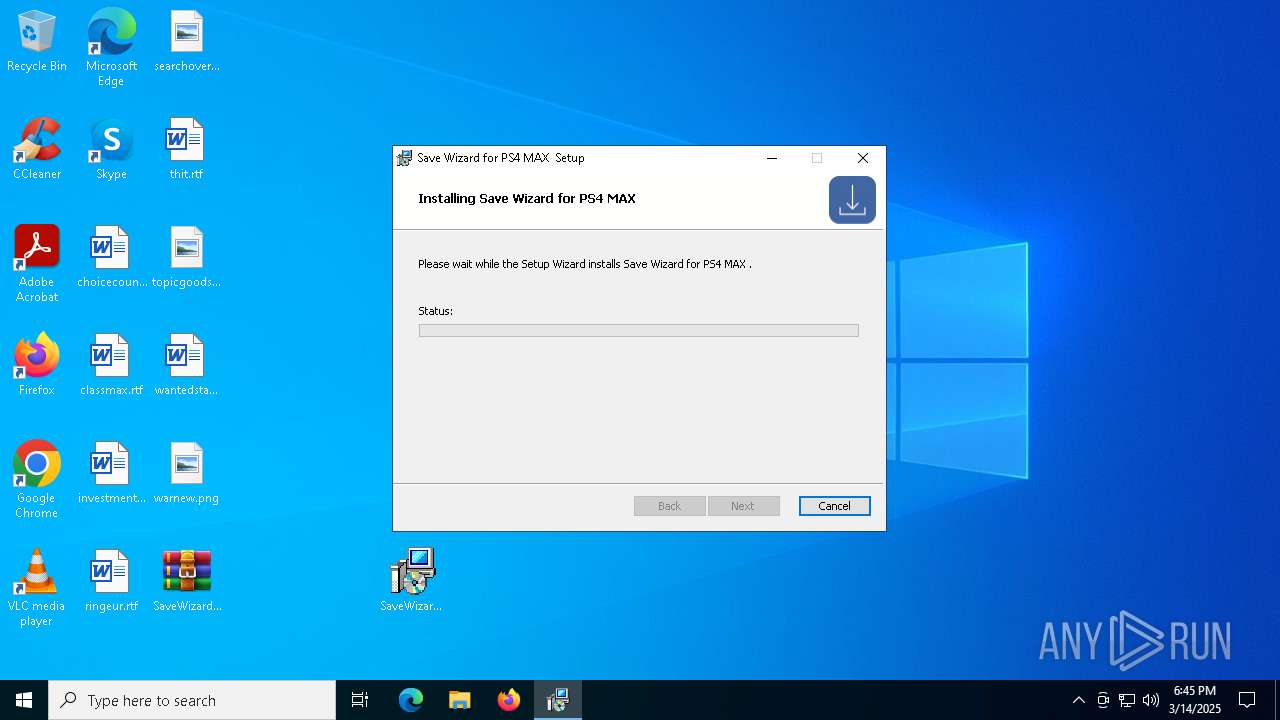
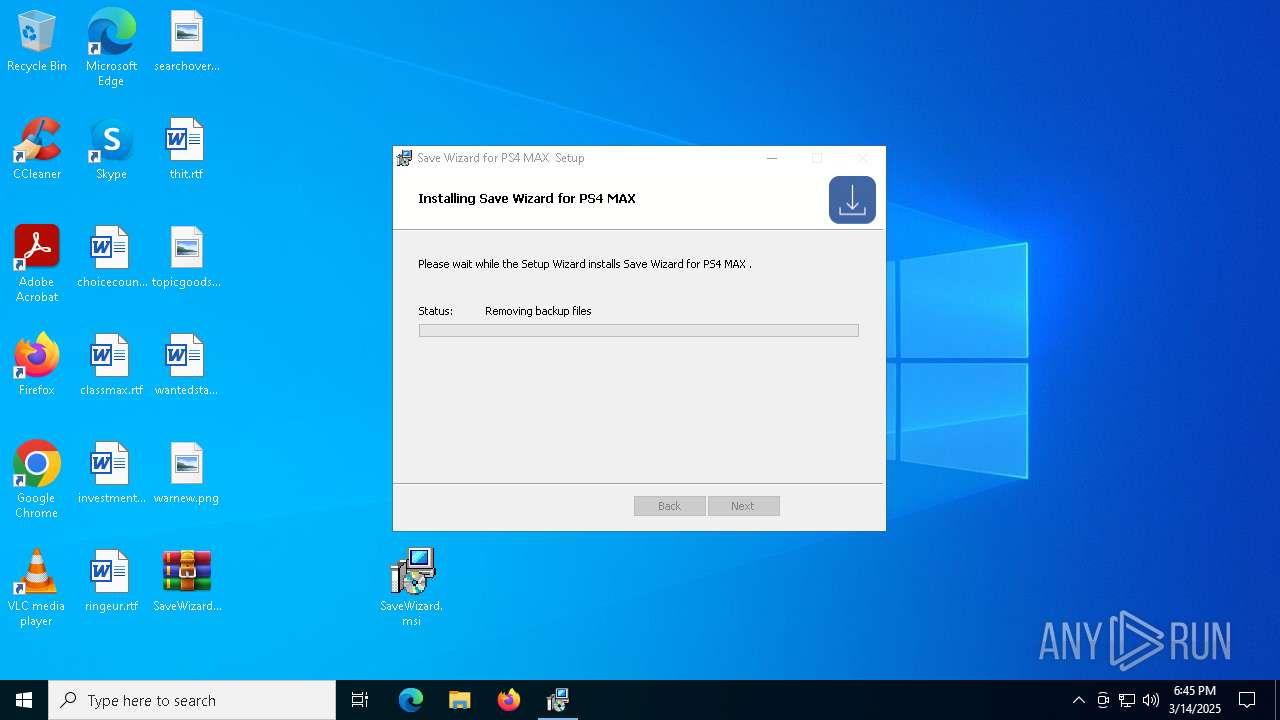
Executable content was dropped or overwritten
- msiexec.exe (PID: 5756)
- msiexec.exe (PID: 4880)
Checks supported languages
- msiexec.exe (PID: 4988)
- msiexec.exe (PID: 4880)
- msiexec.exe (PID: 3768)
- SWPS4MAX.exe (PID: 1748)
- msiexec.exe (PID: 2084)
- ShellExperienceHost.exe (PID: 7036)
Manages system restore points
- SrTasks.exe (PID: 1512)
Reads the machine GUID from the registry
- SWPS4MAX.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:12:14 17:36:16 |
| ZipCRC: | 0xea958477 |
| ZipCompressedSize: | 5367147 |
| ZipUncompressedSize: | 7266304 |
| ZipFileName: | SaveWizard.msi |
Total processes
159
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
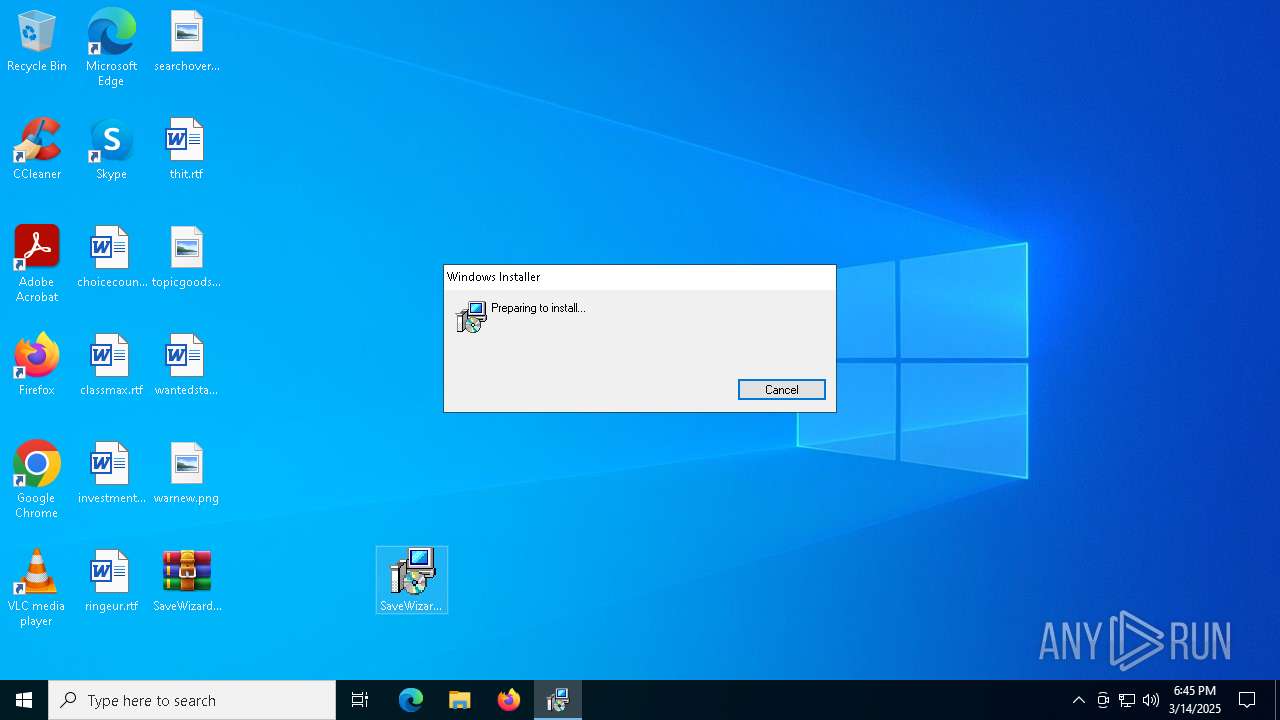
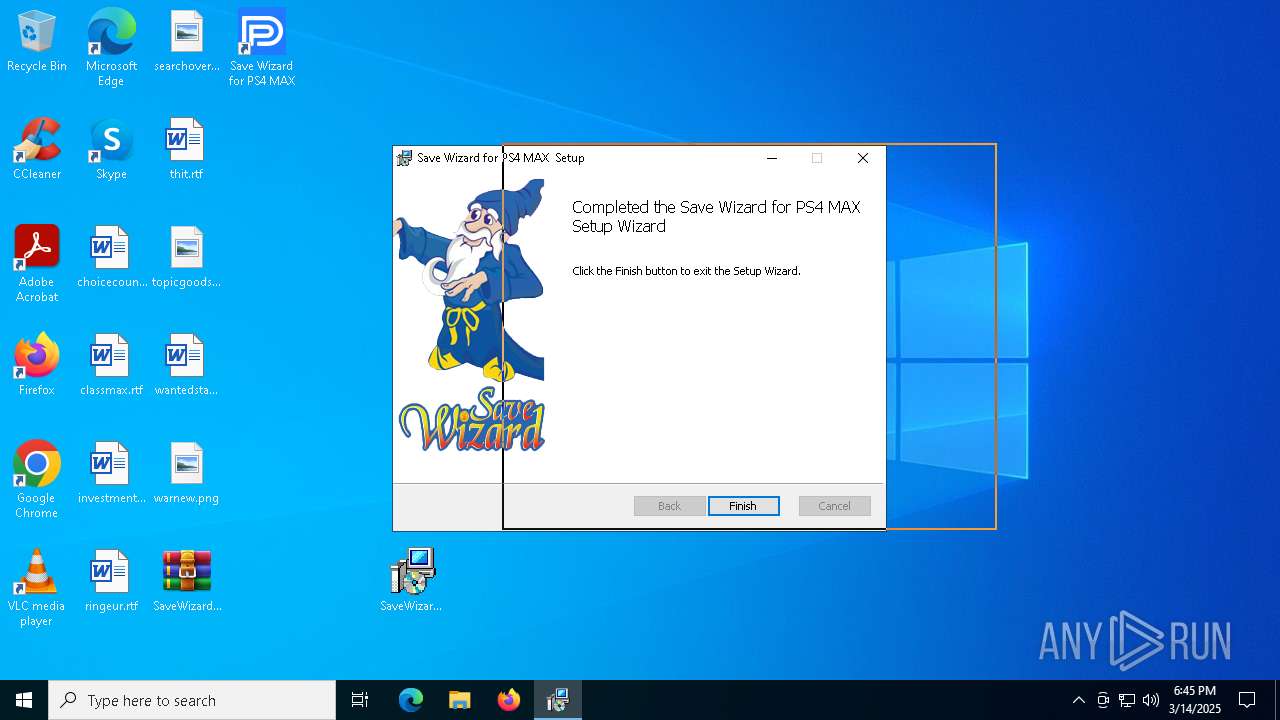
| 1748 | "C:\Program Files (x86)\DataPower\Save Wizard for PS4 MAX\SWPS4MAX.exe" | C:\Program Files (x86)\DataPower\Save Wizard for PS4 MAX\SWPS4MAX.exe | explorer.exe | ||||||||||||
User: admin Company: Datapower Integrity Level: MEDIUM Description: Save Wizard for PS4 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2084 | C:\Windows\syswow64\MsiExec.exe -Embedding A40A8580630D662BE79B8FAC85ED38B1 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\SaveWizard.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3768 | C:\Windows\syswow64\MsiExec.exe -Embedding F111371147C3D27904C2F4456ADB93B0 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 287
Read events
9 942
Write events
328
Delete events
17
Modification events
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SaveWizard.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3888) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3888) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
16
Suspicious files
68
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3676.23055\SaveWizard.msi | — | |
MD5:— | SHA256:— | |||
| 5868 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\cf026209-268a-470a-8829-cfe1ac5ee182.down_data | — | |
MD5:— | SHA256:— | |||
| 4880 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4880 | msiexec.exe | C:\Windows\Installer\1159c5.msi | — | |
MD5:— | SHA256:— | |||
| 5868 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\1d684c1c-65f3-474b-8bf1-fc6d7bc4438c.up_meta_secure | binary | |
MD5:49016AECB2CED2564AAC6F4FC60E344C | SHA256:F7FEEB4C8E44985D6393FCC5D102CF4A22E7827EC9E9650A7763E4629A77BE85 | |||
| 5756 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSICED.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 4880 | msiexec.exe | C:\Windows\Installer\MSI5E99.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 5868 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\1d684c1c-65f3-474b-8bf1-fc6d7bc4438c.4eaf5eb6-4da3-41a8-ba3e-5fdaa92dde32.down_meta | binary | |
MD5:77A0295944886DA1B054BFBD60EFBFBE | SHA256:42F244D2B54CD27E773BBDEF25E90F6914377659C01F79DDCD8DD891E2CA8788 | |||
| 4880 | msiexec.exe | C:\Windows\Installer\MSI5E78.tmp | binary | |
MD5:BCBB1E0F59589AAE32866A89477DD956 | SHA256:39A0BBC684F0A5493767A39412258B616BE62412AD340B3D883E634863B11A7B | |||
| 4880 | msiexec.exe | C:\Program Files (x86)\DataPower\Save Wizard for PS4 MAX\de\SWPS4MAX.resources.dll | executable | |
MD5:33E3CF463957E4565E3F36D8952CF260 | SHA256:DD3B9251FA13CC784D0EF19C07393D381EF9A7EBE4694D696BB1991EA7360F26 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5868 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5156 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
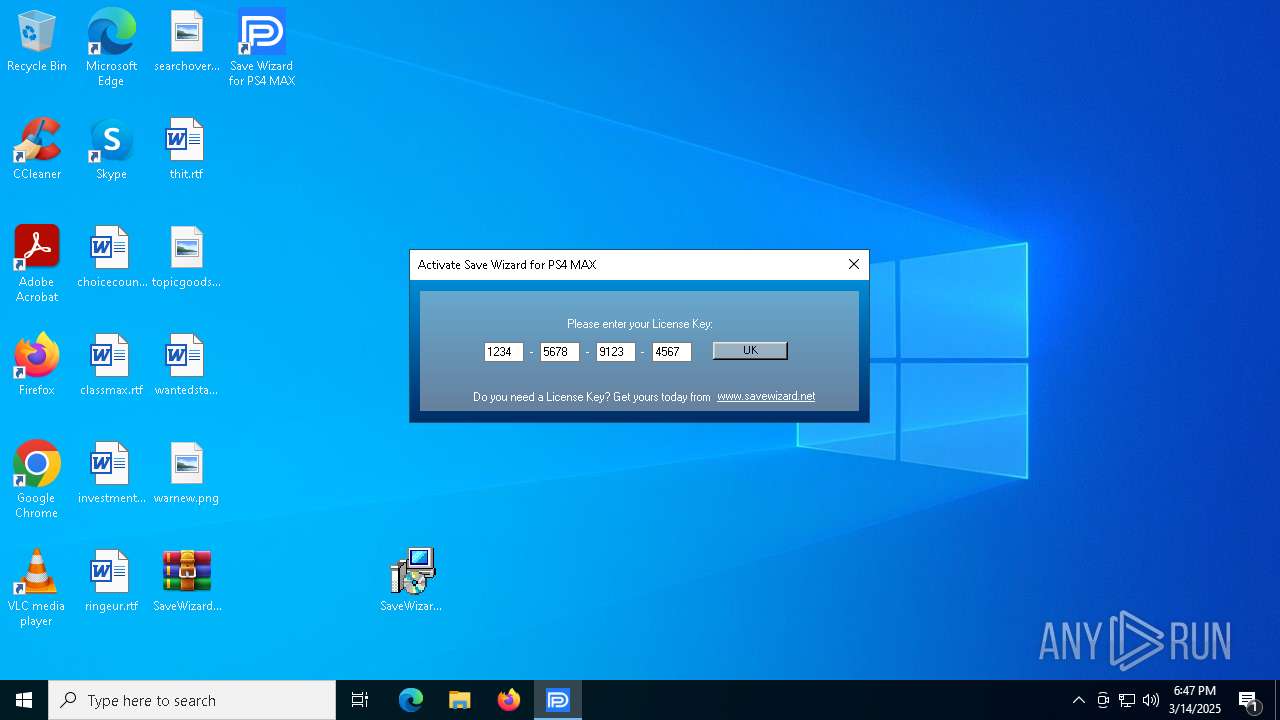
1748 | SWPS4MAX.exe | POST | — | 34.92.104.171:8082 | http://ps4as5.savewizard.net:8082/ps4auth | unknown | — | — | whitelisted |
1748 | SWPS4MAX.exe | POST | 200 | 34.92.104.171:8082 | http://ps4as5.savewizard.net:8082/ps4auth | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5156 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5156 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5868 | BackgroundTransferHost.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1748 | SWPS4MAX.exe | Potential Corporate Privacy Violation | ET INFO Outgoing Basic Auth Base64 HTTP Password detected unencrypted |