| File name: | Cisco_WebEx_Add-On.exe |
| Full analysis: | https://app.any.run/tasks/81df3d76-7f92-4164-90d3-2f7f73f5e023 |
| Verdict: | Suspicious activity |
| Analysis date: | December 13, 2018, 03:39:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D4C8555ADE1027766B06374E598C0D79 |
| SHA1: | 53C193A0FBBEC22F25EC25FDB8BDAF6A493DBF3D |
| SHA256: | 5AEC1B12E09E578A2070C7641F8D6E87372E54BECF2DAF6751F5B102249019DA |
| SSDEEP: | 24576:Y8kWhrykZJxCLN2NW2agR2rywMd+gcxENBvTQ:7kWRykfsB20gePMd+gcxErk |
MALICIOUS
Application was dropped or rewritten from another process
- CiscoWebExStart.exe (PID: 4008)
SUSPICIOUS
Executable content was dropped or overwritten
- Cisco_WebEx_Add-On.exe (PID: 3112)
- CiscoWebExStart.exe (PID: 4008)
Creates files in the user directory
- Cisco_WebEx_Add-On.exe (PID: 3112)
Creates files in the program directory
- Cisco_WebEx_Add-On.exe (PID: 3112)
- CiscoWebExStart.exe (PID: 4008)
Modifies the open verb of a shell class
- CiscoWebExStart.exe (PID: 4008)
INFO
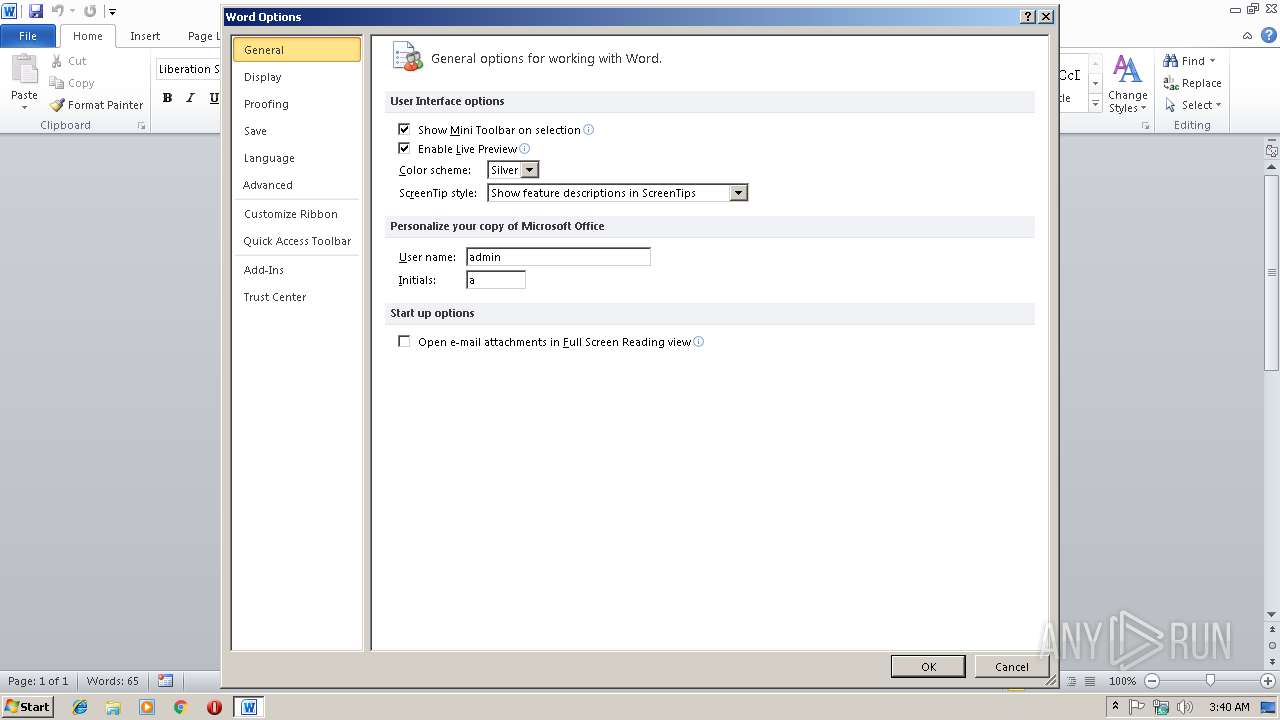
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3076)
- WINWORD.EXE (PID: 2032)
Creates files in the user directory
- WINWORD.EXE (PID: 3076)
- WINWORD.EXE (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:27 06:19:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 119808 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb4d7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3200.0.1610.1300 |
| ProductVersionNumber: | 3200.0.1610.1300 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral 2 |
| CharacterSet: | Unicode |
| CompanyName: | Cisco WebEx LLC |
| FileDescription: | Cisco_WebEx_Add-On |
| FileVersion: | 3200.0.1610.13000 |
| InternalName: | Setup |
| LegalCopyright: | © 1997-2018 Cisco and/or its affiliates. All rights reserved. |
| OriginalFileName: | Cisco_WebEx_Add-On |
| ProductName: | Cisco_WebEx_Add-On |
| ProductVersion: | 3200.0,1610,1300 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2018 04:19:01 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Cisco WebEx LLC |
| FileDescription: | Cisco_WebEx_Add-On |
| FileVersion: | 3200.0.1610.13000 |
| InternalName: | Setup |
| LegalCopyright: | © 1997-2018 Cisco and/or its affiliates. All rights reserved. |
| OriginalFilename: | Cisco_WebEx_Add-On |
| ProductName: | Cisco_WebEx_Add-On |
| ProductVersion: | 3200.0,1610,1300 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Apr-2018 04:19:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001D288 | 0x0001D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64533 |
.rdata | 0x0001F000 | 0x0000B65C | 0x0000B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75487 |
.data | 0x0002B000 | 0x00003F80 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.4654 |
.rsrc | 0x0002F000 | 0x00008170 | 0x00008200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38131 |
.reloc | 0x00038000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61797 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.6961 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.79436 | 488 | UNKNOWN | English - United States | RT_ICON |
4 | 3.55571 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 5.40809 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.11851 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 2.80677 | 142 | UNKNOWN | English - United States | RT_STRING |
8 | 2.47786 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 4.75041 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 5.05013 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
WININET.dll |
ole32.dll |
urlmon.dll |
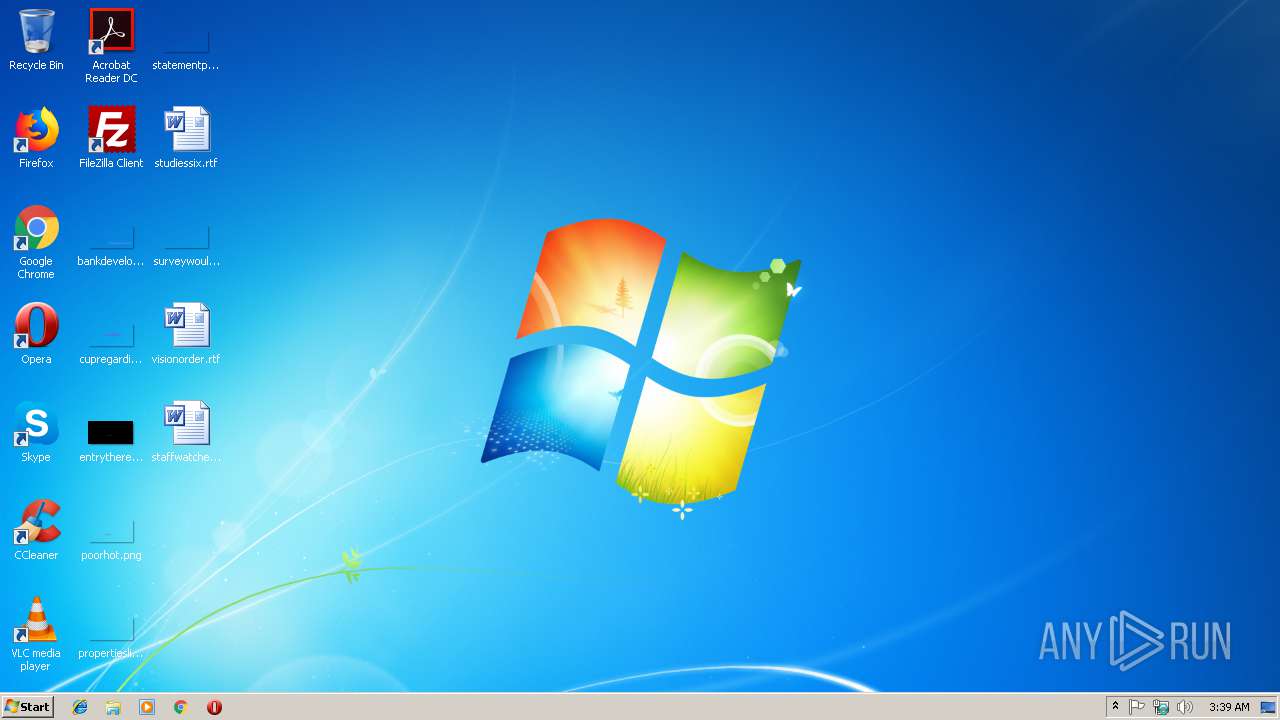
Total processes
35
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
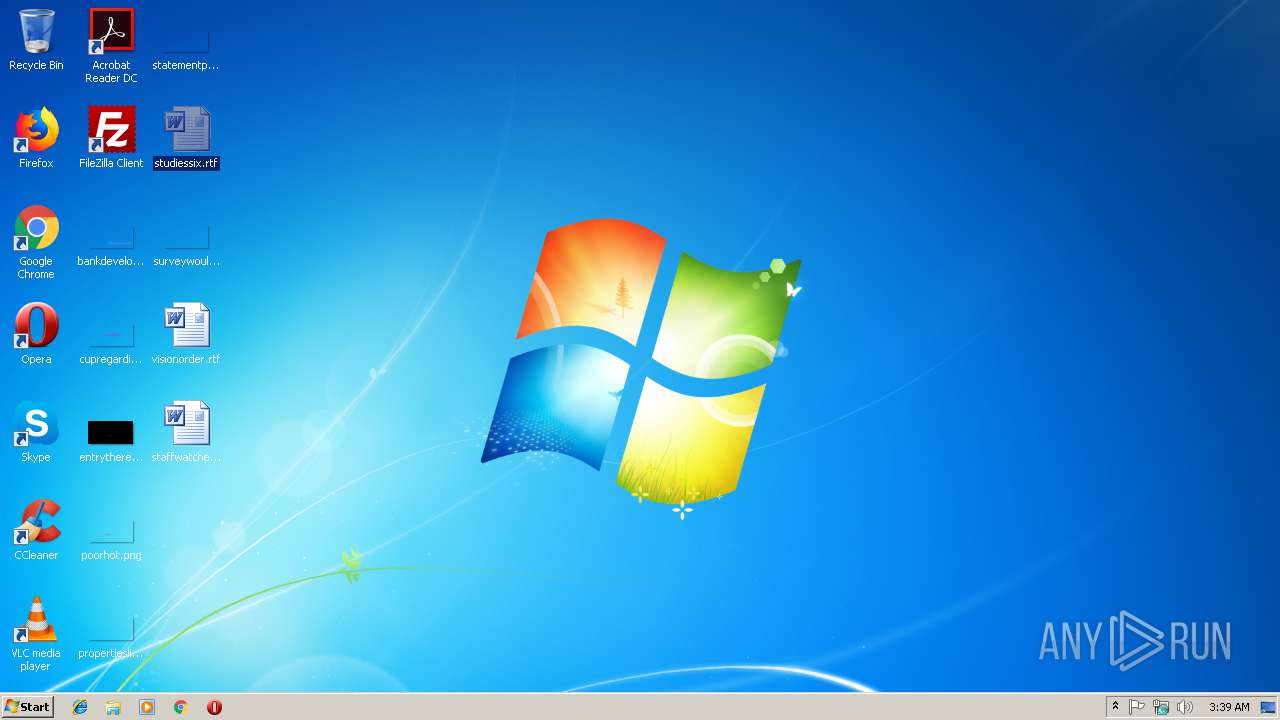
| 2032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\studiessix.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\studiessix.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\Cisco_WebEx_Add-On.exe" | C:\Users\admin\AppData\Local\Temp\Cisco_WebEx_Add-On.exe | explorer.exe | ||||||||||||
User: admin Company: Cisco WebEx LLC Integrity Level: MEDIUM Description: Cisco_WebEx_Add-On Exit code: 0 Version: 3200.0.1610.13000 Modules
| |||||||||||||||
| 4008 | /r | C:\ProgramData\WebEx\CiscoWebExStart.exe | Cisco_WebEx_Add-On.exe | ||||||||||||
User: admin Company: Cisco WebEx LLC Integrity Level: MEDIUM Description: Cisco WebEx Meeting Exit code: 1 Version: 10032,999,2018,426 Modules
| |||||||||||||||
Total events
1 548
Read events
1 415
Write events
107
Delete events
26
Modification events
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\wbx |
| Operation: | write | Name: | |
Value: Cisco WebEx Meeting | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\wbx |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\wbx\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\ProgramData\WebEx\webex.exe | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\wbx\shell\open\command |
| Operation: | write | Name: | |
Value: C:\ProgramData\WebEx\webex.exe "%1" | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\wbx |
| Operation: | write | Name: | Content Type |
Value: application/wbx | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\MIME\Database\Content Type\application/wbx |
| Operation: | write | Name: | Extension |
Value: .wbx | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CLASSES_ROOT\.wbx |
| Operation: | write | Name: | |
Value: wbx | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\User Agent\Post Platform |
| Operation: | write | Name: | wbx 1.0.0 |
Value: | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\ProtocolExecute\wbx |
| Operation: | write | Name: | WarnOnOpen |
Value: 0 | |||
| (PID) Process: | (4008) CiscoWebExStart.exe | Key: | HKEY_CURRENT_USER\Software\WebEx\ElevationPolicy |
| Operation: | write | Name: | C:\ProgramData\WebEx\CiscoWebExStart.exe |
Value: {29BF2760-A8CE-4fe6-8EB3-8931CB415D50} | |||
Executable files
4
Suspicious files
3
Text files
9
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | Cisco_WebEx_Add-On.exe | C:\Users\admin\AppData\Local\Temp\PreA6F2.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF928.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B8B9198E-DE60-4997-B9A1-8AB28E22C5CB}.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B67096FF-11FF-48D7-985B-A3678271A984}.tmp | — | |
MD5:— | SHA256:— | |||
| 2032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR17BC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0C52A066-388C-4DA6-A361-20CB99BBD750}.tmp | — | |
MD5:— | SHA256:— | |||
| 2032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{02F6022D-3973-420E-A4DD-7BB83D39A54D}.tmp | — | |
MD5:— | SHA256:— | |||
| 4008 | CiscoWebExStart.exe | C:\ProgramData\WebEx\chrome.json | text | |
MD5:— | SHA256:— | |||
| 3112 | Cisco_WebEx_Add-On.exe | C:\ProgramData\WebEx\firefox.json | text | |
MD5:— | SHA256:— | |||
| 3112 | Cisco_WebEx_Add-On.exe | C:\Users\admin\AppData\Local\Google\Chrome\Application\Plugins\npatgpc.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Cisco_WebEx_Add-On.exe | WbxMapViewOfFile szMapFileName=WBX_TRACE_MAPVIEW_MAP_NAME_PRE_3112
|
Cisco_WebEx_Add-On.exe | WbxMapViewOfFile szMapFileName=WBX_TRACE_MAPVIEW_MAP_NAME_PRE_3112
|
Cisco_WebEx_Add-On.exe | WbxMapViewOfFile new lpBaseAddress=21561344
|
Cisco_WebEx_Add-On.exe | wbxtra_process_exit ->wbxtra_lib_clean
|
Cisco_WebEx_Add-On.exe | wbxtra_lib_clean start
|
Cisco_WebEx_Add-On.exe | wbxtra_lib_clean ->WbxUnmapViewOfFile
|
Cisco_WebEx_Add-On.exe | WbxUnmapViewOfFile lpBaseAddress=21561344
|
Cisco_WebEx_Add-On.exe | WbxMapViewOfFile AddMapFileRef=0 lpBaseAddress=21561344
|
Cisco_WebEx_Add-On.exe | WbxMapViewOfFile AddMapFileRef data.dwRefCount=0
|
Cisco_WebEx_Add-On.exe | wbxtra_lib_clean end
|