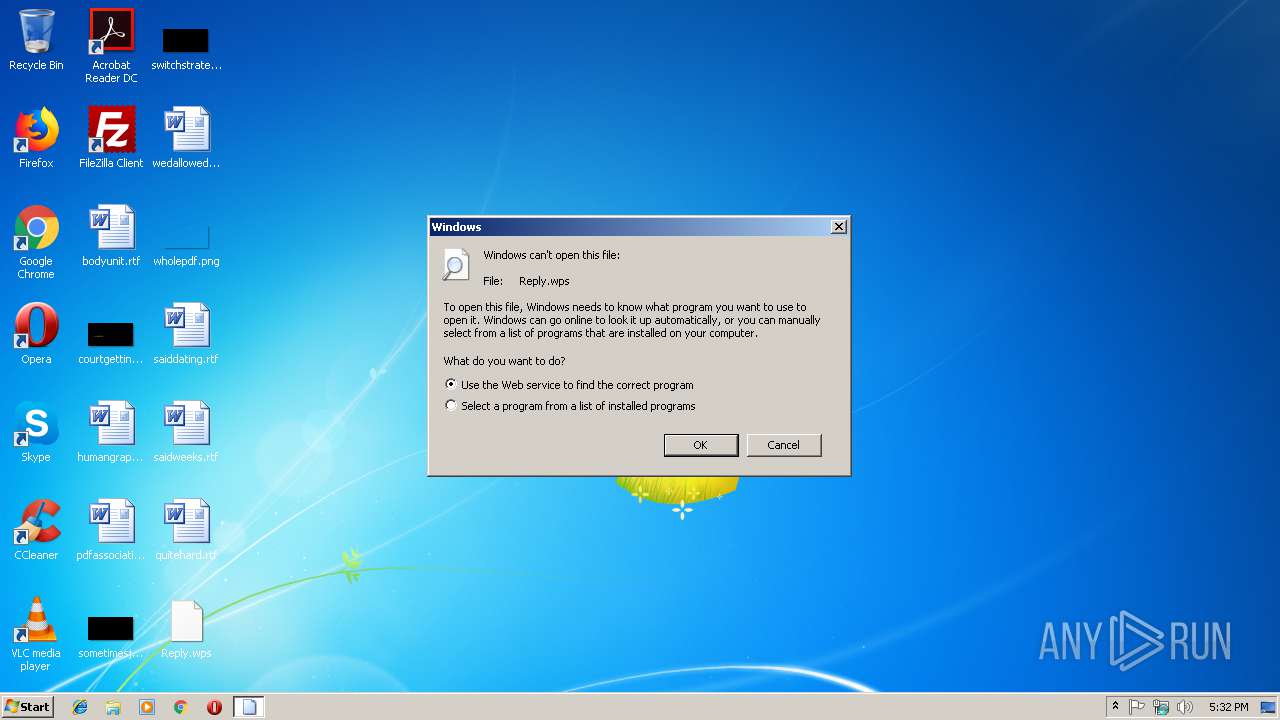
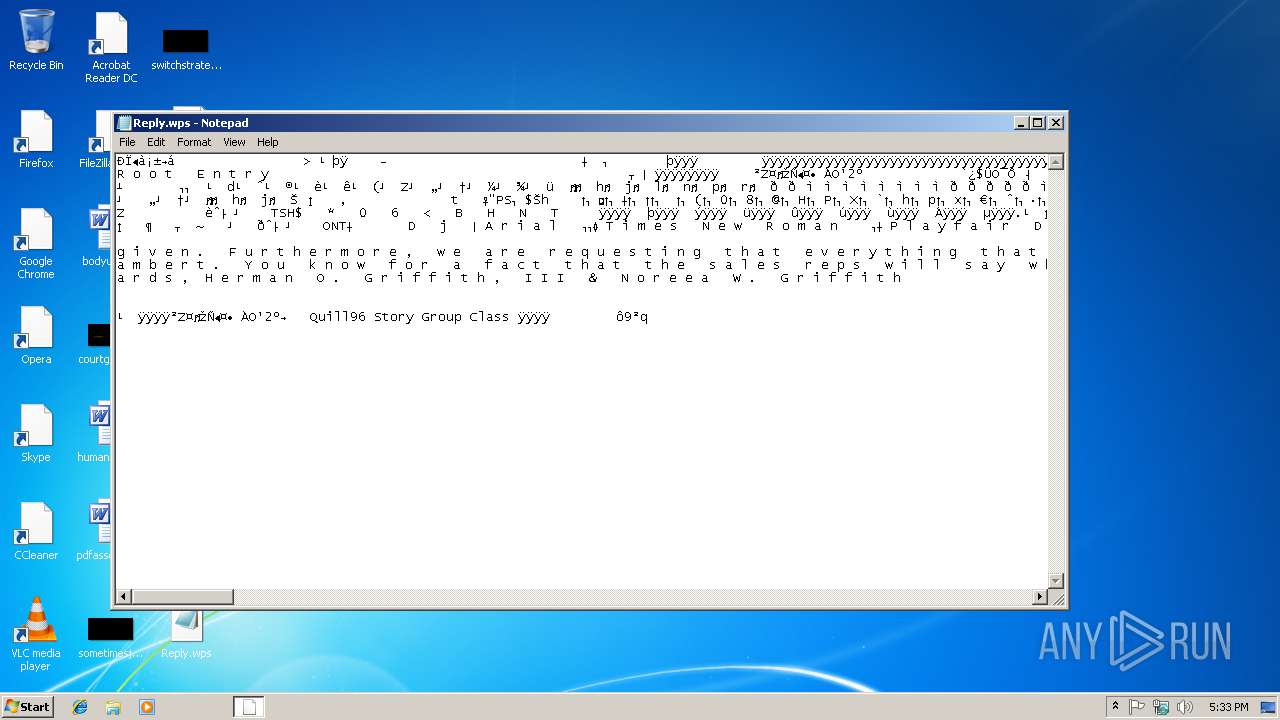
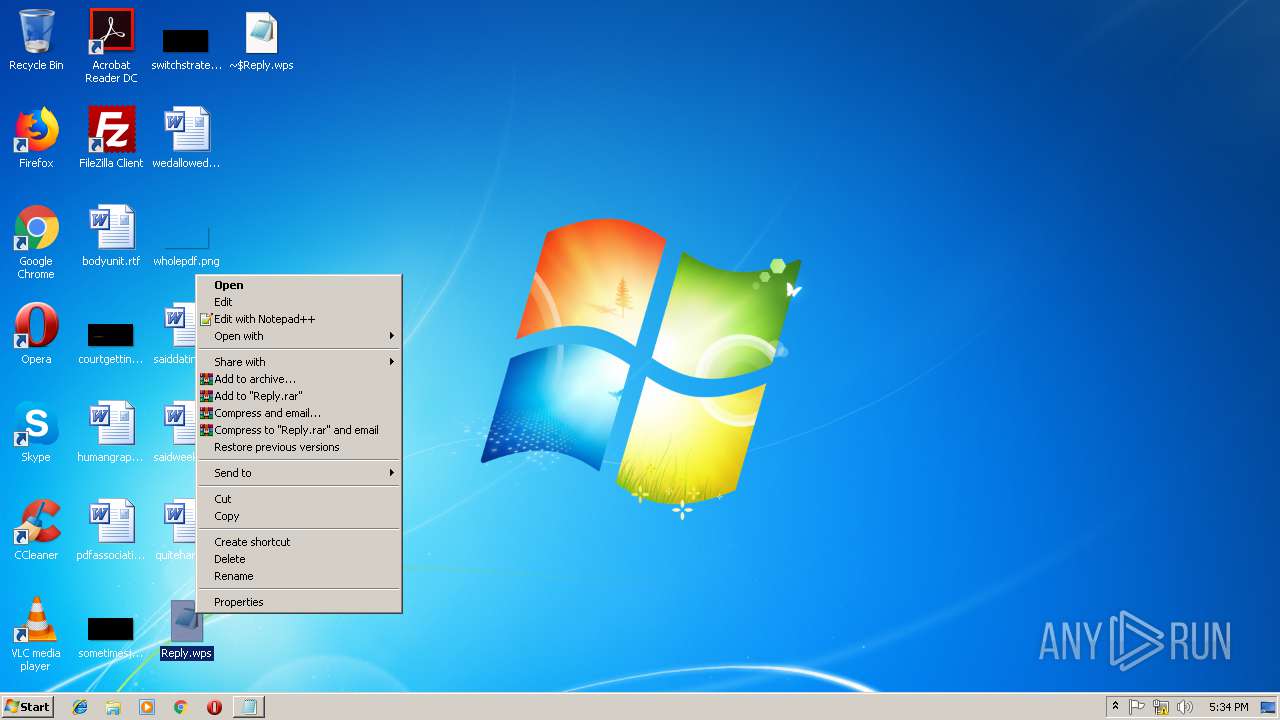
| File name: | Reply.wps |
| Full analysis: | https://app.any.run/tasks/0a28d84b-1bca-4fd6-9de3-36f5f8ed36e0 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 17:32:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/CDFV2 |
| File info: | Composite Document File V2 Document, Cannot read section info |
| MD5: | D54A69A2822EAD598261081B45F23E0F |
| SHA1: | 3BA60440492849C0FEC9EE7BC6D1CEE4ADFF9019 |
| SHA256: | 5ADE47ABF189F38D8E2BF327C99AB5B35FAF0D4C066AC7583F1D667ACBF7158A |
| SSDEEP: | 96:6IhJN7EZCQHaaEcrn7FINpVhnCJpQ8uWZoyrUbEpf4IIBz4CwJYh1WDIffHRffHv:6ItxQPEOncZnCJFbYYQNj0gxnRZ |
MALICIOUS
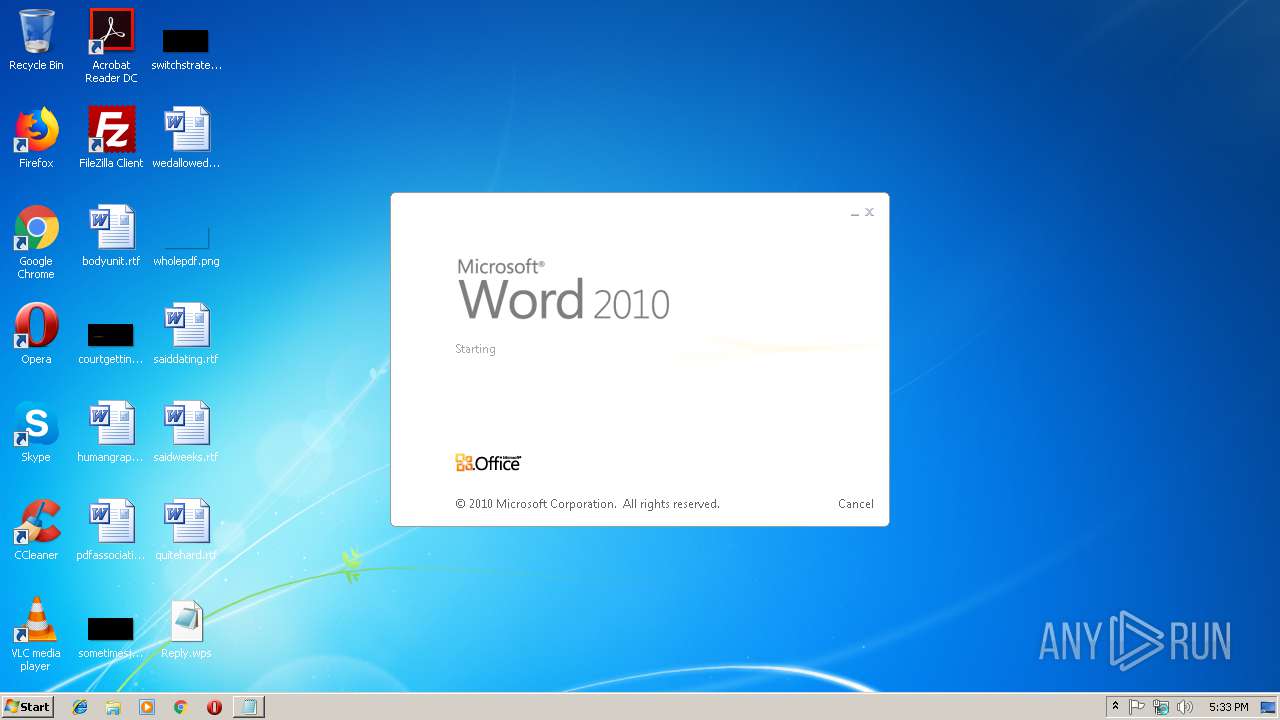
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3224)
SUSPICIOUS
Creates files in the user directory
- notepad++.exe (PID: 3744)
INFO
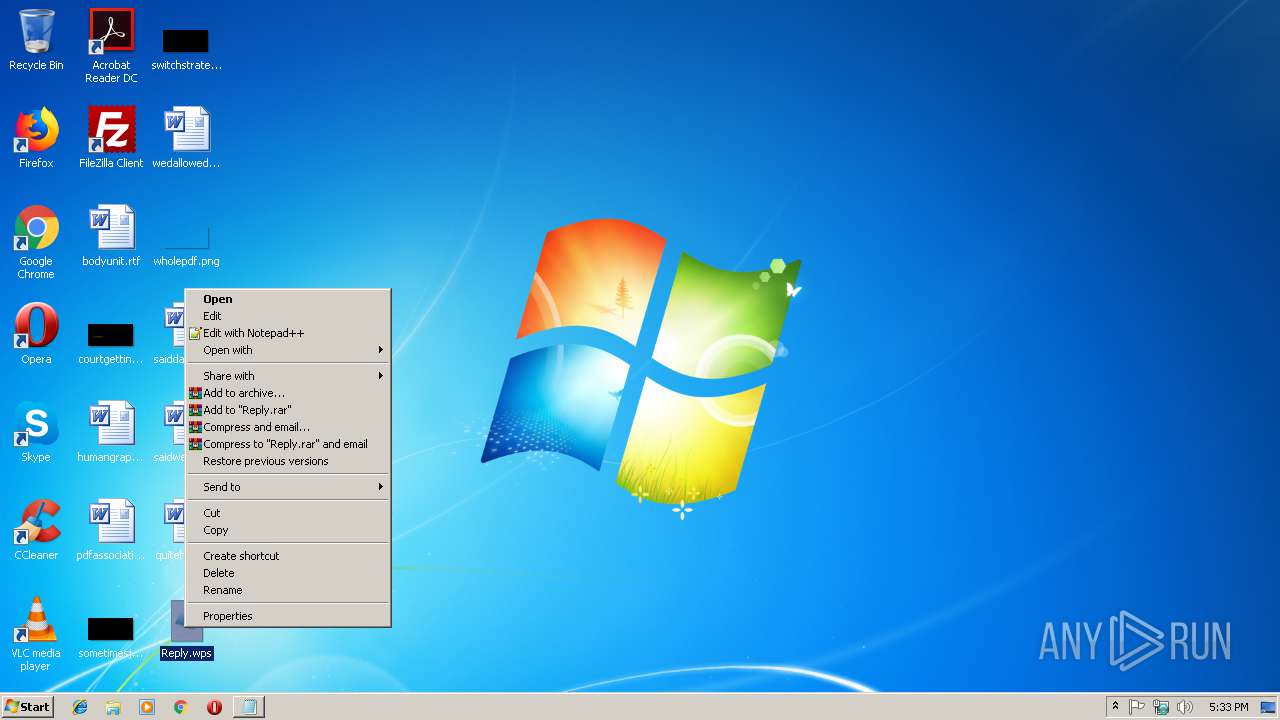
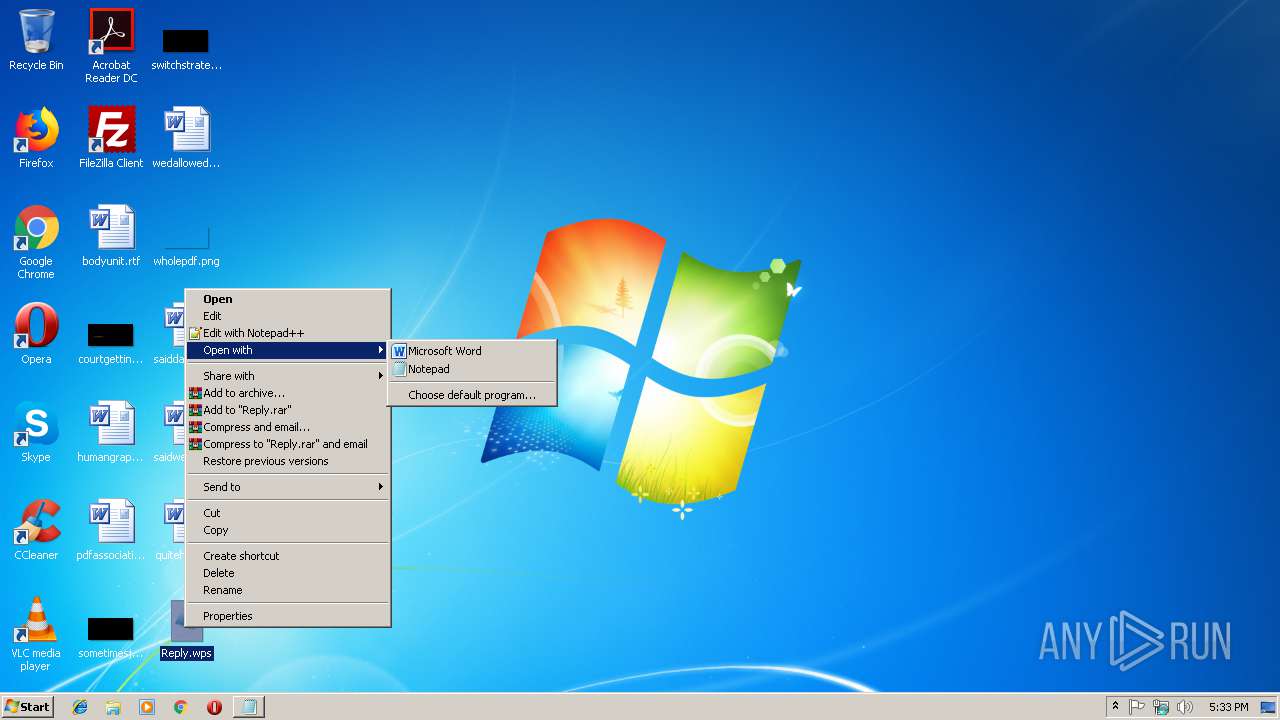
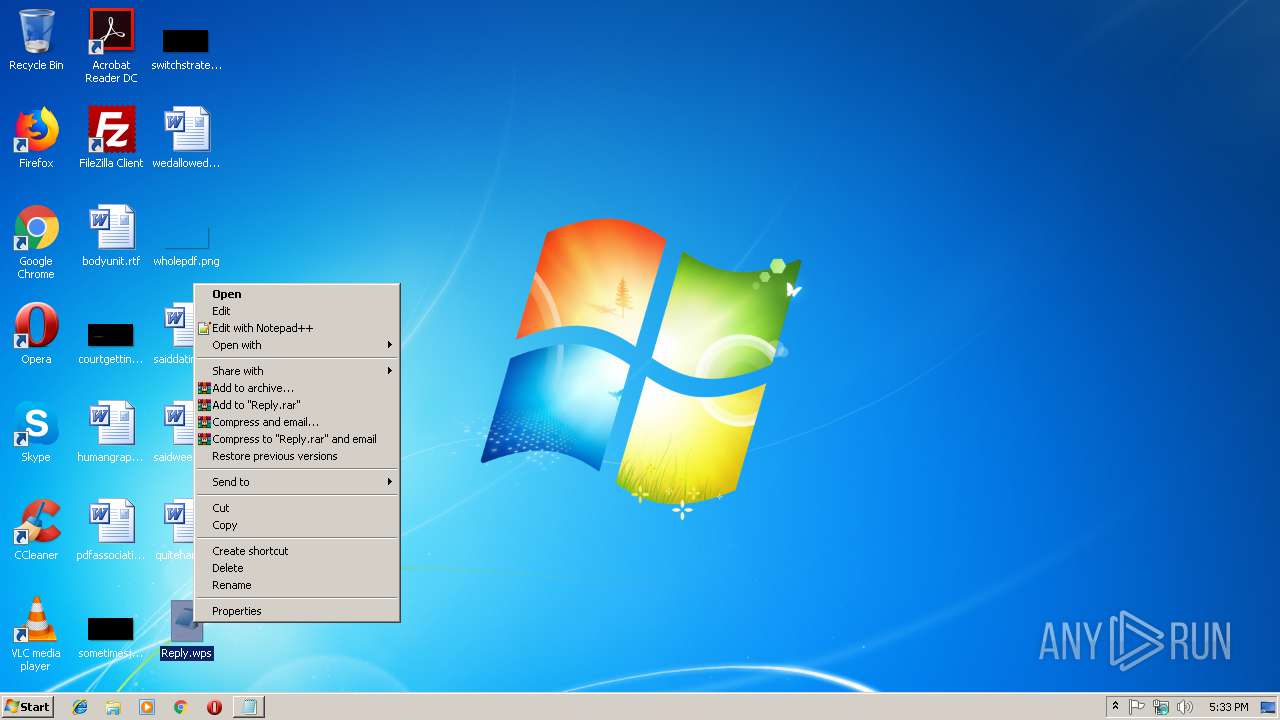
Modifies the open verb of a shell class
- rundll32.exe (PID: 3060)
Creates files in the user directory
- WINWORD.EXE (PID: 3224)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .wps | | | Microsoft Works text document (84.1) |
|---|
EXIF
FlashPix
| CompObjUserTypeLen: | 26 |
|---|---|
| CompObjUserType: | Quill96 Story Group Class |
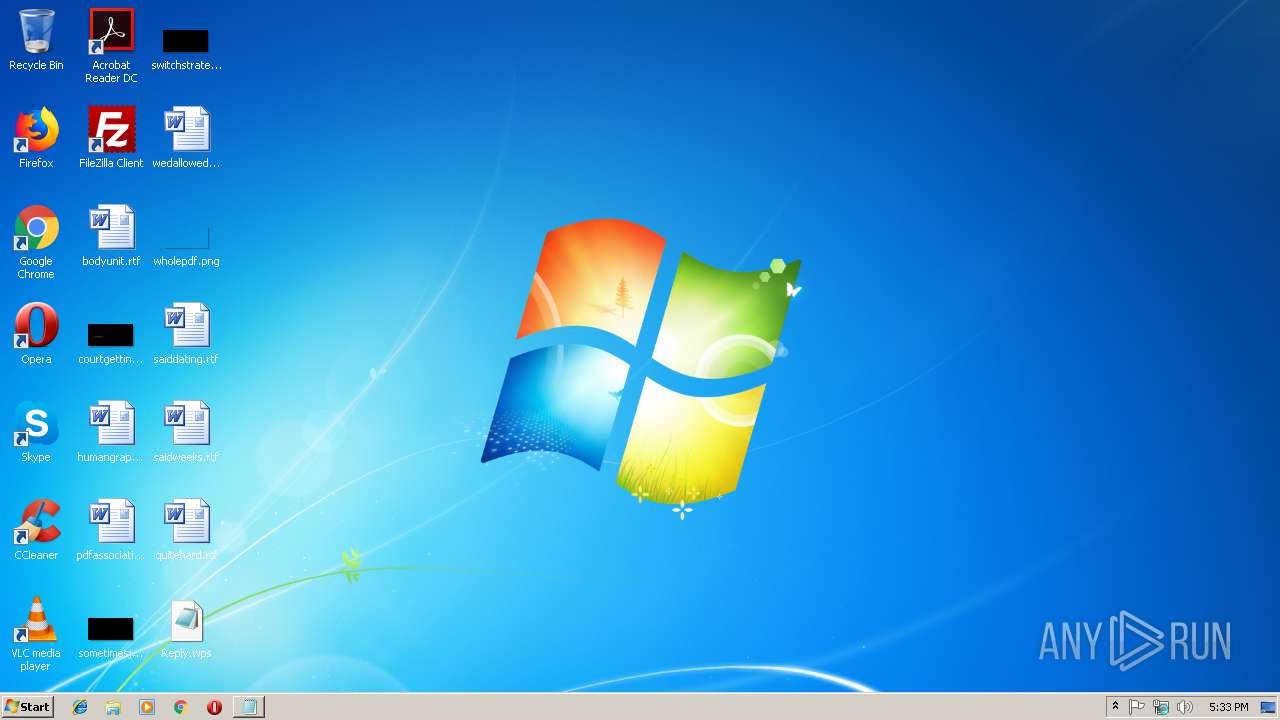
Total processes
38
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
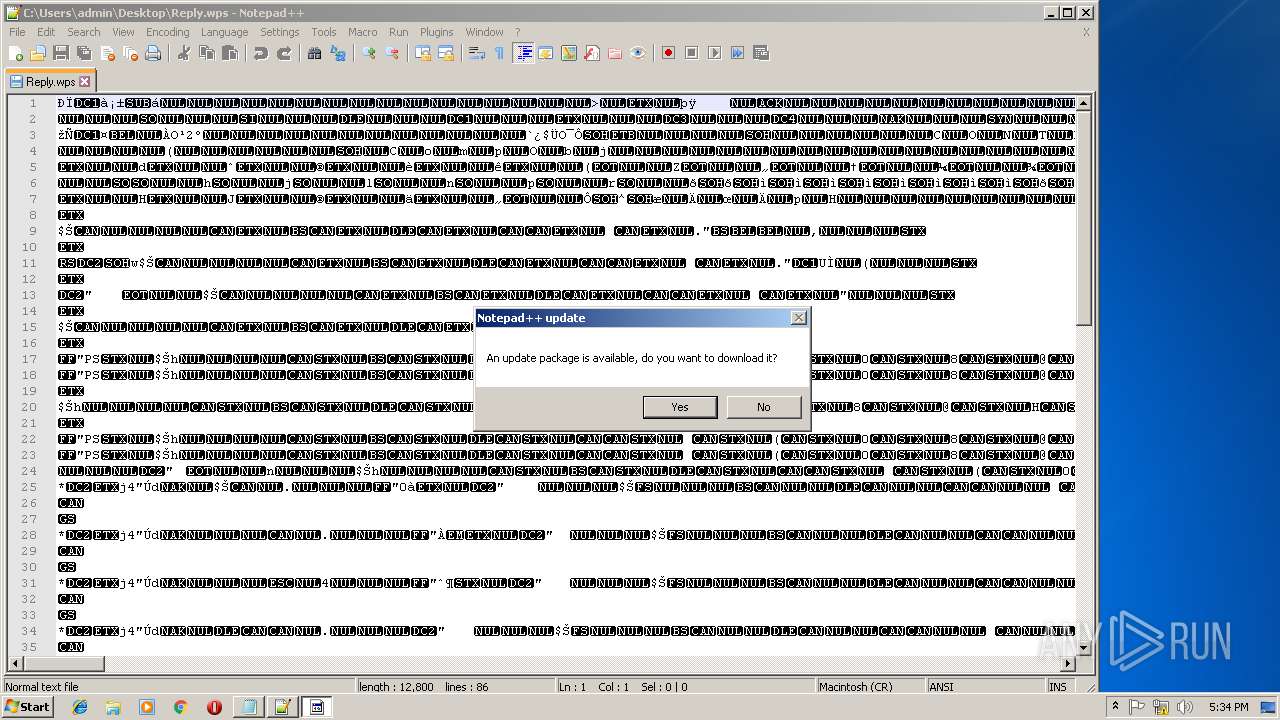
| 1848 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2292 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Reply.wps | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
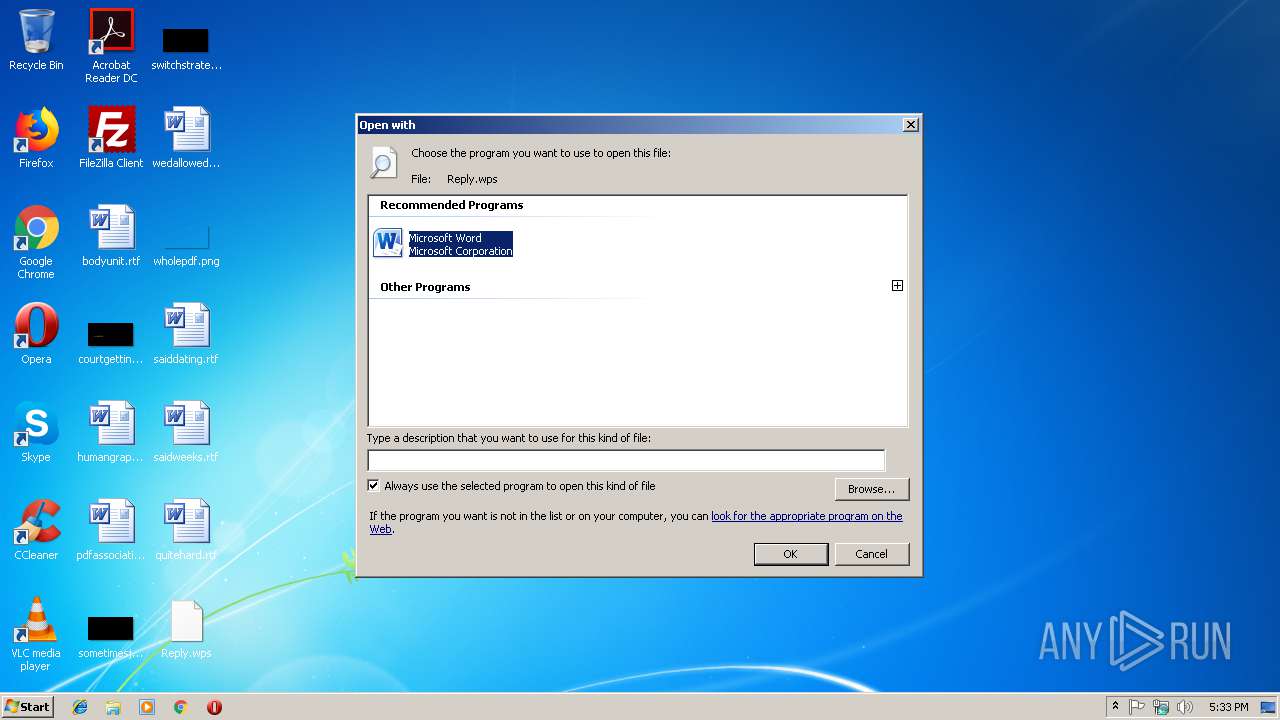
| 3060 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\Reply.wps | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Reply.wps" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
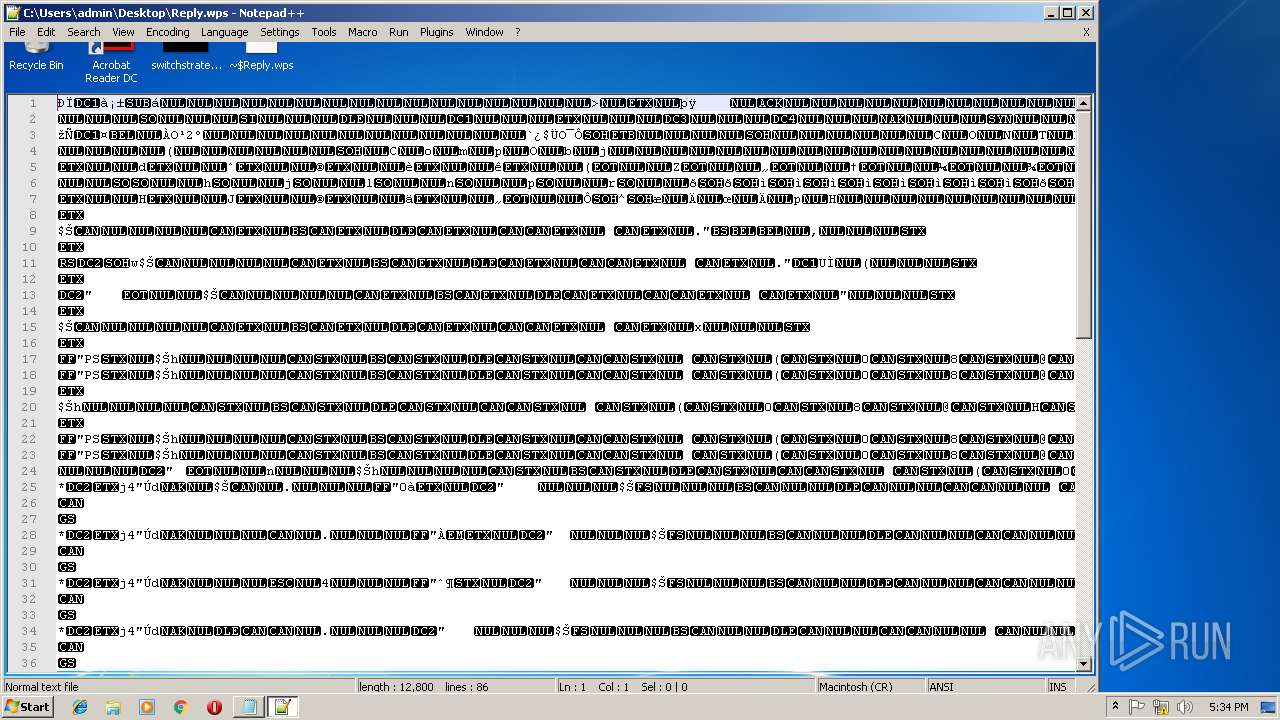
| 3744 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Reply.wps" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Common Files\Microsoft Shared\TextConv\Wksconv\WKCONV.EXE" Local\3192WKC2209656 | C:\Program Files\Common Files\Microsoft Shared\TextConv\Wksconv\WKCONV.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft® Works 6.0 - 9.0 WP RTF Export Converter Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
1 076
Read events
927
Write events
138
Delete events
11
Modification events
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (3060) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB507.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF08D14CEBA912590A.TMP | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF34D7ABFA12087C11.TMP | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFF23D5234A5D24AC.TMP | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_33F03A1A-7627-4F4A-BC4E-2DF4FFC4B50A.0\Reply.wps | — | |
MD5:— | SHA256:— | |||
| 3972 | WKCONV.EXE | C:\Users\admin\AppData\Local\Temp\OICE_33F03A1A-7627-4F4A-BC4E-2DF4FFC4B50A.0\~DFDCC1122B2BD1535F.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | WKCONV.EXE | C:\Users\admin\AppData\Local\Temp\OICE_33F03A1A-7627-4F4A-BC4E-2DF4FFC4B50A.0\22928 | — | |
MD5:— | SHA256:— | |||
| 3972 | WKCONV.EXE | C:\Users\admin\AppData\Local\Temp\OICE_33F03A1A-7627-4F4A-BC4E-2DF4FFC4B50A.0\~DF860DB162C2AC4B16.TMP | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA80264DB2E21F0D3.TMP | — | |
MD5:— | SHA256:— | |||
| 3224 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{25D723C9-243D-46EF-A215-A82D66B6EB9F}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | unknown | der | 471 b | whitelisted |
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.106.50:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
1848 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | TAG 'f2yg': CreateSandBoxedProcessWorker() is called
|
WINWORD.EXE | TAG 'b10e': Created desktop: Microsoft Office Isolated Environment
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|