| File name: | spread.vbe |
| Full analysis: | https://app.any.run/tasks/67562337-626e-41e9-bb03-f9ac86cb0a36 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2025, 14:20:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 9E211DDE65FCB4C5641AB3A170941043 |
| SHA1: | 714FBA73C57EC19C81326BFF854752722819AB5F |
| SHA256: | 5ADDE2D5E13AFEABD05FEA8C9174A26F63E96F7404B57EE5478252A7EF535D3E |
| SSDEEP: | 24:GsjsU7JF23LLU/RybEdfphdHSYckOXGu8OvyBzT:GQ71F27I/JphdyYc3Gu8O8 |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5400)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5400)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5400)
SUSPICIOUS
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 5400)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 5400)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 5400)
Process drops python dynamic module
- 91qsdf.exe (PID: 1760)
Executable content was dropped or overwritten
- 91qsdf.exe (PID: 1760)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 5400)
Process drops legitimate windows executable
- 91qsdf.exe (PID: 1760)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5400)
The process drops C-runtime libraries
- 91qsdf.exe (PID: 1760)
Application launched itself
- 91qsdf.exe (PID: 1760)
Loads Python modules
- 91qsdf.exe (PID: 2324)
Reads security settings of Internet Explorer
- 91qsdf.exe (PID: 2324)
There is functionality for taking screenshot (YARA)
- 91qsdf.exe (PID: 2324)
Possible usage of Discord/Telegram API has been detected (YARA)
- 91qsdf.exe (PID: 2324)
INFO
Drops encrypted VBS script (Microsoft Script Encoder)
- wscript.exe (PID: 5400)
- 91qsdf.exe (PID: 2324)
The process uses the downloaded file
- wscript.exe (PID: 5400)
- 91qsdf.exe (PID: 2324)
Reads the computer name
- 91qsdf.exe (PID: 1760)
- 91qsdf.exe (PID: 2324)
- identity_helper.exe (PID: 1200)
Checks supported languages
- 91qsdf.exe (PID: 1760)
- 91qsdf.exe (PID: 2324)
- identity_helper.exe (PID: 1200)
Checks proxy server information
- wscript.exe (PID: 5400)
- 91qsdf.exe (PID: 2324)
The sample compiled with english language support
- 91qsdf.exe (PID: 1760)
Create files in a temporary directory
- 91qsdf.exe (PID: 1760)
PyInstaller has been detected (YARA)
- 91qsdf.exe (PID: 1760)
Drops encrypted JS script (Microsoft Script Encoder)
- 91qsdf.exe (PID: 2324)
Application launched itself
- msedge.exe (PID: 2996)
- msedge.exe (PID: 4320)
Reads Microsoft Office registry keys
- 91qsdf.exe (PID: 2324)
Manual execution by a user
- msedge.exe (PID: 4320)
Reads Environment values
- identity_helper.exe (PID: 1200)
Application based on Rust
- 91qsdf.exe (PID: 2324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .vbe | | | VBScript Encoded script (100) |
|---|
Total processes
151
Monitored processes
32
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4624 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2292 --field-trial-handle=2296,i,4342875214279442424,11225238253889633691,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5832 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | "C:\Users\admin\91qsdf.exe" | C:\Users\admin\91qsdf.exe | wscript.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2580 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2284 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\91qsdf.exe" | C:\Users\admin\91qsdf.exe | 91qsdf.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2992 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4120 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
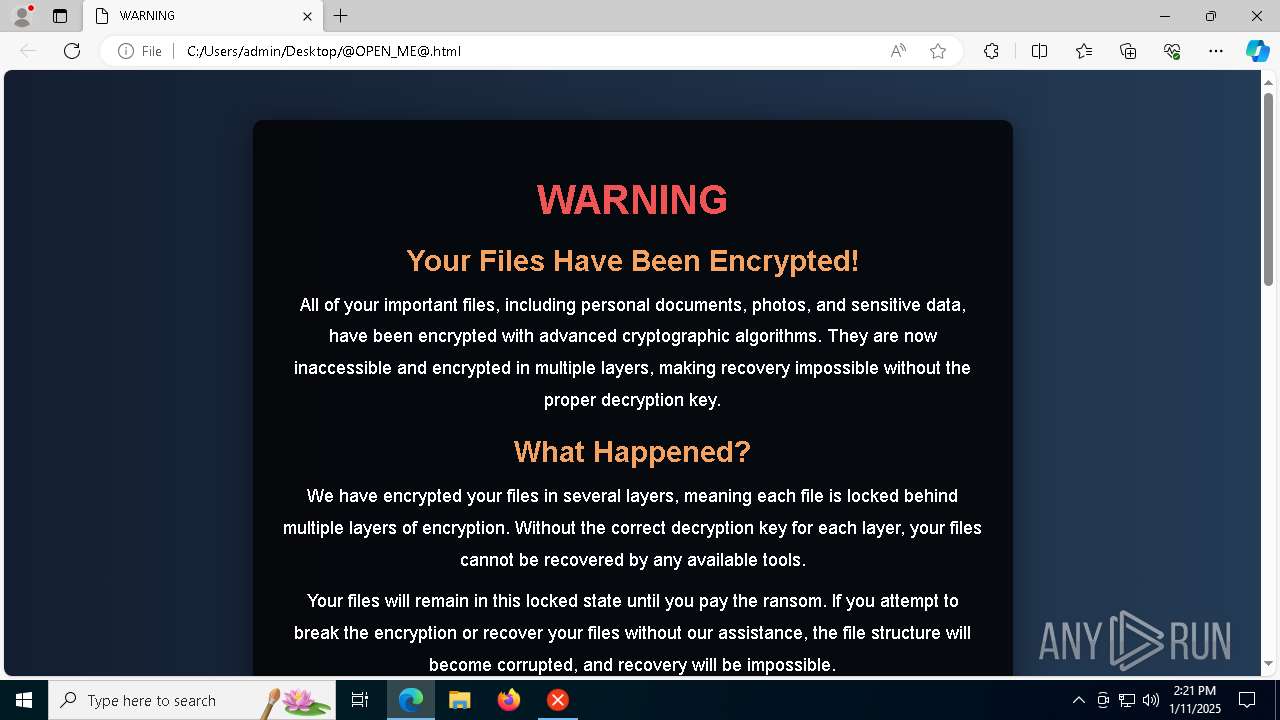
| 2996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Users\admin\Desktop\@OPEN_ME@.html | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 91qsdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=2276,i,9087112112061349104,10632004566093962491,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
8 720
Read events
8 697
Write events
23
Delete events
0
Modification events
| (PID) Process: | (5400) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5400) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5400) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2324) 91qsdf.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4D75537058A2F00 | |||
| (PID) Process: | (4320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4320) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 289D5A37058A2F00 | |||
Executable files
102
Suspicious files
199
Text files
979
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5400 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\Encryptor[1].exe | — | |
MD5:— | SHA256:— | |||
| 5400 | wscript.exe | C:\Users\admin\91qsdf.exe | — | |
MD5:— | SHA256:— | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\PIL\_imaging.cp312-win_amd64.pyd | executable | |
MD5:A050856A30BD6CD5B4B6278DA8C266CE | SHA256:F44FEE1DD1C49E647FBFC60554997D6E5E6C7F578058A7799EE6870B84DF8DA2 | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\PIL\_imagingcms.cp312-win_amd64.pyd | executable | |
MD5:5AE041D7624ED5E7FBBD3BA2F5CB6D3C | SHA256:67D19452ED36656035CC57A7303EB3C7A4A2CCAB30CD2A5D50DA8F8605879BA4 | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\_queue.pyd | executable | |
MD5:7D91DD8E5F1DBC3058EA399F5F31C1E6 | SHA256:76BBA42B1392DC57A867AEF385B990FA302A4F1DCF453705AC119C9C98A36E8D | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\PIL\_imagingtk.cp312-win_amd64.pyd | executable | |
MD5:9A2DFF6A6A44FCF66669F650C1733ABA | SHA256:97974E1BBA8DFDC63C99184AA101ED86D20619129822A993C6E1659F61BA558D | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\_bz2.pyd | executable | |
MD5:DD26ED92888DE9C57660A7AD631BB916 | SHA256:324268786921EC940CBD4B5E2F71DAFD08E578A12E373A715658527E5B211697 | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\PIL\_imagingmath.cp312-win_amd64.pyd | executable | |
MD5:7B5329E2856CACDDEE405251C9A215A8 | SHA256:4B79E2275780970D81311E57A076B890433A62538E6E6BD058CC6F8E6E9CD484 | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\_asyncio.pyd | executable | |
MD5:CC0F232F2A8A359DEE29A573667E6D77 | SHA256:7A5C88CE496BAFDF31A94AE6D70B017070703BC0A7DA1DFAE7C12B21BB61030D | |||
| 1760 | 91qsdf.exe | C:\Users\admin\AppData\Local\Temp\_MEI17602\_multiprocessing.pyd | executable | |
MD5:EB859FC7F54CBA118A321440AD088096 | SHA256:14BDD15D60B9D6141009AEEDC606007C42B46C779A523D21758E57CF126DC2A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
40
DNS requests
32
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | OPTIONS | 504 | 23.53.40.8:443 | https://bzib.nelreports.net/api/report?cat=bingbusiness | unknown | — | — | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | GET | 304 | 204.79.197.239:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | unknown |
— | — | GET | 200 | 204.79.197.239:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=122.0.2365.59&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 774 b | whitelisted |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/122.0.2365.59?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=44&mngd=0&installdate=1661339457&edu=0&bphint=2&soobedate=1504771245&fg=1 | unknown | binary | 768 b | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://edge-mobile-static.azureedge.net/eccp/get?settenant=edge-config&setplatform=win&setmkt=en-US&setchannel=stable | unknown | binary | 14.3 Kb | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://edge-consumer-static.azureedge.net/mouse-gesture/config.json | unknown | binary | 101 b | whitelisted |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=domains_config_gz&version=3.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | unknown | text | 265 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3628 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5400 | wscript.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
3628 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
discord.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
2324 | 91qsdf.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |