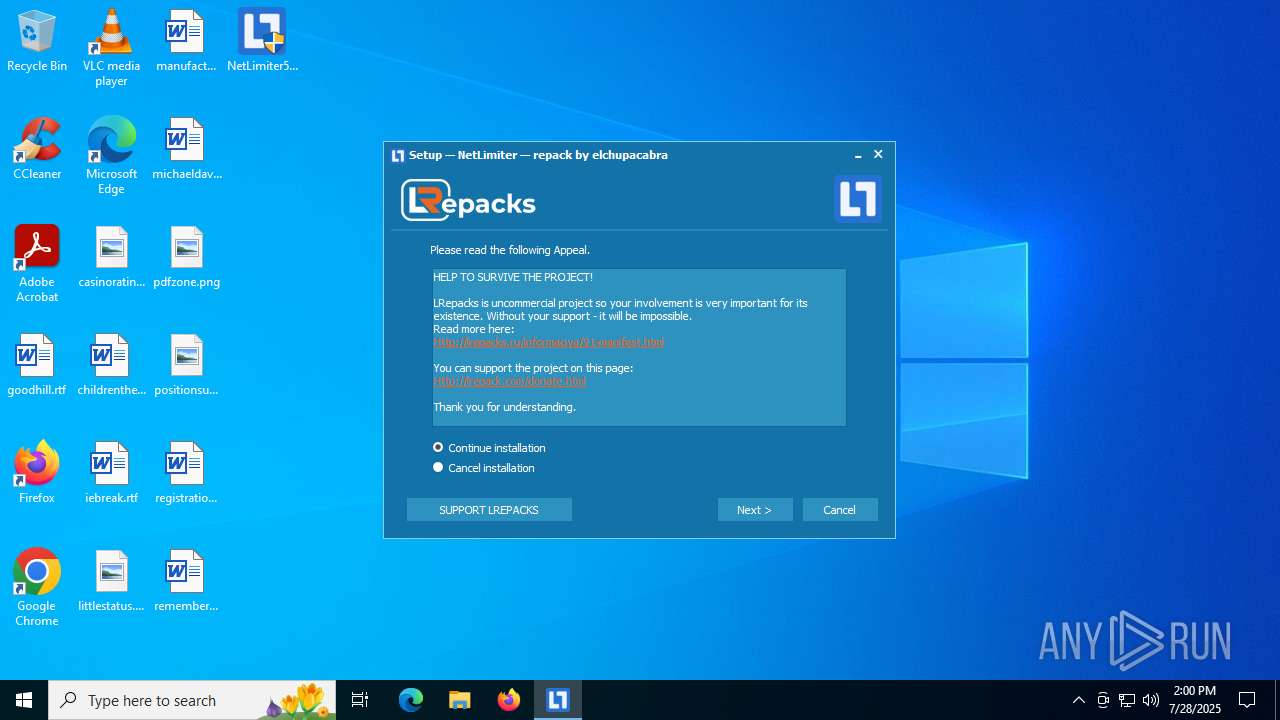
| File name: | NetLimiter5.3.25.0.exe |
| Full analysis: | https://app.any.run/tasks/d0768616-b798-4b5a-b2b5-acd3000719b9 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2025, 14:00:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | E63CFC2CA1B89DAF7DC8155E641AE307 |
| SHA1: | D6EDFF172F70719C7CE78651E8D9929E704480E2 |
| SHA256: | 5ADB96A1D90B94815C0B7C54234C2186C2A866DC146302E4C11B86E8F43B2499 |
| SSDEEP: | 98304:5CriRyXVUnqmtdRT5rjxI9T4X6N4EYeOMhSTGkvxBYPLOezWCRABOcAThhPnNaAi:hsrYMTbmsiYZa+O |
MALICIOUS
Starts NET.EXE for service management
- NetLimiter5.3.25.0.tmp (PID: 6404)
- net.exe (PID: 1936)
Changes the autorun value in the registry
- msiexec.exe (PID: 6732)
SUSPICIOUS
Reads the Windows owner or organization settings
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 6732)
Executable content was dropped or overwritten
- NetLimiter5.3.25.0.exe (PID: 3872)
- NetLimiter5.3.25.0.tmp (PID: 6404)
Process drops legitimate windows executable
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 700)
- msiexec.exe (PID: 6732)
Drops a system driver (possible attempt to evade defenses)
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 6732)
The process drops C-runtime libraries
- msiexec.exe (PID: 700)
Creates files in the driver directory
- msiexec.exe (PID: 6732)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6732)
Reads security settings of Internet Explorer
- NLSvc.exe (PID: 984)
- NLSvc.exe (PID: 3656)
- NLClientApp.exe (PID: 6584)
- NetLimiter5.3.25.0.tmp (PID: 6404)
- NLClientApp.exe (PID: 2140)
Adds/modifies Windows certificates
- NLSvc.exe (PID: 984)
Executes as Windows Service
- NLSvc.exe (PID: 3656)
Reads the date of Windows installation
- NLClientApp.exe (PID: 6584)
INFO
Checks supported languages
- NetLimiter5.3.25.0.exe (PID: 3872)
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 6732)
- msiexec.exe (PID: 700)
- msiexec.exe (PID: 5456)
- NLSvc.exe (PID: 984)
- NLSvc.exe (PID: 3656)
- NLClientApp.exe (PID: 6584)
- NLSvcCliCnnCheck.exe (PID: 2620)
- NLClientApp.exe (PID: 2140)
- identity_helper.exe (PID: 5284)
Create files in a temporary directory
- NetLimiter5.3.25.0.exe (PID: 3872)
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 700)
- msiexec.exe (PID: 5456)
- NLClientApp.exe (PID: 6584)
Reads the computer name
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 6732)
- msiexec.exe (PID: 5456)
- msiexec.exe (PID: 700)
- NLSvc.exe (PID: 984)
- NLSvc.exe (PID: 3656)
- NLClientApp.exe (PID: 6584)
- NLClientApp.exe (PID: 2140)
- identity_helper.exe (PID: 5284)
The sample compiled with english language support
- NetLimiter5.3.25.0.tmp (PID: 6404)
- msiexec.exe (PID: 6732)
- msiexec.exe (PID: 700)
The sample compiled with russian language support
- NetLimiter5.3.25.0.tmp (PID: 6404)
Creates files in the program directory
- NetLimiter5.3.25.0.tmp (PID: 6404)
- NLSvc.exe (PID: 984)
- NLClientApp.exe (PID: 6584)
- NLSvc.exe (PID: 3656)
Detects InnoSetup installer (YARA)
- NetLimiter5.3.25.0.exe (PID: 3872)
- NetLimiter5.3.25.0.tmp (PID: 6404)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6732)
- msiexec.exe (PID: 700)
Reads Environment values
- msiexec.exe (PID: 700)
- identity_helper.exe (PID: 5284)
Compiled with Borland Delphi (YARA)
- NetLimiter5.3.25.0.tmp (PID: 6404)
Creates a software uninstall entry
- msiexec.exe (PID: 6732)
Reads the machine GUID from the registry
- NLSvc.exe (PID: 984)
- NLSvc.exe (PID: 3656)
- NLClientApp.exe (PID: 6584)
- NLClientApp.exe (PID: 2140)
Launching a file from a Registry key
- msiexec.exe (PID: 6732)
Checks proxy server information
- NLSvc.exe (PID: 984)
- slui.exe (PID: 7840)
Creates files or folders in the user directory
- NLSvc.exe (PID: 984)
- NLClientApp.exe (PID: 6584)
Reads the software policy settings
- NLSvc.exe (PID: 984)
- NLSvc.exe (PID: 3656)
- NLClientApp.exe (PID: 6584)
- NLClientApp.exe (PID: 2140)
- slui.exe (PID: 7840)
Manual execution by a user
- NLClientApp.exe (PID: 6584)
- msedge.exe (PID: 4112)
Process checks computer location settings
- NLClientApp.exe (PID: 6584)
Application launched itself
- msedge.exe (PID: 5576)
- msedge.exe (PID: 5032)
- msedge.exe (PID: 4112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c14 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.3.25.0 |
| ProductVersionNumber: | 5.3.25.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | LR |
| FileDescription: | NetLimiter Setup |
| FileVersion: | 5.3.25.0.0 |
| LegalCopyright: | Copyright 2007-2025 LRepacks |
| ProductName: | NetLimiter |
| ProductVersion: | 5.3.25.0 |
Total processes
192
Monitored processes
55
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3564,i,1004689754577706341,12820652924514374680,262144 --variations-seed-version --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | C:\Windows\syswow64\MsiExec.exe -Embedding CE1FC97C01CDC98DDC74C6B2E682AE5F | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
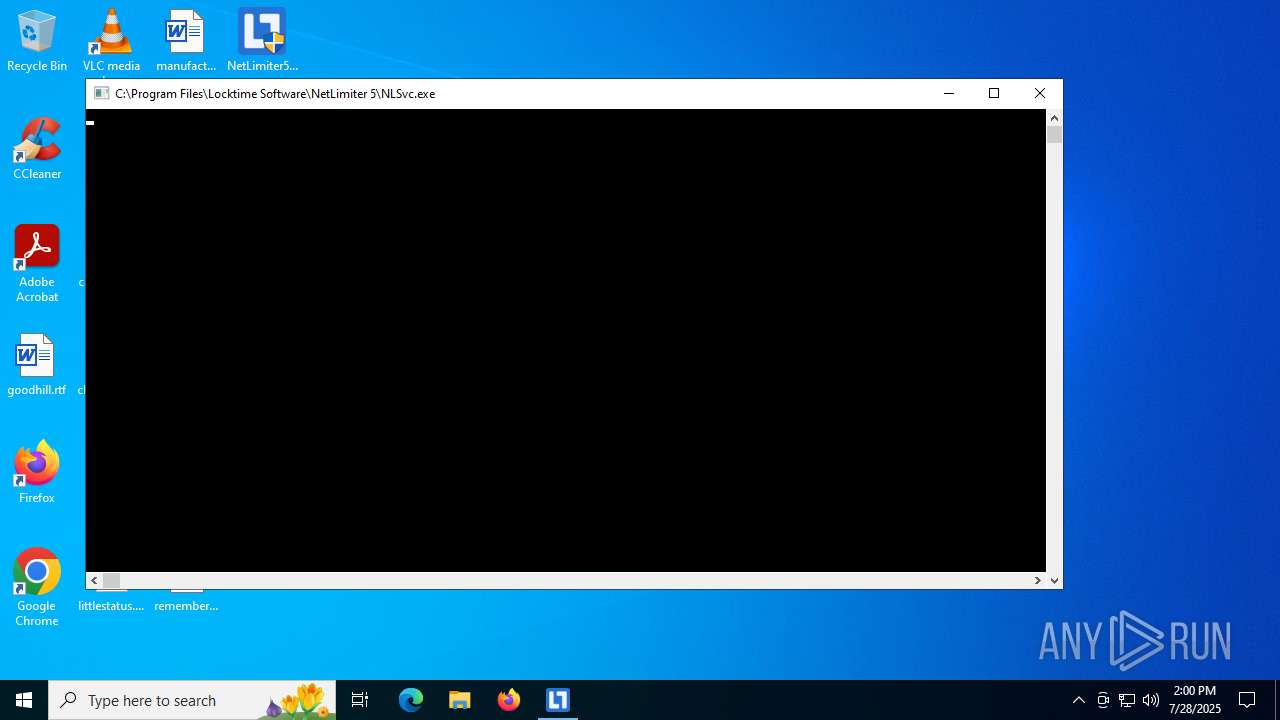
| 984 | "C:\Program Files\Locktime Software\NetLimiter 5\NLSvc.exe" /afterinstall | C:\Program Files\Locktime Software\NetLimiter 5\NLSvc.exe | msiexec.exe | ||||||||||||
User: admin Company: Locktime Software Integrity Level: HIGH Description: NLSvc Exit code: 0 Version: 5.3.25.0 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2448,i,1004689754577706341,12820652924514374680,262144 --variations-seed-version --mojo-platform-channel-handle=2436 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Users\admin\Desktop\NetLimiter5.3.25.0.exe" | C:\Users\admin\Desktop\NetLimiter5.3.25.0.exe | — | explorer.exe | |||||||||||
User: admin Company: LR Integrity Level: MEDIUM Description: NetLimiter Setup Exit code: 3221226540 Version: 5.3.25.0.0 Modules
| |||||||||||||||
| 1336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | NLSvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4280,i,1004689754577706341,12820652924514374680,262144 --variations-seed-version --mojo-platform-channel-handle=4264 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1936 | "net" stop "nlsvc" | C:\Windows\System32\net.exe | — | NetLimiter5.3.25.0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Locktime Software\NetLimiter 5\NLClientApp.exe" /install | C:\Program Files\Locktime Software\NetLimiter 5\NLClientApp.exe | — | msiexec.exe | |||||||||||
User: admin Company: Locktime Software Integrity Level: HIGH Description: NetLimiter Client Exit code: 0 Version: 5.3.25.0 Modules
| |||||||||||||||
| 2168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4024,i,1004689754577706341,12820652924514374680,262144 --variations-seed-version --mojo-platform-channel-handle=6320 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
27 777
Read events
27 401
Write events
366
Delete events
10
Modification events
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 4C1A00008E215507C8FFDB01 | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: F383DE8221B1324333D9236A9BF814ABD10BD0278B911CC65B5E4EAC04E40D58 | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\237EB3FBB1F59884FBD5819832E728B6 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\fa\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\50C2300BEAC076D439ED88022D933C74 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\nb\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\F47DD4A9B04A8C44BA7CF00216717EC0 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\hi\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\A5B3061819D24884BB124F1535F49D8B |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\pl\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\87D95A7F8D9B00843A8382D49DD5E794 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\pt-br\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\13BCF2C7DD7EF2342B45EC80E1543BE8 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\ru\NLClientApp.Core.resources.dll | |||
| (PID) Process: | (6732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\D2379D9166FDCAC42BCC76B03C0AF6F9 |
| Operation: | write | Name: | 9E609C4758ECC1B4598D849E0980E16F |
Value: C:\Program Files\Locktime Software\NetLimiter 5\tr\NLClientApp.Core.resources.dll | |||
Executable files
497
Suspicious files
324
Text files
149
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3872 | NetLimiter5.3.25.0.exe | C:\Users\admin\AppData\Local\Temp\is-J1T01.tmp\NetLimiter5.3.25.0.tmp | executable | |
MD5:EA8BEBD13F78A837C649AD56938E9E6D | SHA256:39C0A95ECD3CEA5052F2D59D617163D804A01783C4D6E7D42524C49F24526E4D | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\ISTask.dll | executable | |
MD5:86A1311D51C00B278CB7F27796EA442E | SHA256:E916BDF232744E00CBD8D608168A019C9F41A68A7E8390AA48CFB525276C483D | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\NETLIM\FamFamFam.Flags.Wpf.dll | executable | |
MD5:83983B0E8817B8246C234C0361593893 | SHA256:8A24783A5DED6EDA4A81C0C5B798E166FA0283FE30A6310ABD3E789E25CC4970 | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\MetroBlue.vsf | binary | |
MD5:295D085196B3DA13BFCD53373F82F8EE | SHA256:CBDC95EB9E7269E0C3E3BDDFD37B0918962795D80BDBA932E46EA16FF5E6CDBF | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\NETLIM\is-372FC.tmp | executable | |
MD5:83983B0E8817B8246C234C0361593893 | SHA256:8A24783A5DED6EDA4A81C0C5B798E166FA0283FE30A6310ABD3E789E25CC4970 | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\VclStylesInno.dll | executable | |
MD5:B0CA93CEB050A2FEFF0B19E65072BBB5 | SHA256:0E93313F42084D804B9AC4BE53D844E549CFCAF19E6F276A3B0F82F01B9B2246 | |||
| 6404 | NetLimiter5.3.25.0.tmp | C:\Users\admin\AppData\Local\Temp\is-VKH36.tmp\NETLIM\is-EL1II.tmp | executable | |
MD5:D7FE7B9E4AB6DC926B1C375C014C3E9D | SHA256:95484EFA24C6A6636EFF8CB8FF5CF7B7ABC4E1C9BEBE6AFB3A3F1F9565032C17 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
132
TCP/UDP connections
150
DNS requests
115
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.134:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.138:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.74:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
984 | NLSvc.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2168 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2168 | RUXIMICS.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2168 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
lrepacks.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6664 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
6664 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |