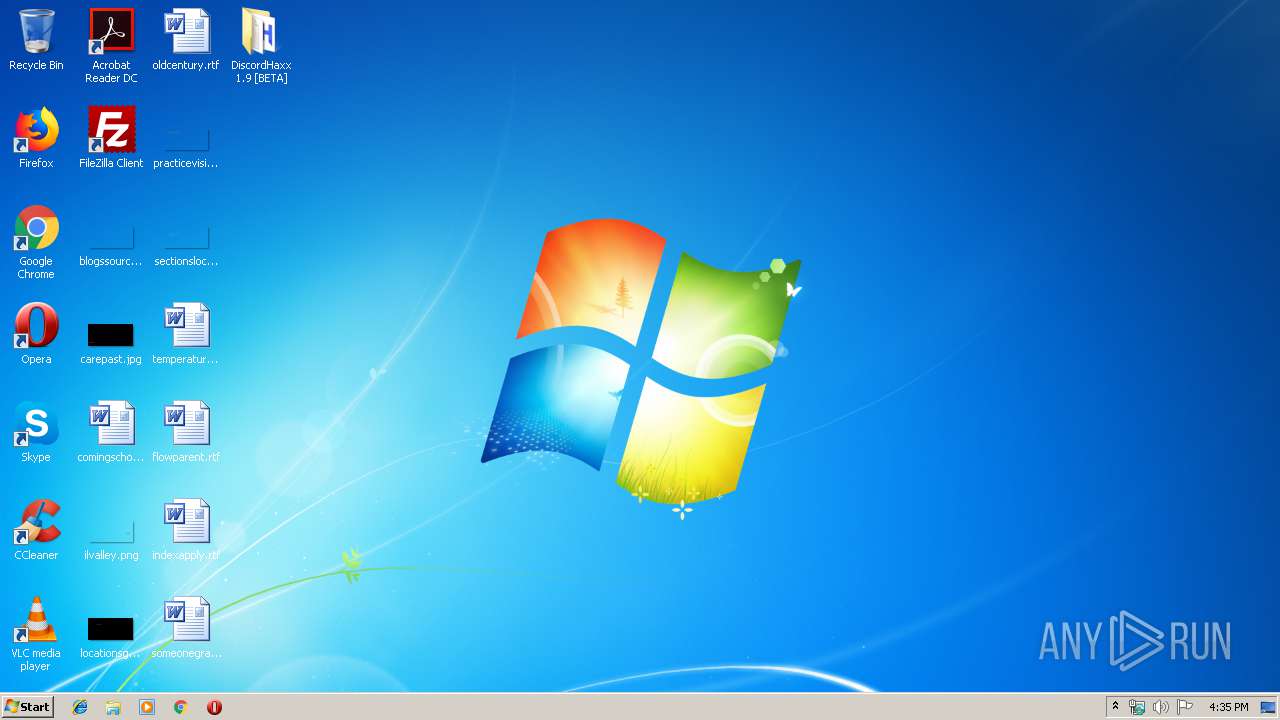
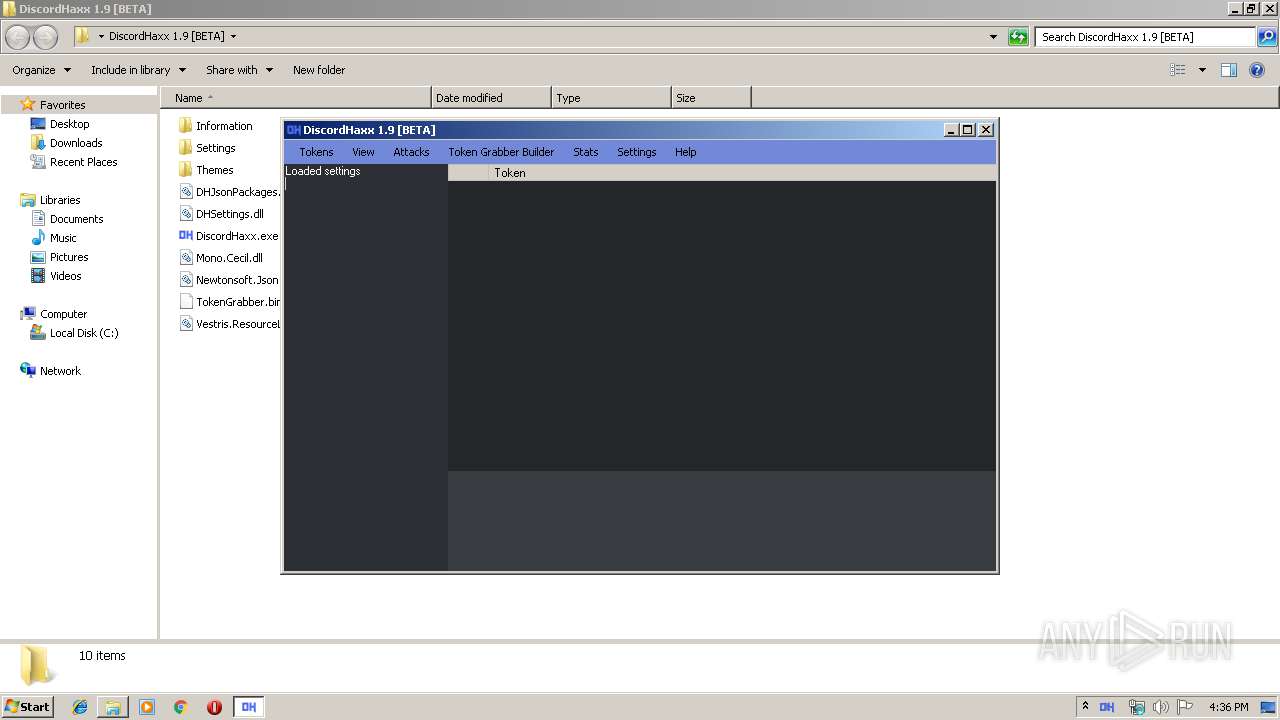
| File name: | DiscordHaxx 1.9 [BETA].zip |
| Full analysis: | https://app.any.run/tasks/c2feb93c-ce16-44f7-a868-bd31346e2009 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 15:35:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | A15C646C47F0D5E75104F316675F2E92 |
| SHA1: | 5A7E81849BE45B0E745BF46E554CCE4305E5EBB5 |
| SHA256: | 5ACEB2366B27F789FF7BF5AFF0AEC5EB3F4E2A52BE5CDB13D8767219BBFAE985 |
| SSDEEP: | 49152:2dH0zADOtKGLdhS7B7PO2tqdWi8BtJtvhA/Cyl77u:aHDDb8jc722QdWlX7v6N7u |
MALICIOUS
Loads dropped or rewritten executable
- DiscordHaxx.exe (PID: 3340)
- SearchProtocolHost.exe (PID: 776)
Application was dropped or rewritten from another process
- DiscordHaxx.exe (PID: 3340)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2952)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
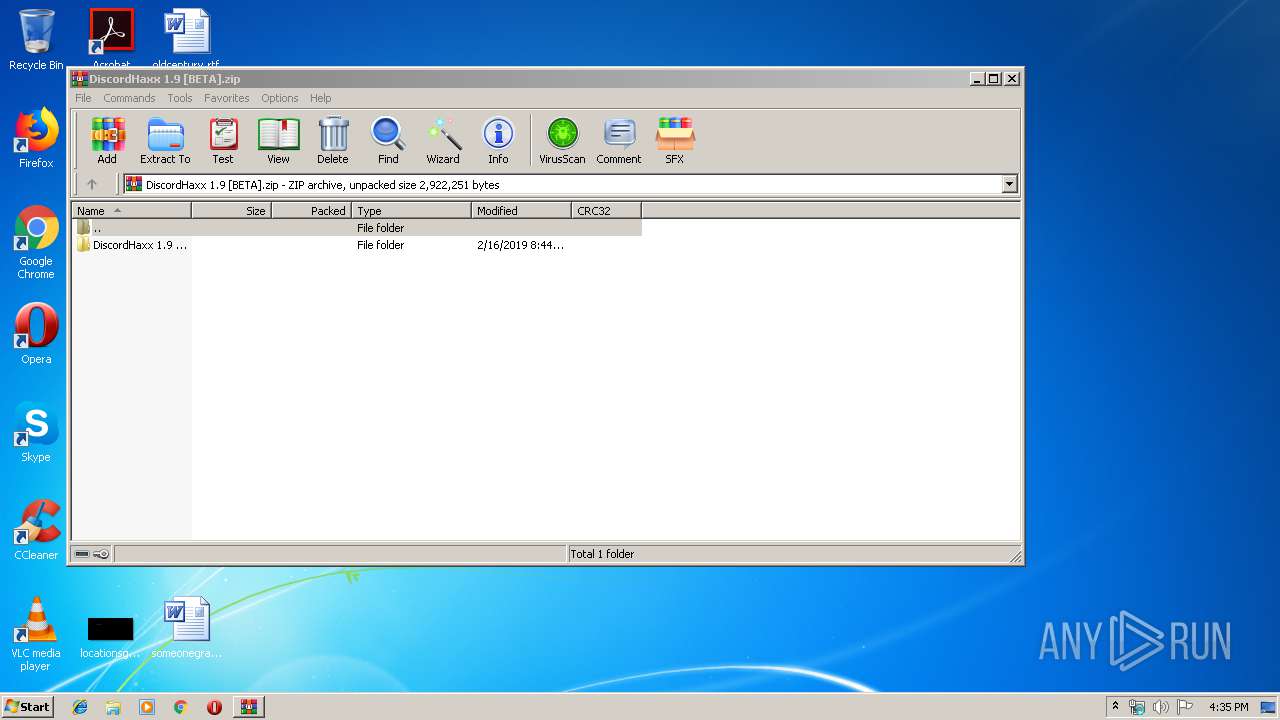
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:02:16 09:44:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | DiscordHaxx 1.9 [BETA]/ |
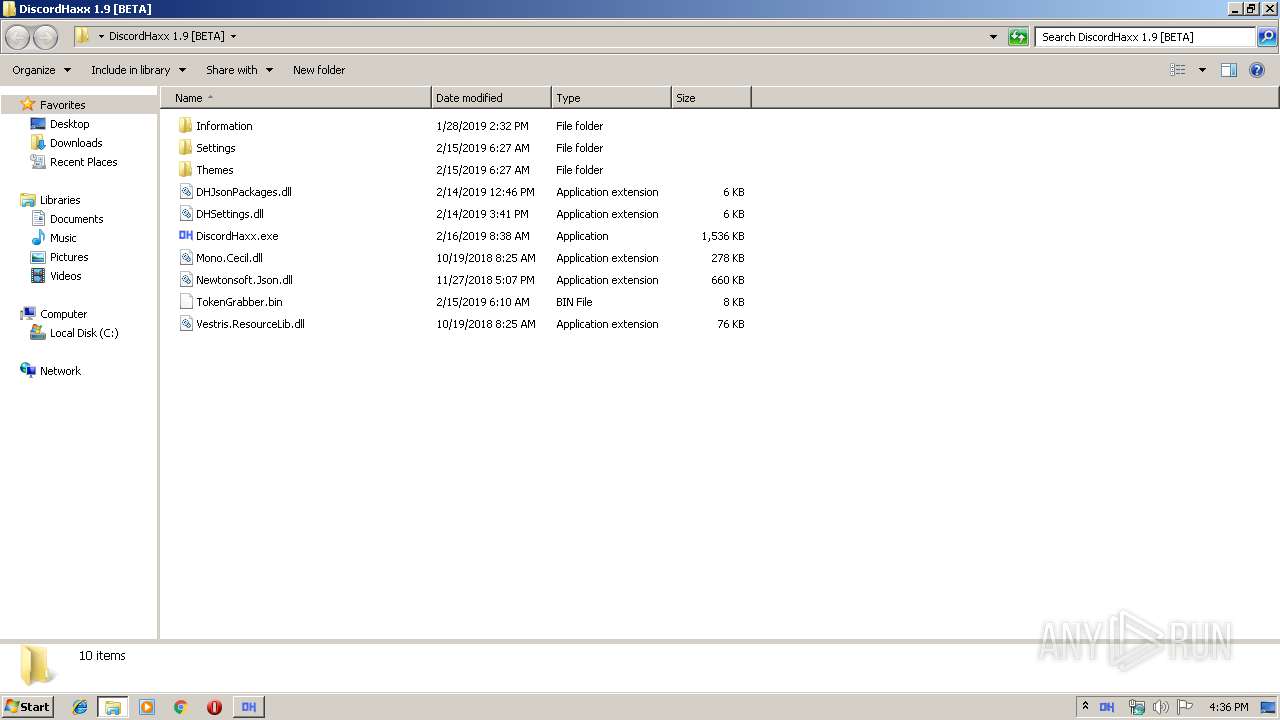
Total processes
33
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
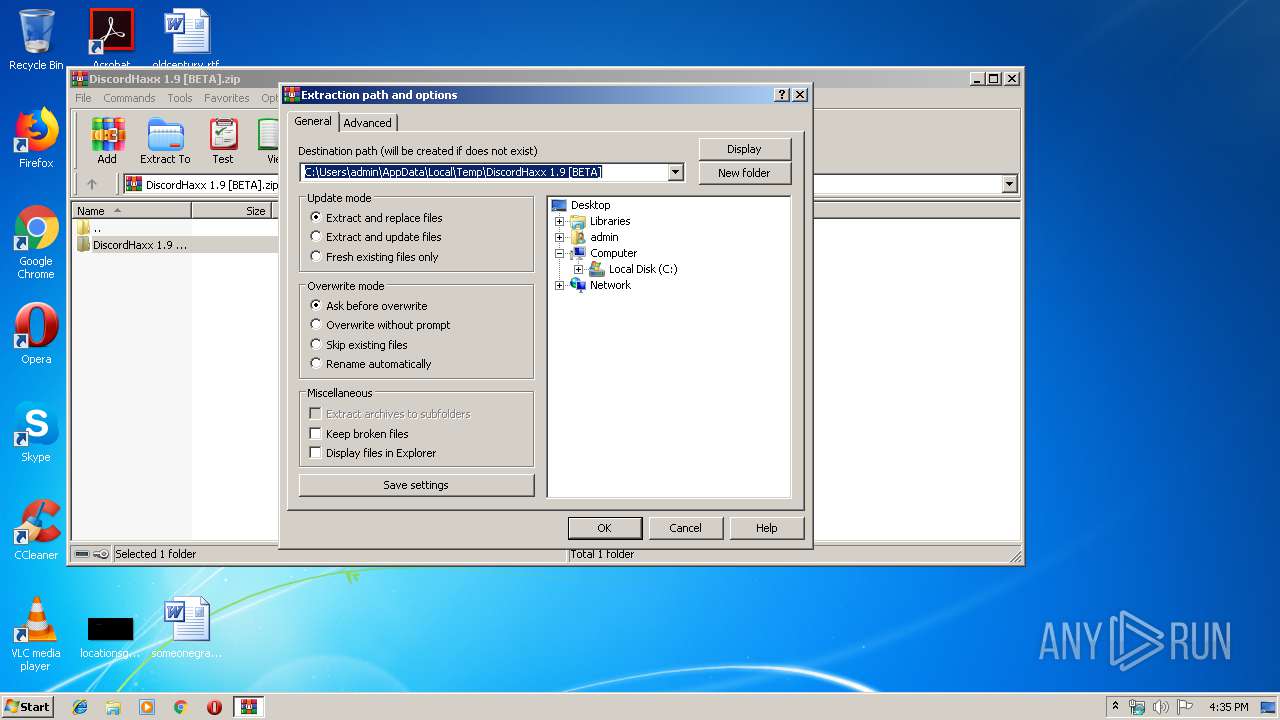
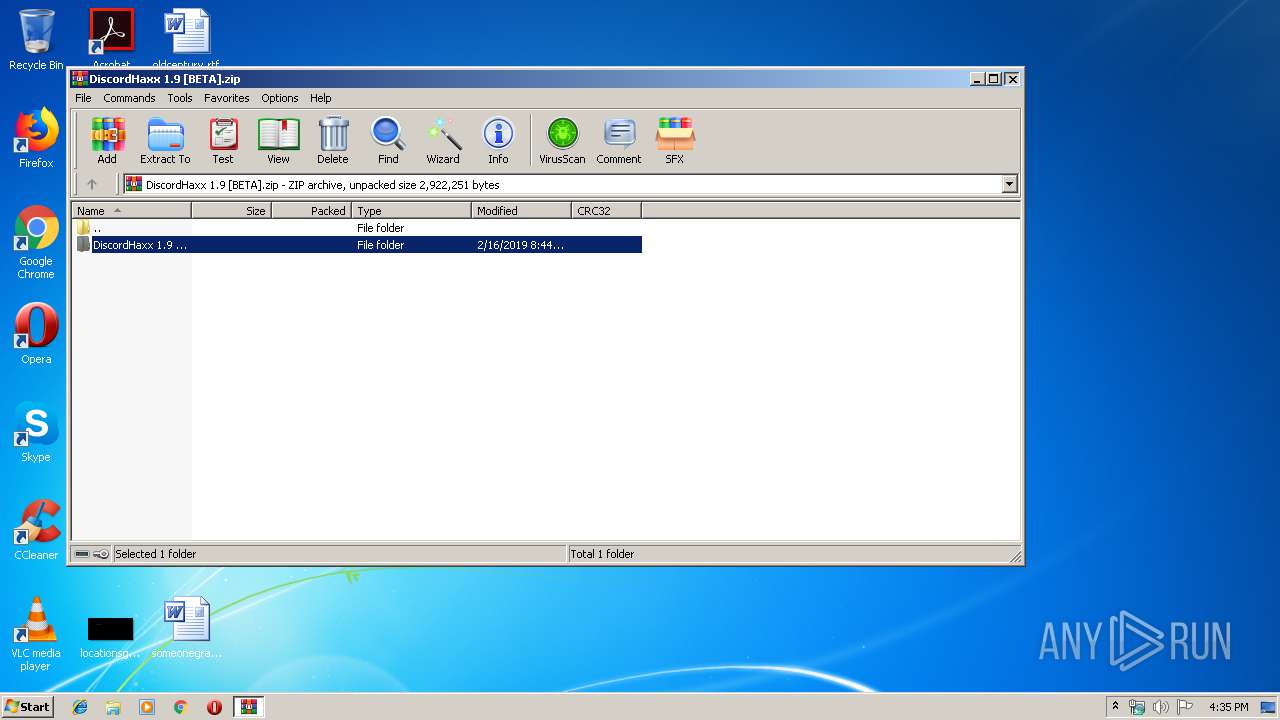
| 2952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.9 [BETA].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3340 | "C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\DiscordHaxx.exe" | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\DiscordHaxx.exe | explorer.exe | ||||||||||||
User: admin Company: iLinked Software Integrity Level: MEDIUM Description: DiscordHaxx Exit code: 0 Version: 1.8.5.0 Modules
| |||||||||||||||
Total events
836
Read events
799
Write events
37
Delete events
0
Modification events
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.9 [BETA].zip | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
7
Suspicious files
0
Text files
8
Unknown types
0
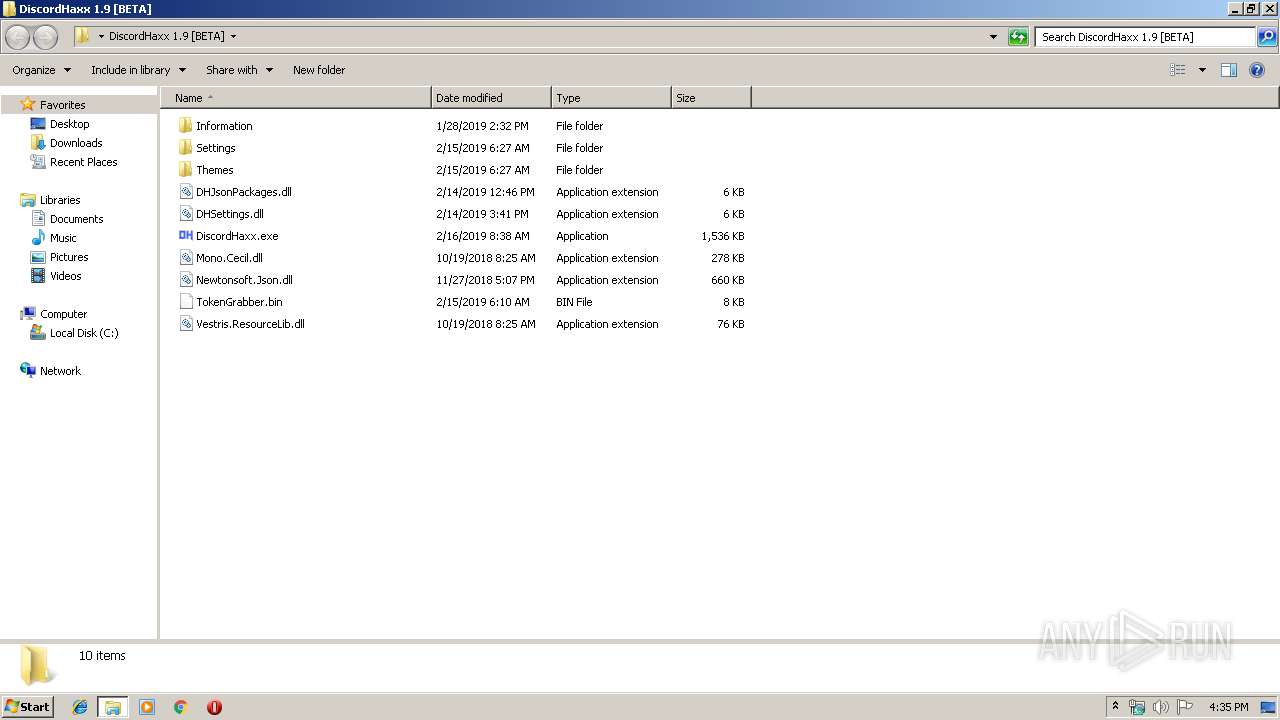
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\DHSettings.dll | executable | |
MD5:BA04E959B6071B4749A08A29EFF2FE9D | SHA256:BEECF1CED20C97A41986BB5EEC8435D8299E884F194A1FE148CB2299C27EA7F7 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Mono.Cecil.dll | executable | |
MD5:8DF4D6B5DC1629FCEFCDC20210A88EAC | SHA256:3E4288B32006FE8499B43A7F605BB7337931847A0AA79A33217A1D6D1A6C397E | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Information\README.txt | text | |
MD5:F6CD338F09657291879605F44F78A7A3 | SHA256:B6505D14BE249D624BB044EE2563F284D77C52B56FFE00BE5167CB1FFDE25479 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\DiscordHaxx.exe | executable | |
MD5:26F173E94F1FA44A405AF7A94BD8C49A | SHA256:B53AE81D91C10E6045033C814788BB537B6E5DB5DAA554FA6C4B5B75699B30F0 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Settings\Settings.json | text | |
MD5:5FD55357E3C9307C94638E2ECD9F694A | SHA256:FDF555CDAB77A9921972673917B014A1198DCCD7E37056B2214E7C0FAF4D18DB | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Themes\Icons\Flame.ico | image | |
MD5:8C9BF4B49D18598CEC89FD04DC807114 | SHA256:6A97402689EF20311547E5A565B6B859B57BDD290E24B89EA92BD723DE6030B8 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\DHJsonPackages.dll | executable | |
MD5:2E6D69E71EDA585F97BDBD6E70220EE9 | SHA256:23D7B46A8D2F24C977781C6E1583A6D8ED778380526465705E2140BCBAC139D9 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Themes\Flame.dht | text | |
MD5:974545594C3AC93B4EFDAB095728DC09 | SHA256:5FFAFE8238C26B98E8447D929E42A5FAE1BFD155560942FD19F287FC2381A787 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Themes\Icons\AppleTheme.ico | image | |
MD5:4EDE8EFF1669E9F4B8889B4DF77F8A0C | SHA256:755CBD5E30832A4AD32CCB211794BD9AD2900909CF2075F6F262C65F3FF7E893 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\DiscordHaxx 1.9 [BETA]\Newtonsoft.Json.dll | executable | |
MD5:D827DD8A8C4B2A2CFA23C7F90F3CCE95 | SHA256:B66749B81E1489FCD8D754B2AD39EBE0DB681344E392A3F49DC9235643BDBD06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |