| URL: | http://www.testautomationguru.com/selenium-webdriver-email-validation-with-disposable-email-addresses/ |
| Full analysis: | https://app.any.run/tasks/9f3e4eb0-ea68-4a95-b015-fbf921e0bcd4 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 06:29:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8F291459147DAC543BEAEFC42FD47E22 |
| SHA1: | 86EDD9C78D4DA9BB8D1D427B0608971B41CF7B42 |
| SHA256: | 5ACB31522BB216A8D3B28529B0E445F4F4E76EAB974983297FFC2D2386BEB699 |
| SSDEEP: | 3:N1KJS4kQqMKQyK3JJIXECBKkMKtA95I5AmN:Cc4ZqsH4PBVMKtA95ItN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- chrome.exe (PID: 2012)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2780)
INFO
Application launched itself
- chrome.exe (PID: 2780)
Reads the hosts file
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2012)
Changes settings of System certificates
- chrome.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8931215060859054849 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14114701710569384303 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6439116875657913651 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12320116234383706059 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8311264012198642220 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17560814780460010256 --mojo-platform-channel-handle=2888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15131314193289776594 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10122195609689896543 --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9831860031498097895 --mojo-platform-channel-handle=4624 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2784 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
627
Read events
533
Write events
89
Delete events
5
Modification events
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2780-13212656979380500 |
Value: 259 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
93
Text files
203
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\150fa11f-89b2-4c9c-8942-8ef5b802eeb5.tmp | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF168939.TMP | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF168939.TMP | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168939.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
82
DNS requests
76
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
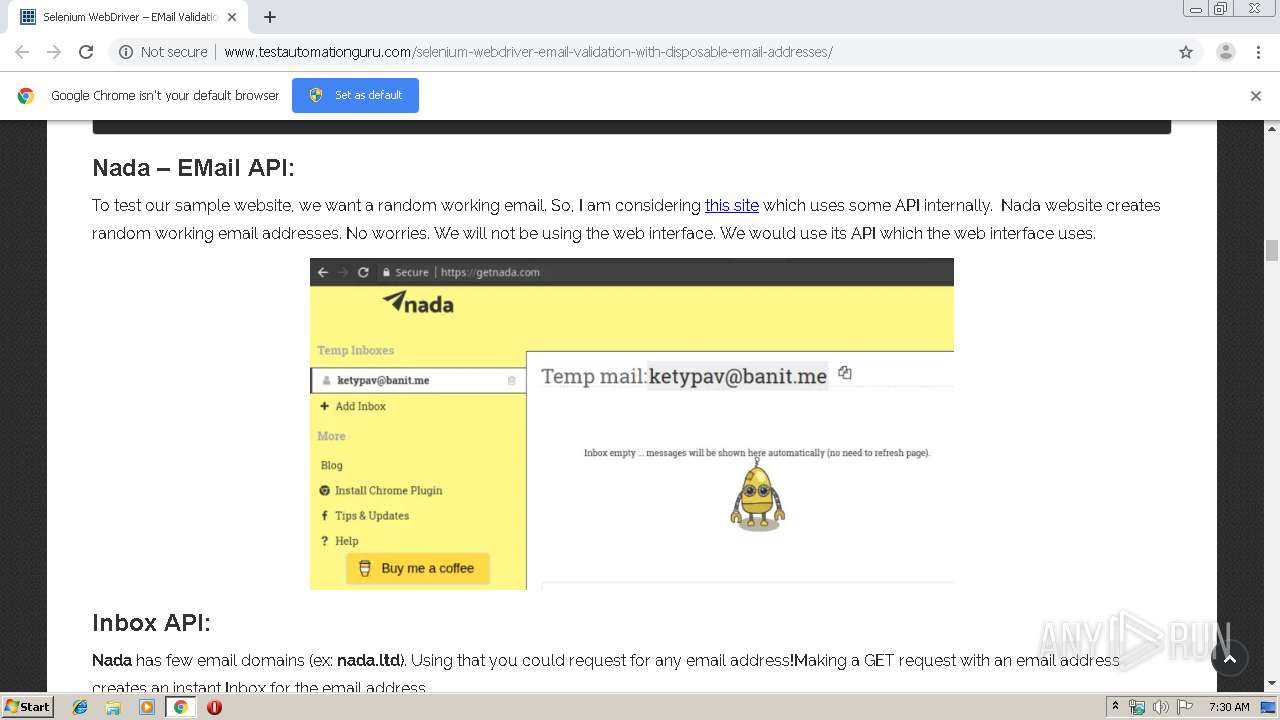
2012 | chrome.exe | GET | 200 | 192.0.77.2:80 | http://i0.wp.com/www.vinsguru.com/wp-content/uploads/2018/04/nada-email-header.gif?resize=800%2C429 | US | image | 405 Kb | whitelisted |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.testautomationguru.com/selenium-webdriver-email-validation-with-disposable-email-addresses/ | US | html | 29.3 Kb | malicious |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.vinsguru.com/wp-content/themes/suevafree/style.css | US | text | 10.8 Kb | malicious |
2012 | chrome.exe | GET | 200 | 52.216.128.149:80 | http://s3.amazonaws.com/mailmunch/static/site.js | US | text | 6.69 Kb | shared |
2012 | chrome.exe | GET | 200 | 172.217.21.234:80 | http://fonts.googleapis.com/css?family=Roboto%3A400%2C100%2C100italic%2C300%2C300italic%2C400italic%2C500%2C500italic%2C700%2C700italic%2C900%2C900italic%7CRaleway%3A400%2C800%2C900%2C700%2C600%2C500%2C300%2C200%2C100%7CAllura&subset=latin%2Cgreek%2Cgreek-ext%2Cvietnamese%2Ccyrillic-ext%2Clatin-ext%2Ccyrillic&ver=4.5.18 | US | text | 1.60 Kb | whitelisted |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.vinsguru.com/wp-content/plugins/wp-share-buttons/style/front.end.css?ver=4.5.18 | US | text | 311 b | malicious |
2012 | chrome.exe | GET | 200 | 172.217.18.170:80 | http://maps.googleapis.com/maps/api/js?key=AIzaSyDgiem5bbeBic1L2fke9TiNU71piPtzI2o&v=3.exp&ver=4.5.18 | US | text | 33.7 Kb | whitelisted |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.vinsguru.com/wp-content/themes/suevafree/assets/css/template.css?ver=4.5.18 | US | text | 201 b | malicious |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.vinsguru.com/wp-content/themes/suevafree/assets/css/woocommerce.css?ver=4.5.18 | US | text | 6.73 Kb | malicious |
2012 | chrome.exe | GET | 200 | 162.241.216.113:80 | http://www.vinsguru.com/wp-content/themes/suevafree/assets/css/prettyPhoto.css?ver=4.5.18 | US | text | 3.79 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2012 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2012 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2012 | chrome.exe | 162.241.216.113:80 | www.testautomationguru.com | CyrusOne LLC | US | malicious |
2012 | chrome.exe | 192.0.77.2:80 | i0.wp.com | Automattic, Inc | US | suspicious |
2012 | chrome.exe | 172.217.18.170:80 | maps.googleapis.com | Google Inc. | US | whitelisted |
2012 | chrome.exe | 172.217.21.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2012 | chrome.exe | 172.217.18.99:80 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2012 | chrome.exe | 192.0.77.32:80 | s0.wp.com | Automattic, Inc | US | suspicious |
2012 | chrome.exe | 52.216.128.149:80 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
2012 | chrome.exe | 192.0.73.2:80 | s.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.testautomationguru.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.vinsguru.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
s3.amazonaws.com |
| shared |
maps.googleapis.com |
| whitelisted |
i0.wp.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s0.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2012 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |