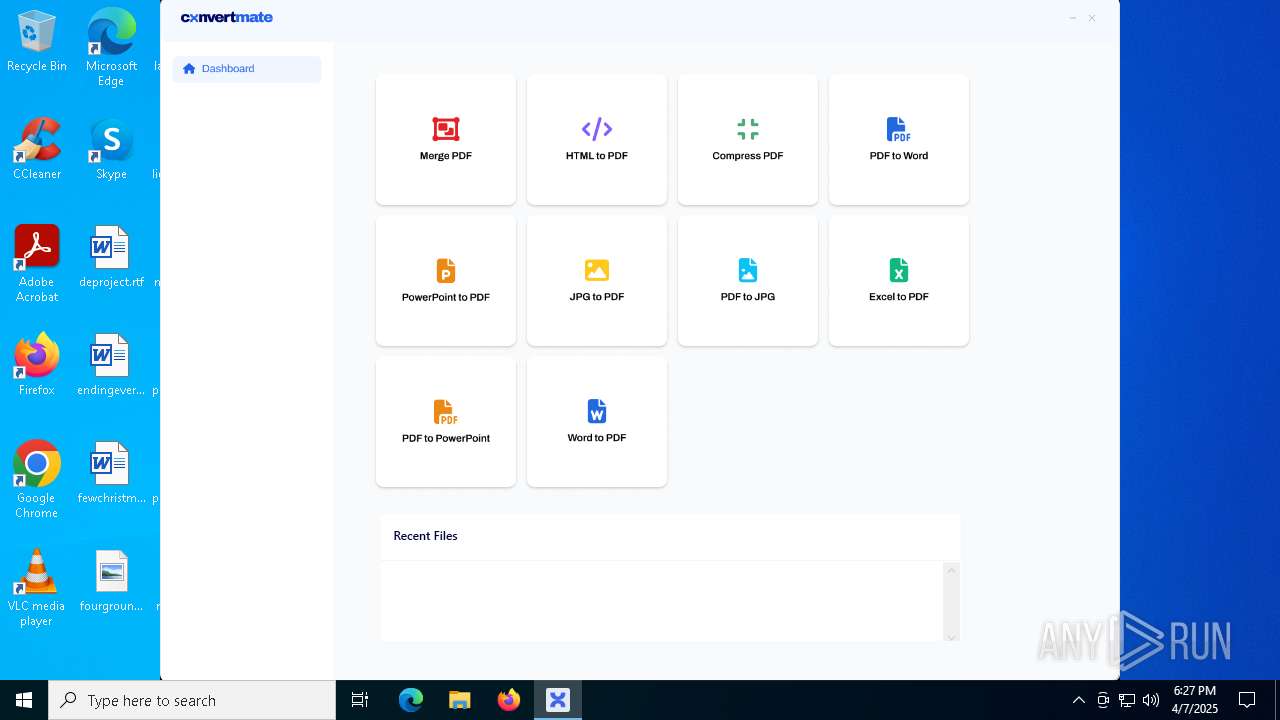
| File name: | ConvertMate.exe |
| Full analysis: | https://app.any.run/tasks/9118ad18-dd64-49cd-ad44-7715016c72e1 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2025, 18:27:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 8E96CEB9844F0EBC28780901AA3AF9FD |
| SHA1: | 0D02ECE3E63702CF54D5865503372F72EF7957FD |
| SHA256: | 5AC2041454D46F138C2AA75A15F43372600143BF952AC656AA96288442A56946 |
| SSDEEP: | 98304:dYBm/AdVa2OH7/qC3DkDr9ac1rI/OS24rr4+uh4Nn9bprVBa091RFS6Nb6F5o8yb:/i5ZrpavLxH |
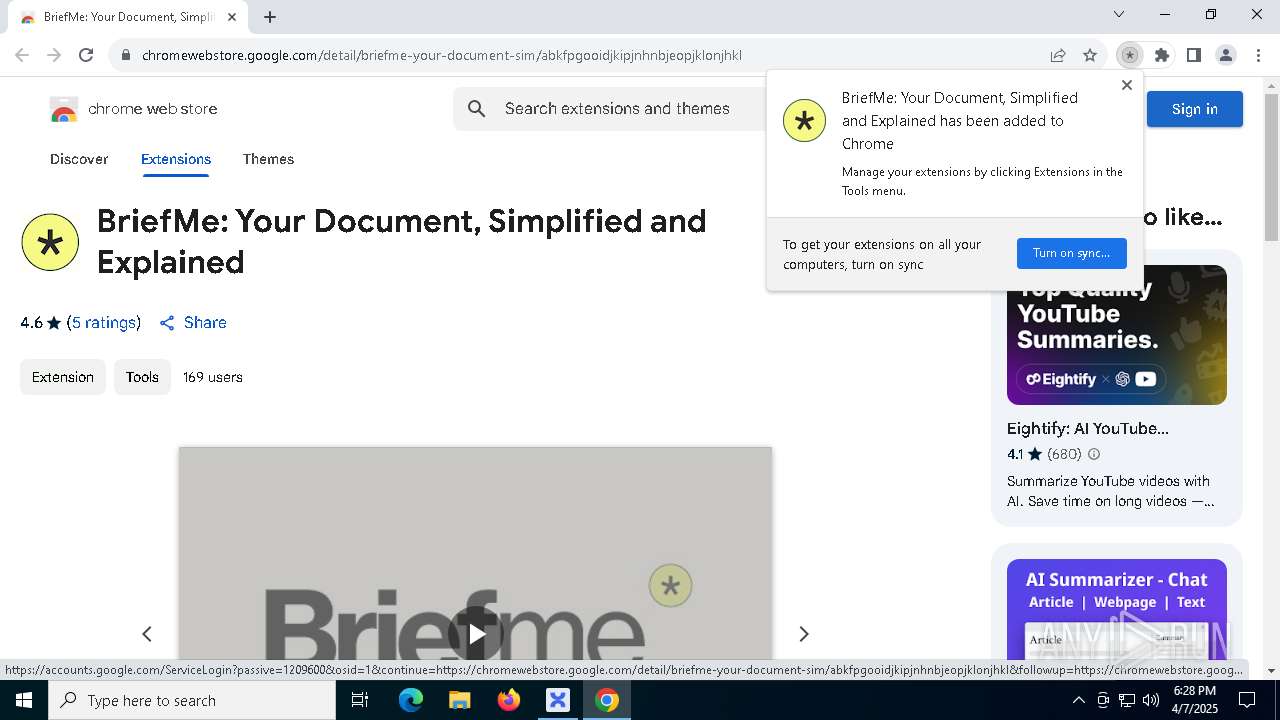
MALICIOUS
Changes powershell execution policy (RemoteSigned)
- ConvertMate.exe (PID: 5352)
SUSPICIOUS
Process drops legitimate windows executable
- ConvertMate.exe (PID: 5352)
Starts POWERSHELL.EXE for commands execution
- ConvertMate.exe (PID: 5352)
The process executes Powershell scripts
- ConvertMate.exe (PID: 5352)
Reads security settings of Internet Explorer
- ConvertMate.exe (PID: 5352)
- Convert Mate.exe (PID: 8144)
Executable content was dropped or overwritten
- ConvertMate.exe (PID: 5352)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7588)
Searches for installed software
- ConvertMate.exe (PID: 5352)
Creates a software uninstall entry
- ConvertMate.exe (PID: 5352)
SQL CE related mutex has been found
- ConvertMate.exe (PID: 5352)
Reads the date of Windows installation
- ConvertMate.exe (PID: 5352)
INFO
Disables trace logs
- ConvertMate.exe (PID: 5352)
Creates files or folders in the user directory
- ConvertMate.exe (PID: 5352)
Checks supported languages
- ConvertMate.exe (PID: 5352)
- Convert Mate.exe (PID: 8144)
Reads the computer name
- ConvertMate.exe (PID: 5352)
- Convert Mate.exe (PID: 8144)
Reads the machine GUID from the registry
- ConvertMate.exe (PID: 5352)
- Convert Mate.exe (PID: 8144)
Reads Environment values
- ConvertMate.exe (PID: 5352)
Reads the software policy settings
- ConvertMate.exe (PID: 5352)
Checks proxy server information
- ConvertMate.exe (PID: 5352)
Process checks computer location settings
- ConvertMate.exe (PID: 5352)
Create files in a temporary directory
- ConvertMate.exe (PID: 5352)
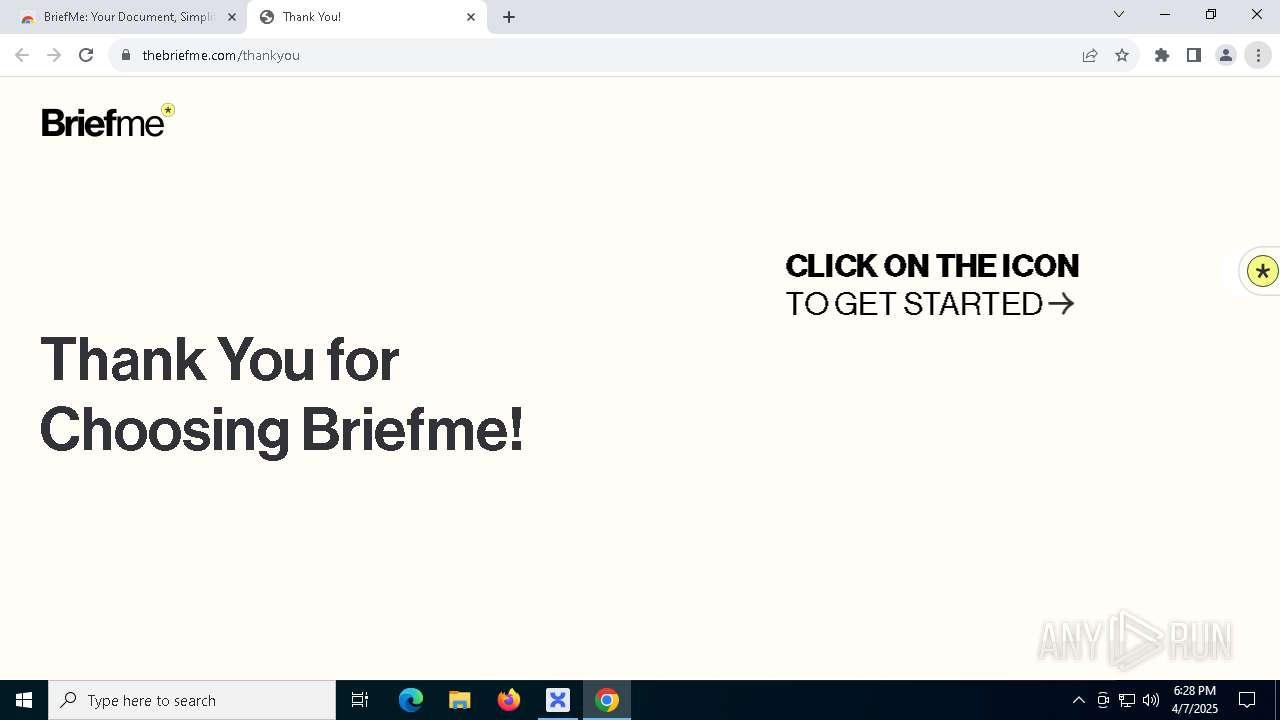
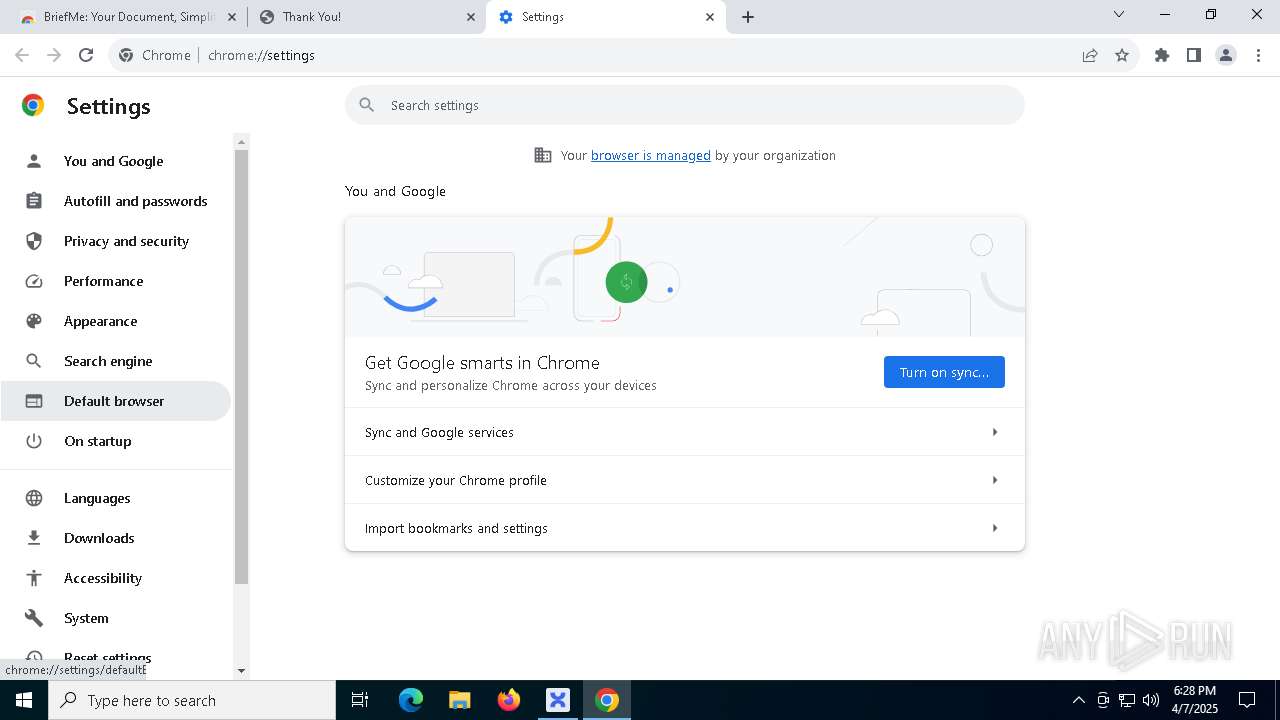
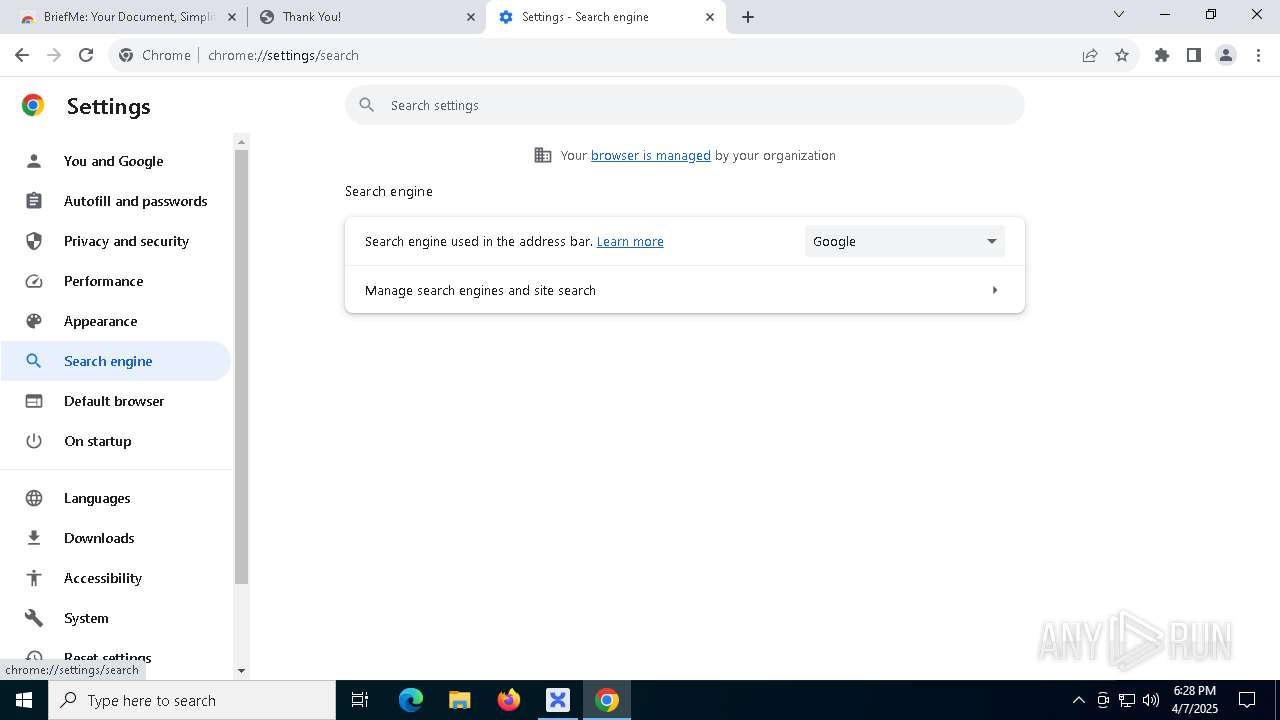
Application launched itself
- chrome.exe (PID: 8136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 1992:12:09 05:20:45+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 7784448 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.1.3.1009 |
| ProductVersionNumber: | 12.1.3.1009 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | ConvertMate |
| FileVersion: | 12.1.3.1009 |
| InternalName: | ConvertMate.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | ConvertMate.exe |
| ProductName: | ConvertMate |
| ProductVersion: | 12.1.3.1009 |
| AssemblyVersion: | 12.1.3.1009 |
Total processes
171
Monitored processes
37
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=6680 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2036 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc7ff7dc40,0x7ffc7ff7dc4c,0x7ffc7ff7dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5788 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6732 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4644 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 | |||||||||||||||
| 4608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5276 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1884 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4824 --field-trial-handle=1888,i,4911887144749146593,4923049527839482666,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 | |||||||||||||||
| 5352 | "C:\Users\admin\AppData\Local\Temp\ConvertMate.exe" | C:\Users\admin\AppData\Local\Temp\ConvertMate.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ConvertMate Exit code: 0 Version: 12.1.3.1009 Modules
| |||||||||||||||
Total events
14 914
Read events
14 799
Write events
95
Delete events
20
Modification events
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5352) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
12
Suspicious files
104
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\FSharp.Core.dll | executable | |
MD5:6D1FB963AFCD008CF6EED945C79C87C8 | SHA256:2EEE5B134A56E6316F3B1E903492DAD41450968D201E2DCCF751CC3C462C02C9 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\Uninstall.zip | compressed | |
MD5:0B99C4182709031E57910EB8330022BB | SHA256:413E0CF5544E9DFC468F420581A73CF13E57CBD3CD756BFBBA8976AA9EC50CF2 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\Uninstaller.exe | executable | |
MD5:6B5E479394633F4AF9957DF1D847C665 | SHA256:965AF63347FFB61F5DD9B78AEE3AE6FC5273A823B189DBFD6159C346BDF12965 | |||
| 7588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g2fdyf2k.24l.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\id.txt | text | |
MD5:DB485F8267C7638C3A716E641D3CDC6F | SHA256:FAD86C8E9AEE05B548B44E3F3AFC283BBE13EE7C0B25554A265A55678D827F61 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\UpdateRetreiver.exe | executable | |
MD5:FE0F5C9C6AADFFEFDCD94CB517A95368 | SHA256:440D4C2E8BB94BF7D16CF59DB73B0AB75D3971536A3FCB2E59E7B4D6E4C094F7 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\System.ValueTuple.dll | executable | |
MD5:7DC7D6205792B66168315A566AE33E16 | SHA256:E1CD89B94E888BDFC6CF8CC8608735C40D4BC0D3580D3F921002304B696C61C3 | |||
| 5352 | ConvertMate.exe | C:\Users\admin\Desktop\Convert Mate.lnk | binary | |
MD5:DAFE6A688DA86D57761878AE967ACD2F | SHA256:A2867E2C22851F91C1D092CD80A8E868EDC41B396924025B305CC9A15FCDFC1A | |||
| 5352 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\Native.zip | compressed | |
MD5:88D70953482E2BFC5910FEFC50905C47 | SHA256:DEB419D16561154DB9D499CA09C6299E365A5DBB41BC283A415B8F21AD208AAC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
73
DNS requests
90
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5352 | ConvertMate.exe | 104.18.24.125:443 | climatcon.com | CLOUDFLARENET | — | unknown |
6404 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
climatcon.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
chrialletworton.com |
| unknown |
accounts.google.com |
| whitelisted |