| File name: | 5a25-gsmt-6810-4c9b-47c0.exe |
| Full analysis: | https://app.any.run/tasks/99875103-1a39-4dff-9a99-a7dc48db17b8 |
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2024, 19:30:14 |
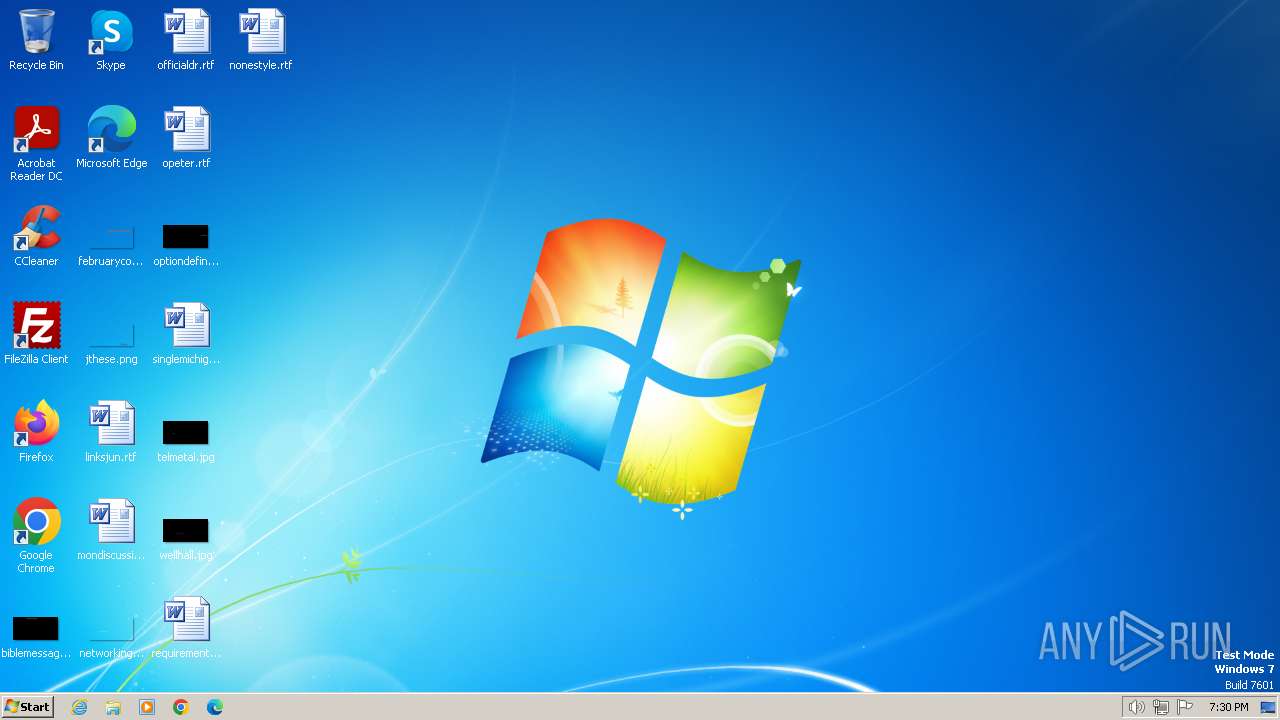
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6E79314C16E9E07FF6833CD4B01D6ED6 |
| SHA1: | 7C6FFC371FAFED48B6394986EBA4E690918CC915 |
| SHA256: | 5AB9A6908B22F7D34289A778CE210A46144034D5334088BBE7F9B176A479AE22 |
| SSDEEP: | 98304:8Yh27WkU8nigM6qhCOh1fbMlsTPLXDyxeuajMSKixVtIKFochT+yK3rFOGPyGJB8:o2 |
MALICIOUS
Drops the executable file immediately after the start
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 4060)
Antivirus name has been found in the command line (generic signature)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 2328)
- WRSA.exe (PID: 4060)
Creates a writable file in the system directory
- WRSA.exe (PID: 4060)
SUSPICIOUS
Reads the Internet Settings
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- WRSA.exe (PID: 2328)
The process verifies whether the antivirus software is installed
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 2328)
- WRSA.exe (PID: 4060)
Application launched itself
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
Executable content was dropped or overwritten
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 4060)
Starts itself from another location
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
Executes as Windows Service
- WRSA.exe (PID: 4060)
Creates or modifies Windows services
- WRSA.exe (PID: 4060)
- WRSA.exe (PID: 2328)
Checks Windows Trust Settings
- WRSA.exe (PID: 4060)
Drops a system driver (possible attempt to evade defenses)
- WRSA.exe (PID: 4060)
Creates/Modifies COM task schedule object
- WRSA.exe (PID: 4060)
Creates files in the driver directory
- WRSA.exe (PID: 4060)
Adds/modifies Windows certificates
- WRSA.exe (PID: 4060)
Creates a software uninstall entry
- WRSA.exe (PID: 4060)
INFO
Checks supported languages
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 2328)
- WRSA.exe (PID: 4060)
Reads the computer name
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 2328)
- WRSA.exe (PID: 4060)
Checks proxy server information
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- WRSA.exe (PID: 2328)
Reads the machine GUID from the registry
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 4052)
- WRSA.exe (PID: 4060)
- WRSA.exe (PID: 2328)
Creates files in the program directory
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 3464)
- WRSA.exe (PID: 4060)
Reads the software policy settings
- WRSA.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:16 21:28:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2413568 |
| InitializedDataSize: | 3383296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21db80 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.35.12 |
| ProductVersionNumber: | 9.0.35.12 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
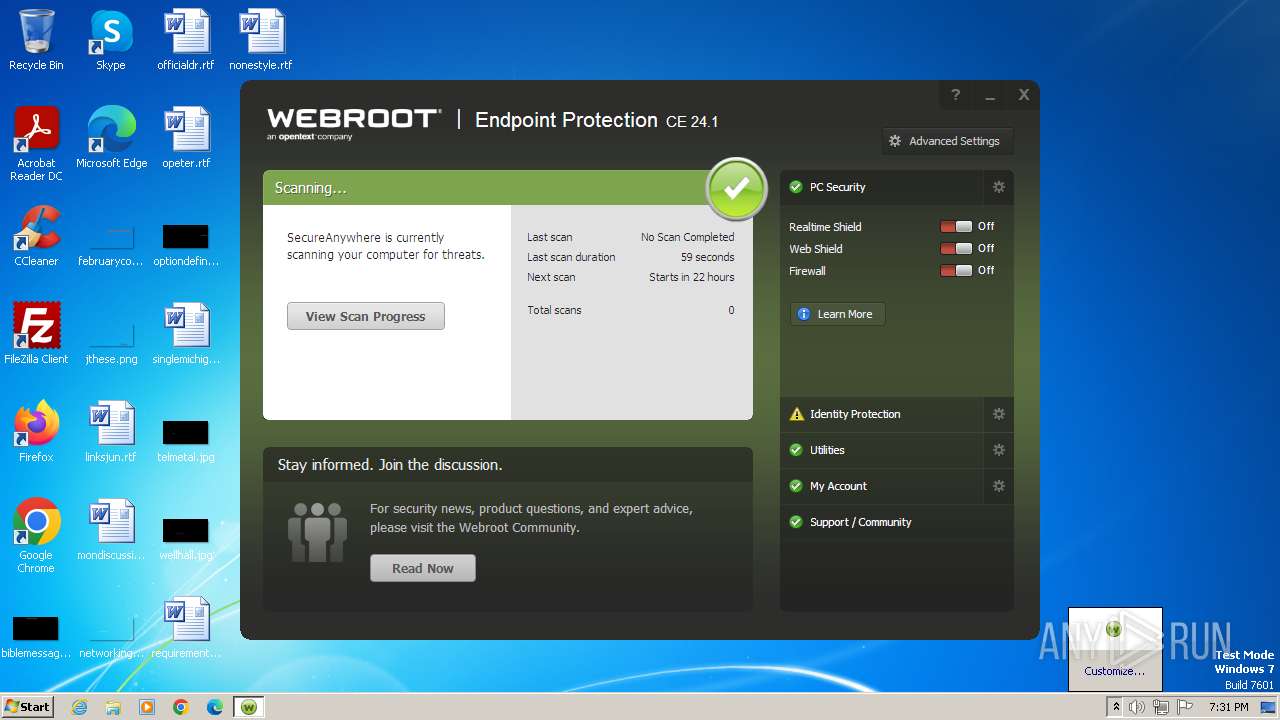
| CompanyName: | Webroot |
| FileDescription: | Webroot SecureAnywhere |
| FileVersion: | 9.0.35.12 |
| InternalName: | WRSA.exe |
| LegalCopyright: | (c) Webroot 2006-2023 |
| OriginalFileName: | WRSA.exe |
| ProductName: | Webroot SecureAnywhere |
| ProductVersion: | 9.0.35.12 |
Total processes
41
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2328 | "C:\Program Files\Webroot\WRSA.exe" -pi /key=5A25GSMT68104C9B47C0 /installing | C:\Program Files\Webroot\WRSA.exe | — | 5a25-gsmt-6810-4c9b-47c0.exe | |||||||||||
User: admin Company: Webroot Integrity Level: HIGH Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe" -insuac="C:\Program Files\Webroot\WRSA.exe" /key=5A25GSMT68104C9B47C0 /installing | C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe | 5a25-gsmt-6810-4c9b-47c0.exe | ||||||||||||
User: admin Company: Webroot Integrity Level: HIGH Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe" | C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe | — | explorer.exe | |||||||||||
User: admin Company: Webroot Integrity Level: MEDIUM Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 4060 | "C:\Program Files\Webroot\WRSA.exe" -service | C:\Program Files\Webroot\WRSA.exe | services.exe | ||||||||||||
User: SYSTEM Company: Webroot Integrity Level: SYSTEM Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
Total events
23 621
Read events
22 188
Write events
1 421
Delete events
12
Modification events
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | LIC |
Value: 5A25GSMT68104C9B47C0 | |||
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | 3 |
Value: 0 | |||
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | USP |
Value: 0 | |||
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | RSP |
Value: | |||
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | RSF |
Value: 0 | |||
| (PID) Process: | (4052) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | InstallOpt |
Value: 2102882 | |||
| (PID) Process: | (3464) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\webroot |
| Operation: | write | Name: | initialOSBuildNumber |
Value: 7601 | |||
| (PID) Process: | (3464) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WRData |
| Operation: | write | Name: | BMV |
Value: 3746433742464237433538433144324641373035413735353035444542463333424343464144433400 | |||
| (PID) Process: | (3464) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WRData |
| Operation: | write | Name: | NIV |
Value: 1 | |||
| (PID) Process: | (3464) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | LIC |
Value: 5A25GSMT68104C9B47C0 | |||
Executable files
5
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | 5a25-gsmt-6810-4c9b-47c0.exe | C:\Program Files\Webroot\WRSA.exe | executable | |
MD5:6E79314C16E9E07FF6833CD4B01D6ED6 | SHA256:5AB9A6908B22F7D34289A778CE210A46144034D5334088BBE7F9B176A479AE22 | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\dbr.db | binary | |
MD5:EB3E7F1928E9CEA173972CBEC36AE725 | SHA256:0E2B957388A1E33640DAFB668F487FEACE71DE30667EC8FD3E59D90496DB795A | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\Lso.db | binary | |
MD5:BFF8CF22A678AD2E0C7EA68A382251D8 | SHA256:557688F494B23D61EC9D8381B263C3EF82127813A3CCCE4BF5DB9C736A53E659 | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\Ccs.db | binary | |
MD5:FA7A90E3C1ADA758D89762EC53D0082C | SHA256:DD0F90595D91E46AB3D9C06489935BC46269E8808EFEBF84C003C6BB64B36932 | |||
| 4060 | WRSA.exe | C:\Windows\system32\drivers\WRkrn.sys | executable | |
MD5:A03E04137422DE01ADC15CDFDB76296E | SHA256:6C7DC6F0B182C4042CB70D55034DDDB03E1F3914721E630146BAFC8AF8890148 | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\Ovr.db | binary | |
MD5:C3DD4A132B23C6710C2CA7089CB8E63F | SHA256:8FD4C44080921D7BD91EDDF2D8D040B20D4937F444B7CE11E9F25D54CC6DB163 | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\qsx.db | binary | |
MD5:908C39A4D1B3094F7BD6B1BE50E2750D | SHA256:A86860EDAD6048638784F7D244935524DCE83A9ABA7CEEB946C83DAE3211C39A | |||
| 4060 | WRSA.exe | C:\Windows\system32\WRusr.dll | executable | |
MD5:2F2CC11A0DE4544F13A1475E46C30A2C | SHA256:18F345482F3B7C05DA846E6B582F9CA98491B831933A6471637EE865527047D9 | |||
| 4060 | WRSA.exe | C:\ProgramData\WRData\Ovr.db.bak | binary | |
MD5:C3DD4A132B23C6710C2CA7089CB8E63F | SHA256:8FD4C44080921D7BD91EDDF2D8D040B20D4937F444B7CE11E9F25D54CC6DB163 | |||
| 4060 | WRSA.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Webroot SecureAnywhere\Webroot SecureAnywhere.lnk | lnk | |
MD5:1035A20E17B641081A98289660D2CFD4 | SHA256:38C9D6CC36676A23514A3A1DDD1B23106513FF1961EA6CC37821DFE5685BB4A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4060 | WRSA.exe | 52.215.71.2:443 | g88.p4.webrootcloudav.com | AMAZON-02 | IE | unknown |
4060 | WRSA.exe | 54.229.234.104:443 | sn.webrootcloudav.com | AMAZON-02 | IE | unknown |
4060 | WRSA.exe | 52.218.182.161:443 | wrskynet-oregon.s3-us-west-2.amazonaws.com | AMAZON-02 | US | unknown |
4060 | WRSA.exe | 66.35.53.201:443 | api.webroot.com | WEBROOT-CORP-AS1 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
g88.p4.webrootcloudav.com |
| unknown |
sn.webrootcloudav.com |
| unknown |
wrskynet-oregon.s3-us-west-2.amazonaws.com |
| shared |
api.webroot.com |
| unknown |