| File name: | 5a25-gsmt-6810-4c9b-47c0.exe |
| Full analysis: | https://app.any.run/tasks/547b623d-4e27-42a7-ba71-1b4c3f7ec4f8 |
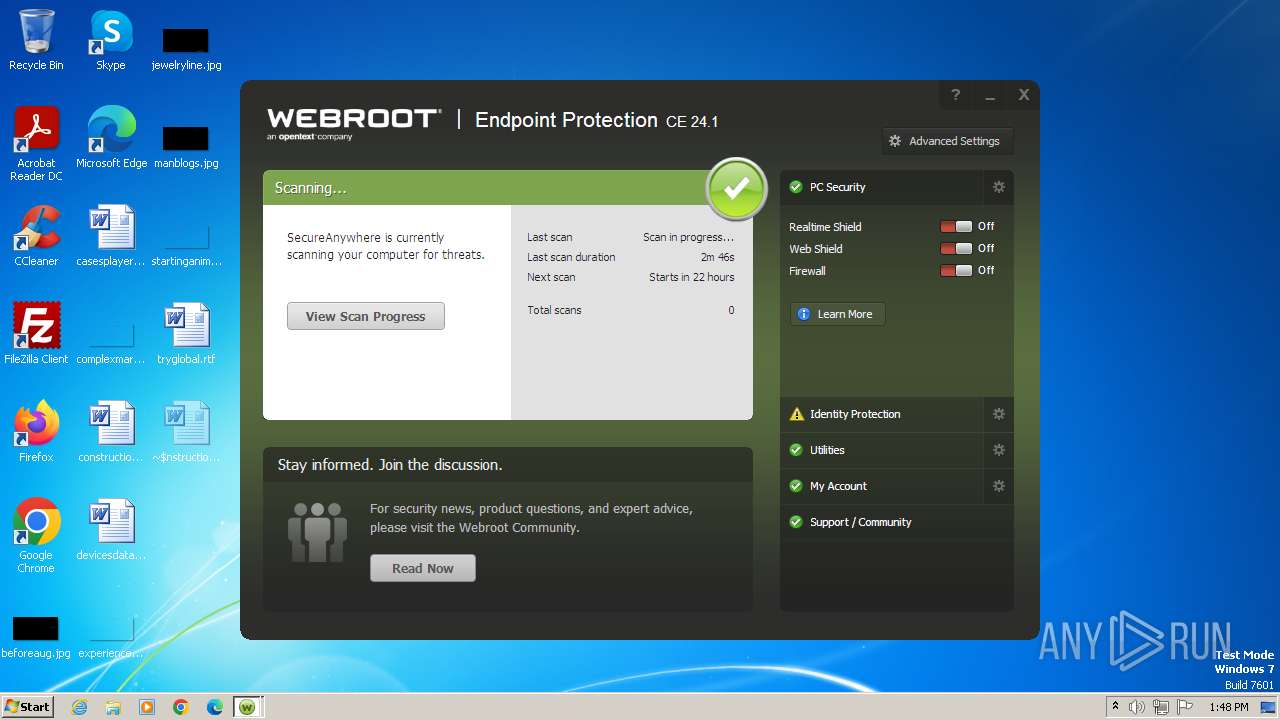
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2024, 13:45:59 |
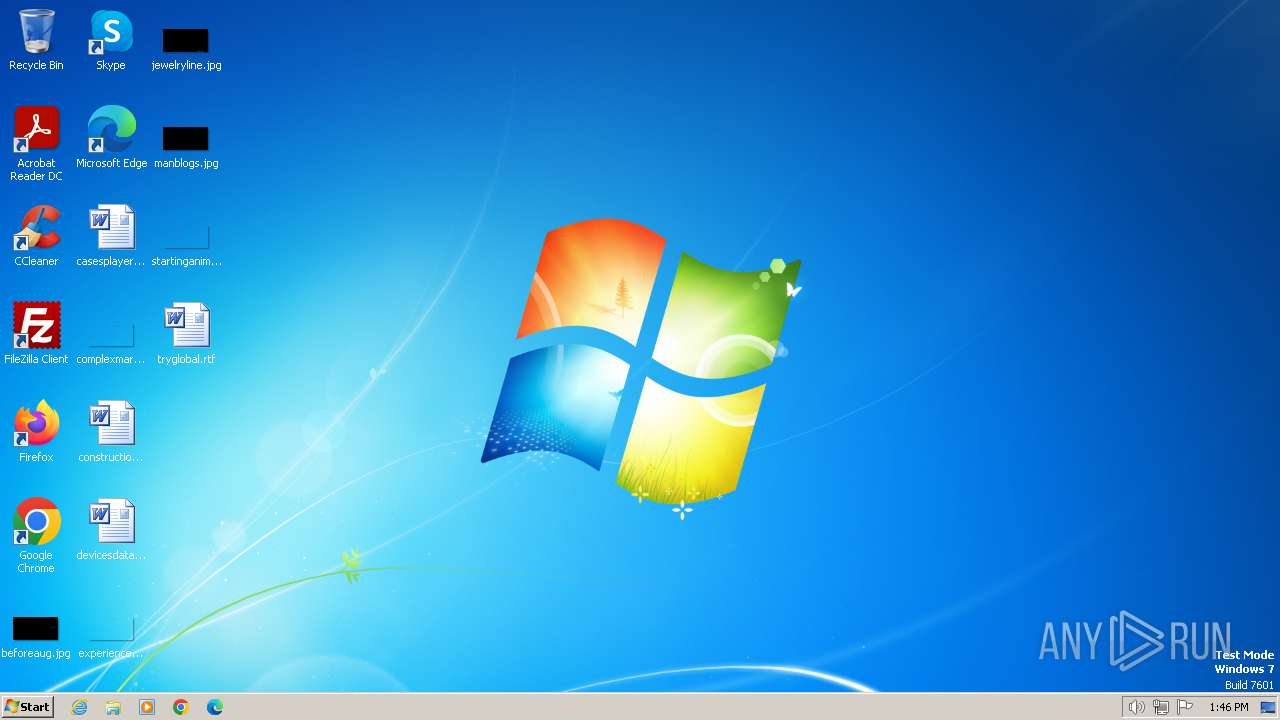
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6E79314C16E9E07FF6833CD4B01D6ED6 |
| SHA1: | 7C6FFC371FAFED48B6394986EBA4E690918CC915 |
| SHA256: | 5AB9A6908B22F7D34289A778CE210A46144034D5334088BBE7F9B176A479AE22 |
| SSDEEP: | 98304:8Yh27WkU8nigM6qhCOh1fbMlsTPLXDyxeuajMSKixVtIKFochT+yK3rFOGPyGJB8:o2 |
MALICIOUS
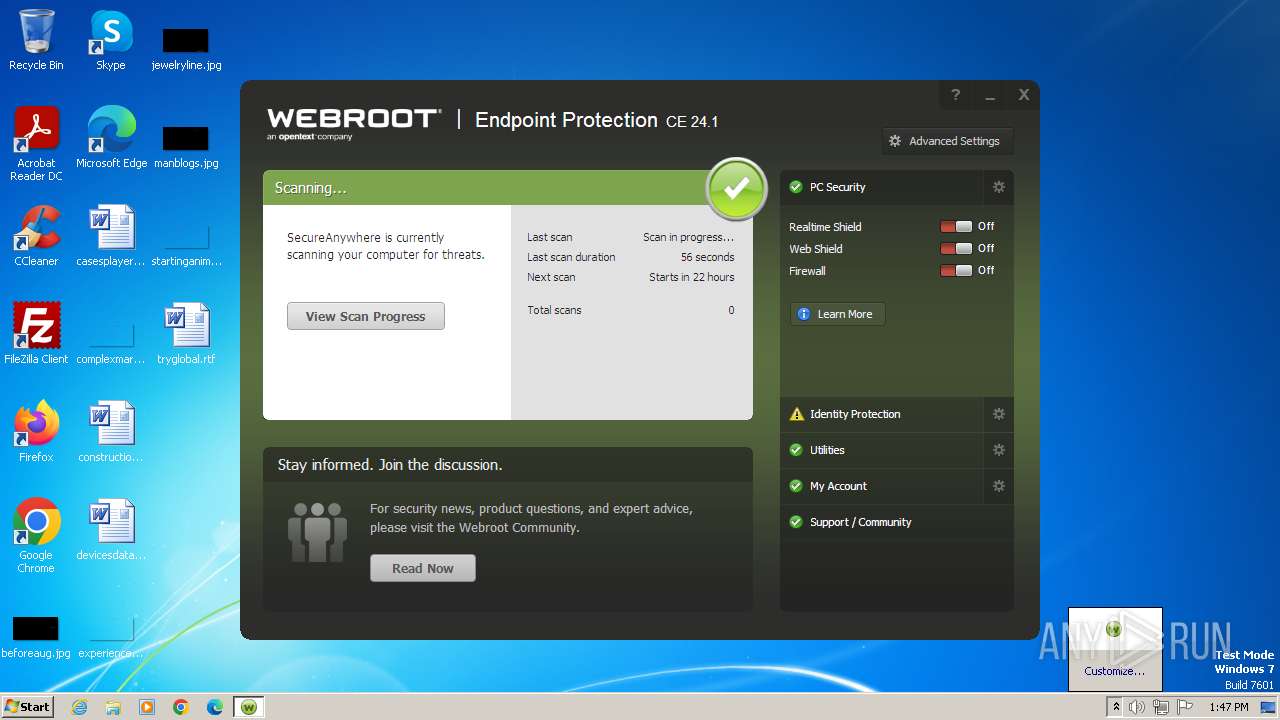
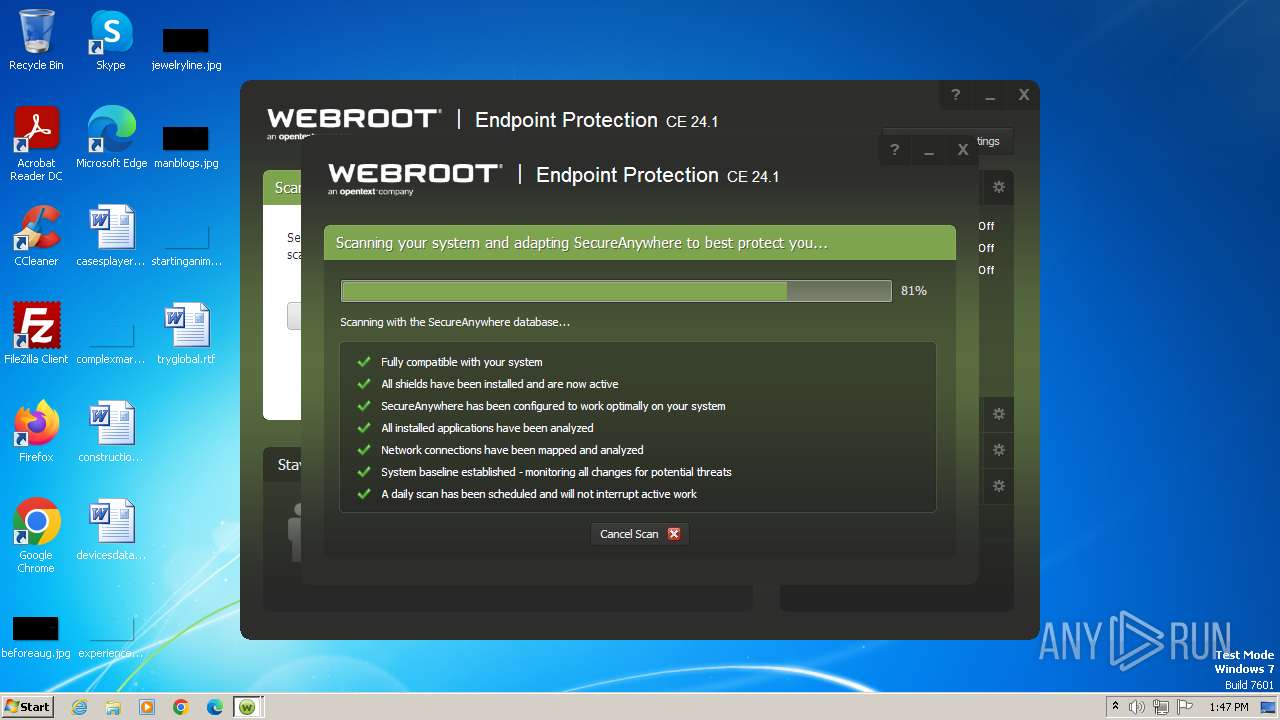
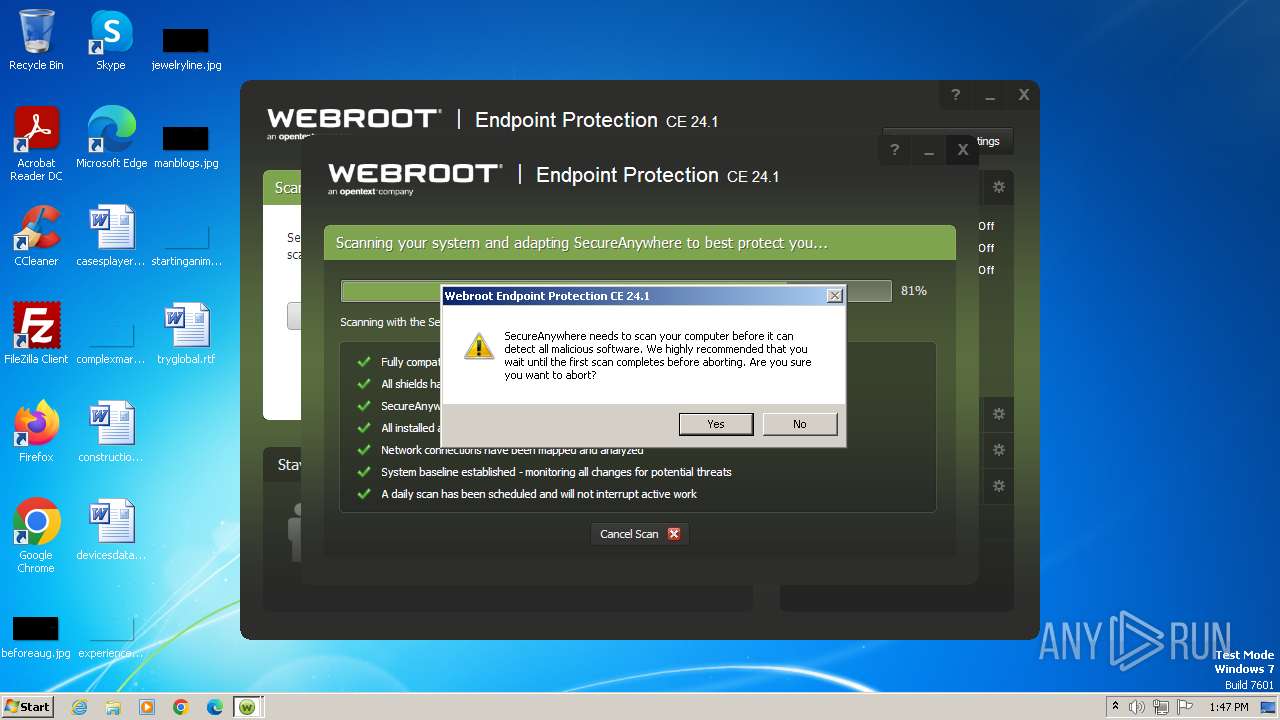
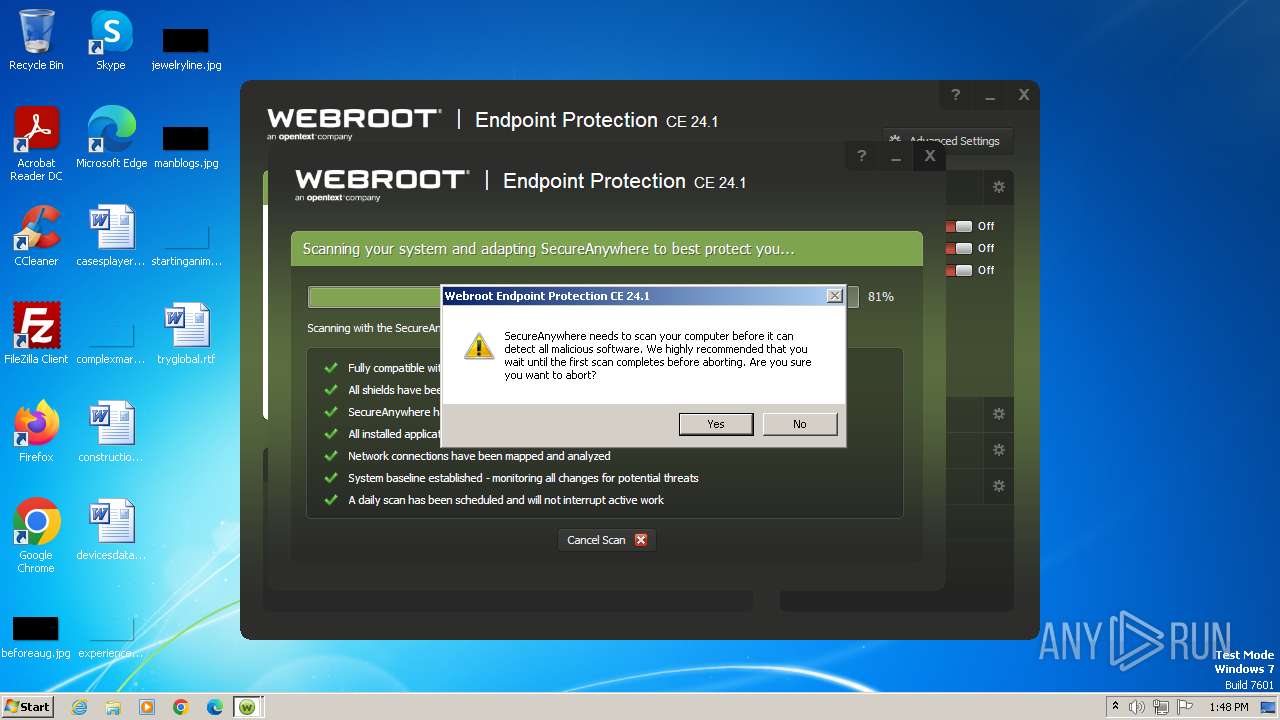
Drops the executable file immediately after the start
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- WRSA.exe (PID: 3428)
Antivirus name has been found in the command line (generic signature)
- WRSA.exe (PID: 1040)
- WRSA.exe (PID: 3428)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
Creates a writable file in the system directory
- WRSA.exe (PID: 3428)
Steals credentials from Web Browsers
- WRSA.exe (PID: 3428)
Actions looks like stealing of personal data
- WRSA.exe (PID: 3428)
SUSPICIOUS
The process verifies whether the antivirus software is installed
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- WRSA.exe (PID: 1040)
- WRSA.exe (PID: 3428)
Reads the Internet Settings
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- WRSA.exe (PID: 1040)
Executable content was dropped or overwritten
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- WRSA.exe (PID: 3428)
Starts itself from another location
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
Creates or modifies Windows services
- WRSA.exe (PID: 3428)
- WRSA.exe (PID: 1040)
Executes as Windows Service
- WRSA.exe (PID: 3428)
Creates files in the driver directory
- WRSA.exe (PID: 3428)
Creates/Modifies COM task schedule object
- WRSA.exe (PID: 3428)
Drops a system driver (possible attempt to evade defenses)
- WRSA.exe (PID: 3428)
Creates a software uninstall entry
- WRSA.exe (PID: 3428)
Adds/modifies Windows certificates
- WRSA.exe (PID: 3428)
Checks Windows Trust Settings
- WRSA.exe (PID: 3428)
Detected use of alternative data streams (AltDS)
- WRSA.exe (PID: 3428)
Read startup parameters
- WRSA.exe (PID: 3428)
Starts application from unusual location
- WRSA.exe (PID: 3428)
Searches for installed software
- WRSA.exe (PID: 3428)
Reads Microsoft Outlook installation path
- WRSA.exe (PID: 3428)
The process checks if it is being run in the virtual environment
- WRSA.exe (PID: 3428)
Application launched itself
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
INFO
Checks supported languages
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- WRSA.exe (PID: 1040)
- WRSA.exe (PID: 3428)
- wmpnscfg.exe (PID: 448)
Reads the computer name
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- wmpnscfg.exe (PID: 448)
- WRSA.exe (PID: 3428)
- WRSA.exe (PID: 1040)
Reads the machine GUID from the registry
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- WRSA.exe (PID: 3428)
- WRSA.exe (PID: 1040)
Checks proxy server information
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 2160)
- WRSA.exe (PID: 1040)
Creates files in the program directory
- 5a25-gsmt-6810-4c9b-47c0.exe (PID: 1876)
- WRSA.exe (PID: 3428)
Reads the software policy settings
- WRSA.exe (PID: 3428)
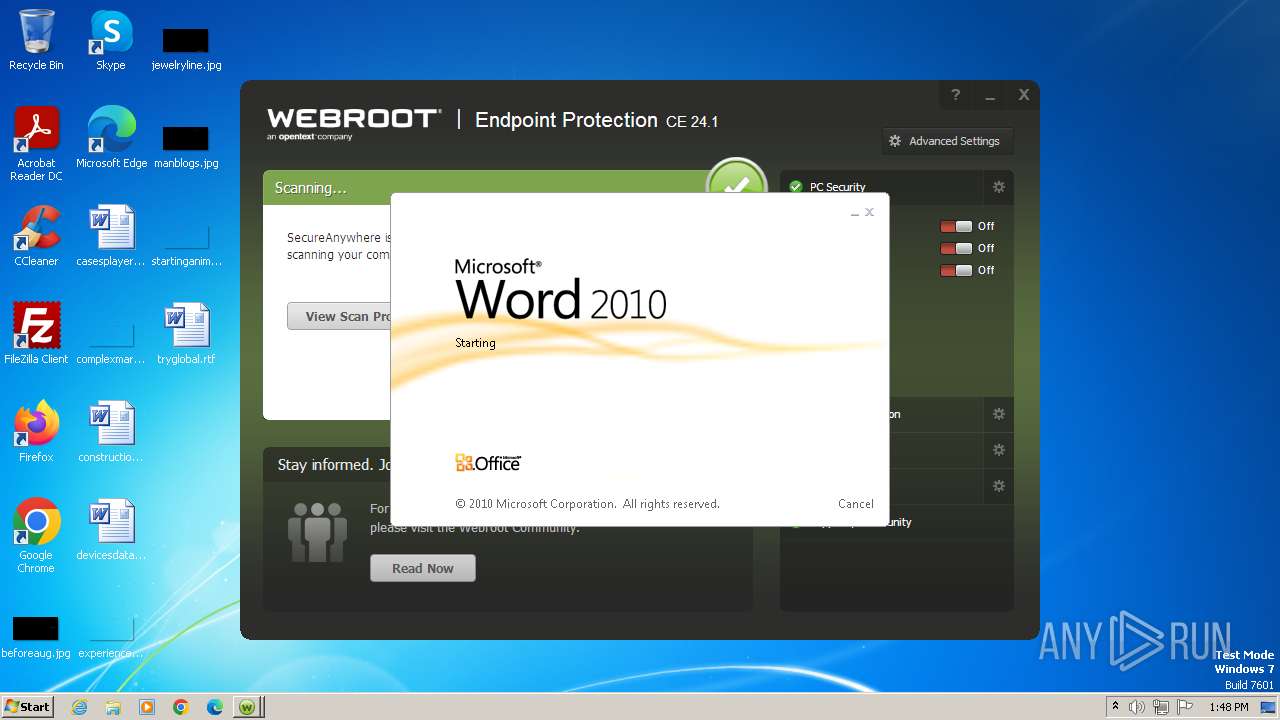
Manual execution by a user
- wmpnscfg.exe (PID: 448)
- WINWORD.EXE (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:16 21:28:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2413568 |
| InitializedDataSize: | 3383296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21db80 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.35.12 |
| ProductVersionNumber: | 9.0.35.12 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
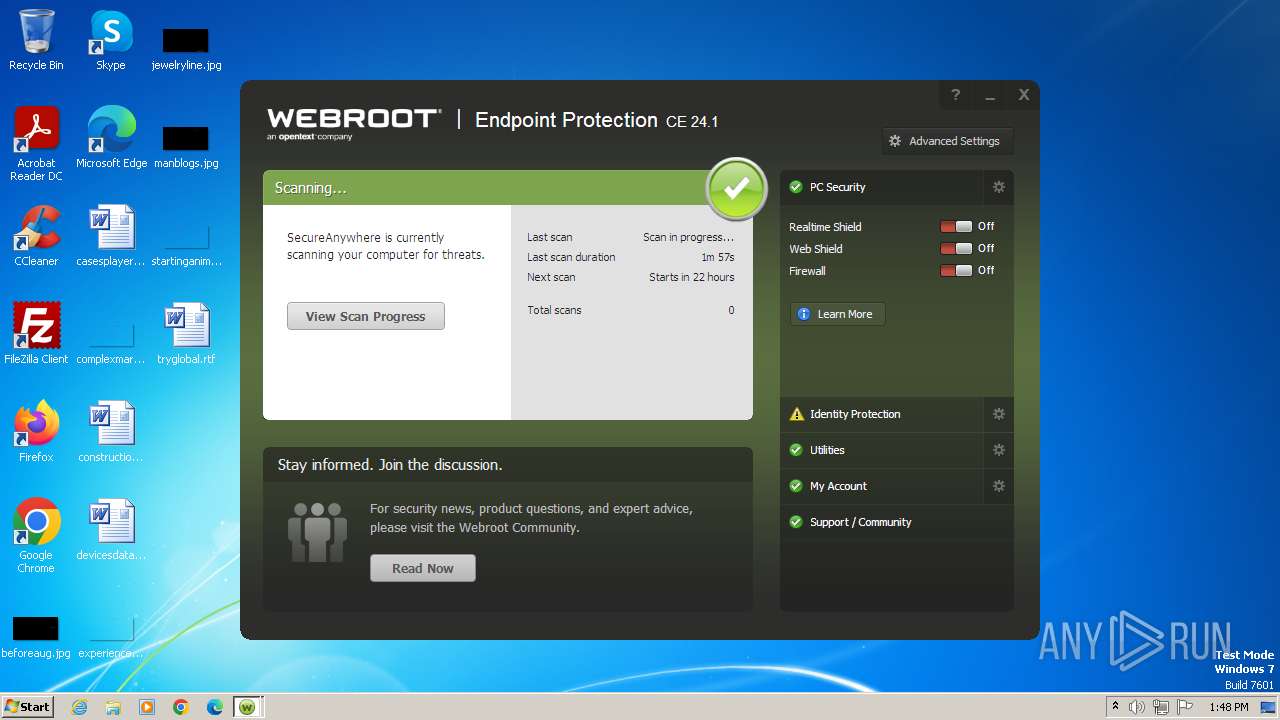
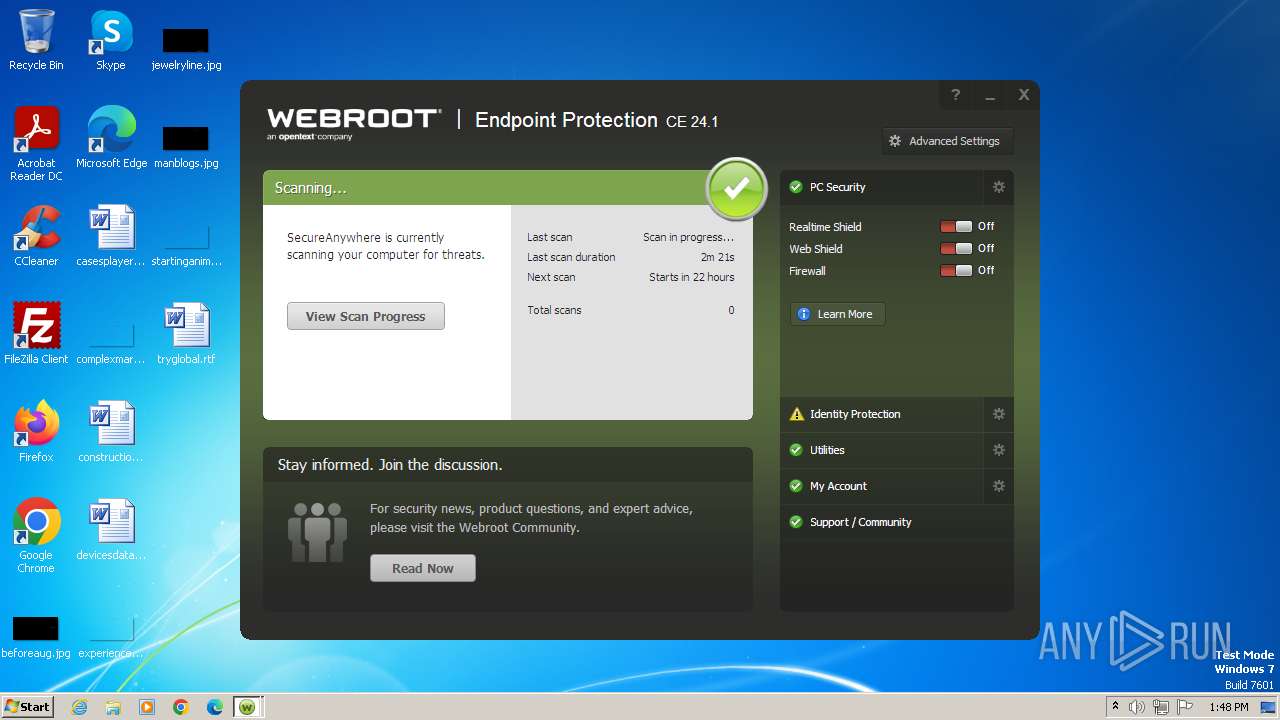
| CompanyName: | Webroot |
| FileDescription: | Webroot SecureAnywhere |
| FileVersion: | 9.0.35.12 |
| InternalName: | WRSA.exe |
| LegalCopyright: | (c) Webroot 2006-2023 |
| OriginalFileName: | WRSA.exe |
| ProductName: | Webroot SecureAnywhere |
| ProductVersion: | 9.0.35.12 |
Total processes
48
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Webroot\WRSA.exe" -pi /key=5A25GSMT68104C9B47C0 /installing | C:\Program Files\Webroot\WRSA.exe | — | 5a25-gsmt-6810-4c9b-47c0.exe | |||||||||||
User: admin Company: Webroot Integrity Level: HIGH Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe" -insuac="C:\Program Files\Webroot\WRSA.exe" /key=5A25GSMT68104C9B47C0 /installing | C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe | 5a25-gsmt-6810-4c9b-47c0.exe | ||||||||||||
User: admin Company: Webroot Integrity Level: HIGH Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe" | C:\Users\admin\AppData\Local\Temp\5a25-gsmt-6810-4c9b-47c0.exe | — | explorer.exe | |||||||||||
User: admin Company: Webroot Integrity Level: MEDIUM Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Webroot\WRSA.exe" -service | C:\Program Files\Webroot\WRSA.exe | services.exe | ||||||||||||
User: SYSTEM Company: Webroot Integrity Level: SYSTEM Description: Webroot SecureAnywhere Exit code: 0 Version: 9.0.35.12 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\constructiongrade.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
91 741
Read events
89 749
Write events
1 665
Delete events
327
Modification events
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | LIC |
Value: 5A25GSMT68104C9B47C0 | |||
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | 3 |
Value: 0 | |||
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | USP |
Value: 0 | |||
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | RSP |
Value: | |||
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | RSF |
Value: 0 | |||
| (PID) Process: | (2160) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | InstallOpt |
Value: 2102882 | |||
| (PID) Process: | (1876) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\webroot |
| Operation: | write | Name: | initialOSBuildNumber |
Value: 7601 | |||
| (PID) Process: | (1876) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WRData |
| Operation: | write | Name: | BMV |
Value: 3746433742464237433538433144324641373035413735353035444542463333424343464144433400 | |||
| (PID) Process: | (1876) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WRData |
| Operation: | write | Name: | NIV |
Value: 1 | |||
| (PID) Process: | (1876) 5a25-gsmt-6810-4c9b-47c0.exe | Key: | HKEY_CURRENT_USER\Software\WRData |
| Operation: | write | Name: | LIC |
Value: 5A25GSMT68104C9B47C0 | |||
Executable files
6
Suspicious files
12
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR78CB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3428 | WRSA.exe | C:\ProgramData\WRData\dbr.db | binary | |
MD5:E3F9D1DB28E0722BA4A5FEB08E8CB6C0 | SHA256:B0D224A378DCC1DFC228DAAB6BE94B75AA1A8E4C62C739F636FC14A073F86A8F | |||
| 3428 | WRSA.exe | C:\Windows\system32\drivers\WRkrn.sys | executable | |
MD5:A03E04137422DE01ADC15CDFDB76296E | SHA256:6C7DC6F0B182C4042CB70D55034DDDB03E1F3914721E630146BAFC8AF8890148 | |||
| 3428 | WRSA.exe | C:\Windows\system32\WRusr.dll | executable | |
MD5:2F2CC11A0DE4544F13A1475E46C30A2C | SHA256:18F345482F3B7C05DA846E6B582F9CA98491B831933A6471637EE865527047D9 | |||
| 3428 | WRSA.exe | C:\Program Files\Webroot\WRSkyClientConnect.x86.dll | executable | |
MD5:351AC52A56D340585E198A2FBA2125D2 | SHA256:FBAC1D40E9A0CFDBD5B4737F56300E9B927BA24CD6BCF144CE298A2900201218 | |||
| 3428 | WRSA.exe | C:\ProgramData\WRData\Ccs.db.bak | binary | |
MD5:FA7A90E3C1ADA758D89762EC53D0082C | SHA256:DD0F90595D91E46AB3D9C06489935BC46269E8808EFEBF84C003C6BB64B36932 | |||
| 3564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{637FB1CC-7799-43DF-B92D-490C508DDCA3}.tmp | smt | |
MD5:5D4D94EE7E06BBB0AF9584119797B23A | SHA256:4826C0D860AF884D3343CA6460B0006A7A2CE7DBCCC4D743208585D997CC5FD1 | |||
| 3428 | WRSA.exe | C:\ProgramData\WRData\e1573000e.dat | executable | |
MD5:DACAFEA3B80C5C08A6ADF69FB3AB7898 | SHA256:D902192FB6CA0B1AEEB6F12BEA0D190A226142EBB71EA80AD3B7CA5FF14395E9 | |||
| 3428 | WRSA.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Webroot SecureAnywhere\Webroot SecureAnywhere.lnk | lnk | |
MD5:DA159CEE16B2F34F024C1A4E9F2CB16C | SHA256:48A086A93A928279CDEA1CB8F01BAA31E5CA9A609132E200966F7C55D13443F9 | |||
| 3564 | WINWORD.EXE | C:\Users\admin\Desktop\~$nstructiongrade.rtf | pgc | |
MD5:EE06EE127C28FE8BEBA41EA88A2851E6 | SHA256:DD56D5DEC997B0D6E192ED0DC6EC2065E61A5FE73781DFE23131B16DDEEC86B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
18
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3428 | WRSA.exe | 34.253.252.74:443 | g88.p4.webrootcloudav.com | AMAZON-02 | IE | unknown |
3428 | WRSA.exe | 34.252.181.17:443 | sn.webrootcloudav.com | AMAZON-02 | IE | unknown |
3428 | WRSA.exe | 3.5.85.208:443 | wrskynet-oregon.s3-us-west-2.amazonaws.com | AMAZON-02 | US | unknown |
3428 | WRSA.exe | 52.92.251.194:443 | wrskynet-oregon.s3-us-west-2.amazonaws.com | AMAZON-02 | US | unknown |
3428 | WRSA.exe | 52.218.168.73:443 | wrskynet-oregon.s3-us-west-2.amazonaws.com | AMAZON-02 | US | unknown |
3428 | WRSA.exe | 66.35.53.201:443 | api.webroot.com | WEBROOT-CORP-AS1 | US | unknown |
3428 | WRSA.exe | 54.194.226.23:443 | sn.webrootcloudav.com | AMAZON-02 | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
g88.p4.webrootcloudav.com |
| unknown |
sn.webrootcloudav.com |
| unknown |
wrskynet-oregon.s3-us-west-2.amazonaws.com |
| shared |
api.webroot.com |
| unknown |
sn-euw1.webrootcloudav.com |
| unknown |
skyversion.webrootcloudav.com |
| unknown |
anywhere.webrootcloudav.com |
| whitelisted |
sn-usw2.webrootcloudav.com |
| unknown |