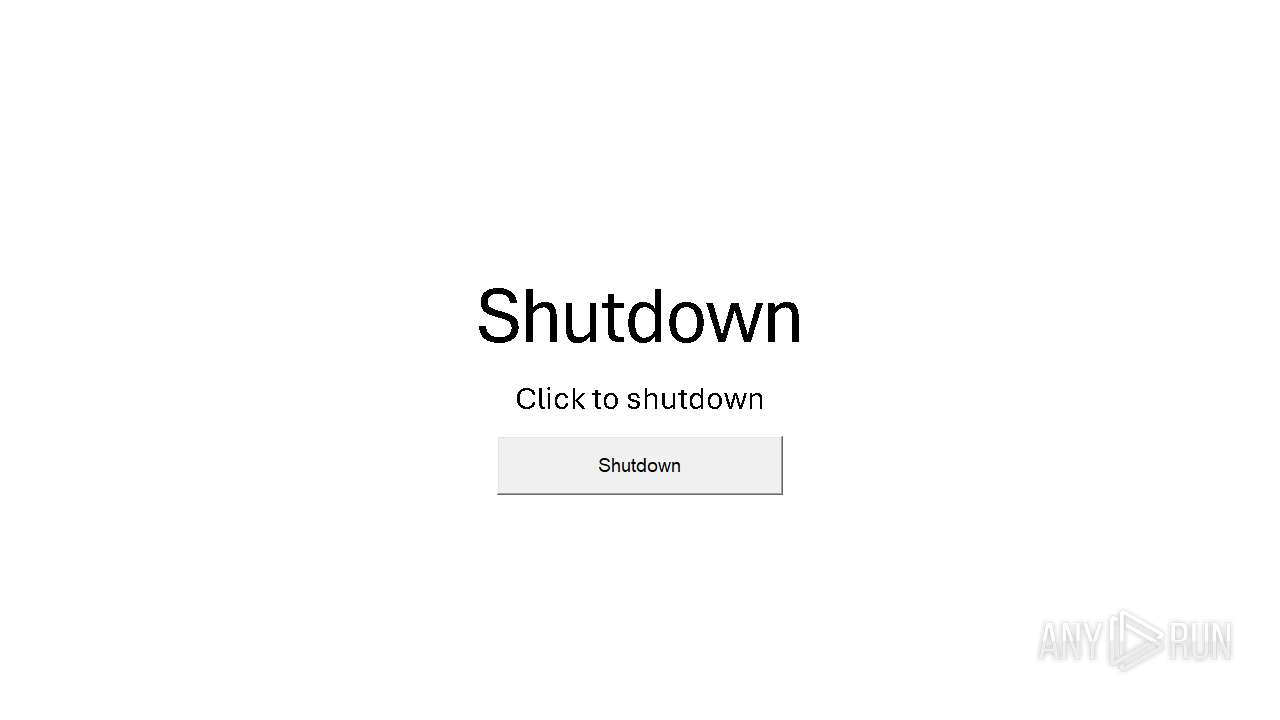
| File name: | Shutdown.pptm |
| Full analysis: | https://app.any.run/tasks/e1b2a297-2bb3-426c-8872-6cb698bb5e6a |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 06:36:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.presentationml.presentation |
| File info: | Microsoft PowerPoint 2007+ |
| MD5: | 3F2C7E86BC4CDE1CEA620515FE17B16E |
| SHA1: | 11E2F2C4B74B26D13D5E4960A8CB5B41AC9EB2BF |
| SHA256: | 5AA7FC6575D15A33E99096945994F7EA82E261E4825125FA48EA8425791E6F66 |
| SSDEEP: | 768:lA0zBOvL7EGSVVW2PmlH+dZhygKD0NlFm4Dm0WhY61DjpT1pGkvp9imsBXBhBYBJ:krSVcHeNjNvDue61xGkXl0UWC |
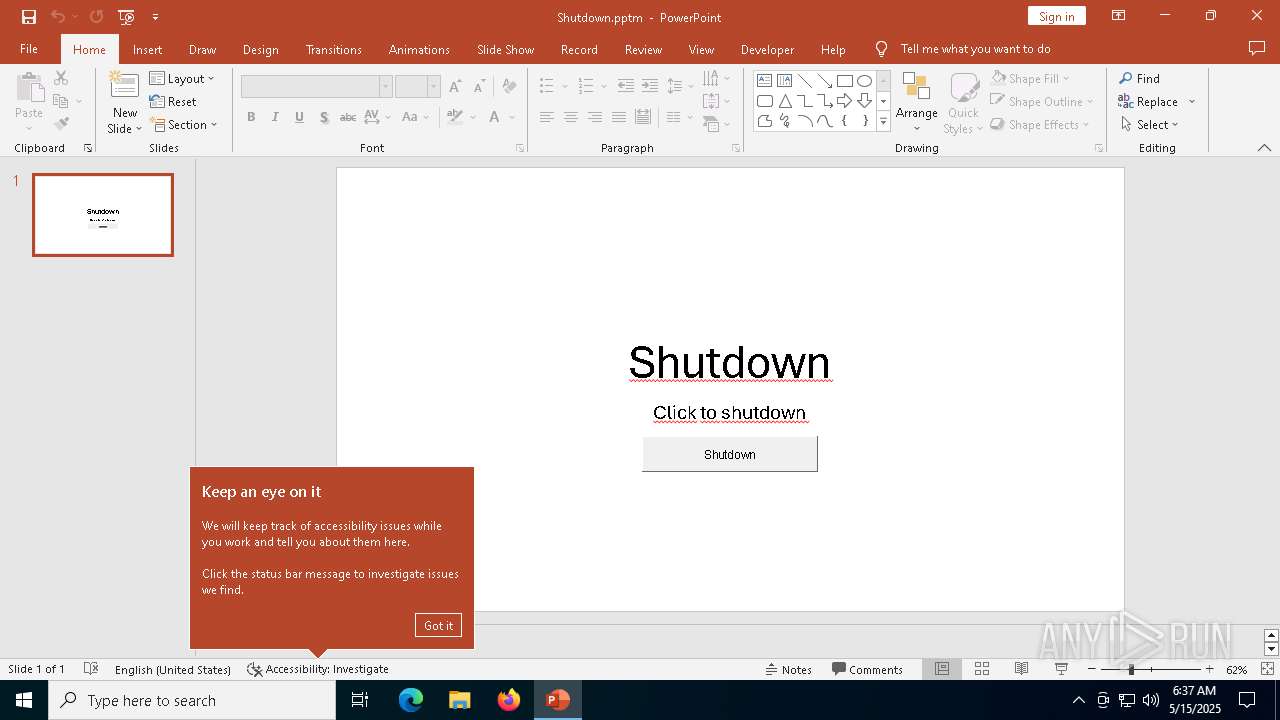
MALICIOUS
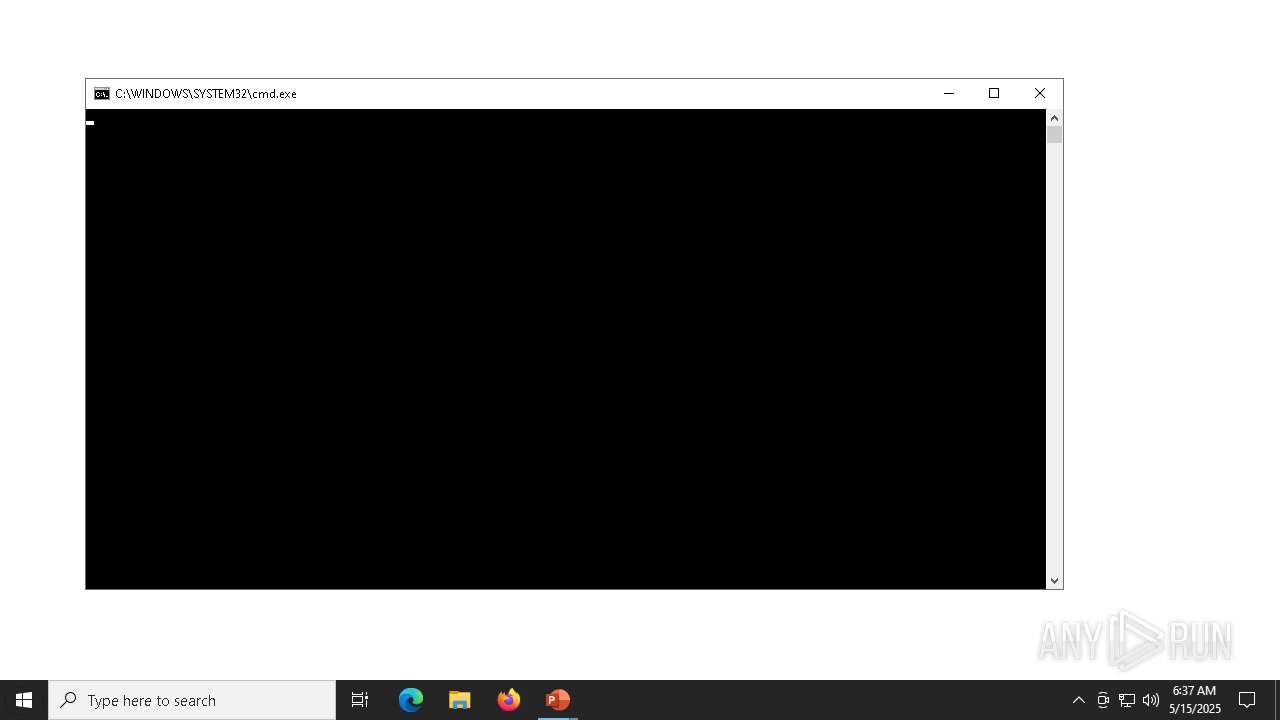
Starts CMD.EXE for commands execution
- POWERPNT.EXE (PID: 4628)
Microsoft Office executes commands via PowerShell or Cmd
- POWERPNT.EXE (PID: 4628)
Unusual execution from MS Office
- POWERPNT.EXE (PID: 4628)
SUSPICIOUS
The system shut down or reboot
- cmd.exe (PID: 7500)
Runs shell command (SCRIPT)
- POWERPNT.EXE (PID: 4628)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pptm | | | PowerPoint Microsoft Office Open XML Format document (with Macro) (42.2) |
|---|---|---|
| .pptx | | | PowerPoint Microsoft Office Open XML Format document (40.2) |
| .ppam | | | PowerPoint Macro-enabled Open XML add-in (11.5) |
| .zip | | | Open Packaging Conventions container (4.8) |
| .zip | | | ZIP compressed archive (1.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x24d5ec86 |
| ZipCompressedSize: | 506 |
| ZipUncompressedSize: | 3443 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Creator: | CAN BARIS ALTINOZ |
XML
| LastModifiedBy: | CAN BARIS ALTINOZ |
|---|---|
| RevisionNumber: | 6 |
| CreateDate: | 2025:05:15 06:31:56Z |
| ModifyDate: | 2025:05:15 06:35:51Z |
| TotalEditTime: | 3 minutes |
| Words: | 4 |
| Application: | Microsoft Office PowerPoint |
| PresentationFormat: | Geniş ekran |
| Paragraphs: | 2 |
| Slides: | 1 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
138
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3784 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | "C:\Program Files\Microsoft Office\Root\Office16\POWERPNT.EXE" C:\Users\admin\Desktop\Shutdown.pptm /ou "" | C:\Program Files\Microsoft Office\root\Office16\POWERPNT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7500 | cmd.exe /c shutdown /t 0 /f /s | C:\Windows\System32\cmd.exe | — | POWERPNT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | shutdown /t 0 /f /s | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 213
Read events
7 917
Write events
281
Delete events
15
Modification events
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 3 |
Value: 011C08000000001000B24E9A3E01000000000000000300000000000000 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\POWERPNT\4628 |
| Operation: | write | Name: | 0 |
Value: 0B0E101D2BF22D33D84945865D45239D76E2F0230046BC9BB482BCACF1ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5119424D2120C70006F0077006500720070006E0074002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4628) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
1
Suspicious files
21
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:8FC509D2B32ACAE4C2326268203D5F32 | SHA256:D5E9254561B803AB5A83DE5862F8BFC644D8BA3D975E47B40BAB083D4FE3C0E2 | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Shutdown.pptm.LNK | binary | |
MD5:633F3DA0C1B2A7FF5DB33048DEEFC247 | SHA256:1CCB412CFE74B05530B75734057E0E0DC69652F8189BB6C7C850305BDCC5688E | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\PreviewFont\flat_officeFontsPreview_4_41.ttf | binary | |
MD5:A807151D5747F6460143DC1FD2C3195F | SHA256:C0C3B354480E34CCC0C25D371B30D0272DB86C786AF6438C217998B0A30E5EB0 | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:3F8D8E689059DCB2DF7722C6D83F259D | SHA256:E3A269319D1EF767912149B53C1A48E3F2D343A7FFB08DE3F1EB8053E54A5A9E | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:B7A41DD39FAB5531E2B73A24149EEE8F | SHA256:19F595BFC47E60B42FAFABF156250BEFD9F042AFCC5E5833A656FF0D24BCB65B | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\PPT11.0\MSForms.exd | binary | |
MD5:DF67CD247B46AF5D21BEC7DC887ECA51 | SHA256:E719A3A70B10046BE5DD0BAB0B9BD493ADB3CD459A282856F683450941F31641 | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:69D2378D7814E585737D134B736E4C22 | SHA256:2C65E46F72FAA13A912386D7A23E89CF0C752C2E0F49CE0806797E63C9086927 | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\CloudFonts\Aptos Display\30169865670.ttf | binary | |
MD5:97B7D33D4AE42144B73E26635A71AD69 | SHA256:AF7A83E6F1D18B62535A8EE97939AB8653D5AC1FE1861CDB8FCE829D3878D901 | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\CloudFonts\Aptos\30153066857.ttf | binary | |
MD5:1250B2192733FA4D140AB32D9D31FBA1 | SHA256:95980114FCFD42F2F9C446DAE429B70582BF2F03097D68433EA9E7D85A49DA0B | |||
| 4628 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:E00B8EE5E993595894013E097DB07B4B | SHA256:17A566EFBE9AB4F4B717748EB6E8B063449B2C0A9CEC191A0E4A7BF2E4BAC793 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4628 | POWERPNT.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4628 | POWERPNT.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4628 | POWERPNT.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4628 | POWERPNT.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |