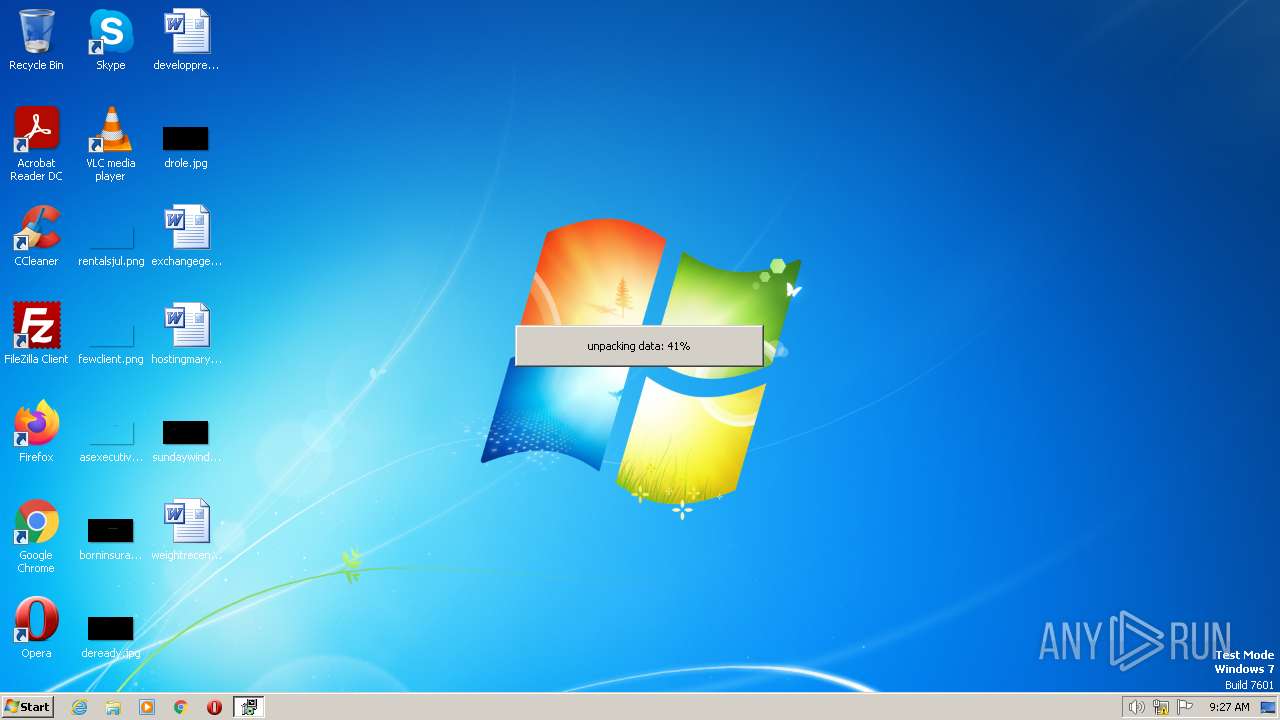
| File name: | Install_RMPrepUSB_Full_v2.1.746.exe |
| Full analysis: | https://app.any.run/tasks/b7995f6b-8e20-4e0e-8846-2545c0b79542 |
| Verdict: | Malicious activity |
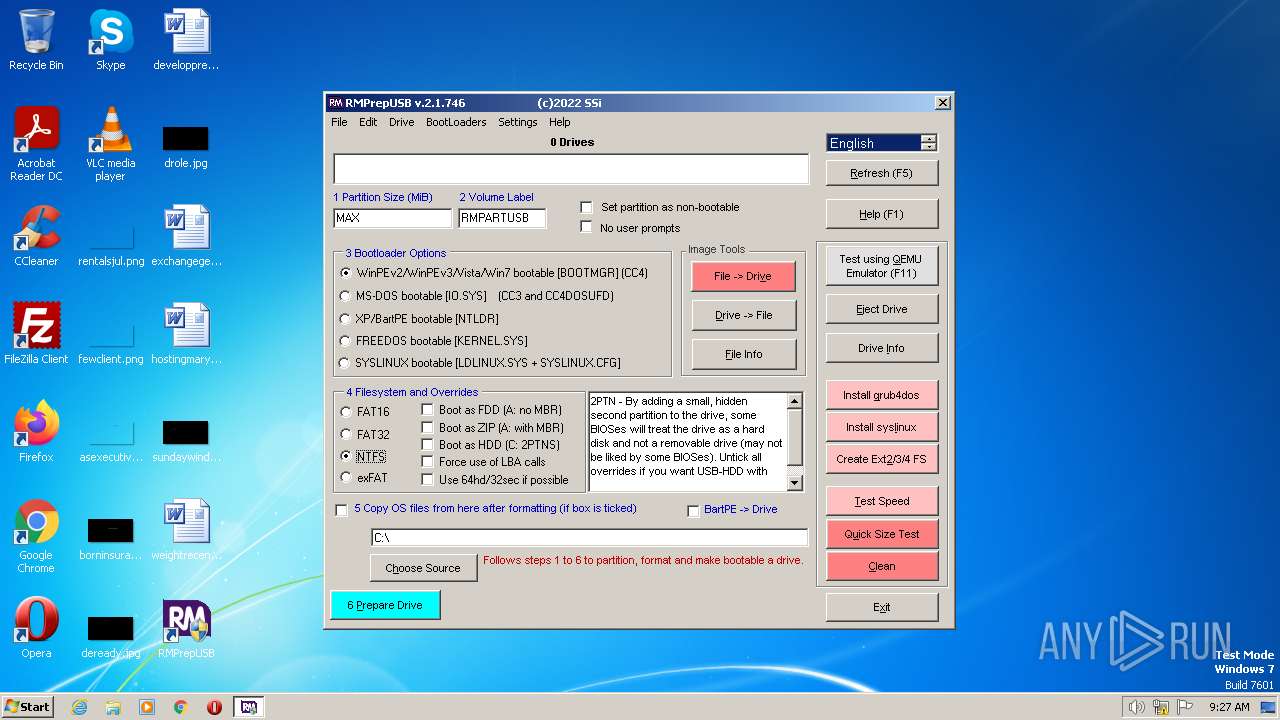
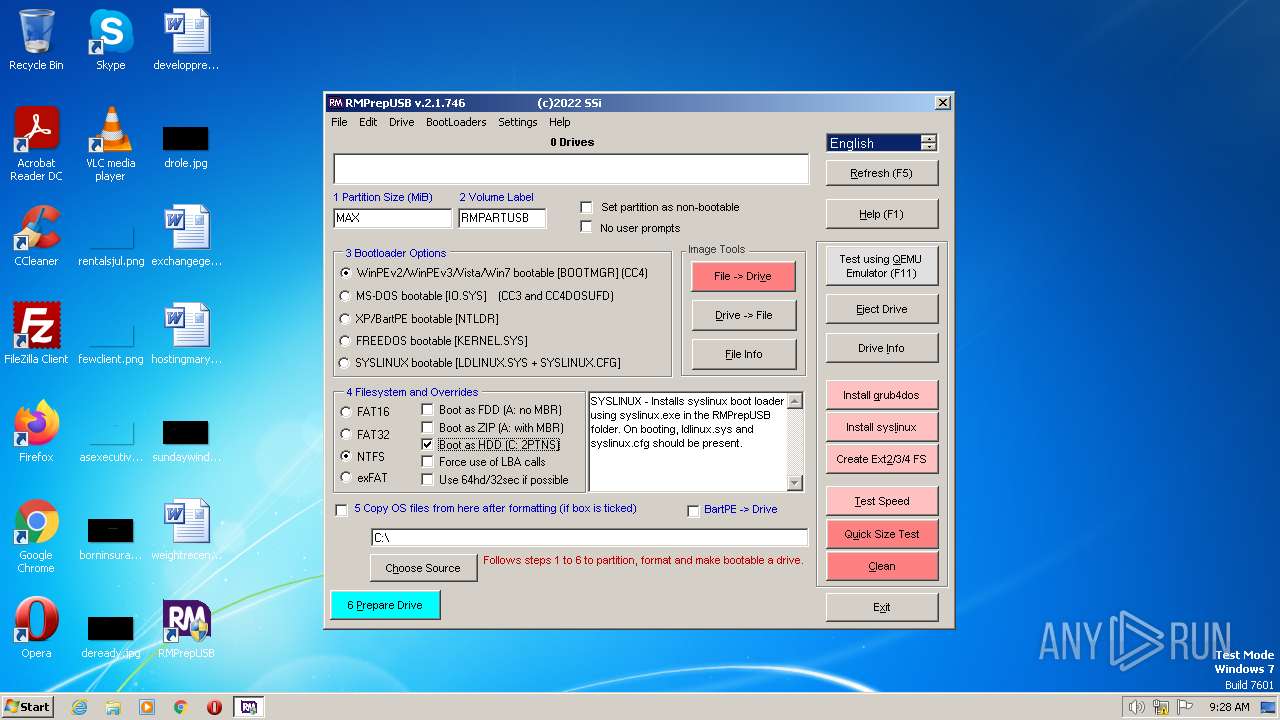
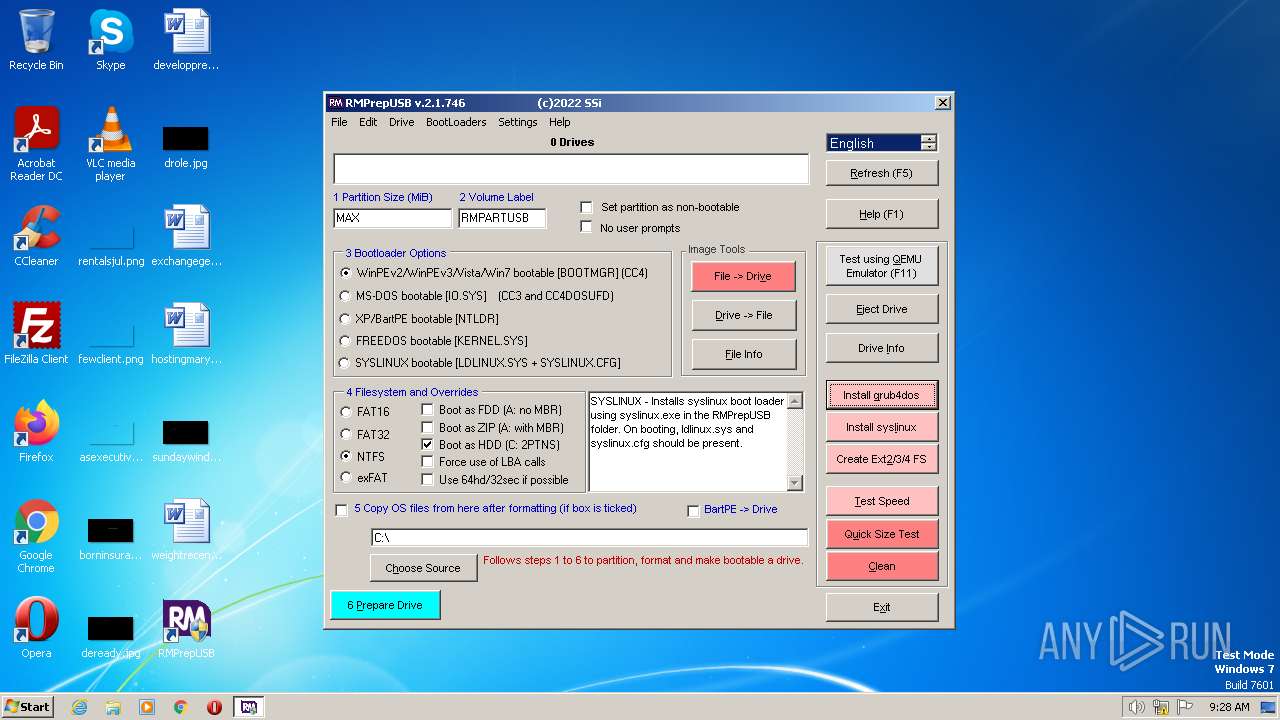
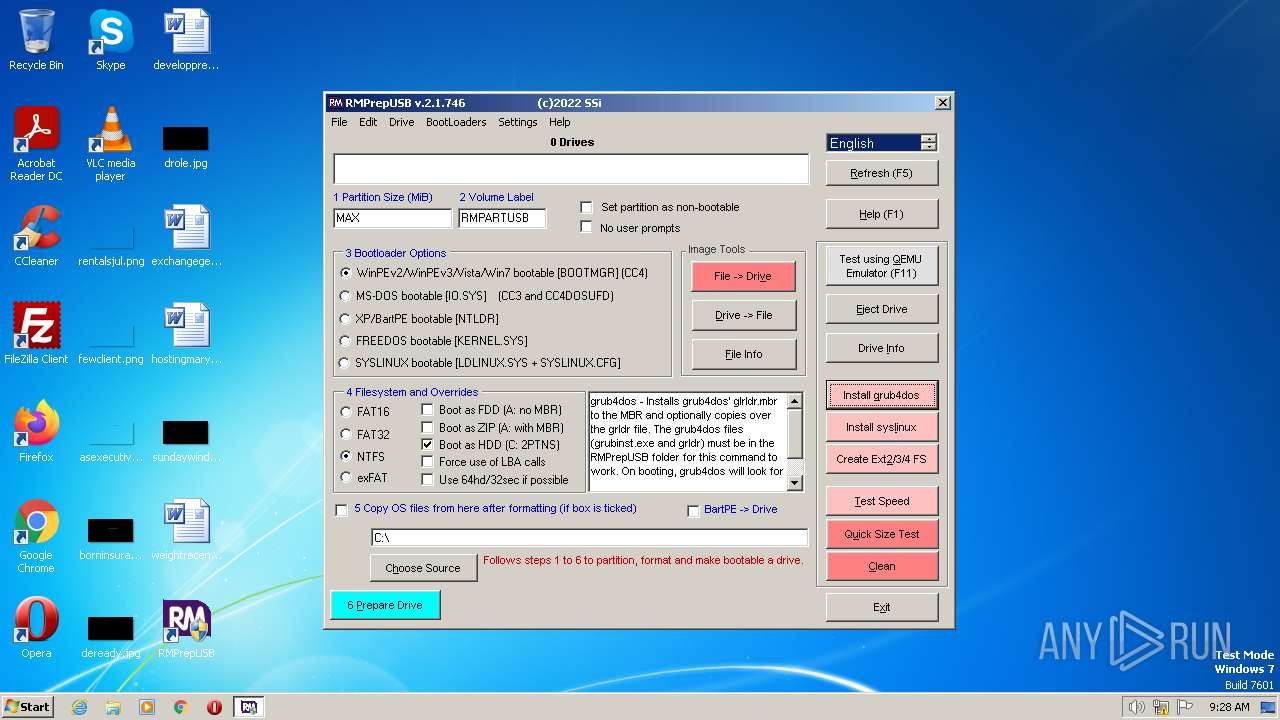
| Analysis date: | June 21, 2023, 08:26:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
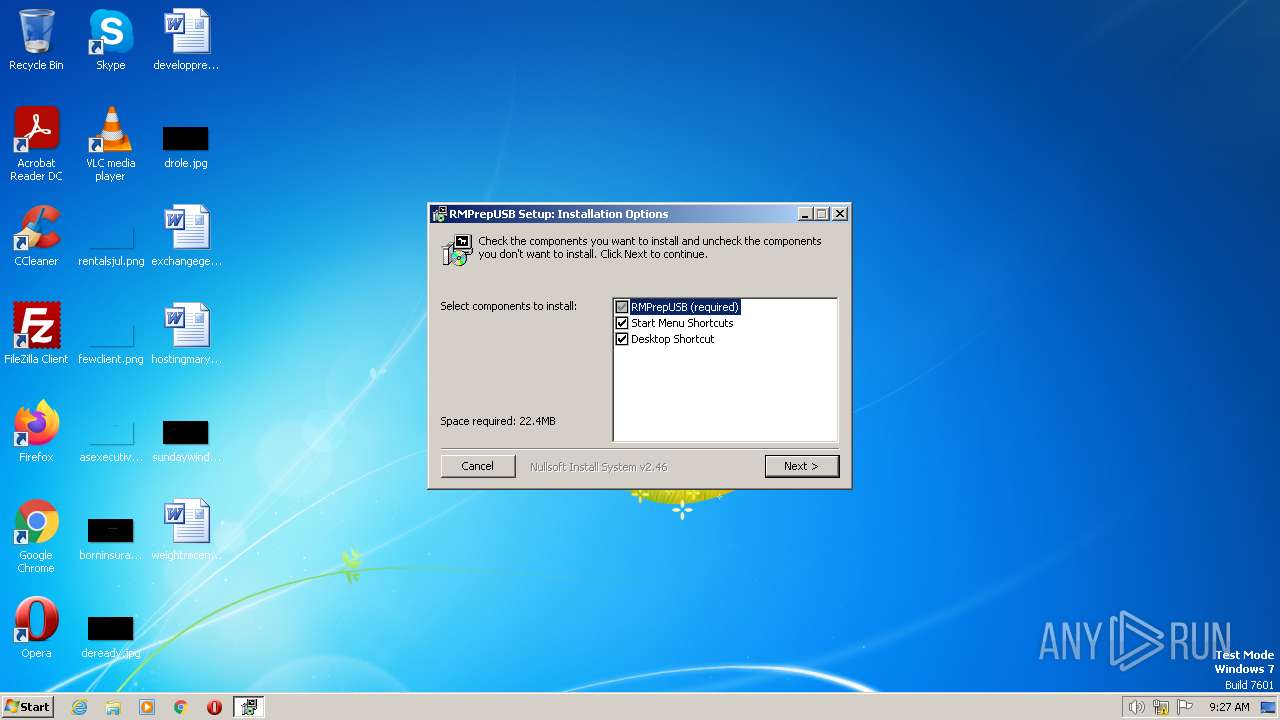
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | ECC4AC0DE4BA3E1DA417671717062BCA |
| SHA1: | 6D9A42C5A190582BF3AC61C7B33F3EAFB953B03C |
| SHA256: | 5A94297D0DCA8F767865F0D374E4E81FD357F58B5932FE666EED614BCC6026CB |
| SSDEEP: | 196608:VrmIUZbYLGWWERnC3xy6LrSfWIbW7AvSDrR+EmggEo39MdSa+PKXlu:Vr5URZ3xy6Xabjy00gIdSa1u |
MALICIOUS
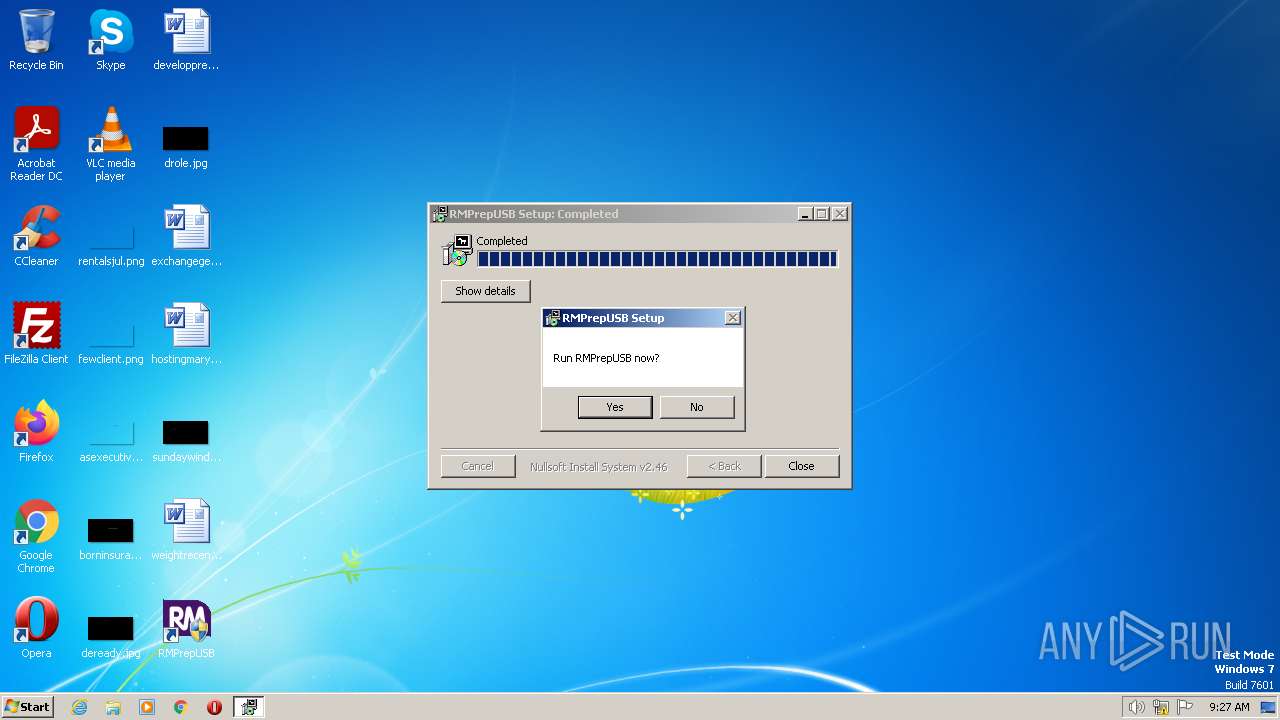
Loads dropped or rewritten executable
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
Application was dropped or rewritten from another process
- RMPREPUSB.exe (PID: 3904)
Detects Cygwin installation
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
SUSPICIOUS
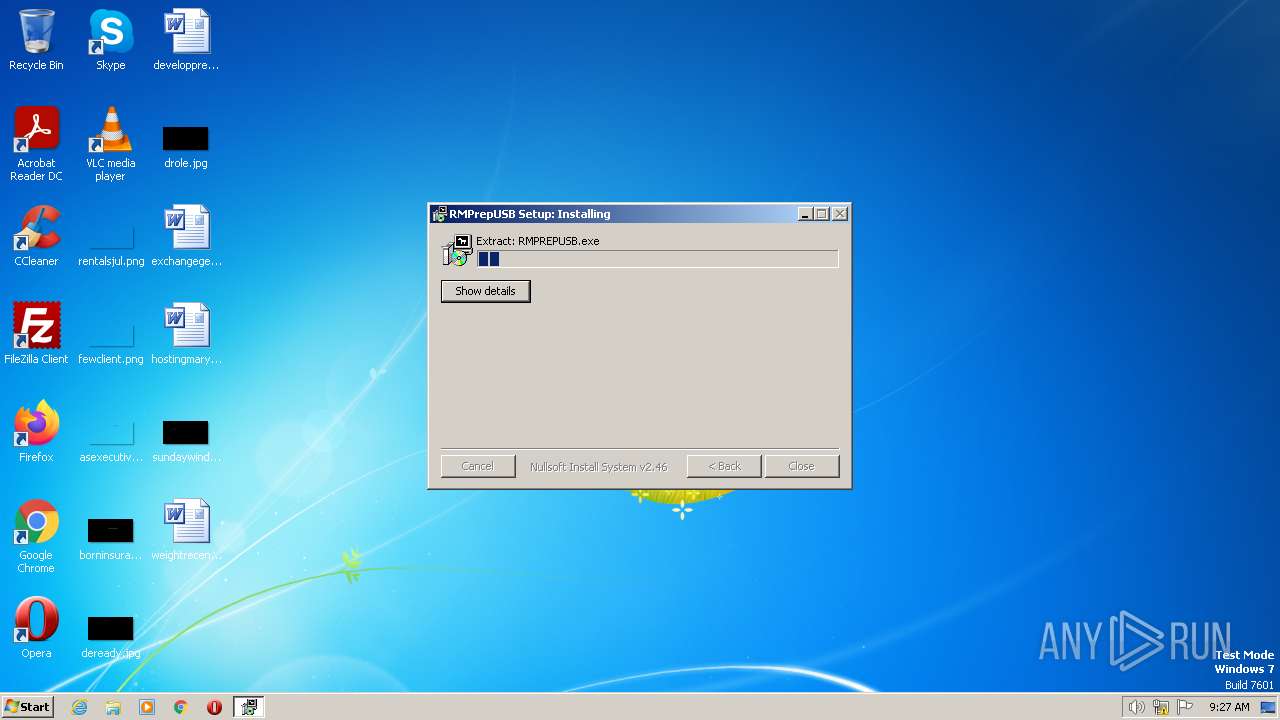
Executable content was dropped or overwritten
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
INFO
The process checks LSA protection
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
- RMPREPUSB.exe (PID: 3904)
Create files in a temporary directory
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
- RMPREPUSB.exe (PID: 3904)
Reads the computer name
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
Checks supported languages
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
- RMPREPUSB.exe (PID: 3904)
Creates files or folders in the user directory
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
Reads the machine GUID from the registry
- RMPREPUSB.exe (PID: 3904)
Creates files in the program directory
- Install_RMPrepUSB_Full_v2.1.746.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002C000 | 0x00001E78 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.78713 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
203 | 2.54013 | 304 | UNKNOWN | English - United States | RT_DIALOG |
204 | 2.65501 | 296 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | "C:\Users\admin\AppData\Local\Temp\Install_RMPrepUSB_Full_v2.1.746.exe" | C:\Users\admin\AppData\Local\Temp\Install_RMPrepUSB_Full_v2.1.746.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\Install_RMPrepUSB_Full_v2.1.746.exe" | C:\Users\admin\AppData\Local\Temp\Install_RMPrepUSB_Full_v2.1.746.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
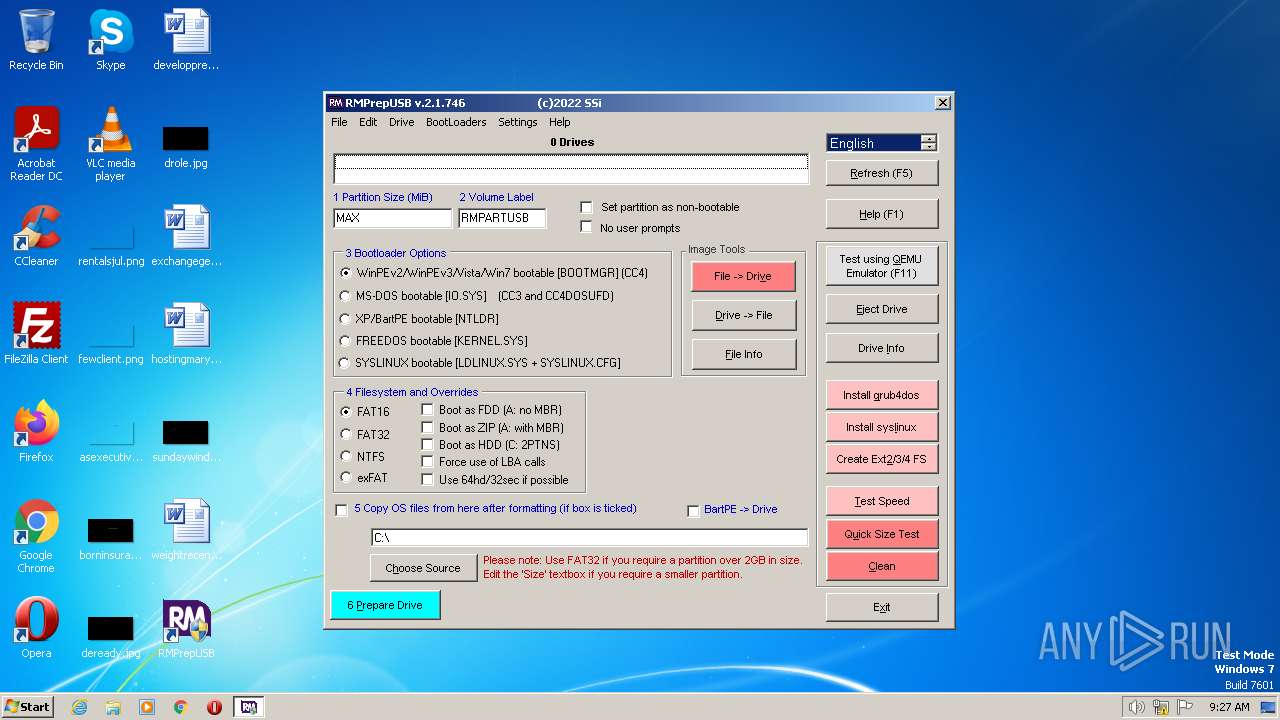
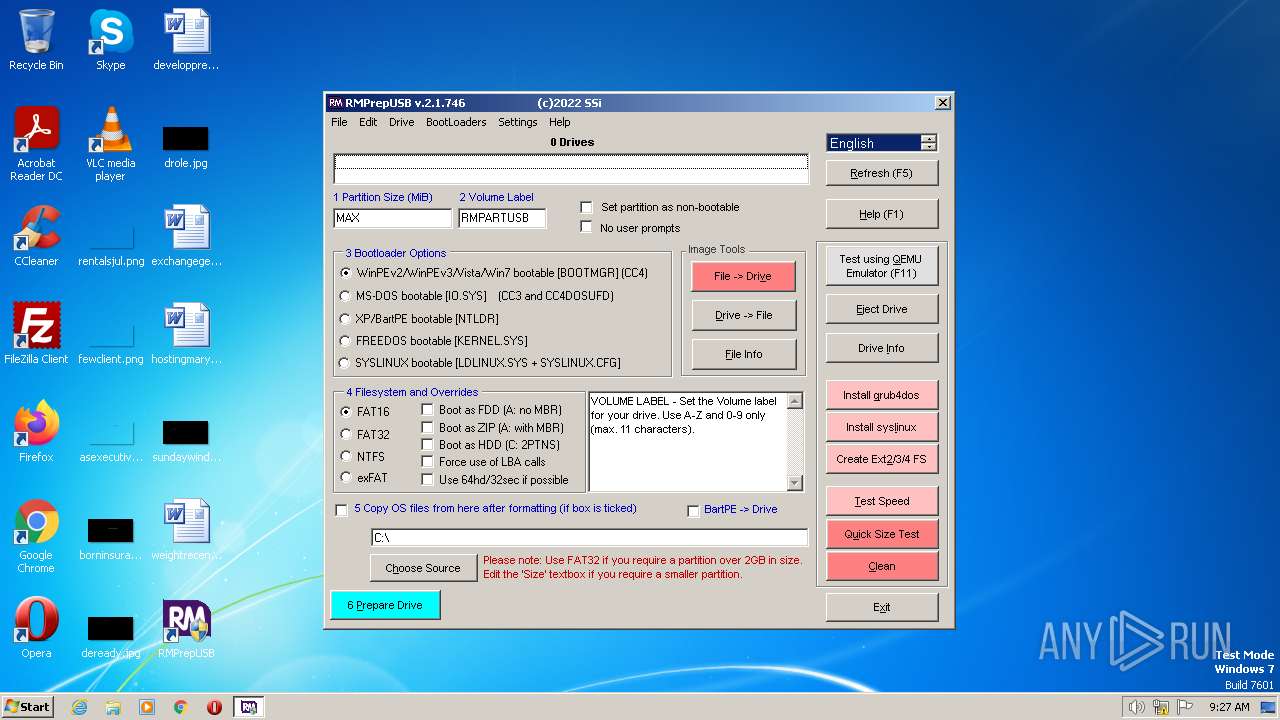
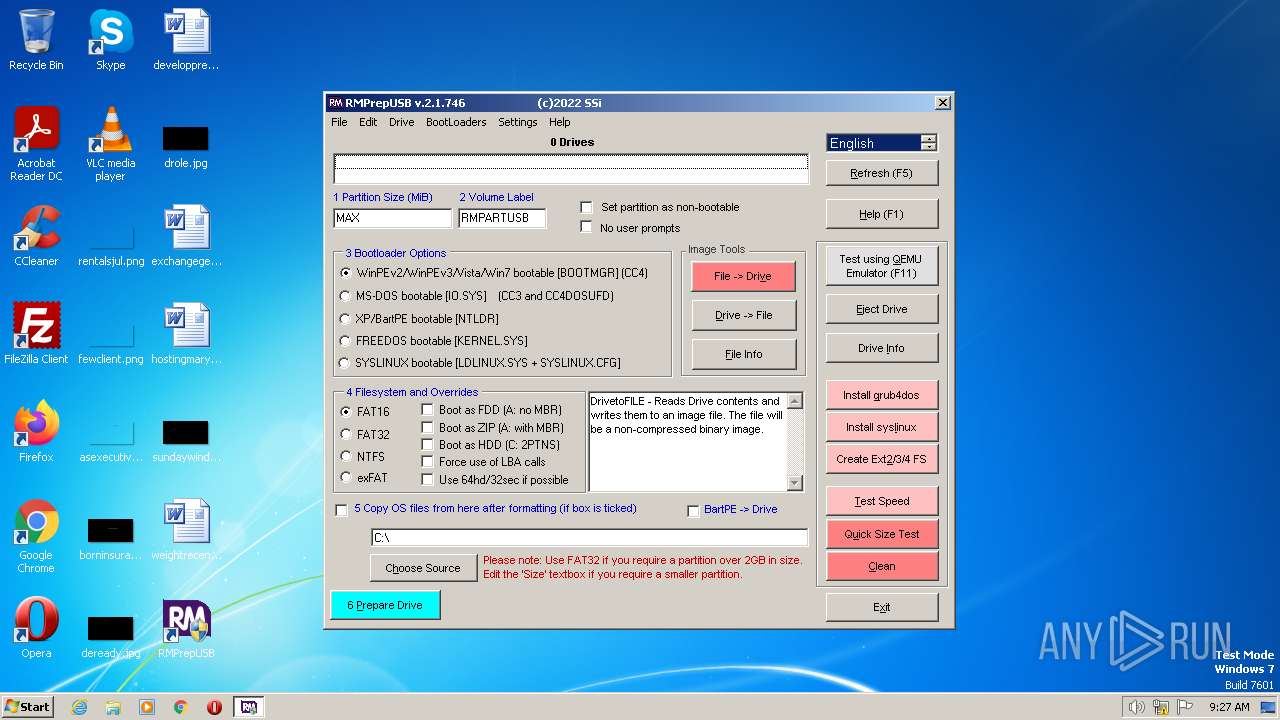
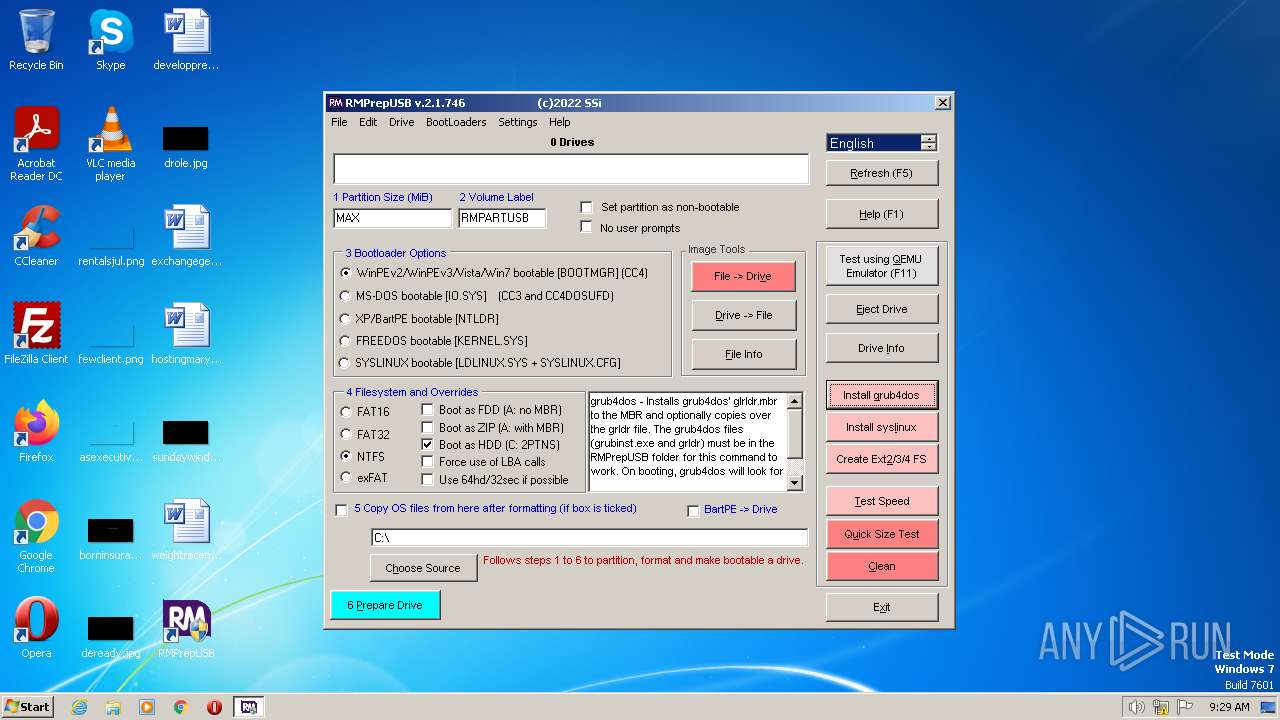
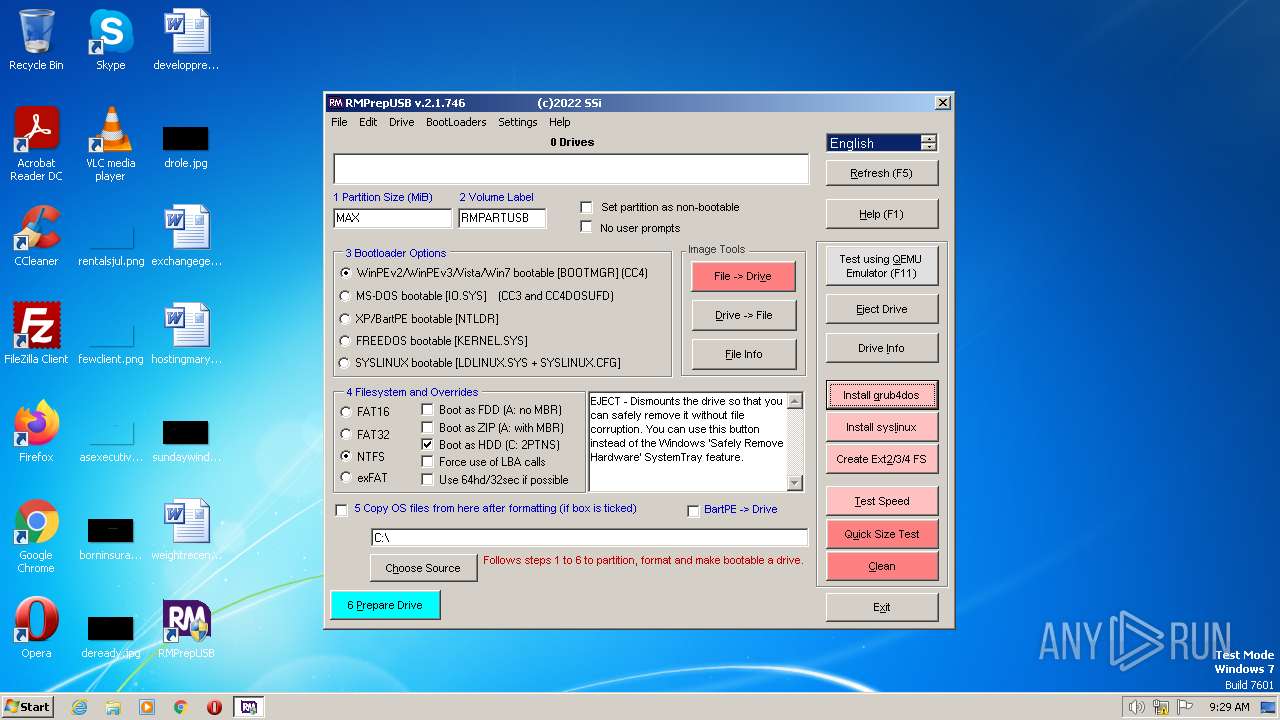
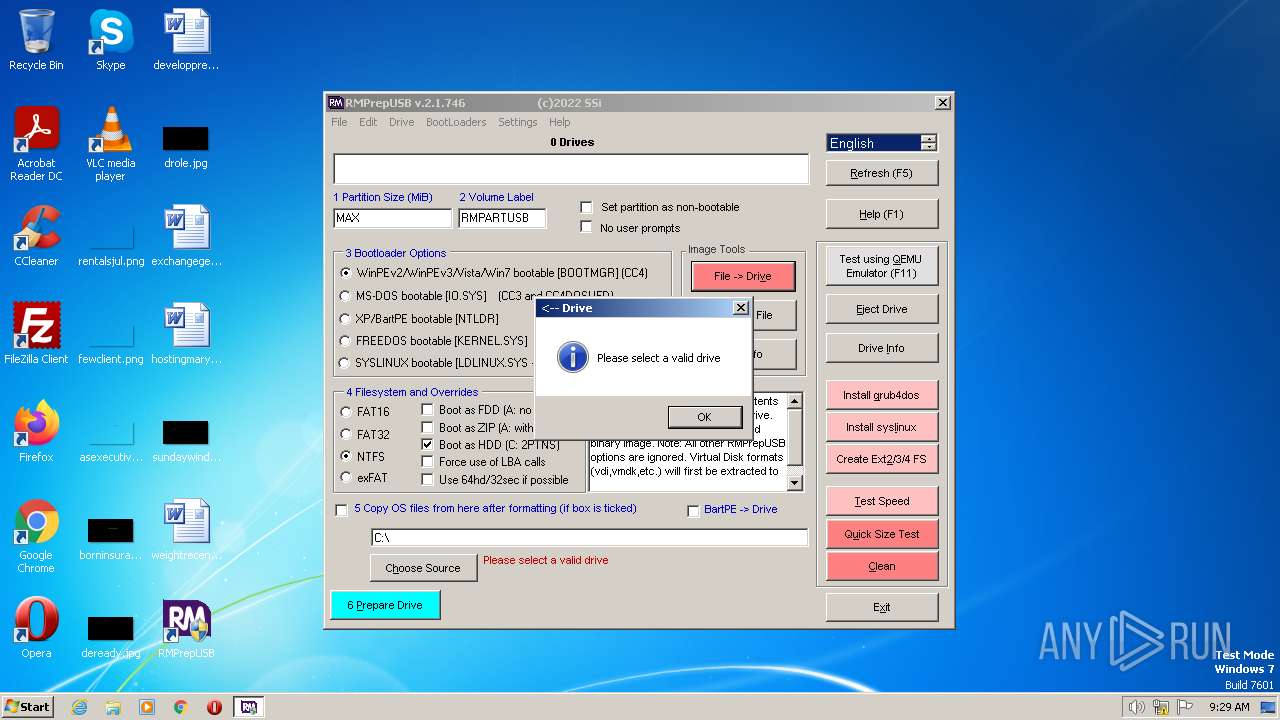
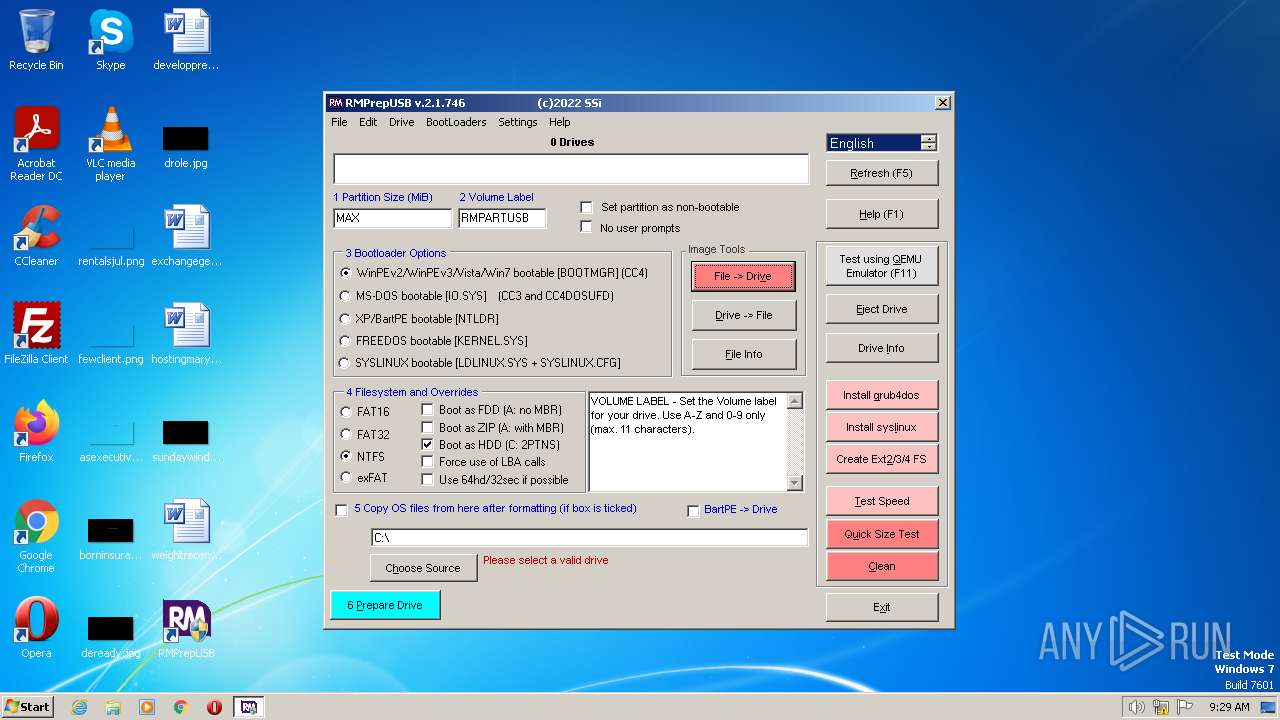
| 3904 | "C:\Program Files\RMPrepUSB\RMPrepUSB.exe" | C:\Program Files\RMPrepUSB\RMPREPUSB.exe | — | Install_RMPrepUSB_Full_v2.1.746.exe | |||||||||||
User: admin Company: RM Education plc Integrity Level: HIGH Description: RMPrepUSB Exit code: 0 Version: 2.01.0746 Modules
| |||||||||||||||
Total events
747
Read events
747
Write events
0
Delete events
0
Modification events
Executable files
44
Suspicious files
61
Text files
89
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\readme.txt | text | |
MD5:E628EFBCA1277C343D59616527BEAC50 | SHA256:6634A778C568872C8C5A8D1D04D94F6CA6174FF43203A43A9A38458010A0E6CA | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\syslinux.exe | executable | |
MD5:F40226F3949AB55D846E6201AE7D4BE0 | SHA256:2A7C0C9468534F1A75AA729203D654C4C57CCCC0263D3BA71384B4ADC56BD980 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\RMPARTUSB.exe.manifest | xml | |
MD5:905729481037D2A6C2DA34DF570D381B | SHA256:2A63525AE4D86AD8BB0CDD2C389FE725E1EEDDD2EA63AD9B18C90F9EA29DB735 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\grubinst.exe | executable | |
MD5:D47C997592734C9534C79B19ED8415AB | SHA256:415EE1CA56711D3B0F477E3E1F5E7D3D6249D54B6DB378D28AFB9591082FB685 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\RMPartUSB.txt | text | |
MD5:75D04FDA9B47063E8FDC1D0167A38ADB | SHA256:CCFA5FB98FC0EFEAAF0ABA2E650BE279C413786595B67BE894A7A6B8CA6AC5D2 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\rmprepusbxp.cmd | text | |
MD5:05709055EC5F6377EF14BB8DBE9D9A1F | SHA256:F8C109DE50B209170ECD5CE77AC9572A03266E3FB51C7764D8A5EC27B5E678D1 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\RMPREPUSB.exe.manifest | xml | |
MD5:AF06EB778202A5A8FF25091CA480F160 | SHA256:3B6489B8CEEE80767CEAB11C4FAAD38CCFF6B7D2400C8DB093E0558FE5E56ADC | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\rmprepusbxp_German.cmd | text | |
MD5:D2BAADD05853D5B24BB521D856A7AD89 | SHA256:CD35D0CD70305D46D9EF8A7389A30ABCFD393A43C70BBAB888F2BB80A776BB56 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\touchdrv.exe | executable | |
MD5:A434D25922BFCCE7D0AD14D578434980 | SHA256:4DB5FEB77095C59B3933737F148E4DEDD7AAE482839A4D693F0B945503714357 | |||
| 3260 | Install_RMPrepUSB_Full_v2.1.746.exe | C:\Program Files\RMPrepUSB\GPL.txt | text | |
MD5:EBF48CADD237B0D517BE5865ED9E5282 | SHA256:1385D5E581E5716B79651F3CA4838DEAE50E00CA6178DBDCB87BD4825E57FACB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |