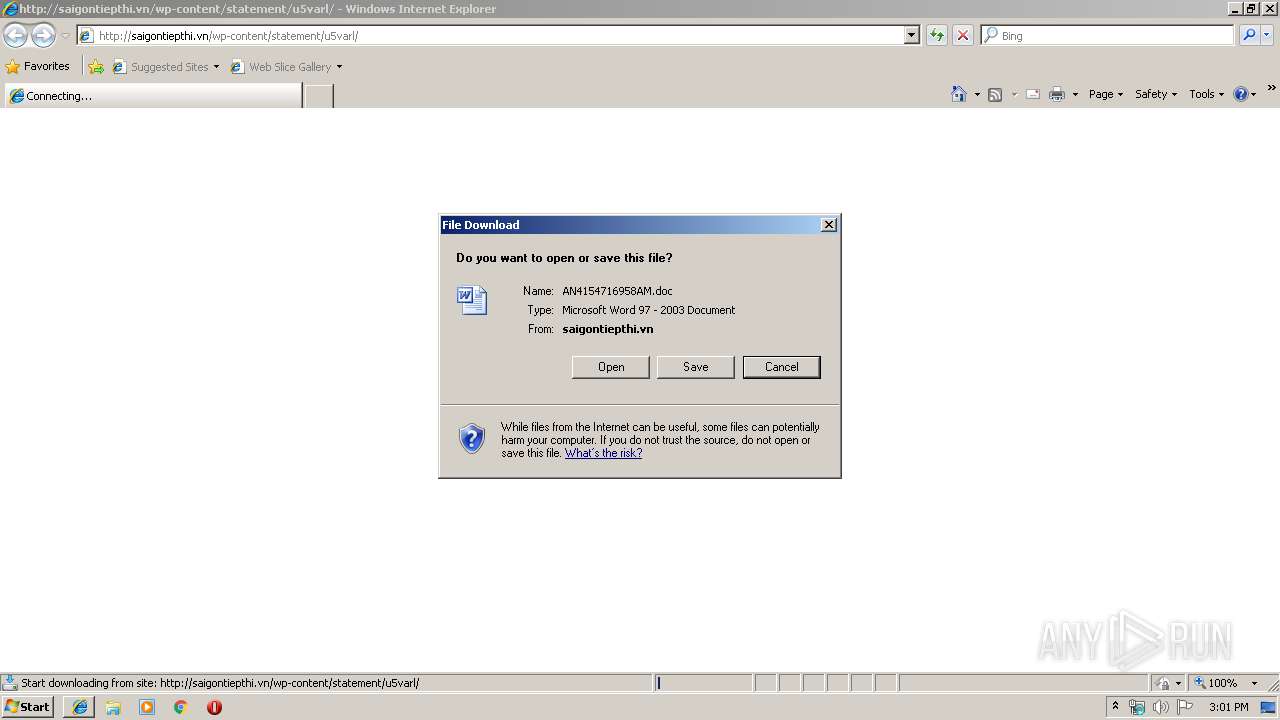
| URL: | http://saigontiepthi.vn/wp-content/statement/u5varl/ |
| Full analysis: | https://app.any.run/tasks/5dc6403d-c1d3-463f-91c9-4a4bdeb3d290 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
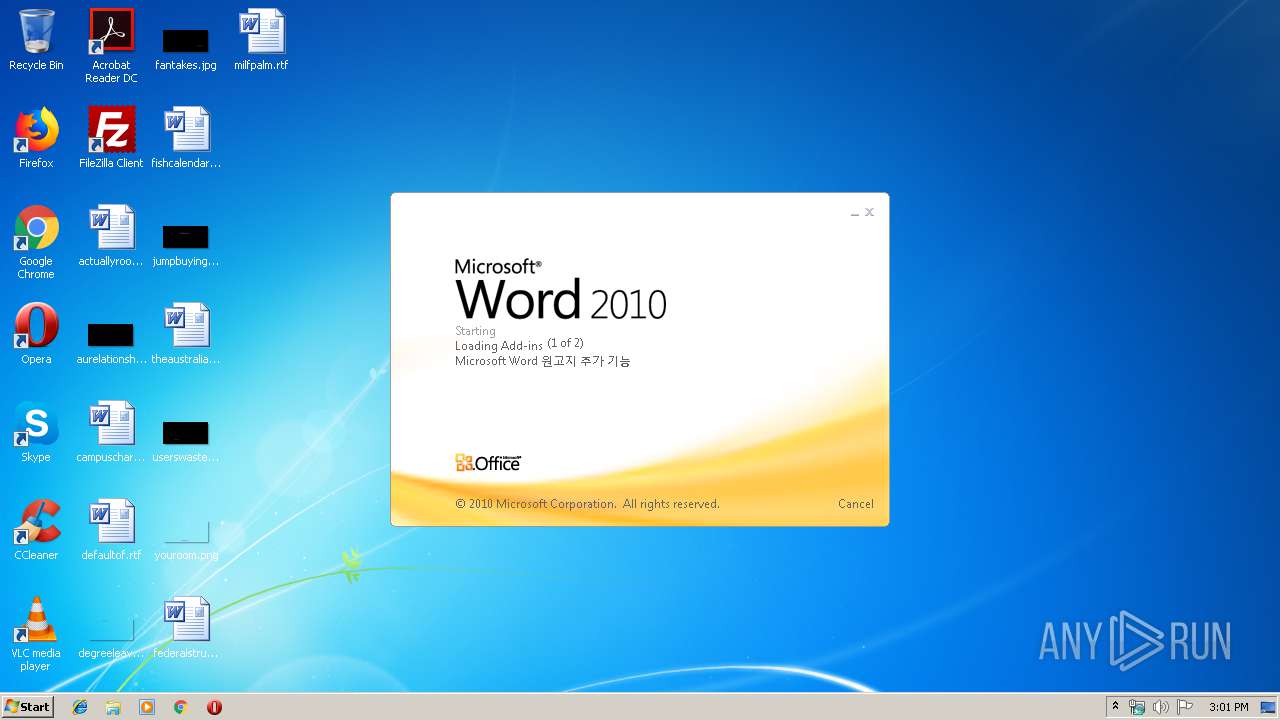
| Analysis date: | January 17, 2020, 15:01:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9FEE2C894CA8011938EE7E7066B4AD5D |
| SHA1: | 6EA3D9B5FF8EF46064181E0C4767D4A22068D52E |
| SHA256: | 5A8953625AF76A12F42A9901E3441376CCF6D77FA246DA70BF49E21ADCF01807 |
| SSDEEP: | 3:N1KNEMt7e+SifAQWNIuRLGtn:CWMt7fSOAJRL4n |
MALICIOUS
Drops known malicious document
- iexplore.exe (PID: 3508)
- WINWORD.EXE (PID: 1884)
Application was dropped or rewritten from another process
- 858.exe (PID: 1896)
- 858.exe (PID: 2916)
- serialfunc.exe (PID: 1024)
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 4080)
- serialfunc.exe (PID: 504)
- serialfunc.exe (PID: 3804)
- WymyprzZaD.exe (PID: 2528)
- WymyprzZaD.exe (PID: 3524)
- serialfunc.exe (PID: 2836)
- serialfunc.exe (PID: 4088)
EMOTET was detected
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 4088)
Emotet process was detected
- 858.exe (PID: 1896)
- WymyprzZaD.exe (PID: 2528)
Connects to CnC server
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 4088)
Changes the autorun value in the registry
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 4088)
Actions looks like stealing of personal data
- serialfunc.exe (PID: 4080)
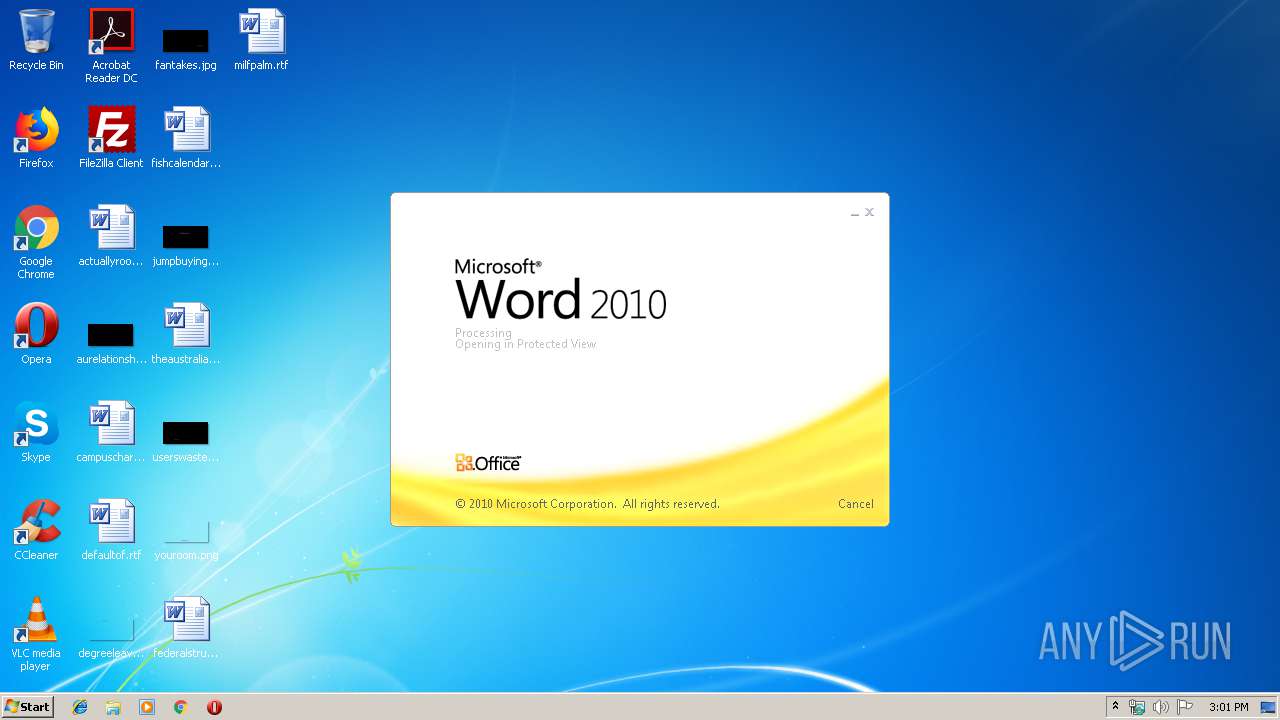
SUSPICIOUS
Creates files in the user directory
- Powershell.exe (PID: 3116)
Application launched itself
- WINWORD.EXE (PID: 1884)
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 1024)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 1884)
- iexplore.exe (PID: 2480)
PowerShell script executed
- Powershell.exe (PID: 3116)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3116)
- 858.exe (PID: 1896)
- serialfunc.exe (PID: 584)
- WymyprzZaD.exe (PID: 2528)
Executed via WMI
- Powershell.exe (PID: 3116)
Starts itself from another location
- 858.exe (PID: 1896)
- serialfunc.exe (PID: 584)
- WymyprzZaD.exe (PID: 2528)
Connects to server without host name
- serialfunc.exe (PID: 584)
- serialfunc.exe (PID: 4088)
Creates files in the program directory
- serialfunc.exe (PID: 584)
Connects to unusual port
- serialfunc.exe (PID: 584)
Loads DLL from Mozilla Firefox
- serialfunc.exe (PID: 4080)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2480)
Application launched itself
- iexplore.exe (PID: 2480)
Creates files in the user directory
- WINWORD.EXE (PID: 1884)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 2480)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1884)
- WINWORD.EXE (PID: 1704)
- serialfunc.exe (PID: 3804)
- serialfunc.exe (PID: 504)
Reads Internet Cache Settings
- iexplore.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
16
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\7FB7.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 584 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1024 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 858.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
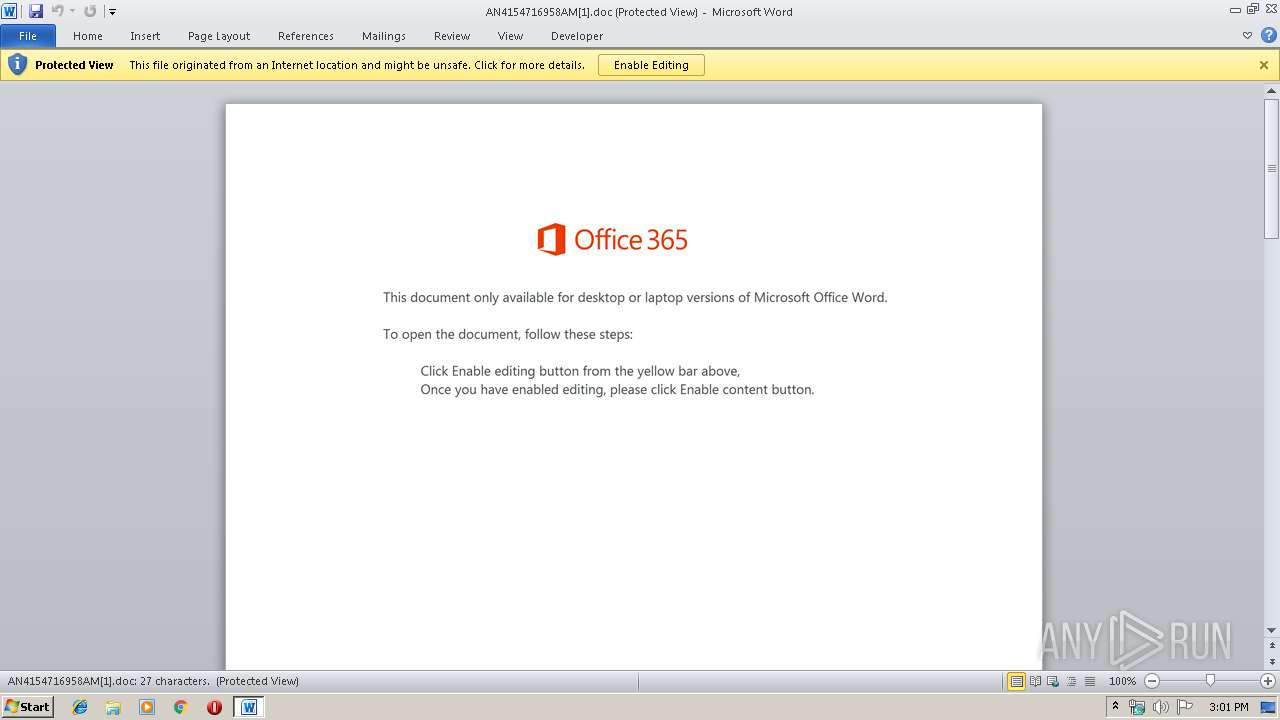
| 1884 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QYYA1EE4\AN4154716958AM[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1896 | --e90241f9 | C:\Users\admin\858.exe | 858.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://saigontiepthi.vn/wp-content/statement/u5varl/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2528 | --5e452eaa | C:\ProgramData\WymyprzZaD.exe | WymyprzZaD.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2836 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | WymyprzZaD.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2916 | "C:\Users\admin\858.exe" | C:\Users\admin\858.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 806
Read events
2 810
Write events
823
Delete events
173
Modification events
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {46E43511-393A-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E4070100050011000F0001002E008000 | |||
Executable files
4
Suspicious files
7
Text files
9
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF98D502A20B20ACA9.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBB7A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2B973E3C-CBD0-4E73-808A-B55AC5B7483A.0\58D87BA0.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF4607E9662C960E3.TMP | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{46E43511-393A-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9C612BBEBFC9F758.TMP | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2B973E3C-CBD0-4E73-808A-B55AC5B7483A.0\~DF43BB110C643DCF06.TMP | — | |
MD5:— | SHA256:— | |||
| 3116 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CS7H0UGWQGTANMT4Z4AO.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
11
DNS requests
3
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4088 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/UV1A8gRjlm7rn2 | PL | binary | 148 b | malicious |
3508 | iexplore.exe | GET | 200 | 45.117.168.215:80 | http://saigontiepthi.vn/wp-content/statement/u5varl/ | VN | document | 165 Kb | unknown |
584 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/P1eIWh2h4 | US | binary | 148 b | malicious |
584 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/prb1 | US | binary | 1.53 Mb | malicious |
584 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/P1eIWh2h4 | PL | binary | 148 b | malicious |
584 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/e1xuS82Lz4oJtbh | PL | — | — | malicious |
584 | serialfunc.exe | POST | 200 | 91.205.215.10:7080 | http://91.205.215.10:7080/teapot/symbols/add/ | NL | binary | 148 b | malicious |
2480 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4088 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/goGh1NW | PL | — | — | malicious |
4088 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/oeDcwci | US | binary | 708 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2480 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3508 | iexplore.exe | 45.117.168.215:80 | saigontiepthi.vn | SUPERDATA | VN | unknown |
3116 | Powershell.exe | 208.91.198.220:80 | neilwilliamson.ca | PDR | US | malicious |
584 | serialfunc.exe | 100.6.23.40:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
584 | serialfunc.exe | 91.236.4.234:443 | — | FHU Climax Rafal Kraj | PL | malicious |
584 | serialfunc.exe | 91.205.215.10:7080 | — | MaxiTEL Telecom B.V. | NL | malicious |
4088 | serialfunc.exe | 100.6.23.40:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
4088 | serialfunc.exe | 91.236.4.234:443 | — | FHU Climax Rafal Kraj | PL | malicious |
4088 | serialfunc.exe | 65.99.217.242:8080 | — | Colo4, LLC | US | malicious |
4088 | serialfunc.exe | 149.210.171.237:8080 | — | Transip B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saigontiepthi.vn |
| unknown |
www.bing.com |
| whitelisted |
neilwilliamson.ca |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3116 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3116 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3116 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
584 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
584 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
584 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
584 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
584 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
584 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
584 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2 ETPRO signatures available at the full report