| URL: | https://anonfiles.com/Ycf7Eb17y6/6.6.1.15_Nero-6.6.1.15_no_at_exe |
| Full analysis: | https://app.any.run/tasks/8d9b2a42-dc84-4dfe-bd14-5cf38a9d57f4 |
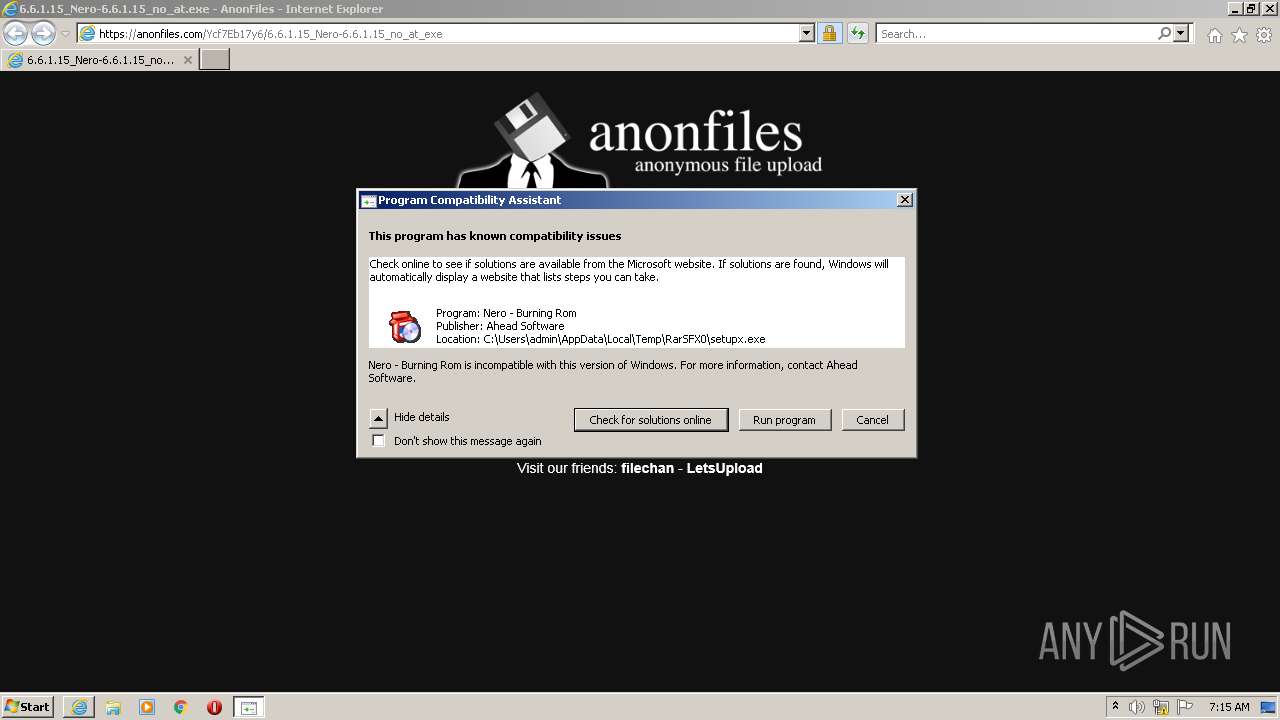
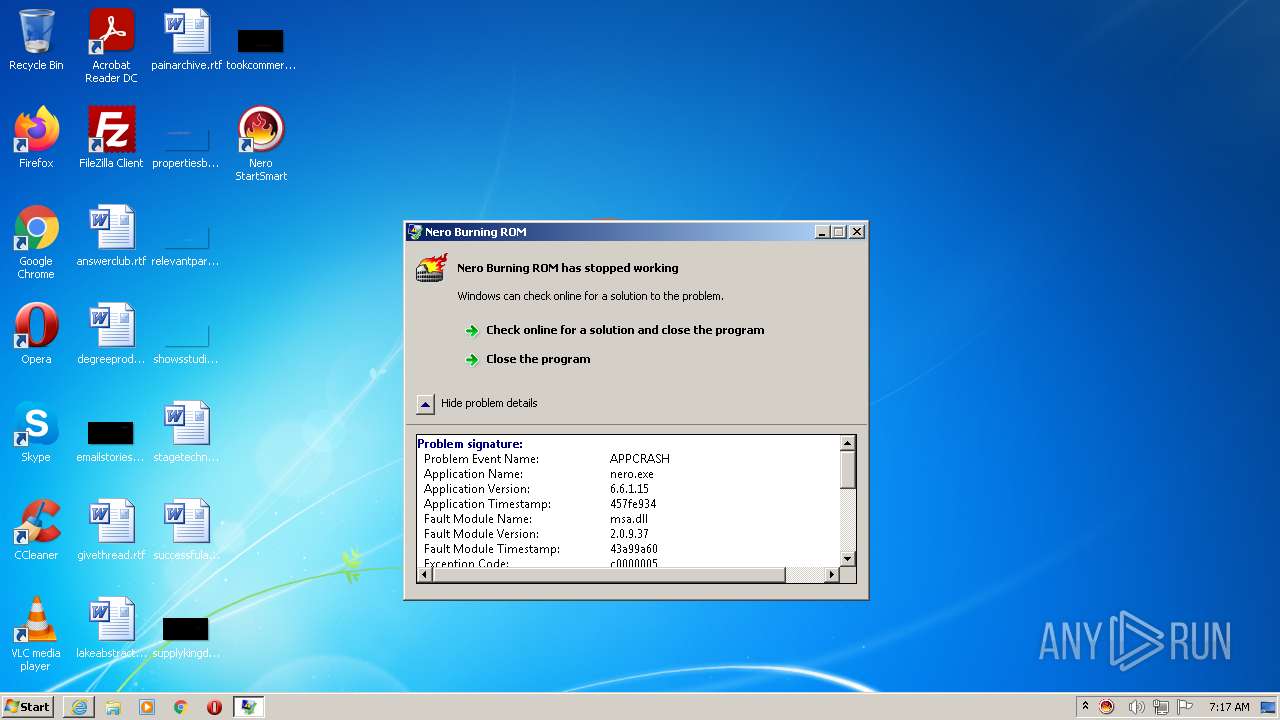
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2022, 06:14:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 30E1CBA6A6A745C38E9F448DDA590EC7 |
| SHA1: | 4B817EA7E8D9A20D76302A84CE85623992DB071E |
| SHA256: | 5A88A7EA2554A6DA7CFBE94301DA4B87EF3316E5FE9CDCE97B9E9BB384747B38 |
| SSDEEP: | 3:N8M2LCJGnGvROn:2M2L8+2ROn |
MALICIOUS
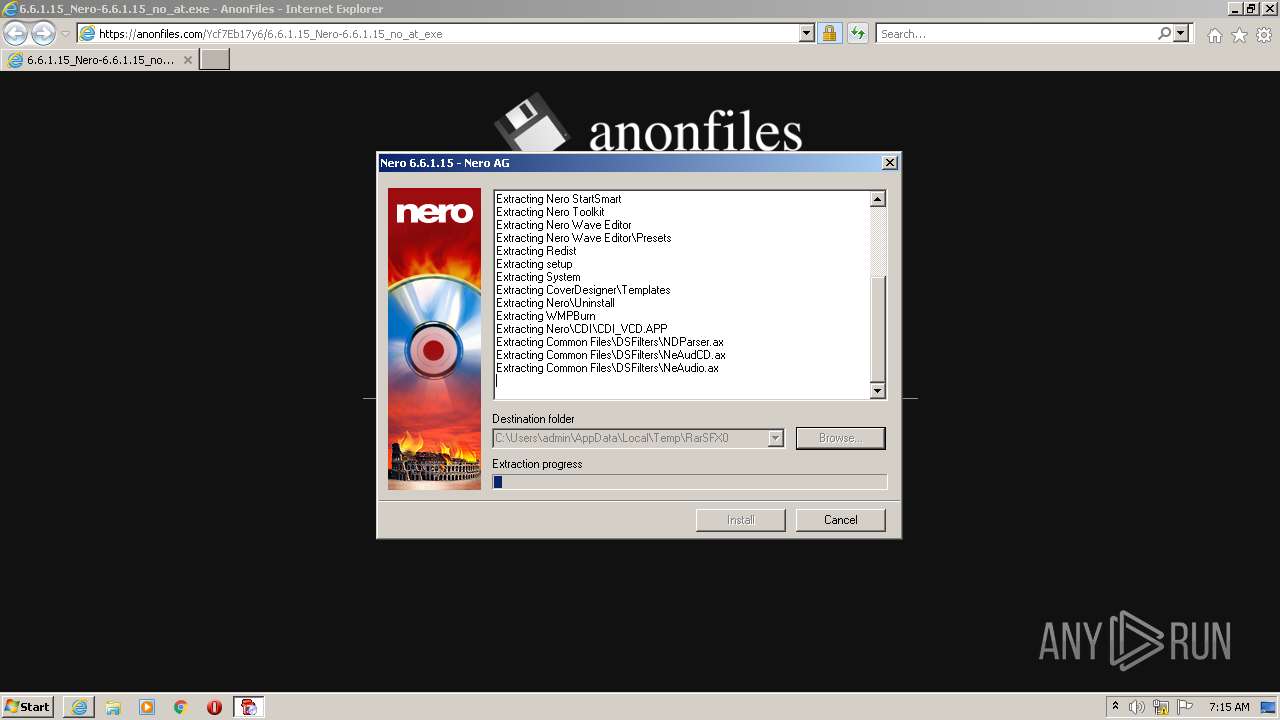
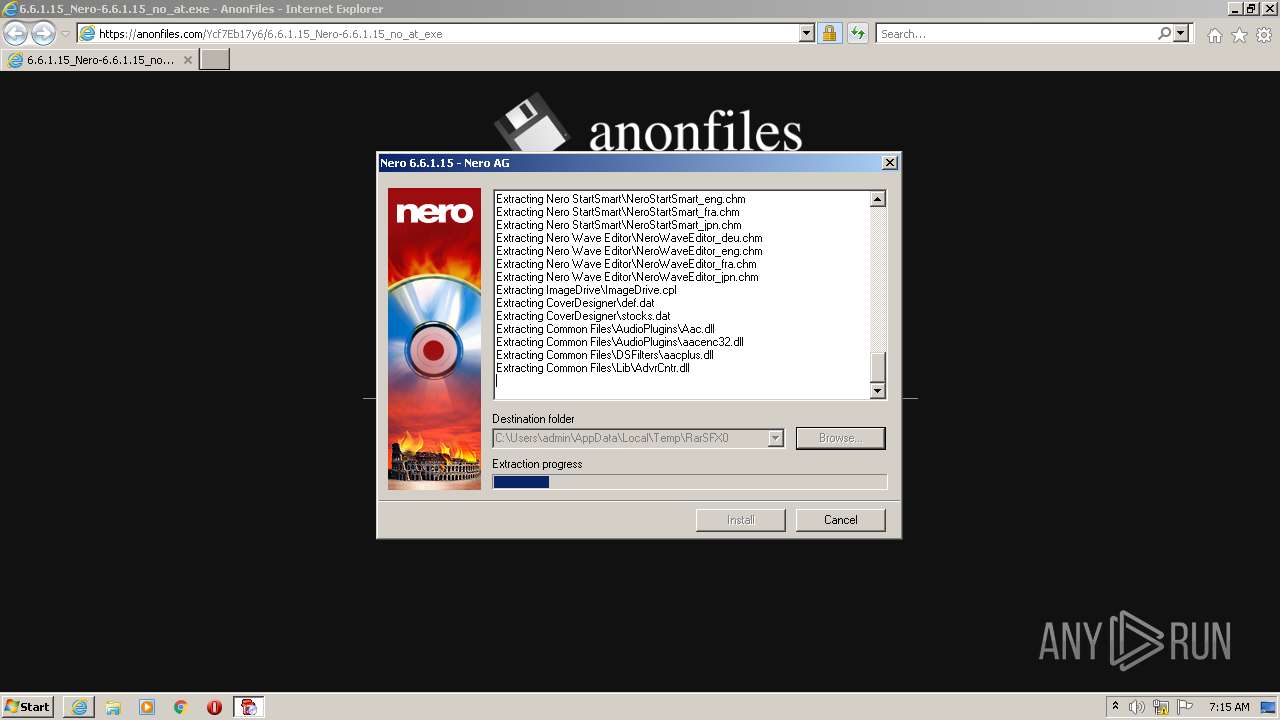
Application was dropped or rewritten from another process
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3020)
- setupx.exe (PID: 2768)
- NeroCheck.exe (PID: 2532)
- NeroStartSmart.exe (PID: 4088)
- nero.exe (PID: 3292)
Drops executable file immediately after starts
- iexplore.exe (PID: 3456)
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- setupx.exe (PID: 2768)
Loads dropped or rewritten executable
- setupx.exe (PID: 2768)
- NeroStartSmart.exe (PID: 4088)
- nero.exe (PID: 3292)
- svchost.exe (PID: 860)
- WerFault.exe (PID: 2836)
Changes the autorun value in the registry
- setupx.exe (PID: 2768)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3456)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3456)
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- setupx.exe (PID: 2768)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3456)
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- setupx.exe (PID: 2768)
Checks supported languages
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- setupx.exe (PID: 2768)
- NeroCheck.exe (PID: 2532)
- NeroStartSmart.exe (PID: 4088)
- nero.exe (PID: 3292)
Reads the computer name
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- NeroStartSmart.exe (PID: 4088)
- setupx.exe (PID: 2768)
- nero.exe (PID: 3292)
Reads Windows owner or organization settings
- setupx.exe (PID: 2768)
Reads the Windows organization settings
- setupx.exe (PID: 2768)
Creates a directory in Program Files
- setupx.exe (PID: 2768)
Changes default file association
- setupx.exe (PID: 2768)
- nero.exe (PID: 3292)
Creates a software uninstall entry
- setupx.exe (PID: 2768)
Reads default file associations for system extensions
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
Creates files in the program directory
- setupx.exe (PID: 2768)
Creates/Modifies COM task schedule object
- setupx.exe (PID: 2768)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2976)
Checks supported languages
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2976)
- pcaui.exe (PID: 2852)
- pcaui.exe (PID: 2608)
- WerFault.exe (PID: 2836)
Reads the computer name
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2976)
- pcaui.exe (PID: 2852)
- pcaui.exe (PID: 2608)
- WerFault.exe (PID: 2836)
Reads settings of System Certificates
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3456)
Checks Windows Trust Settings
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2976)
Changes settings of System certificates
- iexplore.exe (PID: 2976)
Application launched itself
- iexplore.exe (PID: 2976)
Reads internet explorer settings
- iexplore.exe (PID: 3456)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2976)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2976)
Dropped object may contain Bitcoin addresses
- 6.6.1.15_Nero-6.6.1.15_no_at.exe (PID: 3776)
- setupx.exe (PID: 2768)
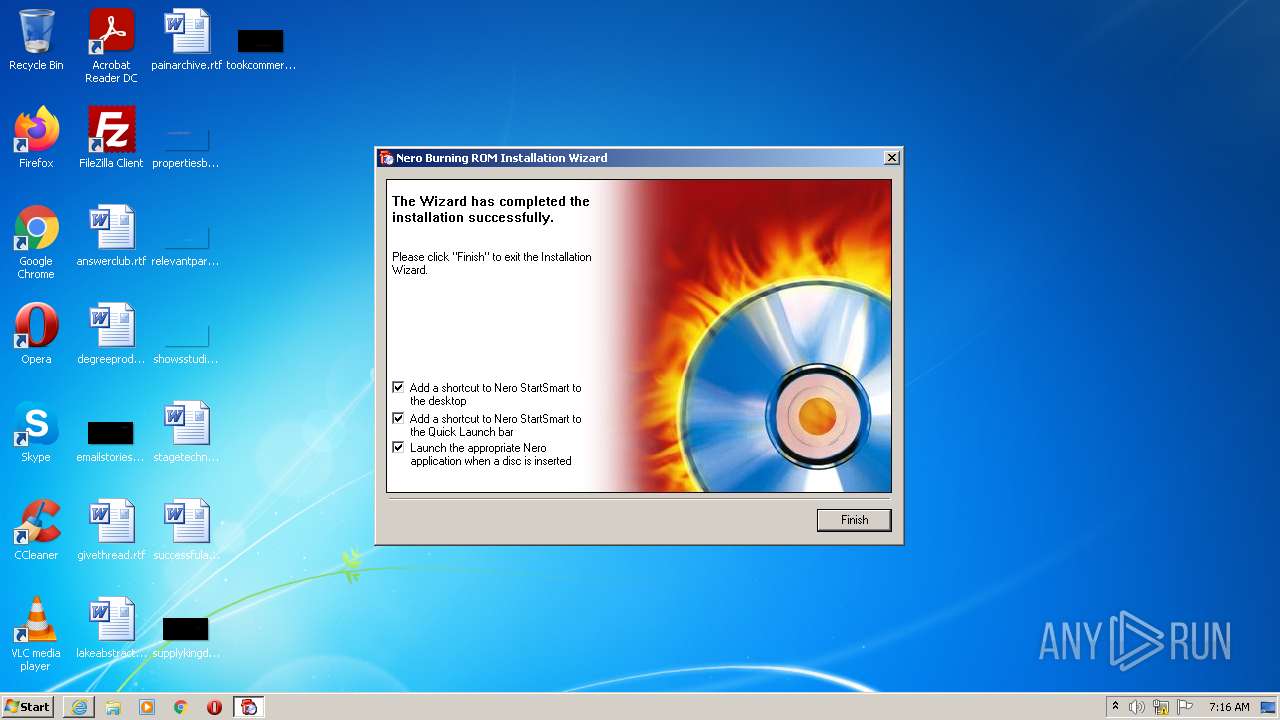
Manual execution by user
- NeroStartSmart.exe (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
12
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
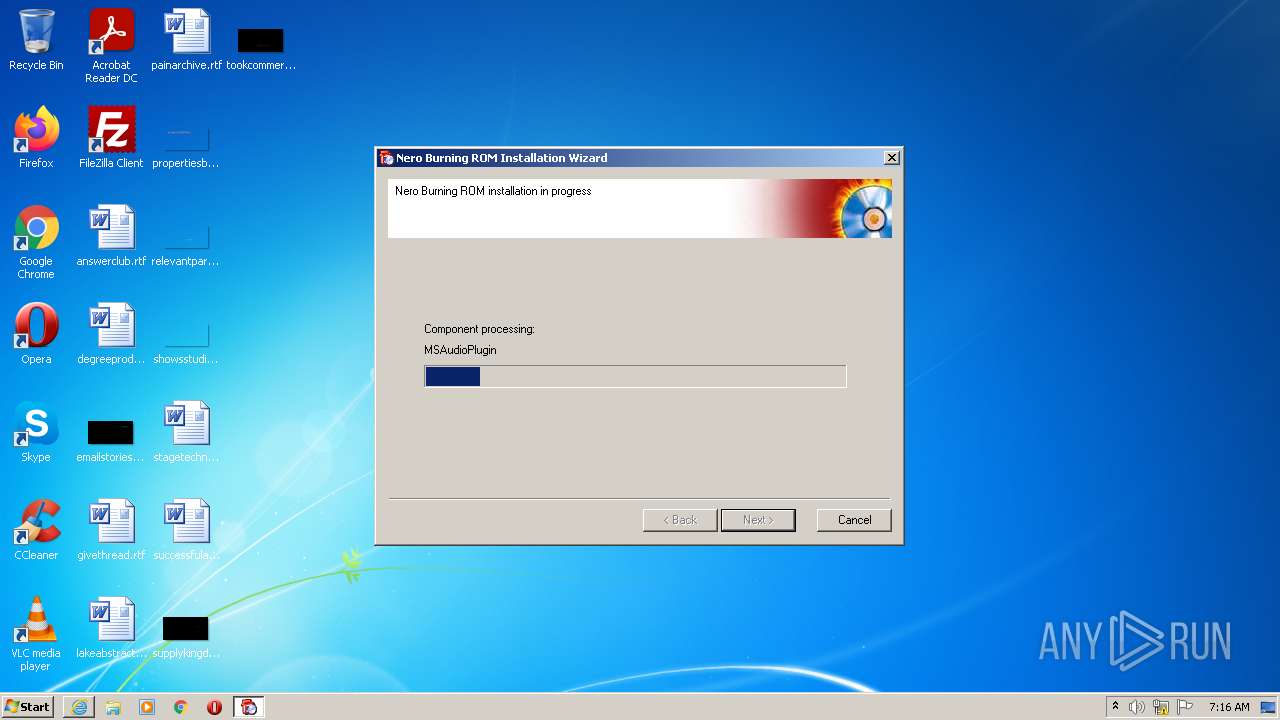
| 2532 | "C:\Windows\System32\NeroCheck.exe" silent | C:\Windows\System32\NeroCheck.exe | — | setupx.exe | |||||||||||
User: admin Company: Nero AG Integrity Level: HIGH Description: NeroCheck Exit code: 8 Version: 1, 0, 0, 5 Modules
| |||||||||||||||
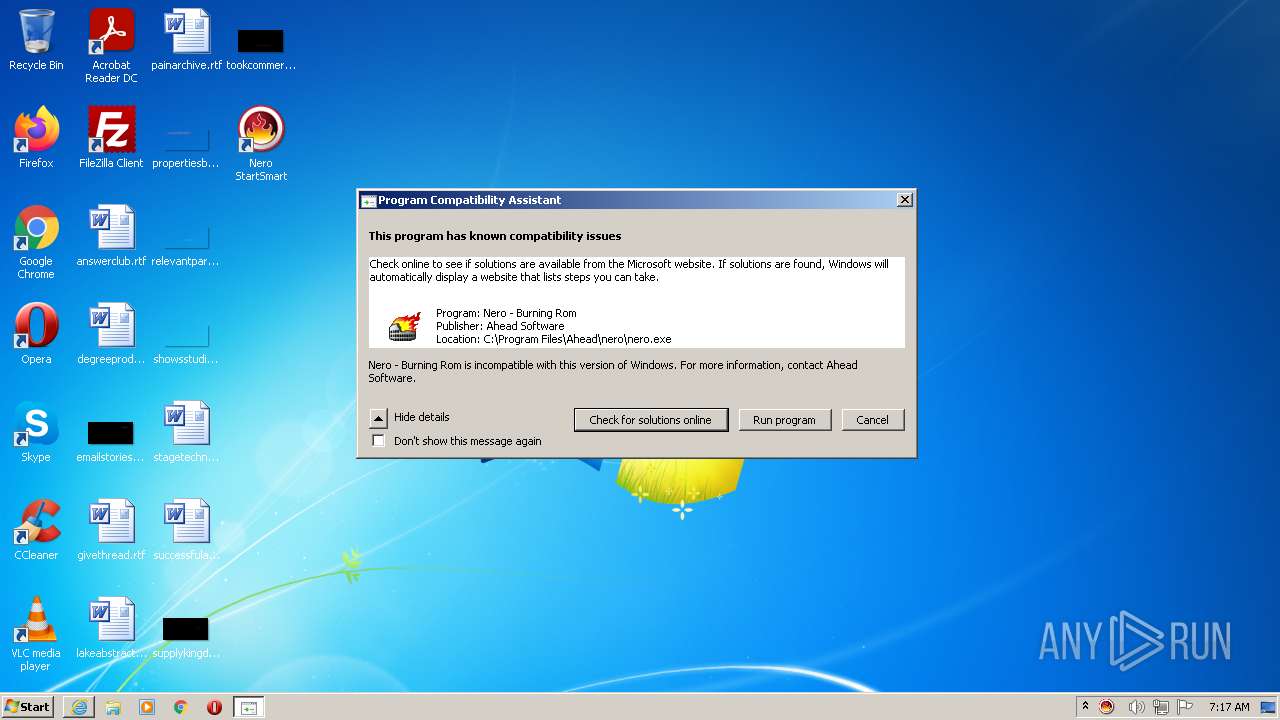
| 2608 | "C:\Windows\System32\pcaui.exe" /g {11111111-1111-1111-1111-111111111111} /x {7ca8005c-9c4c-40c5-8664-9ba090a04e7a} /a "Nero - Burning Rom" /v "Ahead Software" /s "Nero - Burning Rom is incompatible with this version of Windows. For more information, contact Ahead Software." /b 1 /e "C:\Program Files\Ahead\nero\nero.exe" | C:\Windows\System32\pcaui.exe | — | nero.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Assistant User Interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
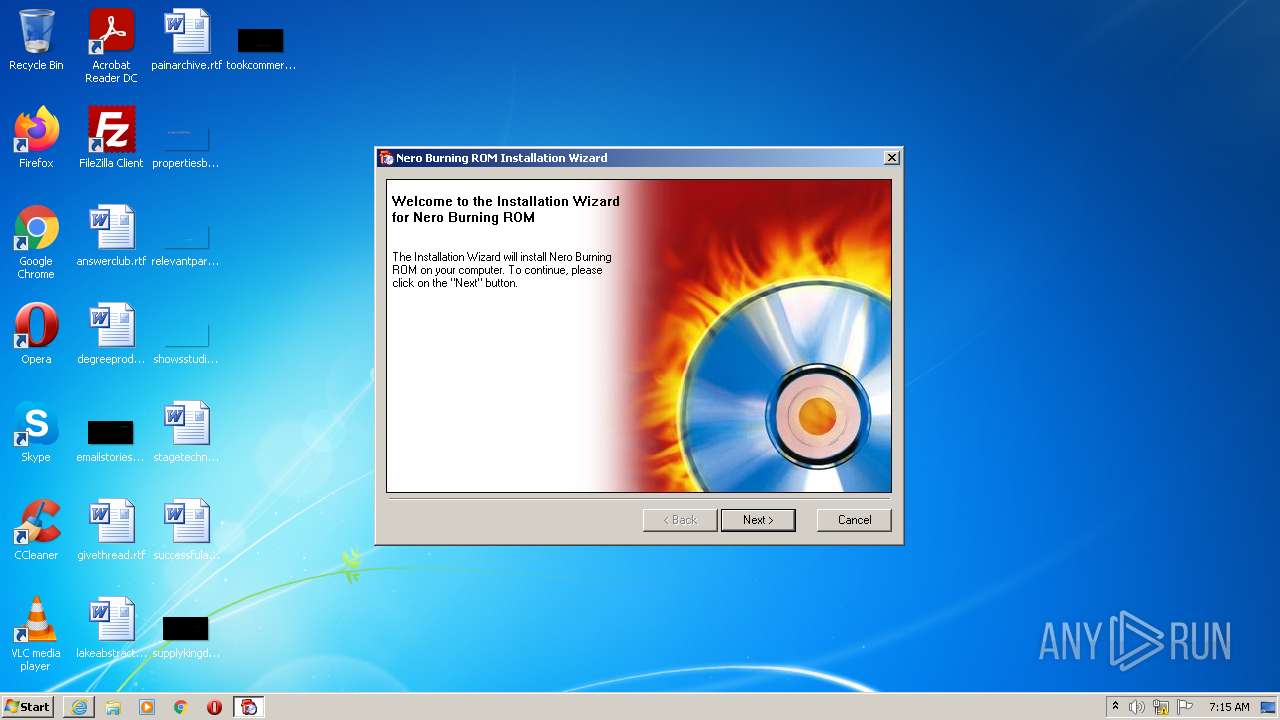
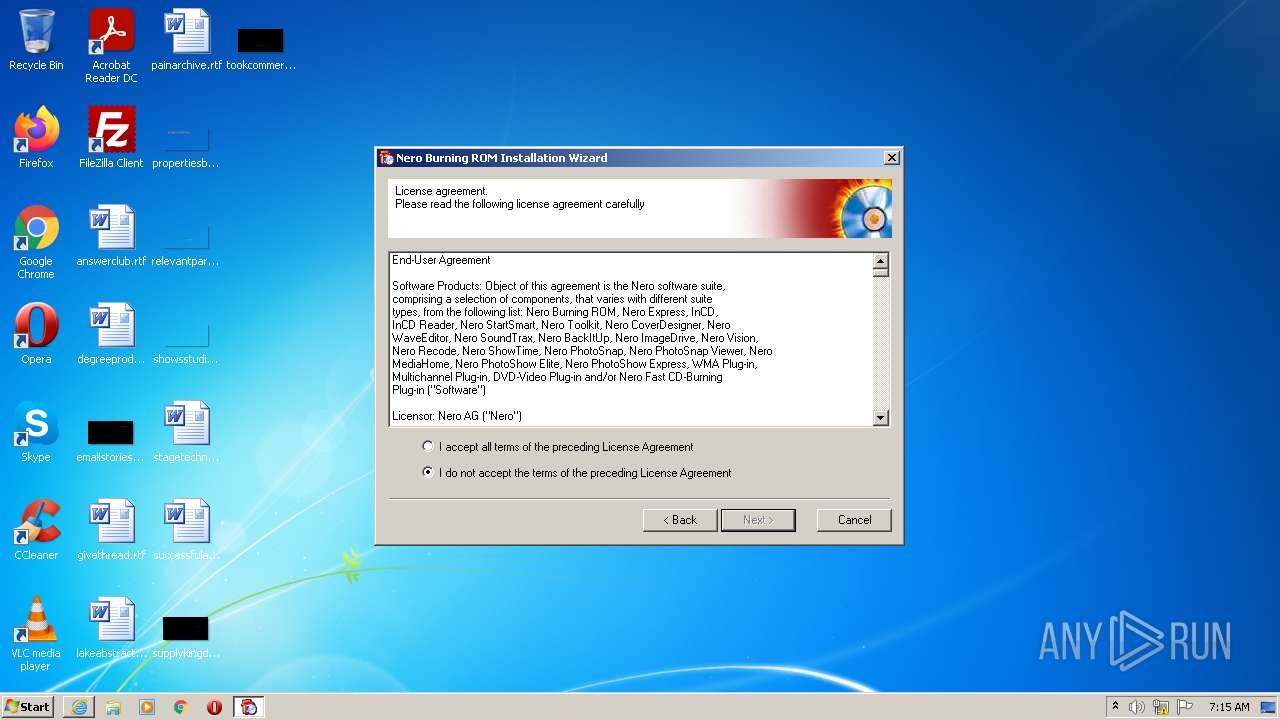
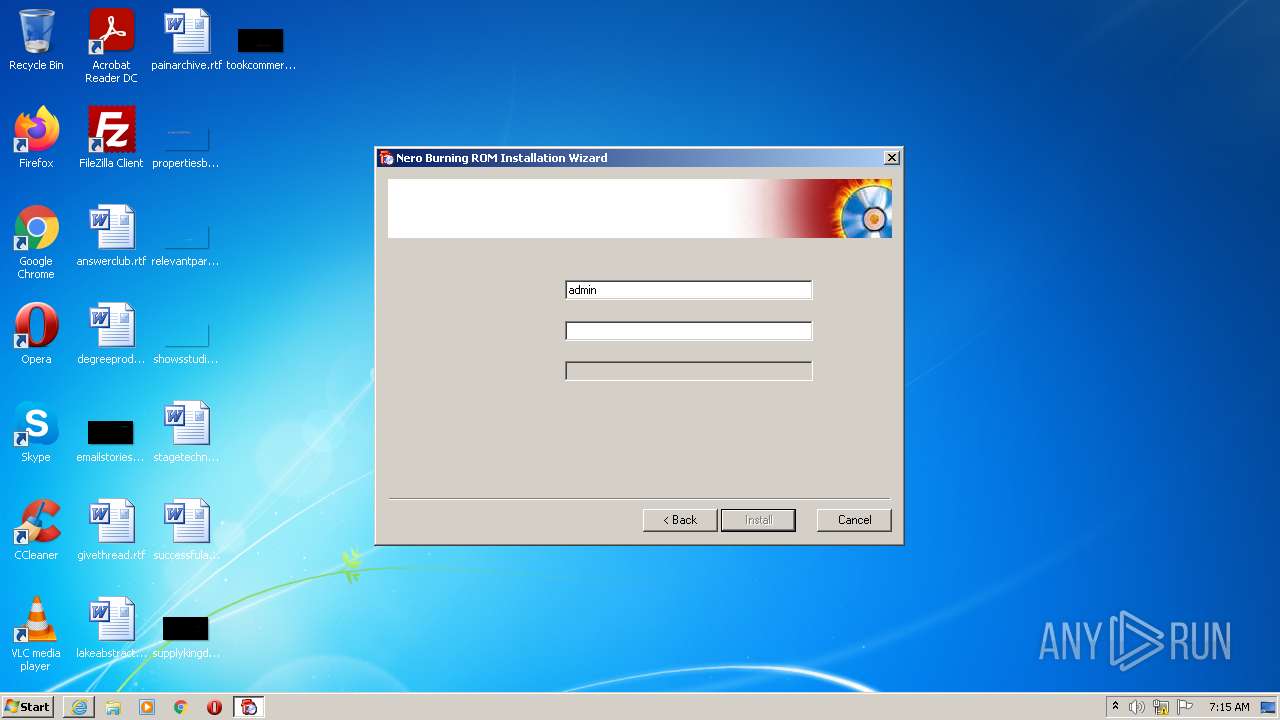
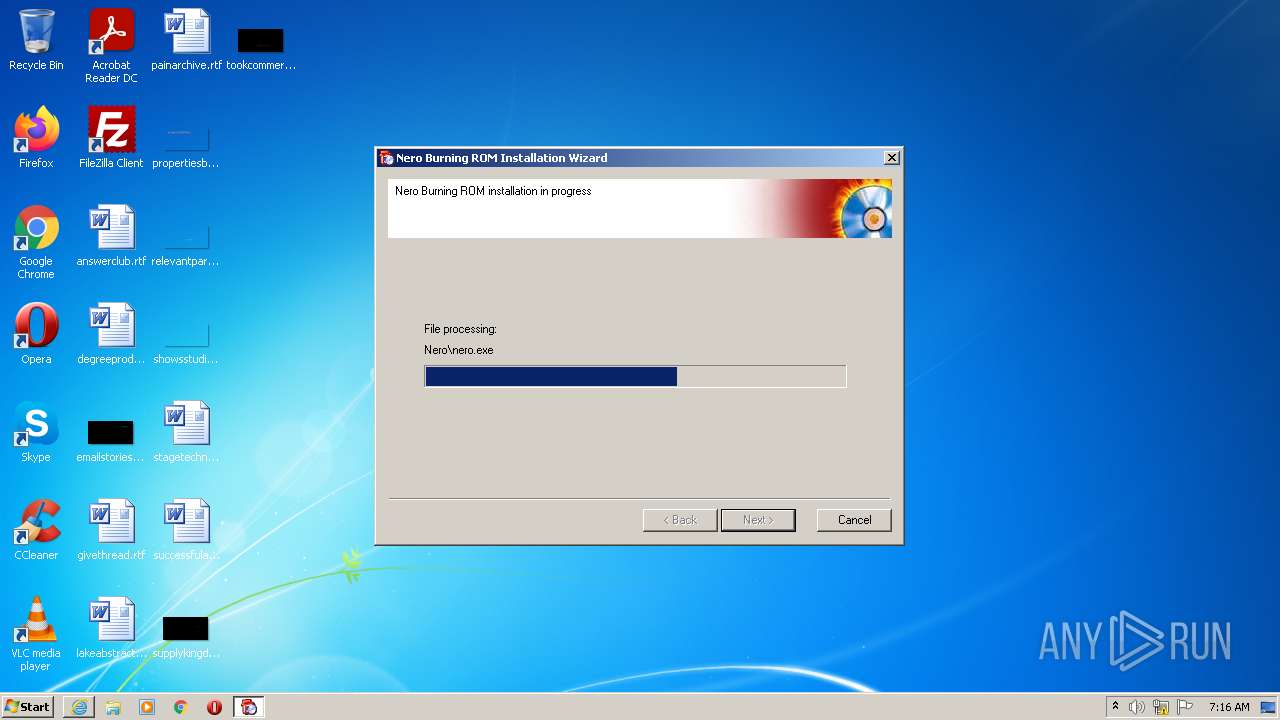
| 2768 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\setupx.exe" /SFX | C:\Users\admin\AppData\Local\Temp\RarSFX0\setupx.exe | 6.6.1.15_Nero-6.6.1.15_no_at.exe | ||||||||||||
User: admin Company: Nero AG Integrity Level: HIGH Description: Nero WebEngine Exit code: 0 Version: 1, 2, 3, 159 Modules
| |||||||||||||||
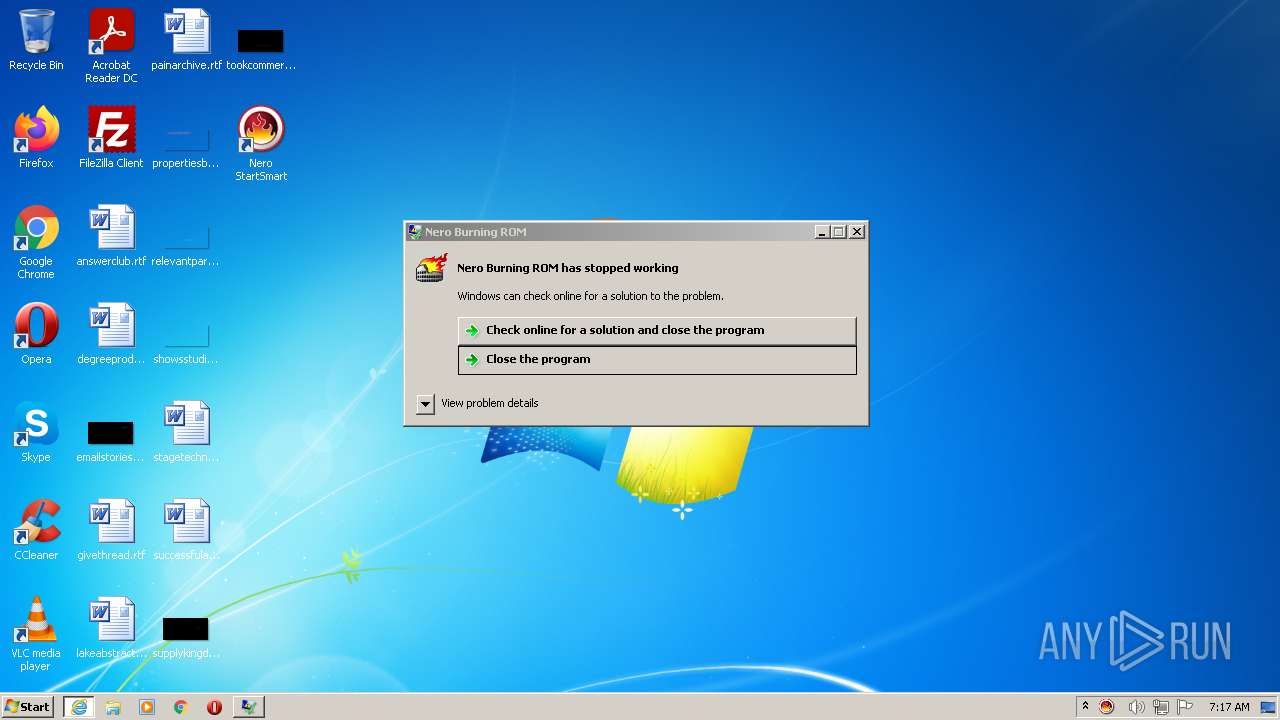
| 2836 | C:\Windows\system32\WerFault.exe -u -p 3292 -s 792 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Windows\System32\pcaui.exe" /g {11111111-1111-1111-1111-111111111111} /x {a83b9c31-a5ef-445a-9b4d-d5e930896194} /a "Nero - Burning Rom" /v "Ahead Software" /s "Nero - Burning Rom is incompatible with this version of Windows. For more information, contact Ahead Software." /b 1 /e "C:\Users\admin\AppData\Local\Temp\RarSFX0\setupx.exe" | C:\Windows\System32\pcaui.exe | — | setupx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Program Compatibility Assistant User Interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://anonfiles.com/Ycf7Eb17y6/6.6.1.15_Nero-6.6.1.15_no_at_exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\6.6.1.15_Nero-6.6.1.15_no_at.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\6.6.1.15_Nero-6.6.1.15_no_at.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Ahead\nero\nero.exe" /w /New:VCD /Media:CD | C:\Program Files\Ahead\nero\nero.exe | NeroStartSmart.exe | ||||||||||||
User: admin Company: Ahead Software AG Integrity Level: MEDIUM Description: Nero Burning ROM Exit code: 3221225477 Version: 6, 6, 1, 15 Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2976 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
41 948
Read events
28 241
Write events
13 418
Delete events
289
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30975341 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 94576018 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30975342 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
310
Suspicious files
103
Text files
95
Unknown types
94
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar27DE.tmp | cat | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab27DF.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar27E0.tmp | cat | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ABE5BEA86CDF3A91EBC3F9F946566003 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
43
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3456 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?60d470456cf65530 | US | compressed | 60.2 Kb | whitelisted |
3456 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3456 | iexplore.exe | GET | 200 | 99.86.1.61:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3456 | iexplore.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMKkbL8LAFVsPfjhHUkFjxBXA%3D%3D | US | der | 503 b | shared |
3456 | iexplore.exe | GET | 200 | 143.204.214.40:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3456 | iexplore.exe | GET | 200 | 99.86.1.61:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3456 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6e9c1355609bf9ed | US | compressed | 60.2 Kb | whitelisted |
3456 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3456 | iexplore.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3456 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
3456 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3456 | iexplore.exe | 184.24.77.54:80 | r3.o.lencr.org | Time Warner Cable Internet LLC | US | suspicious |
3456 | iexplore.exe | 99.86.1.61:80 | ocsp.rootg2.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
2976 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
3456 | iexplore.exe | 99.86.1.182:443 | djv99sxoqpv11.cloudfront.net | AT&T Services, Inc. | US | unknown |
3456 | iexplore.exe | 143.204.214.40:80 | o.ss2.us | — | US | unknown |
3456 | iexplore.exe | 195.96.151.71:443 | cdn-119.anonfiles.com | Archway S.r.l | IQ | suspicious |
2976 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
ocsp2.globalsign.com |
| whitelisted |