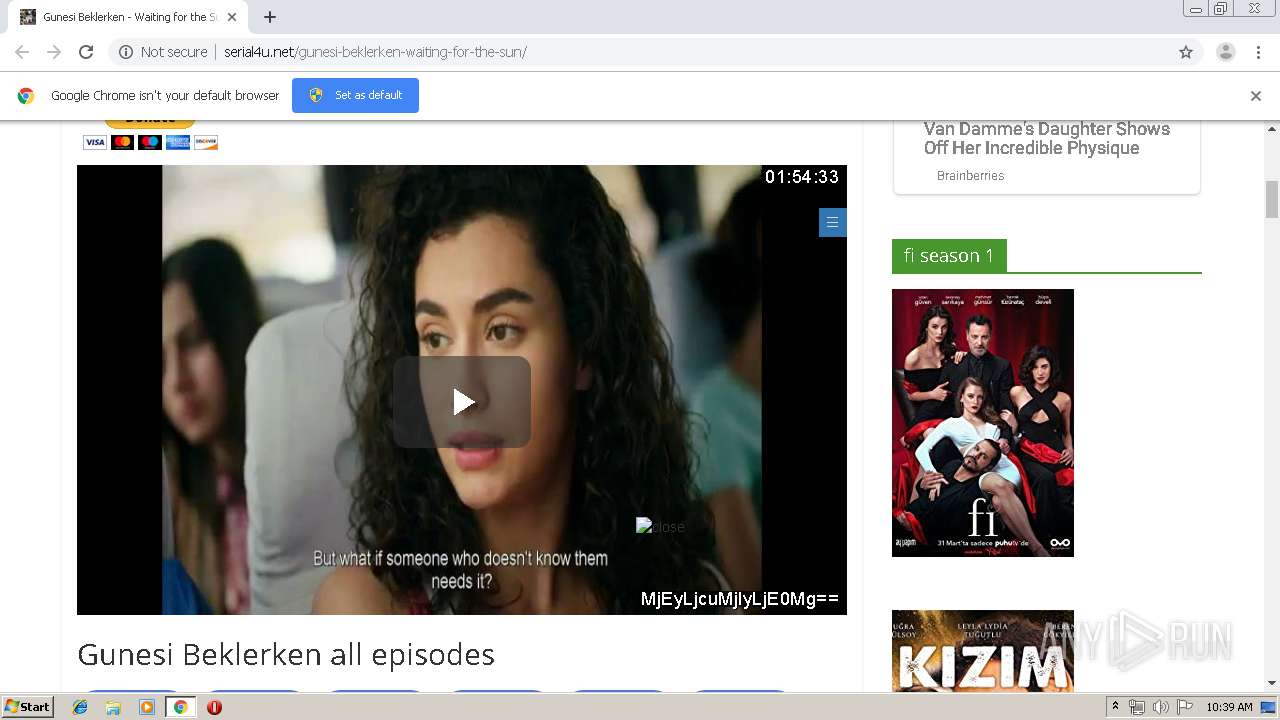
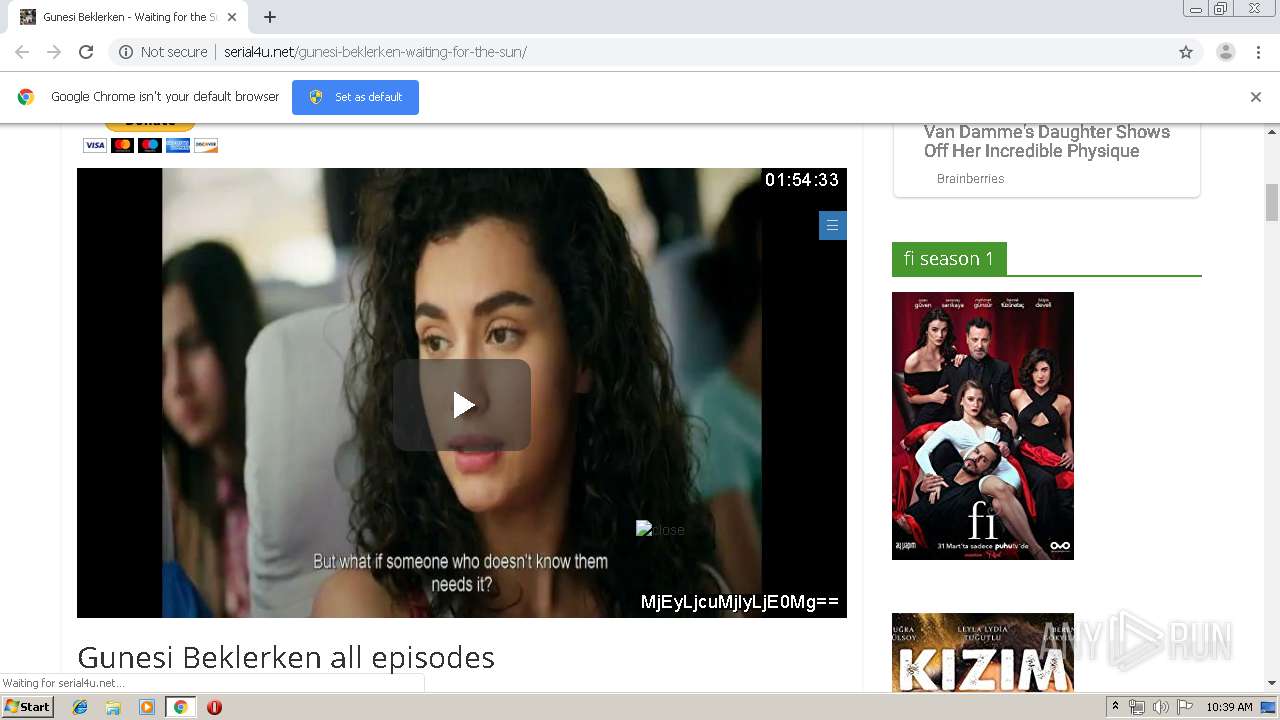
| URL: | http://serial4u.net/gunesi-beklerken-waiting-for-the-sun/ |
| Full analysis: | https://app.any.run/tasks/aef76264-ea45-4f77-bebe-5a8425e08c77 |
| Verdict: | No threats detected |
| Analysis date: | September 04, 2019, 09:38:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2555CDC94A60A44EF29D89837C2A028 |
| SHA1: | 2978E589C465D309AE64D7DCCC830E3271238F82 |
| SHA256: | 5A6E8F68334C1F64DD568E12CCDCB3E7D2EC56F2D82C24E2A5F4BBD7EDFAFA02 |
| SSDEEP: | 3:N1KNAX9QsKCQLA8gOJI9RkKXIUp:CSRZeqToKxp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3588)
Connects to server without host name
- chrome.exe (PID: 2920)
INFO
Reads the hosts file
- chrome.exe (PID: 3588)
- chrome.exe (PID: 2920)
Application launched itself
- chrome.exe (PID: 3588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9176592668264973068 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7020841826625993043 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5049391834950727847 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13112656158481081610 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7730817065983702695 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1755336051117465833 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4521986116316706280 --mojo-platform-channel-handle=2284 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=853437483955874576 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,5120036345417503058,4639523304978371558,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13079485990804027945 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
704
Read events
616
Write events
84
Delete events
4
Modification events
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3588-13212063540240875 |
Value: 259 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
243
Text files
238
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c07debd-0c1f-444a-b4d9-085431c31731.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169b5a.TMP | text | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169b5a.TMP | text | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169b5a.TMP | text | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169b99.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
207
DNS requests
107
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-content/themes/colormag/fontawesome/css/font-awesome.css?ver=4.2.1 | US | html | 274 b | suspicious |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-content/plugins/themify-builder/themify/js/main.js?ver=4.6.0 | US | html | 268 b | suspicious |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-includes/js/jquery/jquery.js?ver=1.12.4-wp | US | html | 250 b | suspicious |
2920 | chrome.exe | GET | 200 | 162.241.148.111:80 | http://serial4u.net/gunesi-beklerken-waiting-for-the-sun/ | US | html | 26.4 Kb | suspicious |
2920 | chrome.exe | GET | 200 | 172.217.23.170:80 | http://fonts.googleapis.com/css?family=Open+Sans%3A400%2C600&ver=5.2.2 | US | text | 626 b | whitelisted |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-content/themes/colormag/style.css?ver=5.2.2 | US | html | 251 b | suspicious |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-content/plugins/themify-builder/css/themify-builder-style.css?ver=4.6.0 | US | html | 279 b | suspicious |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-includes/css/dist/block-library/style.min.css?ver=5.2.2 | US | html | 263 b | suspicious |
2920 | chrome.exe | GET | 302 | 162.241.148.111:80 | http://serial4u.net/wp-includes/js/comment-reply.min.js?ver=5.2.2 | US | html | 250 b | suspicious |
2920 | chrome.exe | GET | 200 | 192.0.73.2:80 | http://2.gravatar.com/avatar/e97729bc0ad395fec91203eb4249a6e7?s=74&d=mm&r=g | US | image | 1.34 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 162.241.148.111:80 | serial4u.net | CyrusOne LLC | US | suspicious |
2920 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 172.217.23.170:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 162.241.148.111:443 | serial4u.net | CyrusOne LLC | US | suspicious |
2920 | chrome.exe | 185.59.220.29:80 | c1.popads.net | Datacamp Limited | DE | malicious |
2920 | chrome.exe | 172.217.21.195:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 192.0.73.2:80 | 2.gravatar.com | Automattic, Inc | US | whitelisted |
2920 | chrome.exe | 23.210.248.226:443 | www.paypalobjects.com | Akamai International B.V. | NL | whitelisted |
2920 | chrome.exe | 104.23.131.67:443 | hqq.tv | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
serial4u.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
c1.popads.net |
| whitelisted |
s.w.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
www.paypal.com |
| whitelisted |
2.gravatar.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | chrome.exe | Potential Corporate Privacy Violation | ET INFO Suspicious Darkwave Popads Pop Under Redirect |
2920 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2920 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2920 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2920 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |