| File name: | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446 |
| Full analysis: | https://app.any.run/tasks/18951250-81cc-4721-9c1d-a8729d5d7da6 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2024, 08:04:31 |
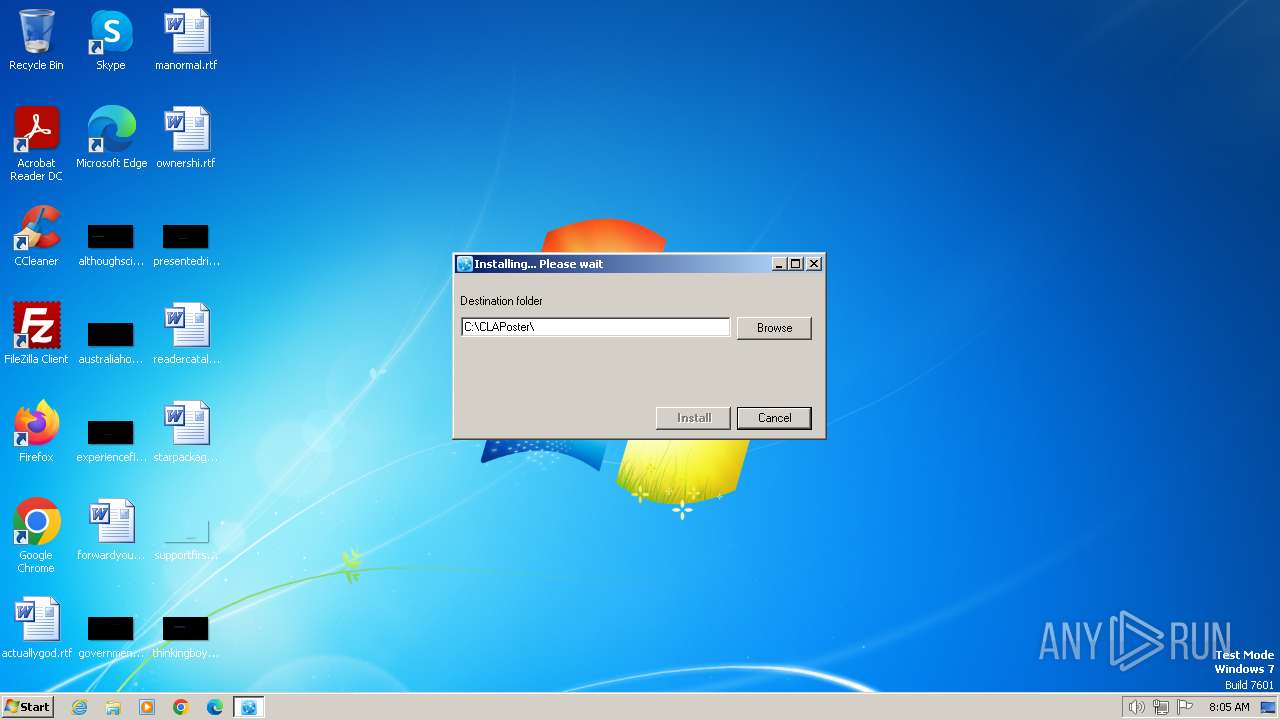
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CCB1F04ACD8F3D2D2DE08DFD82E580DA |
| SHA1: | 08A35E1D86A4D436ECDD50E05DC69E163D46BF33 |
| SHA256: | 5A4DD4AF392F4E13095FC4ED3624761AAAFE8FDEFF36B14C5A764393EA58E446 |
| SSDEEP: | 49152:BGqyZa0uxja2MZRTnIIHFHHHHFHFFHHFFHFFFHHFHFFHHHFHIHFHHHHFFGFGGaaB:BGqyZa0uJwfd7yO |
MALICIOUS
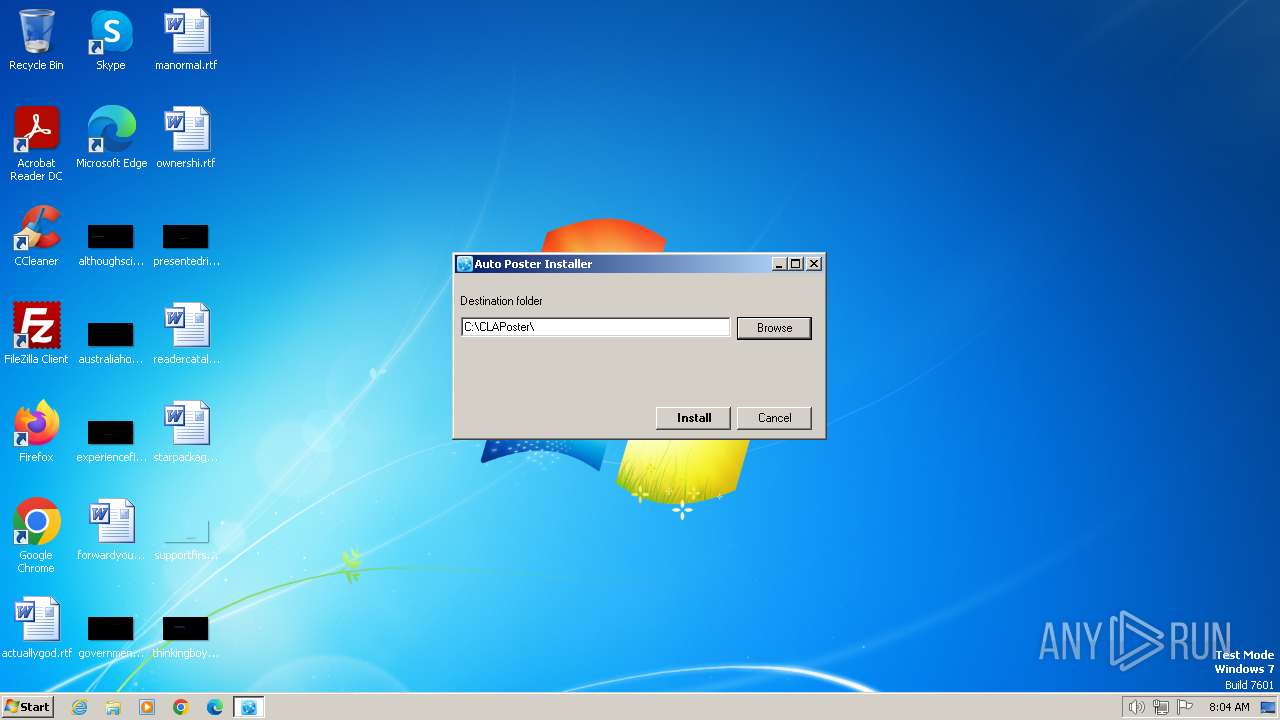
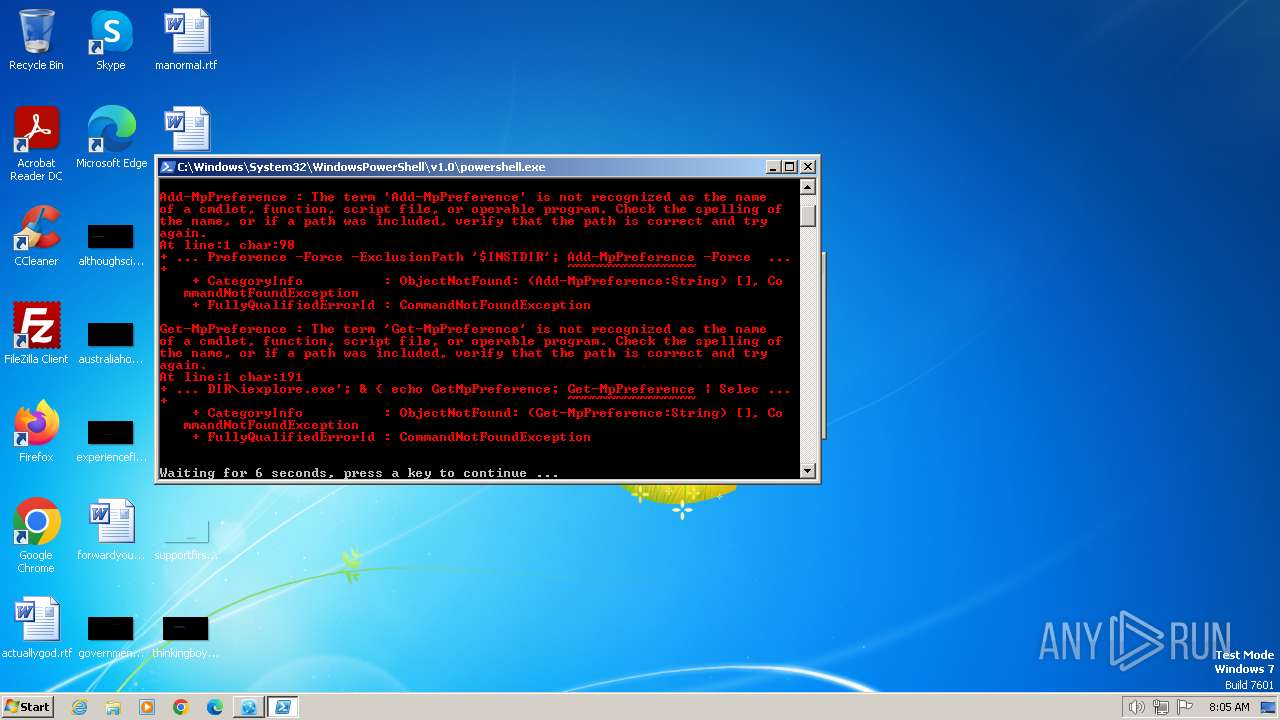
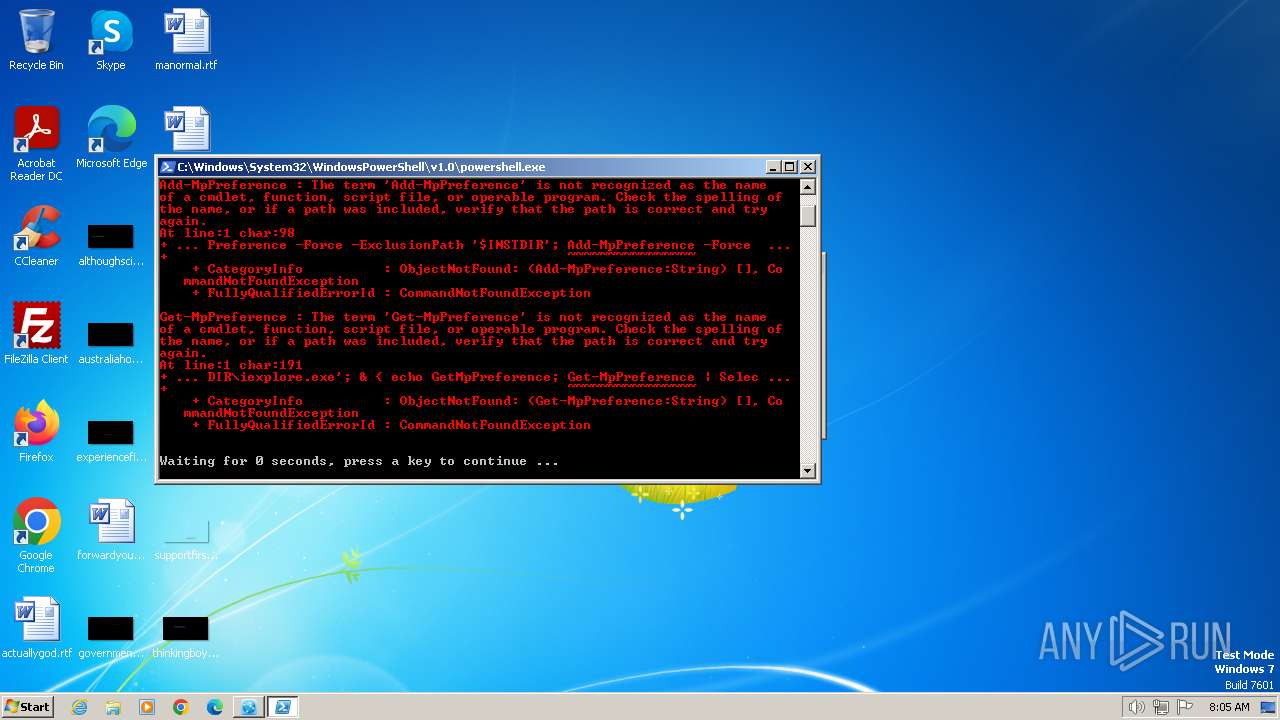
Adds process to the Windows Defender exclusion list
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
SUSPICIOUS
Reads settings of System Certificates
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Reads the Internet Settings
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- powershell.exe (PID: 1344)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1808)
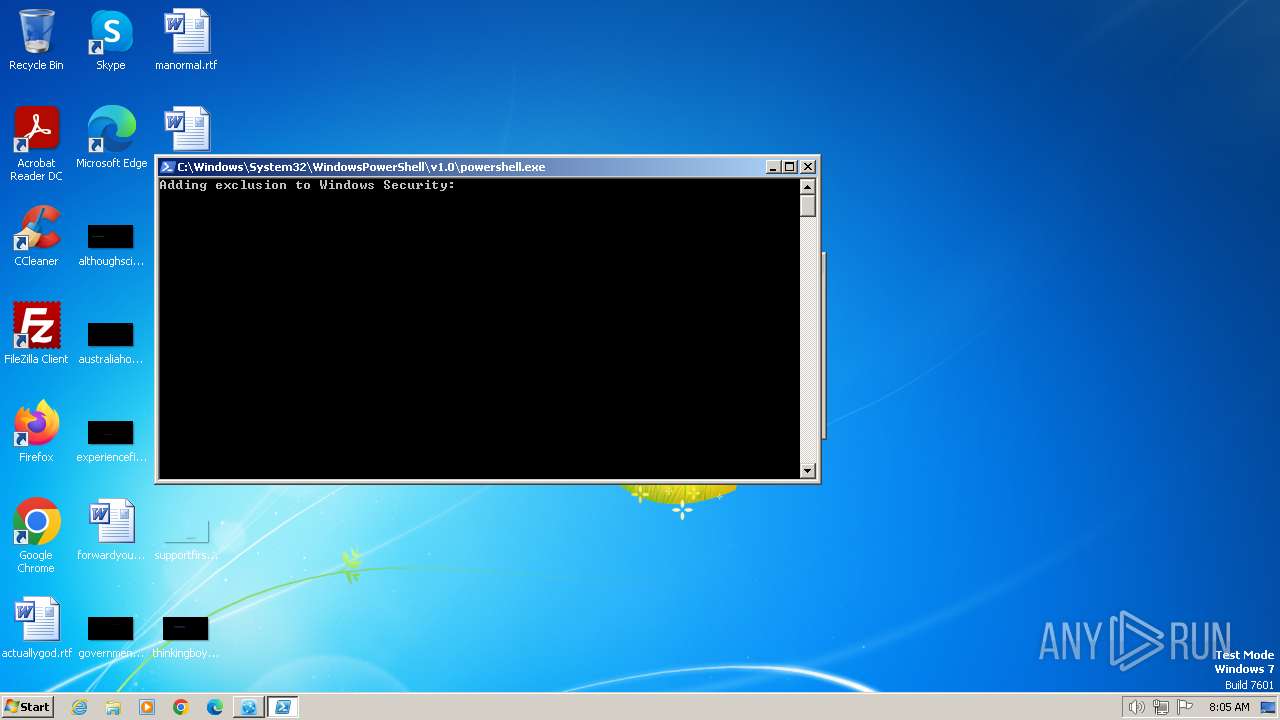
Script adds exclusion path to Windows Defender
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Script adds exclusion process to Windows Defender
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Query Microsoft Defender preferences
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Starts POWERSHELL.EXE for commands execution
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Uses TIMEOUT.EXE to delay execution
- powershell.exe (PID: 1344)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1344)
The process creates files with name similar to system file names
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Reads security settings of Internet Explorer
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1808)
Checks Windows Trust Settings
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Reads Internet Explorer settings
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
INFO
Reads the machine GUID from the registry
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1808)
Drops the executable file immediately after the start
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
Reads the computer name
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Checks supported languages
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Reads Environment values
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Create files in a temporary directory
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Process drops legitimate windows executable
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Starts itself from another location
- 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe (PID: 2120)
Process checks are UAC notifies on
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Process requests binary or script from the Internet
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1808)
Process checks Internet Explorer phishing filters
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Checks proxy server information
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Creates files or folders in the user directory
- iexplore.exe (PID: 1808)
- iexplore.exe (PID: 1232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:08 23:18:56+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 2911232 |
| InitializedDataSize: | 37376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2c8a3e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.0.0 |
| ProductVersionNumber: | 3.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
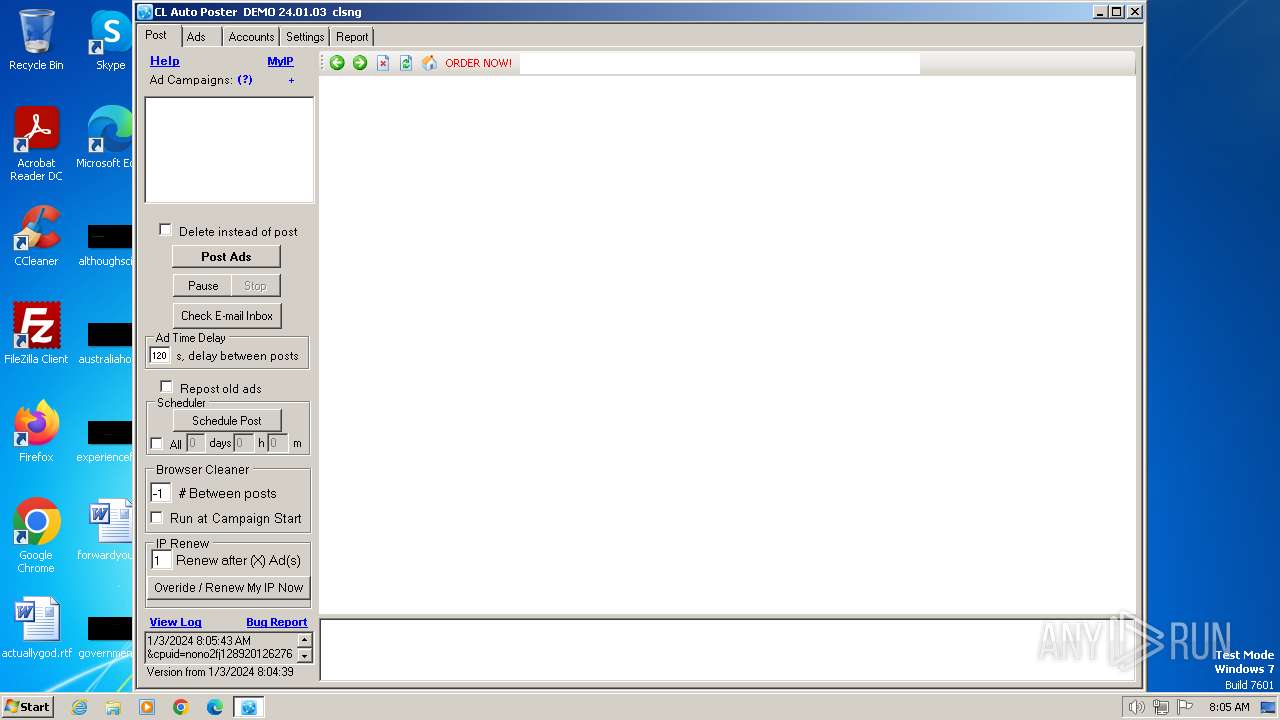
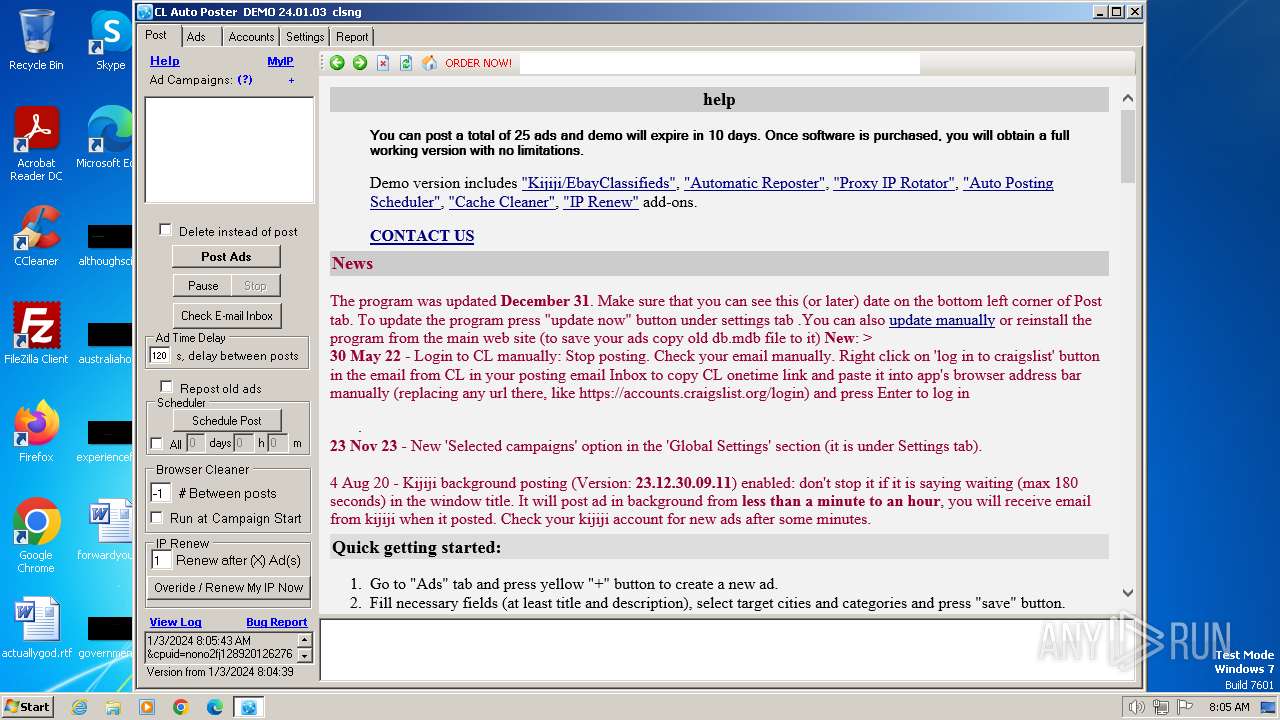
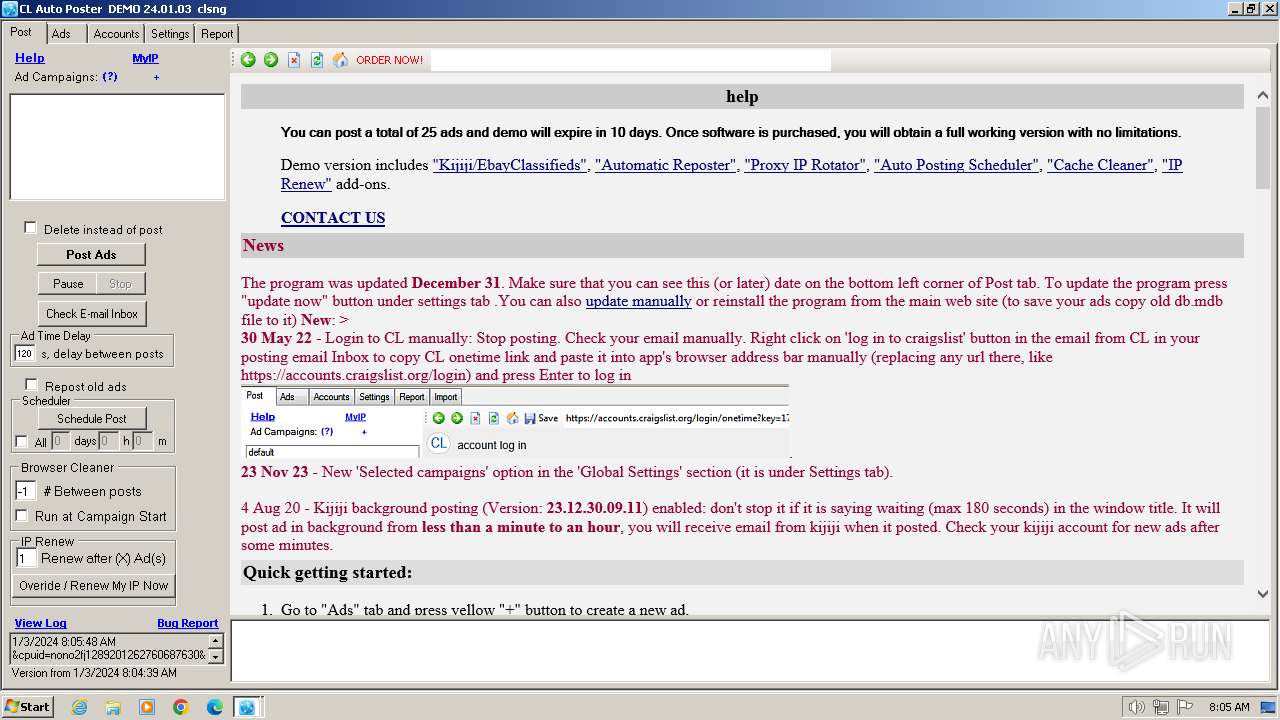
| Comments: | autoposter |
| CompanyName: | multiadposter.com |
| FileDescription: | autoposter |
| FileVersion: | 3.4.0.0 |
| InternalName: | iexplore.exe |
| LegalCopyright: | Copyright (c) 2014 jiposter.com. All Rights Reserved. |
| LegalTrademarks: | autoposter |
| OriginalFileName: | iexplore.exe |
| ProductName: | autoposter |
| ProductVersion: | 3.4.0.0 |
| AssemblyVersion: | 3.4.0.0 |
Total processes
45
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "iexplore.exe" | C:\CLAPoster\iexplore.exe | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | ||||||||||||
User: admin Company: multiadposter.com Integrity Level: MEDIUM Description: autoposter Exit code: 0 Version: 3.4.0.0 Modules
| |||||||||||||||
| 1344 | "powershell" echo 'Adding exclusion to Windows Security:'; Add-MpPreference -Force -ExclusionPath '$INSTDIR'; Add-MpPreference -Force -ExclusionProcess '$INSTDIR\iexplore.exe'; & { echo GetMpPreference; Get-MpPreference | Select-Object -Property ExclusionPath -ExpandProperty ExclusionPath; echo GMpPreference; } | Out-File 'C:\CLAPoster\\cap.log' -Append -Encoding UTF8; TIMEOUT /T 6 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1808 | "iexplore.exe" | C:\CLAPoster\iexplore.exe | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | ||||||||||||
User: admin Company: multiadposter.com Integrity Level: MEDIUM Description: autoposter Exit code: 0 Version: 3.4.0.0 Modules
| |||||||||||||||
| 1936 | "C:\Windows\system32\timeout.exe" /T 6 | C:\Windows\System32\timeout.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe" | C:\Users\admin\AppData\Local\Temp\5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | explorer.exe | ||||||||||||
User: admin Company: multiadposter.com Integrity Level: MEDIUM Description: autoposter Exit code: 0 Version: 3.4.0.0 Modules
| |||||||||||||||
Total events
15 235
Read events
15 116
Write events
118
Delete events
1
Modification events
| (PID) Process: | (2120) 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1808) iexplore.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
31
Suspicious files
24
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\freecap\dotNetFx40_Full_setup.exe | executable | |
MD5:53406E9988306CBD4537677C5336ABA4 | SHA256:FA1AFFF978325F8818CE3A559D67A58297D9154674DE7FD8EB03656D93104425 | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\Users\admin\AppData\Local\Temp\autoposter.exe | executable | |
MD5:CCB1F04ACD8F3D2D2DE08DFD82E580DA | SHA256:5A4DD4AF392F4E13095FC4ED3624761AAAFE8FDEFF36B14C5A764393EA58E446 | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\freecap\Aspose.Email.dll | executable | |
MD5:0B02B292D1EEA7B39834594BFBB77EBD | SHA256:8857A028148D164EF68E2F2A2FF1BBF2B044F7F37BE5C8F26E43707F7AD9CDB0 | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\Users\admin\AppData\Local\Temp\Cab5FA0.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\freecap\ActiveUp.Net.Imap4.dll | executable | |
MD5:103316203A13C13597AABB7DB233DA14 | SHA256:34793E6C470DDF79FC0DD8A5E370D861A24DB76E91D3DA2BA104ADD915DAE310 | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\freecap\ActiveUp.Net.Common.dll | executable | |
MD5:48C195C21919D26B0CF94E2BE43636B5 | SHA256:2563D7FFFE4BA84CC1DC82EA10AE87400539085C43EFEDB6D4D4B54E7B73F9DA | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\freecap\freecap.xml | xml | |
MD5:23315C243D84D507F85C46F6A2107F44 | SHA256:B1F5E40978258CEC839F71F1C30823ED0B668DF900AF1C12789E35DA4DA0C214 | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\claposter.exe.zip | compressed | |
MD5:C9CA0FE68B27DCA78C09C30599EA912C | SHA256:9E36D62E680D45FF2768BE2FCD1B3D3E0FE7410C32F0D374EB6EE832969CC3DA | |||
| 1344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\br2z3krk.zq2.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | C:\CLAPoster\cap.log | text | |
MD5:0192127AE1DE7523D41932C7C483FB2B | SHA256:5A40D6AAEF187228435132BB353892614CB26CD97B286359B5E717A0E3A91FCD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4dfdb6056bb35858 | unknown | compressed | 65.2 Kb | unknown |
1808 | iexplore.exe | GET | 200 | 172.67.177.43:80 | http://dl.multiadposter.com/links.php?update=24%2f01%2f03+08%3a04%3a39.385&op=&udir=l.php?to=downloads/&cpuid=nono2fj1289201262760687630&rid=hRaPRssI1000000000&v=24-01-03+08%3a04%3a39.385&z=2950456&av=,&em=&o=Win7%2fWin2008Server+R24.7%3a%3aMicrosoft+Windows+7+Professional++-+32-bit&mv=iexplore.exe&dt=240103.080544.994+00:00&S=3114 | unknown | text | 157 b | unknown |
1808 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?35cafa7425aa5771 | unknown | compressed | 4.66 Kb | unknown |
1808 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1808 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
1808 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3a2f9bc7d46c481c | unknown | compressed | 4.66 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
1232 | iexplore.exe | GET | 200 | 172.67.177.43:80 | http://dl.multiadposter.com/links.php?update=24%2f01%2f03+08%3a04%3a39.385&op=&udir=l.php?to=downloads/&cpuid=nono2fj1289201262760687630&rid=hRaPRssI1000000000&v=24-01-03+08%3a04%3a39.385&z=2950456&av=,&em=&o=Win7%2fWin2008Server+R24.7%3a%3aMicrosoft+Windows+7+Professional++-+32-bit&mv=iexplore.exe&dt=240103.080550.088+00:00&S=3114 | unknown | text | 157 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | 188.114.96.3:443 | claposter.com | CLOUDFLARENET | NL | unknown |
2120 | 5a4dd4af392f4e13095fc4ed3624761aaafe8fdeff36b14c5a764393ea58e446.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1808 | iexplore.exe | 172.67.177.43:443 | multiadposter.com | CLOUDFLARENET | US | unknown |
1808 | iexplore.exe | 172.67.177.43:80 | multiadposter.com | CLOUDFLARENET | US | unknown |
1232 | iexplore.exe | 172.67.177.43:443 | multiadposter.com | CLOUDFLARENET | US | unknown |
1808 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1808 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
claposter.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
multiadposter.com |
| unknown |
dl.multiadposter.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
jiposter.com |
| unknown |
Threats
Process | Message |
|---|---|
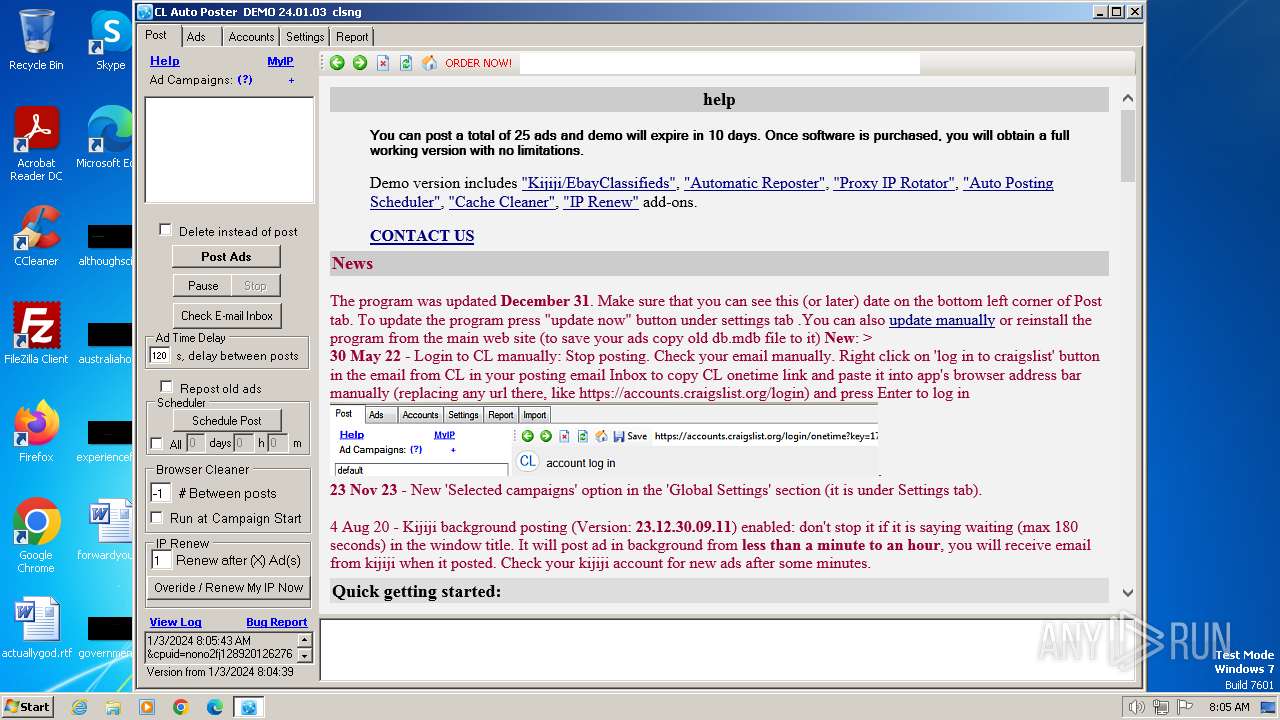
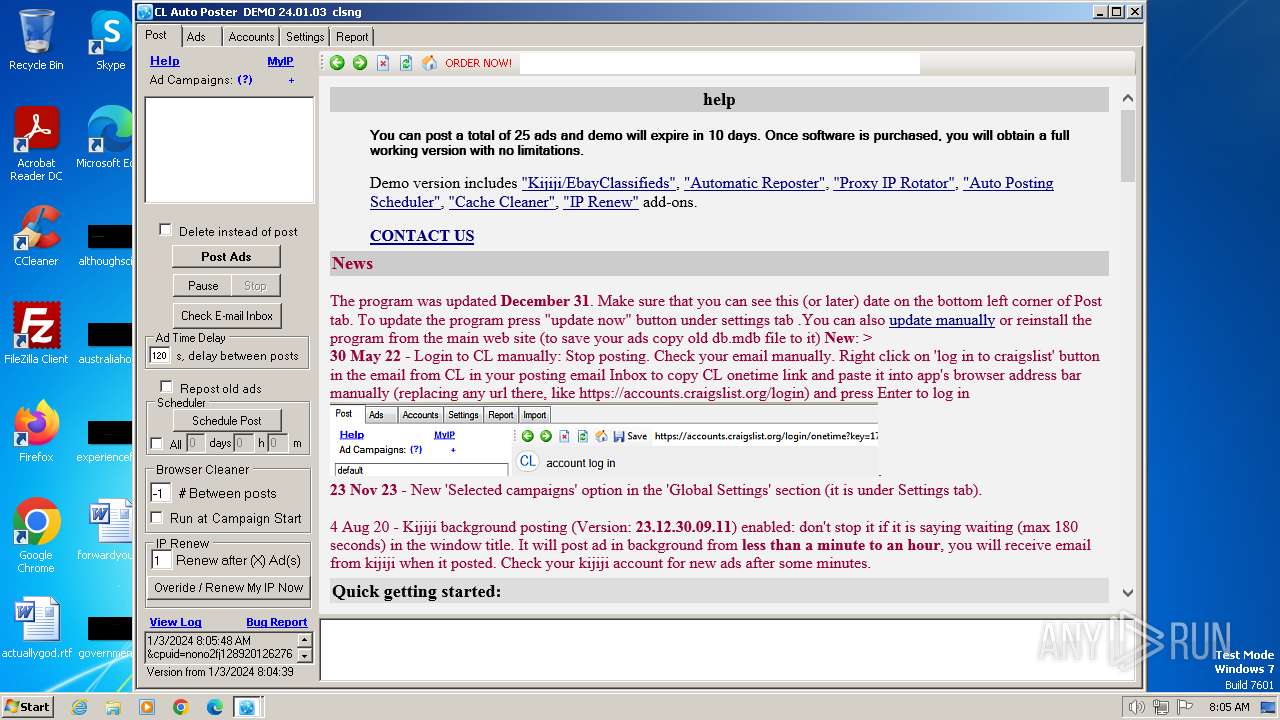
iexplore.exe | Site created
|
iexplore.exe | Get option key path
|
iexplore.exe | LockContainer true
|
iexplore.exe | Document created
|
iexplore.exe | LockContainer
|
iexplore.exe | ActivateMe
|
iexplore.exe | ShowUI
|
iexplore.exe | ShowUI
|
iexplore.exe | Site created
|
iexplore.exe | Get option key path
|