| File name: | CoreRootKit.exe |
| Full analysis: | https://app.any.run/tasks/c807aa4d-a27a-4c4b-ae89-96978f03f662 |
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2025, 17:33:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C063C0E34AFA4AD8F5E61BAAE49C9C5D |
| SHA1: | BC3D68B22F051C6EFE8988A1C18893E97744525A |
| SHA256: | 5A49201C83D9287925AA1D2D541257F2178DE653D5C4C476BC2D8ED09F9D3400 |
| SSDEEP: | 48:YxQQR1L+6FXMZYrDBavHdHZ06XaBMg6sNMGyZDZioOTuolaEYCCbcLAm5m0tdIUT:kZbFuv95va6eu1BgMJjU75azNt |
MALICIOUS
Application was injected by another process
- explorer.exe (PID: 4488)
Runs injected code in another process
- CoreRootKit.exe (PID: 4264)
SUSPICIOUS
Executes application which crashes
- explorer.exe (PID: 4488)
The process creates files with name similar to system file names
- WerFault.exe (PID: 6156)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 7144)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 7144)
- SearchApp.exe (PID: 3524)
INFO
Reads the computer name
- CoreRootKit.exe (PID: 4264)
- TextInputHost.exe (PID: 7100)
- StartMenuExperienceHost.exe (PID: 7144)
- SearchApp.exe (PID: 3524)
Checks supported languages
- CoreRootKit.exe (PID: 4264)
- TextInputHost.exe (PID: 7100)
- StartMenuExperienceHost.exe (PID: 7144)
- SearchApp.exe (PID: 3524)
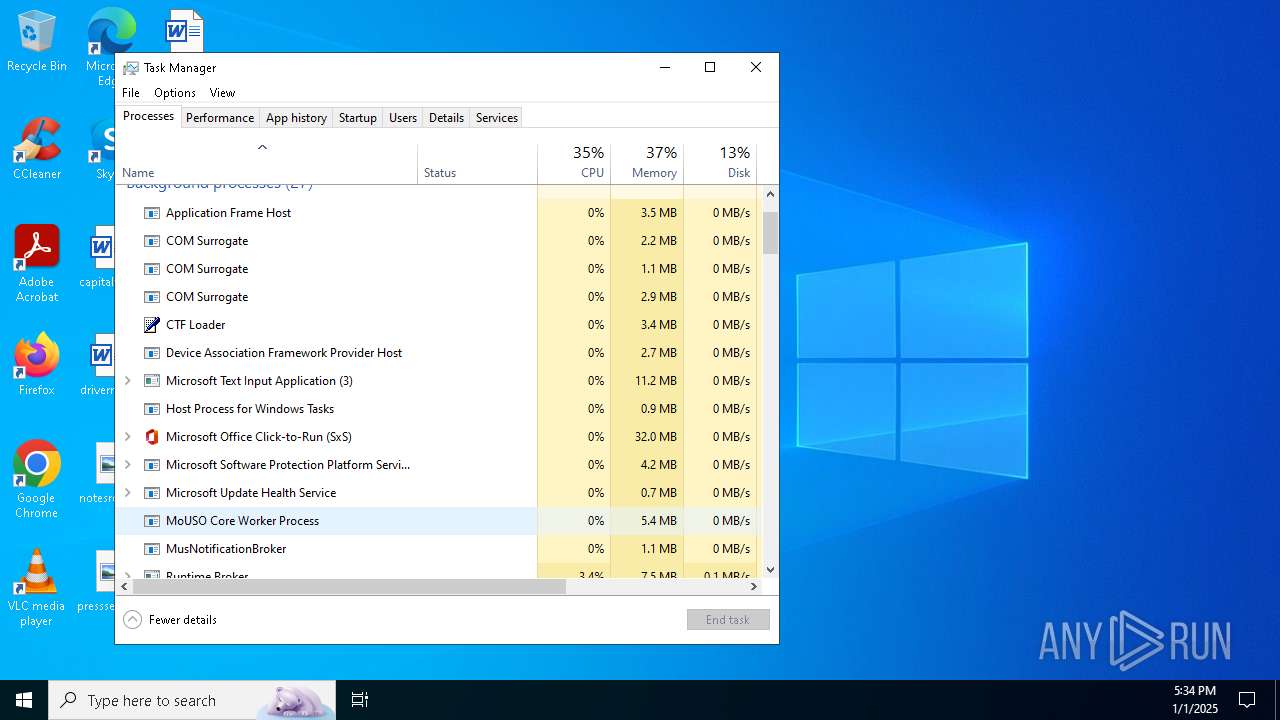
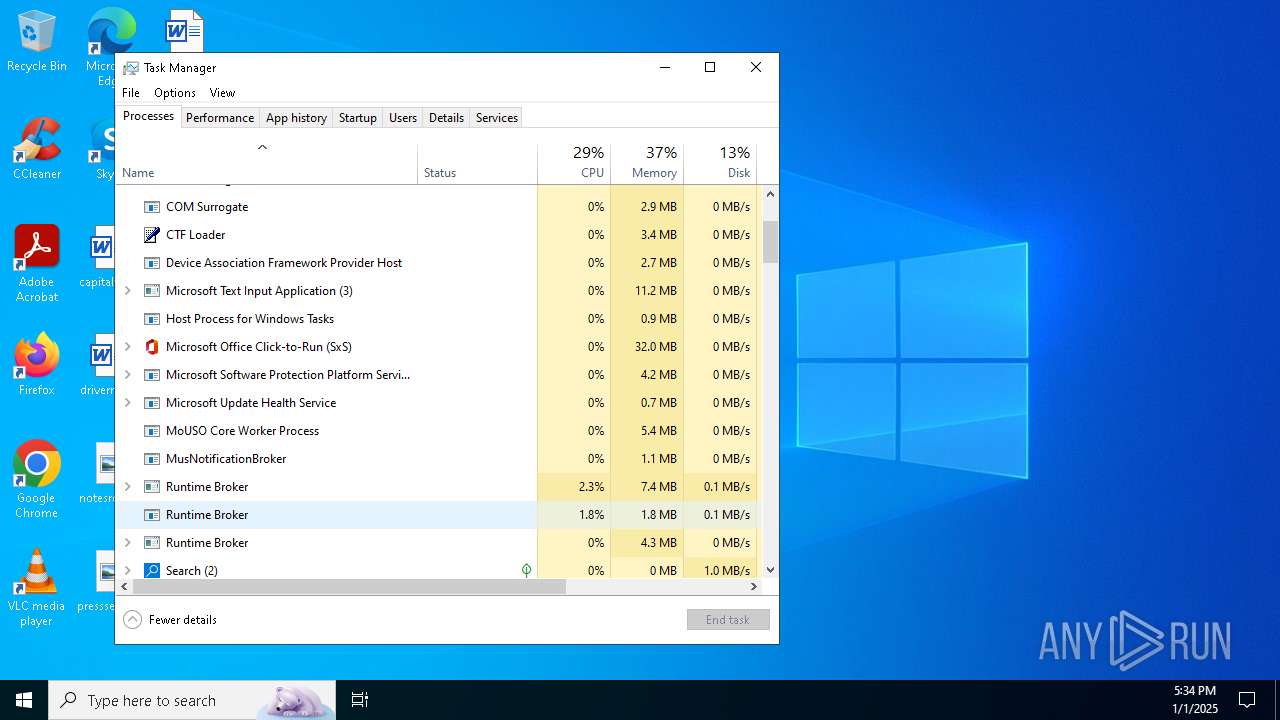
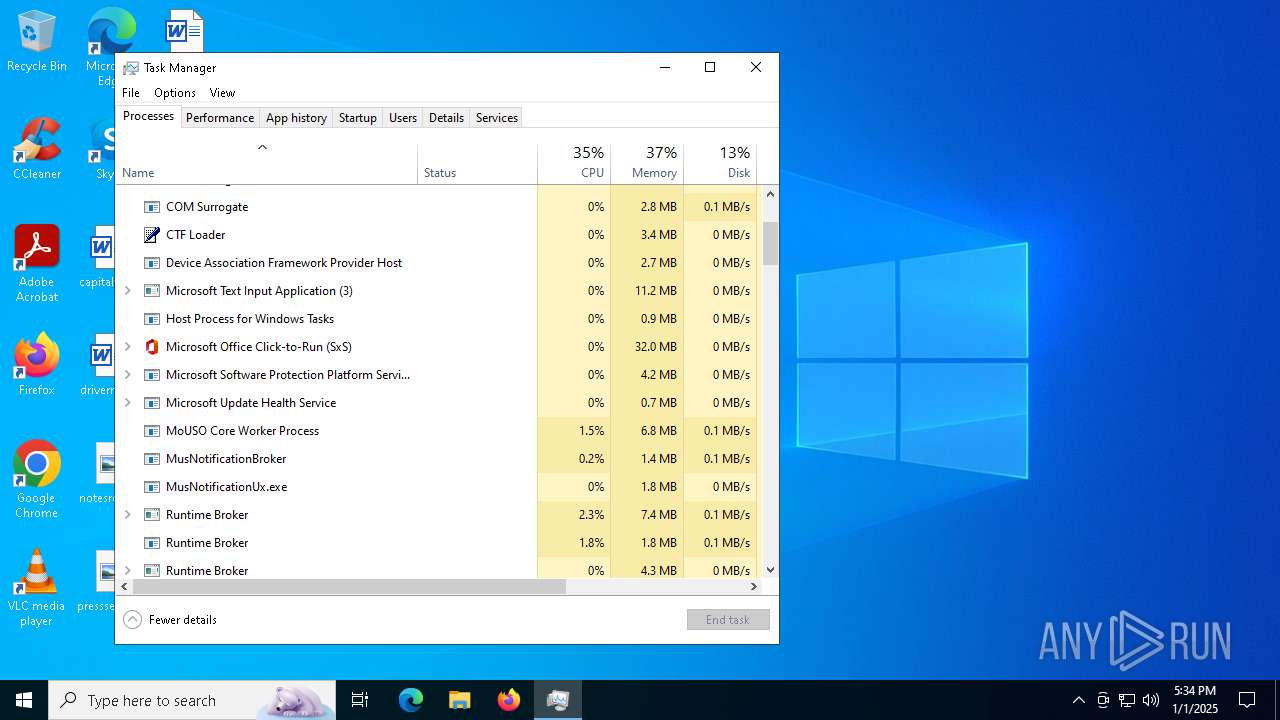
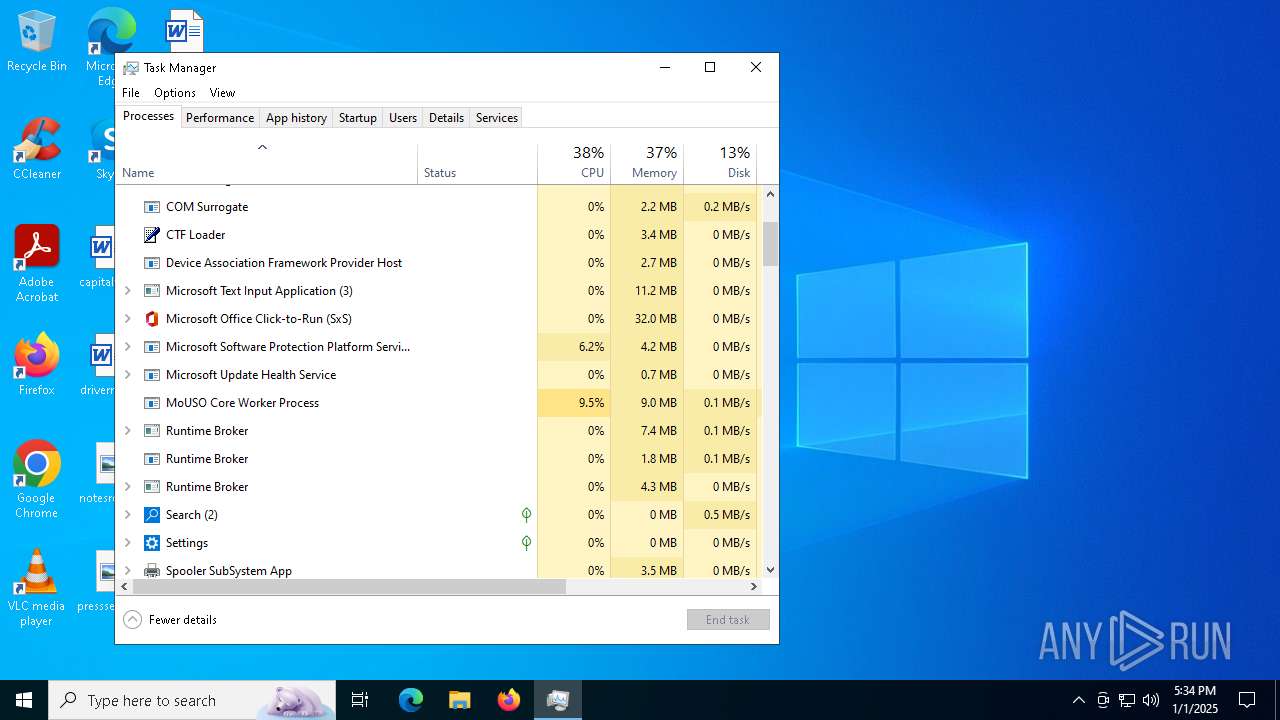
Manual execution by a user
- WerFault.exe (PID: 6156)
- Taskmgr.exe (PID: 3176)
- Taskmgr.exe (PID: 6688)
Creates files or folders in the user directory
- WerFault.exe (PID: 6156)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 7144)
- SearchApp.exe (PID: 3524)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 7144)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 3524)
Checks proxy server information
- SearchApp.exe (PID: 3524)
Reads the software policy settings
- SearchApp.exe (PID: 3524)
Reads Environment values
- SearchApp.exe (PID: 3524)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2077:08:21 02:50:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 3072 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2b56 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CoreRootKit |
| FileVersion: | 1.0.0.0 |
| InternalName: | CoreRootKit.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | CoreRootKit.exe |
| ProductName: | CoreRootKit |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
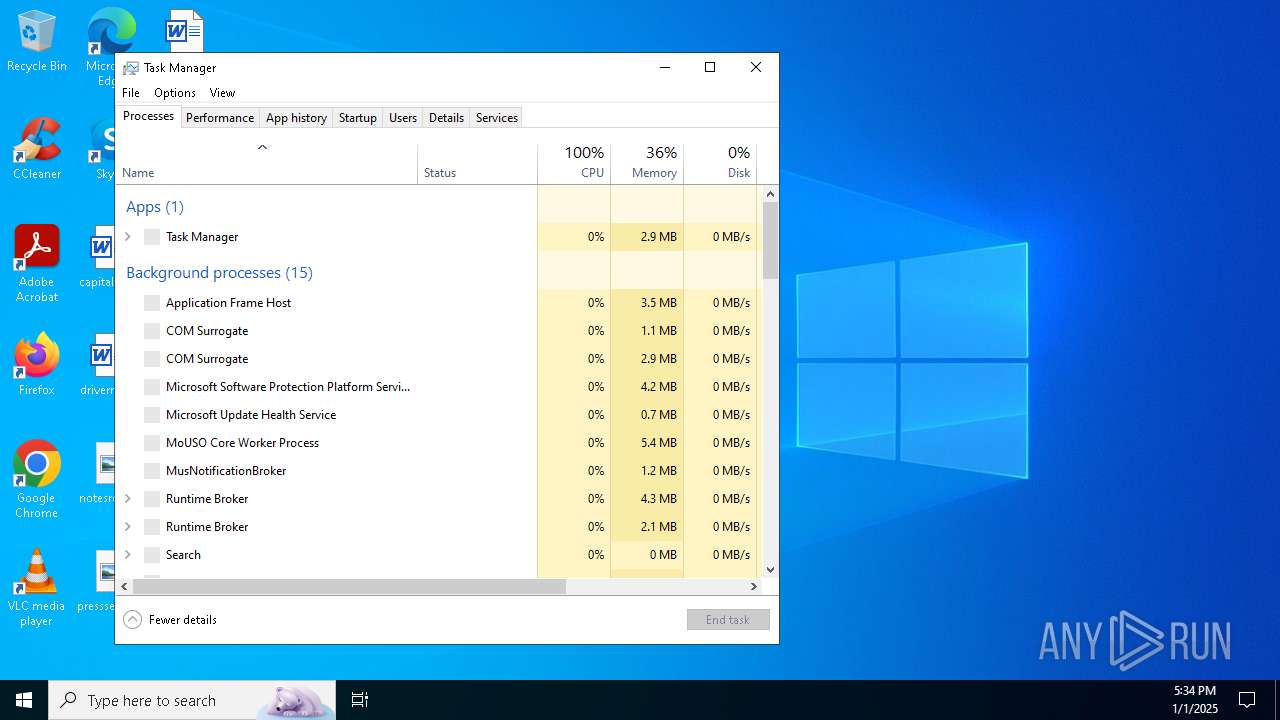
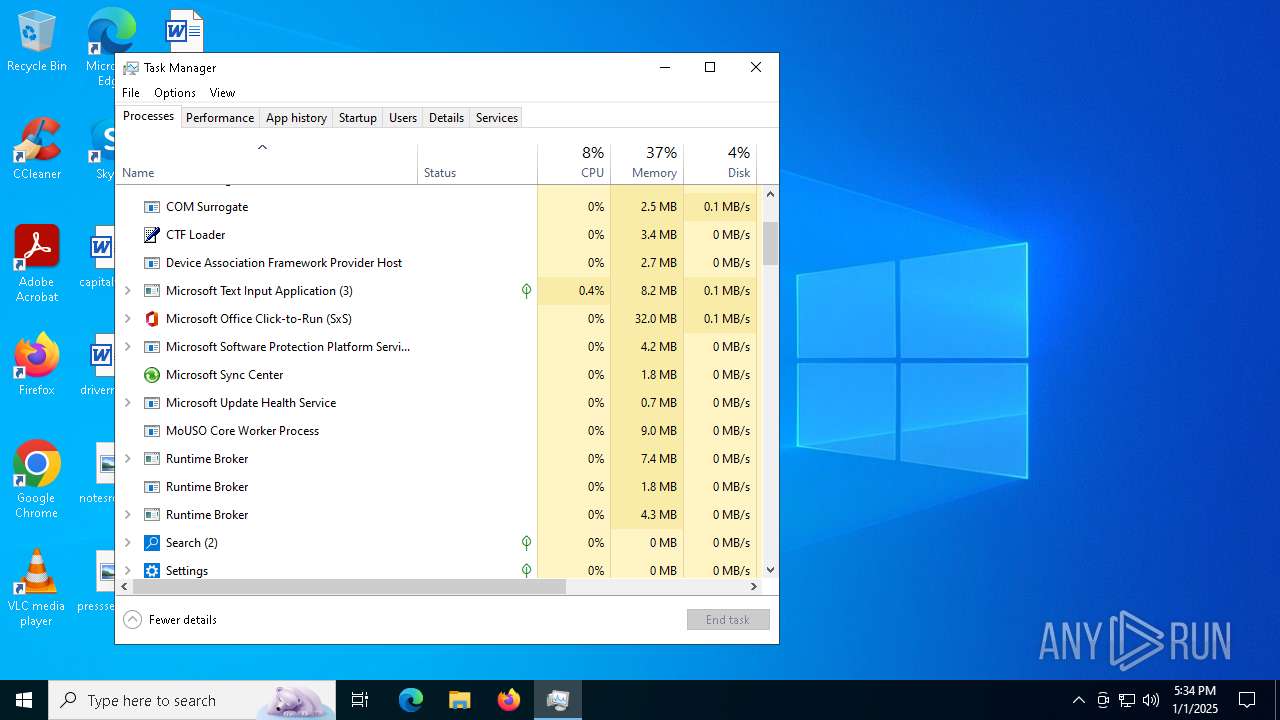
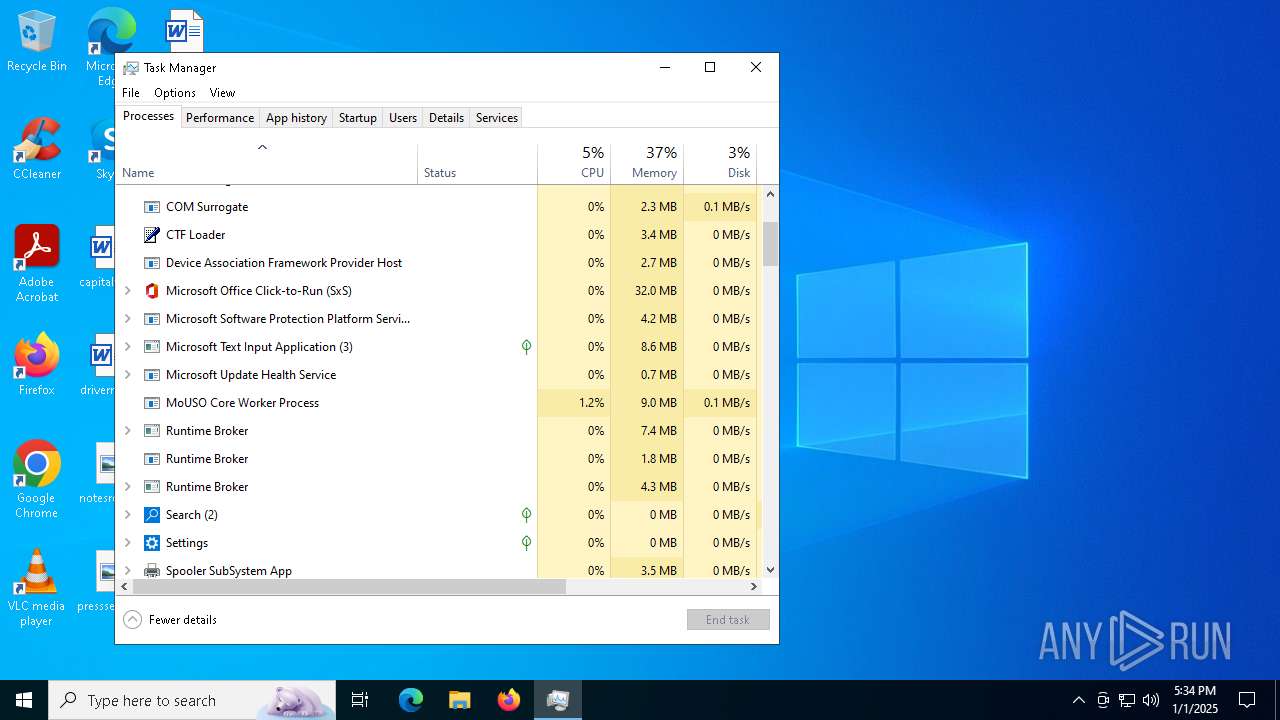
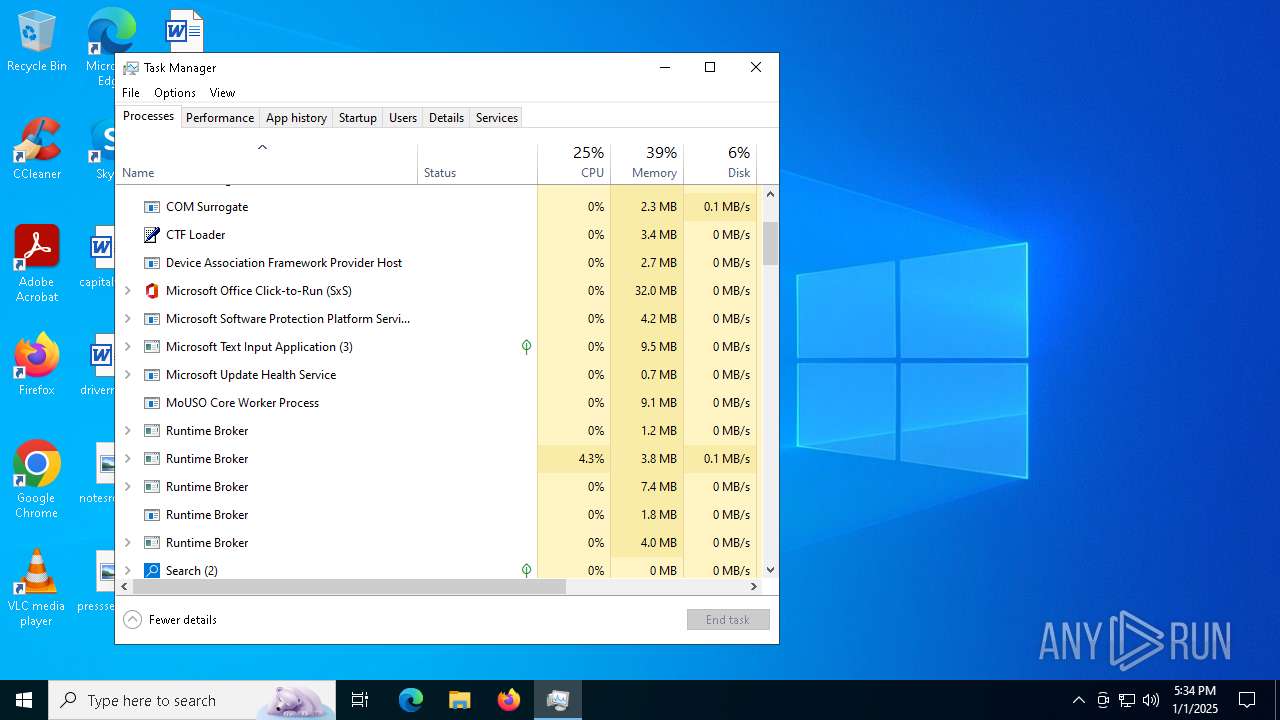
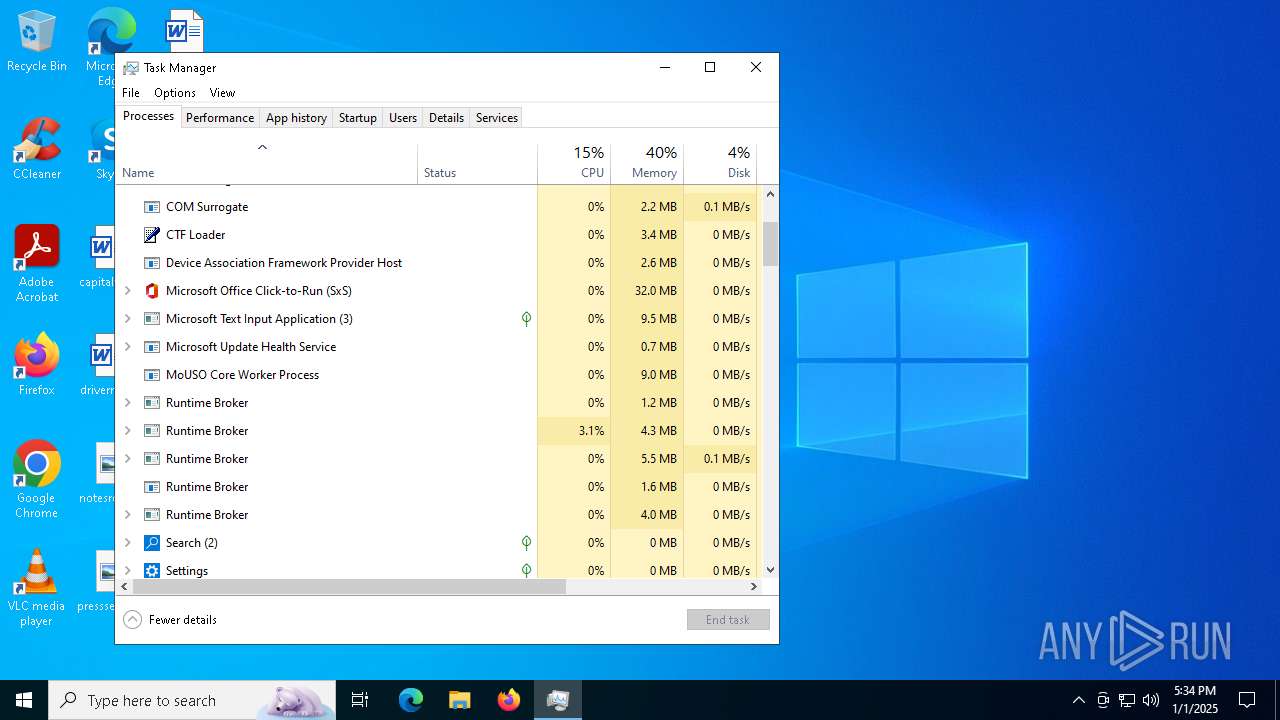
Total processes
148
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3176 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4264 | "C:\Users\admin\Desktop\CoreRootKit.exe" | C:\Users\admin\Desktop\CoreRootKit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CoreRootKit Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1467 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5056 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | C:\WINDOWS\system32\WerFault.exe -u -p 4488 -s 8100 | C:\Windows\System32\WerFault.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6688 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7100 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 7144 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
18 222
Read events
18 118
Write events
100
Delete events
4
Modification events
| (PID) Process: | (7144) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{07c127b4-c15c-98a0-941a-2547439fdec0}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 01000000B11D5758735CDB01 | |||
| (PID) Process: | (7144) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (7144) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_AppUsageData |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (7144) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_TargetedContentTiles |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (5892) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31153267 | |||
| (PID) Process: | (5892) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (3524) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (3524) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | delete value | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (3524) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | write | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (3524) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
51
Text files
114
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Explorer.EXE_e79b52ce07f3db56623275c5534c8742842a35_a6883b46_396cee7a-9e34-4d6c-9709-369bebbf78ad\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6156 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\explorer.exe.4488.dmp | — | |
MD5:— | SHA256:— | |||
| 3524 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\Swi4yFavETfuSZ9mHxnUvb4UdTw[1].js | binary | |
MD5:B2C3CBF8A1D940D6C83D59A67486675C | SHA256:08EA9109346E9018ED50567503D2C141F7A84CFDE80EB25E97FDDCFE270BAA67 | |||
| 3524 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\AptopUBu7_oVDubJxwvaIprW-lI[1].css | text | |
MD5:4E0E75684C84C0102CED12948B95609B | SHA256:4D18E491B2DE4DA34F6C15F0574911613E902F791FE72501E4404802760D1BCA | |||
| 6156 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5566.tmp.dmp | binary | |
MD5:4F6B414B17013D67A3EC4470BFD02058 | SHA256:9445402A9FF1010230C44E1EE2902856920723DD960ACB856B8A2BABA8A5AB31 | |||
| 6156 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5C6C.tmp.WERInternalMetadata.xml | xml | |
MD5:FB6219D41DDB3264B990492B356F9F0D | SHA256:1E9B6CBF5A31E949F511F54D5C4D0CA2A8EF502EC88B41B5F1893EDA6C9906F8 | |||
| 5892 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:432E401C4485823DFD8244AA42F107C9 | SHA256:C7DFF6924661A6CD1DBBCCBF87D91B80A964614114E45AC0E80643318201A616 | |||
| 6156 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5C8D.tmp.xml | xml | |
MD5:F598F839805F0BBC80B2434BA287D4DC | SHA256:CC7093E64F4C63C6A68787BBA65D1E176B571628705AC68CF1D5D2DF664591A8 | |||
| 3524 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\95d9a2a97a42f02325559b453ba7f8fe839baa18.tbres | binary | |
MD5:7C505A203B4AE218D334528E10DBFD33 | SHA256:CCD296C4F9491494D74F1B8442E810653AB6D8F053A218154BA62615844B1884 | |||
| 3524 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:9DA8BCDB31492A355490870B6F5982AD | SHA256:B701BE190B0D22A85E268A130DE889612C3FBA5C278A153C69BE8A3E24FEBF26 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
45
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6244 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
6312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 418 b | whitelisted |
3928 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
6312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4308 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |