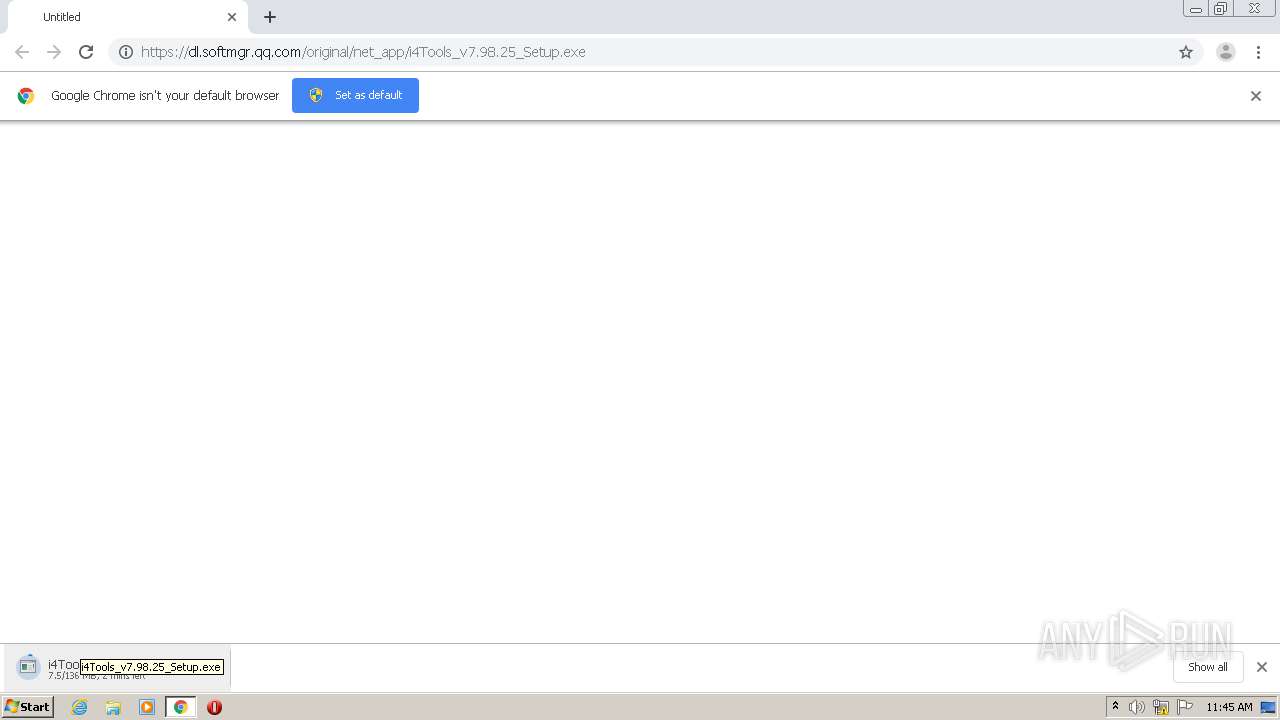
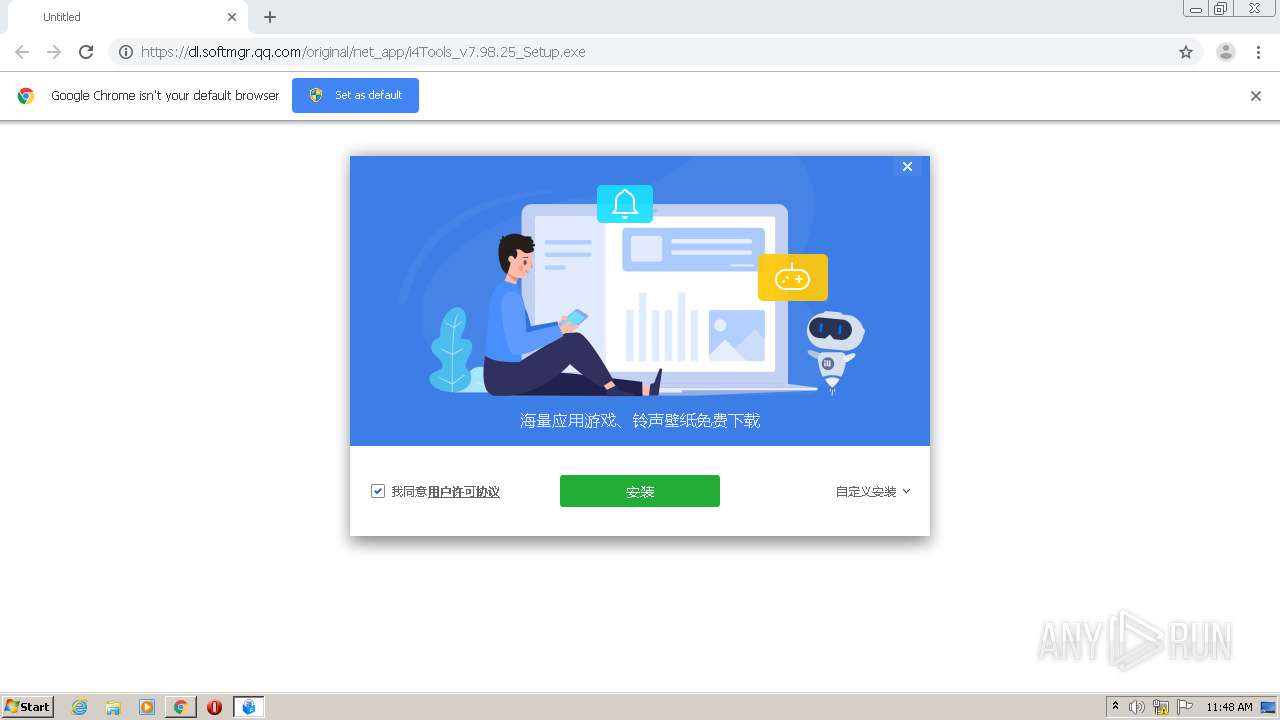
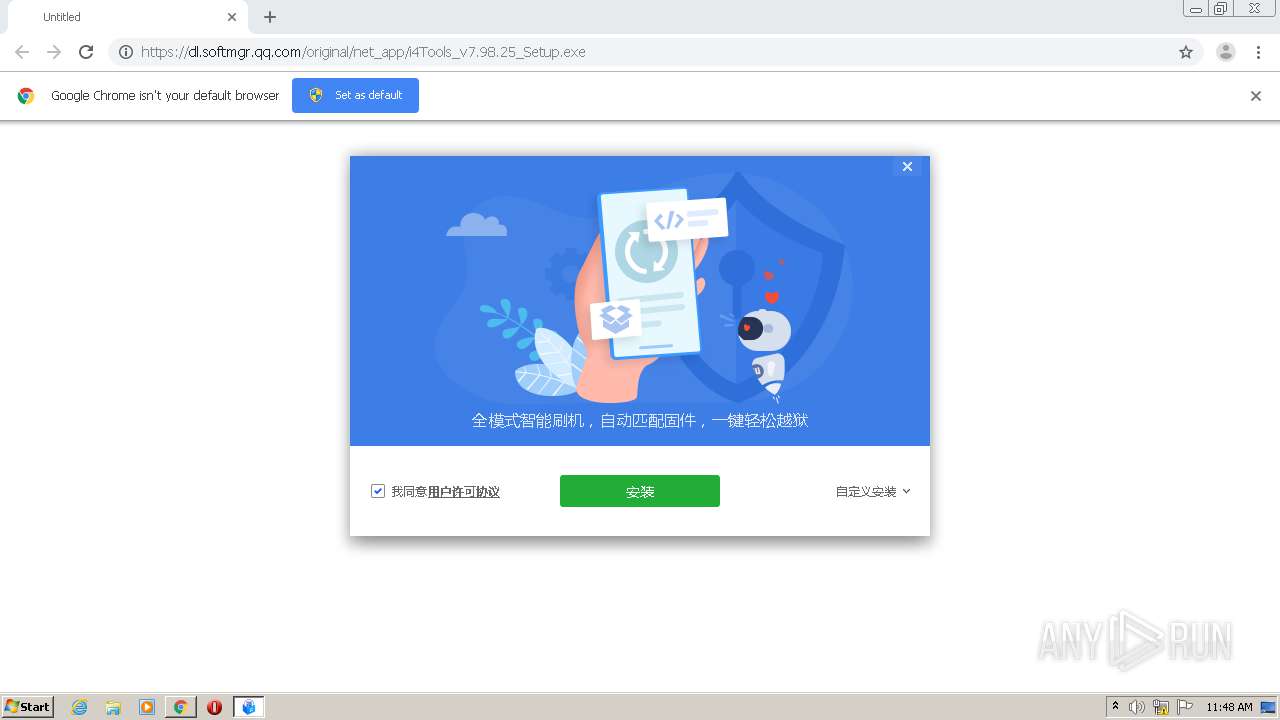
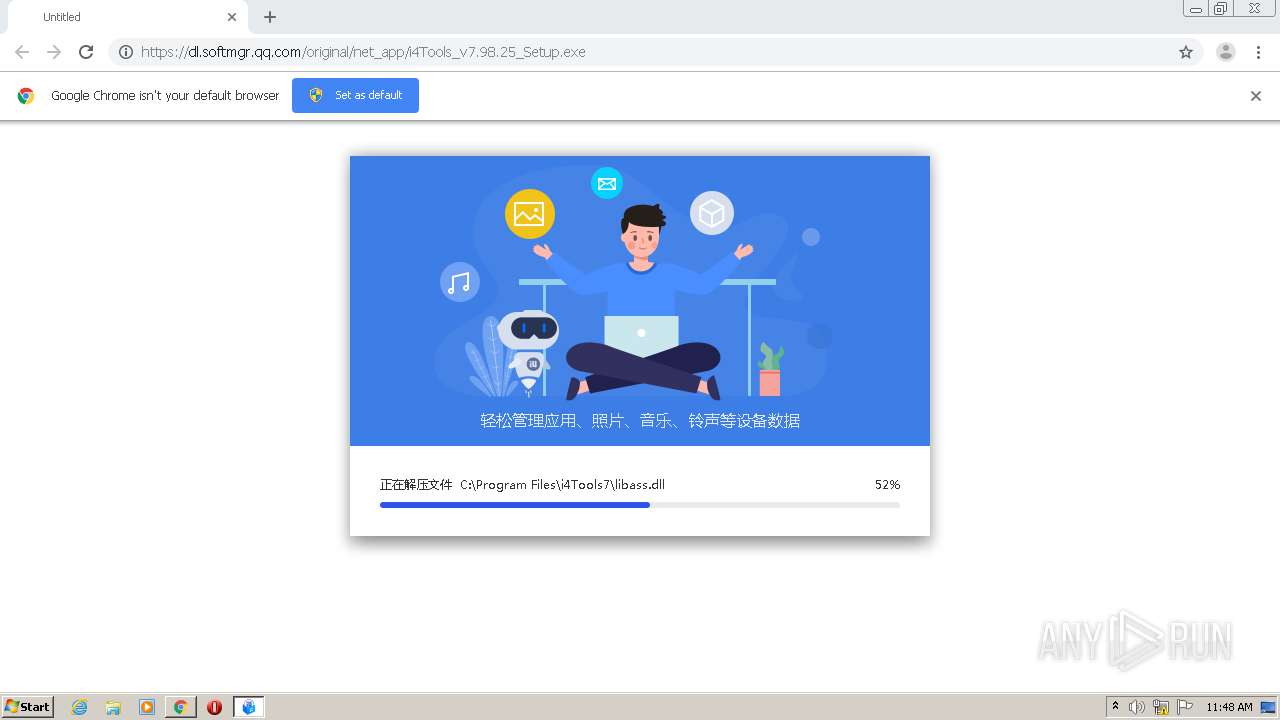
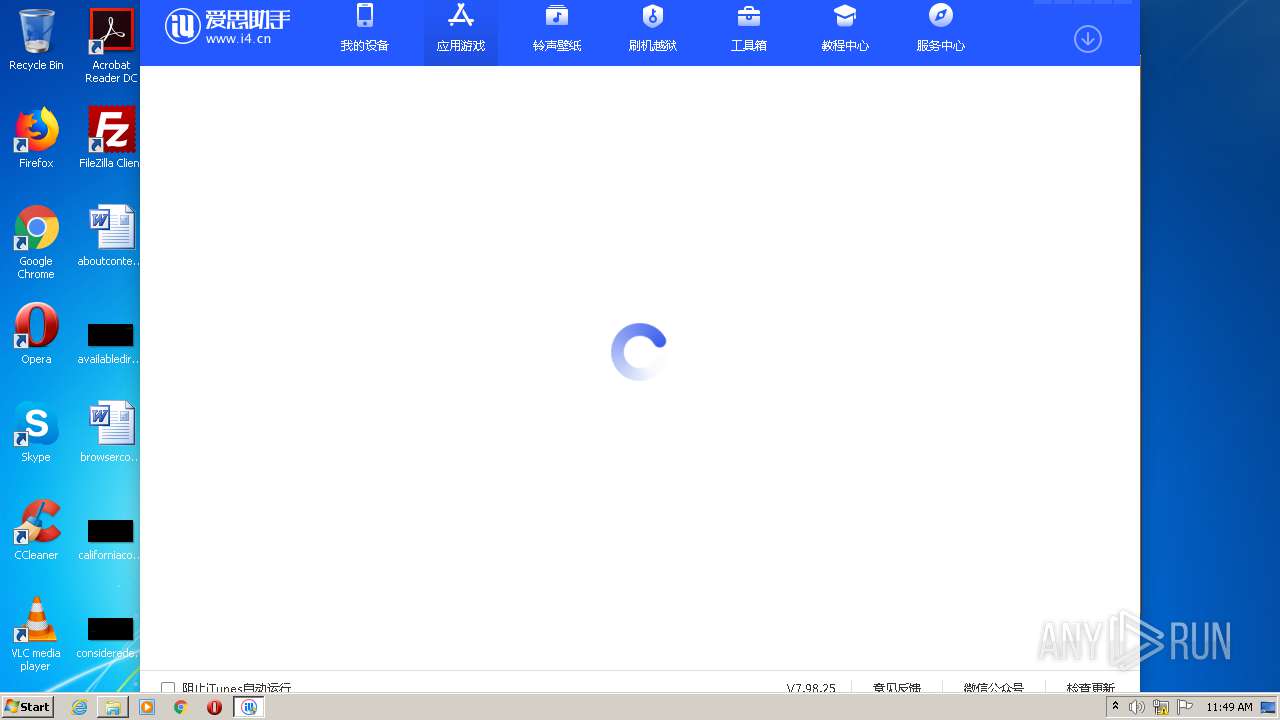
| URL: | https://dl.softmgr.qq.com/original/net_app/i4Tools_v7.98.25_Setup.exe |
| Full analysis: | https://app.any.run/tasks/e7fb733e-3b91-4c89-b9f3-77a957d084a1 |
| Verdict: | Malicious activity |
| Analysis date: | December 29, 2020, 11:44:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D29E5242C09D0A5DD292650B02005667 |
| SHA1: | 63DEB4A1B6D17C18CF1EEF5AEA6A715B4235F866 |
| SHA256: | 5A48440A3DCA0D3549EF1A8871981C9B426D8754B5B12954DDC4DFCF9F0DDA5A |
| SSDEEP: | 3:N8RpNf0K6XeEt68ZKKJxXXA:2DNb6Xew68ZRrA |
MALICIOUS
Application was dropped or rewritten from another process
- i4Tools_v7.98.25_Setup.exe (PID: 2708)
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
- HeicViewer.exe (PID: 3000)
- i4Tools.exe (PID: 3400)
Loads dropped or rewritten executable
- i4Tools.exe (PID: 3400)
- HeicViewer.exe (PID: 3000)
SUSPICIOUS
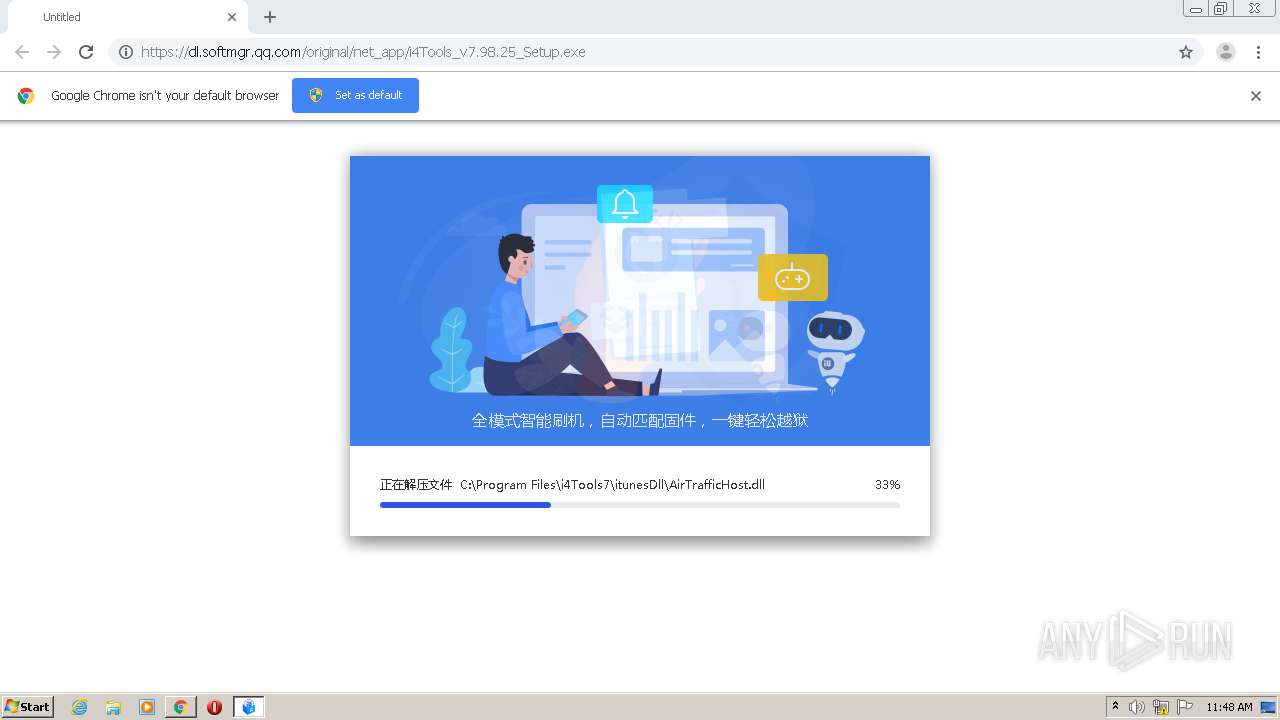
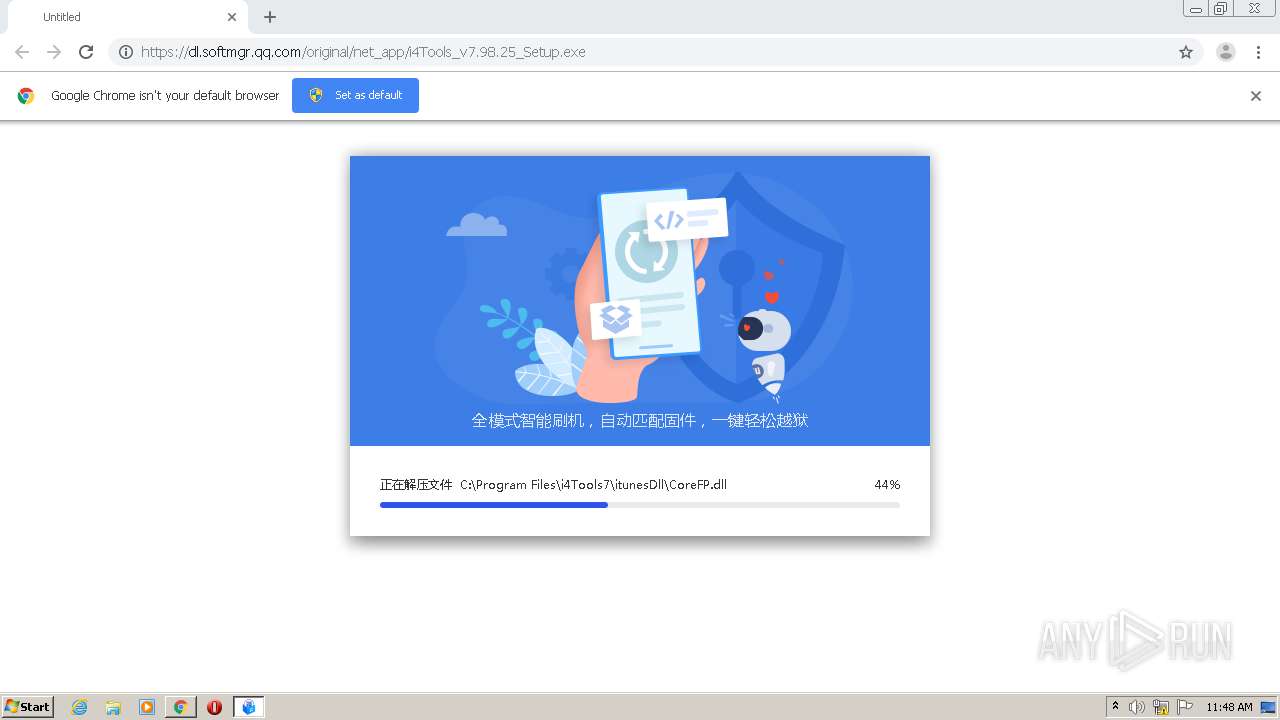
Executable content was dropped or overwritten
- chrome.exe (PID: 2348)
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
Drops a file with a compile date too recent
- chrome.exe (PID: 2348)
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
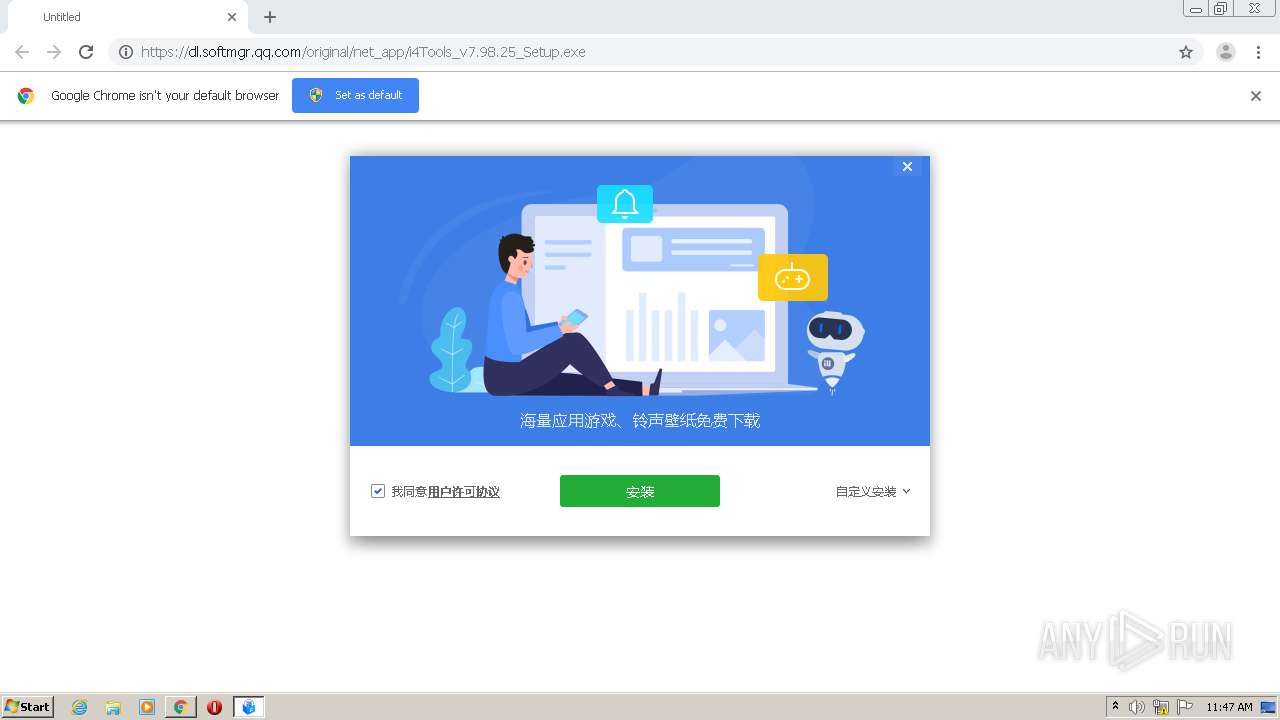
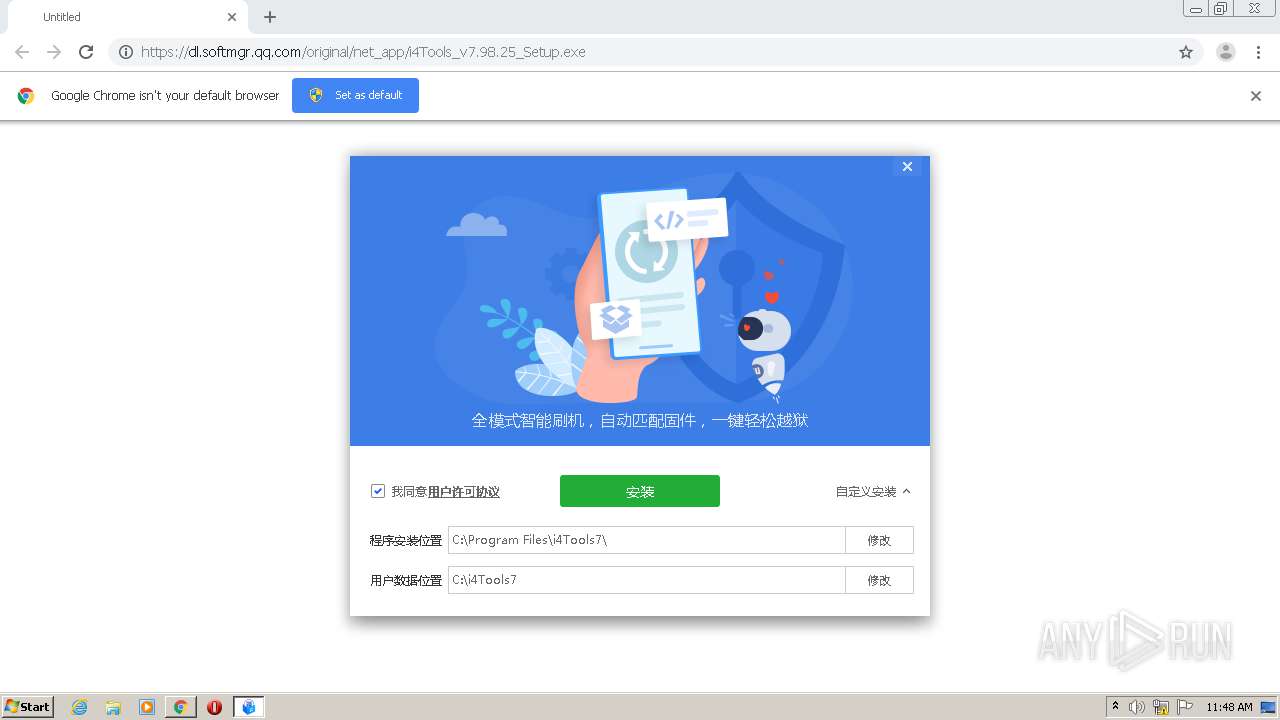
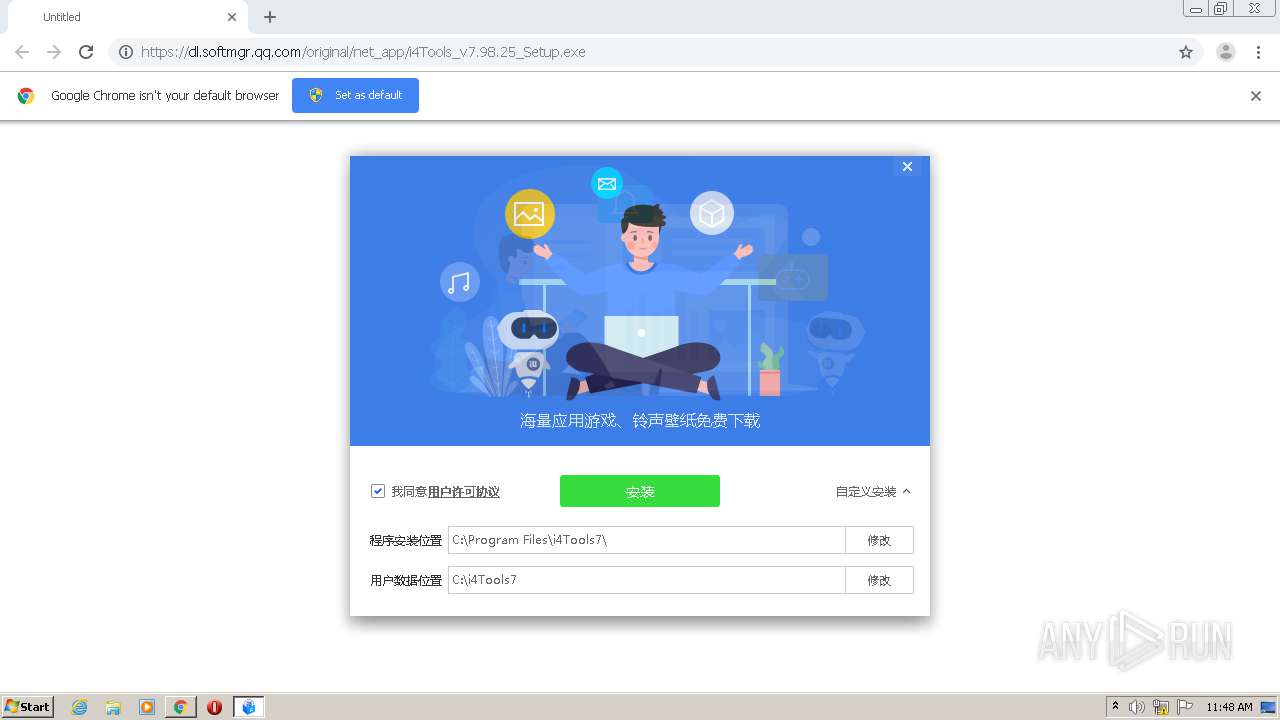
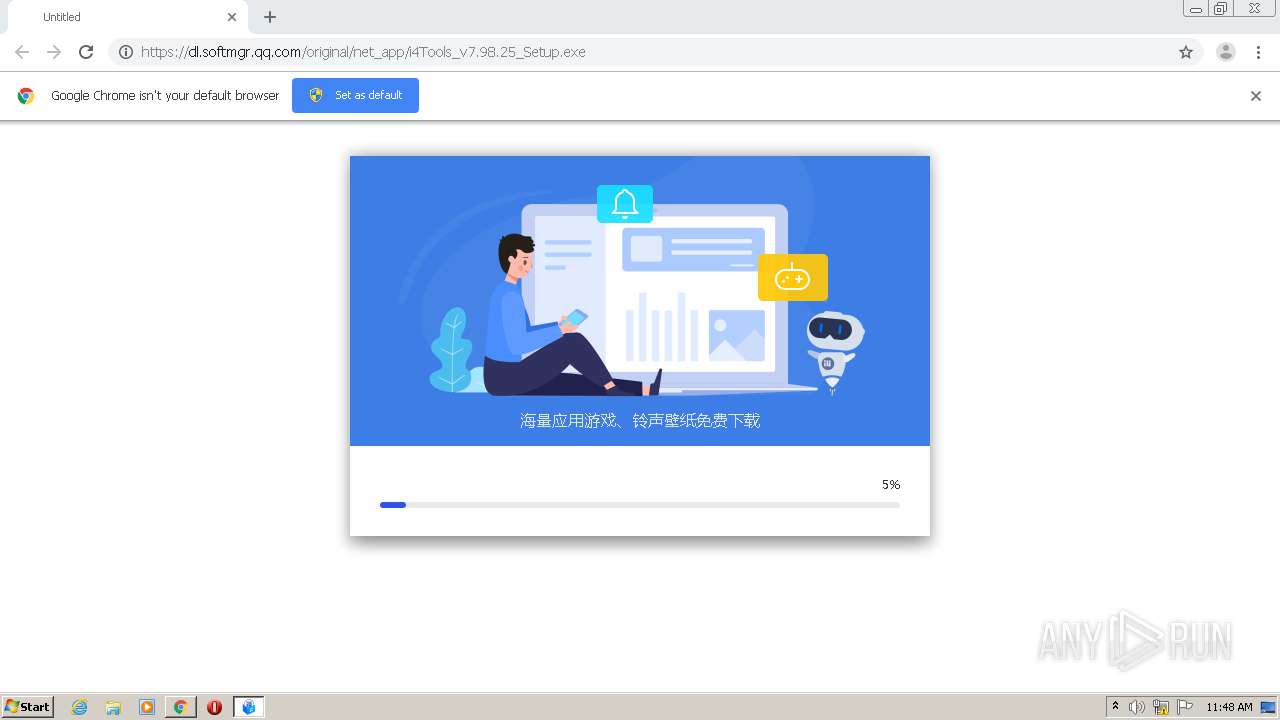
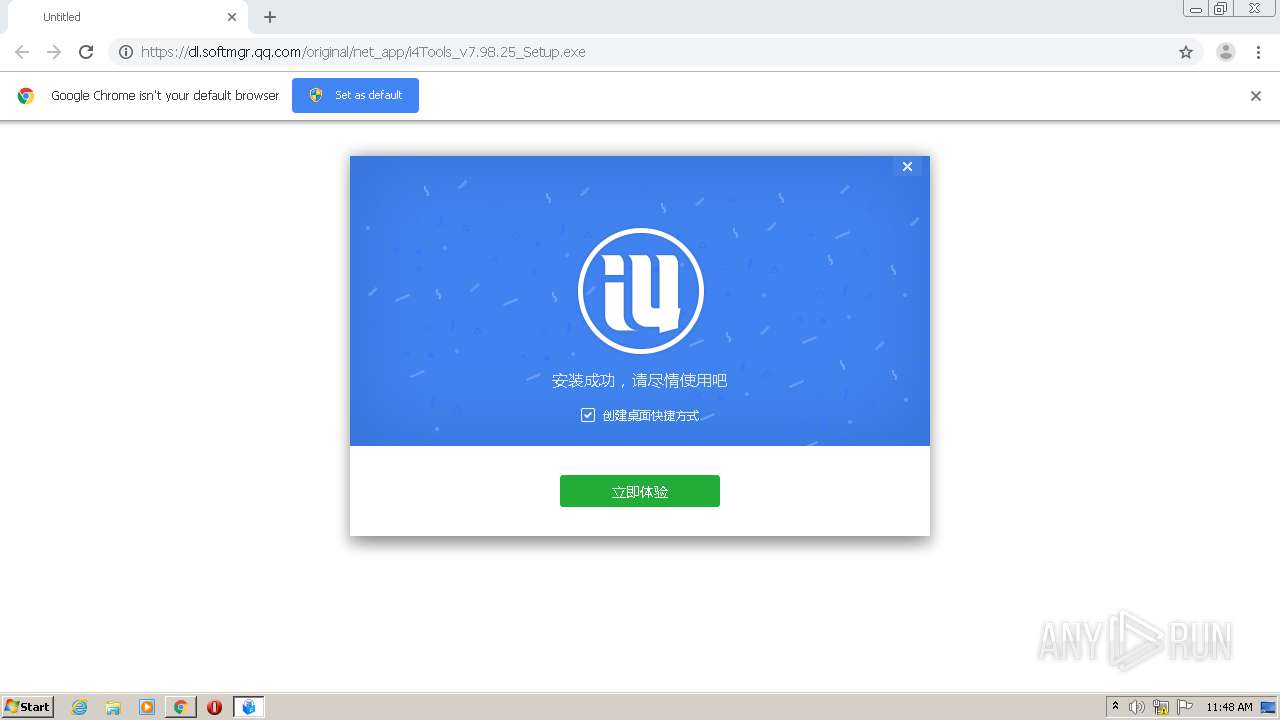
Creates a software uninstall entry
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
Creates a directory in Program Files
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
- i4Tools.exe (PID: 3400)
Creates files in the program directory
- i4Tools.exe (PID: 3400)
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
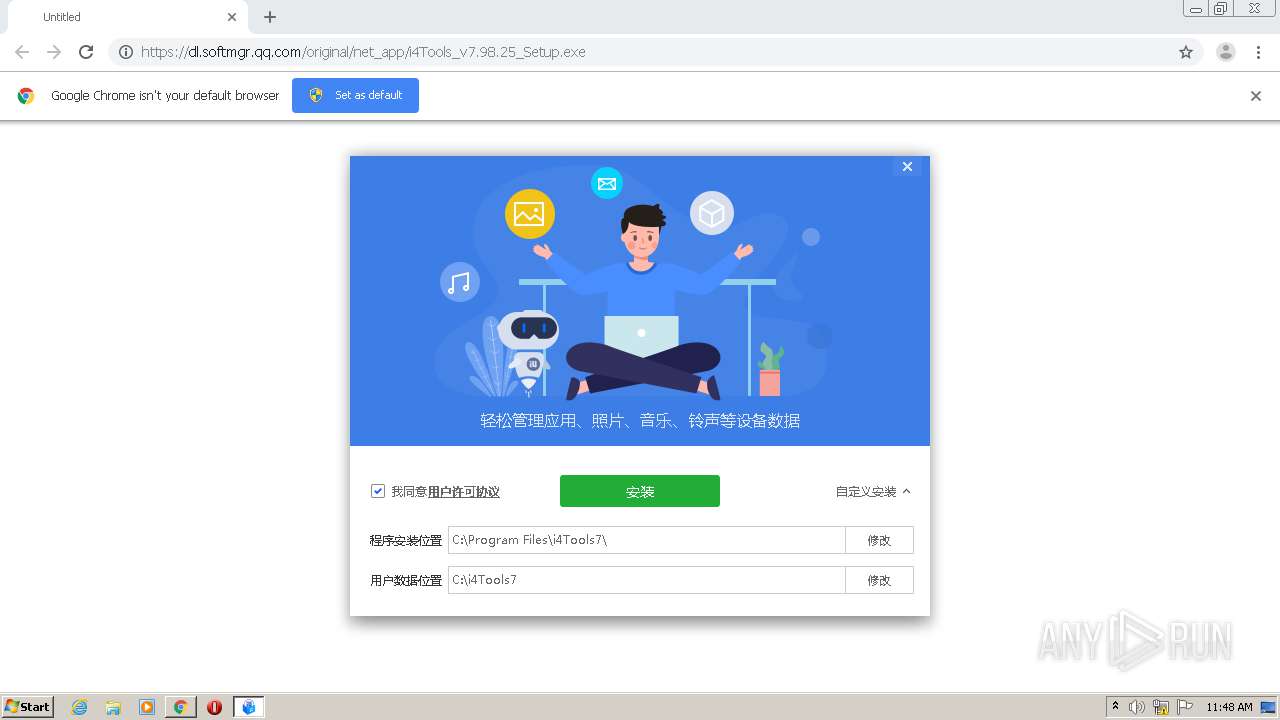
Changes default file association
- i4Tools.exe (PID: 3400)
- HeicViewer.exe (PID: 3000)
Drops a file with too old compile date
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
Drops a file that was compiled in debug mode
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
INFO
Application launched itself
- chrome.exe (PID: 2348)
Reads the hosts file
- chrome.exe (PID: 780)
- chrome.exe (PID: 2348)
Dropped object may contain Bitcoin addresses
- i4Tools_v7.98.25_Setup.exe (PID: 3640)
Manual execution by user
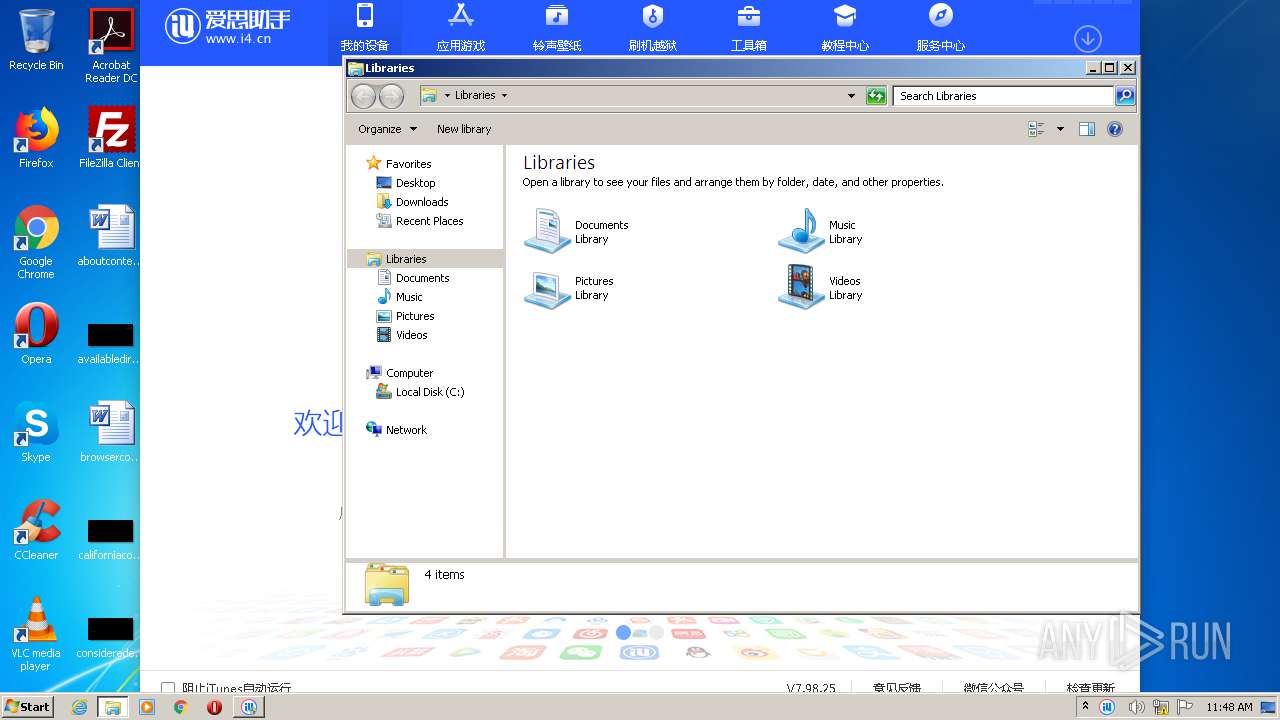
- explorer.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
15
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16227609021151277875,9719748417734680192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11755196357566546315 --mojo-platform-channel-handle=1464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16227609021151277875,9719748417734680192,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6478748476806980264 --mojo-platform-channel-handle=3352 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2388 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16227609021151277875,9719748417734680192,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587933087546928923 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://dl.softmgr.qq.com/original/net_app/i4Tools_v7.98.25_Setup.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\Downloads\i4Tools_v7.98.25_Setup.exe" | C:\Users\admin\Downloads\i4Tools_v7.98.25_Setup.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebda9d0,0x6ebda9e0,0x6ebda9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3000 | HeicViewer.exe /reg | C:\Program Files\i4Tools7\HeicViewer.exe | — | i4Tools.exe | |||||||||||
User: admin Integrity Level: HIGH Description: HEIC查看器 Exit code: 0 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16227609021151277875,9719748417734680192,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7982443821518691530 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 248
Read events
1 140
Write events
105
Delete events
3
Modification events
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2348-13253715889897375 |
Value: 259 | |||
Executable files
213
Suspicious files
19
Text files
166
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FEB16B2-92C.pma | — | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\99f89e3b-64ee-4859-84e6-d8ac3416372e.tmp | — | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15044f.TMP | text | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150681.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
36
DNS requests
26
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/rYjQj2aa | CN | — | — | suspicious |
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/UrMFVraa?pc_vs=7.98.25.016 | CN | — | — | suspicious |
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/index_force.action?pcver=7.98.25.016&guid={02E966E9-28BF-4FCA-BCA5-ABD8FFDC6E52} | CN | — | — | suspicious |
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/QRni2qaa?pc_vs=7.98.25.016 | CN | — | — | suspicious |
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/uE7nymaa | CN | — | — | suspicious |
3640 | i4Tools_v7.98.25_Setup.exe | POST | — | 163.171.128.148:80 | http://ios.pclog.i4.cn/log/info/uploadLog.go?type=2 | US | — | — | malicious |
3400 | i4Tools.exe | POST | — | 163.171.128.148:80 | http://ios.pclog.i4.cn/log/info/uploadLog.go?type=3 | US | — | — | malicious |
3400 | i4Tools.exe | GET | — | 114.55.188.99:80 | http://url.i4.cn/MfaUV3aa | CN | — | — | suspicious |
3400 | i4Tools.exe | POST | 200 | 163.171.128.148:80 | http://ios.pclog.i4.cn/log/info/uploadLog.go?type=1 | US | binary | 1 b | malicious |
3400 | i4Tools.exe | POST | 200 | 163.171.128.148:80 | http://ios.pclog.i4.cn/log/info/uploadLog.go?type=3 | US | binary | 1 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
780 | chrome.exe | 108.177.8.84:443 | accounts.google.com | Google Inc. | US | unknown |
780 | chrome.exe | 203.205.137.101:443 | dl.softmgr.qq.com | Tencent Building, Kejizhongyi Avenue | CN | malicious |
780 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
780 | chrome.exe | 119.28.164.149:443 | dl.softmgr.qq.com | Tencent Cloud Computing (Beijing) Co., Ltd | CN | suspicious |
780 | chrome.exe | 74.125.198.113:443 | clients1.google.com | Google Inc. | US | whitelisted |
3640 | i4Tools_v7.98.25_Setup.exe | 163.171.128.148:80 | ios.pclog.i4.cn | — | US | malicious |
3400 | i4Tools.exe | 163.171.128.148:80 | ios.pclog.i4.cn | — | US | malicious |
— | — | 163.171.128.148:80 | ios.pclog.i4.cn | — | US | malicious |
3400 | i4Tools.exe | 114.55.188.99:80 | url.i4.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
780 | chrome.exe | 74.125.198.139:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.softmgr.qq.com |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ios.pclog.i4.cn |
| malicious |
app4.i4.cn |
| unknown |
url.i4.cn |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
3400 | i4Tools.exe | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET INFO Double User-Agent (User-Agent User-Agent) |
9 ETPRO signatures available at the full report
Process | Message |
|---|---|
i4Tools.exe | QCoreApplication::applicationDirPath: Please instantiate the QApplication object first
|
i4Tools.exe | localhost server bind port succed! |
i4Tools.exe | MainWindows Size Mismatch: QRect(0,0 1060x780)
|
i4Tools.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 560x310+350+151 on QWidgetWindow/'InstallItunesDialogClassWindow'. Resulting geometry: 560x318+350+151 (frame: 0, 0, 0, 0, custom margin: 0, 0, 0, 0, minimum size: 560x310, maximum size: 560x310).
|
i4Tools.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 560x310+360+191 on QWidgetWindow/'InstallItunesDialogClassWindow'. Resulting geometry: 560x318+360+191 (frame: 0, 0, 0, 0, custom margin: 0, 0, 0, 0, minimum size: 560x310, maximum size: 560x310).
|
i4Tools.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 560x310+360+191 on QWidgetWindow/'InstallItunesDialogClassWindow'. Resulting geometry: 560x318+360+191 (frame: 0, 0, 0, 0, custom margin: 0, 0, 0, 0, minimum size: 560x310, maximum size: 560x310).
|